| File name: | 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer |
| Full analysis: | https://app.any.run/tasks/ac3231a7-43d8-49ab-96a9-3435baeabdb7 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 12:06:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 35AA050BA716938A589CD21B1EC4E6FA |
| SHA1: | 0EB8035EF7EFFF14C8FF0B1703B1C538E1AAD565 |
| SHA256: | 3CB491E19ED76BAA9E984B7F69C074F8F44C6194770DE34A4C88251FC57BC8DF |
| SSDEEP: | 24576:aLN9pggkHLWqnivnuhHqaEVYSJJuXjmVCmkn:aLN9SgkHLWqnivnuhHqvVYSruXjmVCmm |
MALICIOUS
Executing a file with an untrusted certificate
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 4676)
- AacSetup.exe (PID: 5456)
- AacSetup.exe (PID: 6656)
- AacSetup.exe (PID: 1896)
- AacSetup.exe (PID: 4012)
Changes the autorun value in the registry
- AacSetup.exe (PID: 5456)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 6536)
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 4676)
- AacSetup.exe (PID: 5456)
- AacSetup.exe (PID: 4012)
Reads security settings of Internet Explorer
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 4676)
Starts itself from another location
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 4676)
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 6536)
Searches for installed software
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 4676)
- AacSetup.exe (PID: 6656)
- AacSetup.exe (PID: 4012)
Creates a software uninstall entry
- AacSetup.exe (PID: 5456)
Application launched itself
- AacSetup.exe (PID: 6656)
- AacSetup.exe (PID: 1896)
INFO
The sample compiled with english language support
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 6536)
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 4676)
- AacSetup.exe (PID: 5456)
- AacSetup.exe (PID: 4012)
Create files in a temporary directory
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 6536)
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 4676)
- AacSetup.exe (PID: 4012)
Checks supported languages
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 4676)
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 6536)
- AacSetup.exe (PID: 5456)
- AacSetup.exe (PID: 1896)
- AacSetup.exe (PID: 6656)
- AacSetup.exe (PID: 4012)
Reads the computer name
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 4676)
- AacSetup.exe (PID: 5456)
- AacSetup.exe (PID: 4012)
Process checks computer location settings
- 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe (PID: 4676)
Creates files in the program directory
- AacSetup.exe (PID: 5456)
Launching a file from a Registry key
- AacSetup.exe (PID: 5456)
Manual execution by a user
- AacSetup.exe (PID: 6656)
Checks proxy server information
- slui.exe (PID: 4112)
Reads the software policy settings
- slui.exe (PID: 4112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:17 05:33:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 299008 |
| InitializedDataSize: | 161792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2df71 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
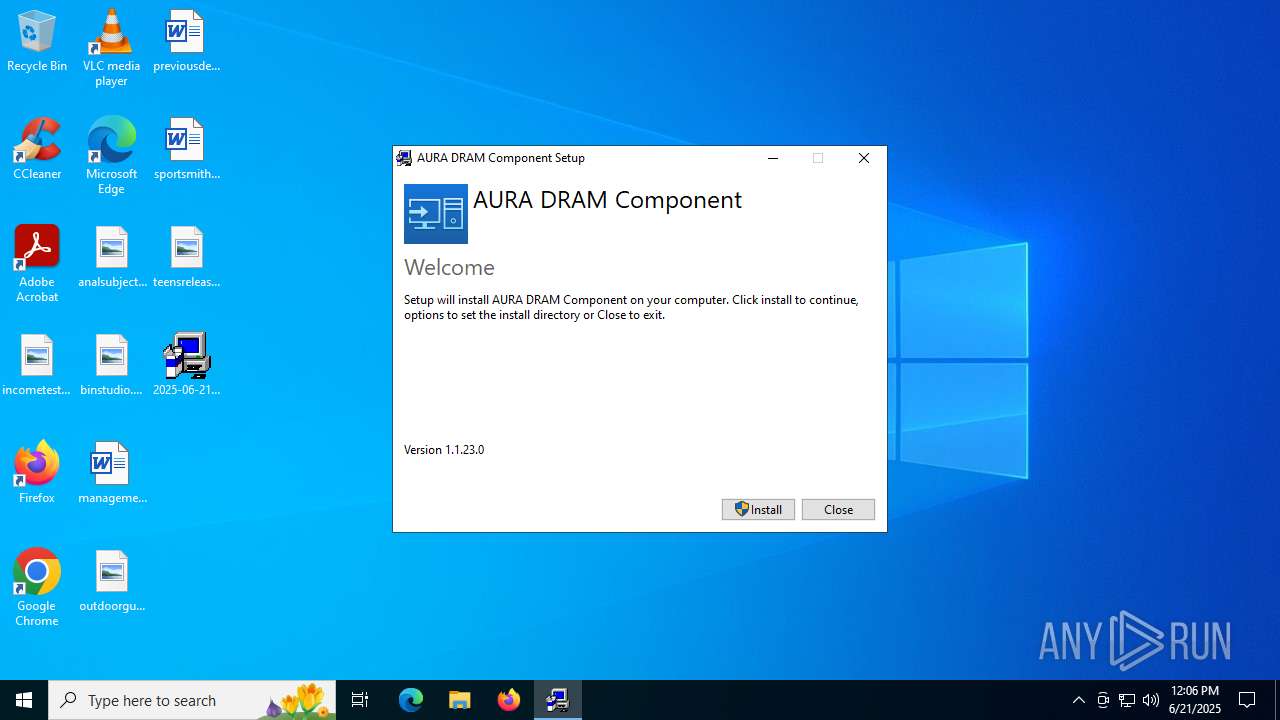
| FileVersionNumber: | 1.1.23.0 |
| ProductVersionNumber: | 1.1.23.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | ASUS |
| FileDescription: | AURA DRAM Component |
| FileVersion: | 1.1.23 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) ASUS. All rights reserved. |
| OriginalFileName: | AacSetup.exe |
| ProductName: | AURA DRAM Component |
| ProductVersion: | 1.1.23 |
Total processes
143
Monitored processes
7
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
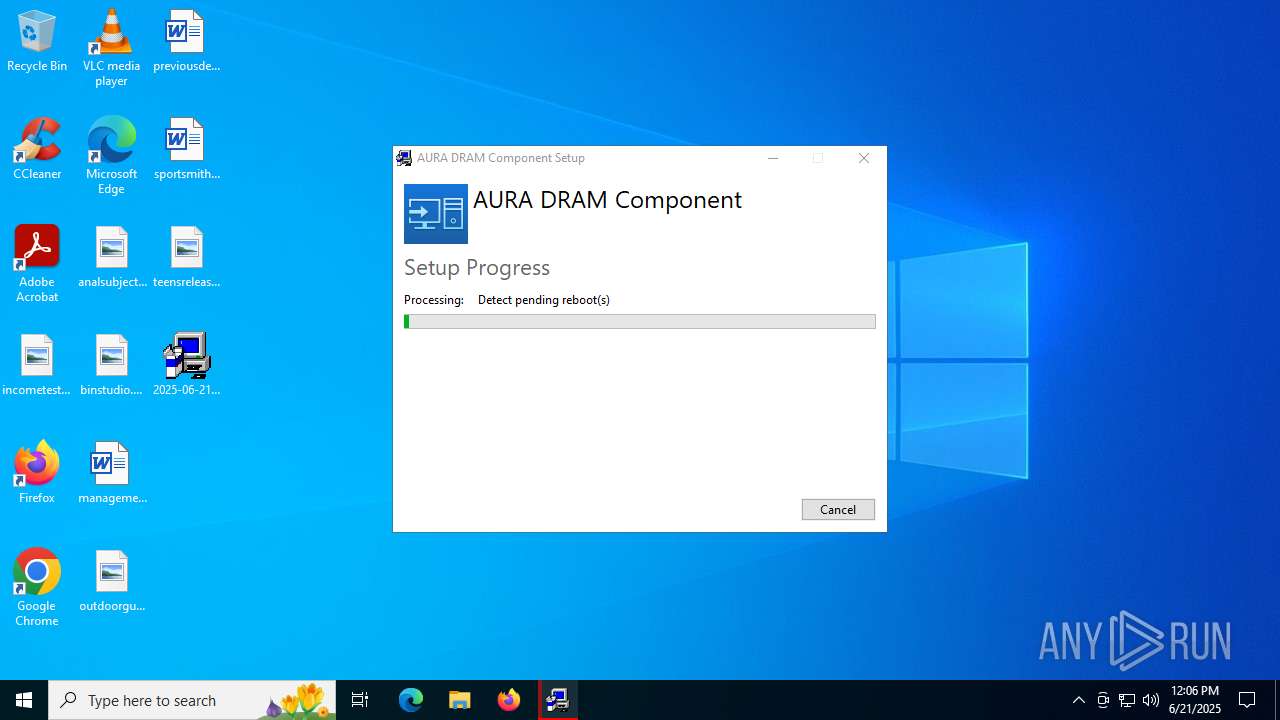
| 1896 | "C:\ProgramData\Package Cache\{179f415f-2ff3-4db1-bcc1-d5730f746db8}\AacSetup.exe" /burn.log.append "C:\Users\admin\AppData\Local\Temp\AURA DRAM Component_20250621120634.log" | C:\ProgramData\Package Cache\{179f415f-2ff3-4db1-bcc1-d5730f746db8}\AacSetup.exe | — | AacSetup.exe | |||||||||||
User: admin Company: ASUS Integrity Level: MEDIUM Description: AURA DRAM Component Exit code: 2 Version: 1.1.23 Modules
| |||||||||||||||
| 4012 | "C:\ProgramData\Package Cache\{179f415f-2ff3-4db1-bcc1-d5730f746db8}\AacSetup.exe" -burn.clean.room="C:\ProgramData\Package Cache\{179f415f-2ff3-4db1-bcc1-d5730f746db8}\AacSetup.exe" -burn.filehandle.attached=520 -burn.filehandle.self=548 /burn.log.append "C:\Users\admin\AppData\Local\Temp\AURA DRAM Component_20250621120634.log" | C:\ProgramData\Package Cache\{179f415f-2ff3-4db1-bcc1-d5730f746db8}\AacSetup.exe | AacSetup.exe | ||||||||||||
User: admin Company: ASUS Integrity Level: MEDIUM Description: AURA DRAM Component Exit code: 2 Version: 1.1.23 Modules
| |||||||||||||||
| 4112 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4676 | "C:\Users\admin\AppData\Local\Temp\{8EA0550D-2E10-453A-A7BE-8AC9544FA45C}\.cr\2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe" -burn.clean.room="C:\Users\admin\Desktop\2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe" -burn.filehandle.attached=580 -burn.filehandle.self=588 | C:\Users\admin\AppData\Local\Temp\{8EA0550D-2E10-453A-A7BE-8AC9544FA45C}\.cr\2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | ||||||||||||
User: admin Company: ASUS Integrity Level: MEDIUM Description: AURA DRAM Component Exit code: 1 Version: 1.1.23 Modules
| |||||||||||||||
| 5456 | "C:\Users\admin\AppData\Local\Temp\{D44E989D-E48F-4E9A-9E3B-36D716FA7FBF}\.be\AacSetup.exe" -q -burn.elevated BurnPipe.{C5868CB3-706A-4B0C-ABC7-C5A98FB86D81} {B2D58863-6DDE-4F4C-A476-CB464299D35B} 4676 | C:\Users\admin\AppData\Local\Temp\{D44E989D-E48F-4E9A-9E3B-36D716FA7FBF}\.be\AacSetup.exe | 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | ||||||||||||
User: admin Company: ASUS Integrity Level: HIGH Description: AURA DRAM Component Exit code: 1 Version: 1.1.23 Modules
| |||||||||||||||
| 6536 | "C:\Users\admin\Desktop\2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe" | C:\Users\admin\Desktop\2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | explorer.exe | ||||||||||||
User: admin Company: ASUS Integrity Level: MEDIUM Description: AURA DRAM Component Exit code: 1 Version: 1.1.23 Modules
| |||||||||||||||
| 6656 | "C:\ProgramData\Package Cache\{179f415f-2ff3-4db1-bcc1-d5730f746db8}\AacSetup.exe" /burn.runonce | C:\ProgramData\Package Cache\{179f415f-2ff3-4db1-bcc1-d5730f746db8}\AacSetup.exe | — | explorer.exe | |||||||||||
User: admin Company: ASUS Integrity Level: MEDIUM Description: AURA DRAM Component Exit code: 0 Version: 1.1.23 Modules
| |||||||||||||||
Total events
4 420
Read events
4 387
Write events
26
Delete events
7
Modification events
| (PID) Process: | (5456) AacSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{179f415f-2ff3-4db1-bcc1-d5730f746db8} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\ProgramData\Package Cache\{179f415f-2ff3-4db1-bcc1-d5730f746db8}\AacSetup.exe | |||
| (PID) Process: | (5456) AacSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{179f415f-2ff3-4db1-bcc1-d5730f746db8} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {309FDD32-53A2-45FF-9275-D5414ED0EEDC} | |||
| (PID) Process: | (5456) AacSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{179f415f-2ff3-4db1-bcc1-d5730f746db8} |
| Operation: | write | Name: | BundleAddonCode |
Value: | |||
| (PID) Process: | (5456) AacSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{179f415f-2ff3-4db1-bcc1-d5730f746db8} |
| Operation: | write | Name: | BundleDetectCode |
Value: | |||
| (PID) Process: | (5456) AacSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{179f415f-2ff3-4db1-bcc1-d5730f746db8} |
| Operation: | write | Name: | BundlePatchCode |
Value: | |||
| (PID) Process: | (5456) AacSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{179f415f-2ff3-4db1-bcc1-d5730f746db8} |
| Operation: | write | Name: | BundleVersion |
Value: 1.1.23.0 | |||
| (PID) Process: | (5456) AacSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{179f415f-2ff3-4db1-bcc1-d5730f746db8} |
| Operation: | write | Name: | VersionMajor |
Value: 1 | |||
| (PID) Process: | (5456) AacSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{179f415f-2ff3-4db1-bcc1-d5730f746db8} |
| Operation: | write | Name: | VersionMinor |
Value: 1 | |||
| (PID) Process: | (5456) AacSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{179f415f-2ff3-4db1-bcc1-d5730f746db8} |
| Operation: | write | Name: | BundleProviderKey |
Value: {179f415f-2ff3-4db1-bcc1-d5730f746db8} | |||
| (PID) Process: | (5456) AacSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{179f415f-2ff3-4db1-bcc1-d5730f746db8} |
| Operation: | write | Name: | BundleTag |
Value: | |||
Executable files
7
Suspicious files
1
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4676 | 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{D44E989D-E48F-4E9A-9E3B-36D716FA7FBF}\.ba\wixstdba.dll | executable | |
MD5:FE7E0BD53F52E6630473C31299A49FDD | SHA256:2BEA14D70943A42D344E09B7C9DE5562FA7E109946E1C615DD584DA30D06CC80 | |||
| 4676 | 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{D44E989D-E48F-4E9A-9E3B-36D716FA7FBF}\.ba\logo.png | image | |
MD5:80DF19F22C1D266C06ACE7C8B9831762 | SHA256:E8E37845754F62B6426CE39CBDA1DB032856BD551E6D39BBACA06AA7C44625C4 | |||
| 6536 | 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{8EA0550D-2E10-453A-A7BE-8AC9544FA45C}\.cr\2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | executable | |
MD5:35AA050BA716938A589CD21B1EC4E6FA | SHA256:3CB491E19ED76BAA9E984B7F69C074F8F44C6194770DE34A4C88251FC57BC8DF | |||
| 4676 | 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{D44E989D-E48F-4E9A-9E3B-36D716FA7FBF}\.ba\thm.wxl | xml | |
MD5:FC0DB4142556D3F38B0744A12F5F9D3D | SHA256:8FBEB7F0B546D394D99B49D678D516402E8F54E5DEA590CC91733F502F288019 | |||
| 5456 | AacSetup.exe | C:\ProgramData\Package Cache\{179f415f-2ff3-4db1-bcc1-d5730f746db8}\state.rsm | binary | |
MD5:57CC2C19F23D2407C2D52E2BC5B28C84 | SHA256:268E2E0A1D5450081E691CCCDDC073AF35E71E38077E4D302B3F99FEED2E6056 | |||
| 4676 | 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{D44E989D-E48F-4E9A-9E3B-36D716FA7FBF}\.ba\BootstrapperApplicationData.xml | xml | |
MD5:7A15C61B3863A56296D1065C37B9FB78 | SHA256:D5544677AA6C16EC4C97545D3AE4709E13D10D4C9B48737843B2A6D78401E54B | |||
| 4676 | 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{D44E989D-E48F-4E9A-9E3B-36D716FA7FBF}\.be\AacSetup.exe | executable | |
MD5:35AA050BA716938A589CD21B1EC4E6FA | SHA256:3CB491E19ED76BAA9E984B7F69C074F8F44C6194770DE34A4C88251FC57BC8DF | |||
| 4676 | 2025-06-21_35aa050ba716938a589cd21b1ec4e6fa_amadey_black-basta_coinminer_elex_hijackloader_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{D44E989D-E48F-4E9A-9E3B-36D716FA7FBF}\09BBCC2C0A9BF6C5E3943C822C6F1D87337A4F73 | executable | |
MD5:35AA050BA716938A589CD21B1EC4E6FA | SHA256:3CB491E19ED76BAA9E984B7F69C074F8F44C6194770DE34A4C88251FC57BC8DF | |||
| 5456 | AacSetup.exe | C:\ProgramData\Package Cache\{179f415f-2ff3-4db1-bcc1-d5730f746db8}\AacSetup.exe | executable | |
MD5:35AA050BA716938A589CD21B1EC4E6FA | SHA256:3CB491E19ED76BAA9E984B7F69C074F8F44C6194770DE34A4C88251FC57BC8DF | |||
| 5456 | AacSetup.exe | C:\Users\admin\AppData\Local\Temp\DEL877F.tmp | executable | |
MD5:35AA050BA716938A589CD21B1EC4E6FA | SHA256:3CB491E19ED76BAA9E984B7F69C074F8F44C6194770DE34A4C88251FC57BC8DF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
44
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 20.190.159.128:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
6776 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
6776 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.159.0:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4984 | RUXIMICS.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
6776 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4984 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4984 | RUXIMICS.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |