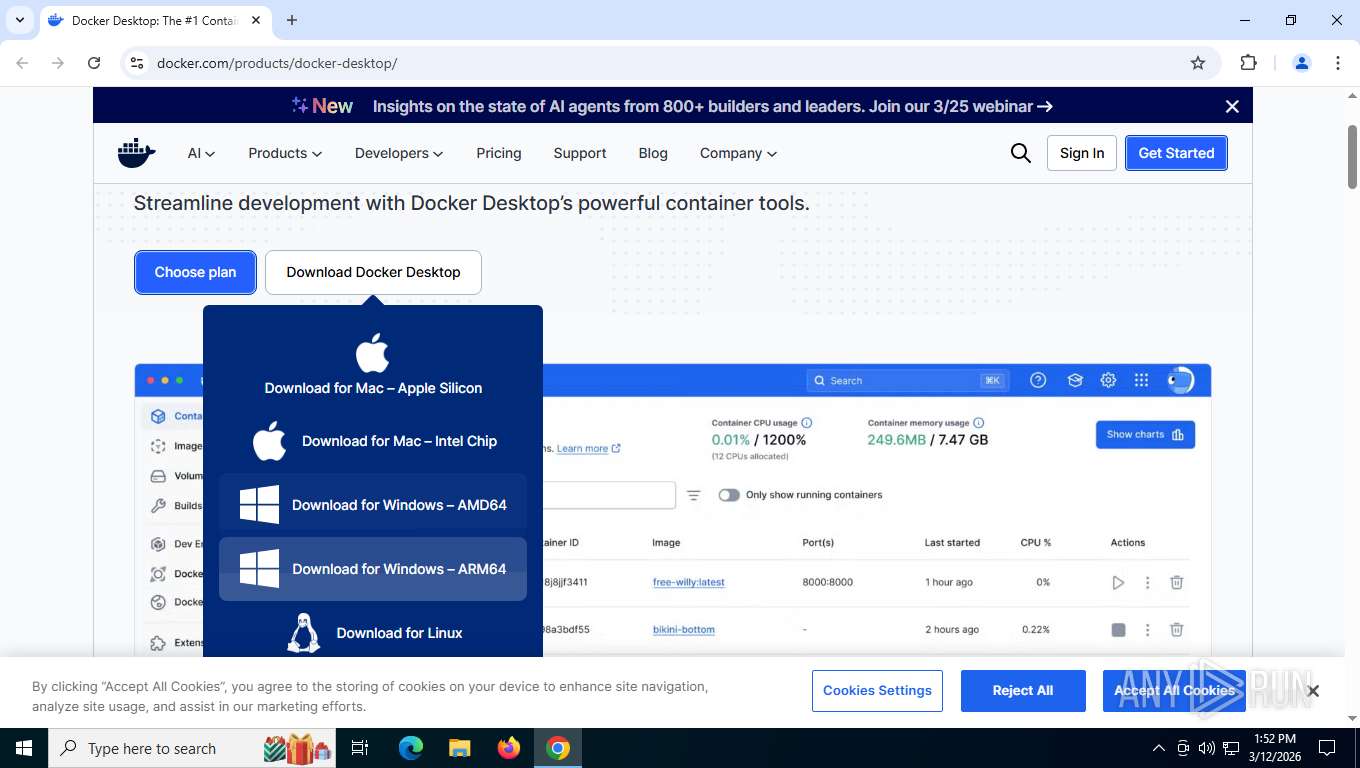
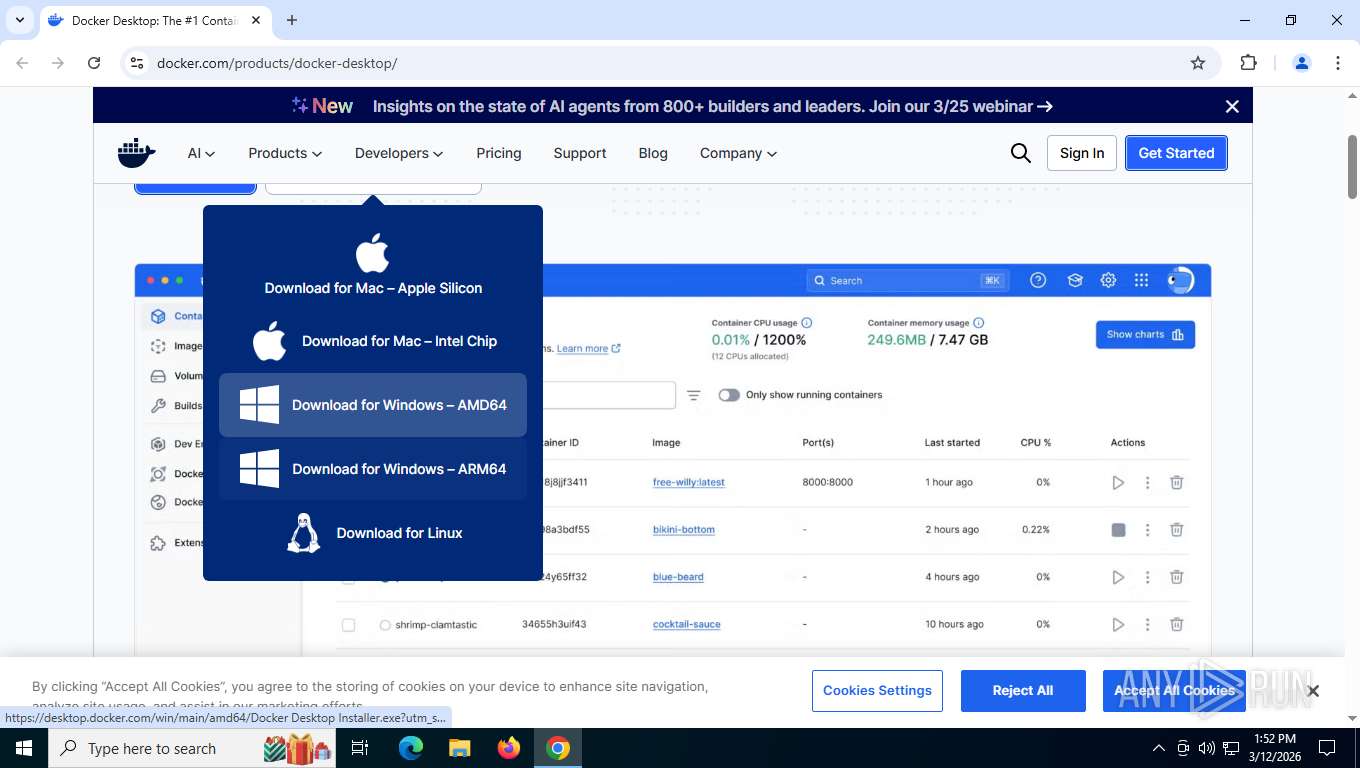
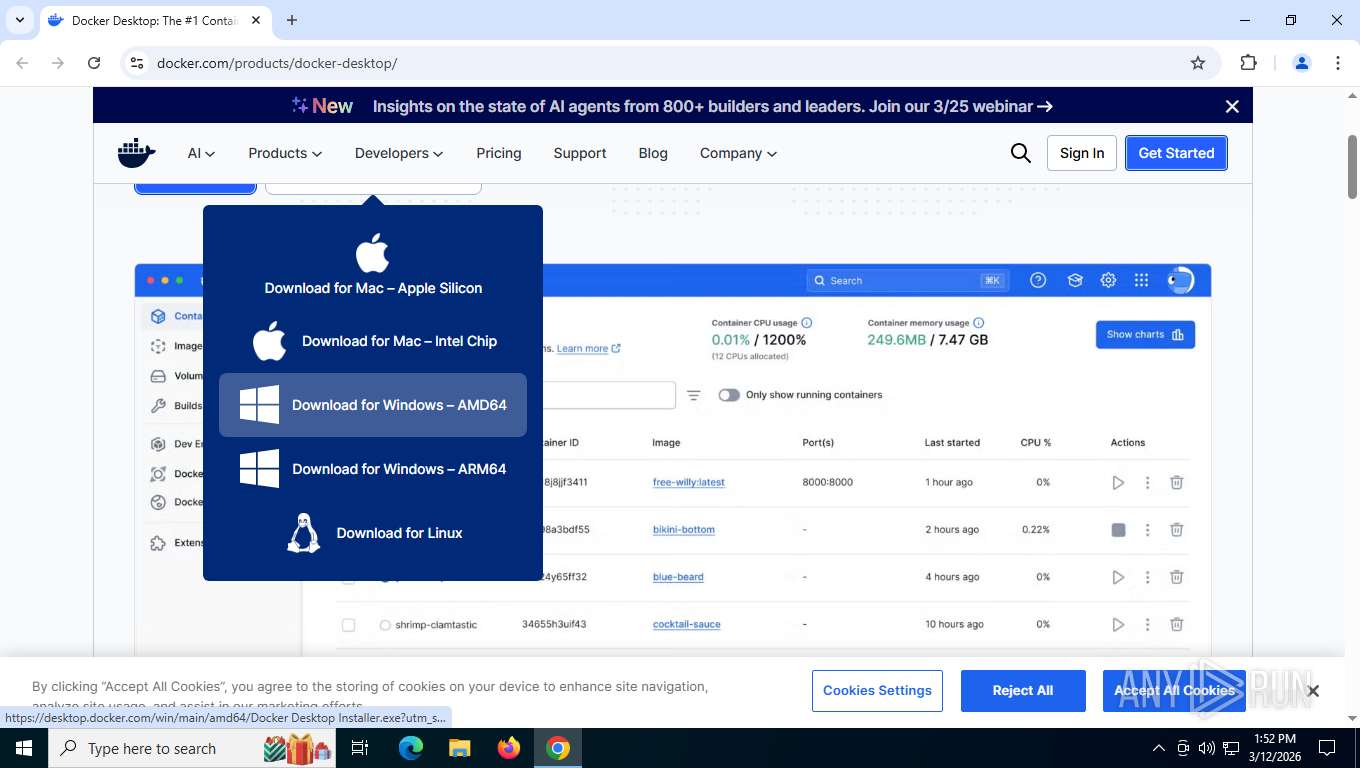
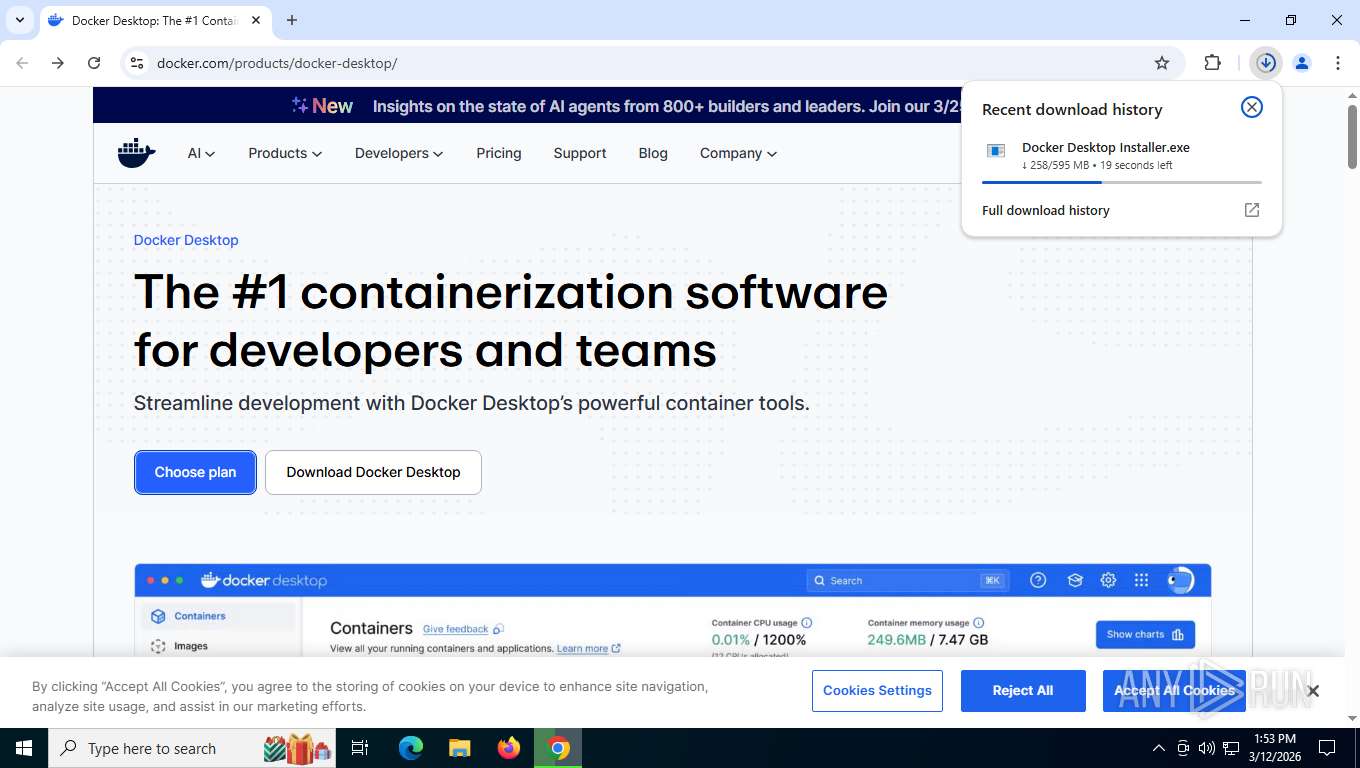
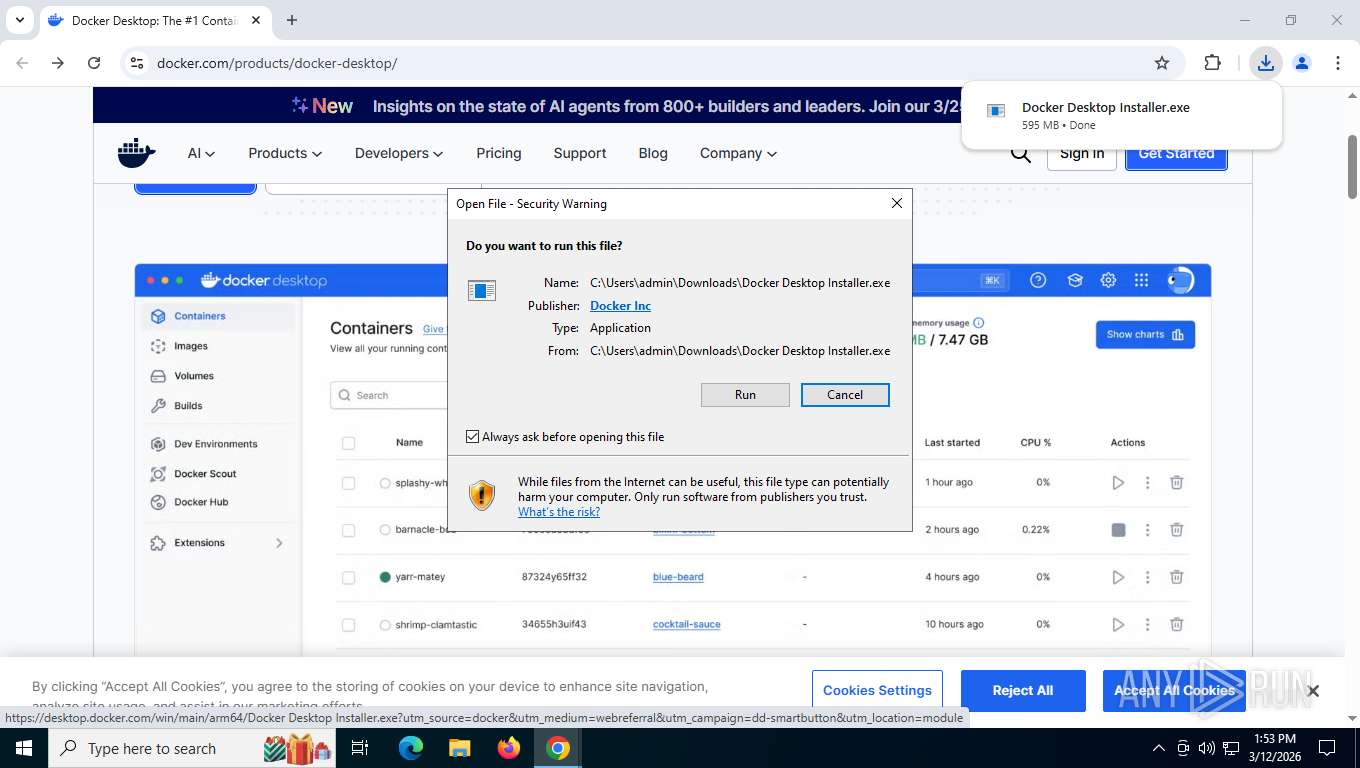
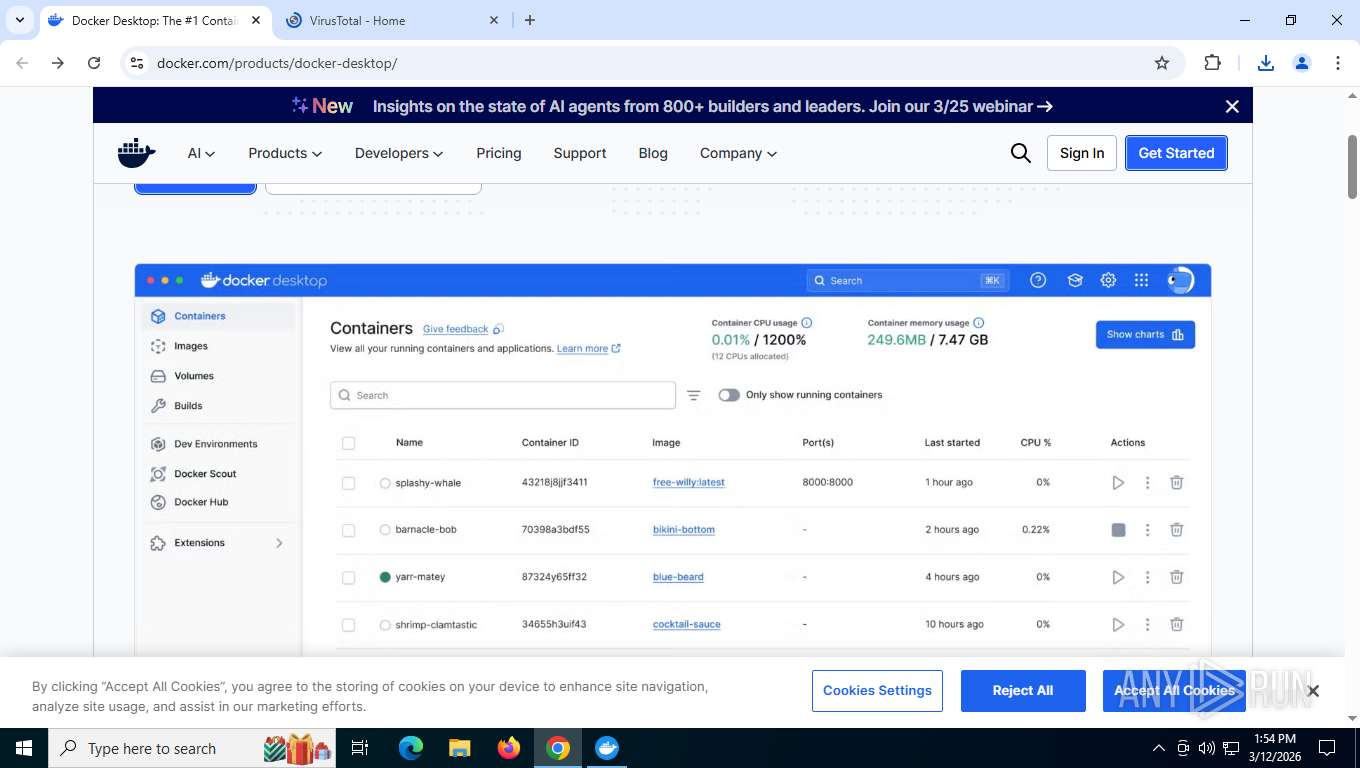
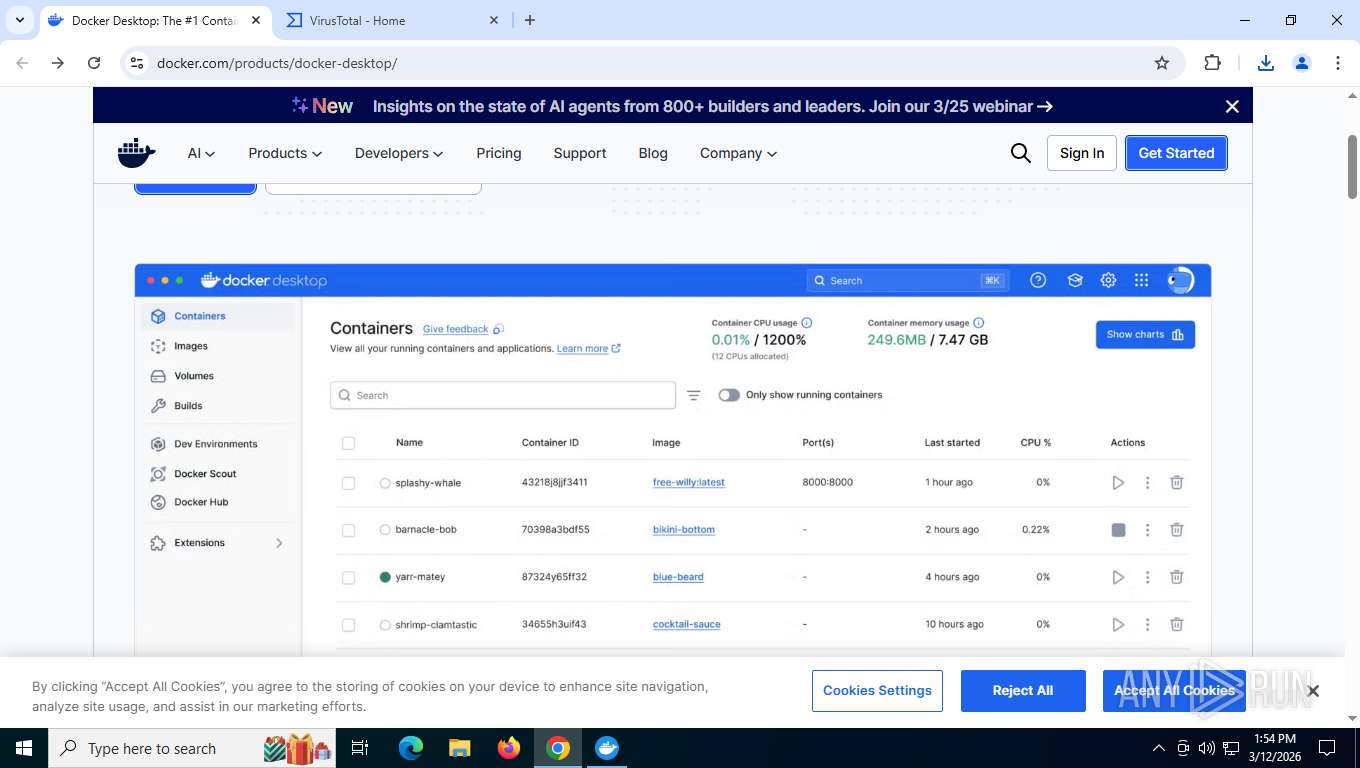
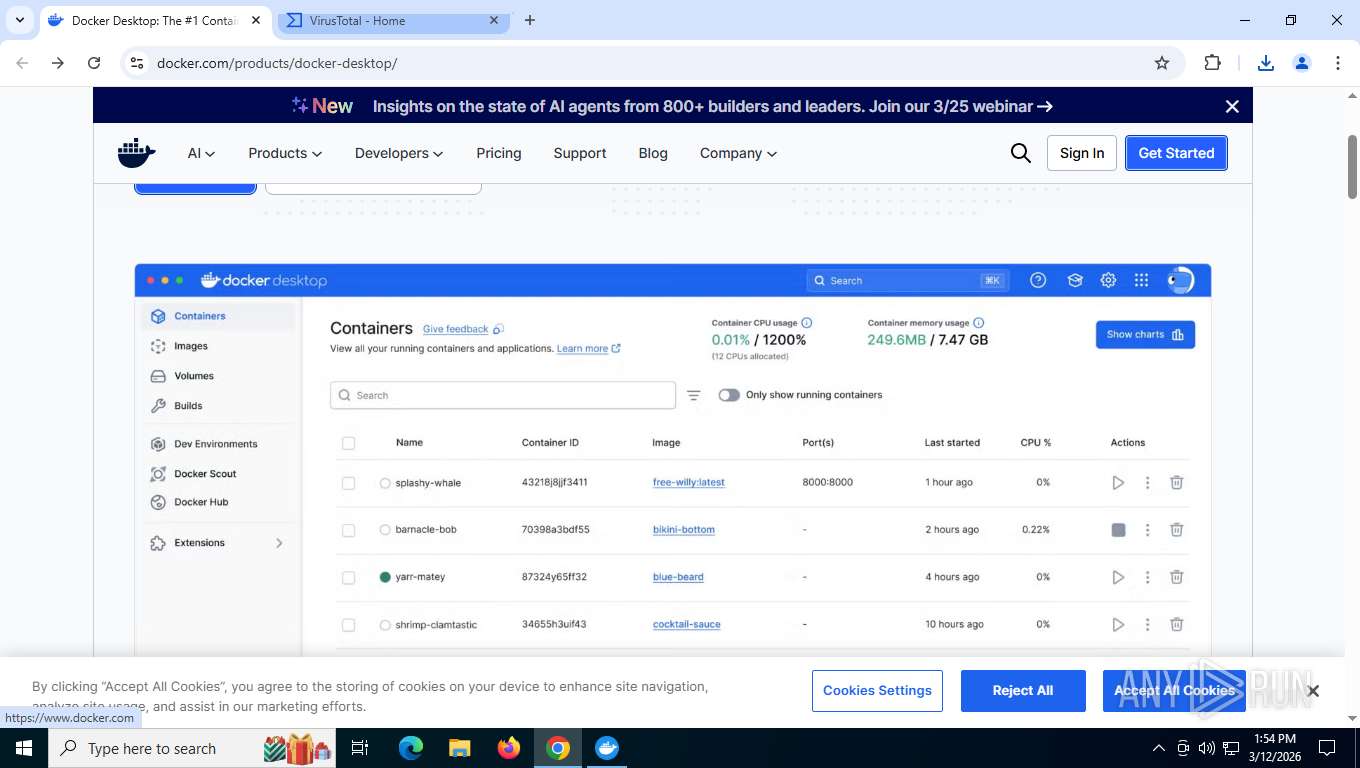
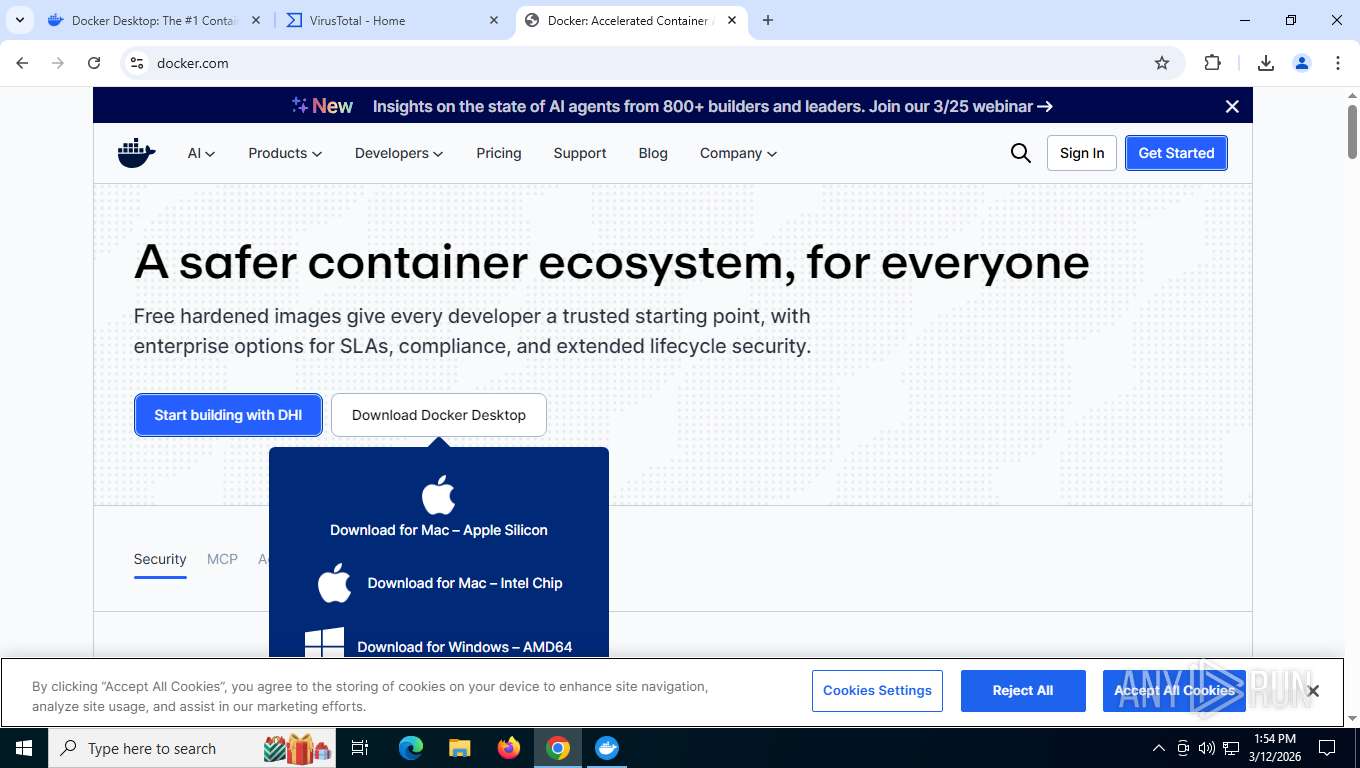
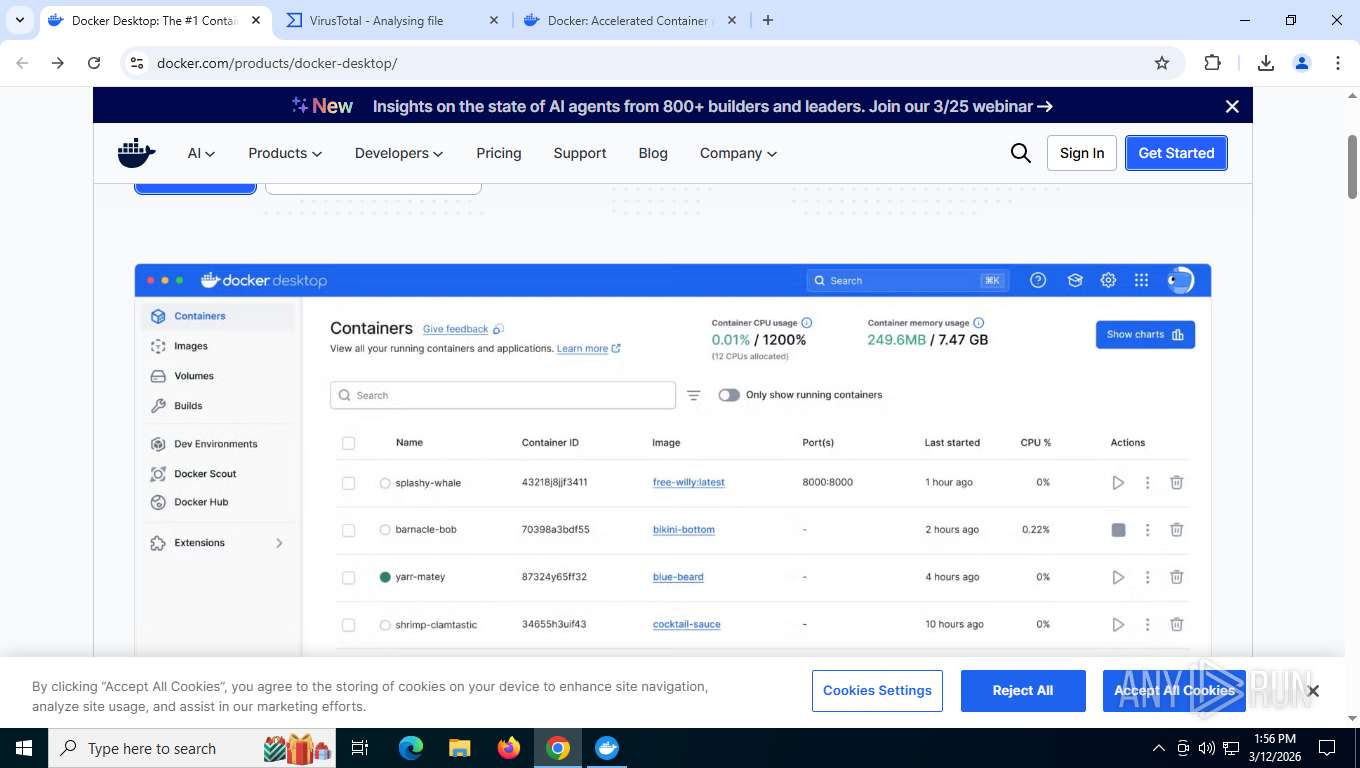
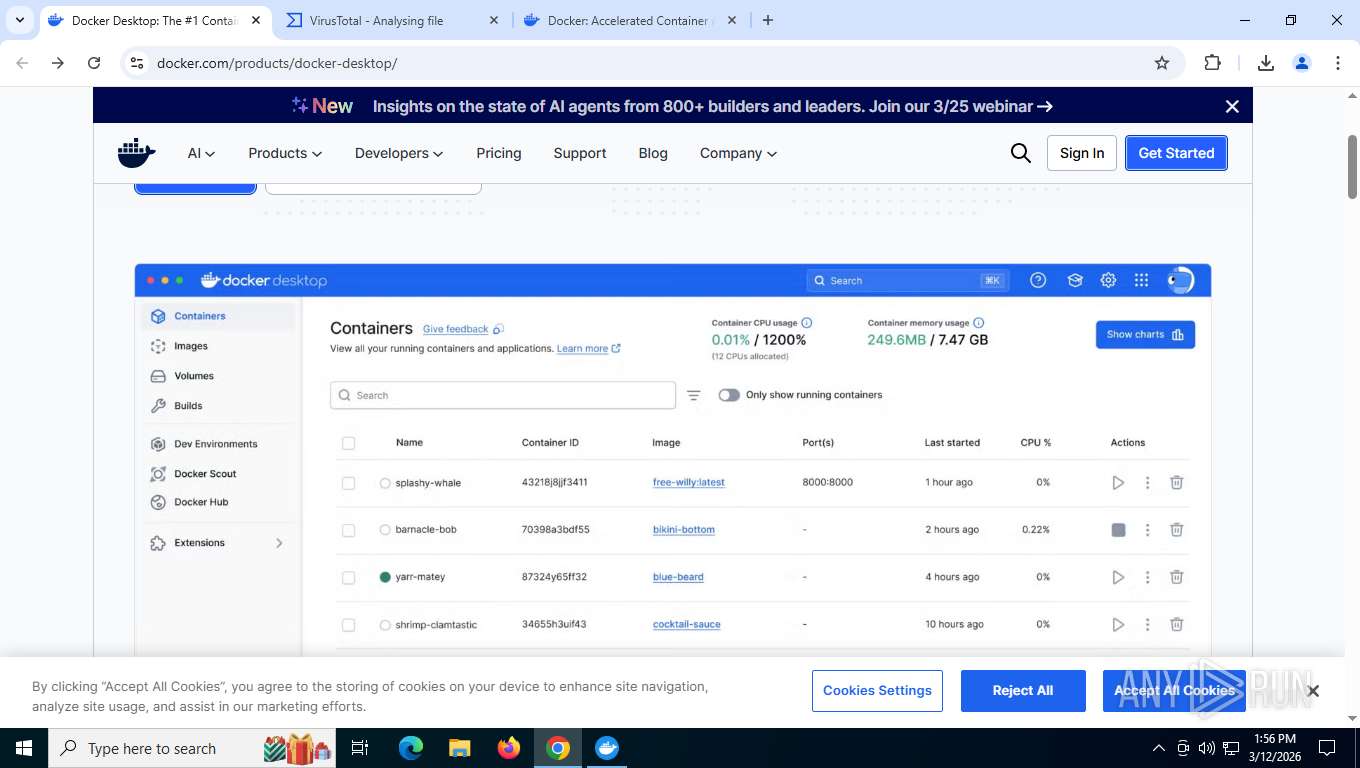
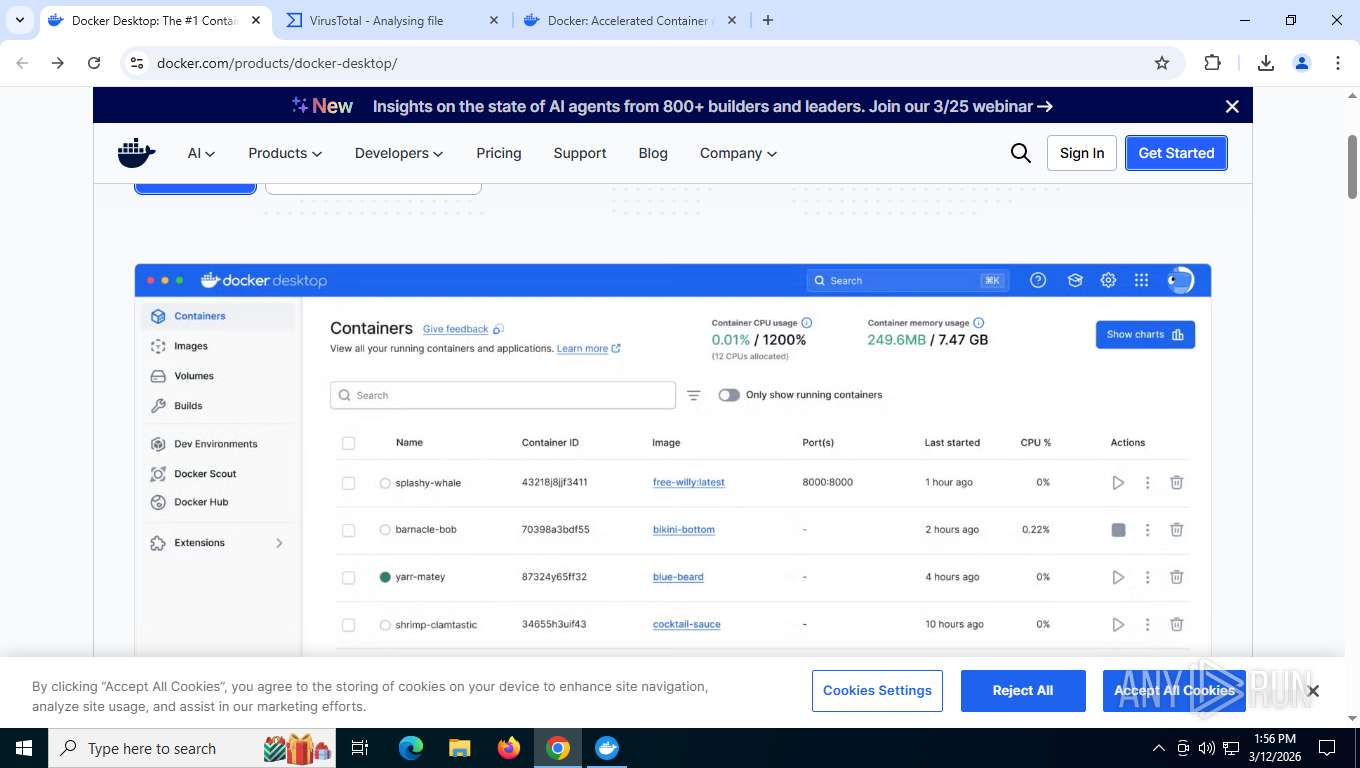
| URL: | https://www.docker.com/products/docker-desktop/ |
| Full analysis: | https://app.any.run/tasks/a2d805f1-cf8a-40d2-86bc-f36908366ba0 |
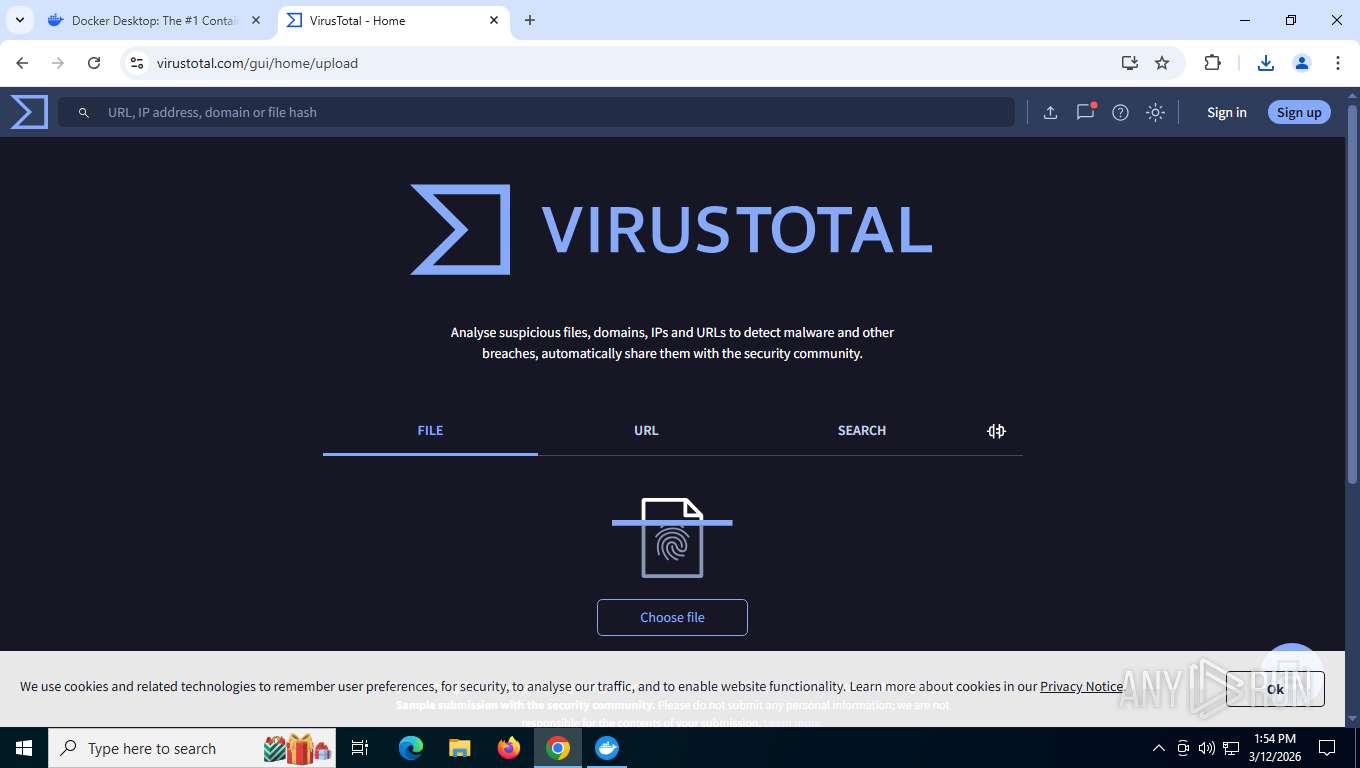
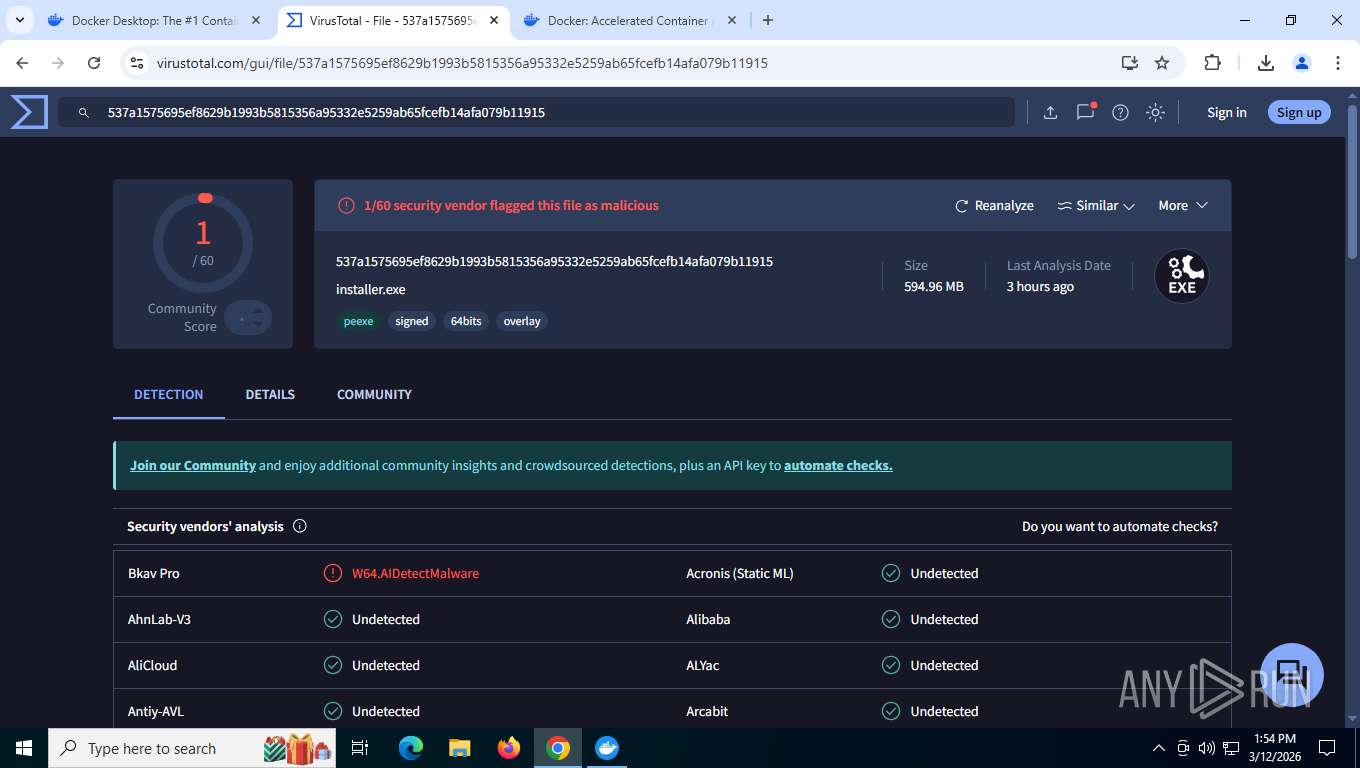
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2026, 17:52:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
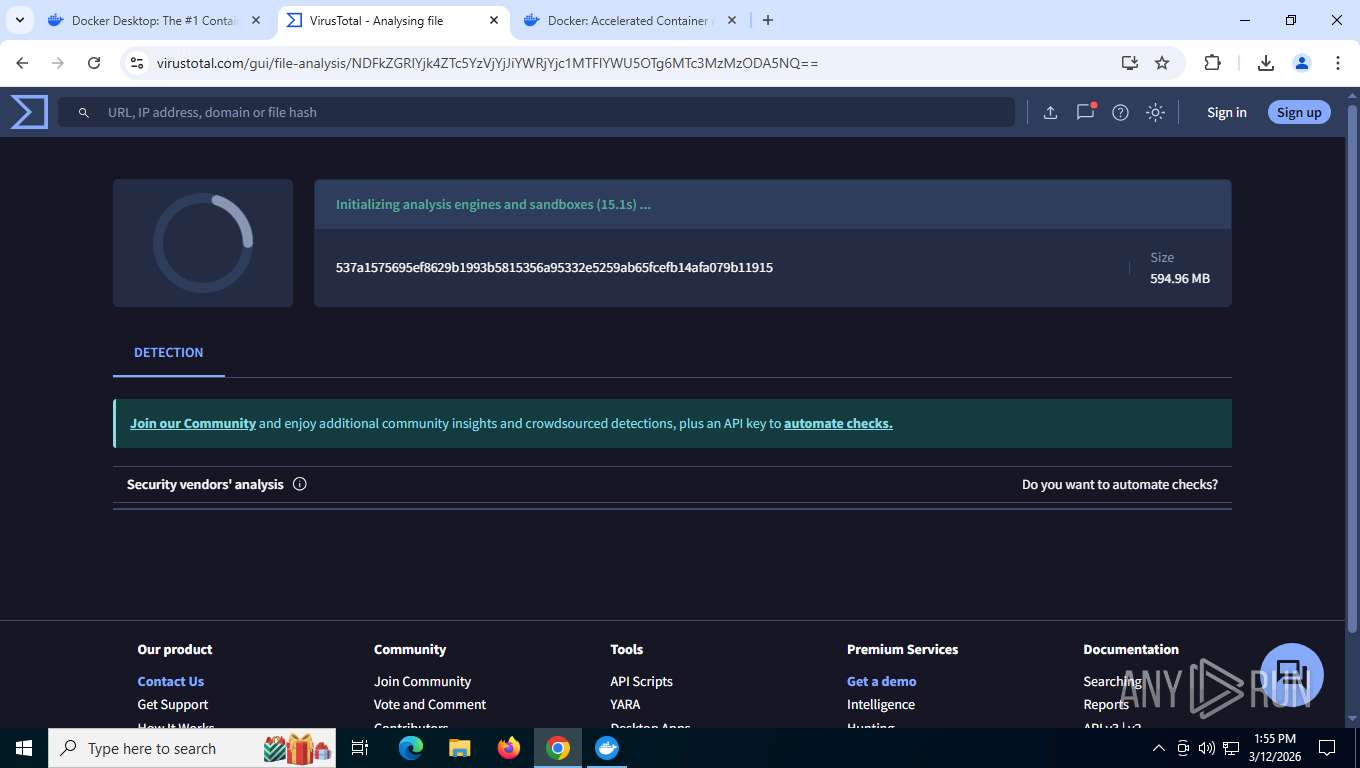
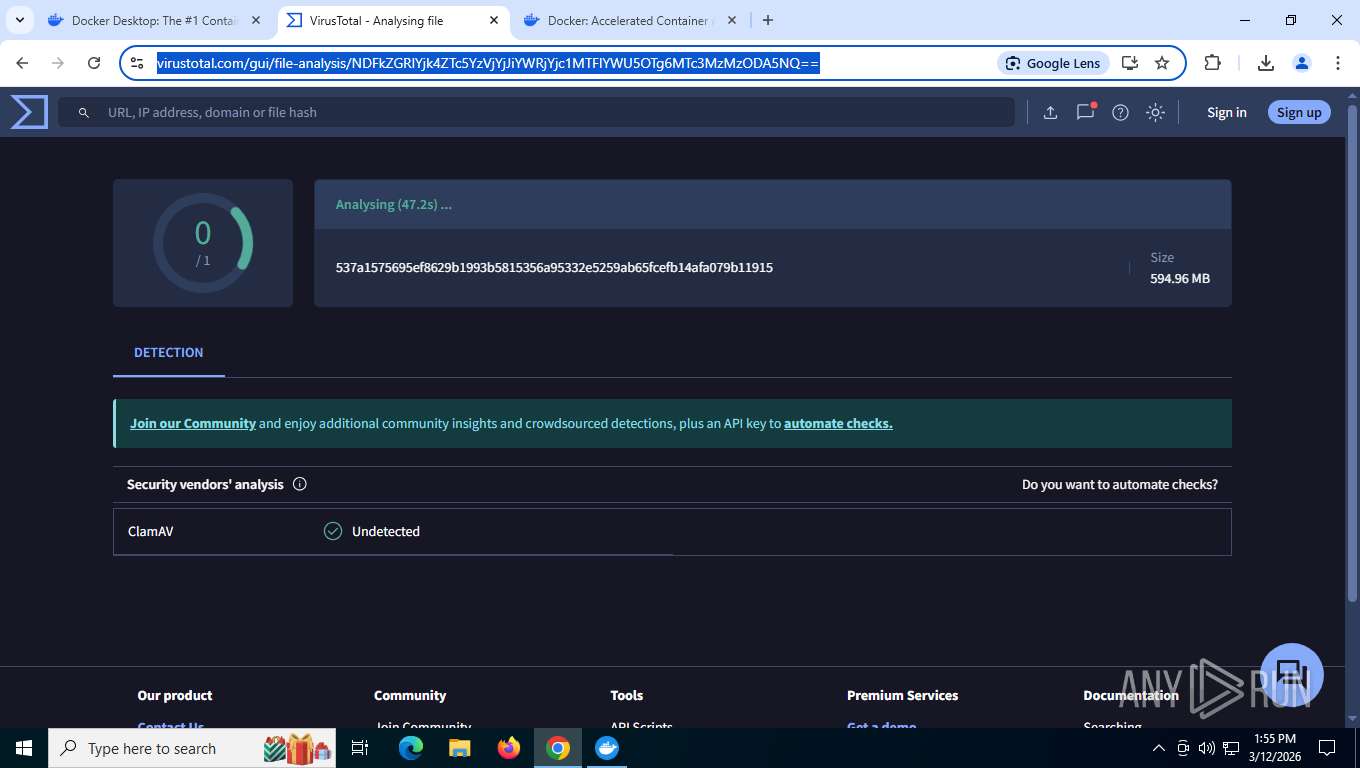
| MD5: | 75416DE75D00099B17A2127DAF850906 |
| SHA1: | E9C696BDBDCF94B72BF3BF0AACFF40F91D75D686 |
| SHA256: | 3C4E7B07F06E31433BB9C9326C14742105C41BE818AB06E7ED89C98145B1E718 |
| SSDEEP: | 3:N8DSL/aQGRWaK2ROKn:2OLKRWB2OK |
MALICIOUS
No malicious indicators.SUSPICIOUS
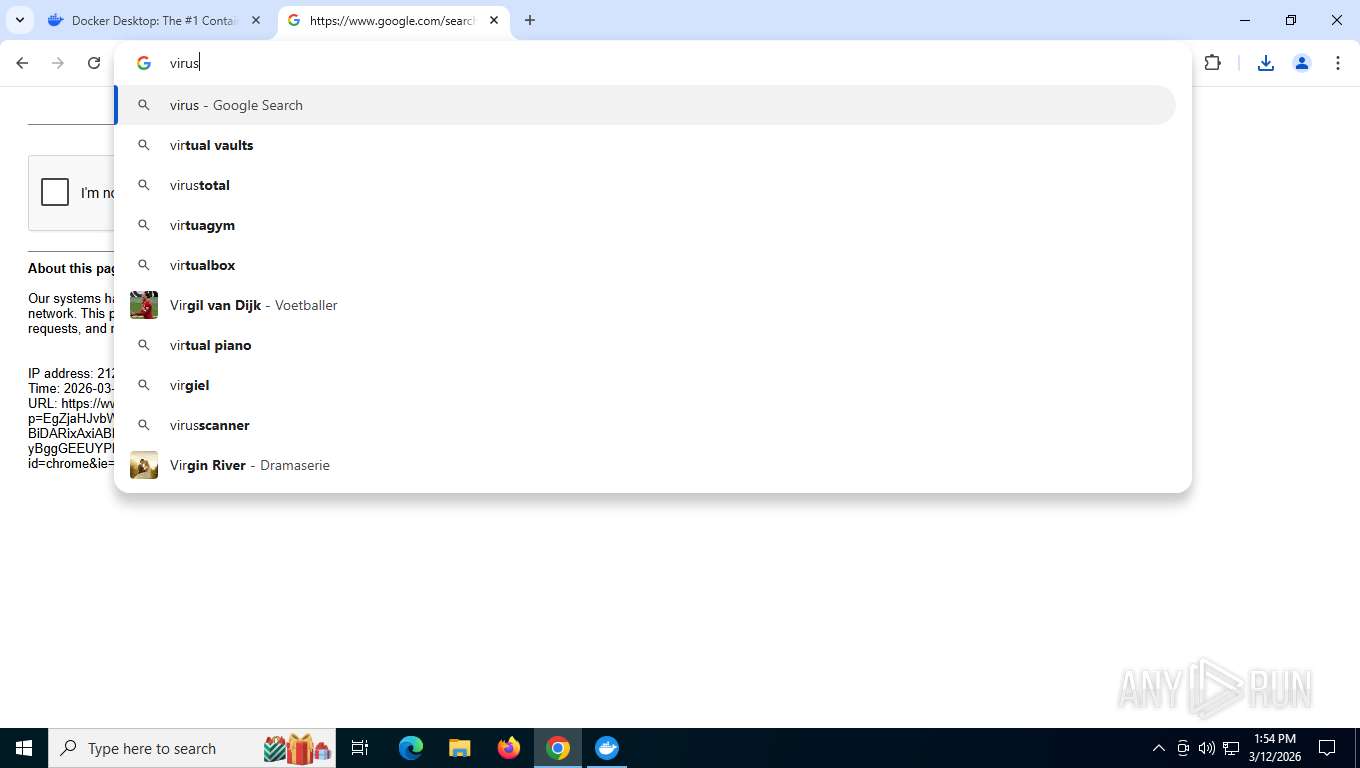
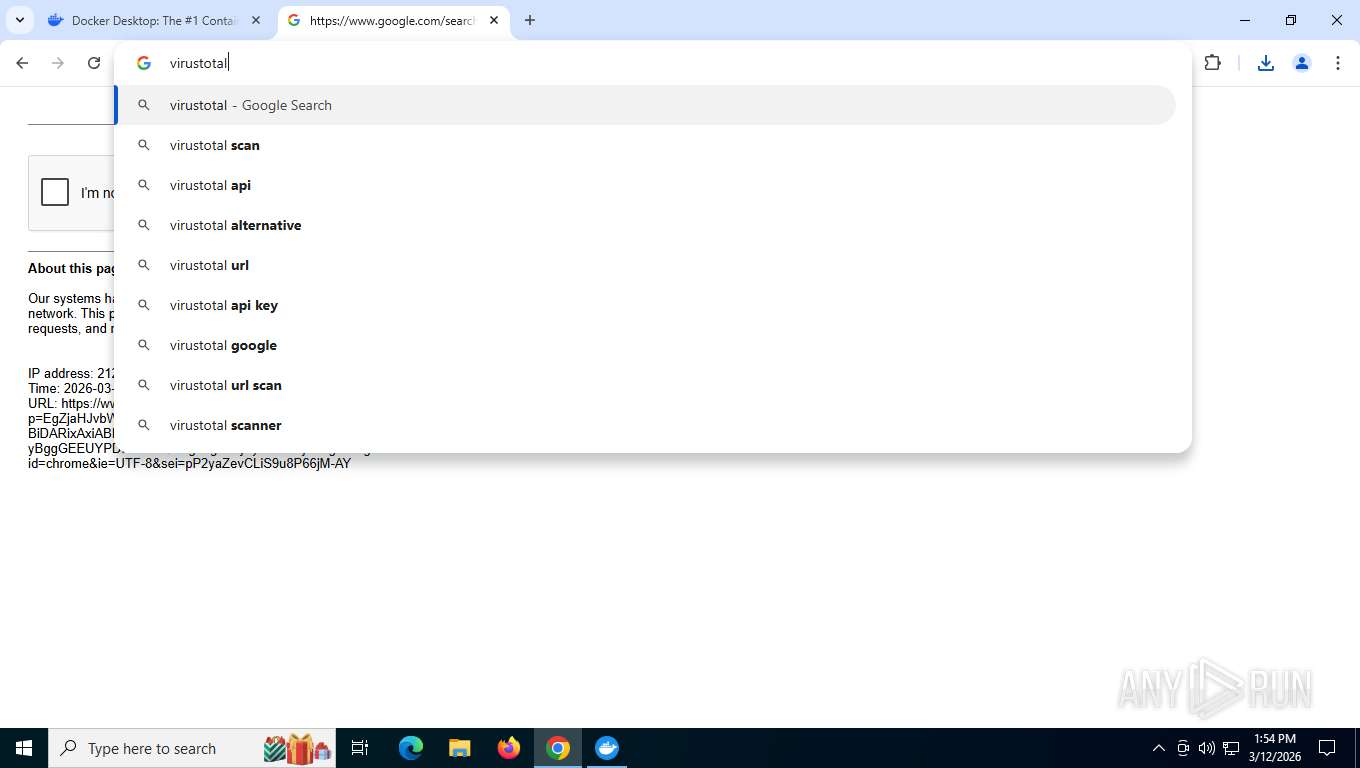
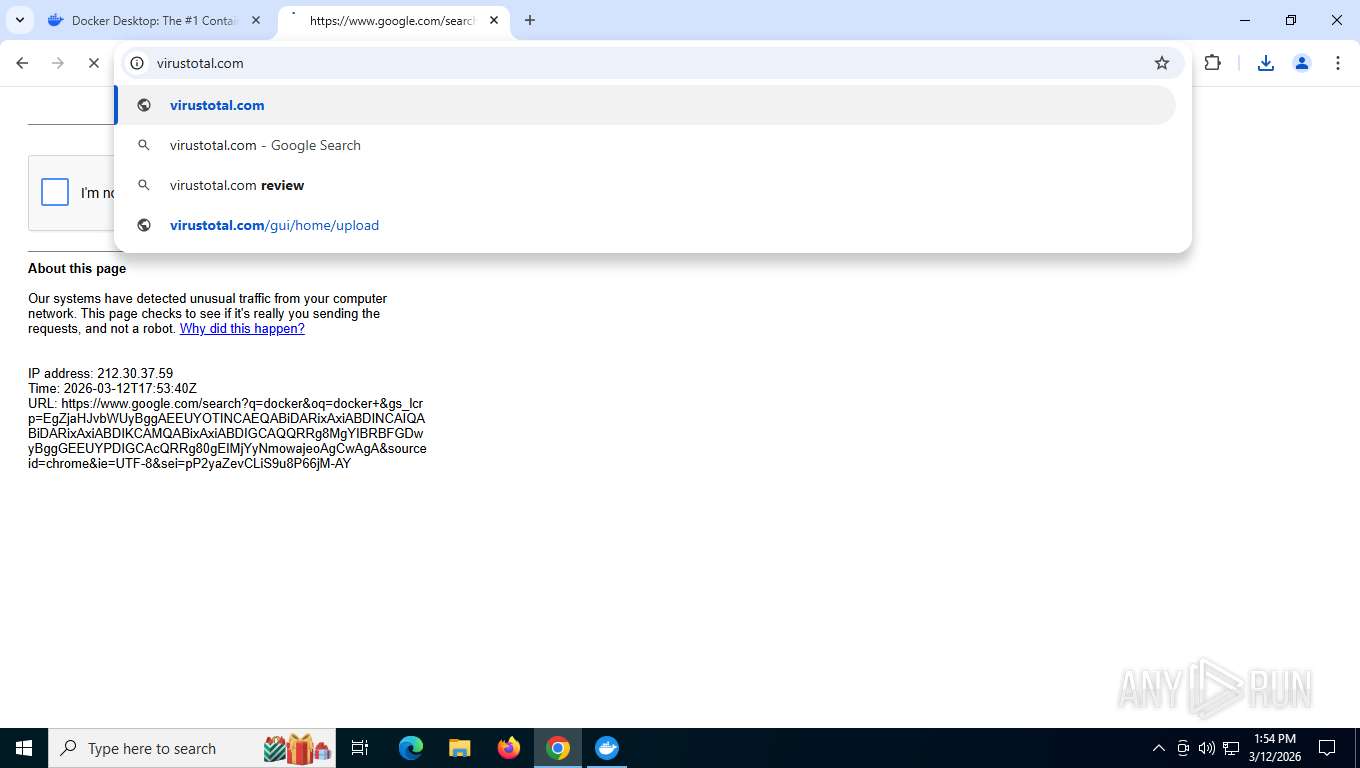
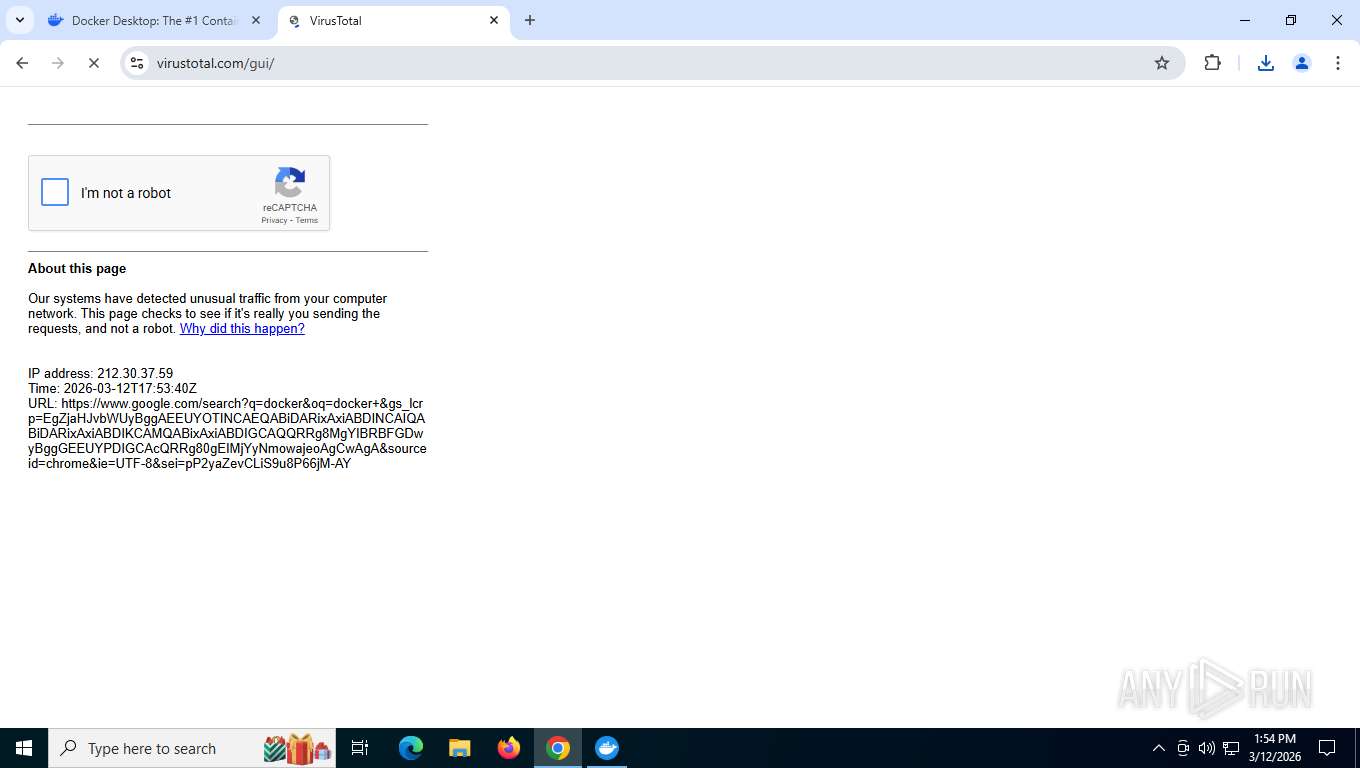
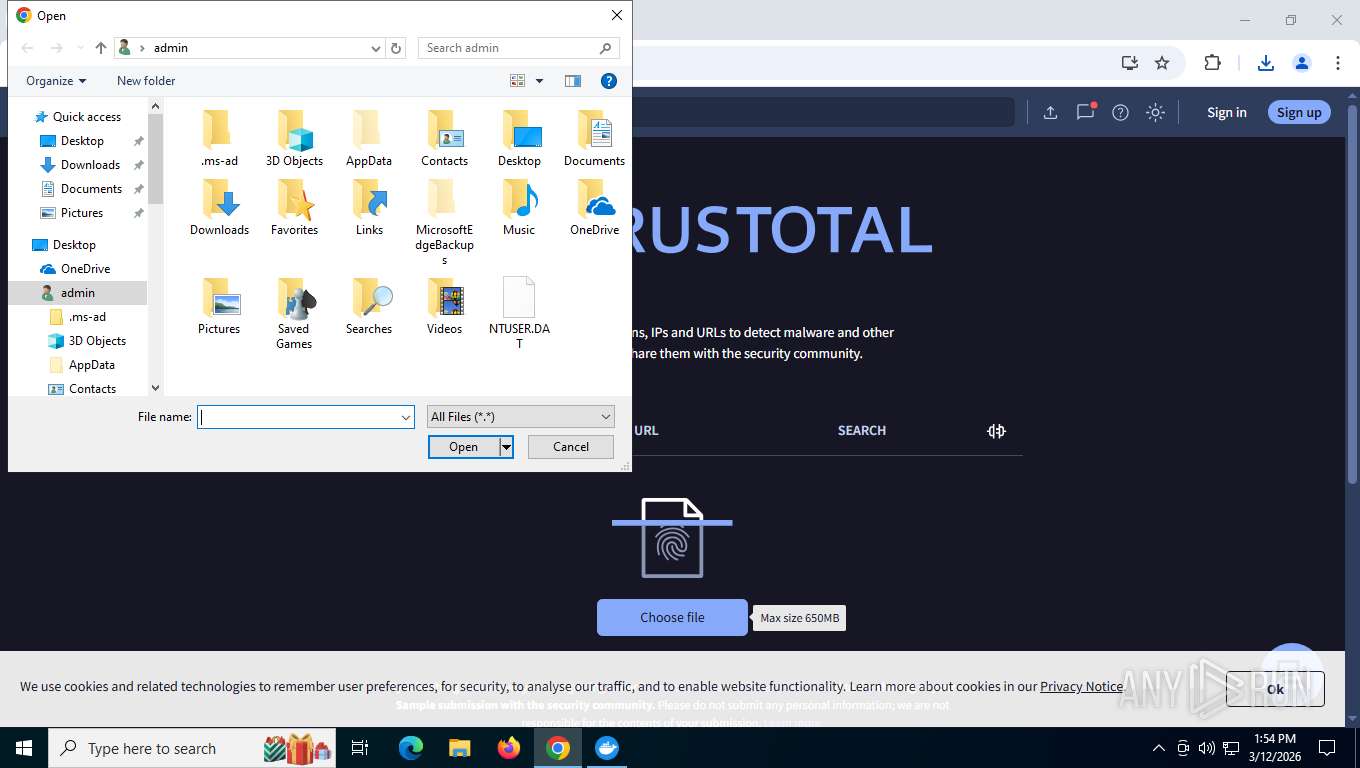
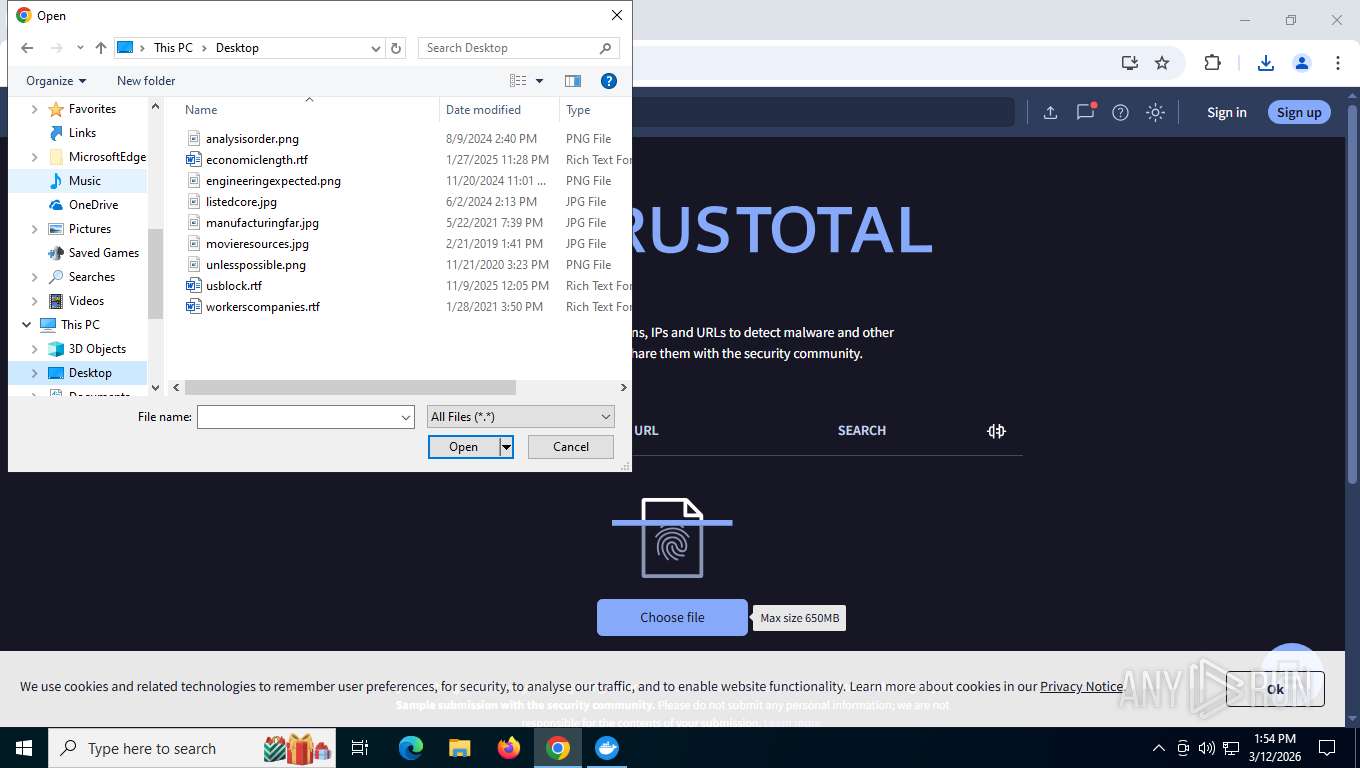
Potential Corporate Privacy Violation
- chrome.exe (PID: 8168)
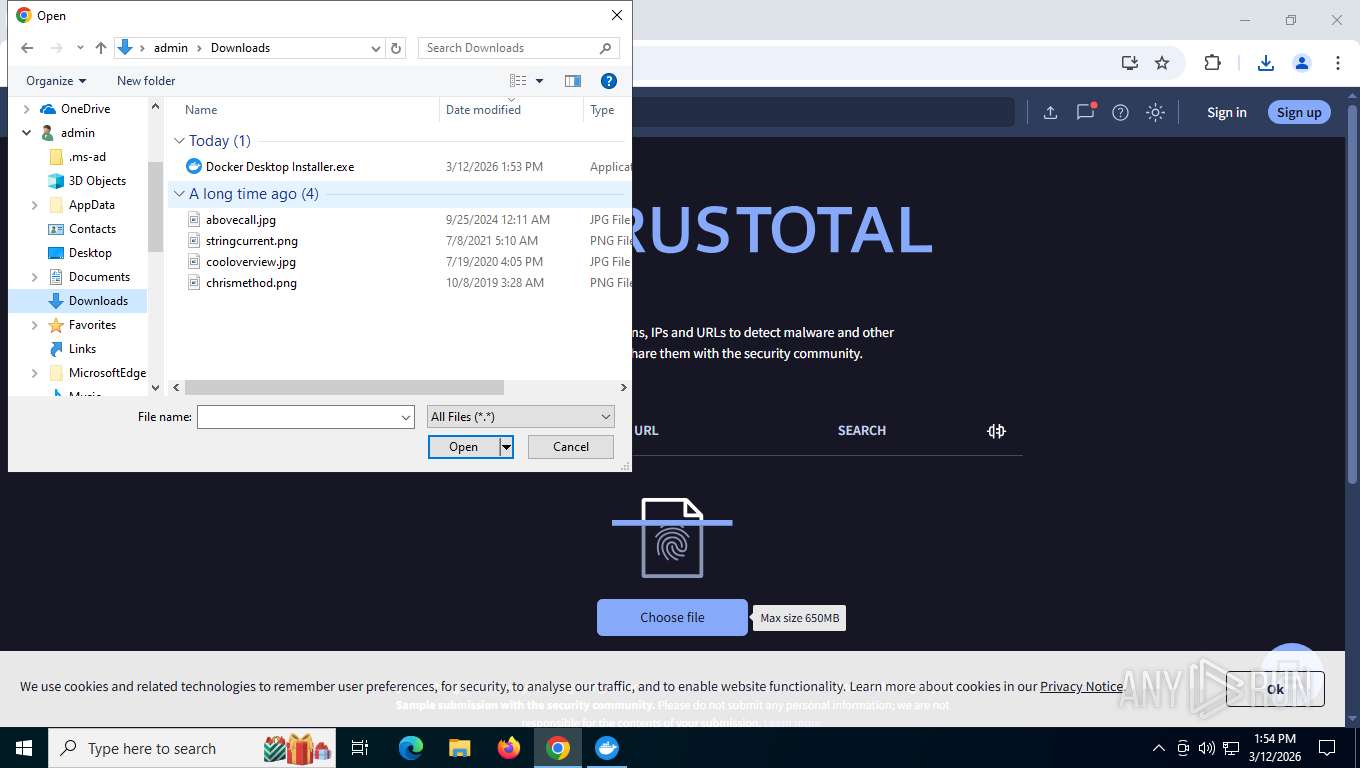
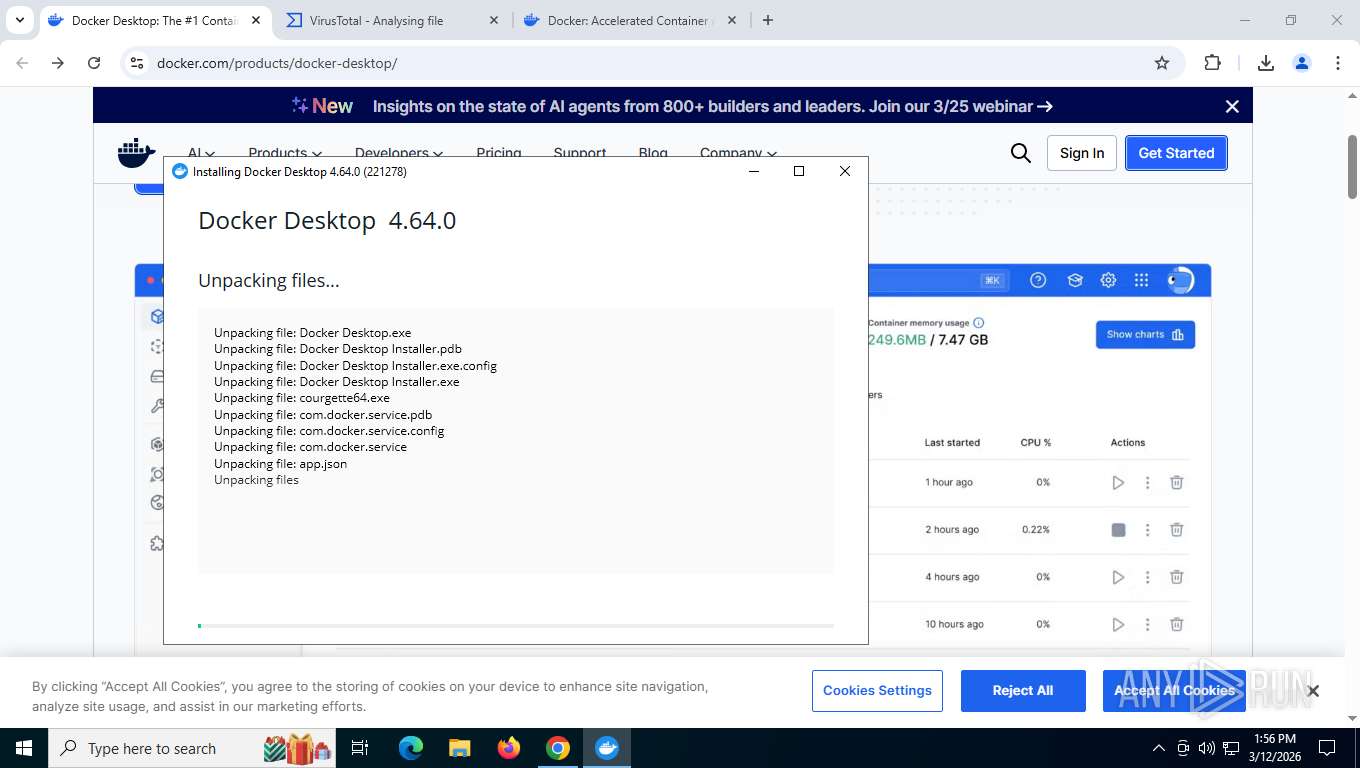
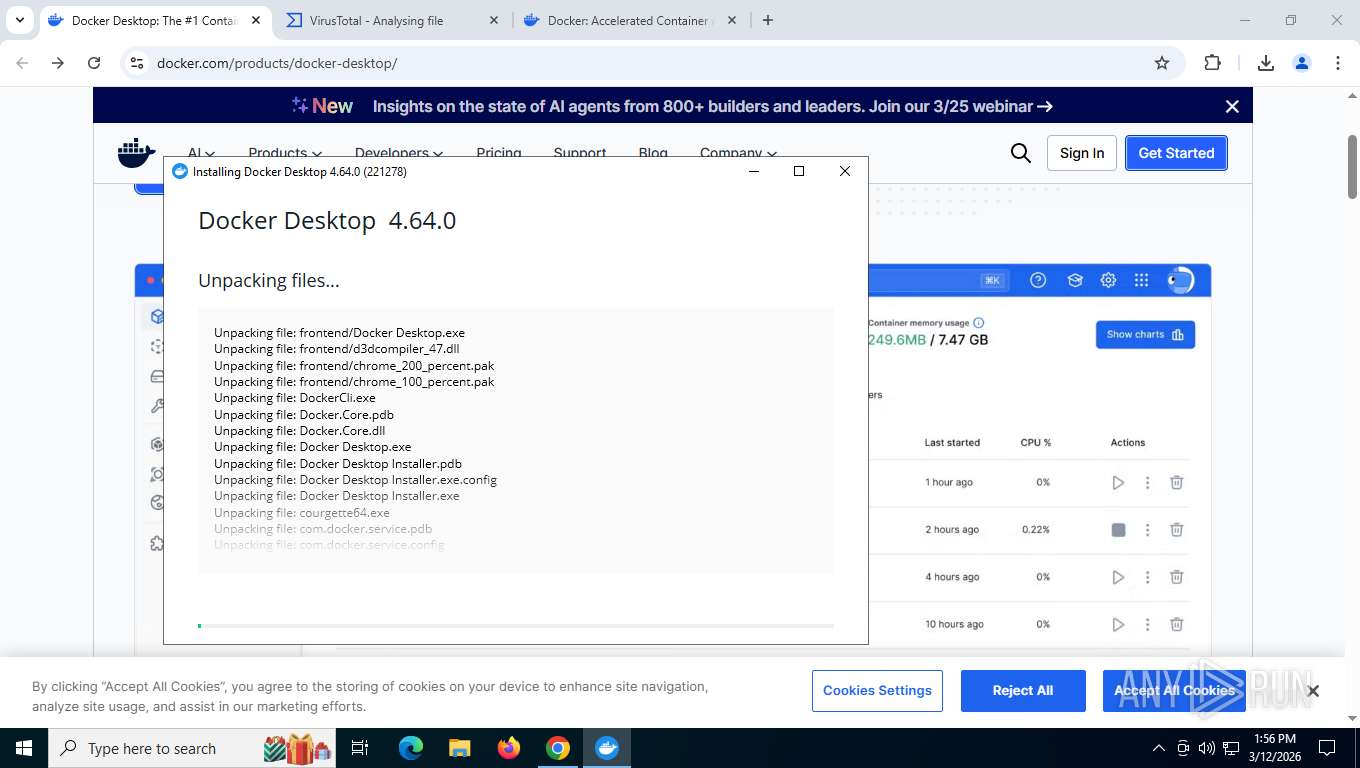
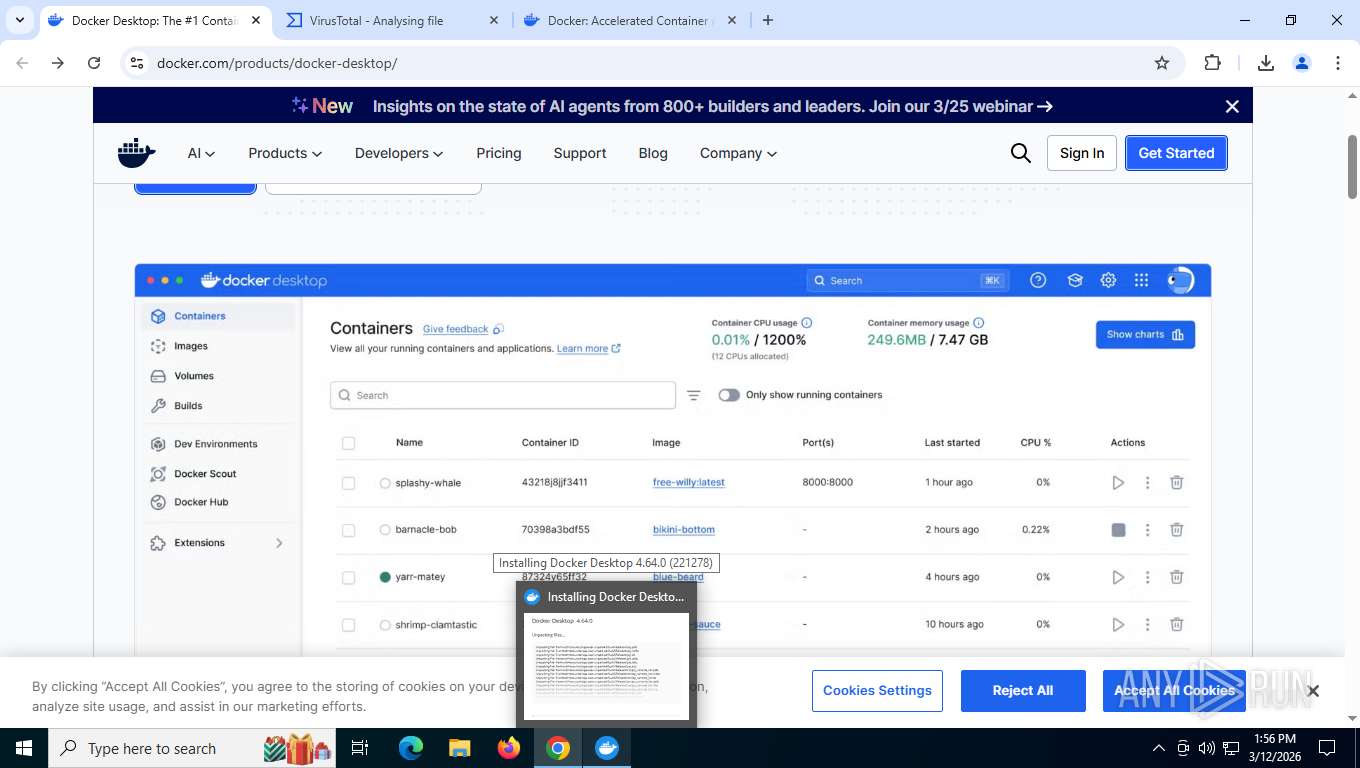
Executable content was dropped or overwritten
- Docker Desktop Installer.exe (PID: 4024)
- Docker Desktop Installer.exe (PID: 1824)
Reads the date of Windows installation
- Docker Desktop Installer.exe (PID: 8696)
Application launched itself
- Docker Desktop Installer.exe (PID: 8696)
Found regular expressions for crypto-addresses (YARA)
- Docker Desktop Installer.exe (PID: 4024)
INFO
Checks supported languages
- Docker Desktop Installer.exe (PID: 4024)
- Docker Desktop Installer.exe (PID: 8696)
- Docker Desktop Installer.exe (PID: 1824)
Reads the computer name
- Docker Desktop Installer.exe (PID: 8696)
- Docker Desktop Installer.exe (PID: 4024)
- Docker Desktop Installer.exe (PID: 1824)
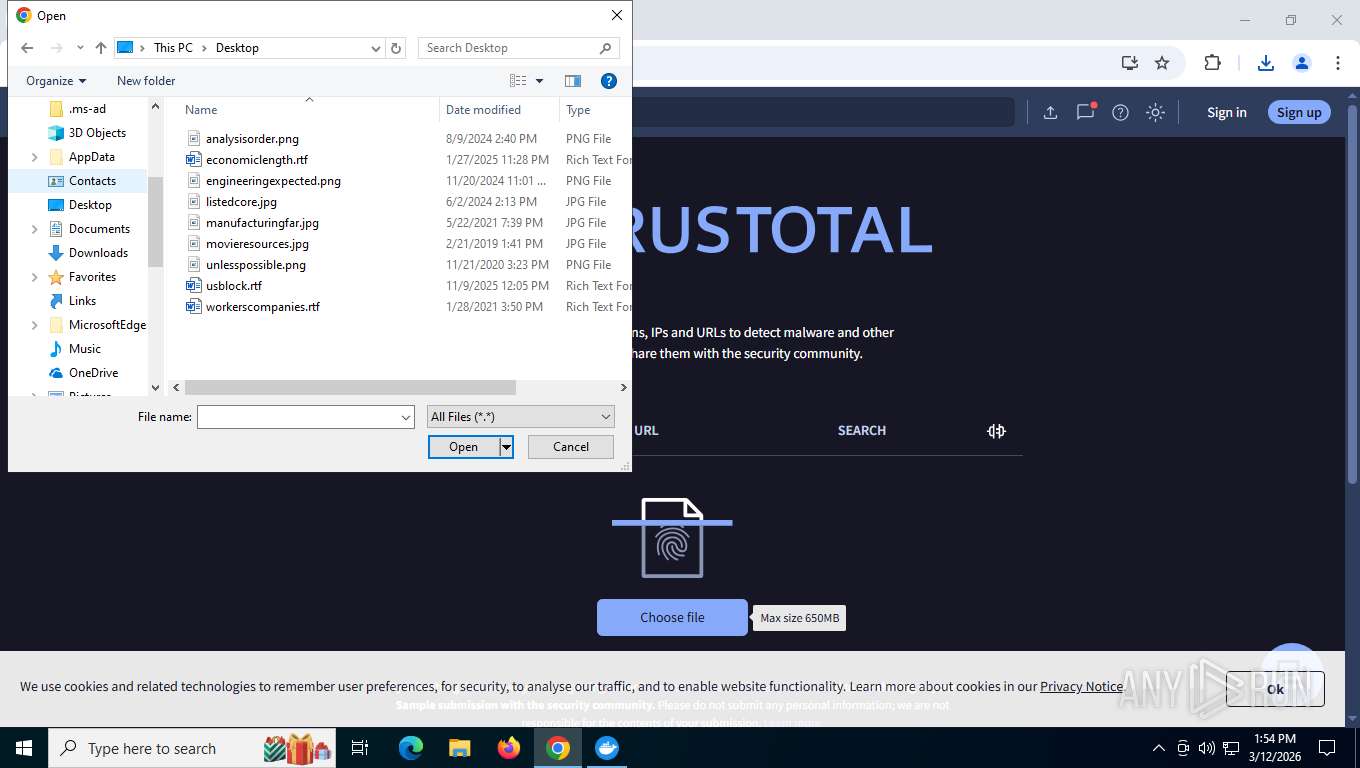
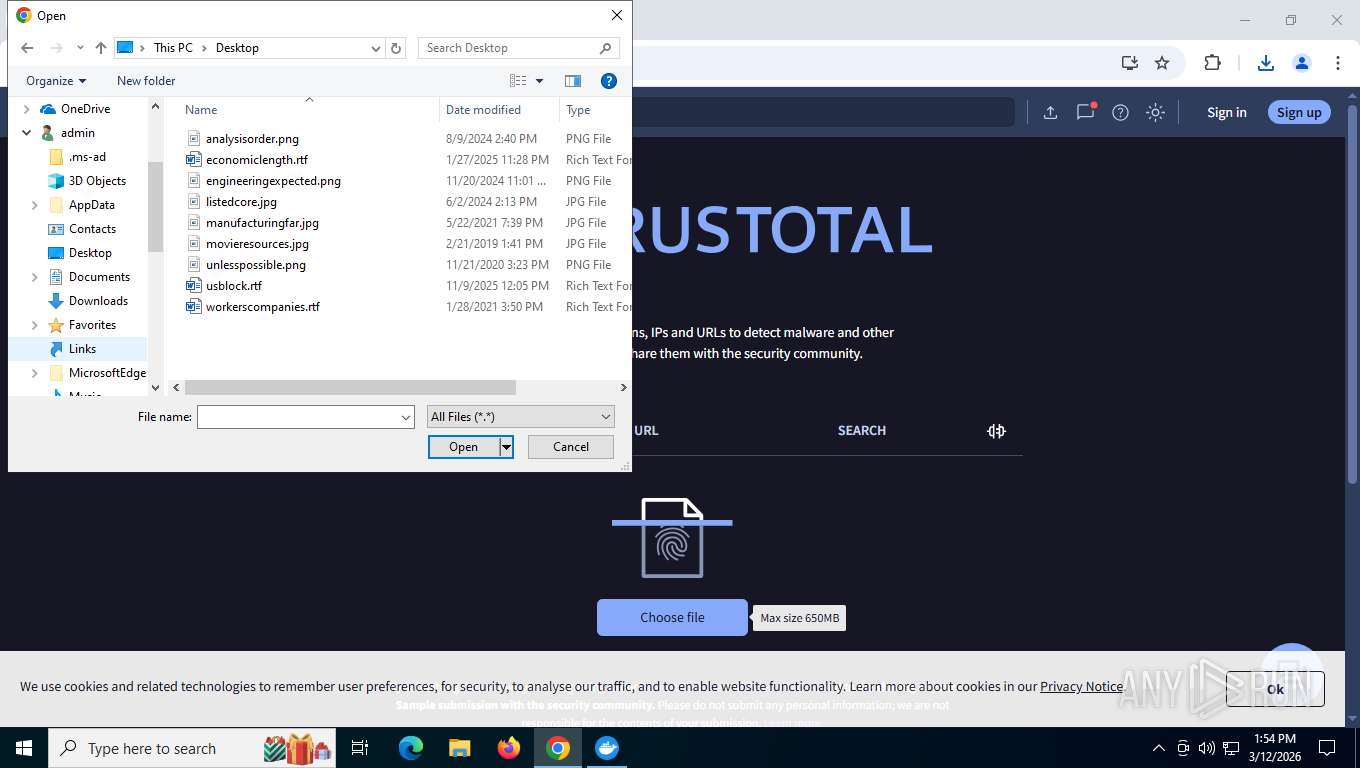
Creates files or folders in the user directory
- Docker Desktop Installer.exe (PID: 4024)
- Docker Desktop Installer.exe (PID: 8696)
Reads the machine GUID from the registry
- Docker Desktop Installer.exe (PID: 8696)
- Docker Desktop Installer.exe (PID: 1824)
- Docker Desktop Installer.exe (PID: 4024)
Create files in a temporary directory
- Docker Desktop Installer.exe (PID: 4024)
Reads Environment values
- Docker Desktop Installer.exe (PID: 1824)
- Docker Desktop Installer.exe (PID: 8696)
Reads product name
- Docker Desktop Installer.exe (PID: 1824)
- Docker Desktop Installer.exe (PID: 8696)
Executable content was dropped or overwritten
- chrome.exe (PID: 8064)
- chrome.exe (PID: 1040)
- chrome.exe (PID: 7256)
Reads security settings of Internet Explorer
- Docker Desktop Installer.exe (PID: 8696)
- Docker Desktop Installer.exe (PID: 1824)
Process checks computer location settings
- Docker Desktop Installer.exe (PID: 8696)
Application launched itself
- chrome.exe (PID: 8064)
Creates files in the program directory
- Docker Desktop Installer.exe (PID: 1824)
The sample compiled with english language support
- chrome.exe (PID: 7256)
- chrome.exe (PID: 1040)
- Docker Desktop Installer.exe (PID: 1824)
Disables trace logs
- Docker Desktop Installer.exe (PID: 1824)
Detects GO elliptic curve encryption (YARA)
- Docker Desktop Installer.exe (PID: 4024)
Application based on Golang
- Docker Desktop Installer.exe (PID: 4024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
220
Monitored processes
67
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=8520,i,6322444098949801265,11423615819971062229,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=8720 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=28 --field-trial-handle=6340,i,6322444098949801265,11423615819971062229,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1200 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6152,i,6322444098949801265,11423615819971062229,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
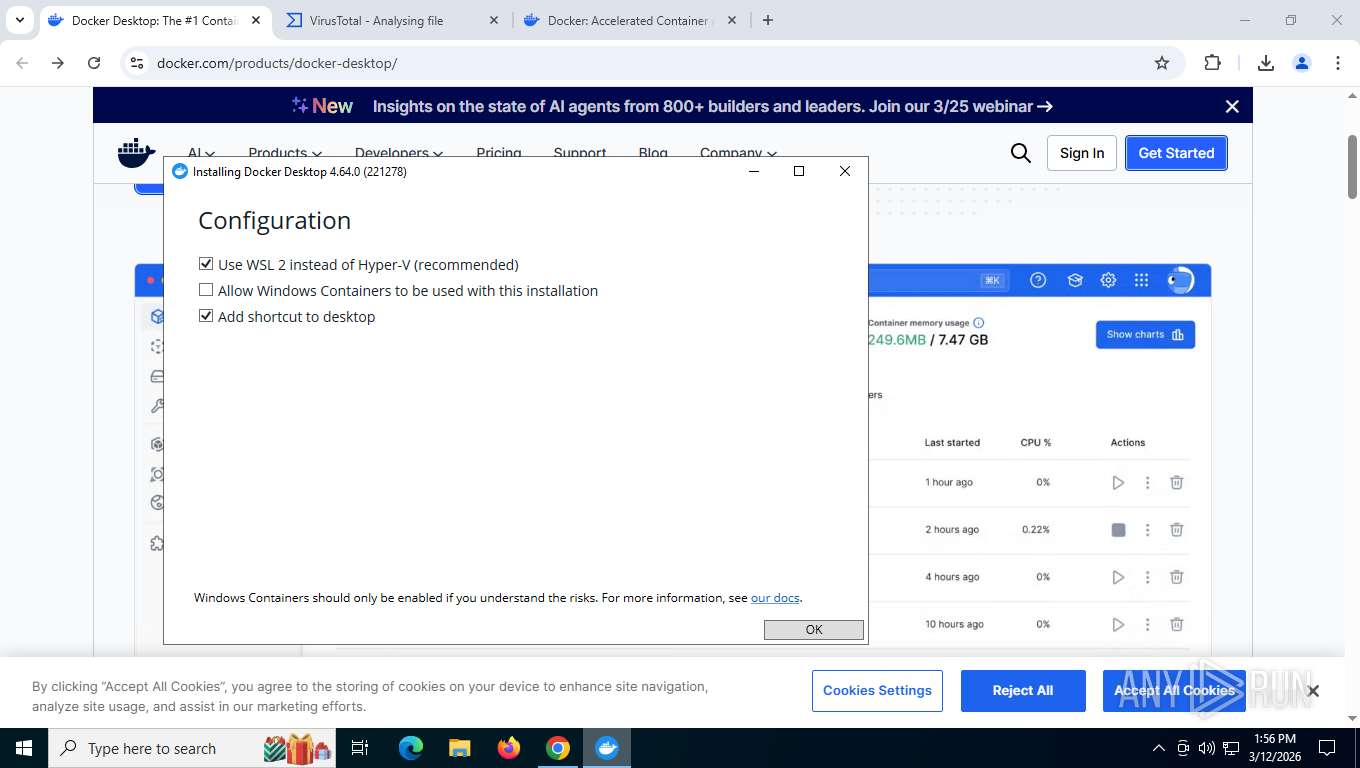
| 1824 | "C:\Users\admin\AppData\Local\Temp\DockerDesktopInstallers\1773338013988420600\Docker Desktop Installer.exe" "install" -package "C:\Users\admin\AppData\Local\Temp\DockerDesktopInstallers\1773338014083066100\DockerDesktop.d4w" --relaunch-as-admin | C:\Users\admin\AppData\Local\Temp\DockerDesktopInstallers\1773338013988420600\Docker Desktop Installer.exe | Docker Desktop Installer.exe | ||||||||||||
User: admin Company: Docker Inc. Integrity Level: HIGH Description: Docker Desktop Installer Version: 4.64.0.221278 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1868,i,6322444098949801265,11423615819971062229,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=1880 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5548,i,6322444098949801265,11423615819971062229,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=7756 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=8648,i,6322444098949801265,11423615819971062229,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=8412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5536,i,6322444098949801265,11423615819971062229,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
38 047
Read events
38 021
Write events
21
Delete events
5
Modification events
| (PID) Process: | (1824) Docker Desktop Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docker Desktop Installer_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1824) Docker Desktop Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docker Desktop Installer_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1824) Docker Desktop Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docker Desktop Installer_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1824) Docker Desktop Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docker Desktop Installer_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1824) Docker Desktop Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docker Desktop Installer_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1824) Docker Desktop Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docker Desktop Installer_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1824) Docker Desktop Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docker Desktop Installer_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1824) Docker Desktop Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docker Desktop Installer_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1824) Docker Desktop Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docker Desktop Installer_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1824) Docker Desktop Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docker Desktop Installer_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
57
Suspicious files
517
Text files
228
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1e5419.TMP | — | |
MD5:— | SHA256:— | |||
| 8064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1e5419.TMP | — | |
MD5:— | SHA256:— | |||
| 8064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1e5429.TMP | — | |
MD5:— | SHA256:— | |||
| 8064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RF1e5438.TMP | — | |
MD5:— | SHA256:— | |||
| 8064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1e5438.TMP | — | |
MD5:— | SHA256:— | |||
| 8064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1e5438.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
593
TCP/UDP connections
165
DNS requests
208
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
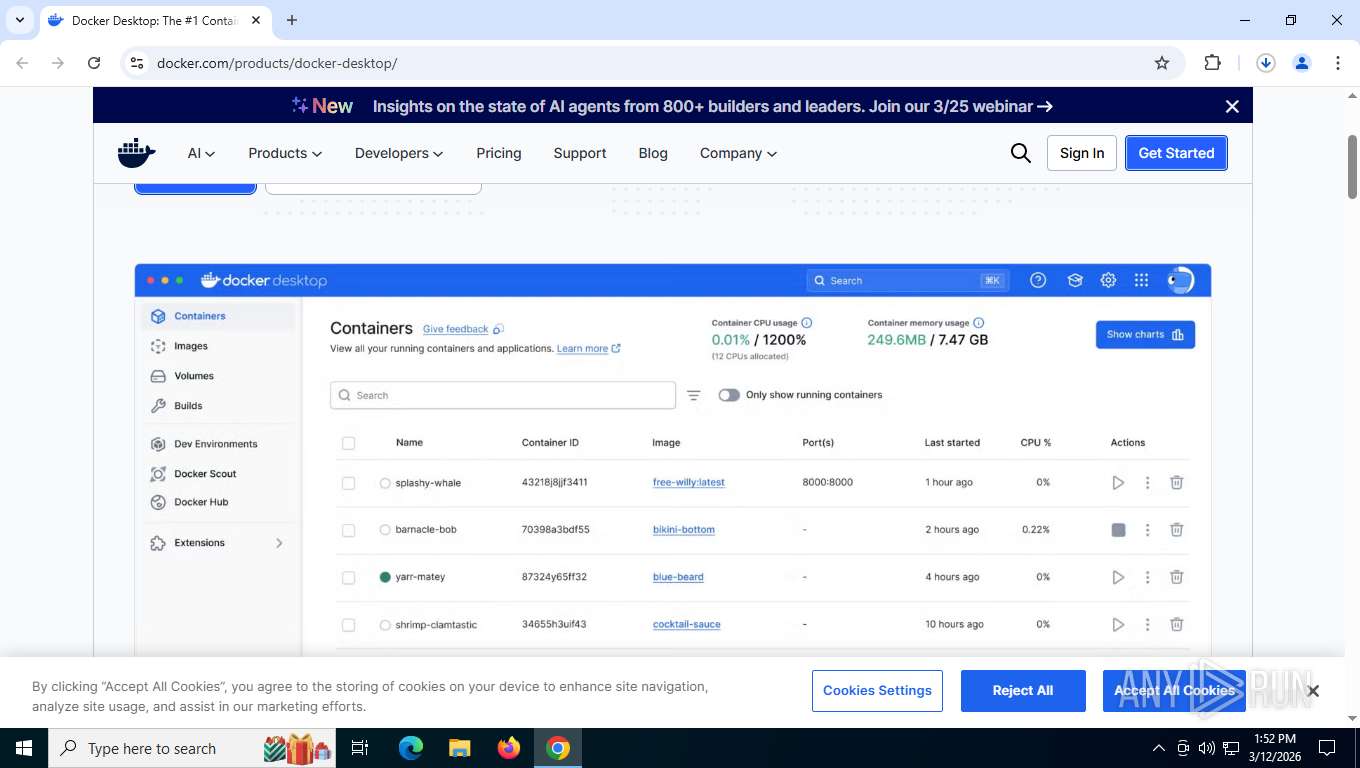
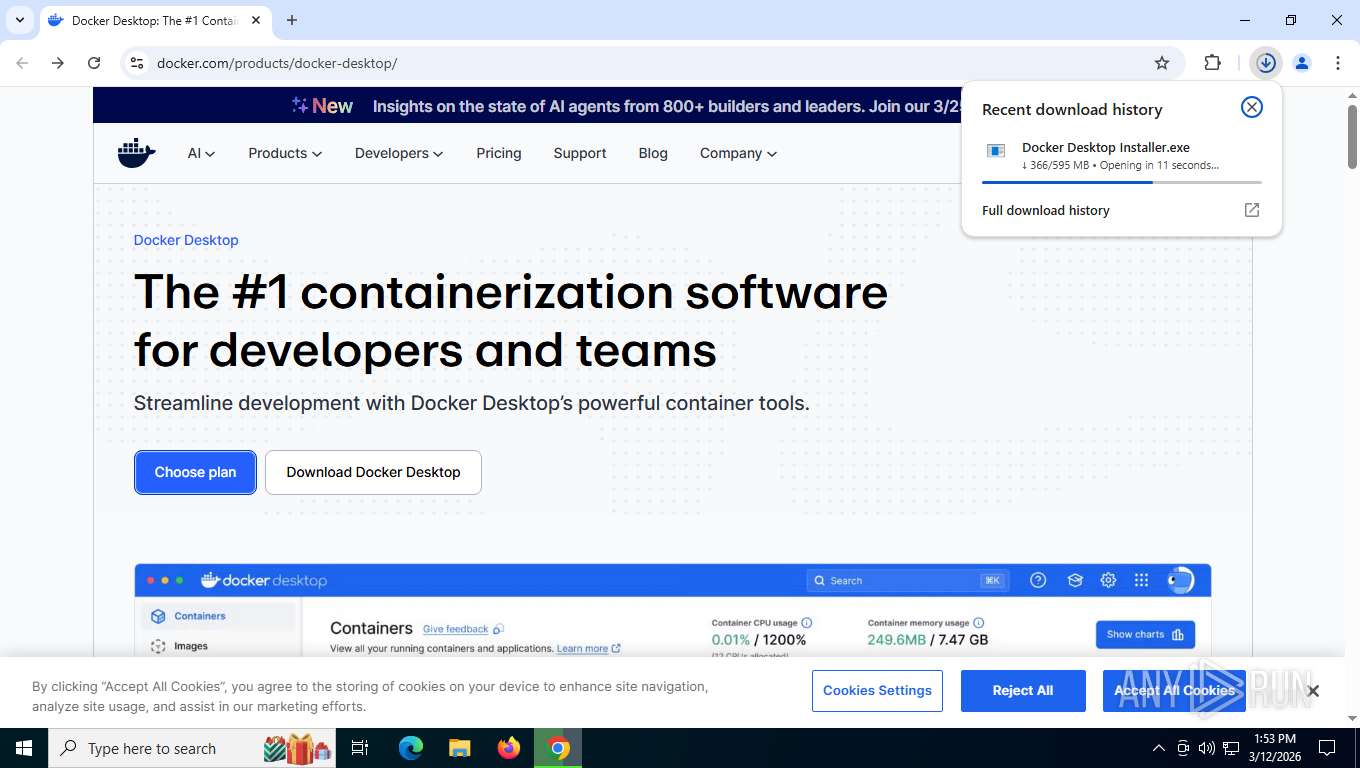
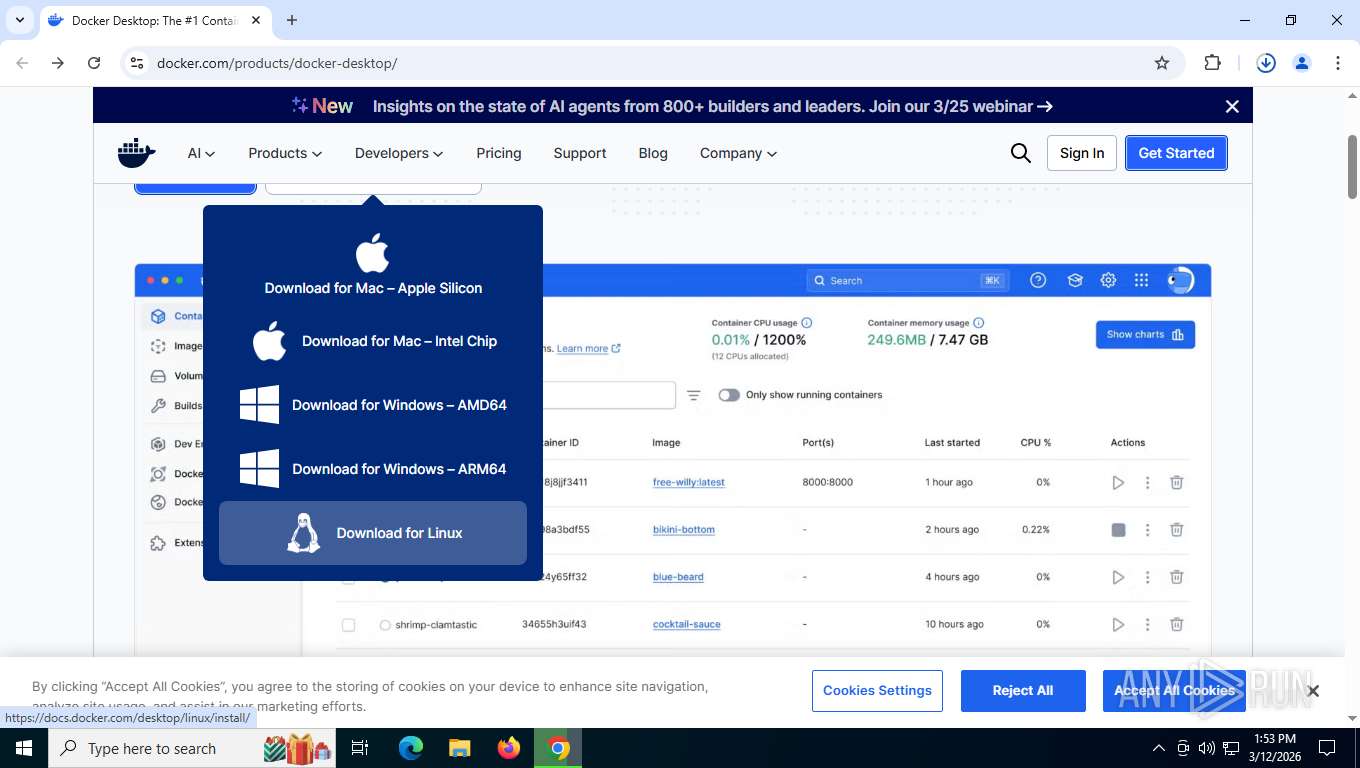
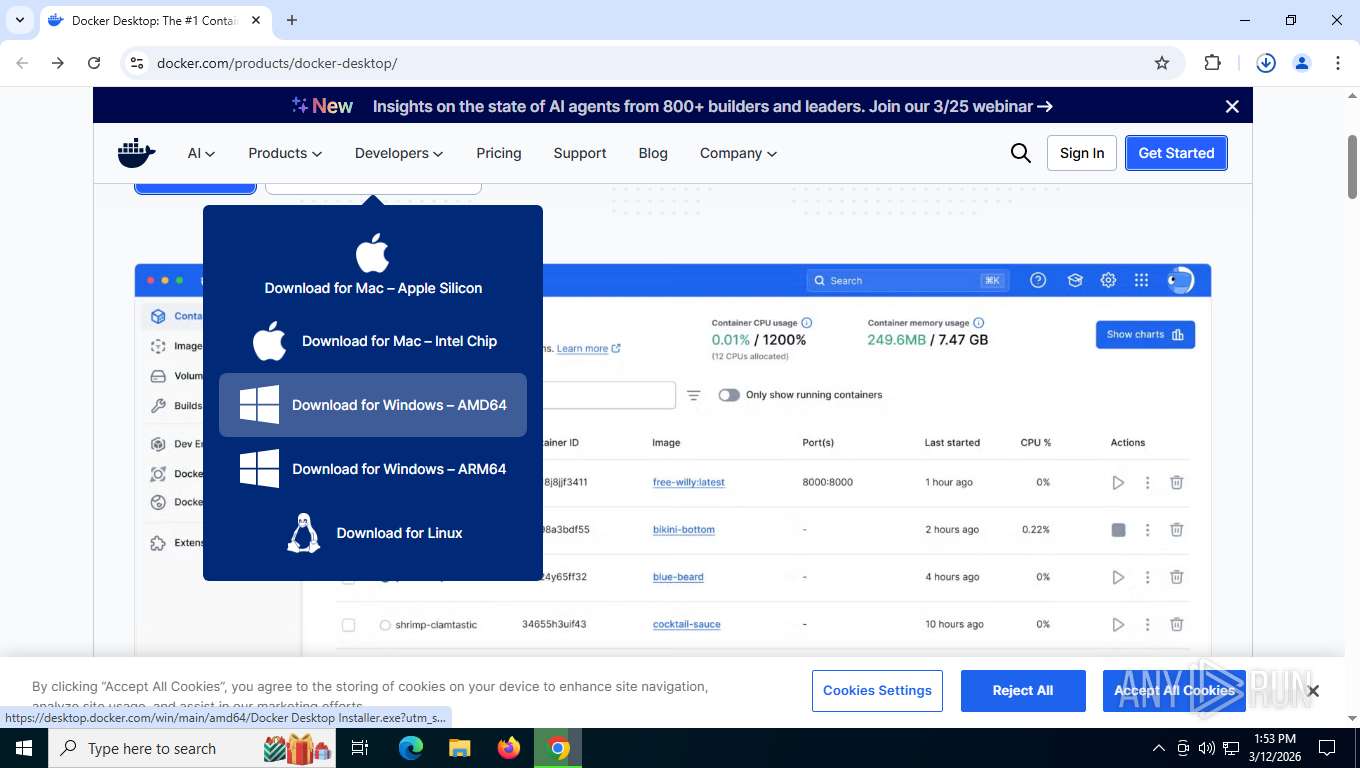
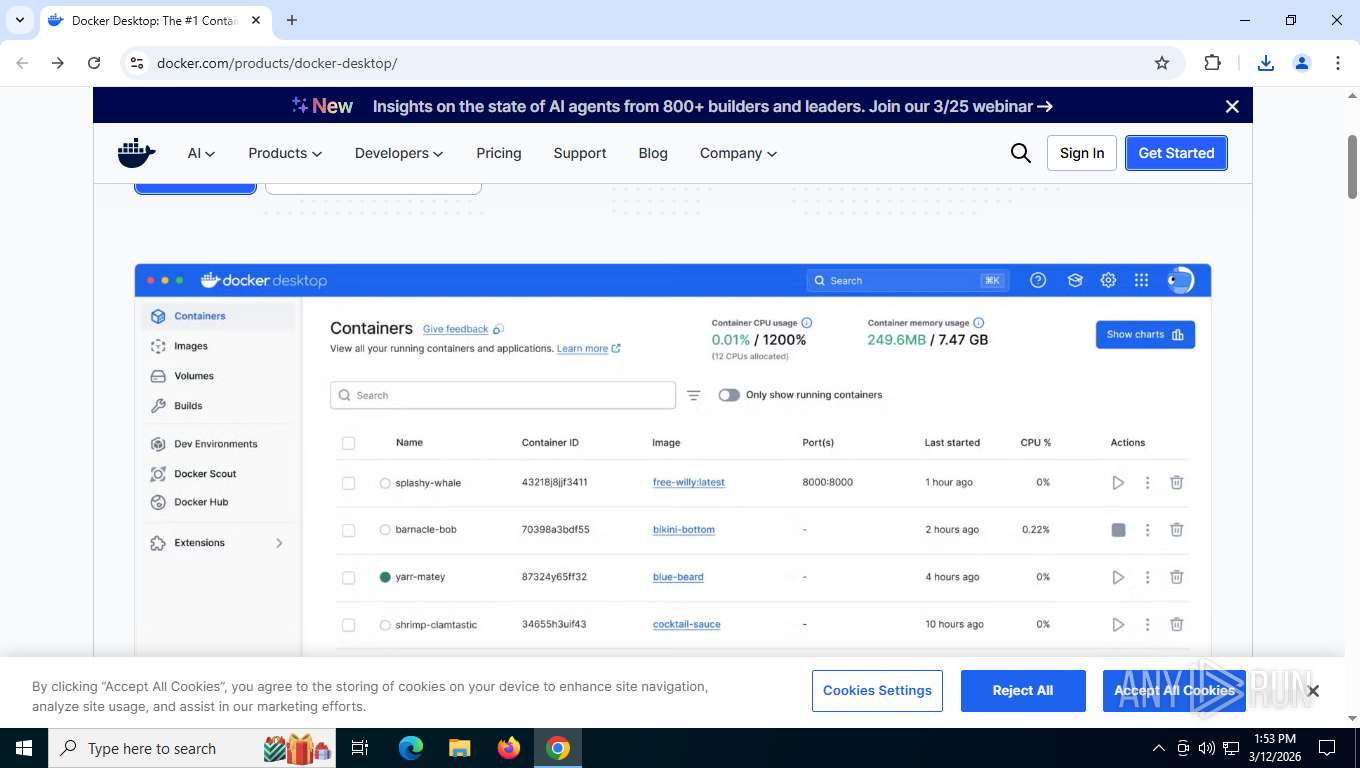
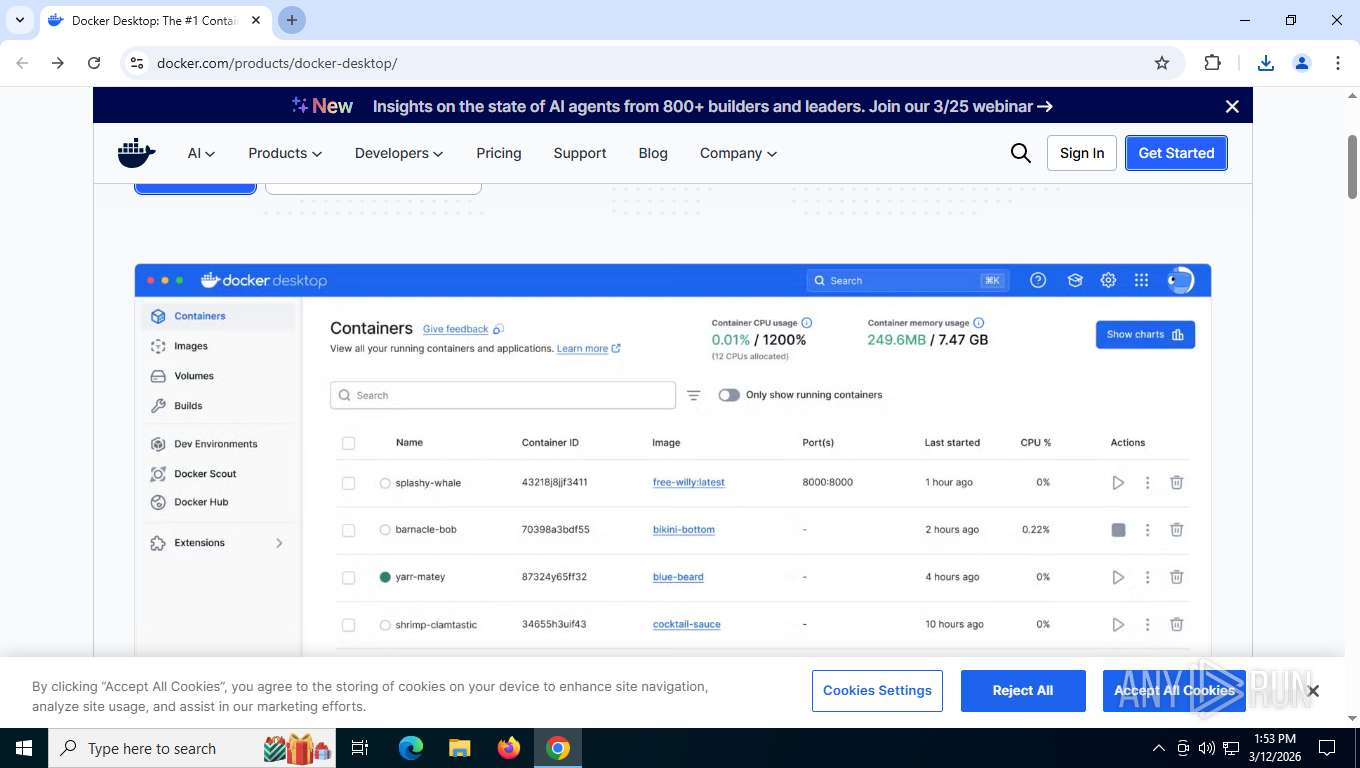
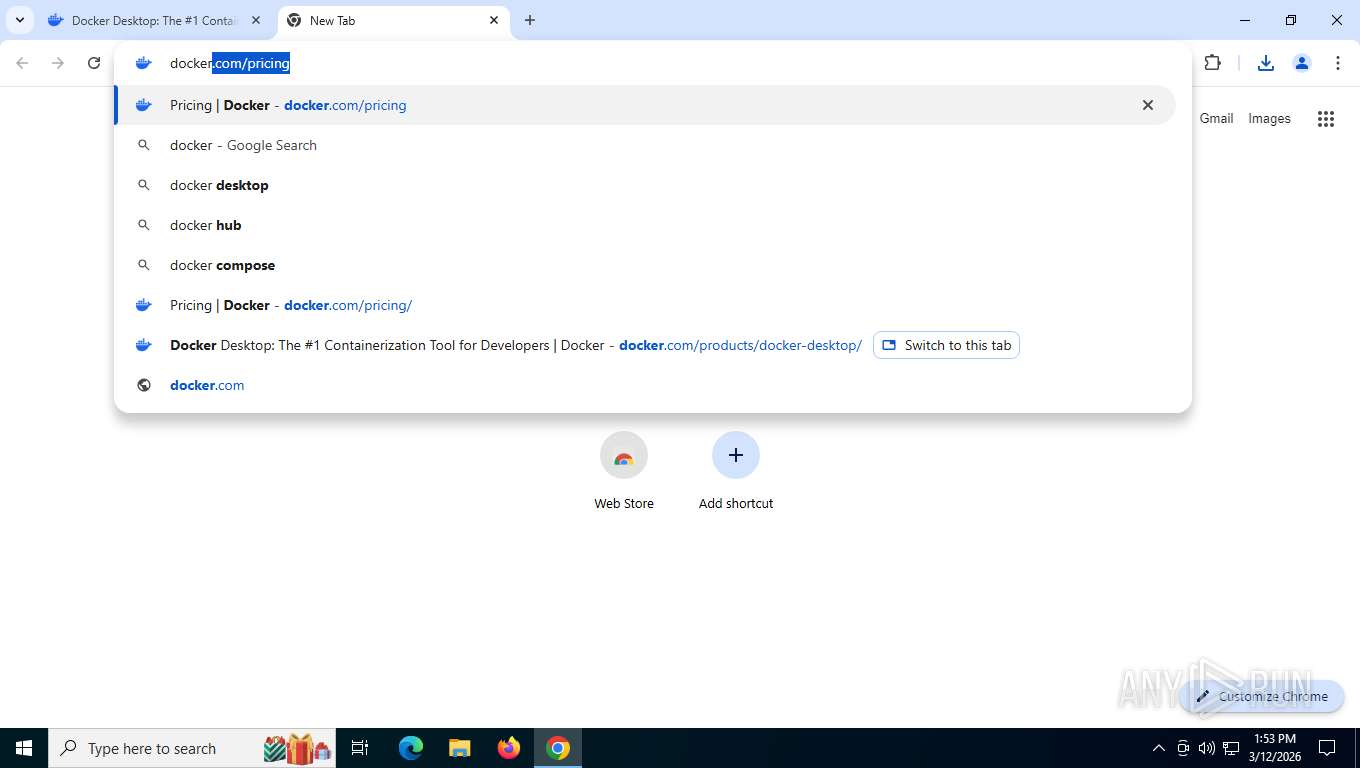
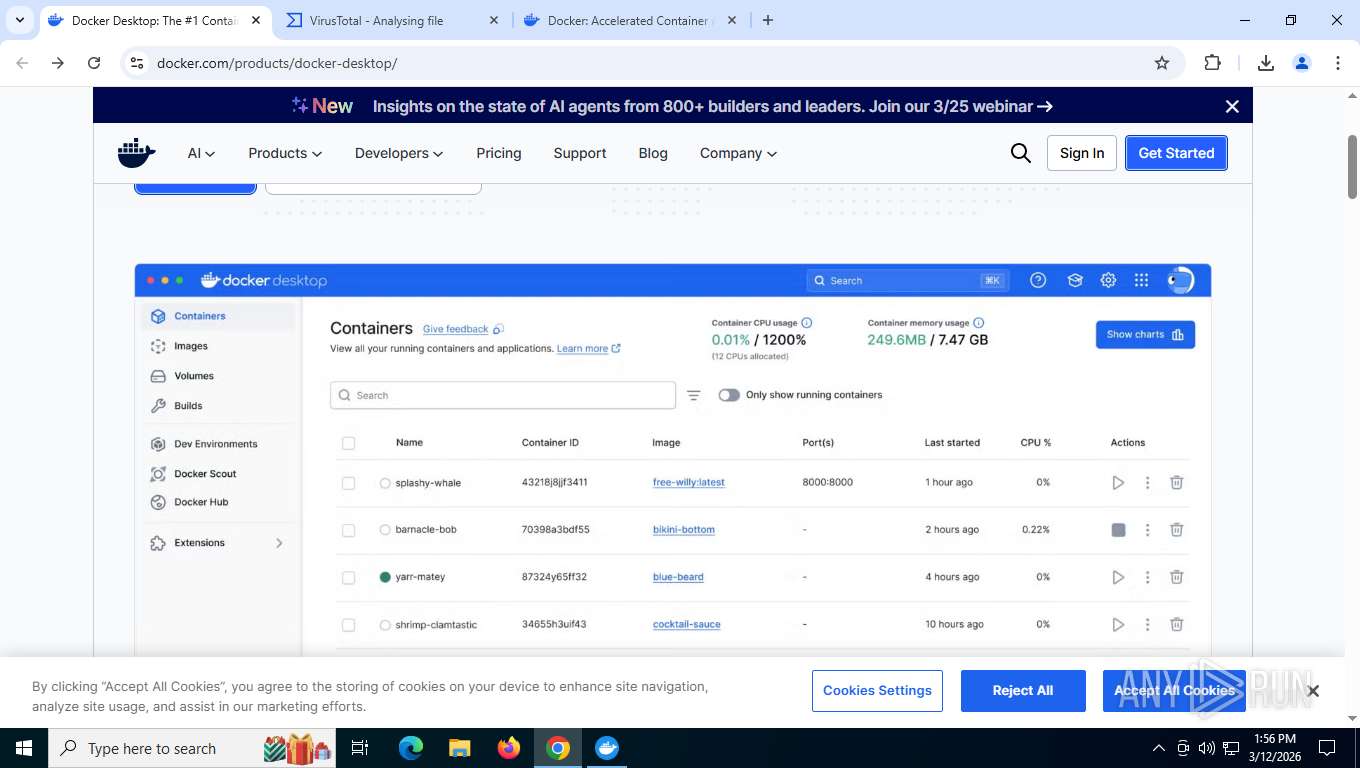
8168 | chrome.exe | GET | 200 | 23.185.0.4:443 | https://www.docker.com/products/docker-desktop/ | unknown | html | 245 Kb | unknown |
8168 | chrome.exe | GET | 200 | 216.58.206.46:80 | http://clients2.google.com/time/1/current?cup2key=8:rTK2jOcp1nkqPrM31ns7k_h_vGCbiUYFCivPEQzho3A&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
8168 | chrome.exe | GET | 200 | 23.185.0.4:443 | https://www.docker.com/app/themes/Ponyo/dist/blocks/atoms/pill/pill-style.css?ver=1773151335 | unknown | text | 595 b | unknown |
8168 | chrome.exe | GET | 200 | 23.185.0.4:443 | https://www.docker.com/app/themes/Ponyo/dist/css/screen.css?ver=cd6305f0d30503f31cfc | unknown | text | 98.7 Kb | unknown |
8168 | chrome.exe | GET | 200 | 23.185.0.4:443 | https://www.docker.com/wp/wp-includes/js/jquery/jquery.min.js?ver=3.7.1 | unknown | text | 85.5 Kb | unknown |
8168 | chrome.exe | GET | 200 | 23.185.0.4:443 | https://www.docker.com/wp/wp-includes/js/jquery/jquery-migrate.min.js?ver=3.4.1 | unknown | text | 13.2 Kb | unknown |
8168 | chrome.exe | GET | 200 | 23.185.0.4:443 | https://www.docker.com/app/uploads/brand/background/gray-1536x793.png | unknown | image | 28.5 Kb | unknown |
8168 | chrome.exe | GET | 200 | 23.185.0.4:443 | https://www.docker.com/app/uploads/2025/05/DD-hiroko-1536x964.png.webp | unknown | binary | 62.7 Kb | unknown |
8168 | chrome.exe | GET | 200 | 23.185.0.4:443 | https://www.docker.com/app/uploads/2024/09/docker-desktop-manage-extensions.svg | unknown | image | 478 Kb | unknown |
8168 | chrome.exe | GET | 200 | 23.185.0.4:443 | https://www.docker.com/app/plugins/syntaxhighlighter/syntaxhighlighter3/scripts/shCore.js?ver=3.0.9b | unknown | text | 23.3 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4256 | svchost.exe | 51.11.168.232:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7236 | RUXIMICS.exe | 51.11.168.232:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.11.168.232:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8168 | chrome.exe | 216.58.206.46:80 | clients2.google.com | GOOGLE | US | whitelisted |
8168 | chrome.exe | 142.251.208.170:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
8168 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
8168 | chrome.exe | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.docker.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8168 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
8168 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
8168 | chrome.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
8168 | chrome.exe | Potentially Bad Traffic | ET INFO Executable served from Amazon S3 |
1824 | Docker Desktop Installer.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |