| File name: | AdobeGenP-3.4.13.4.exe |
| Full analysis: | https://app.any.run/tasks/5cfa8606-d1d1-47ee-9153-c50ead0a5b24 |
| Verdict: | Malicious activity |
| Analysis date: | September 05, 2024, 02:40:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | DDA7AC07C4630A25A65A40EB4065B0C8 |
| SHA1: | 37EBCF8F91C0B739A62823BE6E89443E1D36A026 |
| SHA256: | 3C80BA8FCDF07DCF7F676FA69F043BBC0C127680514281ACED70C2BA9775C1FB |
| SSDEEP: | 49152:YE/XUraxm5O9QMal0QRO8tfDqSnXmYwj9hCcGaH6BBpOn2qv:Y9rem5Oidkv |
MALICIOUS
Modifies hosts file to block updates
- powershell.exe (PID: 6424)
SUSPICIOUS
Application launched itself
- AdobeGenP-3.4.13.4.exe (PID: 780)
Reads security settings of Internet Explorer
- AdobeGenP-3.4.13.4.exe (PID: 4668)
- AdobeGenP-3.4.13.4.exe (PID: 780)
Starts POWERSHELL.EXE for commands execution
- AdobeGenP-3.4.13.4.exe (PID: 4668)
Reads the date of Windows installation
- AdobeGenP-3.4.13.4.exe (PID: 780)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- AdobeGenP-3.4.13.4.exe (PID: 4668)
Found IP address in command line
- powershell.exe (PID: 6140)
Uses NETSH.EXE to add a firewall rule or allowed programs
- AdobeGenP-3.4.13.4.exe (PID: 4668)
Probably obfuscated PowerShell command line is found
- AdobeGenP-3.4.13.4.exe (PID: 4668)
The process bypasses the loading of PowerShell profile settings
- AdobeGenP-3.4.13.4.exe (PID: 4668)
The process checks if current user has admin rights
- AdobeGenP-3.4.13.4.exe (PID: 4668)
Request a resource from the Internet using PowerShell's cmdlet
- AdobeGenP-3.4.13.4.exe (PID: 4668)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 6424)
INFO
Process checks computer location settings
- AdobeGenP-3.4.13.4.exe (PID: 780)
The process uses the downloaded file
- AdobeGenP-3.4.13.4.exe (PID: 780)
- powershell.exe (PID: 4576)
Checks supported languages
- AdobeGenP-3.4.13.4.exe (PID: 780)
- AdobeGenP-3.4.13.4.exe (PID: 4668)
Reads the computer name
- AdobeGenP-3.4.13.4.exe (PID: 4668)
- AdobeGenP-3.4.13.4.exe (PID: 780)
Creates files in the program directory
- AdobeGenP-3.4.13.4.exe (PID: 4668)
Disables trace logs
- powershell.exe (PID: 6424)
Checks proxy server information
- powershell.exe (PID: 6424)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6424)
Reads mouse settings
- AdobeGenP-3.4.13.4.exe (PID: 780)
- AdobeGenP-3.4.13.4.exe (PID: 4668)
Create files in a temporary directory
- AdobeGenP-3.4.13.4.exe (PID: 4668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:04:04 16:17:11+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 734208 |
| InitializedDataSize: | 470528 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2549c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.4.13.4 |
| ProductVersionNumber: | 3.4.13.4 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 3.4.13.4 |
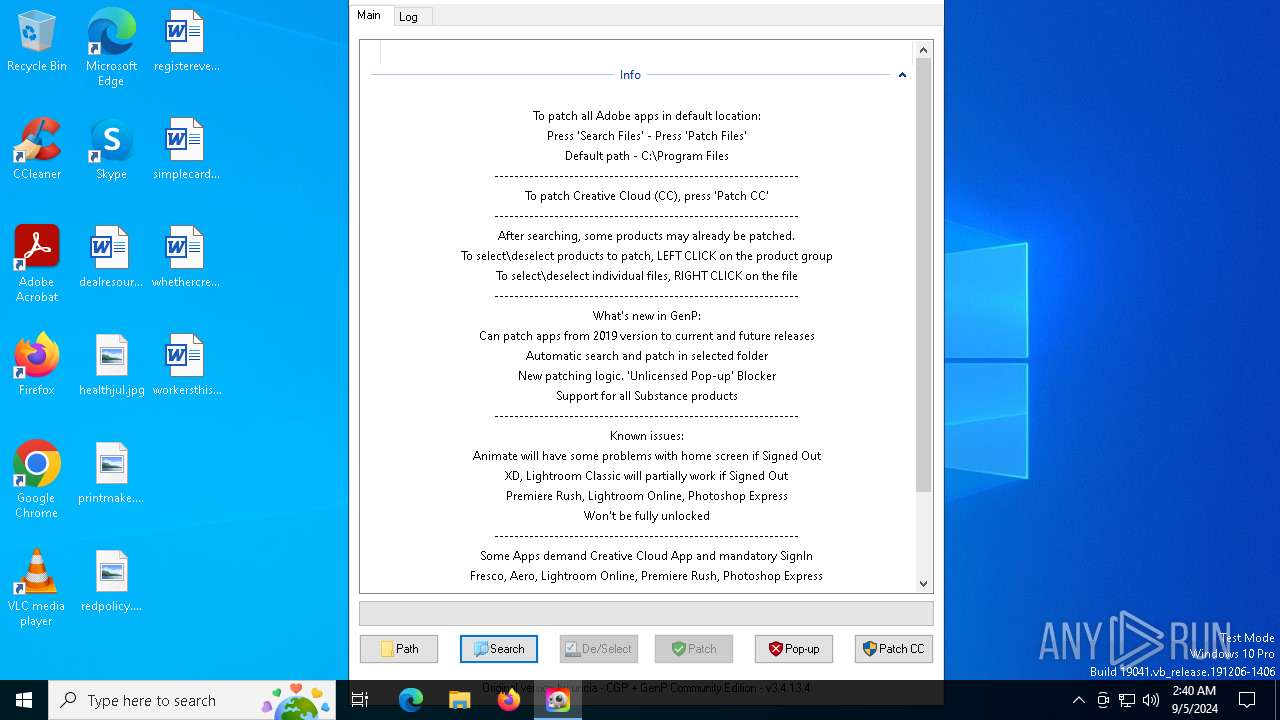
| Comments: | Adobe GenP v3.4.13.4 |
| FileDescription: | Adobe GenP v3.4.13.4 |
| ProductName: | Adobe GenP v3.4.13.4 |
| ProductVersion: | 3.4.13.4 |
| CompanyName: | GenP |
| LegalCopyright: | GenP |
| LegalTradeMarks: | GenP |
Total processes
138
Monitored processes
12
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | netsh advfirewall firewall add rule name="Adobe Unlicensed Pop-up" dir=out action=block remoteip="107.22.247.231,18.207.85.246,18.66.192.110,18.66.192.121,18.66.192.13,18.66.192.90,23.22.254.206,34.193.227.236,52.202.204.11,52.5.13.197,54.144.73.197,54.227.187.23" | C:\Windows\System32\netsh.exe | — | AdobeGenP-3.4.13.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | "C:\Users\admin\Downloads\AdobeGenP-3.4.13.4.exe" | C:\Users\admin\Downloads\AdobeGenP-3.4.13.4.exe | — | explorer.exe | |||||||||||
User: admin Company: GenP Integrity Level: MEDIUM Description: Adobe GenP v3.4.13.4 Exit code: 0 Version: 3.4.13.4 Modules
| |||||||||||||||
| 876 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4060 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4576 | "C:\Windows\System32\WindowsPowerShell\v1.0\PowerShell.exe" -Command "$currentDate=Get-Date;$ipAddresses=@();try{$SOA=(Resolve-DnsName -Name adobe.io -Type SOA -ErrorAction Stop).PrimaryServer}catch{$SOA=$null};if($SOA){Do{if((New-TimeSpan -Start $currentDate -End (Get-Date)).TotalSeconds -gt 5){if($ipAddresses.Count -eq 0){$ipAddresses+='False'};break};try{$ipAddress=(Resolve-DnsName -Name adobe.io -Server $SOA -ErrorAction Stop).IPAddress}catch{$ipAddress=$null};if($ipAddress){$ipAddresses+=$ipAddress};$ipAddresses=$ipAddresses|Select -Unique|Sort-Object}While($ipAddresses.Count -lt 8)}else{$ipAddresses+='False'};Do{if((New-TimeSpan -Start $currentDate -End (Get-Date)).TotalSeconds -gt 5 -or $ipAddresses[0] -eq 'False'){break};try{$ipAddress=(Resolve-DnsName -Name 3u6k9as4bj.adobestats.io -ErrorAction Stop).IPAddress}catch{$ipAddress=$null};if($ipAddress){$ipAddresses+=$ipAddress};$ipAddresses=$ipAddresses|Select -Unique|Sort-Object}While($ipAddresses.Count -lt 12 -and $ipAddresses[0] -ne 'False');$ipAddresses=$ipAddresses -ne 'False'|Select -Unique|Sort-Object;$ipAddressList=if($ipAddresses.Count -eq 0){'False'}else{$ipAddresses -join ','};$ipAddressList" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | AdobeGenP-3.4.13.4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4668 | "C:\Users\admin\Downloads\AdobeGenP-3.4.13.4.exe" ! | C:\Users\admin\Downloads\AdobeGenP-3.4.13.4.exe | AdobeGenP-3.4.13.4.exe | ||||||||||||
User: admin Company: GenP Integrity Level: HIGH Description: Adobe GenP v3.4.13.4 Version: 3.4.13.4 Modules
| |||||||||||||||
| 5344 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6140 | "C:\Windows\System32\WindowsPowerShell\v1.0\PowerShell.exe" -Command "Test-Connection 8.8.8.8 -Count 1 -Quiet" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | AdobeGenP-3.4.13.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 017
Read events
19 932
Write events
81
Delete events
4
Modification events
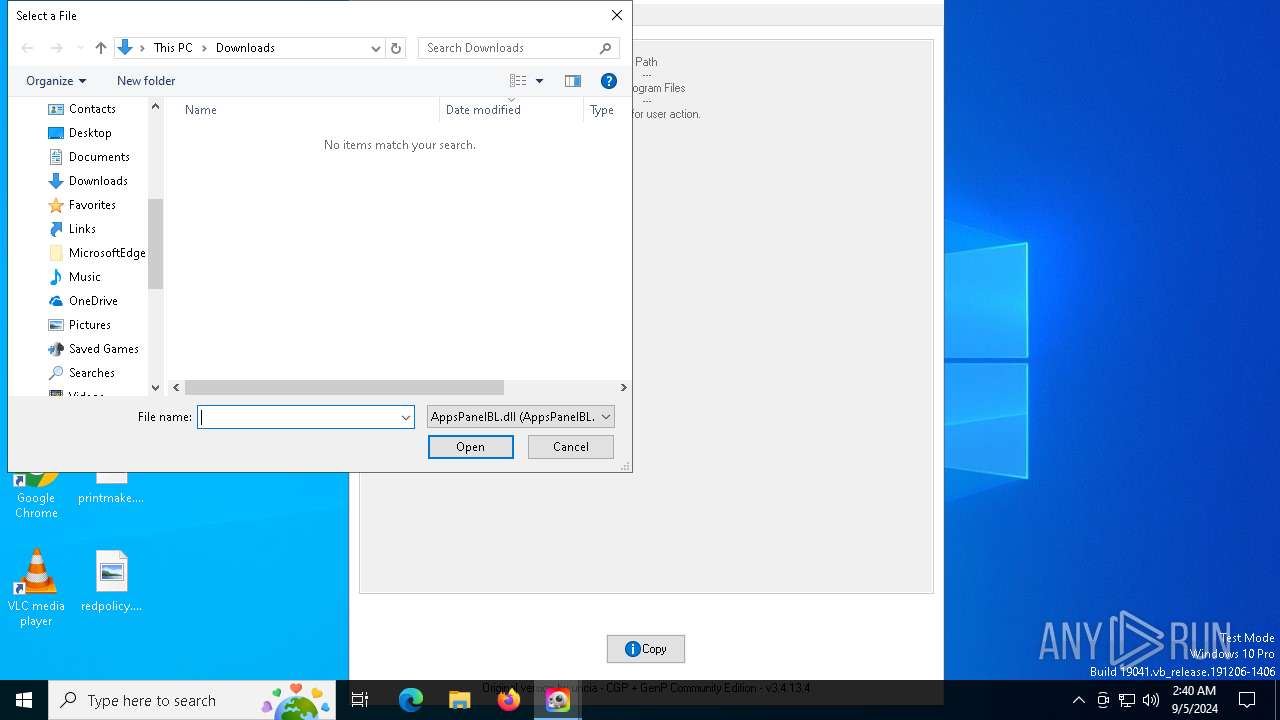
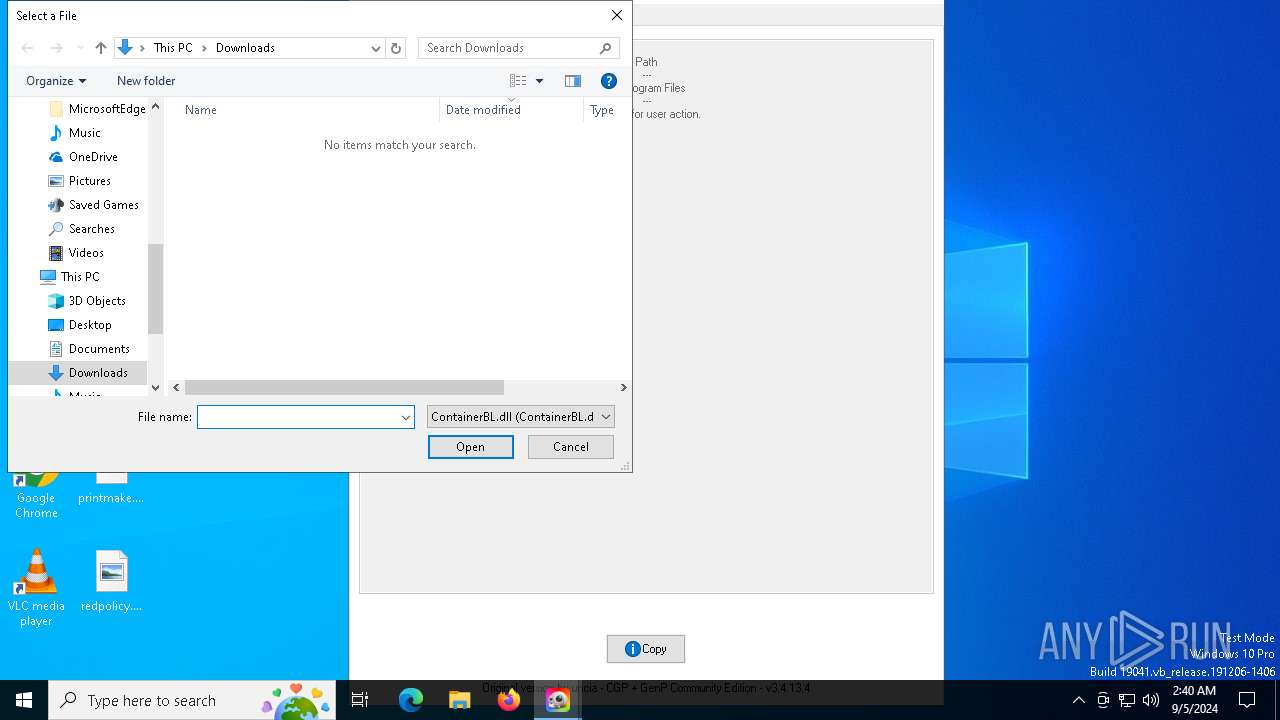
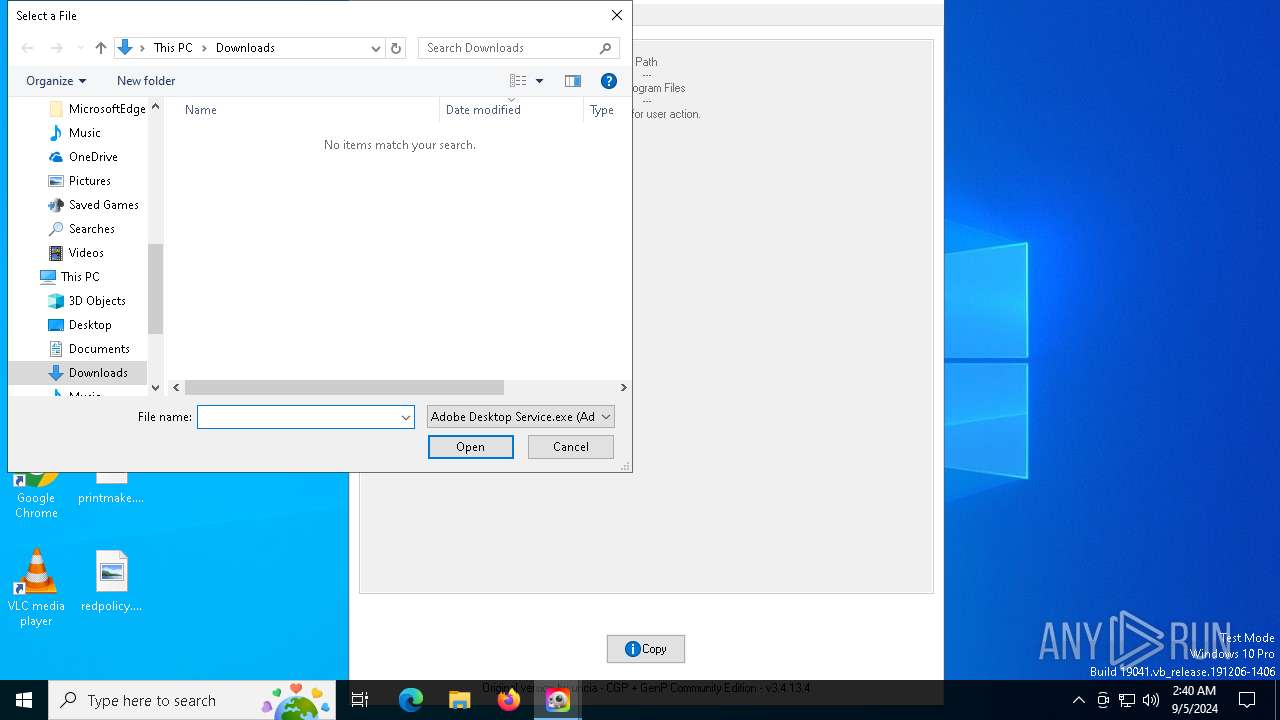
| (PID) Process: | (4668) AdobeGenP-3.4.13.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (4668) AdobeGenP-3.4.13.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0044006F0077006E006C006F006100640073005C00410064006F0062006500470065006E0050002D0033002E0034002E00310033002E0034002E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C0044006F0077006E006C006F006100640073000000 | |||
| (PID) Process: | (4668) AdobeGenP-3.4.13.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (4668) AdobeGenP-3.4.13.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4668) AdobeGenP-3.4.13.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0400000000000000030000000E0000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (4668) AdobeGenP-3.4.13.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 050000000000000004000000020000000100000003000000FFFFFFFF | |||
| (PID) Process: | (4668) AdobeGenP-3.4.13.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Downloads | |||
| (PID) Process: | (4668) AdobeGenP-3.4.13.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\ComDlg\{885A186E-A440-4ADA-812B-DB871B942259} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (4668) AdobeGenP-3.4.13.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\ComDlg\{885A186E-A440-4ADA-812B-DB871B942259} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (4668) AdobeGenP-3.4.13.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\ComDlg\{885A186E-A440-4ADA-812B-DB871B942259} |
| Operation: | write | Name: | FFlags |
Value: | |||
Executable files
0
Suspicious files
2
Text files
8
Unknown types
0
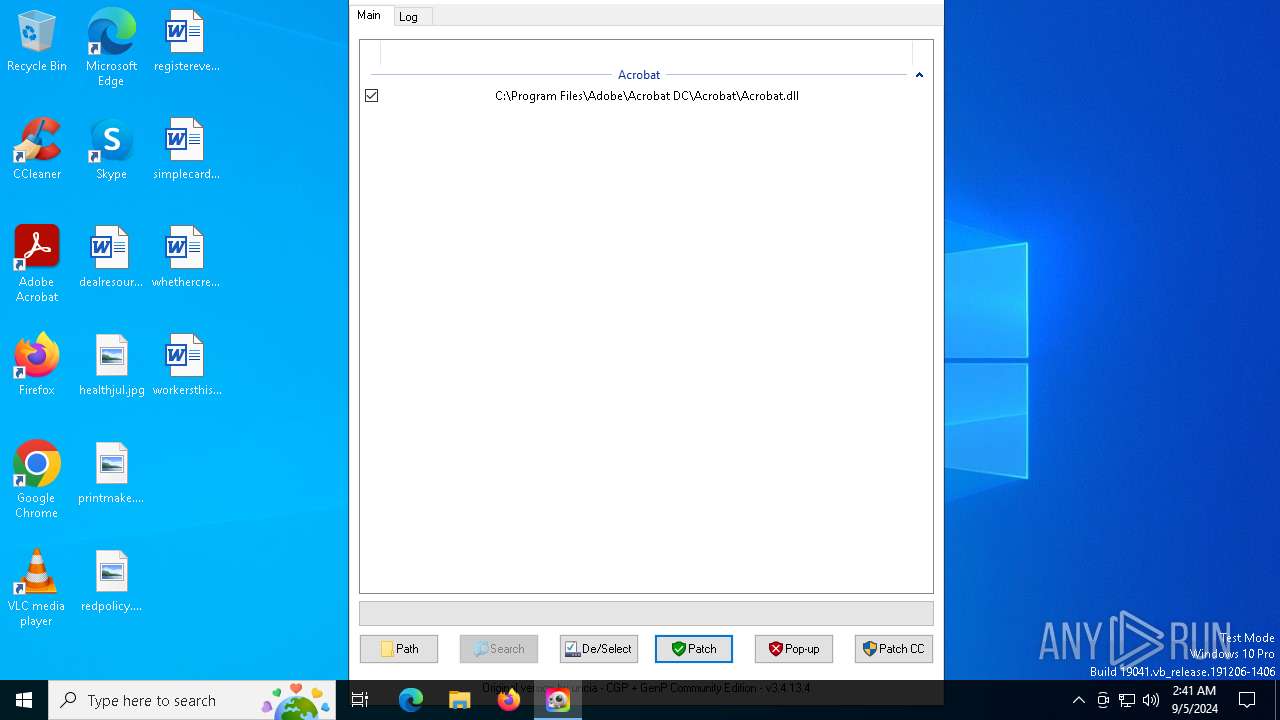
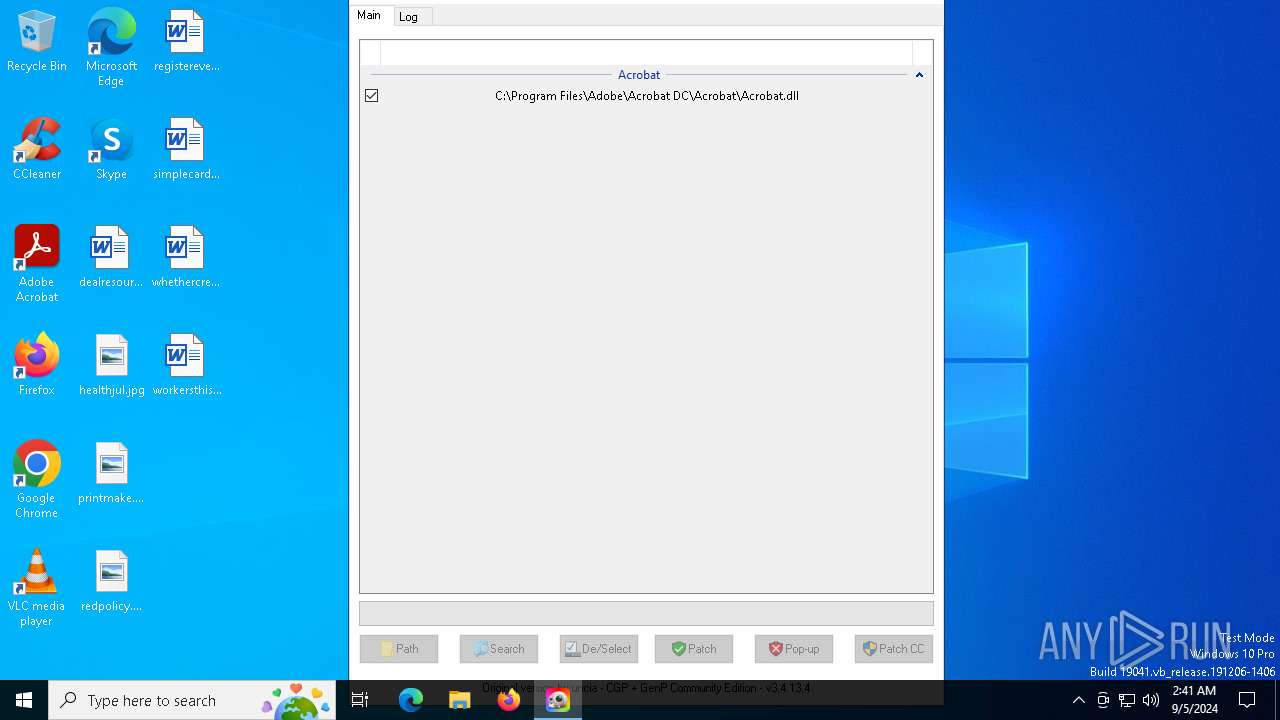
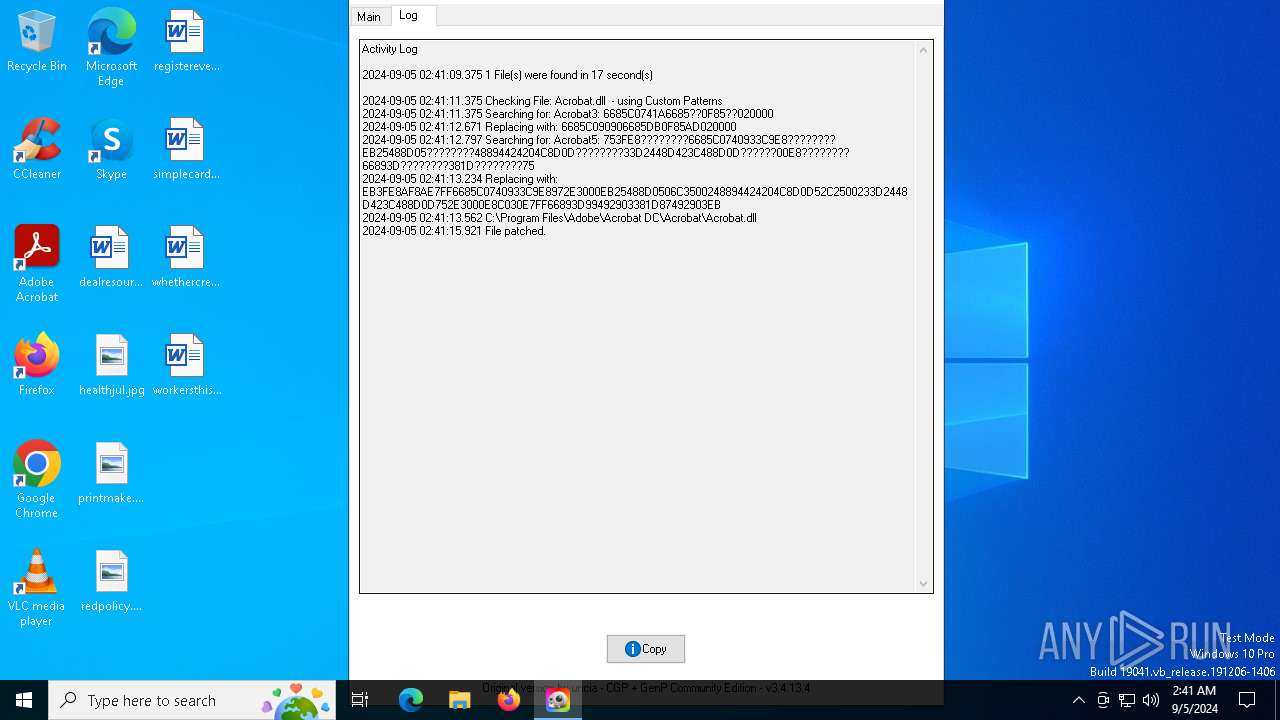
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
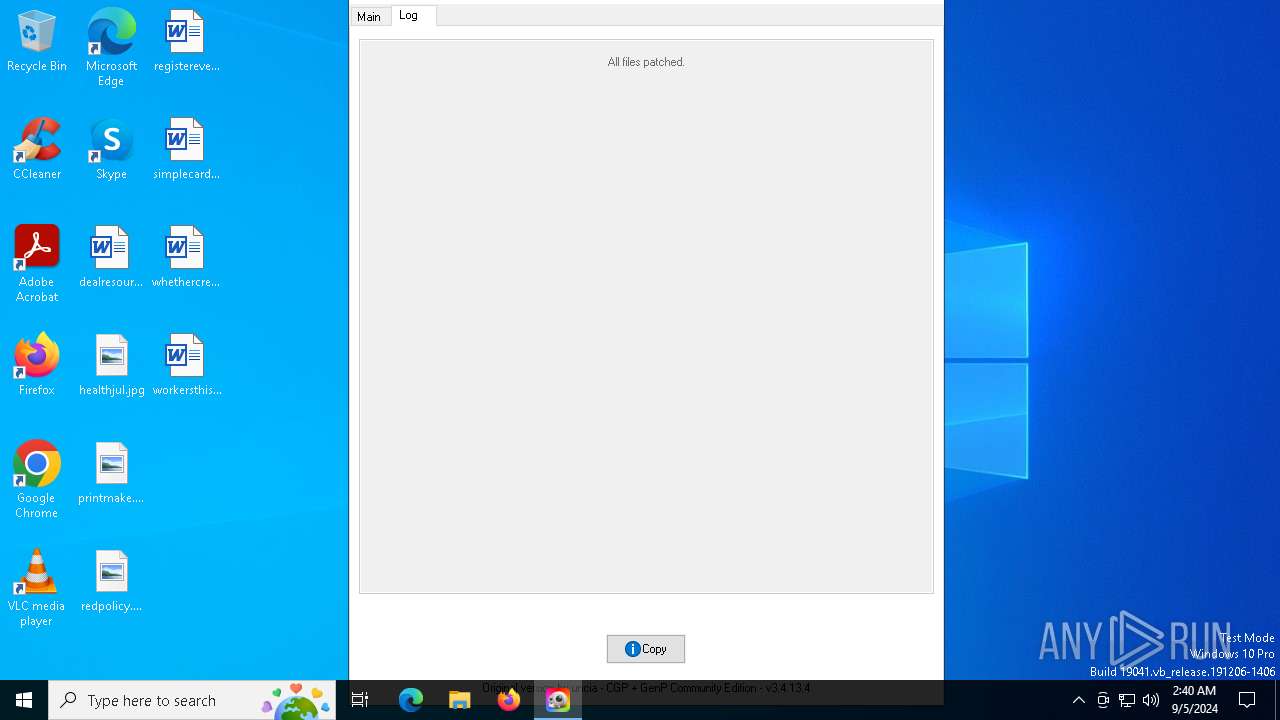
| 4668 | AdobeGenP-3.4.13.4.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll.bak | — | |
MD5:— | SHA256:— | |||
| 4668 | AdobeGenP-3.4.13.4.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll | — | |
MD5:— | SHA256:— | |||
| 4668 | AdobeGenP-3.4.13.4.exe | C:\Users\admin\Downloads\config.ini | ini | |
MD5:B0C34CC14886B2BD2F72B56957C55A66 | SHA256:1277DD76C6F9770A3DDA70C8F425FB1DBD72DD629726DA36B842CDF0BA2B2C7E | |||
| 4576 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jwujv14d.na3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4576 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_z3dbuidu.in0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6140 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:177877952B50B0CA93C7096793E662B9 | SHA256:44C4A952671099EEA0D5071B815A3C2327404608AA1BEA7D24E2B2FAC807156B | |||
| 6424 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_a5enkare.nfa.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6140 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ehzehwug.o2p.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4668 | AdobeGenP-3.4.13.4.exe | C:\Users\admin\AppData\Local\Temp\aut9F36.tmp | binary | |
MD5:676E7BE9E8E977819EAAF83654627BD9 | SHA256:0007DA89F7DC235EBDF9BCA31EB1926405E5B8F755DD84107B87D001B43659B6 | |||
| 6140 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kxczk4kj.ijl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
22
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1556 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3832 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1556 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7084 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7072 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3832 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3832 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
adobe.io |
| whitelisted |
ns-1159.awsdns-16.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |