| File name: | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d |
| Full analysis: | https://app.any.run/tasks/d18fa40c-95c6-4347-85df-e0de07c002a6 |
| Verdict: | Malicious activity |
| Analysis date: | July 24, 2019, 17:30:15 |
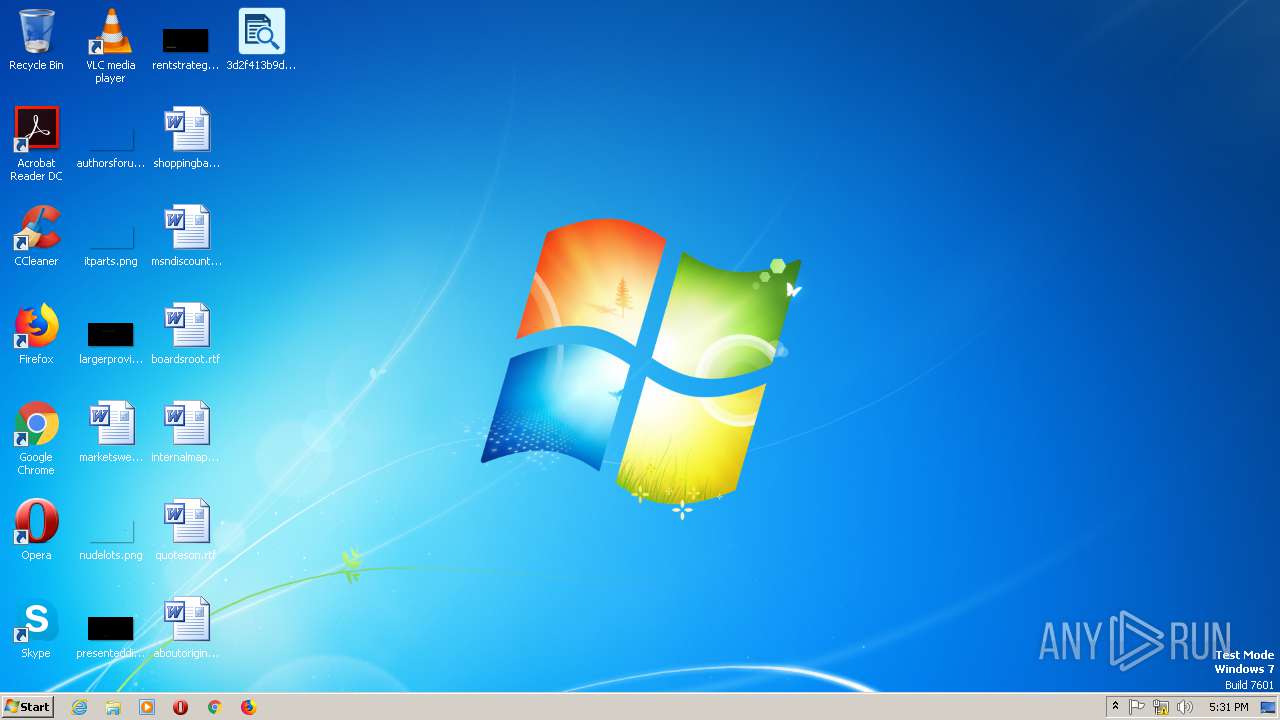
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | B62F8B7E0CD16CD72AF373DBDC98AFA7 |
| SHA1: | 005133DA8B676B3282F7A1616504A8B8FC31E806 |
| SHA256: | 3D2F413B9D1F451261CDD24A6DC6A06C168EBD70151B0CE7432F40DF371E4C6D |
| SSDEEP: | 6144:bbUTp14JuP1rKlDM+/87wBeat1RAAx94DqoJgXPRSDJikrHLAPS7EQRMuOBfA:bIoJ2rqP87wBe2Rf4DqoaPRSDskrHMBE |
MALICIOUS
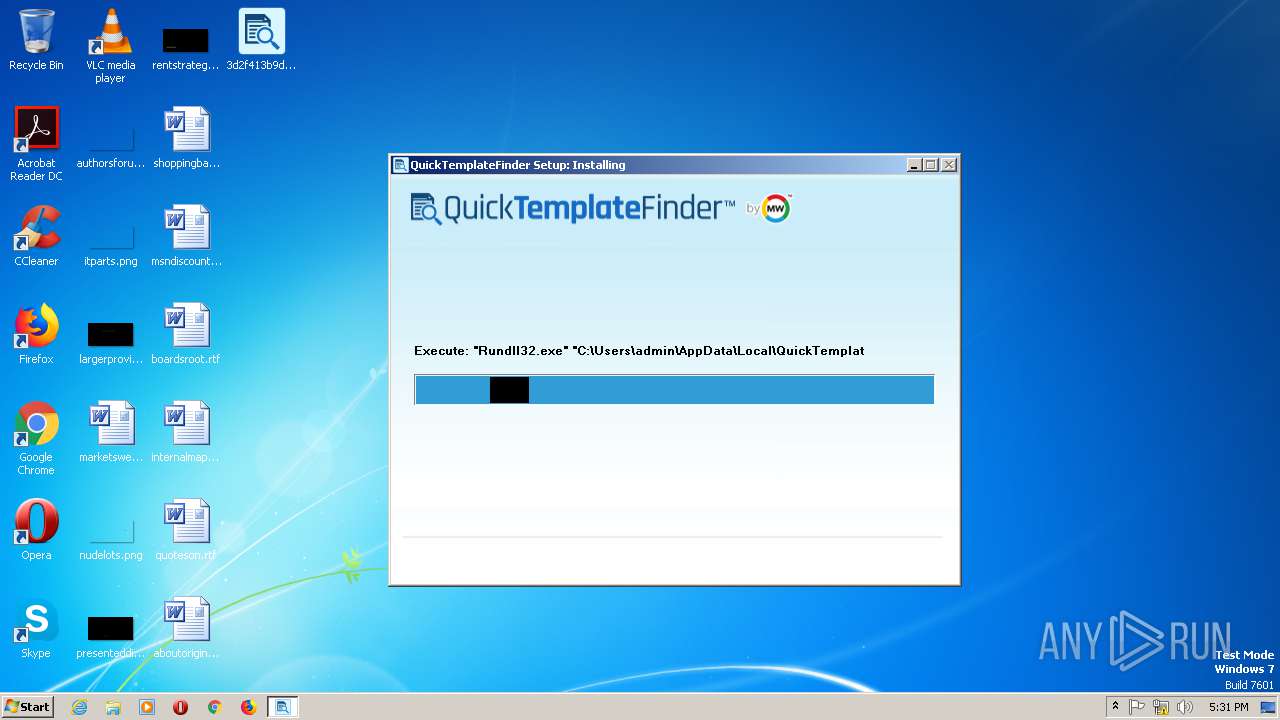
Loads dropped or rewritten executable
- 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe (PID: 2980)
- Rundll32.exe (PID: 2776)
Changes settings of System certificates
- Rundll32.exe (PID: 2776)
SUSPICIOUS
Executable content was dropped or overwritten
- 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe (PID: 2980)
Creates a software uninstall entry
- 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe (PID: 2980)
Executed via COM
- iexplore.exe (PID: 1936)
- DllHost.exe (PID: 812)
Uses RUNDLL32.EXE to load library
- 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe (PID: 2980)
Reads Internet Cache Settings
- 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe (PID: 2980)
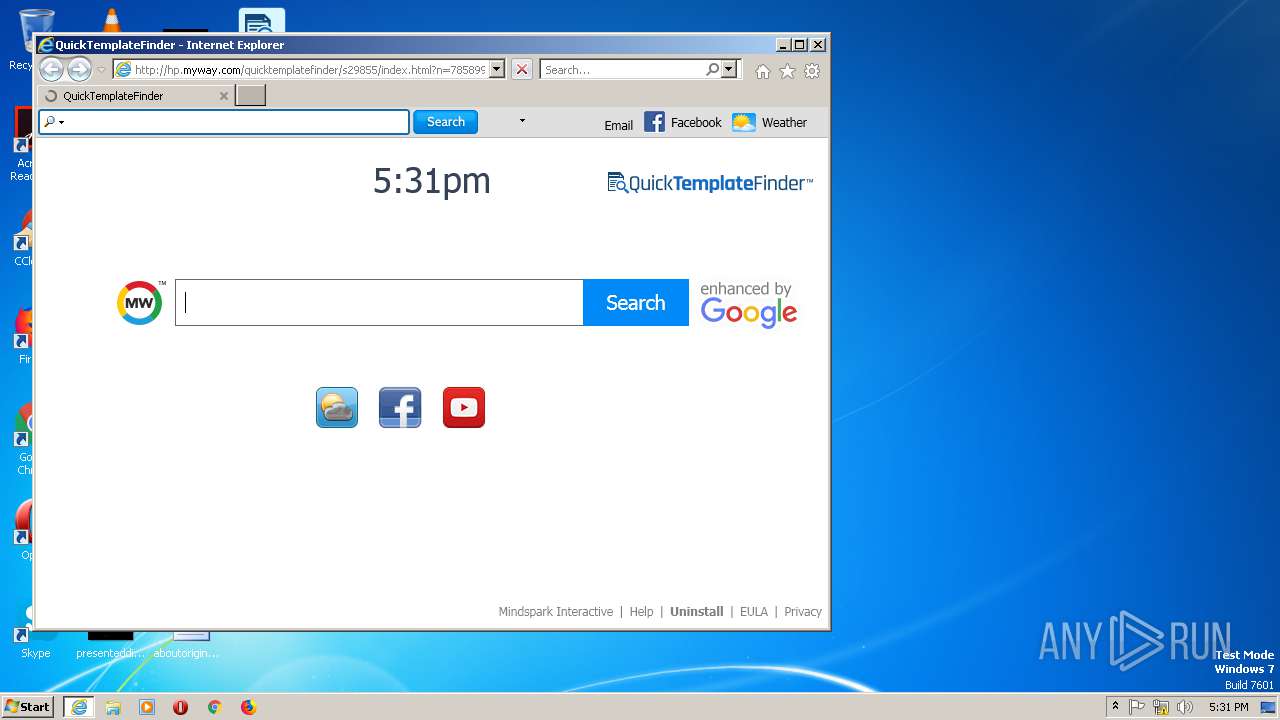
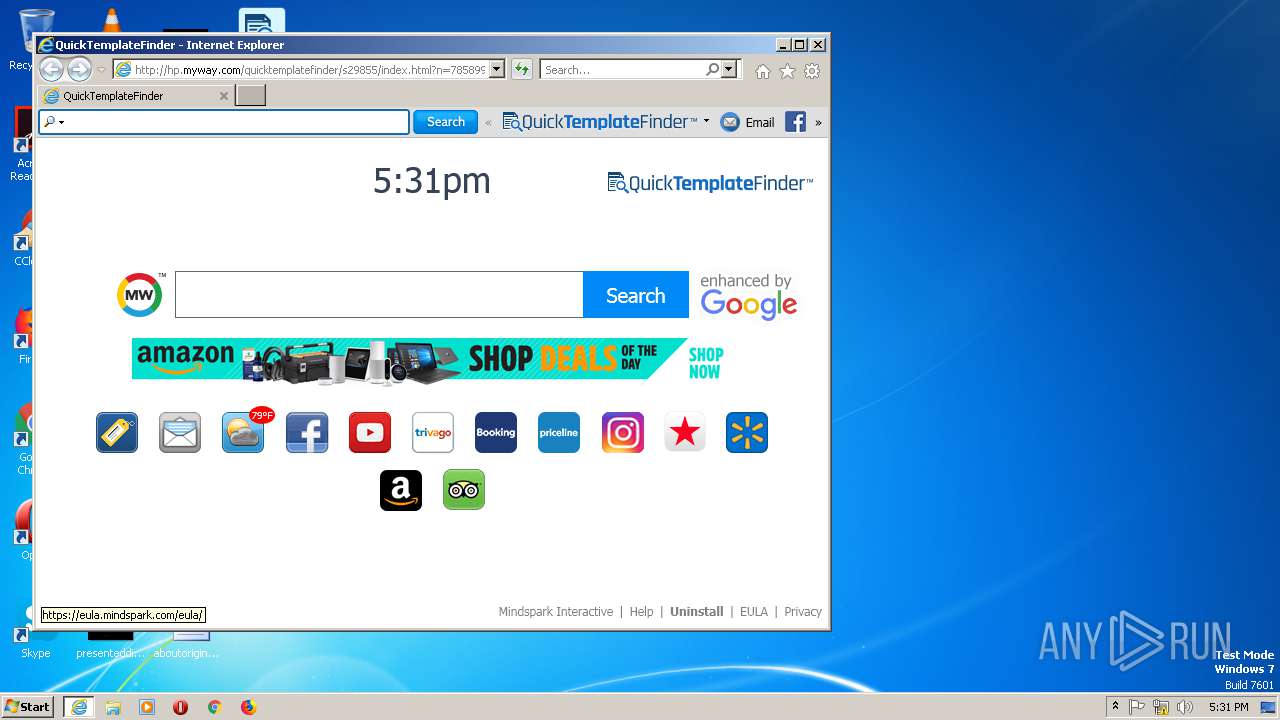
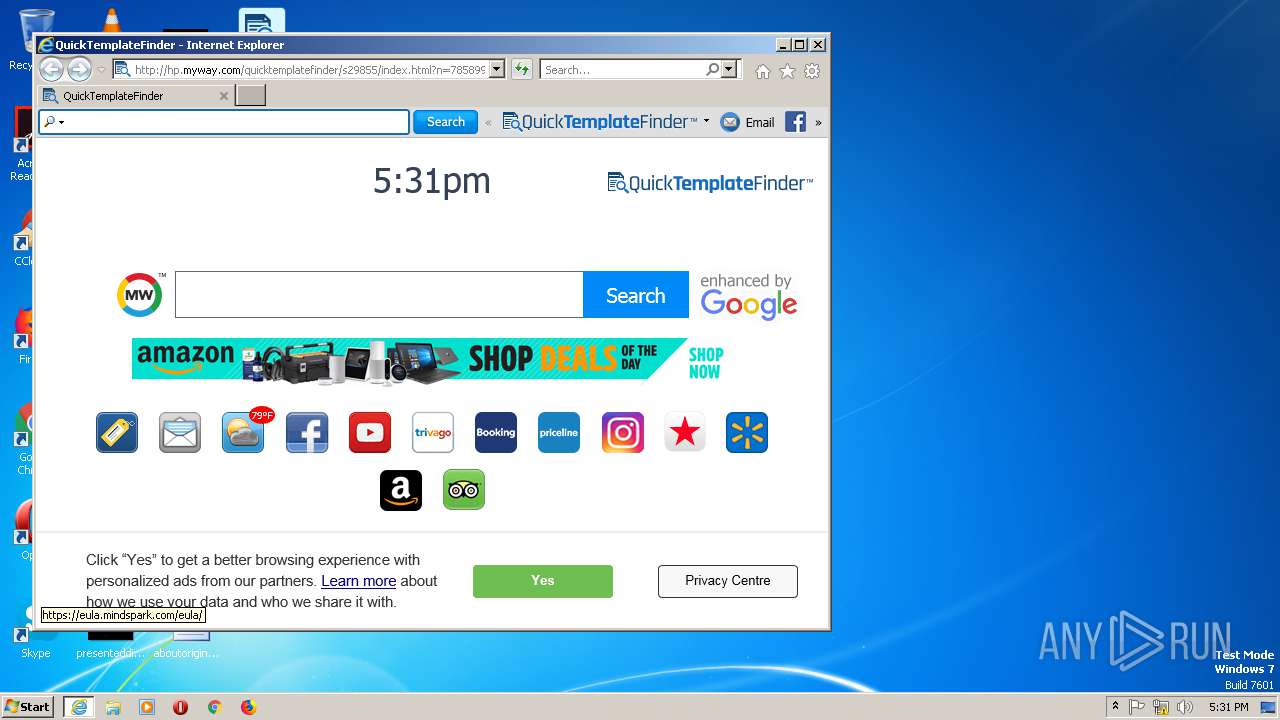
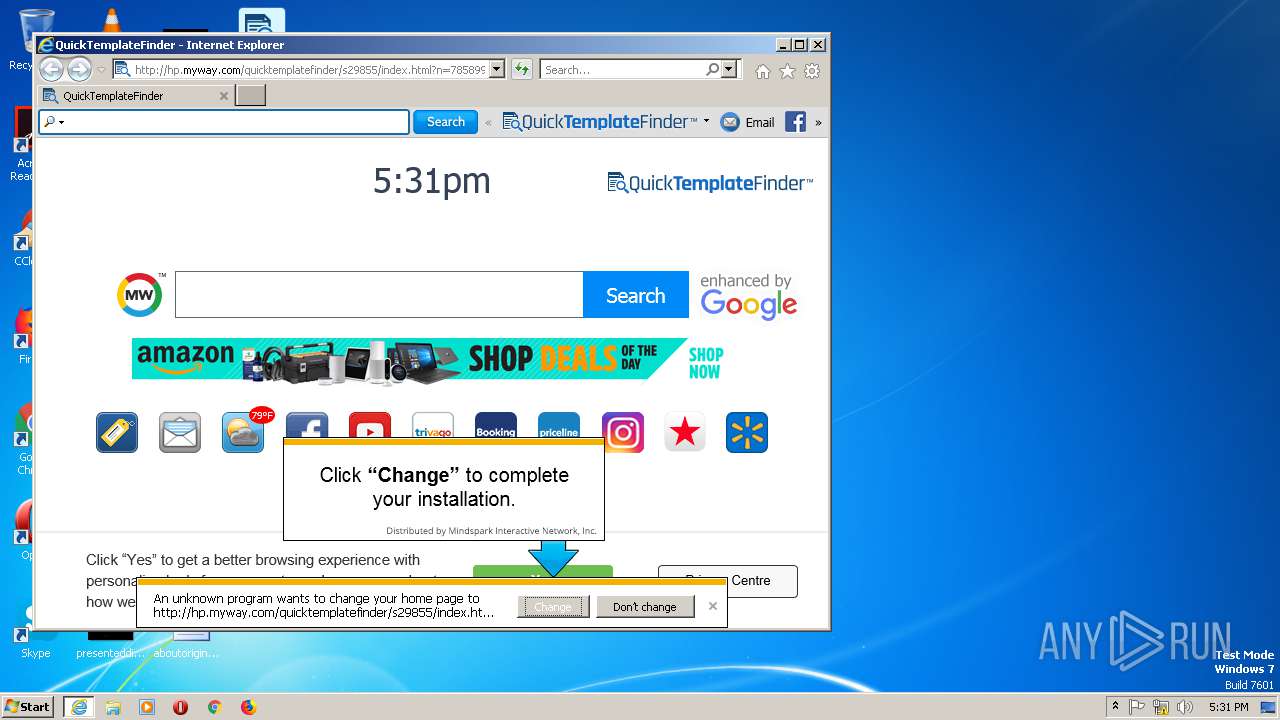
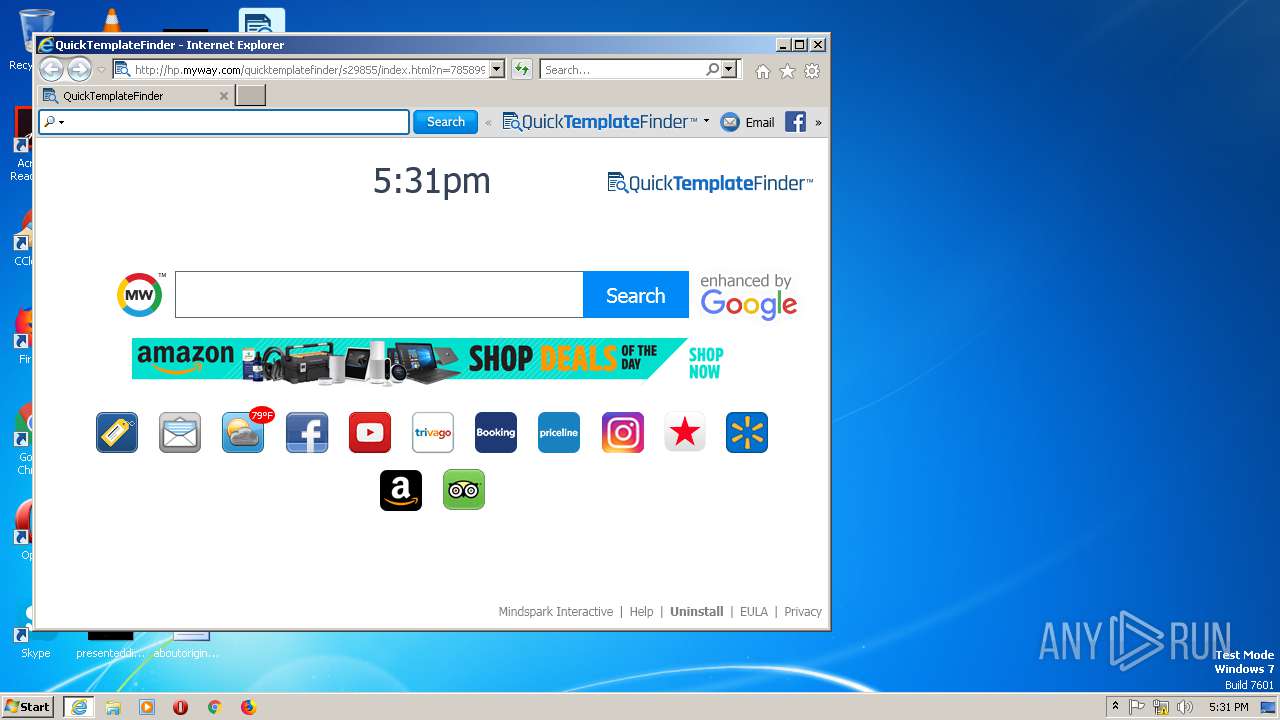
Changes the started page of IE
- 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe (PID: 2980)
Creates files in the user directory
- 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe (PID: 2980)
Reads the machine GUID from the registry
- DllHost.exe (PID: 812)
Adds / modifies Windows certificates
- Rundll32.exe (PID: 2776)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1936)
Changes internet zones settings
- iexplore.exe (PID: 1936)
Reads settings of System Certificates
- 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe (PID: 2980)
- IEXPLORE.EXE (PID: 1088)
- iexplore.exe (PID: 1936)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 1088)
Creates files in the user directory
- IEXPLORE.EXE (PID: 1088)
Reads the machine GUID from the registry
- iexplore.exe (PID: 1936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 06:01:44+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3229 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.8.1.1000 |
| ProductVersionNumber: | 2.8.1.1000 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
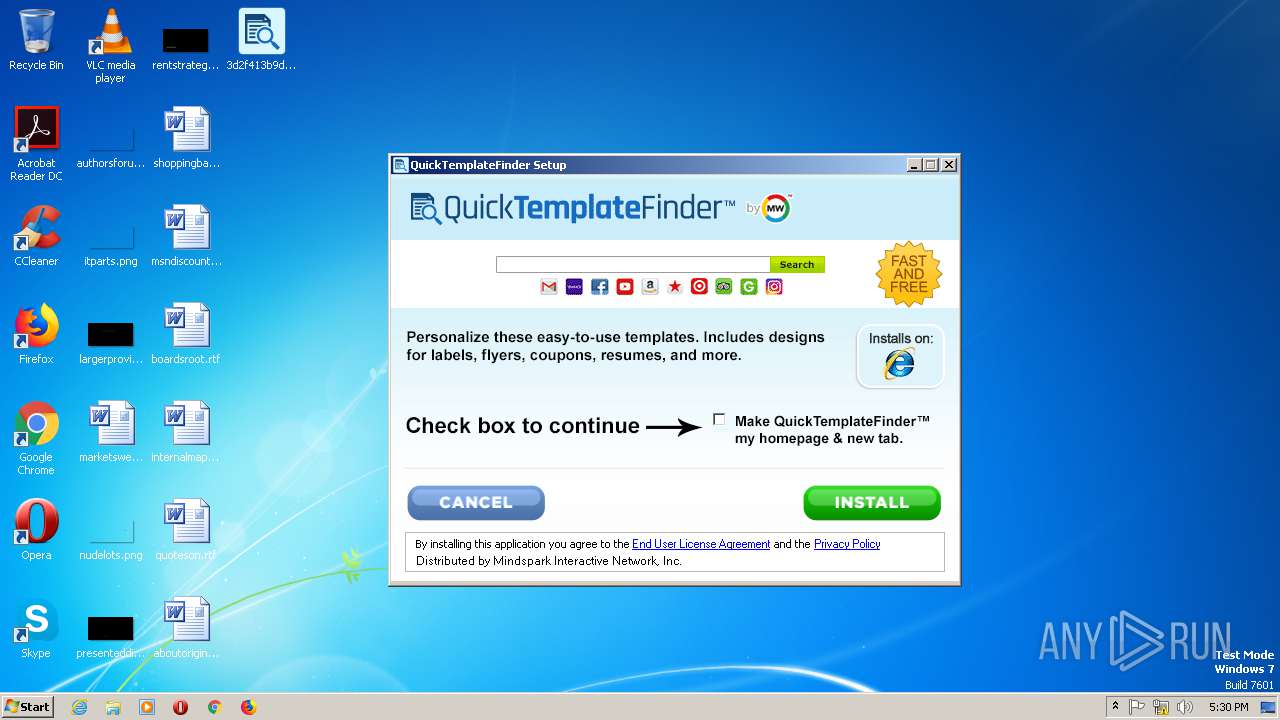
| Comments: | http://www.mindspark.com |
| CompanyName: | Mindspark Interactive Network, Inc. |
| FileDescription: | QuickTemplateFinder Setup |
| FileVersion: | 2.8.1.1000 |
| InternalName: | QuickTemplateFinder |
| LegalCopyright: | © 2015 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | QuickTemplateFinder |
| ProductVersion: | 2.8.1.1000 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-2013 05:01:44 |
| Detected languages: |
|
| Comments: | http://www.mindspark.com |
| CompanyName: | Mindspark Interactive Network, Inc. |
| FileDescription: | QuickTemplateFinder Setup |
| FileVersion: | 2.8.1.1000 |
| InternalName: | QuickTemplateFinder |
| LegalCopyright: | © 2015 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | QuickTemplateFinder |
| ProductVersion: | 2.8.1.1000 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Dec-2013 05:01:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000606C | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45707 |
.rdata | 0x00008000 | 0x00001460 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94596 |
.data | 0x0000A000 | 0x0002AF98 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79535 |
.ndata | 0x00035000 | 0x00055000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0008A000 | 0x000049F0 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.6257 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31253 | 1118 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.43234 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.5695 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.27308 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.89384 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
39
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 812 | C:\Windows\system32\DllHost.exe /Processid:{49F171DD-B51A-40D3-9A6C-52D674CC729D} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:1936 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2776 | "Rundll32.exe" "C:\Users\admin\AppData\Local\QuickTemplateFinderTooltab\TooltabExtension.dll",A -hp=http://hp.myway.com/quicktemplatefinder/s29855/index.html -ua="(Windows NT 6.1; Win64; MSIE 11.0; Build 7601; SP 1)" -ul=https://anx.mindspark.com/anx.gif?anxa=%251&anxe=%252&anxt=655D9BAF-C50C-4273-8B69-05B7A37CE48B&anxtv=2.8.1.1000&anxp=^CRC^mni000^S29855&anxsi=&anxv=%253&anxd=2019-07-24&anxr=%254 -hu=SHOW | C:\Windows\SysWOW64\Rundll32.exe | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2980 | "C:\Users\admin\Desktop\3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe" | C:\Users\admin\Desktop\3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | explorer.exe | ||||||||||||
User: admin Company: Mindspark Interactive Network, Inc. Integrity Level: MEDIUM Description: QuickTemplateFinder Setup Exit code: 0 Version: 2.8.1.1000 Modules
| |||||||||||||||
Total events
774
Read events
574
Write events
196
Delete events
4
Modification events
| (PID) Process: | (2980) 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2980) 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000079000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2980) 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2980) 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2980) 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2980) 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2980) 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2980) 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2980) 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2980) 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\71\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
3
Suspicious files
5
Text files
109
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | C:\Users\admin\AppData\Local\Temp\CabB377.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | C:\Users\admin\AppData\Local\Temp\TarB378.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | C:\Users\admin\AppData\Local\Temp\nsmAA7D.tmp\installerParams | text | |
MD5:— | SHA256:— | |||
| 2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | C:\Users\admin\AppData\Local\Temp\nsmAA7D.tmp\QTF_msi_bg-copy_1501802100782.bmp | image | |
MD5:— | SHA256:— | |||
| 2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E0F5C59F9FA661F6F4C50B87FEF3A15A | binary | |
MD5:— | SHA256:— | |||
| 2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\installerParams[1].js | text | |
MD5:— | SHA256:— | |||
| 2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\CQMKGI2V.txt | text | |
MD5:— | SHA256:— | |||
| 2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | C:\Users\admin\AppData\Local\Temp\nsmAA7D.tmp\QTF_msi_bg-copy_1501802238877.bmp | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
80
TCP/UDP connections
51
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | GET | 200 | 205.185.216.42:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?111c61fc9c77c789 | US | compressed | 56.3 Kb | whitelisted |
1088 | IEXPLORE.EXE | GET | 200 | 2.18.232.251:80 | http://hp.myway.com/quicktemplatefinder/s29855/assets/1557953242155/app.js | unknown | text | 120 Kb | whitelisted |
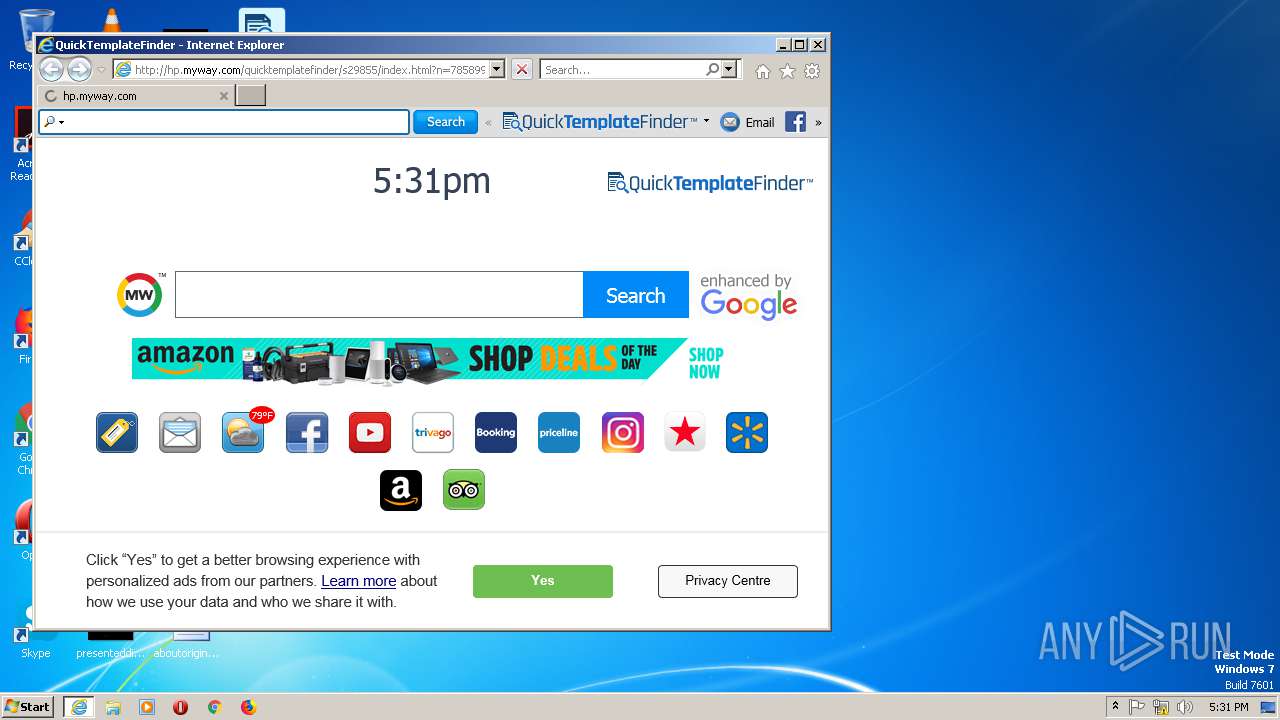
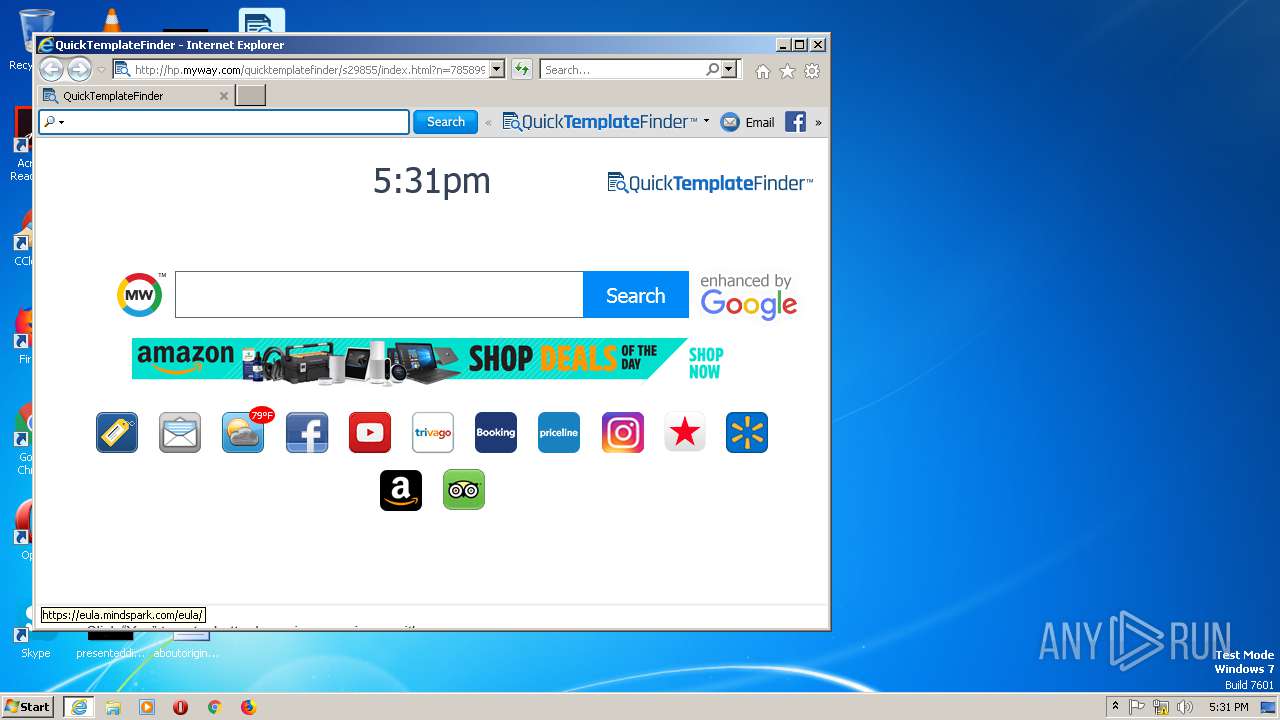
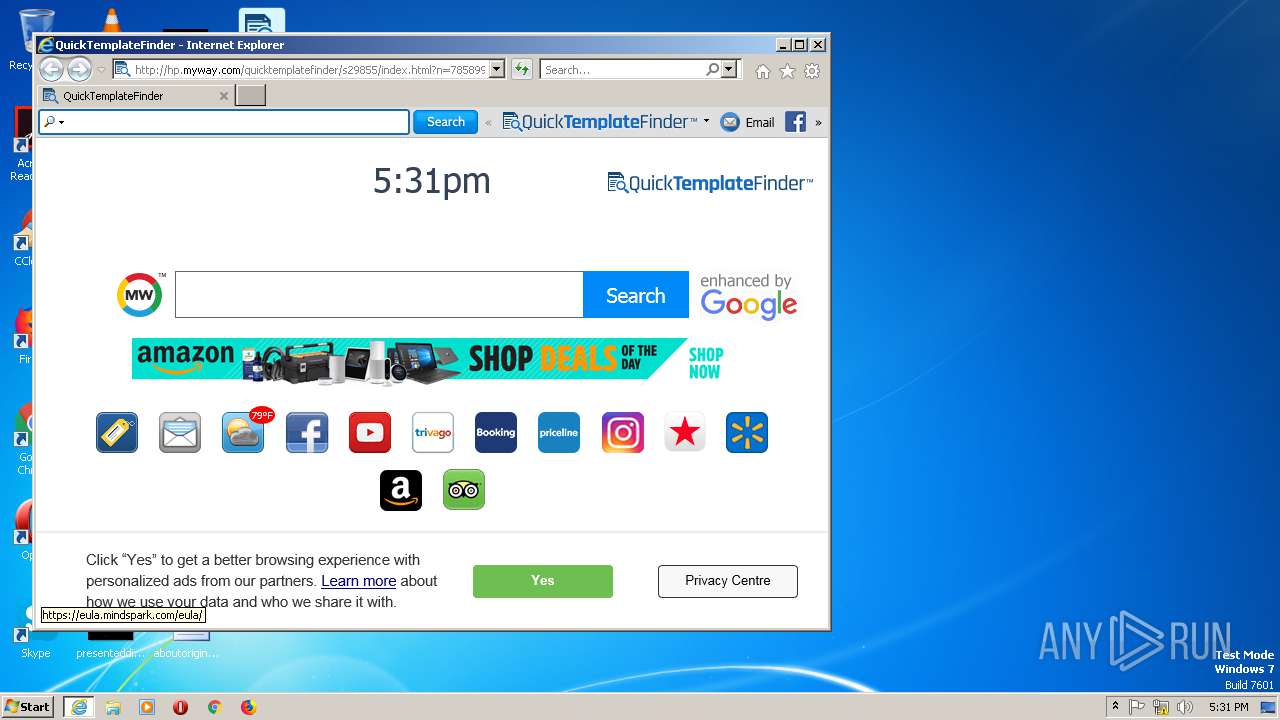
1088 | IEXPLORE.EXE | GET | 200 | 2.18.232.251:80 | http://hp.myway.com/quicktemplatefinder/s29855/index.html?n=785899A1&p2=^CRC^mni000^S29855&ptb=655D9BAF-C50C-4273-8B69-05B7A37CE48B&coid=c60861cc5e674e8580c7cff4ef38b0bc | unknown | html | 3.13 Kb | whitelisted |
1088 | IEXPLORE.EXE | GET | 200 | 2.18.232.251:80 | http://ak.staticimgfarm.com/images/webtooltab/assets/logos/CRC.png | unknown | image | 6.22 Kb | whitelisted |
1088 | IEXPLORE.EXE | GET | 200 | 2.18.232.251:80 | http://ak.staticimgfarm.com/images/webtooltab/assets/searchbar/QuickTemplateFinder/logo.png | unknown | image | 2.55 Kb | whitelisted |
1088 | IEXPLORE.EXE | GET | 200 | 2.18.232.251:80 | http://ak.staticimgfarm.com/images/webtooltab/assets/searchbar/QuickTemplateFinder/email.png | unknown | image | 547 b | whitelisted |
1088 | IEXPLORE.EXE | GET | 200 | 2.18.232.251:80 | http://ak.staticimgfarm.com/images/webtooltab/chiclets/youtube.png | unknown | image | 824 b | whitelisted |
1088 | IEXPLORE.EXE | GET | 200 | 2.18.232.251:80 | http://ak.staticimgfarm.com/images/webtooltab/chiclets/Control/control_chiclet_weather.png | unknown | image | 1.54 Kb | whitelisted |
2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | GET | 200 | 192.35.177.64:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | US | cat | 893 b | shared |
1088 | IEXPLORE.EXE | GET | 200 | 2.18.232.251:80 | http://ak.staticimgfarm.com/images/webtooltab/assets/logos/final_logo_newtab.png | unknown | image | 3.68 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | 74.113.237.192:443 | anx.mindspark.com | Mindspark Interactive Network, Inc. | US | malicious |
2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | 205.185.216.42:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2980 | 3d2f413b9d1f451261cdd24a6dc6a06c168ebd70151b0ce7432f40df371e4c6d.exe | 35.244.218.203:443 | dp.tb.ask.com | — | US | whitelisted |
1088 | IEXPLORE.EXE | 2.18.232.251:80 | hp.myway.com | Akamai International B.V. | — | whitelisted |
1088 | IEXPLORE.EXE | 152.195.132.202:443 | cdn.cookielaw.org | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1088 | IEXPLORE.EXE | 2.18.232.251:443 | hp.myway.com | Akamai International B.V. | — | whitelisted |
1088 | IEXPLORE.EXE | 205.185.208.52:443 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
1088 | IEXPLORE.EXE | 35.227.202.20:80 | weatherblink.wdgserv.com | — | US | unknown |
1088 | IEXPLORE.EXE | 104.20.184.68:443 | geolocation.onetrust.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anx.mindspark.com |
| whitelisted |
apps.identrust.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
dp.tb.ask.com |
| whitelisted |
hp.myway.com |
| whitelisted |
ak.staticimgfarm.com |
| whitelisted |
cdn.cookielaw.org |
| whitelisted |
code.jquery.com |
| whitelisted |
anx.tb.ask.com |
| whitelisted |
weatherblink.wdgserv.com |
| unknown |