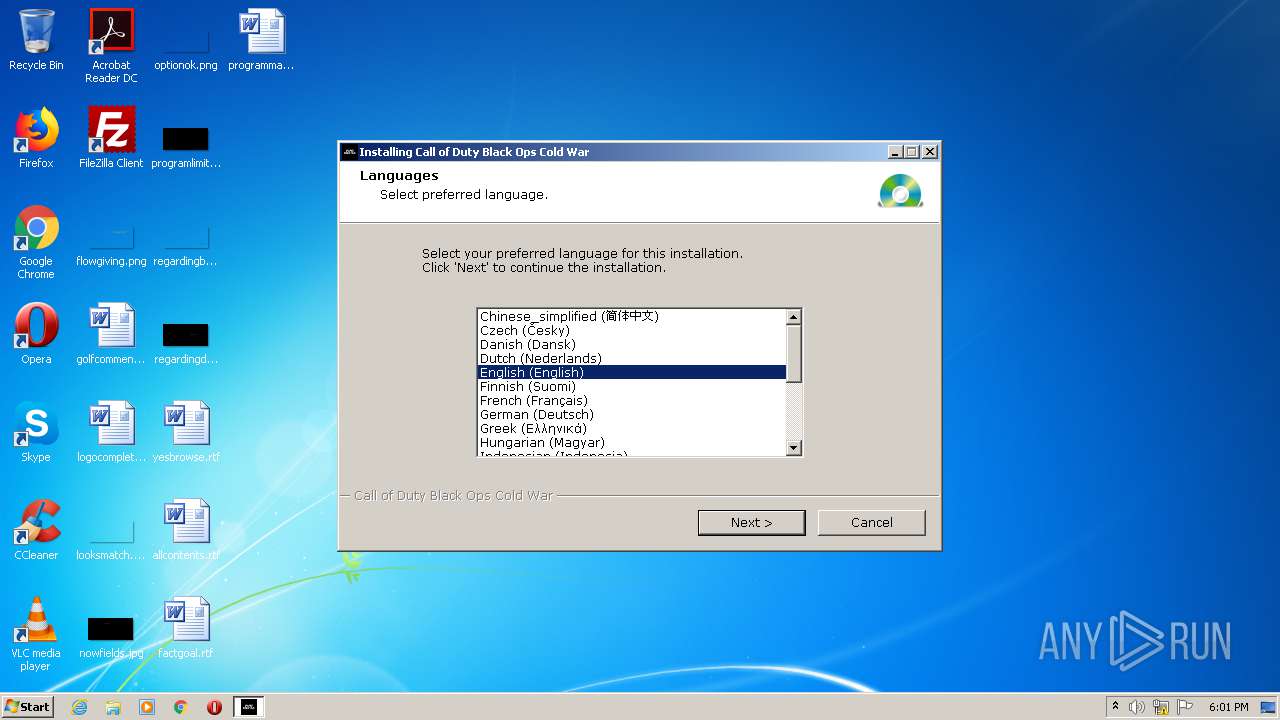
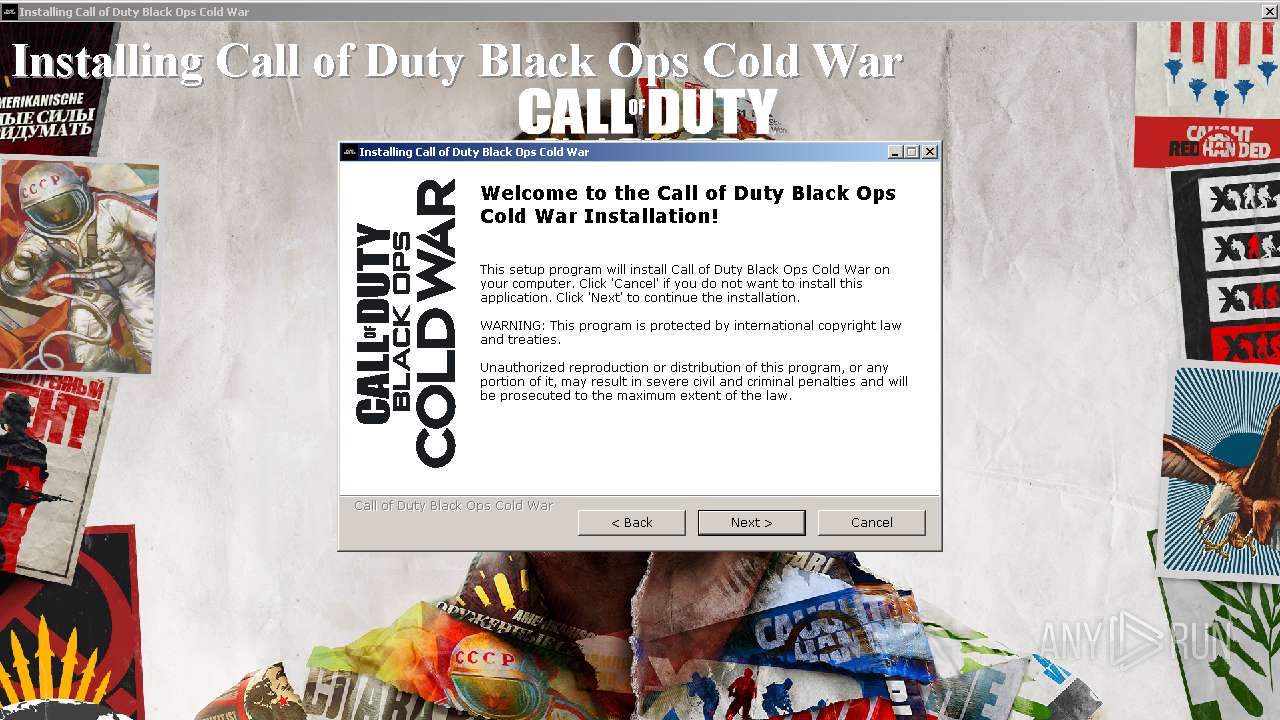
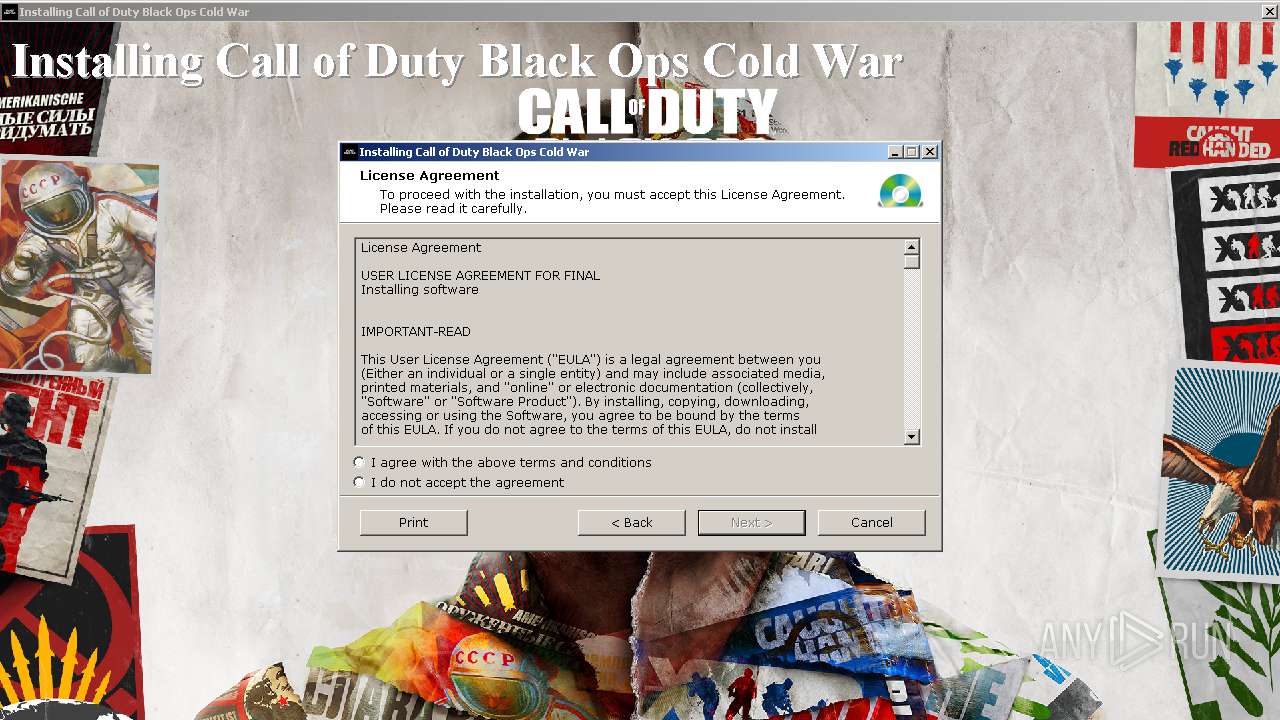
| File name: | Call of Duty Black Ops Cold War Setup.exe |
| Full analysis: | https://app.any.run/tasks/1250a11c-e826-46ef-ac89-60871221c770 |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2020, 18:00:54 |
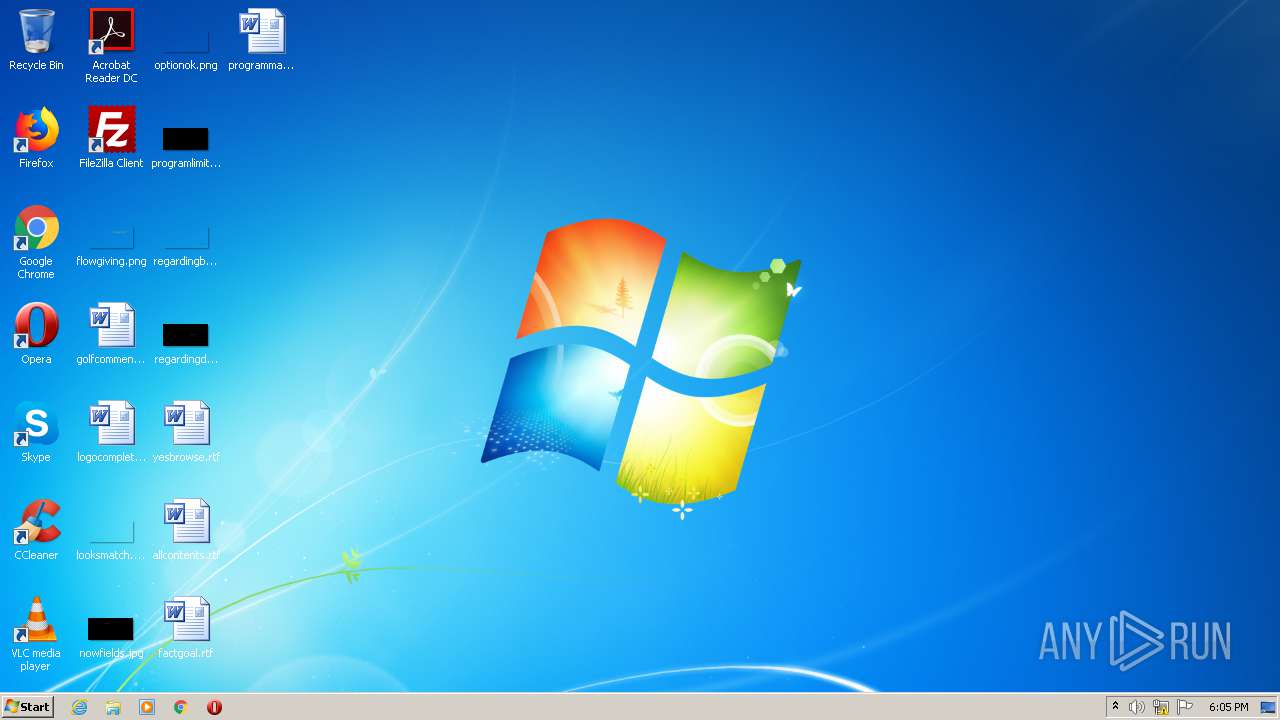
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 330EDFA47C4140A2DF7297B9FF3E1E05 |
| SHA1: | BC4B8099C061342FCF3FDCE6EDBC41B18F2FCF51 |
| SHA256: | 3C652A0595815E2DEC267973E955DFA8D3420FD6657BA95A6F648709D3E544AA |
| SSDEEP: | 196608:jgAG6cAeoXfVJ6nccyAtvXCp6NFQPinZZ:jgFKVIcsC6Ne6ZZ |
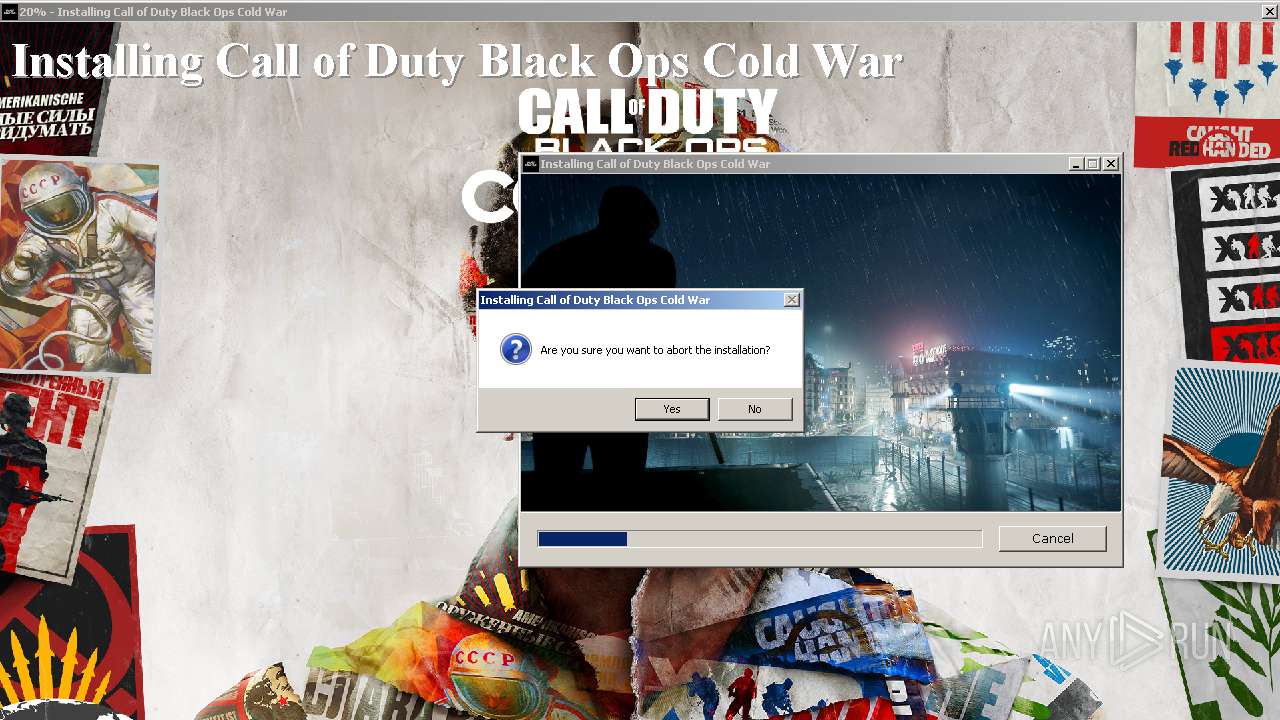
MALICIOUS
Drops executable file immediately after starts
- Call of Duty Black Ops Cold War Setup.exe (PID: 3640)
Loads dropped or rewritten executable
- Call of Duty Black Ops Cold War Setup.exe (PID: 3640)
SUSPICIOUS
Executable content was dropped or overwritten
- Call of Duty Black Ops Cold War Setup.exe (PID: 3640)
Reads the Windows organization settings
- Call of Duty Black Ops Cold War Setup.exe (PID: 3640)
Creates a directory in Program Files
- Call of Duty Black Ops Cold War Setup.exe (PID: 3640)
Reads Windows owner or organization settings
- Call of Duty Black Ops Cold War Setup.exe (PID: 3640)
Creates files in the program directory
- Call of Duty Black Ops Cold War Setup.exe (PID: 3640)
Starts CMD.EXE for commands execution
- Call of Duty Black Ops Cold War Setup.exe (PID: 3640)
INFO
Manual execution by user
- opera.exe (PID: 1788)
Creates files in the user directory
- opera.exe (PID: 1788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:01:31 18:44:13+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 4096 |
| InitializedDataSize: | 2813952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d20 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Jan-2011 17:44:13 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 31-Jan-2011 17:44:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000EAC | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.942 |
.rdata | 0x00002000 | 0x00000488 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.74466 |
.data | 0x00003000 | 0x00000560 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.01054 |
.gentee | 0x00004000 | 0x000165E7 | 0x00017000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.94217 |
.rsrc | 0x0001B000 | 0x00295668 | 0x00296000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.9893 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07161 | 1930 | Latin 1 / Western European | English - United States | RT_MANIFEST |
1000 | 2.23119 | 54 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGLANG | 2.60717 | 344 | Latin 1 / Western European | English - United States | RT_DIALOG |
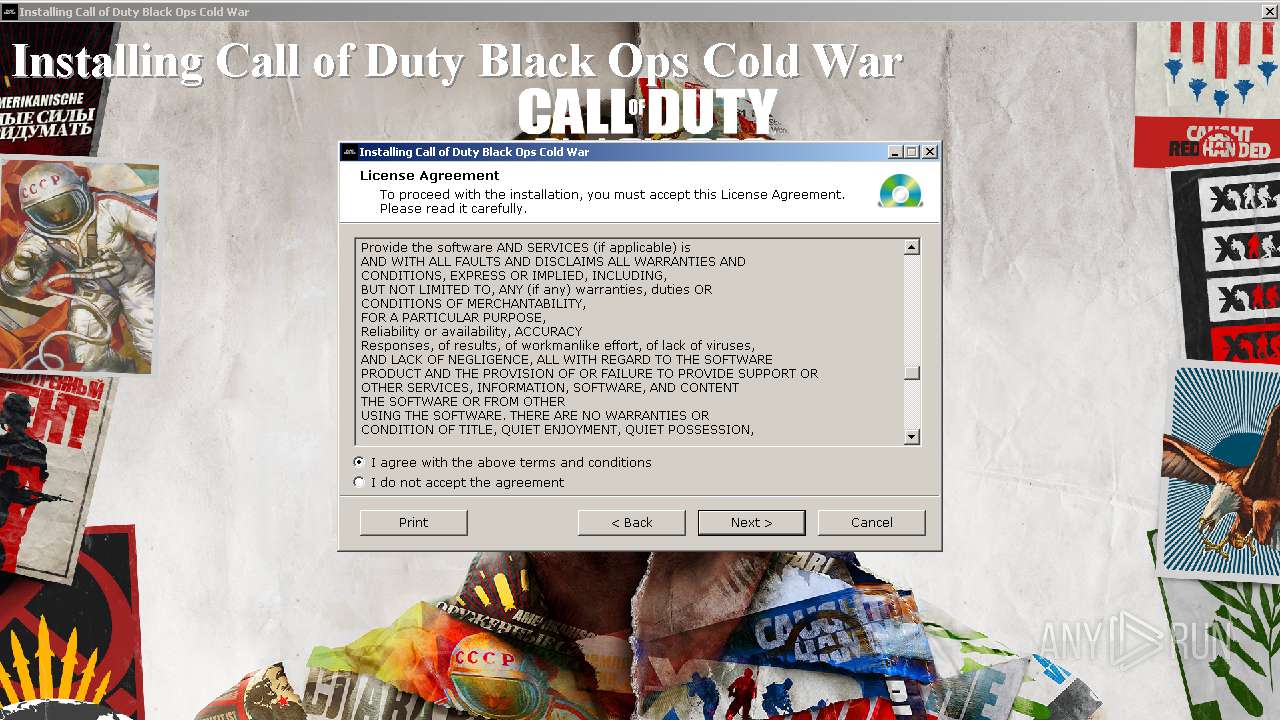
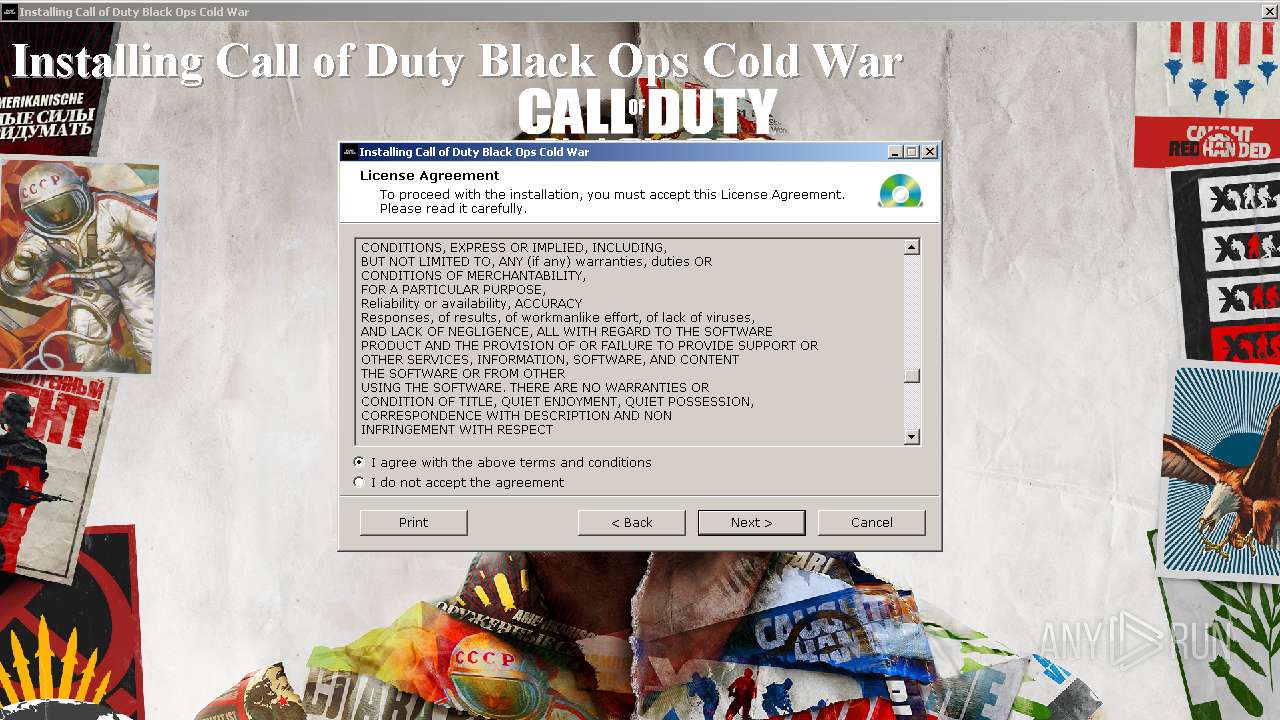
IDD_DLGLIC2 | 2.88953 | 460 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGPATH | 2.68908 | 544 | Latin 1 / Western European | English - United States | RT_DIALOG |
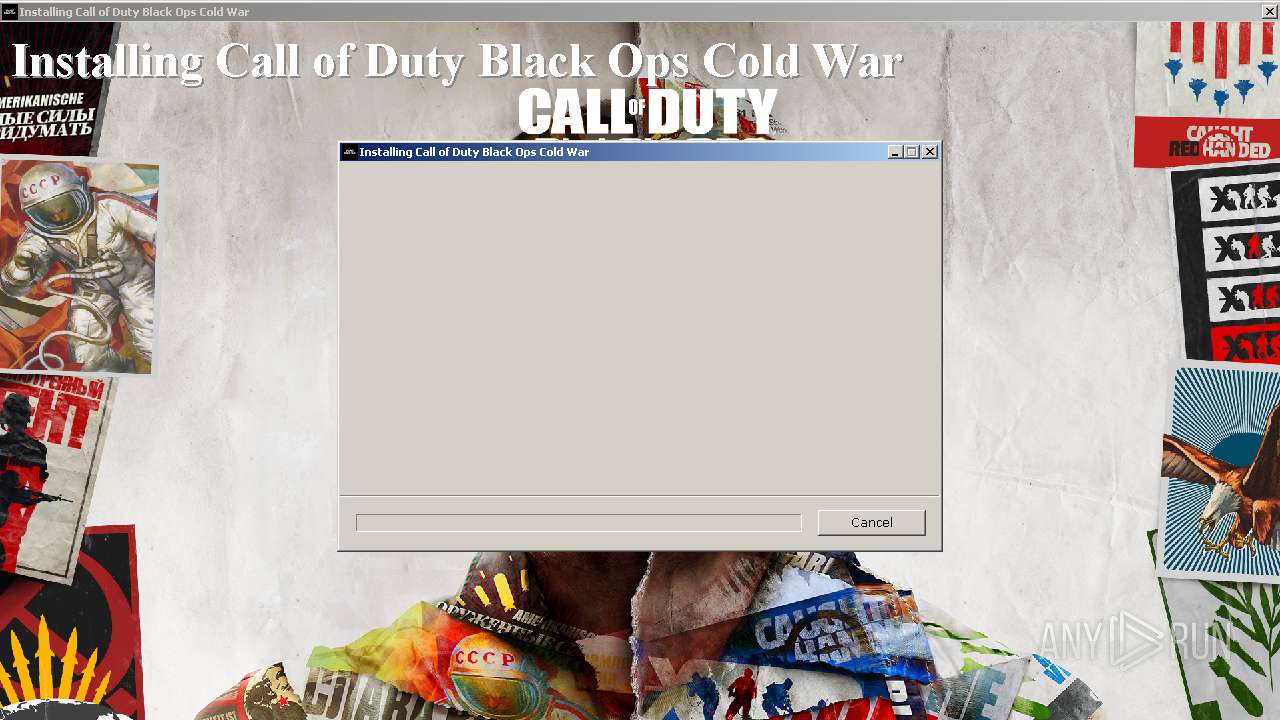
IDD_DLGPROG | 2.78207 | 600 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGREADY | 2.6391 | 344 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
IDD_DLGSETS | 2.73533 | 504 | Latin 1 / Western European | English - United States | RT_DIALOG |
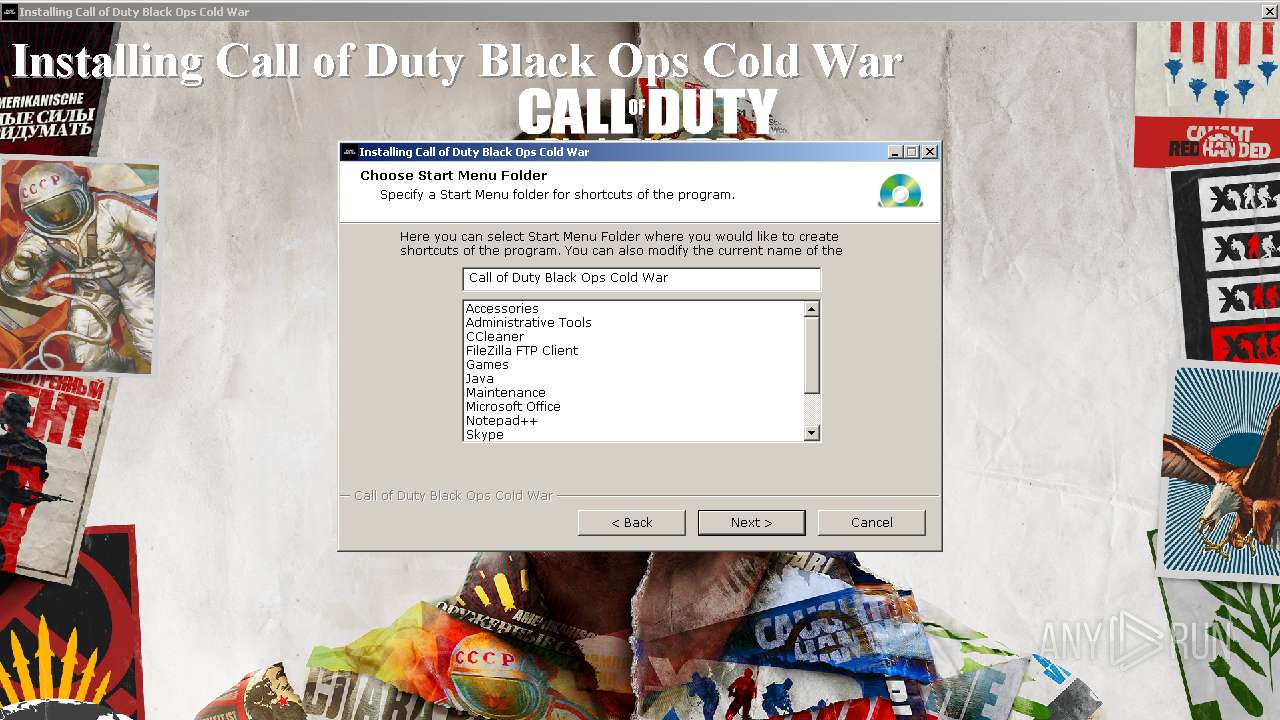
IDD_DLGSHFOLDER | 2.72865 | 440 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGSLIDESHOW | 2.71998 | 248 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
Imports
KERNEL32.dll |
MSVCRT.dll |
USER32.dll |
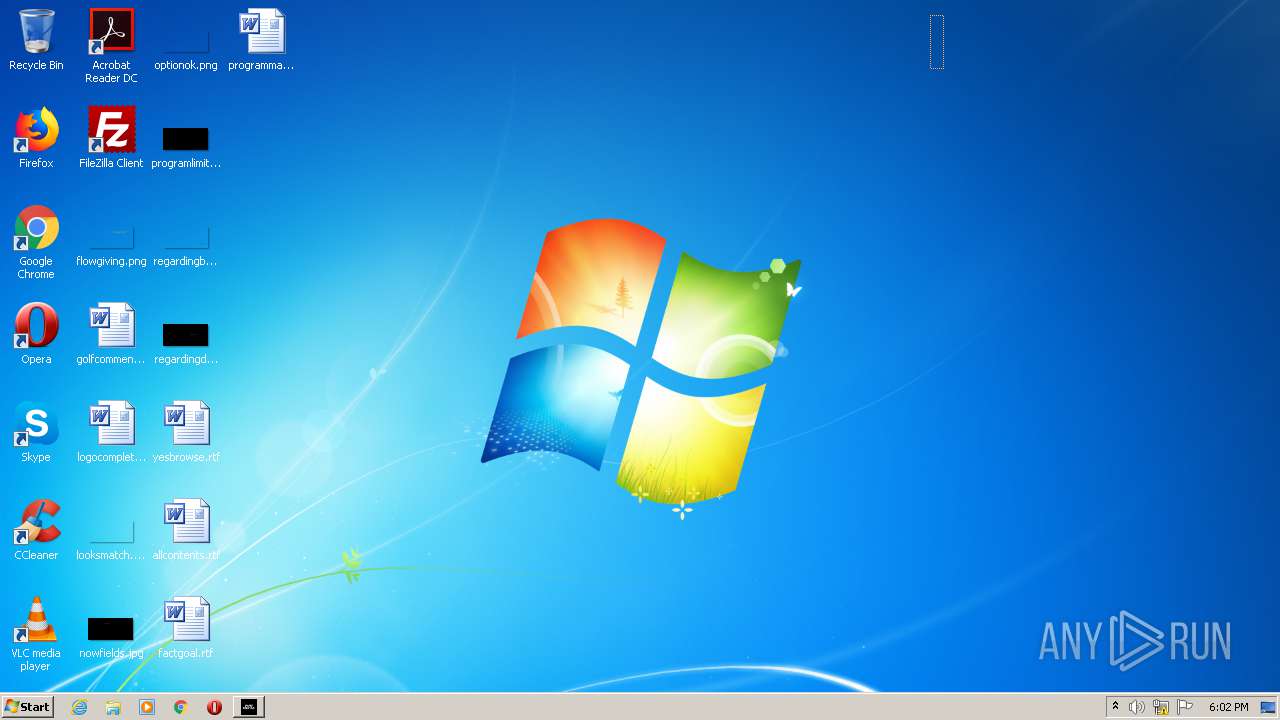
Total processes
41
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1788 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\AppData\Local\Temp\Call of Duty Black Ops Cold War Setup.exe" | C:\Users\admin\AppData\Local\Temp\Call of Duty Black Ops Cold War Setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3060 | cmd /c ""C:\Users\admin\AppData\Local\Temp\deldll.bat" " | C:\Windows\system32\cmd.exe | — | Call of Duty Black Ops Cold War Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3640 | "C:\Users\admin\AppData\Local\Temp\Call of Duty Black Ops Cold War Setup.exe" | C:\Users\admin\AppData\Local\Temp\Call of Duty Black Ops Cold War Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
Total events
589
Read events
525
Write events
63
Delete events
1
Modification events
| (PID) Process: | (3640) Call of Duty Black Ops Cold War Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\tmp |
| Operation: | delete key | Name: | (default) |
Value: | |||
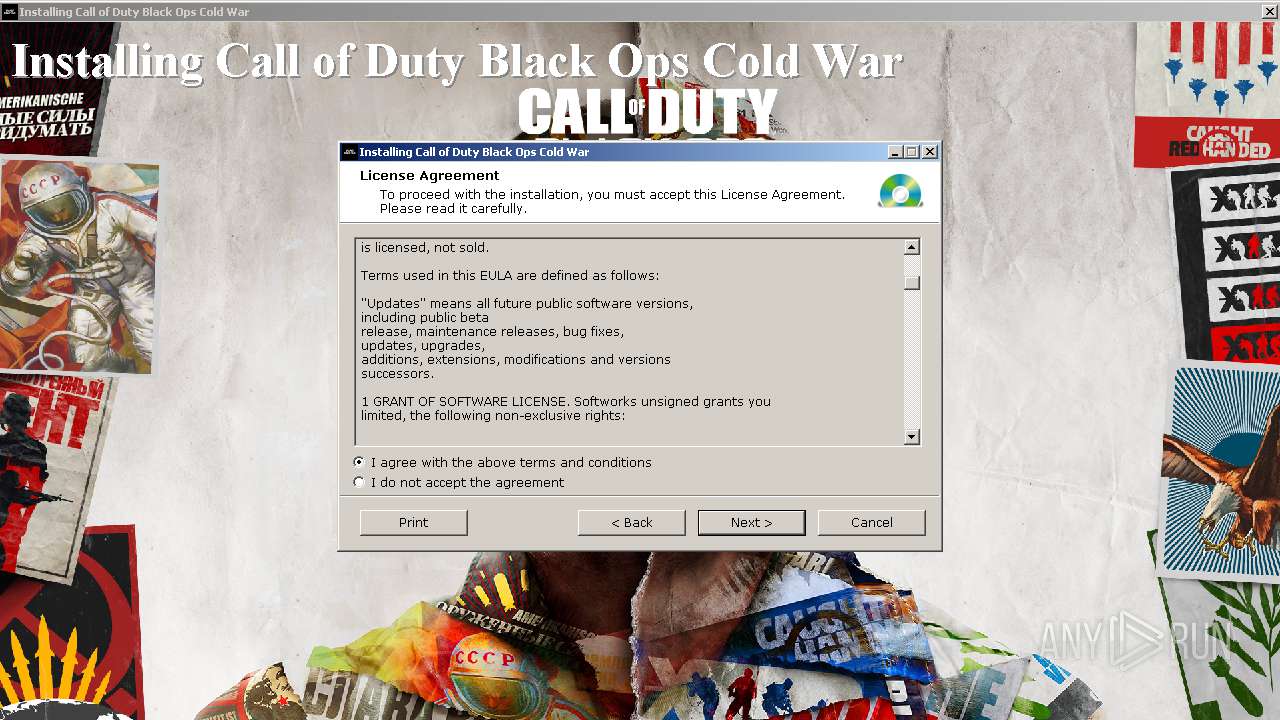
| (PID) Process: | (3640) Call of Duty Black Ops Cold War Setup.exe | Key: | HKEY_CURRENT_USER\Software\Call of Duty Black Ops Cold War |
| Operation: | write | Name: | InstLang |
Value: english | |||
| (PID) Process: | (3640) Call of Duty Black Ops Cold War Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3640) Call of Duty Black Ops Cold War Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1788) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (1788) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
23
Text files
20
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3640 | Call of Duty Black Ops Cold War Setup.exe | C:\Users\admin\AppData\Local\Temp\gentee02\93.jpg | image | |
MD5:— | SHA256:— | |||
| 3640 | Call of Duty Black Ops Cold War Setup.exe | C:\Users\admin\AppData\Local\Temp\~DF2268C83B8EB3859A.TMP | — | |
MD5:— | SHA256:— | |||
| 3640 | Call of Duty Black Ops Cold War Setup.exe | C:\Users\admin\AppData\Local\Temp\gentee02\setup_temp.gea | bs | |
MD5:— | SHA256:— | |||
| 1788 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprA2BE.tmp | — | |
MD5:— | SHA256:— | |||
| 3640 | Call of Duty Black Ops Cold War Setup.exe | C:\Users\admin\AppData\Local\Temp\gentee02\coverPC.jpg | image | |
MD5:— | SHA256:— | |||
| 1788 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprA2EE.tmp | — | |
MD5:— | SHA256:— | |||
| 3640 | Call of Duty Black Ops Cold War Setup.exe | C:\Users\admin\AppData\Local\Temp\gentee02\4logo-menu.jpg | image | |
MD5:— | SHA256:— | |||
| 3640 | Call of Duty Black Ops Cold War Setup.exe | C:\Users\admin\AppData\Local\Temp\gentee02\2banner.gif | image | |
MD5:— | SHA256:— | |||
| 3640 | Call of Duty Black Ops Cold War Setup.exe | C:\Users\admin\AppData\Local\Temp\gentee02\82.jpg | image | |
MD5:— | SHA256:— | |||
| 3640 | Call of Duty Black Ops Cold War Setup.exe | C:\Users\admin\AppData\Local\Temp\gentee02\71.jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1788 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1788 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
1788 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |