| File name: | get.ps1 |
| Full analysis: | https://app.any.run/tasks/16342436-0a1c-4ac3-8cdb-03502893a593 |
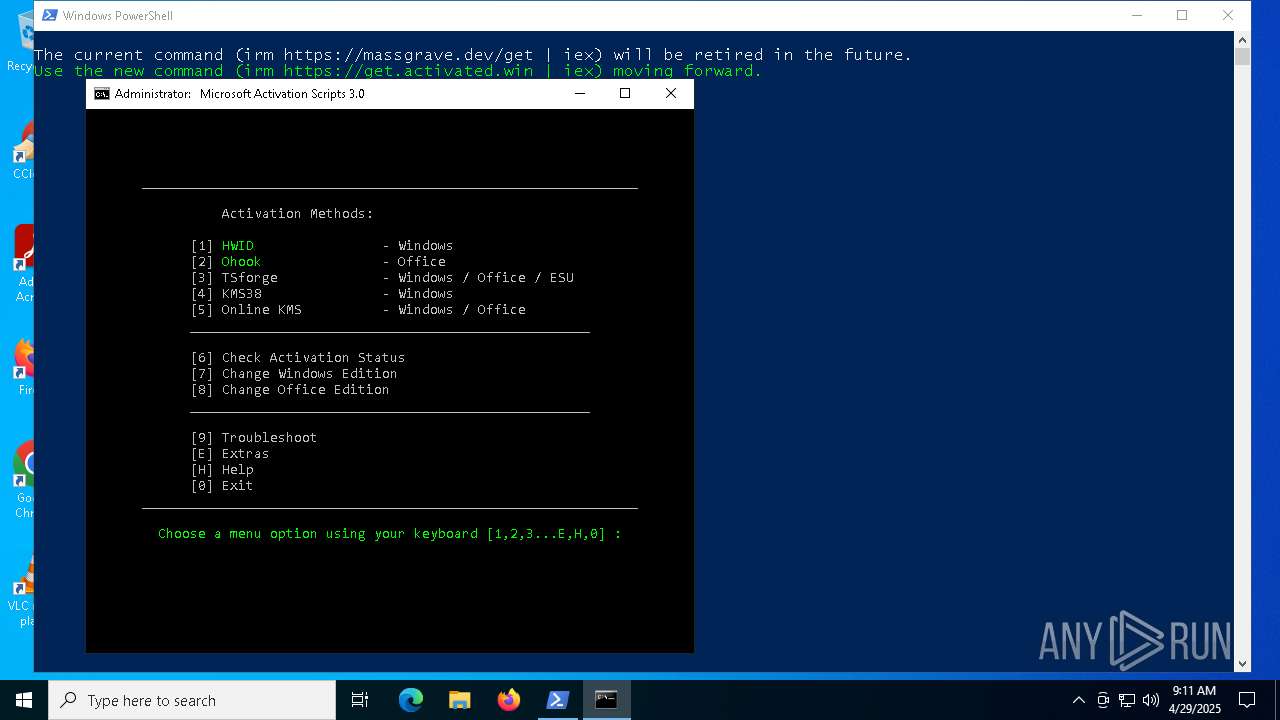
| Verdict: | Malicious activity |
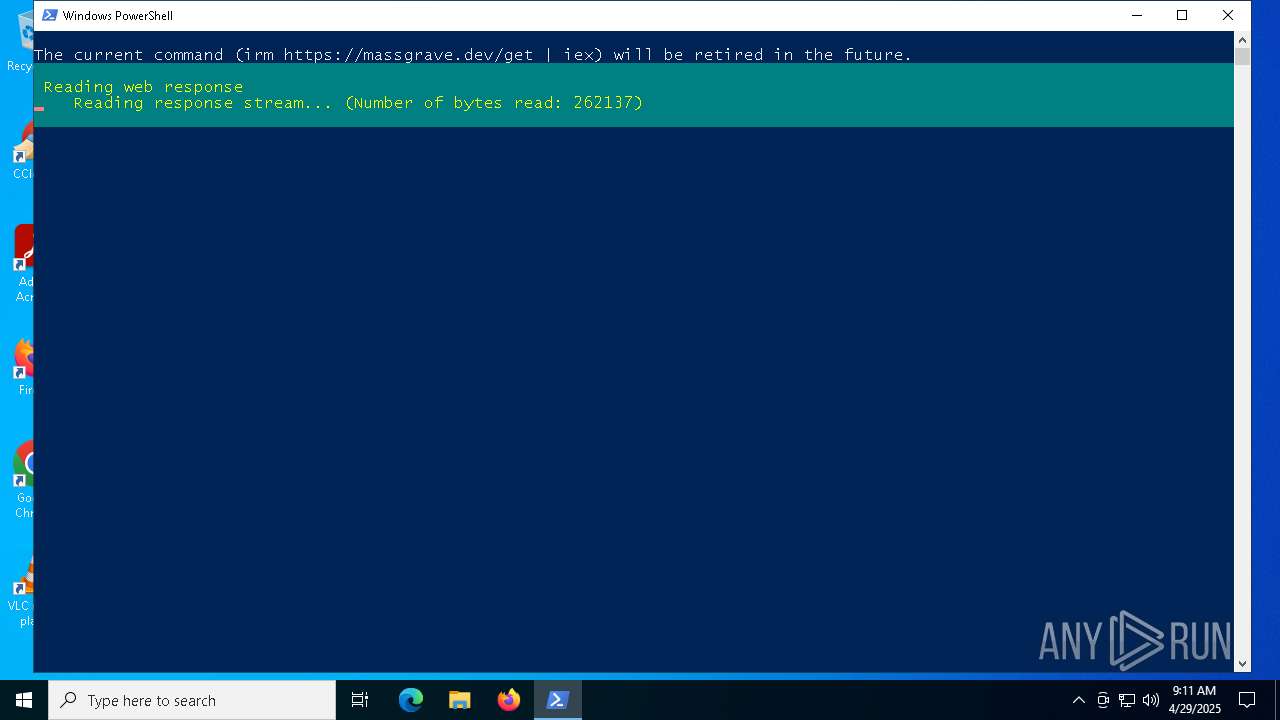
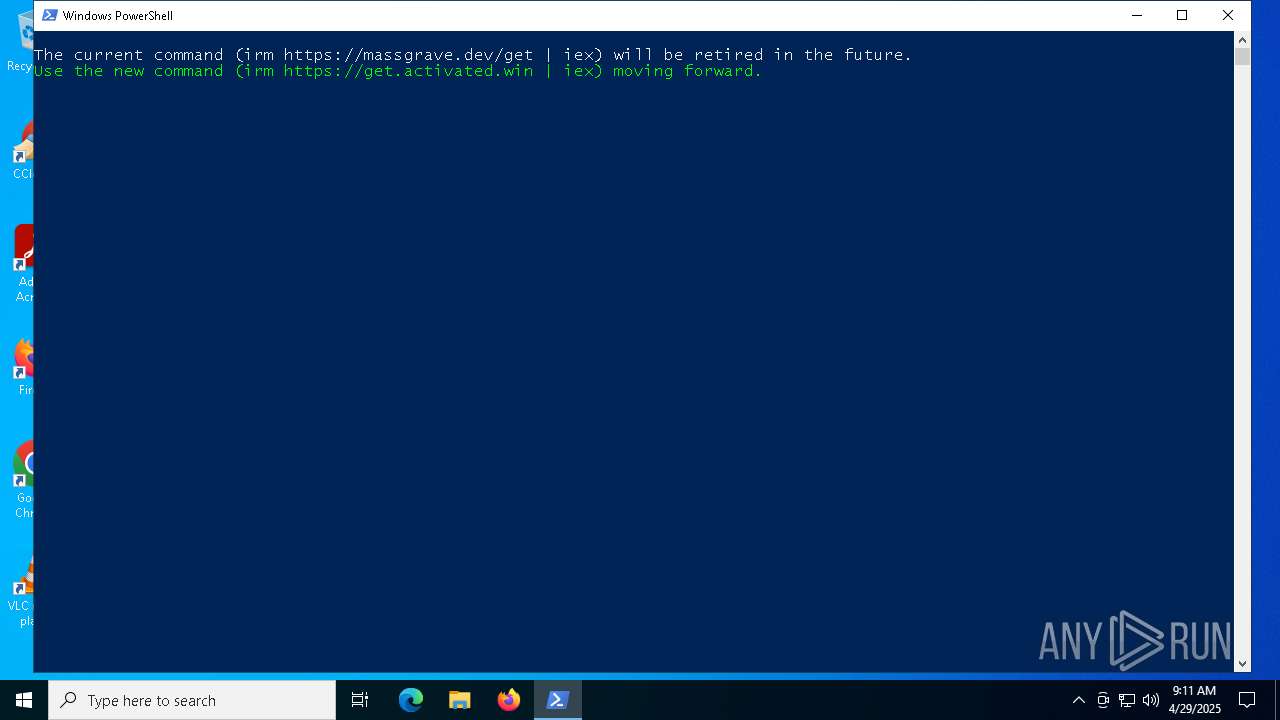
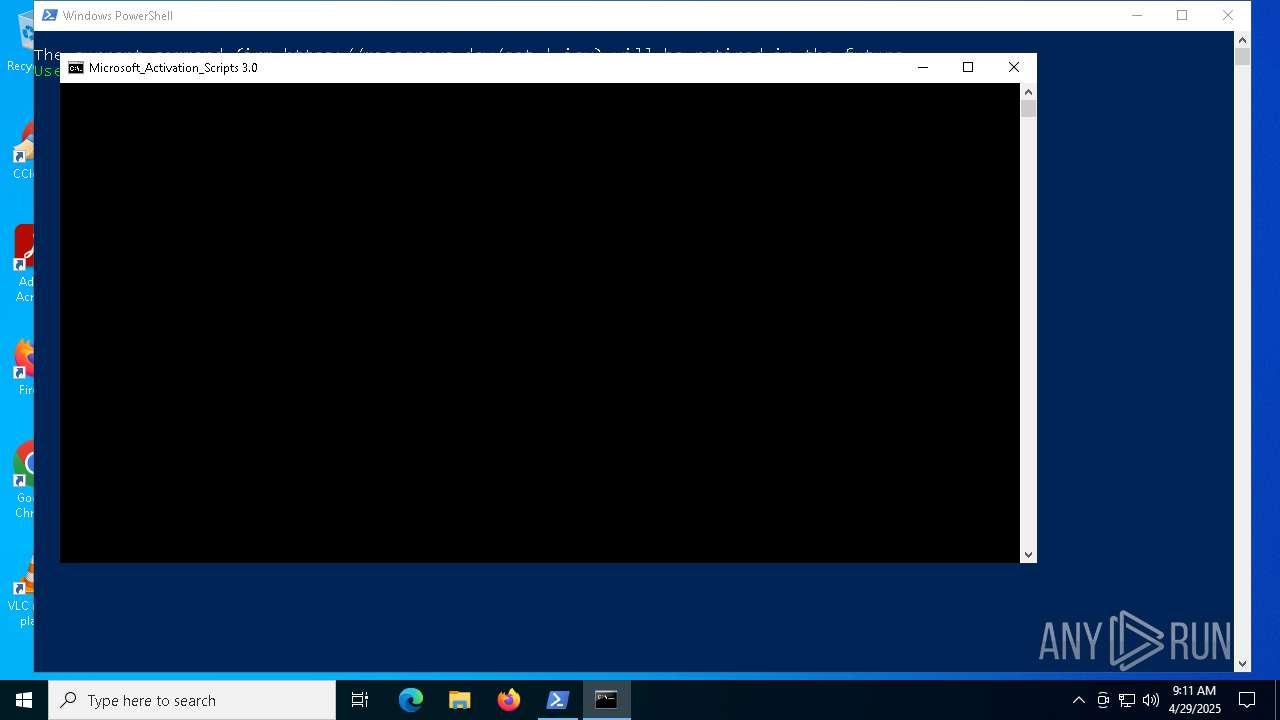
| Analysis date: | April 29, 2025, 09:11:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 7CE5D913E423B1F45F98E4702E622117 |
| SHA1: | A418E8D56F9BD8048AFD327122BA149984866F28 |
| SHA256: | 3D1DEC008033C40244324D129EFE76468F56A1B021D5212A26A25641DAB7DB10 |
| SSDEEP: | 96:HKFUuBVkDx+uy6OphNHOSSDrSSSKDU4SXDZAByg+TlkXeQo6CGefWrG/a:qFUOVk1+uyp/SD2zKDUtXDZABygKlkOY |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7344)
SUSPICIOUS
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7344)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 4976)
- powershell.exe (PID: 2908)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 7344)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 4976)
- powershell.exe (PID: 2908)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7344)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7268)
- cmd.exe (PID: 5124)
- powershell.exe (PID: 8152)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 7812)
- powershell.exe (PID: 7620)
Executing commands from ".cmd" file
- powershell.exe (PID: 7344)
- cmd.exe (PID: 7652)
- powershell.exe (PID: 8152)
- cmd.exe (PID: 7268)
- powershell.exe (PID: 7620)
- cmd.exe (PID: 7812)
Windows service management via SC.EXE
- sc.exe (PID: 7712)
- sc.exe (PID: 6944)
- sc.exe (PID: 7828)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7268)
- cmd.exe (PID: 7812)
Starts SC.EXE for service management
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7268)
- cmd.exe (PID: 7812)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 4976)
- powershell.exe (PID: 2908)
Application launched itself
- cmd.exe (PID: 7876)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7268)
- cmd.exe (PID: 5124)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 8040)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7984)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 8140)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7984)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 7268)
- cmd.exe (PID: 7812)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7984)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 8140)
INFO
Disables trace logs
- powershell.exe (PID: 7344)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 4976)
- powershell.exe (PID: 2908)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 4976)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 2908)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 4976)
- powershell.exe (PID: 2908)
Checks operating system version
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7268)
- cmd.exe (PID: 7812)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 4976)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 2908)
Checks proxy server information
- powershell.exe (PID: 7344)
- slui.exe (PID: 2240)
Starts MODE.COM to configure console settings
- mode.com (PID: 812)
Checks supported languages
- mode.com (PID: 812)
Reads the software policy settings
- slui.exe (PID: 2240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
210
Monitored processes
82
Malicious processes
6
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | C:\WINDOWS\System32\cmd.exe /c ping -4 -n 1 activated.win | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | find /i "FullLanguage" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | mode 76, 34 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "-el" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | C:\WINDOWS\System32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2908 | powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_f0561469-bd06-4921-b910-3659fd044b40.cmd') -split ':PStest:\s*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 146
Read events
39 146
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
4
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7344 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:E2B5FCB9A42EC26ACA006F805CEABE95 | SHA256:5012EAD4BE1C455855DB2BCE293B8F8F7E35970359657BDC277DCC84C288F827 | |||
| 8016 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hw1ksx2a.akh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7344 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pfhv32ij.xsa.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7344 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10c9ca.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7344 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RQFTN1G16208KDOC3GKG.temp | binary | |
MD5:E2B5FCB9A42EC26ACA006F805CEABE95 | SHA256:5012EAD4BE1C455855DB2BCE293B8F8F7E35970359657BDC277DCC84C288F827 | |||
| 8016 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_phgl4fhi.t4w.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8016 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:BAB7CE0DE8038869A479206F25C513A4 | SHA256:40452CD7A3813CB4858B842463D4E69059BFD02EAC5A6F80FC0B35BCCC858E7F | |||
| 8152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cmaew2e2.c0p.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tm03leix.trx.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7428 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ncb4lqi3.i11.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
53
DNS requests
19
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2564 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2564 | RUXIMICS.exe | GET | 200 | 23.216.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.22.68:443 | https://dev.azure.com/massgrave/Microsoft-Activation-Scripts/_apis/git/repositories/Microsoft-Activation-Scripts/items?path=/MAS/All-In-One-Version-KL/MAS_AIO.cmd&versionType=Commit&version=313f240448953cd5fe3c5631f4e4de502f23fc9a | unknown | — | — | unknown |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5072 | SIHClient.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
5072 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5072 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 52.165.164.15:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
5072 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 23.216.77.22:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2564 | RUXIMICS.exe | 23.216.77.22:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2564 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
dev.azure.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
activated.win |
| unknown |
updatecheck30.activated.win |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-WmiObject Cmdlet has been detected |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Windows OS Version extraction by PS.Script has been detected |
— | — | A Network Trojan was detected | ET ATTACK_RESPONSE PowerShell Internet Connectivity Check via Network GUID Inbound |