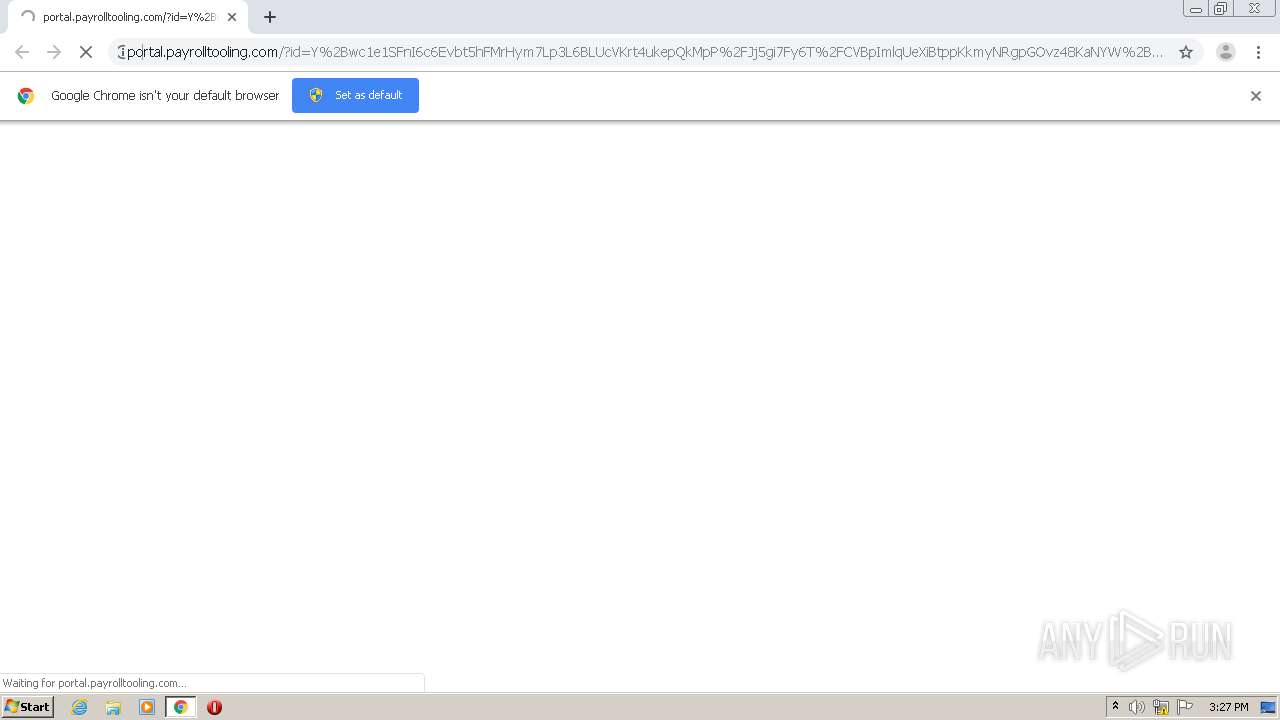
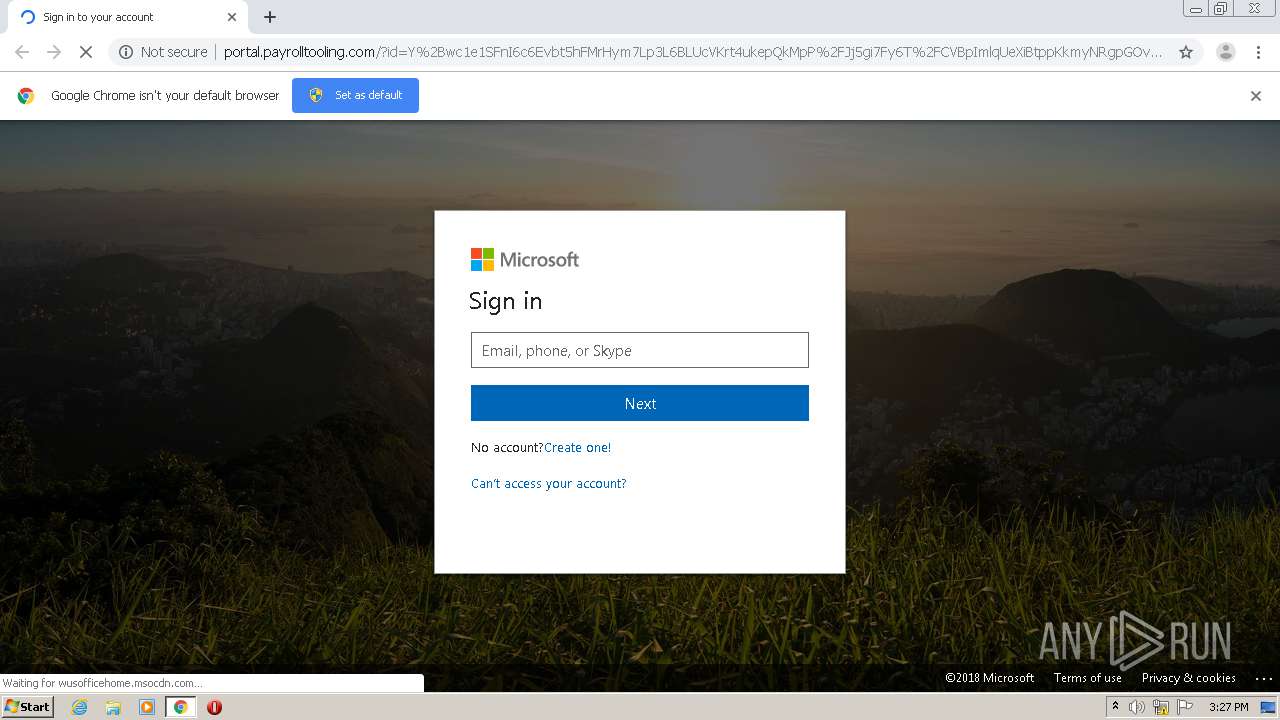
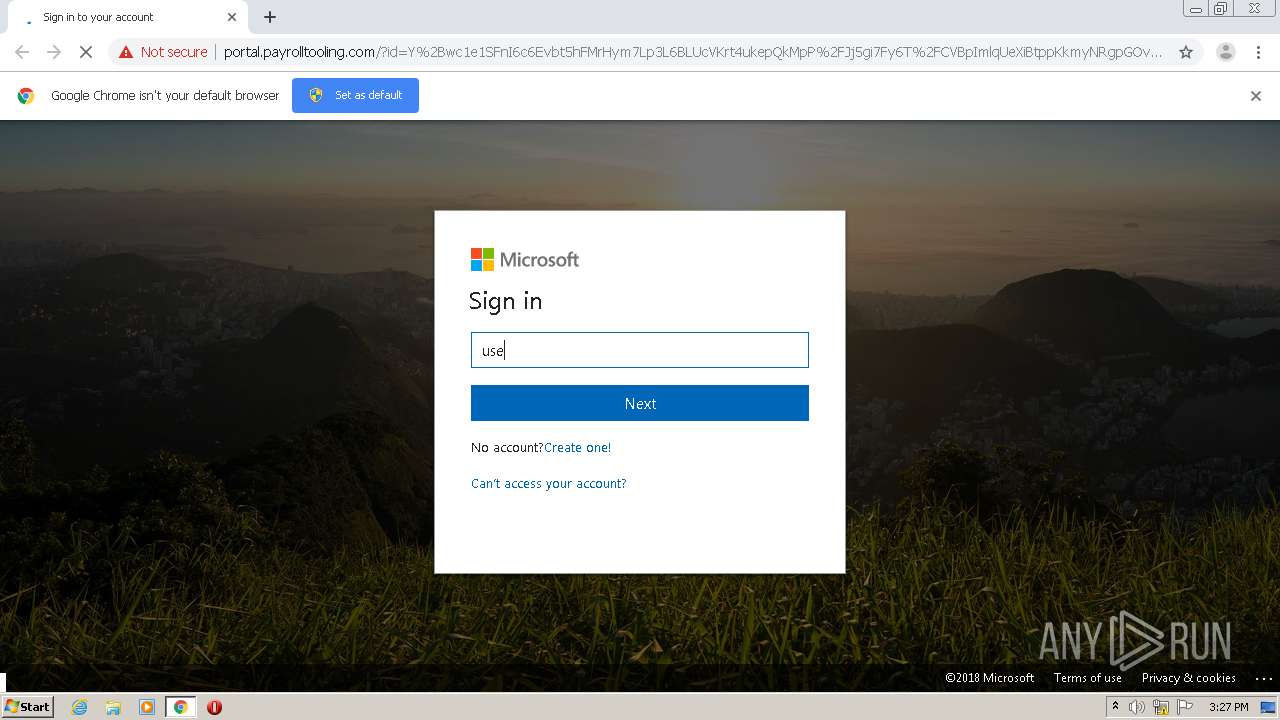
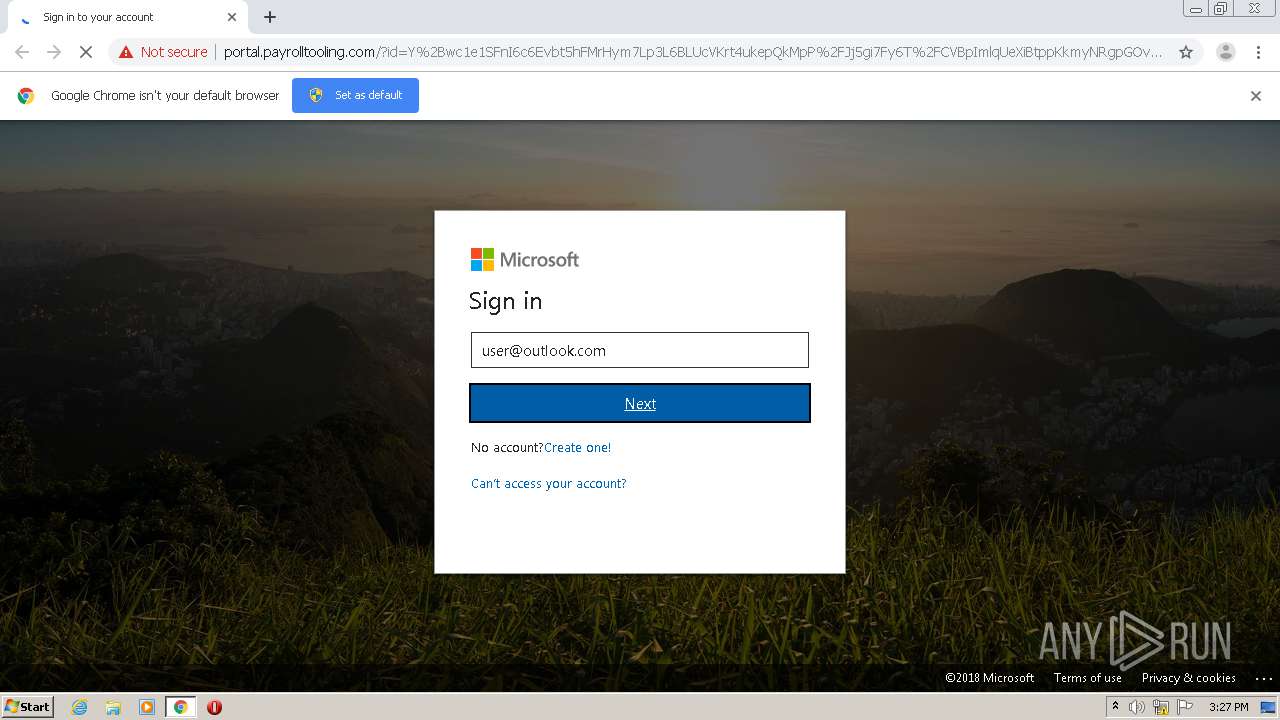
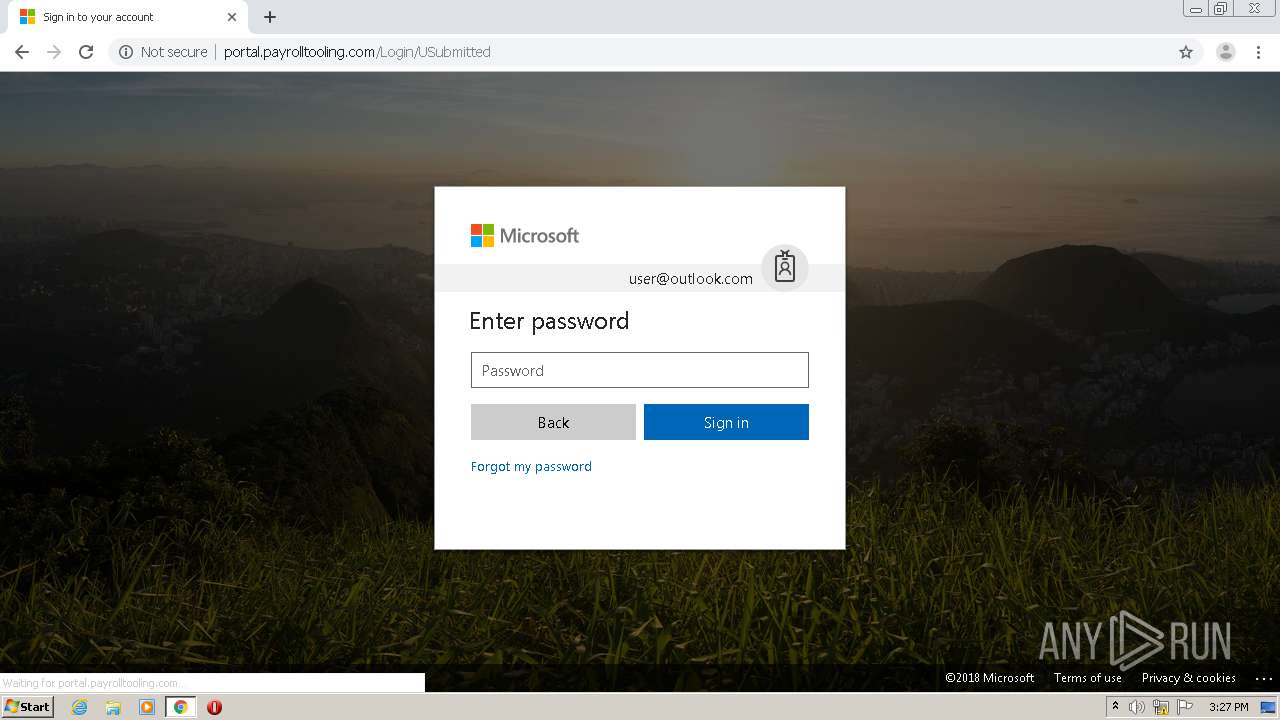
| URL: | http://portal.payrolltooling.com/?id=Y%2Bwc1e1SFnI6c6Evbt5hFMrHym7Lp3L6BLUcVKrt4ukepQkMpP%2FJj5gi7Fy6T%2FCVBpImlqUeXiBtppKkmyNRgpGOvz48KaNYW%2BeGTbqSNwuZCki1p9xEWPUiOXjGyOOvPADfphPO6nhCH0%2FduCHus%2BbgHluw8SUuG%2FvgYr0dWVgwpWNnrXd2e%2BV5m%2BfCGsZ0uLauGMprBuG6XWFYAsSxyBkzexnVG6YZwhnisQJE0abncghcensr8%2FxLrC09RiFlExlu4dRGAfB7%2FP5mz33z6H%2BHyFCzF4v8ImIaOOdHDyAhbAoTwZ%2B3CXHfgPyl3EN1ux8GCsgNxNxnvM4x3LZ%2BZQ%3D%3D |
| Full analysis: | https://app.any.run/tasks/6d8af248-e741-4544-ab2a-d31204e71ca0 |
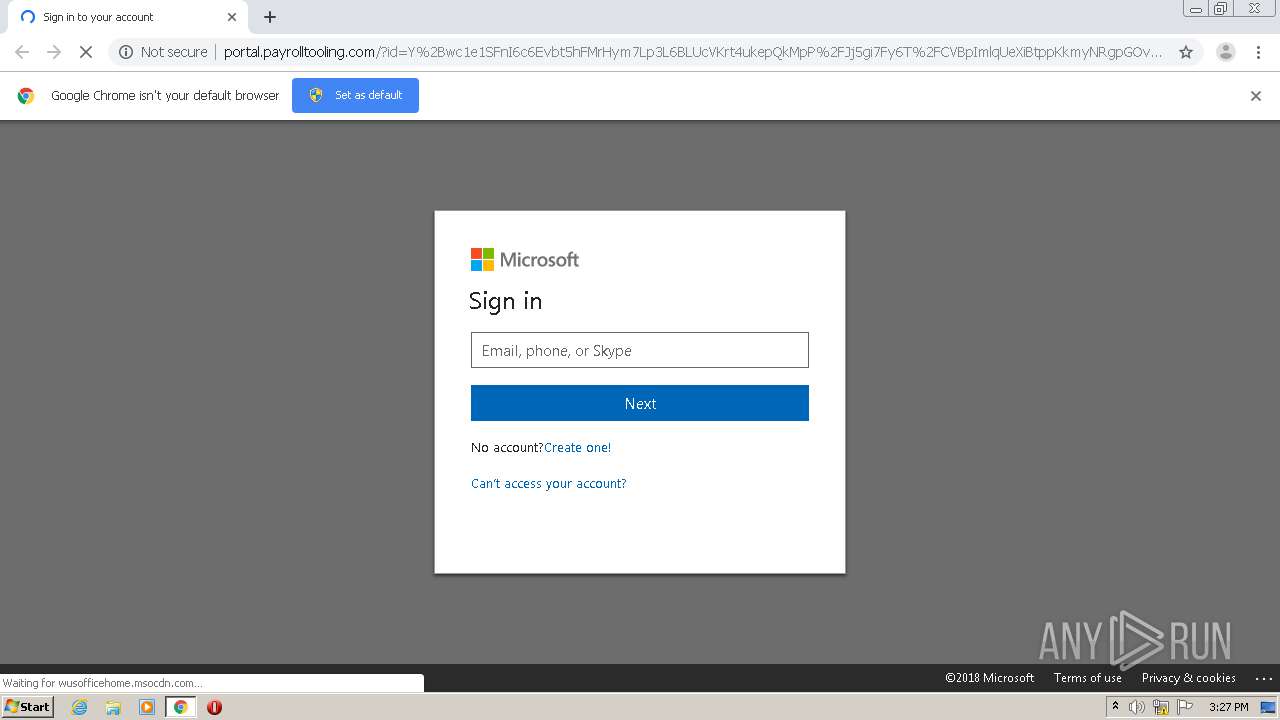
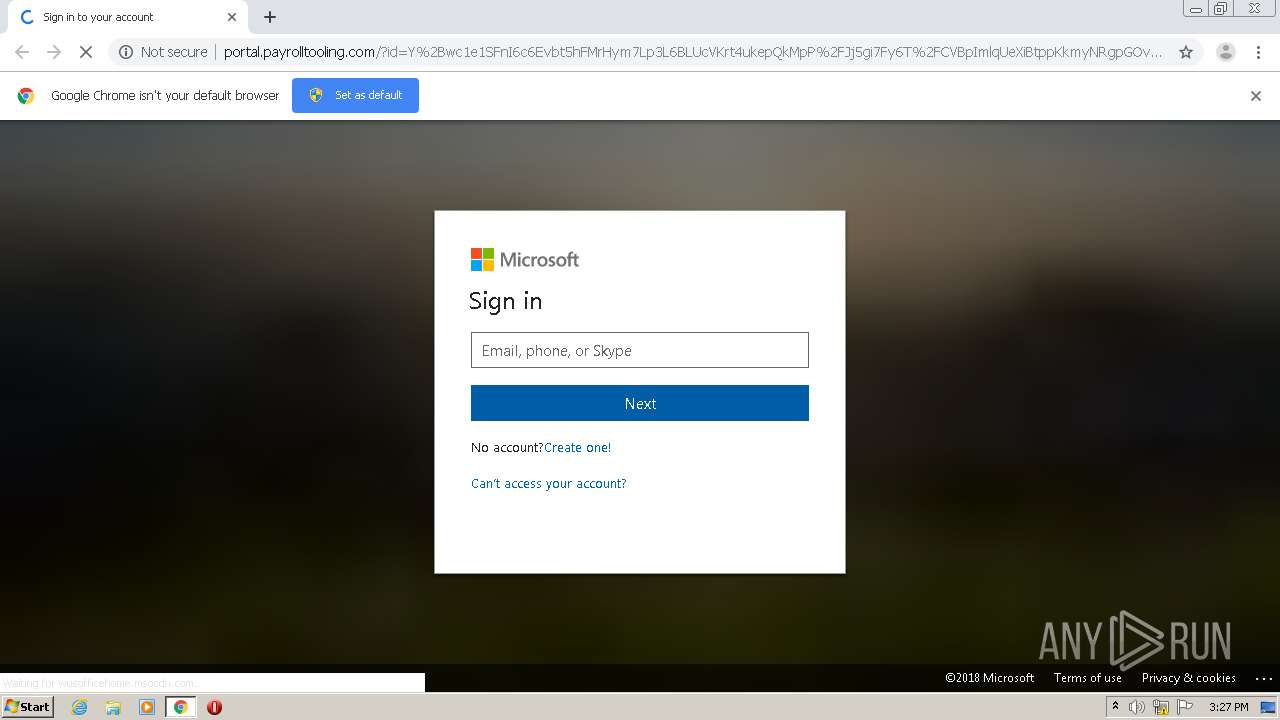
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2020, 14:27:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8D297A7359A6BDBFFC504E9731C09D7B |
| SHA1: | BF1382B4E293278A50A0F4CCCC5741DF05A6DF91 |
| SHA256: | 3C9CC1EDAA6E8ADAC6F6655A172CB984138A290C734390F2B2A537311A0013BA |
| SSDEEP: | 12:j5U8y0VMbDT5+w2TYVPb73zPvQYu1h4HD+8S7:jXVoTIx4Pb77pEYjS7 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 988)
Reads settings of System Certificates
- chrome.exe (PID: 1408)
Reads the hosts file
- chrome.exe (PID: 988)
- chrome.exe (PID: 1408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://portal.payrolltooling.com/?id=Y%2Bwc1e1SFnI6c6Evbt5hFMrHym7Lp3L6BLUcVKrt4ukepQkMpP%2FJj5gi7Fy6T%2FCVBpImlqUeXiBtppKkmyNRgpGOvz48KaNYW%2BeGTbqSNwuZCki1p9xEWPUiOXjGyOOvPADfphPO6nhCH0%2FduCHus%2BbgHluw8SUuG%2FvgYr0dWVgwpWNnrXd2e%2BV5m%2BfCGsZ0uLauGMprBuG6XWFYAsSxyBkzexnVG6YZwhnisQJE0abncghcensr8%2FxLrC09RiFlExlu4dRGAfB7%2FP5mz33z6H%2BHyFCzF4v8ImIaOOdHDyAhbAoTwZ%2B3CXHfgPyl3EN1ux8GCsgNxNxnvM4x3LZ%2BZQ%3D%3D" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,17371721906754113867,6201162969581006349,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7393577414079477781 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,17371721906754113867,6201162969581006349,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=196394105050177619 --mojo-platform-channel-handle=1500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,17371721906754113867,6201162969581006349,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5856086332346522720 --mojo-platform-channel-handle=2904 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1020 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,17371721906754113867,6201162969581006349,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9993098020467490574 --mojo-platform-channel-handle=1312 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,17371721906754113867,6201162969581006349,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6314949654309946373 --mojo-platform-channel-handle=2928 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,17371721906754113867,6201162969581006349,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16474029975119185241 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,17371721906754113867,6201162969581006349,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=523705134039293927 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6e60a9d0,0x6e60a9e0,0x6e60a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
719
Read events
654
Write events
60
Delete events
5
Modification events
| (PID) Process: | (988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
49
Text files
71
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\161051da-a77a-4230-87d7-2b9576e08f34.tmp | — | |
MD5:— | SHA256:— | |||
| 988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
26
DNS requests
15
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1408 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.payrolltooling.com/?id=Y%2Bwc1e1SFnI6c6Evbt5hFMrHym7Lp3L6BLUcVKrt4ukepQkMpP%2FJj5gi7Fy6T%2FCVBpImlqUeXiBtppKkmyNRgpGOvz48KaNYW%2BeGTbqSNwuZCki1p9xEWPUiOXjGyOOvPADfphPO6nhCH0%2FduCHus%2BbgHluw8SUuG%2FvgYr0dWVgwpWNnrXd2e%2BV5m%2BfCGsZ0uLauGMprBuG6XWFYAsSxyBkzexnVG6YZwhnisQJE0abncghcensr8%2FxLrC09RiFlExlu4dRGAfB7%2FP5mz33z6H%2BHyFCzF4v8ImIaOOdHDyAhbAoTwZ%2B3CXHfgPyl3EN1ux8GCsgNxNxnvM4x3LZ%2BZQ%3D%3D | US | html | 10.0 Kb | suspicious |
1408 | chrome.exe | GET | 404 | 52.168.52.134:80 | http://portal.payrolltooling.com/Content/newSignInFiles/~/Content/newSignInFiles/sharedFontStyles.css | US | html | 762 b | suspicious |
1408 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.payrolltooling.com/Content/newSignInFiles/firstScript.js | US | text | 22.5 Kb | suspicious |
1408 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.payrolltooling.com/Content/newSignInFiles/converged.login.min.css | US | text | 22.1 Kb | suspicious |
1408 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.payrolltooling.com/Content/newSignInFiles/prefetch_1.html | US | html | 1.40 Kb | suspicious |
1408 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.payrolltooling.com/Content/newSignInFiles/jsonjs.js | US | text | 4.45 Kb | suspicious |
1408 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.payrolltooling.com/Content/newSignInFiles/microsoft_logo.svg | US | image | 3.57 Kb | suspicious |
1408 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.payrolltooling.com/Content/newSignInFiles/morescript.js | US | text | 390 b | suspicious |
1408 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.payrolltooling.com/Content/newSignInFiles/convergedloginpaginatedstrings-en.min.js | US | text | 4.80 Kb | suspicious |
1408 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.payrolltooling.com/Content/newSignInFiles/ellipsis_white.svg | US | image | 915 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1408 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1408 | chrome.exe | 52.168.52.134:80 | portal.payrolltooling.com | Microsoft Corporation | US | suspicious |
1408 | chrome.exe | 95.100.79.183:443 | secure.aadcdn.microsoftonline-p.com | Akamai Technologies, Inc. | — | whitelisted |
1408 | chrome.exe | 216.58.205.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
1408 | chrome.exe | 23.210.248.93:443 | r4.res.office365.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.100.79.183:443 | secure.aadcdn.microsoftonline-p.com | Akamai Technologies, Inc. | — | whitelisted |
1408 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1408 | chrome.exe | 172.217.18.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1408 | chrome.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
1408 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
portal.payrolltooling.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
secure.aadcdn.microsoftonline-p.com |
| whitelisted |
clients1.google.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
privacy.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
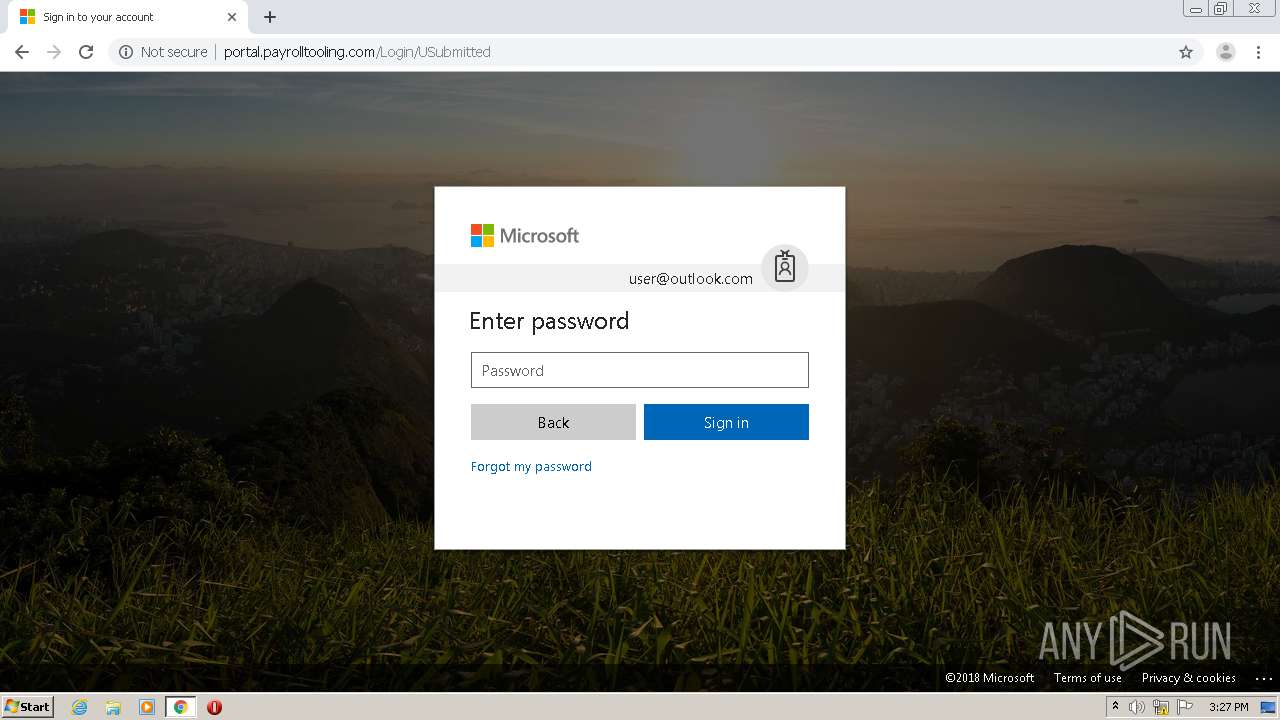
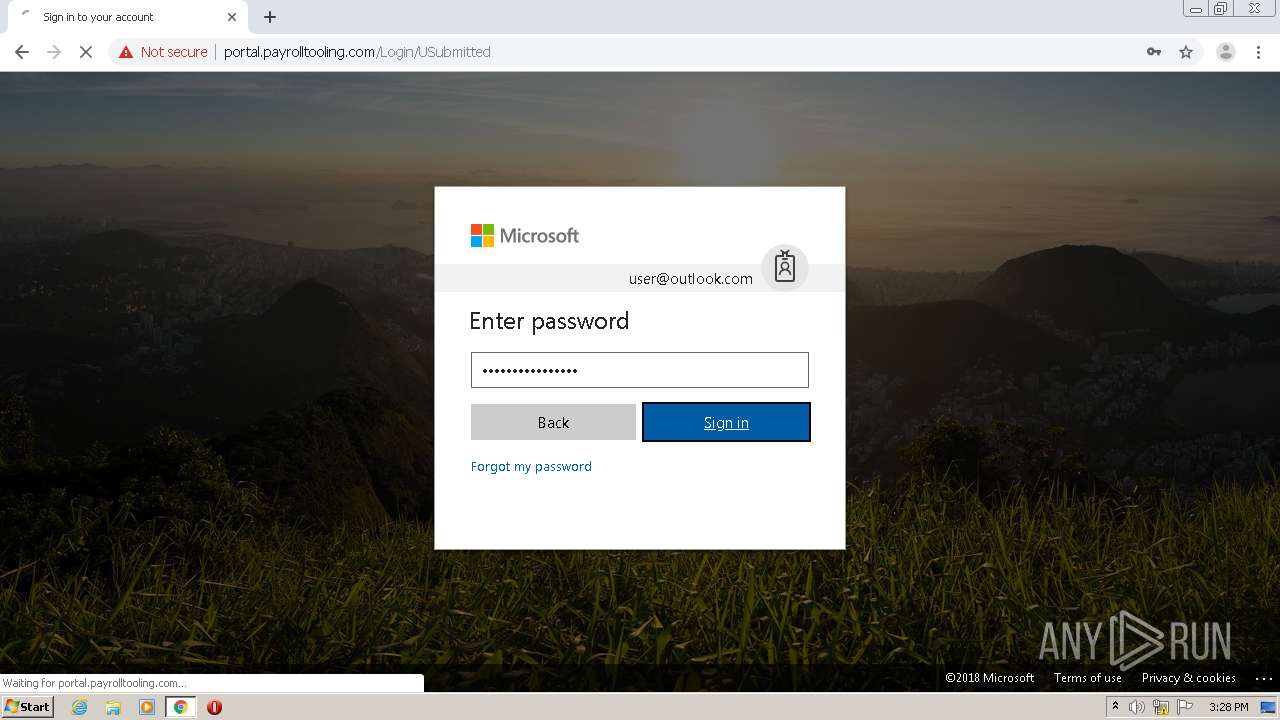
1408 | chrome.exe | Potentially Bad Traffic | ET INFO Possible Phish - Saved Website Comment Observed |
1408 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Cloned Website Phishing Landing - Saved Website Comment Observed |
1408 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
1408 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
2 ETPRO signatures available at the full report