| File name: | dive.exe |
| Full analysis: | https://app.any.run/tasks/b88d5c33-3bc4-4283-a150-0c3cdab6d99b |
| Verdict: | Malicious activity |
| Analysis date: | June 22, 2025, 00:03:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | FCE3FA5D2B4AAA74507A82E67433B4E3 |
| SHA1: | 52378943D25A02BEFC0B1EFE8A91424212A6BC24 |
| SHA256: | 3CEBB88691A10231A10EDAD0D84179B48FFD115904F8D23C2448621DF80A069A |
| SSDEEP: | 3072:/3BOxcTRe/bAp4CQoAOUBSgkelKM3pNzmKaSI7yFpceNRckl2yp89FHp5qwar+SO: |
MALICIOUS
SNOJAN has been detected (SURICATA)
- el.exe (PID: 6016)
- el.exe (PID: 4232)
- el.exe (PID: 4888)
- el.exe (PID: 6980)
- el.exe (PID: 6772)
- el.exe (PID: 6260)
- el.exe (PID: 6124)
- el.exe (PID: 1232)
- el.exe (PID: 3844)
SUSPICIOUS
Executable content was dropped or overwritten
- dive.exe (PID: 2044)
- el.exe (PID: 4888)
- el.exe (PID: 4232)
- el.exe (PID: 3844)
- el.exe (PID: 6016)
- el.exe (PID: 6980)
- el.exe (PID: 6172)
- el.exe (PID: 6772)
- el.exe (PID: 1232)
- el.exe (PID: 6260)
- el.exe (PID: 6124)
INFO
Checks supported languages
- dive.exe (PID: 2044)
- el.exe (PID: 4232)
- el.exe (PID: 6124)
- el.exe (PID: 6172)
- el.exe (PID: 1232)
- el.exe (PID: 6260)
- el.exe (PID: 4888)
- el.exe (PID: 6016)
- el.exe (PID: 3844)
- el.exe (PID: 6772)
- el.exe (PID: 6980)
Disables trace logs
- dive.exe (PID: 2044)
Checks proxy server information
- dive.exe (PID: 2044)
- slui.exe (PID: 4172)
Reads the computer name
- dive.exe (PID: 2044)
- el.exe (PID: 6980)
- el.exe (PID: 6772)
- el.exe (PID: 4232)
- el.exe (PID: 1232)
- el.exe (PID: 6124)
- el.exe (PID: 6172)
- el.exe (PID: 6260)
- el.exe (PID: 4888)
- el.exe (PID: 6016)
- el.exe (PID: 3844)
Reads Environment values
- dive.exe (PID: 2044)
Reads the machine GUID from the registry
- dive.exe (PID: 2044)
Reads the software policy settings
- dive.exe (PID: 2044)
- slui.exe (PID: 4172)
Create files in a temporary directory
- dive.exe (PID: 2044)
- el.exe (PID: 6980)
- el.exe (PID: 6016)
- el.exe (PID: 3844)
- el.exe (PID: 6260)
- el.exe (PID: 6124)
- el.exe (PID: 4888)
- el.exe (PID: 4232)
- el.exe (PID: 6172)
- el.exe (PID: 6772)
- el.exe (PID: 1232)
UPX packer has been detected
- el.exe (PID: 6124)
- el.exe (PID: 6260)
- el.exe (PID: 4888)
- el.exe (PID: 6772)
- el.exe (PID: 1232)
- el.exe (PID: 6172)
- el.exe (PID: 6016)
- el.exe (PID: 4232)
- el.exe (PID: 3844)
- el.exe (PID: 6980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:21 23:58:26+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 683008 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2bee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | ConsoleApplication2 |
| FileVersion: | 1.0.0.0 |
| InternalName: | ConsoleApplication2.exe |
| LegalCopyright: | Copyright © 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | ConsoleApplication2.exe |
| ProductName: | ConsoleApplication2 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
165
Monitored processes
15
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1232 | "el.exe" | C:\Users\admin\AppData\Local\Temp\el.exe | dive.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2044 | "C:\Users\admin\AppData\Local\Temp\dive.exe" | C:\Users\admin\AppData\Local\Temp\dive.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ConsoleApplication2 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3584 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 3844 | "el.exe" | C:\Users\admin\AppData\Local\Temp\el.exe | dive.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4172 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4232 | "el.exe" | C:\Users\admin\AppData\Local\Temp\el.exe | dive.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4676 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | dive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4888 | "el.exe" | C:\Users\admin\AppData\Local\Temp\el.exe | dive.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6016 | "el.exe" | C:\Users\admin\AppData\Local\Temp\el.exe | dive.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6124 | "el.exe" | C:\Users\admin\AppData\Local\Temp\el.exe | dive.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
4 024
Read events
4 010
Write events
14
Delete events
0
Modification events
| (PID) Process: | (2044) dive.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dive_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2044) dive.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dive_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2044) dive.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dive_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2044) dive.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dive_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2044) dive.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dive_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2044) dive.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dive_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2044) dive.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dive_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2044) dive.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dive_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2044) dive.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dive_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2044) dive.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dive_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
93
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1232 | el.exe | C:\Users\admin\AppData\Local\Temp\rifaien2-scU2V4e3glL5AWmF.exe | executable | |
MD5:0BB15E37F5360755C15F9990C171BB73 | SHA256:A6F04A0AC0C7B1586818CADF944A325E4C3A520B3689AB0E9FED8C358D7F6A7B | |||
| 6772 | el.exe | C:\Users\admin\AppData\Local\Temp\rifaien2-Wxyf40F2AAwyhADH.exe | executable | |
MD5:222A7159D428396AC9662C3734A35DF7 | SHA256:54FC9EAE8EF00E41EFECD3B3133F75773F1B91D927F21532EF4081AE120EFB1C | |||
| 4888 | el.exe | C:\Users\admin\AppData\Local\Temp\rifaien2-mnffdyGq84KQU2vn.exe | executable | |
MD5:496D798695BC6A2AB5AC8A265CD30304 | SHA256:516390E5D748A4D4E09539EE9B2FBA29155869E1EC9E5F772384A6E83E638DD1 | |||
| 1232 | el.exe | C:\Users\admin\AppData\Local\Temp\rifaien2-DJWfnpo87PtRB9rd.exe | executable | |
MD5:904EF8694DD71D6652DF395651670A79 | SHA256:44CCB7033C1E0BAAD1C28C58B1504041B027648A84887D606BA43C7565D9FA3F | |||
| 6016 | el.exe | C:\Users\admin\AppData\Local\Temp\rifaien2-vM04pNUXnr0S4sK8.exe | executable | |
MD5:7FADB07CBDF3E862B1EDA3B68373594F | SHA256:1D84AC96C5D32944B2436664478FF96602A7722C92C910DAB563F29C69C72577 | |||
| 4232 | el.exe | C:\Users\admin\AppData\Local\Temp\rifaien2-2tVL7RnmZfbzvuz5.exe | executable | |
MD5:326AE26C49463B8313282A2D5BBE78E4 | SHA256:DFA1EA17141114233D282DCFC14D0BC87DAE9751A266F8E7E0EF8D7FA8567CD4 | |||
| 3844 | el.exe | C:\Users\admin\AppData\Local\Temp\rifaien2-1Uae4R95J9hO5oD0.exe | executable | |
MD5:04319DBE11D46598BB3CFC789E2AA626 | SHA256:2E689C6FC37883F373D7AE7D5355CC162259CC6F912D29B79E3DC1148F768E98 | |||
| 6260 | el.exe | C:\Users\admin\AppData\Local\Temp\rifaien2-FQkwn4v7kR3ZeJ1u.exe | executable | |
MD5:83F9BF736229CA4661A88AA9039DCD48 | SHA256:12D505B74DE42FB679126879C011EF64AFFA81F3BDE2BFEC3E7C924922AF02D6 | |||
| 6124 | el.exe | C:\Users\admin\AppData\Local\Temp\rifaien2-LllTO8RXh9ricWK2.exe | executable | |
MD5:2FC96A7BA32CF42B94E34AA155869B01 | SHA256:AB5D872C13C65ECE7969D5DA91274A2DFAEE1E273282638191F20291B52DA710 | |||
| 6980 | el.exe | C:\Users\admin\AppData\Local\Temp\rifaien2-mEFjJniuOEqeRo3j.exe | executable | |
MD5:489C62B914773B144643076C8D84C807 | SHA256:3E6581F2915FEC6B5D6B2D312E675B1D46C6B4BAE31852FA30346810B254693D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
135
DNS requests
26
Threats
184
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1352 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1352 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2596 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
5556 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7052 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
472 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
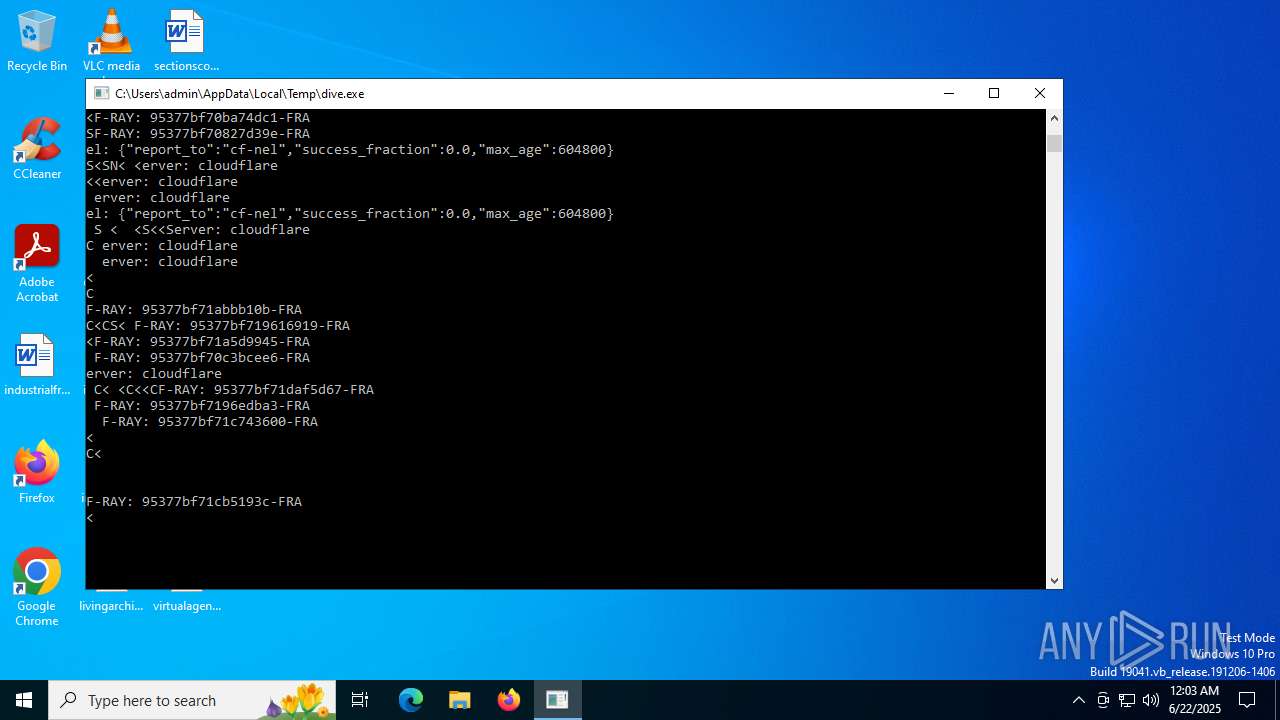
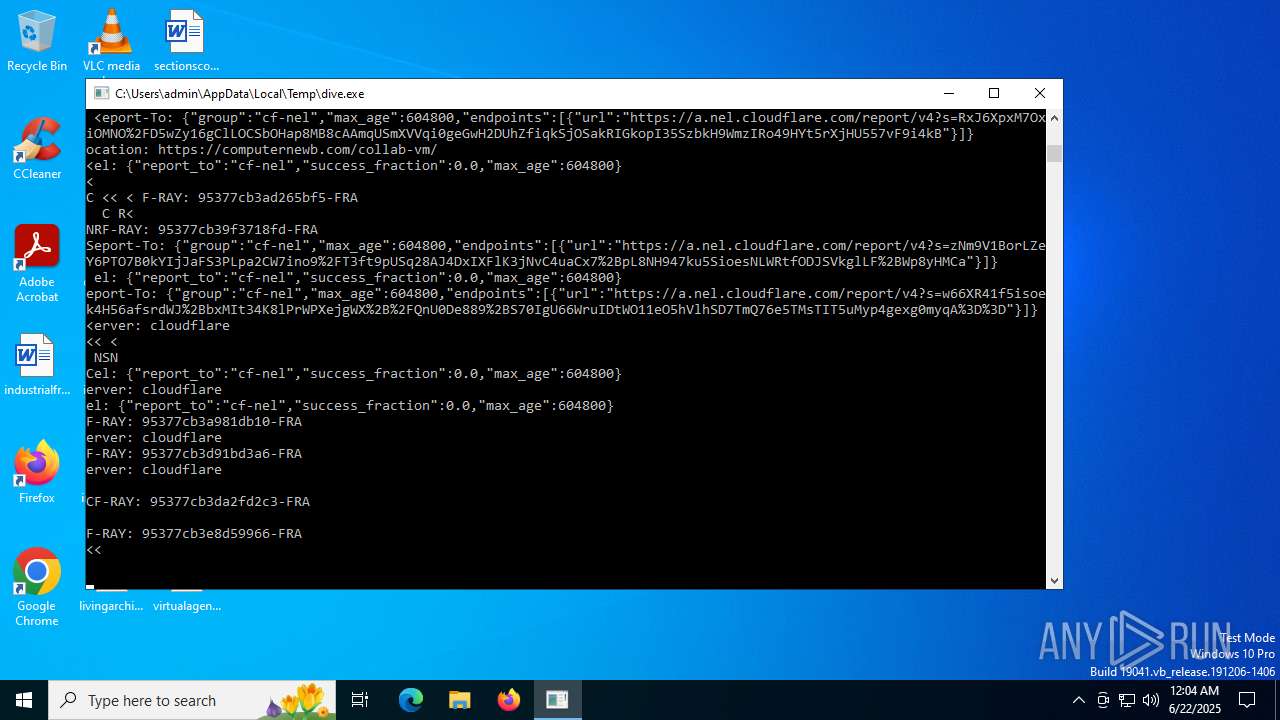
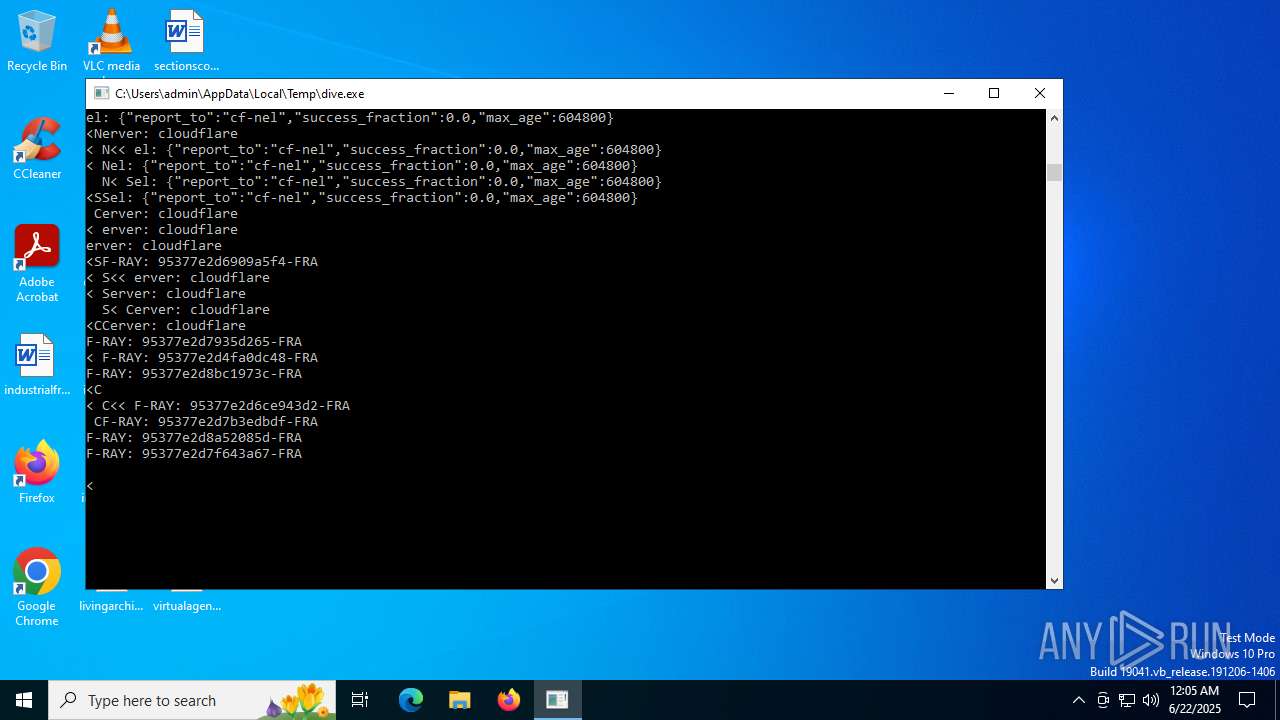
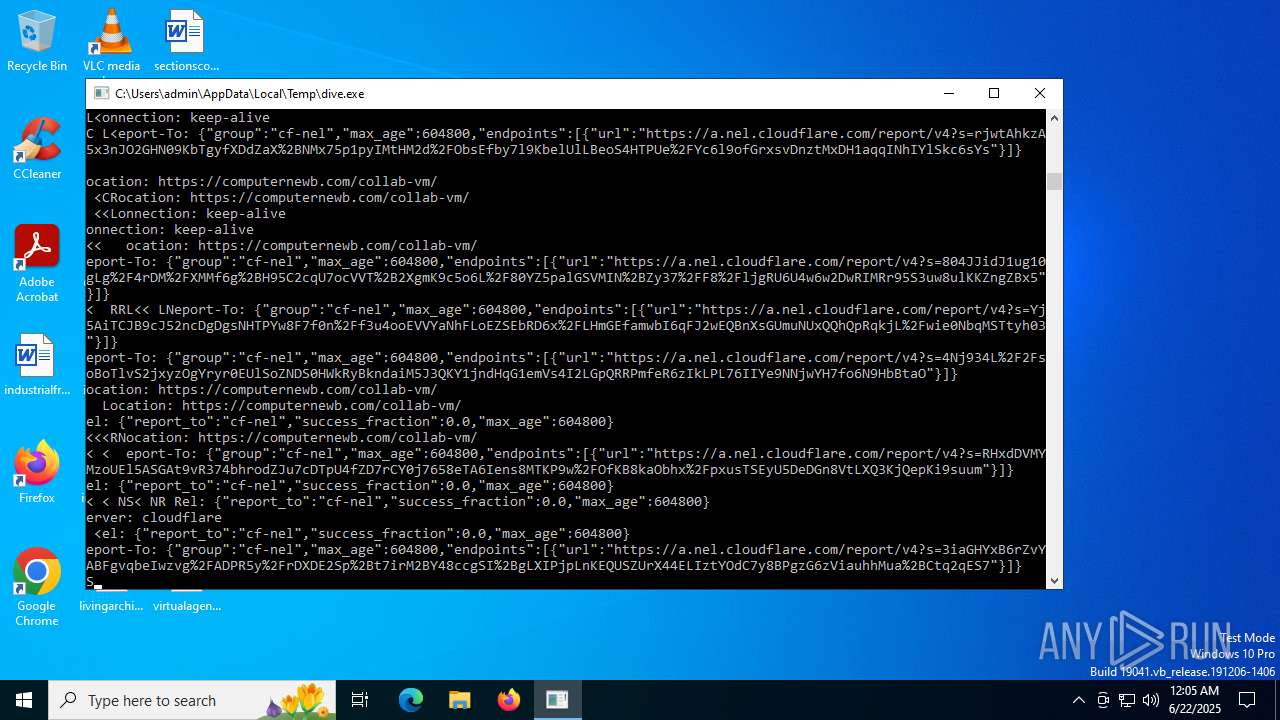
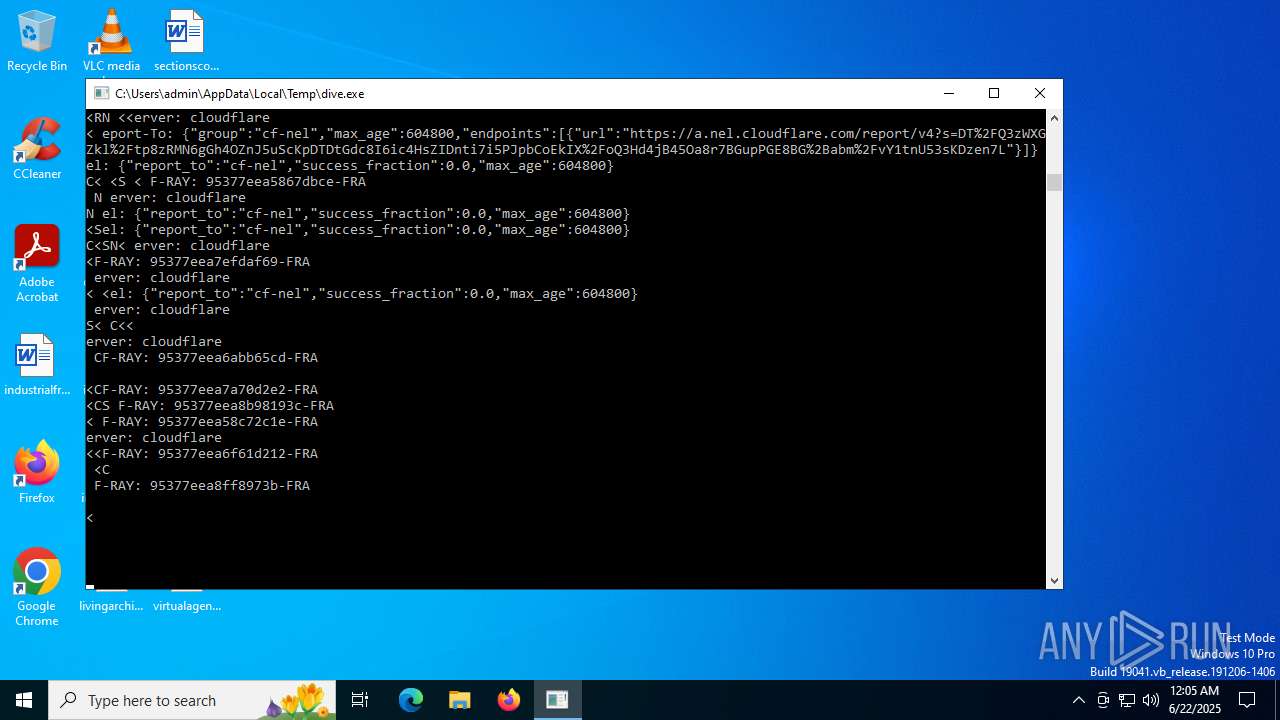
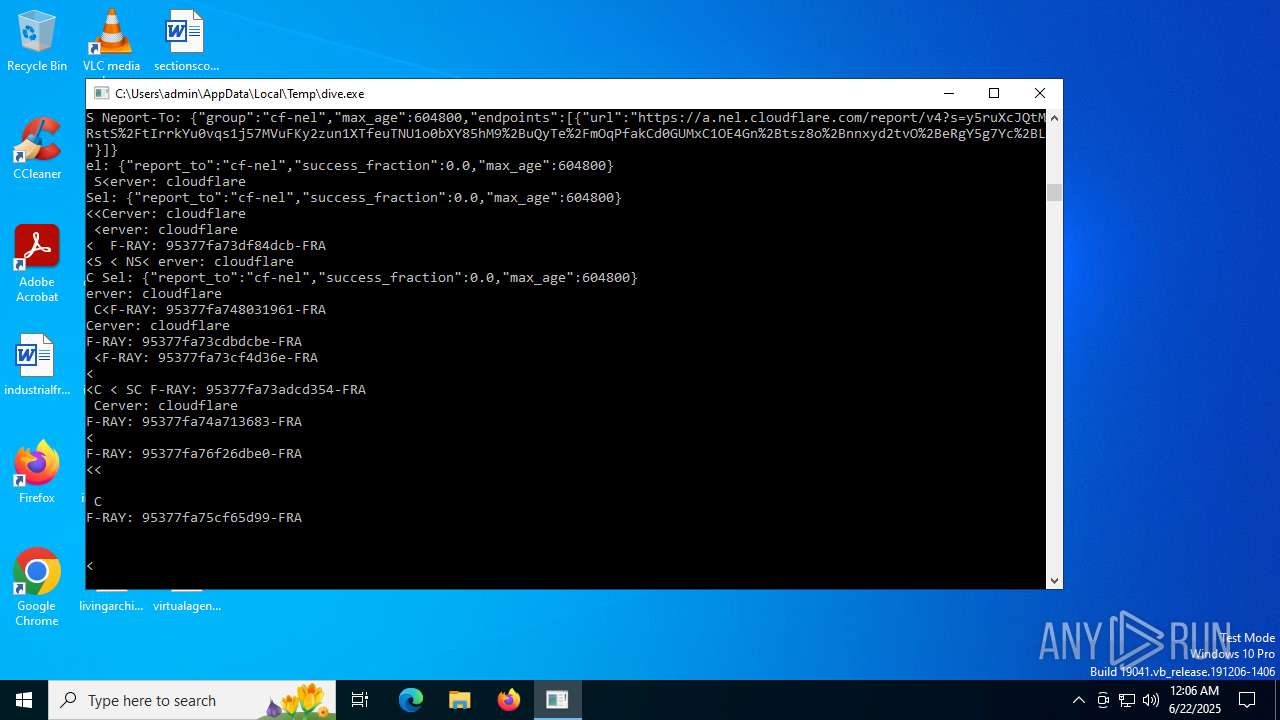
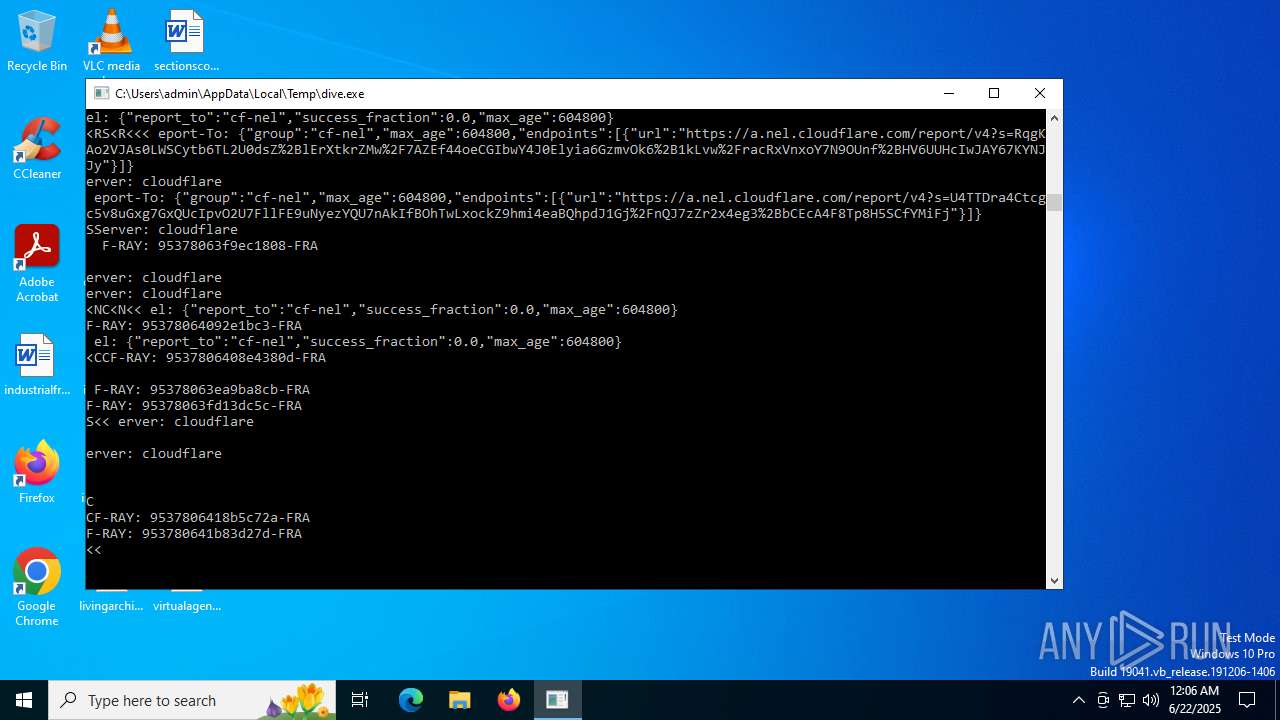
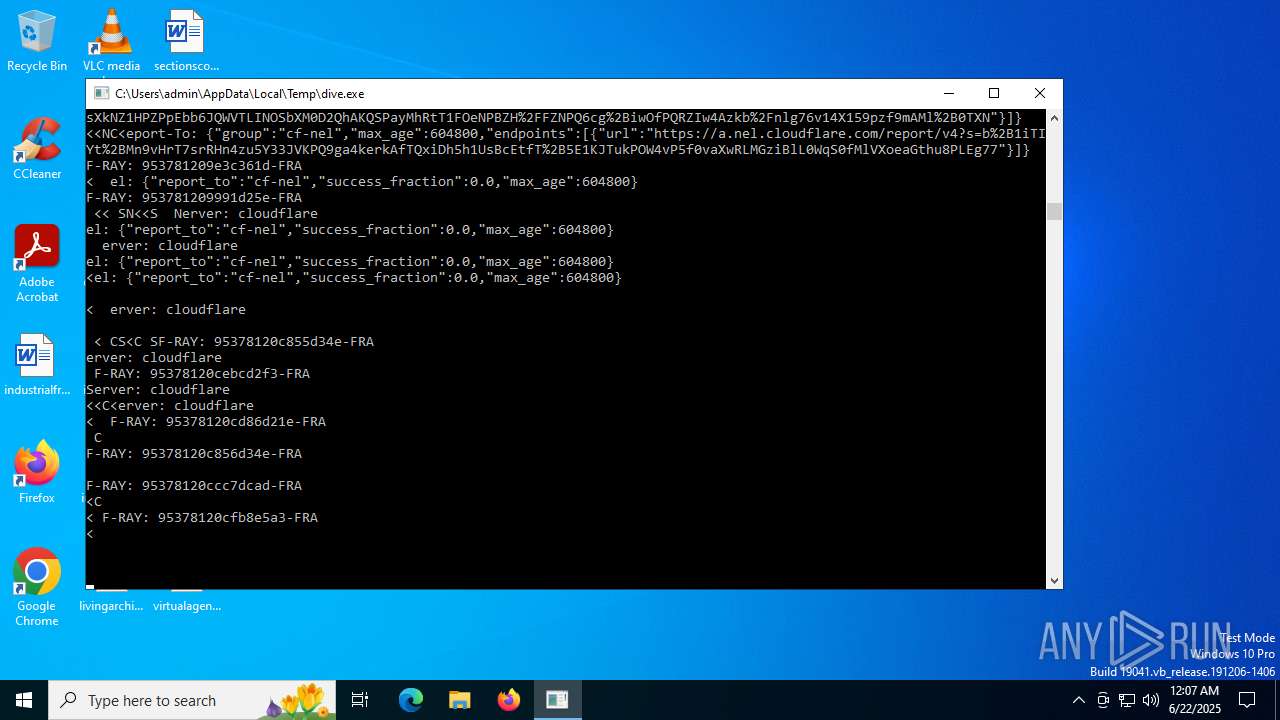
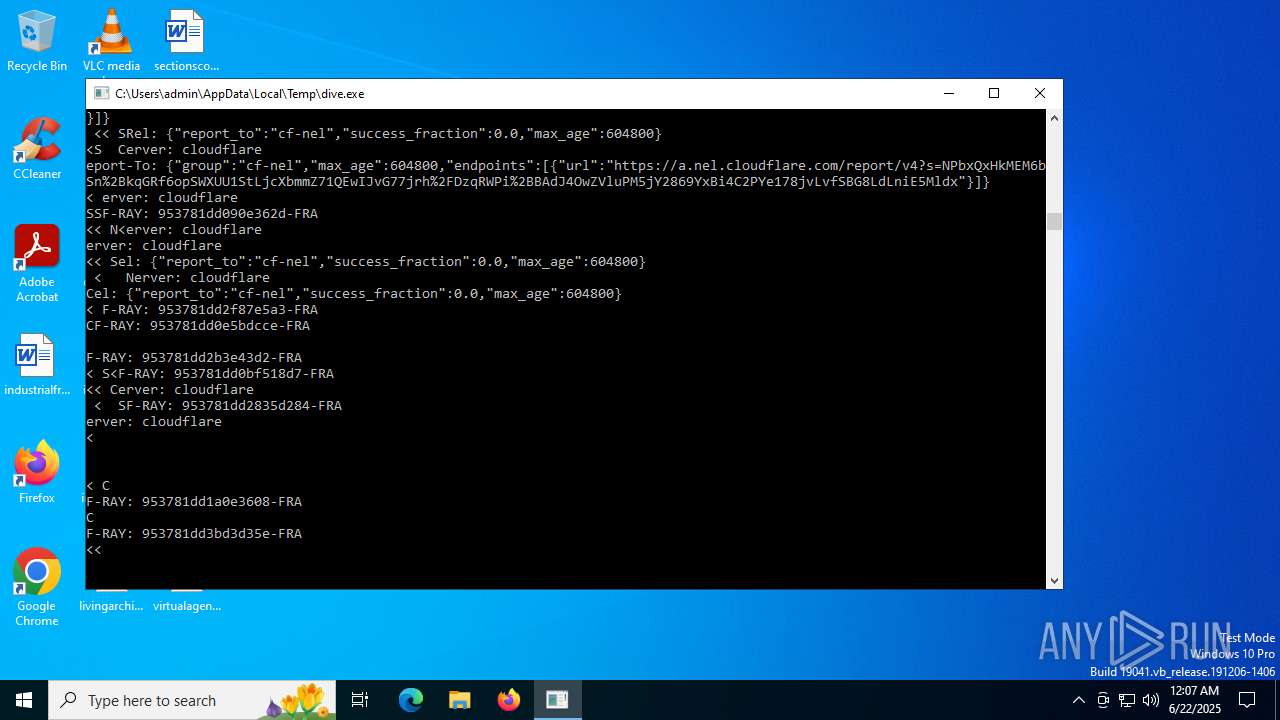
2044 | dive.exe | 104.26.2.158:443 | computernewb.com | CLOUDFLARENET | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
computernewb.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
wecan.hasthe.technology |
| malicious |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6124 | el.exe | Misc activity | ET INFO Generic HTTP EXE Upload Outbound |
6124 | el.exe | Misc activity | ET INFO Generic HTTP EXE Upload Outbound |
6124 | el.exe | Misc activity | ET INFO Generic HTTP EXE Upload Outbound |
6124 | el.exe | Misc activity | ET INFO Generic HTTP EXE Upload Outbound |
6124 | el.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Snojan malware uploading .exe |
6124 | el.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Snojan malware uploading .exe |
6124 | el.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Snojan malware uploading .exe |
6124 | el.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Snojan malware uploading .exe |
6124 | el.exe | Misc activity | ET INFO Generic HTTP EXE Upload Outbound |
6124 | el.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Snojan malware uploading .exe |