| File name: | WaffMEMZ-1.0-Destructive.exe |
| Full analysis: | https://app.any.run/tasks/abf878c7-2924-4a02-94a2-a1d358a17fb5 |
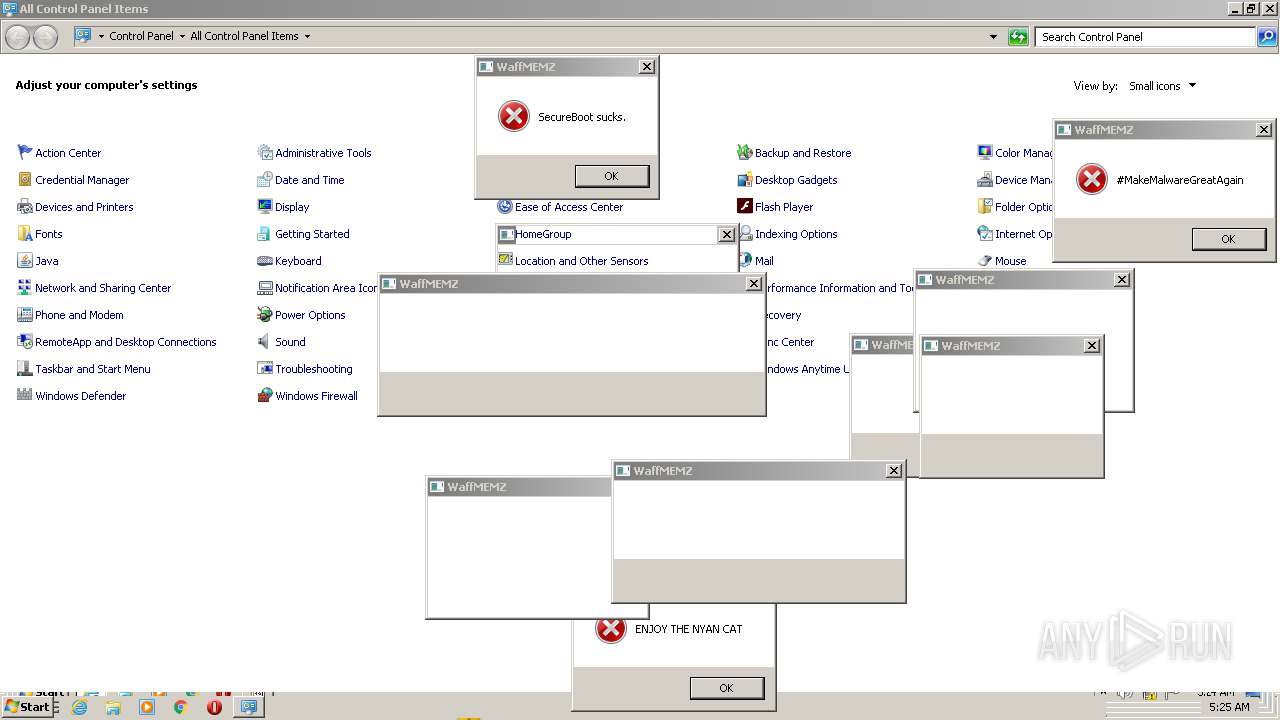
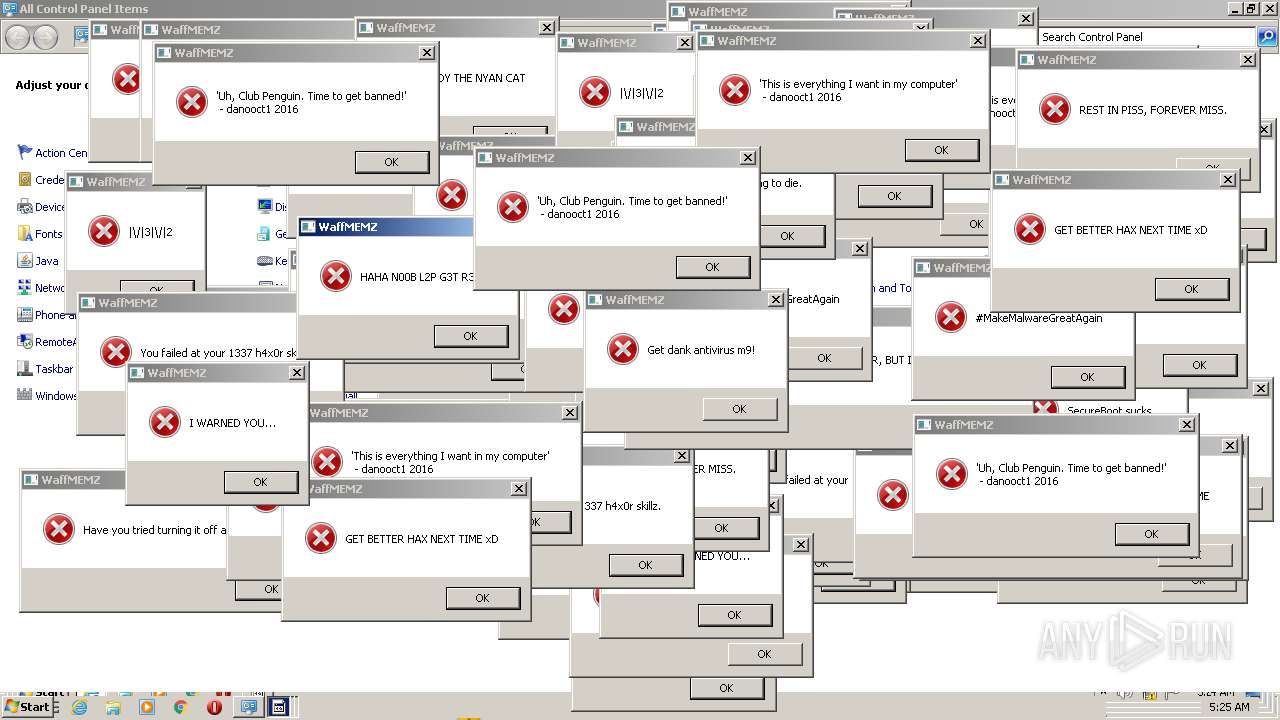
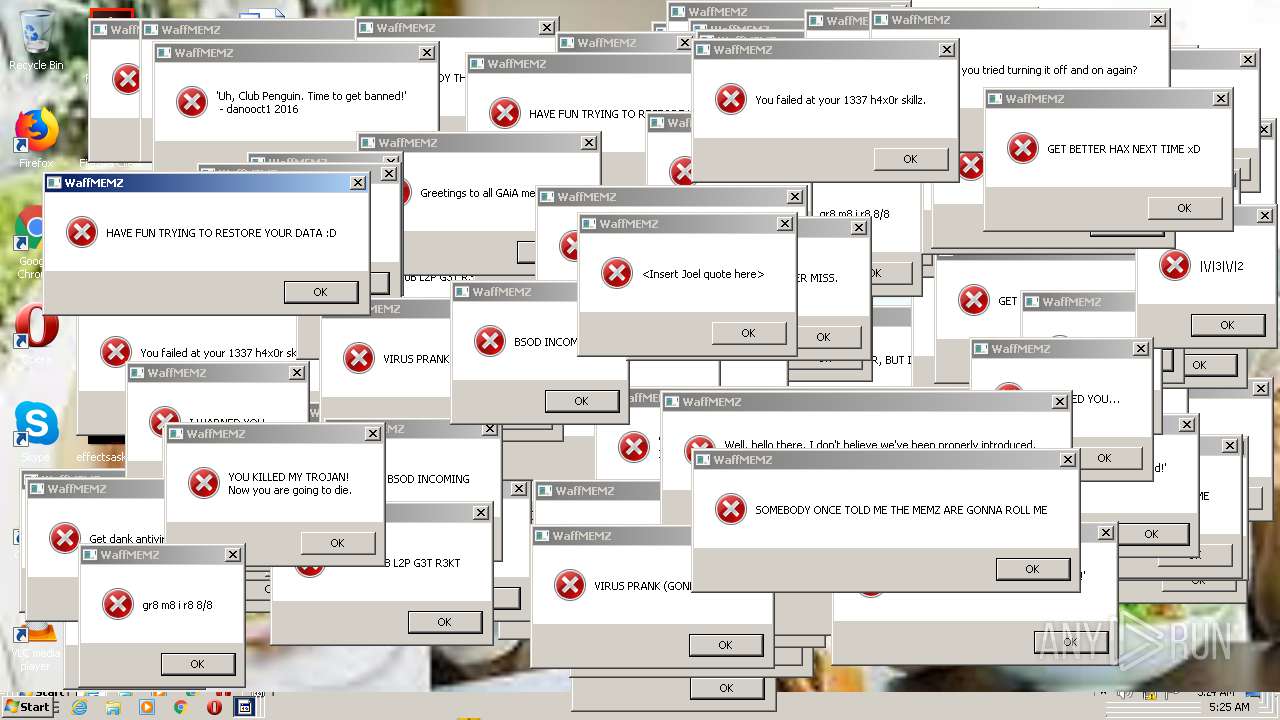
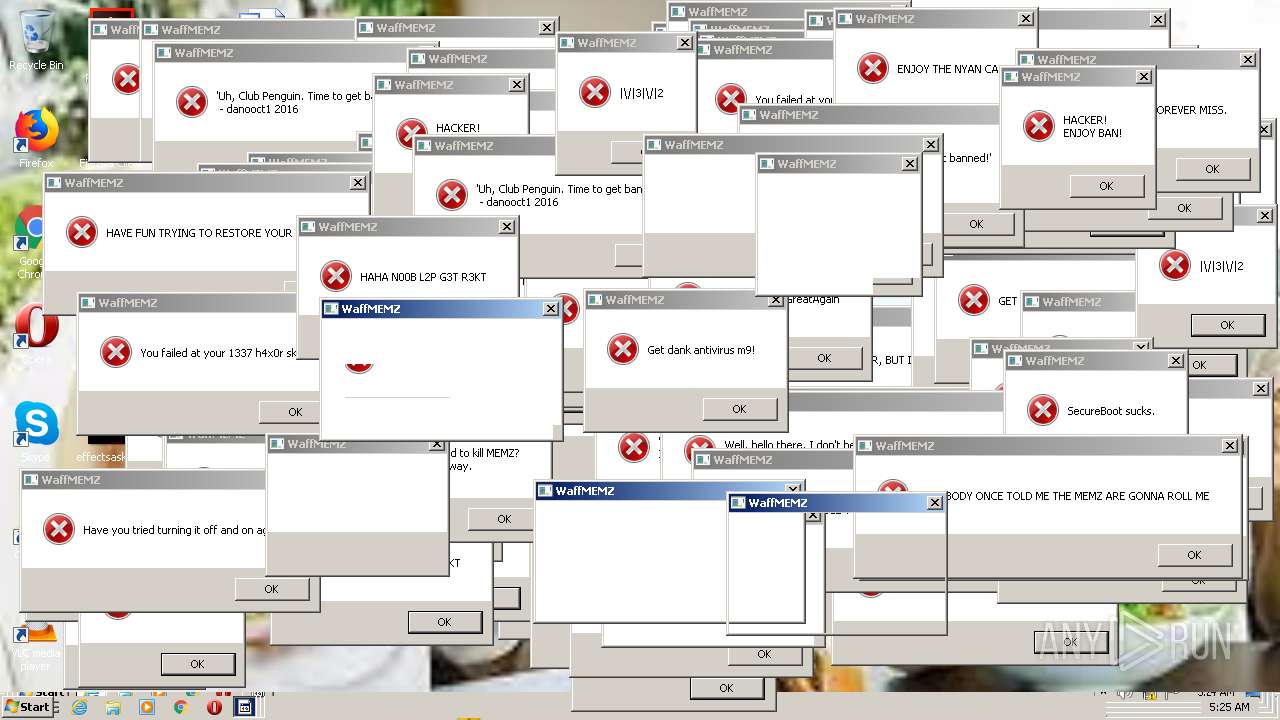
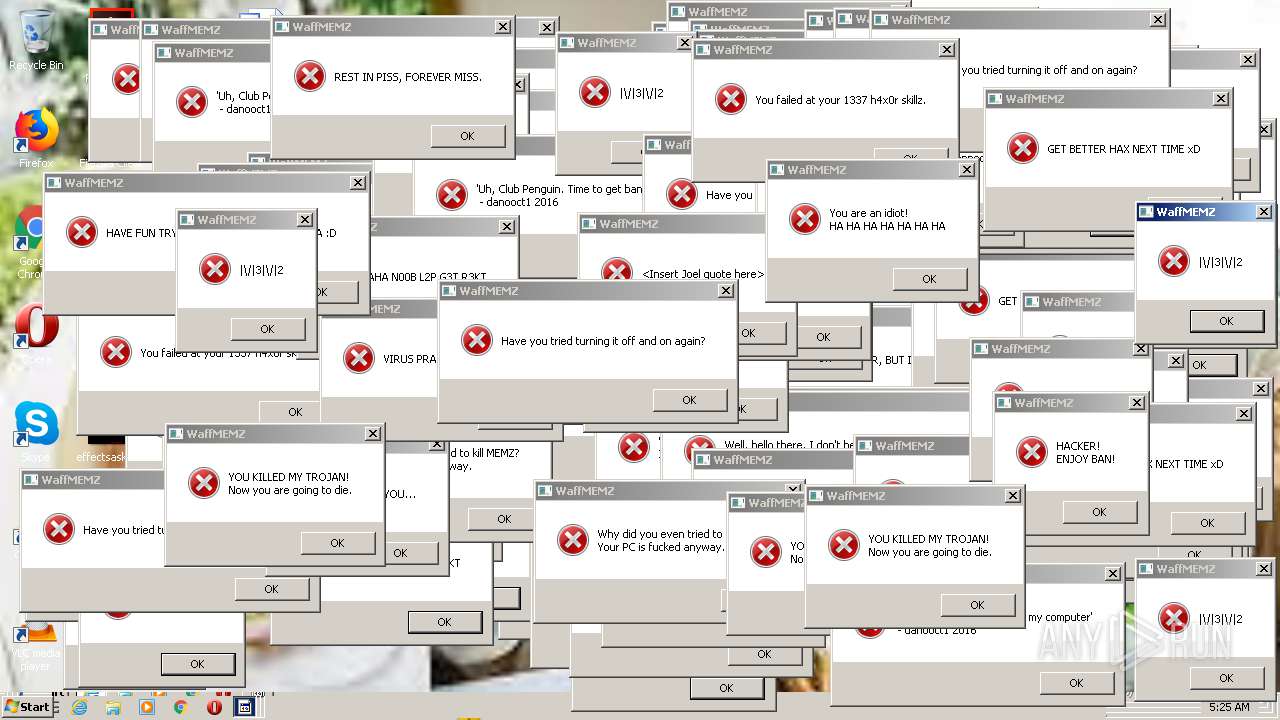
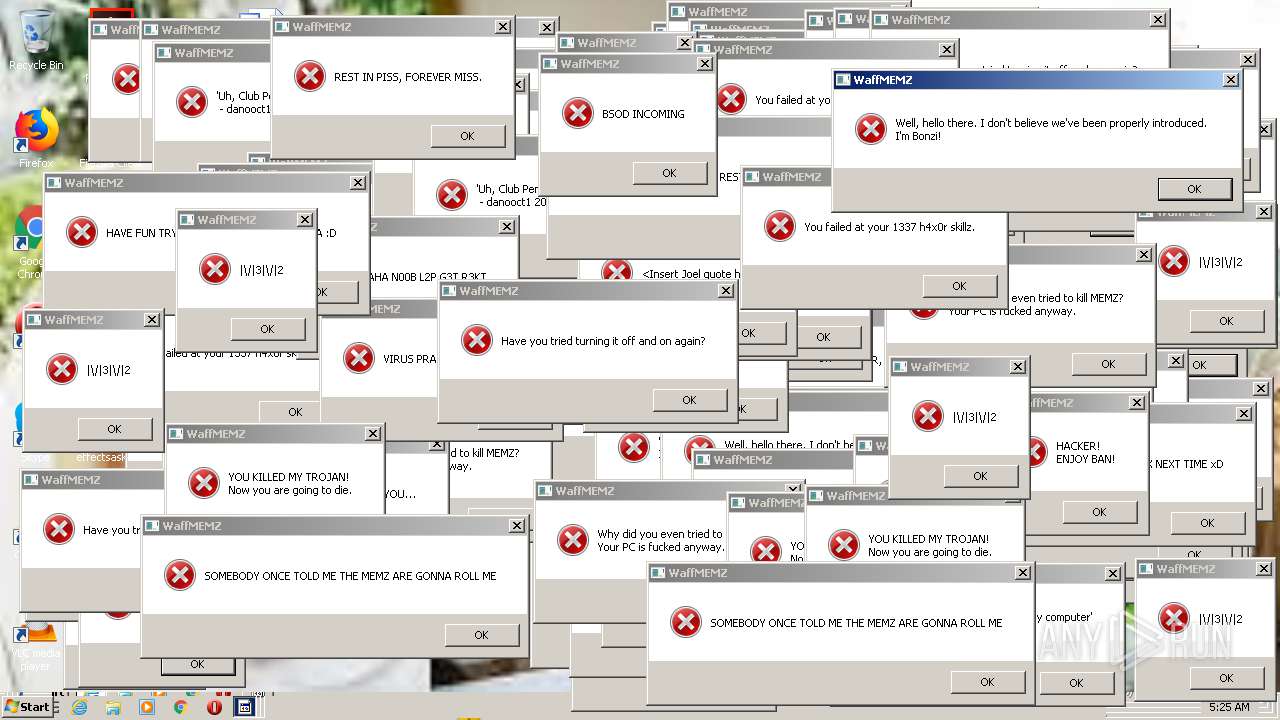
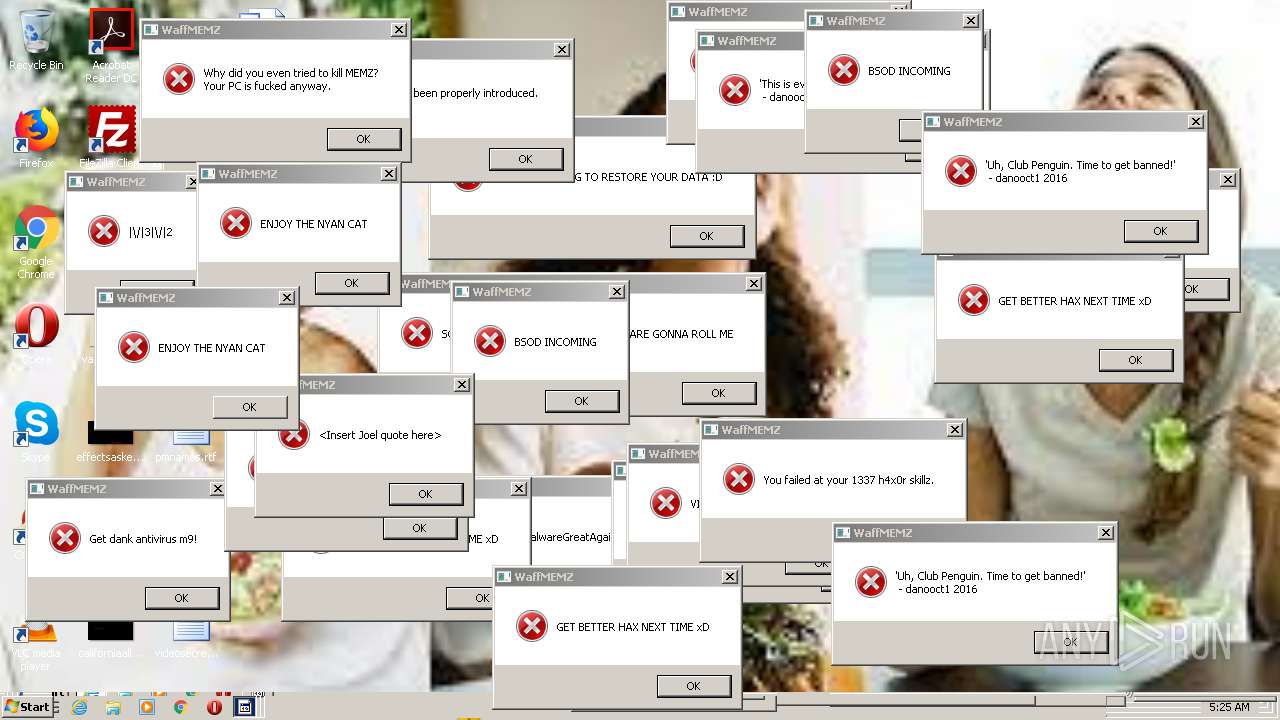
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2021, 04:20:14 |
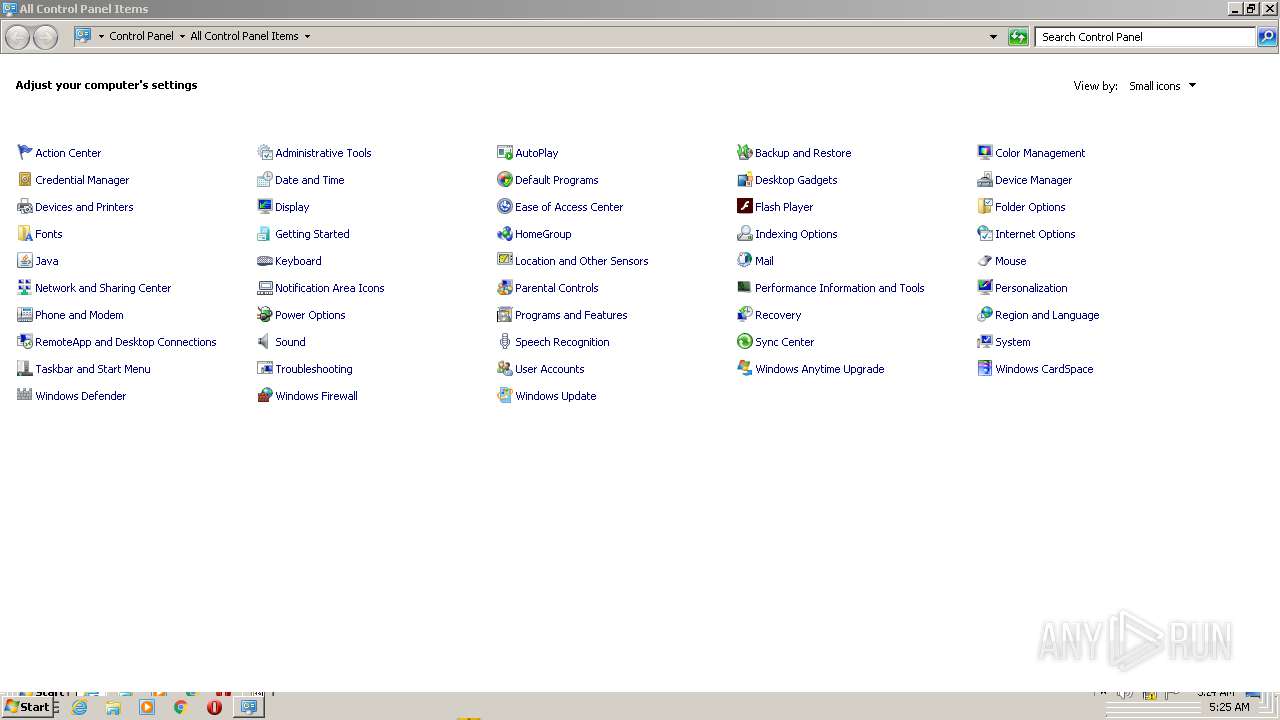
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 90611031CB0669CE1CA71FA3D04F6E47 |
| SHA1: | 5E2C3015356CFA19D180C7D76BC73E60A2DD63C0 |
| SHA256: | 3D1C271C943780768EF58880C4A402811ADD9EA4A4CF5DAB4C5B679F160EE373 |
| SSDEEP: | 384:ZTEIVEFqcIqq05E7zYyC3mDUq1bbCpczB+Tgvg2NZTX:5EIuFqcIqqzsyC3EVXr4TgJNd |
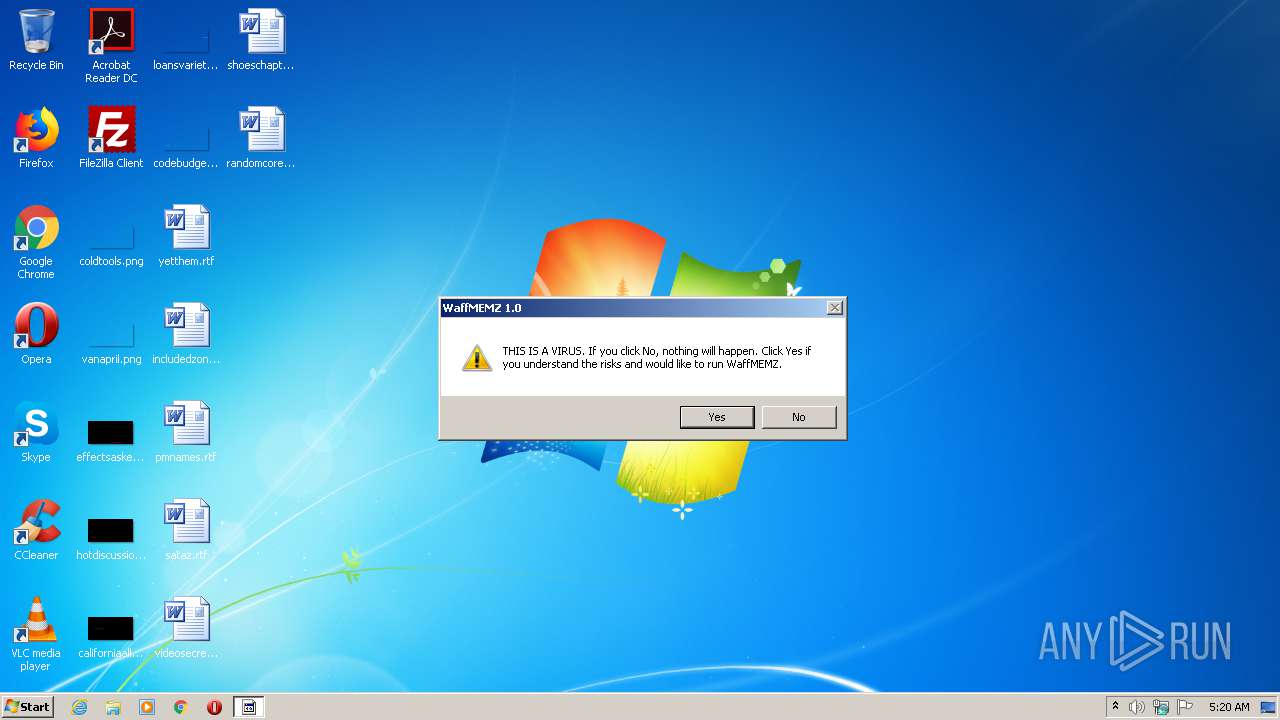
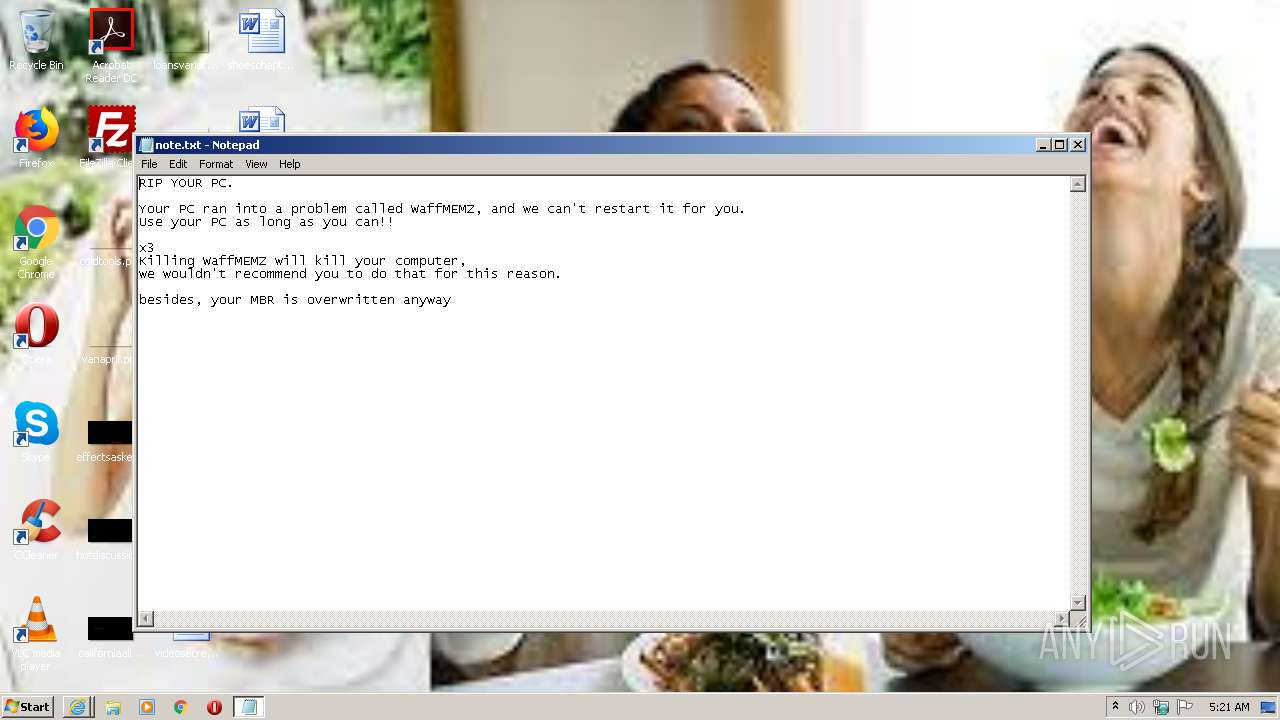
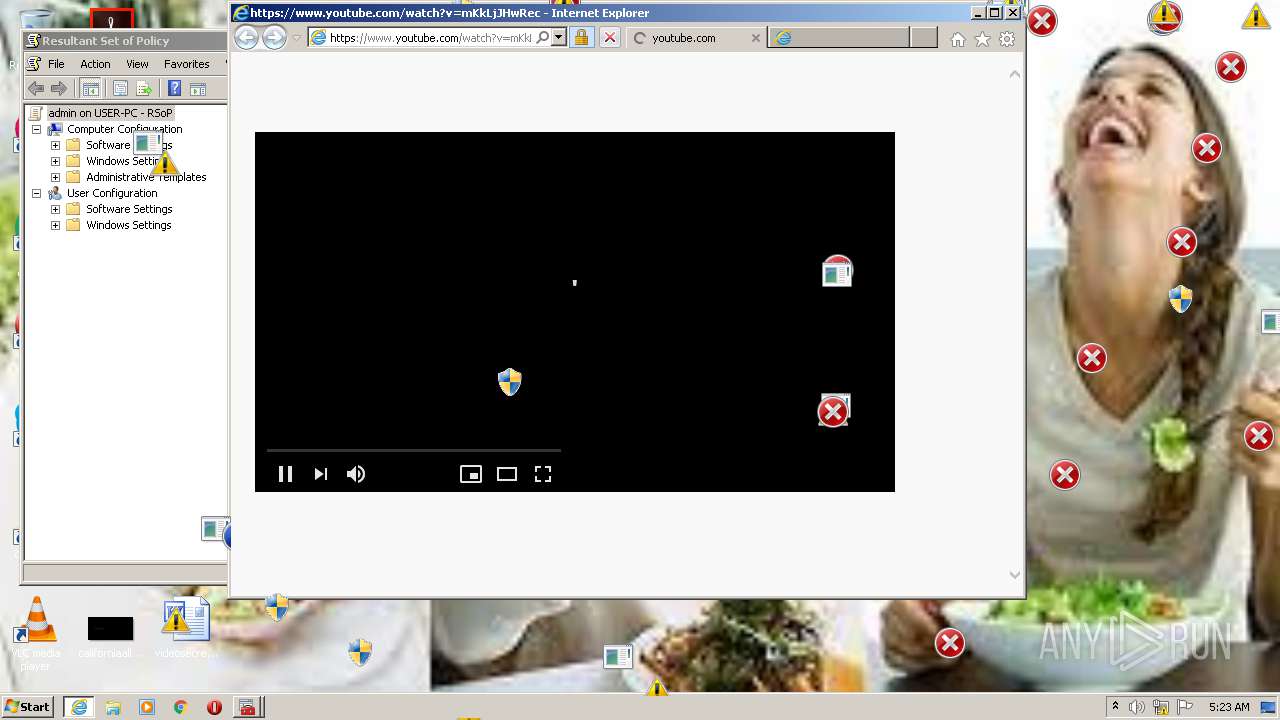
MALICIOUS
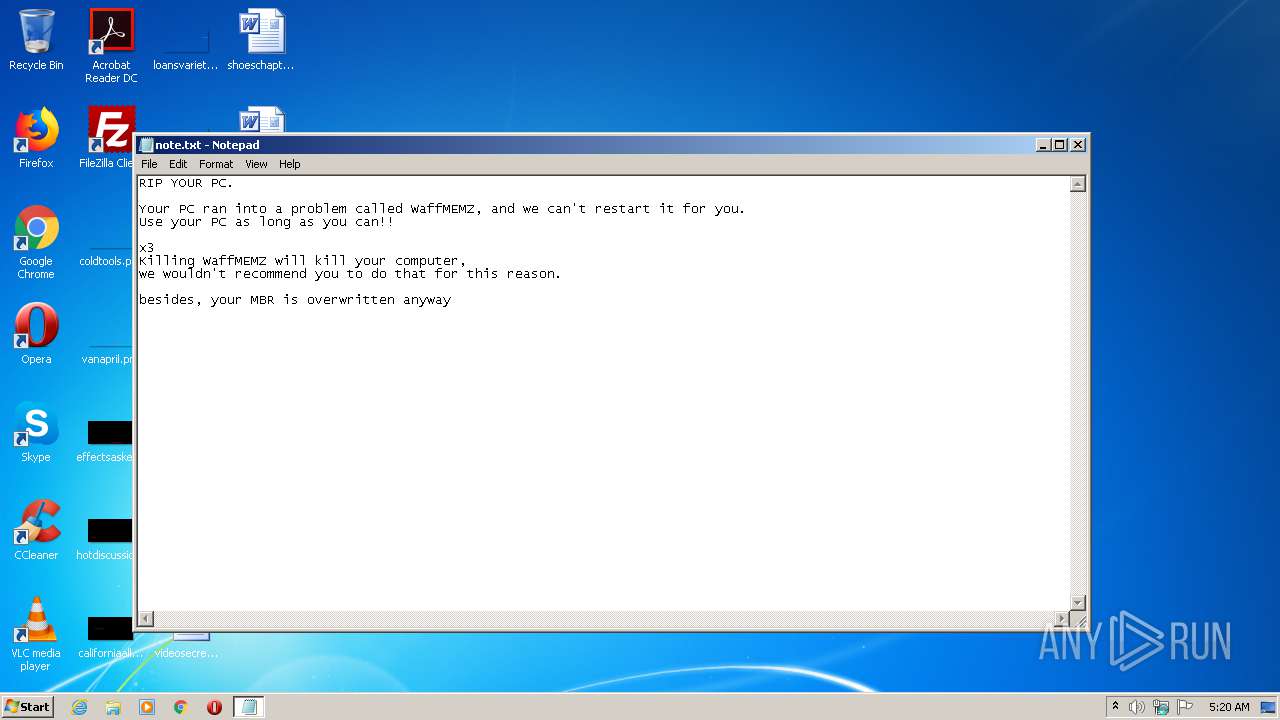
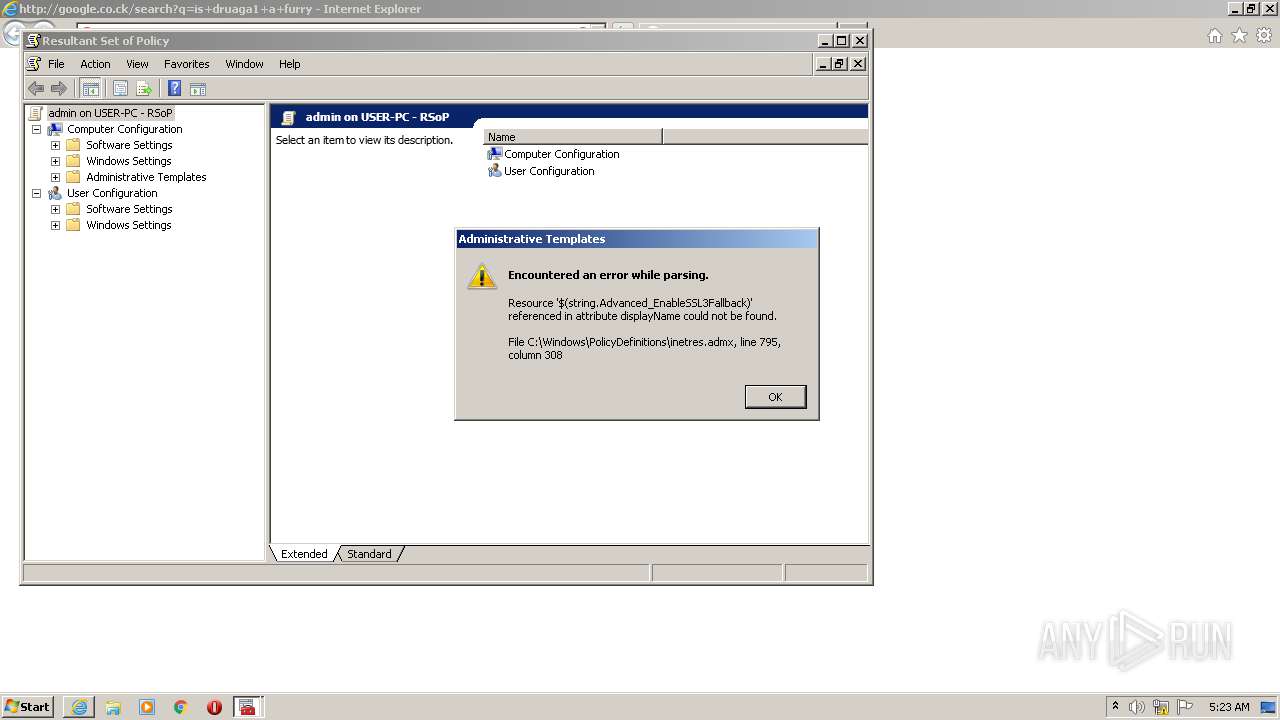
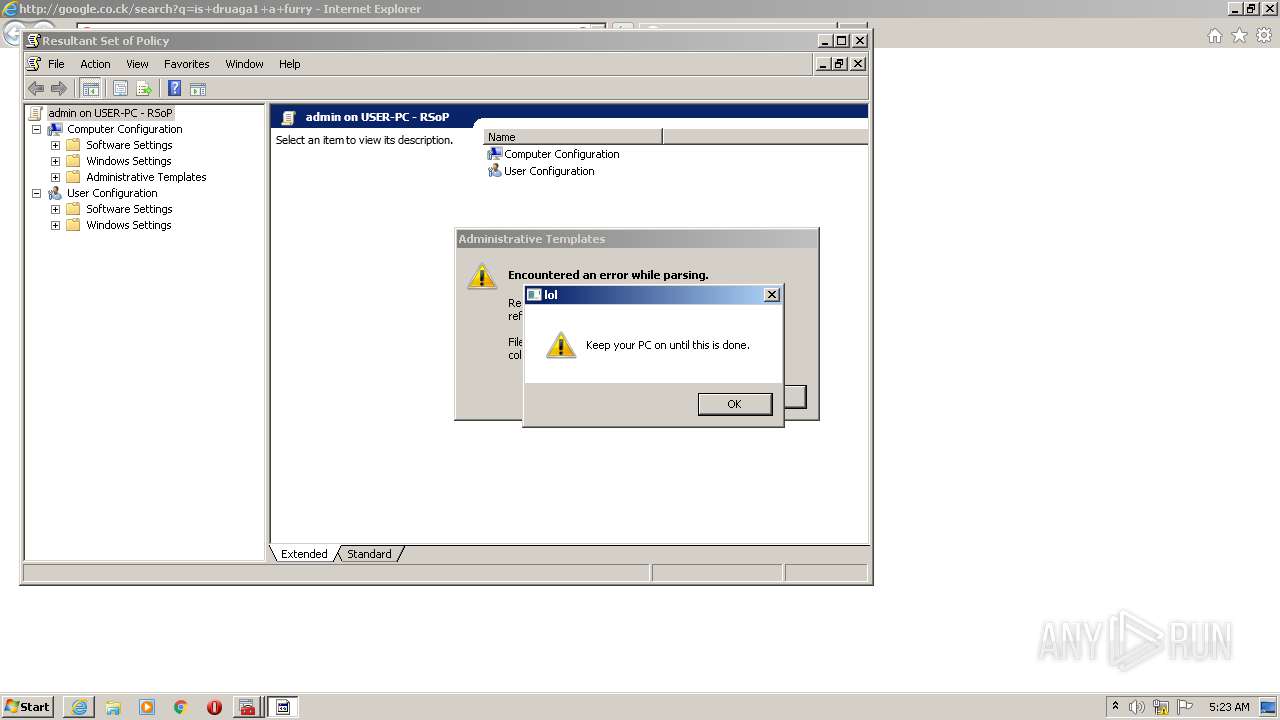
Low-level write access rights to disk partition
- WaffMEMZ-1.0-Destructive.exe (PID: 2432)
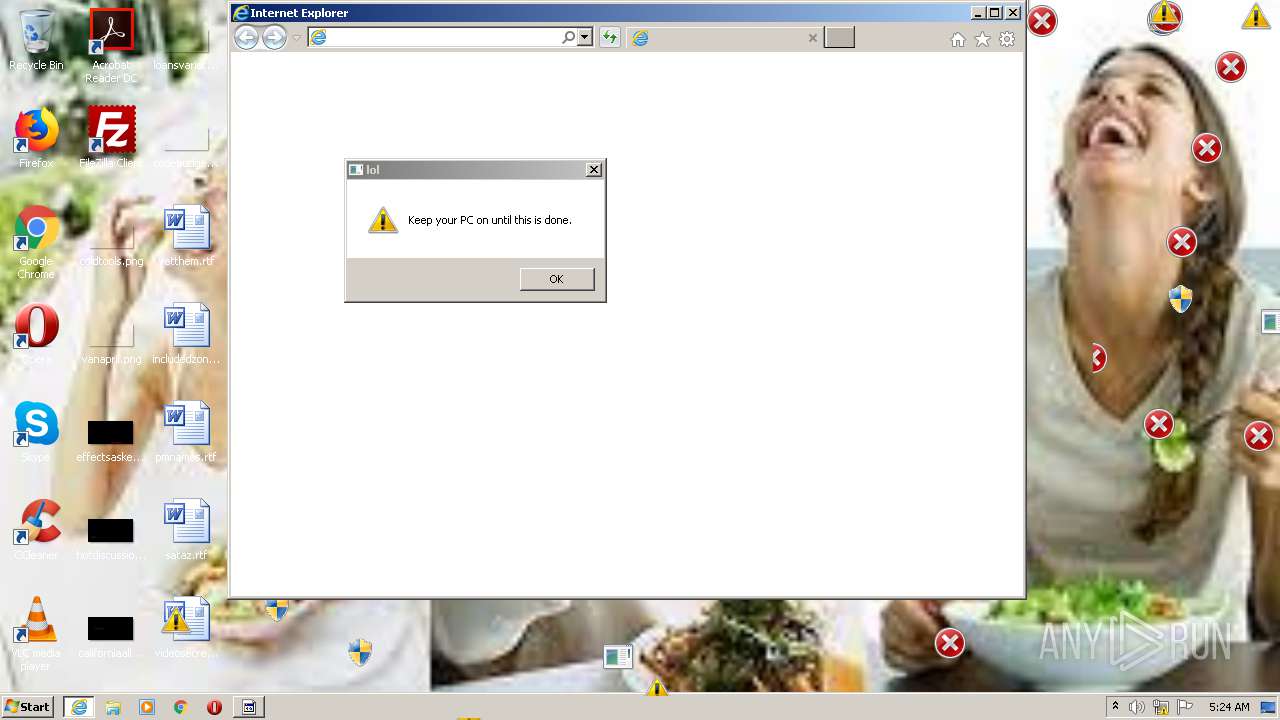
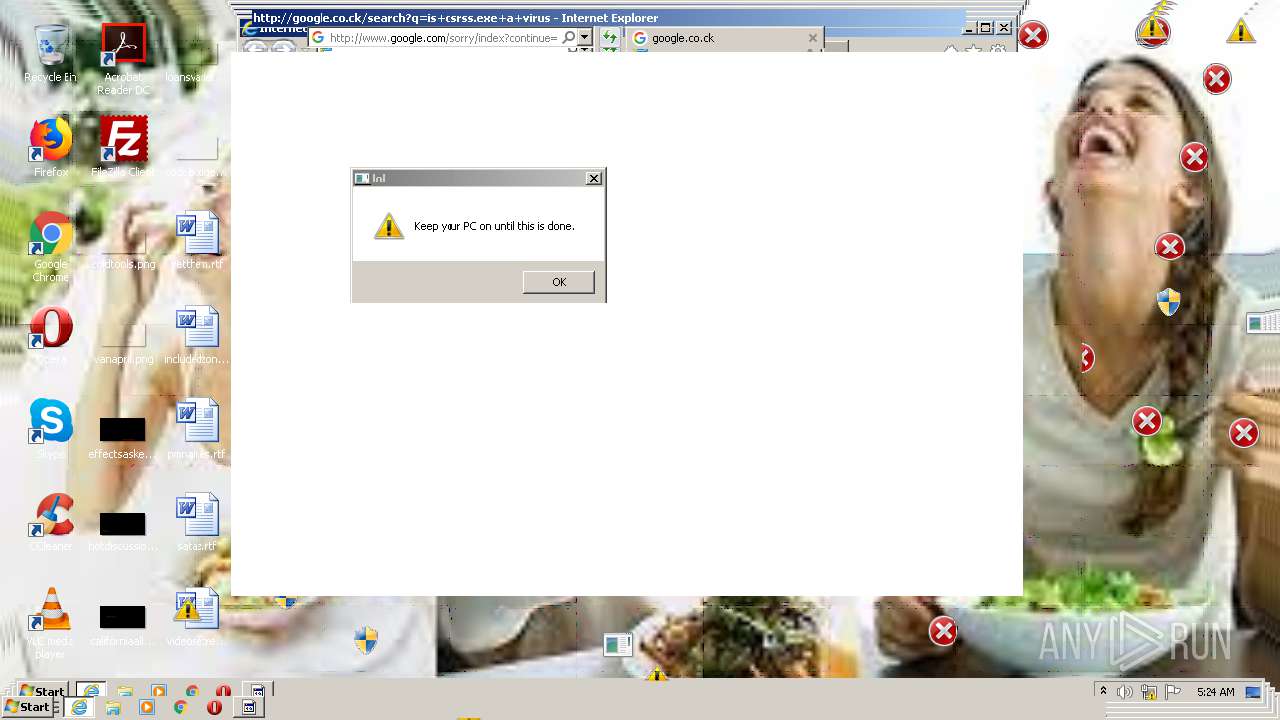
Runs app for hidden code execution
- WaffMEMZ-1.0-Destructive.exe (PID: 2432)
SUSPICIOUS
Low-level read access rights to disk partition
- WaffMEMZ-1.0-Destructive.exe (PID: 2432)
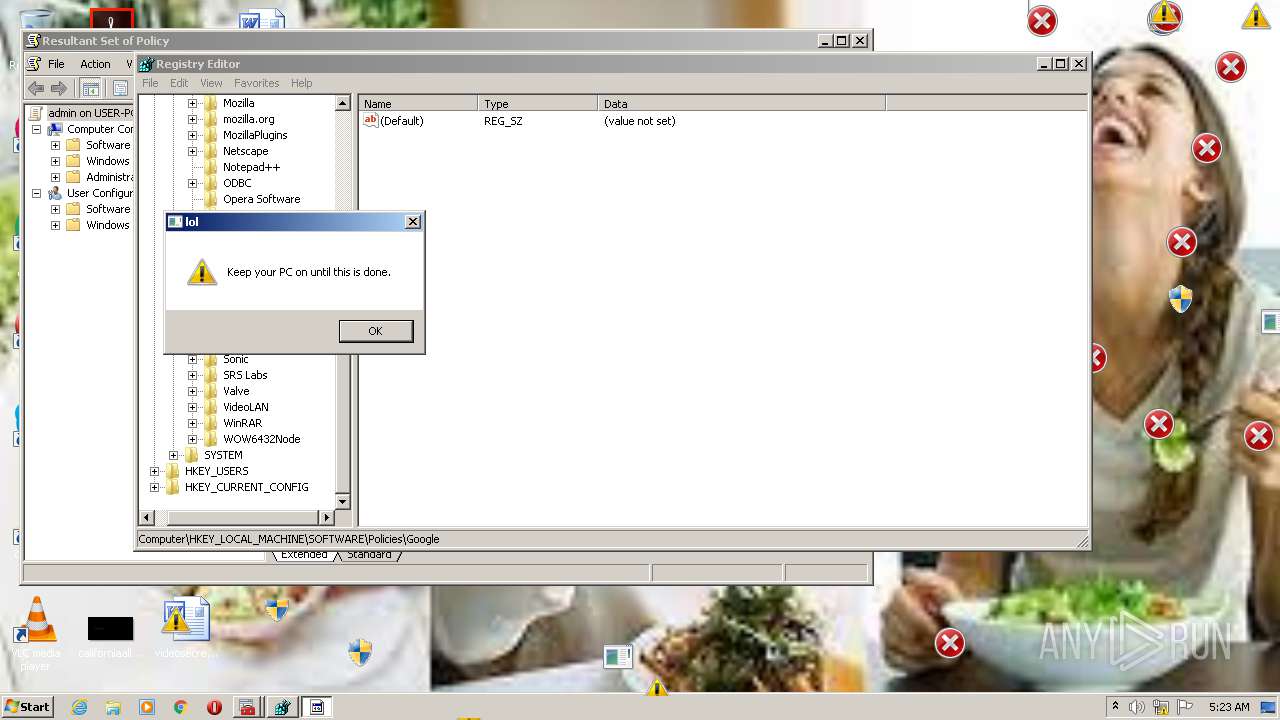
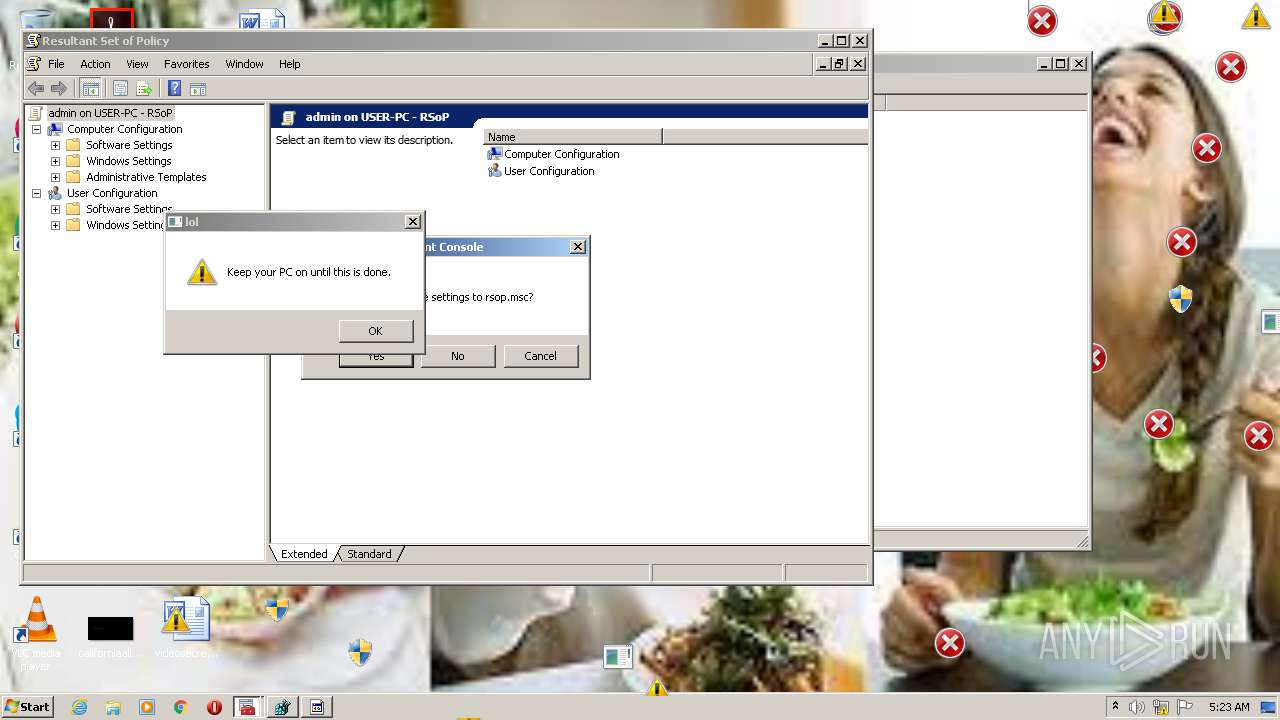
Application launched itself
- WaffMEMZ-1.0-Destructive.exe (PID: 3592)
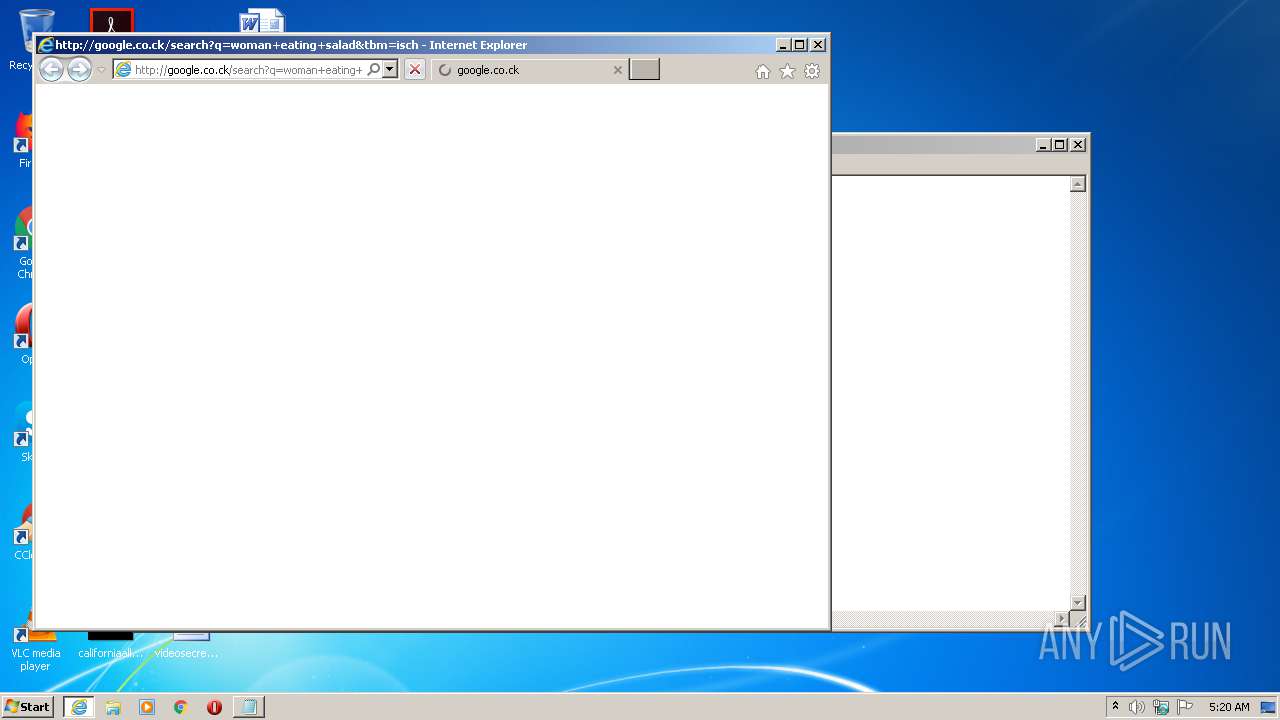
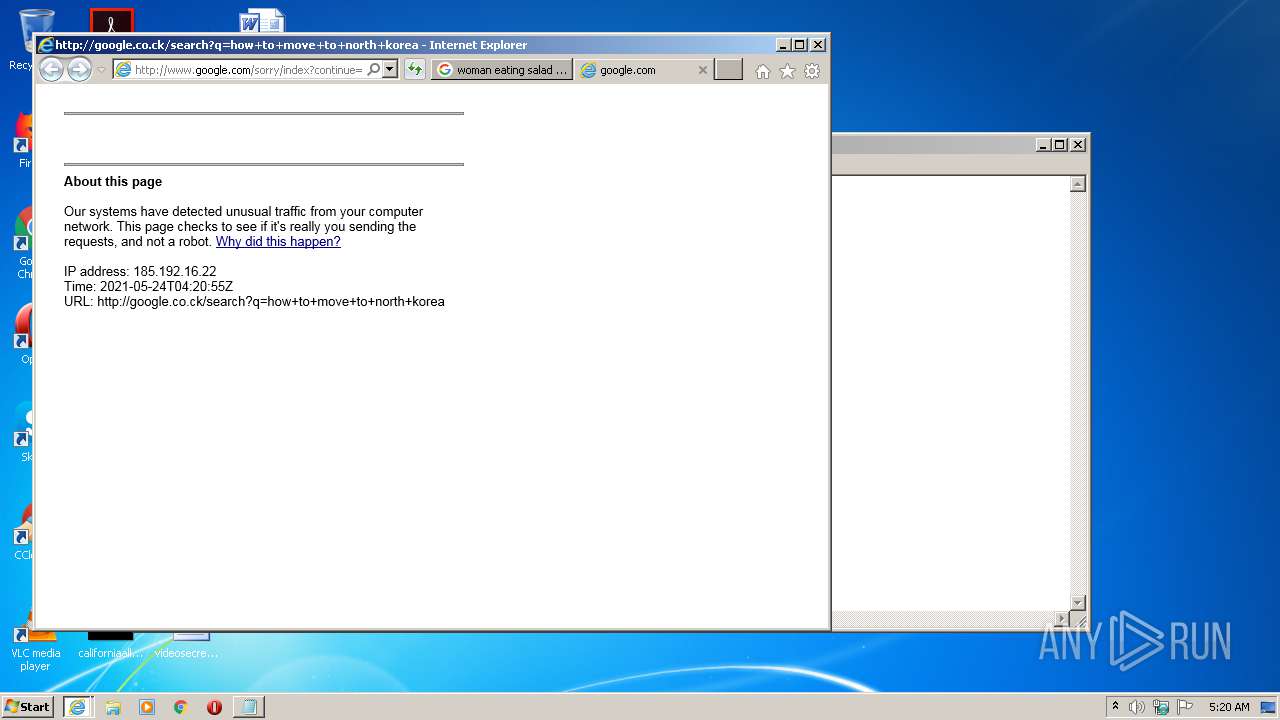
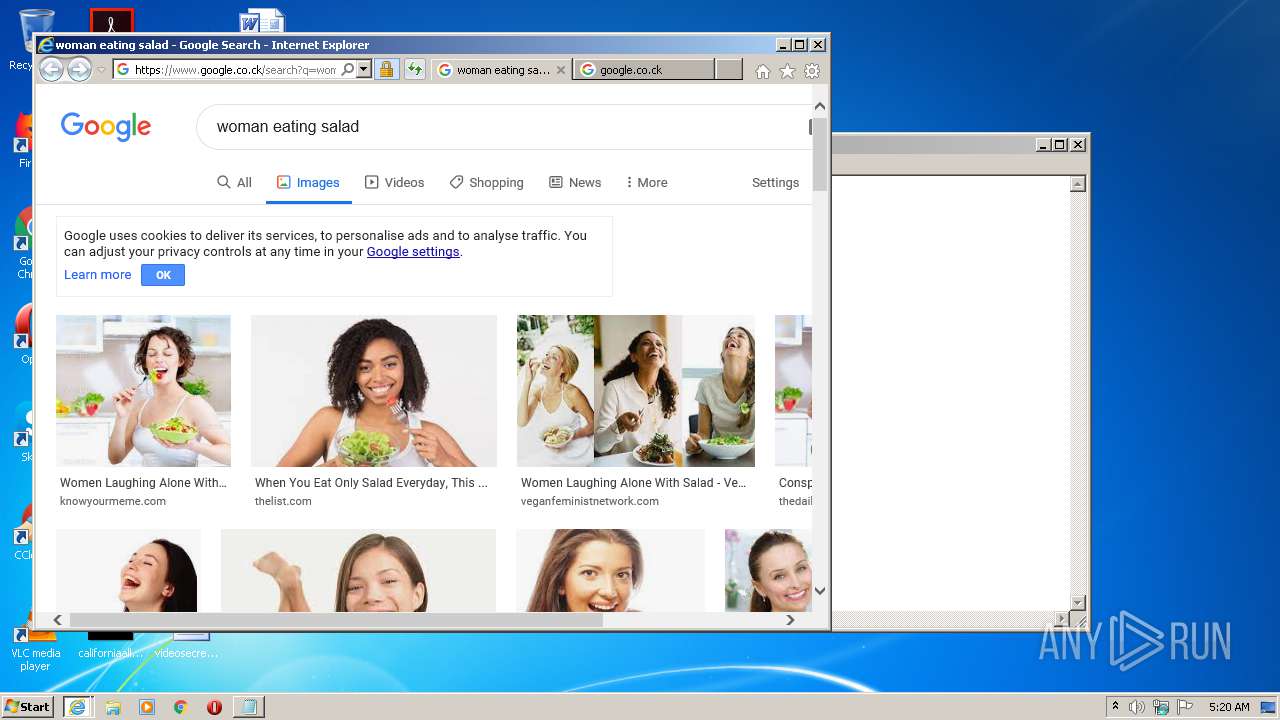
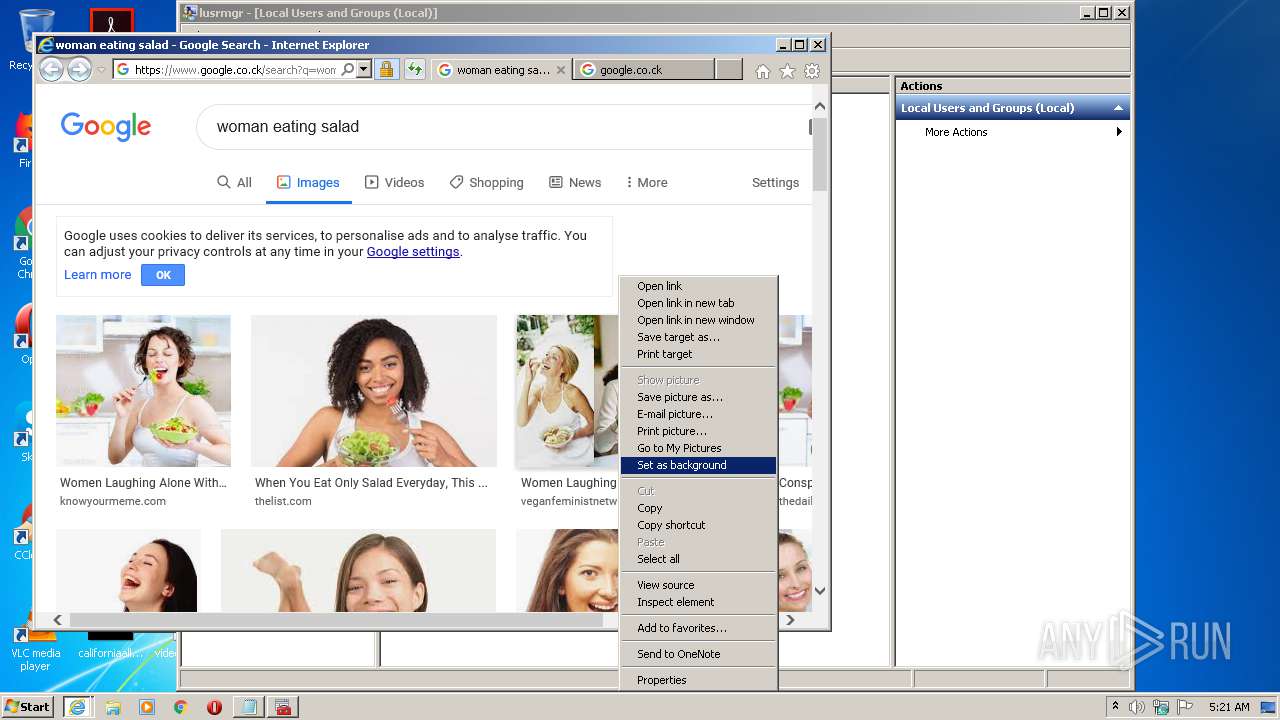
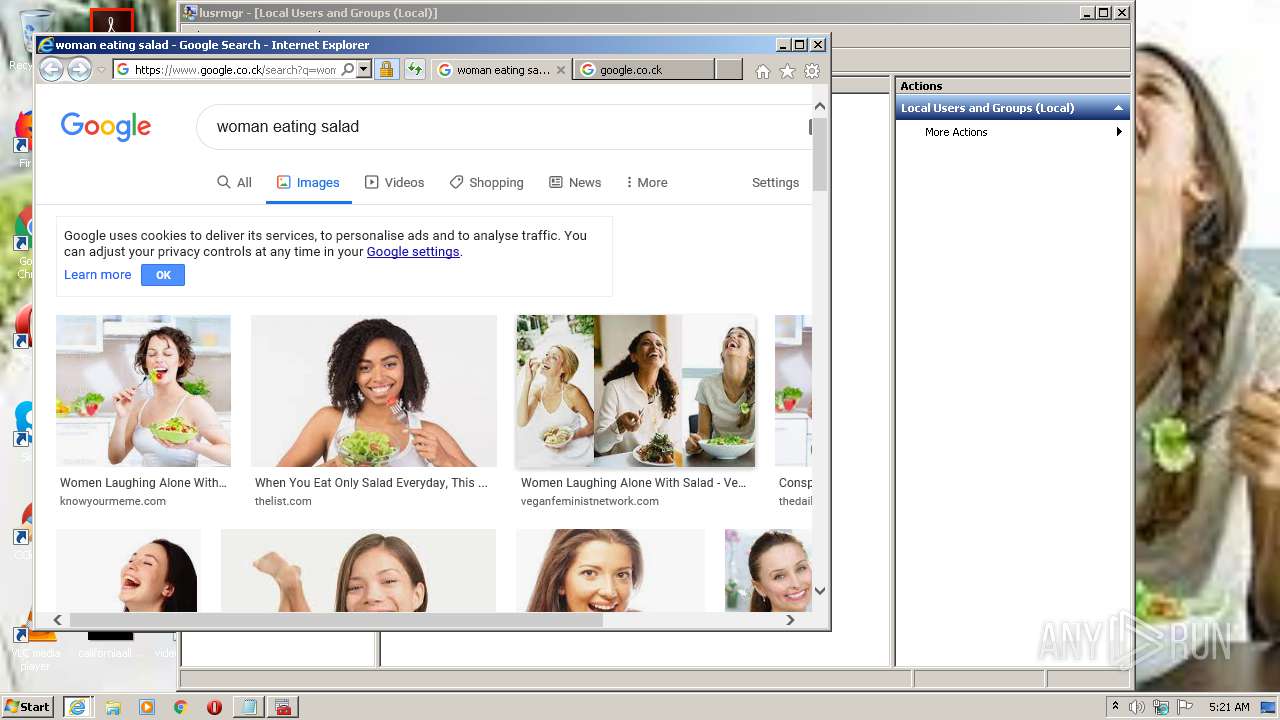
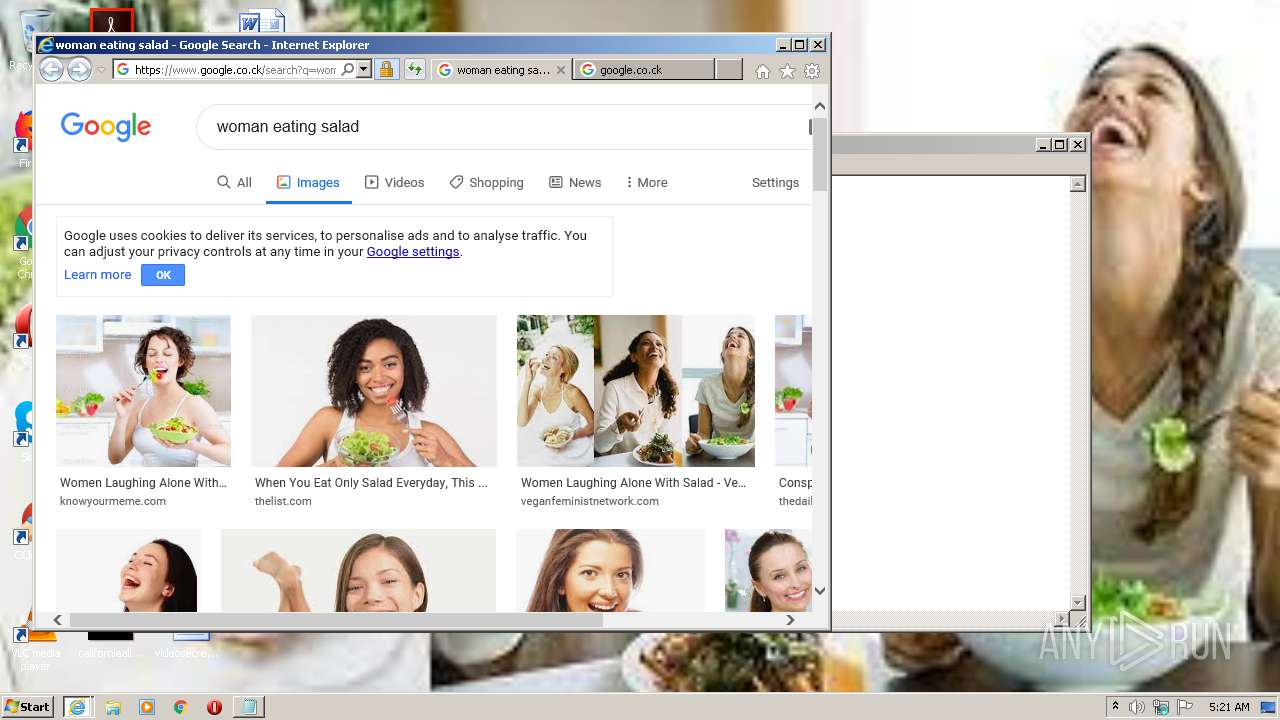
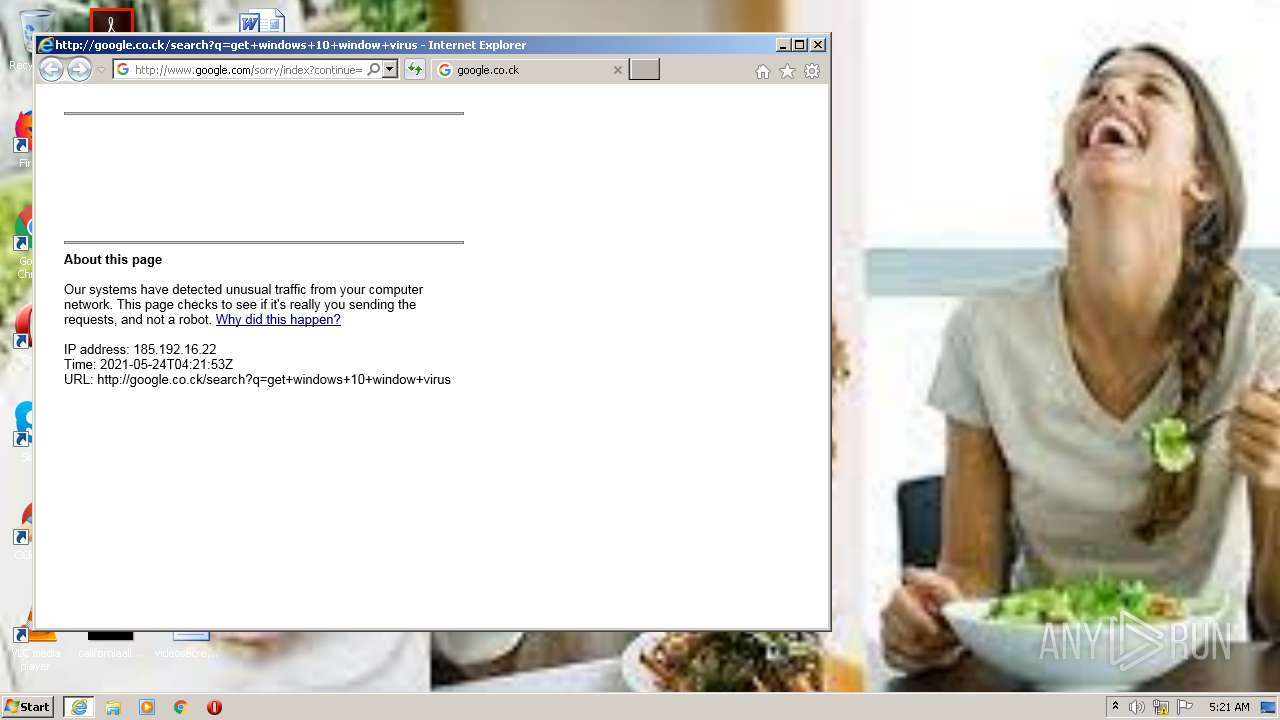
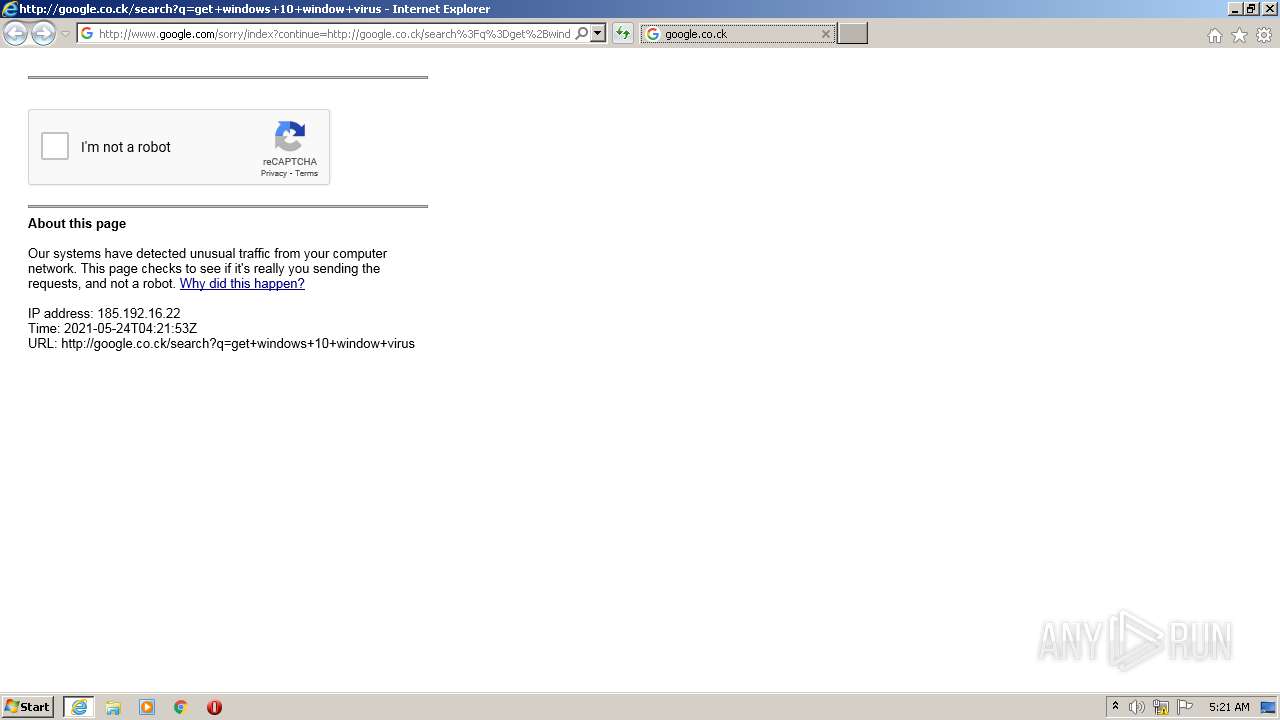
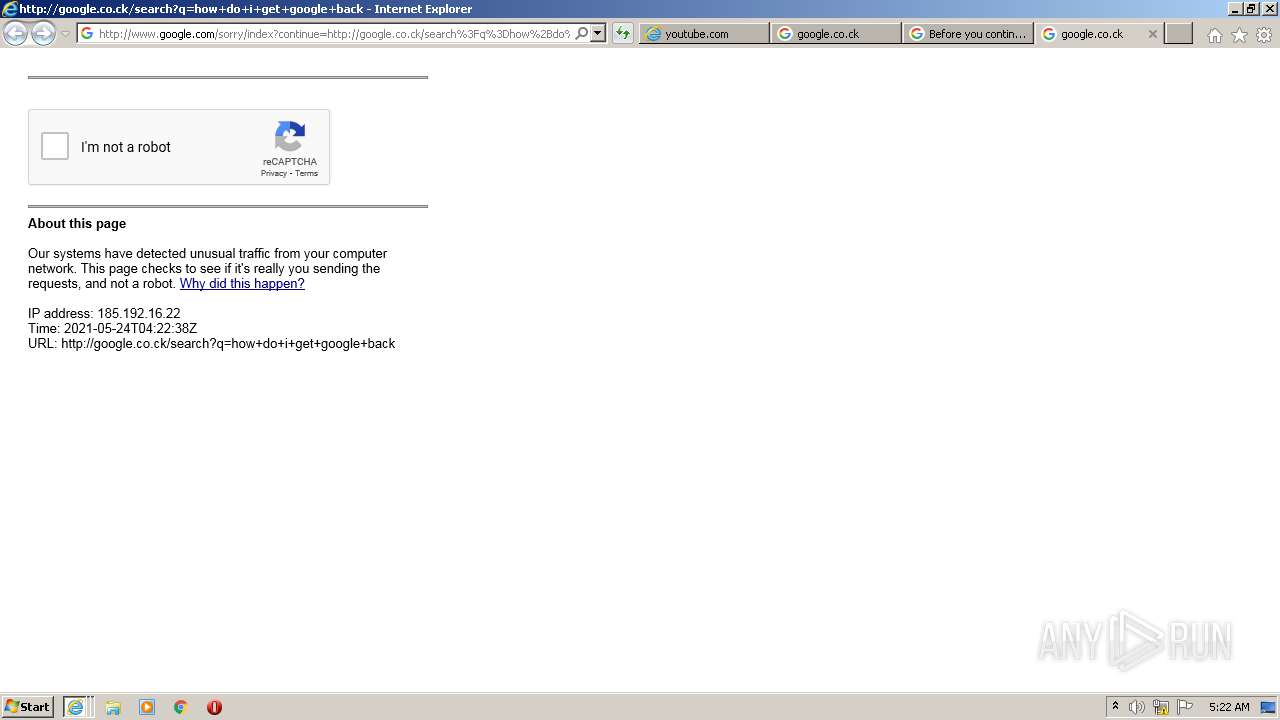
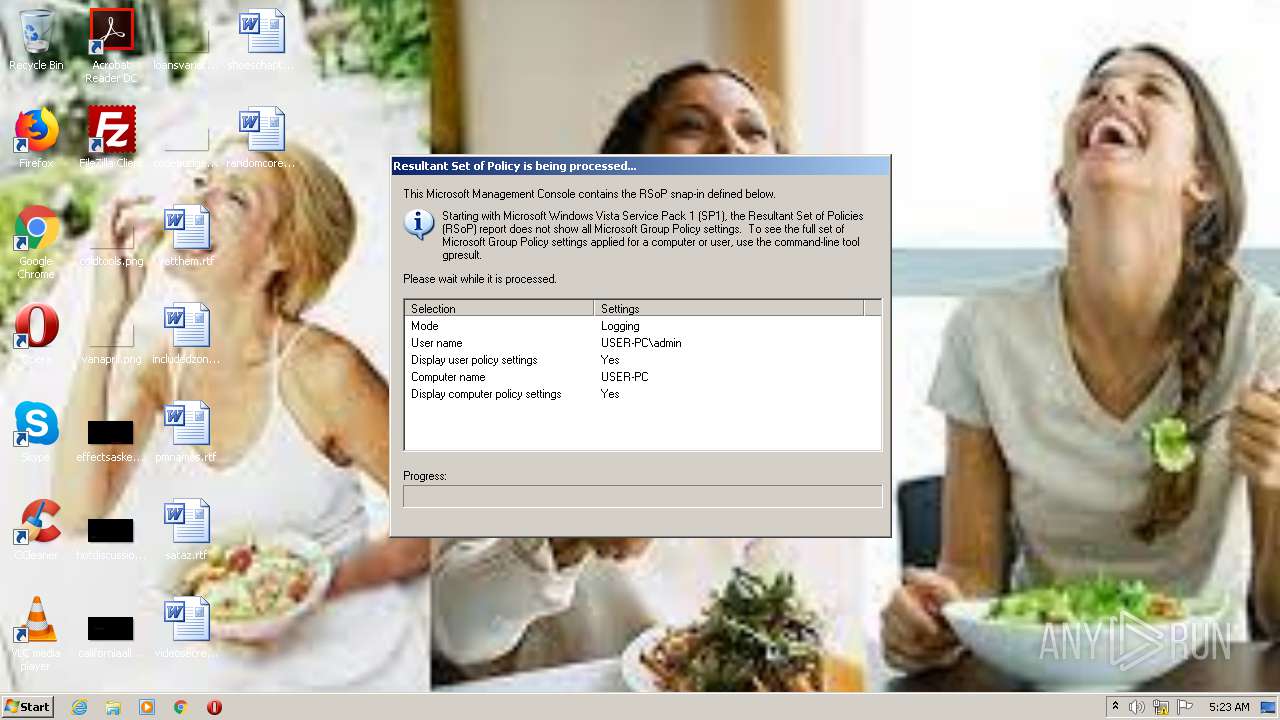
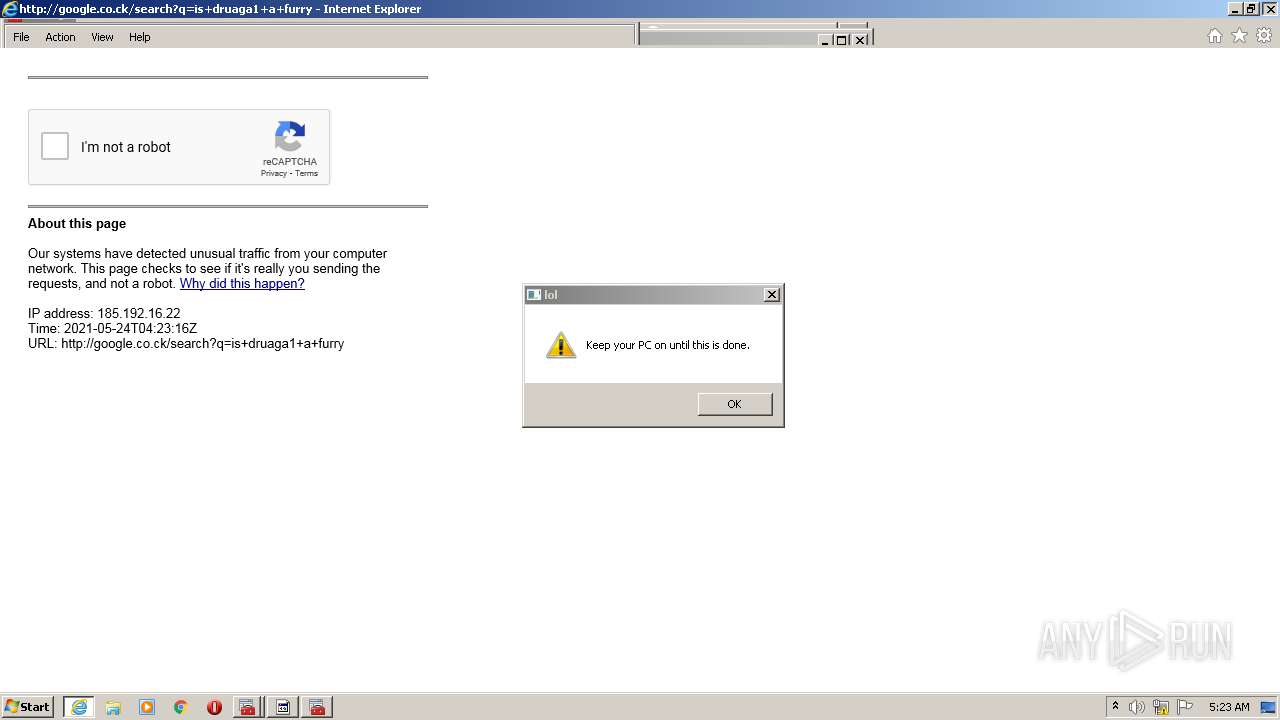
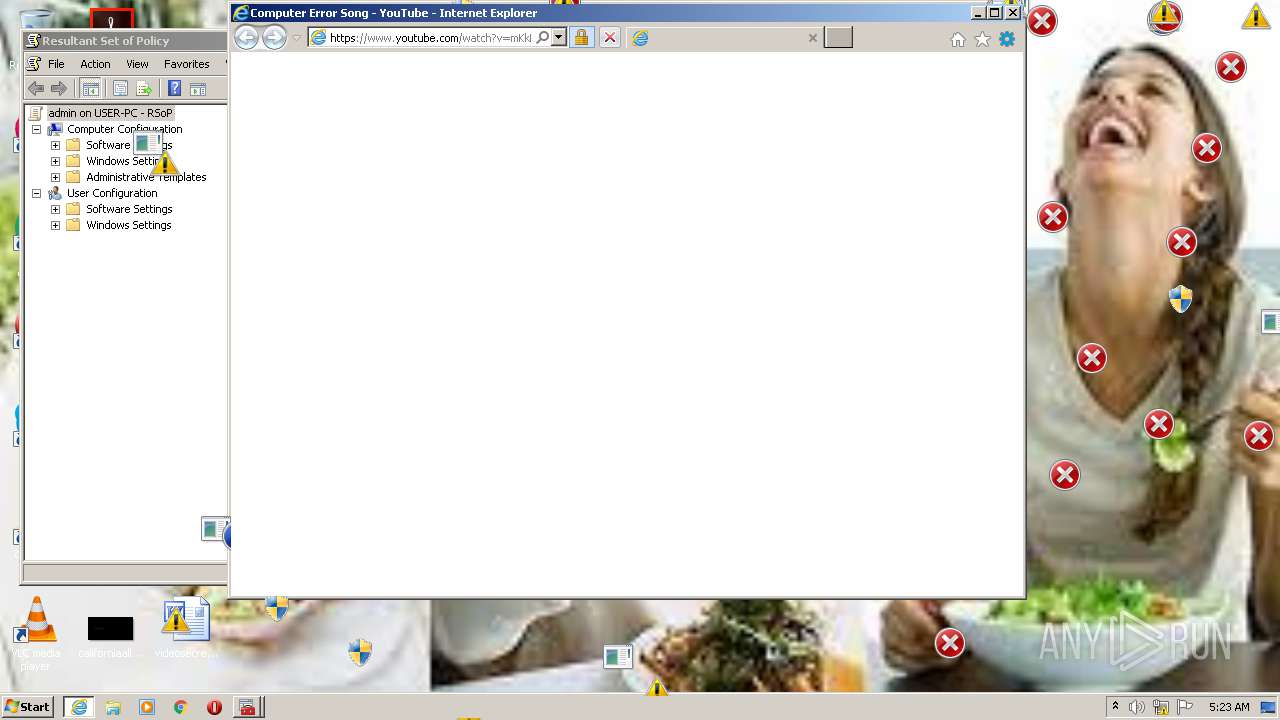
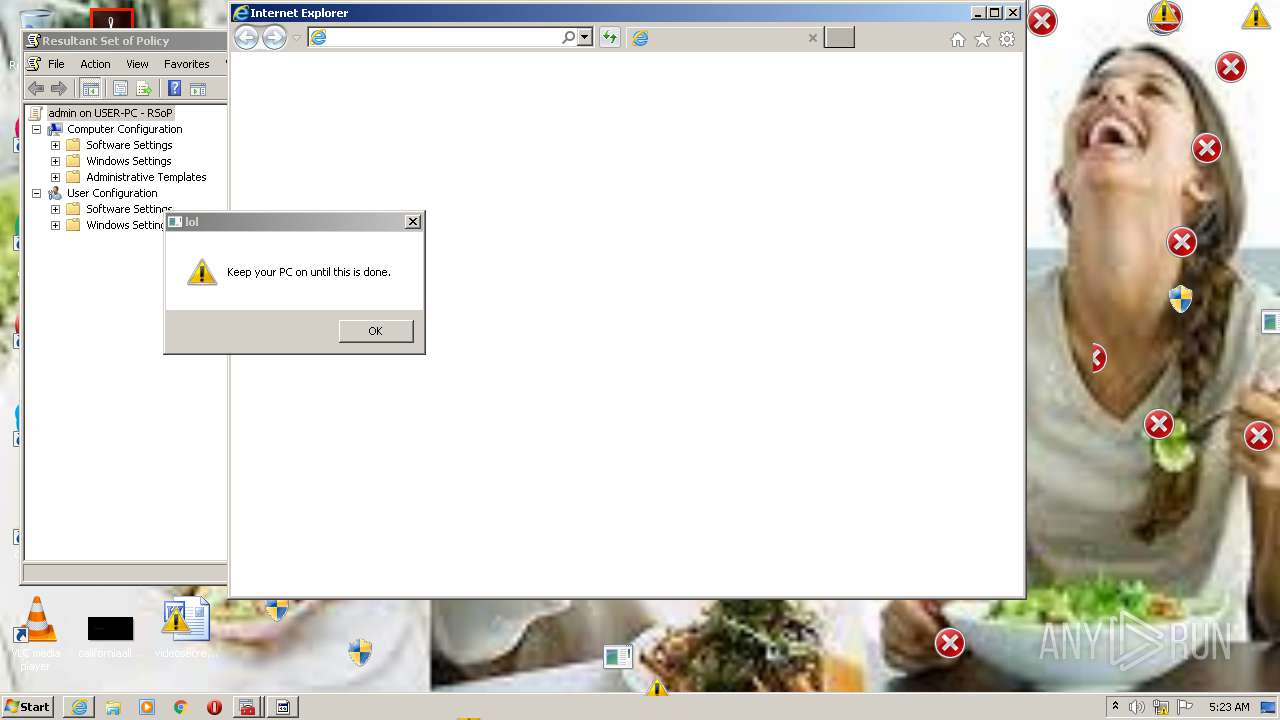
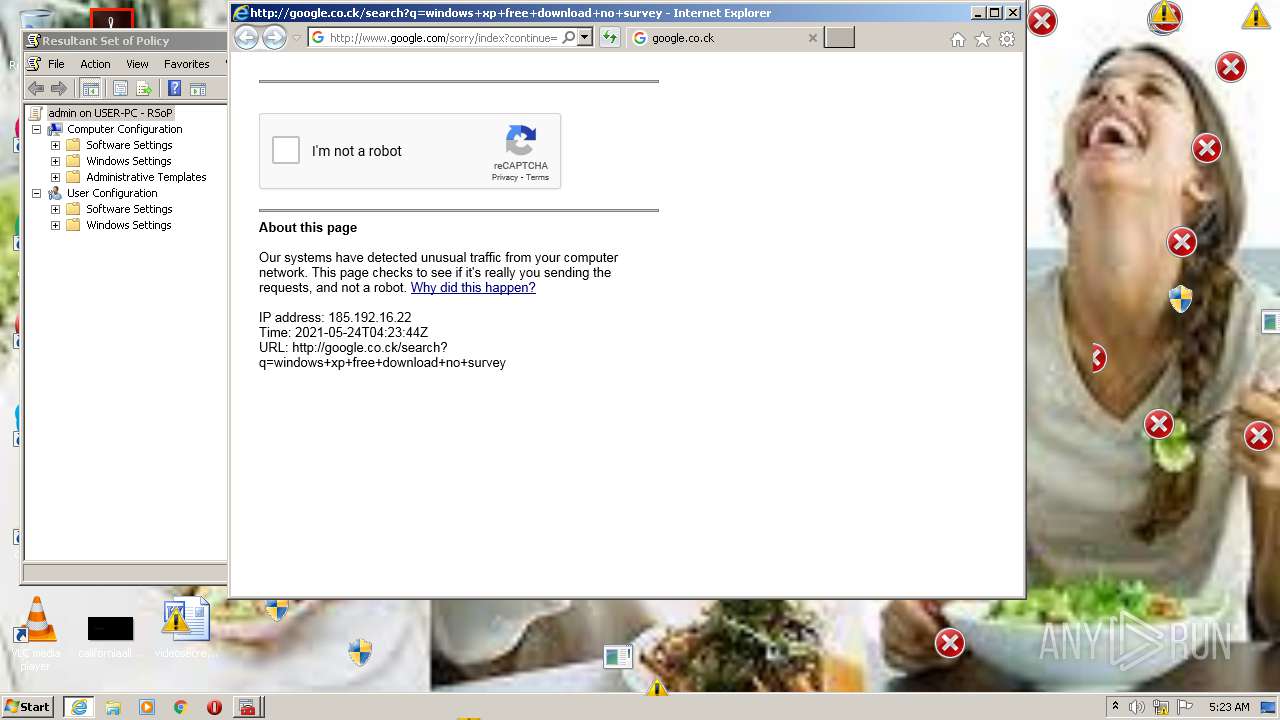
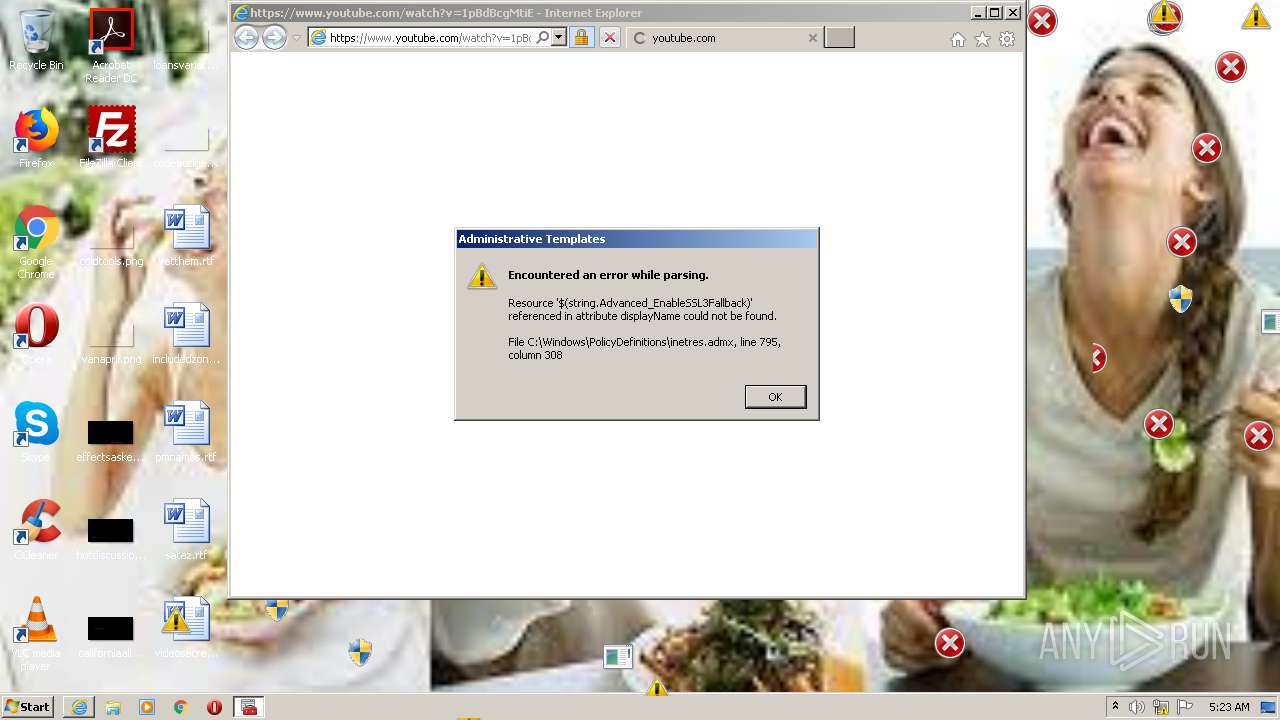
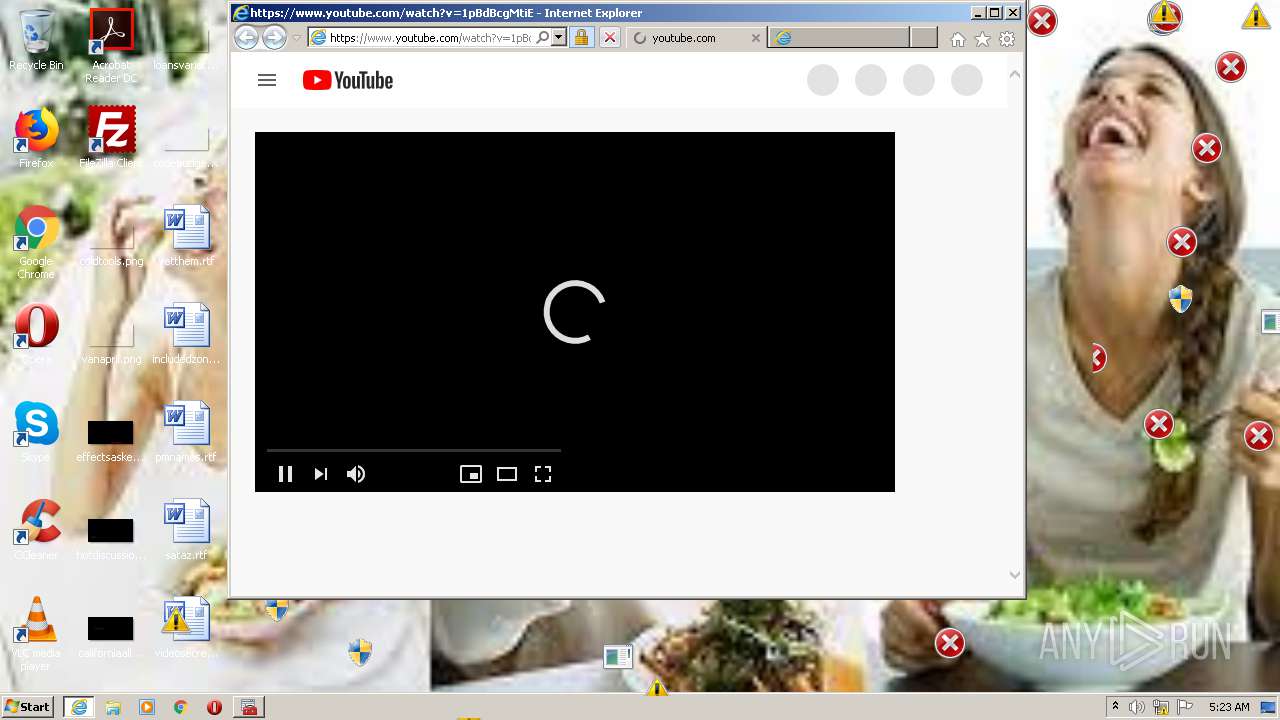
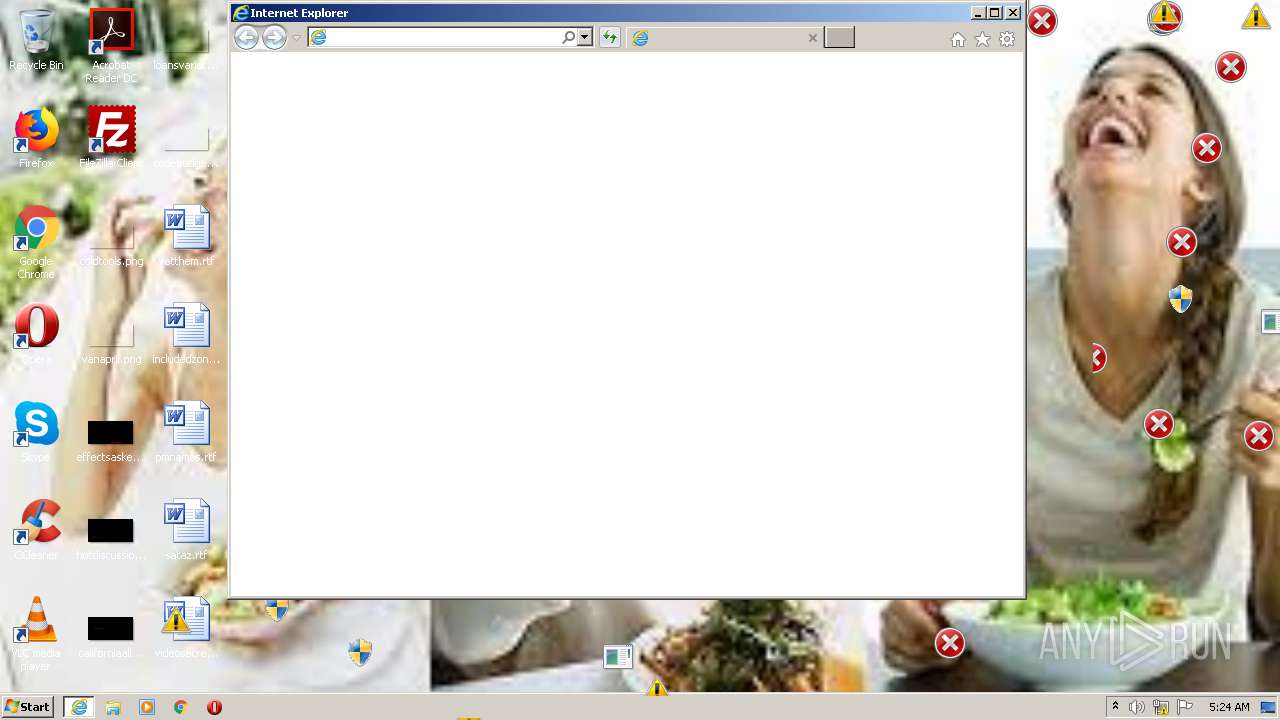
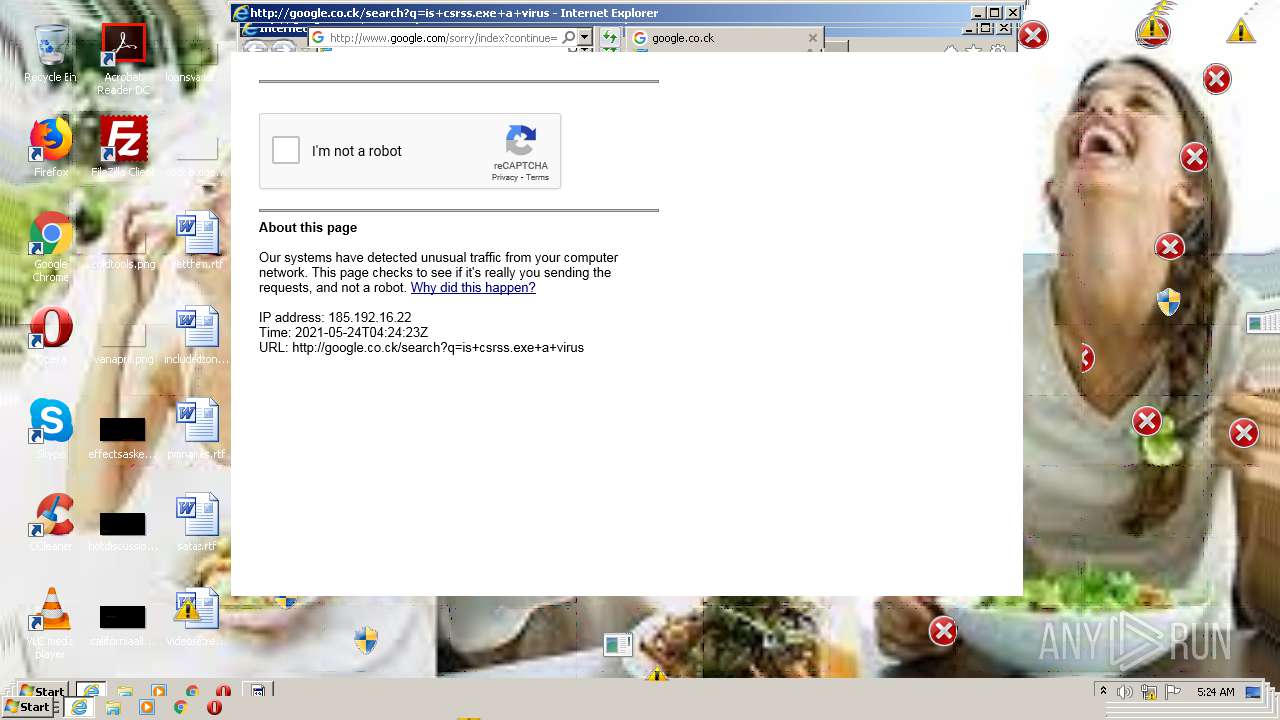
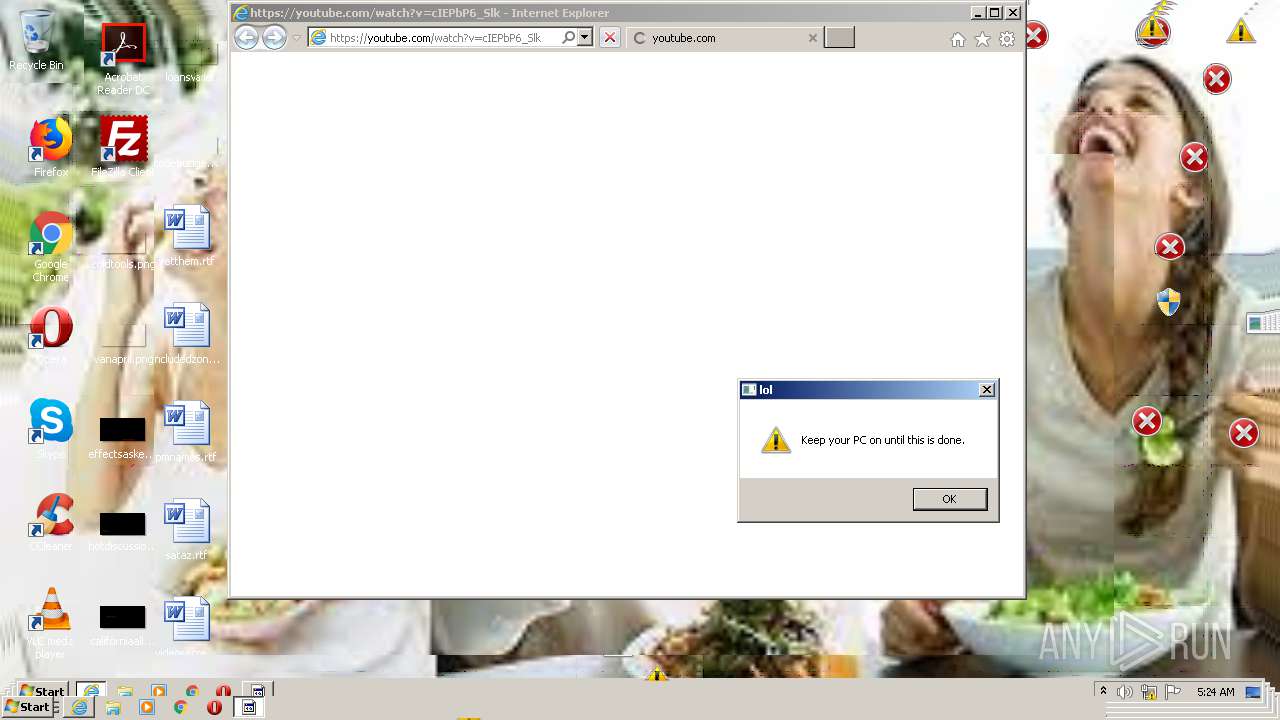
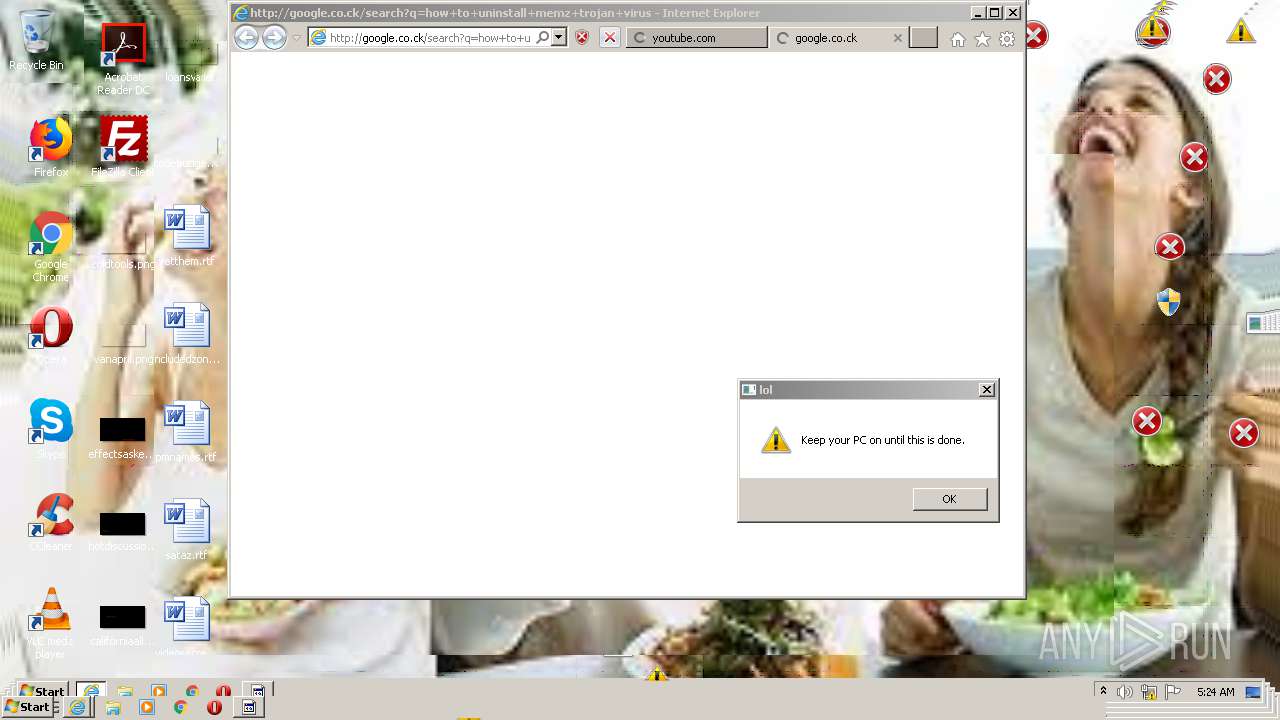
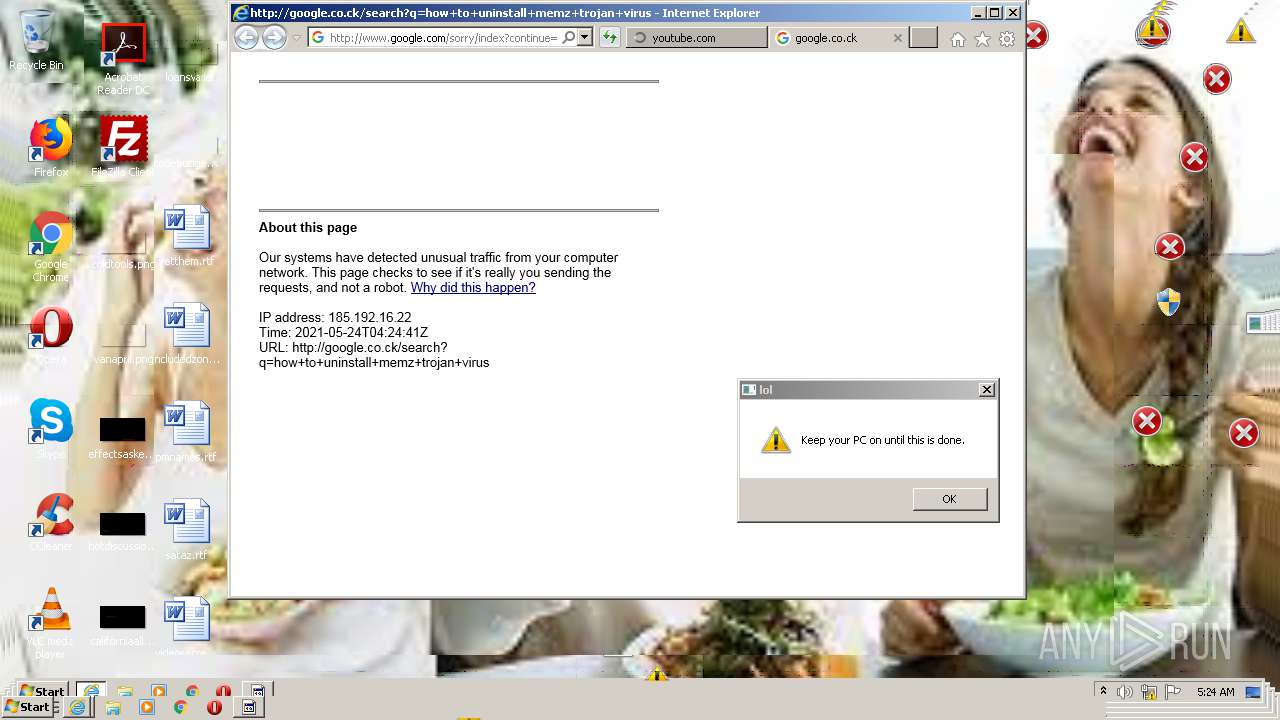
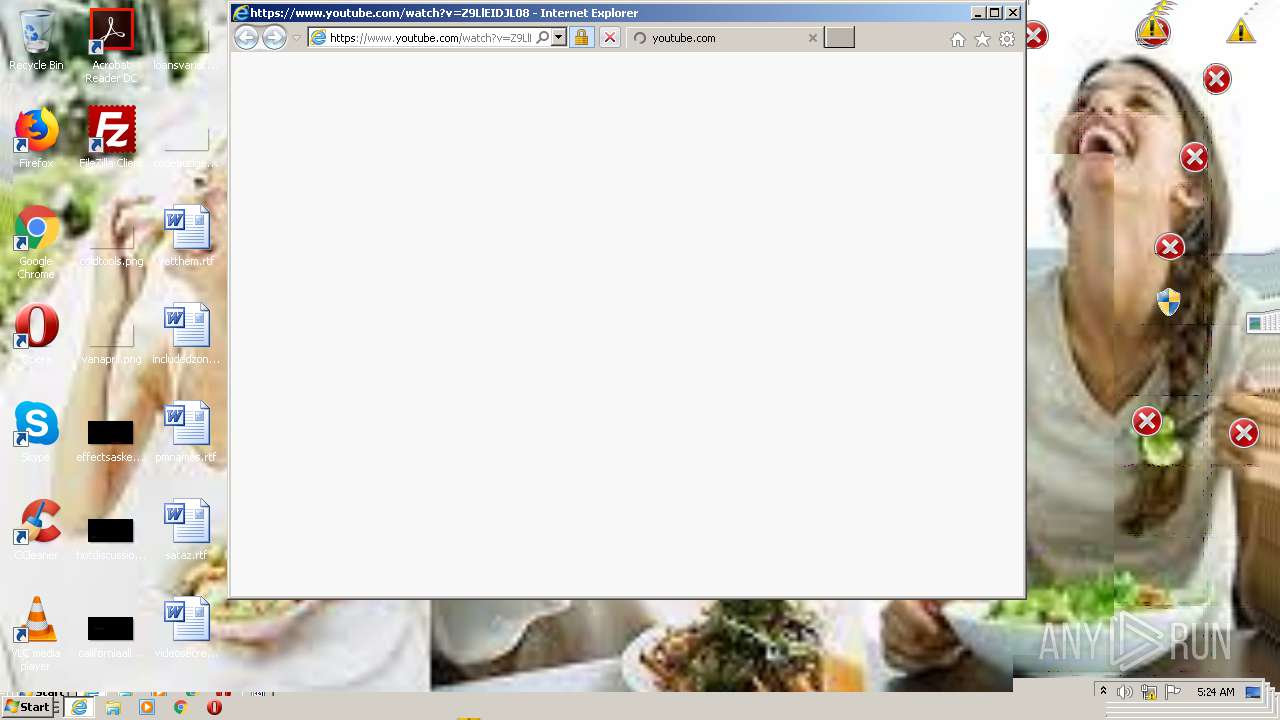
Starts Internet Explorer
- WaffMEMZ-1.0-Destructive.exe (PID: 2432)
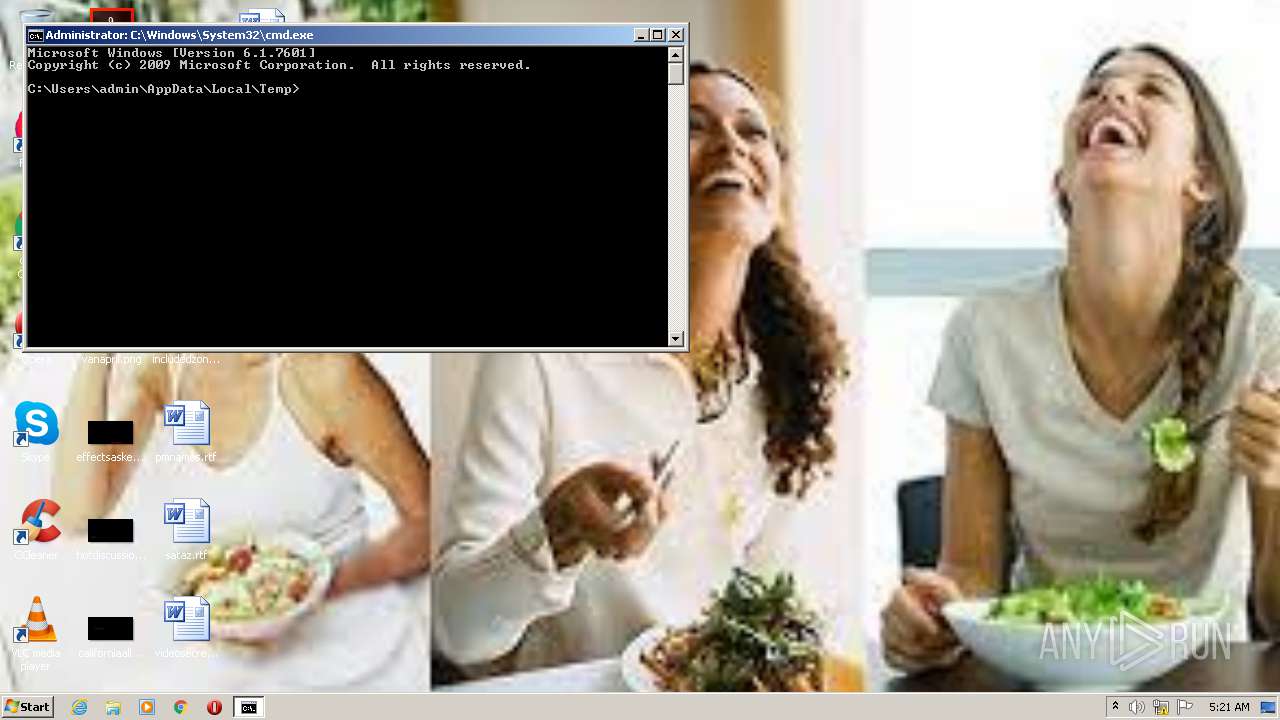
Starts CMD.EXE for commands execution
- WaffMEMZ-1.0-Destructive.exe (PID: 2432)
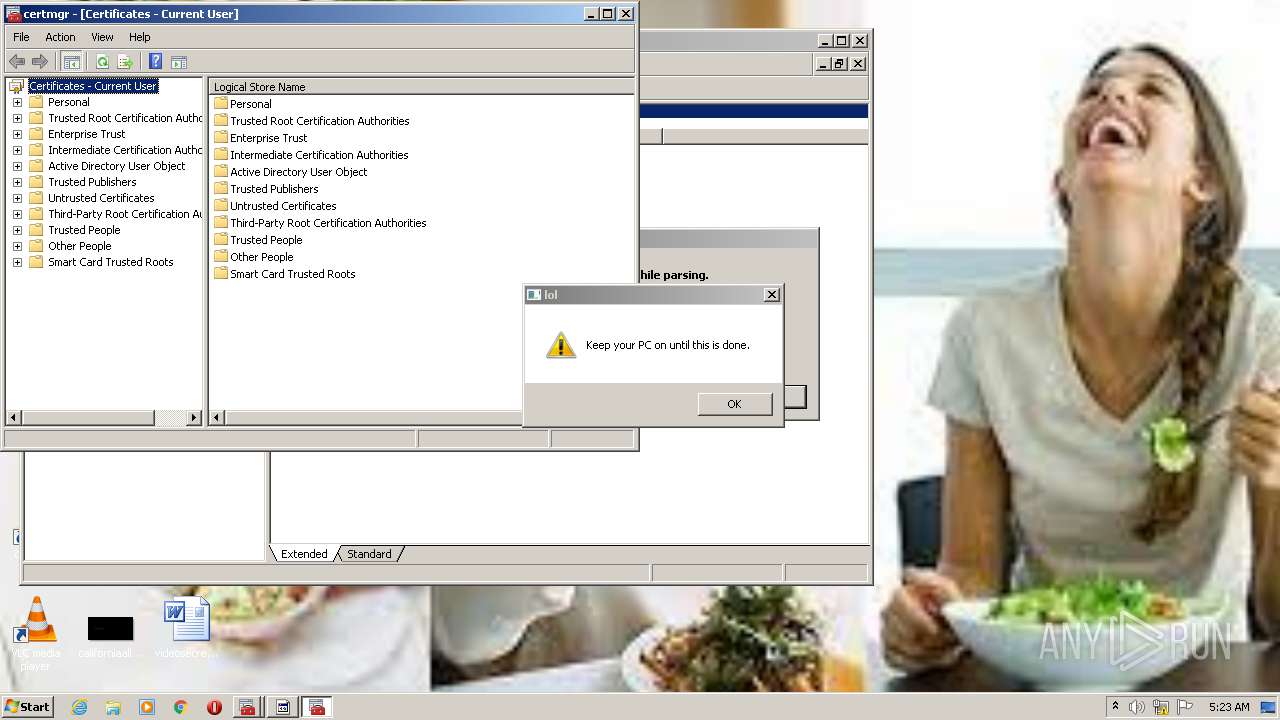
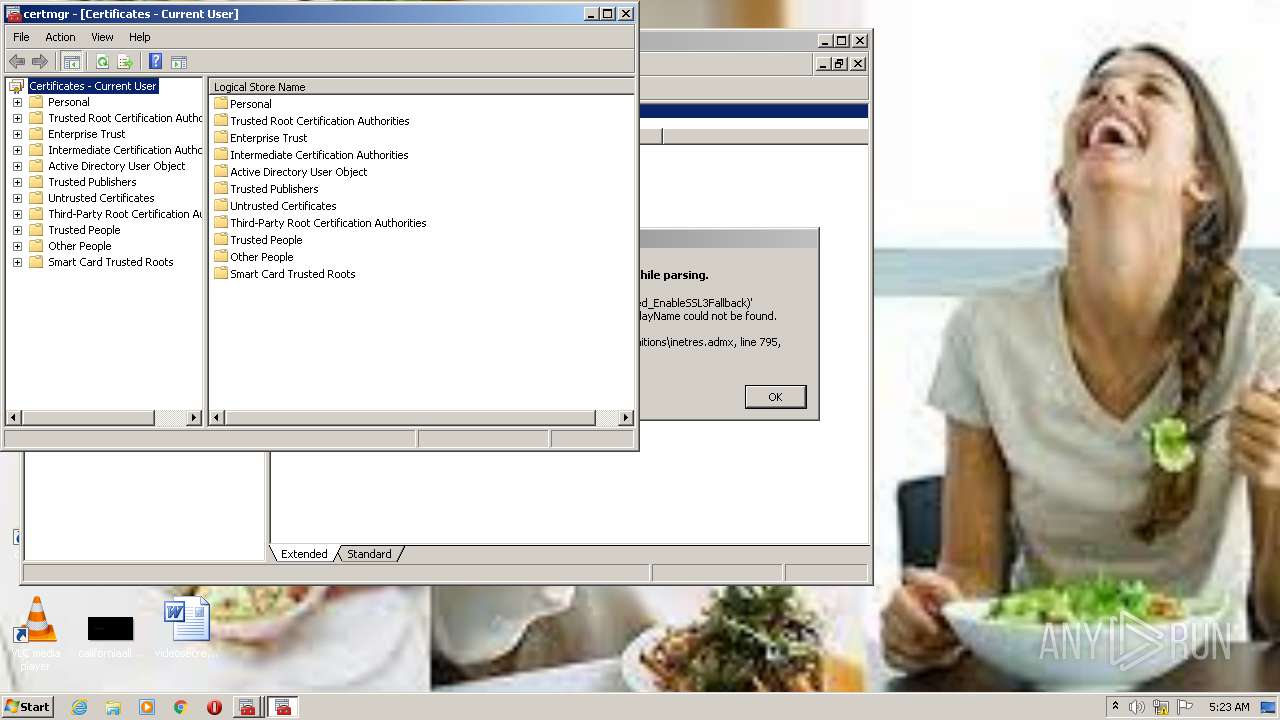
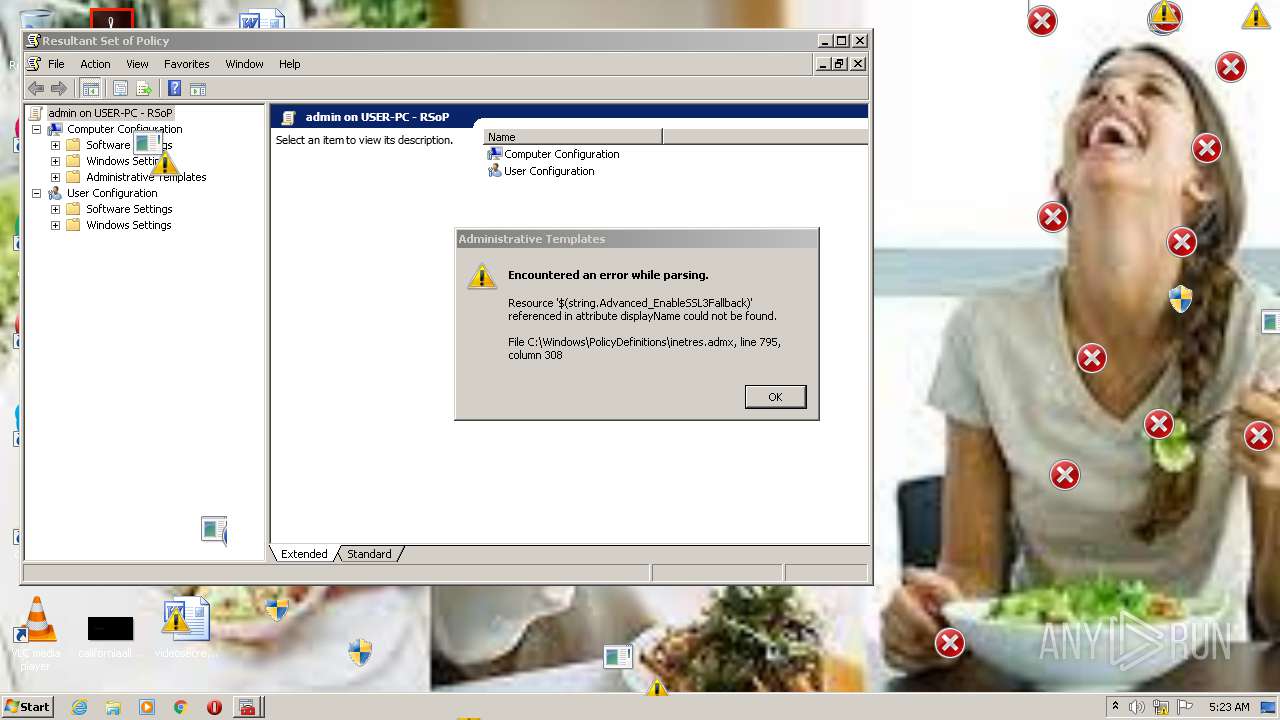
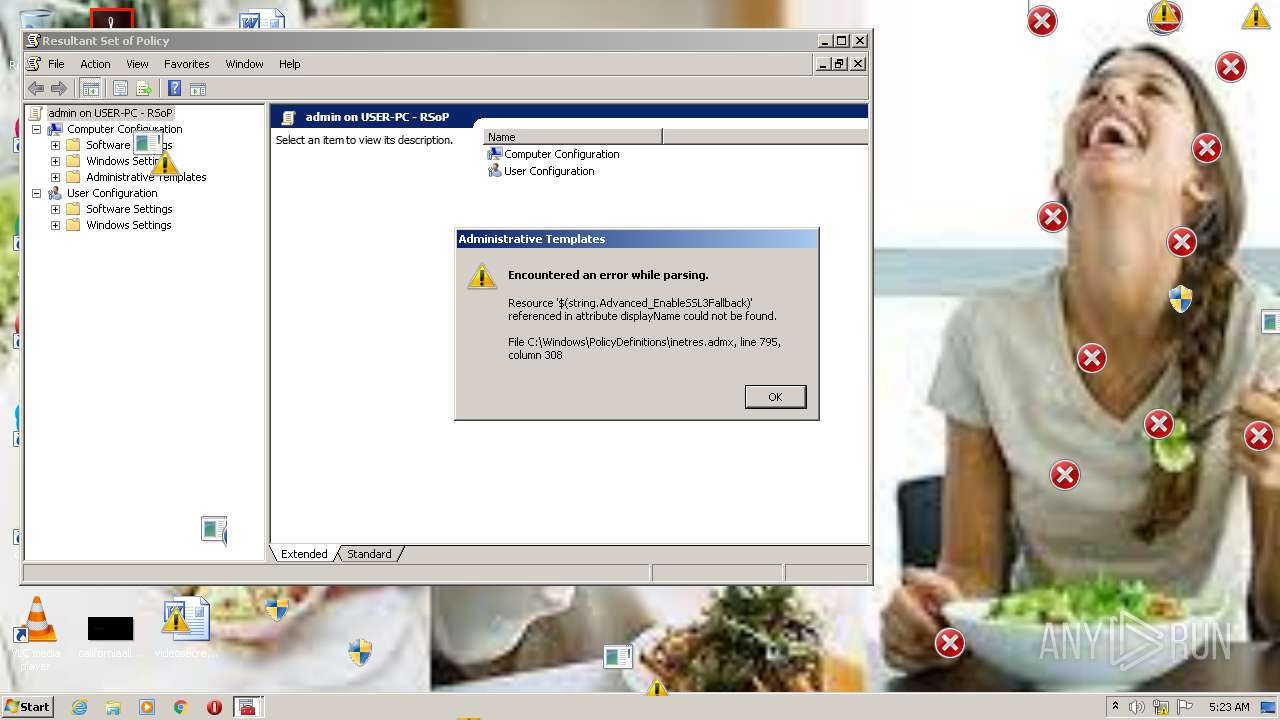
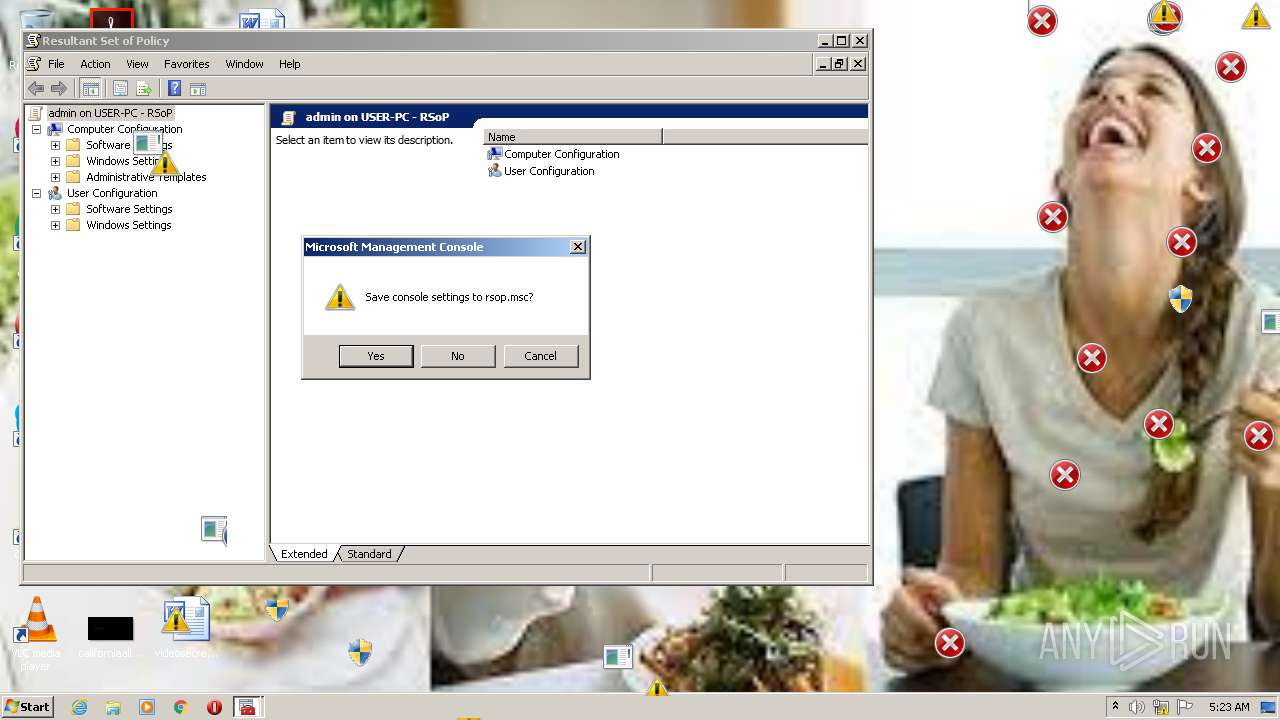
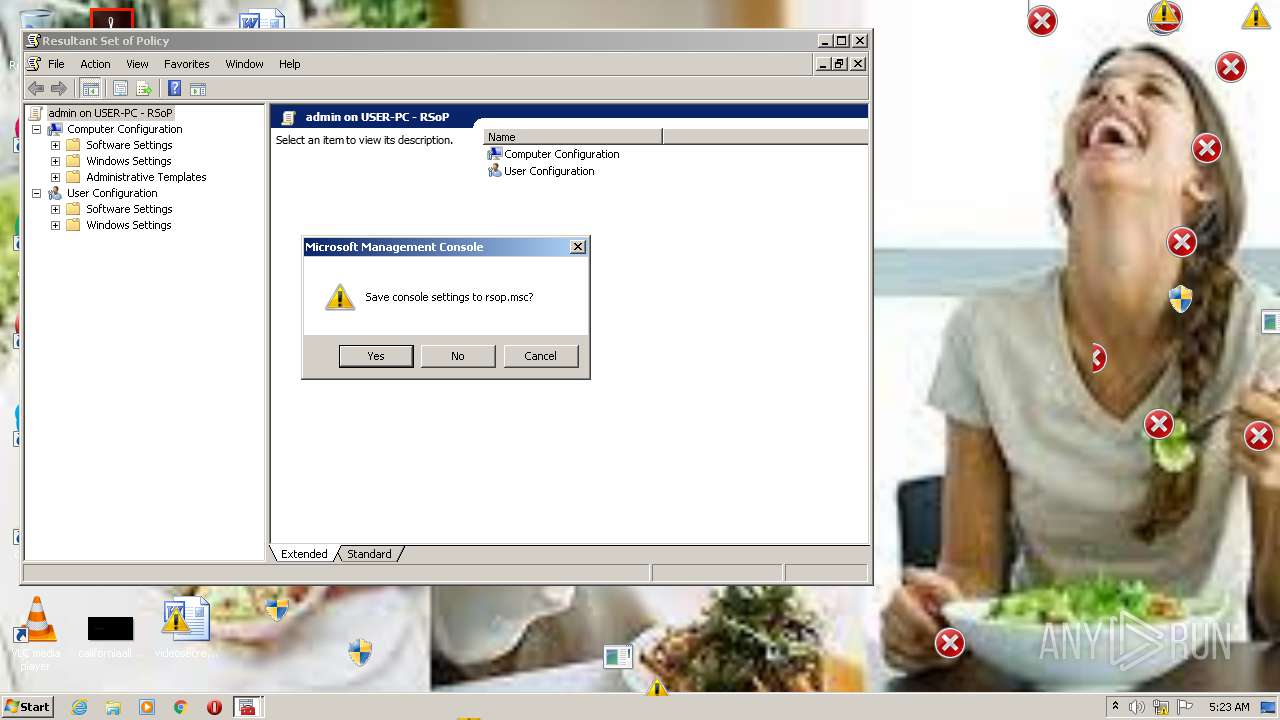
Reads internet explorer settings
- mmc.exe (PID: 832)
- mmc.exe (PID: 3920)
- mmc.exe (PID: 3504)
- mmc.exe (PID: 4072)
Creates files in the user directory
- mmc.exe (PID: 3240)
Executed via COM
- unsecapp.exe (PID: 3800)
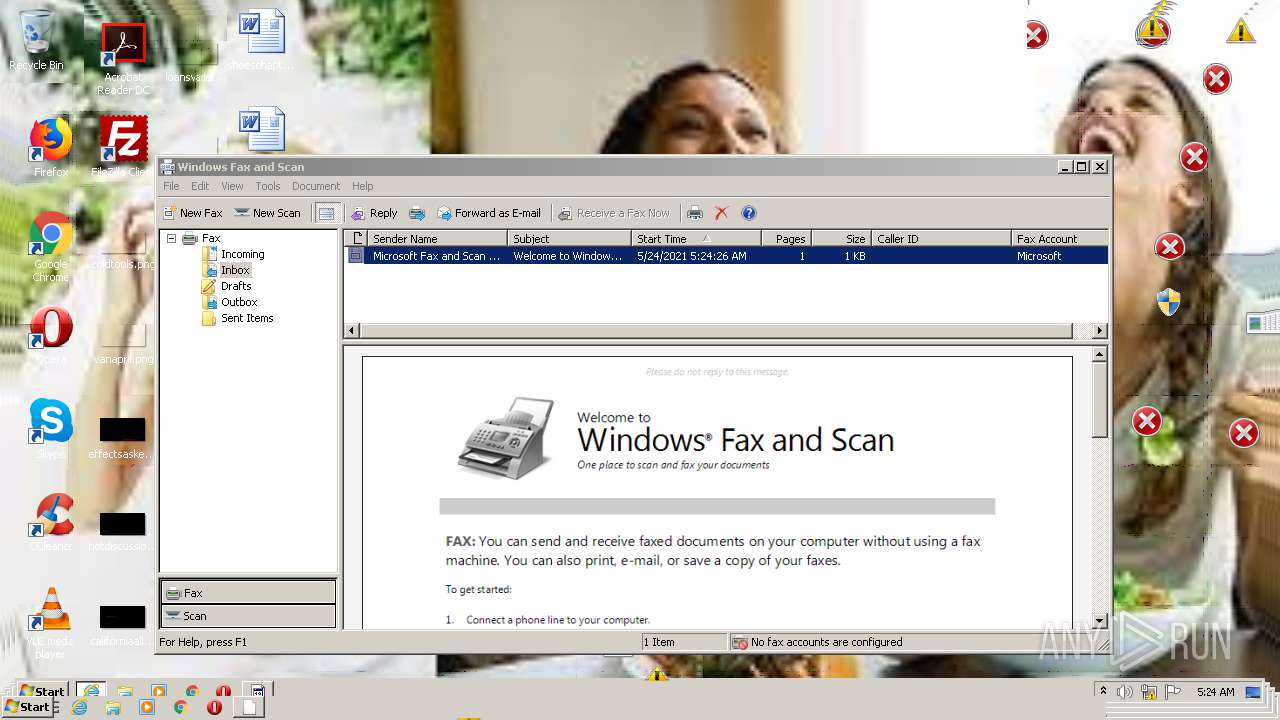
Writes to a desktop.ini file (may be used to cloak folders)
- WFS.exe (PID: 3836)
Creates files in the Windows directory
- fxssvc.exe (PID: 2792)
Executed as Windows Service
- fxssvc.exe (PID: 2792)
Creates files in the program directory
- fxssvc.exe (PID: 2792)
INFO
Creates files in the user directory
- iexplore.exe (PID: 1556)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 2568)
- iexplore.exe (PID: 3412)
- iexplore.exe (PID: 2384)
Reads settings of System Certificates
- iexplore.exe (PID: 2848)
- iexplore.exe (PID: 3044)
- iexplore.exe (PID: 2708)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 1800)
- iexplore.exe (PID: 2180)
- iexplore.exe (PID: 1524)
- iexplore.exe (PID: 2568)
- iexplore.exe (PID: 3412)
- iexplore.exe (PID: 3700)
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 2384)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 3588)
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 572)
- iexplore.exe (PID: 3488)
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 2596)
- iexplore.exe (PID: 3500)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 2512)
Application launched itself
- iexplore.exe (PID: 1800)
- iexplore.exe (PID: 1524)
- iexplore.exe (PID: 3016)
- iexplore.exe (PID: 1576)
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 3192)
- iexplore.exe (PID: 2384)
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 2712)
- iexplore.exe (PID: 1824)
- iexplore.exe (PID: 2648)
- iexplore.exe (PID: 2544)
- iexplore.exe (PID: 2688)
- iexplore.exe (PID: 884)
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 1712)
- iexplore.exe (PID: 2700)
- iexplore.exe (PID: 2080)
Reads internet explorer settings
- iexplore.exe (PID: 1556)
- iexplore.exe (PID: 2708)
- iexplore.exe (PID: 2848)
- iexplore.exe (PID: 3044)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 2180)
- iexplore.exe (PID: 2568)
- iexplore.exe (PID: 1736)
- iexplore.exe (PID: 2488)
- iexplore.exe (PID: 3412)
- iexplore.exe (PID: 3700)
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 3588)
- iexplore.exe (PID: 1884)
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 572)
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 2596)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 1476)
- iexplore.exe (PID: 3944)
- iexplore.exe (PID: 3500)
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 3496)
Changes internet zones settings
- iexplore.exe (PID: 1800)
- iexplore.exe (PID: 1524)
- iexplore.exe (PID: 3016)
- iexplore.exe (PID: 1576)
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 3192)
- iexplore.exe (PID: 2384)
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 2712)
- iexplore.exe (PID: 1824)
- iexplore.exe (PID: 2648)
- iexplore.exe (PID: 2544)
- iexplore.exe (PID: 2688)
- iexplore.exe (PID: 884)
- iexplore.exe (PID: 1712)
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 2700)
- iexplore.exe (PID: 2080)
Changes settings of System certificates
- iexplore.exe (PID: 1556)
- iexplore.exe (PID: 1800)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1556)
- iexplore.exe (PID: 1800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x12a0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 19456 |
| CodeSize: | 3584 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2017:06:10 05:46:05+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jun-2017 03:46:05 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Jun-2017 03:46:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000CA2 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.54319 |
.rdata | 0x00002000 | 0x00003CDA | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.9781 |
.data | 0x00006000 | 0x00000520 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.84143 |
.rsrc | 0x00007000 | 0x000002F0 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.28746 |
.reloc | 0x00008000 | 0x00000374 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.58581 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05508 | 649 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
WINMM.dll |
Total processes
124
Monitored processes
74
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2648 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
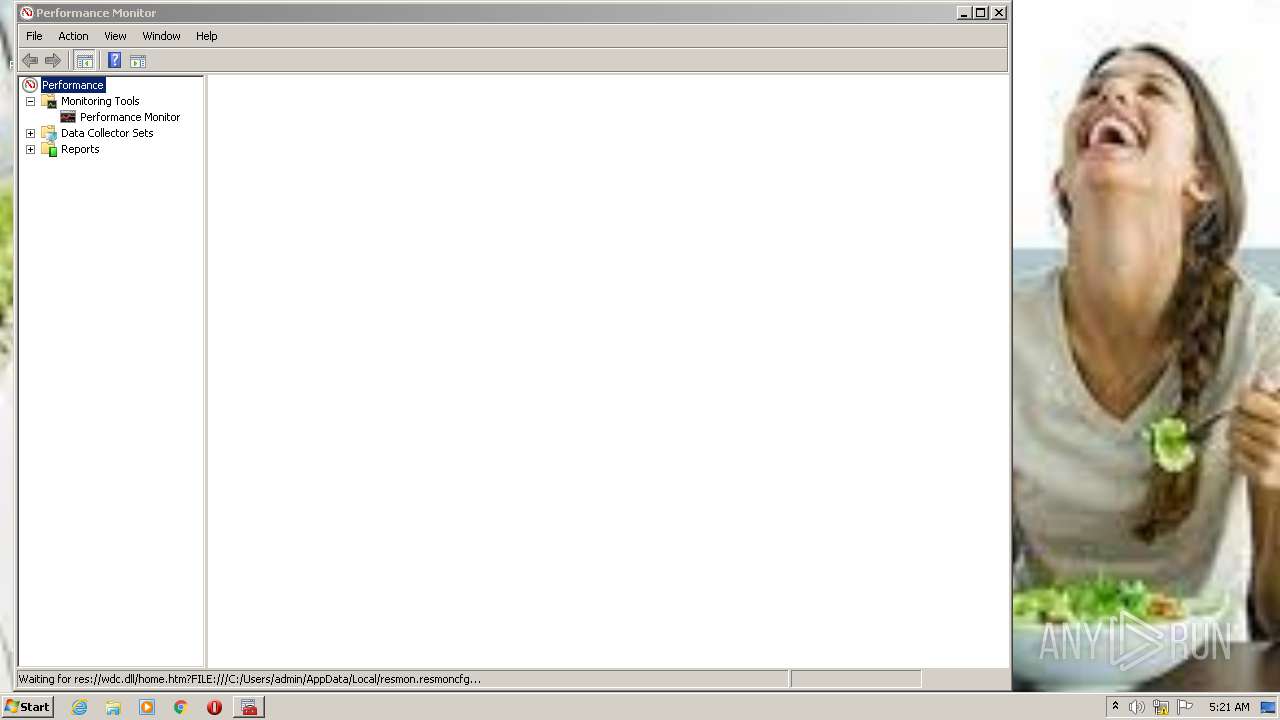
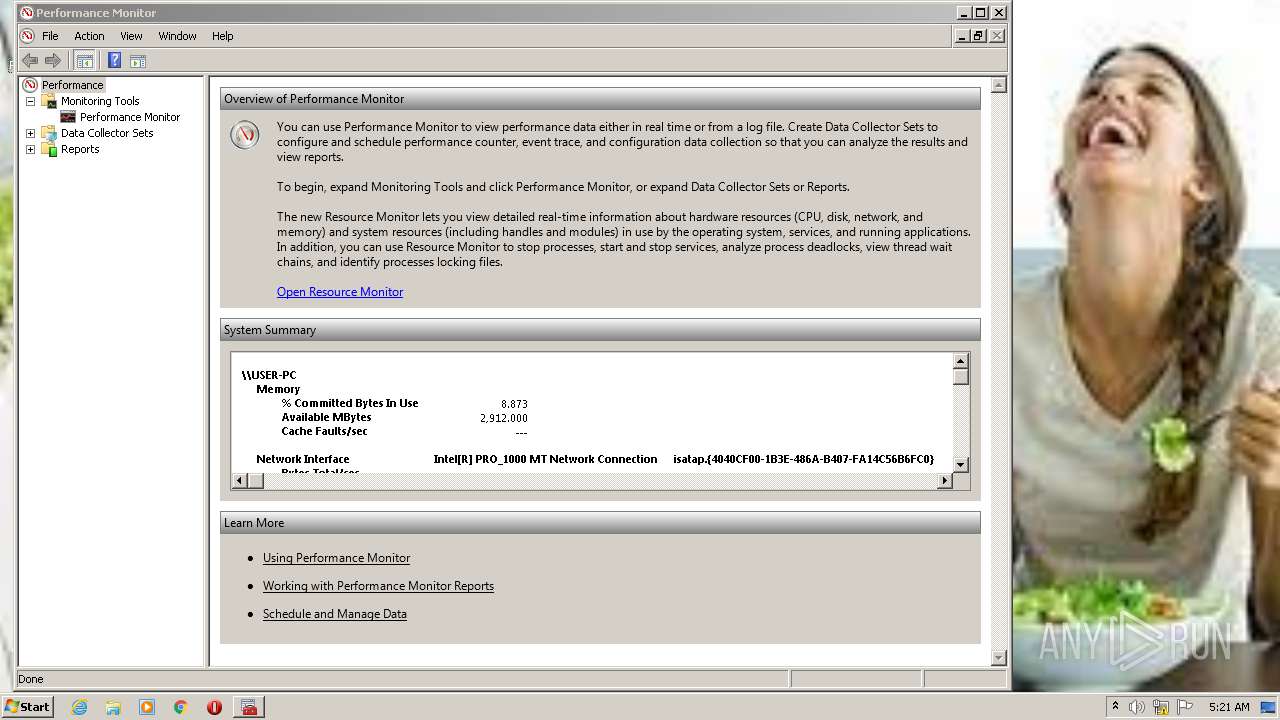
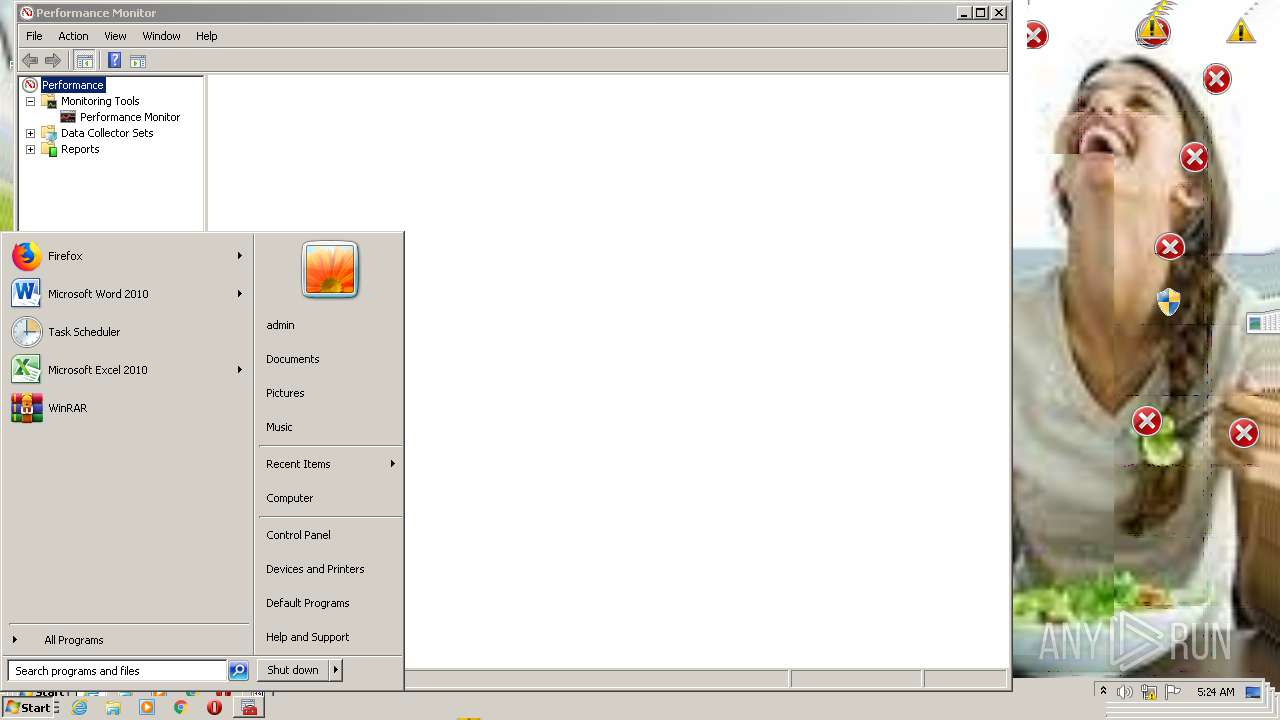
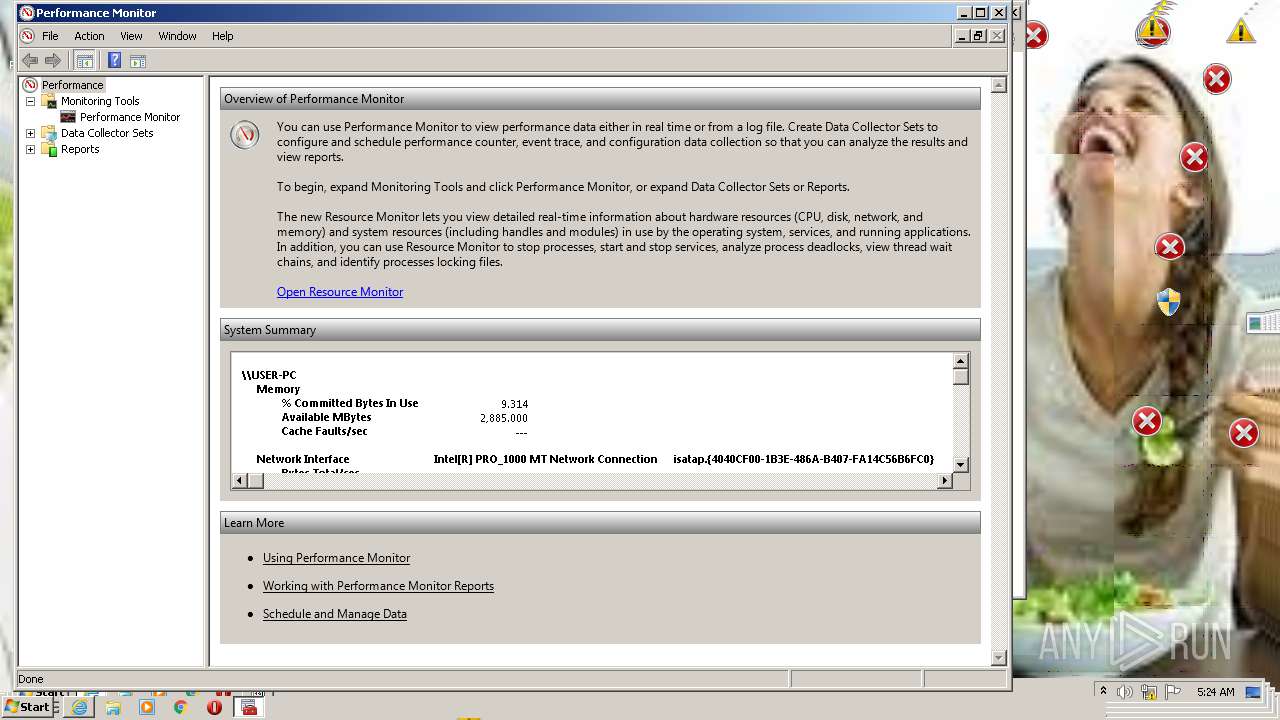
| 832 | "C:\Windows\system32\mmc.exe" "C:\Windows\System32\perfmon.msc" | C:\Windows\system32\mmc.exe | — | WaffMEMZ-1.0-Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
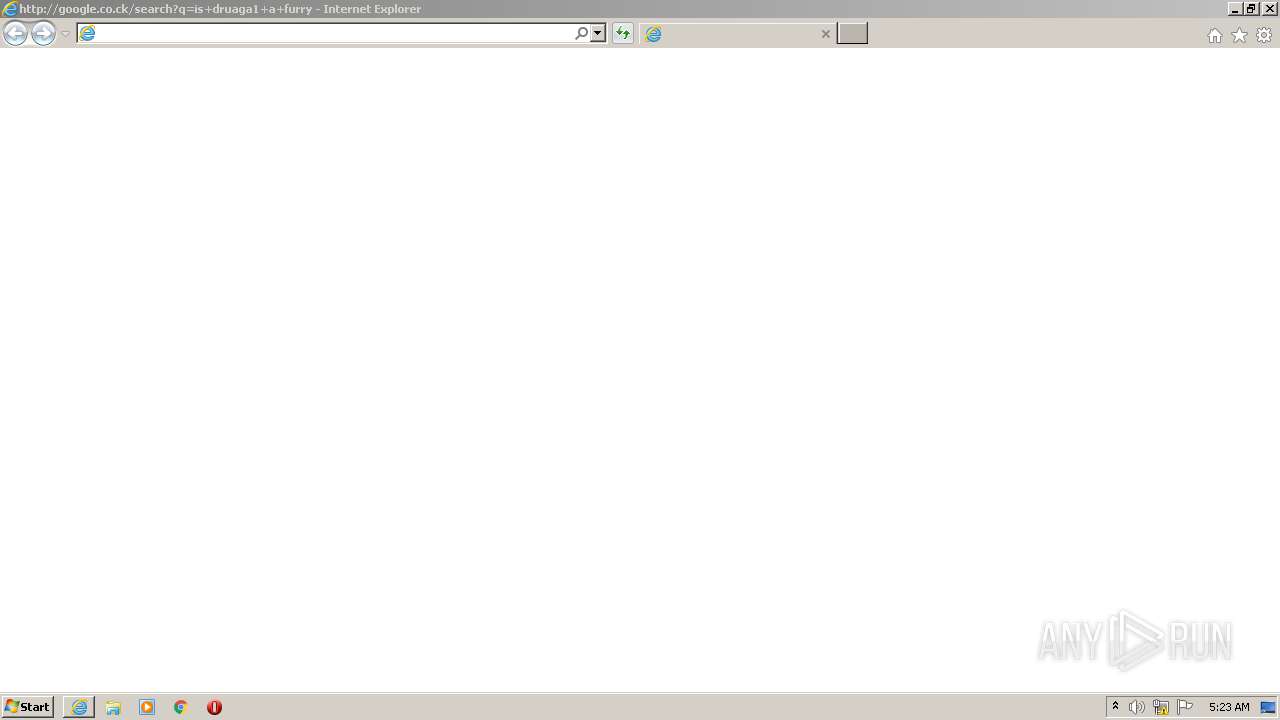
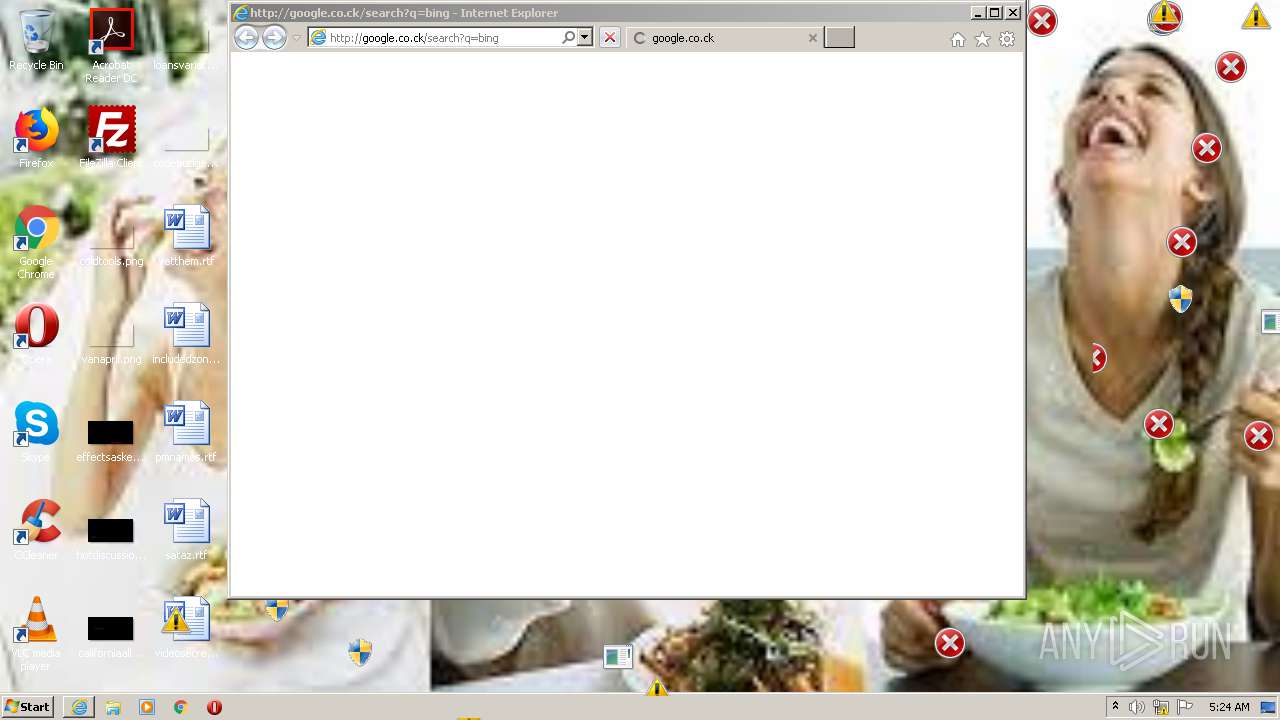
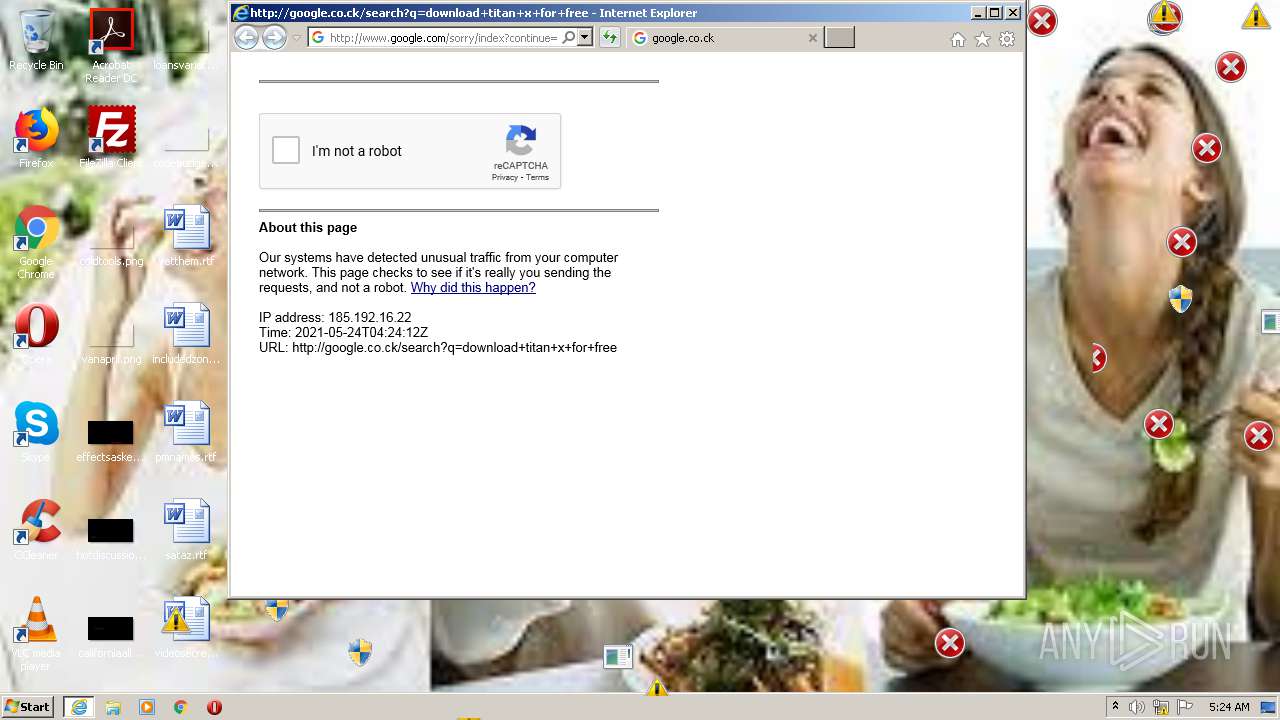
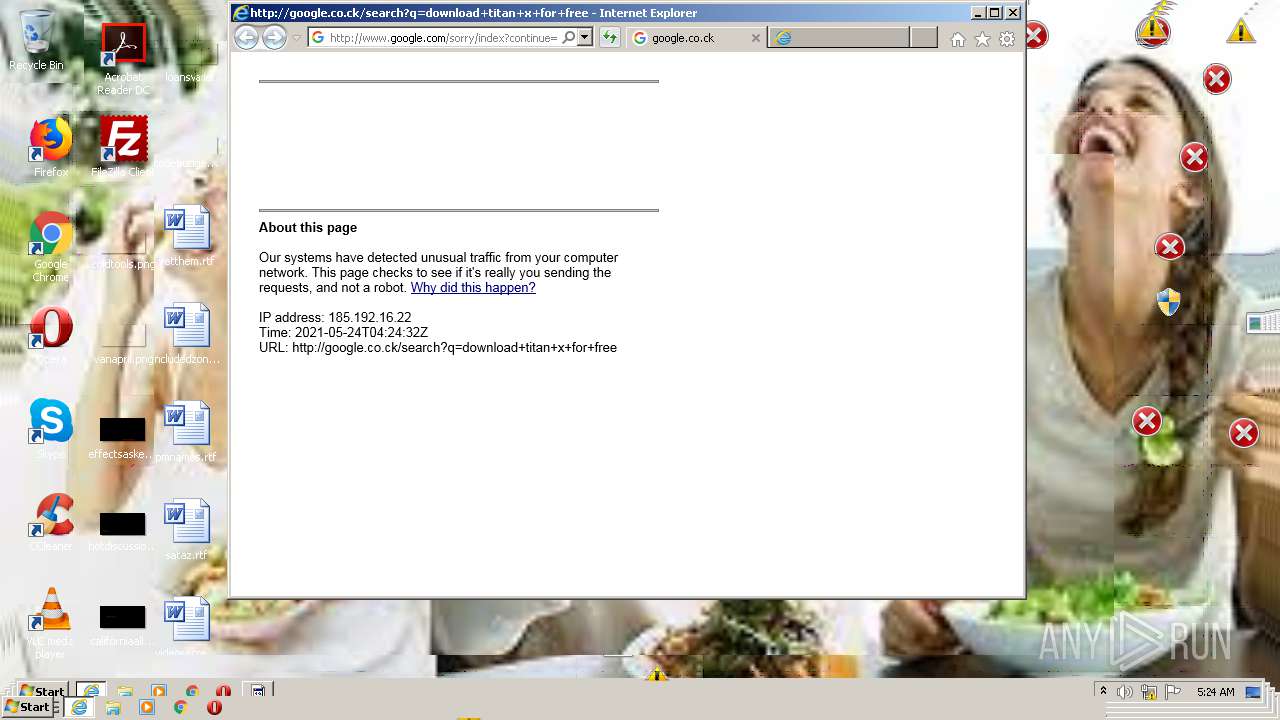
| 884 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=download+titan+x+for+free | C:\Program Files\Internet Explorer\iexplore.exe | — | WaffMEMZ-1.0-Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
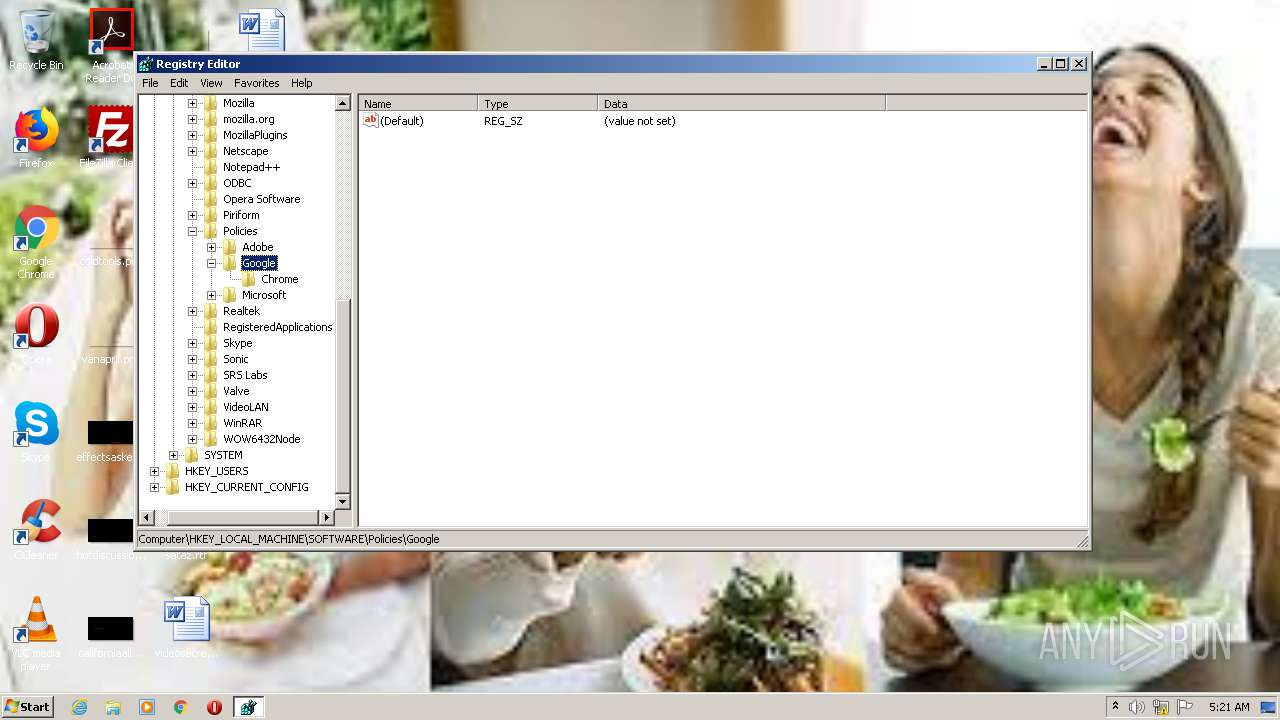
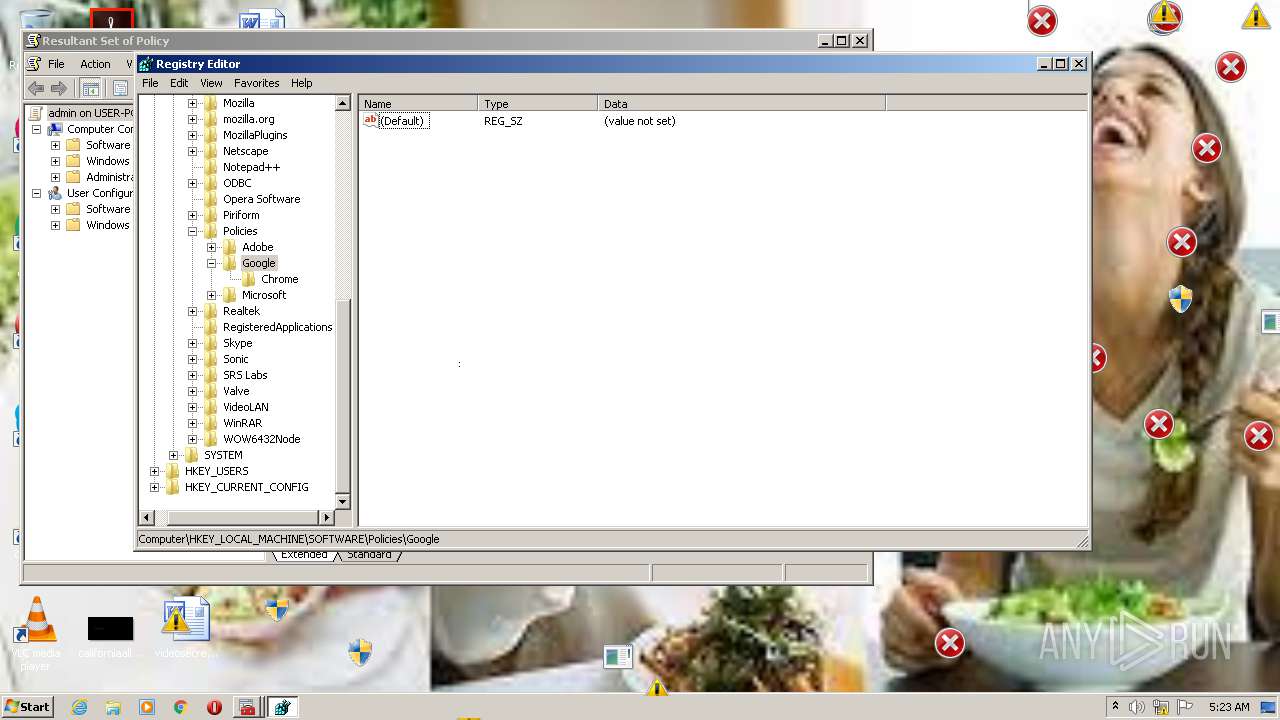
| 996 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | — | WaffMEMZ-1.0-Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3768 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
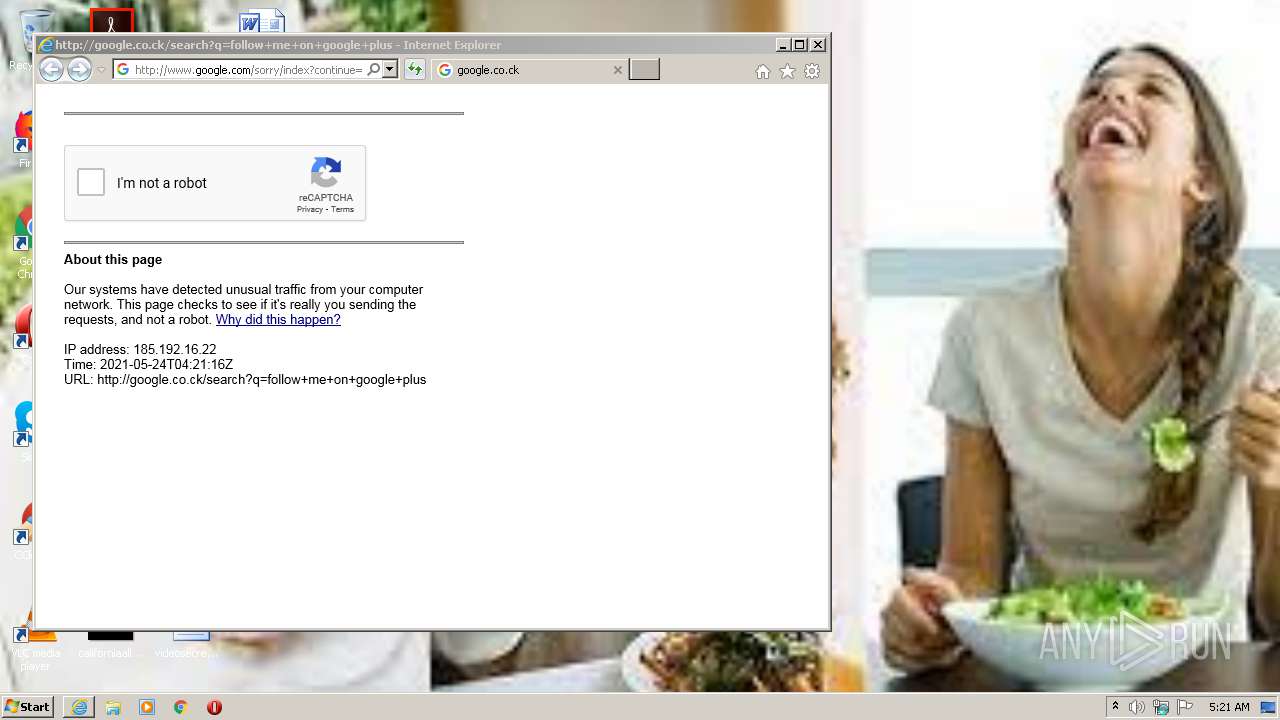
| 1524 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=follow+me+on+google+plus | C:\Program Files\Internet Explorer\iexplore.exe | WaffMEMZ-1.0-Destructive.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1800 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
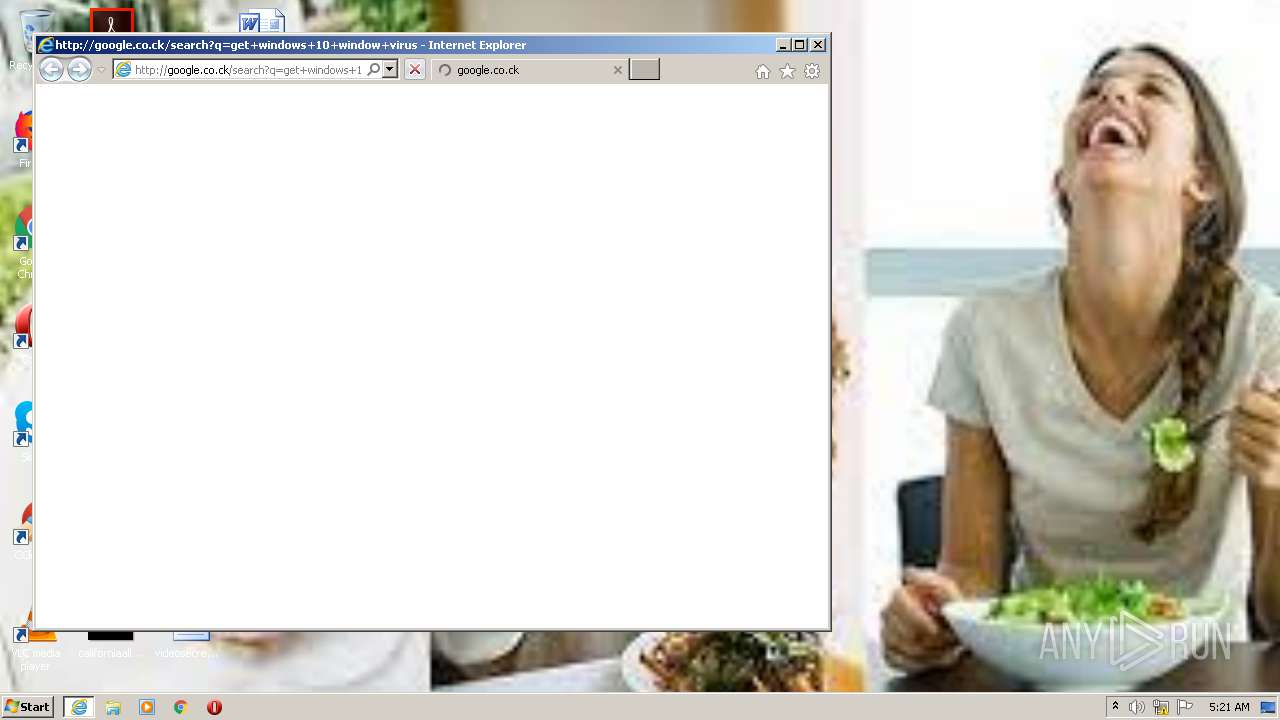
| 1576 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=get+windows+10+window+virus | C:\Program Files\Internet Explorer\iexplore.exe | — | WaffMEMZ-1.0-Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1592 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | WaffMEMZ-1.0-Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=download+titan+x+for+free | C:\Program Files\Internet Explorer\iexplore.exe | — | WaffMEMZ-1.0-Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
11 522
Read events
8 947
Write events
2 545
Delete events
30
Modification events
| (PID) Process: | (3592) WaffMEMZ-1.0-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3592) WaffMEMZ-1.0-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2432) WaffMEMZ-1.0-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2432) WaffMEMZ-1.0-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2432) WaffMEMZ-1.0-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 01000000000000005259F12B5450D701 | |||
| (PID) Process: | (1800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1039112330 | |||
| (PID) Process: | (1800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30888020 | |||
| (PID) Process: | (1800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
158
Text files
242
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabBB4B.tmp | — | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarBB4C.tmp | — | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\MNVYZ73H.txt | — | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\M871N767.txt | text | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F2DDCD2B5F37625B82E81F4976CEE400_8BDEE109E6B78A0DDC6FCD27FF91E8FD | der | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F2DDCD2B5F37625B82E81F4976CEE400_8BDEE109E6B78A0DDC6FCD27FF91E8FD | binary | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\9R3CG1WR.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
67
TCP/UDP connections
299
DNS requests
74
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1556 | iexplore.exe | GET | 302 | 142.250.185.99:80 | http://www.google.co.ck/search?q=woman+eating+salad&tbm=isch | US | html | 277 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2848 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD%2B3Y3H7vbrSQUAAAAAh8wX | US | der | 472 b | whitelisted |
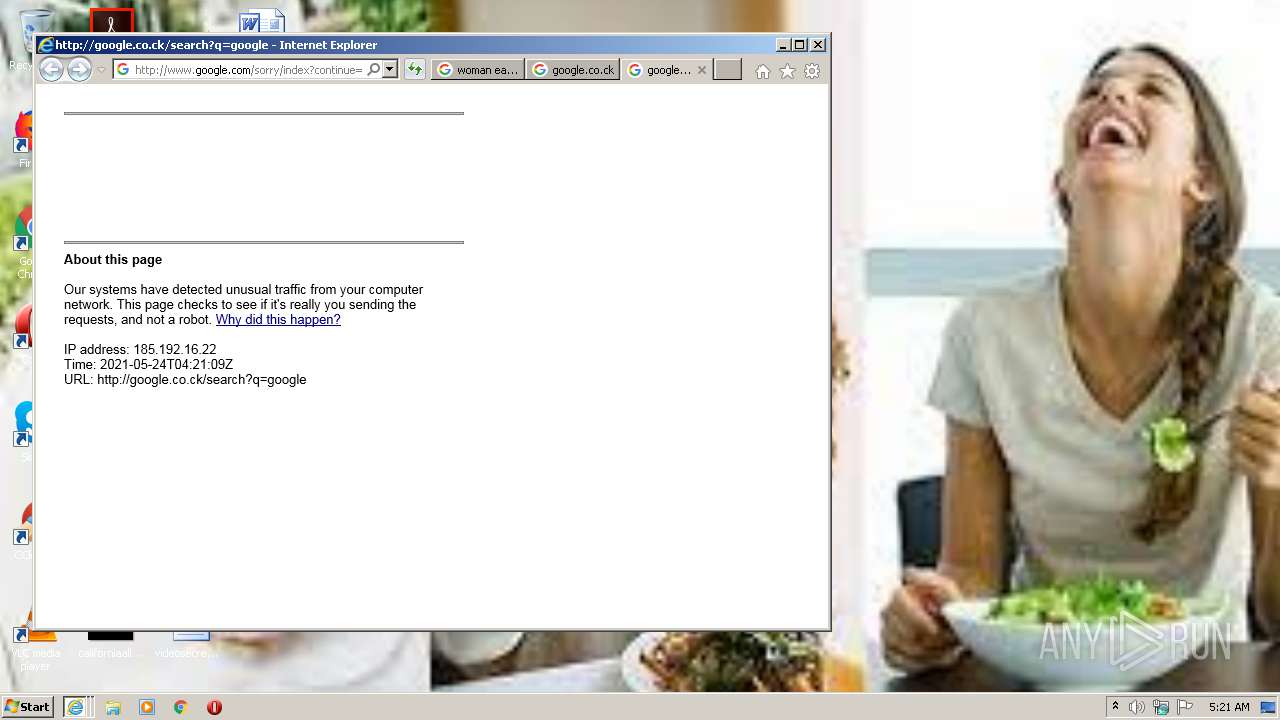
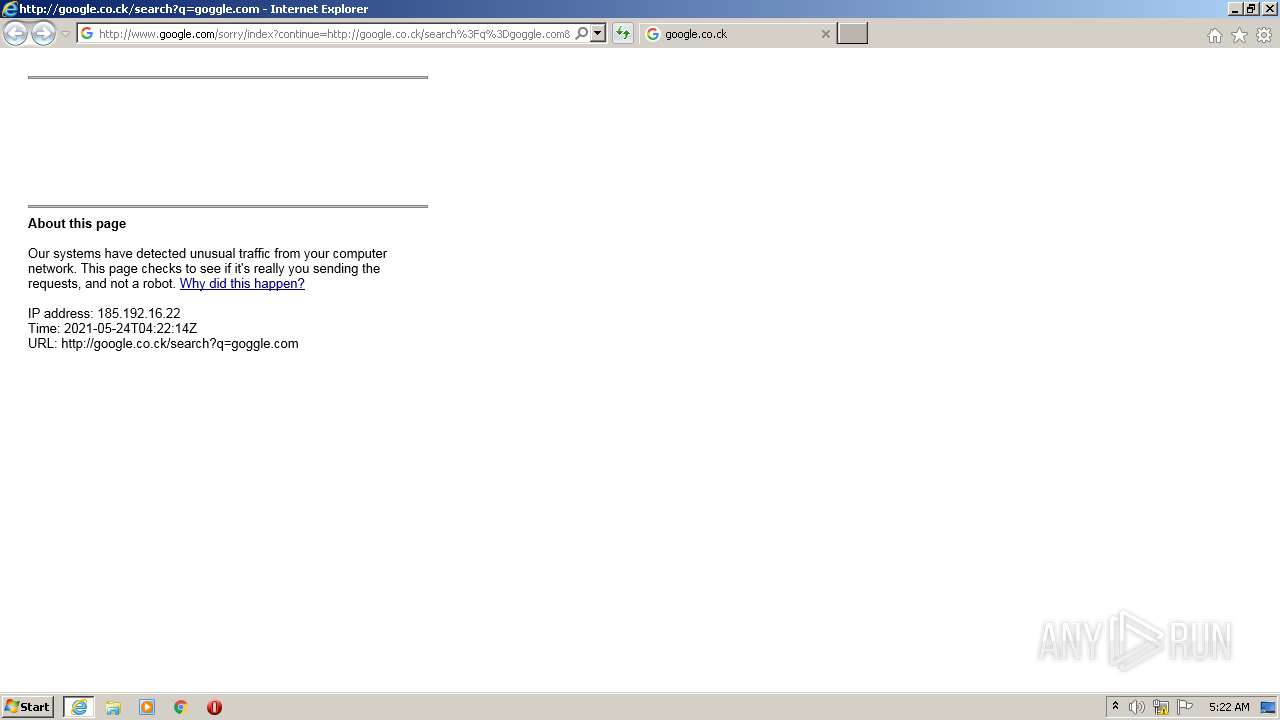
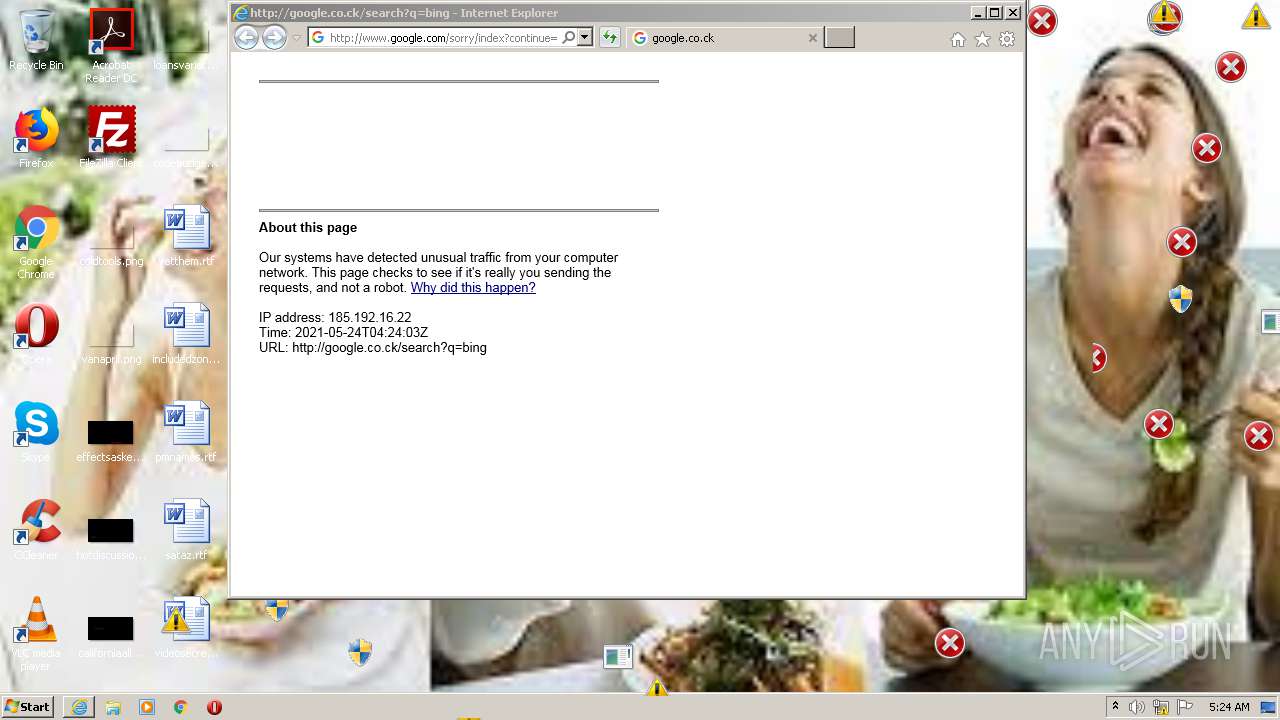
2708 | iexplore.exe | GET | 302 | 142.250.181.228:80 | http://google.co.ck/search?q=google | US | html | 330 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
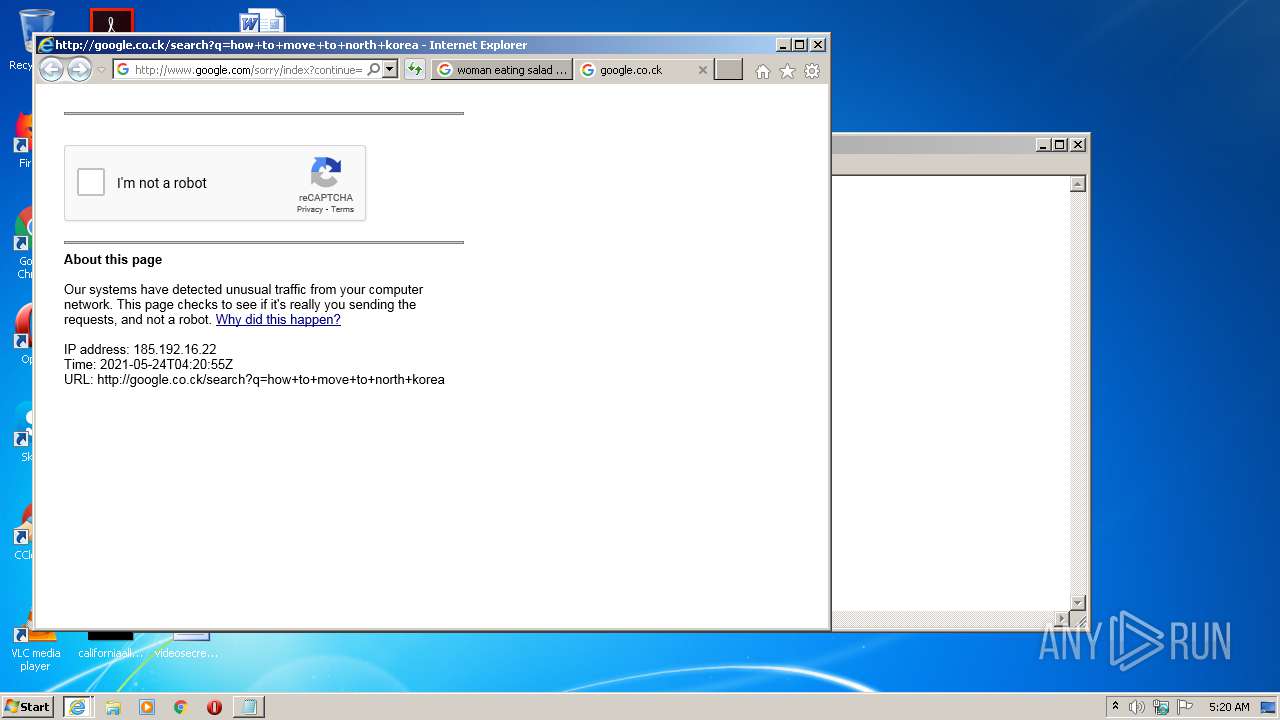
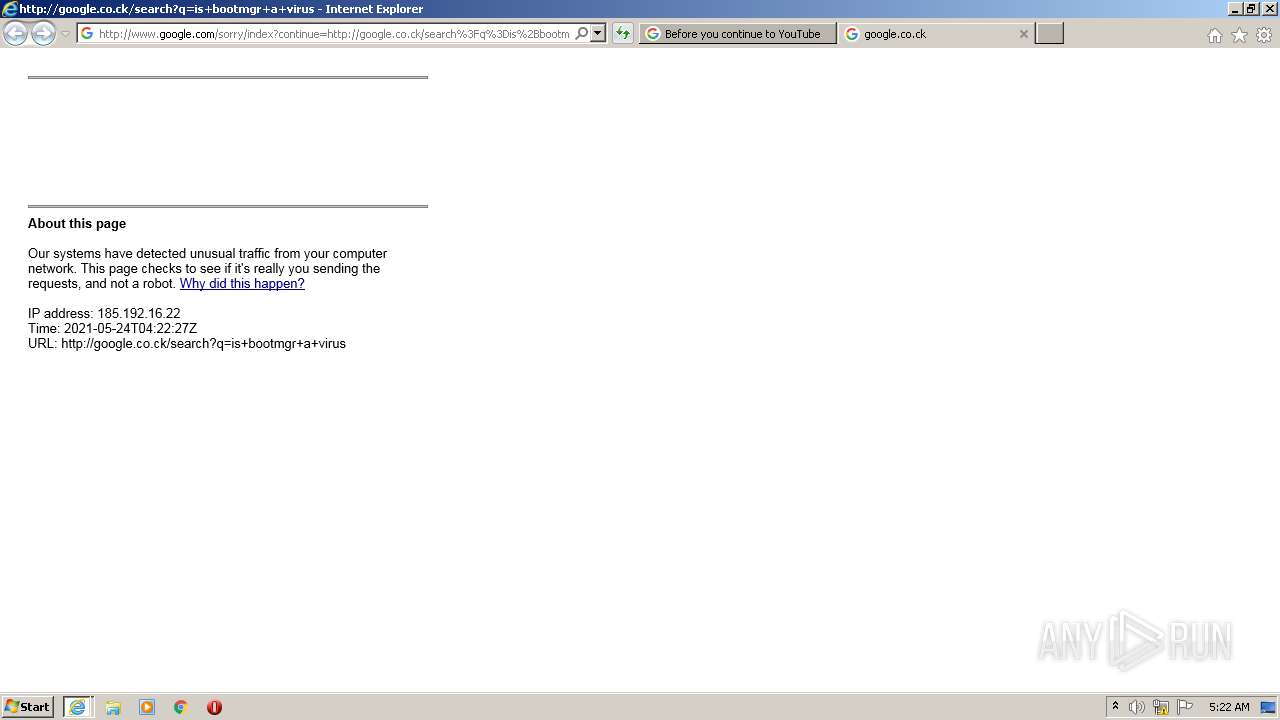
2708 | iexplore.exe | GET | 429 | 172.217.19.100:80 | http://www.google.com/sorry/index?continue=http://google.co.ck/search%3Fq%3Dgoogle&q=EgS5wBAWGLXTrIUGIhBSn1_Dr-DLhxqX4sg-PcEFMgFy | US | html | 2.74 Kb | malicious |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCpCh2XInXvhAMAAAAAzA%2Bj | US | der | 472 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDxx3f8WPfw%2FQoAAAAAzlvO | US | der | 472 b | whitelisted |
1556 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCyLOF%2BWIn0QAMAAAAAzA6w | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1556 | iexplore.exe | 142.250.185.99:80 | www.google.co.ck | Google Inc. | US | whitelisted |
1556 | iexplore.exe | 142.250.185.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1556 | iexplore.exe | 142.250.181.228:80 | google.co.ck | Google Inc. | US | whitelisted |
1556 | iexplore.exe | 142.250.185.99:443 | www.google.co.ck | Google Inc. | US | whitelisted |
1556 | iexplore.exe | 172.217.23.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1556 | iexplore.exe | 142.250.185.131:443 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1800 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1556 | iexplore.exe | 172.217.20.14:443 | apis.google.com | Google Inc. | US | whitelisted |
1556 | iexplore.exe | 142.250.185.110:443 | ogs.google.co.ck | Google Inc. | US | whitelisted |
1556 | iexplore.exe | 142.250.186.142:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.co.ck |
| whitelisted |
www.google.co.ck |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.co.ck |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |