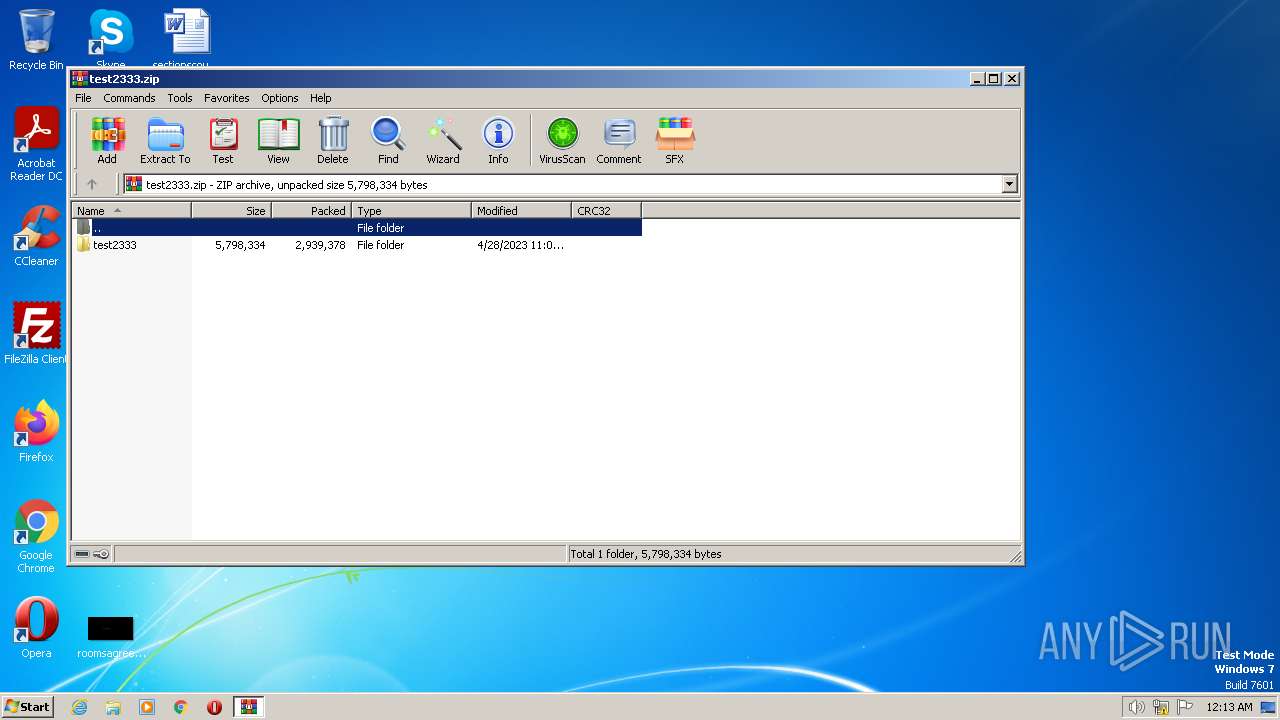
| File name: | test2333.zip |
| Full analysis: | https://app.any.run/tasks/6c6bfd22-bb2e-4362-968a-5ccddbb97e37 |
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2023, 23:13:40 |
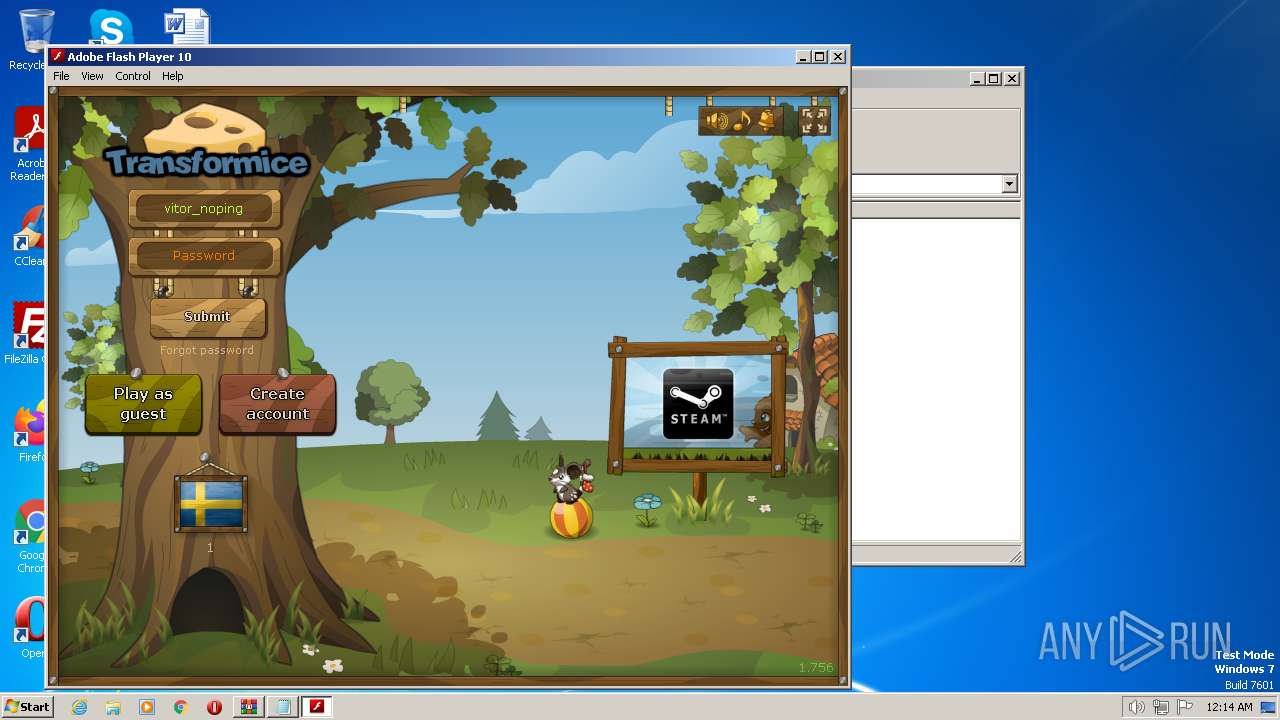
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 68A48CBCED111CB9BB15A098D4C483B9 |
| SHA1: | 471324A12696D2E216B1A3EAA568219B3CD33AF0 |
| SHA256: | 3C818B838CE68DEEAE74ED0F767D5F6812C1E92484C3C74F5D4DEDC8C094D858 |
| SSDEEP: | 49152:0HpFkFMe2J2lqNwiIf6CP3lQPQDOcInjxMdHpqBtwHteL+EwR5idSieFSyNk85DZ:u30c2ILE3lQ4DOcCxuHpqrMt2+z5kBw5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
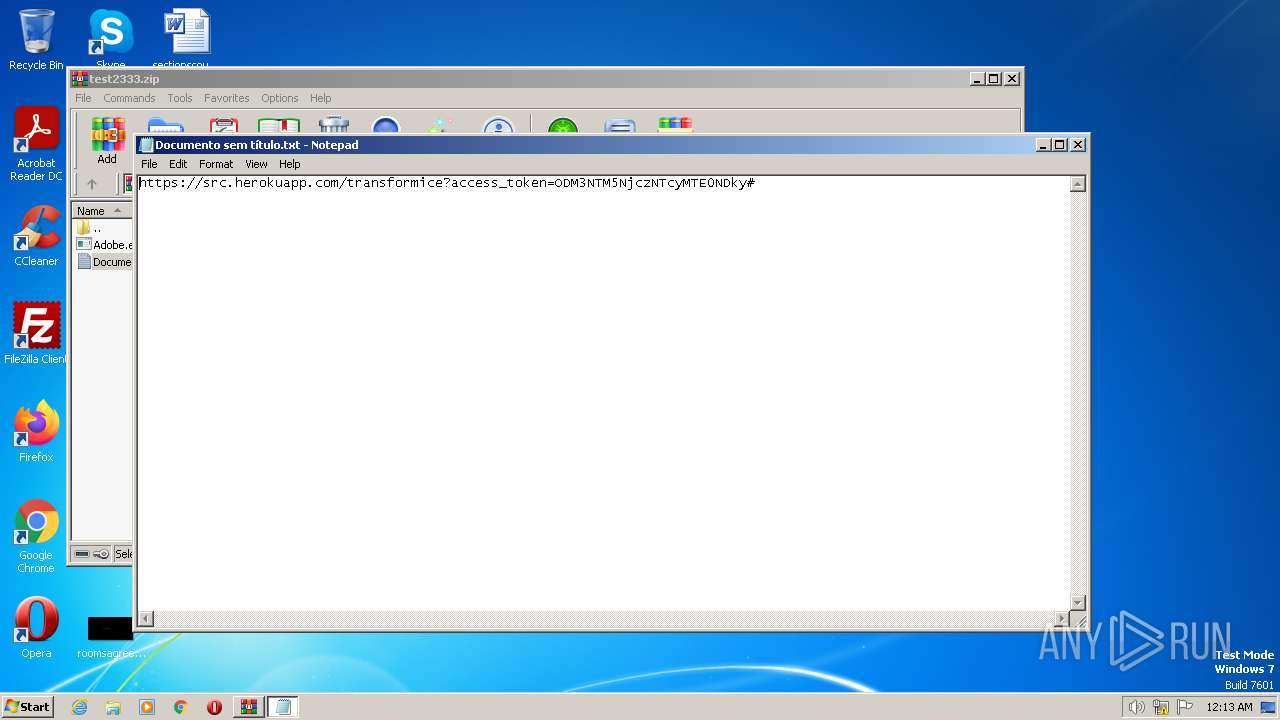
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 1352)
Reads the Internet Settings
- Adobe.exe (PID: 1492)
Reads settings of System Certificates
- Adobe.exe (PID: 1492)
Checks Windows Trust Settings
- Adobe.exe (PID: 1492)
Reads security settings of Internet Explorer
- Adobe.exe (PID: 1492)
Connects to unusual port
- Adobe.exe (PID: 1492)
INFO
Checks supported languages
- Adobe.exe (PID: 1492)
- wmpnscfg.exe (PID: 4080)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1352)
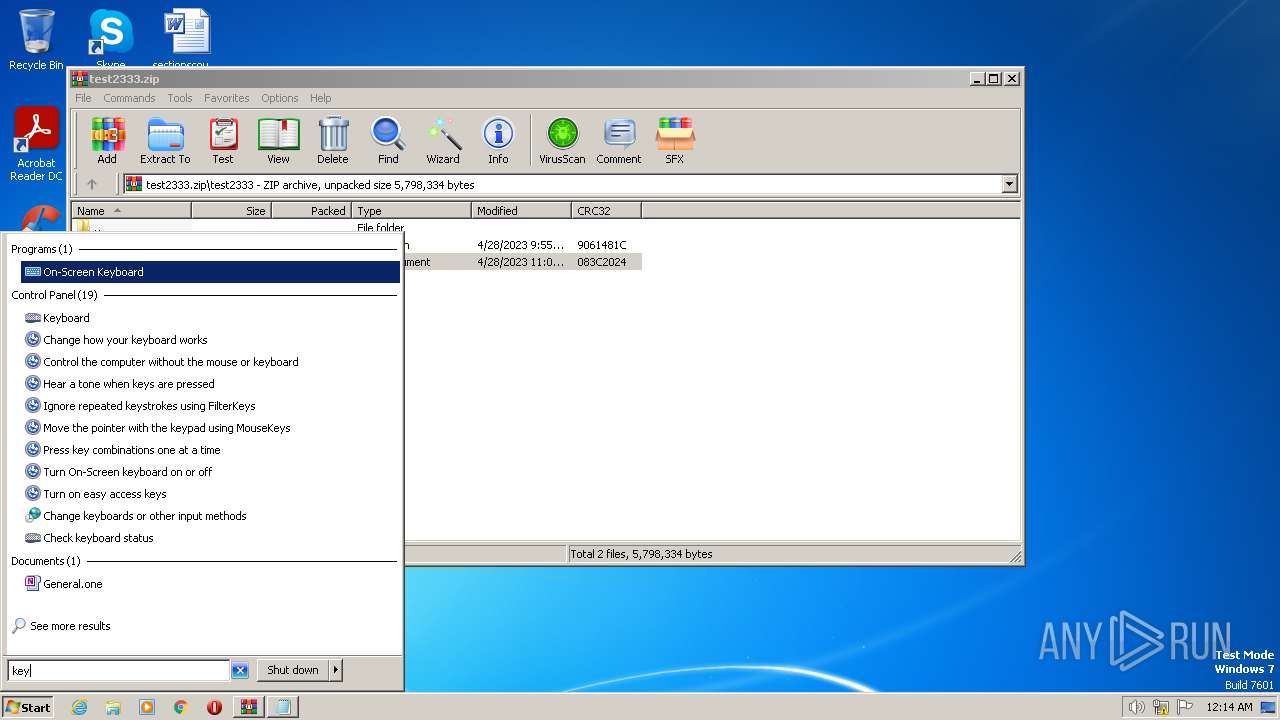
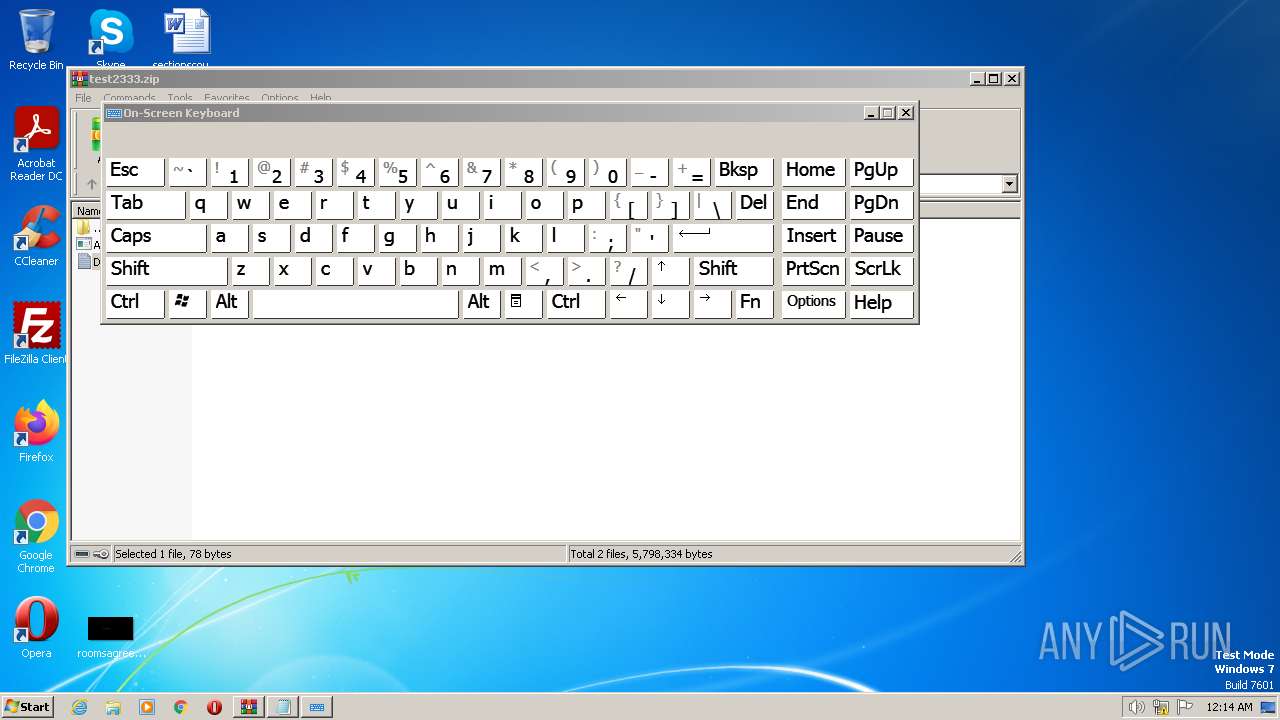
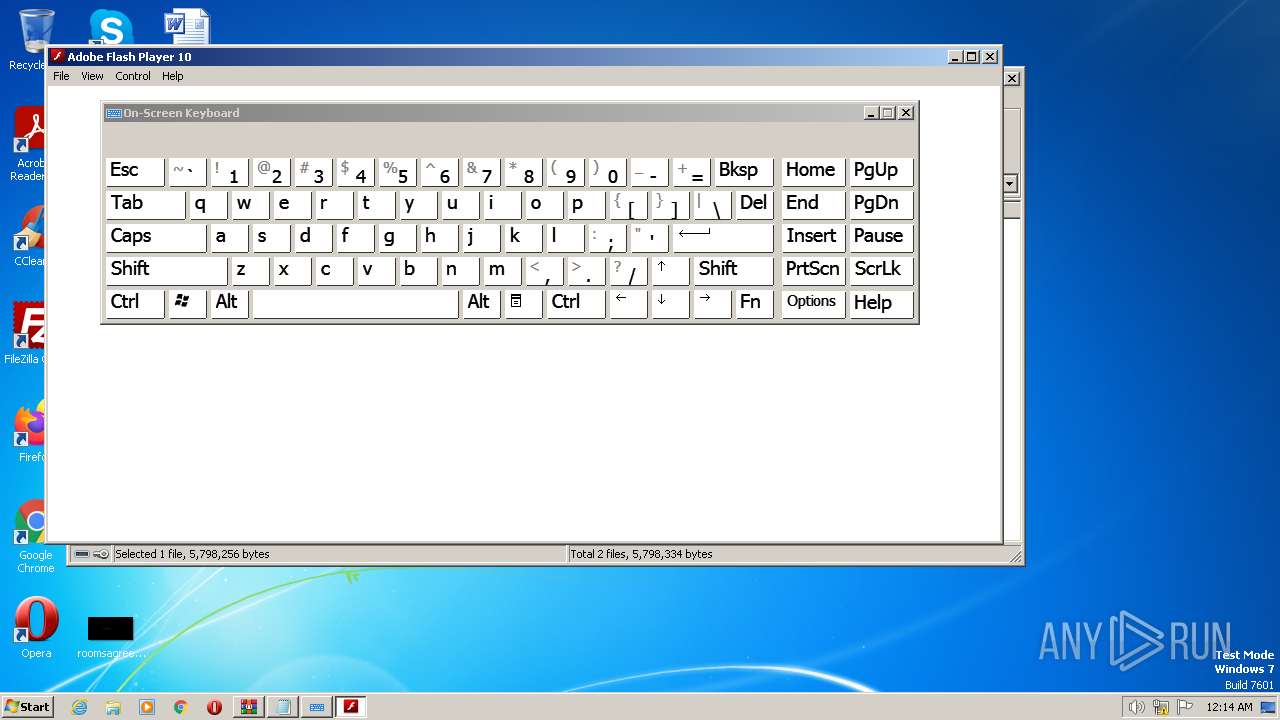
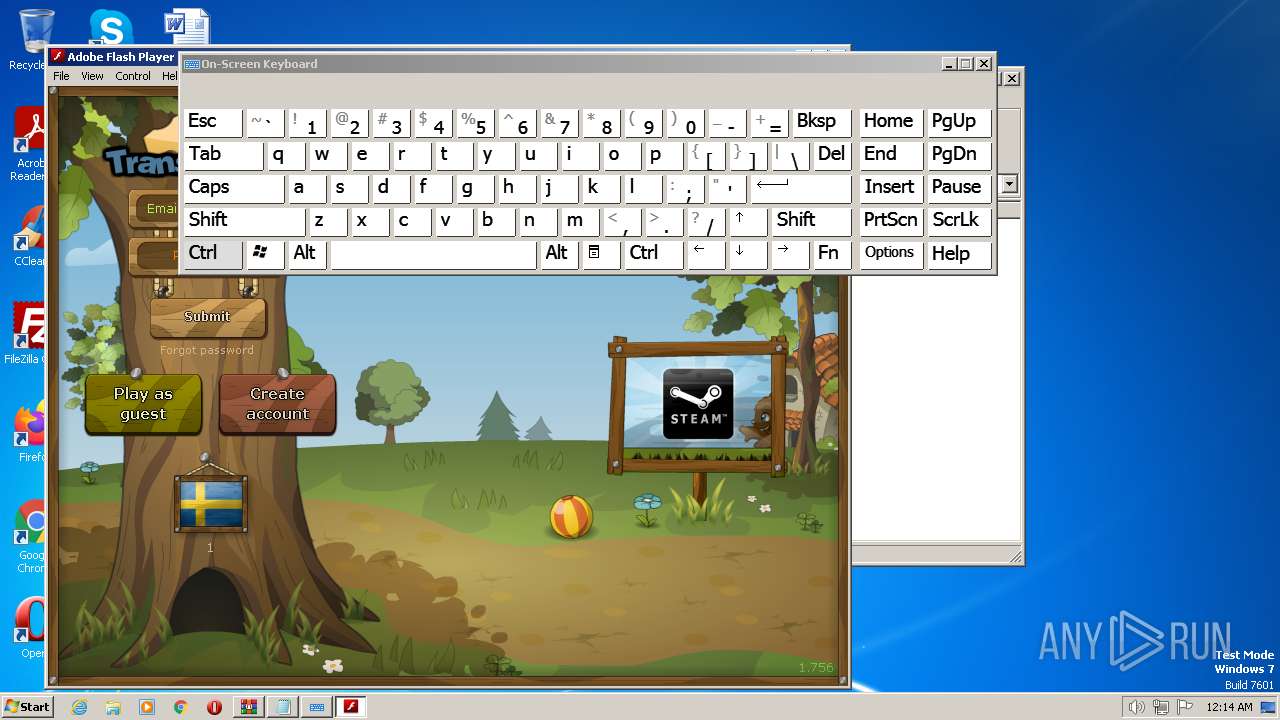
Manual execution by a user
- osk.exe (PID: 1652)
- osk.exe (PID: 2984)
- wmpnscfg.exe (PID: 4080)
The process checks LSA protection
- Adobe.exe (PID: 1492)
- wmpnscfg.exe (PID: 4080)
Reads CPU info
- Adobe.exe (PID: 1492)
Reads the machine GUID from the registry
- Adobe.exe (PID: 1492)
- wmpnscfg.exe (PID: 4080)
Reads the computer name
- Adobe.exe (PID: 1492)
- wmpnscfg.exe (PID: 4080)
Checks proxy server information
- Adobe.exe (PID: 1492)
Create files in a temporary directory
- Adobe.exe (PID: 1492)
Creates files or folders in the user directory
- Adobe.exe (PID: 1492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | test2333/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2023:04:28 19:01:08 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 788 |
Total processes
48
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
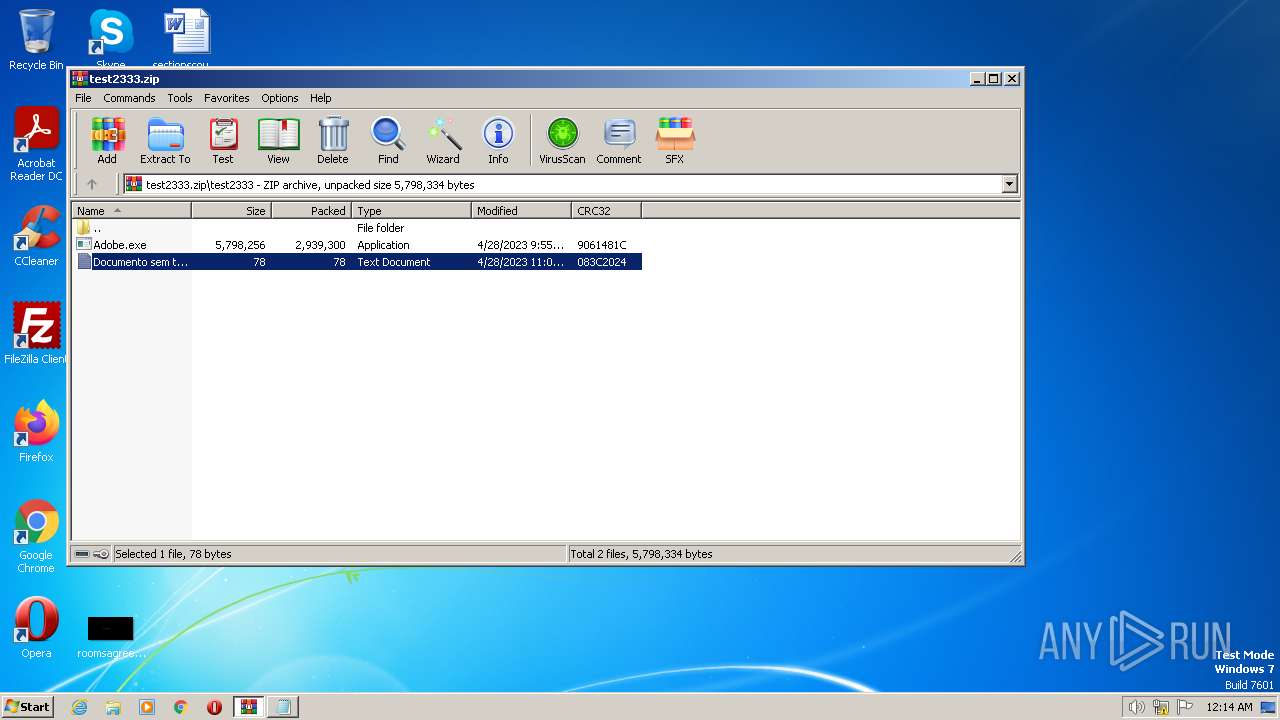
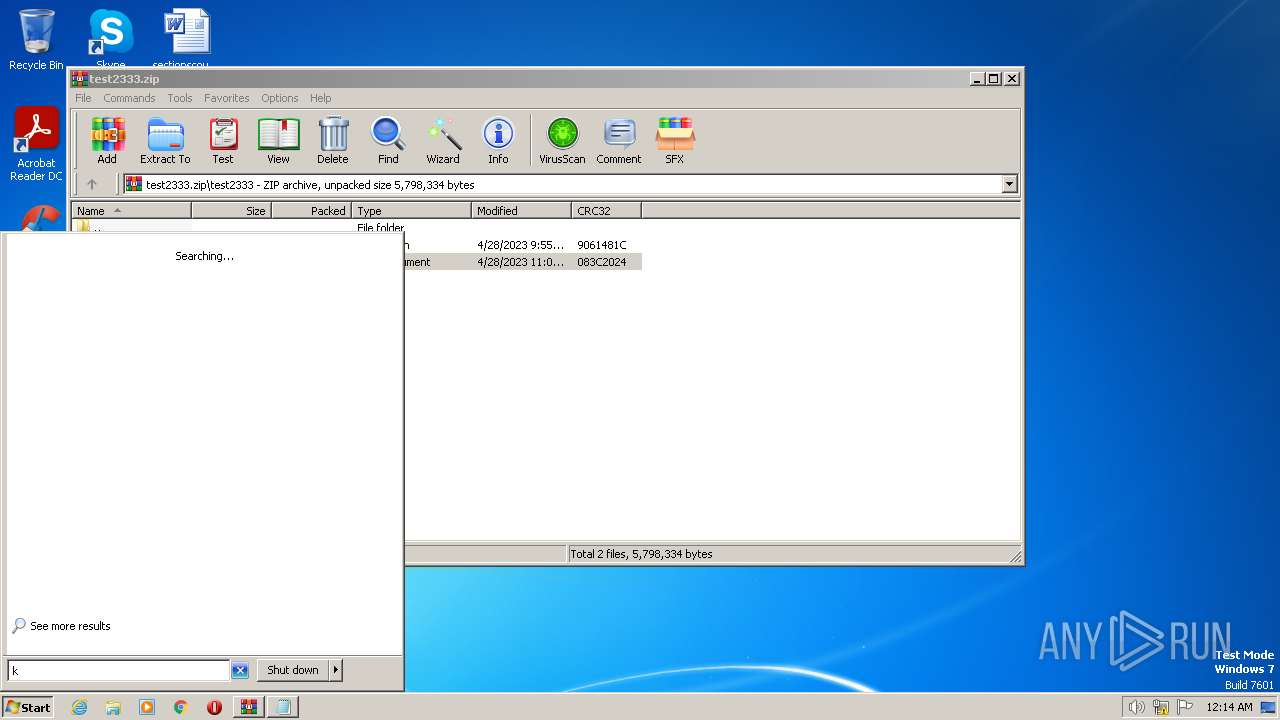
| 1352 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\test2333.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
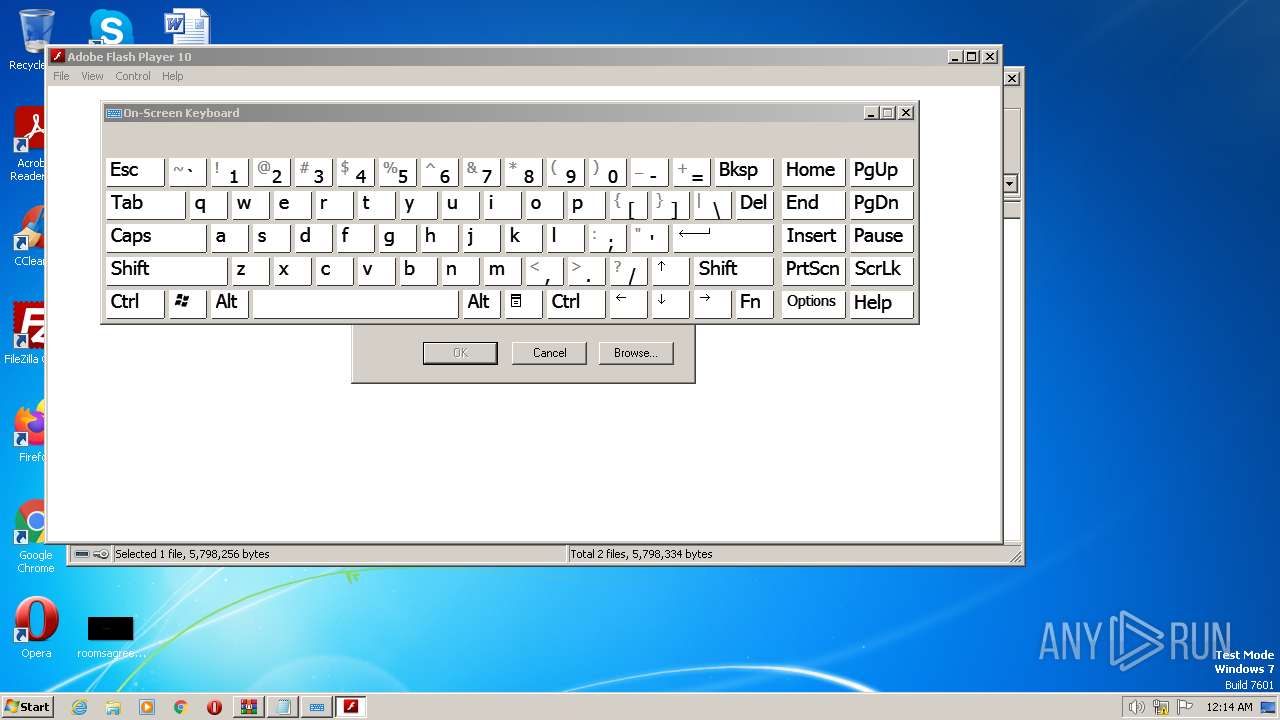
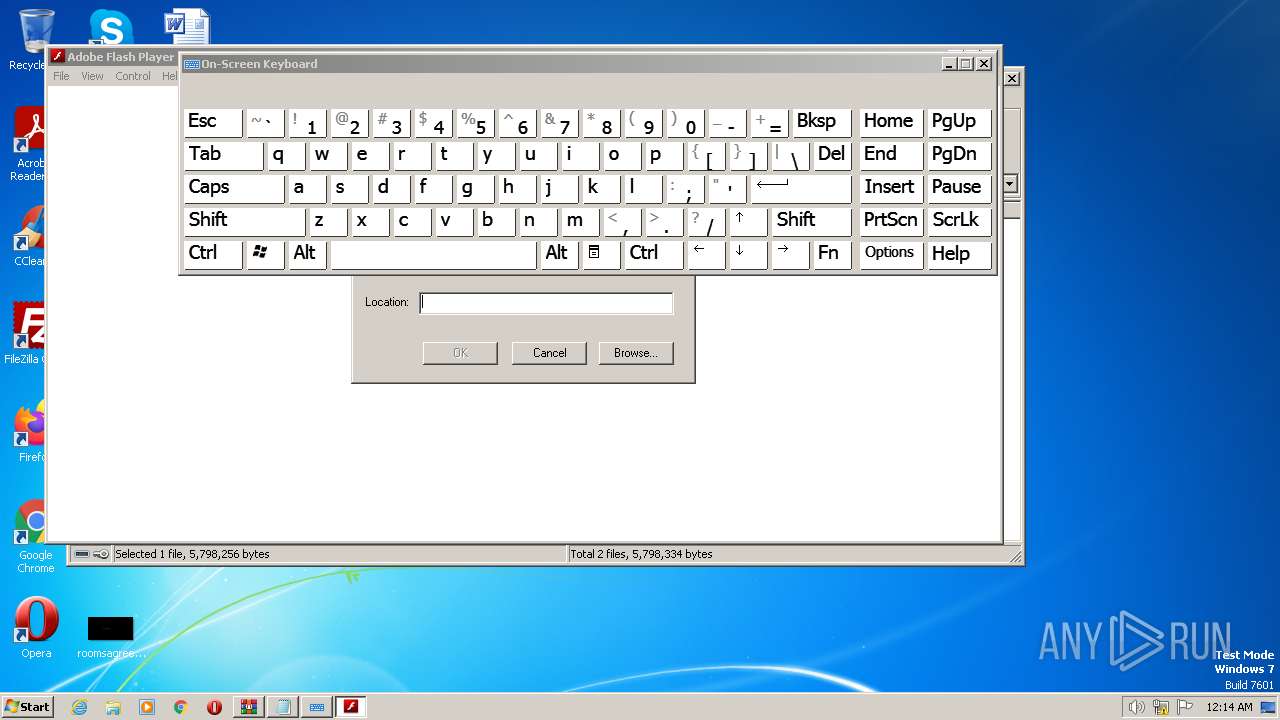
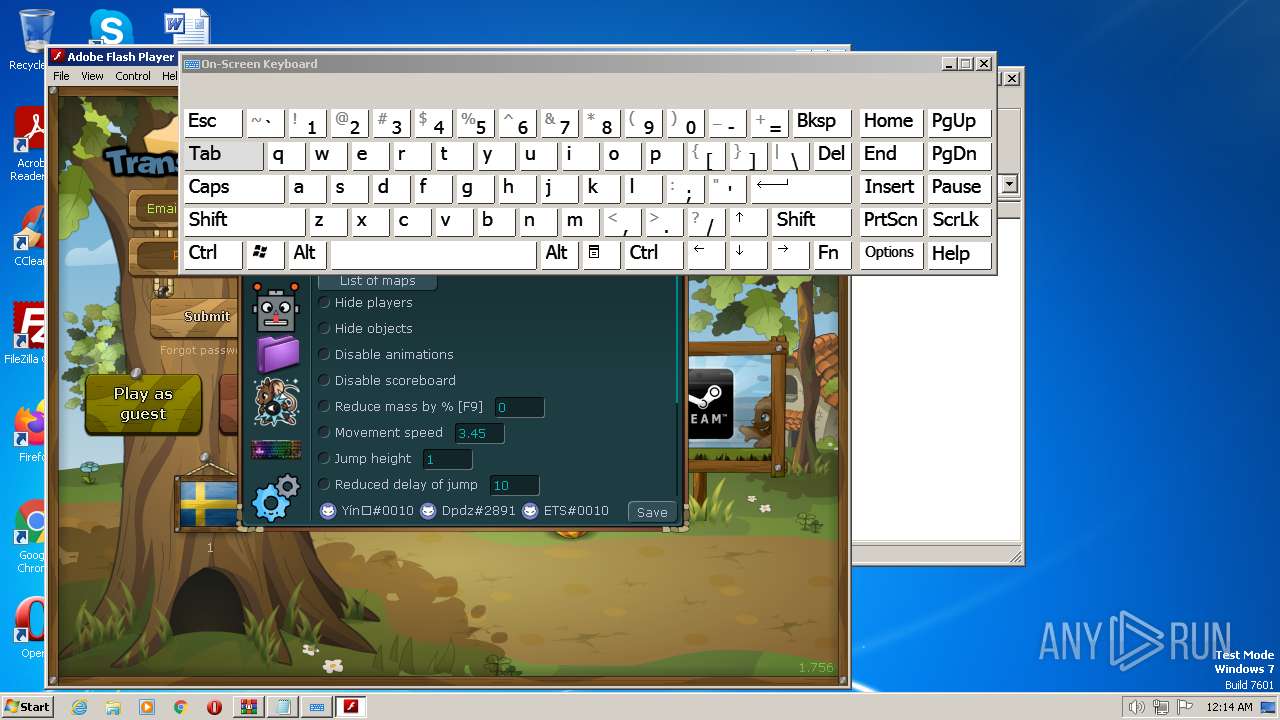
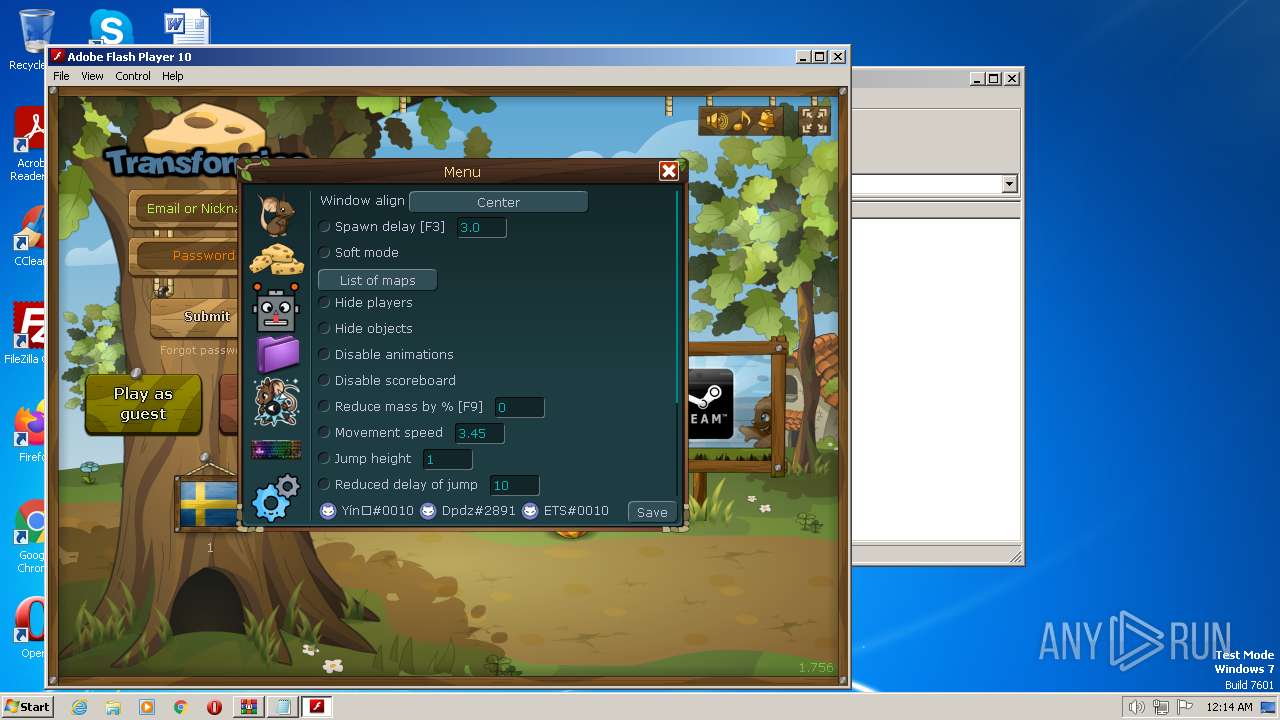
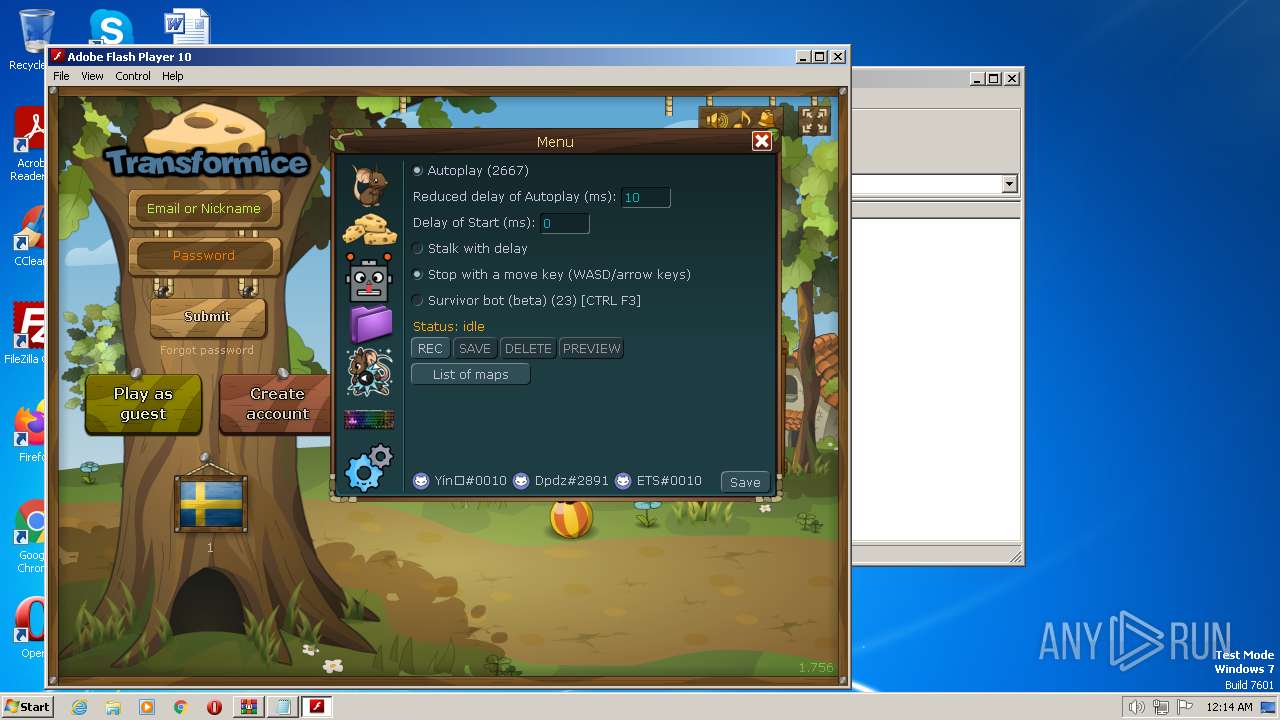
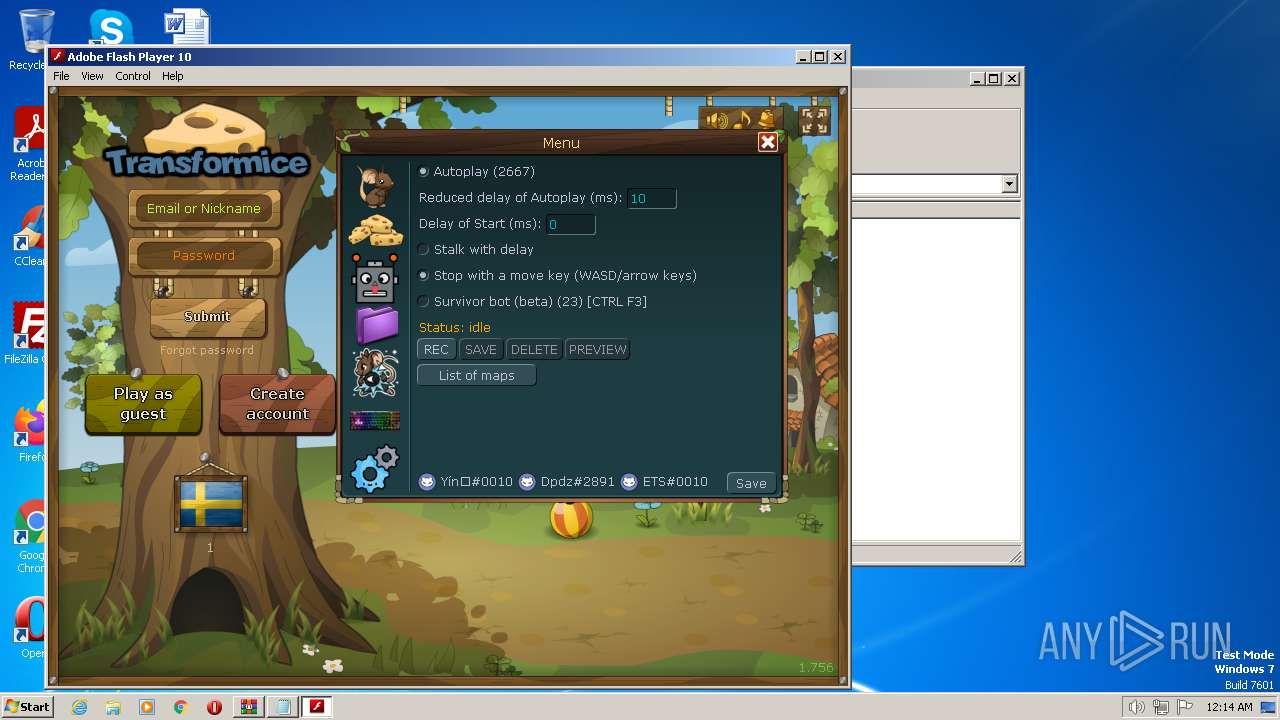
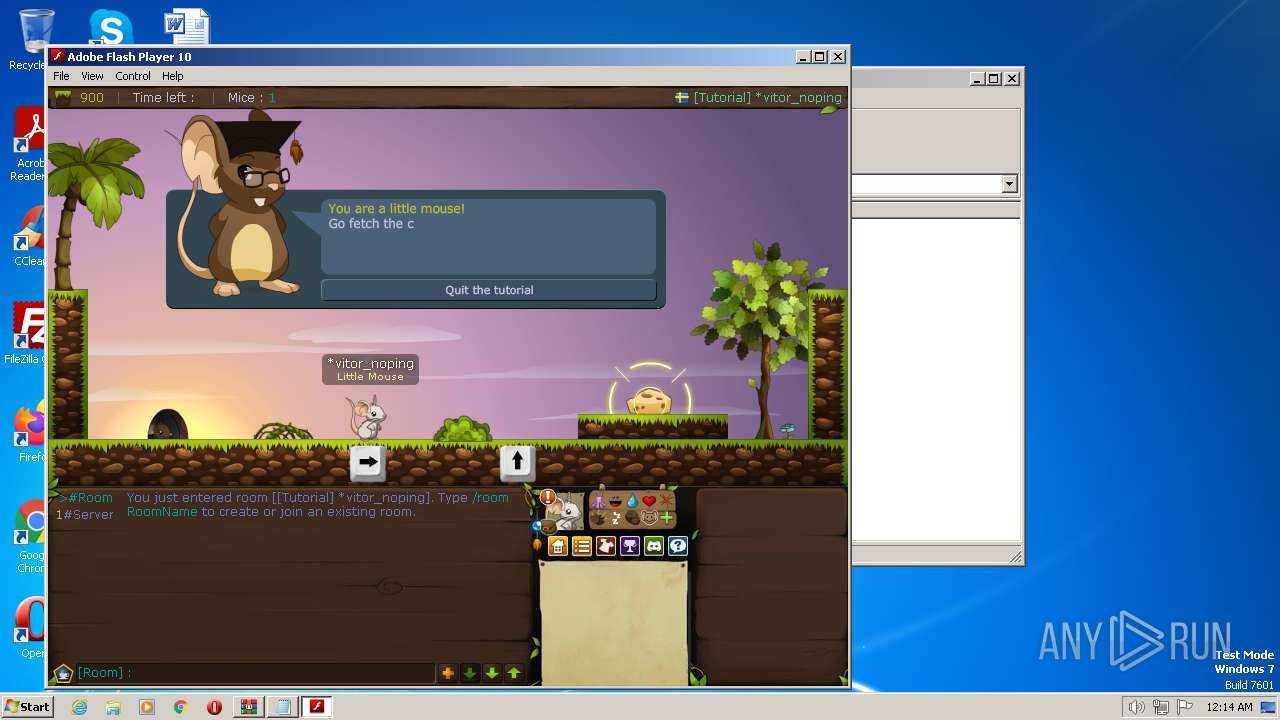
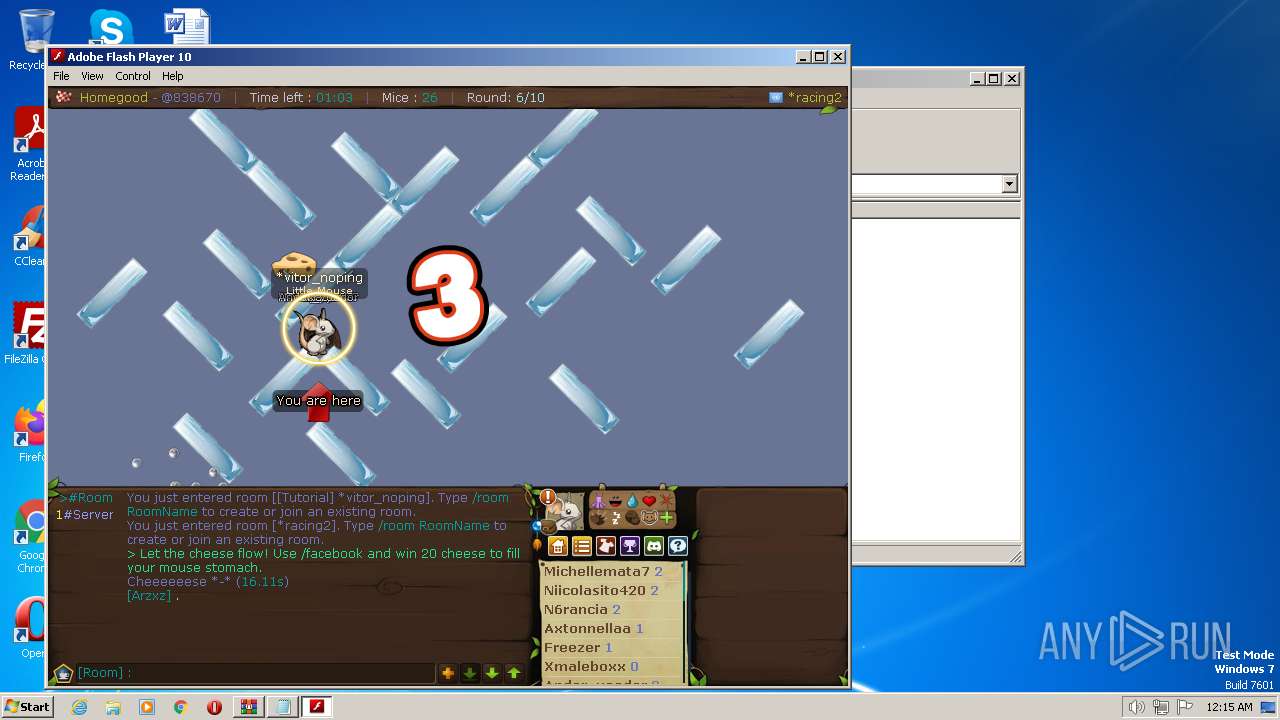
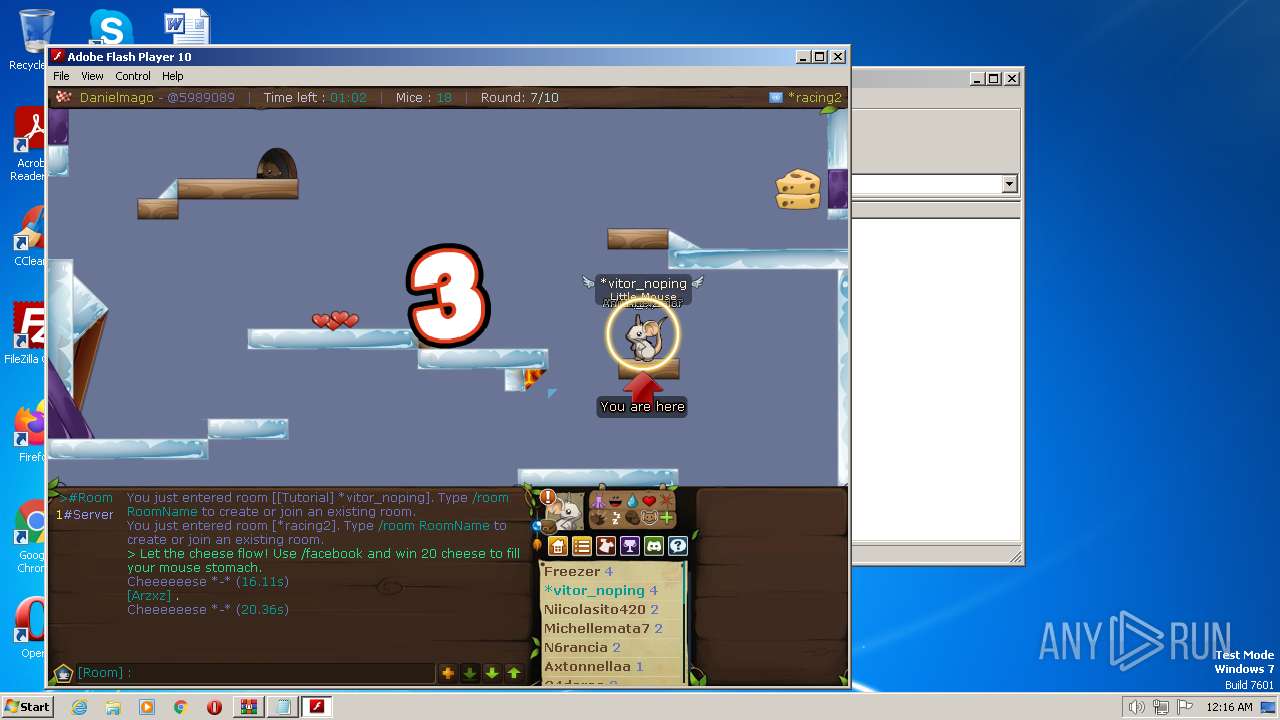
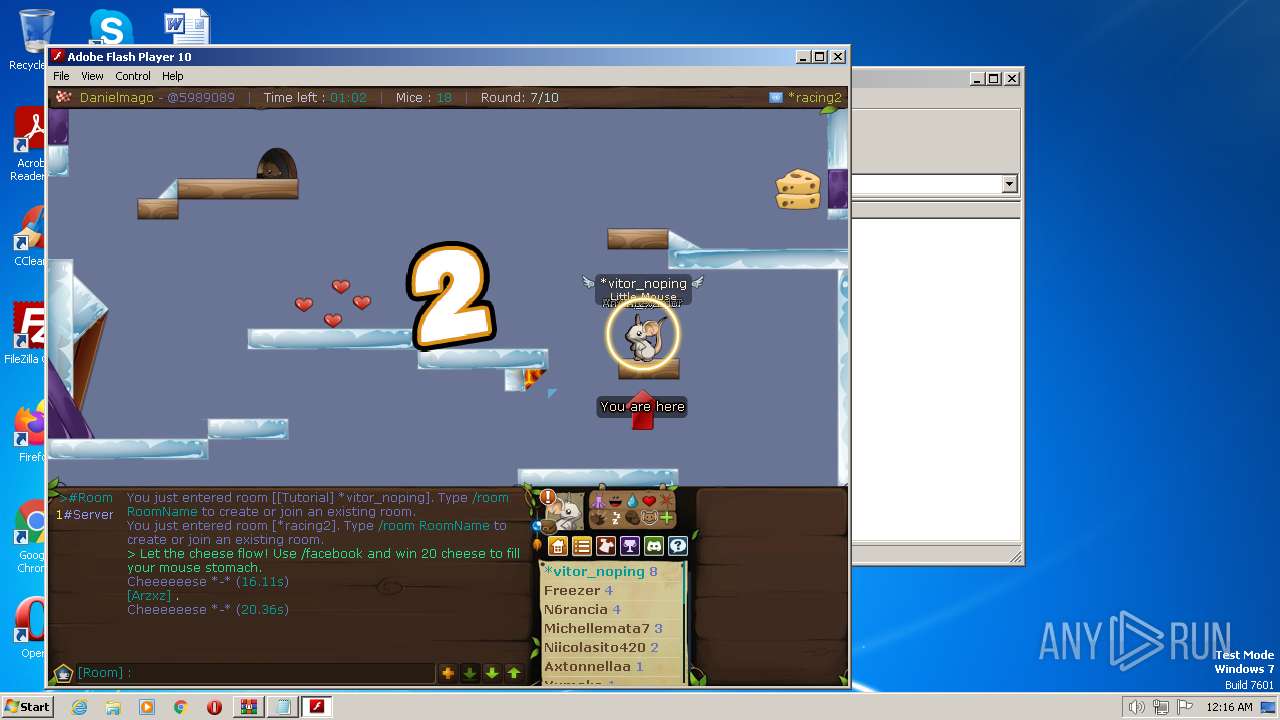
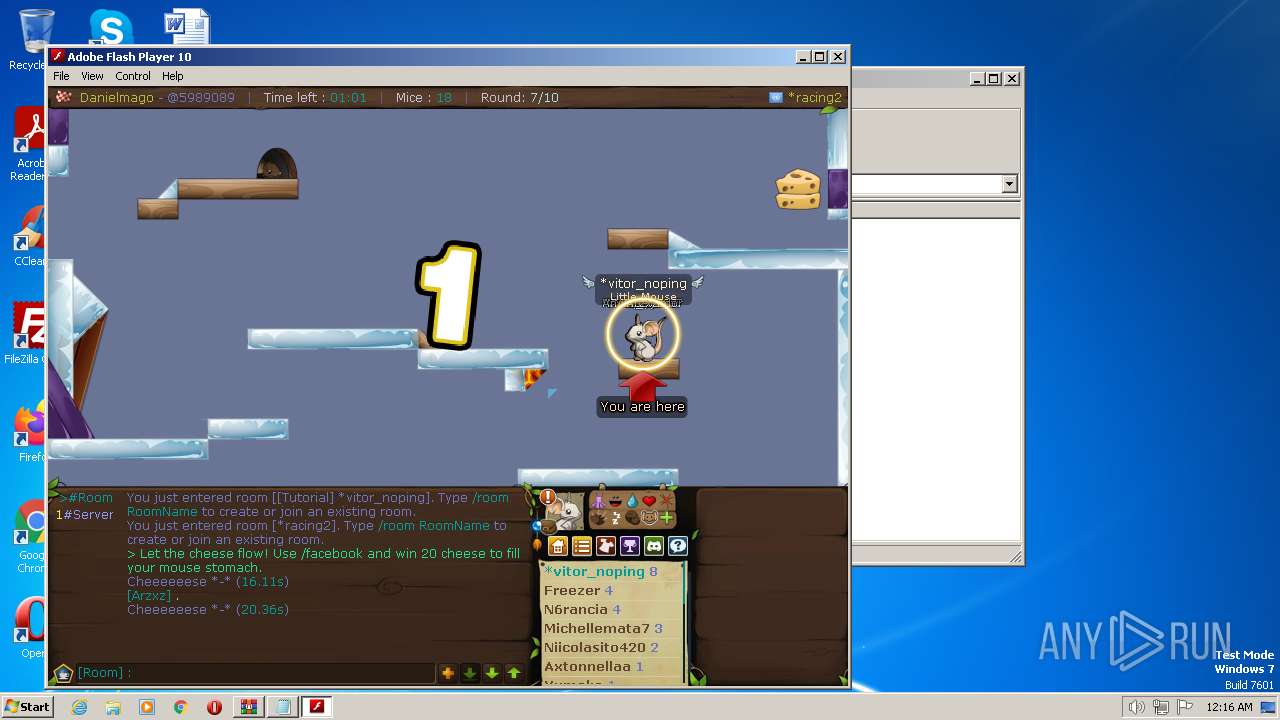
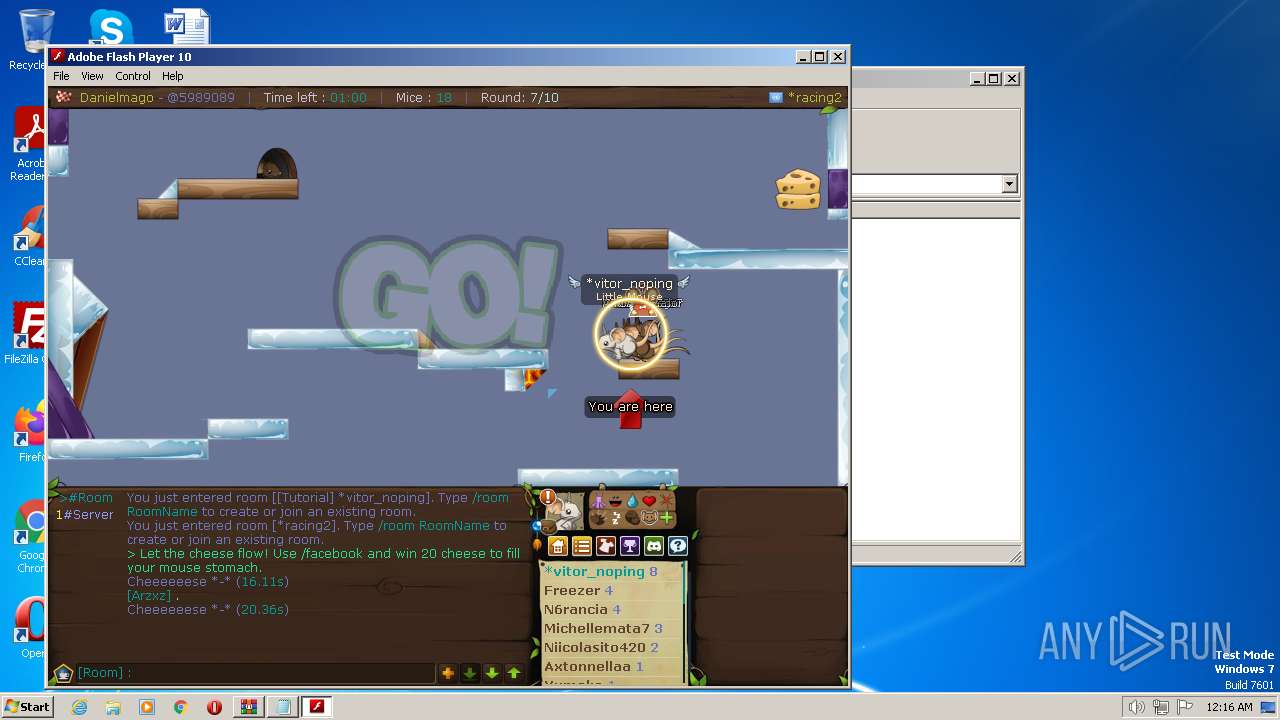
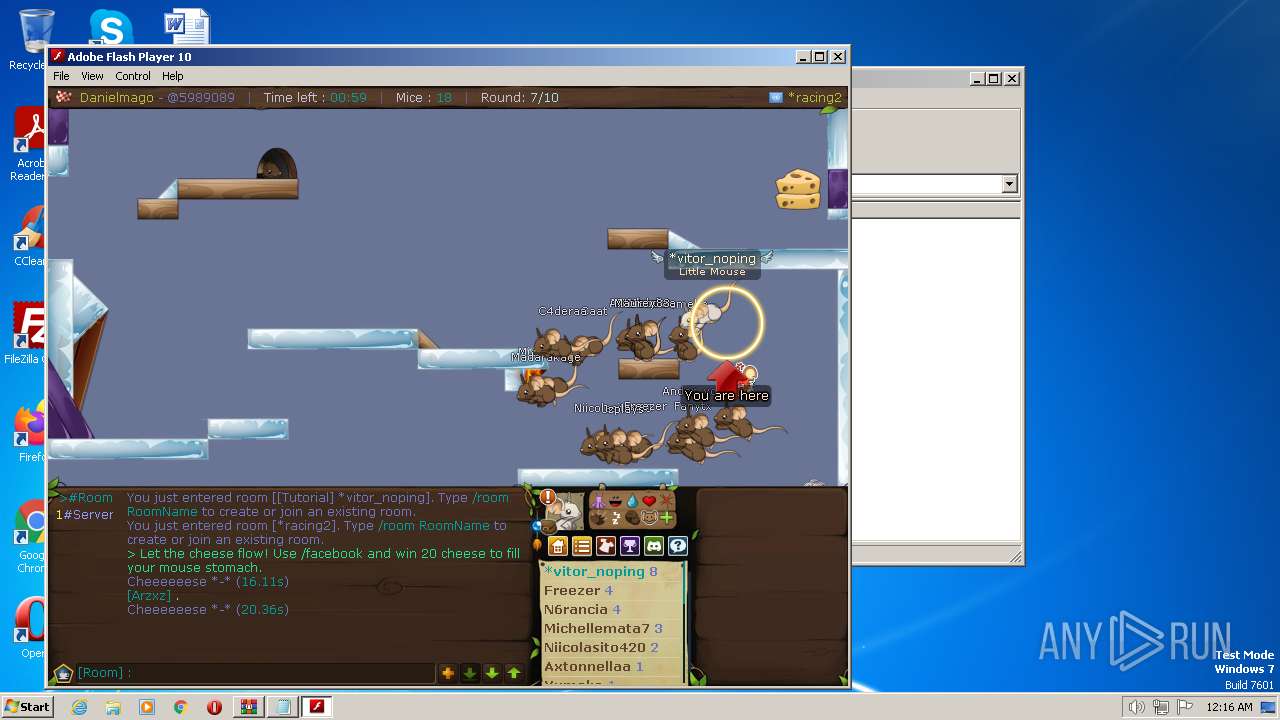
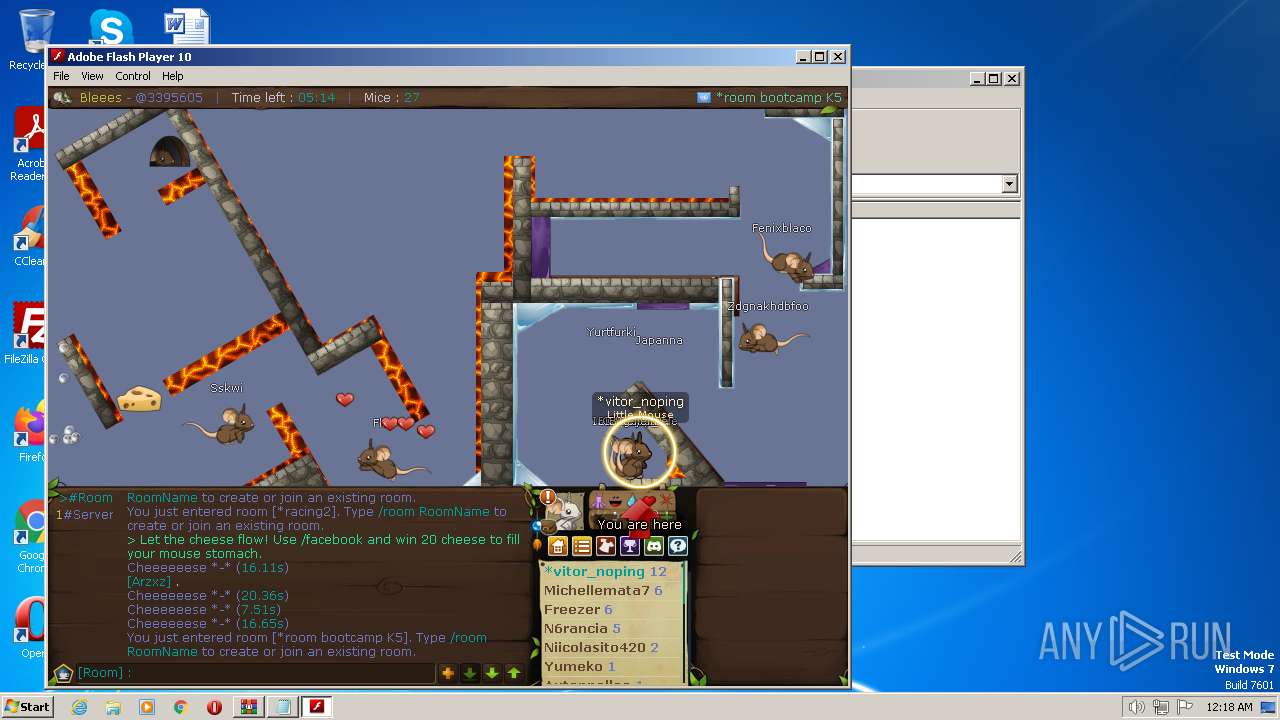
| 1492 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1352.13655\test2333\Adobe.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1352.13655\test2333\Adobe.exe | WinRAR.exe | ||||||||||||
User: admin Company: Adobe Systems, Inc. Integrity Level: MEDIUM Description: Adobe Flash Player 10.3 r183 Exit code: 0 Version: 10,3,183,90 Modules
| |||||||||||||||
| 1652 | "C:\Windows\system32\osk.exe" | C:\Windows\System32\osk.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Accessibility On-Screen Keyboard Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2984 | "C:\Windows\system32\osk.exe" | C:\Windows\System32\osk.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Accessibility On-Screen Keyboard Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3860 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa1352.11998\Documento sem título.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4080 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
15 464
Read events
15 372
Write events
86
Delete events
6
Modification events
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
2
Suspicious files
248
Text files
106
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
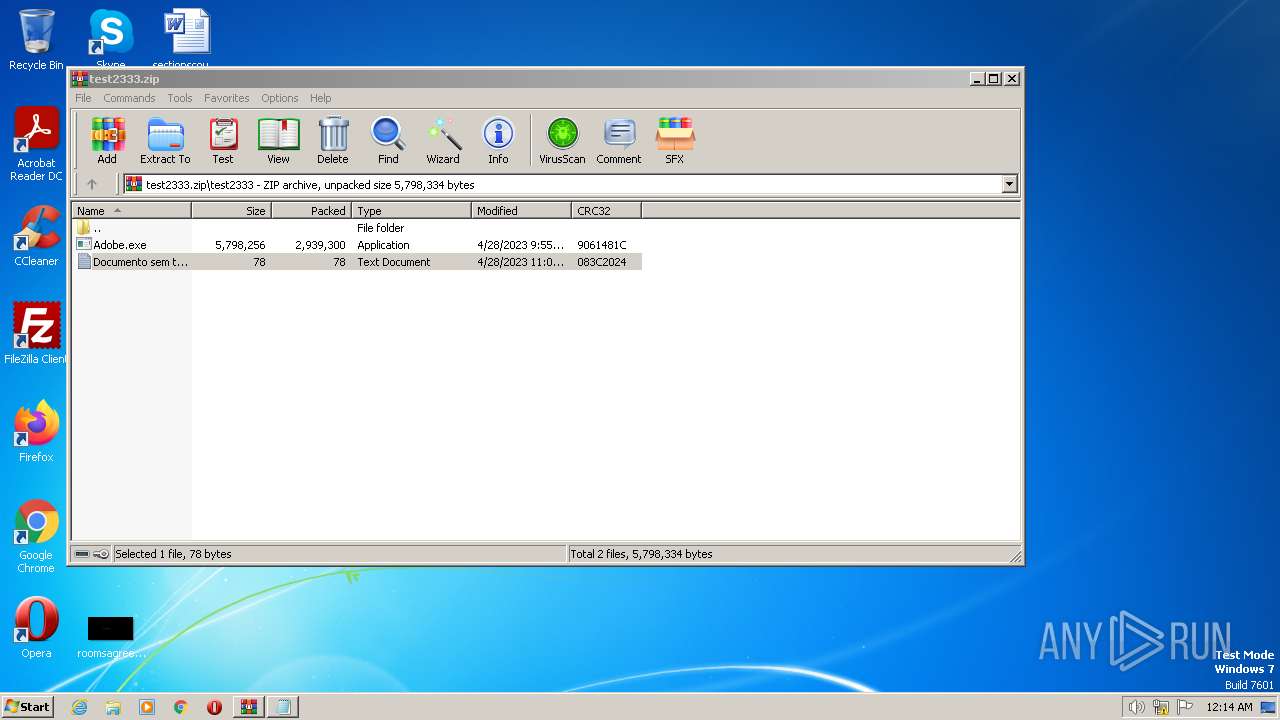
| 1352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1352.13655\test2333\Adobe.exe | executable | |
MD5:6F4432D4272293B6E829EC8A7150BBE5 | SHA256:3A5F87AFA90DA2245E3714FECB56780DC5AC02DEB101C2E4B8B83F0958C89CDC | |||
| 1352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa1352.11998\Documento sem título.txt | text | |
MD5:ECB9C61621D7820BE1D1ABEA5F5AAEEC | SHA256:5CD345F846D4A9014A2FD720C61AC40931B761135027810AC2890048F48CF98F | |||
| 1492 | Adobe.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:A5A75B9854AC1411A3116E9405EB0236 | SHA256:0BF76A2BB5DA13FB57DFBC68D9A0FBAEE117A4CFF08B83B554DCFF582764D697 | |||
| 1352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1352.13655\test2333\Documento sem título.txt | text | |
MD5:ECB9C61621D7820BE1D1ABEA5F5AAEEC | SHA256:5CD345F846D4A9014A2FD720C61AC40931B761135027810AC2890048F48CF98F | |||
| 1492 | Adobe.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:F94370B1B3D6EB3C8086C92EC02D8D13 | SHA256:81506E690465A45AC1F155A1A93EE45485E18AA370E65593179D323A5EF7A52D | |||
| 1492 | Adobe.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:631C1423E6AA5183FEAB01EEFD5FEC3C | SHA256:AB588D8C66EE594693916029B665D62B5B1B1C8ABFDAAE1CE515B2A113D3F233 | |||
| 1492 | Adobe.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sol | binary | |
MD5:4E442C66F85325FE25C83EE8855432CA | SHA256:C1F7F9394B37899EC9EFE36DD2C26C80837F357D86F20F67DC13F6491F0CFEA9 | |||
| 1492 | Adobe.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:024D9D87A9A7637BDEC89DA98DEB2155 | SHA256:D0B5319342E89E35FA31D7F1B870D7414E881705FBCAD531E5F5025D973DFA3C | |||
| 1492 | Adobe.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:19BF2A2C52C9FEC89689D71F4450B15F | SHA256:A87DBE7D275CD30F151BC8B168060D106EDC65FC157EB66DBC48758615F0311A | |||
| 1492 | Adobe.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F53EB4E574DE32C870452087D92DBEBB_A74B00104CB35A3EF31C35050C26C909 | binary | |
MD5:2876CEFFBC849524F23BBB78A062363C | SHA256:23F3CBE4BFCA5BCA8603BFF92F32029F1463715A7B62EF548F1F83E20C1BBEAD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
31
DNS requests
10
Threats
59
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
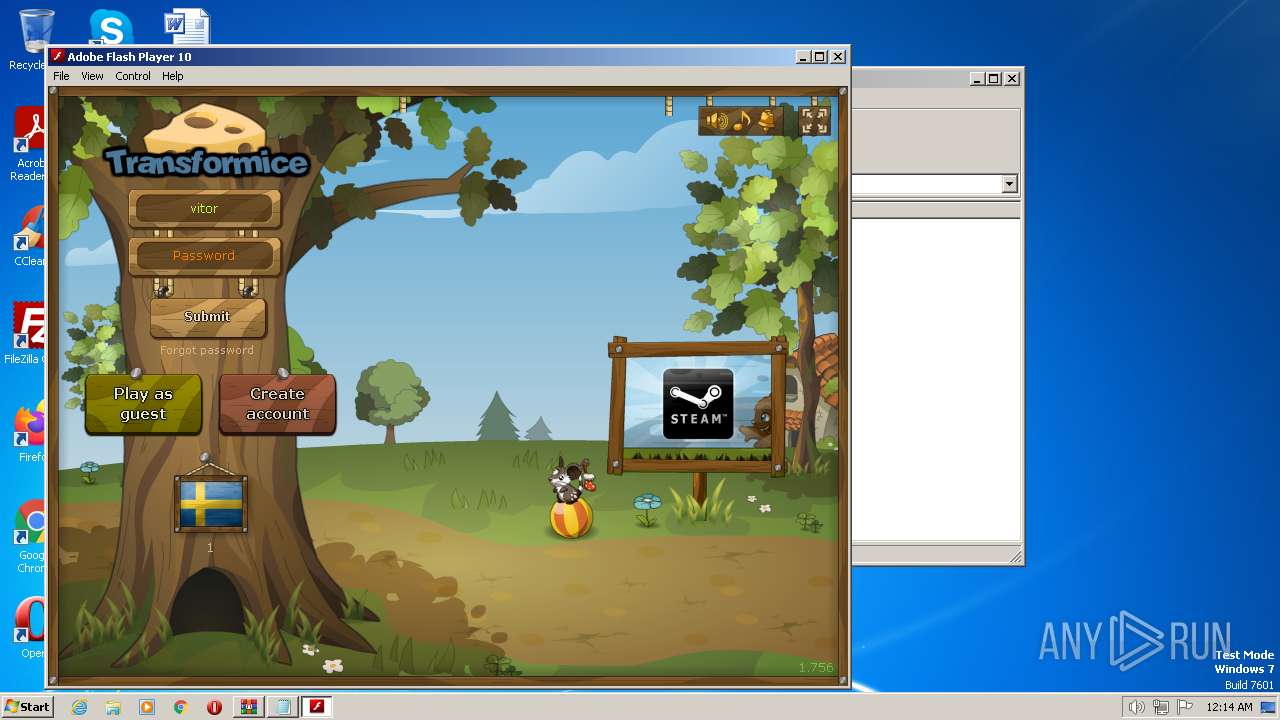
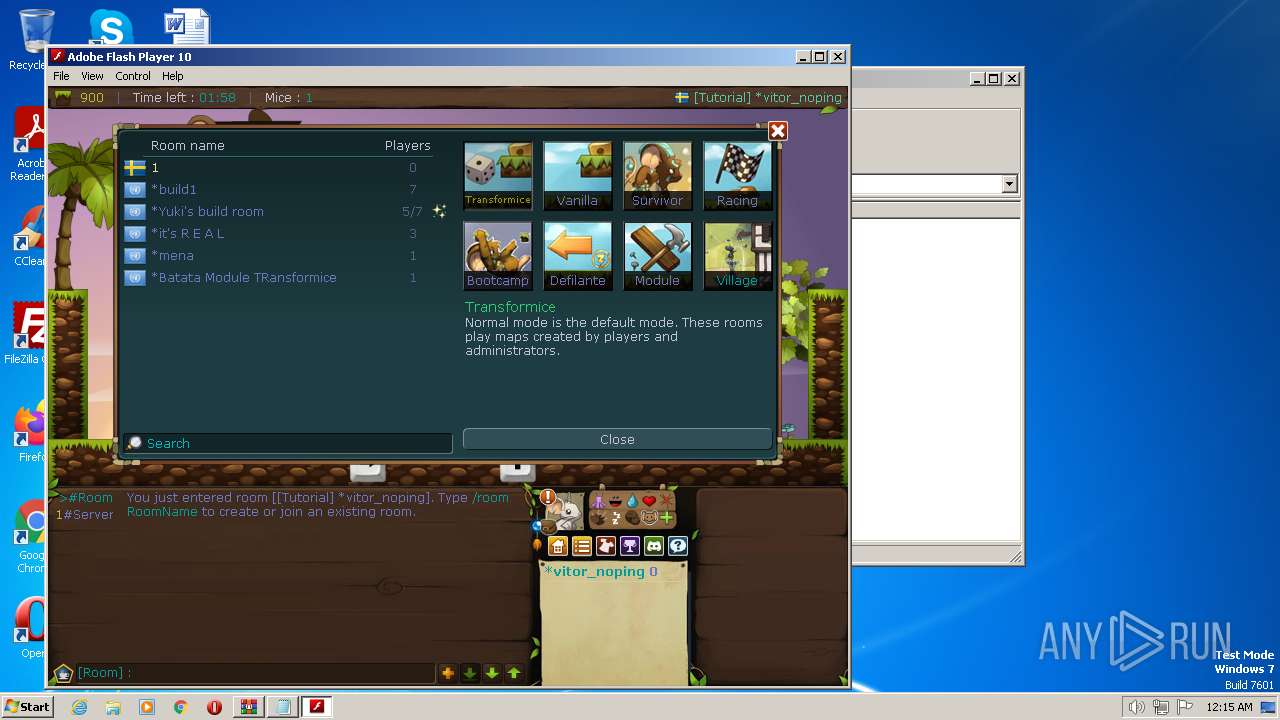
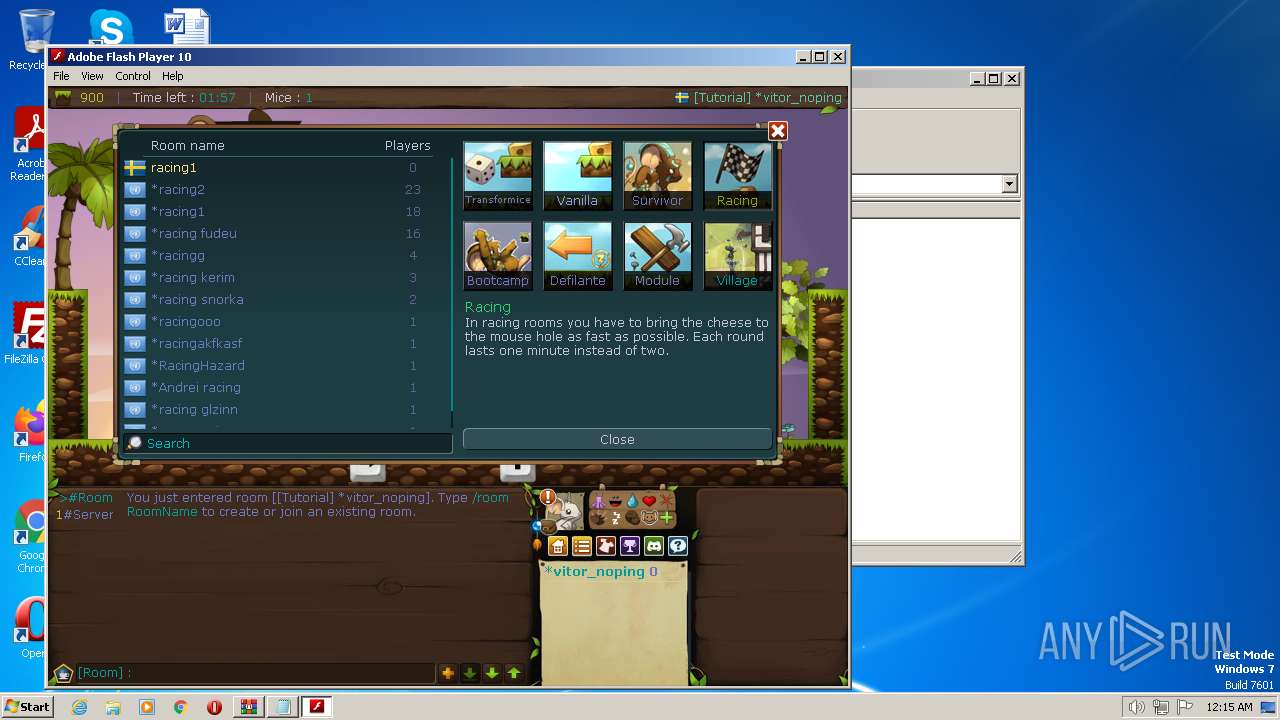
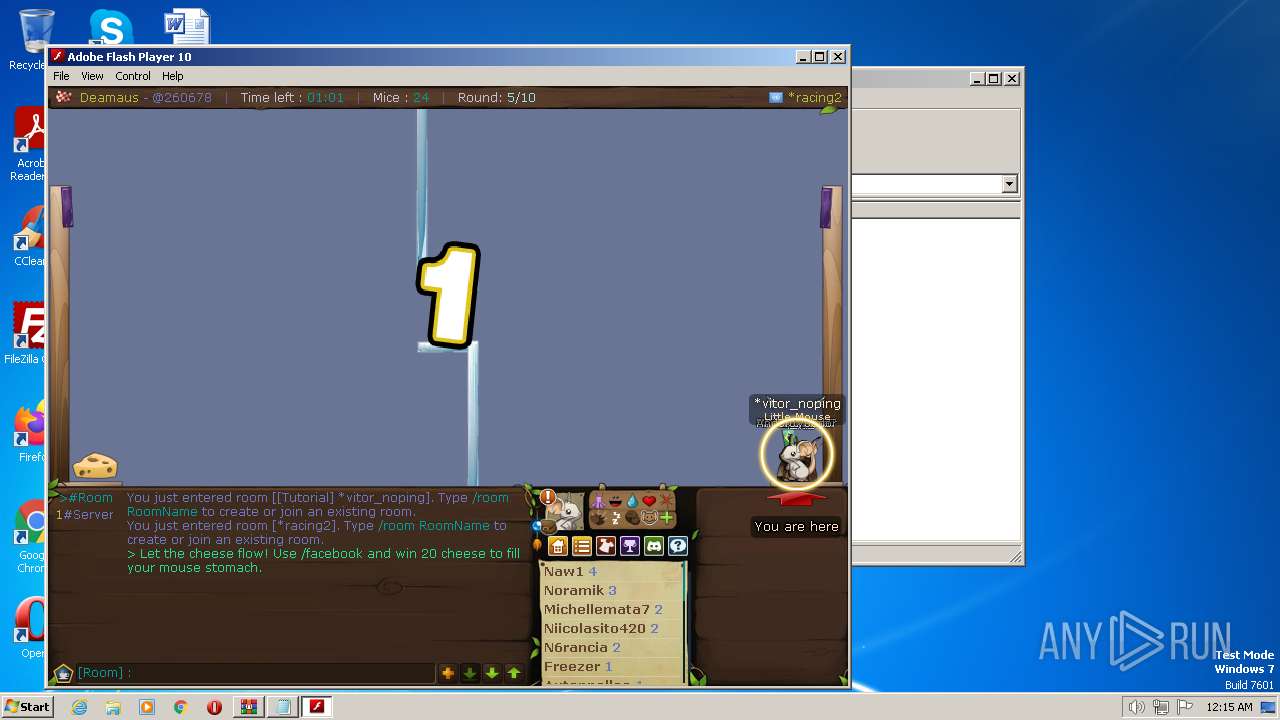
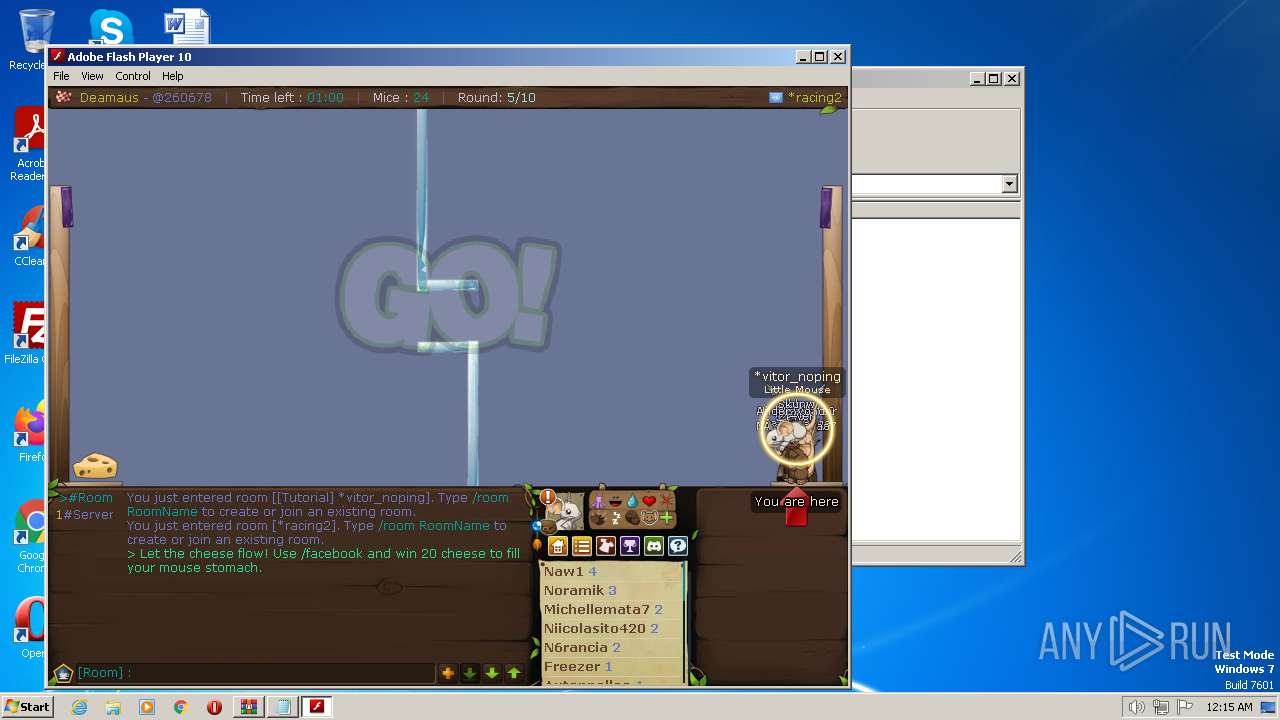
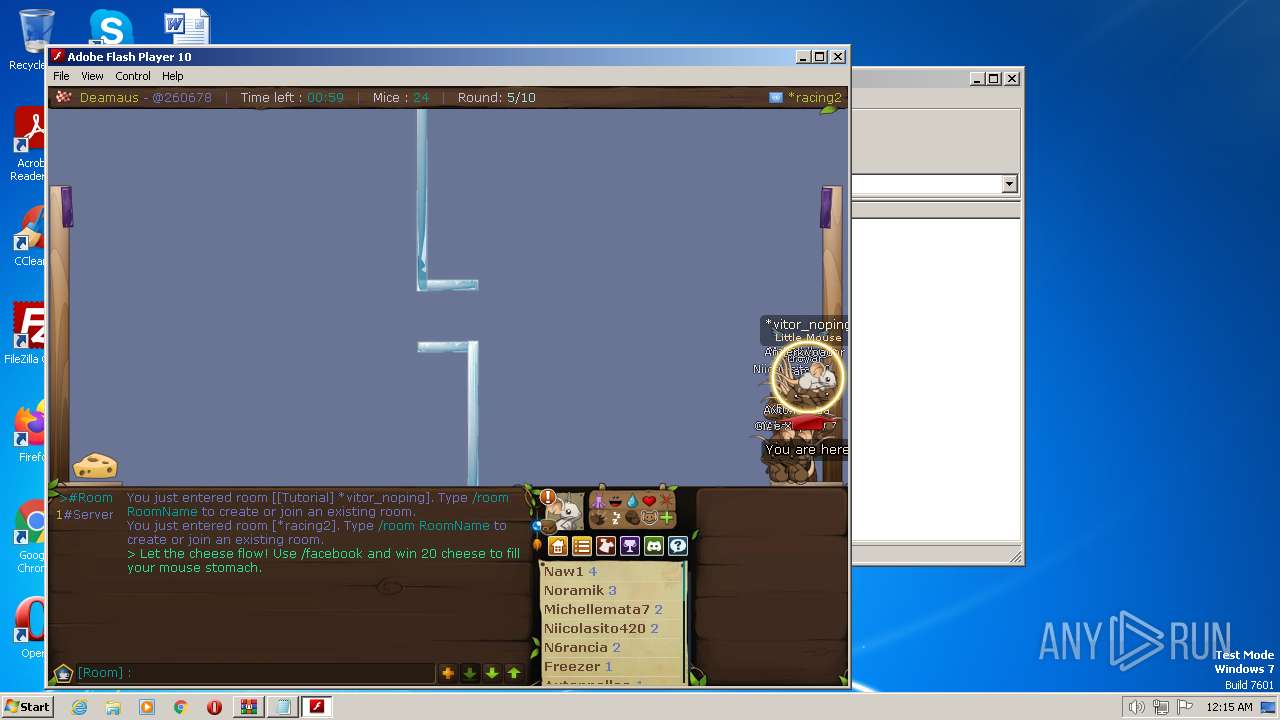
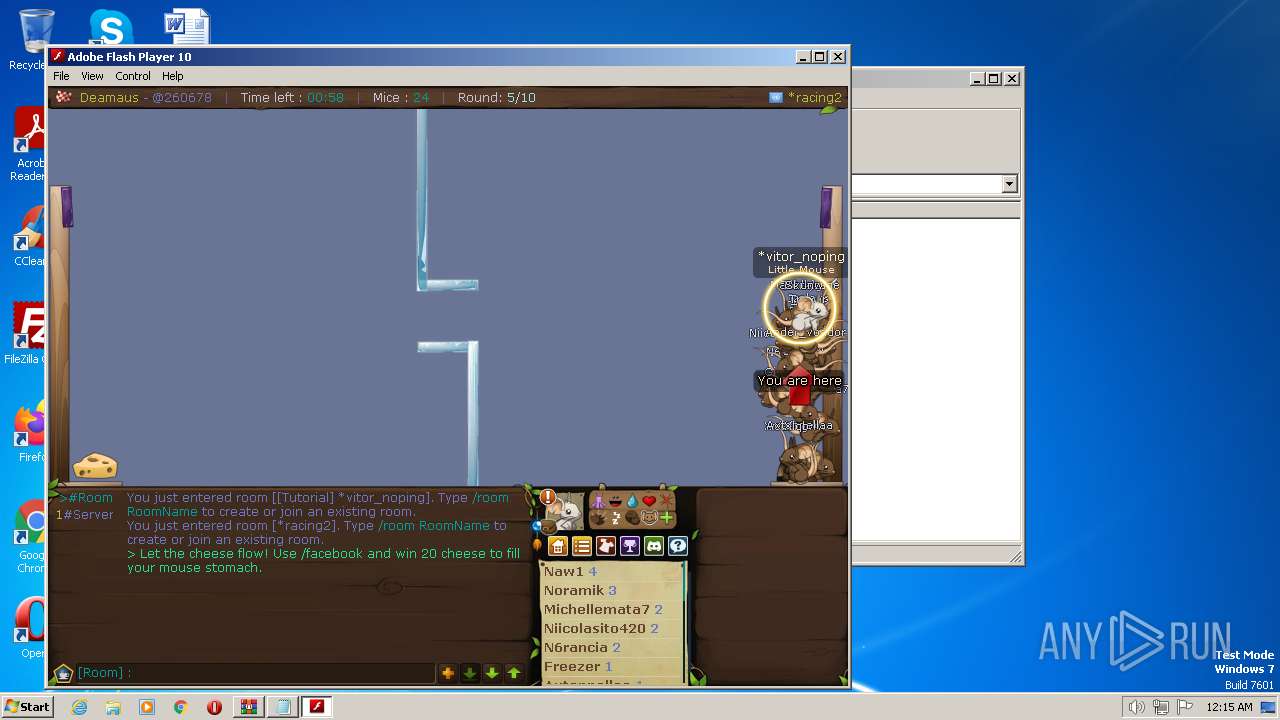
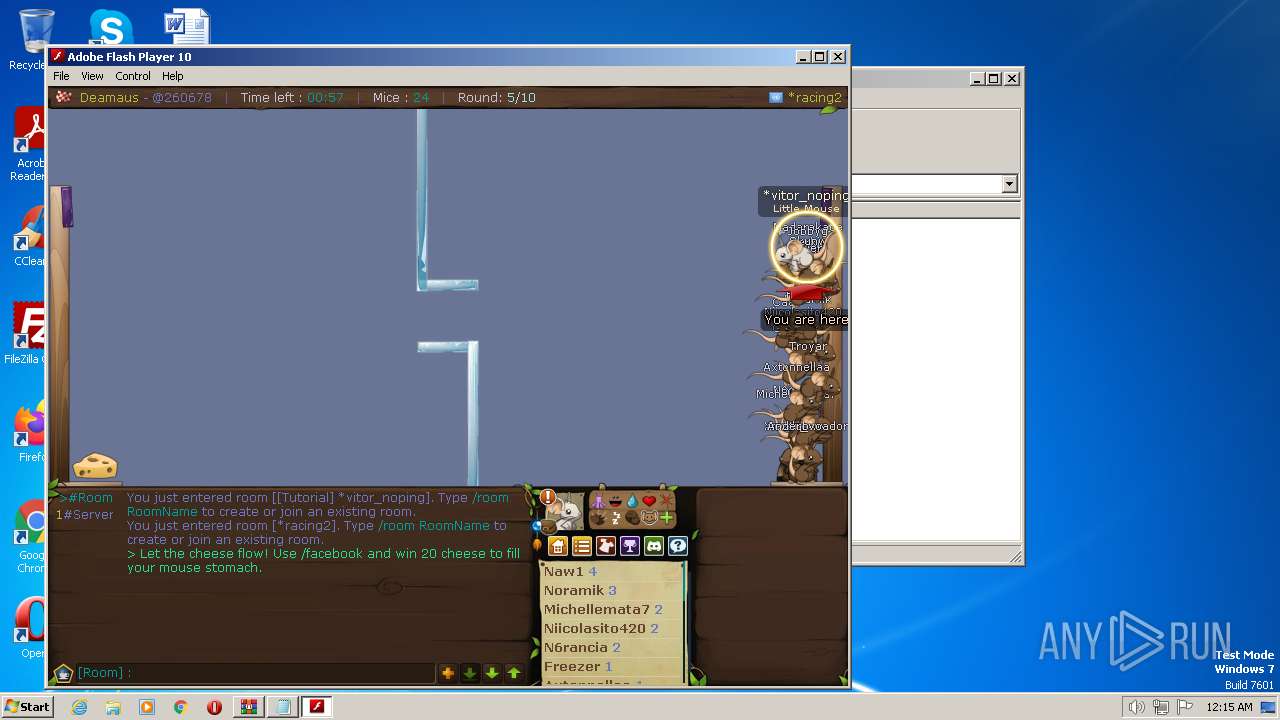
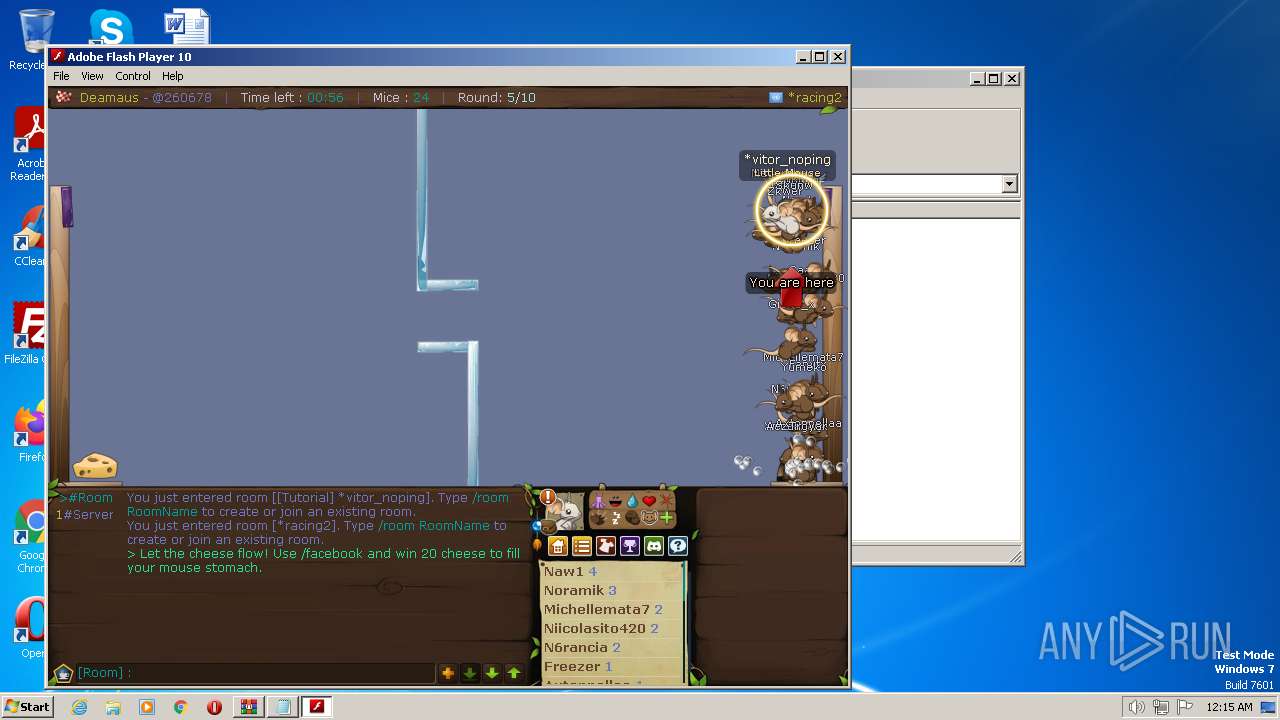
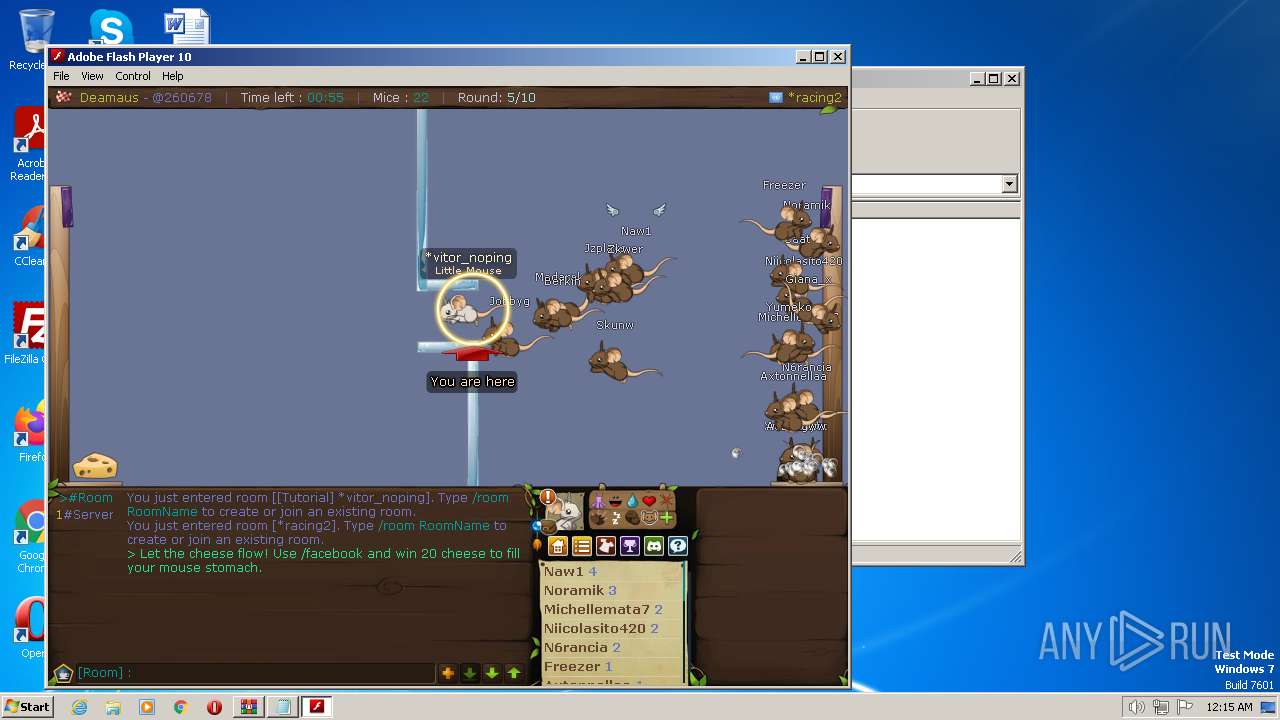
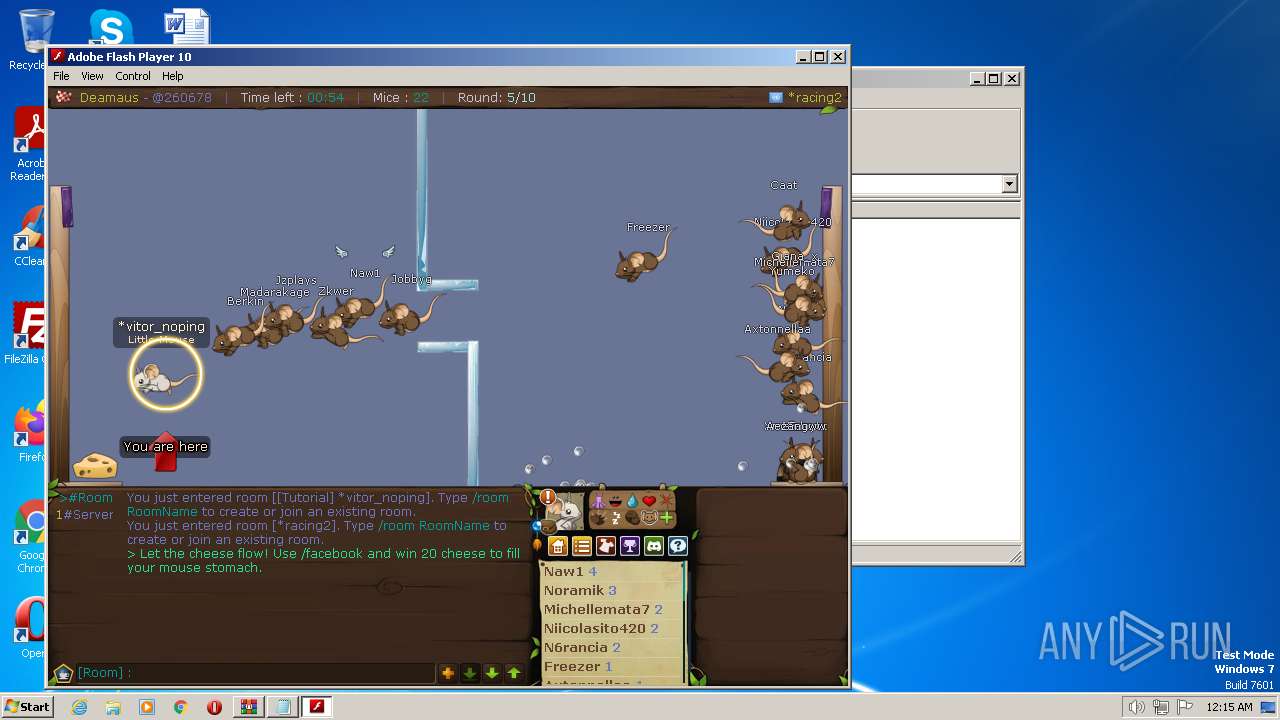
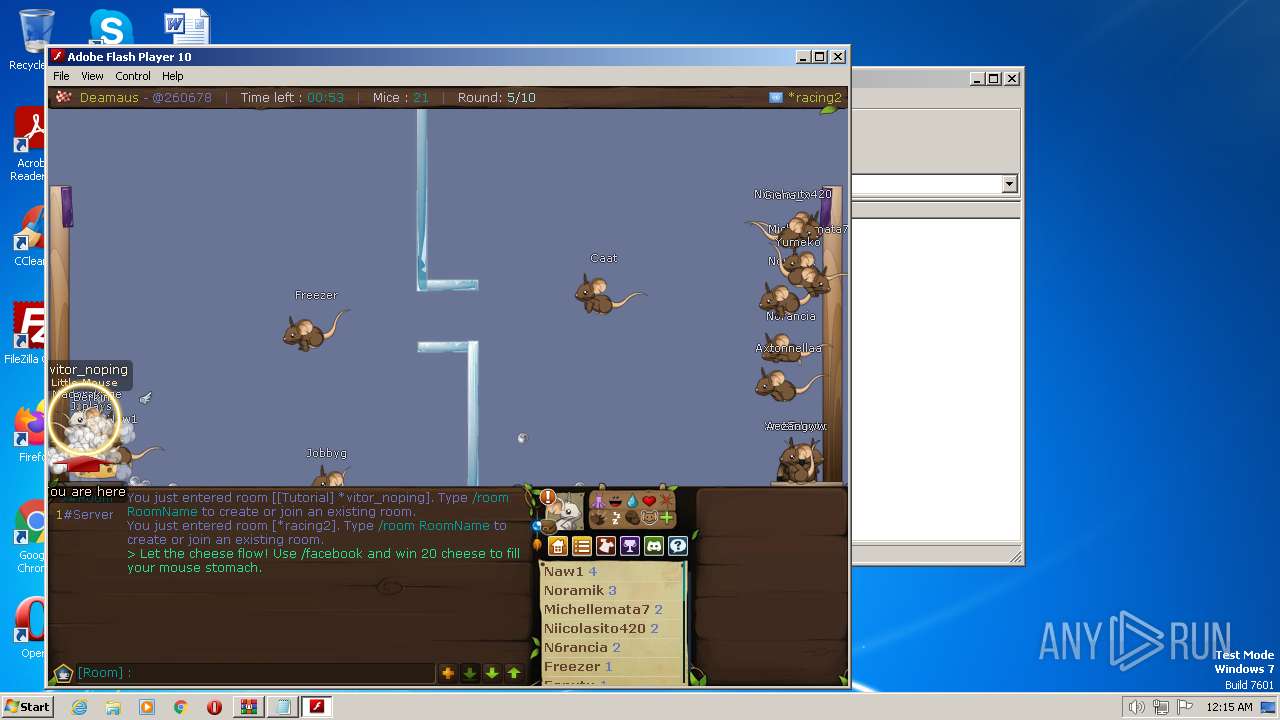
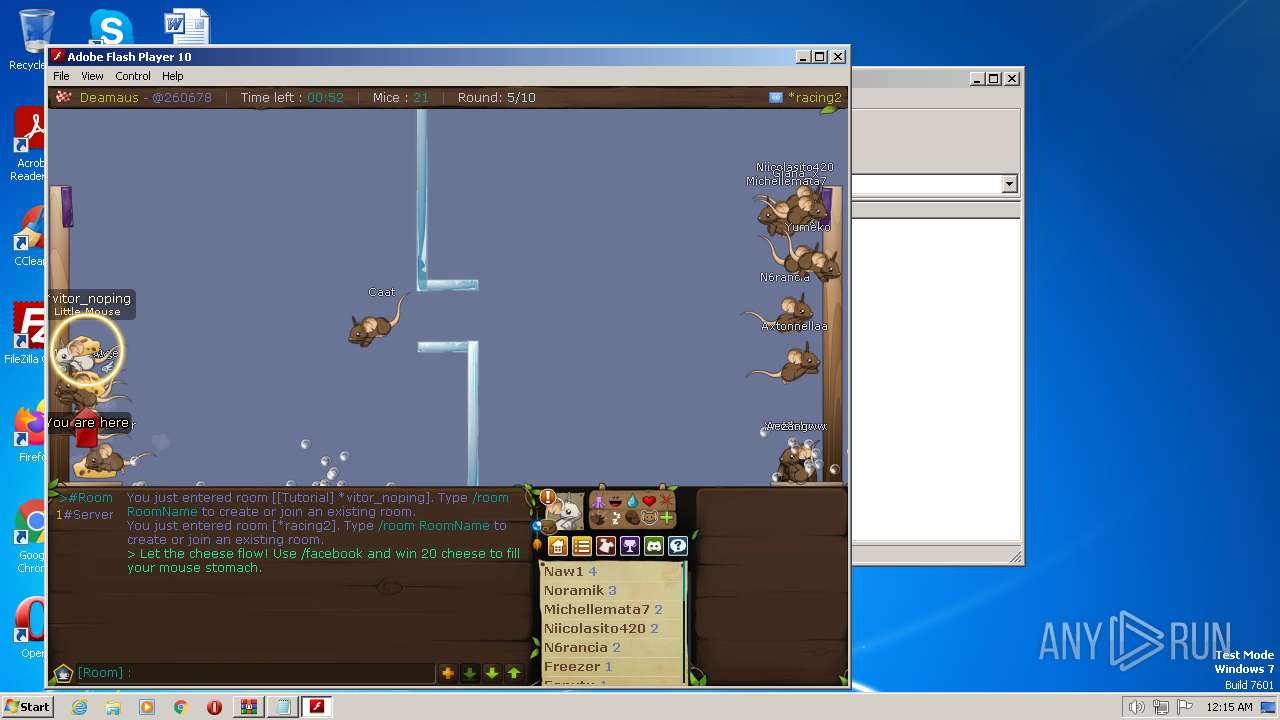
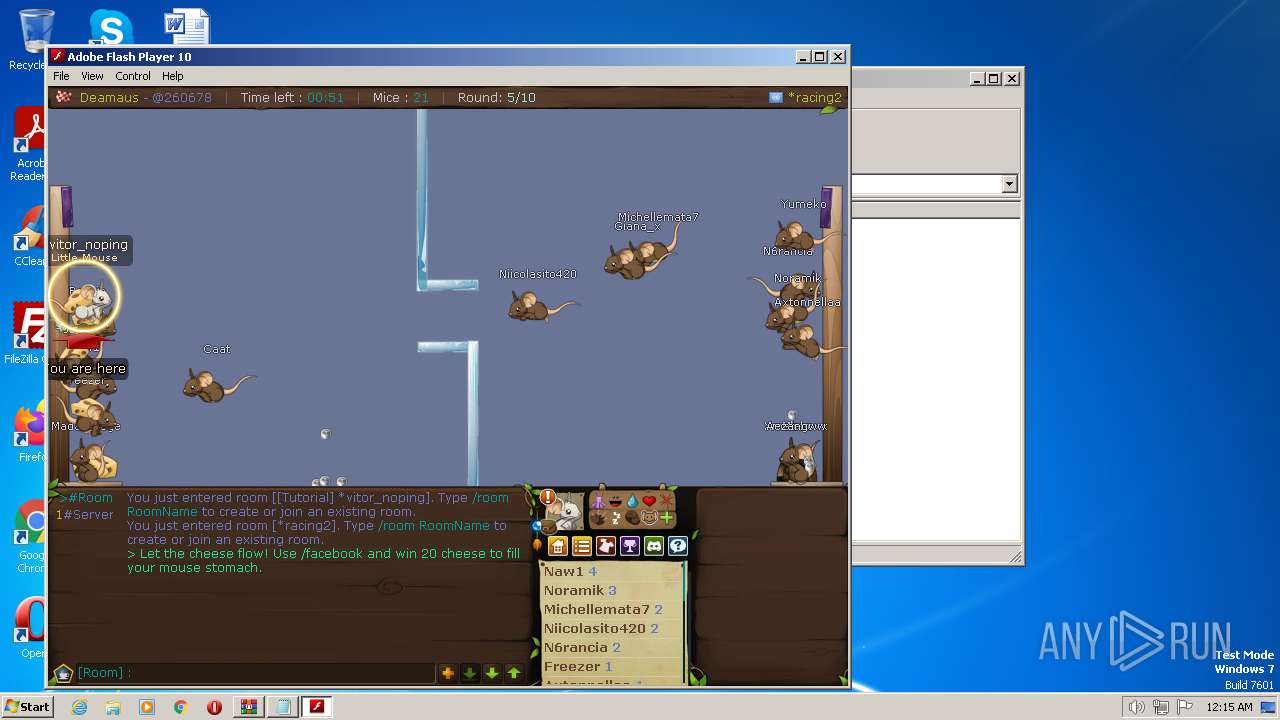
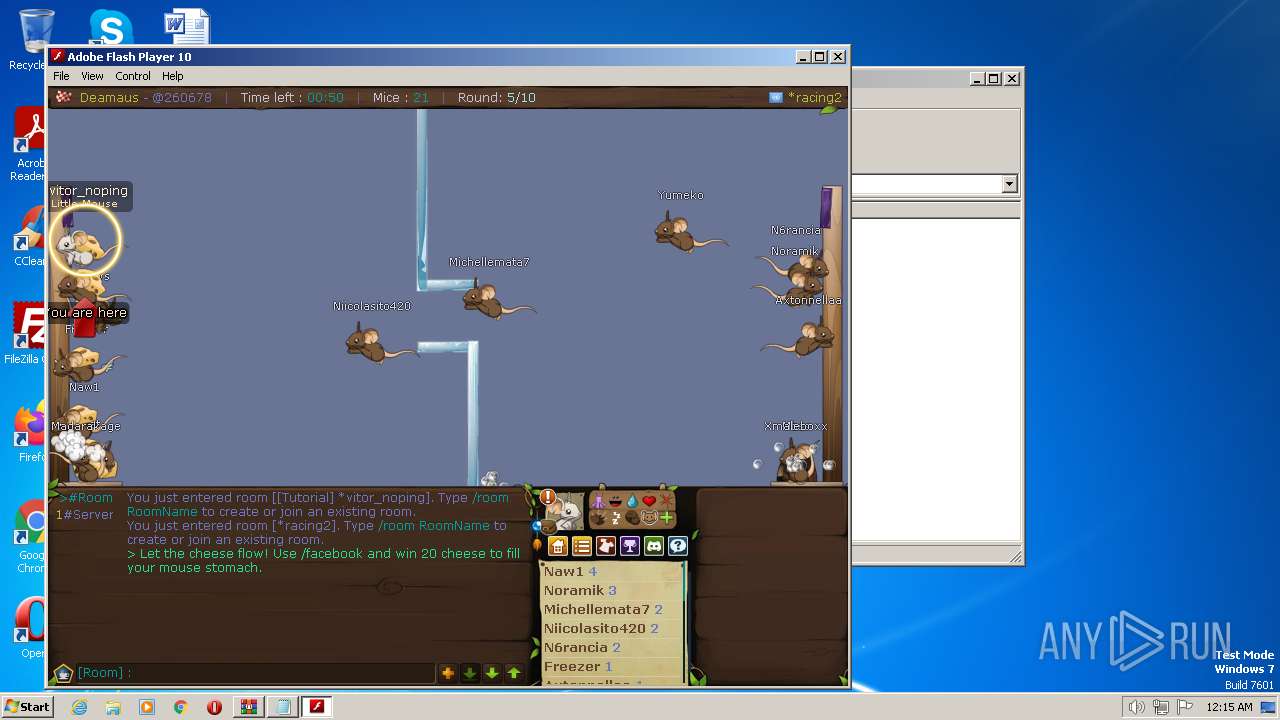
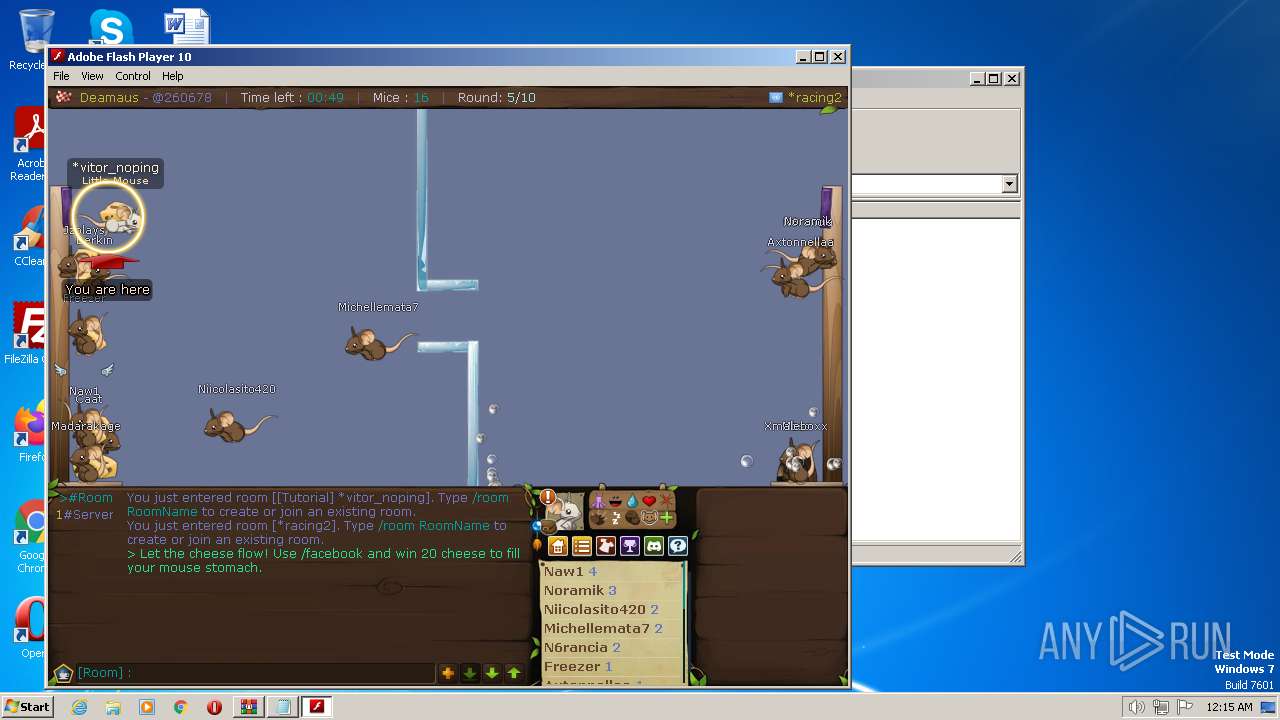
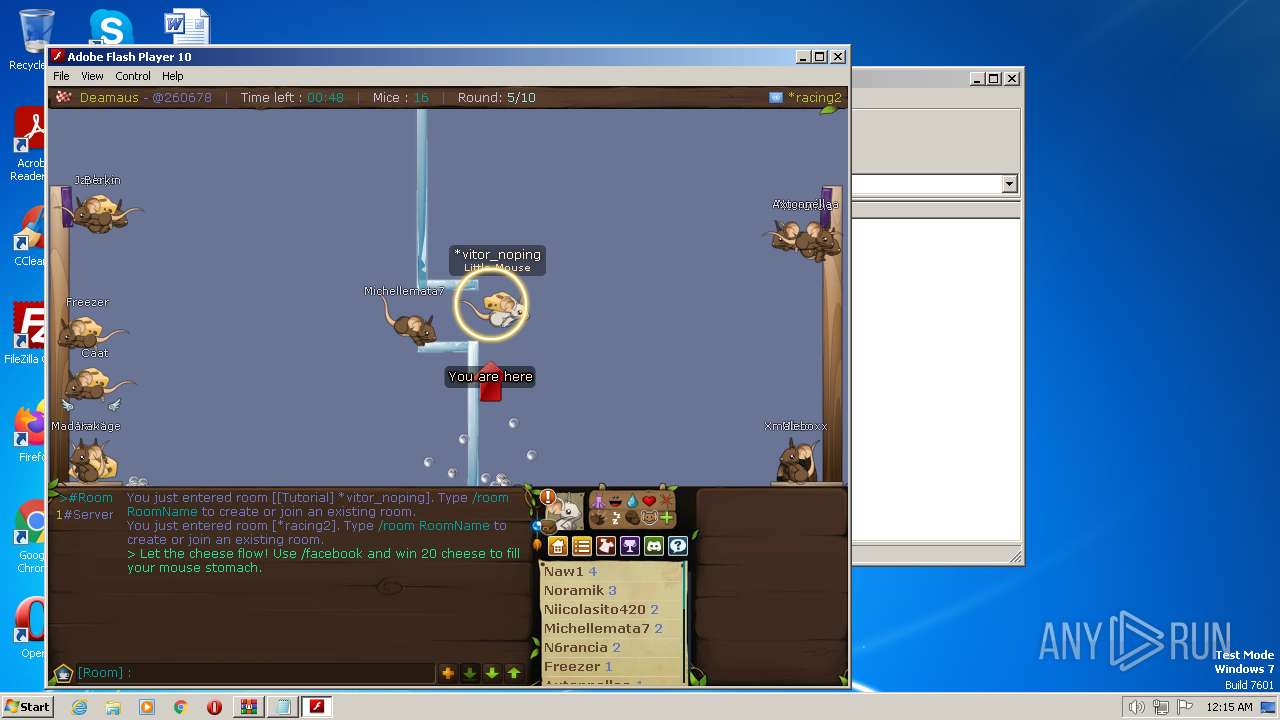
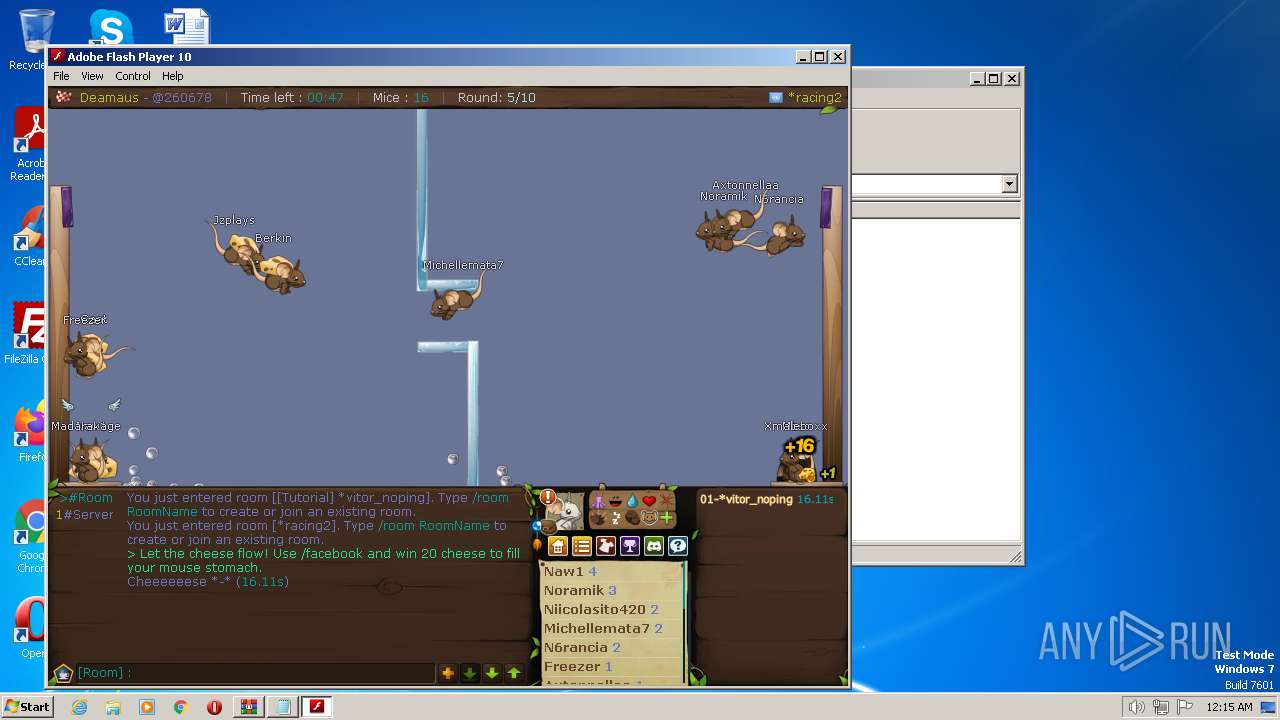
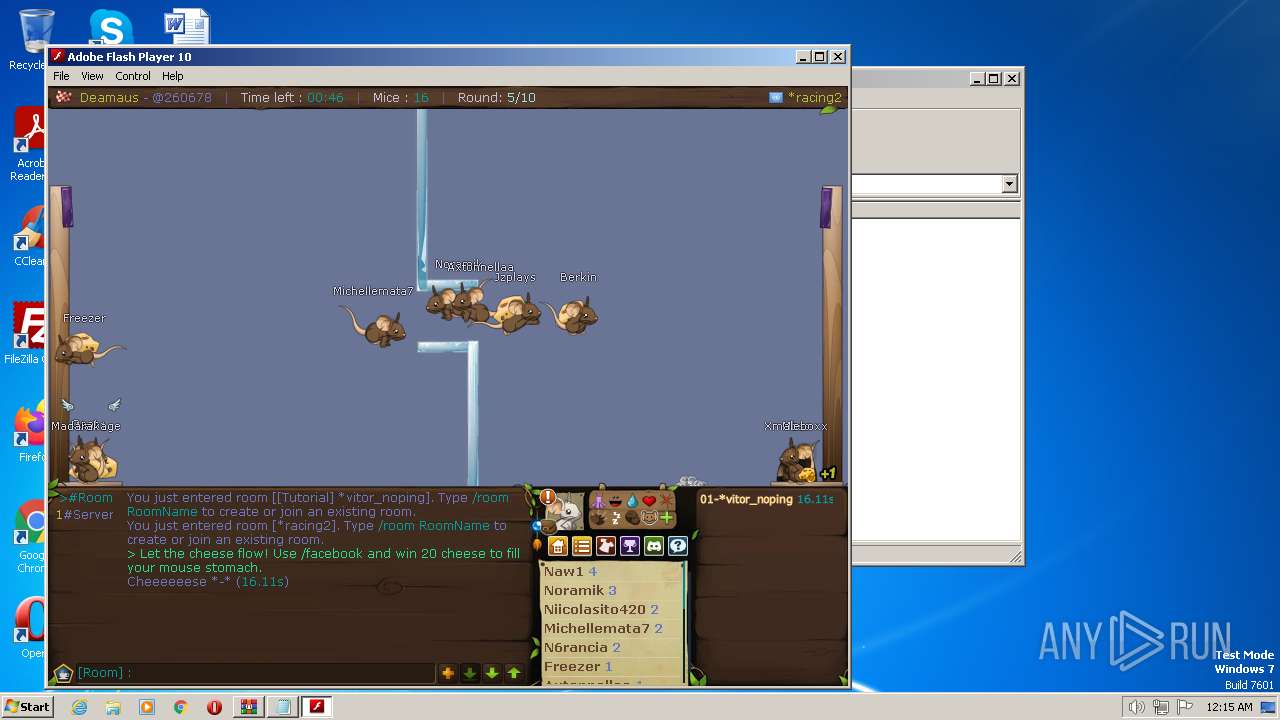
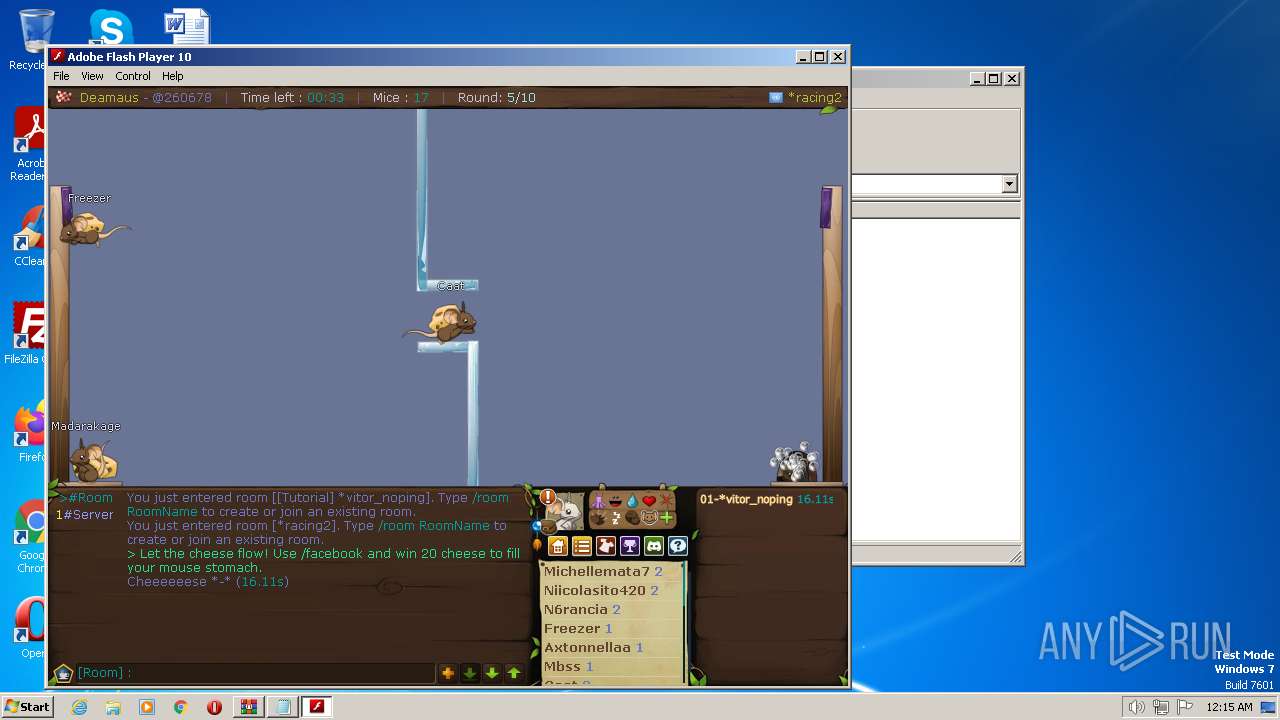
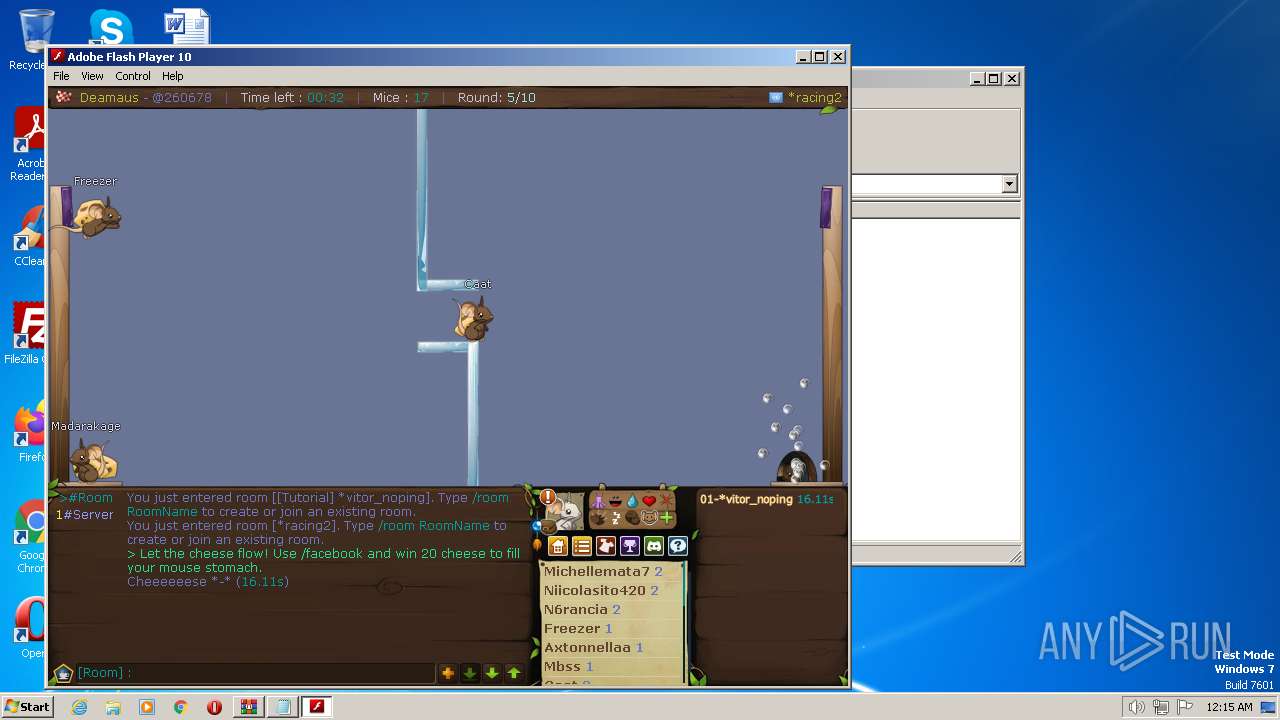
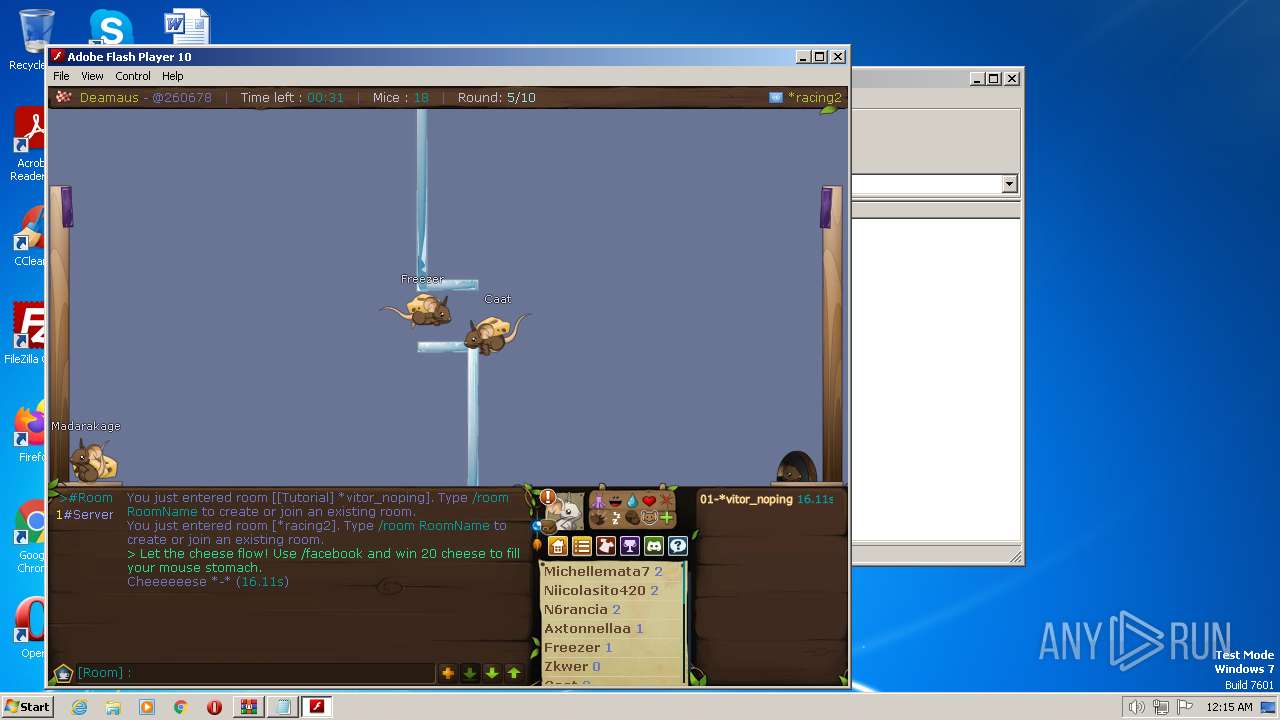
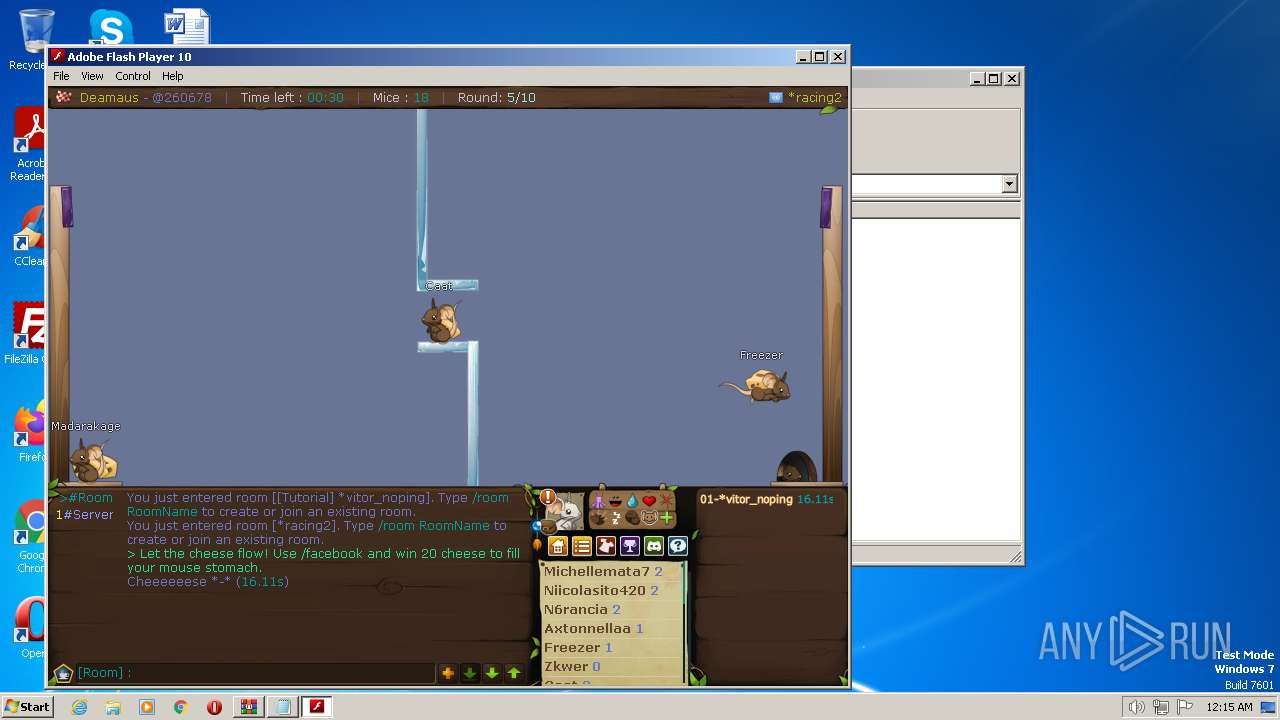
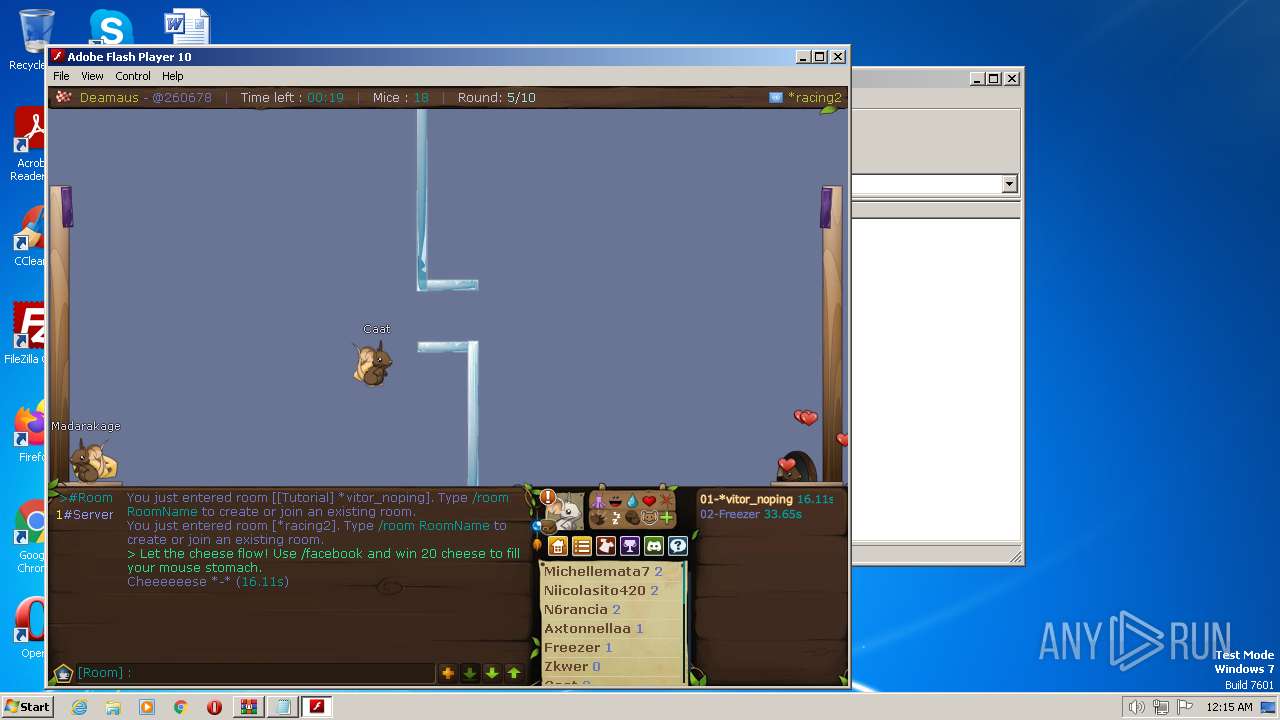
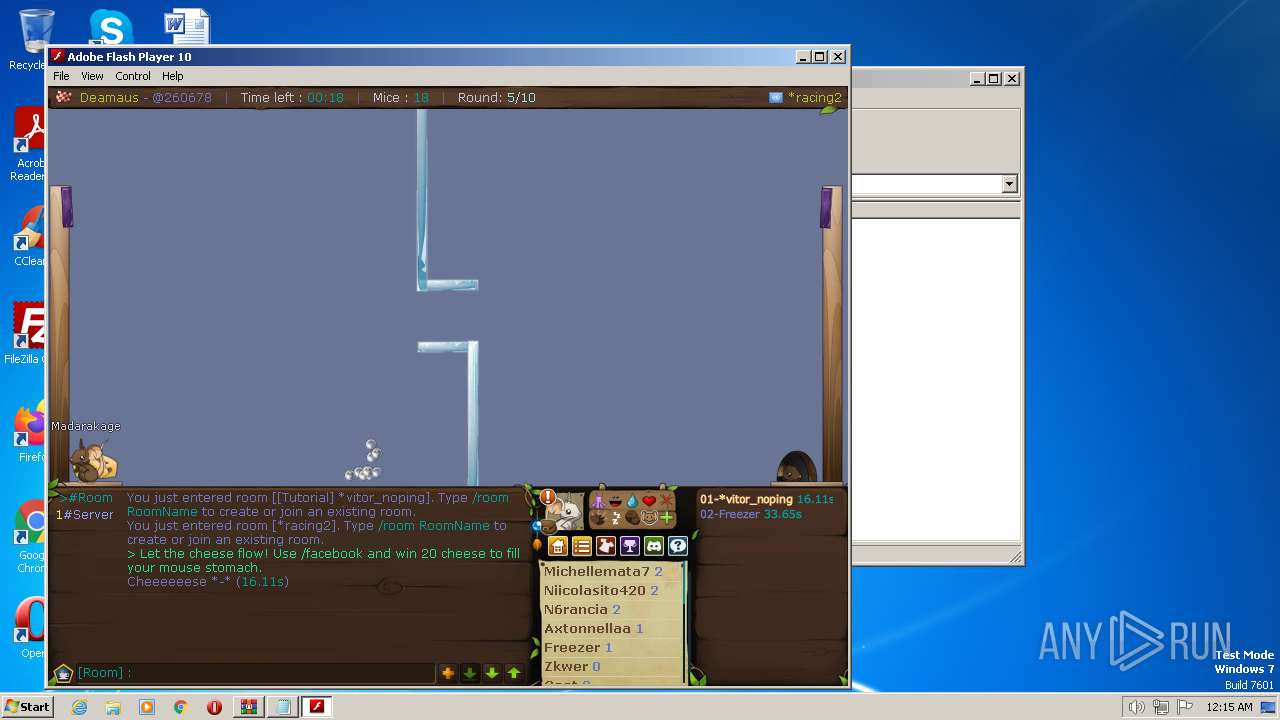
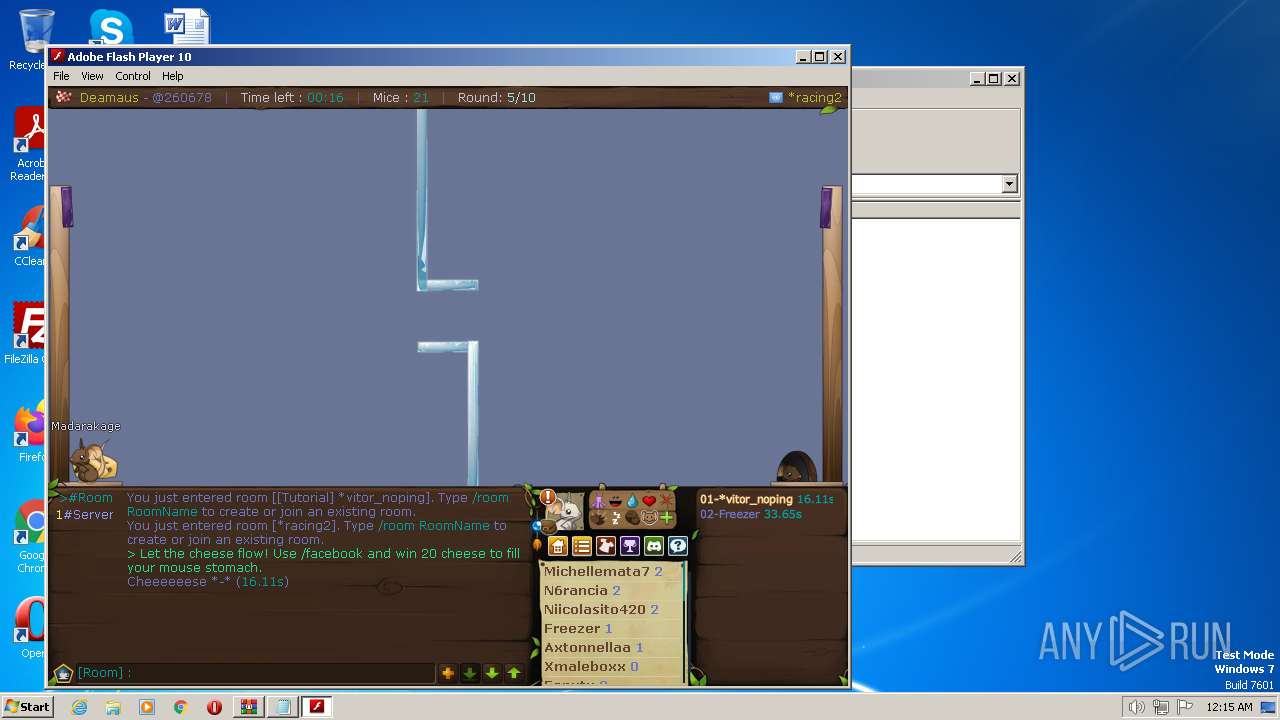
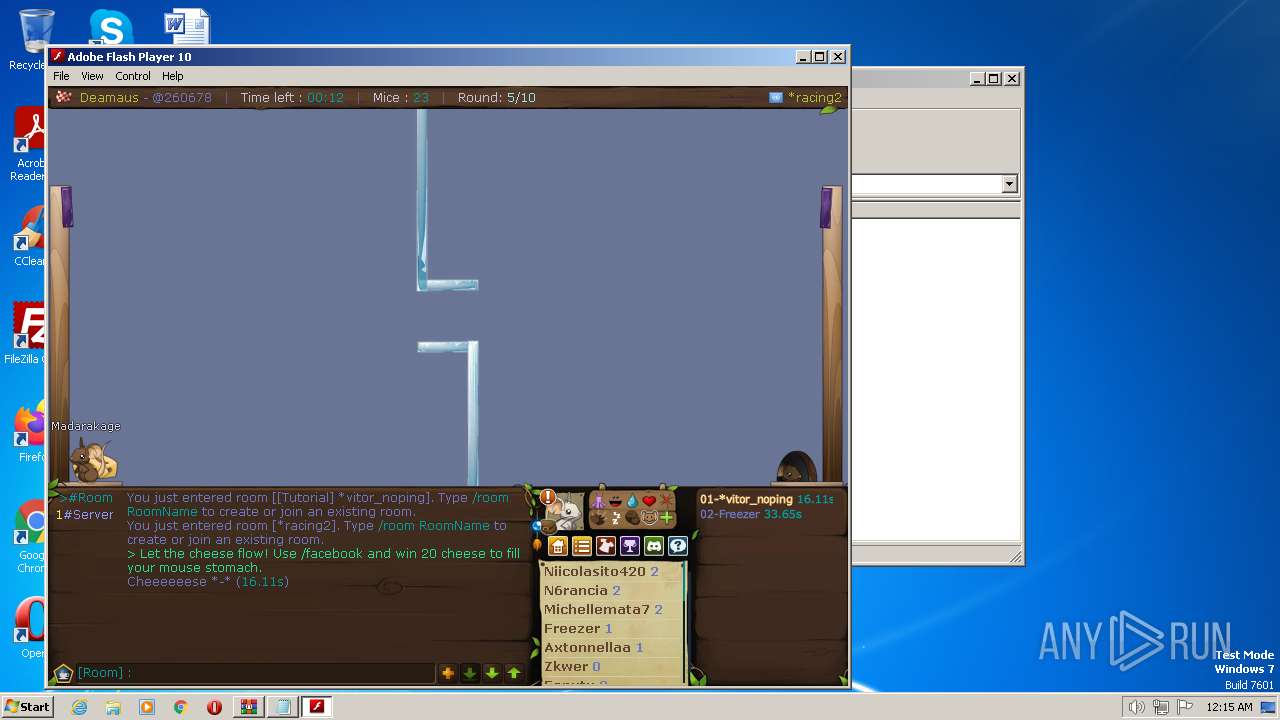
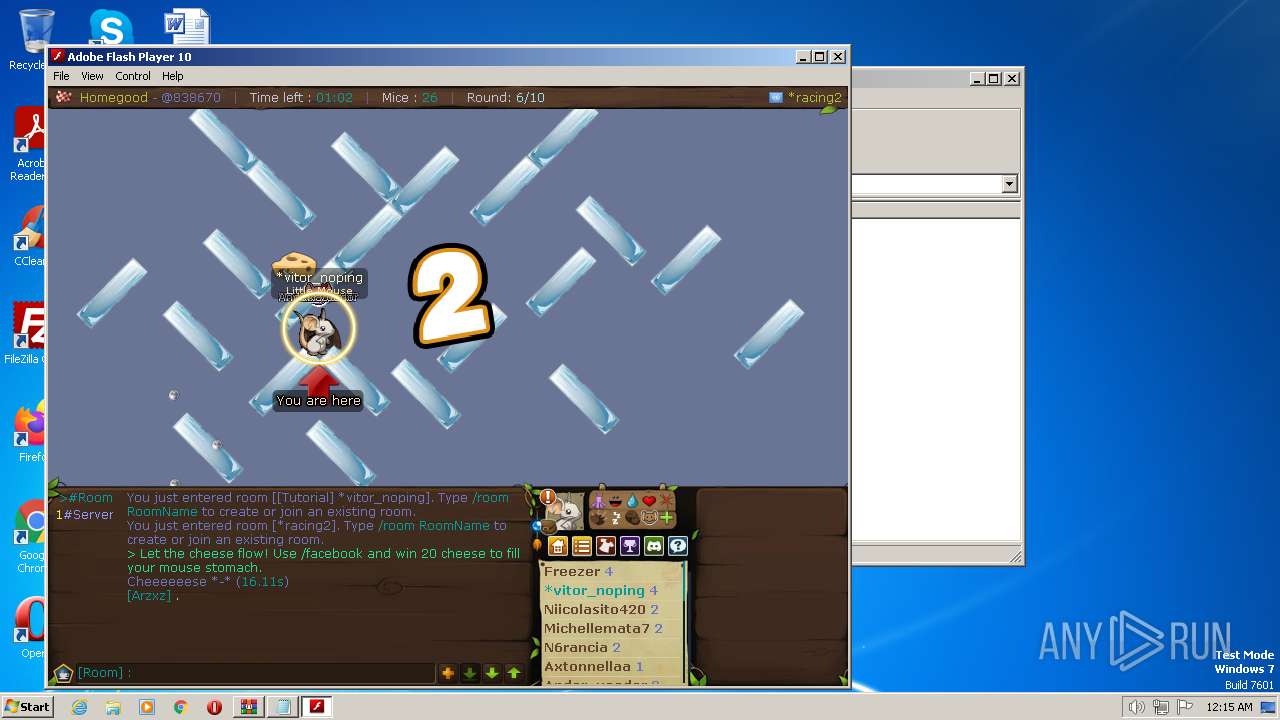
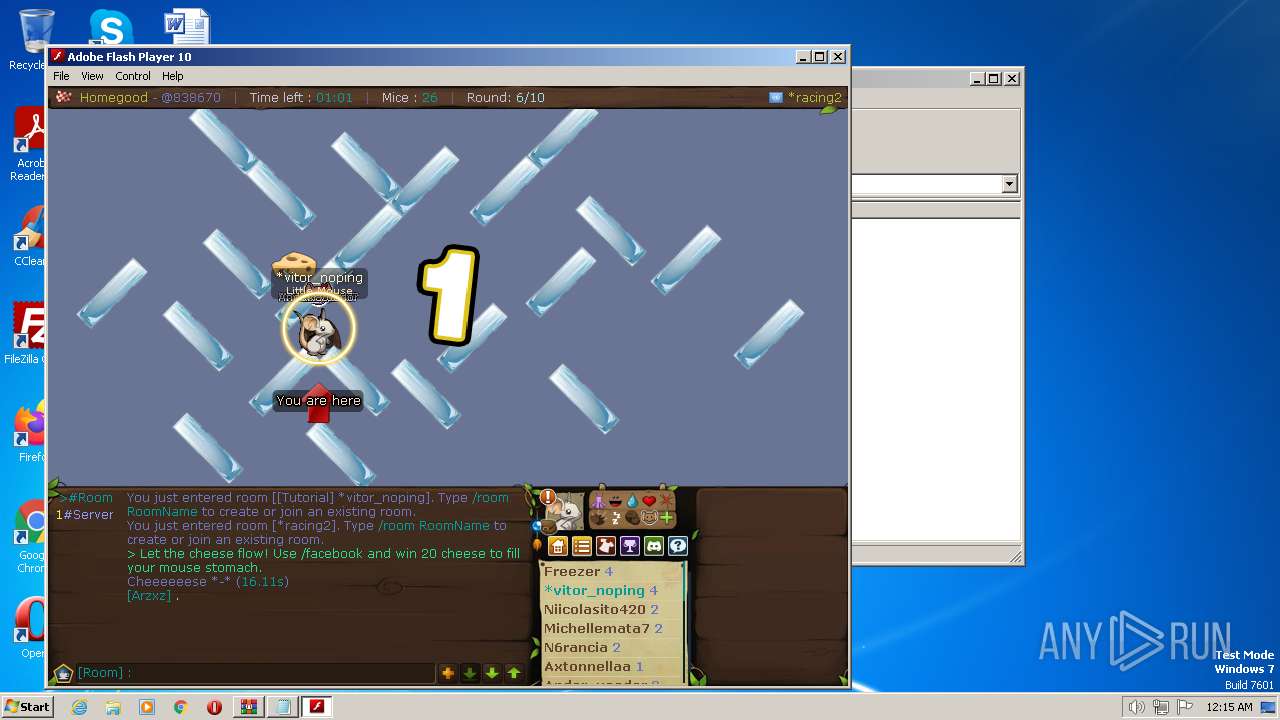
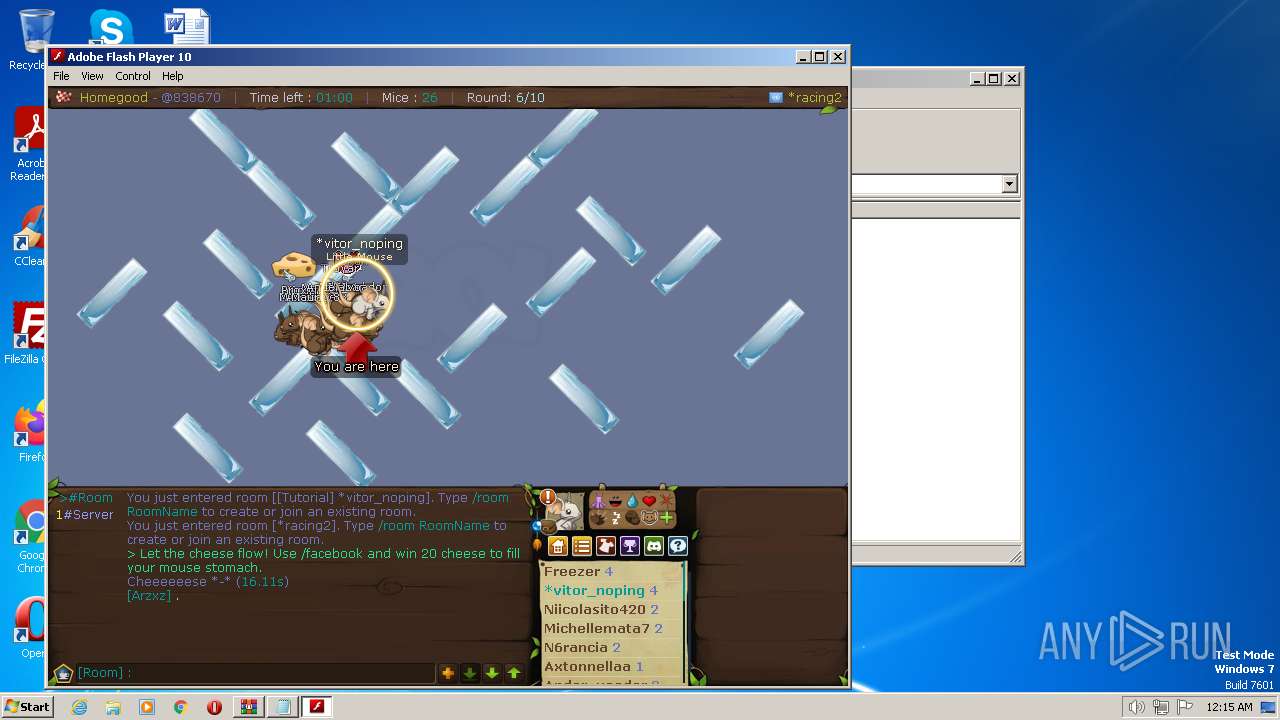
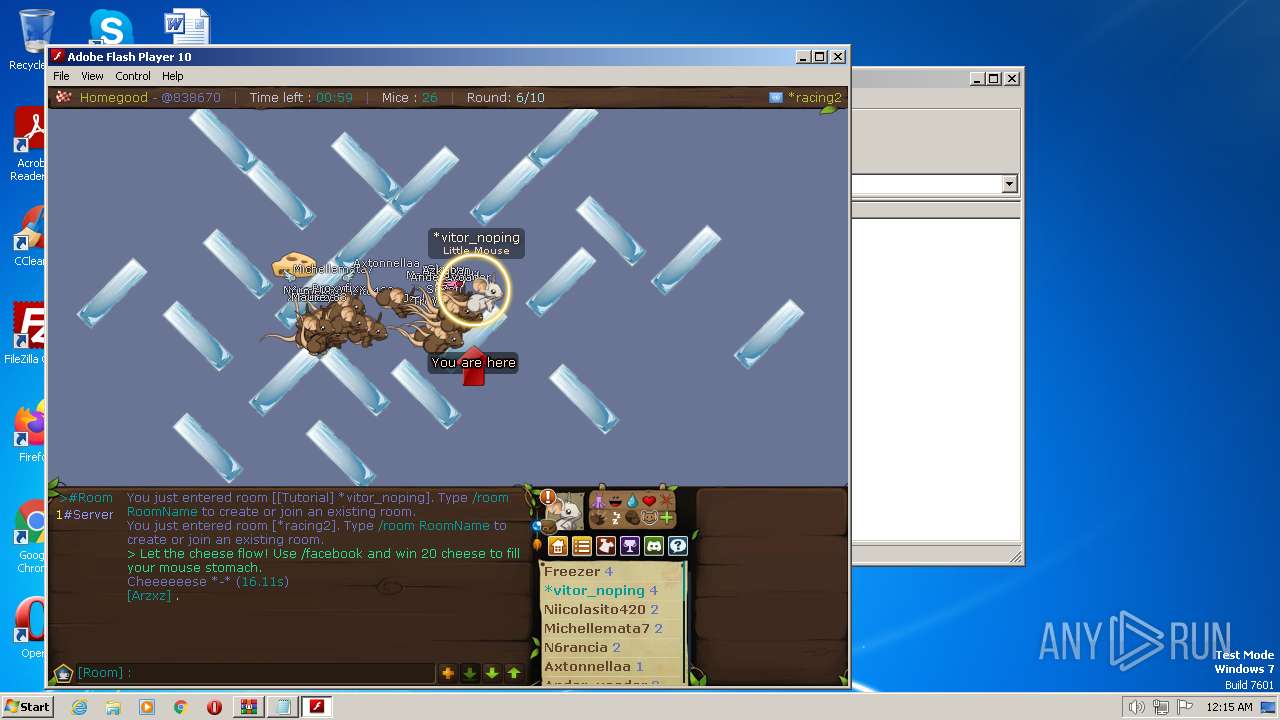
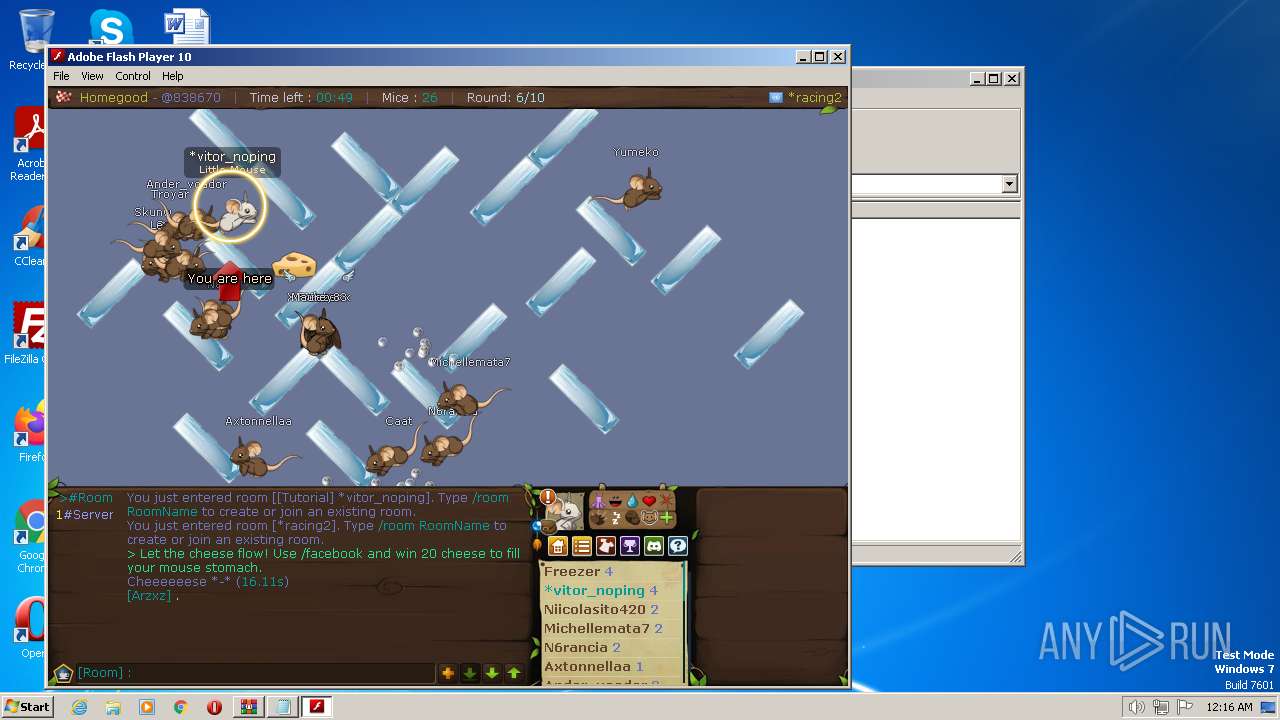
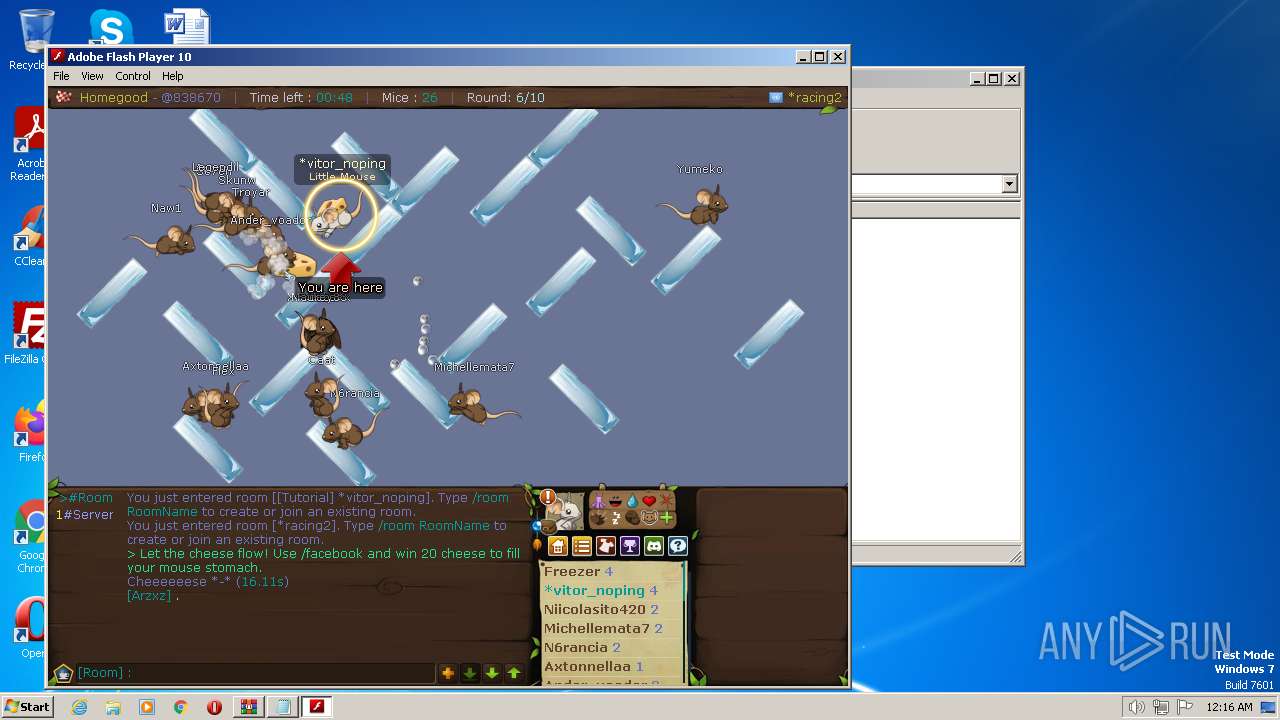
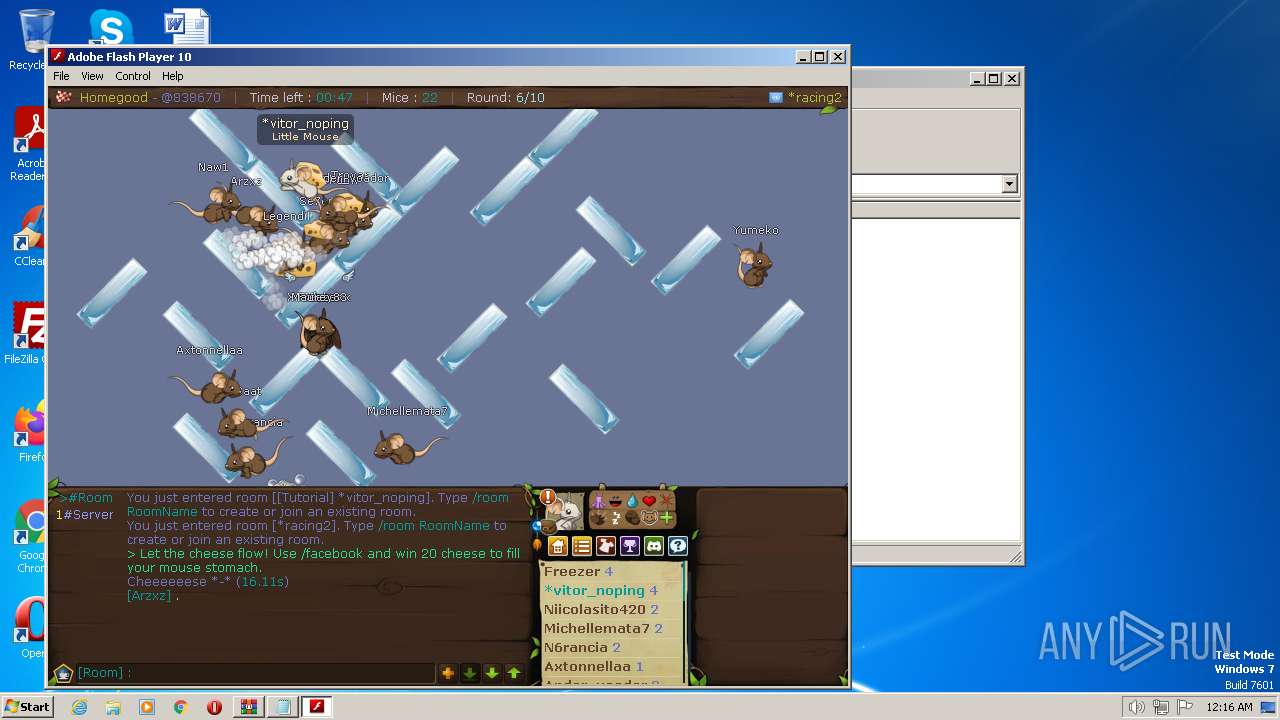
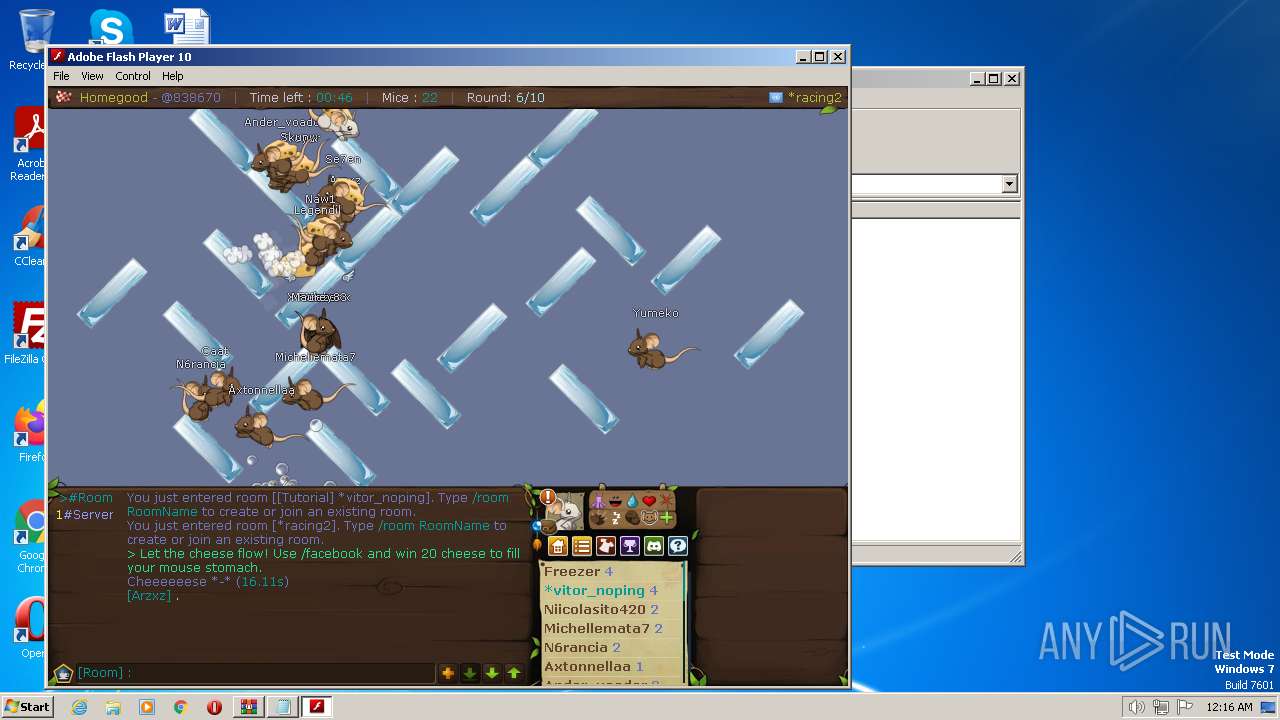
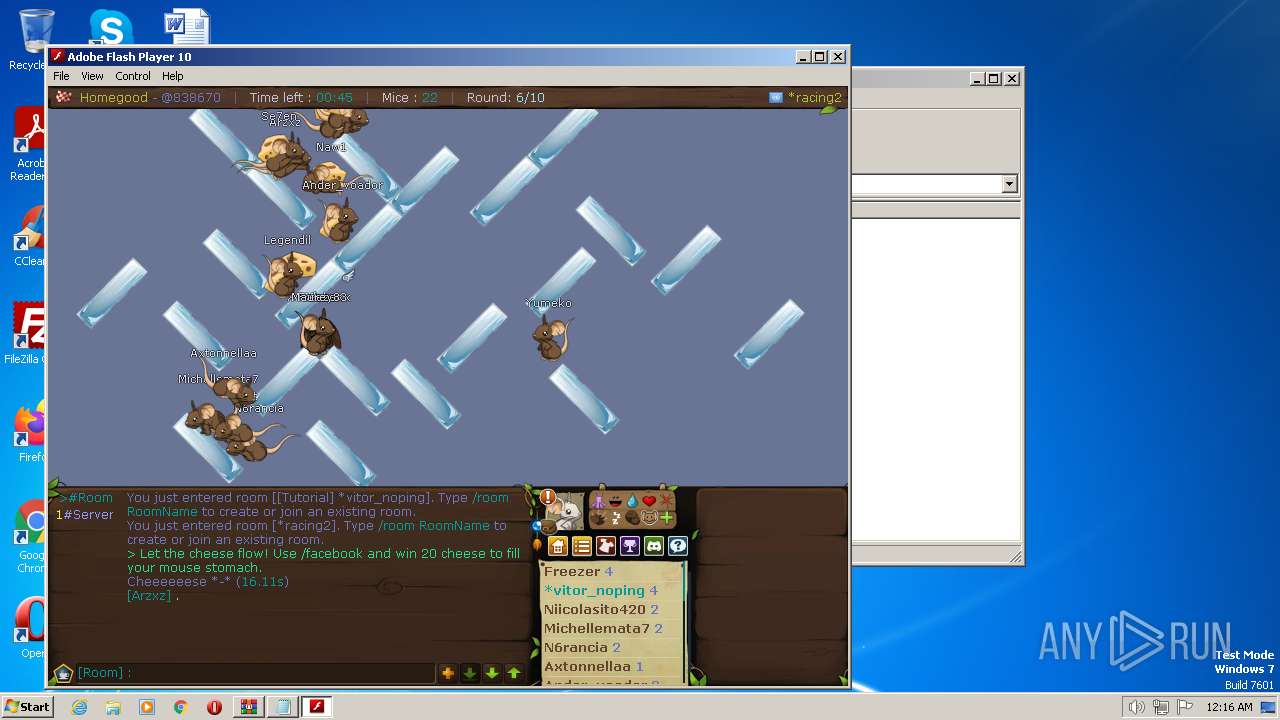
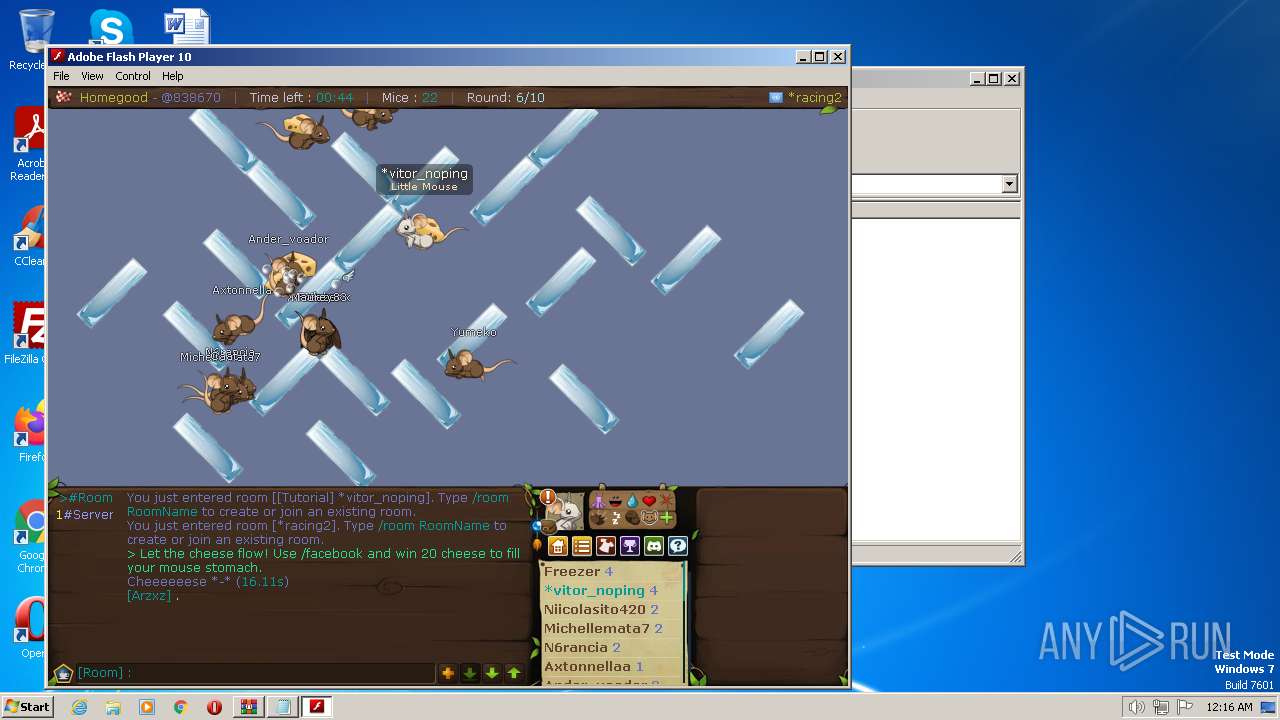
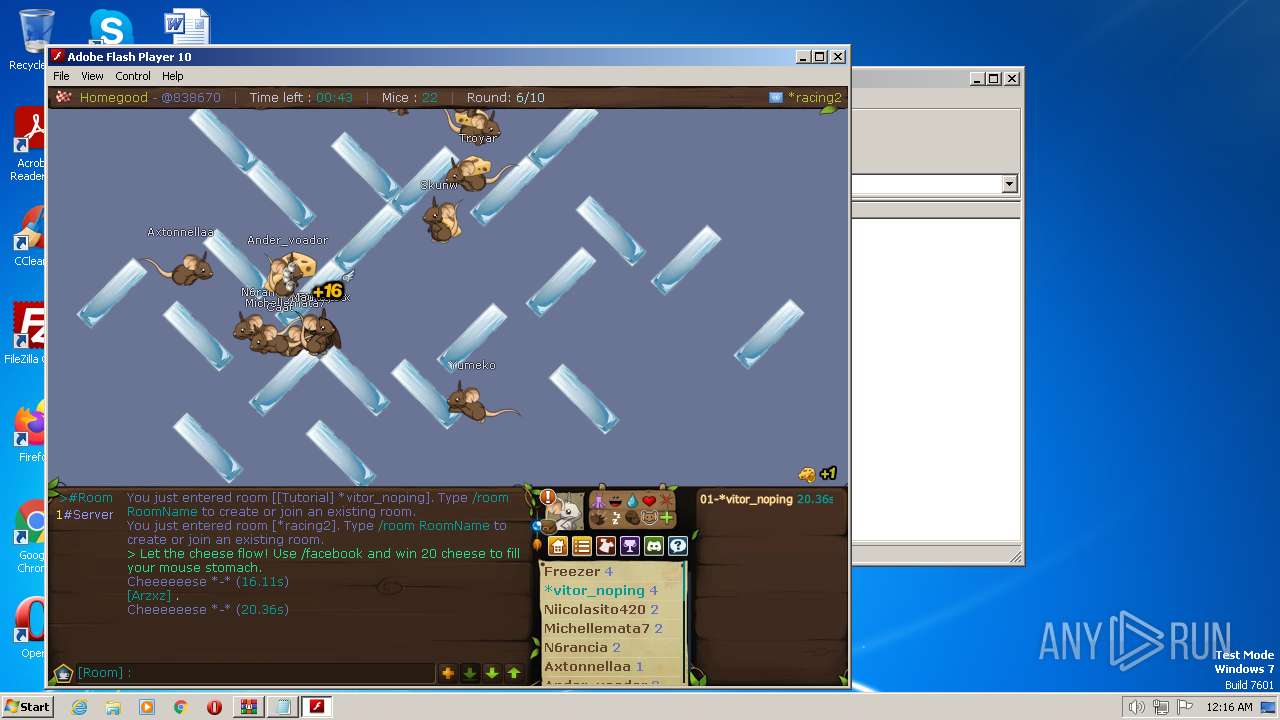
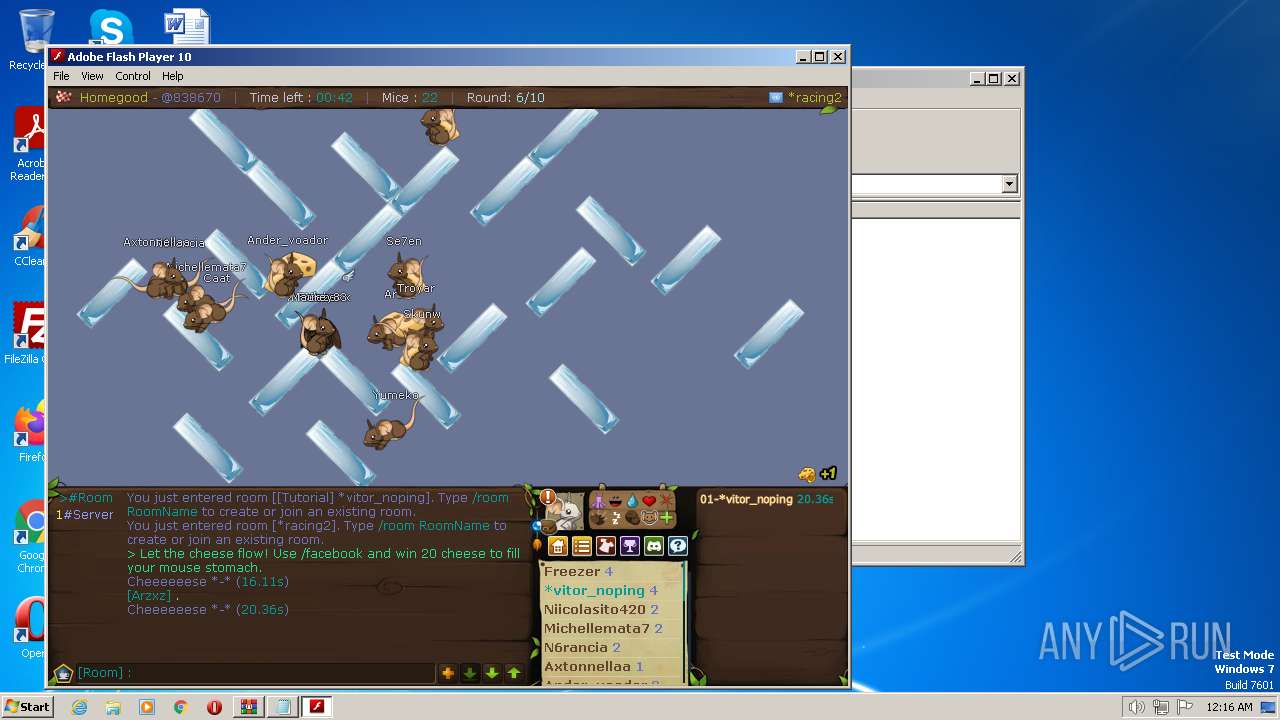
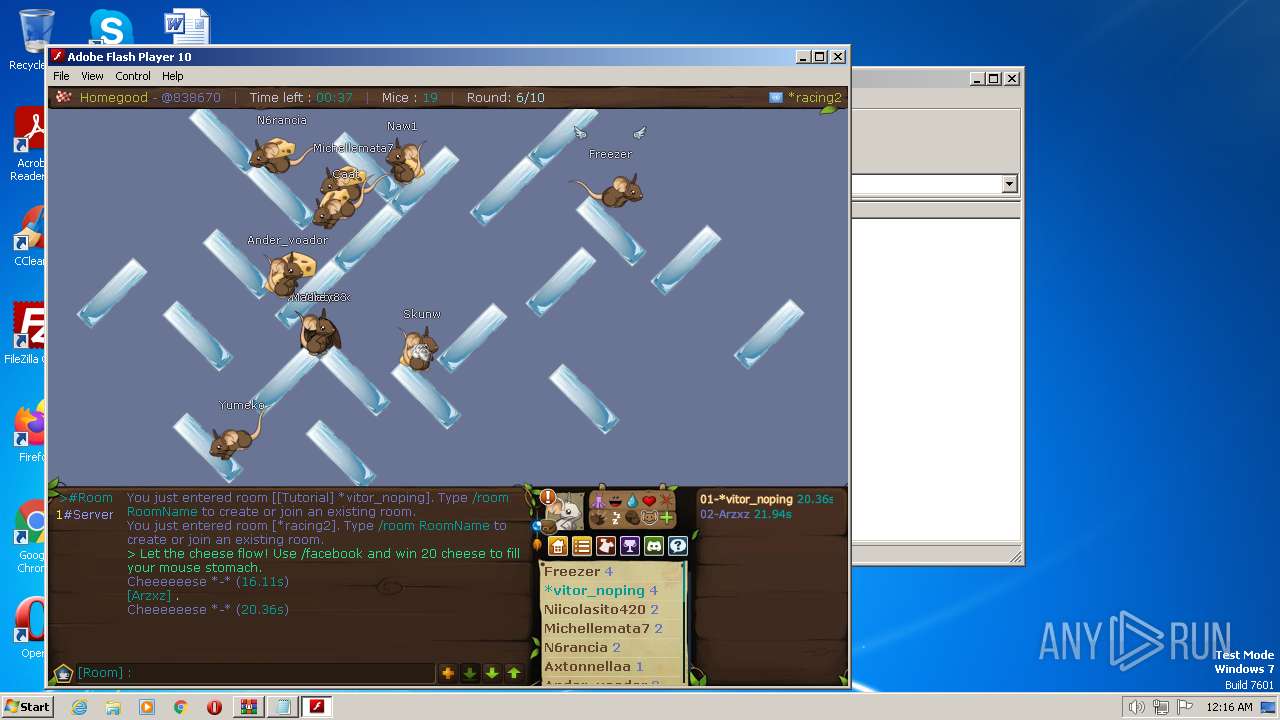
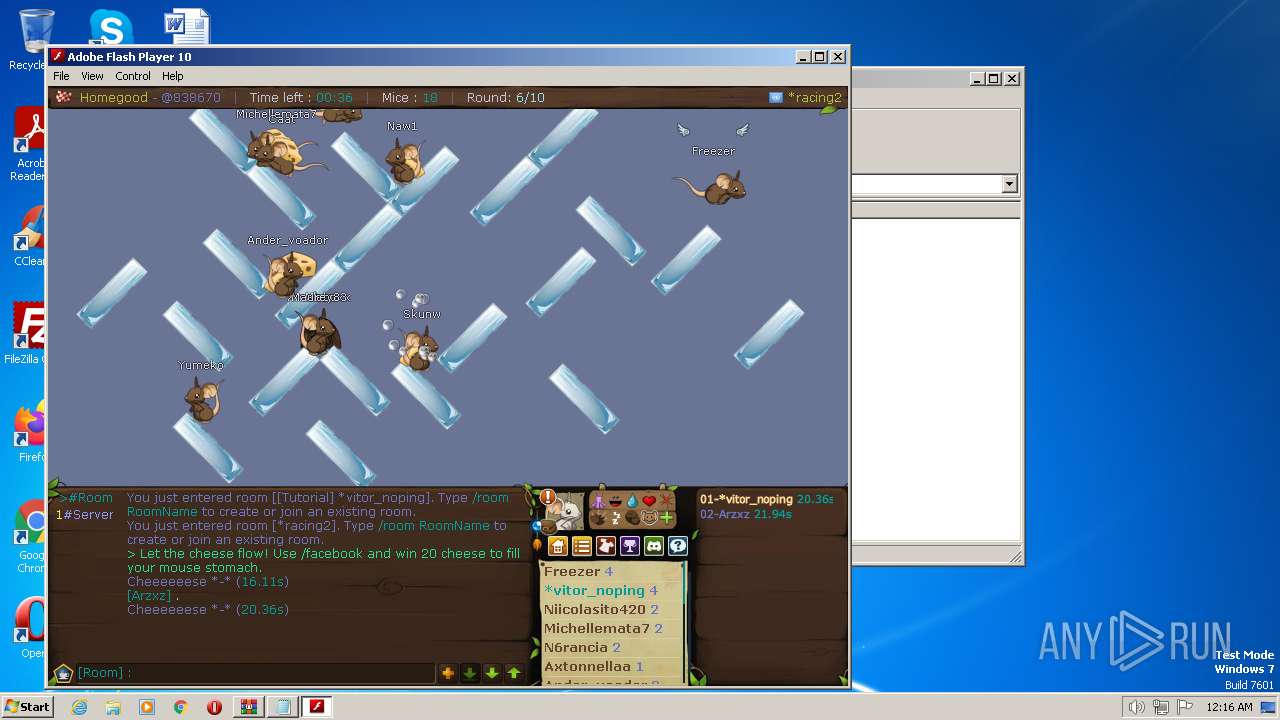
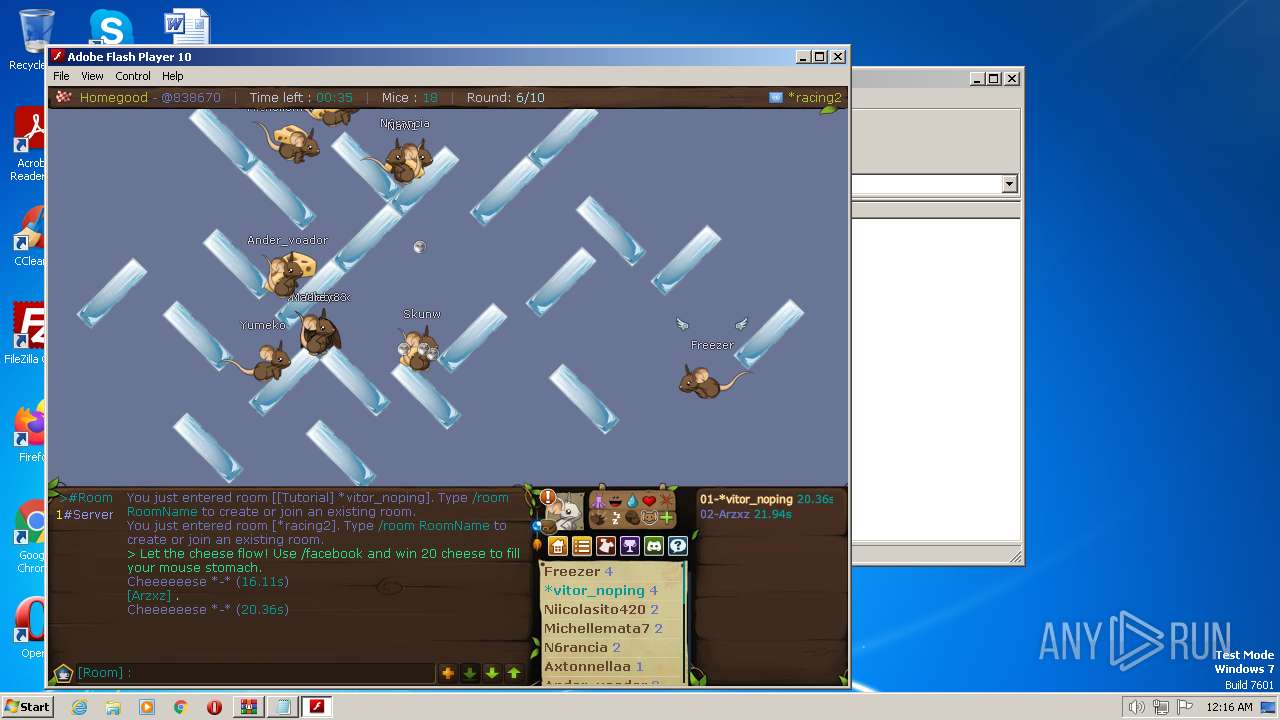
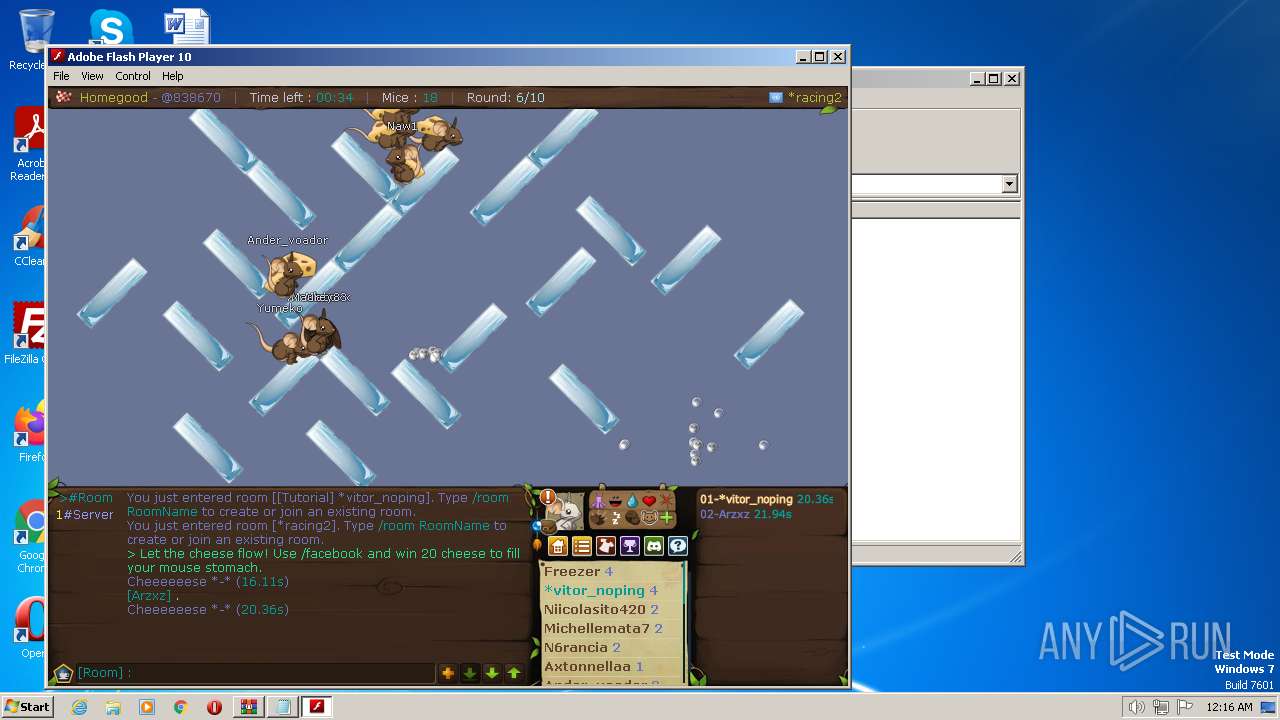
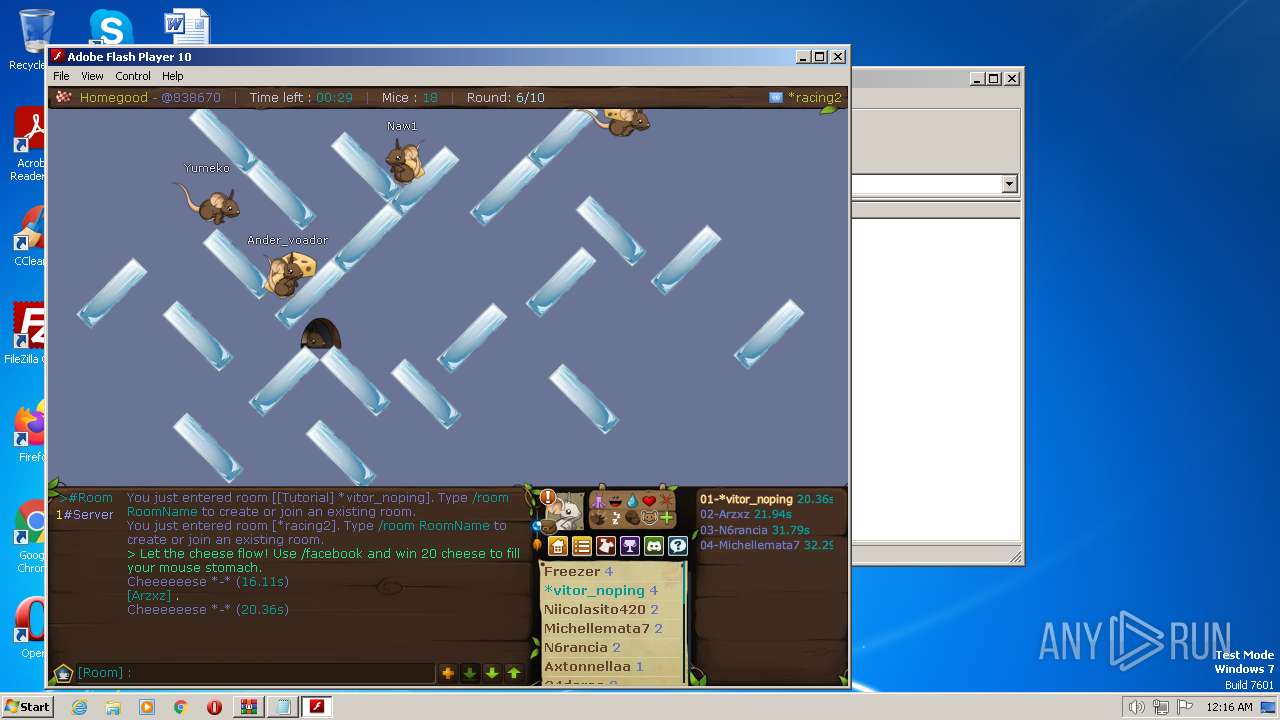
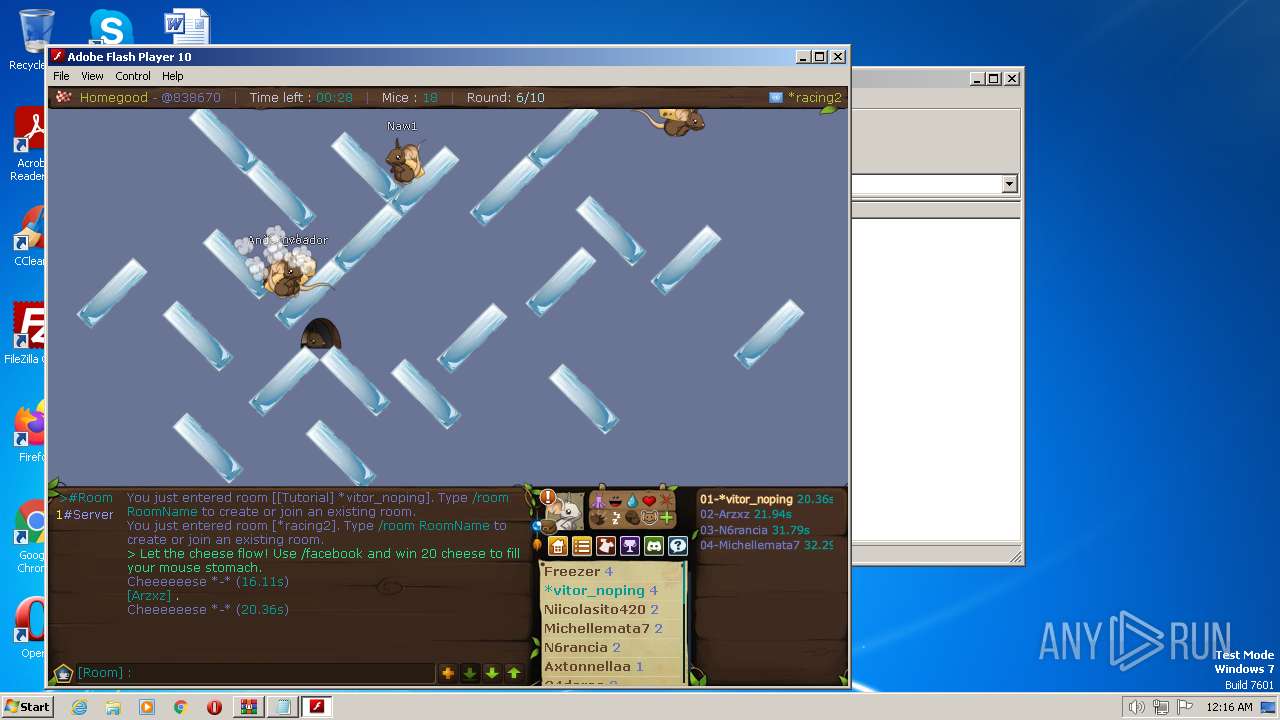
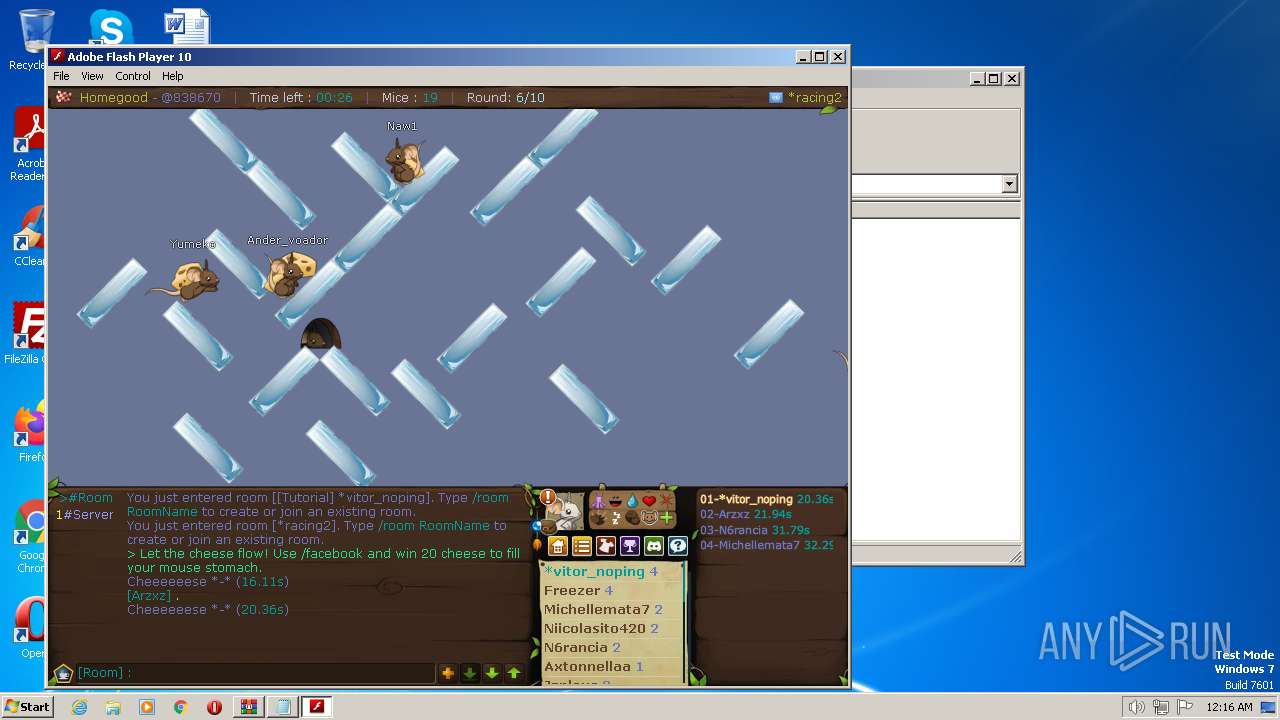
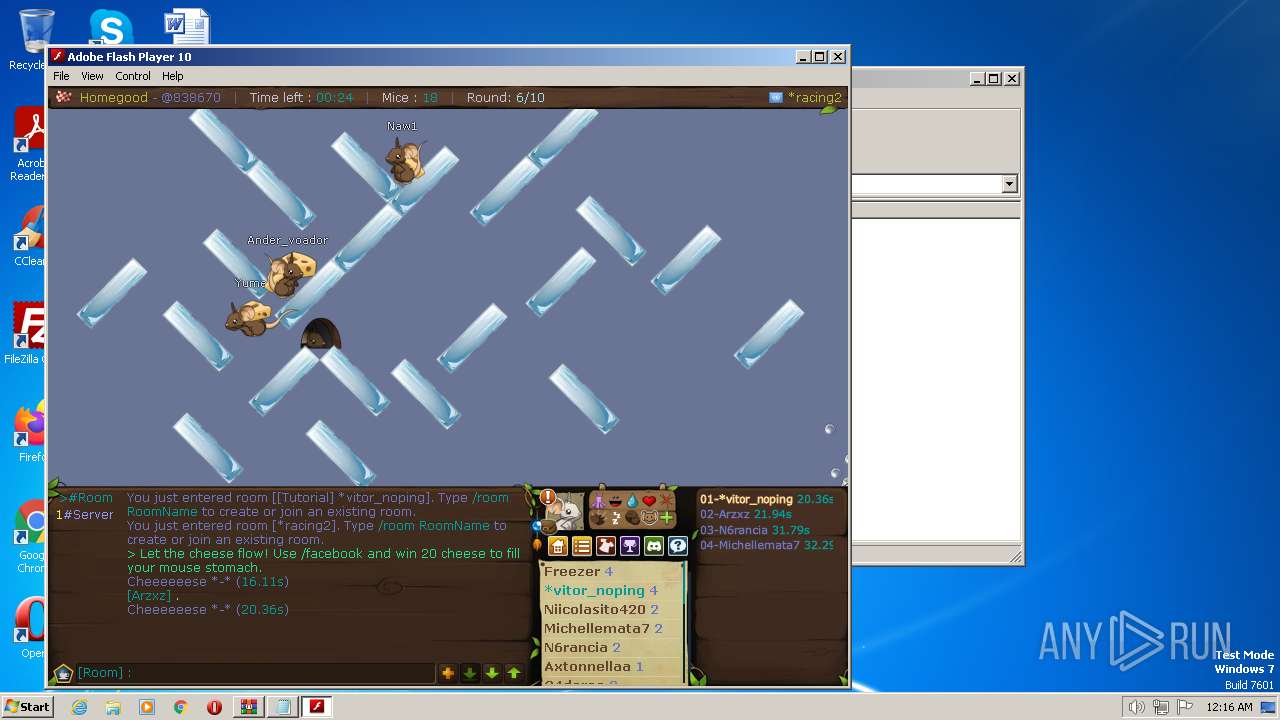
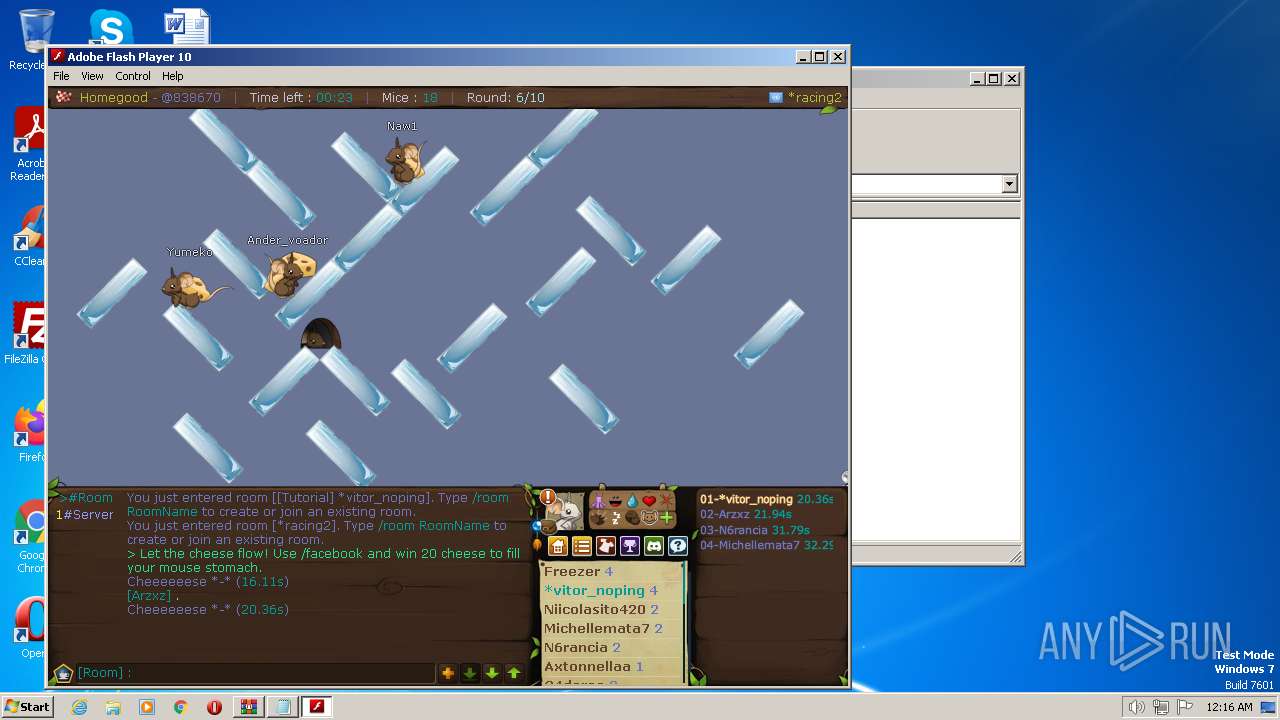
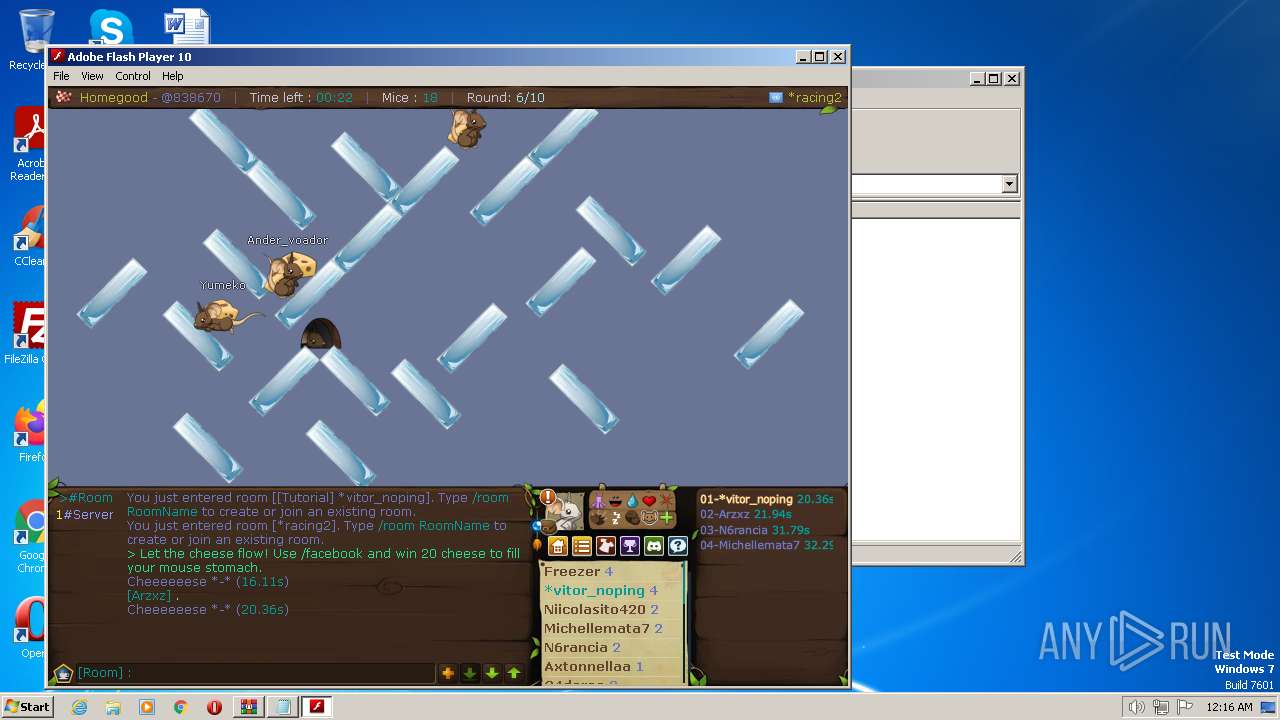
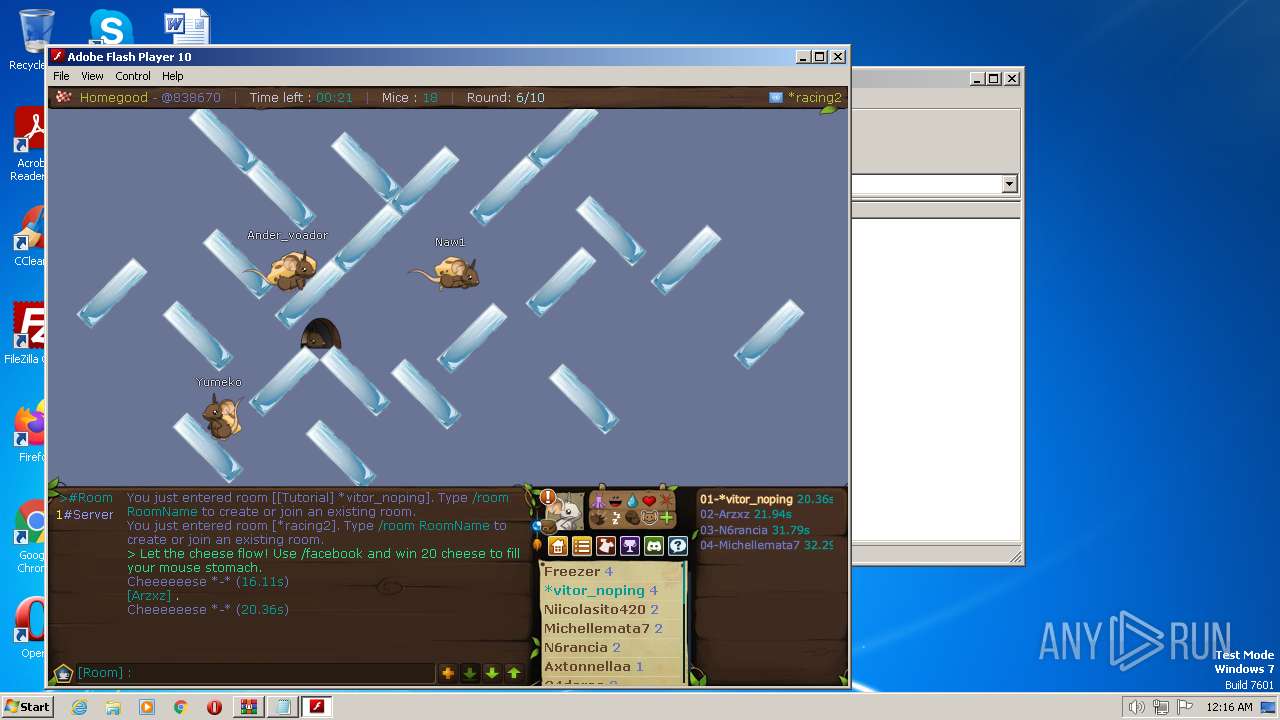
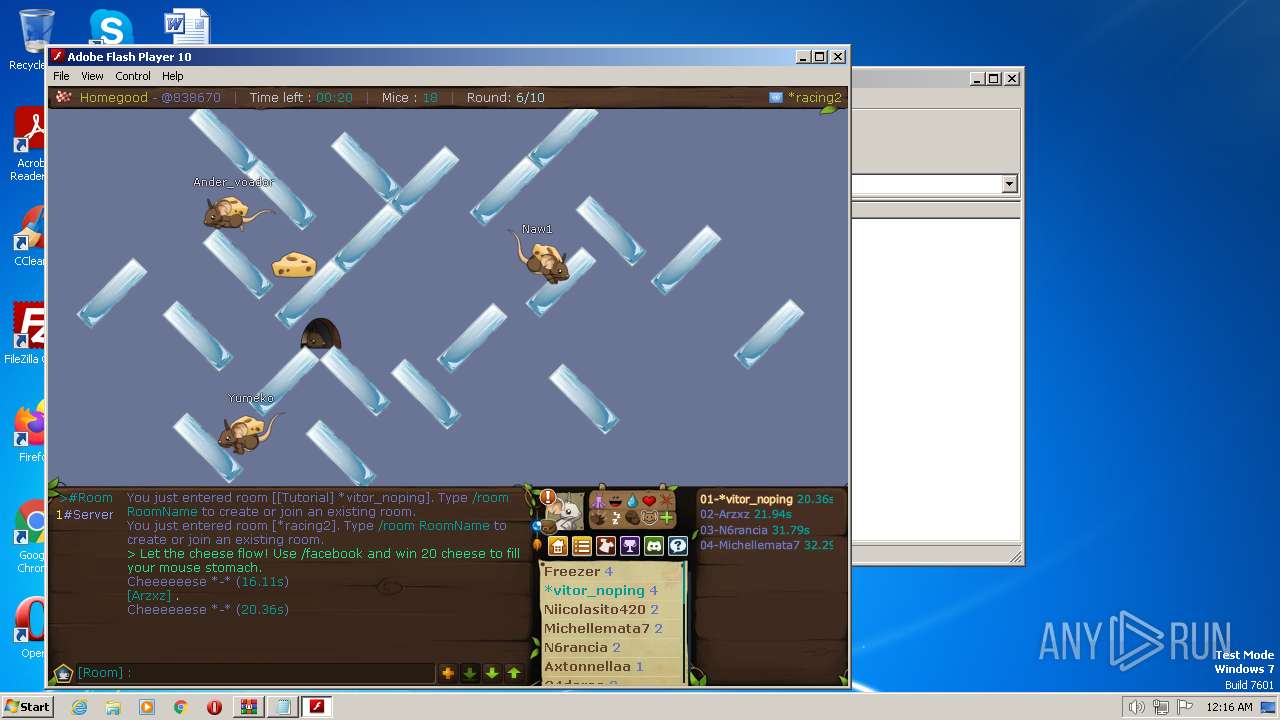
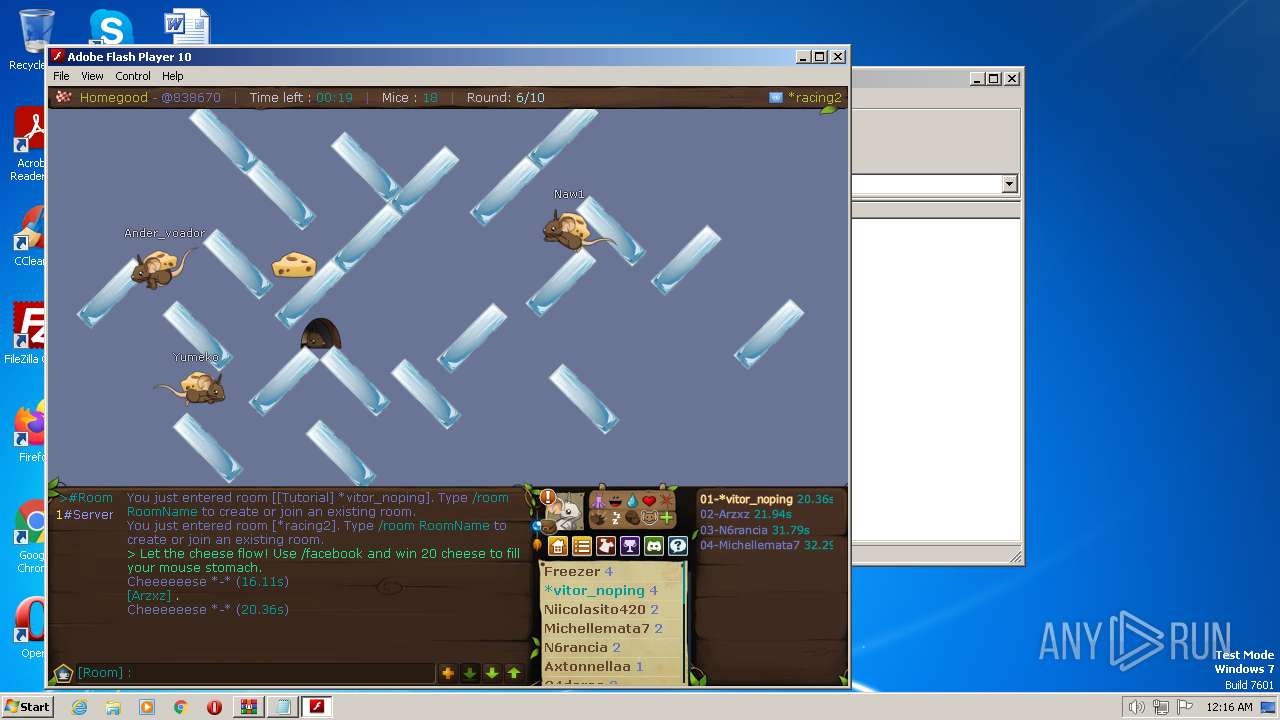
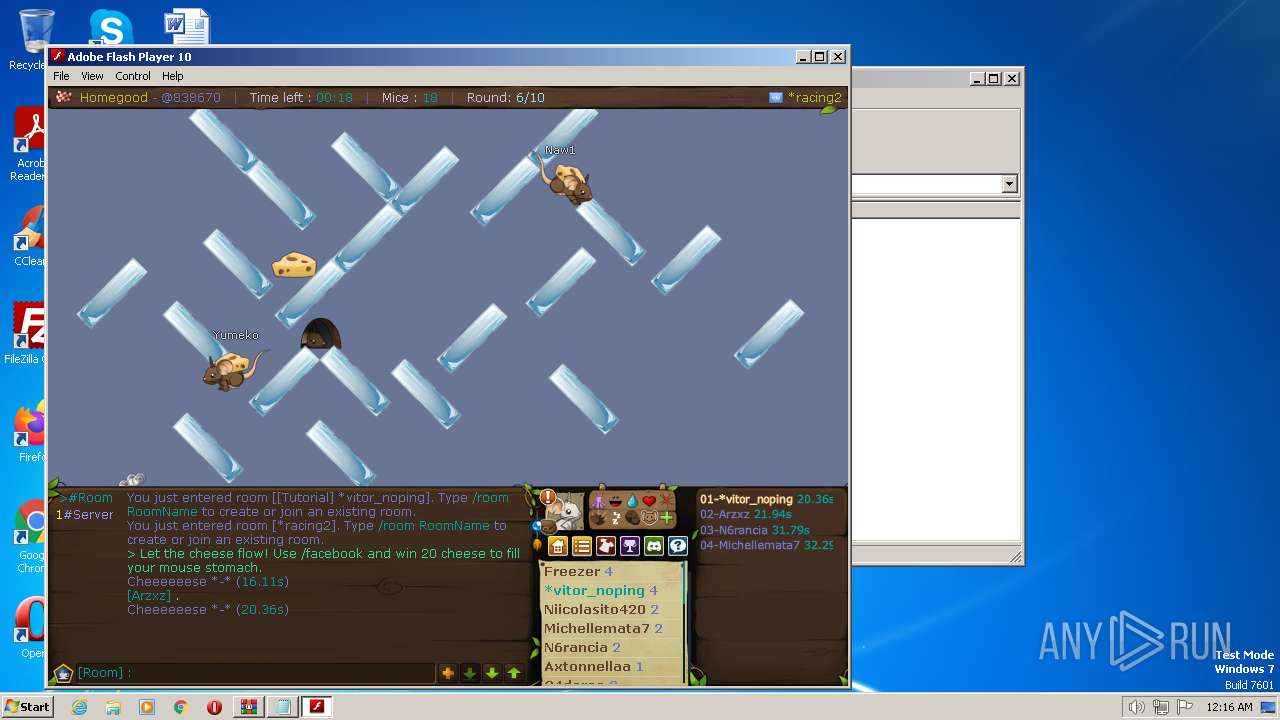
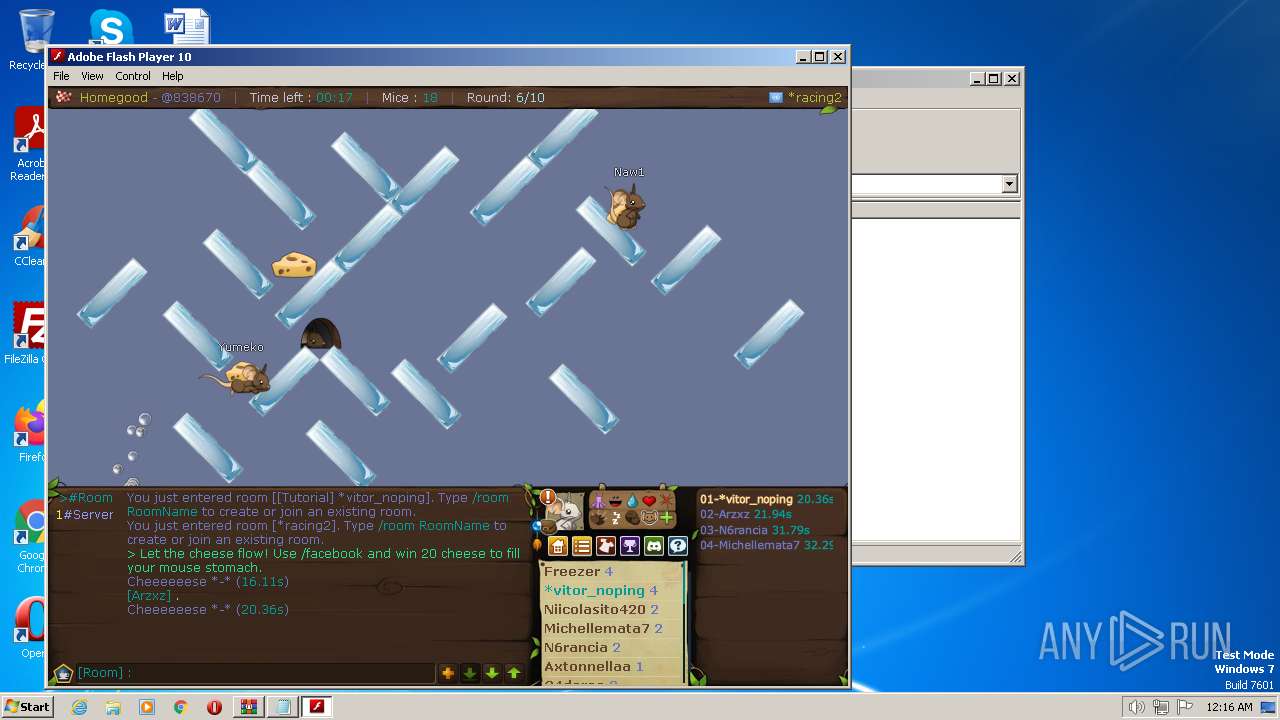
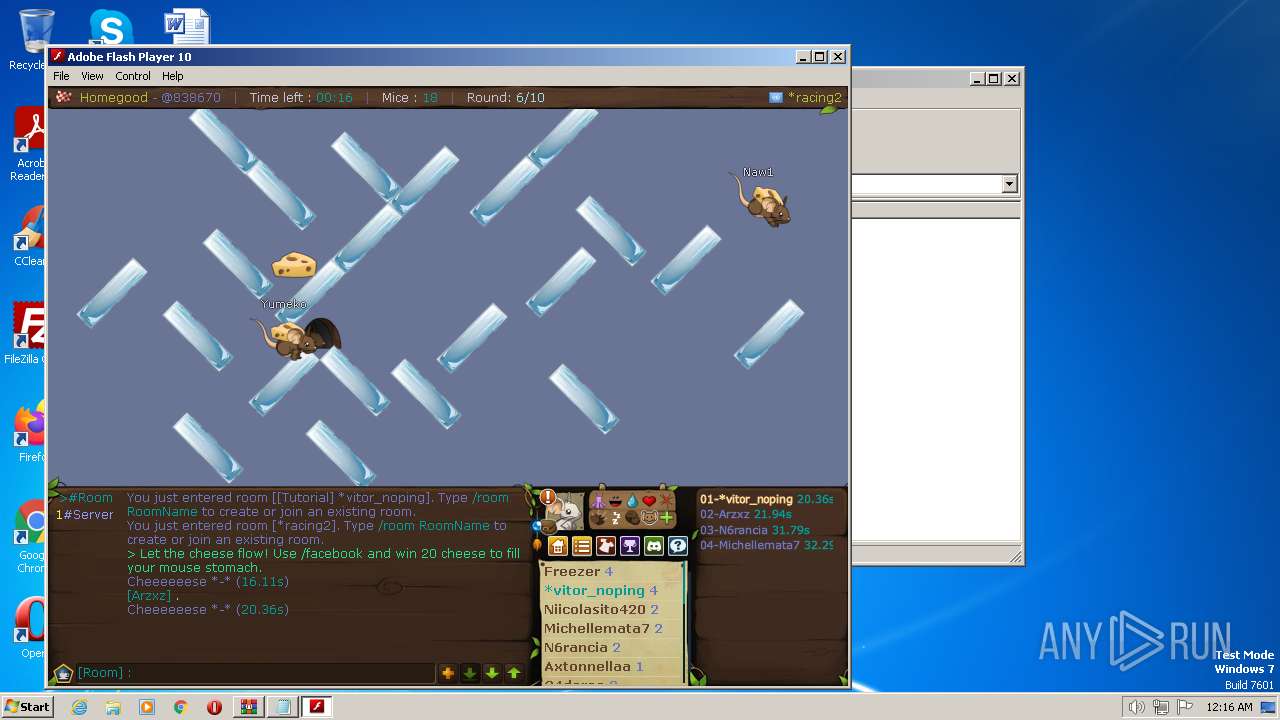
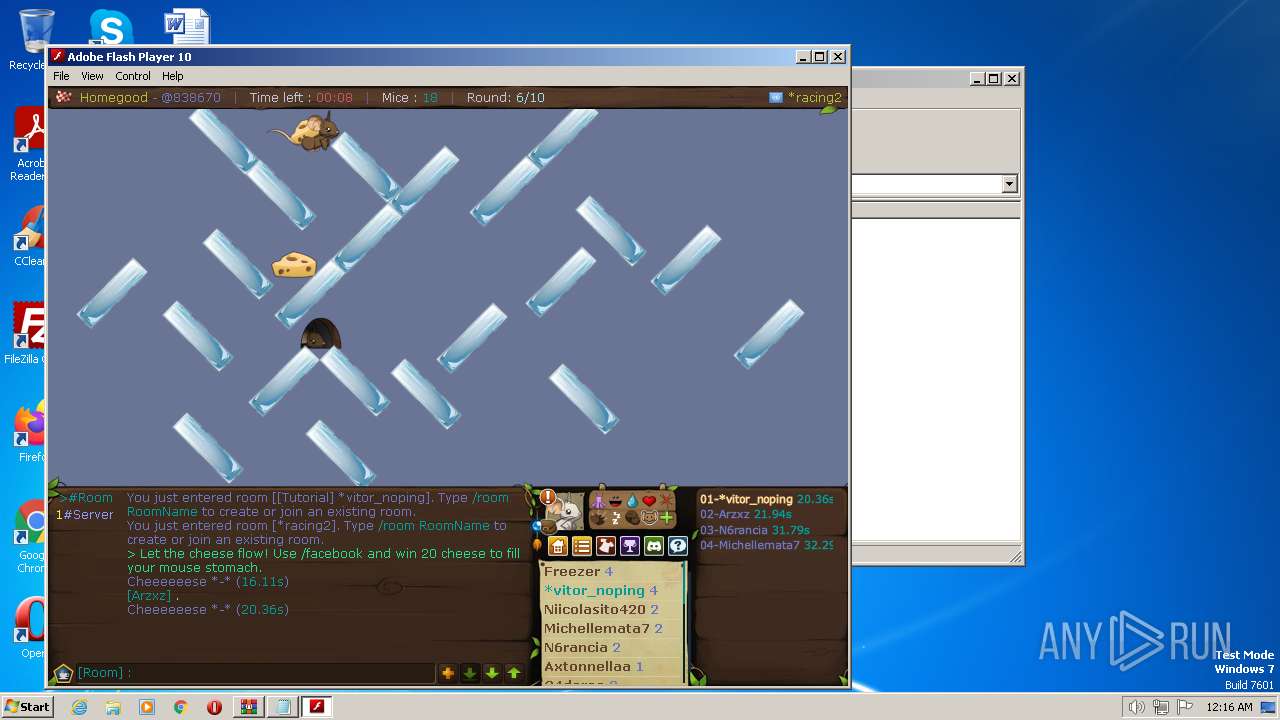
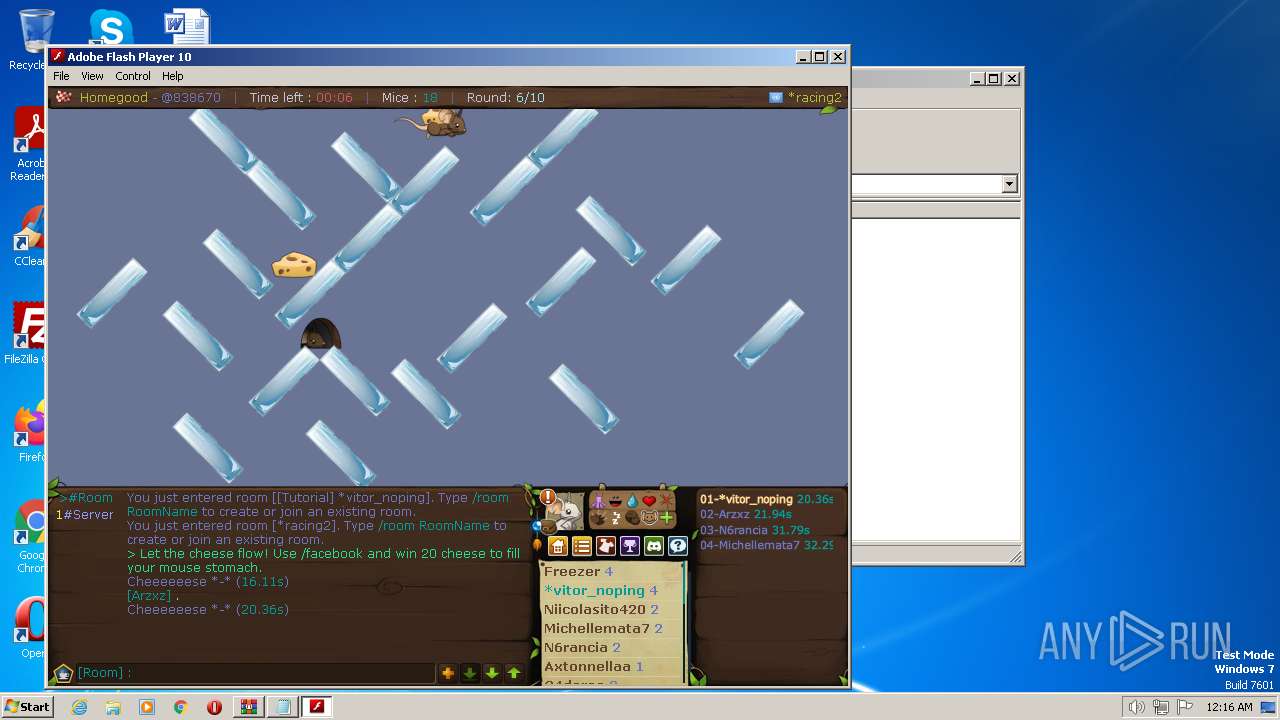
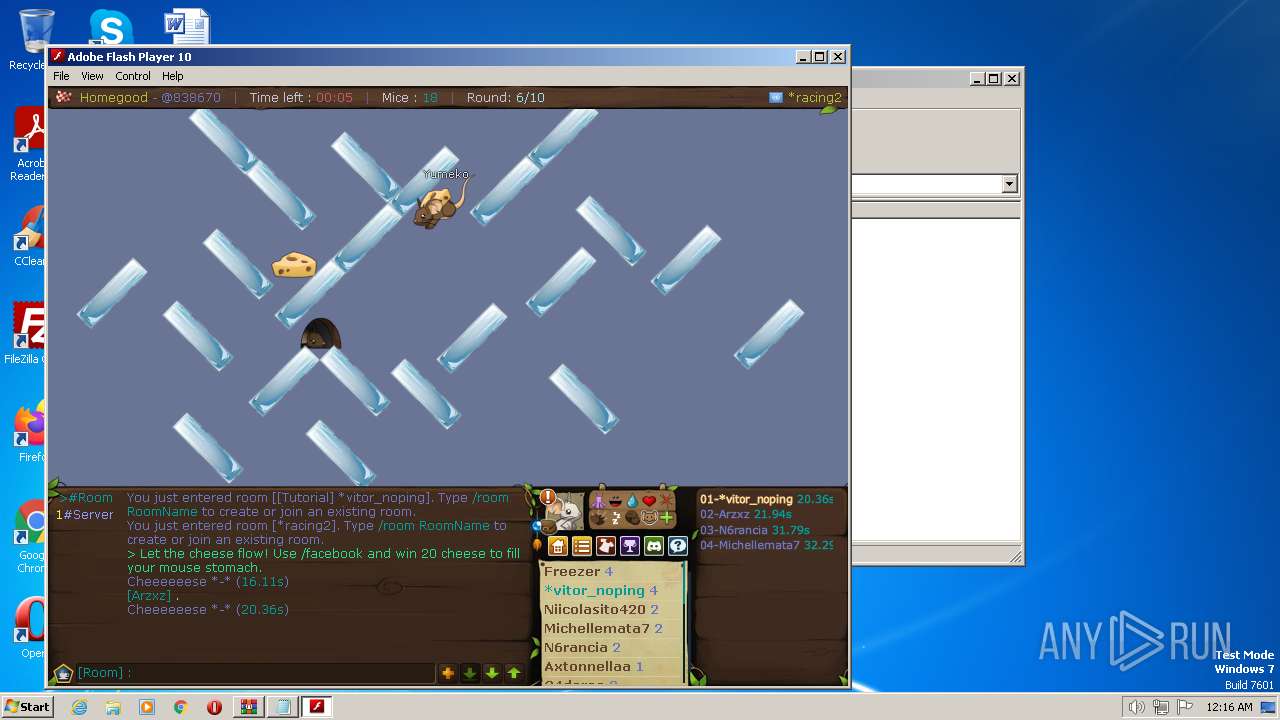
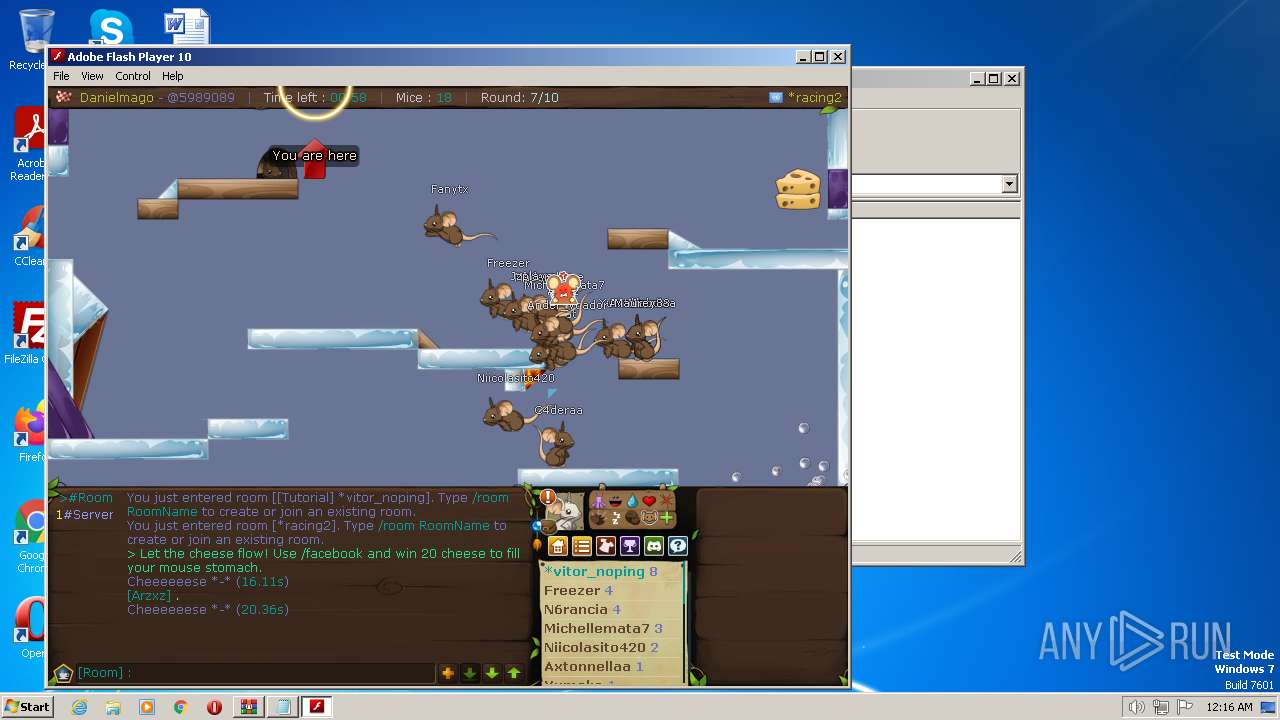
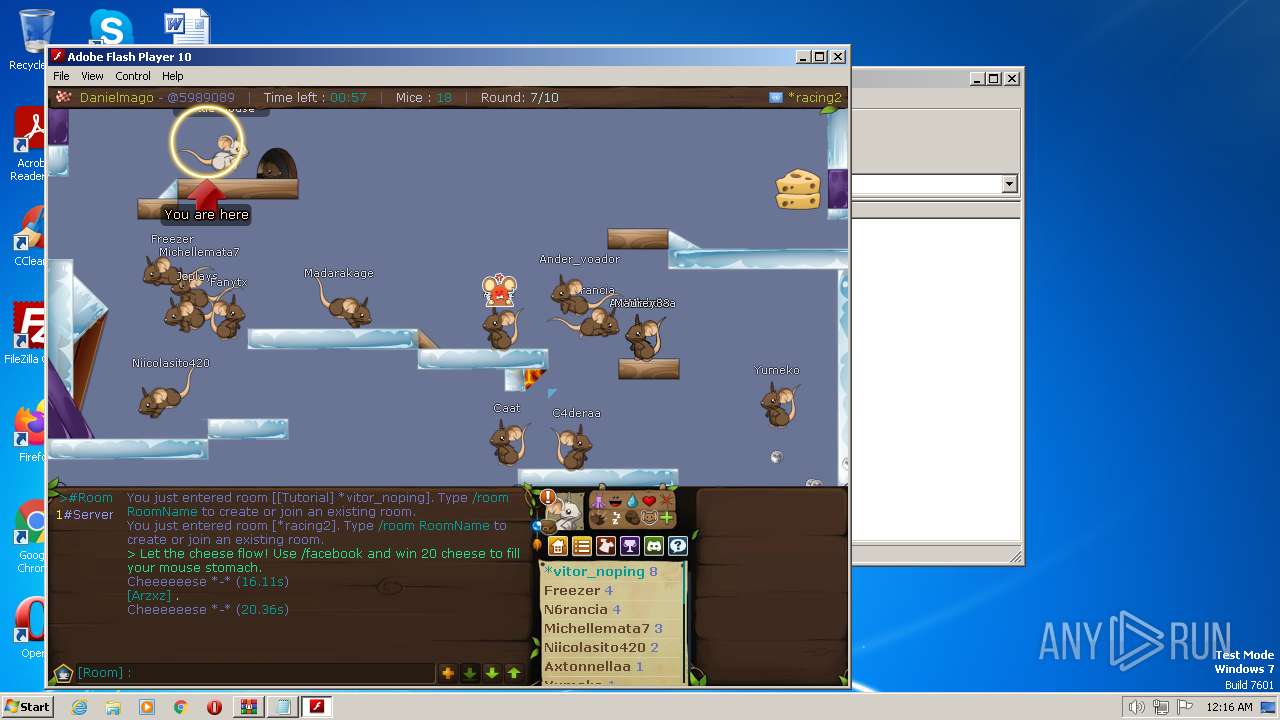
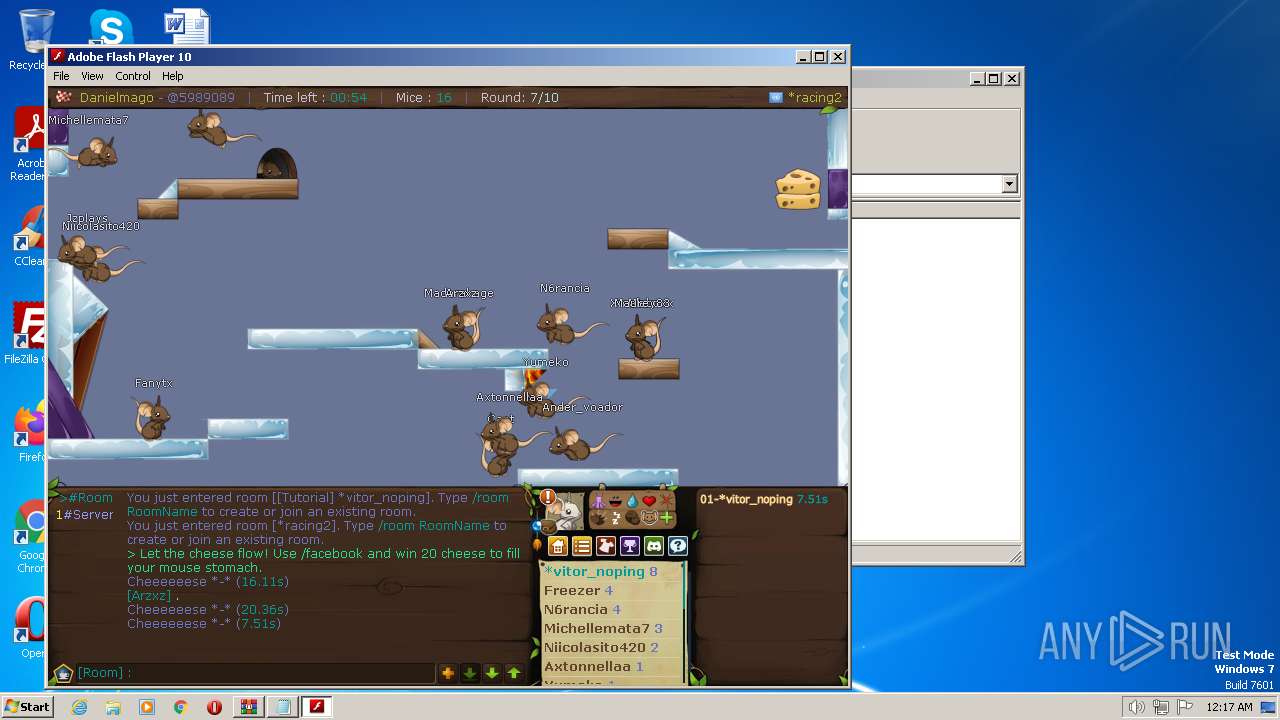
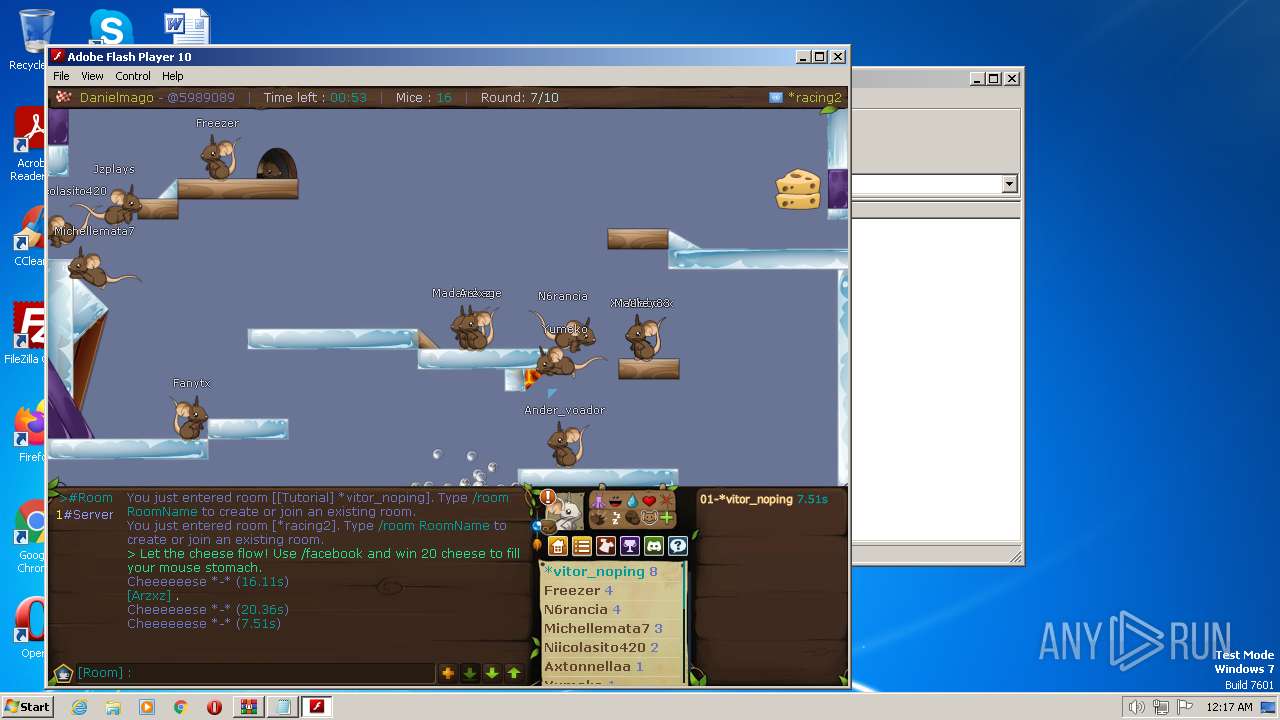
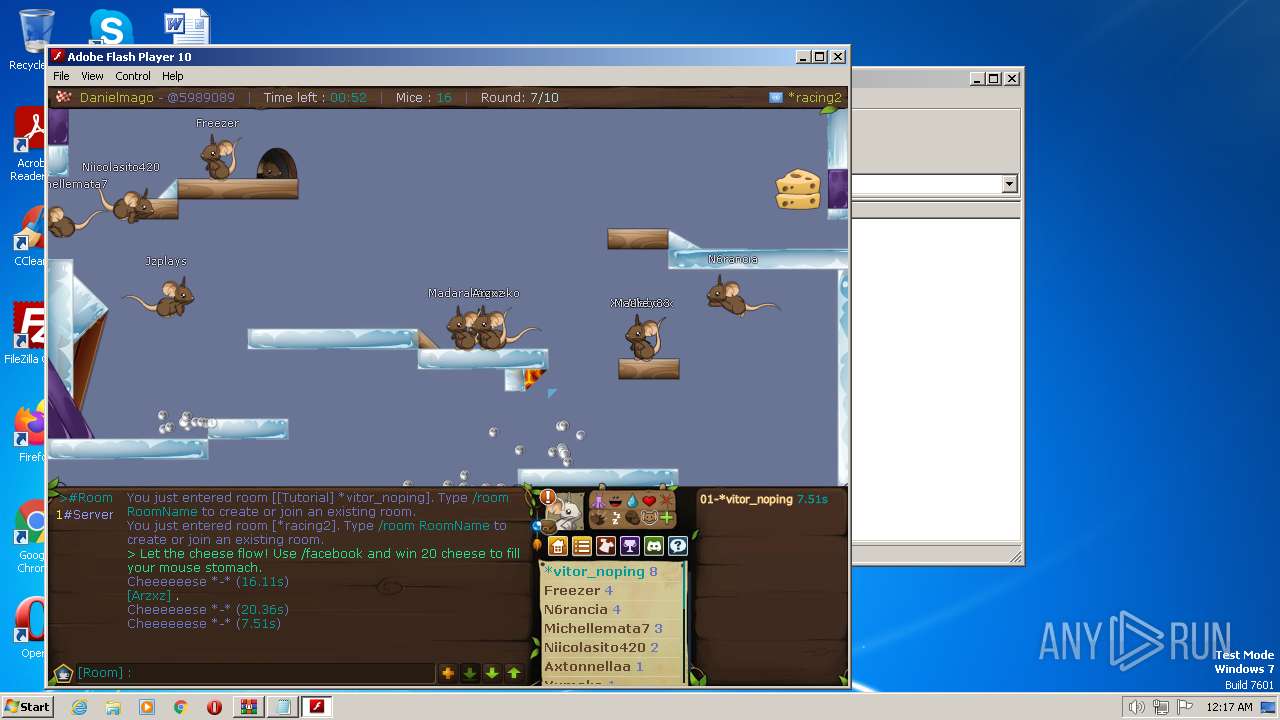
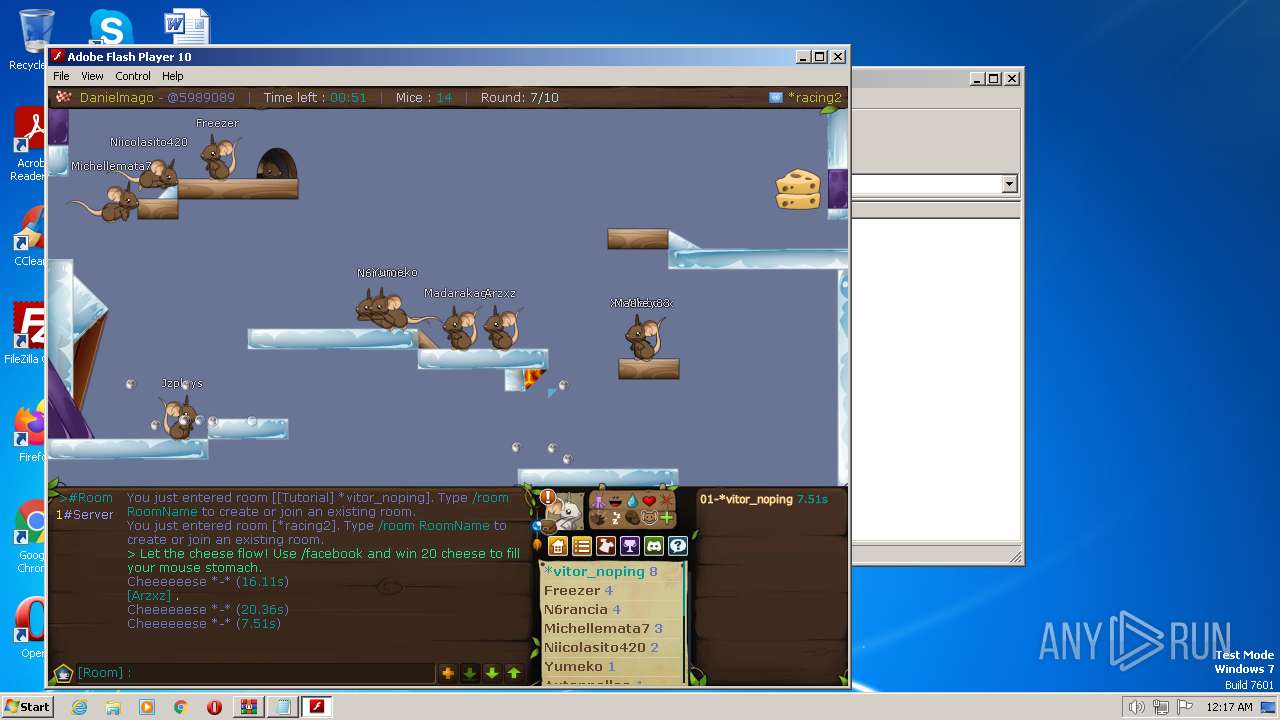
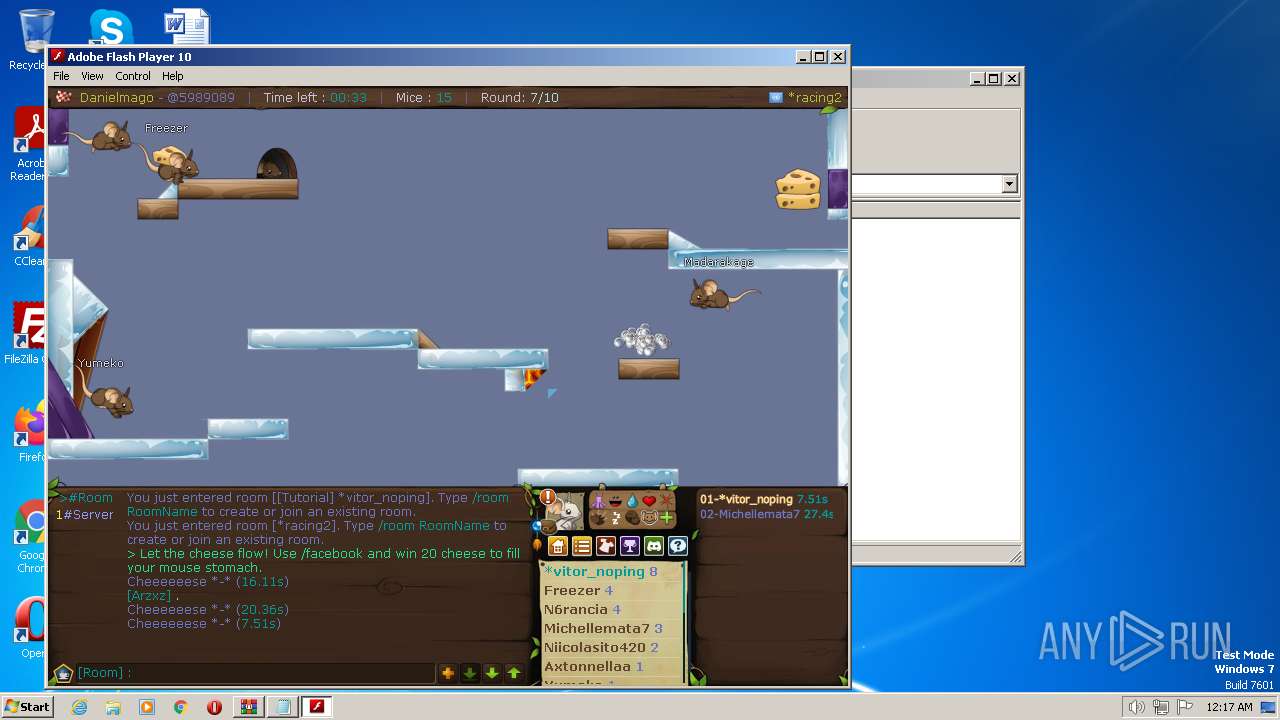
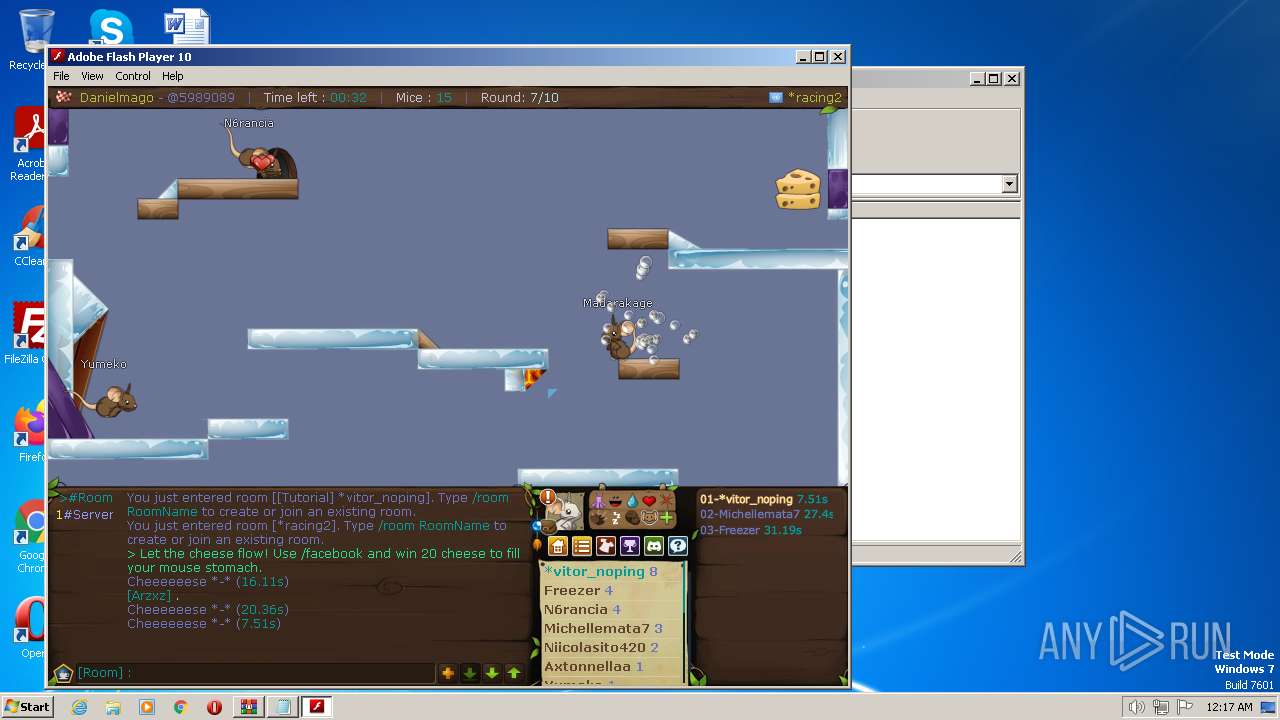
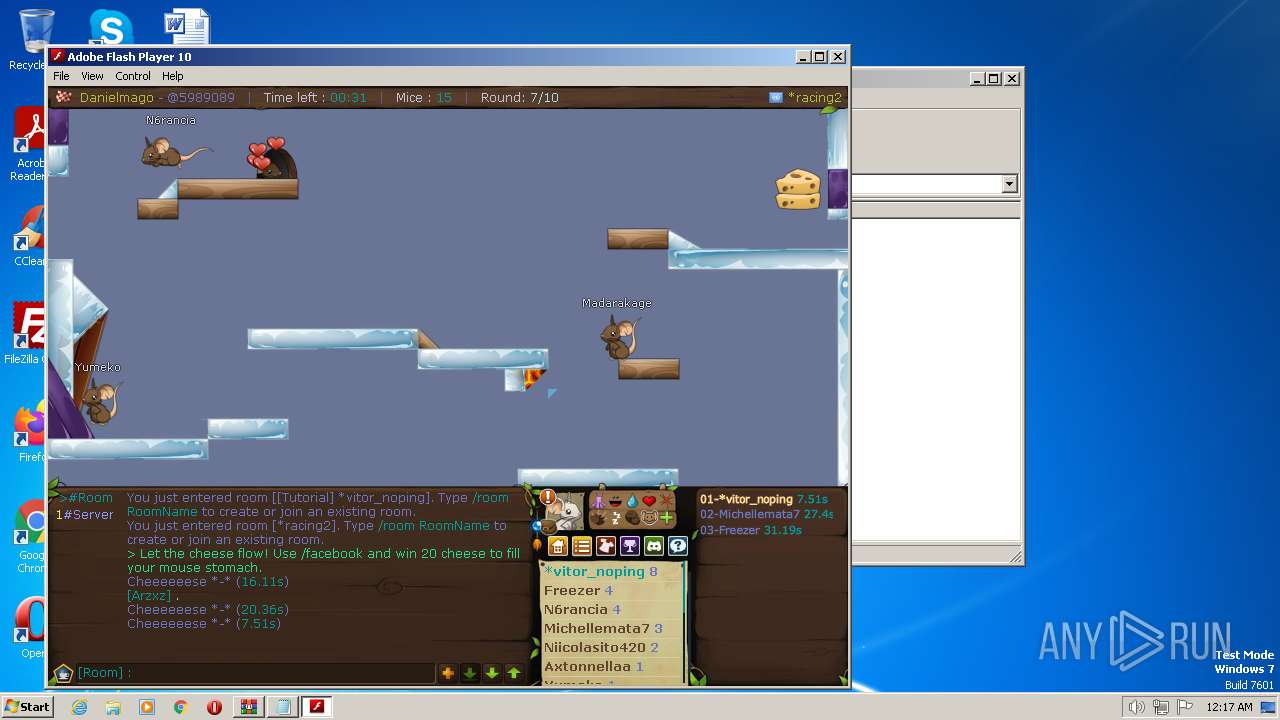
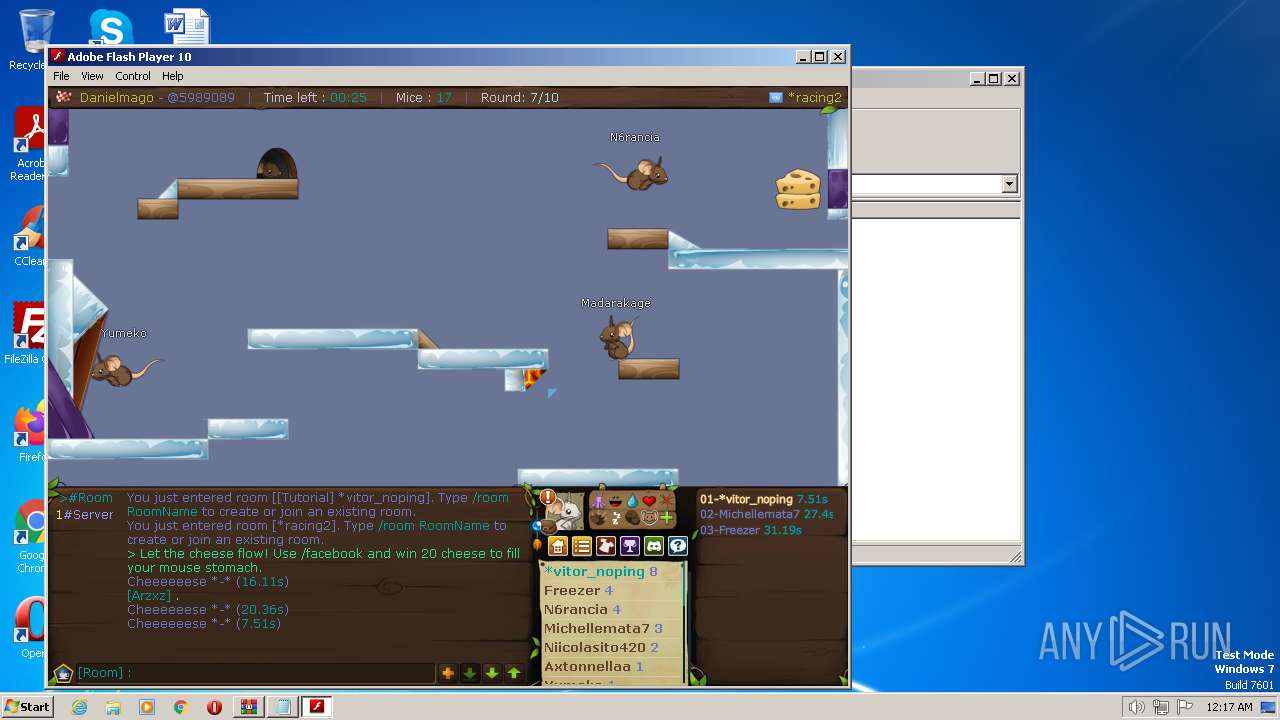
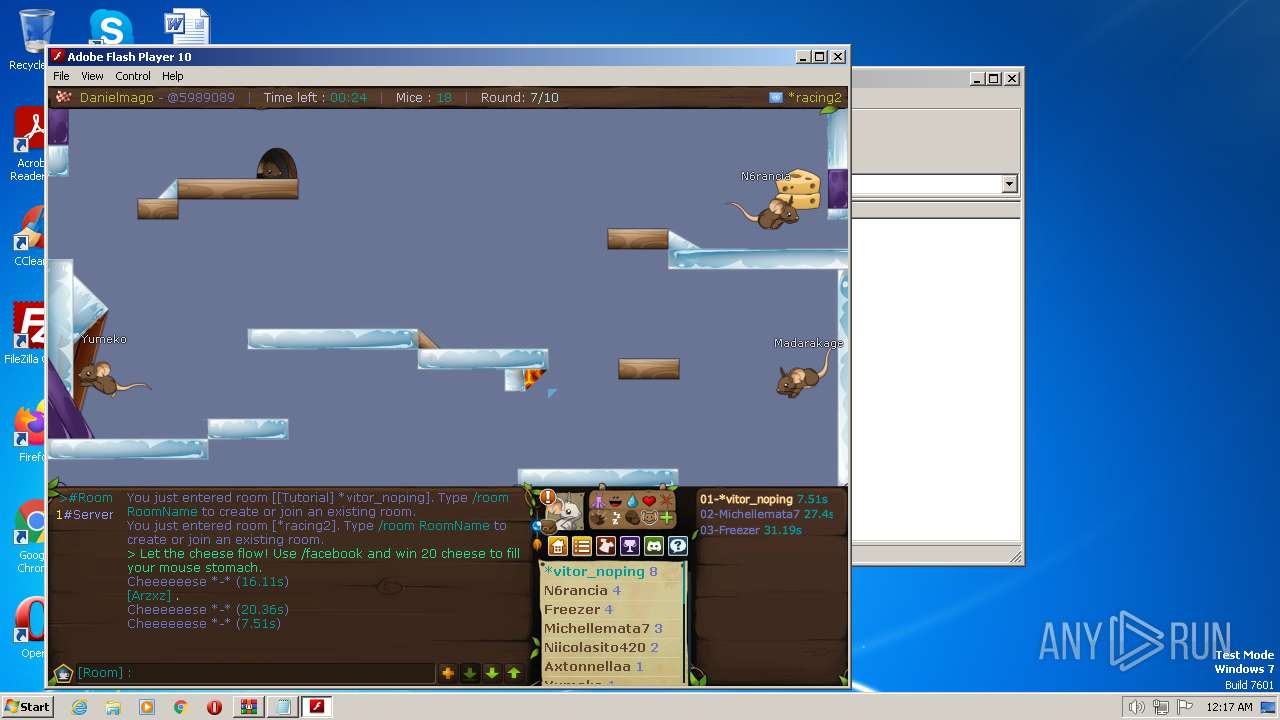
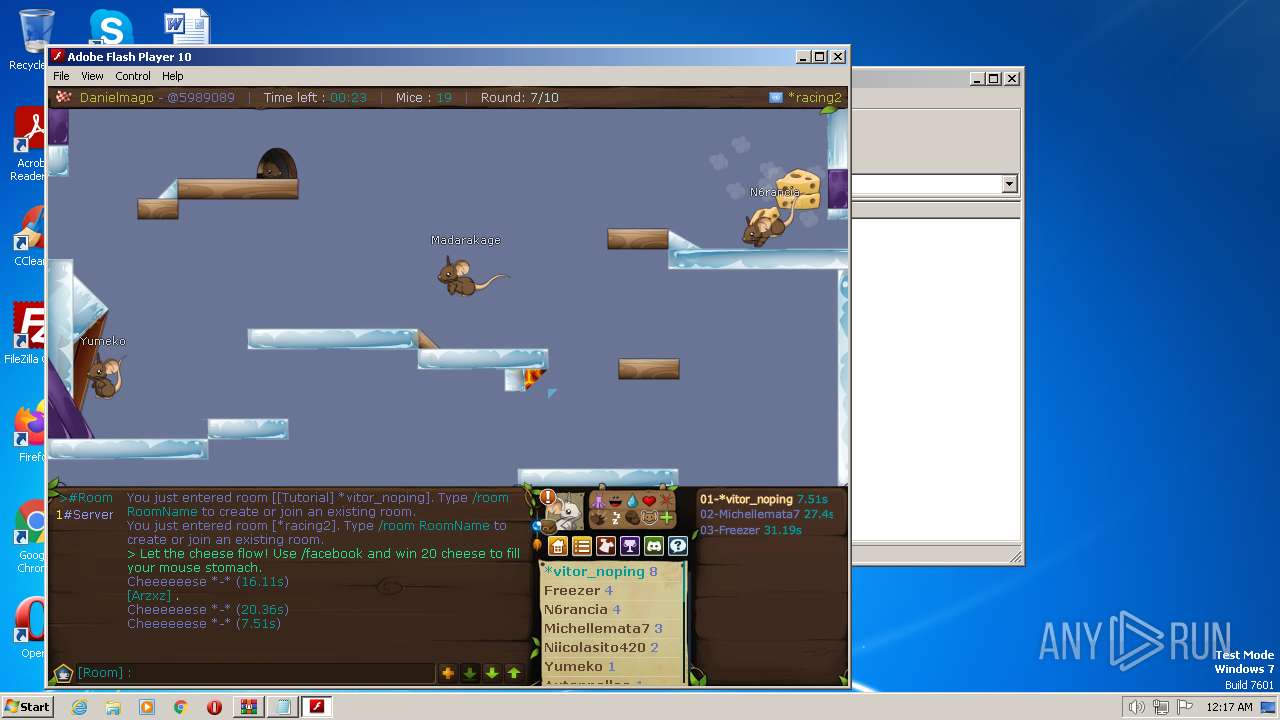
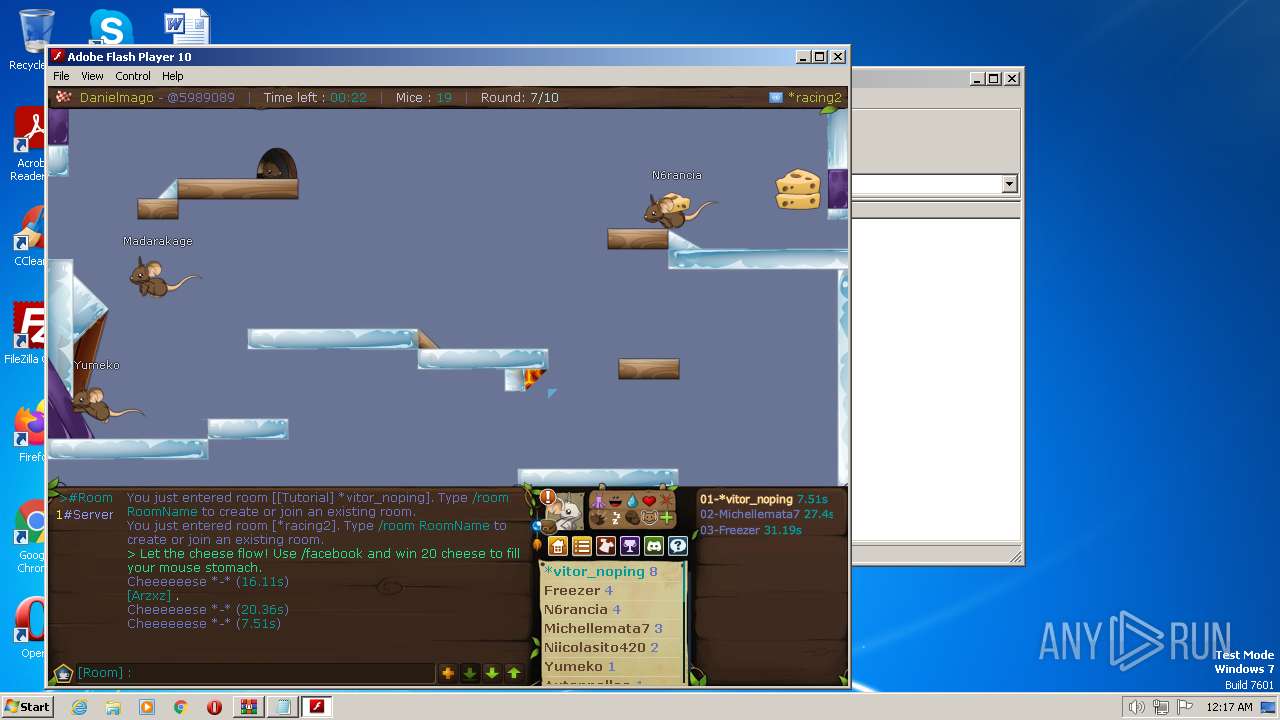
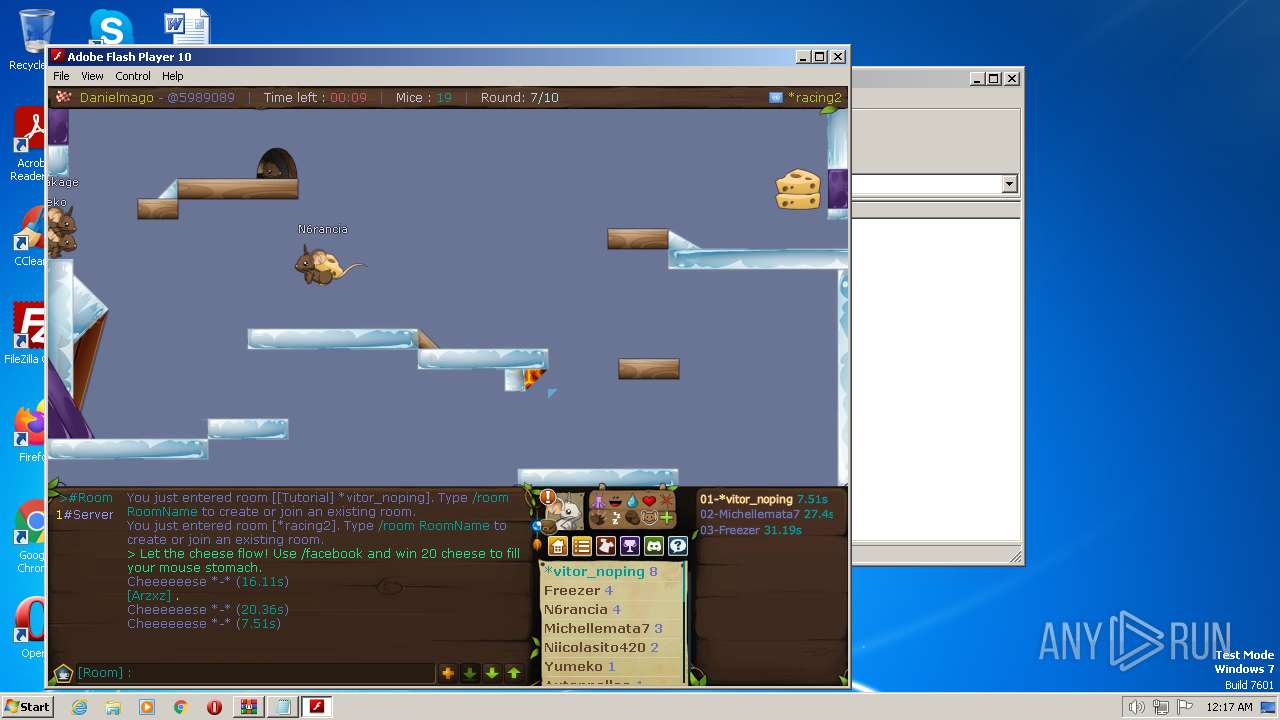
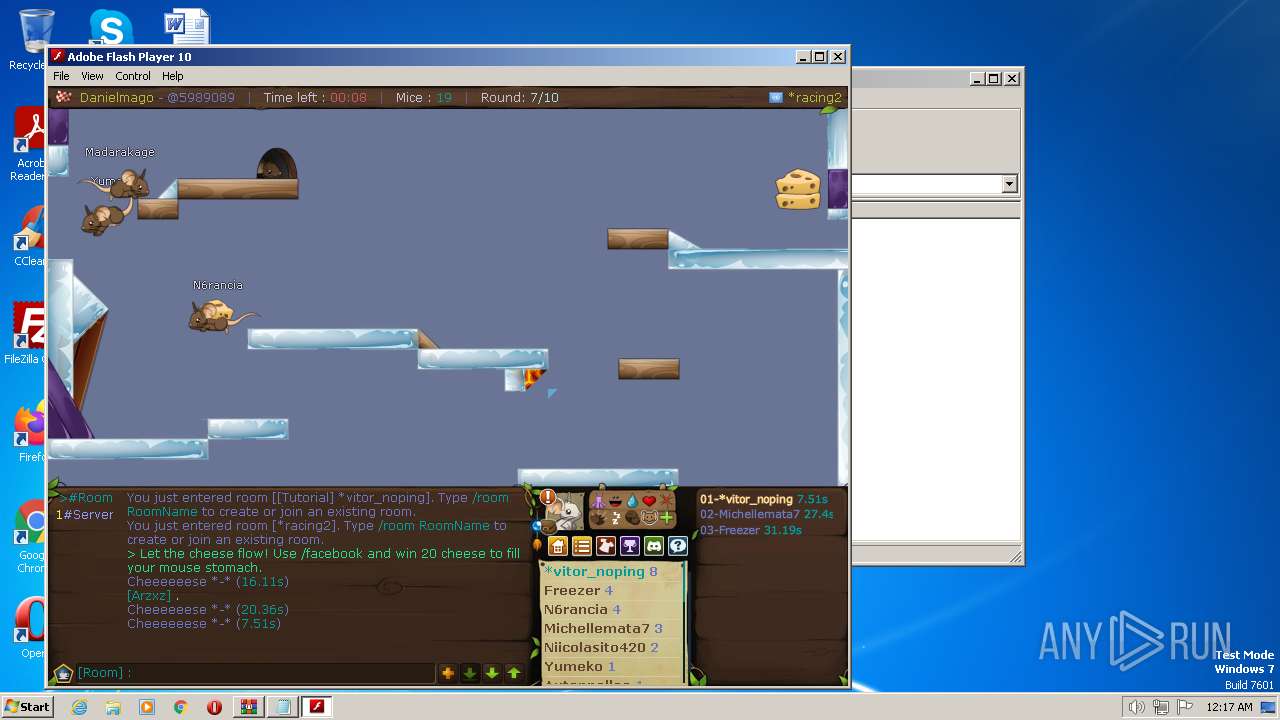
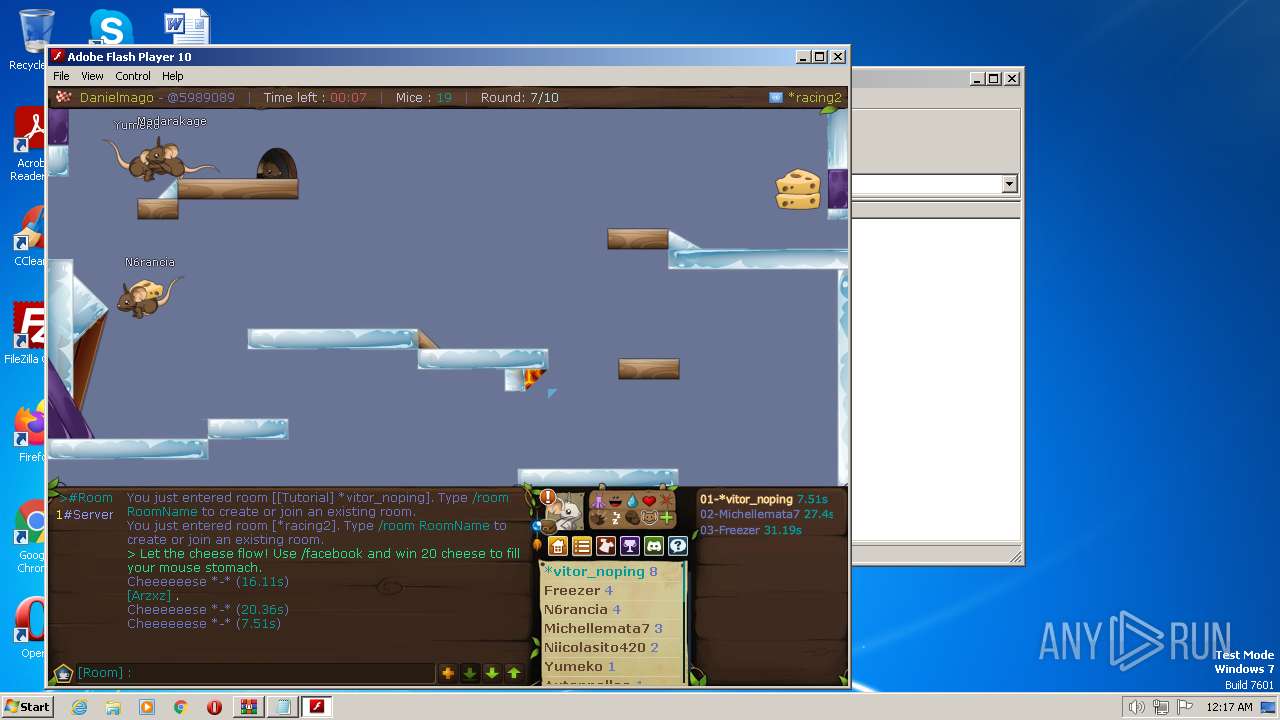
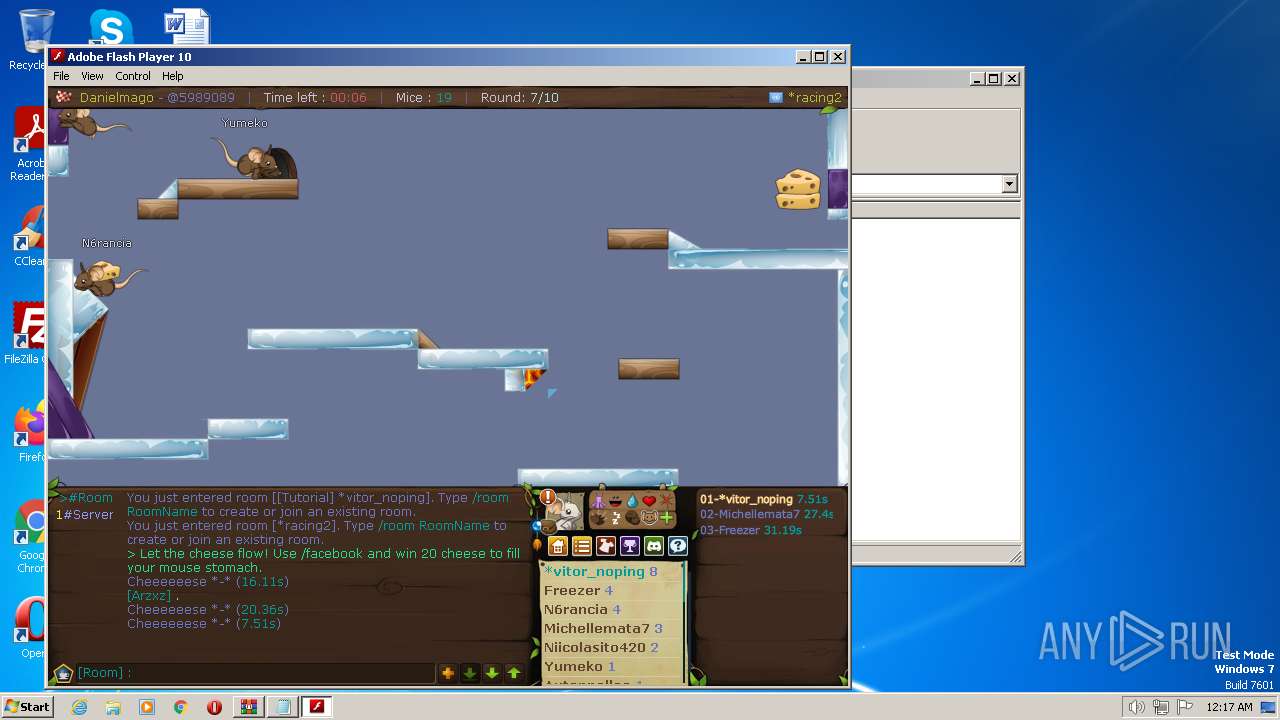
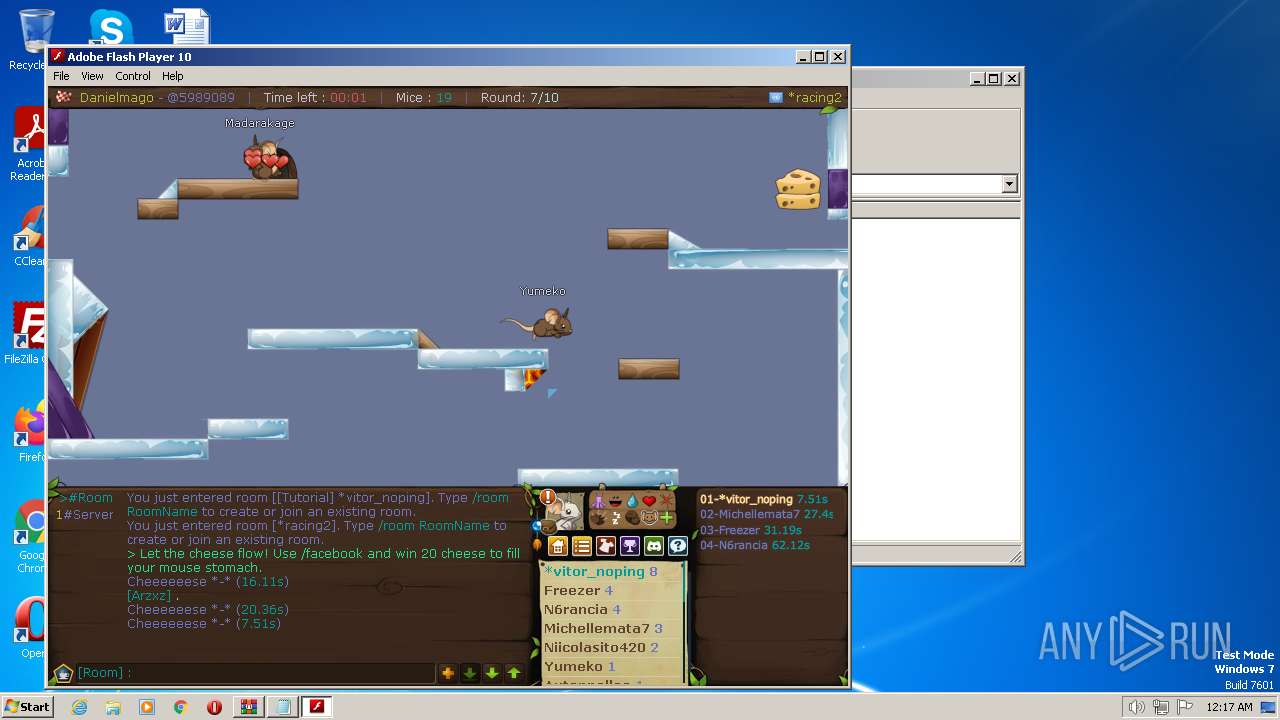
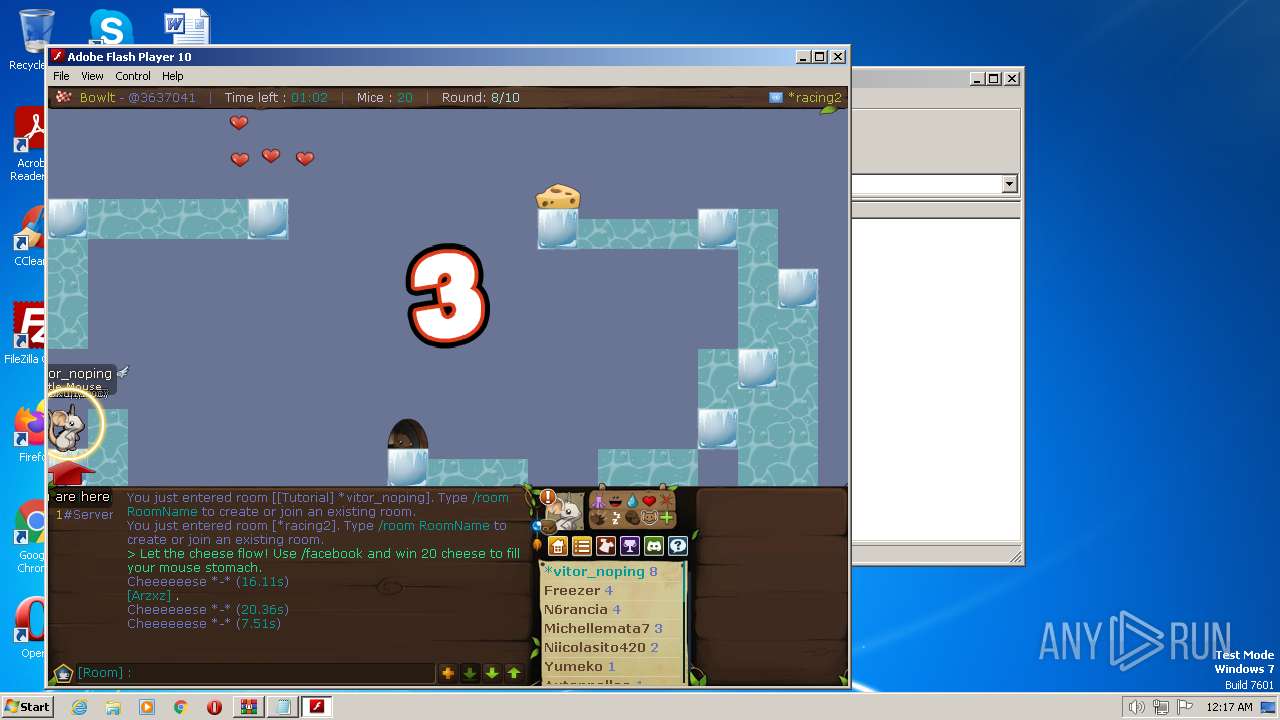
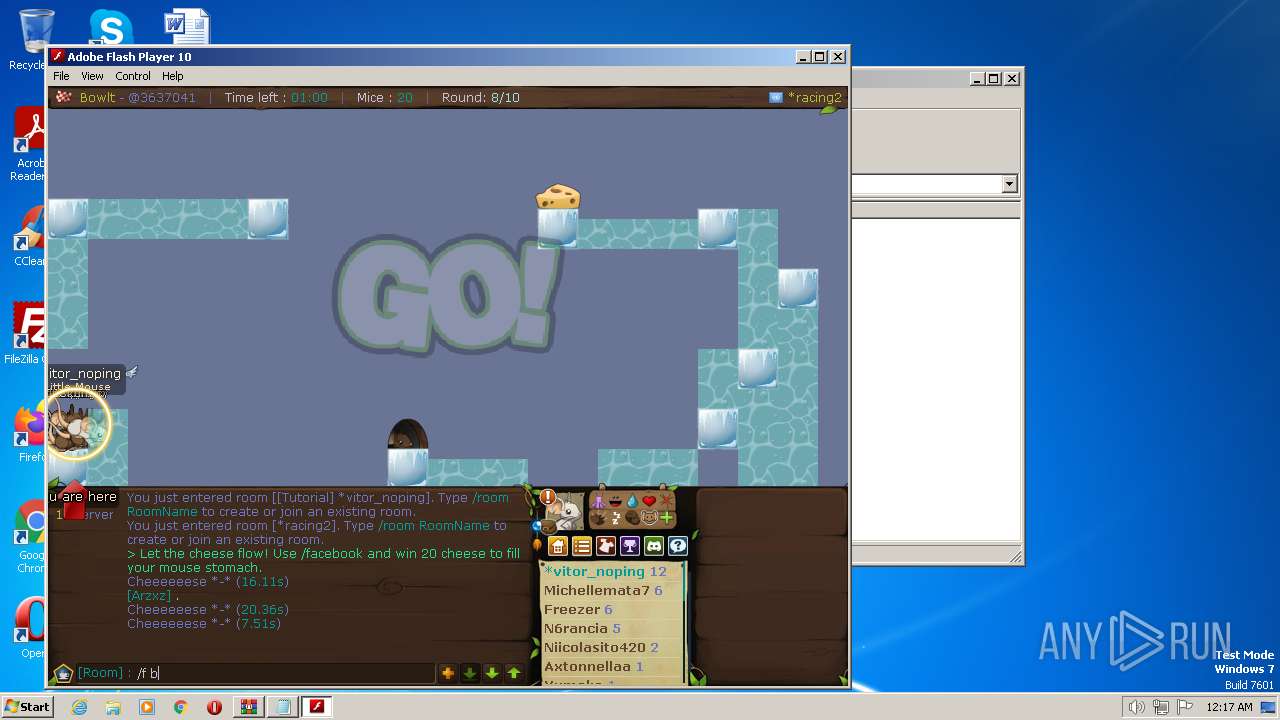
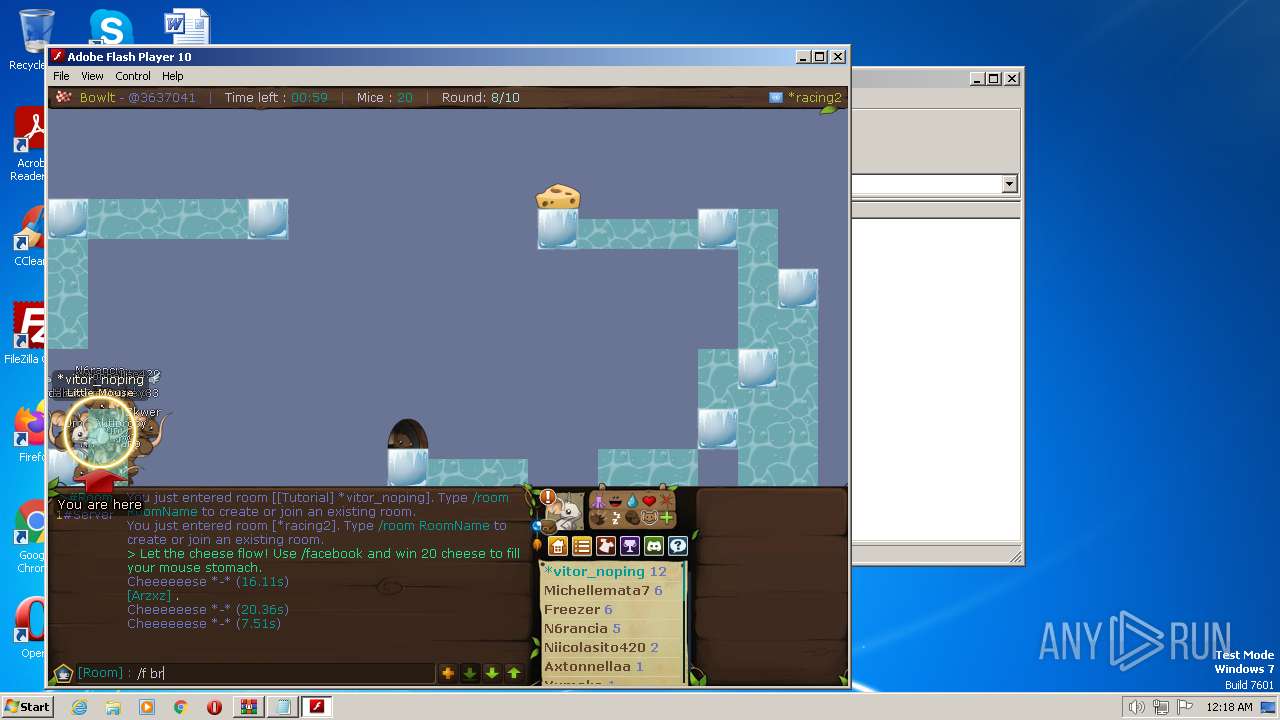
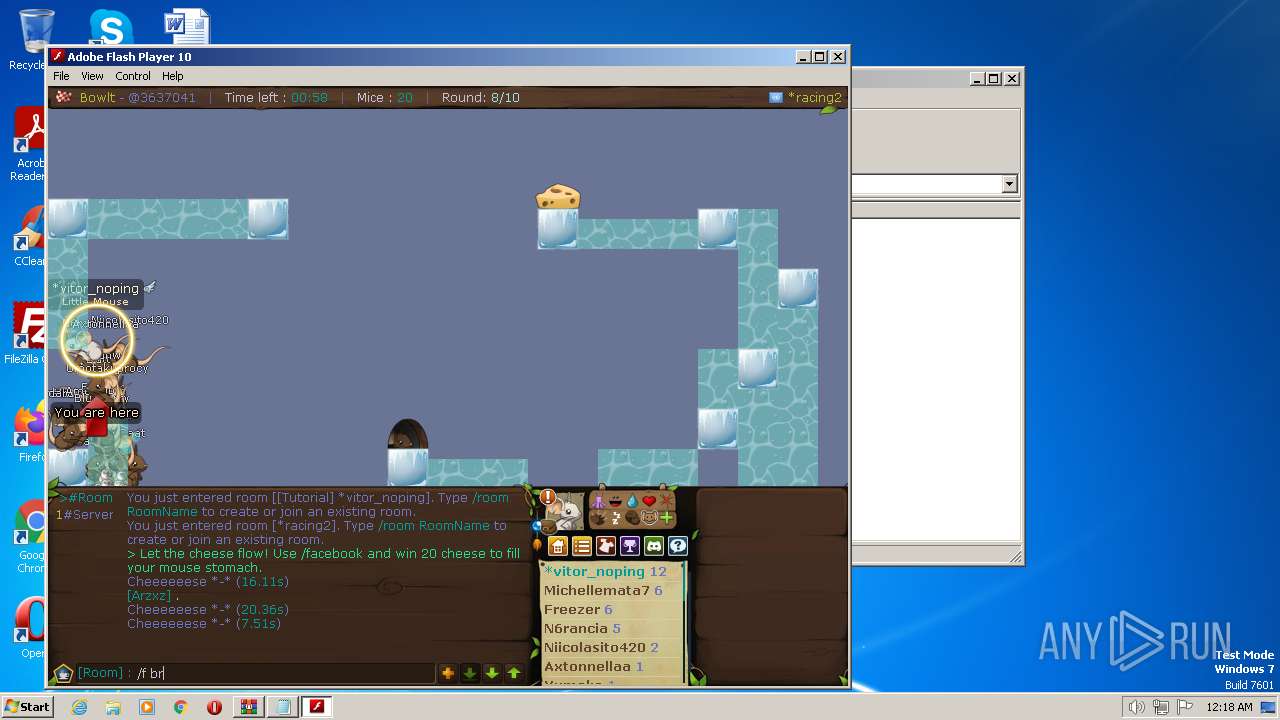
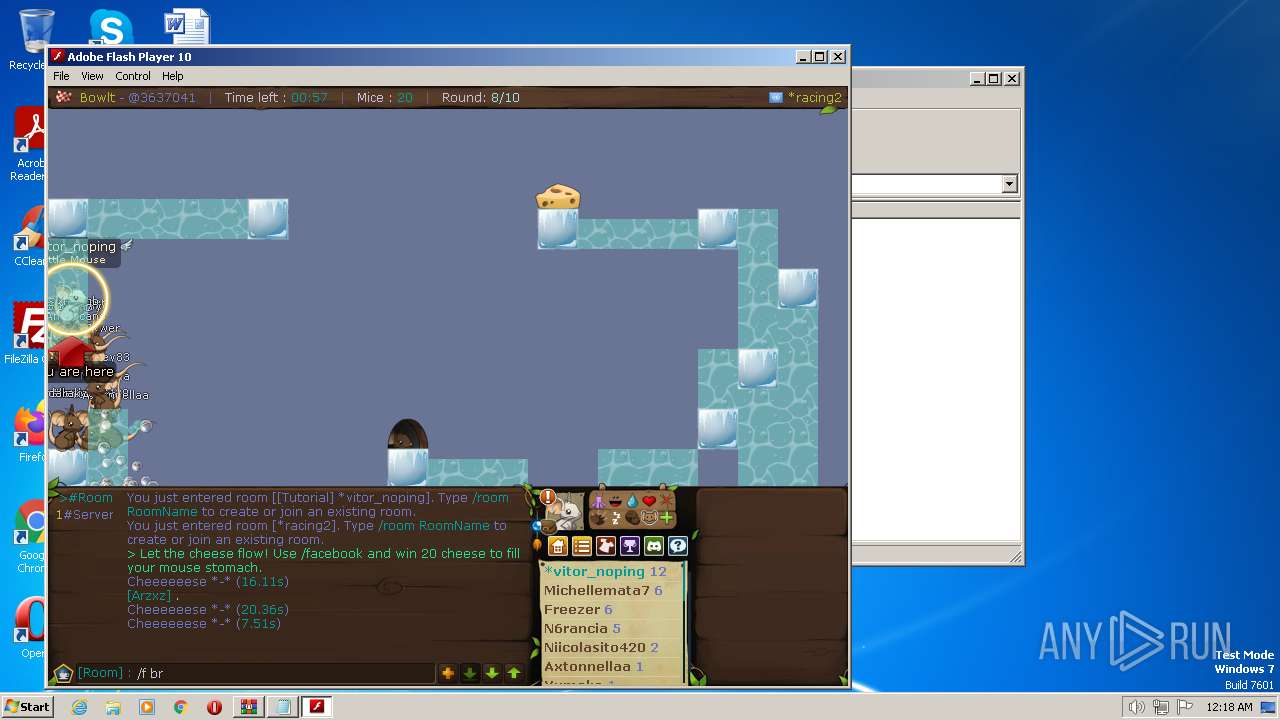
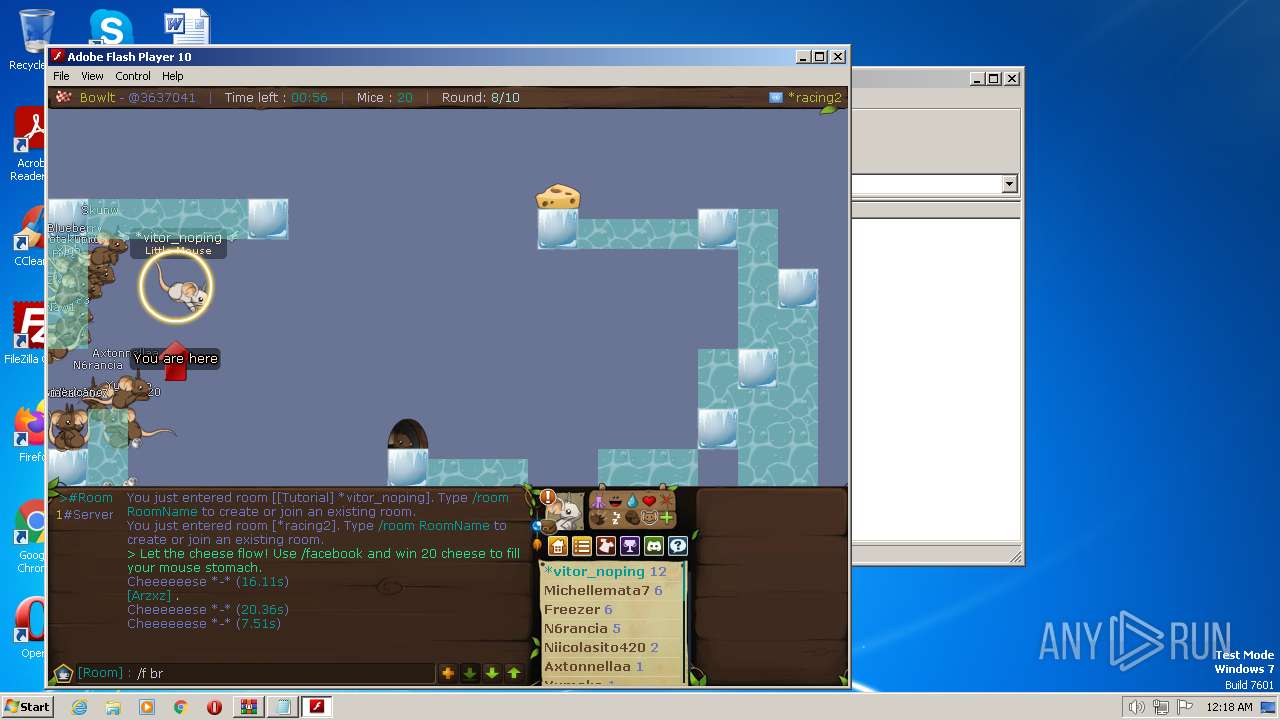
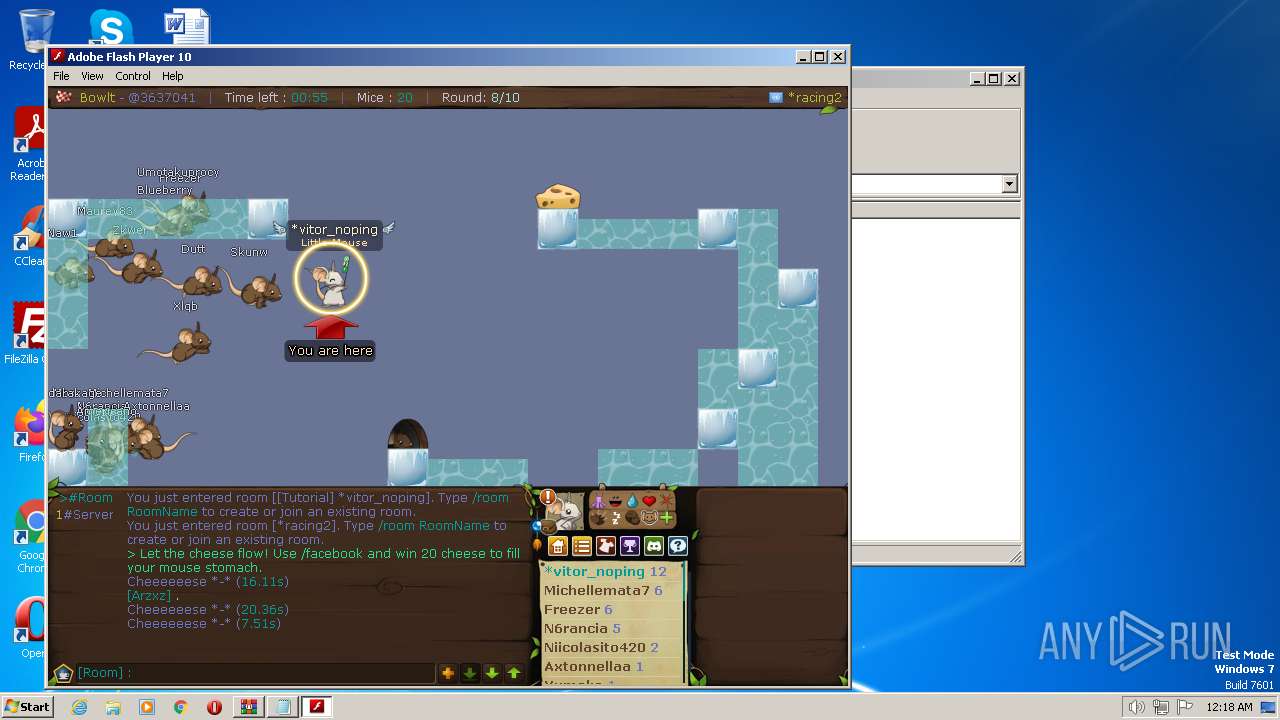
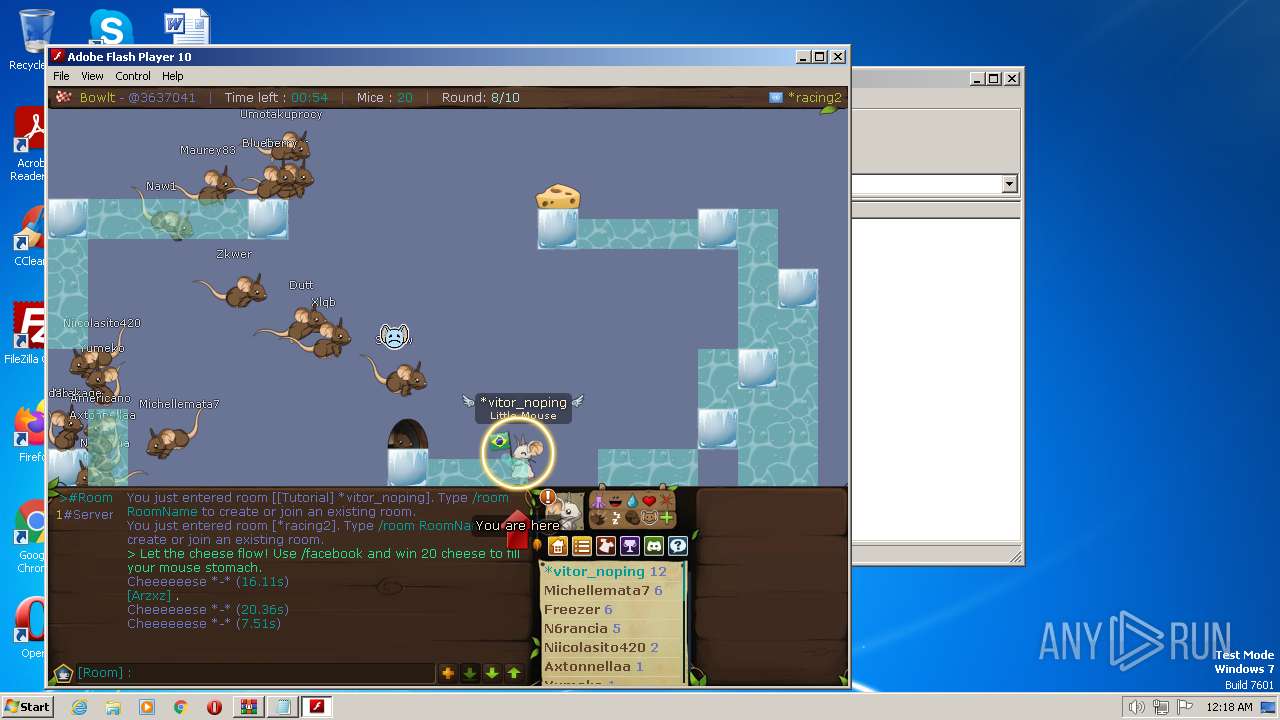
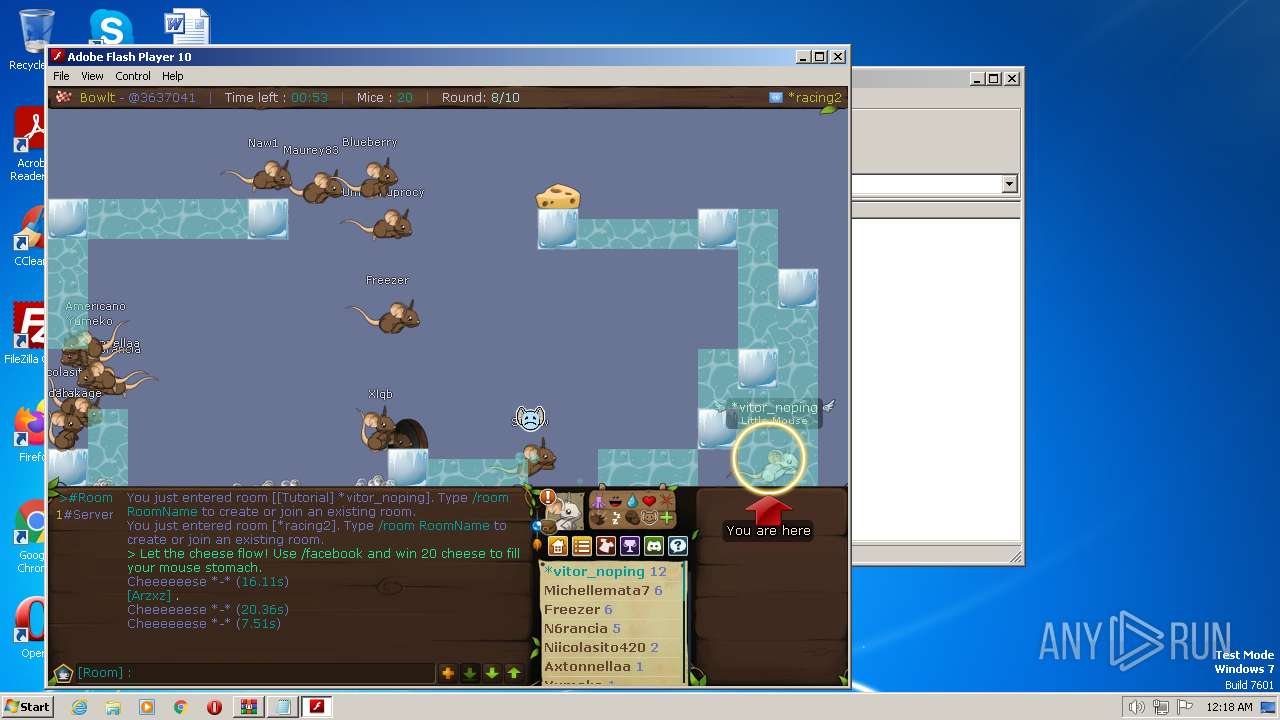
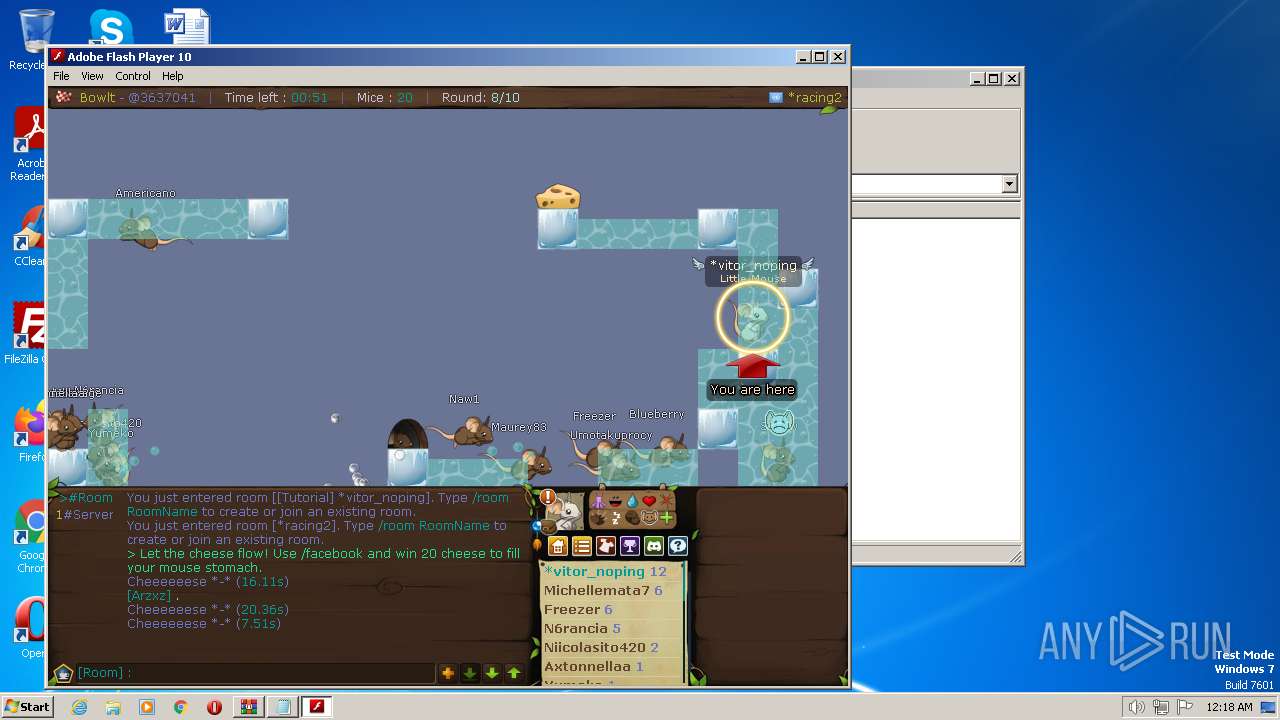
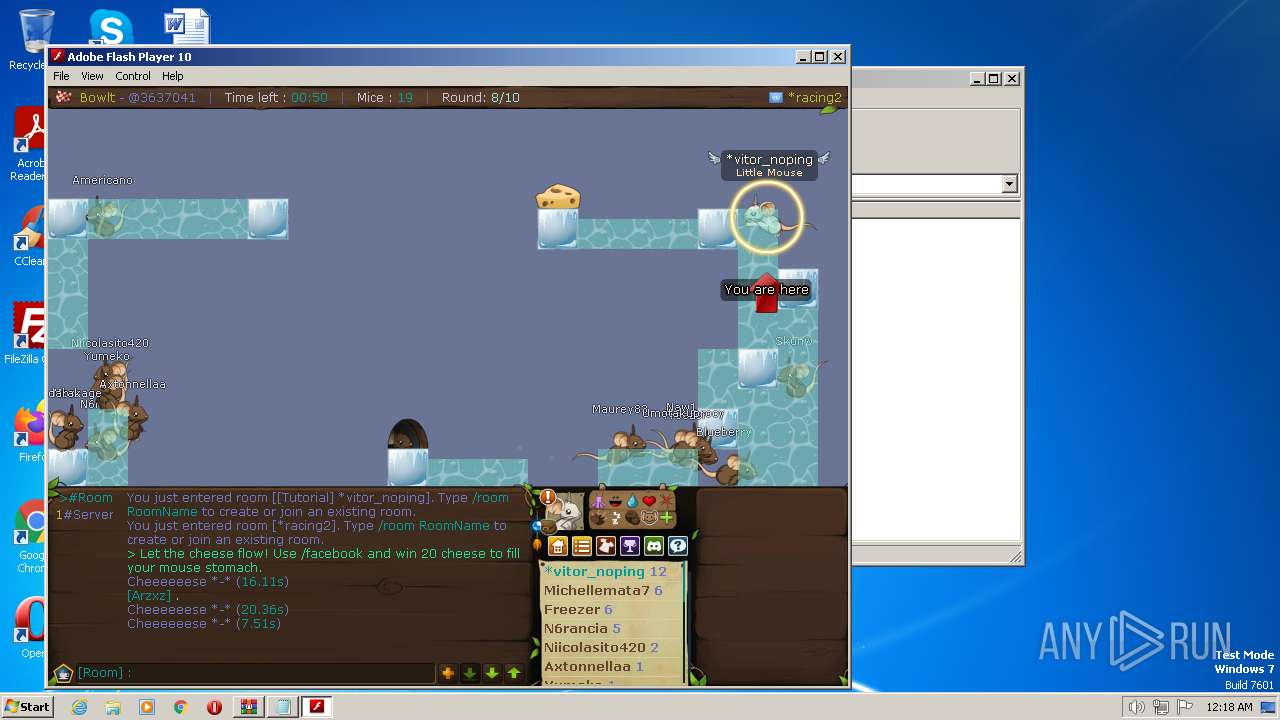
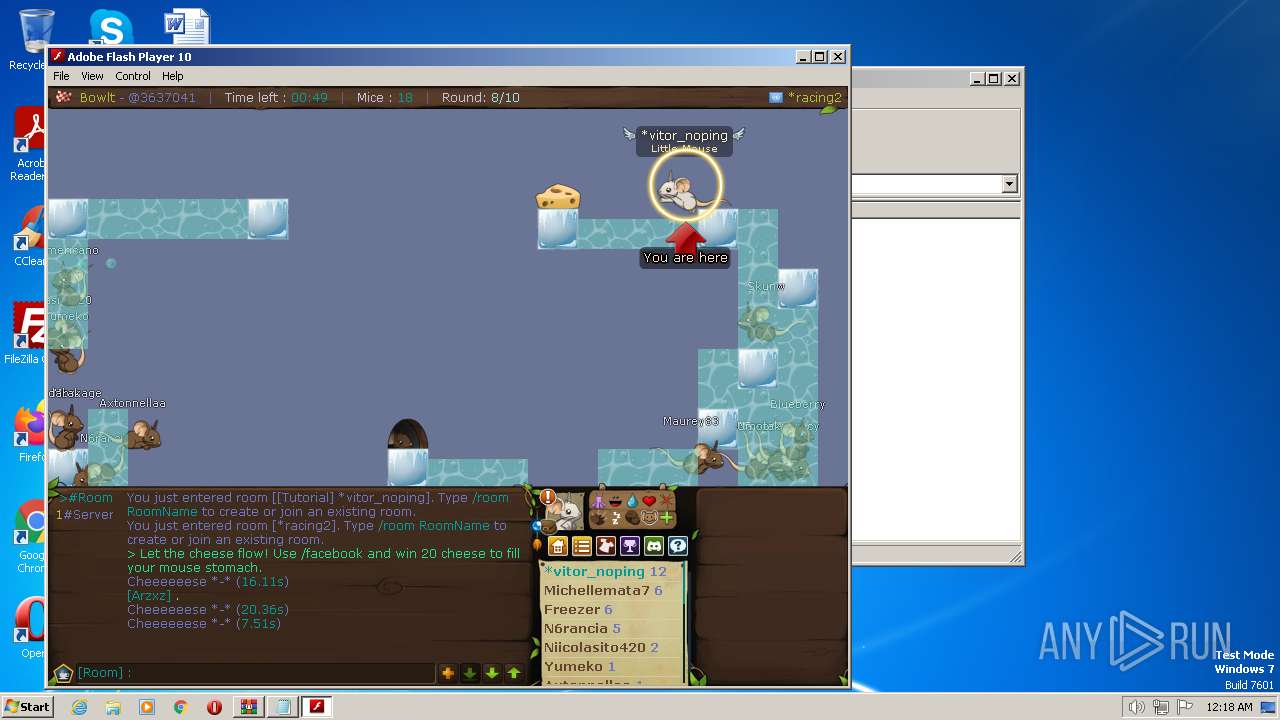
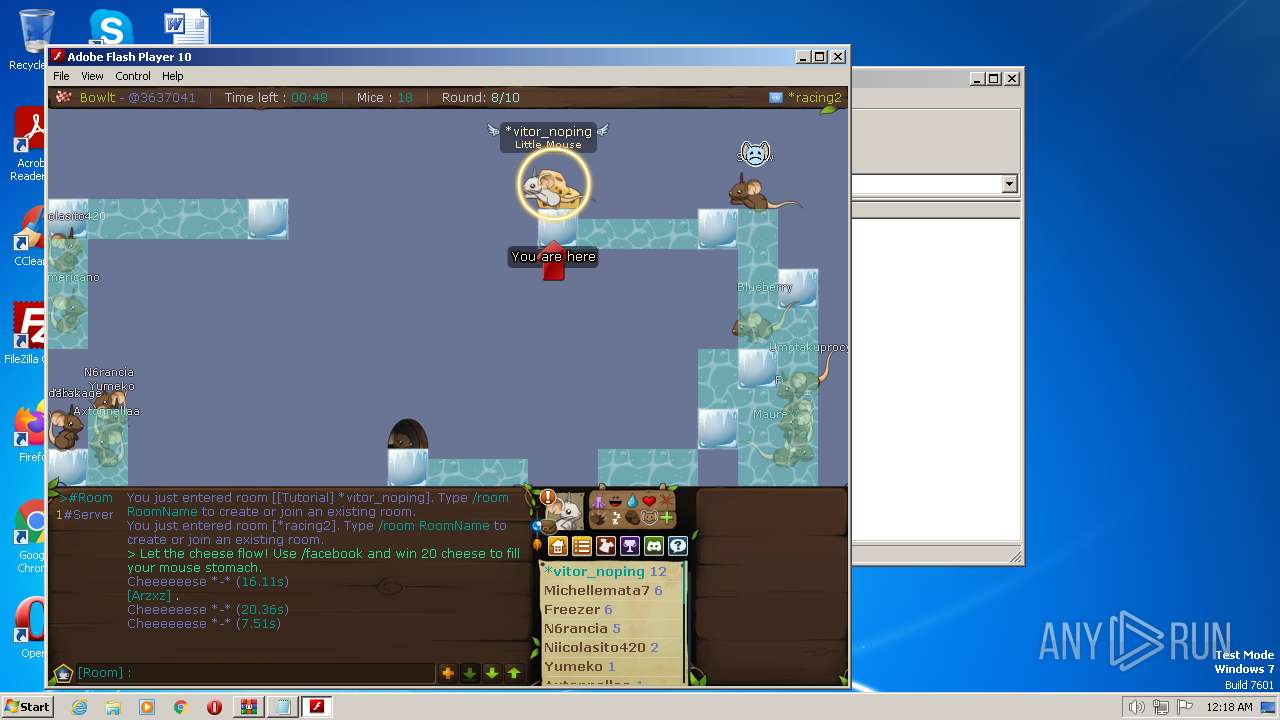
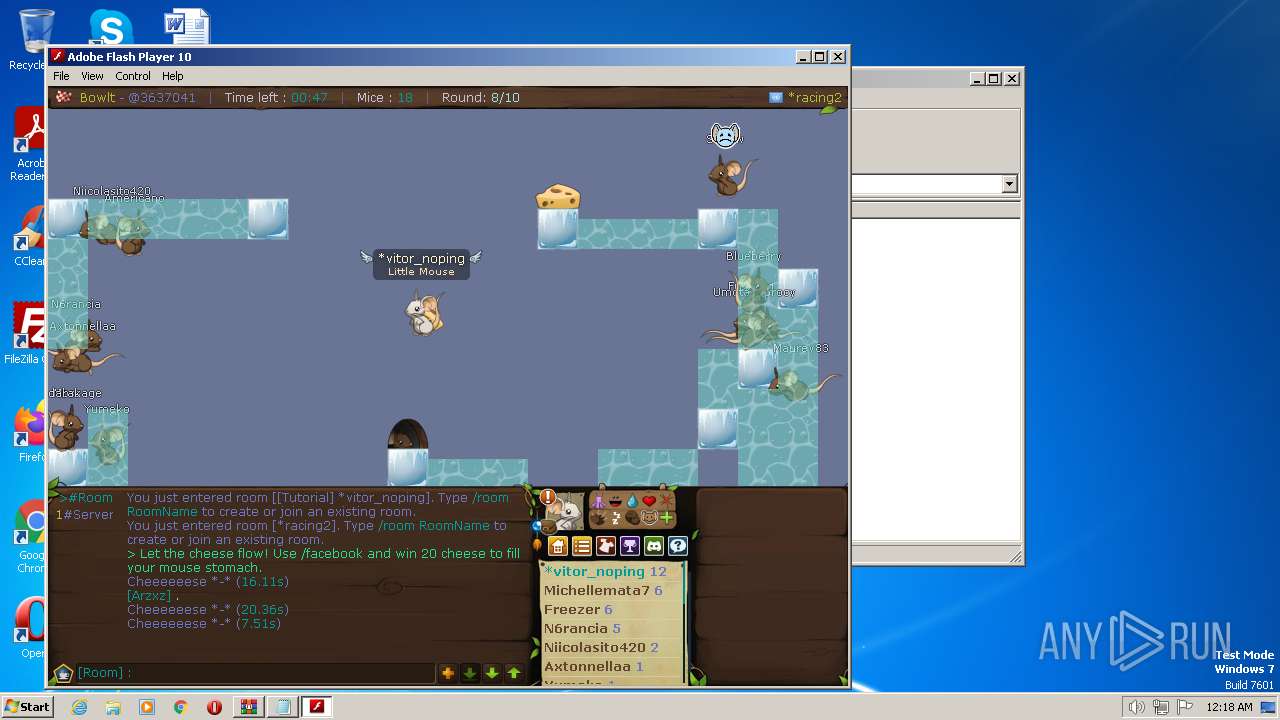
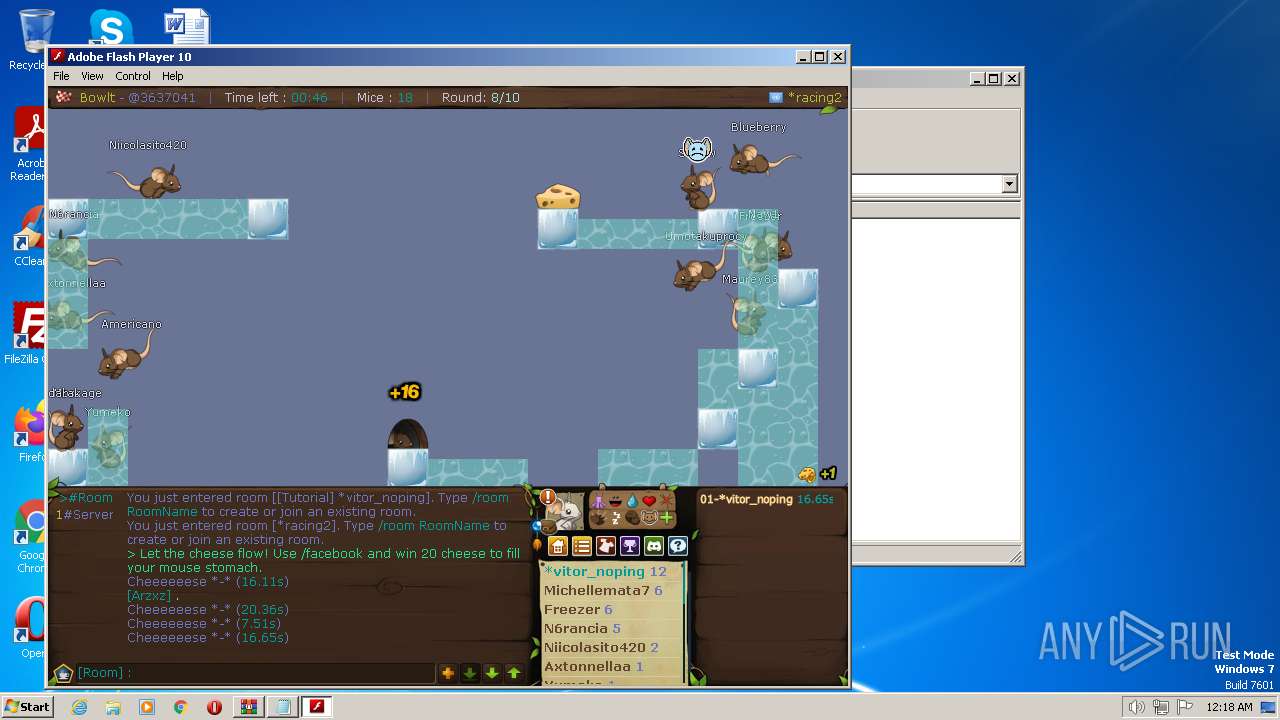
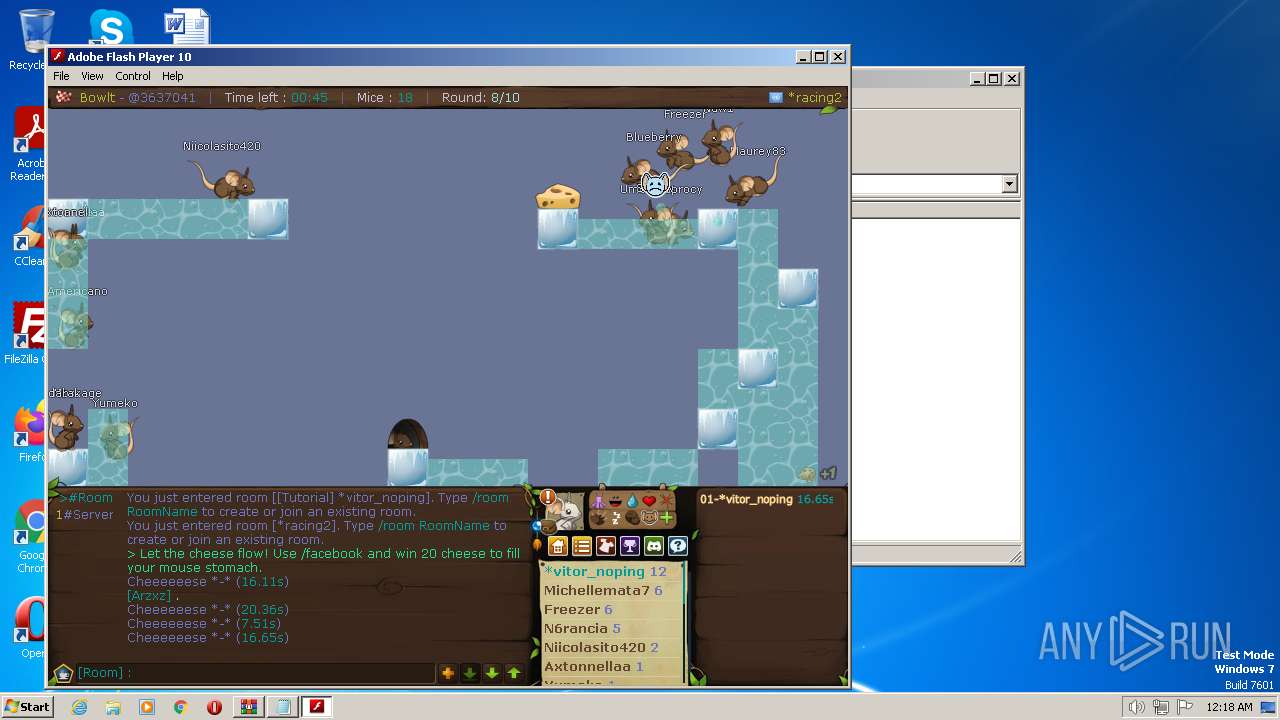
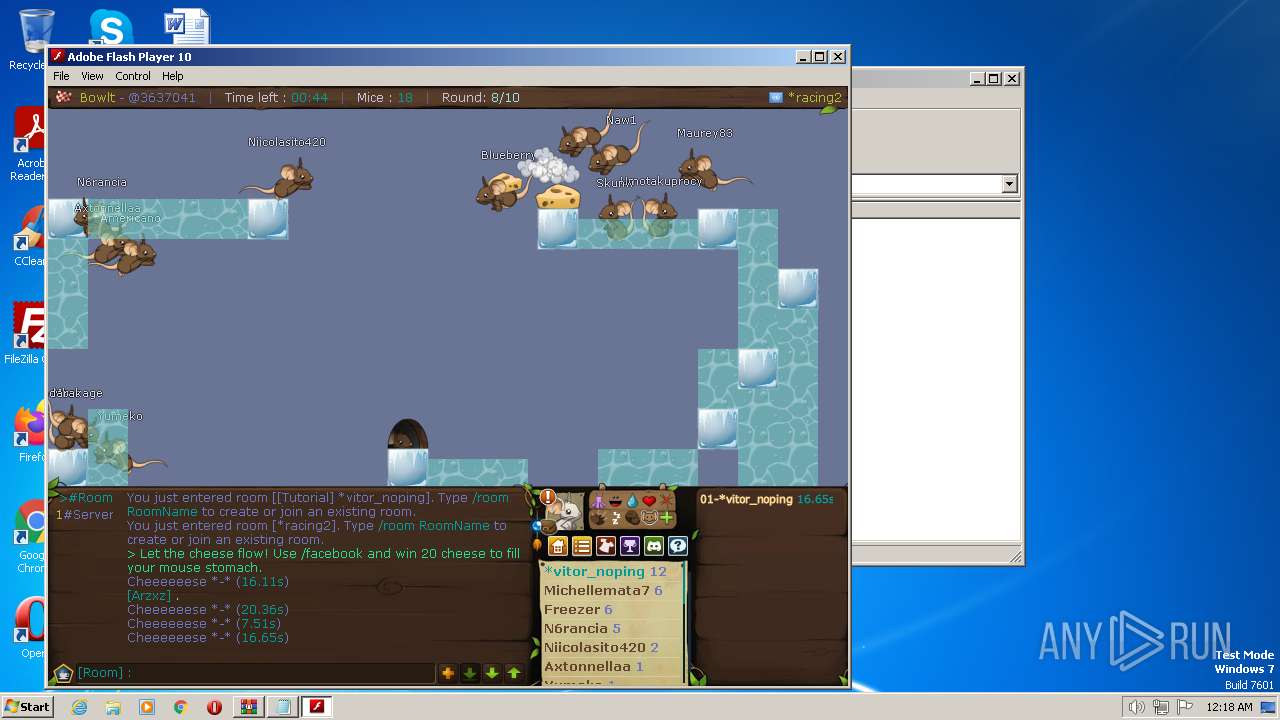
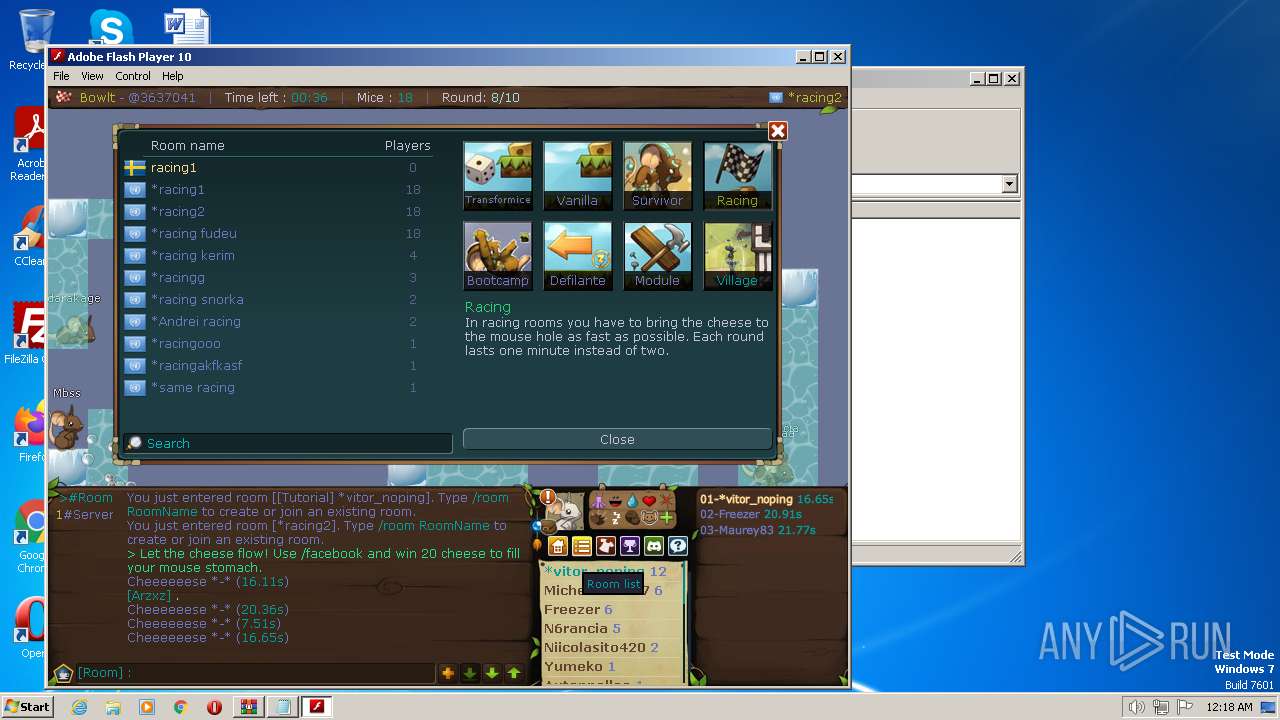
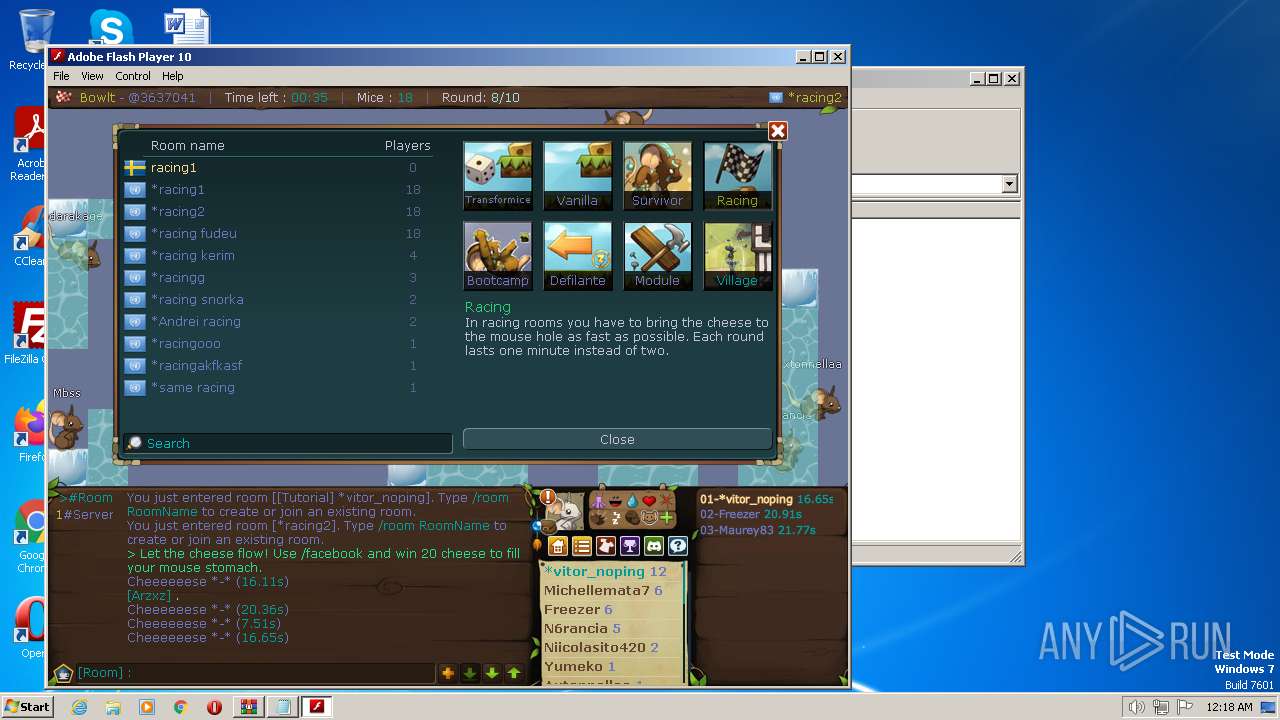
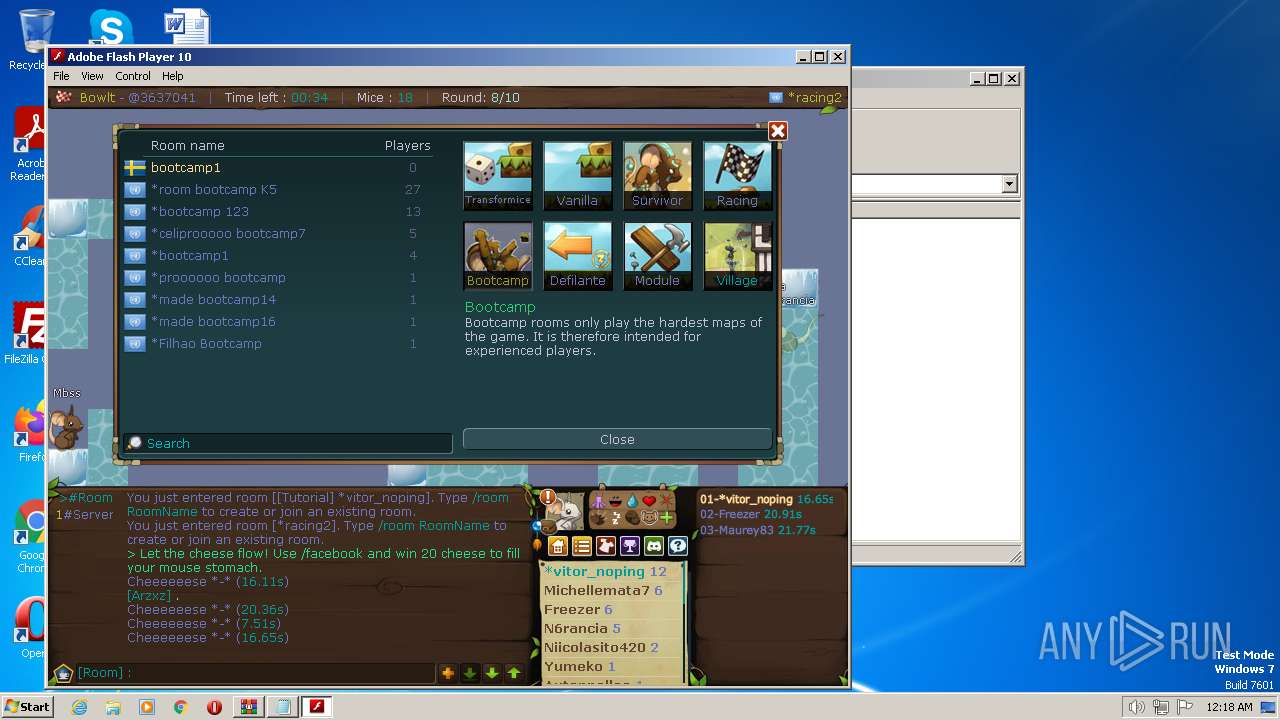
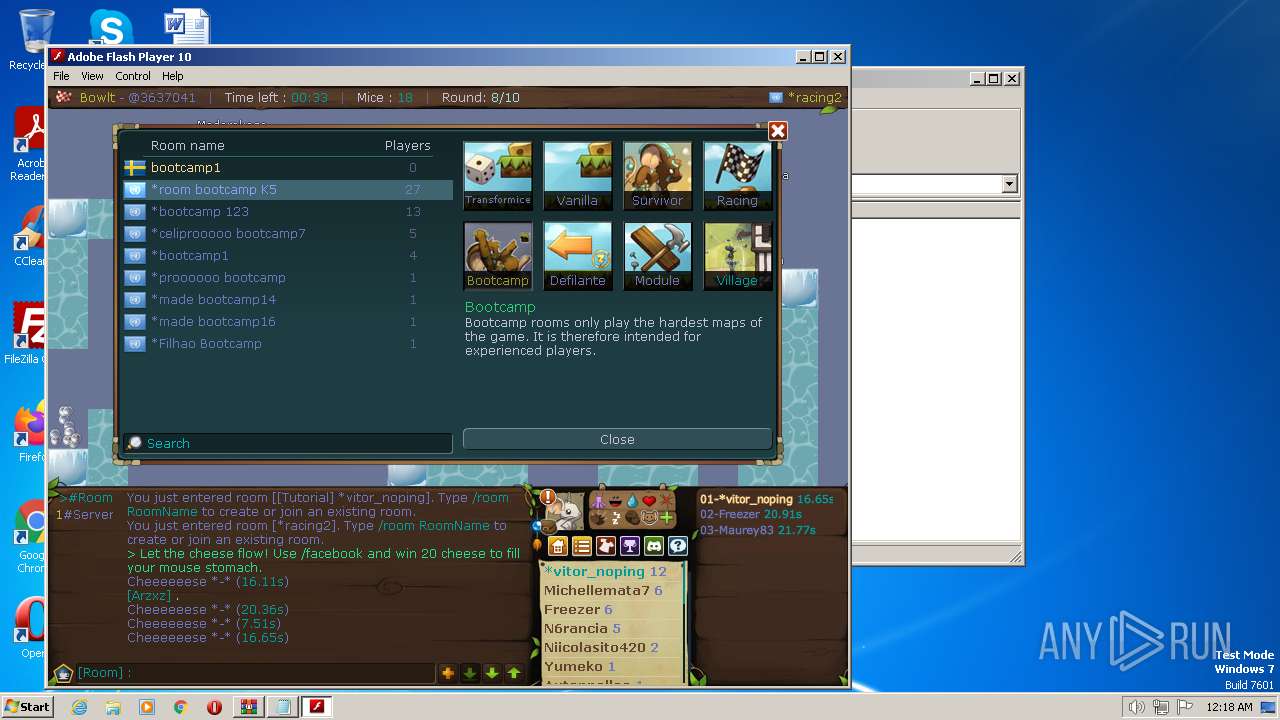
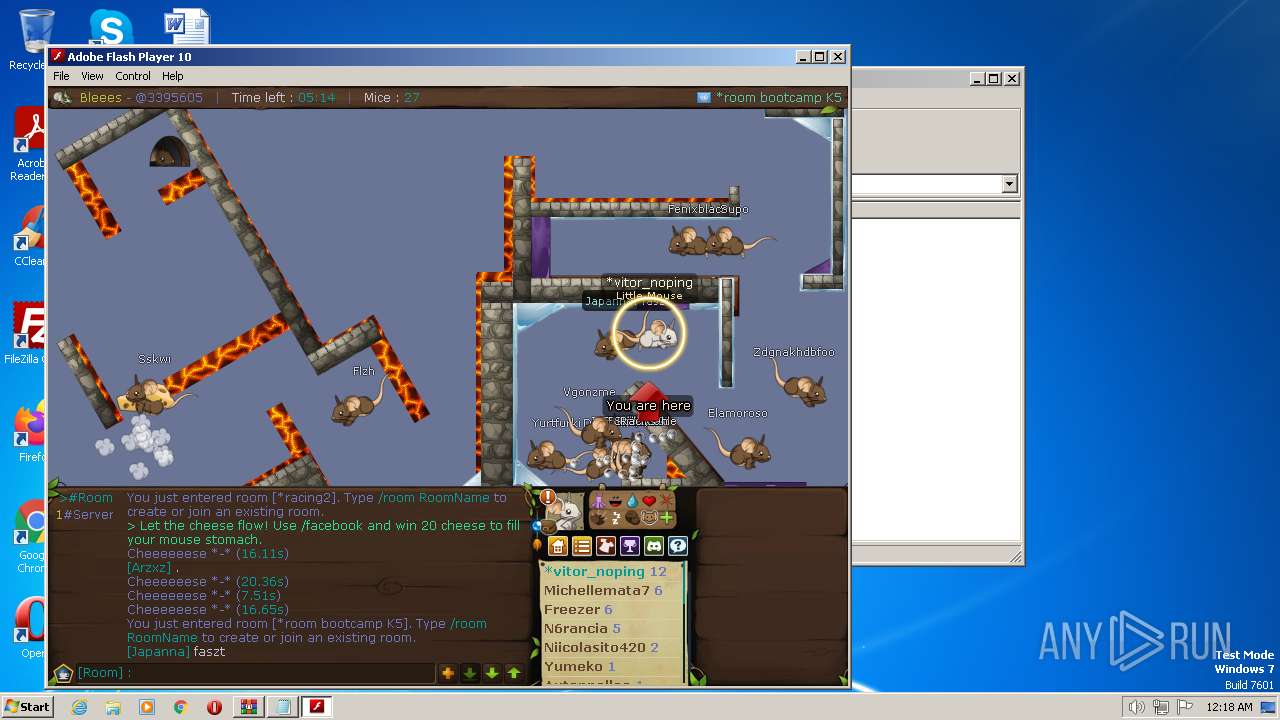
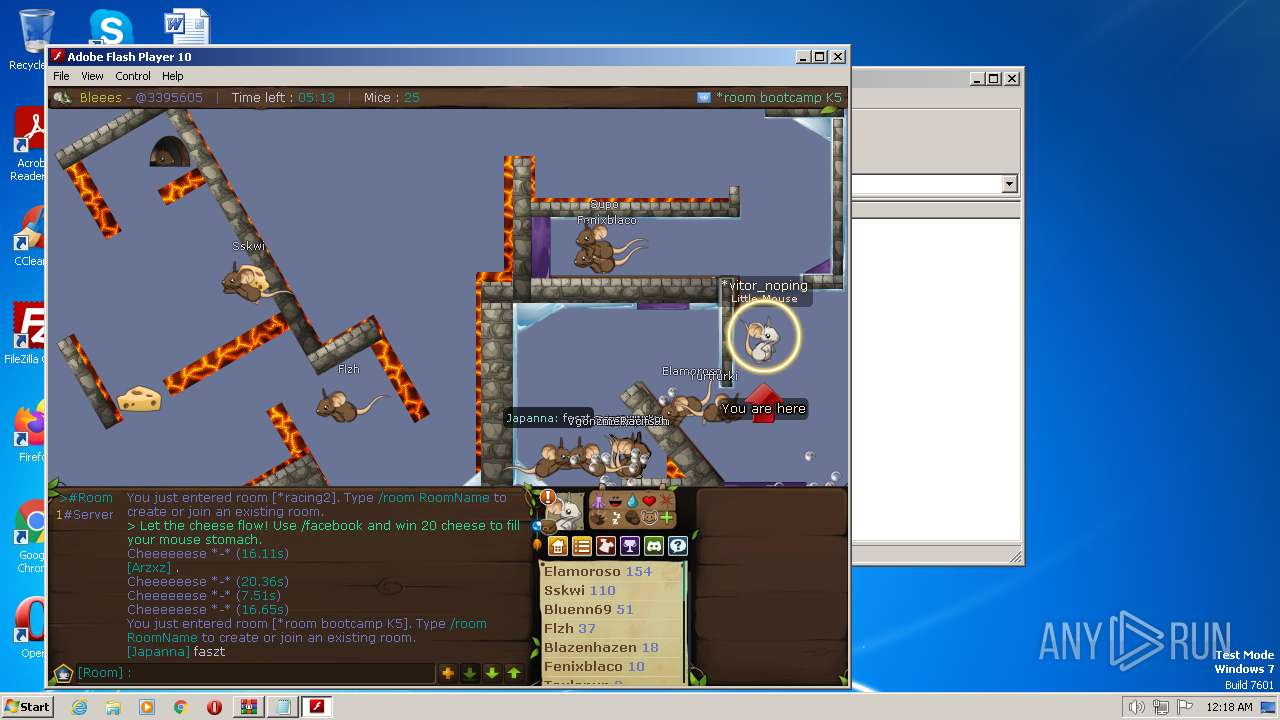
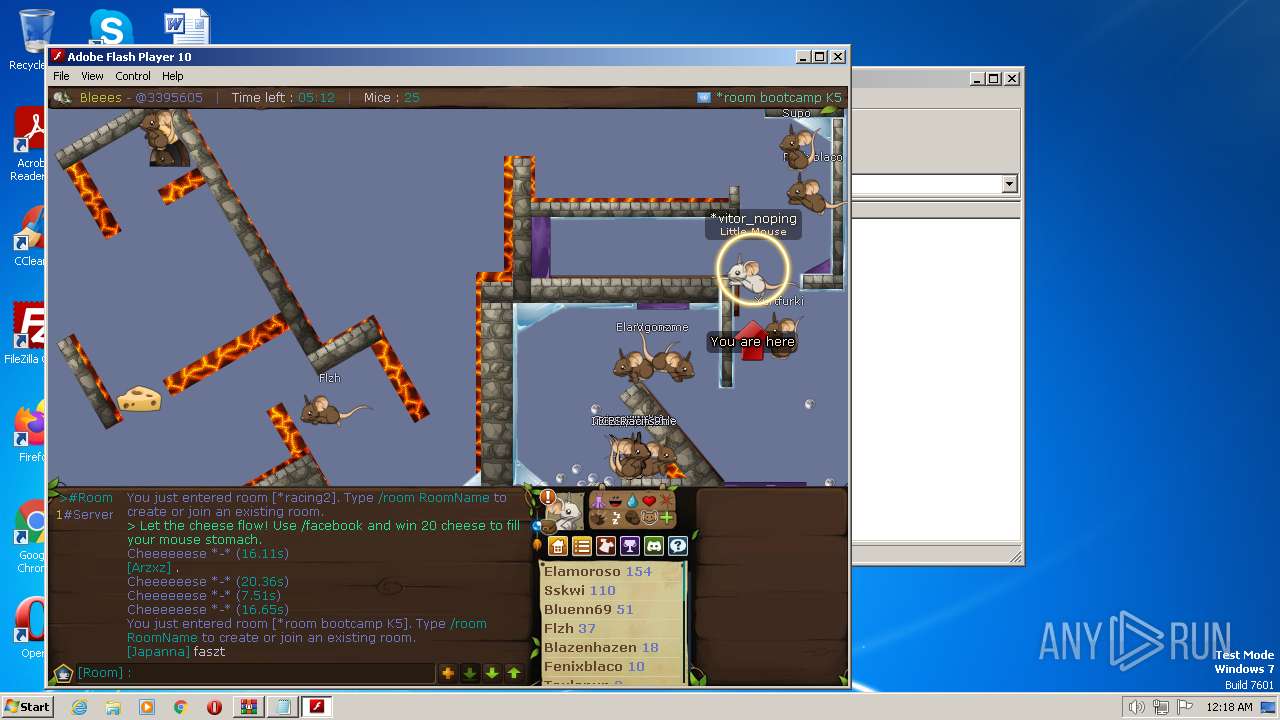
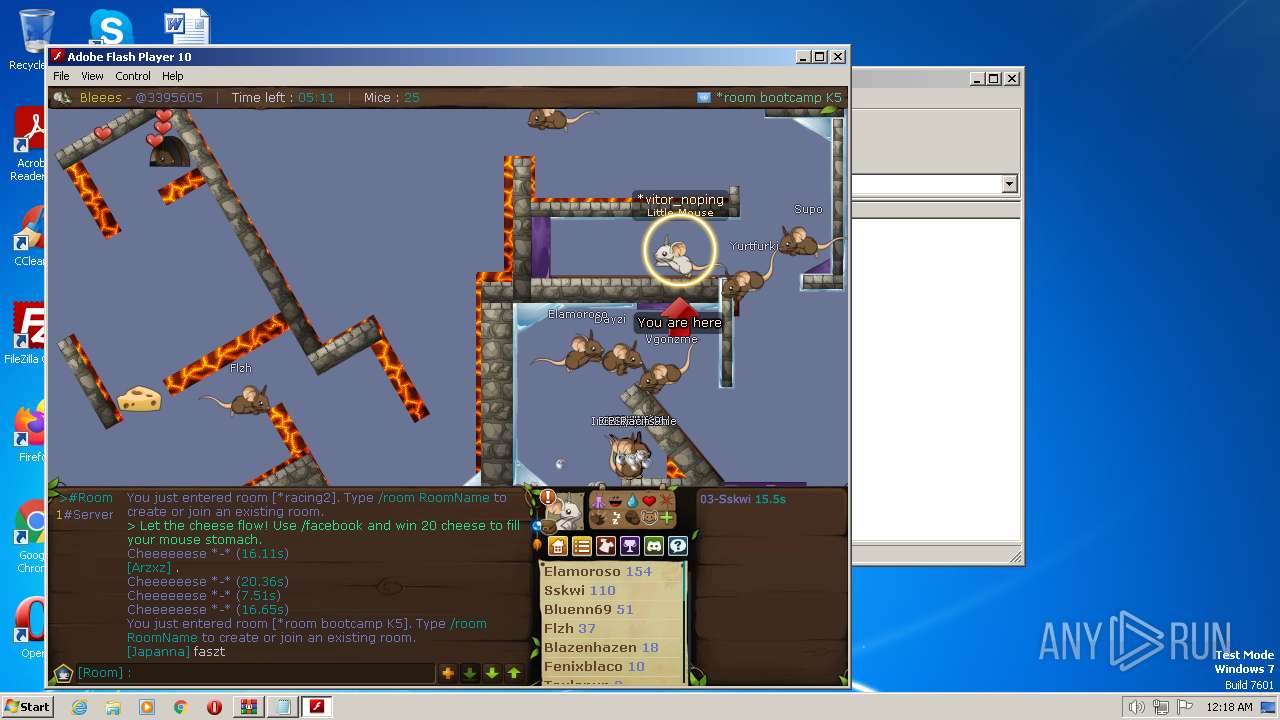
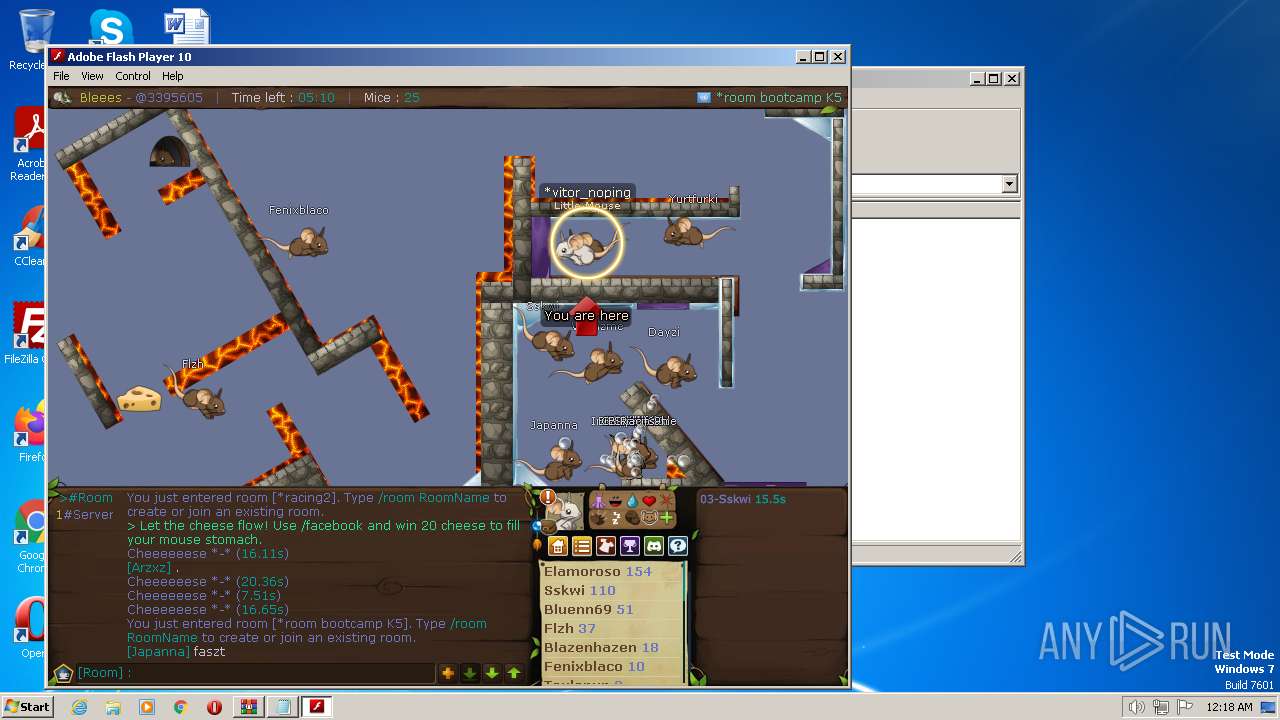
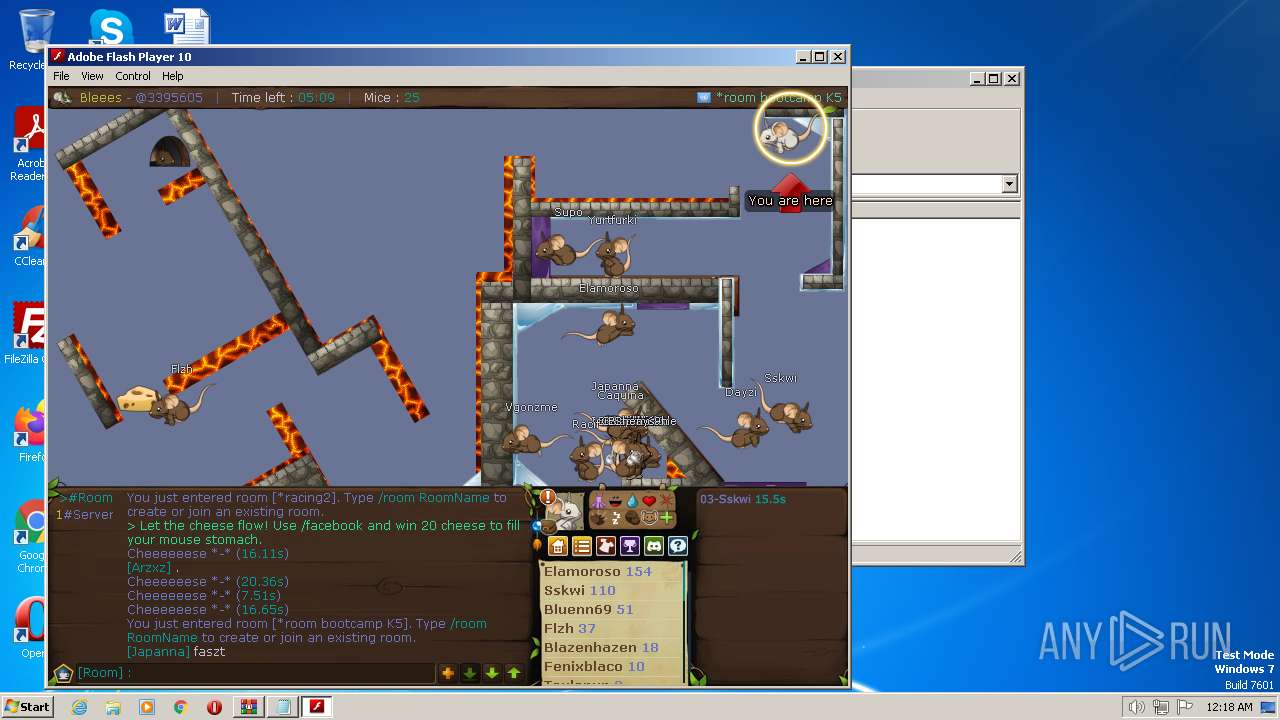
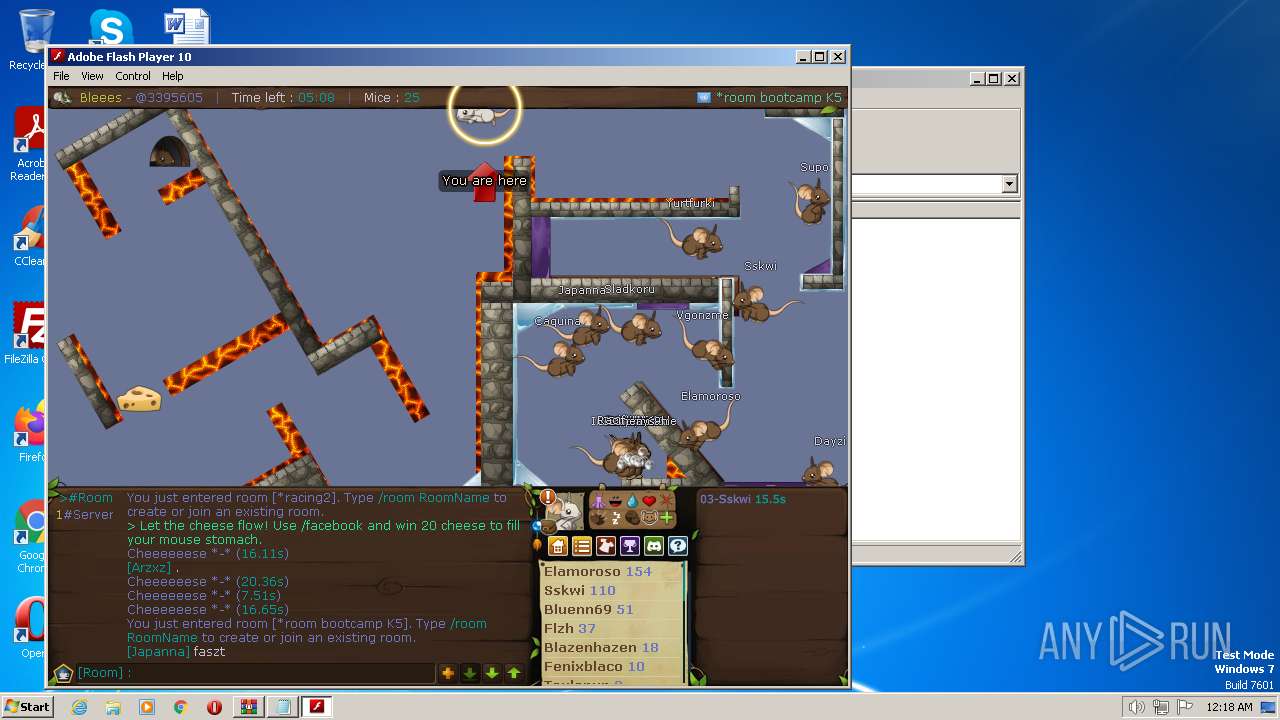
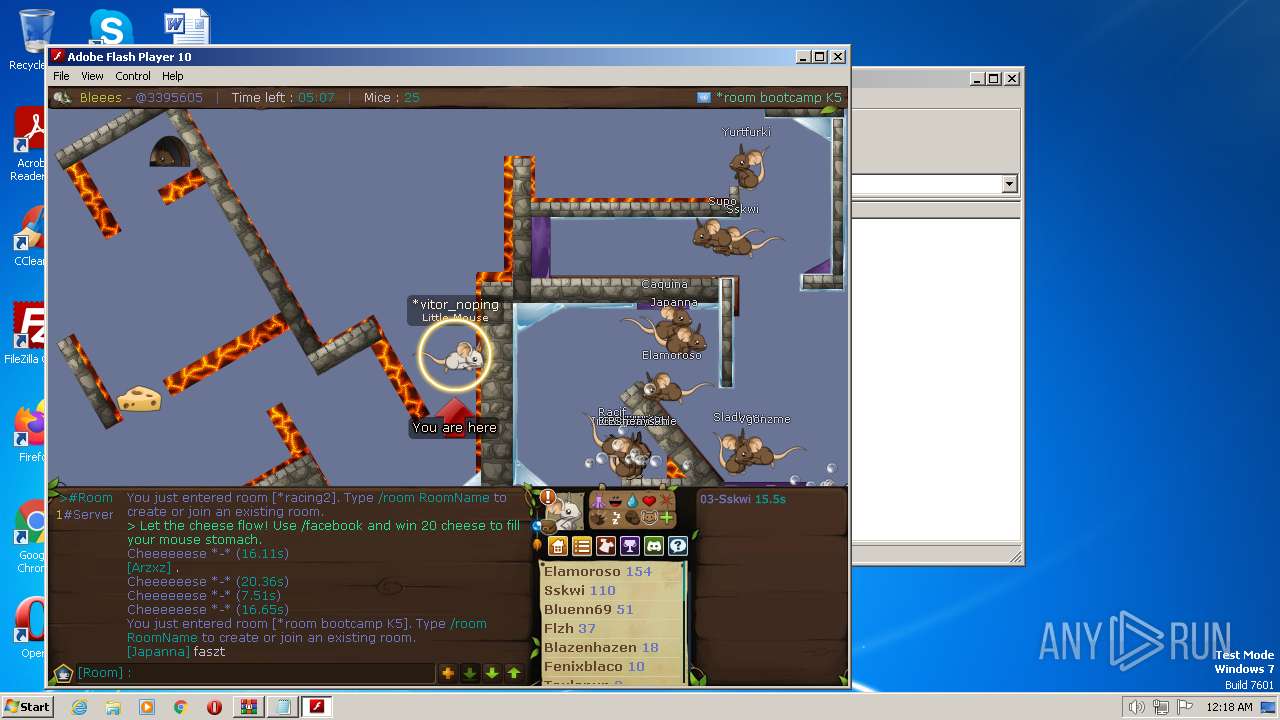
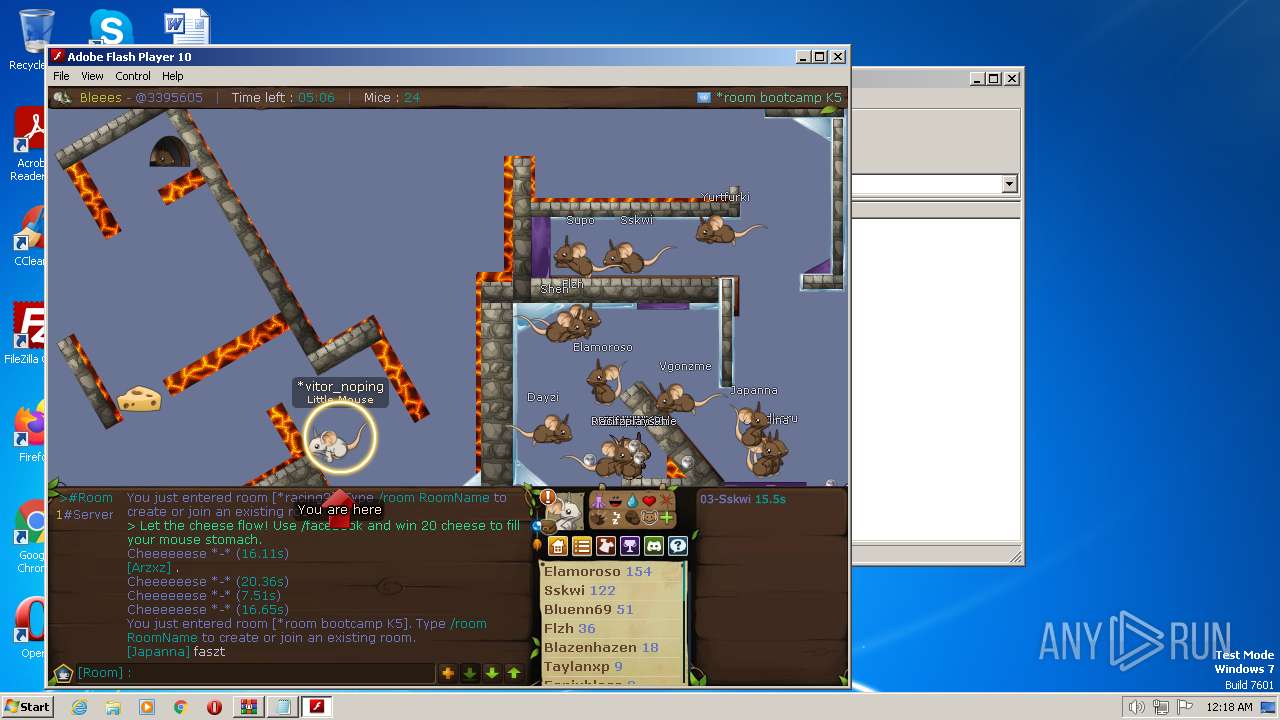
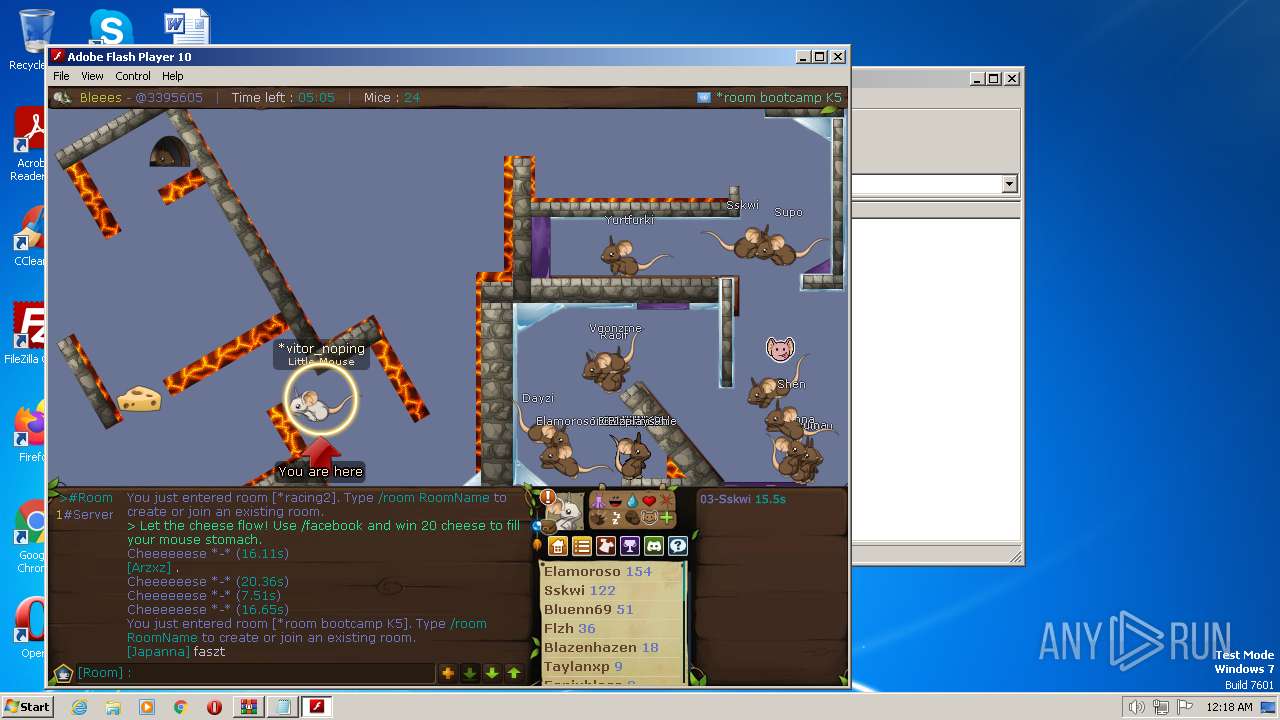
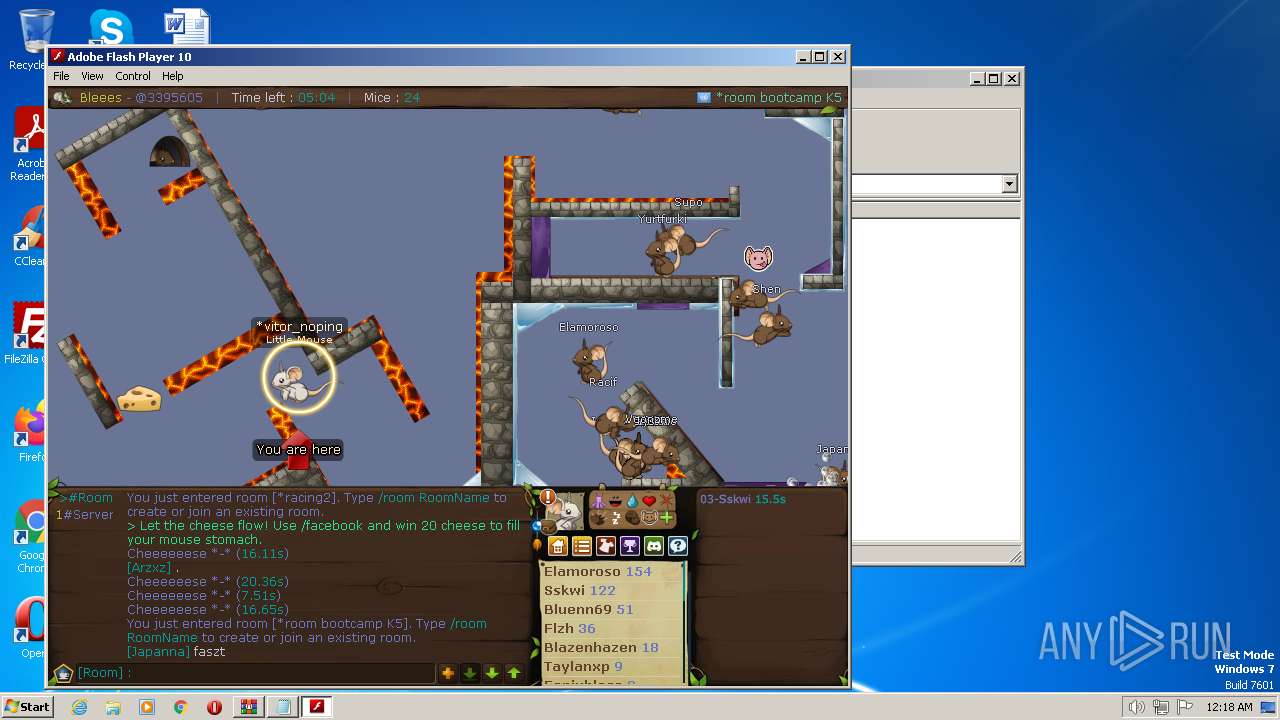
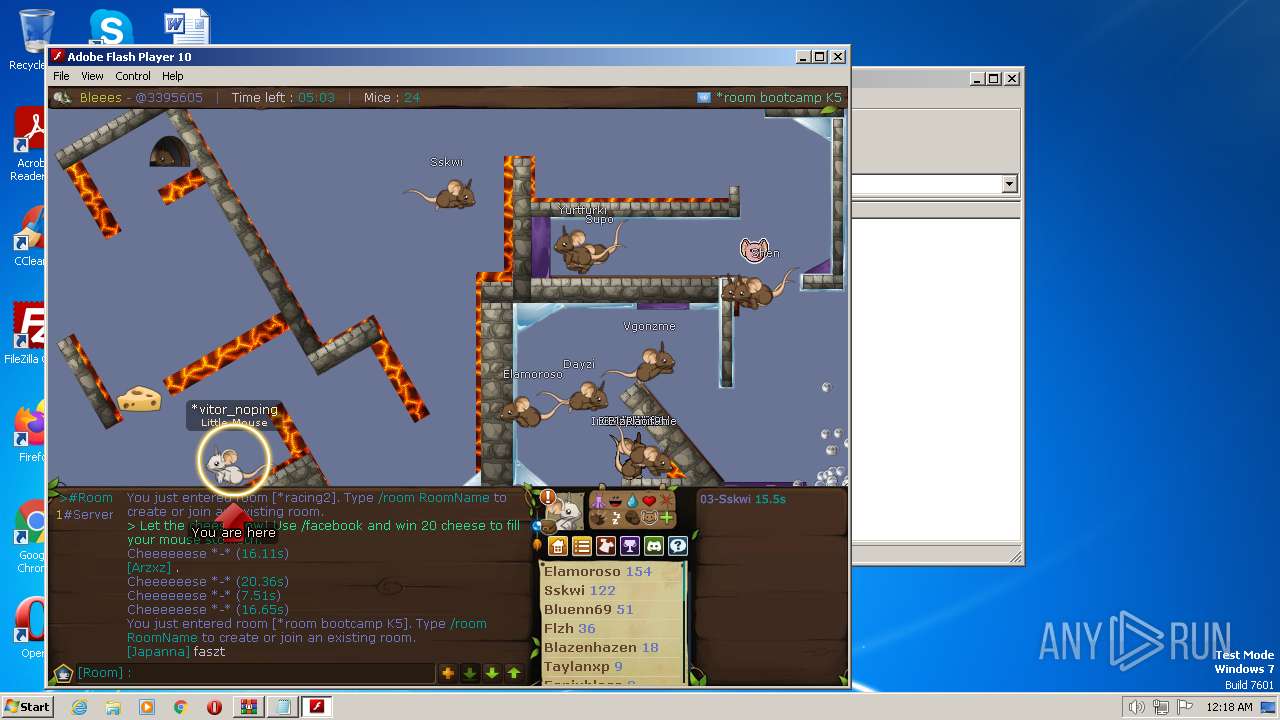
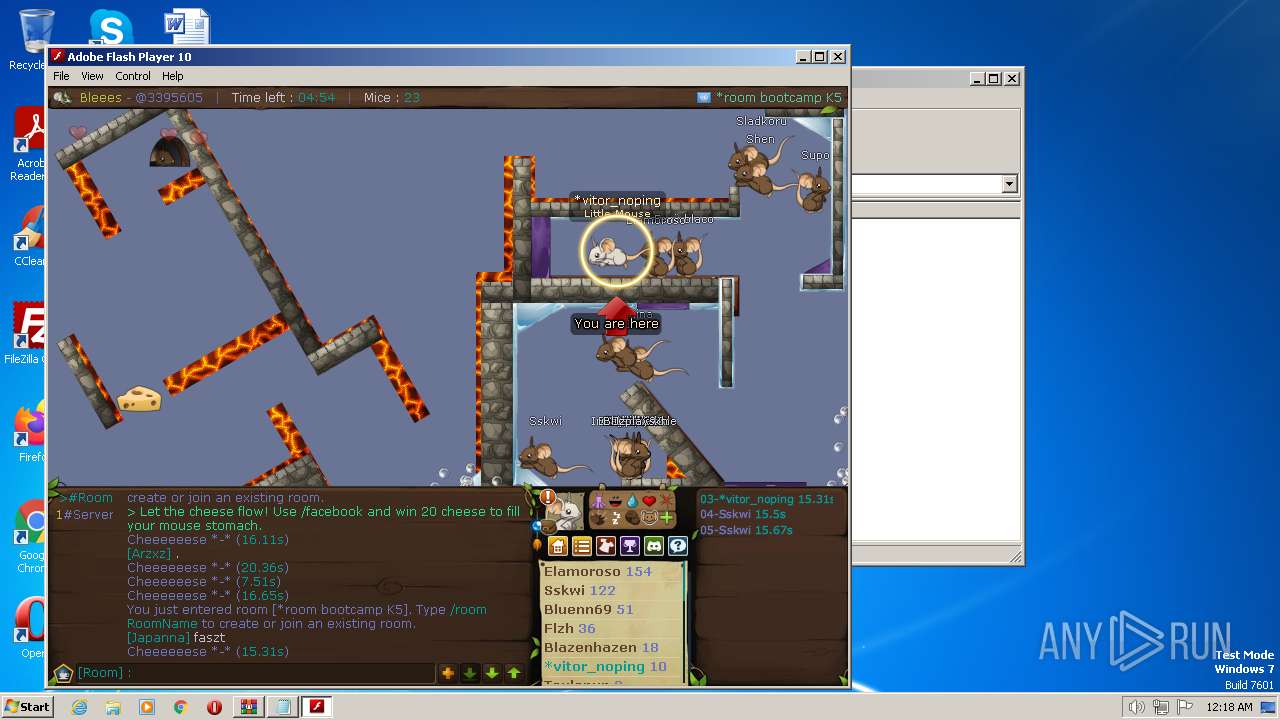
1492 | Adobe.exe | GET | 200 | 51.75.128.119:80 | http://www.transformice.com/crossdomain.xml | GB | text | 231 b | suspicious |
1492 | Adobe.exe | GET | 200 | 51.75.128.119:80 | http://www.transformice.com/images/x_transformice/x_interface/go.png?d=766 | GB | image | 9.50 Kb | suspicious |
1492 | Adobe.exe | GET | 200 | 108.156.0.73:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | US | binary | 1.39 Kb | shared |
1492 | Adobe.exe | GET | 200 | 23.37.41.57:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
1492 | Adobe.exe | GET | 200 | 52.222.226.205:80 | http://ocsp.r2m02.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRmbQtwnInkvkvr7BNFR%2BS2lTYPjAQUwDFSzVpQw4J8dHHOy%2Bmc%2BXrrguICEAIQIYEWnOrZU009A4w%2FQ80%3D | US | binary | 471 b | whitelisted |
1492 | Adobe.exe | GET | 200 | 51.75.128.119:80 | http://www.transformice.com/images/x_transformice/x_interface/c1.png?d=766 | GB | image | 2.59 Kb | suspicious |
1492 | Adobe.exe | GET | 200 | 51.75.128.119:80 | http://www.transformice.com/images/x_transformice/x_interface/c3.png?d=766 | GB | image | 4.61 Kb | suspicious |
1492 | Adobe.exe | GET | 200 | 51.75.128.119:80 | http://www.transformice.com/images/x_transformice/x_interface/c2.png?d=766 | GB | image | 4.09 Kb | suspicious |
1492 | Adobe.exe | GET | 200 | 51.75.128.119:80 | http://www.transformice.com/images/x_transformice/x_connexion/x_steam_.jpg?d=766 | GB | image | 12.1 Kb | suspicious |
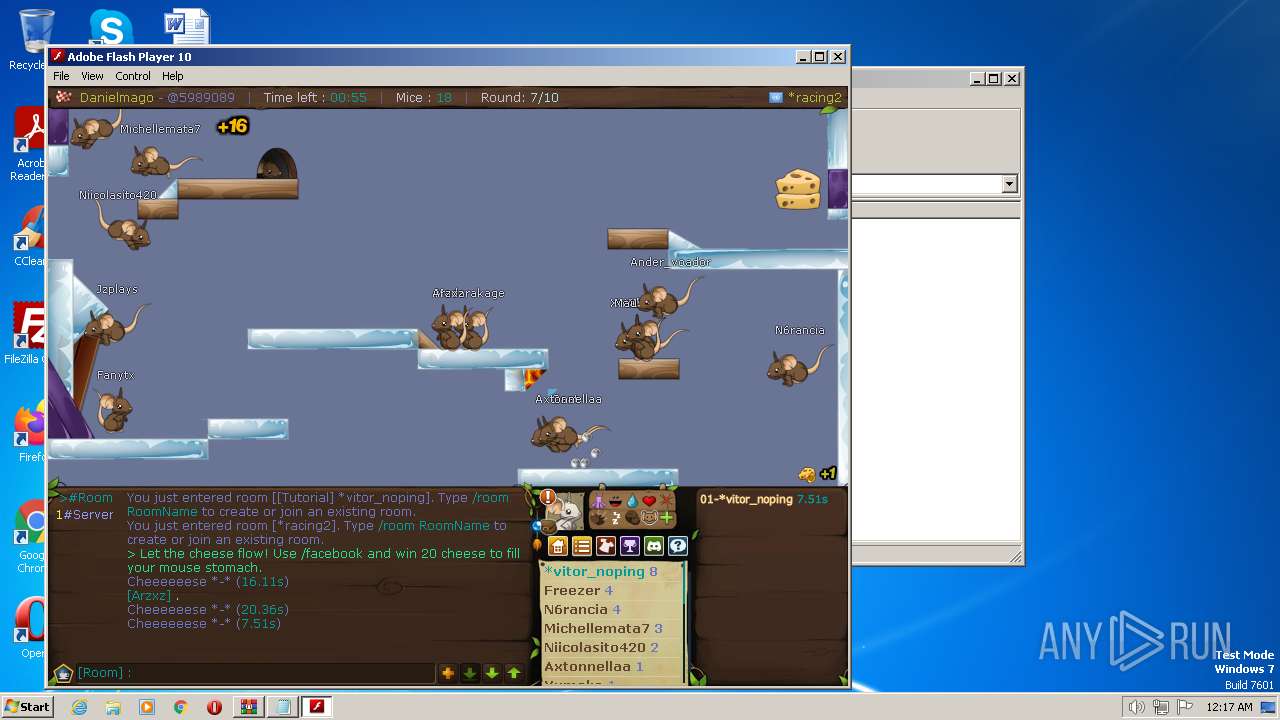
1492 | Adobe.exe | GET | 200 | 212.47.246.230:80 | http://audio.atelier801.com/transformice/musique/intro.mp3 | FR | binary | 931 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1492 | Adobe.exe | 108.156.0.73:80 | ocsp.rootca1.amazontrust.com | AMAZON-02 | US | whitelisted |
1492 | Adobe.exe | 3.216.88.24:443 | src.herokuapp.com | AMAZON-AES | US | suspicious |
— | — | 193.70.81.30:843 | — | OVH SAS | FR | unknown |
— | — | 193.70.81.30:12801 | — | OVH SAS | FR | unknown |
— | — | 51.75.128.119:80 | www.transformice.com | OVH SAS | FR | suspicious |
— | — | 51.75.128.119:443 | www.transformice.com | OVH SAS | FR | suspicious |
1492 | Adobe.exe | 23.37.41.57:80 | x1.c.lencr.org | AKAMAI-AS | DE | suspicious |
1492 | Adobe.exe | 2.16.241.15:80 | r3.o.lencr.org | Akamai International B.V. | DE | suspicious |
1492 | Adobe.exe | 212.47.246.230:80 | audio.atelier801.com | Online S.a.s. | FR | suspicious |
1492 | Adobe.exe | 51.75.128.119:443 | www.transformice.com | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
src.herokuapp.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.r2m02.amazontrust.com |
| whitelisted |
www.transformice.com |
| suspicious |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
audio.atelier801.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
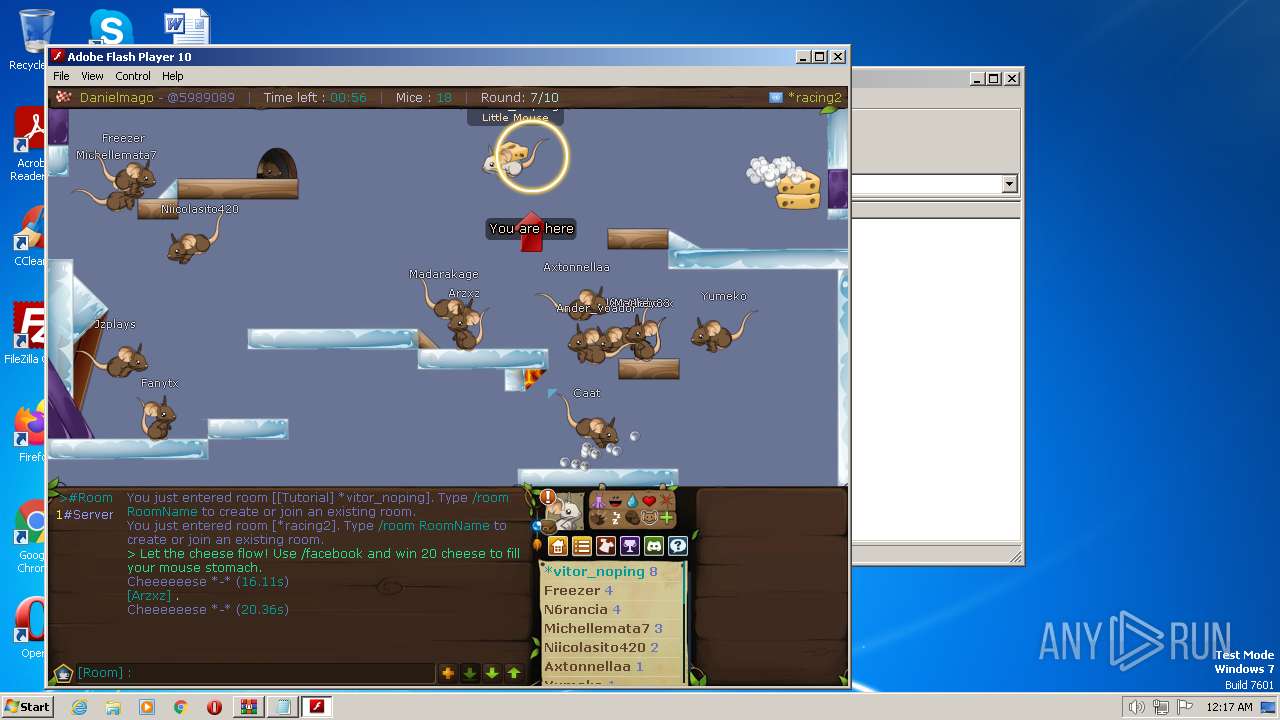
1492 | Adobe.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |
1492 | Adobe.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |
1492 | Adobe.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |
56 ETPRO signatures available at the full report