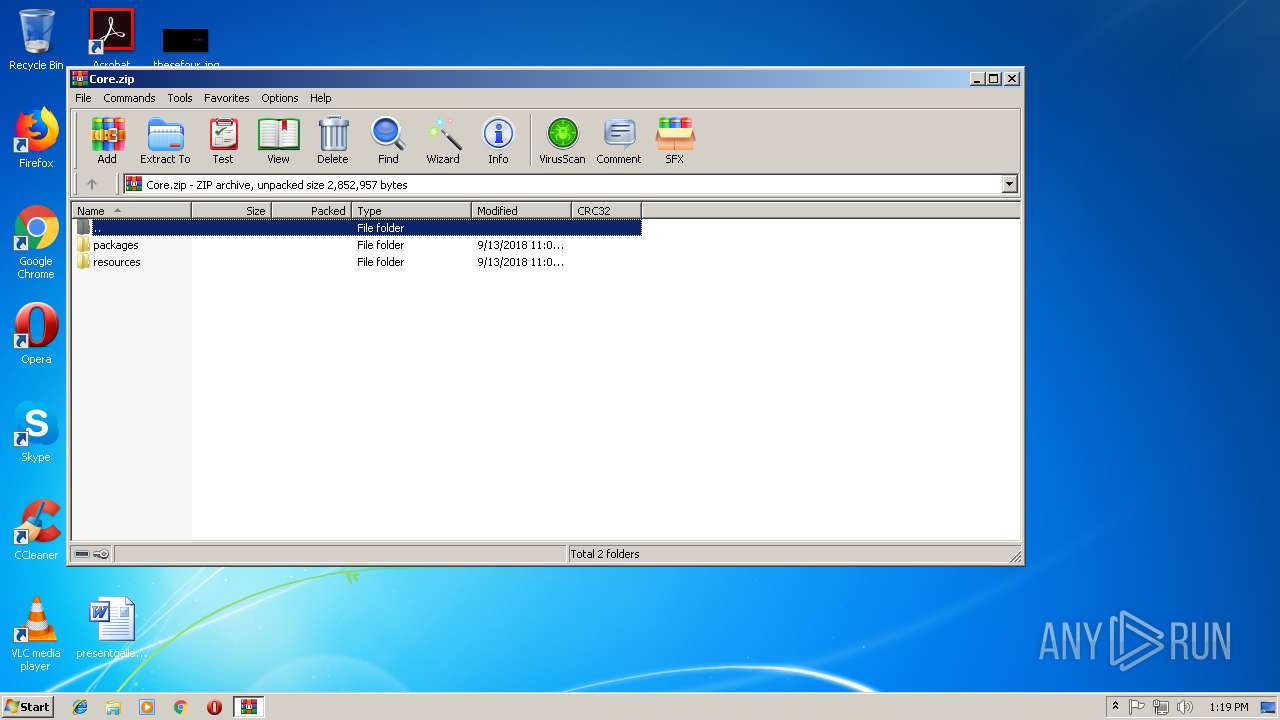
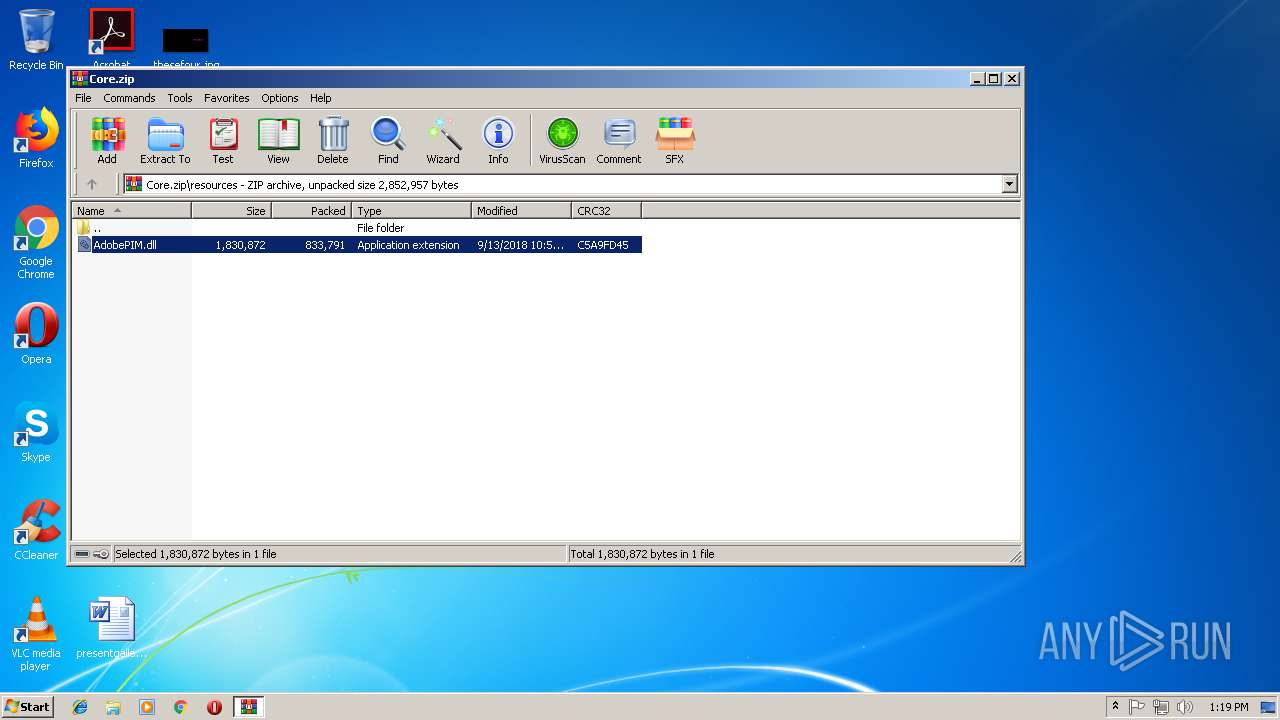
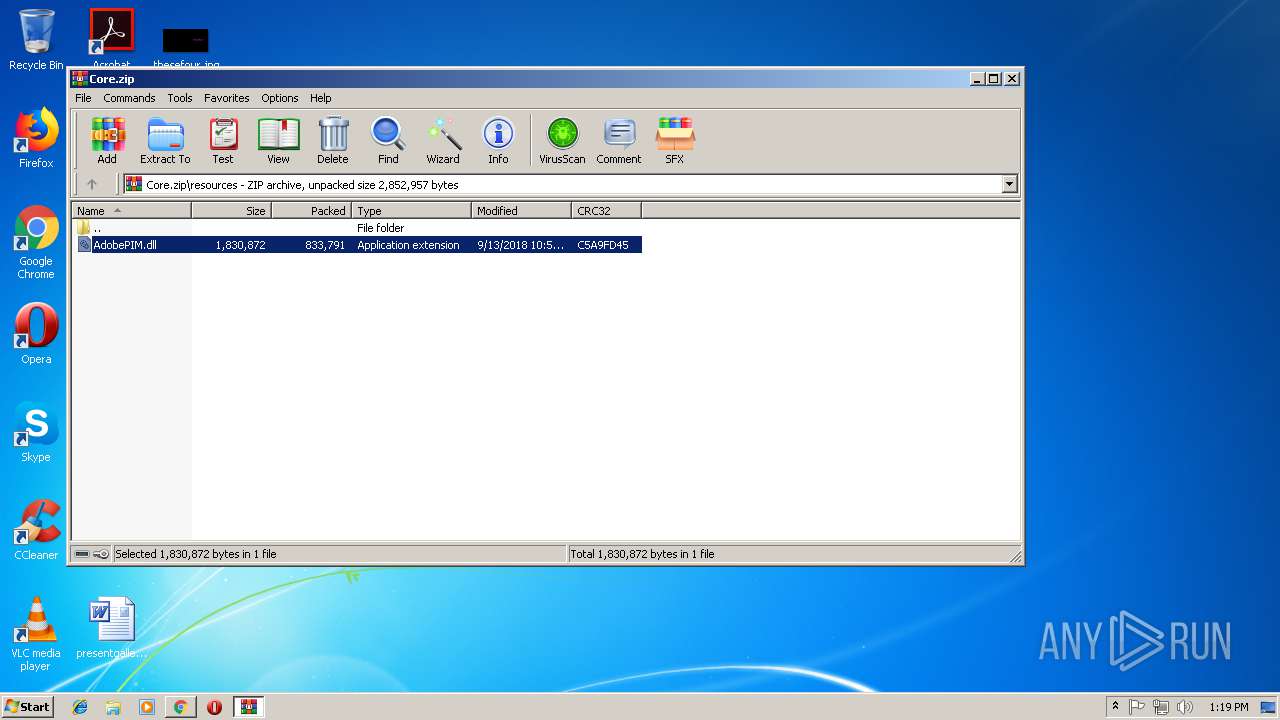
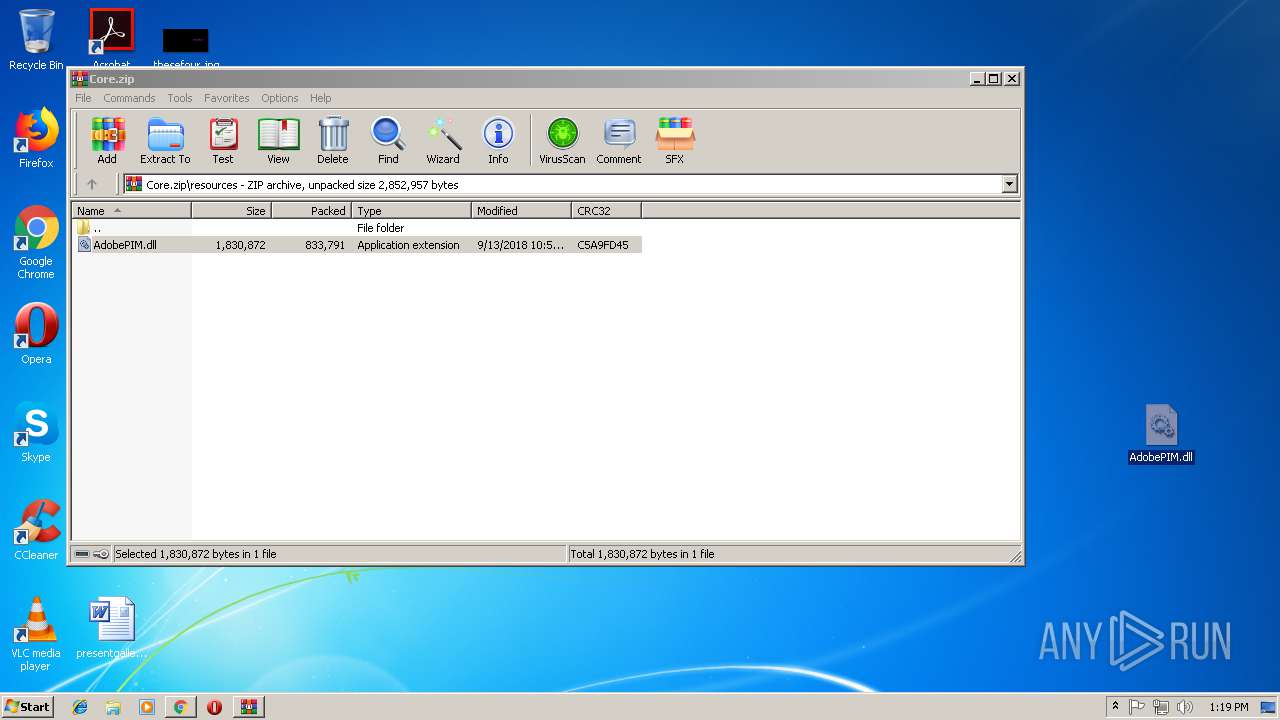
| download: | Core.zip |
| Full analysis: | https://app.any.run/tasks/f8533ded-ce84-4164-9930-0cce397ffc26 |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 13:18:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1809D5CFD607A1AB6CC968A49407F391 |
| SHA1: | 3464BBF854AC449A7DE610A1E77337BD658D55AC |
| SHA256: | 3C7DF3DAD4E70F562ECA663C217D5D5203E9AB90FDFD35FD18FC3075D28FCC62 |
| SSDEEP: | 49152:jTgl3aBVQkqnqUvI1yXHq7XXTgl3aBVQkqnqUvI1yXv:jT/BSkqqR9XT/BSkqqRC |
MALICIOUS
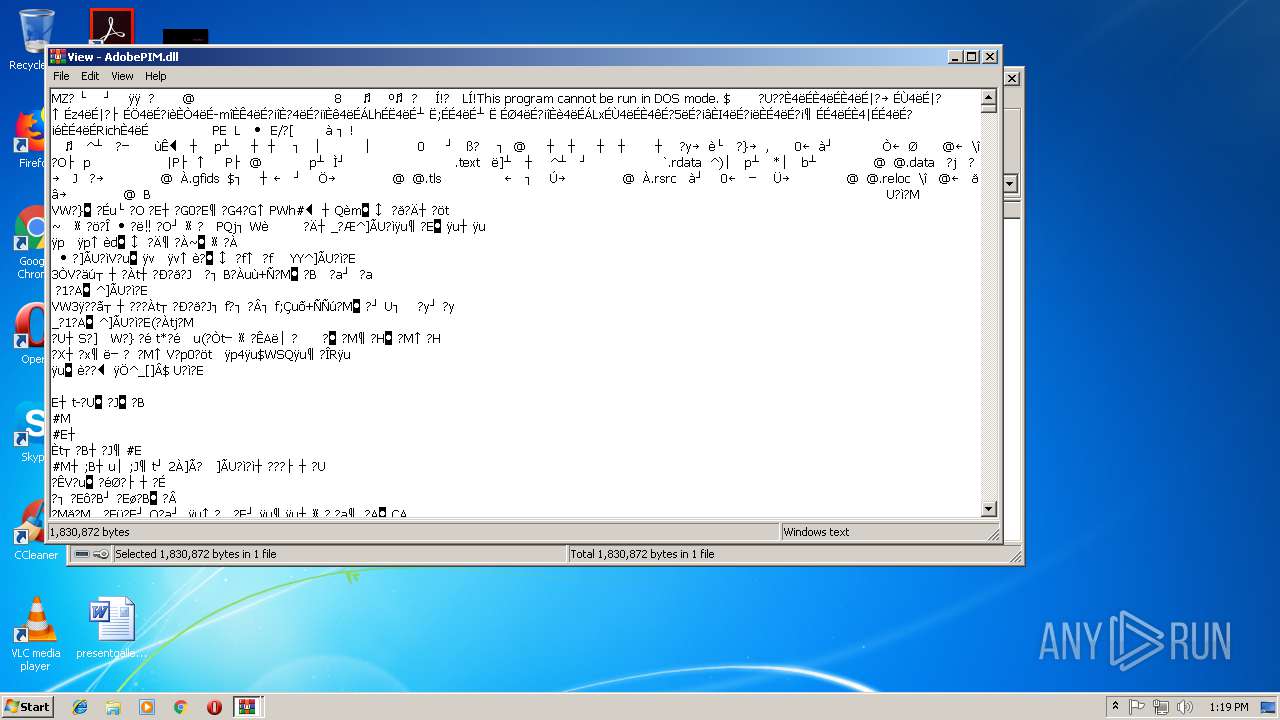
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 716)
- chrome.exe (PID: 2420)
SUSPICIOUS
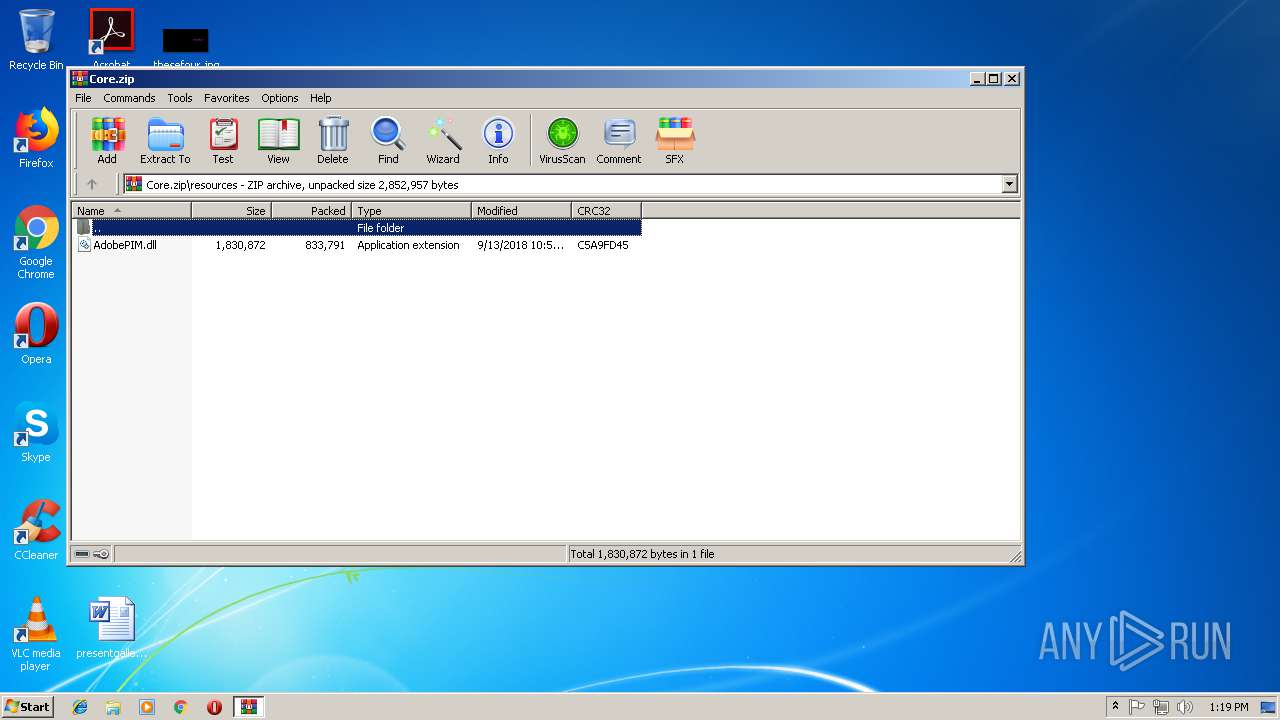
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3636)
INFO
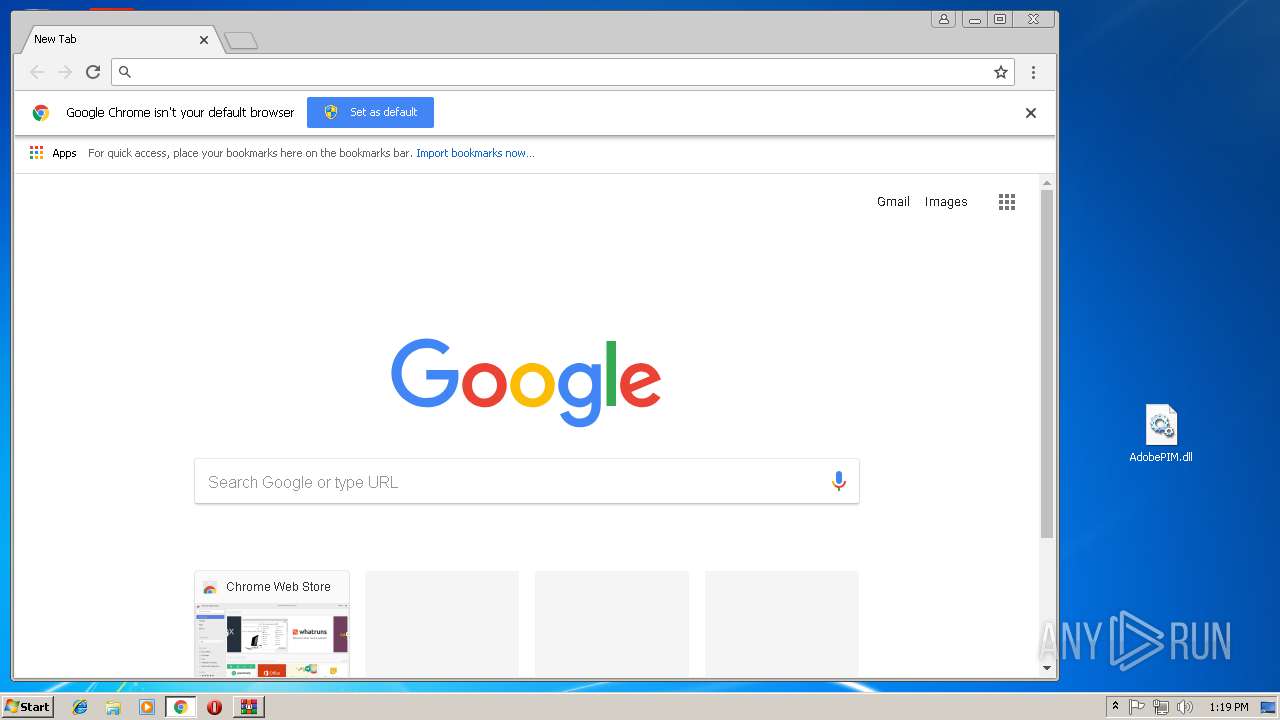
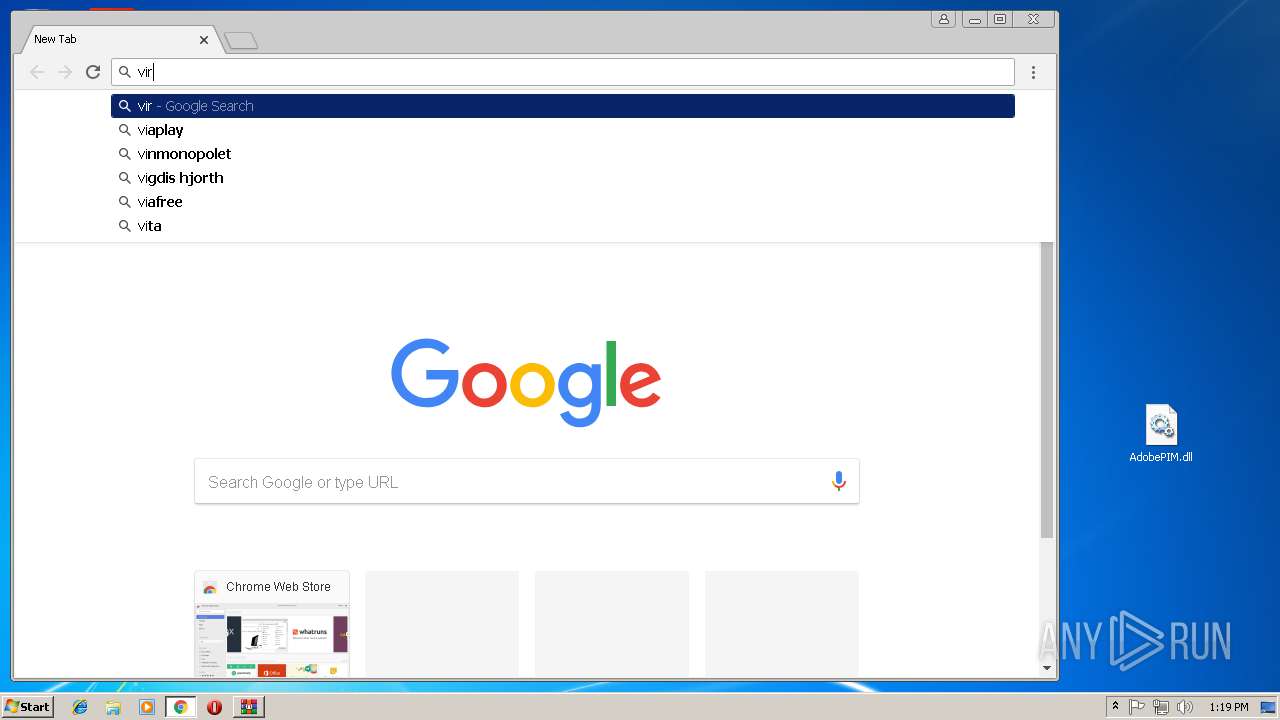
Application launched itself
- chrome.exe (PID: 2420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:09:13 03:05:06 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | packages/ |
Total processes
44
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 716 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe14_ Global\UsGthrCtrlFltPipeMssGthrPipe14 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f8700b0,0x6f8700c0,0x6f8700cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,7424766313668636990,14586464130631814228,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0F24306FDDEA27CD72A1E5B780F30F00 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0F24306FDDEA27CD72A1E5B780F30F00 --renderer-client-id=10 --mojo-platform-channel-handle=3820 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=872,7424766313668636990,14586464130631814228,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=0D290BA2A1B03B5F9060C7C242472E2B --mojo-platform-channel-handle=3760 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,7424766313668636990,14586464130631814228,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=D3FBD71E1206F4360532BE0444B97654 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D3FBD71E1206F4360532BE0444B97654 --renderer-client-id=8 --mojo-platform-channel-handle=3840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=872,7424766313668636990,14586464130631814228,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=D54ADAFA212F40C1A5CB19682A7AD74B --mojo-platform-channel-handle=3744 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3664 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,7424766313668636990,14586464130631814228,131072 --enable-features=PasswordImport --service-pipe-token=DF78B4E9B1BDD8E42D230617A36F8300 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=DF78B4E9B1BDD8E42D230617A36F8300 --renderer-client-id=5 --mojo-platform-channel-handle=1884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,7424766313668636990,14586464130631814228,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9DF0A5B50FF5D5808BD0DFE45E4780A9 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9DF0A5B50FF5D5808BD0DFE45E4780A9 --renderer-client-id=6 --mojo-platform-channel-handle=3452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 045
Read events
948
Write events
94
Delete events
3
Modification events
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Core.zip | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Viewer |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF2C0000002C000000EC03000021020000 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
2
Suspicious files
45
Text files
55
Unknown types
1
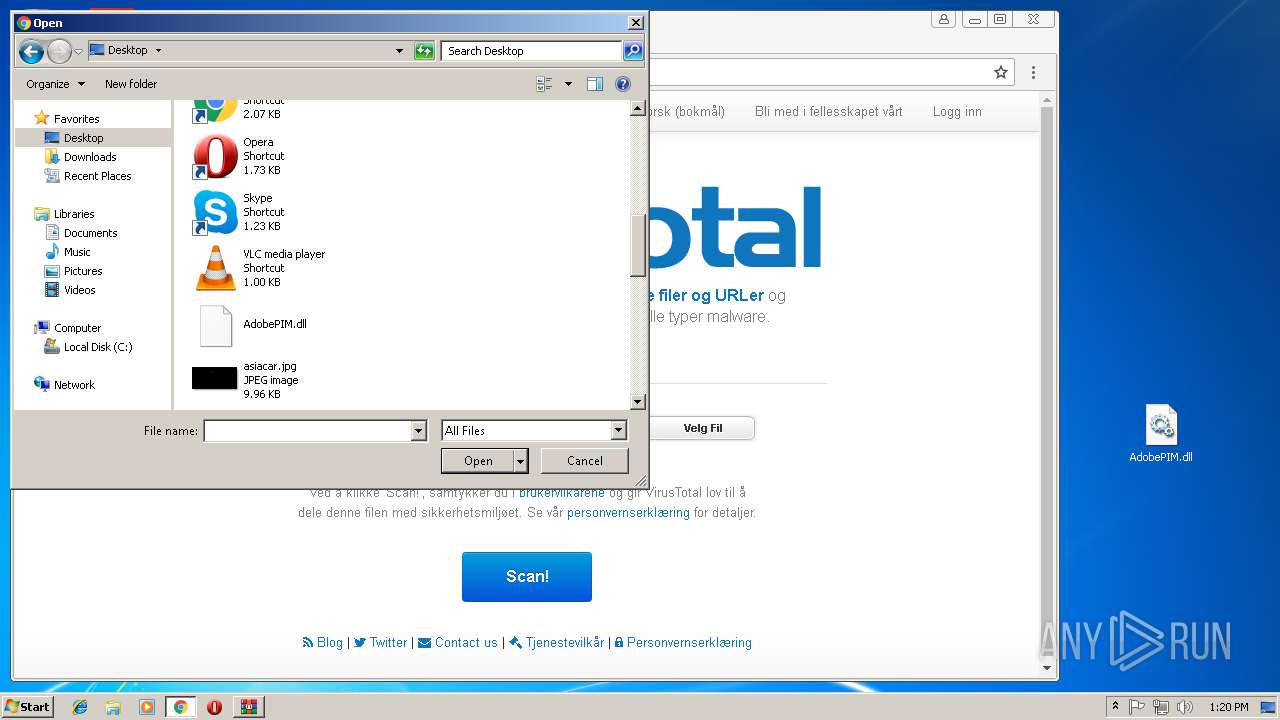
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bd314a26-2cb9-4e47-ba48-80a0de7dbb3c.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF5e17e4.TMP | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF5e17e4.TMP | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
29
DNS requests
19
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2420 | chrome.exe | 216.58.215.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 216.58.215.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 172.217.168.4:443 | www.google.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 172.217.168.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 172.217.168.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 216.58.215.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 216.58.215.238:443 | apis.google.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 172.217.168.34:443 | adservice.google.no | Google Inc. | US | whitelisted |
2420 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
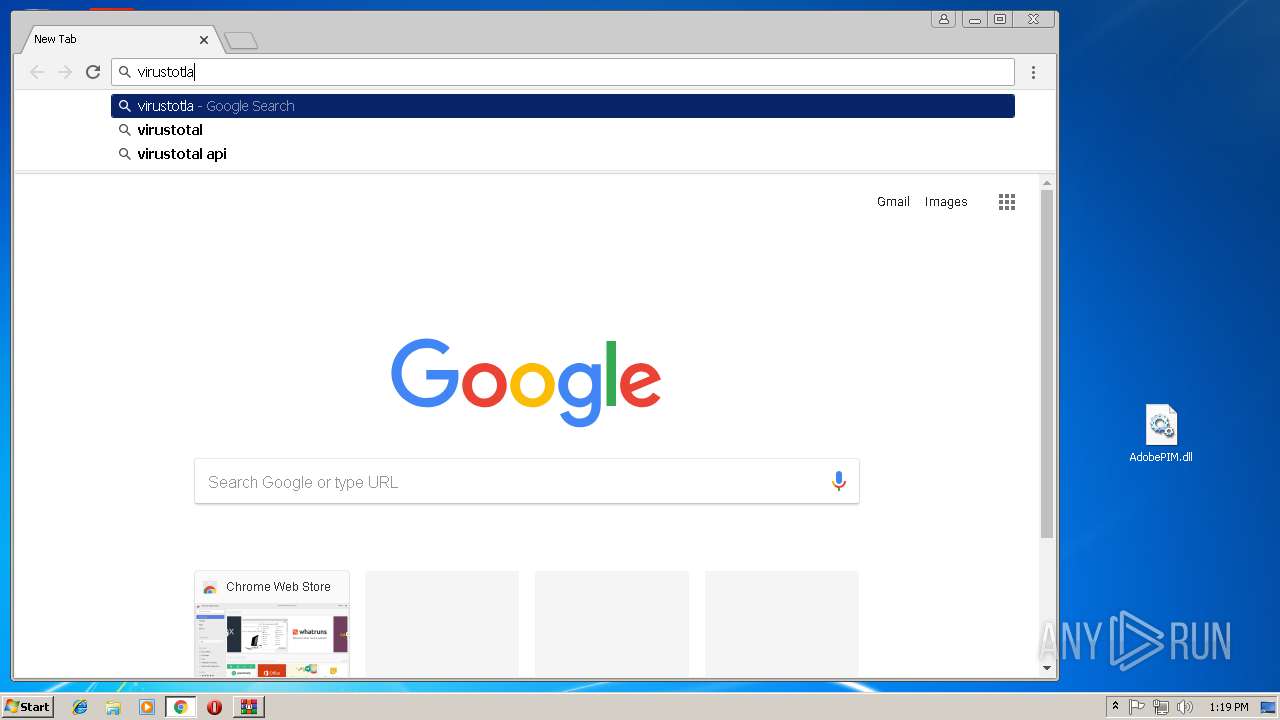
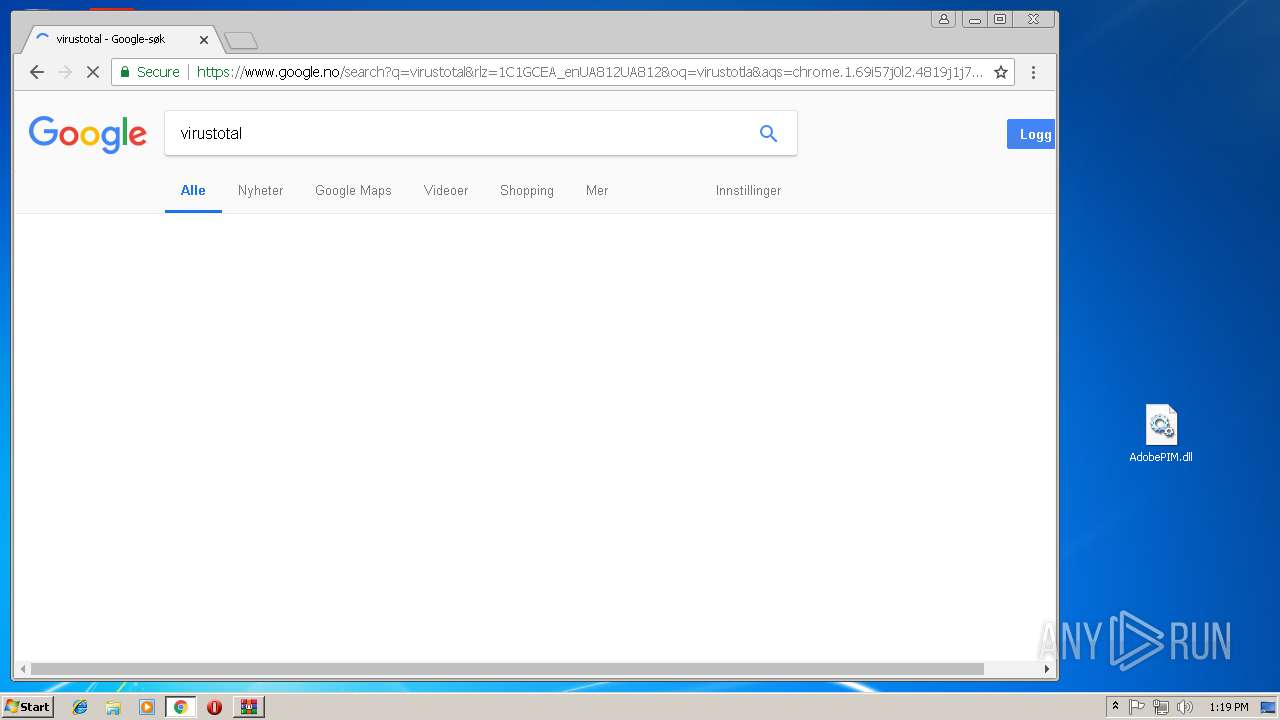
2420 | chrome.exe | 74.125.34.46:443 | www.virustotal.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
www.google.no |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |