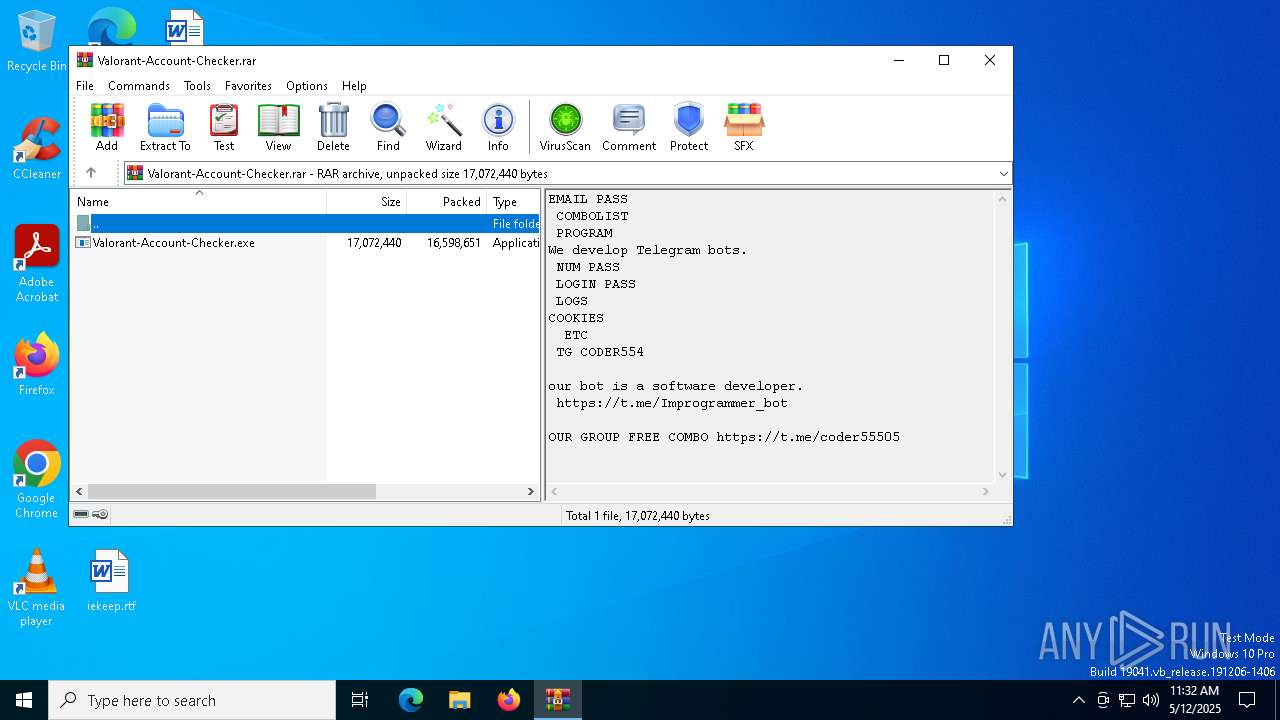
| File name: | Valorant-Account-Checker.rar |
| Full analysis: | https://app.any.run/tasks/ca47f193-5257-4019-872b-c2a36500d787 |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2025, 11:32:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 63235AF0732E9FC2E14A8A688CFA27DD |
| SHA1: | 066C93CCC246AA7A188EA6FF90CDE8A7046458E2 |
| SHA256: | 3D31BBEA70A2CFF0128F3050D9F44E3FC11C59FE8A8807C3C4979C74A79015AD |
| SSDEEP: | 98304:WWRuthTulQmiDt725ZV2QOlQ5EjX61Uiap3kKpgv15acFROx0FlS3XOl6K42a11I:Qkb+dUD2wNC07xya0OfC+FfHbNZ |
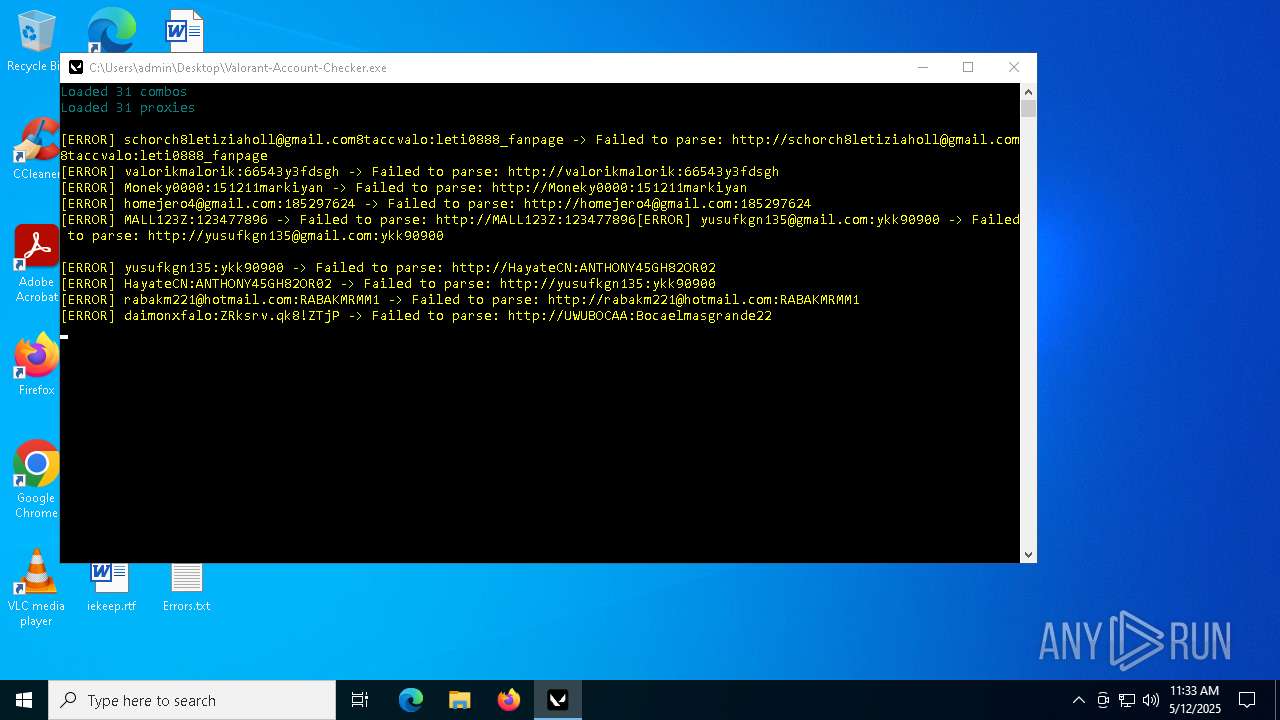
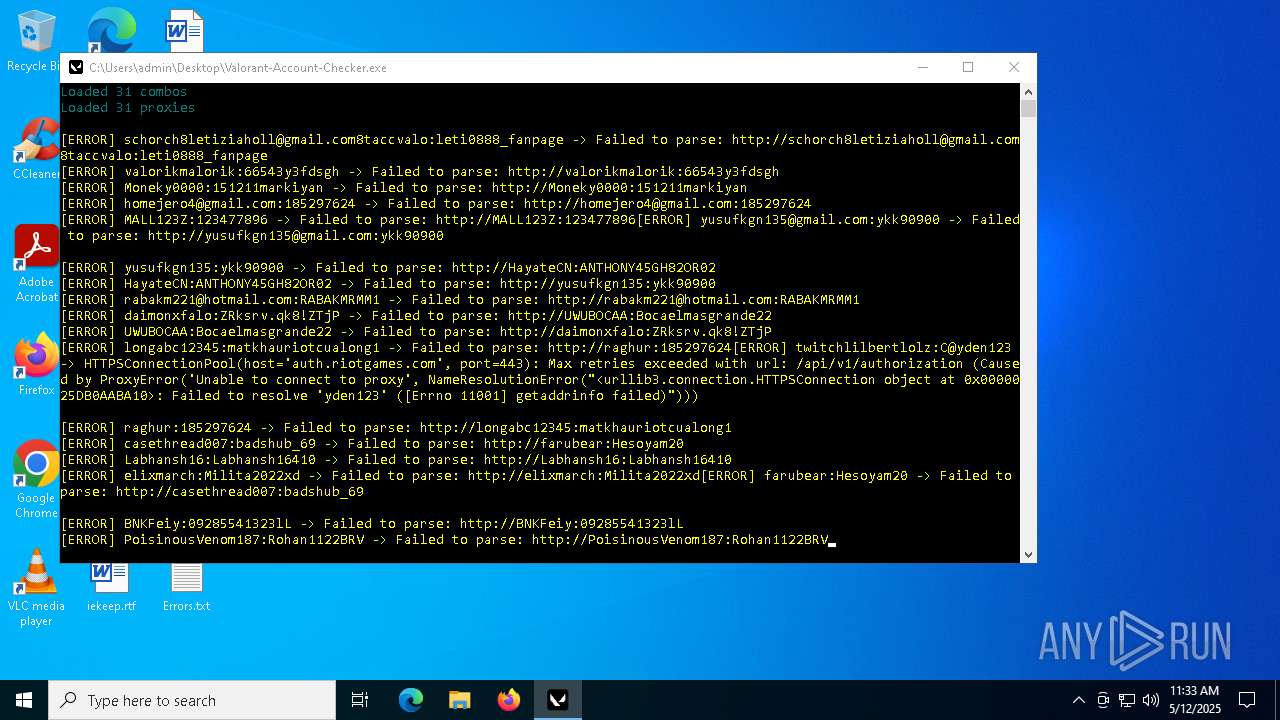
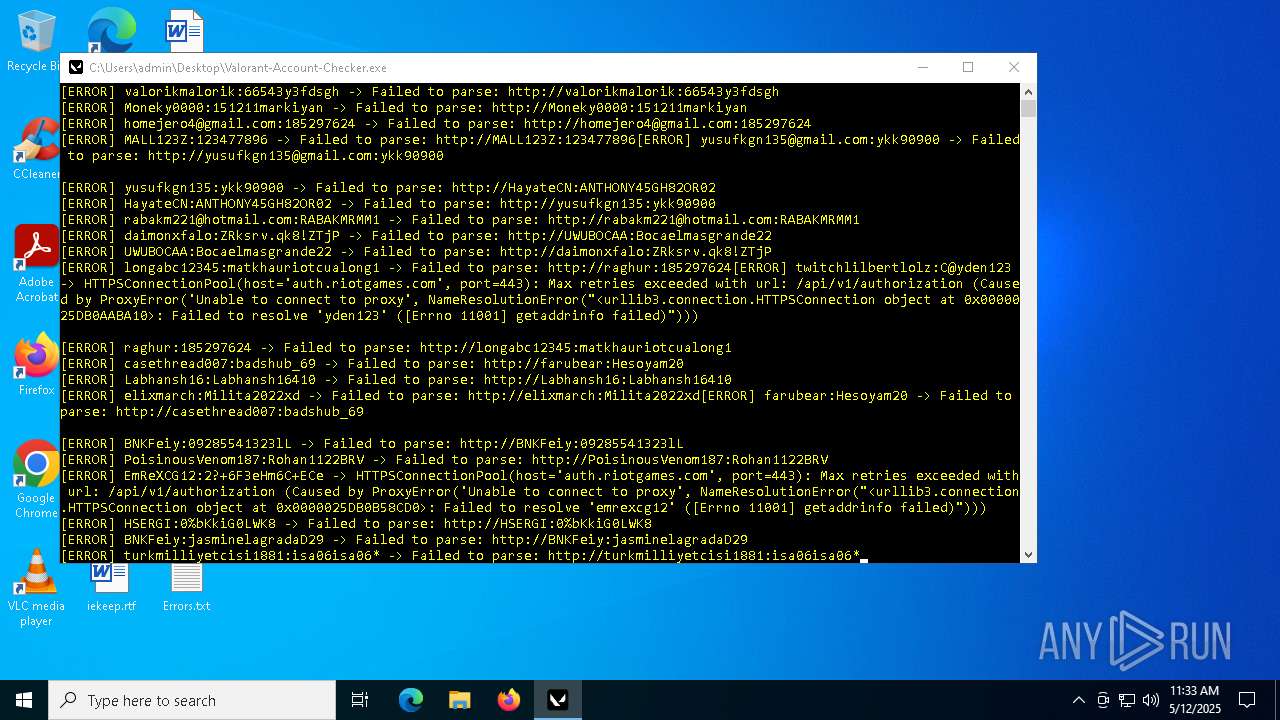
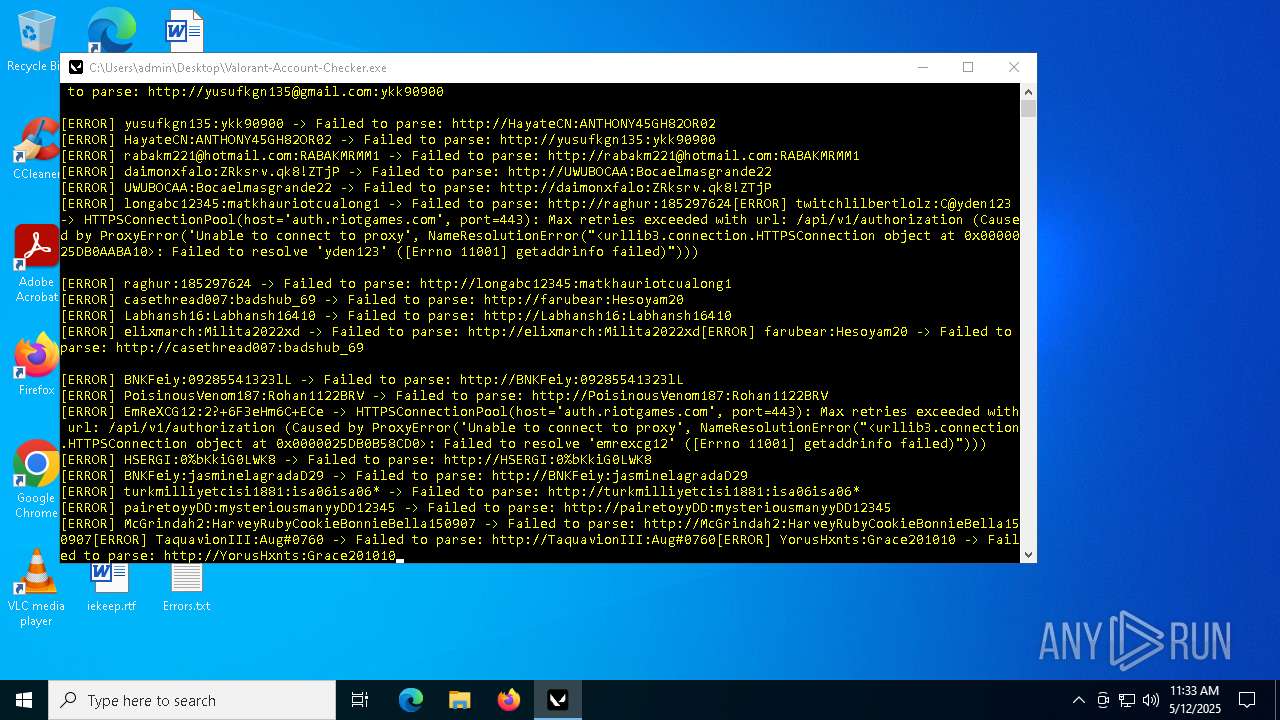
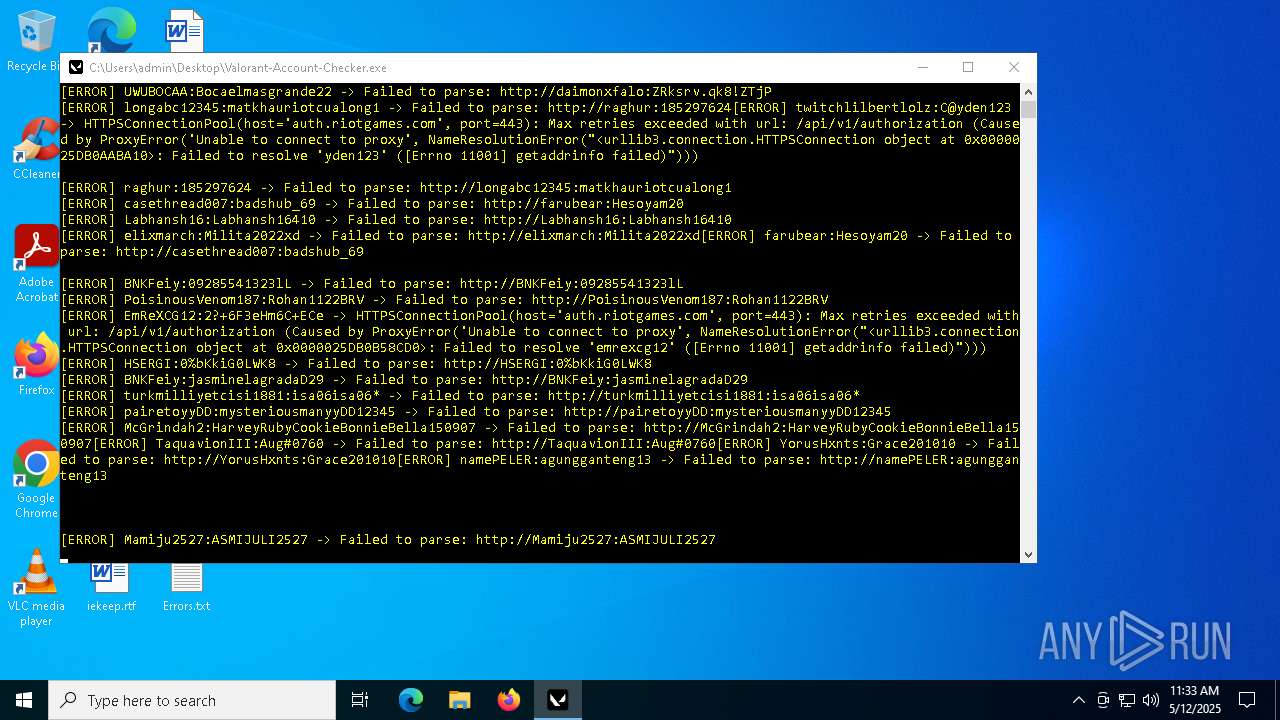
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- Valorant-Account-Checker.exe (PID: 2420)
Process drops legitimate windows executable
- Valorant-Account-Checker.exe (PID: 2420)
Process drops python dynamic module
- Valorant-Account-Checker.exe (PID: 2420)
The process drops C-runtime libraries
- Valorant-Account-Checker.exe (PID: 2420)
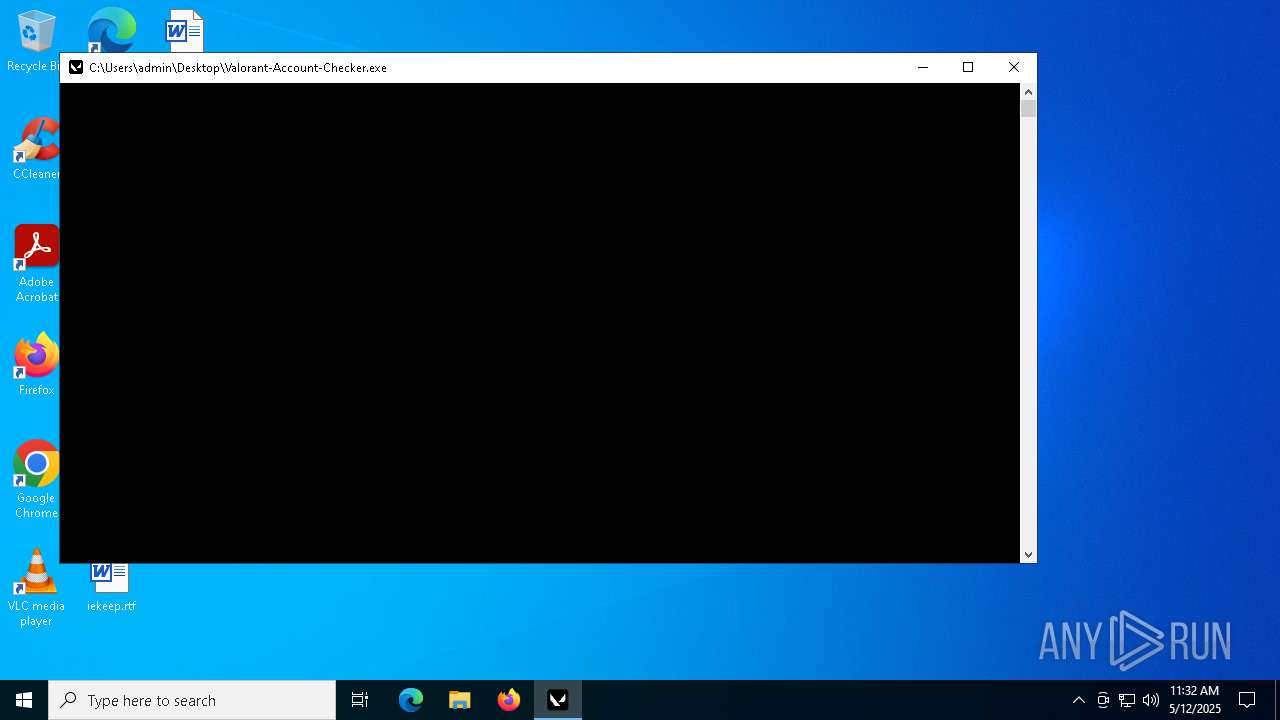
Application launched itself
- Valorant-Account-Checker.exe (PID: 2420)
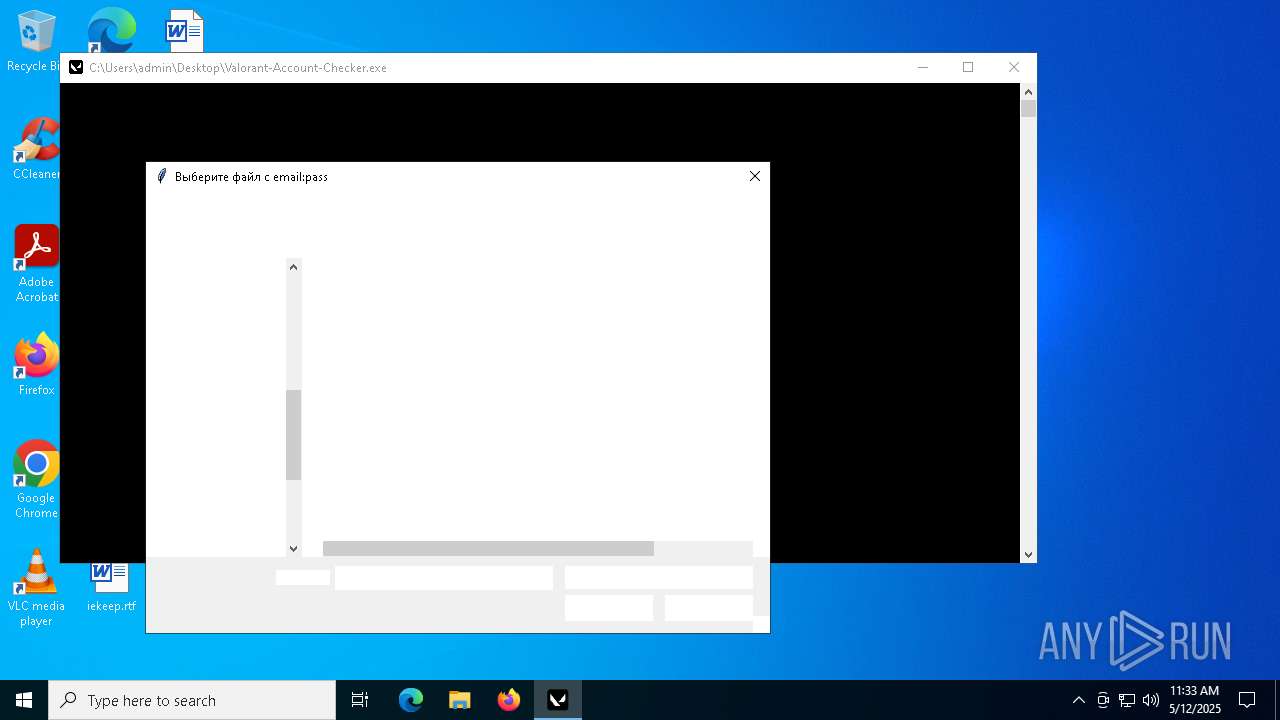
Loads Python modules
- Valorant-Account-Checker.exe (PID: 4120)
Reads security settings of Internet Explorer
- Valorant-Account-Checker.exe (PID: 4120)
Starts CMD.EXE for commands execution
- Valorant-Account-Checker.exe (PID: 4120)
There is functionality for taking screenshot (YARA)
- Valorant-Account-Checker.exe (PID: 4120)
INFO
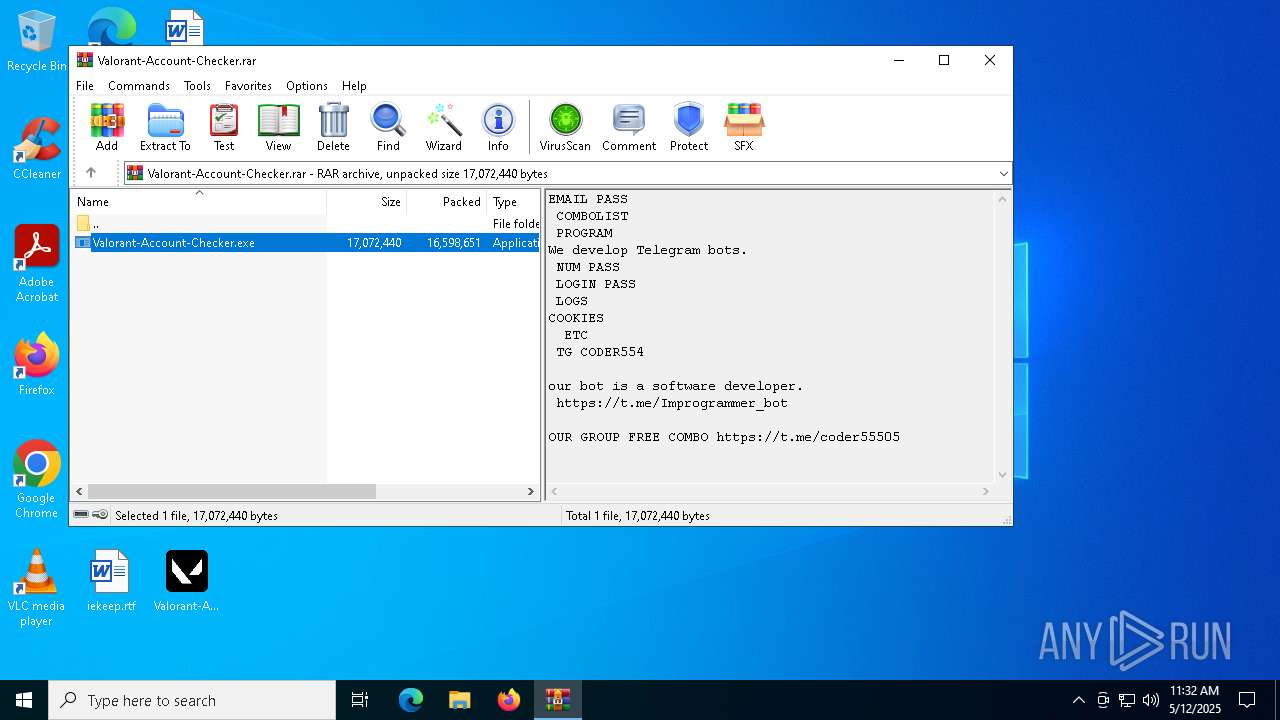
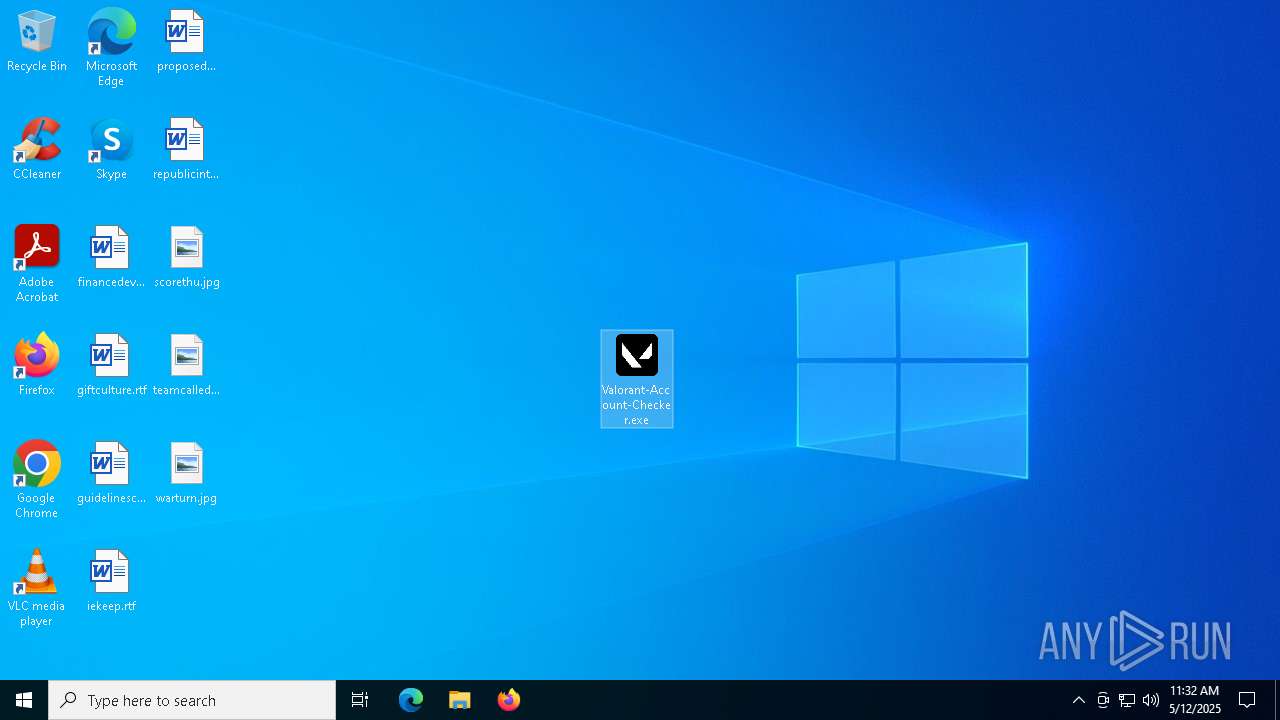
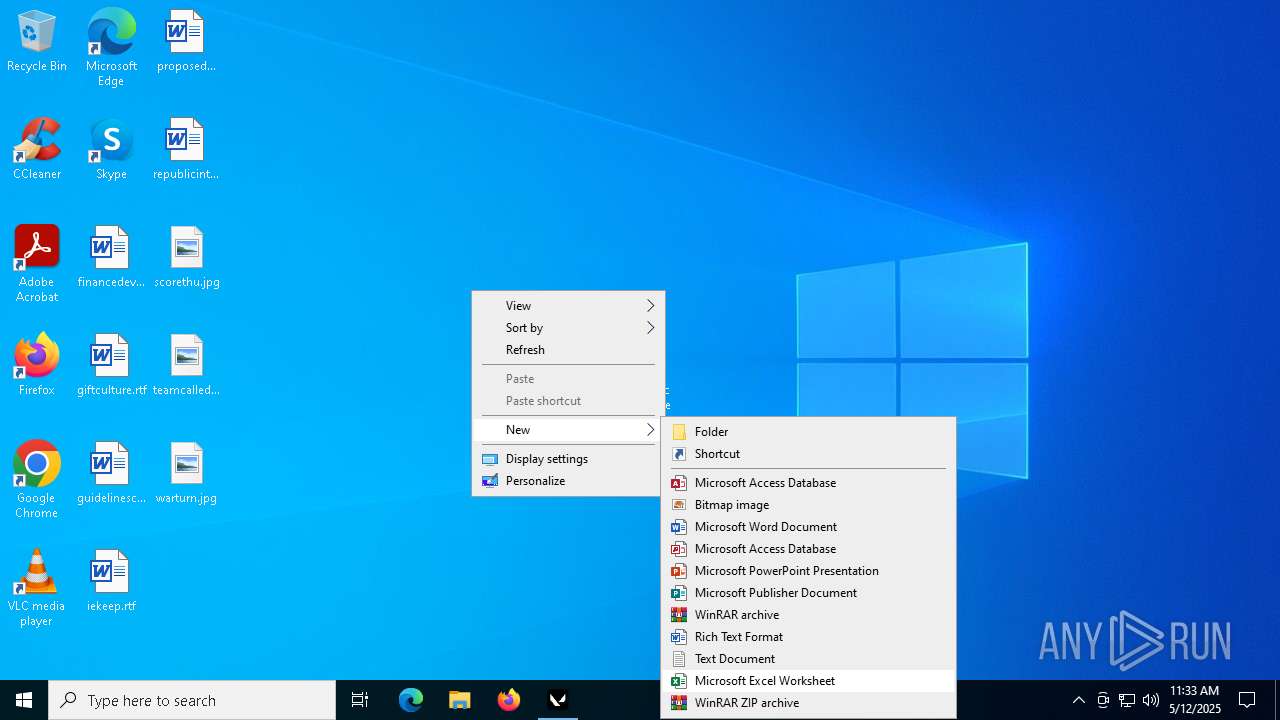
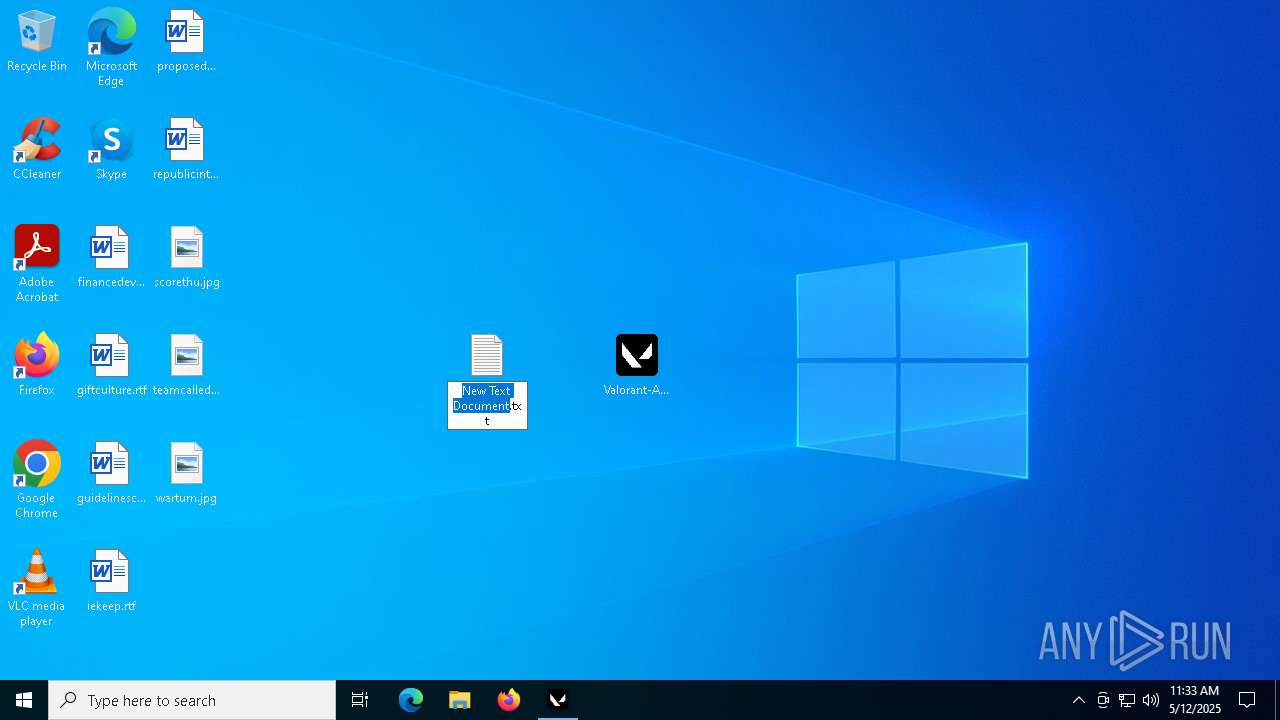
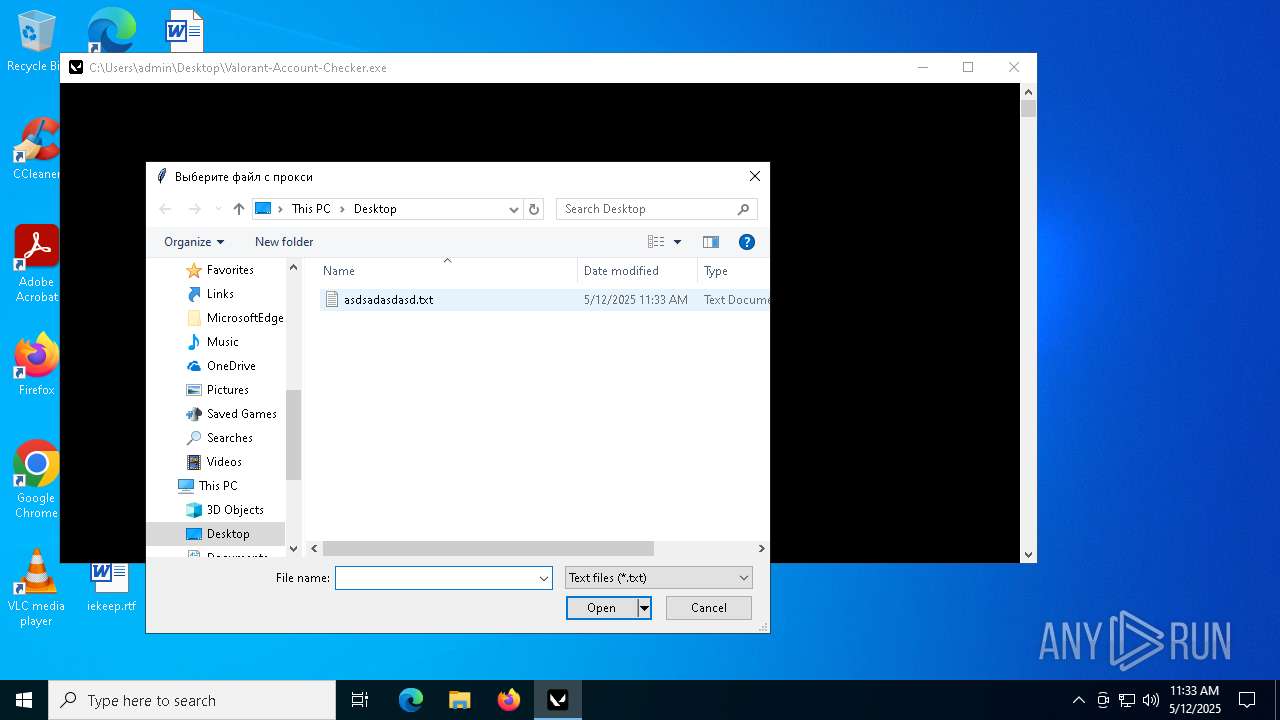
Manual execution by a user
- Valorant-Account-Checker.exe (PID: 2420)
- notepad.exe (PID: 1228)
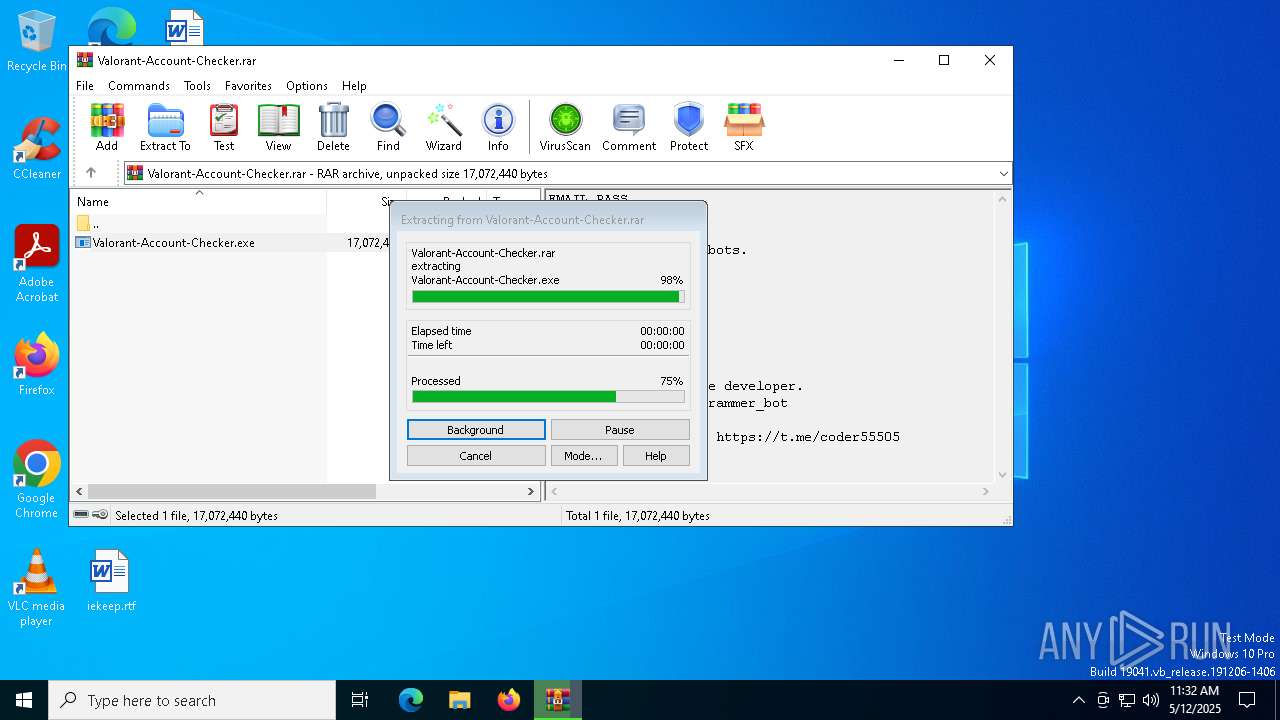
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7012)
Checks supported languages
- Valorant-Account-Checker.exe (PID: 2420)
- Valorant-Account-Checker.exe (PID: 4120)
Reads the computer name
- Valorant-Account-Checker.exe (PID: 2420)
- Valorant-Account-Checker.exe (PID: 4120)
The sample compiled with english language support
- Valorant-Account-Checker.exe (PID: 2420)
Create files in a temporary directory
- Valorant-Account-Checker.exe (PID: 2420)
PyInstaller has been detected (YARA)
- Valorant-Account-Checker.exe (PID: 2420)
- Valorant-Account-Checker.exe (PID: 4120)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1228)
Reads the software policy settings
- slui.exe (PID: 3956)
Checks proxy server information
- Valorant-Account-Checker.exe (PID: 4120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
136
Monitored processes
9
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
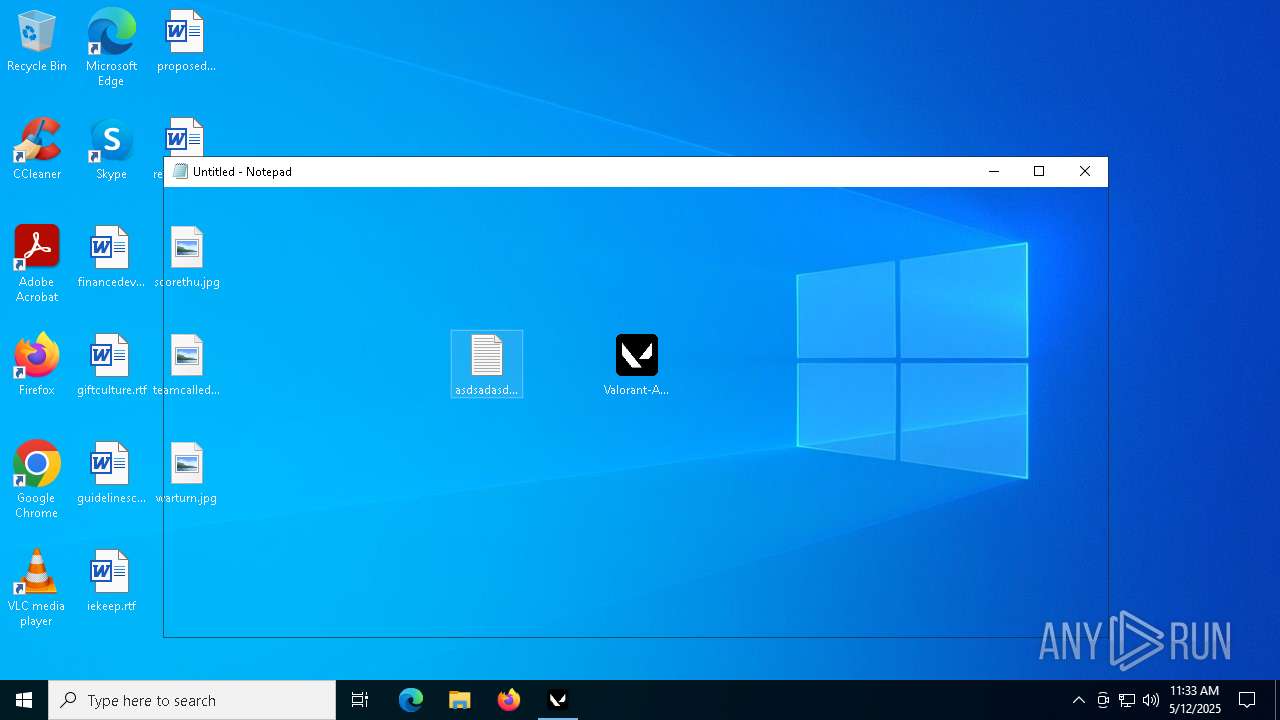
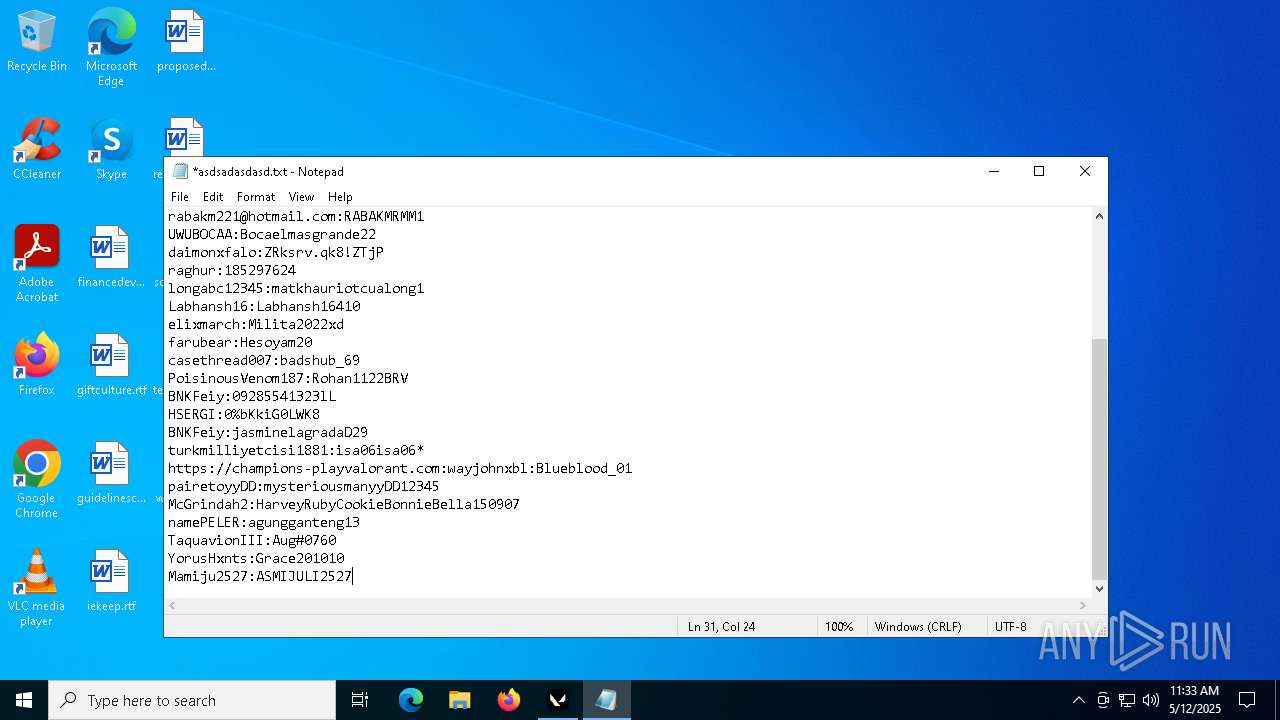
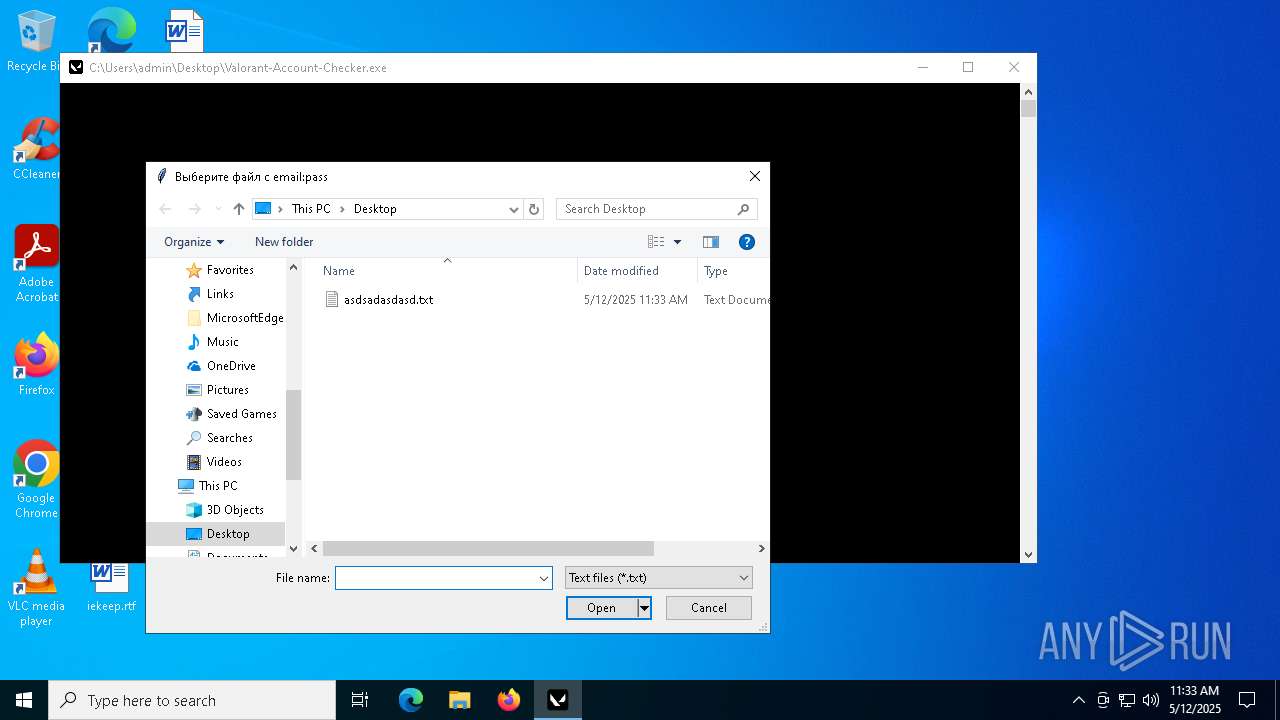
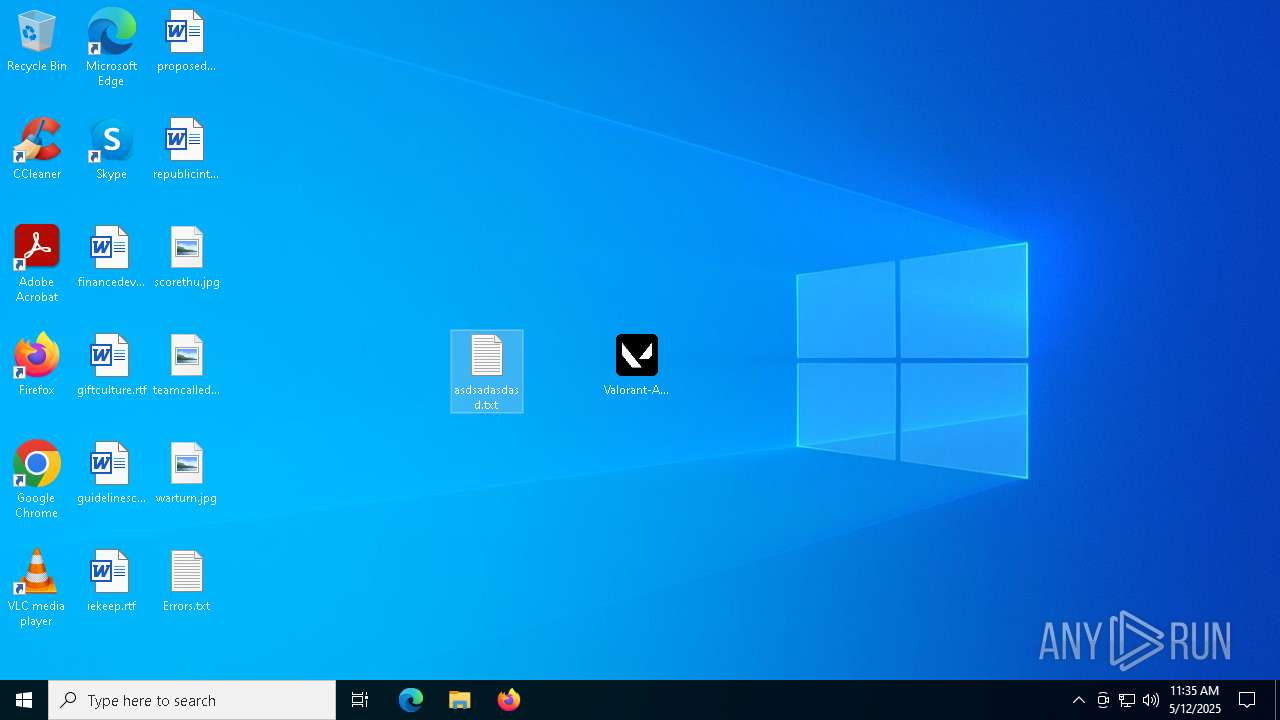
| 1228 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\asdsadasdasd.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Valorant-Account-Checker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
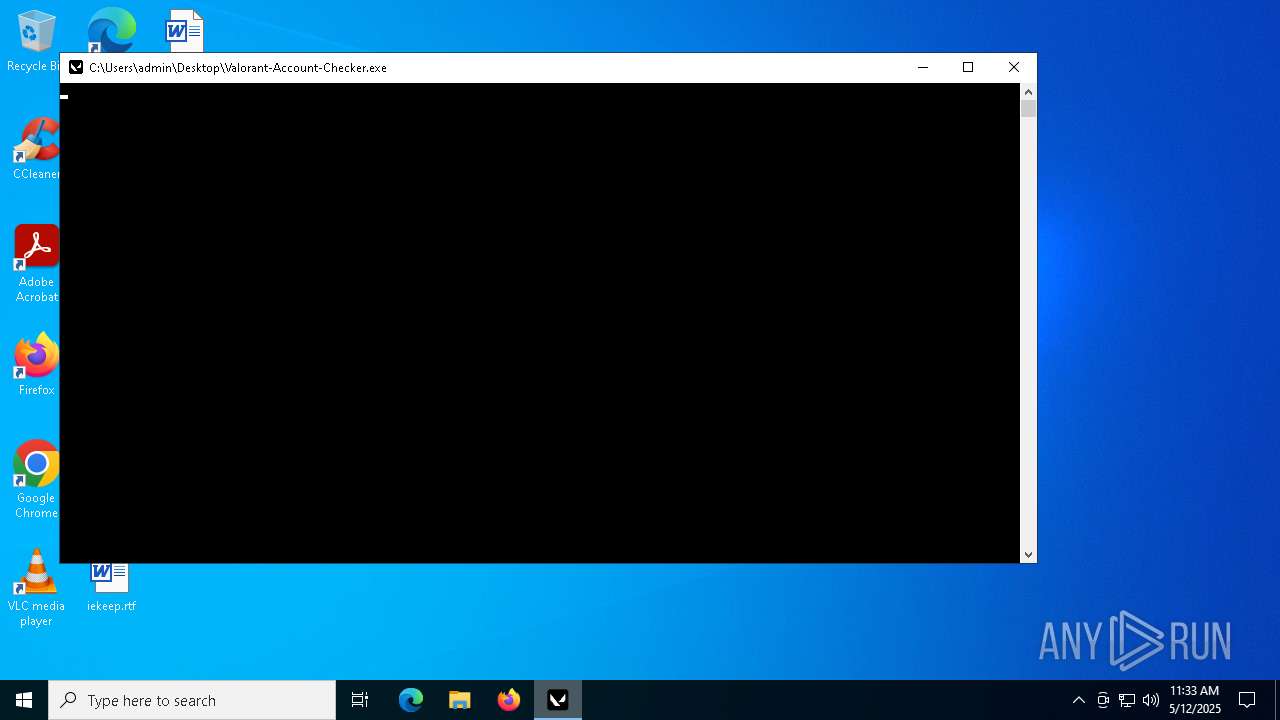
| 2420 | "C:\Users\admin\Desktop\Valorant-Account-Checker.exe" | C:\Users\admin\Desktop\Valorant-Account-Checker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3956 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | "C:\Users\admin\Desktop\Valorant-Account-Checker.exe" | C:\Users\admin\Desktop\Valorant-Account-Checker.exe | — | Valorant-Account-Checker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4436 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5968 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
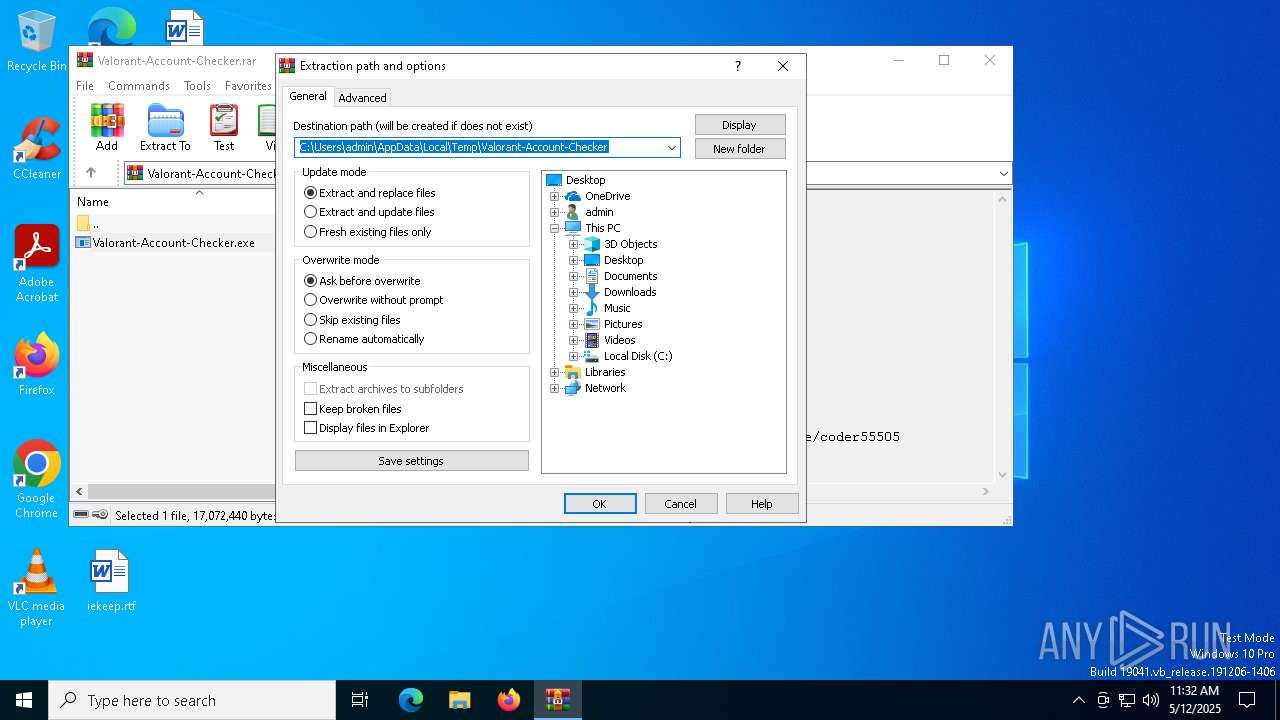
| 7012 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Valorant-Account-Checker.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7052 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | Valorant-Account-Checker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
97 608
Read events
97 512
Write events
80
Delete events
16
Modification events
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Valorant-Account-Checker.rar | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
72
Suspicious files
3
Text files
940
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | Valorant-Account-Checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI24202\_socket.pyd | executable | |
MD5:69C4A9A654CF6D1684B73A431949B333 | SHA256:8DAEFAFF53E6956F5AEA5279A7C71F17D8C63E2B0D54031C3B9E82FCB0FB84DB | |||
| 2420 | Valorant-Account-Checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI24202\_ctypes.pyd | executable | |
MD5:2185849BC0423F6641EE30804F475478 | SHA256:199CD8D7DB743C316771EF7BBF414BA9A9CDAE1F974E90DA6103563B2023538D | |||
| 2420 | Valorant-Account-Checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI24202\_decimal.pyd | executable | |
MD5:F465C15E7BACEAC920DC58A5FB922C1C | SHA256:F4A486A0CA6A53659159A404614C7E7EDCCB6BFBCDEB844F6CEE544436A826CB | |||
| 2420 | Valorant-Account-Checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI24202\VCRUNTIME140_1.dll | executable | |
MD5:68156F41AE9A04D89BB6625A5CD222D4 | SHA256:82A2F9AE1E6146AE3CB0F4BC5A62B7227E0384209D9B1AEF86BBCC105912F7CD | |||
| 7012 | WinRAR.exe | C:\Users\admin\Desktop\Valorant-Account-Checker.exe | executable | |
MD5:E6C6C2F02756DC4F84F1904A05EFA1B8 | SHA256:6E8033716D2FFE636DB8858E696700195C9CEC0F82BD6BF017FB2D1E1E99D512 | |||
| 2420 | Valorant-Account-Checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI24202\_multiprocessing.pyd | executable | |
MD5:24AEE7D83525CB43AD02FD3116B28274 | SHA256:3262EC7496D397C0B6BFB2F745516E9E225BD9246F78518852C61D559AA89485 | |||
| 2420 | Valorant-Account-Checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI24202\_ssl.pyd | executable | |
MD5:CE19076F6B62292ED66FD06E5BA67BBA | SHA256:21CA71B2C1766FC68734CB3D1E7C2C0439B86BCFB95E00B367C5FD48C59E617C | |||
| 2420 | Valorant-Account-Checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI24202\_queue.pyd | executable | |
MD5:59C05030E47BDE800AD937CCB98802D8 | SHA256:E4956834DF819C1758D17C1C42A152306F7C0EA7B457CA24CE2F6466A6CB1CAA | |||
| 2420 | Valorant-Account-Checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI24202\_hashlib.pyd | executable | |
MD5:CF4120BAD9A7F77993DD7A95568D83D7 | SHA256:14765E83996FE6D50AEDC11BB41D7C427A3E846A6A6293A4A46F7EA7E3F14148 | |||
| 2420 | Valorant-Account-Checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI24202\_tcl_data\auto.tcl | text | |
MD5:97EFA9EBE840EA051F9706504C8BD783 | SHA256:08113823951619D659EB03A1F6ACD2F9500E1264795219125A5DF7B83CABCB99 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
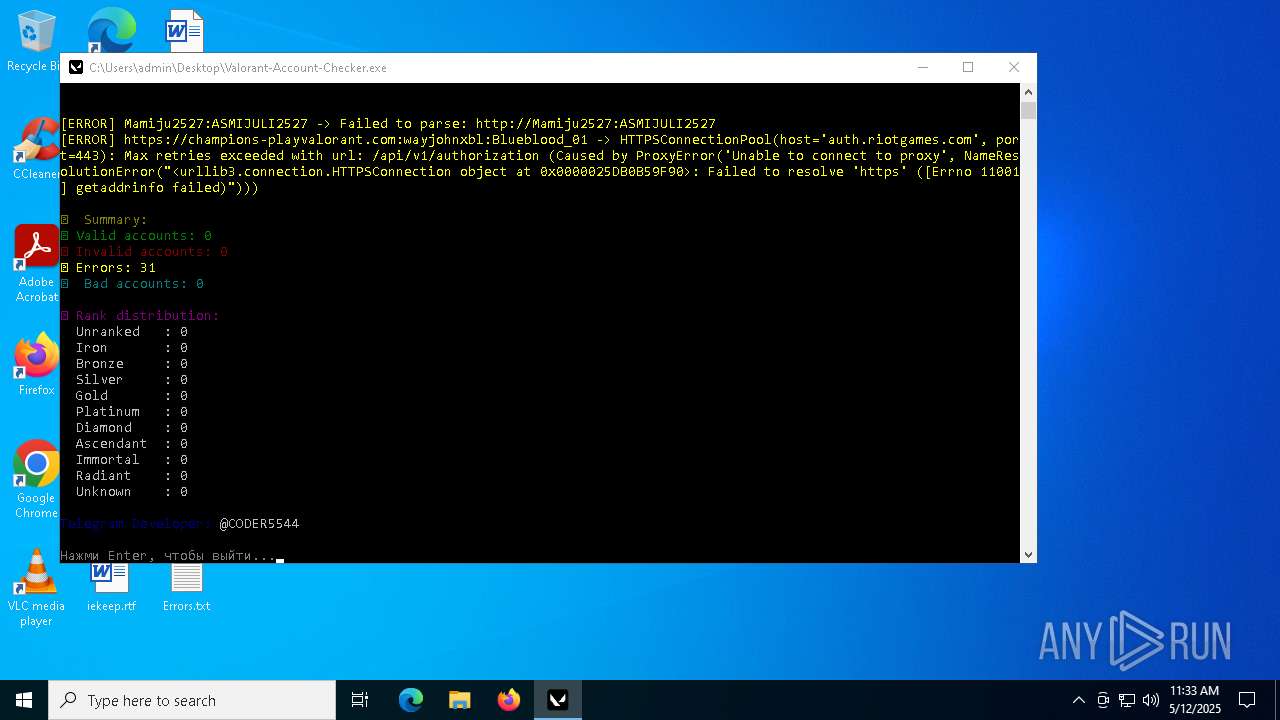
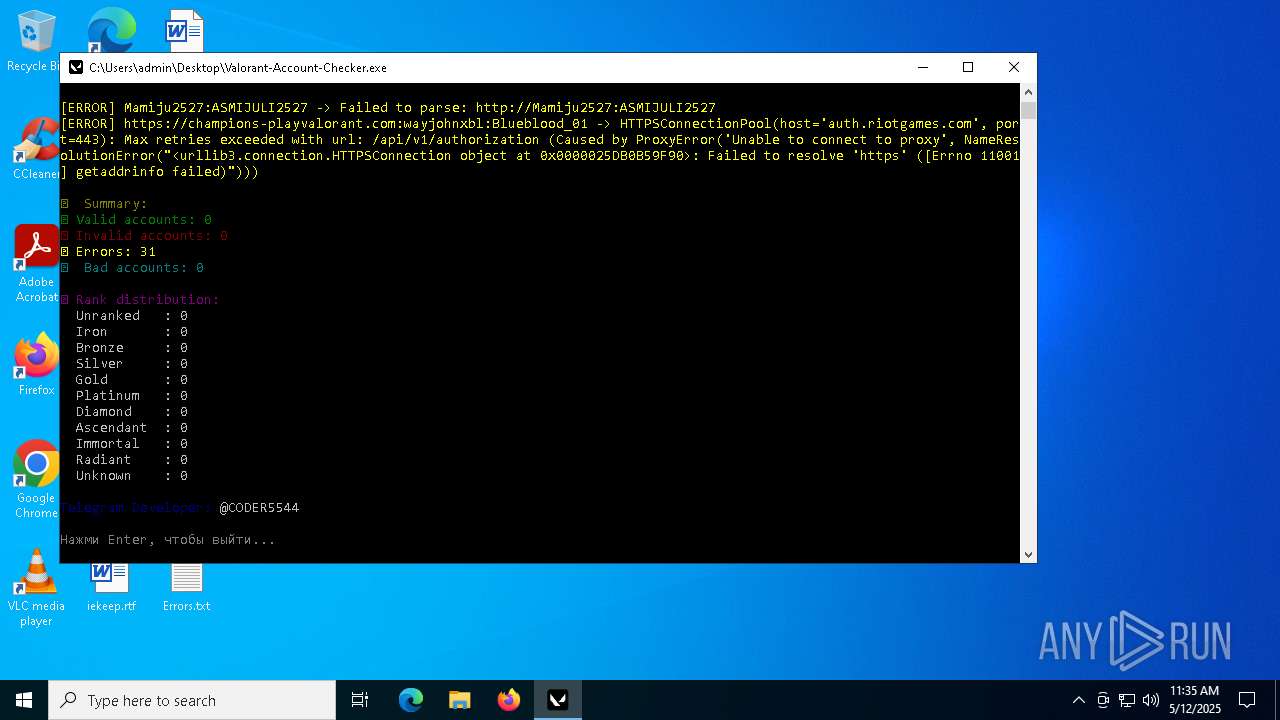
HTTP(S) requests
6
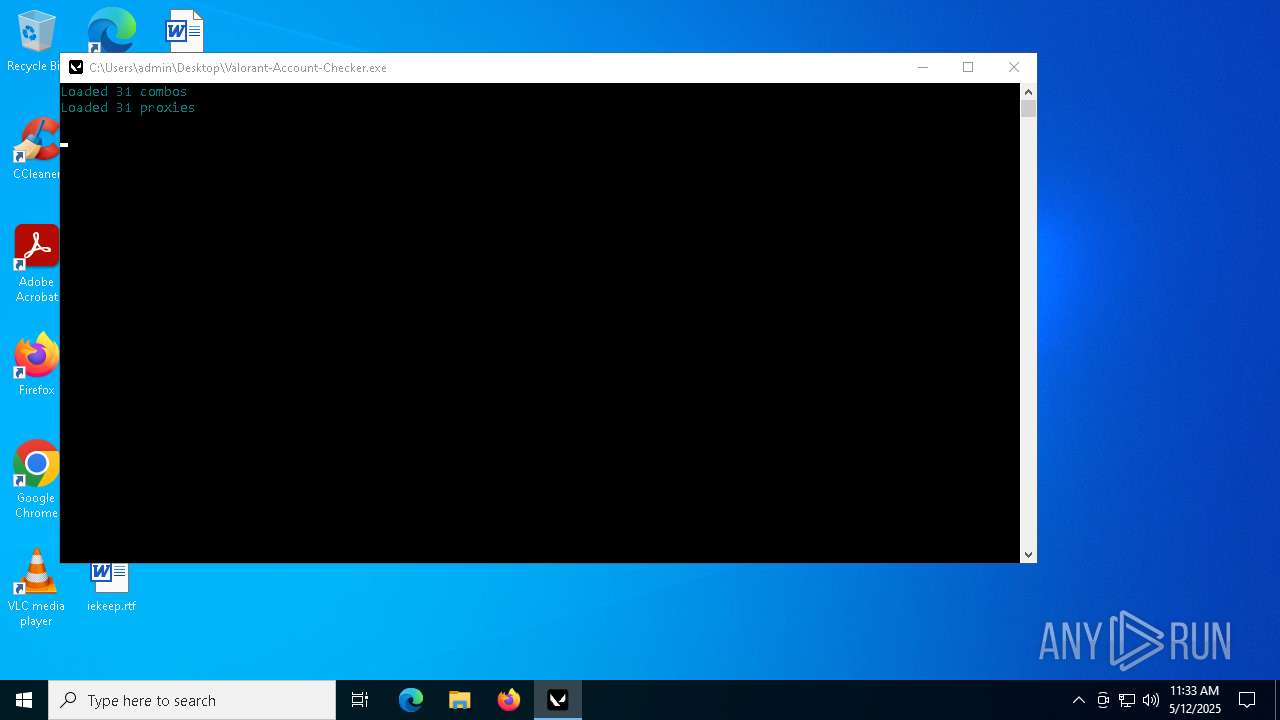
TCP/UDP connections
31
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3900 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3900 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |