| File name: | Chromium Setup x64.exe |
| Full analysis: | https://app.any.run/tasks/76dc1c41-0c1d-4b4a-b3d2-9516cd9c2fb5 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2024, 12:47:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | B408E3DA98F0E457D627510165374DDD |
| SHA1: | 49DE055D881896670CE8B1BA1633D5F8B4F8E193 |
| SHA256: | 3C3F458400C557D279C4D4993F67ADC8BA3DA4BAD8FC844ADFEF8C7DE475A1F7 |
| SSDEEP: | 786432:cf9I04sVpGuNS6r0aMdCRzM9jhXtoe8qCs2VVsh48:cf9IvqGuS807dljhXqe2VVsh48 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- Chromium Setup x64.exe (PID: 2312)
The process creates files with name similar to system file names
- Chromium Setup x64.exe (PID: 2312)
Starts CMD.EXE for commands execution
- Chromium Setup x64.exe (PID: 2312)
- Teams.exe (PID: 4232)
Get information on the list of running processes
- cmd.exe (PID: 3028)
- Chromium Setup x64.exe (PID: 2312)
Executable content was dropped or overwritten
- Chromium Setup x64.exe (PID: 2312)
Drops 7-zip archiver for unpacking
- Chromium Setup x64.exe (PID: 2312)
Process drops legitimate windows executable
- Chromium Setup x64.exe (PID: 2312)
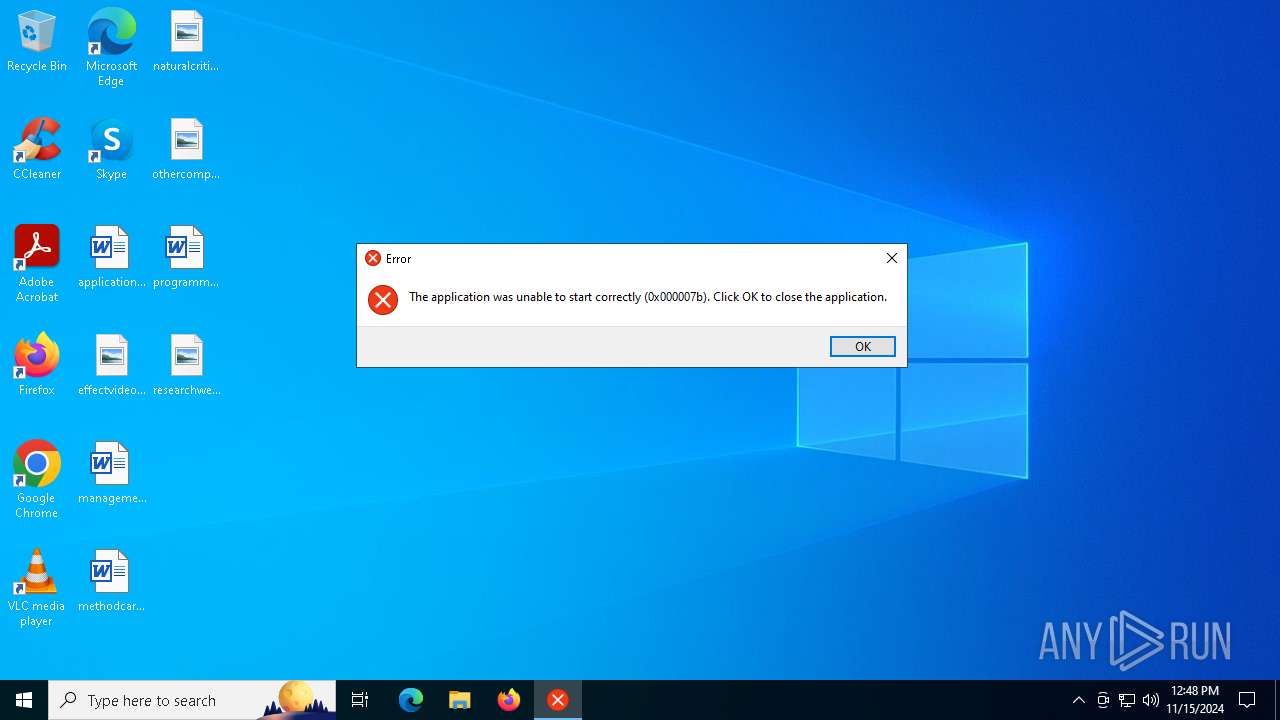
Application launched itself
- Teams.exe (PID: 4232)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7032)
Connects to unusual port
- Teams.exe (PID: 4232)
INFO
Checks supported languages
- Chromium Setup x64.exe (PID: 2312)
Reads the computer name
- Chromium Setup x64.exe (PID: 2312)
Create files in a temporary directory
- Chromium Setup x64.exe (PID: 2312)
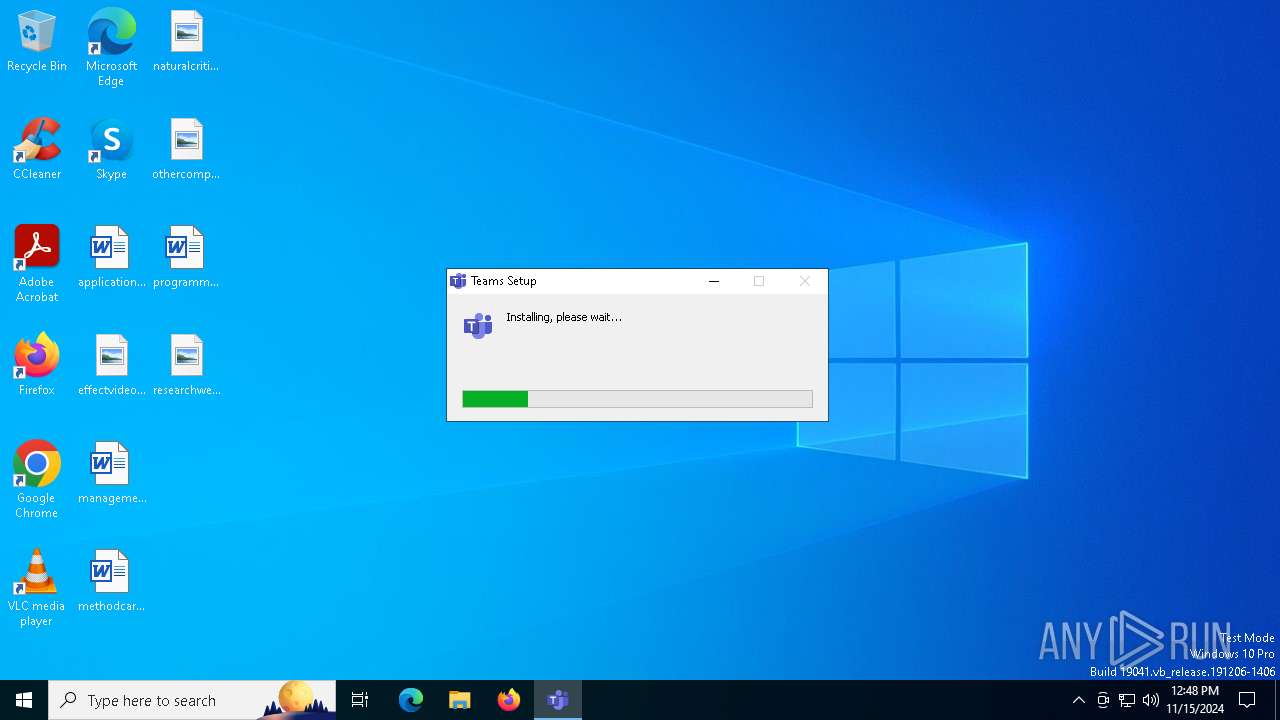
Manual execution by a user
- Teams.exe (PID: 4232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 22:26:14+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 473088 |
| UninitializedDataSize: | 16384 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.1.1.0 |
| ProductVersionNumber: | 5.1.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | - |
| FileVersion: | 5.1.1 |
| LegalCopyright: | Copyright © 2024 Teams |
| ProductName: | Teams |
| ProductVersion: | 5.1.1 |
Total processes
133
Monitored processes
11
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1884 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2312 | "C:\Users\admin\AppData\Local\Temp\Chromium Setup x64.exe" | C:\Users\admin\AppData\Local\Temp\Chromium Setup x64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.1.1 Modules
| |||||||||||||||
| 3000 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3028 | "C:\WINDOWS\system32\cmd.exe" /c tasklist /FI "USERNAME eq %USERNAME%" /FI "IMAGENAME eq Teams.exe" /FO csv | "C:\WINDOWS\system32\find.exe" "Teams.exe" | C:\Windows\SysWOW64\cmd.exe | — | Chromium Setup x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3972 | powershell "$s=(New-Object -COM WScript.Shell).CreateShortcut('C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\MyElectronApp.lnk');$s.TargetPath='C:\Users\admin\AppData\Local\Programs\Teams\Teams.exe';$s.Save()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4232 | "C:\Users\admin\AppData\Local\Programs\Teams\Teams.exe" | C:\Users\admin\AppData\Local\Programs\Teams\Teams.exe | explorer.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Teams Version: 5.1.1 Modules
| |||||||||||||||
| 5980 | "C:\Users\admin\AppData\Local\Programs\Teams\Teams.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\Teams" --field-trial-handle=2072,i,17582284235630167712,11660429960721029902,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2068 /prefetch:3 | C:\Users\admin\AppData\Local\Programs\Teams\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Teams Version: 5.1.1 Modules
| |||||||||||||||
| 6216 | tasklist /FI "USERNAME eq admin" /FI "IMAGENAME eq Teams.exe" /FO csv | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6224 | "C:\WINDOWS\system32\find.exe" "Teams.exe" | C:\Windows\SysWOW64\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6836 | "C:\Users\admin\AppData\Local\Programs\Teams\Teams.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\Teams" --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1736,i,17582284235630167712,11660429960721029902,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=1724 /prefetch:2 | C:\Users\admin\AppData\Local\Programs\Teams\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: Teams Version: 5.1.1 Modules
| |||||||||||||||
Total events
6 363
Read events
6 352
Write events
11
Delete events
0
Modification events
| (PID) Process: | (2312) Chromium Setup x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\8013f783-e1a2-5f53-80da-b1ad483bd59f |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\Teams | |||
| (PID) Process: | (2312) Chromium Setup x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\8013f783-e1a2-5f53-80da-b1ad483bd59f |
| Operation: | write | Name: | KeepShortcuts |
Value: true | |||
| (PID) Process: | (2312) Chromium Setup x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\8013f783-e1a2-5f53-80da-b1ad483bd59f |
| Operation: | write | Name: | ShortcutName |
Value: Teams | |||
| (PID) Process: | (2312) Chromium Setup x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\8013f783-e1a2-5f53-80da-b1ad483bd59f |
| Operation: | write | Name: | DisplayName |
Value: Teams 5.1.1 | |||
| (PID) Process: | (2312) Chromium Setup x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\8013f783-e1a2-5f53-80da-b1ad483bd59f |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\Teams\Uninstall Teams.exe" /currentuser | |||
| (PID) Process: | (2312) Chromium Setup x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\8013f783-e1a2-5f53-80da-b1ad483bd59f |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\Teams\Uninstall Teams.exe" /currentuser /S | |||
| (PID) Process: | (2312) Chromium Setup x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\8013f783-e1a2-5f53-80da-b1ad483bd59f |
| Operation: | write | Name: | DisplayVersion |
Value: 5.1.1 | |||
| (PID) Process: | (2312) Chromium Setup x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\8013f783-e1a2-5f53-80da-b1ad483bd59f |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\Programs\Teams\Teams.exe,0 | |||
| (PID) Process: | (2312) Chromium Setup x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\8013f783-e1a2-5f53-80da-b1ad483bd59f |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (2312) Chromium Setup x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\8013f783-e1a2-5f53-80da-b1ad483bd59f |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
Executable files
24
Suspicious files
98
Text files
6
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2312 | Chromium Setup x64.exe | C:\Users\admin\AppData\Local\Temp\nsx1A24.tmp\app-64.7z | — | |
MD5:— | SHA256:— | |||
| 2312 | Chromium Setup x64.exe | C:\Users\admin\AppData\Local\Temp\nsx1A24.tmp\7z-out\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 2312 | Chromium Setup x64.exe | C:\Users\admin\AppData\Local\Temp\nsx1A24.tmp\7z-out\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 2312 | Chromium Setup x64.exe | C:\Users\admin\AppData\Local\Temp\nsx1A24.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 2312 | Chromium Setup x64.exe | C:\Users\admin\AppData\Local\Temp\nsx1A24.tmp\7z-out\chrome_100_percent.pak | pgc | |
MD5:83EC43F2AF9FC52025F3F807B185D424 | SHA256:A659EE9EB38636F85F5336587C578FB29740D3EFFAFF9B92852C8A210E92978C | |||
| 2312 | Chromium Setup x64.exe | C:\Users\admin\AppData\Local\Temp\nsx1A24.tmp\7z-out\LICENSE.electron.txt | text | |
MD5:4D42118D35941E0F664DDDBD83F633C5 | SHA256:5154E165BD6C2CC0CFBCD8916498C7ABAB0497923BAFCD5CB07673FE8480087D | |||
| 2312 | Chromium Setup x64.exe | C:\Users\admin\AppData\Local\Temp\nsx1A24.tmp\StdUtils.dll | executable | |
MD5:C6A6E03F77C313B267498515488C5740 | SHA256:B72E9013A6204E9F01076DC38DABBF30870D44DFC66962ADBF73619D4331601E | |||
| 2312 | Chromium Setup x64.exe | C:\Users\admin\AppData\Local\Temp\nsx1A24.tmp\nsis7z.dll | executable | |
MD5:80E44CE4895304C6A3A831310FBF8CD0 | SHA256:B393F05E8FF919EF071181050E1873C9A776E1A0AE8329AEFFF7007D0CADF592 | |||
| 2312 | Chromium Setup x64.exe | C:\Users\admin\AppData\Local\Temp\nsx1A24.tmp\SpiderBanner.dll | executable | |
MD5:17309E33B596BA3A5693B4D3E85CF8D7 | SHA256:996A259E53CA18B89EC36D038C40148957C978C0FD600A268497D4C92F882A93 | |||
| 2312 | Chromium Setup x64.exe | C:\Users\admin\AppData\Local\Temp\nsx1A24.tmp\7z-out\chrome_200_percent.pak | pgc | |
MD5:DC48A33BD20BFC7CACFC925A84B015B6 | SHA256:2C1B3E4B8A0CF837AE0A390FCA54F45D7D22418E040F1DFEA979622383ACCED6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
40
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6596 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4360 | SearchApp.exe | 2.23.209.137:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.209.133:443 | th.bing.com | Akamai International B.V. | GB | whitelisted |
4360 | SearchApp.exe | 2.23.209.133:443 | th.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Misc activity | ET INFO Observed DNS Query to .zip TLD |