| URL: | https://www.acethinker.com/support/download-video-keeper-pro?pro=aquaclip&url=https%3A%2F%2Fwww.acethinker.com%2Fonline-downloader-1 |
| Full analysis: | https://app.any.run/tasks/7353fa3b-8a0e-4005-a591-3067199d17f9 |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2023, 20:04:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0299DA6DEA03E8571E8251241FEE3BB1 |
| SHA1: | CD871FA465034C852CFE2EFD783802BB2FE23C22 |
| SHA256: | 3C5A795BD65CC7B371F99B48F2BE533AA57EAC7CE7EB45BF15F56861D3BBE9CD |
| SSDEEP: | 3:N8DSLYrVAbdnViK8SATM44XjXDyEeM+XWNRRVHWCXjGArVAbdk9M08yXp:2OLYrqpVikK47DyRM+XKRR3zXrqpk9gC |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2076)
Reads the computer name
- wmpnscfg.exe (PID: 3636)
Checks supported languages
- wmpnscfg.exe (PID: 3636)
Manual execution by a user
- wmpnscfg.exe (PID: 3636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
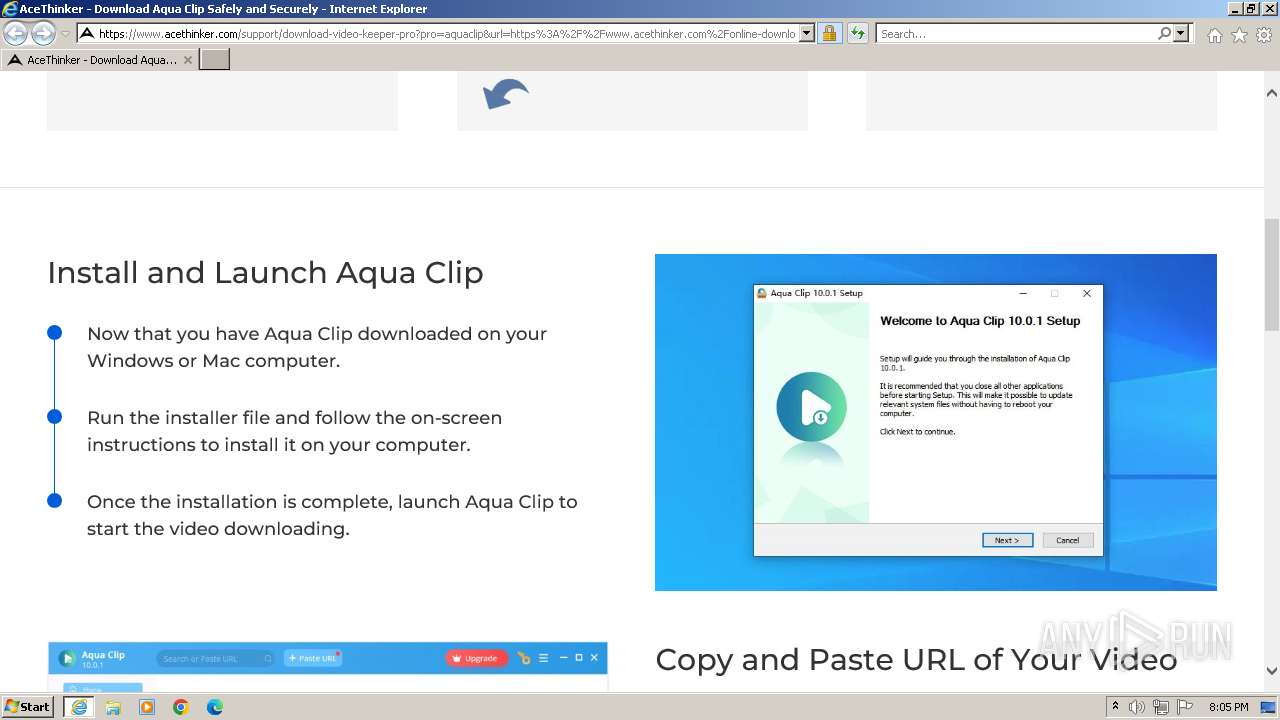
| 2076 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.acethinker.com/support/download-video-keeper-pro?pro=aquaclip&url=https%3A%2F%2Fwww.acethinker.com%2Fonline-downloader-1" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2076 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3636 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
18 470
Read events
18 402
Write events
66
Delete events
2
Modification events
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
40
Text files
44
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download-video-keeper-pro[1].htm | html | |
MD5:E946814CFBB98D60F4261811DE9AF533 | SHA256:0474E62193BBFB32C9A0F3E9A5BB4B347B11747DB6655DB138B85242746E094D | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:6E98820D0144AE35D248A3A135D82B8F | SHA256:F304DA87AA952781EADDAD69949C28D6F87CF883F6F146ECAD88AC16263B6763 | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:A3B69DD0A789BBF32085771EF5071D21 | SHA256:E0CA3C190D58FFA8CCFA444DA04BDF21AB40AFD2143005F78AF90C9C6E7CF224 | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:4A4AAEE301787BAB0CC1F829FE28D081 | SHA256:6D57F45B4B17DA01F1DAEA867C3CC13975D3ED0C01A6E6C3A2C7B3A18E0BEE80 | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\firefox[1].jpg | image | |
MD5:4AD925919709B8CE09028136CA00D986 | SHA256:4FE9EF91C932DE989EDD644445B4F3277D605133040C8D23FFCECDCE4593049A | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\chorm-google[1].jpg | image | |
MD5:689CF66FFE300AE1F57270B348466F1D | SHA256:CC00DB75A931D1437097AA8C18BA026B74ECDD19AB72060914505C02F10C4C9C | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\bootstrap.min[1].css | text | |
MD5:E2E108E84140F4BD35D1F5DB9F9094E7 | SHA256:ABB2F53AA1E48F2F1713C393C37A817A75AC310D0556159C2783E5281BE1C617 | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:9893918188D52D9DB9C70BBB543887A0 | SHA256:726C1438E9613A213596C4985BC076678182891B1506B93A65E679F1CB09A07F | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\icon-acepdf-60[1].png | image | |
MD5:F671524850A694530AD73AFC25E7C174 | SHA256:A20B72AD24D604FE480710409FBC635EBEA20D8EC94A86BFF55546032180264E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
39
DNS requests
24
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2184 | iexplore.exe | GET | 200 | 193.108.153.18:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b27ea2cbe4dcc735 | DE | compressed | 4.66 Kb | unknown |
2184 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
2184 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | binary | 1.47 Kb | unknown |
2184 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
2184 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDmzKJl66ZMrRKtZxoAGQQd | US | binary | 472 b | unknown |
2184 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCVN9Jf3G%2B1pAqd7QzTt1vx | US | binary | 472 b | unknown |
2184 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCVN9Jf3G%2B1pAqd7QzTt1vx | US | binary | 472 b | unknown |
2184 | iexplore.exe | GET | 200 | 23.56.202.135:80 | http://x1.c.lencr.org/ | GB | binary | 717 b | unknown |
2184 | iexplore.exe | GET | 200 | 184.24.77.72:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgN1cMLkoYgKaGUssnG5uL4xWg%3D%3D | DE | binary | 503 b | unknown |
2184 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | binary | 1.42 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2184 | iexplore.exe | 104.26.11.14:443 | www.acethinker.com | CLOUDFLARENET | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2184 | iexplore.exe | 193.108.153.18:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2184 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2184 | iexplore.exe | 142.250.186.74:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2184 | iexplore.exe | 172.217.16.195:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
2184 | iexplore.exe | 172.67.68.62:443 | aquapp.net | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.acethinker.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
aquapp.net |
| unknown |
ocsp.pki.goog |
| whitelisted |
limeerror.org |
| malicious |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (limeerror .org) |
2184 | iexplore.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in TLS SNI (limeerror .org) |
2184 | iexplore.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in TLS SNI (limeerror .org) |
1080 | svchost.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (sermon .pastorbriantubbs .com) |
2184 | iexplore.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in TLS SNI (sermon .pastorbriantubbs .com) |
2184 | iexplore.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2184 | iexplore.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in TLS SNI (sermon .pastorbriantubbs .com) |
2184 | iexplore.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |