| File name: | LauncherforZapret.exe |
| Full analysis: | https://app.any.run/tasks/7c99f0fd-7f47-433b-9b6d-cb593794af55 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 18:17:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 4F3B4B1A5012E54ADC4809011FE935E8 |
| SHA1: | B87BD68349089AC370A2403983FC1B821F443B7A |
| SHA256: | 3C46D668DCA40015D5462F4C61868E602F42CD255885BBABCDFE3D3BF7868F92 |
| SSDEEP: | 49152:zBuP2PD2veXRMYQOAMP+vPkL4cqMjktg5S8GjgfiETpIw339oMj2P9Uc7G7F3PLa:9LtFWOWiWuWhuupruuuu5uupauuuuzWv |
MALICIOUS
Executing a file with an untrusted certificate
- LauncherforZapret.exe (PID: 7100)
- LauncherforZapret.exe (PID: 3504)
SUSPICIOUS
Process run an executable payload
- rundll32.exe (PID: 768)
Uses REG/REGEDIT.EXE to modify registry
- rundll32.exe (PID: 768)
INFO
The sample compiled with english language support
- LauncherforZapret.exe (PID: 3504)
Checks supported languages
- LauncherforZapret.exe (PID: 3504)
Reads the computer name
- LauncherforZapret.exe (PID: 3504)
Create files in a temporary directory
- LauncherforZapret.exe (PID: 3504)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 768)
Checks proxy server information
- slui.exe (PID: 6540)
Reads the software policy settings
- slui.exe (PID: 6540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (69.4) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.3) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:05 00:35:34+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1064960 |
| InitializedDataSize: | 40960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7b50 |
| OSVersion: | 4 |
| ImageVersion: | 2.7 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.7.0.0 |
| ProductVersionNumber: | 2.7.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | This Program is Free! |
| CompanyName: | Topersoft.com |
| FileDescription: | Launcher for Zapret |
| LegalCopyright: | Program by TOPER © 2024-2025 |
| LegalTrademarks: | TOPERSOFT © 2024-2025 |
| ProductName: | Launcher for Zapret |
| FileVersion: | 2.07 |
| ProductVersion: | 2.07 |
| InternalName: | Launcher for Zapret |
| OriginalFileName: | Launcher for Zapret.exe |
Total processes
138
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 768 | RunDLL32.EXE shell32.dll,ShellExec_RunDLL reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers" /v "C:\Users\admin\Desktop\LauncherforZapret.exe" /d "~ GDIDPISCALING DPIUNAWARE" /f | C:\Windows\SysWOW64\rundll32.exe | — | LauncherforZapret.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2648 | "C:\WINDOWS\system32\reg.exe" add "HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers" /v "C:\Users\admin\Desktop\LauncherforZapret.exe" /d "~ GDIDPISCALING DPIUNAWARE" /f | C:\Windows\SysWOW64\reg.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3504 | "C:\Users\admin\Desktop\LauncherforZapret.exe" | C:\Users\admin\Desktop\LauncherforZapret.exe | explorer.exe | ||||||||||||
User: admin Company: Topersoft.com Integrity Level: HIGH Description: Launcher for Zapret Exit code: 0 Version: 2.07 Modules
| |||||||||||||||
| 6172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6540 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
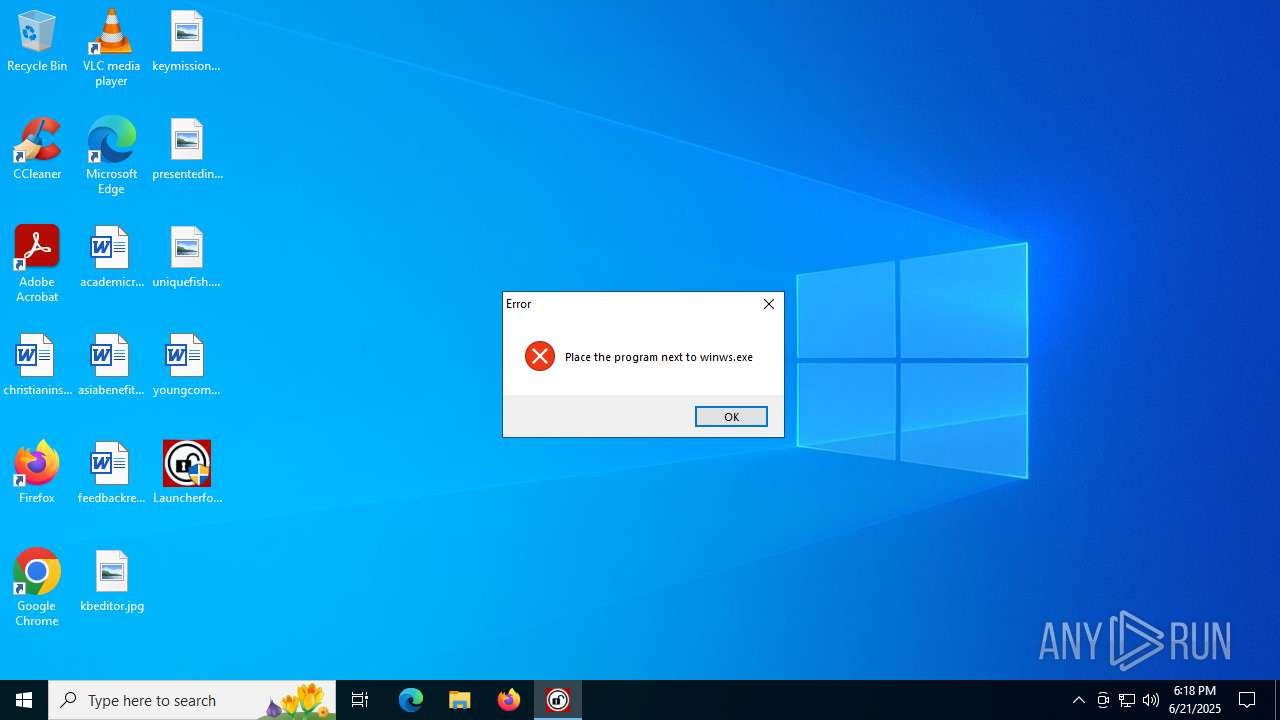
| 7100 | "C:\Users\admin\Desktop\LauncherforZapret.exe" | C:\Users\admin\Desktop\LauncherforZapret.exe | — | explorer.exe | |||||||||||
User: admin Company: Topersoft.com Integrity Level: MEDIUM Description: Launcher for Zapret Exit code: 3221226540 Version: 2.07 Modules
| |||||||||||||||
Total events
3 826
Read events
3 825
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2648) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Users\admin\Desktop\LauncherforZapret.exe |
Value: ~ GDIDPISCALING DPIUNAWARE | |||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3504 | LauncherforZapret.exe | C:\Users\admin\AppData\Local\Temp\~DF6E50D07A421BA928.TMP | binary | |
MD5:52F39CEA0D9796E27A44F90E151620E9 | SHA256:D1E2727C0A1D5D3DC0F80F6E9B9D8B5DEF27C9CF811890BEA64495835D28B6D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
19
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.16:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.16:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6256 | RUXIMICS.exe | GET | 200 | 184.24.77.16:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6256 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6256 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.24.77.16:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.24.77.16:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6256 | RUXIMICS.exe | 184.24.77.16:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |