| File name: | AutoKMS.exe |
| Full analysis: | https://app.any.run/tasks/c2848626-6947-46ed-a5ac-d0d49e2a795c |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2024, 14:32:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | C746CD166372F3C6F364B62F2C2C8B20 |
| SHA1: | F1EEBA9E906322A37AA1EFB1D2FAAAD78E217587 |
| SHA256: | 3D1D4CE1DB1EA2563C361CBD66A5471F10D84D344C057D753459F311A187AC2F |
| SSDEEP: | 98304:dPEc61x3BJELz8gu9g4TfQgloemE1pFYDp9k8YBNnna9rqJ2TvjH+aBoa5xfGaHy:dqyQ |
MALICIOUS
Drops the executable file immediately after the start
- AutoKMS.exe (PID: 4080)
SUSPICIOUS
Reads security settings of Internet Explorer
- AutoKMS.exe (PID: 4080)
Reads the Internet Settings
- AutoKMS.exe (PID: 4080)
INFO
Checks supported languages
- AutoKMS.exe (PID: 4080)
Reads the computer name
- AutoKMS.exe (PID: 4080)
Reads the machine GUID from the registry
- AutoKMS.exe (PID: 4080)
Creates files in the program directory
- AutoKMS.exe (PID: 4080)
Create files in a temporary directory
- AutoKMS.exe (PID: 4080)
Reads Microsoft Office registry keys
- AutoKMS.exe (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:07:18 23:11:28+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3363328 |
| InitializedDataSize: | 374784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3370b8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 2.5.2.0 |
| ProductVersionNumber: | 2.5.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | AutoKMS |
| FileVersion: | 2.5.2.0 |
| InternalName: | AutoKMS.exe |
| LegalCopyright: | CODYQX4 |
| OriginalFileName: | AutoKMS.exe |
| ProductName: | AutoKMS |
| ProductVersion: | 2.5.2.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
41
Monitored processes
2
Malicious processes
0
Suspicious processes
1
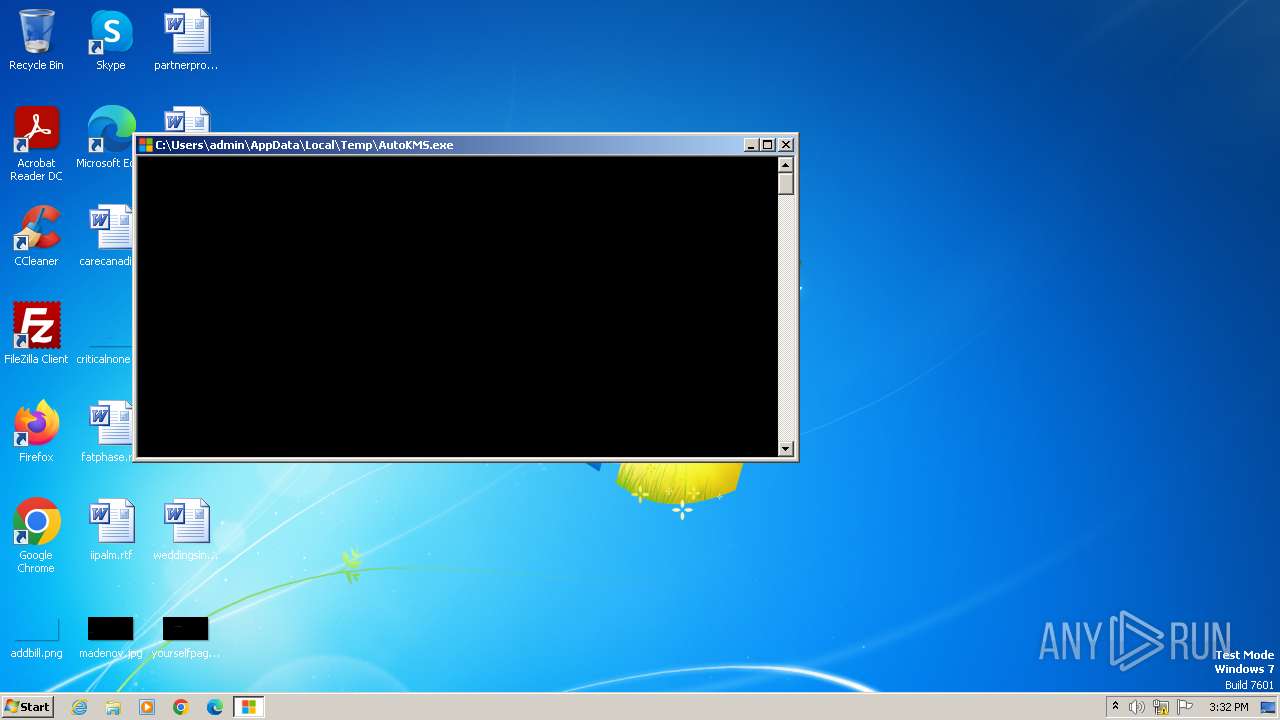
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3976 | "C:\Users\admin\AppData\Local\Temp\AutoKMS.exe" | C:\Users\admin\AppData\Local\Temp\AutoKMS.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AutoKMS Exit code: 3221226540 Version: 2.5.2.0 Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\AppData\Local\Temp\AutoKMS.exe" | C:\Users\admin\AppData\Local\Temp\AutoKMS.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: AutoKMS Exit code: 0 Version: 2.5.2.0 Modules
| |||||||||||||||
Total events
1 776
Read events
1 768
Write events
8
Delete events
0
Modification events
| (PID) Process: | (4080) AutoKMS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4080) AutoKMS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4080) AutoKMS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4080) AutoKMS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | AutoKMS.exe | C:\ProgramData\Microsoft Toolkit\Settings.xml | xml | |
MD5:A97C232B9BE25E5437B15E1EA7DE11D6 | SHA256:062592BB39713ABB43C09B0A1B35B45570E1581E82CD7A23AE9AD0338E01518C | |||
| 4080 | AutoKMS.exe | C:\Users\admin\AppData\Local\Temp\AutoKMS.log | text | |
MD5:527AA64BCE310783522CA4D4908C6D5D | SHA256:969D6D5B8740A5AD407FDB7785750174D51CE4CE5BB968C7D5B871B72EEE137A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |