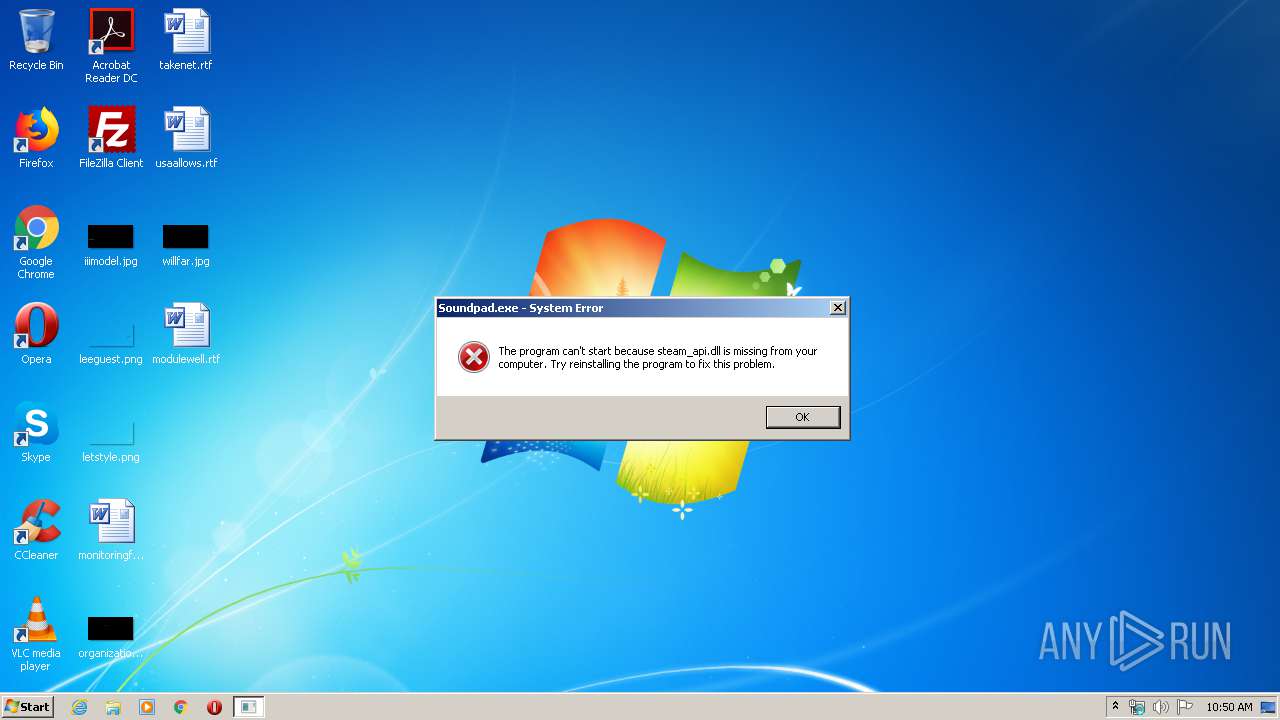
| File name: | Soundpad.exe |
| Full analysis: | https://app.any.run/tasks/2394f31d-eac7-4c75-bd8a-b1bb01c1fd62 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2020, 09:50:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 63C9498201254AB0B2C0753271D52904 |
| SHA1: | B0596DEA6C0F67E915133DCCE40597AB802E0C04 |
| SHA256: | 3C5F2D4C38834DAA7A66DDE3D554B3B80E35ECE971B5875564A1195960850766 |
| SSDEEP: | 98304:F69vTrbMUo8ZQRLc3djGgPApK3D5NZAok4CPknVbjrTAVdQM3efopyh/5tHUq3QZ:F69DM74NjGgopKxAS7jImfdt3B2 |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 372)
Changes settings of System certificates
- msdt.exe (PID: 3224)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 372)
Creates files in the user directory
- explorer.exe (PID: 372)
Removes files from Windows directory
- msdt.exe (PID: 3224)
Executable content was dropped or overwritten
- msdt.exe (PID: 3164)
- msdt.exe (PID: 3224)
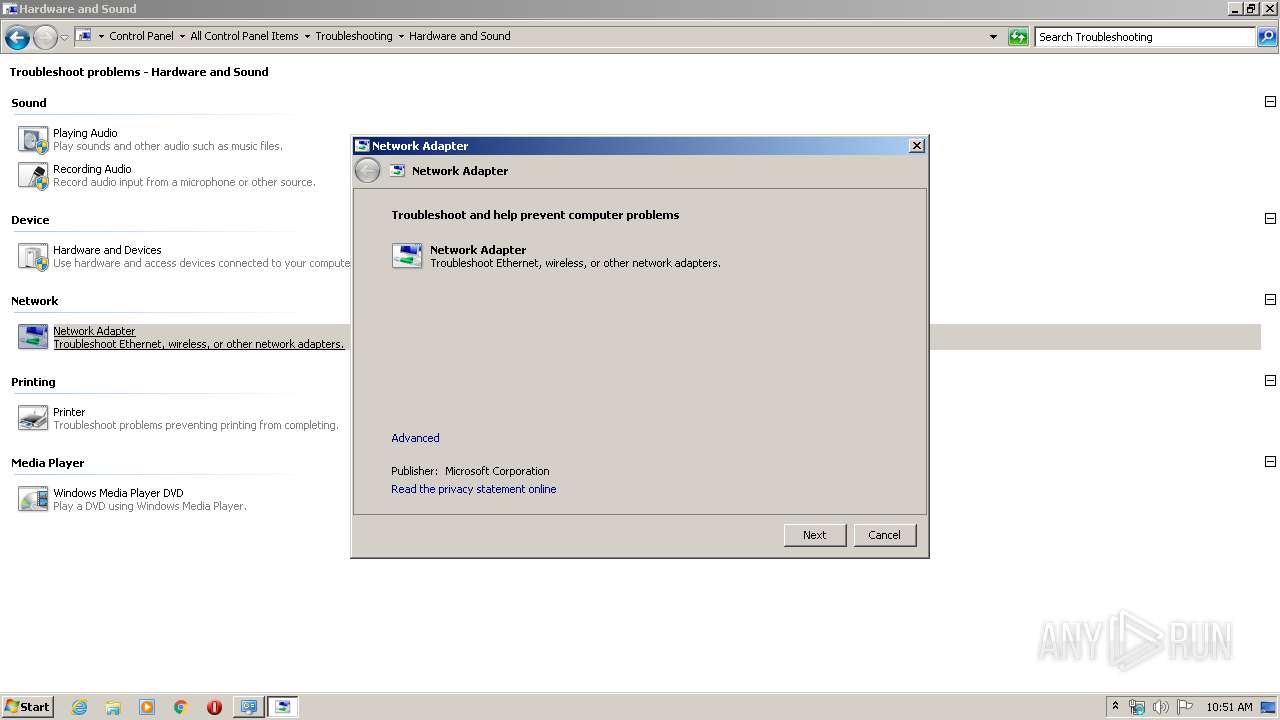
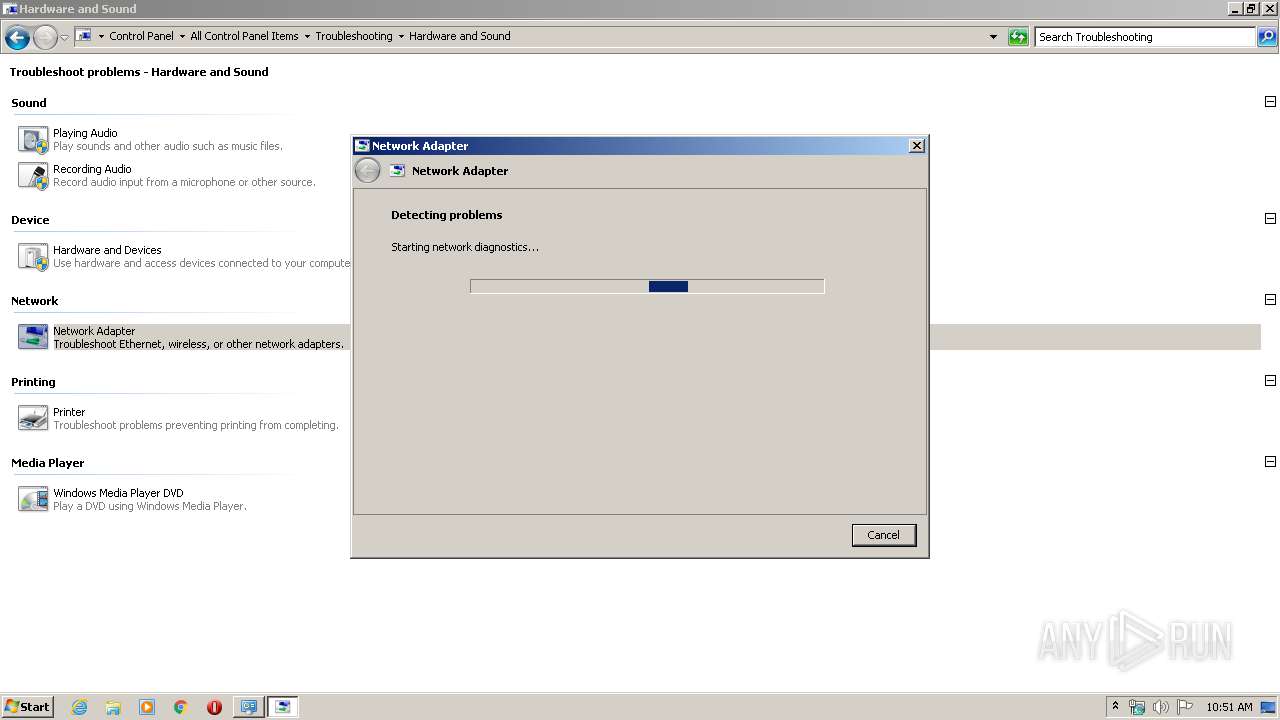
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 3996)
Executed via COM
- sdiagnhost.exe (PID: 3996)
Creates files in the Windows directory
- msdt.exe (PID: 3224)
Adds / modifies Windows certificates
- msdt.exe (PID: 3224)
INFO
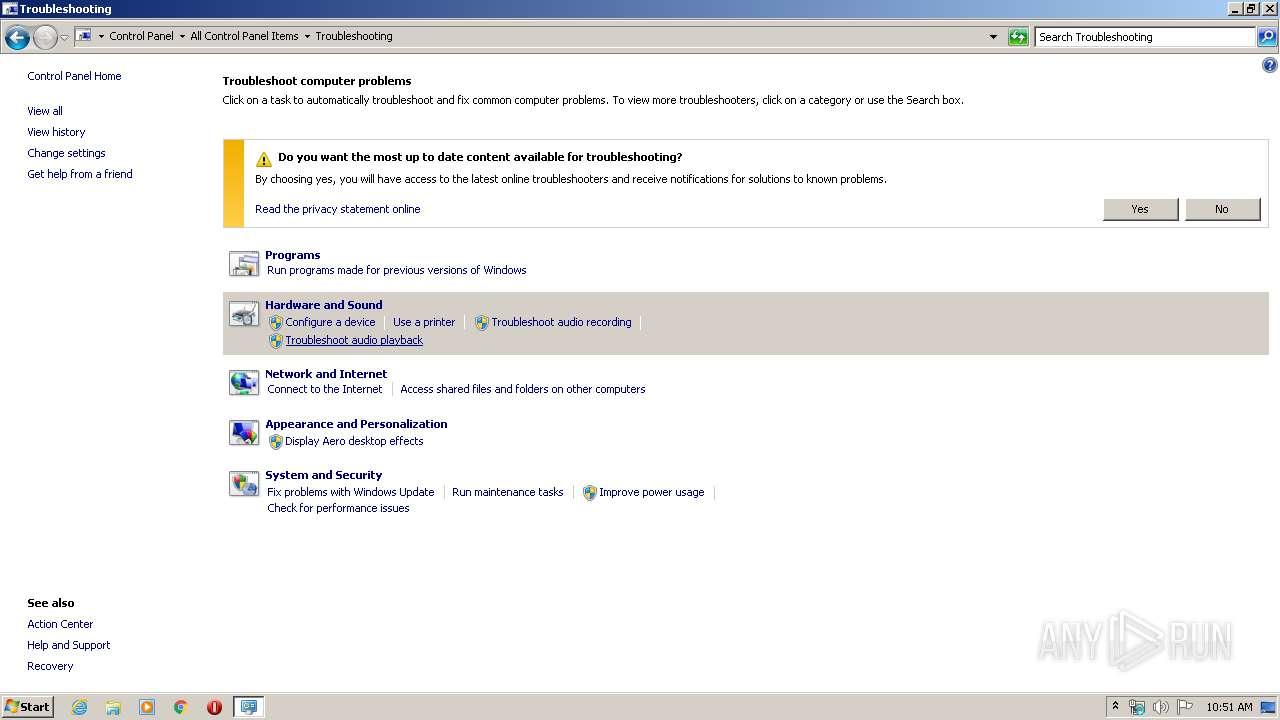
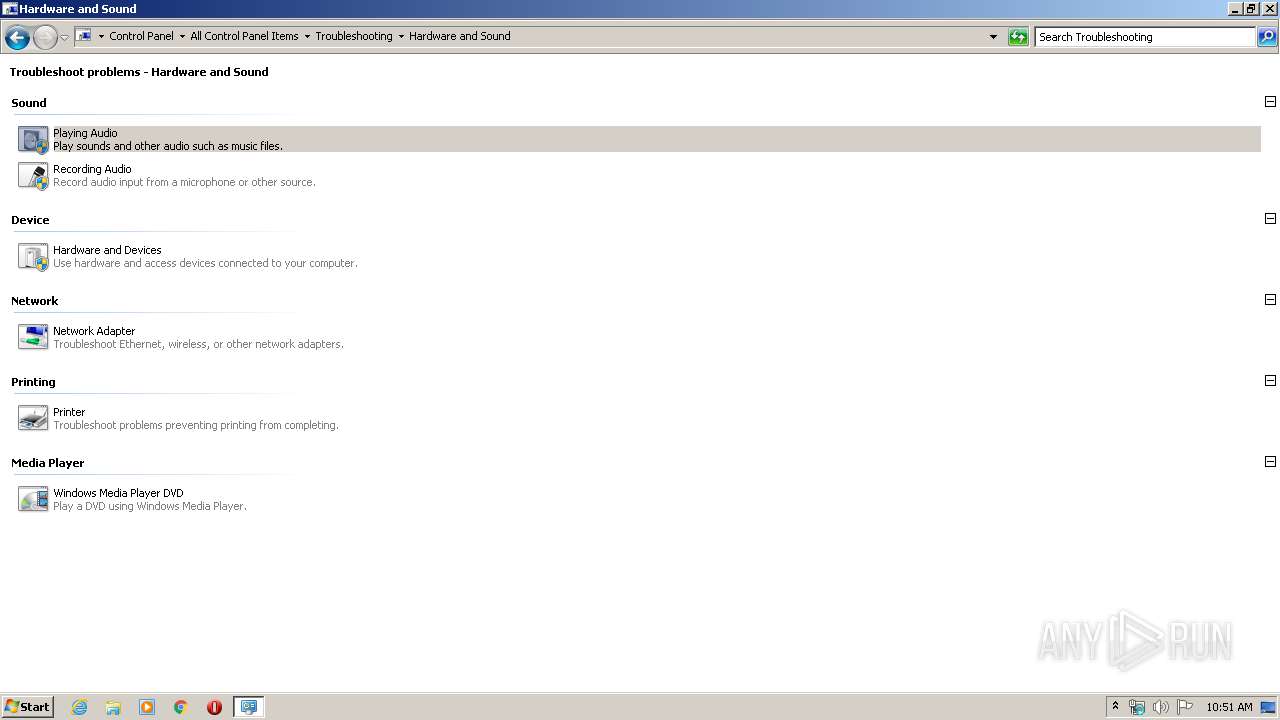
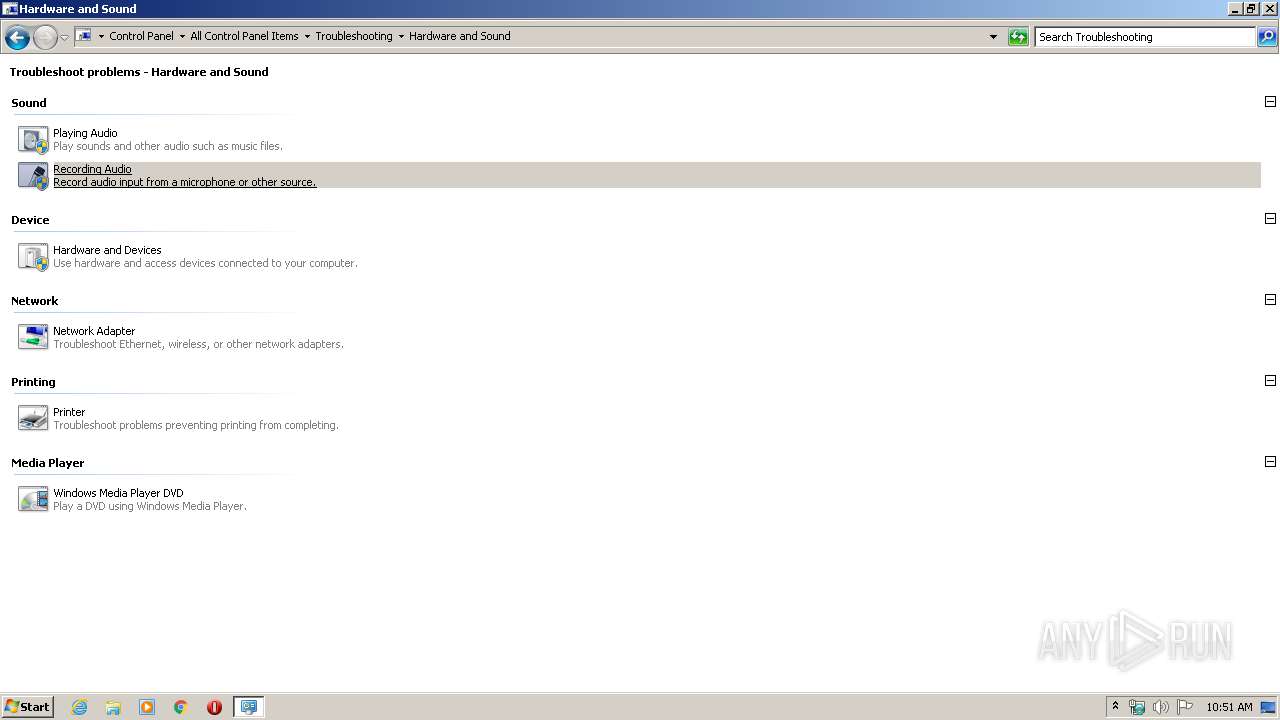
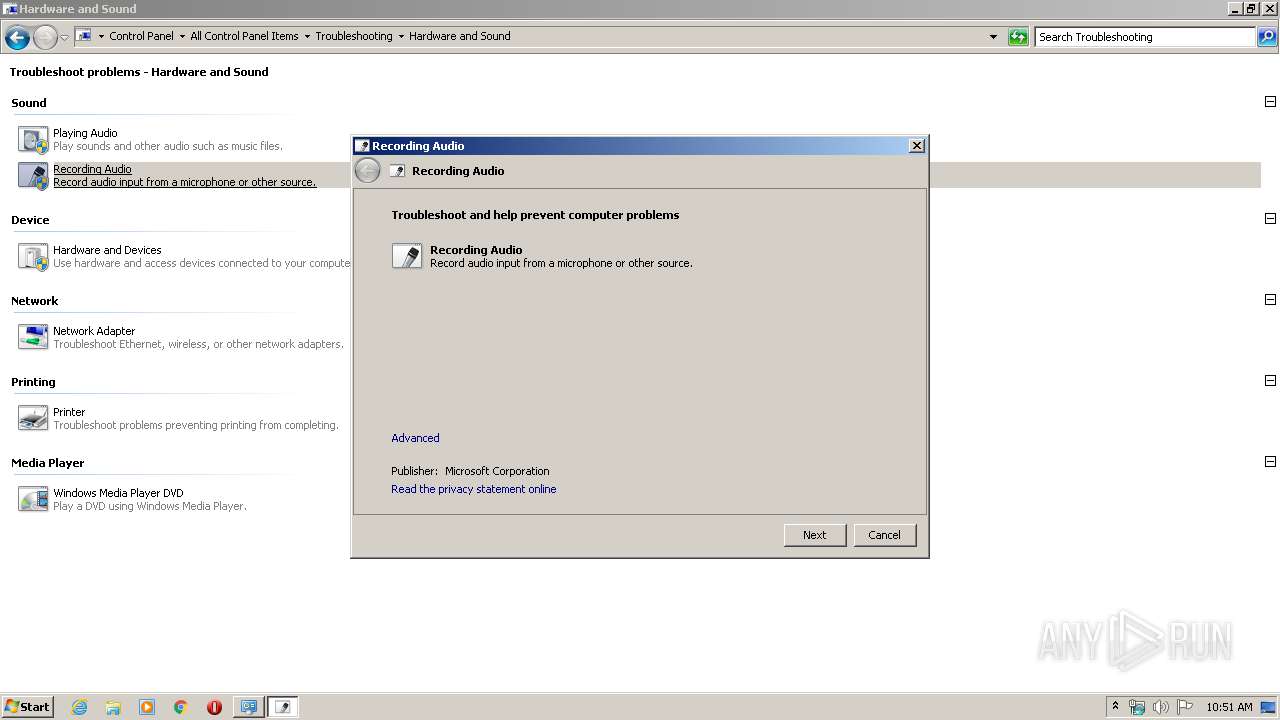
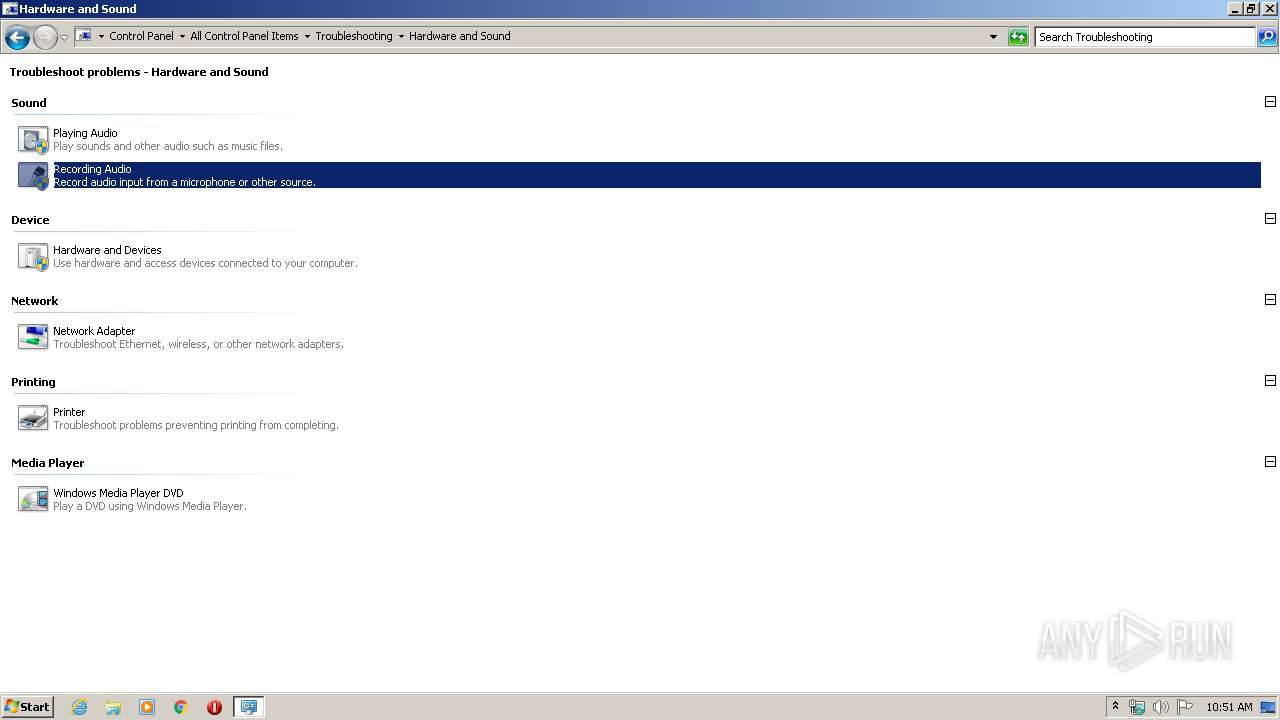
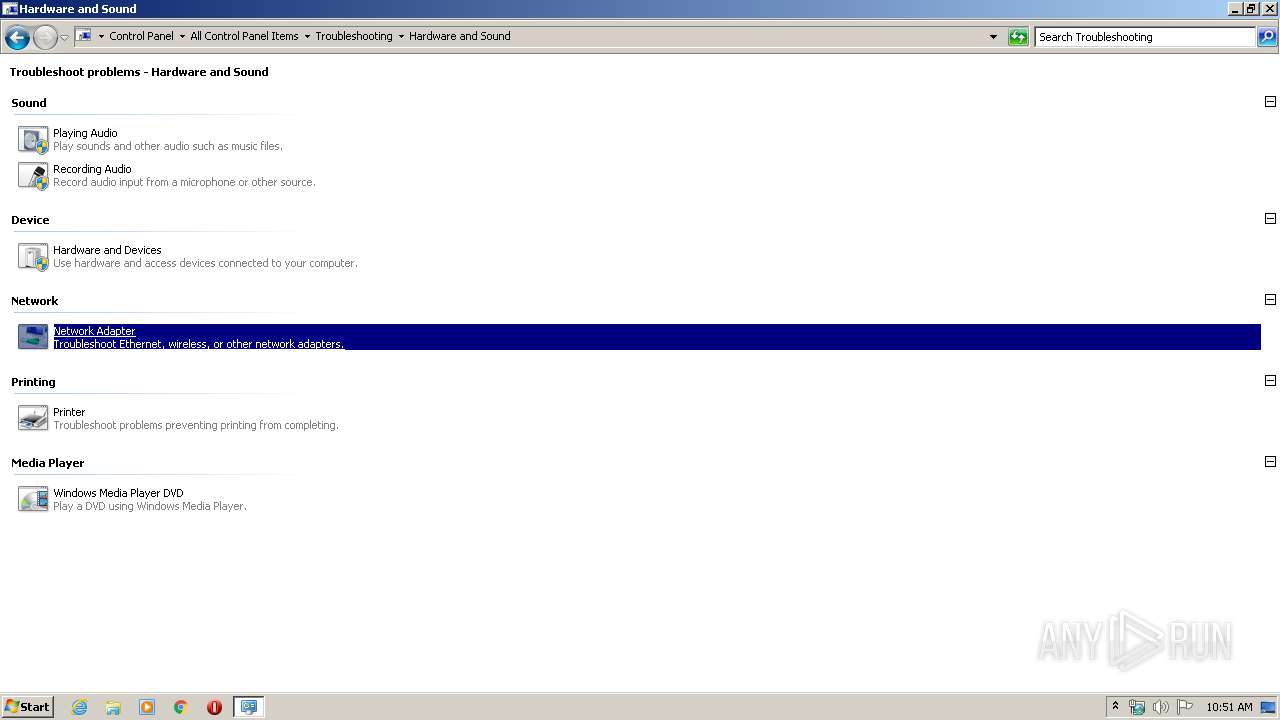
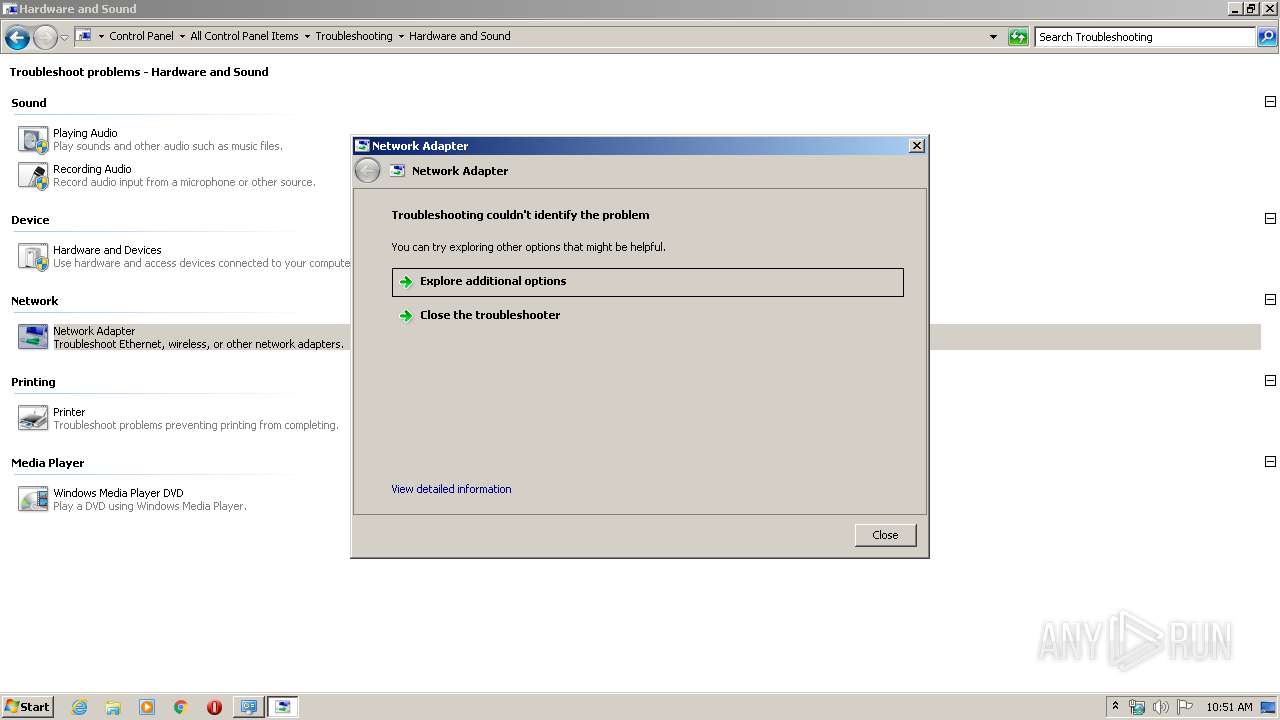
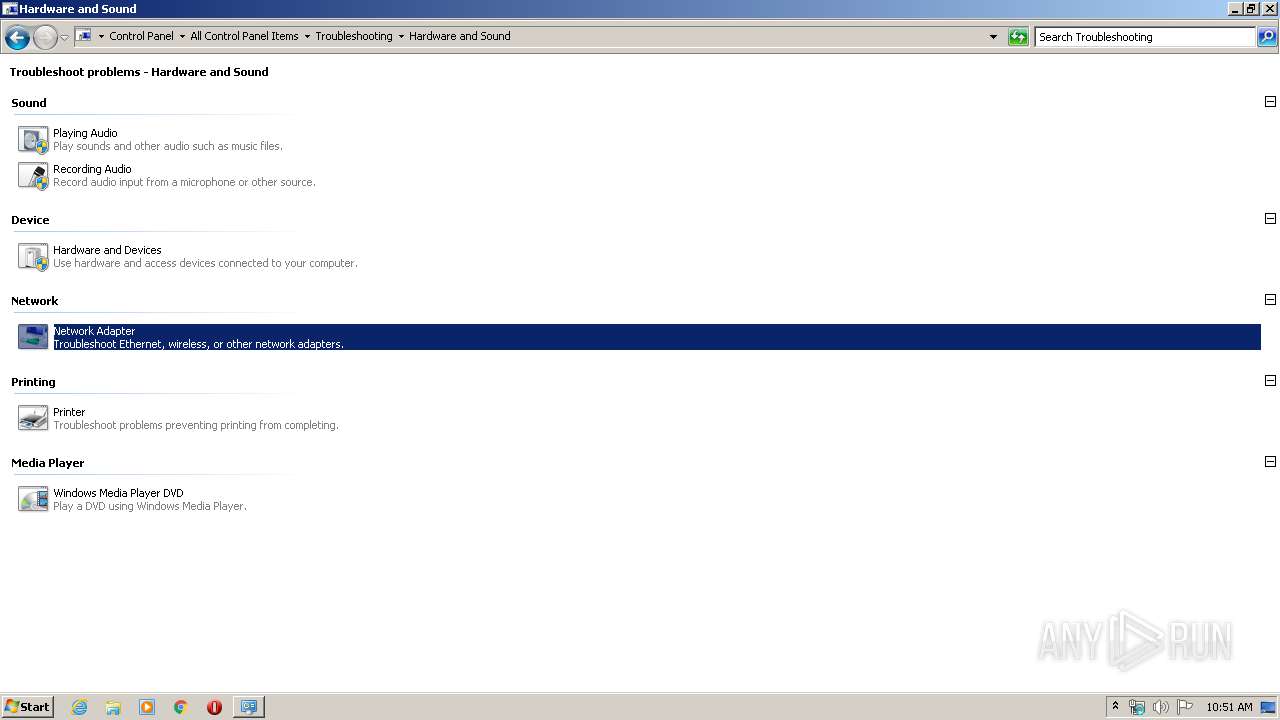
Manual execution by user
- msdt.exe (PID: 3224)
- rundll32.exe (PID: 3064)
- rundll32.exe (PID: 3840)
Reads settings of System Certificates
- msdt.exe (PID: 3224)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1348)
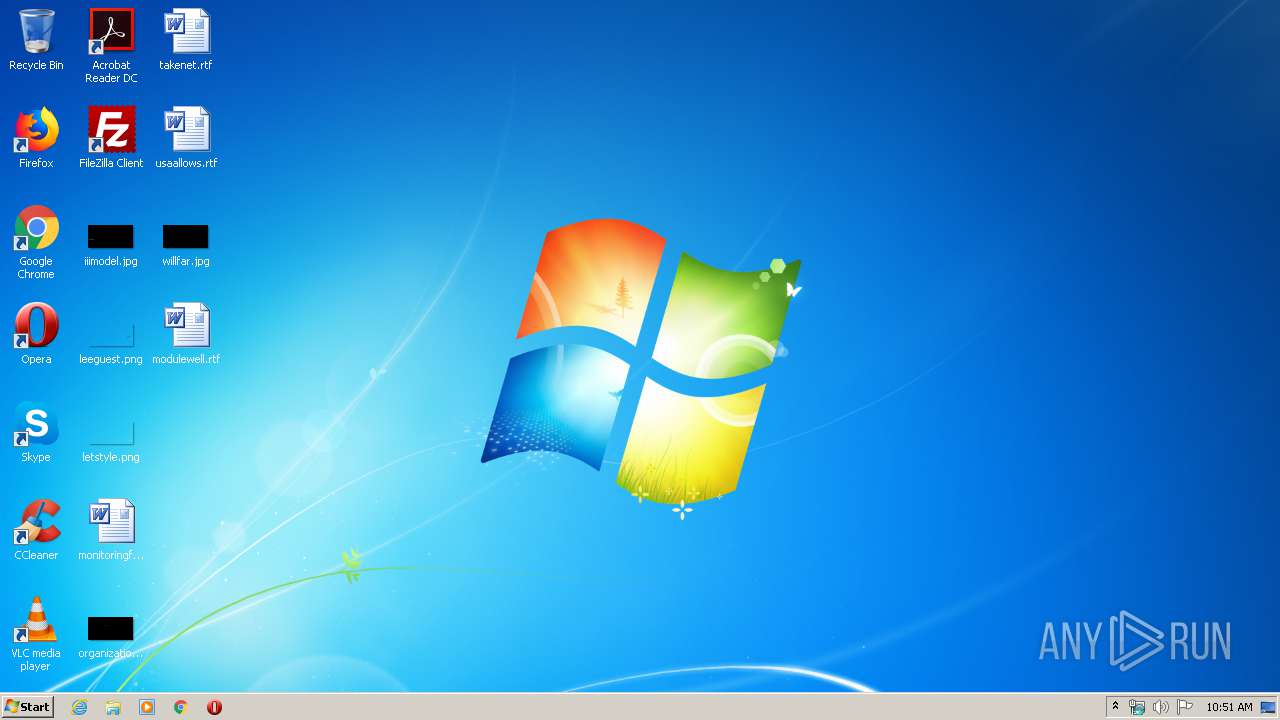
Creates files in the user directory
- WINWORD.EXE (PID: 1348)
Starts Microsoft Office Application
- explorer.exe (PID: 372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:27 13:19:45+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 6988800 |
| InitializedDataSize: | 4240896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x54f580 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.2.1.0 |
| ProductVersionNumber: | 3.2.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Leppsoft |
| FileDescription: | Soundpad |
| FileVersion: | 3.2.1 |
| InternalName: | Soundpad |
| LegalCopyright: | Copyright (C) 2016-2019 Leppsoft |
| OriginalFileName: | Soundpad.exe |
| ProductName: | Soundpad |
| ProductVersion: | 3.2.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Dec-2019 12:19:45 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Leppsoft |
| FileDescription: | Soundpad |
| FileVersion: | 3.2.1 |
| InternalName: | Soundpad |
| LegalCopyright: | Copyright (C) 2016-2019 Leppsoft |
| OriginalFilename: | Soundpad.exe |
| ProductName: | Soundpad |
| ProductVersion: | 3.2.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000158 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 27-Dec-2019 12:19:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x006AA387 | 0x006AA400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43213 |
.rdata | 0x006AC000 | 0x001D002E | 0x001D0200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.49412 |
.data | 0x0087D000 | 0x000AA778 | 0x0001F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.94562 |
_RDATA | 0x00928000 | 0x000005E0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.68054 |
.rsrc | 0x00929000 | 0x00104578 | 0x00104600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04701 |
.reloc | 0x00A2E000 | 0x0008BFC4 | 0x0008C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.54195 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33093 | 1117 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.58151 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3 | 2.38255 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 3.30709 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.54523 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.05581 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.21025 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 2.2093 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 1.14151 | 308 | UNKNOWN | English - United States | RT_CURSOR |
10 | 1.52552 | 308 | UNKNOWN | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
AVRT.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
MF.dll |
MFPlat.DLL |
MFReadWrite.dll |
MSIMG32.dll |
Total processes
52
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Users\admin\AppData\Local\Temp\Soundpad.exe" | C:\Users\admin\AppData\Local\Temp\Soundpad.exe | — | explorer.exe | |||||||||||
User: admin Company: Leppsoft Integrity Level: MEDIUM Description: Soundpad Exit code: 3221225781 Version: 3.2.1 Modules
| |||||||||||||||
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 480 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\system32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 620 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\system32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | "C:\Windows\System32\msdt.exe" -ep TSControlPanel -path C:\Windows\Diagnostics\Index\NetworkDiagnostics_4_NetworkAdapter.xml -context {66613A6E-0783-40B4-92E8-119C2728CB12} | C:\Windows\System32\msdt.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\monitoringfriday.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3036 | "C:\Windows\System32\msdt.exe" -ep TSControlPanel -path C:\Windows\Diagnostics\Index\NetworkDiagnostics_4_NetworkAdapter.xml -context {CF0003A8-7488-471C-A63E-C32481965724} | C:\Windows\System32\msdt.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3040 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\system32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3064 | "C:\Windows\System32\rundll32.exe" werconcpl.dll, LaunchErcApp -queuereporting | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3164 | "C:\Windows\System32\msdt.exe" -ep TSControlPanel -path C:\Windows\Diagnostics\Index\NetworkDiagnostics_4_NetworkAdapter.xml -context {189519DB-D834-411E-BD2F-69C26B0BA8A5} | C:\Windows\System32\msdt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 474
Read events
2 044
Write events
2 287
Delete events
143
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs\Folder |
| Operation: | delete value | Name: | 0 |
Value: 530079007300740065006D00200061006E0064002000530065006300750072006900740079000000820032000000000000000000000053797374656D20616E642053656375726974792E6C6E6B005C0008000400EFBE00000000000000002A00000000000000000000000000000000000000000000000000530079007300740065006D00200061006E0064002000530065006300750072006900740079002E006C006E006B00000026000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs |
| Operation: | delete value | Name: | 0 |
Value: 530079007300740065006D00200061006E0064002000530065006300750072006900740079000000820032000000000000000000000053797374656D20616E642053656375726974792E6C6E6B005C0008000400EFBE00000000000000002A00000000000000000000000000000000000000000000000000530079007300740065006D00200061006E0064002000530065006300750072006900740079002E006C006E006B00000026000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs |
| Operation: | write | Name: | 0 |
Value: 530079007300740065006D00200061006E0064002000530065006300750072006900740079000000820032000000000000000000000053797374656D20616E642053656375726974792E6C6E6B005C0008000400EFBE00000000000000002A00000000000000000000000000000000000000000000000000530079007300740065006D00200061006E0064002000530065006300750072006900740079002E006C006E006B00000026000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs\Folder |
| Operation: | write | Name: | 0 |
Value: 530079007300740065006D00200061006E0064002000530065006300750072006900740079000000820032000000000000000000000053797374656D20616E642053656375726974792E6C6E6B005C0008000400EFBE00000000000000002A00000000000000000000000000000000000000000000000000530079007300740065006D00200061006E0064002000530065006300750072006900740079002E006C006E006B00000026000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs\Folder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000030000000200000001000000FFFFFFFF | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs |
| Operation: | write | Name: | MRUListEx |
Value: 000000000800000007000000060000000500000004000000030000000200000001000000FFFFFFFF | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0000000001000000020000000A00000007000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\0 |
| Operation: | write | Name: | MRUListEx |
Value: 020000000300000004000000050000000100000000000000FFFFFFFF | |||
Executable files
5
Suspicious files
8
Text files
51
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 372 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\7e4dca80246863e3.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 3224 | msdt.exe | C:\Windows\TEMP\SDIAG_9e5530fb-51fb-4af7-83df-3a621a73a6df\AudioDiagnosticSnapIn.dll | executable | |
MD5:CEC3219ADB6EFE764885FE9E449F413C | SHA256:6395338F3128C64FAA1817C38D8800C914139C9A9B4D04FB6E9B64D072012FD5 | |||
| 3224 | msdt.exe | C:\Windows\TEMP\SDIAG_9e5530fb-51fb-4af7-83df-3a621a73a6df\DiagPackage.diagpkg | xml | |
MD5:03A8CE31B72A2DB80676ABB7346720D1 | SHA256:4647F7EEE5C5605295719DE89C6ECCE4CCF56690372B97253090530F45779028 | |||
| 3224 | msdt.exe | C:\Windows\TEMP\SDIAG_9e5530fb-51fb-4af7-83df-3a621a73a6df\CL_RunDiagnosticScript.ps1 | text | |
MD5:46FE69F4CA3FAF3E393A0A8426EE1BC8 | SHA256:4025BECB8CA4749E812722A31CA1089FBD0895E55333C05E19756EE0B9BE7DEB | |||
| 3224 | msdt.exe | C:\Windows\TEMP\SDIAG_9e5530fb-51fb-4af7-83df-3a621a73a6df\CL_LoadAssembly.ps1 | text | |
MD5:60664405B4987C371003FD83B745BFB7 | SHA256:8271203C21B325746A5A439D733EFD3ADE8C326092337643293BFBA9750C534E | |||
| 3224 | msdt.exe | C:\Windows\TEMP\SDIAG_9e5530fb-51fb-4af7-83df-3a621a73a6df\DiagPackage.dll | executable | |
MD5:CEAE1097384BB922DF649EF5EF8BD356 | SHA256:6B0326997835FF43B32C31BF3D61DCC4CA41A505E7A15B40EB218F0820D0188A | |||
| 3224 | msdt.exe | C:\Windows\TEMP\SDIAG_9e5530fb-51fb-4af7-83df-3a621a73a6df\result\results.xsl | — | |
MD5:— | SHA256:— | |||
| 3224 | msdt.exe | C:\Windows\TEMP\SDIAG_9e5530fb-51fb-4af7-83df-3a621a73a6df\CL_RegSnapin.ps1 | text | |
MD5:4B653C3126F5E3AE7C75BBCFCCFABFE3 | SHA256:980AB436E3DB22AB1EFD665147E6B1165A892DD75DBAD26FDEEE6C76D1D9EA8D | |||
| 3224 | msdt.exe | C:\Windows\TEMP\SDIAG_9e5530fb-51fb-4af7-83df-3a621a73a6df\CL_Invocation.ps1 | text | |
MD5:84CBFA6929EDFD657192244615E6E614 | SHA256:18DC8E1D82DA96068148C42DCCDBFDBB8C58590A6E28E9FB4D7F7B1AB664F5B4 | |||
| 3224 | msdt.exe | C:\Windows\TEMP\SDIAG_9e5530fb-51fb-4af7-83df-3a621a73a6df\MF_AudioDiagnostic.ps1 | text | |
MD5:A3FE5EC679E4A822C0612D7BFE8DCFF2 | SHA256:F83665873B0A9C5A4491F9C837E008062BBDFACFFA6BBEF63087DE5E19F8AEA4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report