| File name: | BootstrapperNew.exe |
| Full analysis: | https://app.any.run/tasks/9a012ff2-fccd-4300-9c80-53ba90efd5a5 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2025, 16:38:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 4D207914AB7B161D4A8E6BF45CD27DE4 |
| SHA1: | ACCD340B49754A770FD8DEBC10A379FE587336F6 |
| SHA256: | 3C4DCF944E748C91DF983422349E3A10F8271D3EF77CEEE73D071B3D5E764F1B |
| SSDEEP: | 98304:FYzoojJRba+nPSqNCrRasNk0LW4kr+zIIvt4Fi1VG86jieQEnYr2OCQekIflB2bQ:y+J |
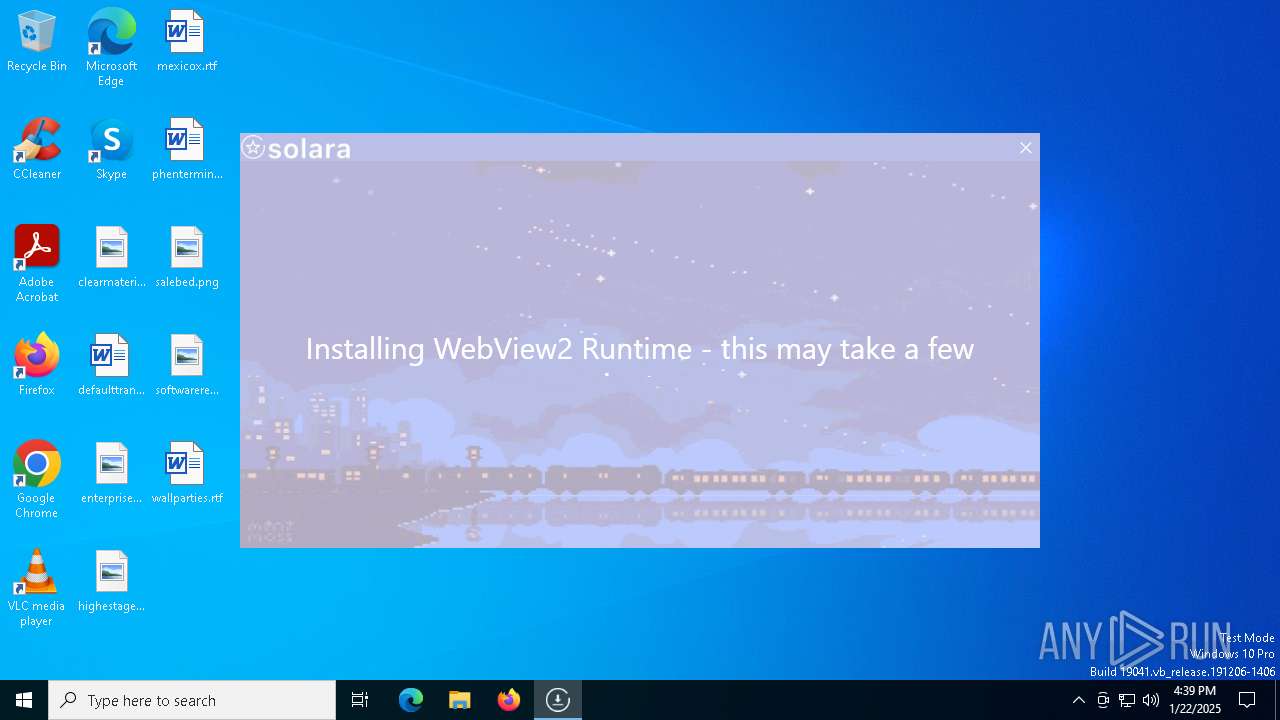
MALICIOUS
Adds path to the Windows Defender exclusion list
- BootstrapperNew.exe (PID: 6160)
SUSPICIOUS
Reads security settings of Internet Explorer
- BootstrapperNew.exe (PID: 6160)
Query Microsoft Defender preferences
- BootstrapperNew.exe (PID: 6160)
Script adds exclusion path to Windows Defender
- BootstrapperNew.exe (PID: 6160)
Starts POWERSHELL.EXE for commands execution
- BootstrapperNew.exe (PID: 6160)
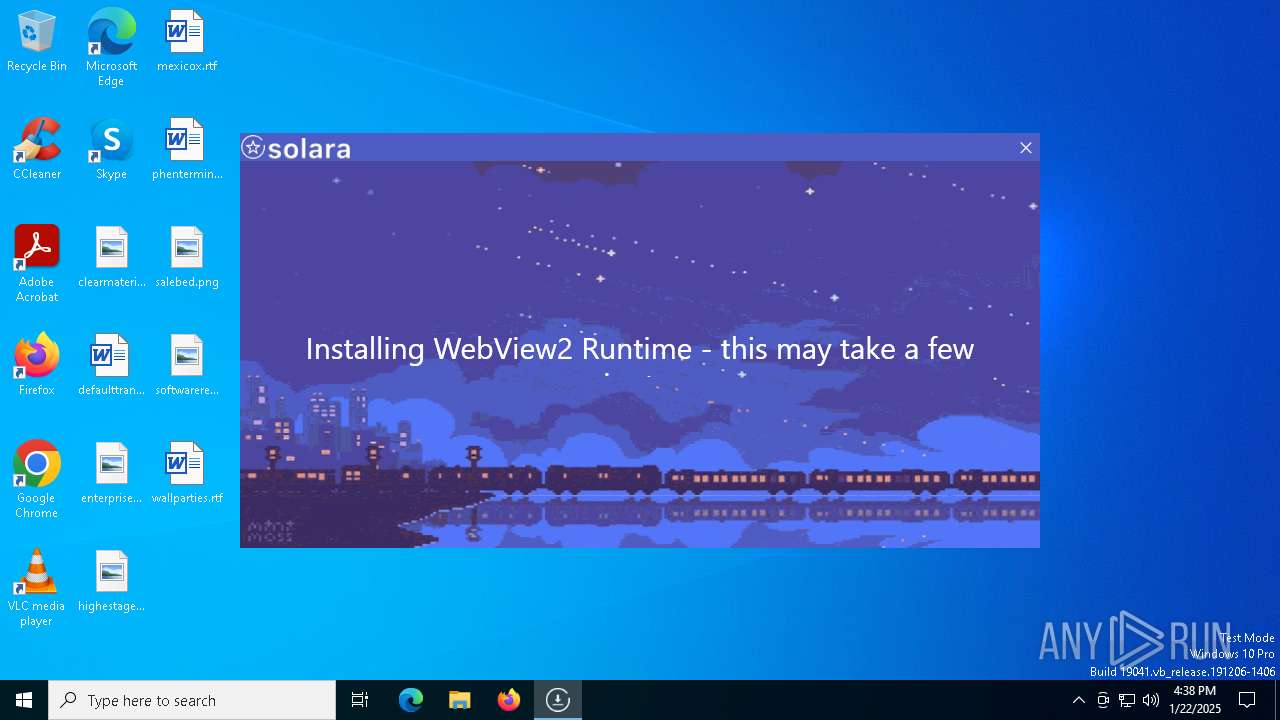
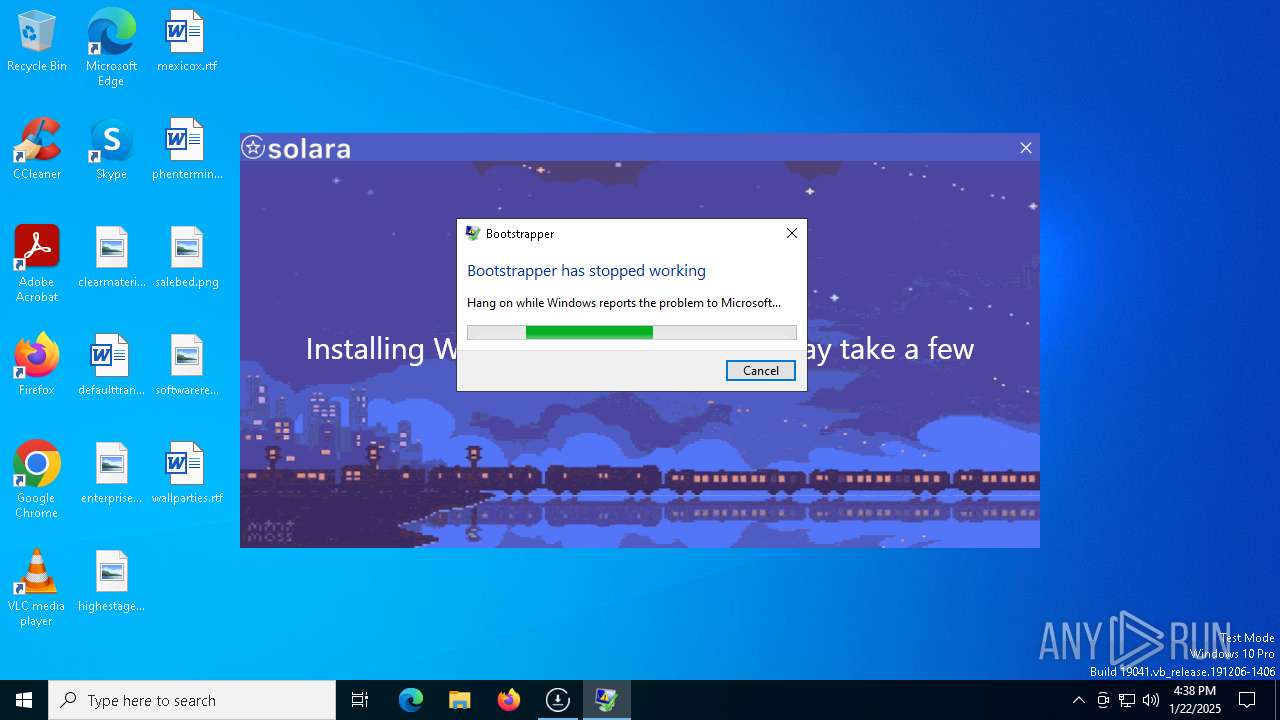
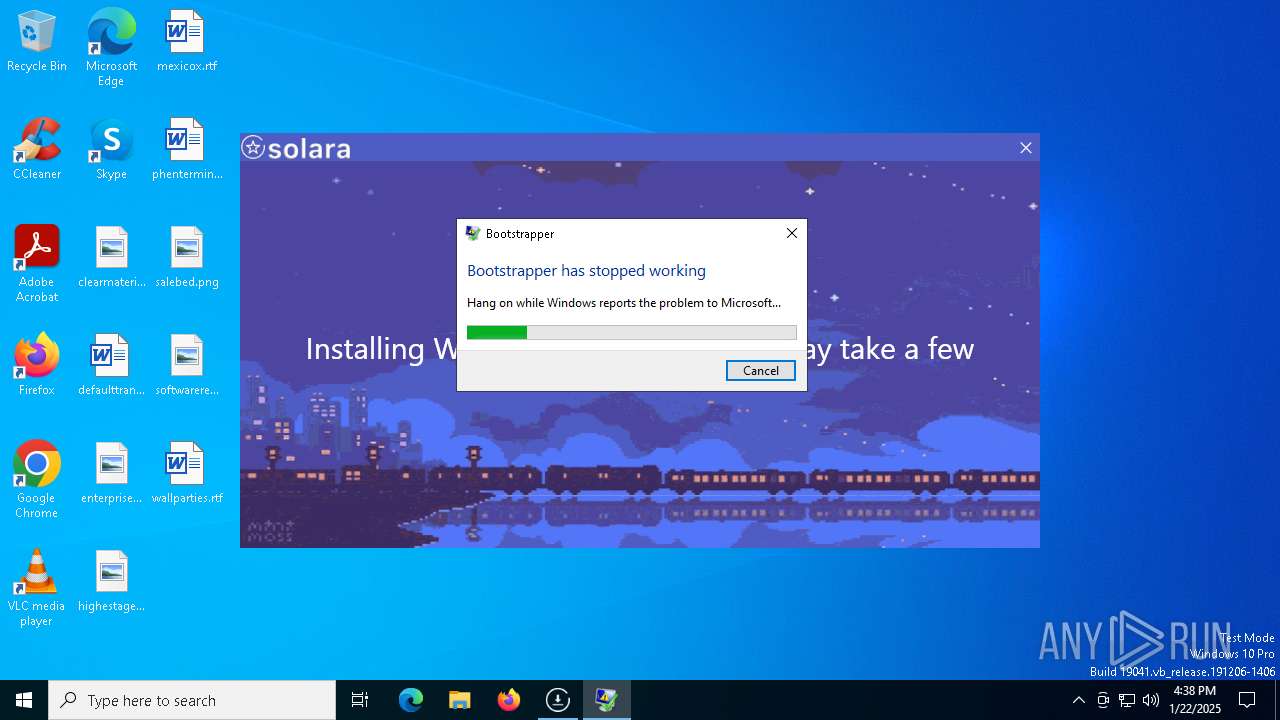
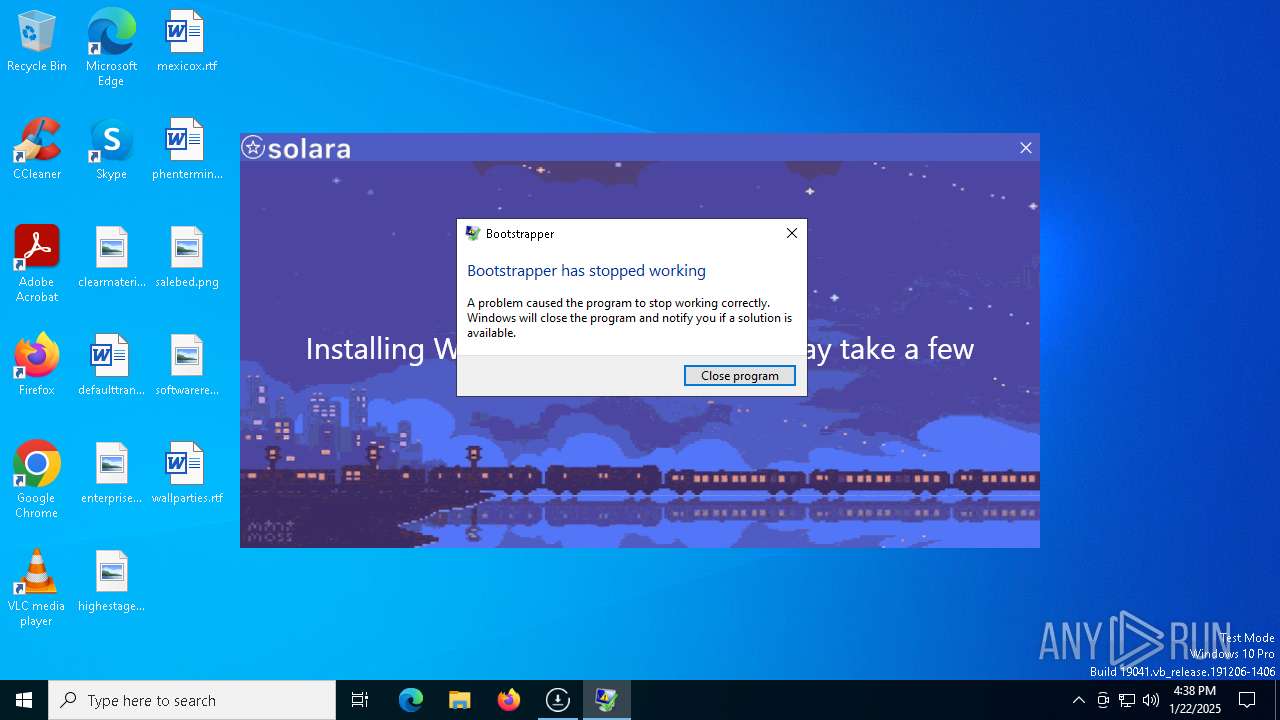
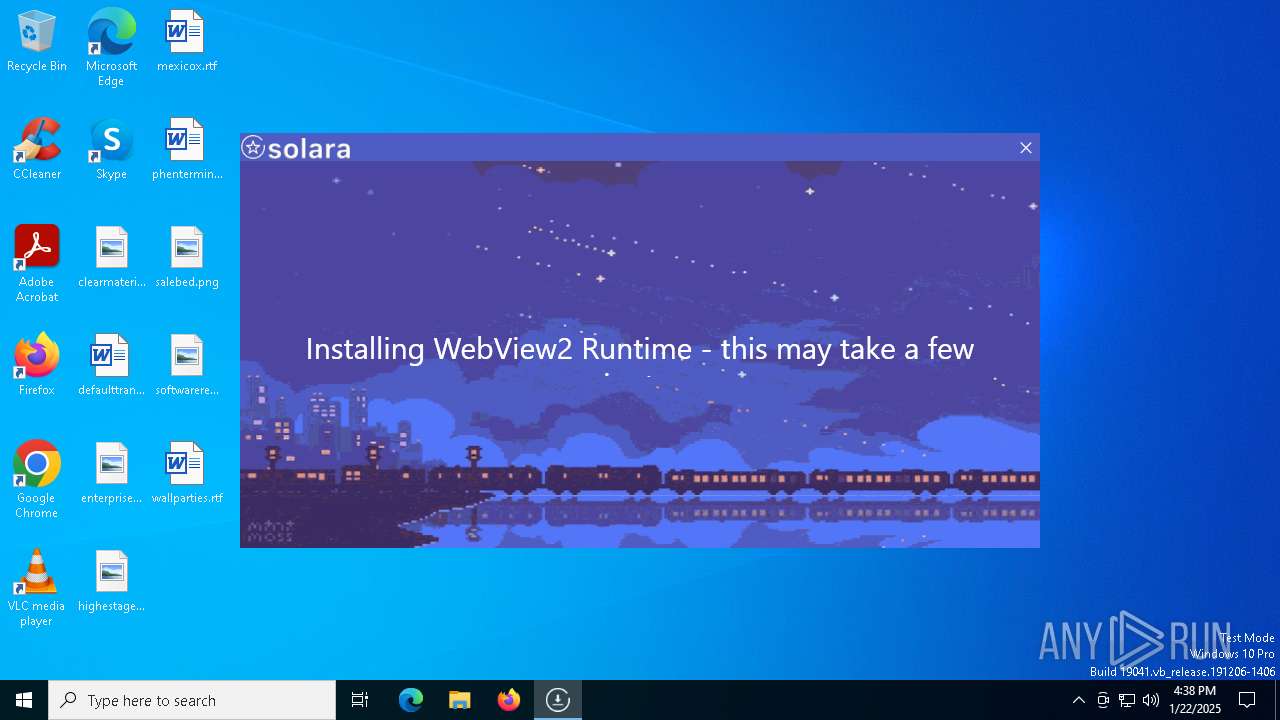
Executes application which crashes
- BootstrapperNew.exe (PID: 6160)
Executable content was dropped or overwritten
- BootstrapperNew.exe (PID: 6160)
Process drops legitimate windows executable
- BootstrapperNew.exe (PID: 6160)
INFO
Reads the computer name
- BootstrapperNew.exe (PID: 6160)
Creates files in the program directory
- BootstrapperNew.exe (PID: 6160)
Checks supported languages
- BootstrapperNew.exe (PID: 6160)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 7120)
- powershell.exe (PID: 4444)
- powershell.exe (PID: 4504)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7120)
- powershell.exe (PID: 4444)
Reads Environment values
- BootstrapperNew.exe (PID: 6160)
Checks proxy server information
- BootstrapperNew.exe (PID: 6160)
- WerFault.exe (PID: 6384)
Disables trace logs
- BootstrapperNew.exe (PID: 6160)
Reads the machine GUID from the registry
- BootstrapperNew.exe (PID: 6160)
Reads the software policy settings
- BootstrapperNew.exe (PID: 6160)
- WerFault.exe (PID: 6384)
Create files in a temporary directory
- BootstrapperNew.exe (PID: 6160)
Creates files or folders in the user directory
- WerFault.exe (PID: 6384)
The sample compiled with english language support
- BootstrapperNew.exe (PID: 6160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2080:06:10 14:23:56+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 2994688 |
| InitializedDataSize: | 9216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Bootstrapper |
| FileVersion: | 1.0.0.0 |
| InternalName: | Bootstrapper.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | Bootstrapper.exe |
| ProductName: | Bootstrapper |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
140
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 648 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Local\Temp\BootstrapperNew.exe" | C:\Users\admin\AppData\Local\Temp\BootstrapperNew.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Bootstrapper Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
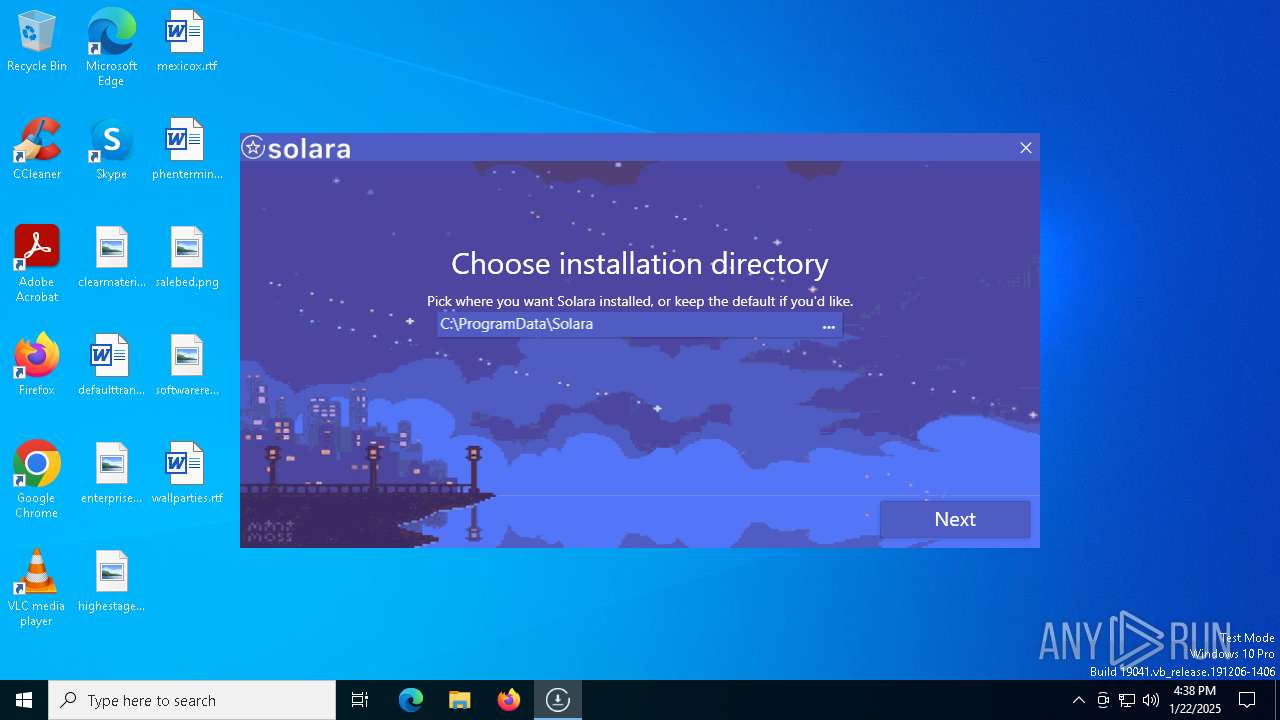
| 4444 | "powershell" -Command "Add-MpPreference -ExclusionPath 'C:\ProgramData\Solara'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | BootstrapperNew.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4504 | "powershell" -Command "Get-MpPreference | Select-Object -ExpandProperty ExclusionPath" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | BootstrapperNew.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5308 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6160 | "C:\Users\admin\AppData\Local\Temp\BootstrapperNew.exe" | C:\Users\admin\AppData\Local\Temp\BootstrapperNew.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Bootstrapper Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6384 | C:\WINDOWS\system32\WerFault.exe -u -p 6160 -s 1920 | C:\Windows\System32\WerFault.exe | BootstrapperNew.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6800 | "powershell" -Command "Get-MpPreference | Select-Object -ExpandProperty ExclusionPath" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | BootstrapperNew.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6808 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7120 | "powershell" -Command "Add-MpPreference -ExclusionPath 'C:\ProgramData\Solara'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | BootstrapperNew.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 135
Read events
27 115
Write events
17
Delete events
3
Modification events
| (PID) Process: | (6160) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6160) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6160) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6160) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6160) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6160) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6160) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6160) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6160) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6160) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
9
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6384 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_BootstrapperNew._2278685badcfc7cdb59eab4d9ac44071ea8a_611f641e_63028763-53c4-4866-987c-ed8efd675427\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6384 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\BootstrapperNew.exe.6160.dmp | — | |
MD5:— | SHA256:— | |||
| 6384 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERD0EF.tmp.dmp | binary | |
MD5:18AE9CDB4F70970018000B752ACB25E5 | SHA256:EC3D465D495710C5F6F865586268AD92D68C915931E21A95F4C735BE667196B4 | |||
| 7120 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pzshmpqm.fxl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6384 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERD3FF.tmp.xml | xml | |
MD5:0C91A4E58B270C8F44755F7C0A2DF563 | SHA256:1B4770ACCEB27C558FA94F488C44B5706A0673CED4D62215A93A36684B4274D6 | |||
| 6800 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:C6A35172E8D289DA0245937E02C39E56 | SHA256:BD880EDEEBEBD257F4FE05B4BF035F634042AE4C9D0DCFA0CC572B17D8E66B6E | |||
| 6800 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1dzeishi.ovz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6384 | WerFault.exe | C:\Windows\appcompat\Programs\Amcache.hve | binary | |
MD5:A7EB0B4DF512C5834FAA91F4E2F1886B | SHA256:721F8A98A2FD7D02A9A29D7C2CA4BD215A358F38D6FFA88D21A592C0328F8AA4 | |||
| 6800 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ruwm5miu.wfb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6384 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERD3CF.tmp.WERInternalMetadata.xml | binary | |
MD5:27F7D6A2A4CFB1C5C9124F3B153FE5F8 | SHA256:F6FF7BBFA83CF08FDF031AC962C1E961FE4D5EE4ED287AB8DD1E1EBB47AFF777 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
33
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5032 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6488 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5032 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6384 | WerFault.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6384 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2092 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 184.30.18.9:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6160 | BootstrapperNew.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
msedge.sf.dl.delivery.mp.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |