| File name: | tswebsetup.exe |
| Full analysis: | https://app.any.run/tasks/7d8a9e06-7f83-4255-aab8-dbc9fa8bd3d5 |
| Verdict: | Malicious activity |
| Analysis date: | January 03, 2021, 18:57:12 |
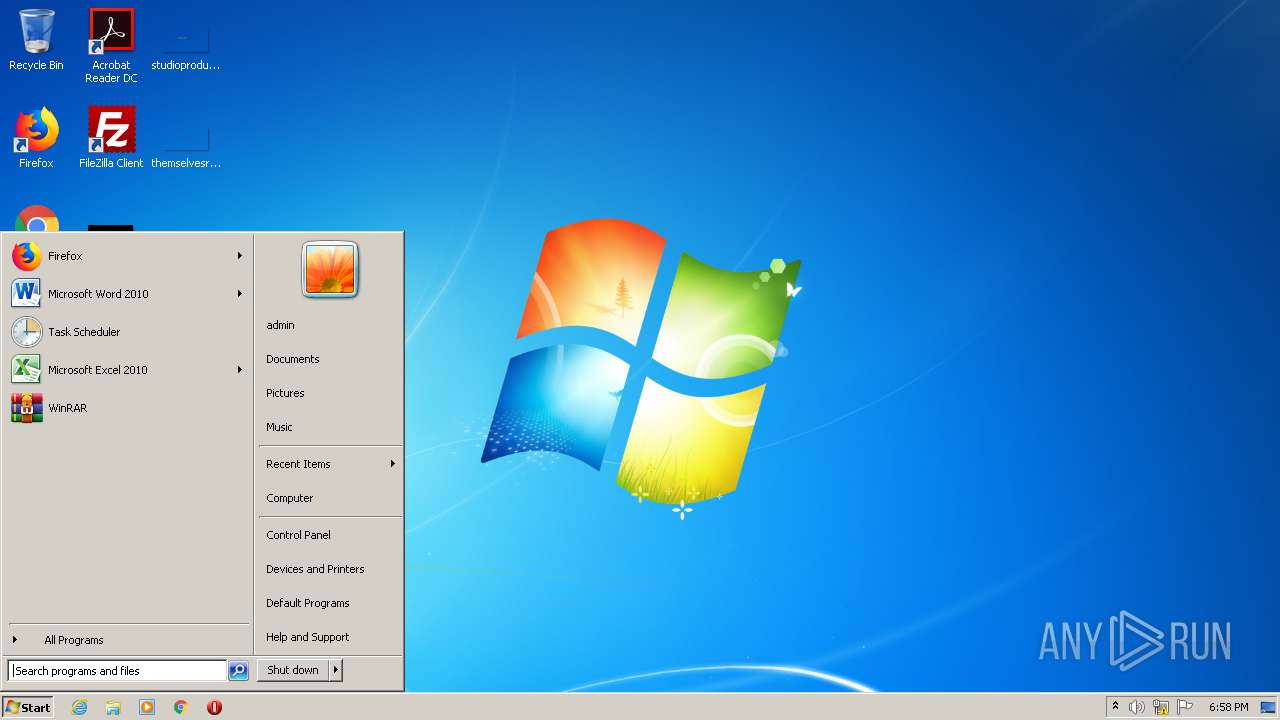
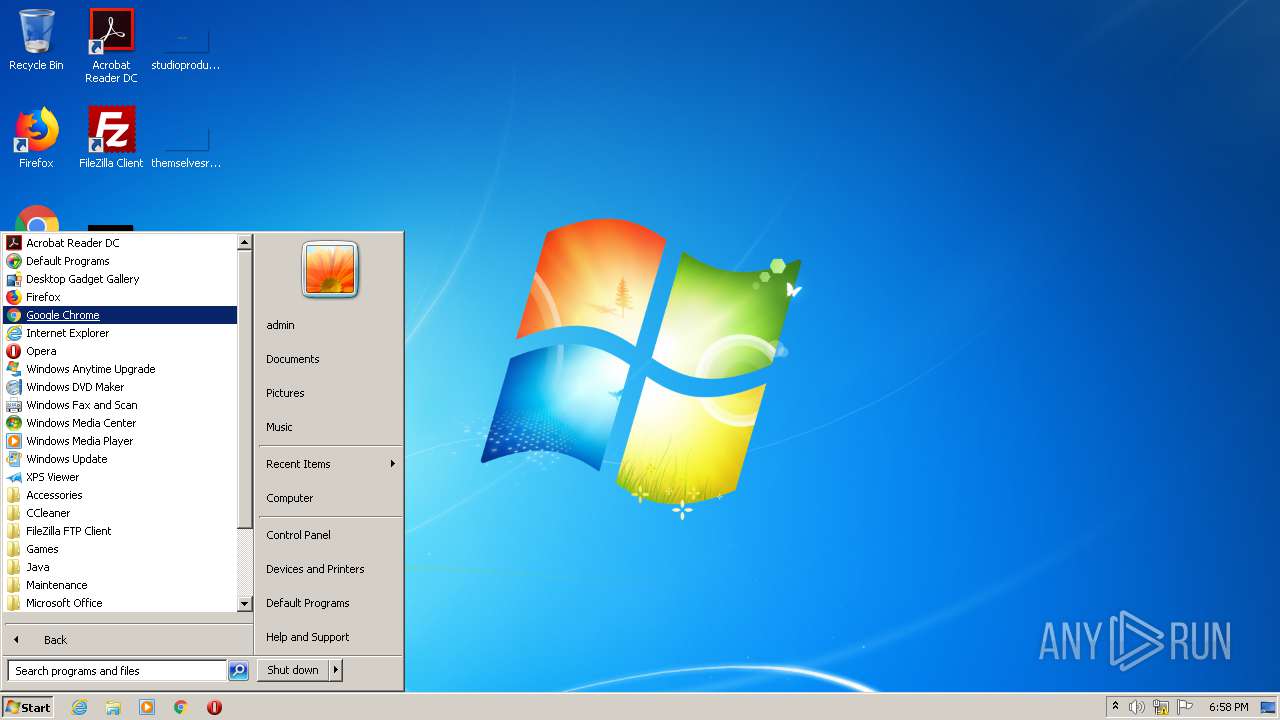
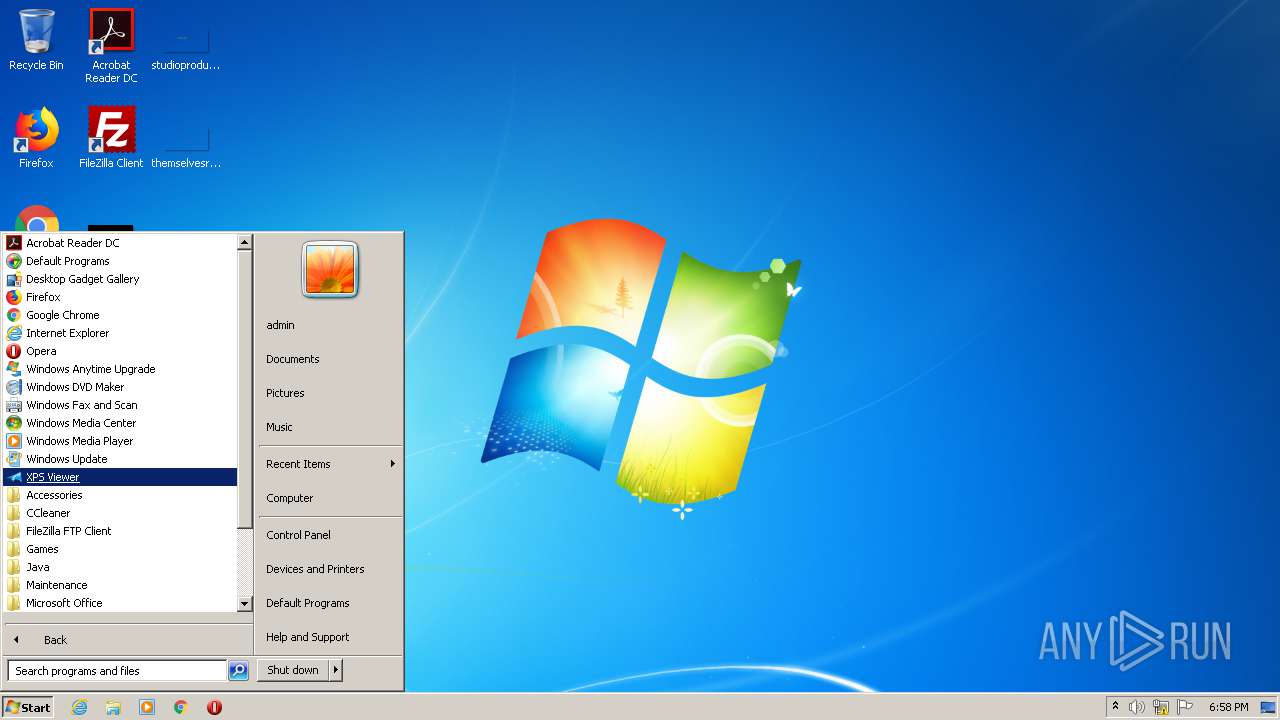
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, MS CAB-Installer self-extracting archive |
| MD5: | AE9AC5DD30B8F88AE2A5255CFC2C8949 |
| SHA1: | FEA0072E467E70E25F4519A3FFCC69D2E191E846 |
| SHA256: | 3C6D01A893058CF06878F3A7C86AFD9B03DD0D7DEAA283B0F26EB3E6F547D635 |
| SSDEEP: | 12288:jlYdhp42LgN2KvRQGOFJSY4SsYZ6o1nNME1zG1:z2EN2yRqJSAsQQ1 |
MALICIOUS
Loads dropped or rewritten executable
- rundll32.exe (PID: 2596)
- tswebsetup.exe (PID: 2964)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- tswebsetup.exe (PID: 2964)
Drops a file with a compile date too recent
- tswebsetup.exe (PID: 2964)
Creates a software uninstall entry
- tswebsetup.exe (PID: 2964)
Drops a file with too old compile date
- tswebsetup.exe (PID: 2964)
Drops a file that was compiled in debug mode
- tswebsetup.exe (PID: 2964)
Executable content was dropped or overwritten
- tswebsetup.exe (PID: 2964)
Executed via COM
- DllHost.exe (PID: 3108)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Microsoft Update - Self Extracting Cabinet (82.1) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (7.5) |
| .exe | | | Win64 Executable (generic) (6.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.5) |
| .exe | | | Win32 Executable (generic) (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2001:07:25 05:03:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7 |
| CodeSize: | 34816 |
| InitializedDataSize: | 461824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5a5e |
| OSVersion: | 5.1 |
| ImageVersion: | 5.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.2526.0 |
| ProductVersionNumber: | 6.0.2526.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Spanish (Modern) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 6.00.2526.0000 (xpclient.010724-1758) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. Reservados todos los derechos. |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Sistema operativo Microsoft® Windows® |
| ProductVersion: | 6.00.2526.0000 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jul-2001 03:03:49 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 6.00.2526.0000 (xpclient.010724-1758) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. Reservados todos los derechos. |
| OriginalFilename: | WEXTRACT.EXE |
| ProductName: | Sistema operativo Microsoft® Windows® |
| ProductVersion: | 6.00.2526.0000 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Jul-2001 03:03:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000861A | 0x00008800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59597 |
.data | 0x0000A000 | 0x00001BE4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.18428 |
.rsrc | 0x0000C000 | 0x00071000 | 0x00070800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.92881 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.34681 | 1136 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_VERSION |
2 | 3.53793 | 296 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_ICON |
63 | 2.60379 | 140 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
76 | 3.14683 | 1672 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
77 | 3.23934 | 1740 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
80 | 3.19427 | 1484 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
83 | 3.28161 | 1236 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
85 | 3.10839 | 1032 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
2001 | 3.37774 | 764 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_DIALOG |
2002 | 3.36505 | 392 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
Total processes
40
Monitored processes
5
Malicious processes
2
Suspicious processes
0
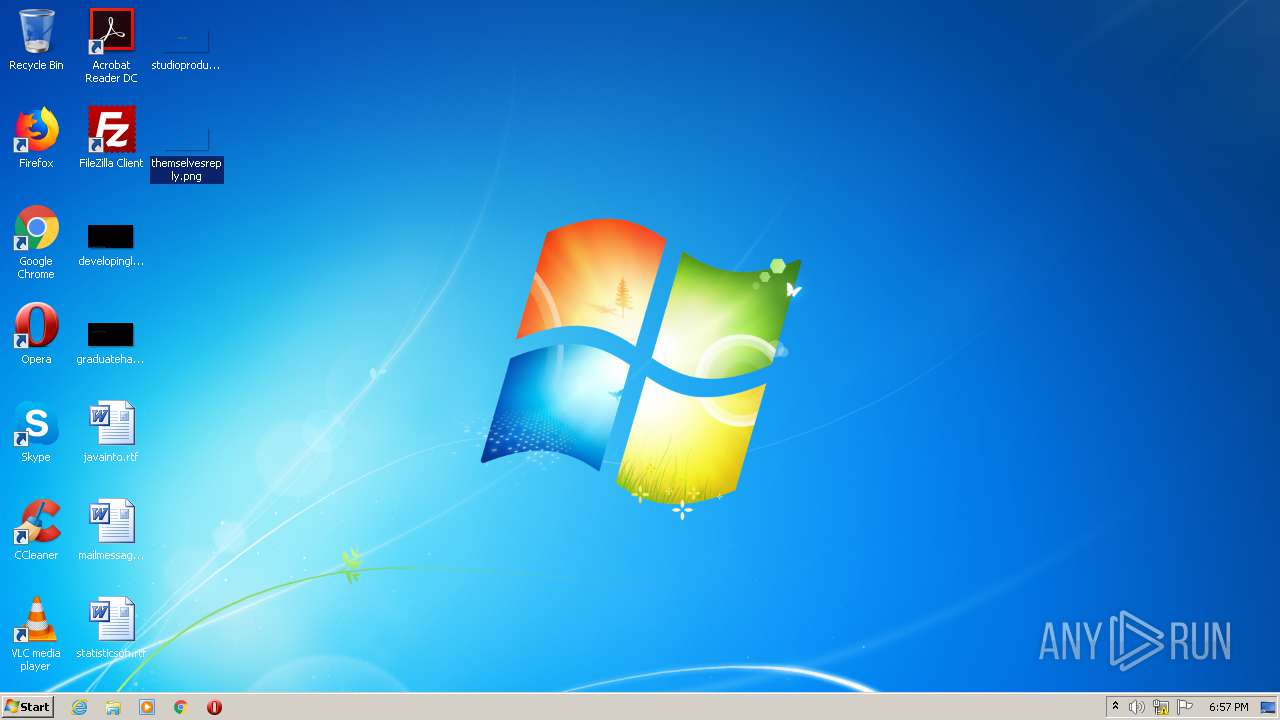
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2576 | "C:\Users\admin\AppData\Local\Temp\tswebsetup.exe" | C:\Users\admin\AppData\Local\Temp\tswebsetup.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 3221226540 Version: 6.00.2526.0000 (xpclient.010724-1758) Modules
| |||||||||||||||
| 2596 | rundll32 advpack.dll,LaunchINFSection C:\InetPub\wwwroot\TSWeb\setup.inf,ReadMe,, | C:\Windows\system32\rundll32.exe | — | tswebsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2964 | "C:\Users\admin\AppData\Local\Temp\tswebsetup.exe" | C:\Users\admin\AppData\Local\Temp\tswebsetup.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 6.00.2526.0000 (xpclient.010724-1758) Modules
| |||||||||||||||
| 3108 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3544 | extrac32 /c /y msrdp.cab "C:\InetPub\wwwroot\TSWeb" | C:\Windows\system32\extrac32.exe | — | tswebsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® CAB File Extract Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
59
Read events
51
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2964) tswebsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | SM_AccessoriesName |
Value: Accessories | |||
| (PID) Process: | (2964) tswebsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | PF_AccessoriesName |
Value: Accessories | |||
| (PID) Process: | (2964) tswebsetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
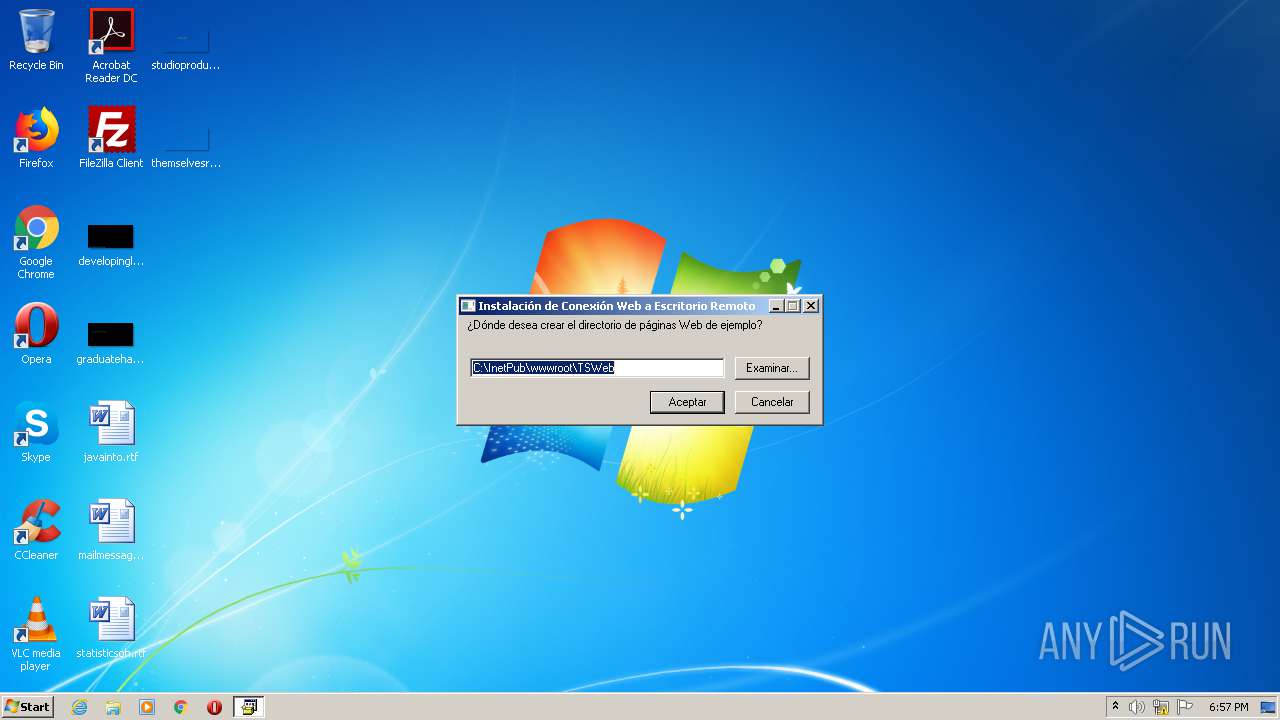
| (PID) Process: | (2964) tswebsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\TS Web Clients |
| Operation: | write | Name: | InstallDir |
Value: C:\InetPub\wwwroot\TSWeb | |||
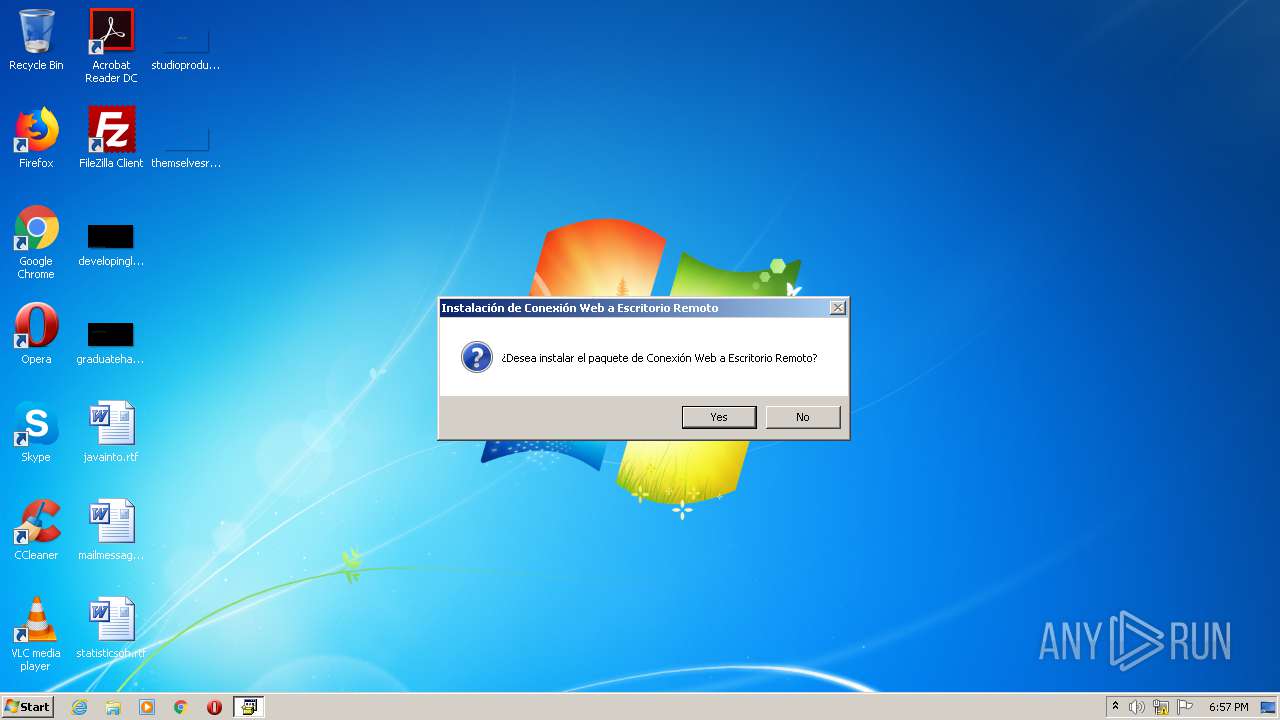
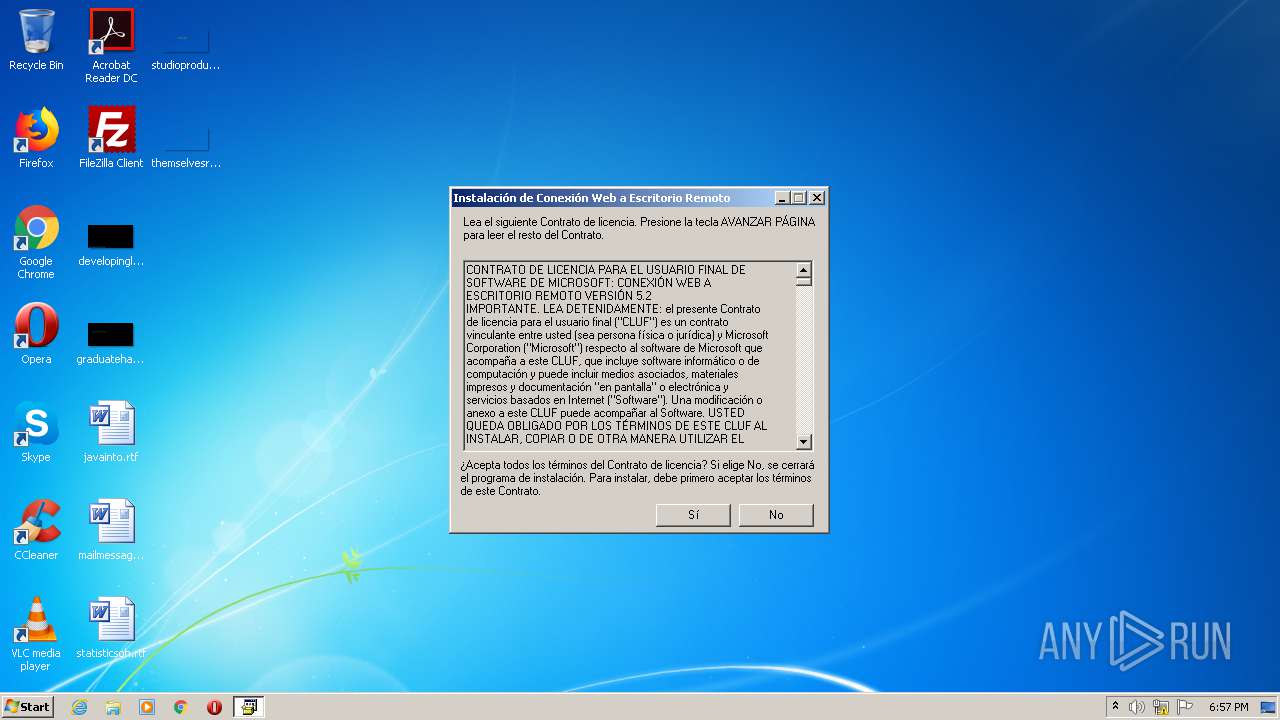
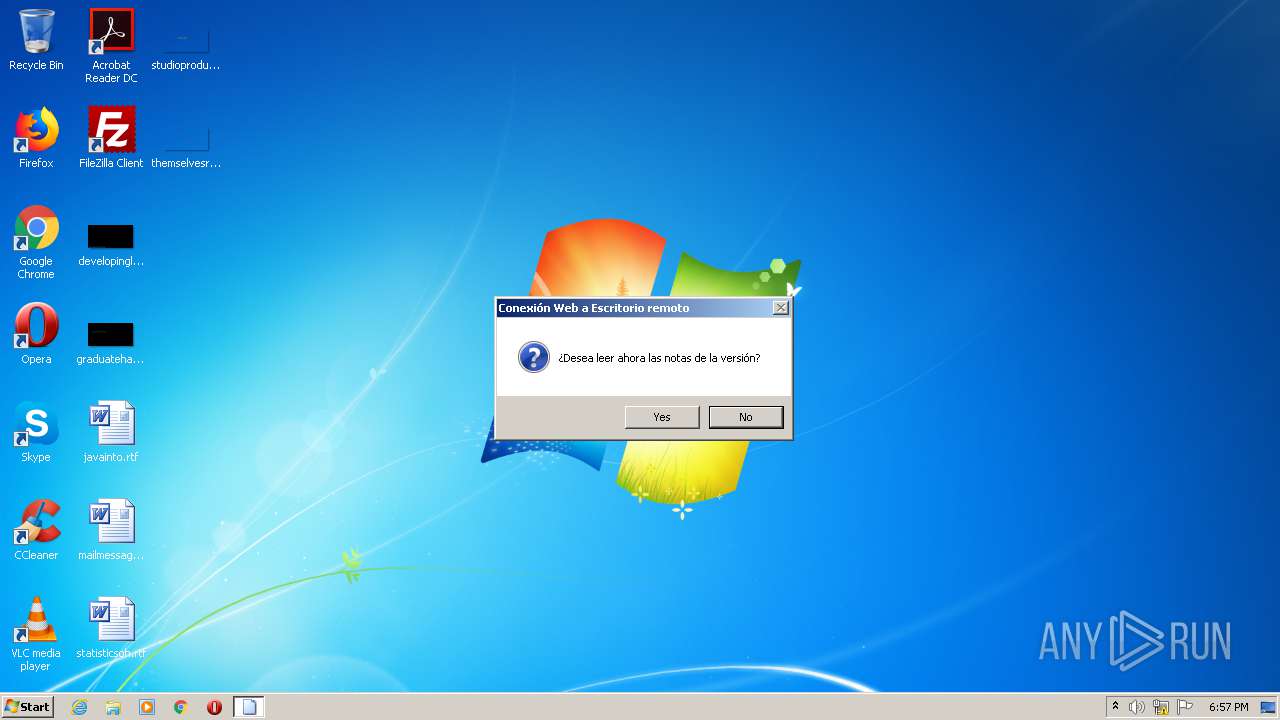
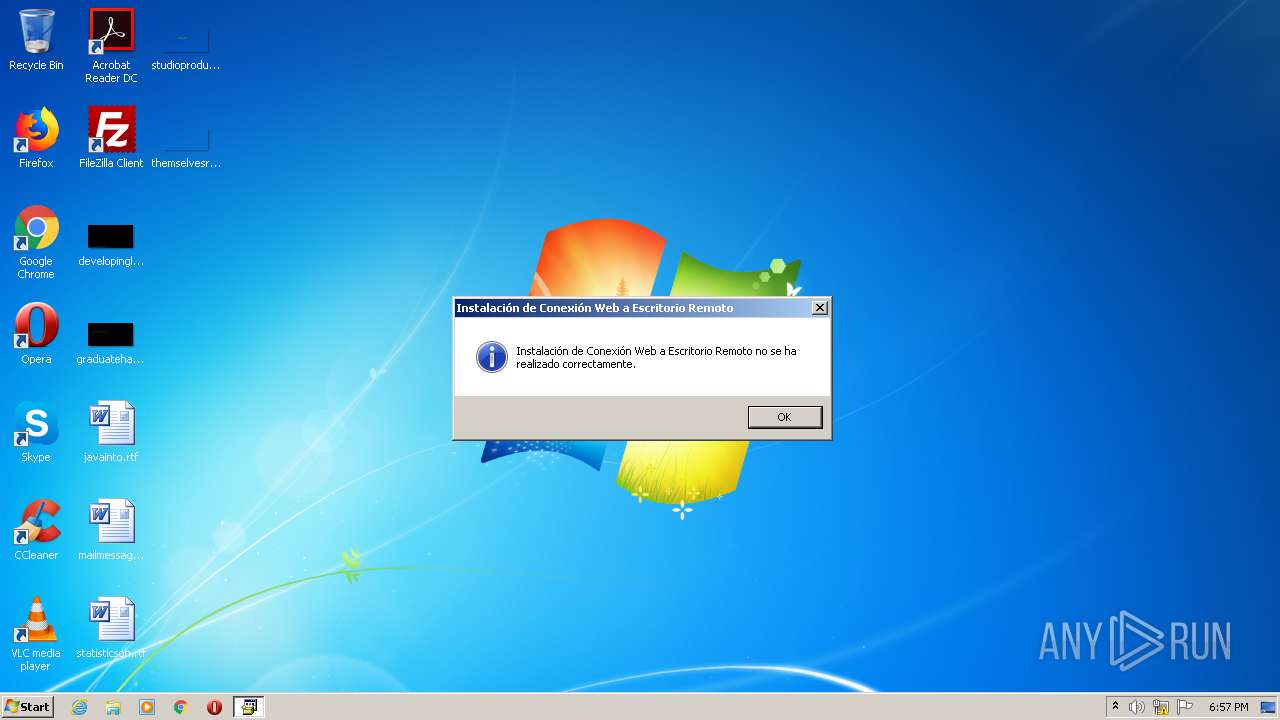
| (PID) Process: | (2964) tswebsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TsActiveXClient |
| Operation: | write | Name: | DisplayName |
Value: Conexión Web a Escritorio remoto | |||
| (PID) Process: | (2964) tswebsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TsActiveXClient |
| Operation: | write | Name: | UninstallString |
Value: rundll32 advpack.dll,LaunchINFSection C:\InetPub\wwwroot\TSWeb\setup.inf,DefaultUninstall,, | |||
| (PID) Process: | (3108) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (3108) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
Executable files
3
Suspicious files
2
Text files
58
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | tswebsetup.exe | C:\InetPub\wwwroot\TSWeb\SET1353.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | tswebsetup.exe | C:\InetPub\wwwroot\TSWeb\SET1363.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | tswebsetup.exe | C:\InetPub\wwwroot\TSWeb\SET1364.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | tswebsetup.exe | C:\InetPub\wwwroot\TSWeb\SET1375.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | tswebsetup.exe | C:\InetPub\wwwroot\TSWeb\SET1376.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | tswebsetup.exe | C:\InetPub\wwwroot\TSWeb\SET1377.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | tswebsetup.exe | C:\InetPub\wwwroot\TSWeb\SET1388.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | tswebsetup.exe | C:\InetPub\wwwroot\TSWeb\setup.inf | ini | |
MD5:— | SHA256:— | |||
| 2964 | tswebsetup.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\setup.inf | ini | |
MD5:— | SHA256:— | |||
| 2964 | tswebsetup.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\msrdp.cab | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report