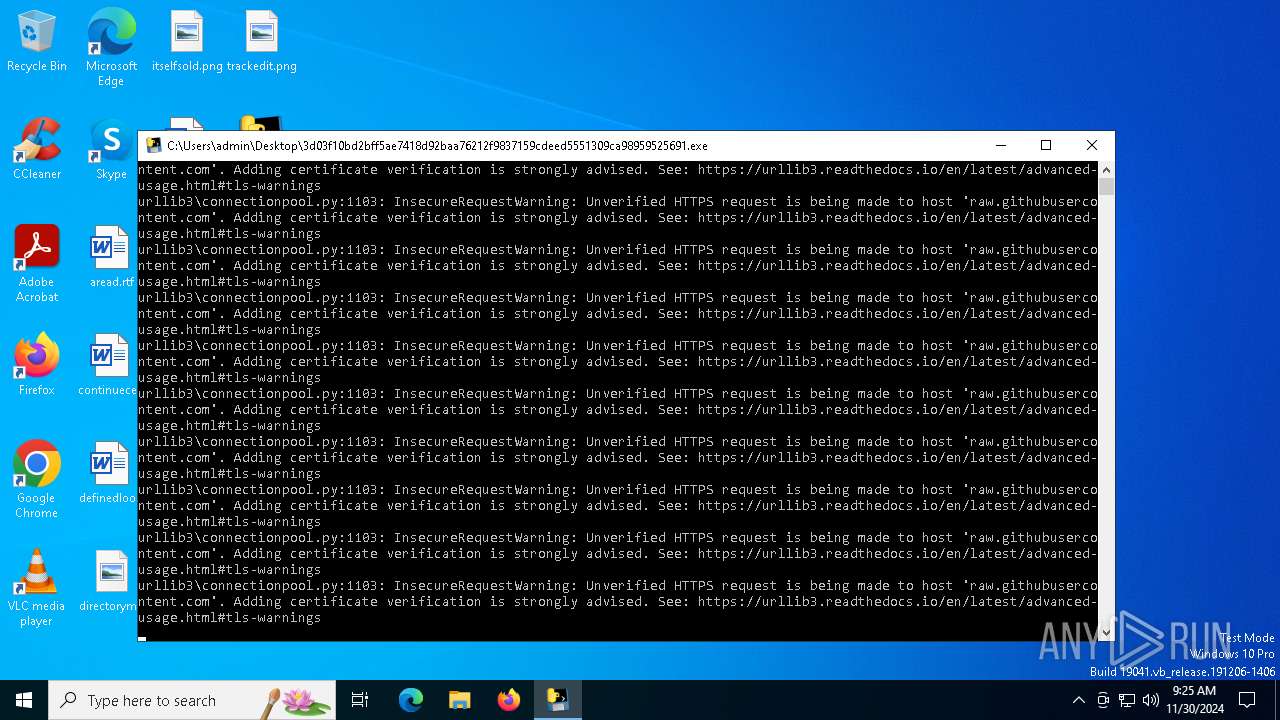
| File name: | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691 |
| Full analysis: | https://app.any.run/tasks/676a1fb1-68f3-4fde-90f9-ceaece2b88c2 |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2024, 09:24:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | BFFA318FF60FD764C100849B4DE0EA97 |
| SHA1: | 538D9B9008BA3BC68E5B3B90406CF6E581193934 |
| SHA256: | 3D03F10BD2BFF5AE7418D92BAA76212F9837159CDEED5551309CA98959525691 |
| SSDEEP: | 98304:mQWOcZPZ+KLTAHNMl/v0TqKJtT9IFLdZJULG8/Gkmu/ndyHGBMi0Ya/pNkLdANBC:BzPuGRCxLXY9QyreqdchnIG6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 5580)
Process drops python dynamic module
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 5580)
Process drops legitimate windows executable
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 5580)
Application launched itself
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 5580)
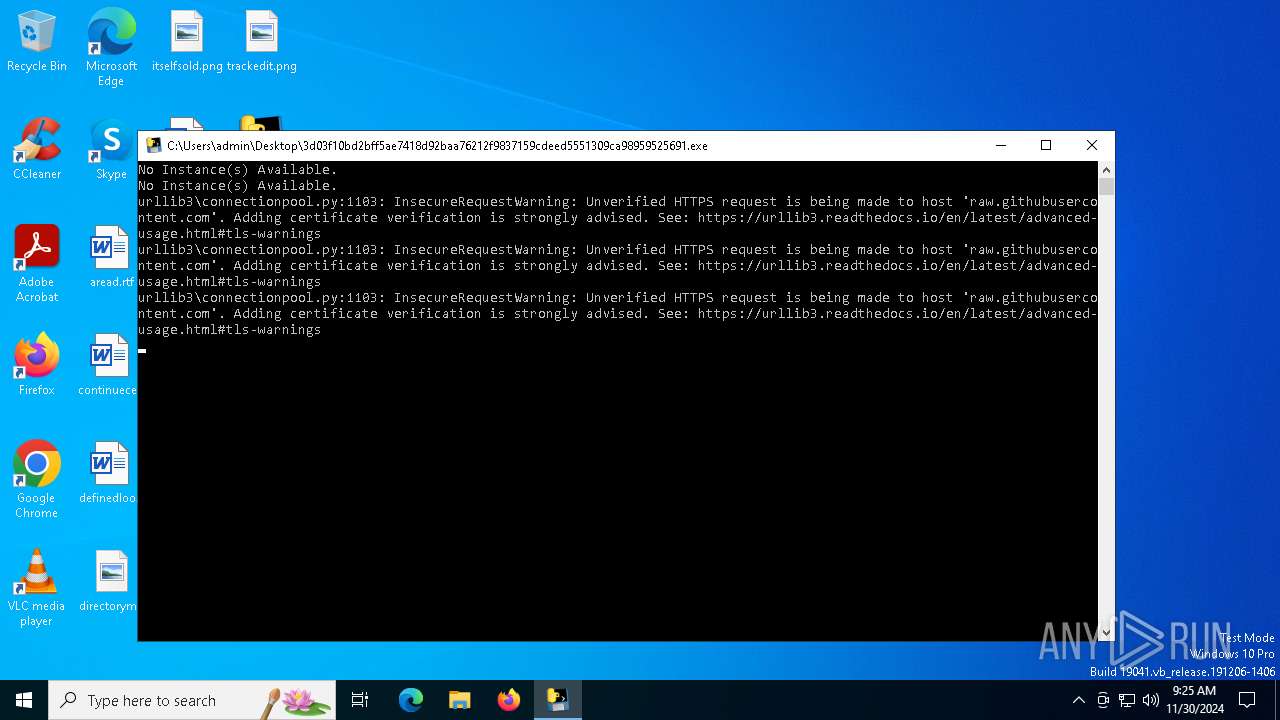
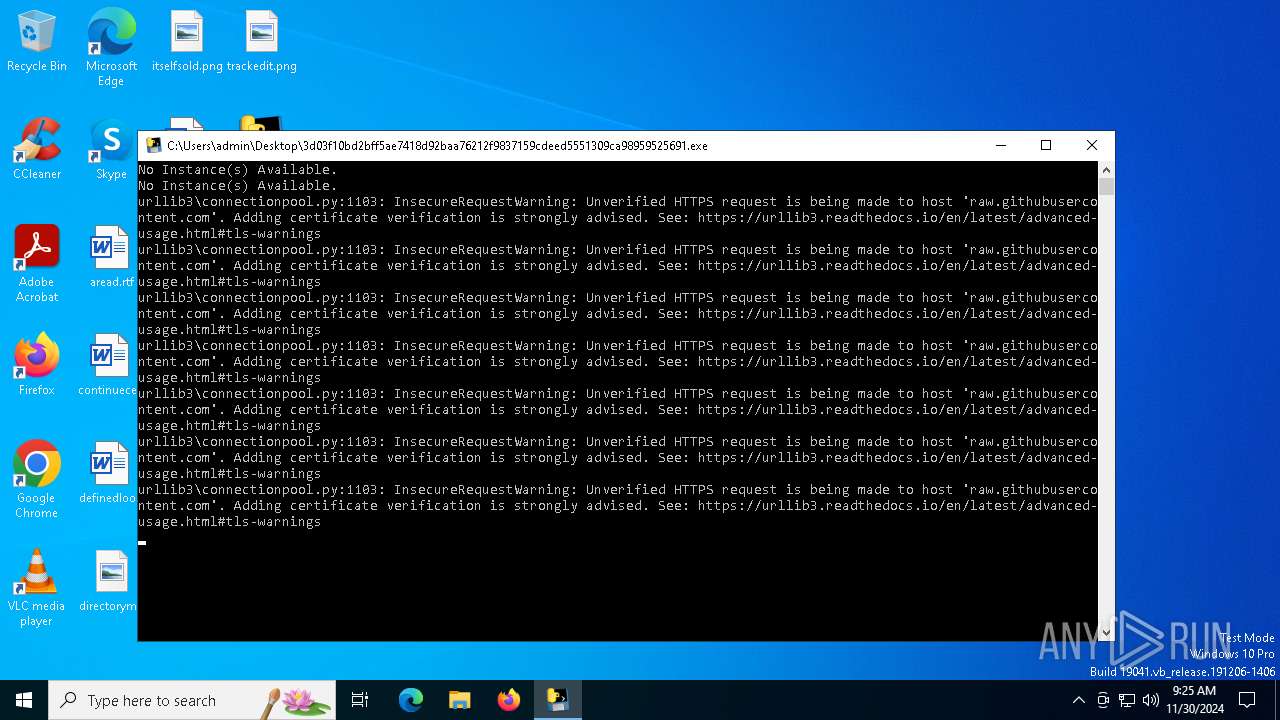
Uses WMIC.EXE to obtain BIOS management information
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
The process drops C-runtime libraries
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 5580)
Loads Python modules
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
Uses WMIC.EXE to obtain Windows Installer data
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 4264)
Uses WMIC.EXE to obtain data on the base board management (motherboard or system board)
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
Uses WMIC.EXE to obtain physical disk drive information
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
Uses WMIC.EXE to obtain CPU information
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
Possible usage of Discord/Telegram API has been detected (YARA)
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
Checks for external IP
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
INFO
Reads the computer name
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 5580)
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
Checks supported languages
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 5580)
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
Create files in a temporary directory
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 5580)
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5748)
- WMIC.exe (PID: 6096)
- WMIC.exe (PID: 4264)
- WMIC.exe (PID: 5000)
- WMIC.exe (PID: 5548)
- WMIC.exe (PID: 4592)
Checks proxy server information
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
PyInstaller has been detected (YARA)
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 5580)
Application based on Rust
- 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe (PID: 3736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:04:19 14:28:26+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 176640 |
| InitializedDataSize: | 154112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb9e0 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
125
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1344 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3736 | "C:\Users\admin\Desktop\3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe" | C:\Users\admin\Desktop\3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 4264 | wmic csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4592 | wmic bios get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5000 | wmic baseboard get manufacturer | C:\Windows\System32\wbem\WMIC.exe | — | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | wmic diskdrive get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5580 | "C:\Users\admin\Desktop\3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe" | C:\Users\admin\Desktop\3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 5748 | wmic cpu get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6096 | wmic baseboard get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
44 843
Read events
44 843
Write events
0
Delete events
0
Modification events
Executable files
74
Suspicious files
1
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5580 | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | C:\Users\admin\AppData\Local\Temp\_MEI55802\Pythonwin\mfc140u.dll | executable | |
MD5:03A161718F1D5E41897236D48C91AE3C | SHA256:E06C4BD078F4690AA8874A3DEB38E802B2A16CCB602A7EDC2E077E98C05B5807 | |||
| 5580 | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | C:\Users\admin\AppData\Local\Temp\_MEI55802\Pythonwin\win32ui.pyd | executable | |
MD5:D335339C3508604925016C1F3EE0600D | SHA256:8B992A0333990A255C6DF4395AE2E4153300596D75C7FBD17780214FB359B6A7 | |||
| 5580 | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | C:\Users\admin\AppData\Local\Temp\_MEI55802\_cffi_backend.cp312-win_amd64.pyd | executable | |
MD5:0572B13646141D0B1A5718E35549577C | SHA256:D8A76D1E31BBD62A482DEA9115FC1A109CB39AF4CF6D1323409175F3C93113A7 | |||
| 5580 | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | C:\Users\admin\AppData\Local\Temp\_MEI55802\_ctypes.pyd | executable | |
MD5:2A834C3738742D45C0A06D40221CC588 | SHA256:F20DFA748B878751EA1C4FE77A230D65212720652B99C4E5577BCE461BBD9089 | |||
| 5580 | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | C:\Users\admin\AppData\Local\Temp\_MEI55802\VCRUNTIME140.dll | executable | |
MD5:BE8DBE2DC77EBE7F88F910C61AEC691A | SHA256:4D292623516F65C80482081E62D5DADB759DC16E851DE5DB24C3CBB57B87DB83 | |||
| 5580 | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | C:\Users\admin\AppData\Local\Temp\_MEI55802\_bz2.pyd | executable | |
MD5:59D60A559C23202BEB622021AF29E8A9 | SHA256:706D4A0C26DD454538926CBB2FF6C64257C3D9BD48C956F7CABD6DEF36FFD13E | |||
| 5580 | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | C:\Users\admin\AppData\Local\Temp\_MEI55802\_hashlib.pyd | executable | |
MD5:B0262BD89A59A3699BFA75C4DCC3EE06 | SHA256:4ADFBBD6366D9B55D902FC54D2B42E7C8C989A83016ED707BD7A302FC3FC7B67 | |||
| 5580 | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | C:\Users\admin\AppData\Local\Temp\_MEI55802\_ssl.pyd | executable | |
MD5:DDB21BD1ACDE4264754C49842DE7EBC9 | SHA256:72BB15CD8C14BA008A52D23CDCFC851A9A4BDE13DEEE302A5667C8AD60F94A57 | |||
| 5580 | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | C:\Users\admin\AppData\Local\Temp\_MEI55802\_queue.pyd | executable | |
MD5:F3ECA4F0B2C6C17ACE348E06042981A4 | SHA256:FB57EE6ADF6E7B11451B6920DDD2FB943DCD9561C9EAE64FDDA27C7ED0BC1B04 | |||
| 5580 | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | C:\Users\admin\AppData\Local\Temp\_MEI55802\VCRUNTIME140_1.dll | executable | |
MD5:F8DFA78045620CF8A732E67D1B1EB53D | SHA256:A113F192195F245F17389E6ECBED8005990BCB2476DDAD33F7C4C6C86327AFE5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
35
DNS requests
10
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5448 | svchost.exe | GET | 200 | 2.16.164.97:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
5448 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/6nz/virustotal-vm-blacklist/main/hwid_list.txt | US | text | 10.1 Kb | unknown |
— | — | GET | 200 | 172.67.74.152:443 | https://api.ipify.org/ | US | text | 12 b | malicious |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/6nz/virustotal-vm-blacklist/main/ip_list.txt | US | text | 2.79 Kb | unknown |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/6nz/virustotal-vm-blacklist/main/mac_list.txt | US | text | 8.17 Kb | unknown |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/6nz/virustotal-vm-blacklist/main/pc_name_list.txt | US | text | 3.07 Kb | unknown |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/6nz/virustotal-vm-blacklist/main/pc_username_list.txt | US | text | 1.25 Kb | unknown |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/6nz/virustotal-vm-blacklist/main/gpu_list.txt | US | text | 1.22 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.204.148:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5448 | svchost.exe | 2.16.164.97:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5448 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5448 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
api.ipify.org |
| shared |
raw.githubusercontent.com |
| shared |
api.github.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
3736 | 3d03f10bd2bff5ae7418d92baa76212f9837159cdeed5551309ca98959525691.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |