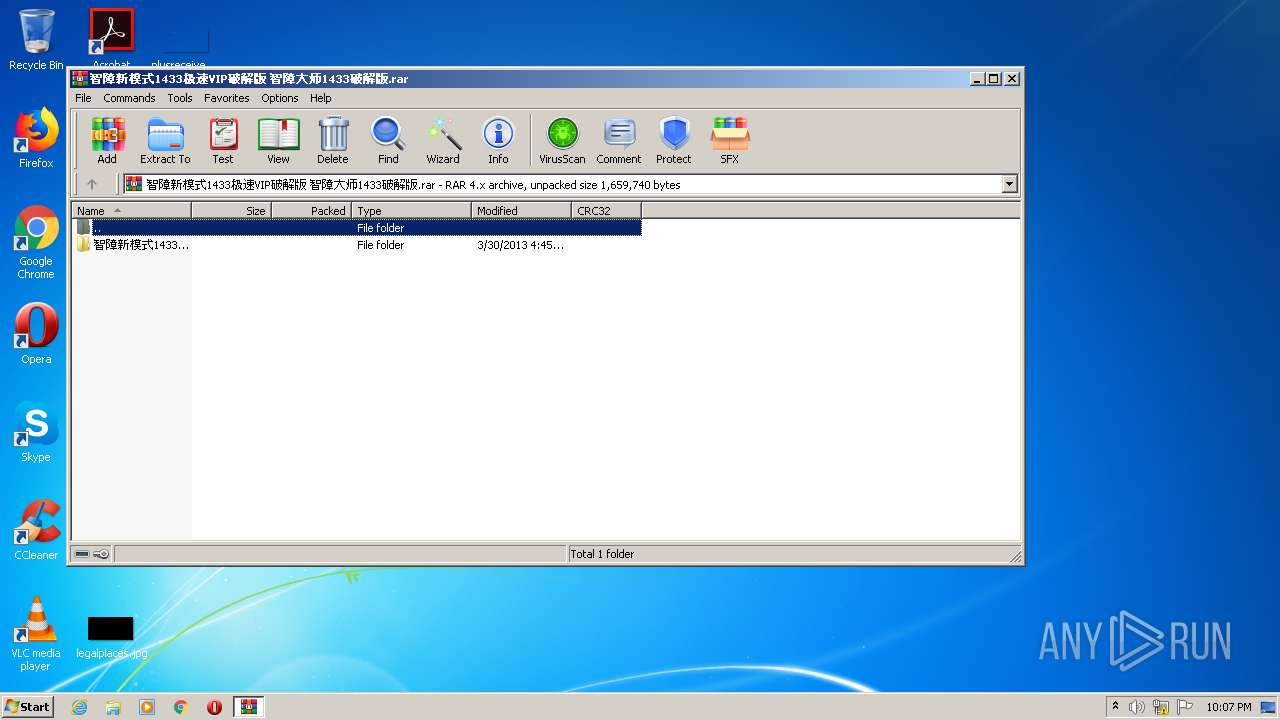
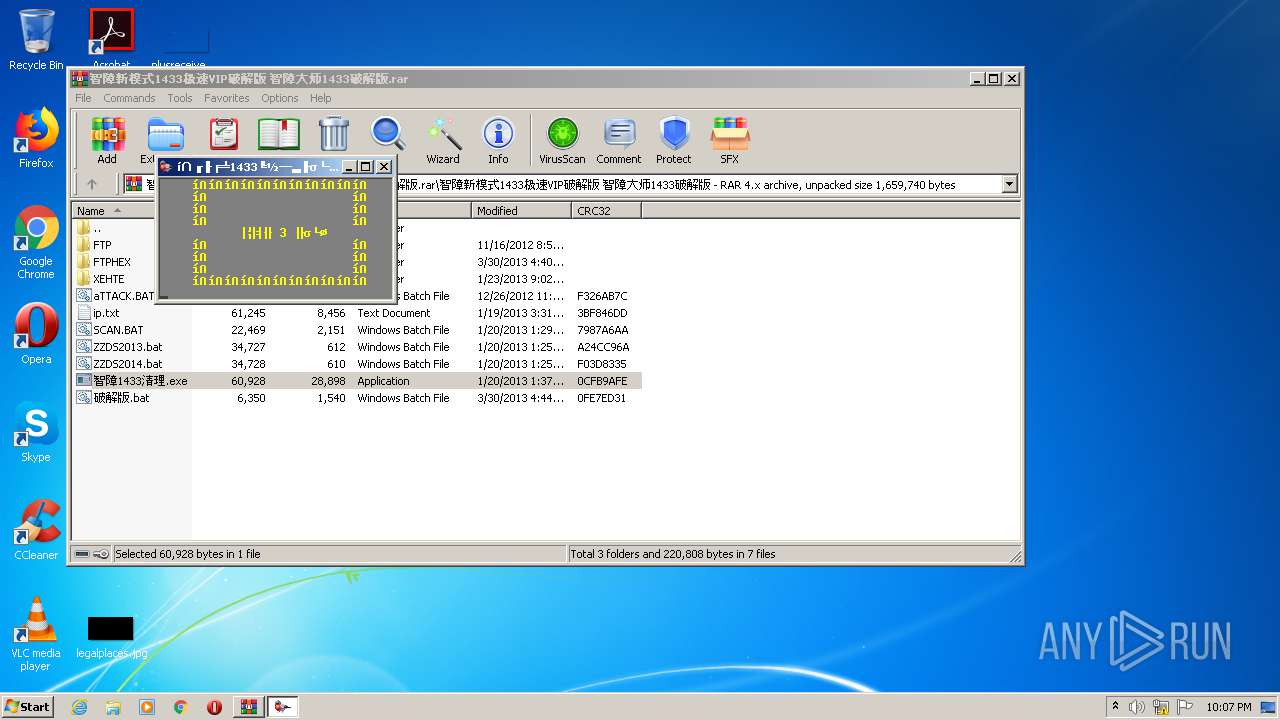
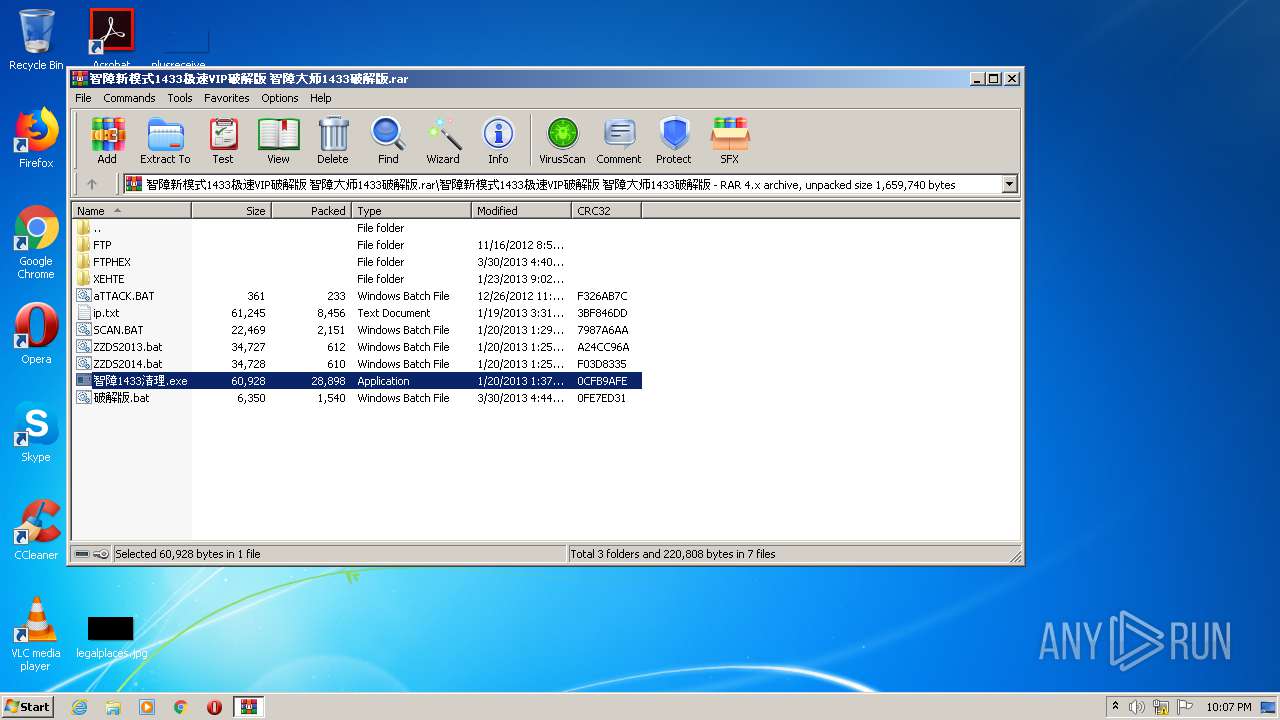
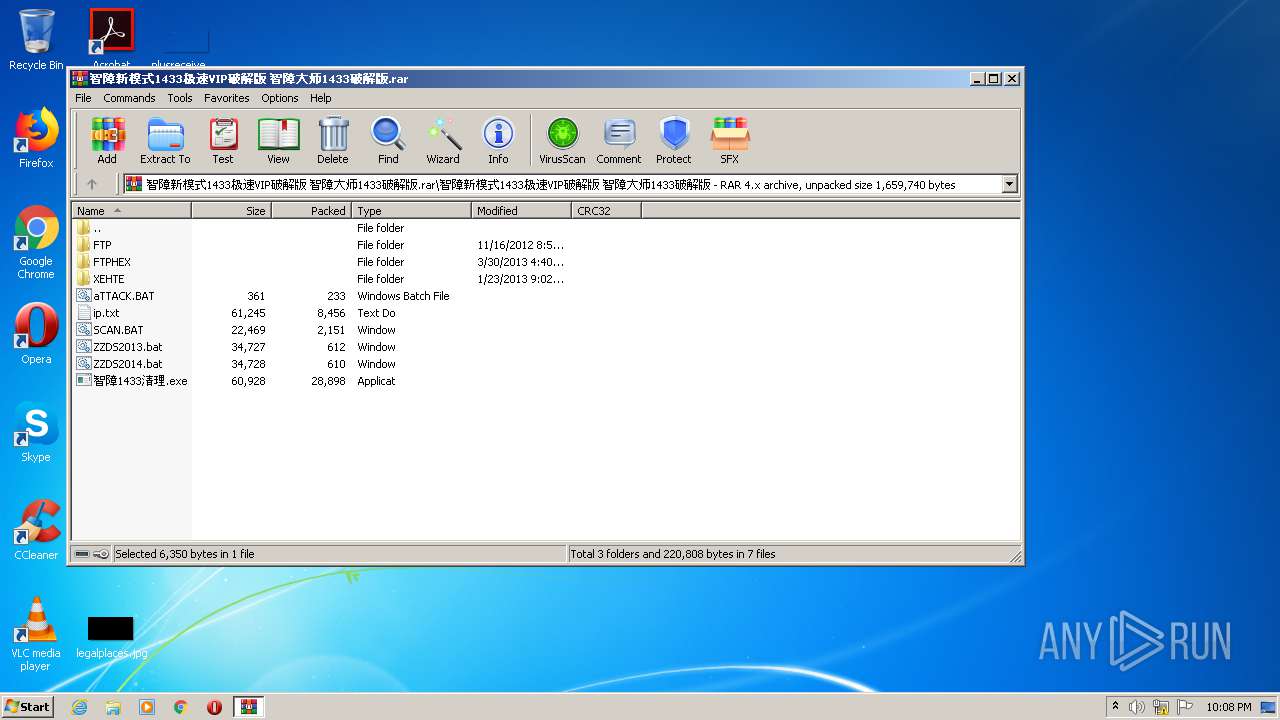
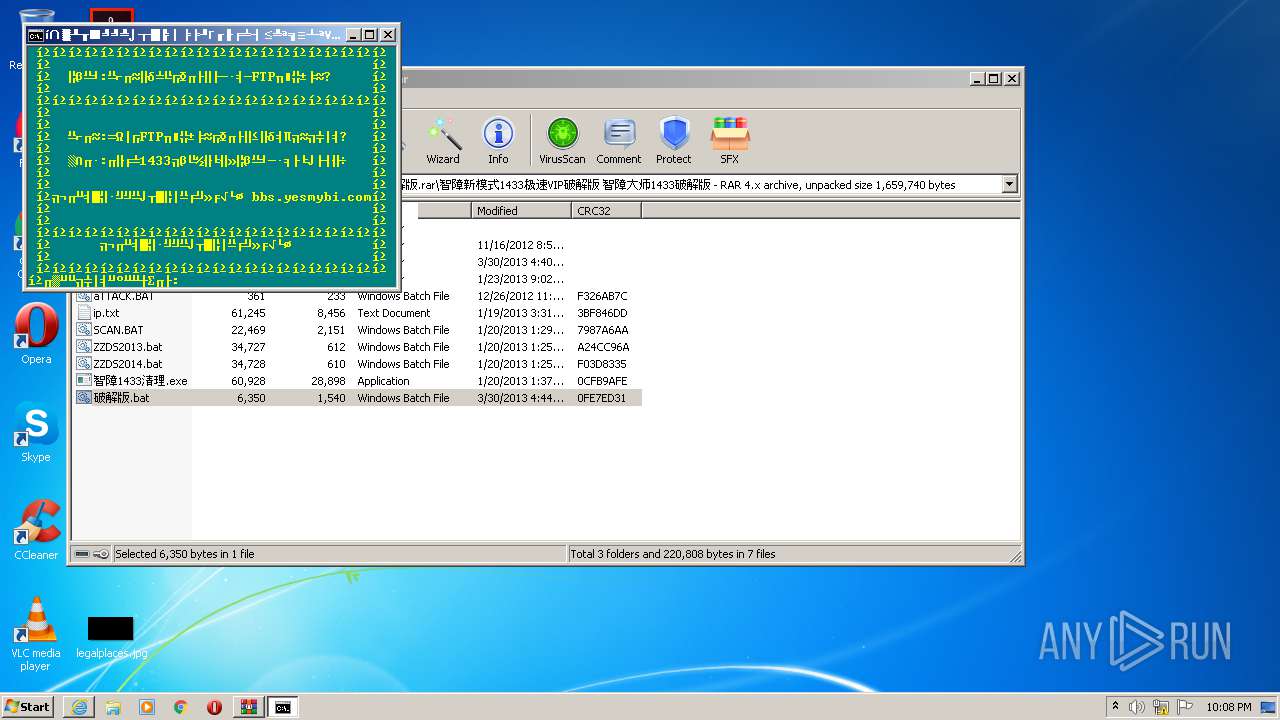
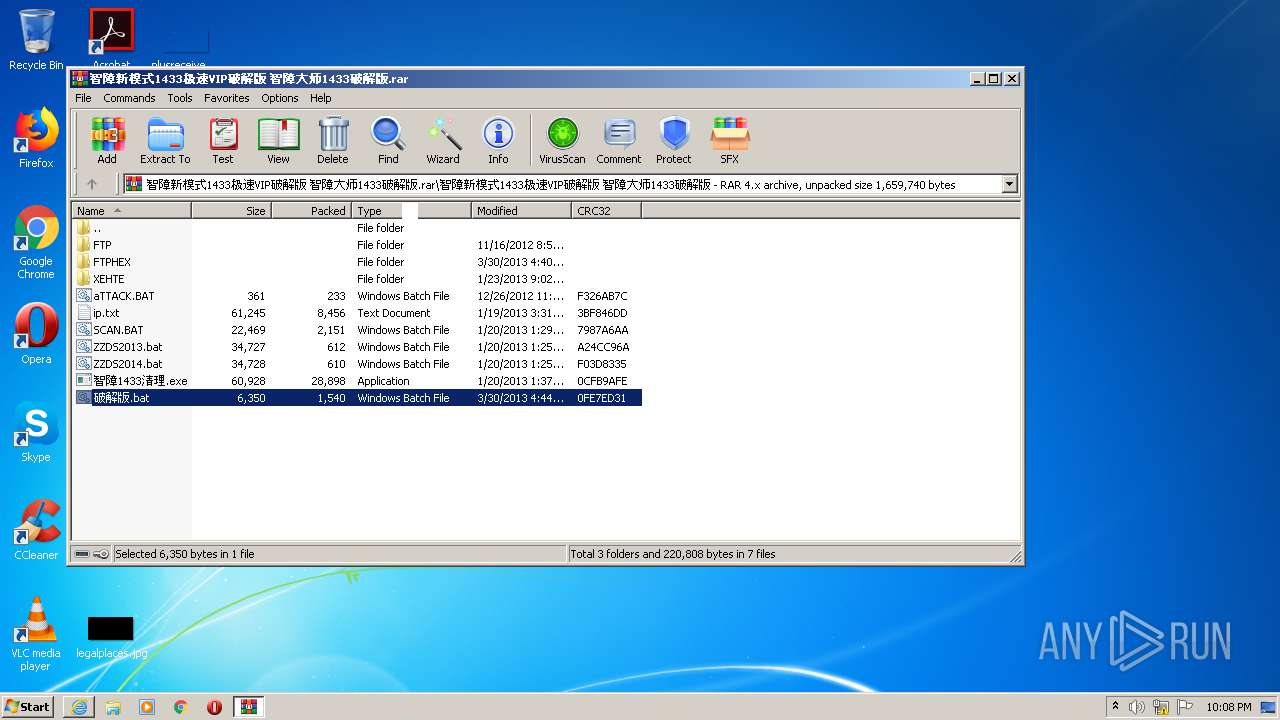
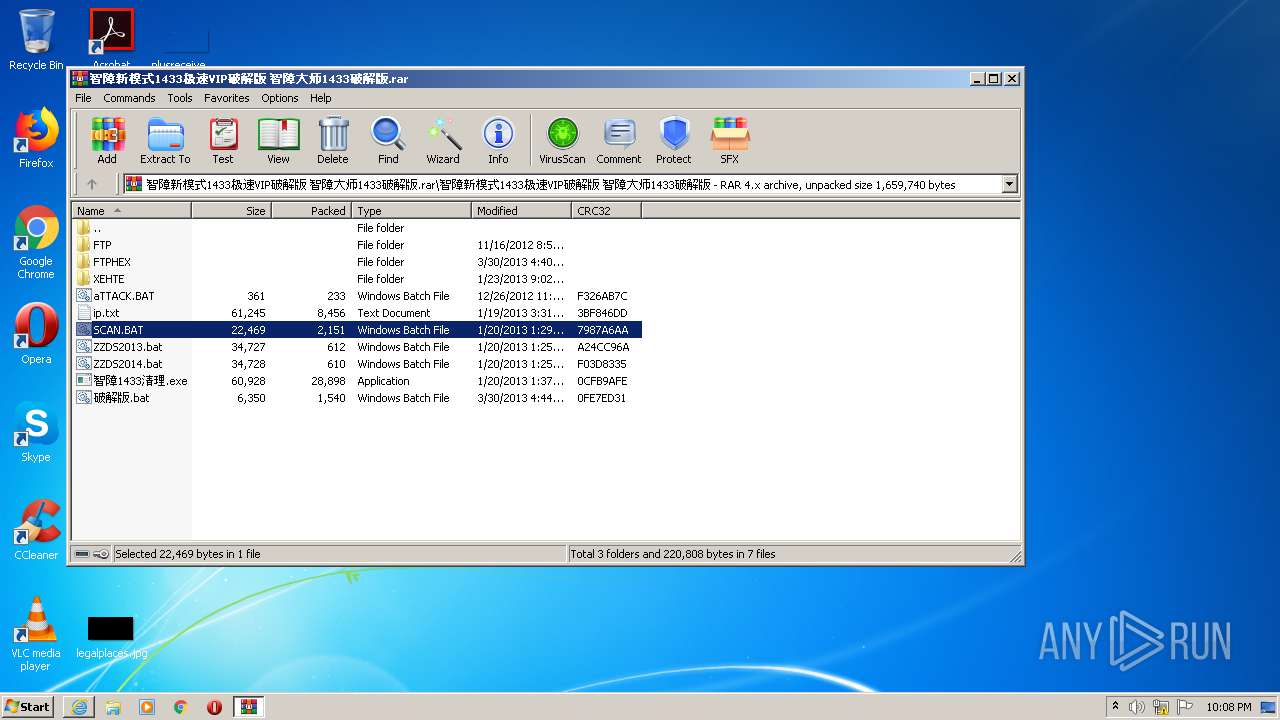
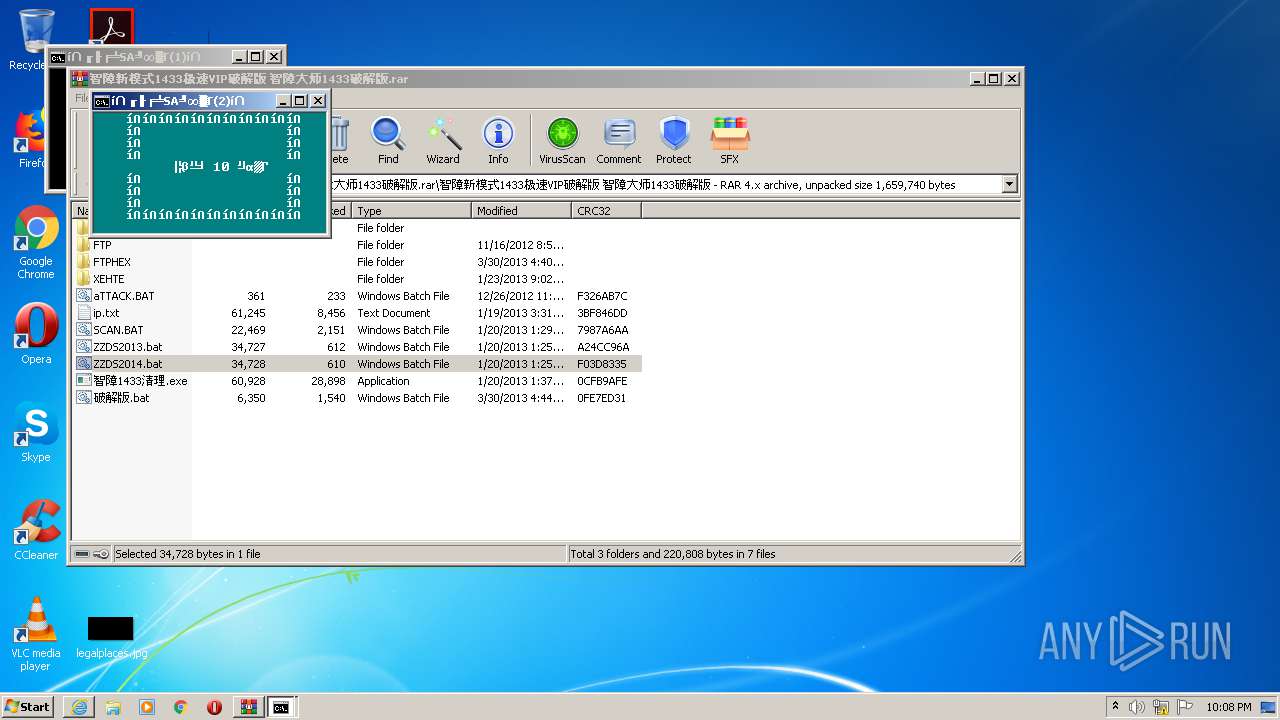
| File name: | 智障新模式1433极速VIP破解版 智障大师1433破解版.rar |
| Full analysis: | https://app.any.run/tasks/067ff1b8-f8a4-4d53-ac36-8dbd9516acf2 |
| Verdict: | Malicious activity |
| Analysis date: | April 02, 2021, 21:07:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | C46D9CBA4E3A5171277ABEFEEAA014B8 |
| SHA1: | AD9B0CD603B54FC0F84B3CD6FC66ADC81904CFCA |
| SHA256: | 3C9FEDF9E86ED68684C2BE06295F6268B7FAC0FFA1982780506E061230F6914B |
| SSDEEP: | 12288:rmfVEXxK/ORtEUfylr9DG1bJHejvR/myyIqM/LIdff/8YiEiTpd:rmKXx5tEUaAbRejlmy1quLofi1d |
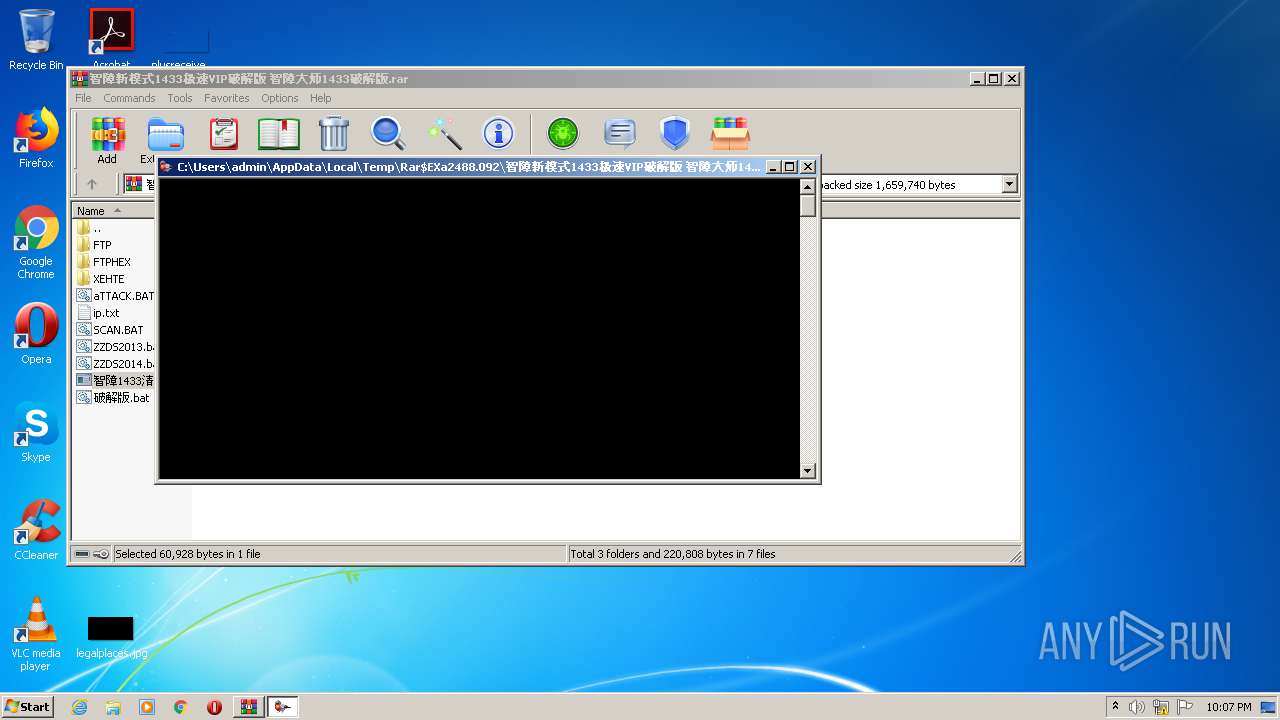
MALICIOUS
Application was dropped or rewritten from another process
- 智障1433清理.exe (PID: 3060)
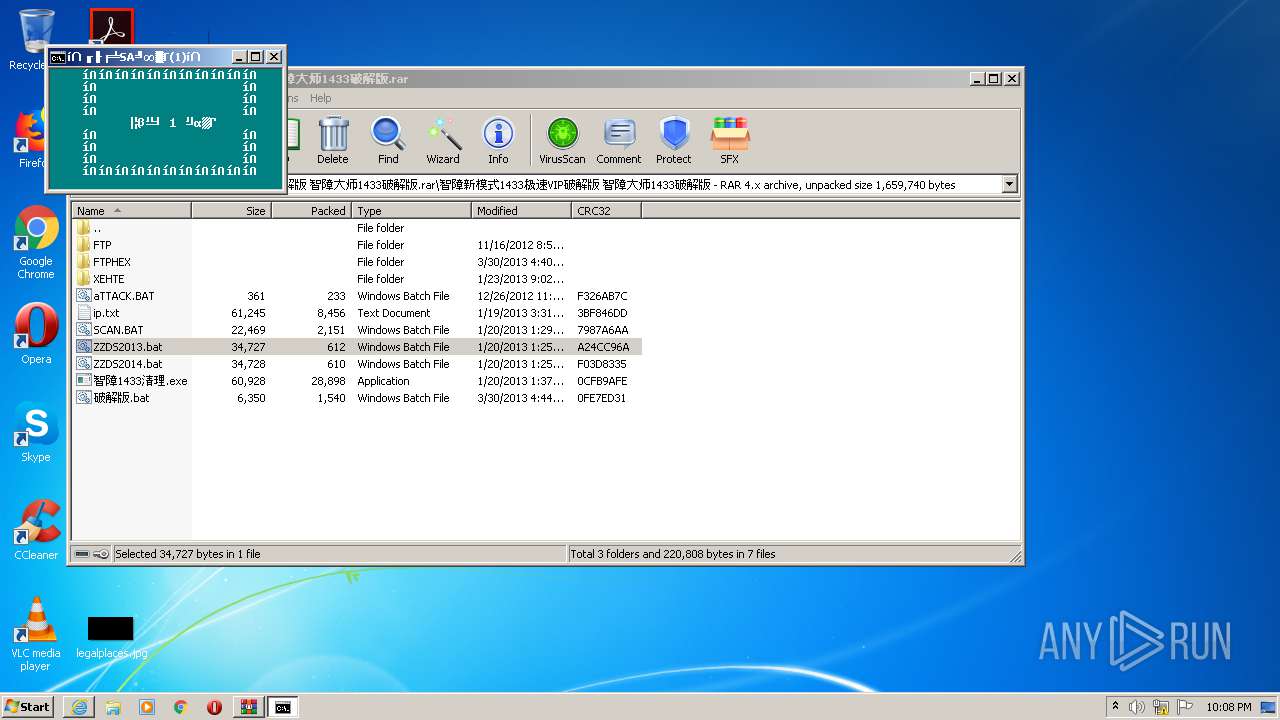
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1276)
- cmd.exe (PID: 1544)
- cmd.exe (PID: 2732)
SUSPICIOUS
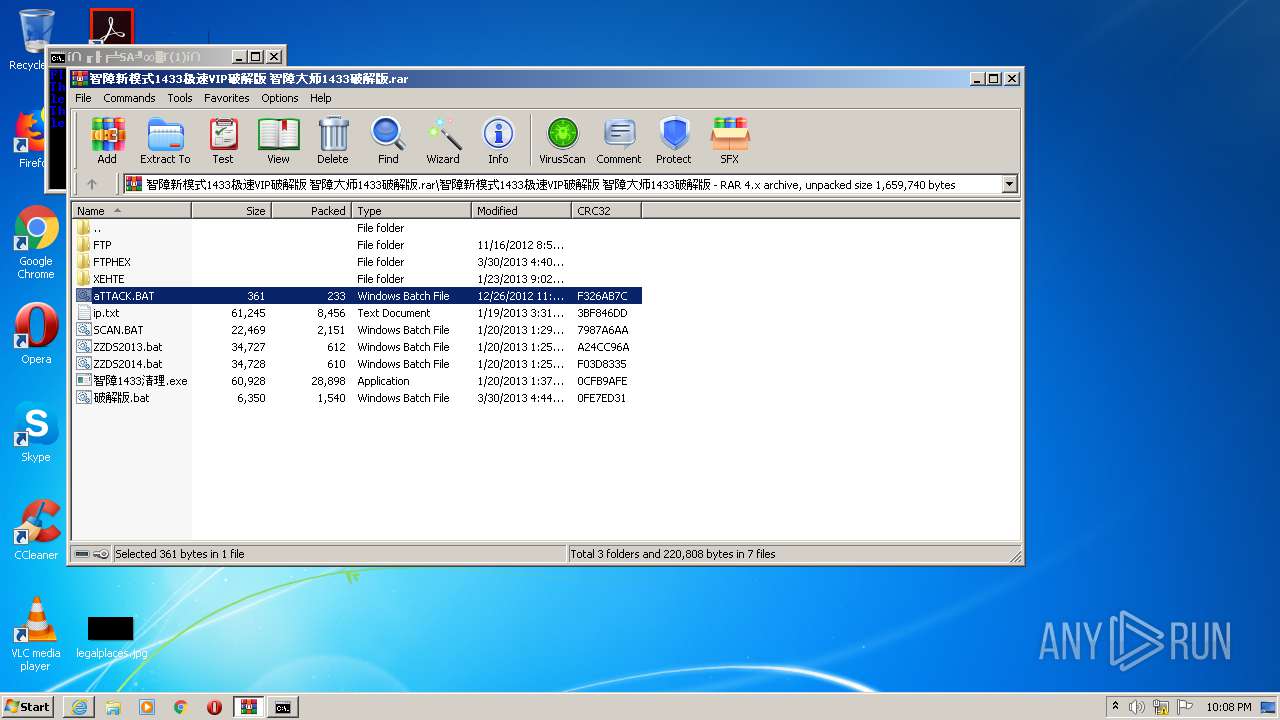
Drops a file with too old compile date
- WinRAR.exe (PID: 2488)
Starts CMD.EXE for commands execution
- 智障1433清理.exe (PID: 3060)
- WinRAR.exe (PID: 2488)
- cmd.exe (PID: 3116)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2488)
Starts Internet Explorer
- cmd.exe (PID: 400)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2488)
Application launched itself
- cmd.exe (PID: 3116)
INFO
Application launched itself
- iexplore.exe (PID: 3436)
Changes internet zones settings
- iexplore.exe (PID: 3436)
Reads internet explorer settings
- iexplore.exe (PID: 3664)
Reads settings of System Certificates
- iexplore.exe (PID: 3664)
Creates files in the user directory
- iexplore.exe (PID: 3664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 378 |
|---|---|
| UncompressedSize: | 361 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2012:12:26 11:23:15 |
| PackingMethod: | Normal |
| ArchivedFileName: | ??????ģʽ1433????VIP?ƽ??? ???ϴ?ʦ1433?ƽ???\aTTACK.BAT |
Total processes
93
Monitored processes
55
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | ping -n 2 localhost | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 400 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa2488.1316\破解版.bat" " | C:\Windows\system32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 532 | mode con: cols=46 lines=20 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | findstr /v /g:attack.txt weakpassword.txt | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 816 | ping -n 2 localhost | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | ping -n 2 localhost | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1180 | ping -n 2 localhost | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1264 | findstr /v /g:attack.txt weakpassword.txt | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1276 | cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\30606A9T.bat" "C:\Users\admin\AppData\Local\Temp\Rar$EXa2488.092\?????1433??VIP??? ????1433???\??1433??.exe" " | C:\Windows\system32\cmd.exe | — | 智障1433清理.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1488 | mode con: cols=29 lines=10 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 561
Read events
2 494
Write events
67
Delete events
0
Modification events
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\智障新模式1433极速VIP破解版 智障大师1433破解版.rar | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
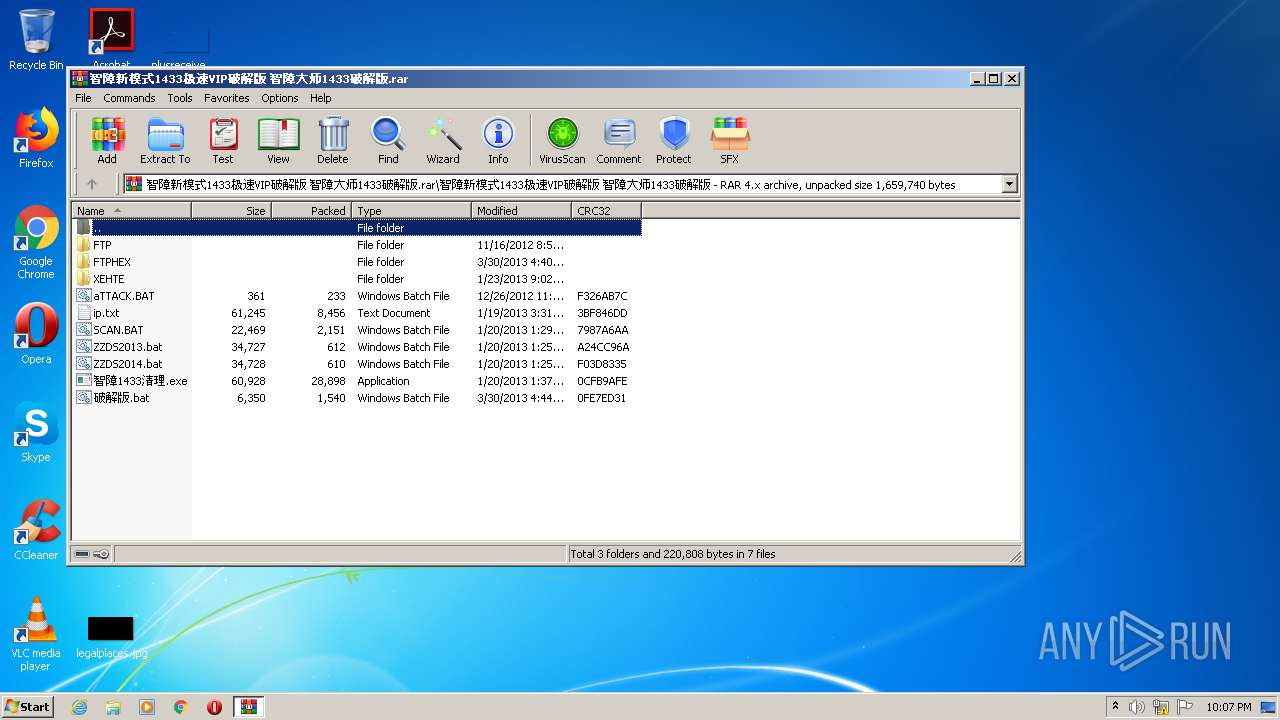
Executable files
9
Suspicious files
40
Text files
81
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2488.092\智障新模式1433极速VIP破解版 智障大师1433破解版\FTPHEX\ftp.dll | executable | |
MD5:— | SHA256:— | |||
| 2488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2488.092\智障新模式1433极速VIP破解版 智障大师1433破解版\FTP\ftp3.6.exe | executable | |
MD5:— | SHA256:— | |||
| 2488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2488.092\智障新模式1433极速VIP破解版 智障大师1433破解版\FTPHEX\Hex.hta | html | |
MD5:— | SHA256:— | |||
| 2488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2488.092\智障新模式1433极速VIP破解版 智障大师1433破解版\XEHTE\JF2013.dll | text | |
MD5:— | SHA256:— | |||
| 2488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2488.092\智障新模式1433极速VIP破解版 智障大师1433破解版\XEHTE\PASSWORD.DIC | text | |
MD5:— | SHA256:— | |||
| 2488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2488.092\智障新模式1433极速VIP破解版 智障大师1433破解版\XEHTE\QL.BAT | text | |
MD5:— | SHA256:— | |||
| 2488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2488.092\智障新模式1433极速VIP破解版 智障大师1433破解版\XEHTE\s.exe | executable | |
MD5:— | SHA256:— | |||
| 2488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2488.092\智障新模式1433极速VIP破解版 智障大师1433破解版\XEHTE\PiSTOl.EXE | executable | |
MD5:— | SHA256:— | |||
| 2488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2488.092\智障新模式1433极速VIP破解版 智障大师1433破解版\ZZDS2013.bat | text | |
MD5:— | SHA256:— | |||
| 2488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2488.092\智障新模式1433极速VIP破解版 智障大师1433破解版\XEHTE\SF.EXE | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
54
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3664 | iexplore.exe | GET | 200 | 154.210.189.12:80 | http://www.yesmybi.com/template/default_pc/images/ui-icon.gif | US | image | 9.19 Kb | unknown |
3664 | iexplore.exe | GET | 200 | 154.210.189.12:80 | http://www.yesmybi.com/ | US | html | 22.9 Kb | unknown |
3664 | iexplore.exe | GET | 200 | 34.102.136.180:80 | http://www.kuyunzyw.vip/pic/uploadimg/2020-7/202072711312230685.png | US | html | 2.46 Kb | whitelisted |
3664 | iexplore.exe | GET | 200 | 154.210.189.12:80 | http://www.yesmybi.com/template/default_pc/images/tabx.png | US | image | 919 b | unknown |
3664 | iexplore.exe | GET | 200 | 154.210.189.12:80 | http://www.yesmybi.com/upload/site/20210108-1/b19399f3e815e78194add445c3977867.jpg | US | image | 6.50 Kb | unknown |
3664 | iexplore.exe | GET | 200 | 154.210.189.12:80 | http://www.yesmybi.com/template/default_pc/images/ico.png | US | image | 2.91 Kb | unknown |
3664 | iexplore.exe | GET | 200 | 154.210.189.12:80 | http://www.yesmybi.com/template/default_pc/css/style.css | US | text | 25.5 Kb | unknown |
3664 | iexplore.exe | GET | 200 | 154.210.189.12:80 | http://www.yesmybi.com/static/css/home.css | US | text | 5.69 Kb | unknown |
3664 | iexplore.exe | GET | 200 | 154.210.189.12:80 | http://www.yesmybi.com/template/default_pc/js/jquery.superslide.js | US | text | 2.84 Kb | unknown |
3664 | iexplore.exe | GET | 200 | 154.210.189.12:80 | http://www.yesmybi.com/template/default_pc/js/jquery.base.js | US | text | 2.17 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3664 | iexplore.exe | 151.101.130.133:80 | ocsp.globalsign.com | Fastly | US | malicious |
3436 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3664 | iexplore.exe | 106.11.84.7:443 | z12.cnzz.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3664 | iexplore.exe | 213.159.202.34:80 | pic.szjal.cn | Stek Kazan LLC | RU | unknown |
3664 | iexplore.exe | 154.210.189.12:80 | www.yesmybi.com | MULTACOM CORPORATION | US | unknown |
3664 | iexplore.exe | 34.102.136.180:80 | www.kuyunzyw.vip | — | US | whitelisted |
3664 | iexplore.exe | 198.11.136.24:443 | cnzz.mmstat.com | Alibaba (China) Technology Co., Ltd. | US | suspicious |
3664 | iexplore.exe | 213.108.7.113:80 | pic.htpan.net | Net By Net Holding LLC | RU | unknown |
3664 | iexplore.exe | 222.188.8.250:443 | s9.cnzz.com | No.31,Jin-rong Street | CN | unknown |
3664 | iexplore.exe | 218.94.207.228:443 | s9.cnzz.com | No.31,Jin-rong Street | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.yesmybi.com |
| unknown |
pic.szjal.cn |
| malicious |
img.kuyun88.com |
| unknown |
www.kuyunzyw.vip |
| whitelisted |
s9.cnzz.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
statuse.digitalcertvalidation.com |
| whitelisted |