| File name: | Minecraft 1.5.2.jar |
| Full analysis: | https://app.any.run/tasks/e70e7be9-7d17-41e1-8256-4ccc3c15ec9f |
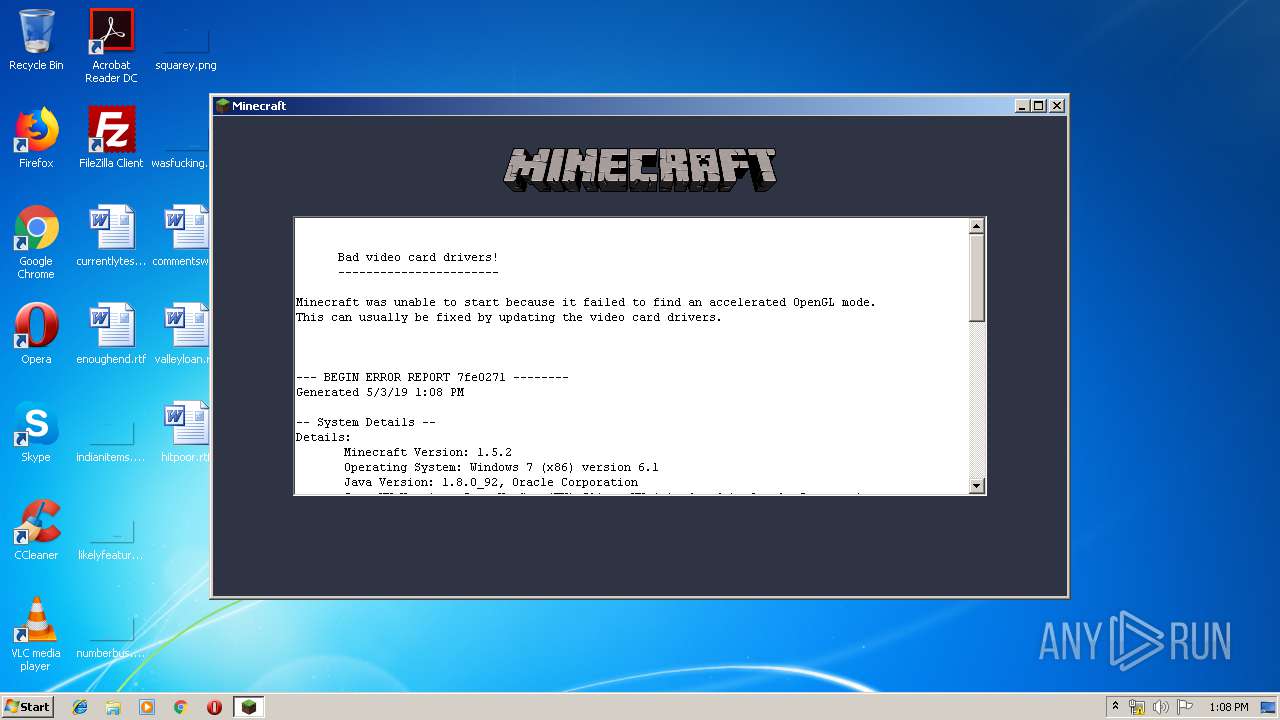
| Verdict: | Malicious activity |
| Analysis date: | May 03, 2019, 12:07:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | 4ECA7879FF514CDD79C290701443EEDD |
| SHA1: | 6380000447E5048759B9AF0F7610C993B9AAF890 |
| SHA256: | 3D1DBCA922045D5ECCC744E6F9F6E56FEF73A371A8BC0826E76FB041824073C0 |
| SSDEEP: | 3072:mAUqErMQiHKp6XqaCU3ydzSFMpRAIj1FSQm+/F7WCAQWLLidaf+K5ISzuxEPrPX4:UaUJOaF |
MALICIOUS
Loads dropped or rewritten executable
- javaw.exe (PID: 3860)
SUSPICIOUS
Executes JAVA applets
- javaw.exe (PID: 1752)
Application launched itself
- javaw.exe (PID: 1752)
Executable content was dropped or overwritten
- javaw.exe (PID: 3860)
Creates files in the user directory
- javaw.exe (PID: 3860)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (78.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (21.6) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2010:10:20 18:03:26 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | META-INF/ |
Total processes
33
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
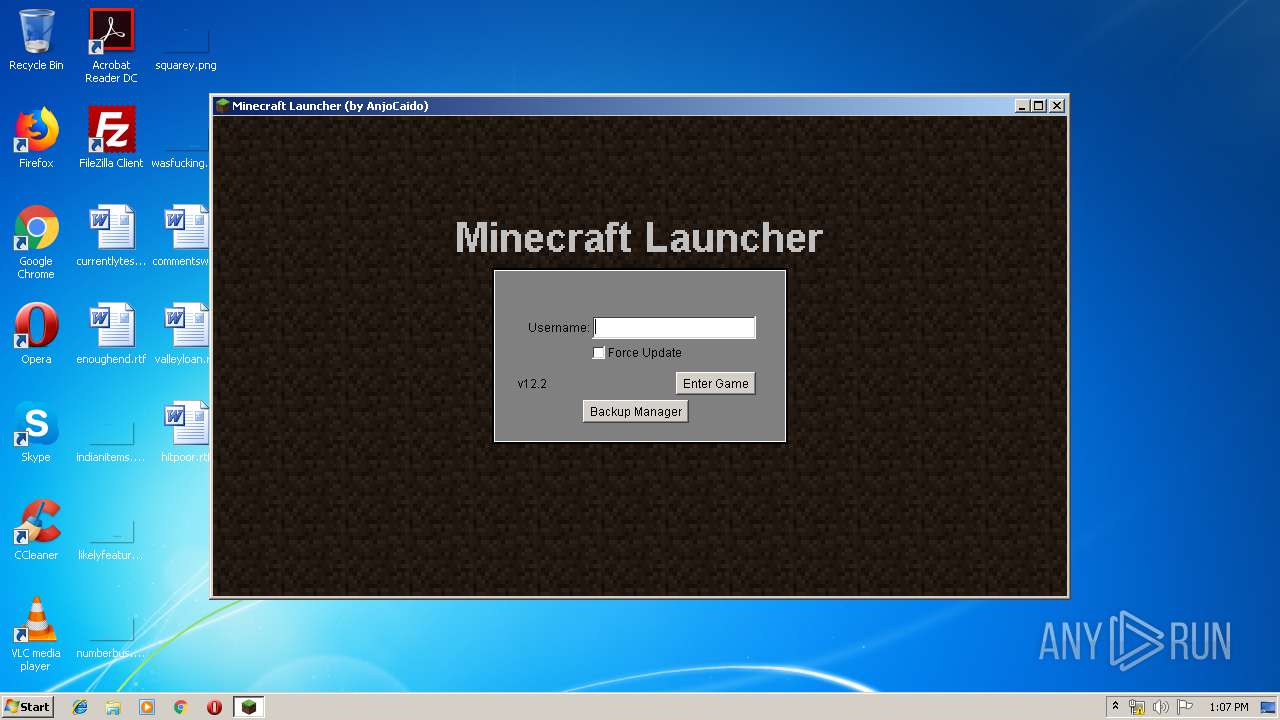
| 1752 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\Minecraft 1.5.2.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
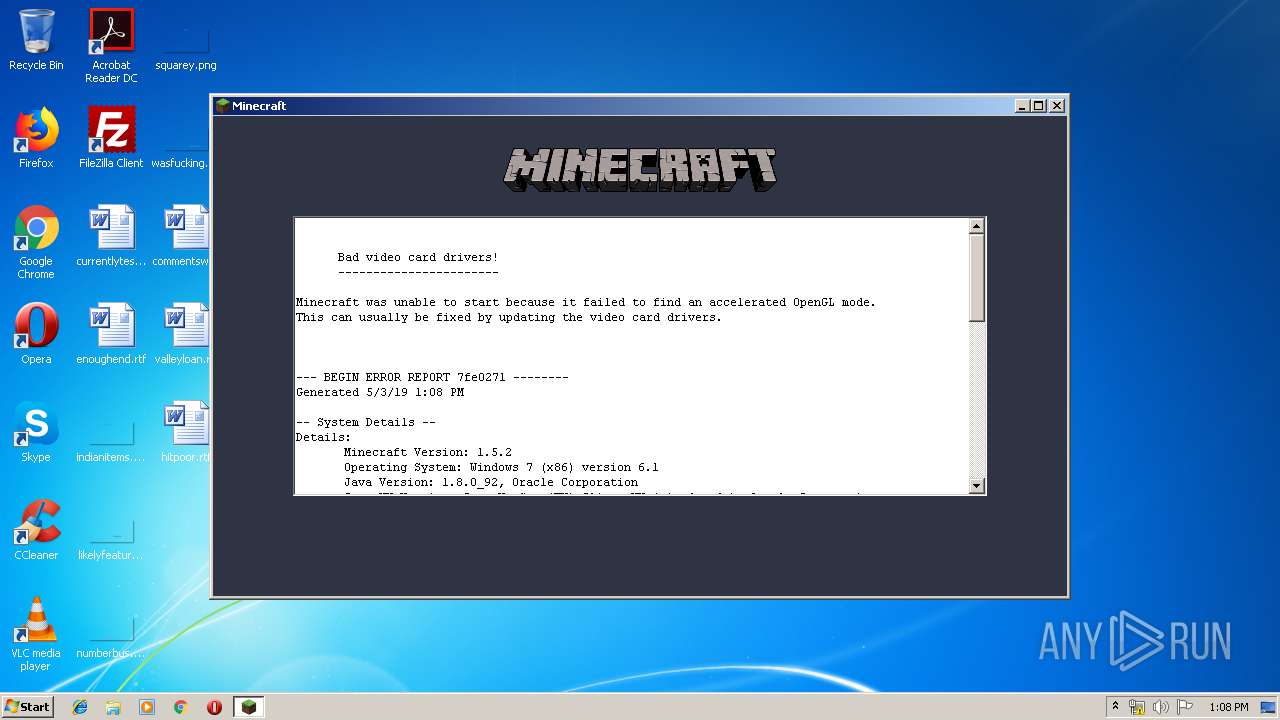
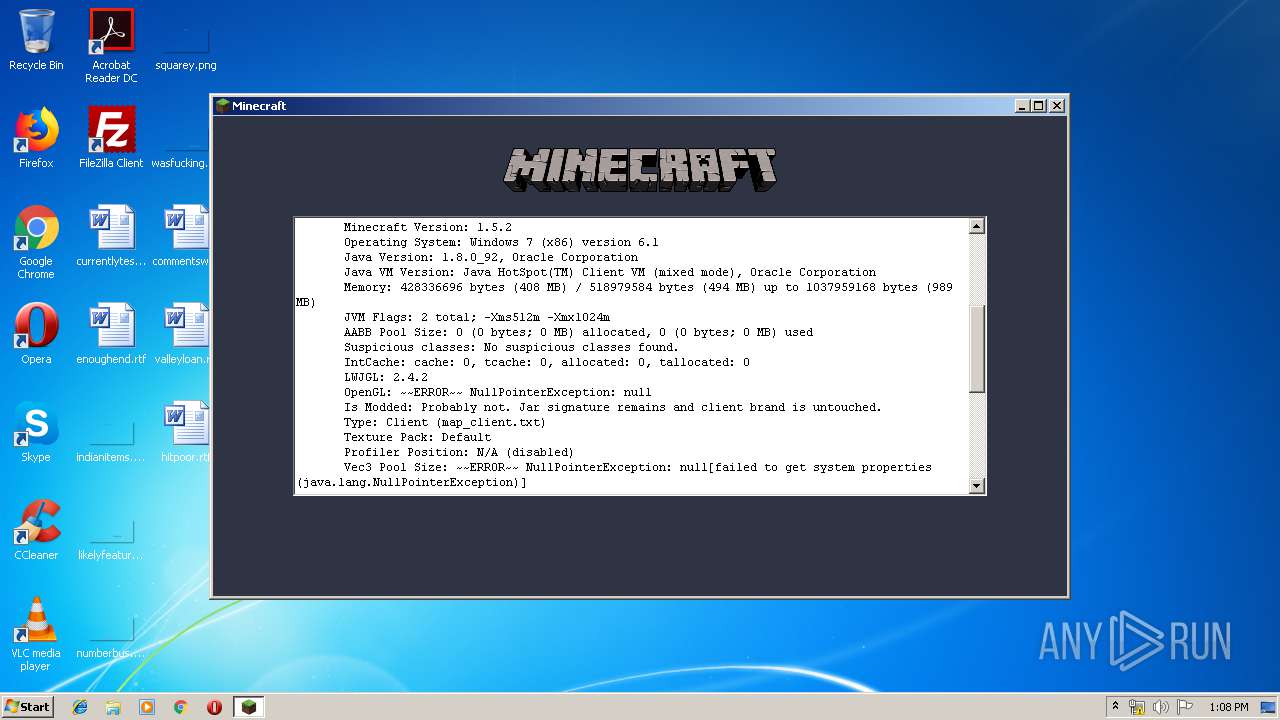
| 3860 | javaw -Xms512m -Xmx1024m -Dsun.java2d.noddraw=true -Dsun.java2d.d3d=false -Dsun.java2d.opengl=false -Dsun.java2d.pmoffscreen=false -classpath "/C:/Users/admin/AppData/Local/Temp/Minecraft 1.5.2.jar" net.minecraft.LauncherFrame | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
7
Read events
7
Write events
0
Delete events
0
Modification events
Executable files
8
Suspicious files
4
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3860 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio2673477093938451432.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio8501765799511810971.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio2507395258132107717.tmp | — | |
MD5:— | SHA256:— | |||
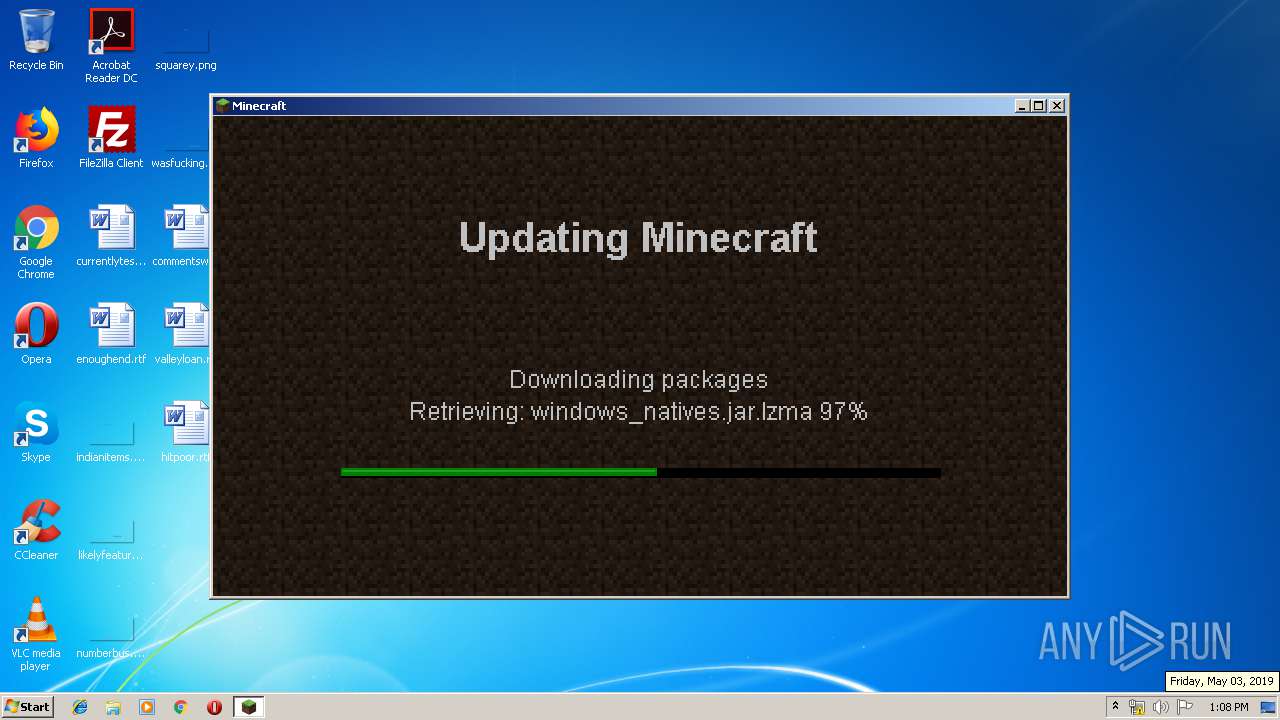
| 3860 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\bin\windows_natives.jar.lzma | — | |
MD5:— | SHA256:— | |||
| 3860 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\bin\windows_natives.jar | — | |
MD5:— | SHA256:— | |||
| 3860 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio4185194156051975885.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 3860 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\lastlogin | text | |
MD5:A058BD8EAC041E27CADAF84E0F676D79 | SHA256:1438E0ED49F9577C28D8A254ADEE5B1462DCFC37C59EA15261B0D2CAE09BD5D0 | |||
| 1752 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:53A1BF05E2D06960566E888424D422F9 | SHA256:CDAA1EB23302972D30A7D2F2B6A0F29A112BBD8513590EC41CFABB225E192526 | |||
| 3860 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:4FCDCF15EF8070685652D0B79C116B8D | SHA256:EE5930E1CA3C08BDE961299ADD01BBD01D52B7C35379D1A6BE89C471C4393C4A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
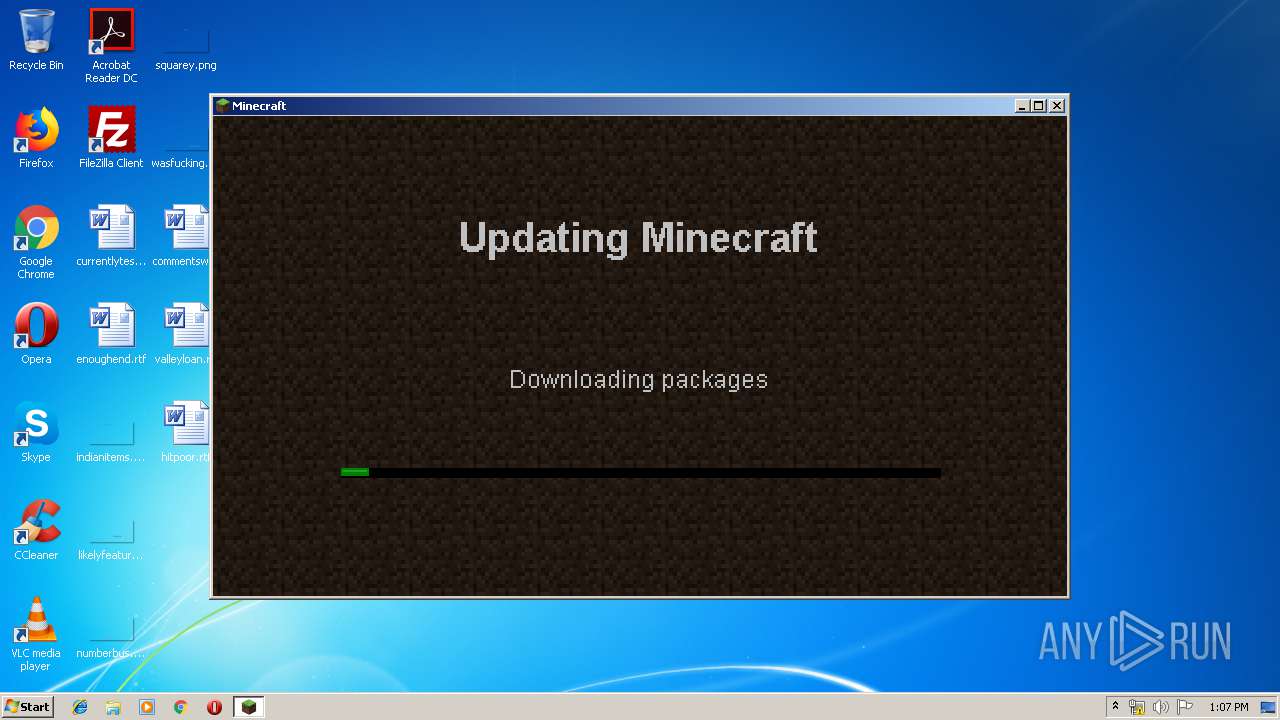
3860 | javaw.exe | HEAD | 200 | 52.216.170.149:80 | http://s3.amazonaws.com/MinecraftDownload/lwjgl.jar | US | — | — | shared |
3860 | javaw.exe | GET | 200 | 52.216.170.149:80 | http://s3.amazonaws.com/MinecraftDownload/jinput.jar | US | compressed | 222 Kb | shared |
3860 | javaw.exe | HEAD | 200 | 52.216.170.149:80 | http://s3.amazonaws.com/MinecraftDownload/jinput.jar | US | — | — | shared |
3860 | javaw.exe | HEAD | 200 | 52.216.170.149:80 | http://s3.amazonaws.com/MinecraftDownload/windows_natives.jar.lzma | US | — | — | shared |
3860 | javaw.exe | GET | 200 | 52.216.170.149:80 | http://s3.amazonaws.com/MinecraftDownload/lwjgl.jar | US | compressed | 721 Kb | shared |
3860 | javaw.exe | HEAD | 200 | 52.216.170.149:80 | http://s3.amazonaws.com/MinecraftDownload/lwjgl_util.jar | US | — | — | shared |
3860 | javaw.exe | GET | 200 | 52.216.170.149:80 | http://s3.amazonaws.com/MinecraftDownload/lwjgl_util.jar | US | compressed | 135 Kb | shared |
3860 | javaw.exe | GET | 200 | 52.216.170.149:80 | http://s3.amazonaws.com/MinecraftDownload/windows_natives.jar.lzma | US | lzma | 479 Kb | shared |
3860 | javaw.exe | GET | 200 | 52.216.170.149:80 | http://s3.amazonaws.com/MinecraftDownload/minecraft.jar | US | compressed | 5.31 Mb | shared |
3860 | javaw.exe | HEAD | 200 | 52.216.170.149:80 | http://s3.amazonaws.com/MinecraftDownload/minecraft.jar | US | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3860 | javaw.exe | 52.216.170.149:80 | s3.amazonaws.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s3.amazonaws.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3860 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3860 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3860 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |