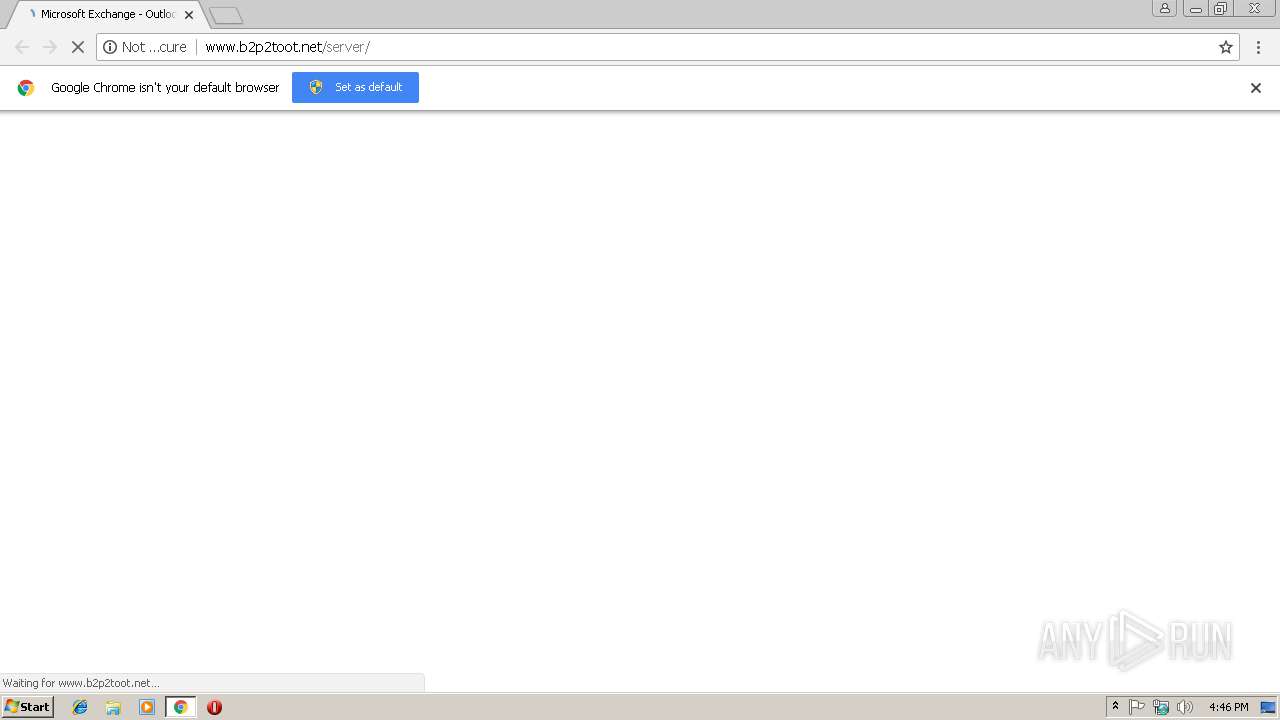
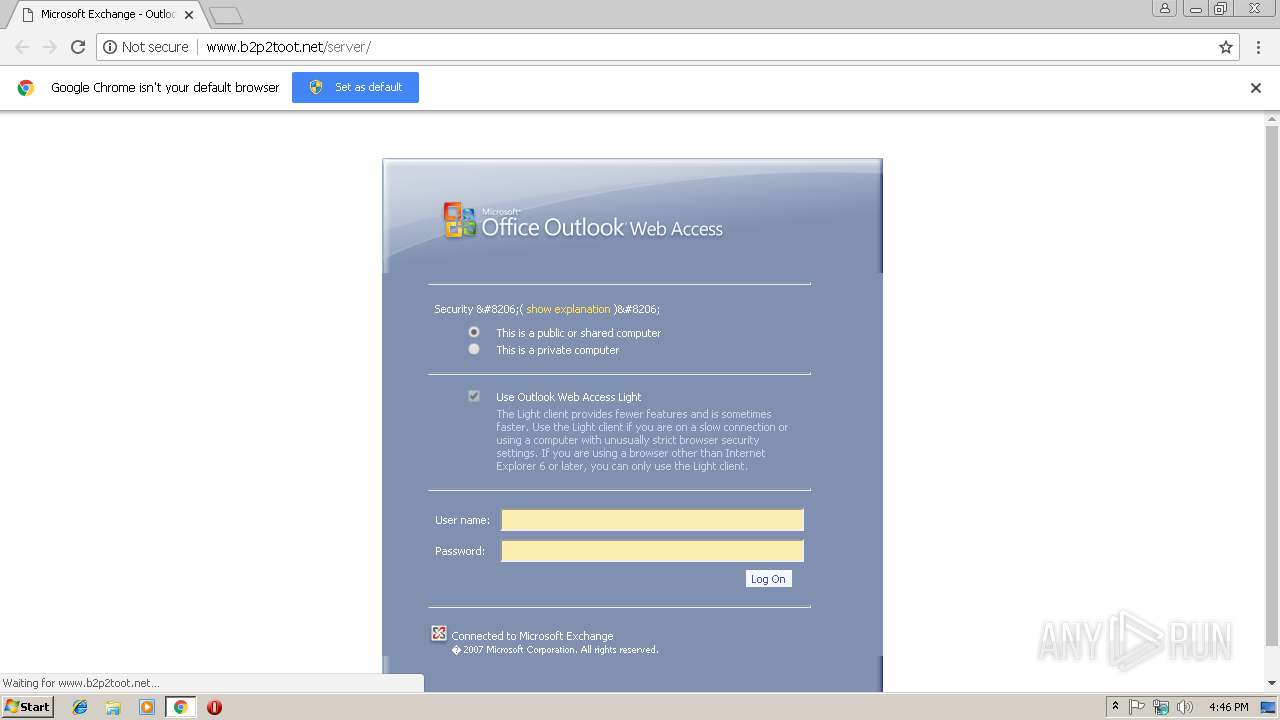
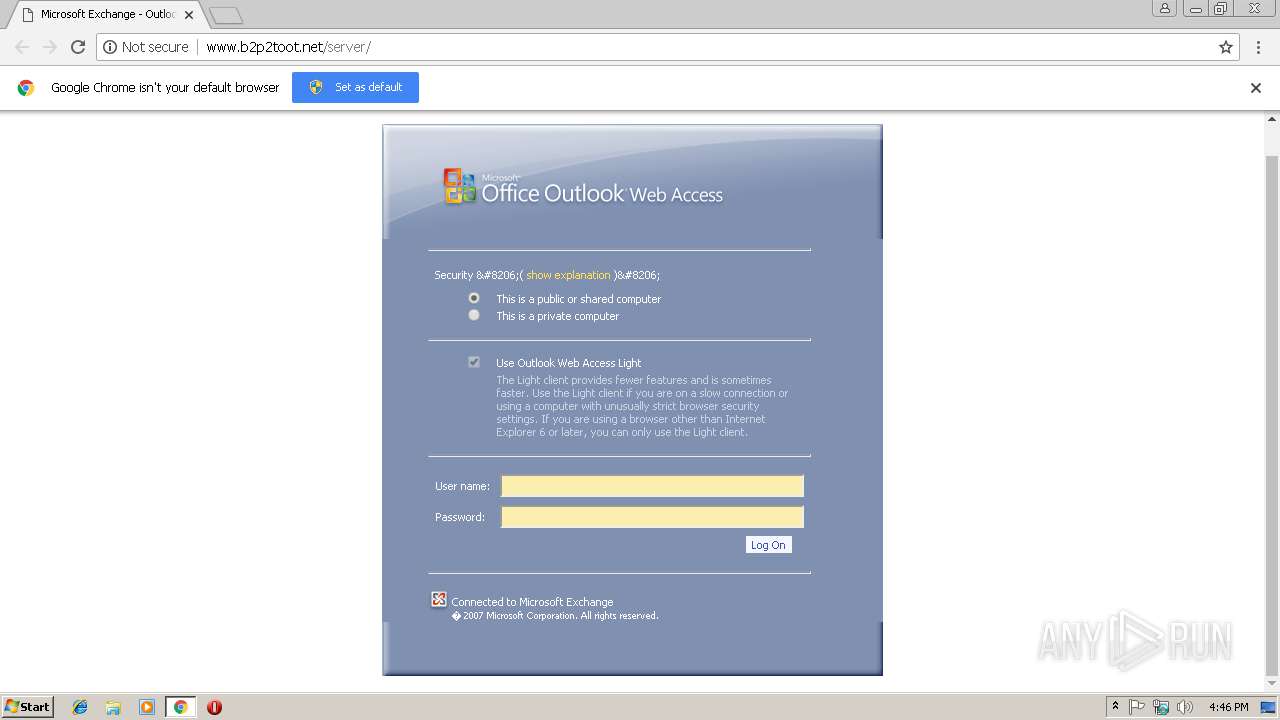
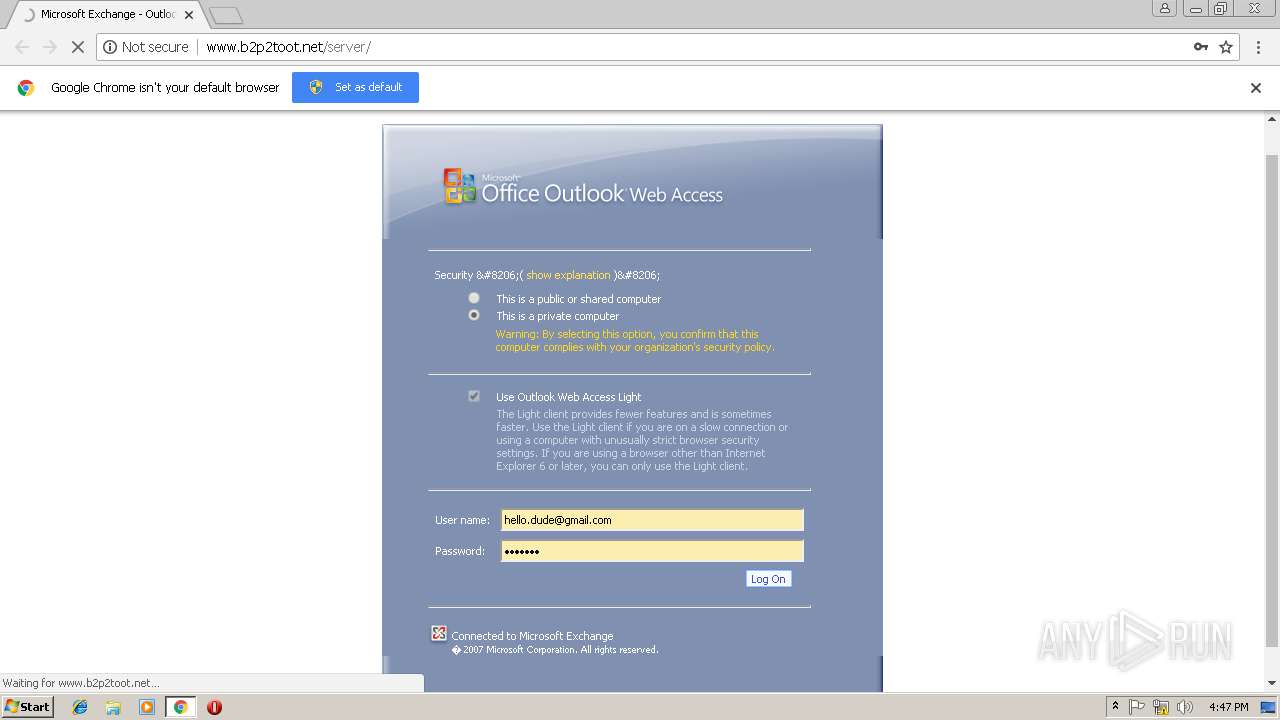
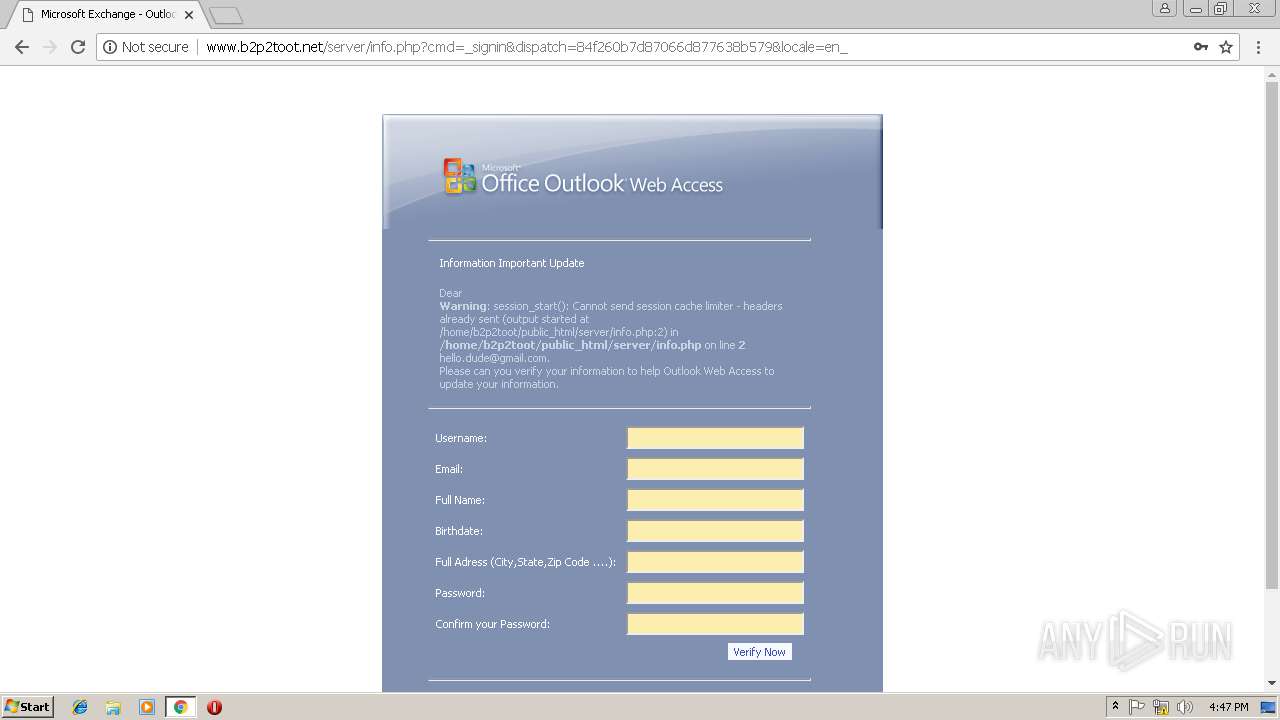
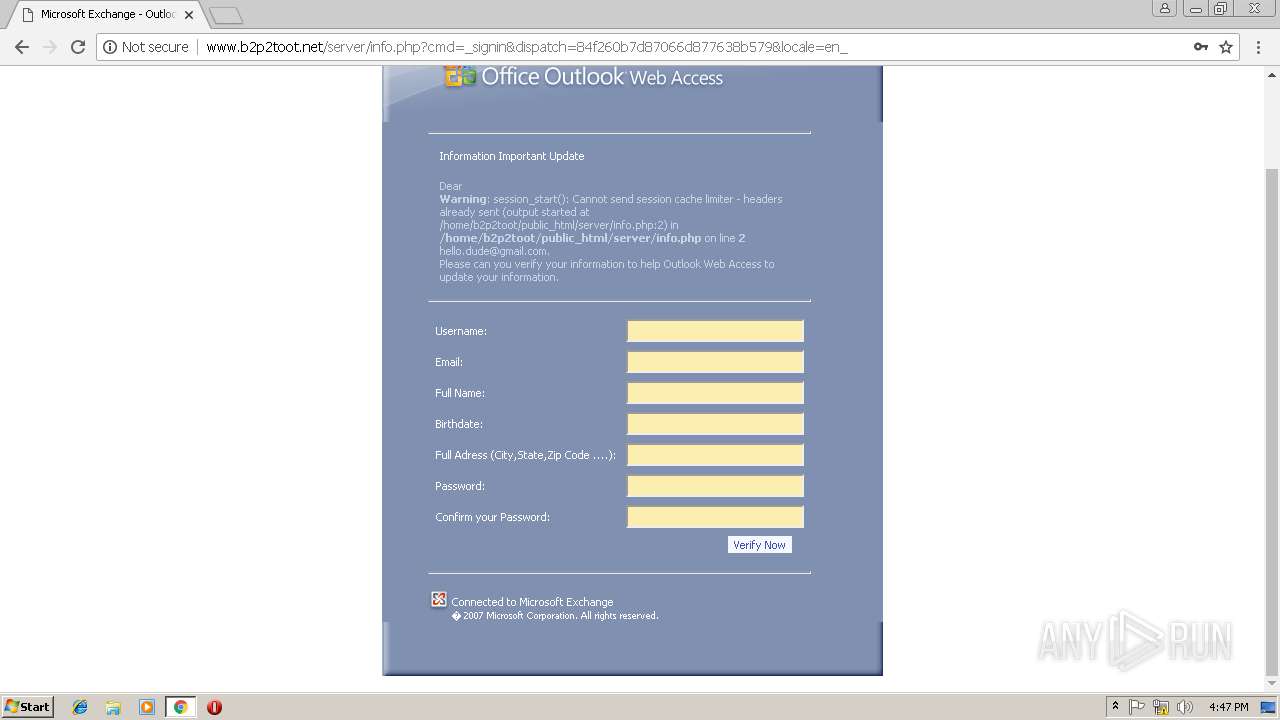
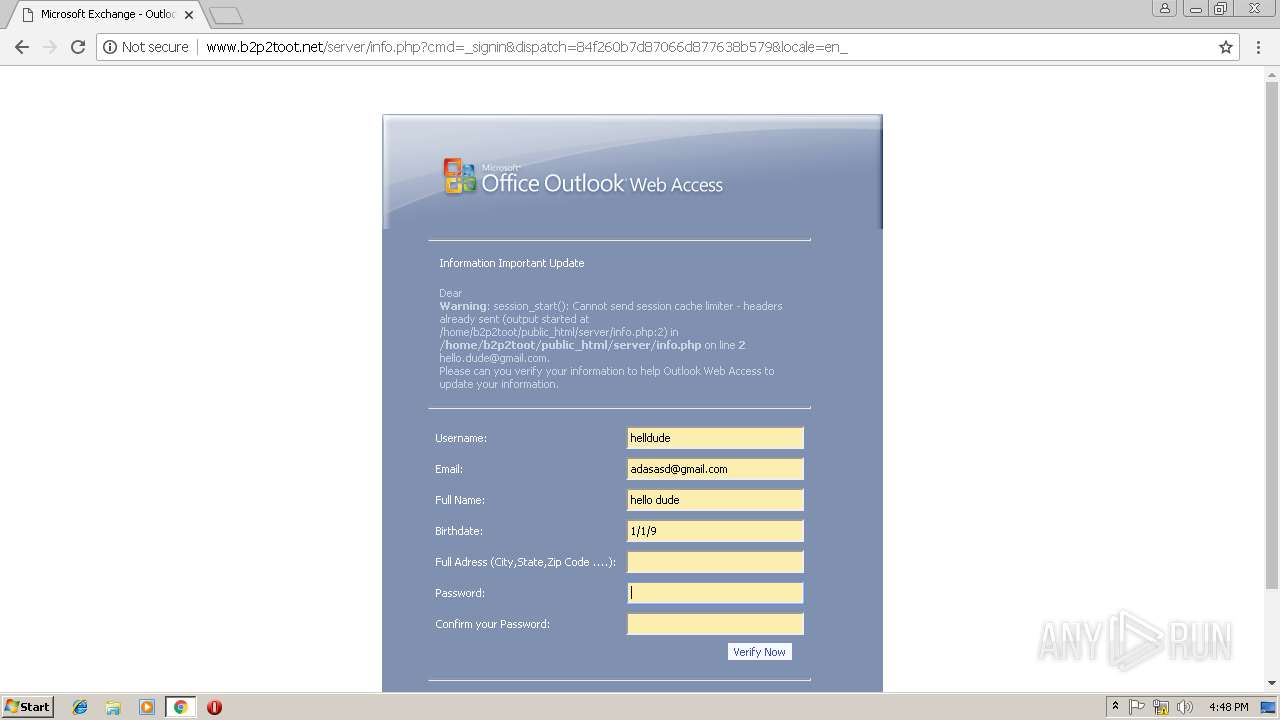
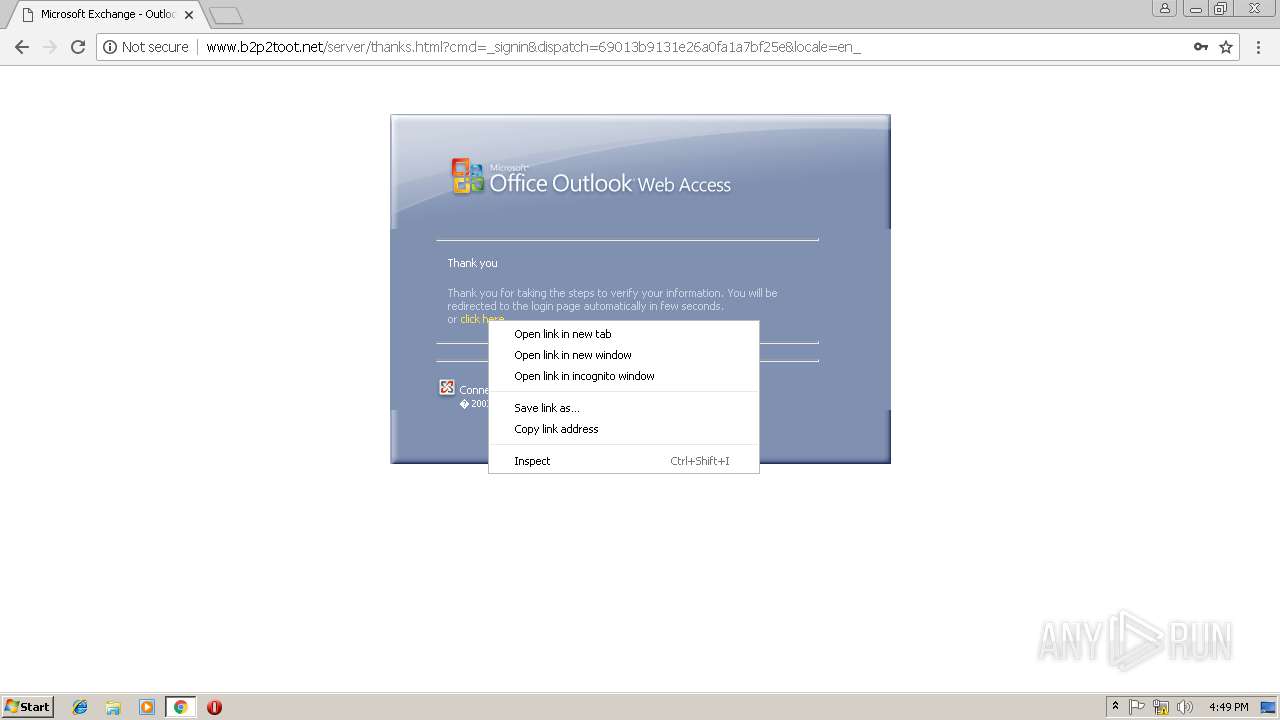
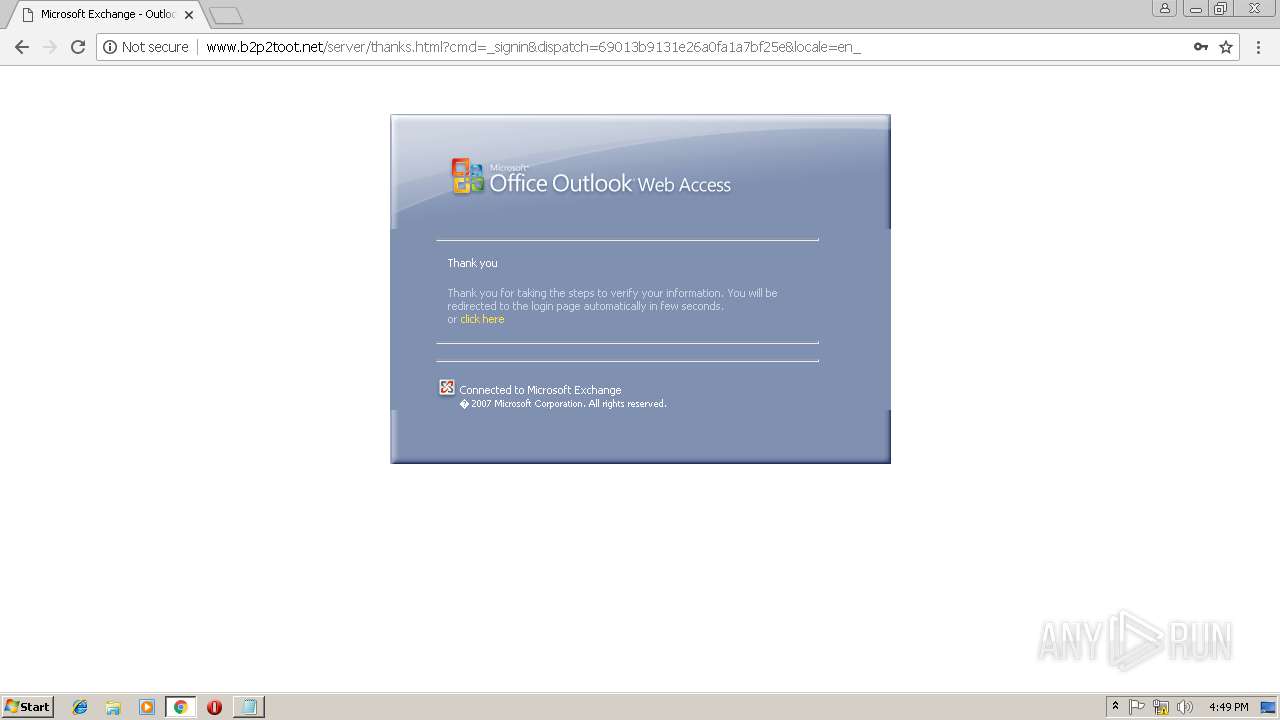
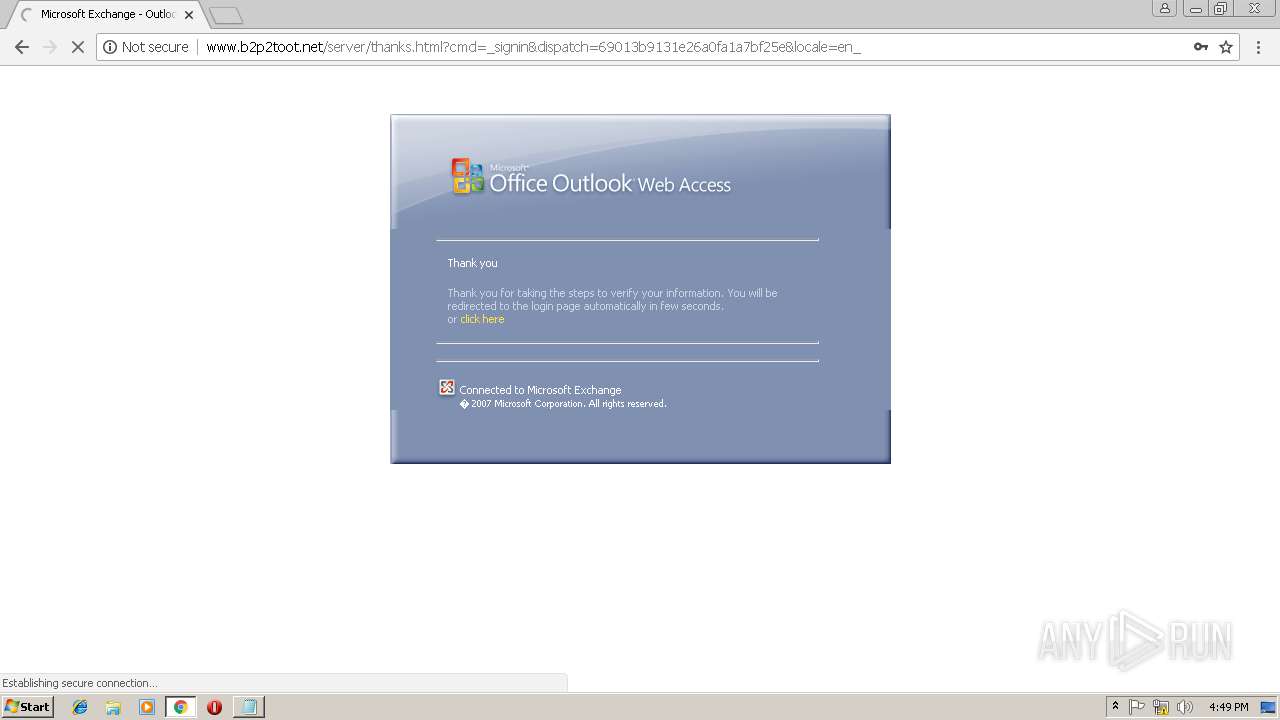
| URL: | http://www.b2p2toot.net/server/ |
| Full analysis: | https://app.any.run/tasks/f075d462-f5dd-4ee7-9151-e32cd421cf84 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2019, 16:45:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D60A1D53DCB15127E3A1F7794E2D4FD3 |
| SHA1: | 3C21E46D381F780CA0D5909123DD05FF50CBF72E |
| SHA256: | 3CFDDFD8106ED7712BB6B185BC66E04F4BF6609BBA525C30649B648BB0080A32 |
| SSDEEP: | 3:N1KJS4NR7XHXMXK:Cc4NxX3Ma |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=322297126918742E09D9A2DE0386031C --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=8A06F70D374E981BF1B0C8A1342079BF --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=F092FA22CB1F45F61C799A1FDB4C4436 --mojo-platform-channel-handle=608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
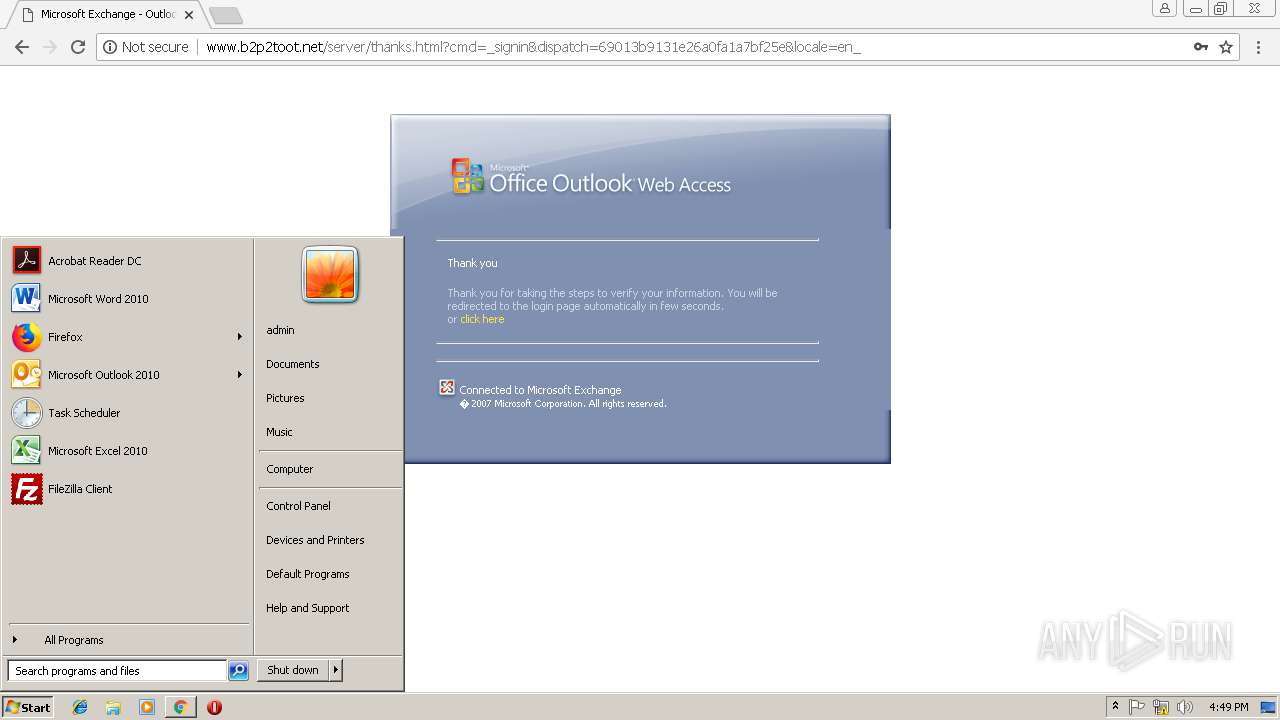
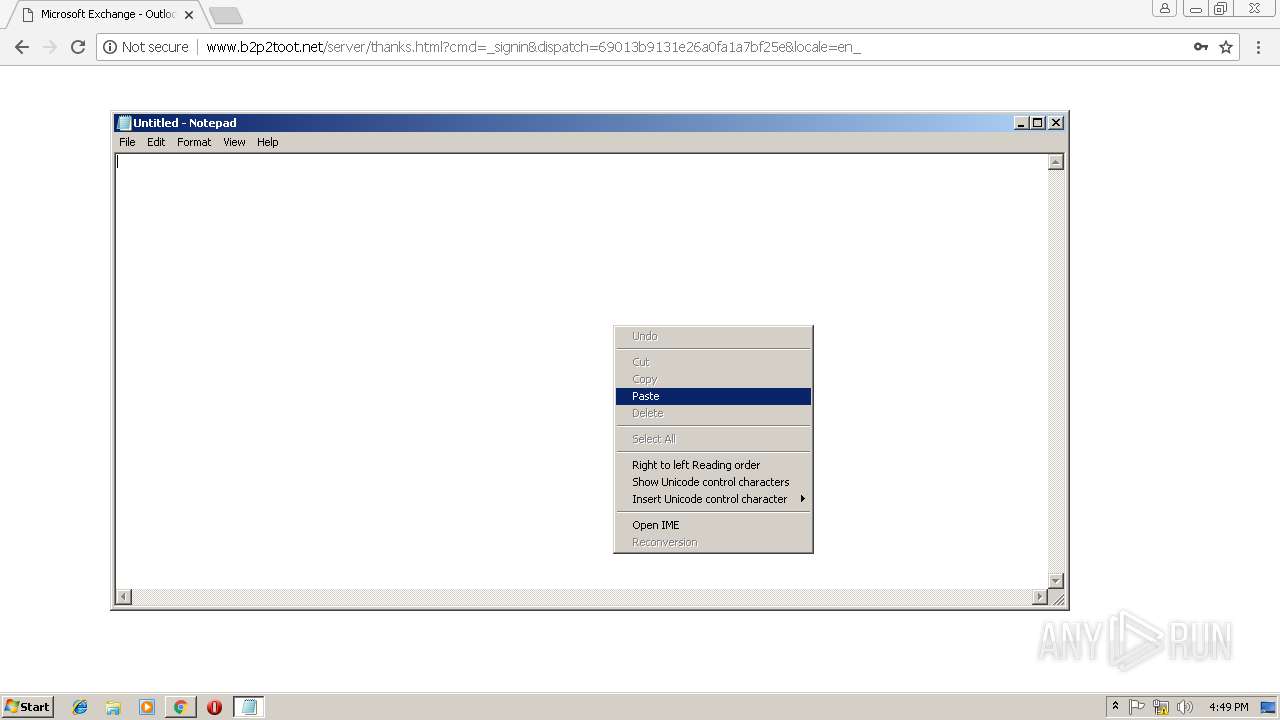
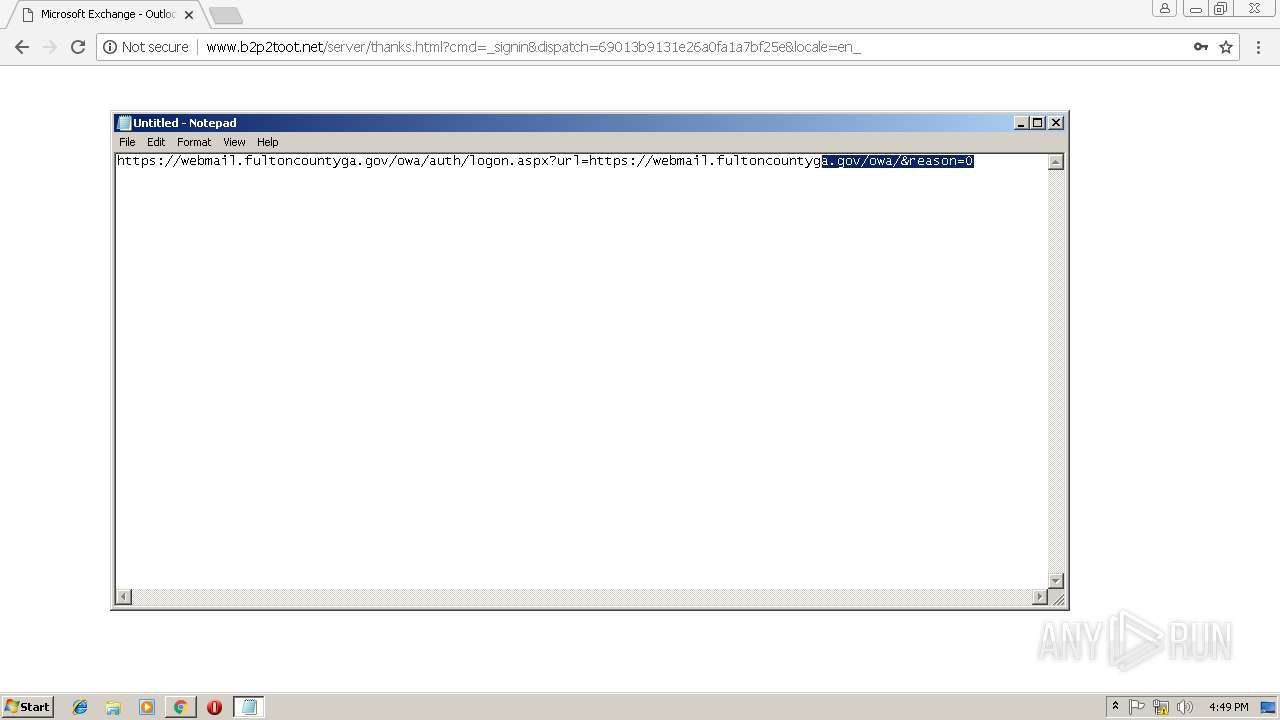
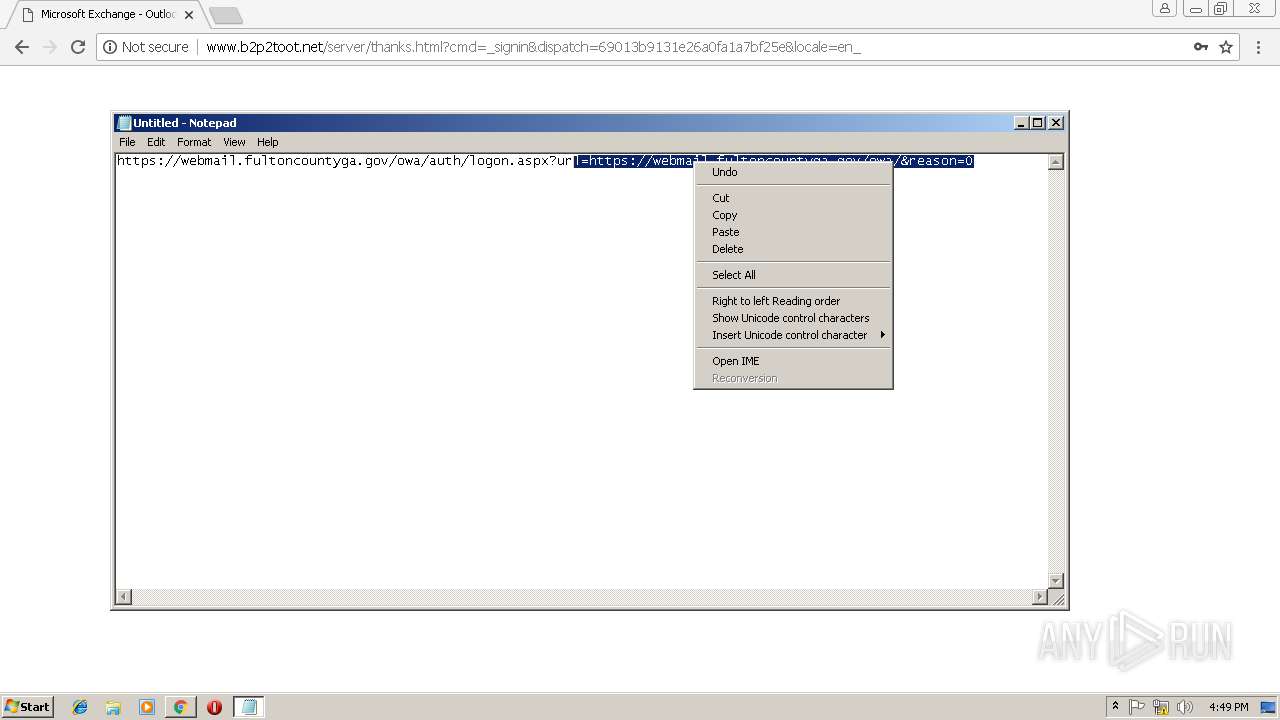
| 2816 | "C:\Windows\system32\notepad.exe" | C:\Windows\system32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3032 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://www.b2p2toot.net/server/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --service-pipe-token=EC89310963B0D0C975B05C03951C1B60 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=EC89310963B0D0C975B05C03951C1B60 --renderer-client-id=4 --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --service-pipe-token=DC4117E6C36385A02CE2449B8D68C817 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=DC4117E6C36385A02CE2449B8D68C817 --renderer-client-id=3 --mojo-platform-channel-handle=2036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=D76971E5A3FE8DFD08321EE0E797BEEF --mojo-platform-channel-handle=2440 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=FC9426793893831288FC776BD5CD19AB --mojo-platform-channel-handle=3536 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
529
Read events
464
Write events
61
Delete events
4
Modification events
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3028-13192217166031625 |
Value: 259 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3028-13192217166031625 |
Value: 259 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
12
Text files
81
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f886a3cf-311d-463d-8feb-c936aa0163c7.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0f931cbc-30fe-4ad4-a72c-674b7ccdadae.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1998ea.TMP | text | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF199948.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
24
DNS requests
11
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | chrome.exe | GET | 200 | 103.247.11.93:80 | http://www.b2p2toot.net/server/Microsoft%20Exchange%20-%20Outlook%20Web%20Access_files/flogon.js | ID | text | 3.60 Kb | suspicious |
3028 | chrome.exe | GET | 200 | 103.247.11.93:80 | http://www.b2p2toot.net/server/Microsoft%20Exchange%20-%20Outlook%20Web%20Access_files/owafont.css | ID | text | 3.38 Kb | suspicious |
3028 | chrome.exe | GET | 200 | 103.247.11.93:80 | http://www.b2p2toot.net/server/Microsoft%20Exchange%20-%20Outlook%20Web%20Access_files/lgnbotl.gif | ID | image | 1.10 Kb | suspicious |
3028 | chrome.exe | GET | 200 | 103.247.11.93:80 | http://www.b2p2toot.net/server/Microsoft%20Exchange%20-%20Outlook%20Web%20Access_files/lgntopr.gif | ID | image | 2.45 Kb | suspicious |
3028 | chrome.exe | GET | 200 | 103.247.11.93:80 | http://www.b2p2toot.net/server/ | ID | html | 36.6 Kb | suspicious |
3028 | chrome.exe | GET | 200 | 103.247.11.93:80 | http://www.b2p2toot.net/server/Microsoft%20Exchange%20-%20Outlook%20Web%20Access_files/lgntopl.gif | ID | image | 14.6 Kb | suspicious |
3028 | chrome.exe | GET | 200 | 103.247.11.93:80 | http://www.b2p2toot.net/server/Microsoft%20Exchange%20-%20Outlook%20Web%20Access_files/logon.css | ID | text | 2.26 Kb | suspicious |
3028 | chrome.exe | GET | 404 | 103.247.11.93:80 | http://www.b2p2toot.net/server/Microsoft%20Exchange%20-%20Outlook%20Web%20Access_files/lgnbotm.gif | ID | html | 381 b | suspicious |
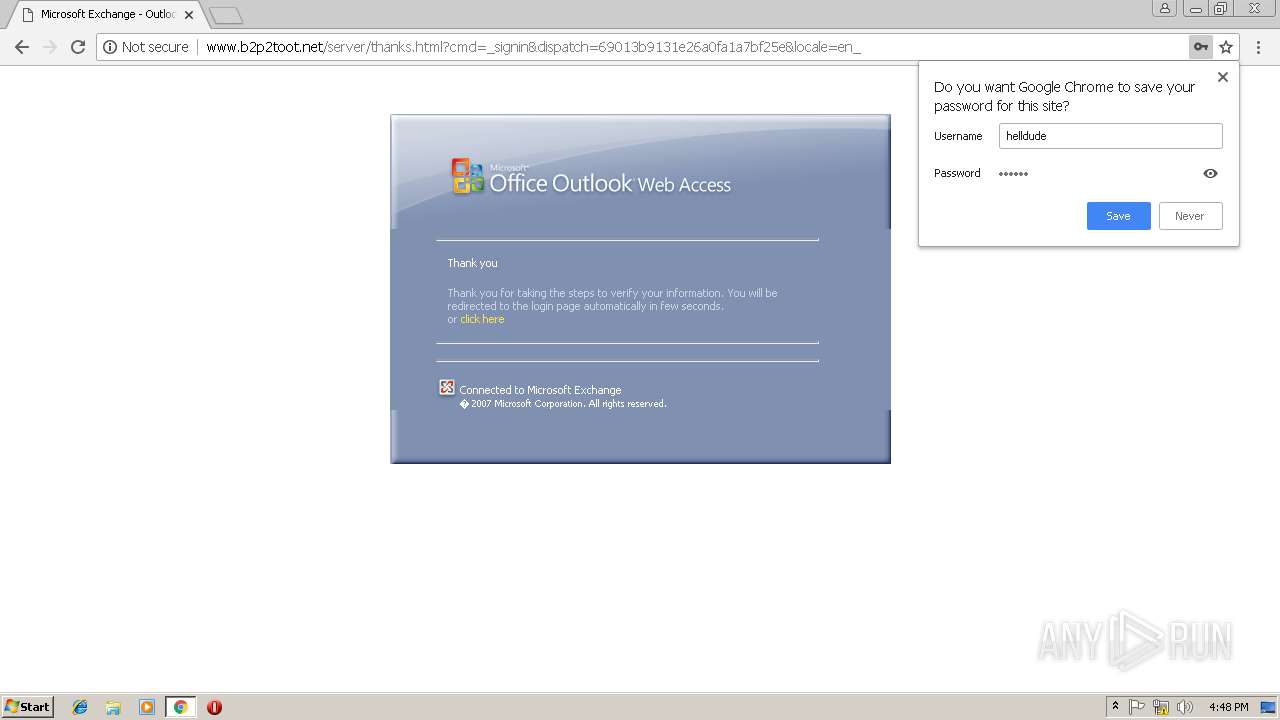
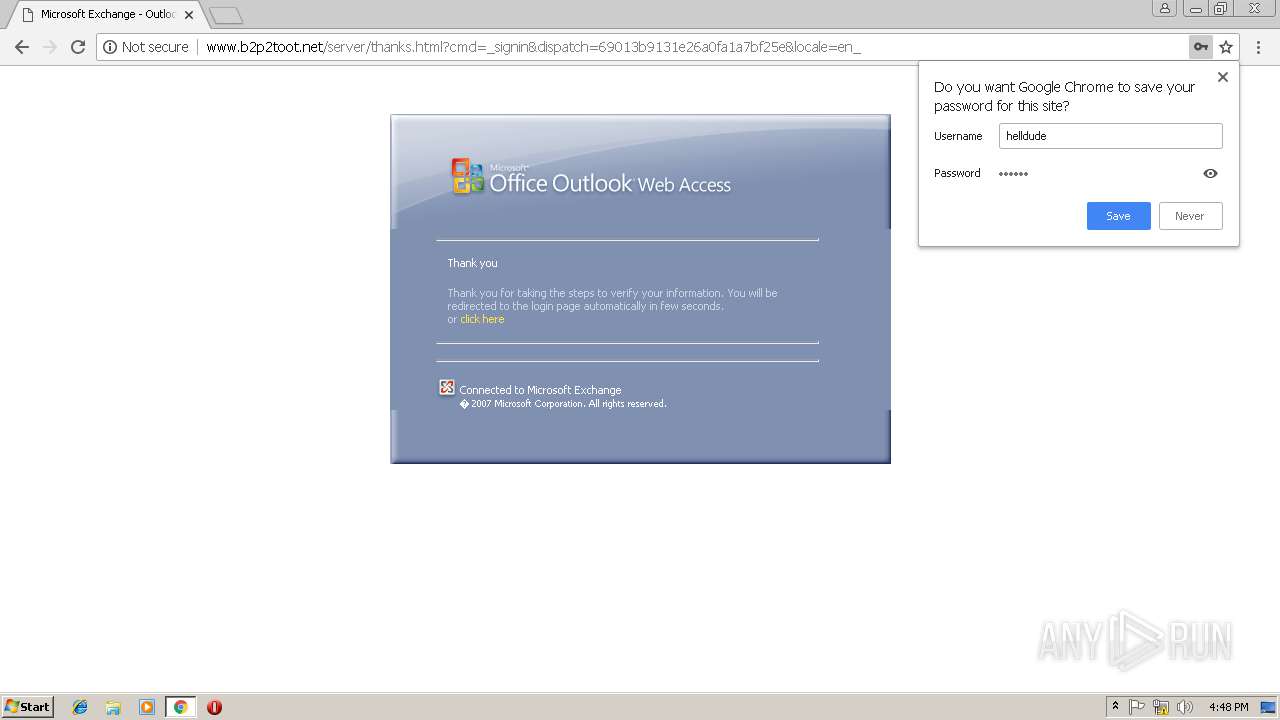
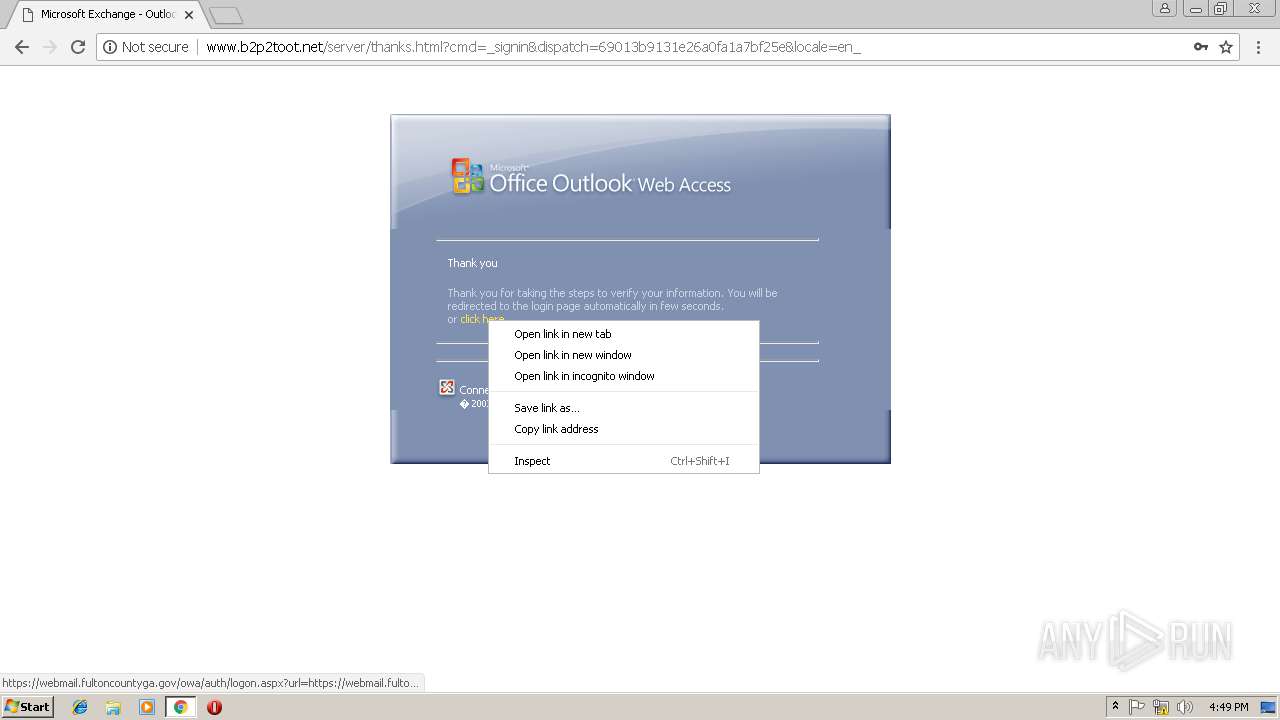
3028 | chrome.exe | POST | 302 | 103.247.11.93:80 | http://www.b2p2toot.net/server/access.php | ID | — | — | suspicious |
3028 | chrome.exe | GET | 200 | 103.247.11.93:80 | http://www.b2p2toot.net/server/Microsoft%20Exchange%20-%20Outlook%20Web%20Access_files/lgnbotr.gif | ID | image | 516 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3028 | chrome.exe | 103.247.11.93:80 | www.b2p2toot.net | Rumahweb Indonesia CV. | ID | suspicious |
3028 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3028 | chrome.exe | 216.58.210.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
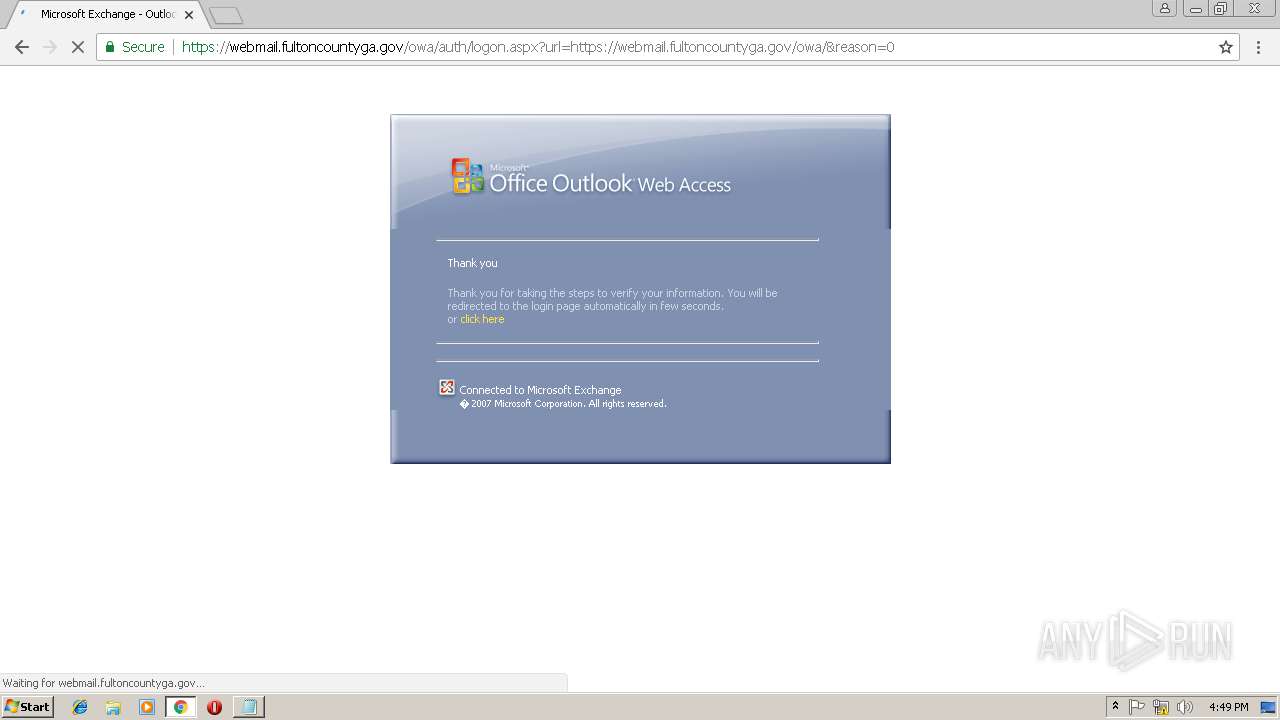
3028 | chrome.exe | 68.208.11.209:443 | webmail.fultoncountyga.gov | BellSouth.net Inc. | US | unknown |
3028 | chrome.exe | 2.16.186.56:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3028 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3028 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3028 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.b2p2toot.net |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
dns.msftncsi.com |
| shared |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
webmail.fultoncountyga.gov |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report