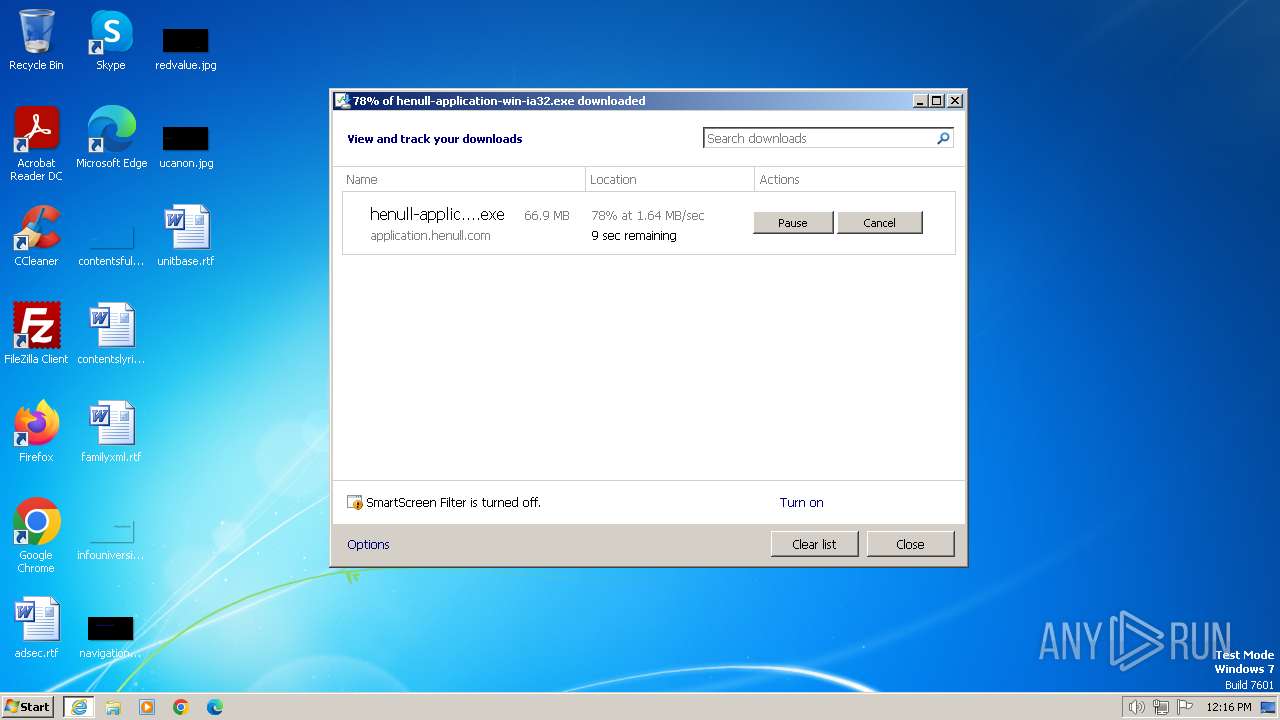
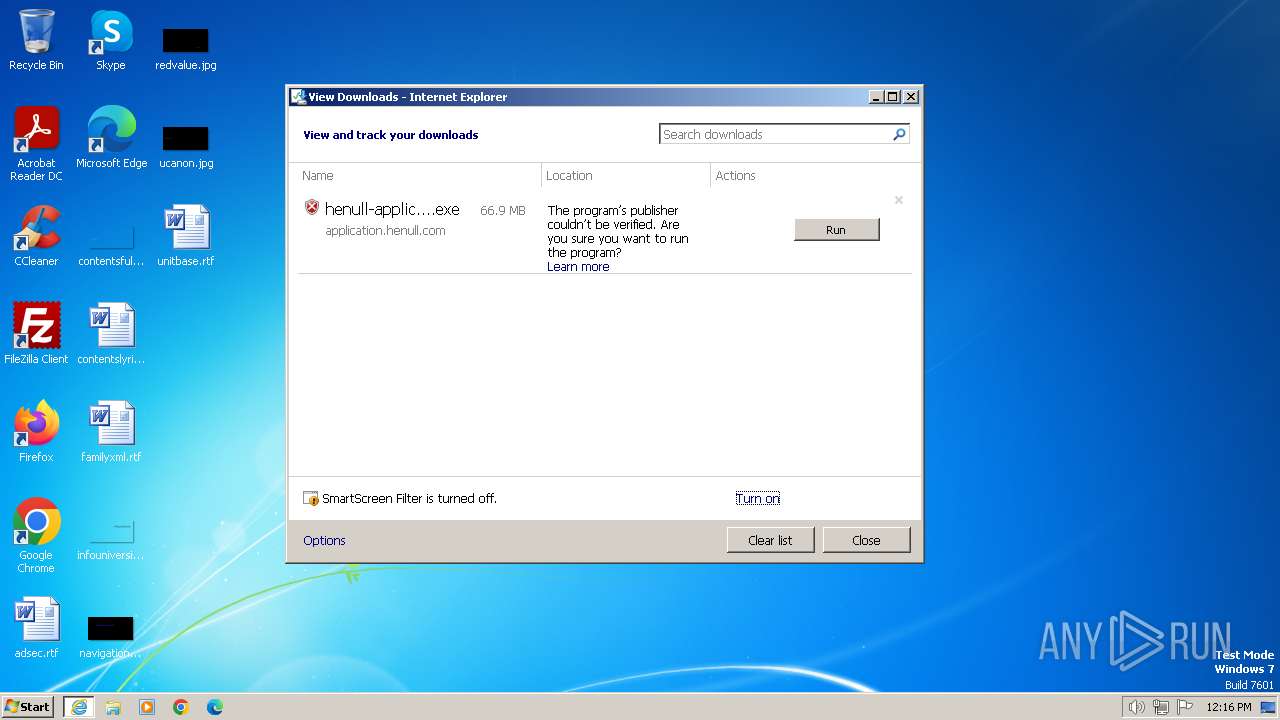
| URL: | https://application.henull.com/henull-application-win-ia32.exe |
| Full analysis: | https://app.any.run/tasks/9d4ff2b4-8654-4bfc-8813-f6123791d44f |
| Verdict: | Malicious activity |
| Analysis date: | February 23, 2024, 12:15:28 |
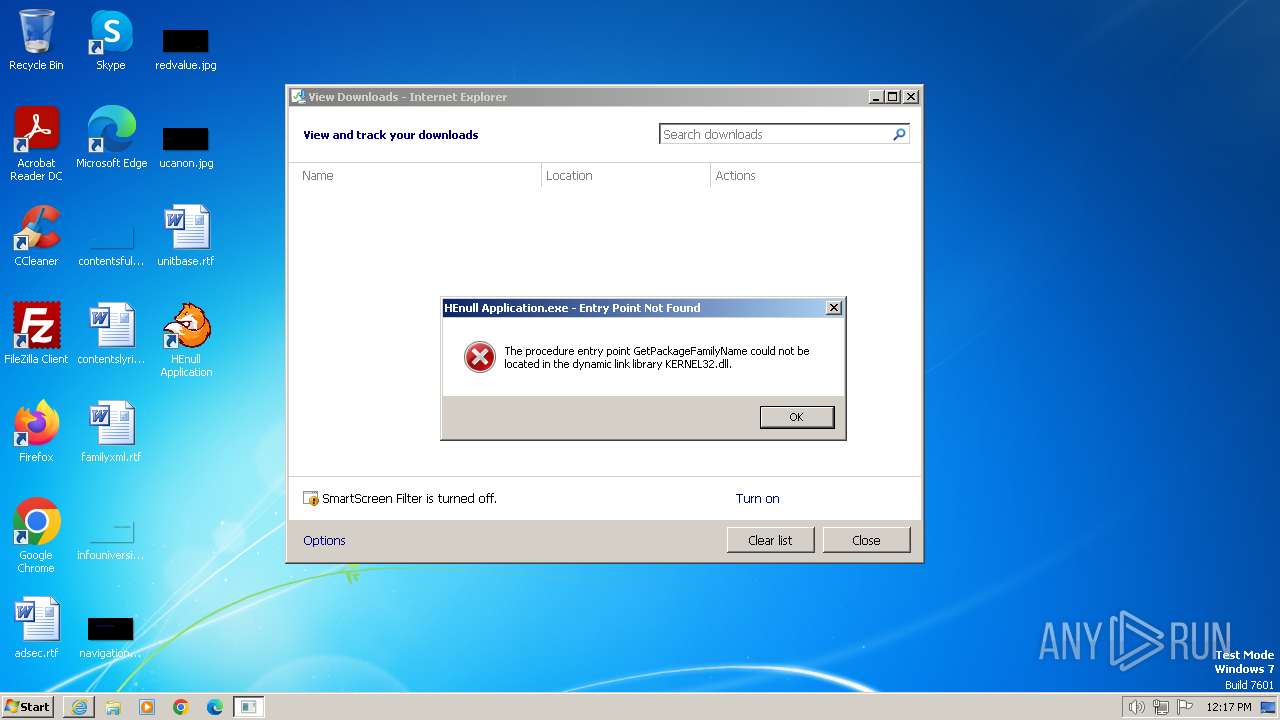
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C6AD256E5D3A9E7398C156EBAABF16AD |
| SHA1: | 038CBB1EFAAAF157F157C1CC8D3007E841BA9B37 |
| SHA256: | 3C3CE05F64DC9CF021BA73CB0A45898B628F2930FEBD532539A12B6BE837B65E |
| SSDEEP: | 3:N8aCdMQekJZAkH5BH4MQ7LA:2aEoCHD |
MALICIOUS
Drops the executable file immediately after the start
- henull-application-win-ia32.exe (PID: 2072)
Actions looks like stealing of personal data
- henull-application-win-ia32.exe (PID: 2072)
SUSPICIOUS
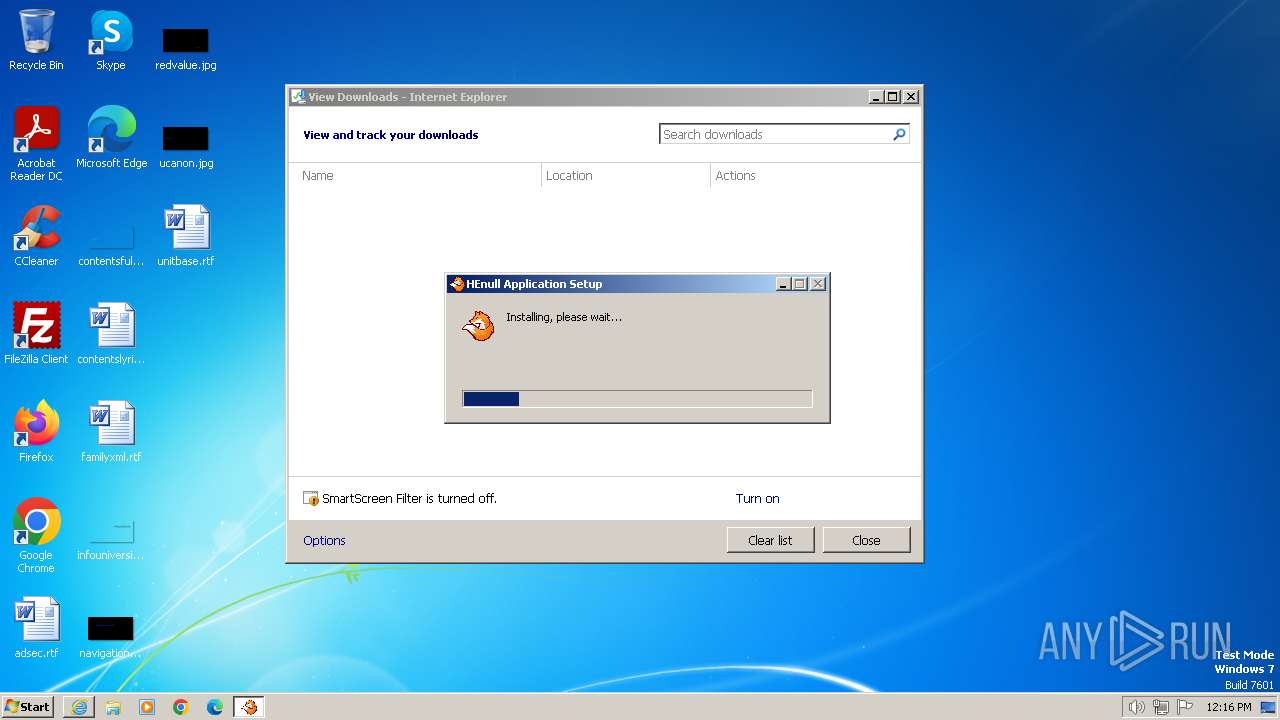
Malware-specific behavior (creating "System.dll" in Temp)
- henull-application-win-ia32.exe (PID: 2072)
Get information on the list of running processes
- henull-application-win-ia32.exe (PID: 2072)
- cmd.exe (PID: 2596)
- ns18D0.tmp (PID: 3776)
The process creates files with name similar to system file names
- henull-application-win-ia32.exe (PID: 2072)
Starts application with an unusual extension
- henull-application-win-ia32.exe (PID: 2072)
Drops 7-zip archiver for unpacking
- henull-application-win-ia32.exe (PID: 2072)
Executable content was dropped or overwritten
- henull-application-win-ia32.exe (PID: 2072)
Starts CMD.EXE for commands execution
- ns18D0.tmp (PID: 3776)
Creates a software uninstall entry
- henull-application-win-ia32.exe (PID: 2072)
Process drops legitimate windows executable
- henull-application-win-ia32.exe (PID: 2072)
INFO
Application launched itself
- iexplore.exe (PID: 2472)
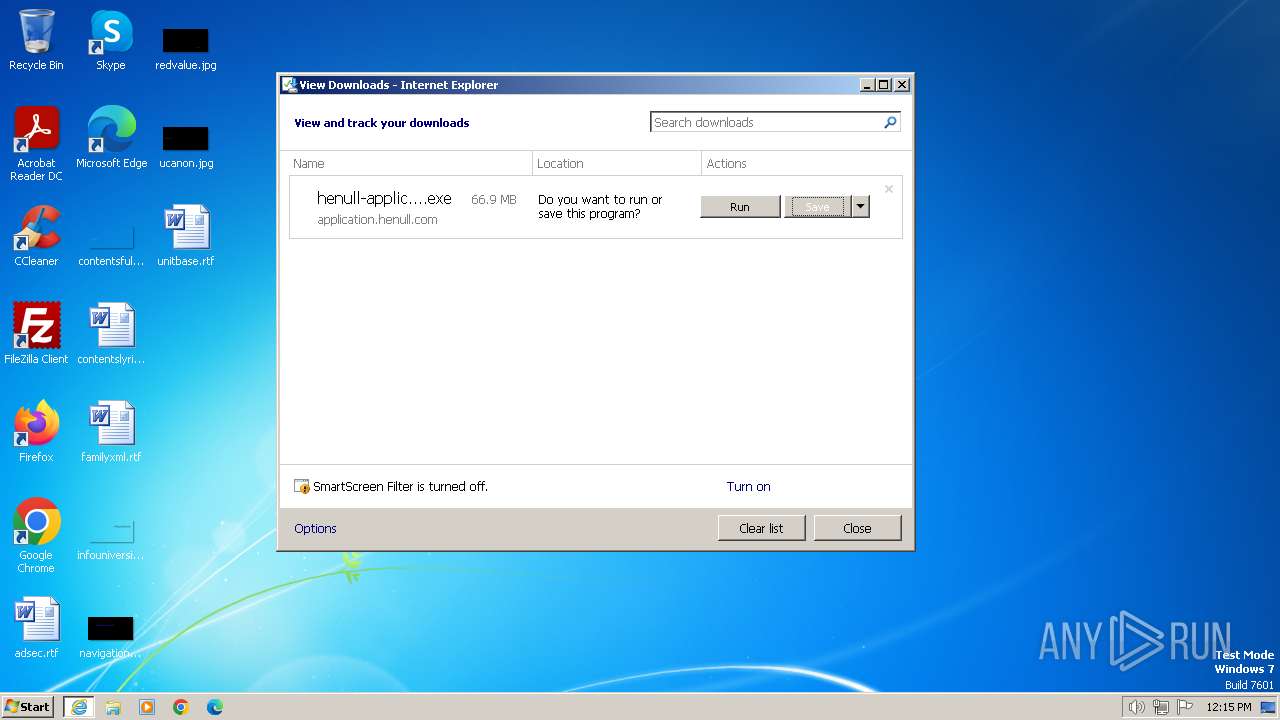
Modifies the phishing filter of IE
- iexplore.exe (PID: 2472)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3348)
Checks supported languages
- henull-application-win-ia32.exe (PID: 2072)
- ns18D0.tmp (PID: 3776)
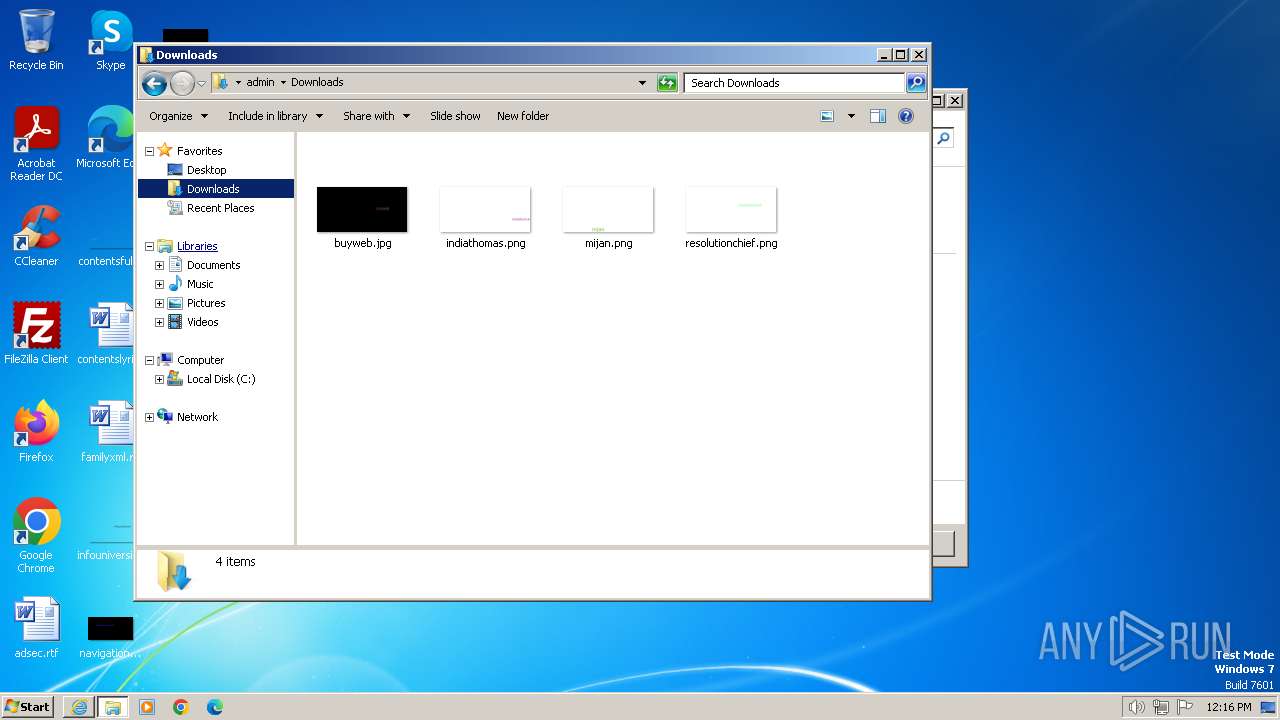
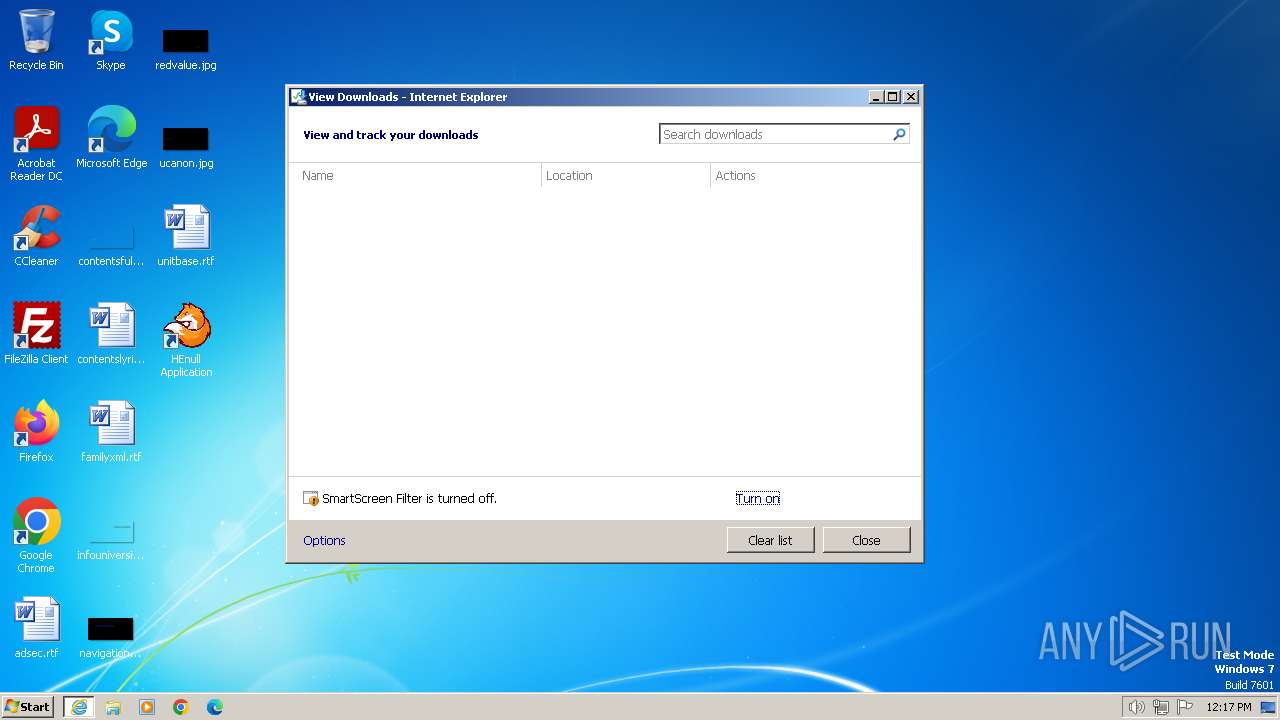
Manual execution by a user
- explorer.exe (PID: 2860)
- HEnull Application.exe (PID: 3616)
- HEnull Application.exe (PID: 1864)
Reads the computer name
- henull-application-win-ia32.exe (PID: 2072)
Drops the executable file immediately after the start
- iexplore.exe (PID: 3348)
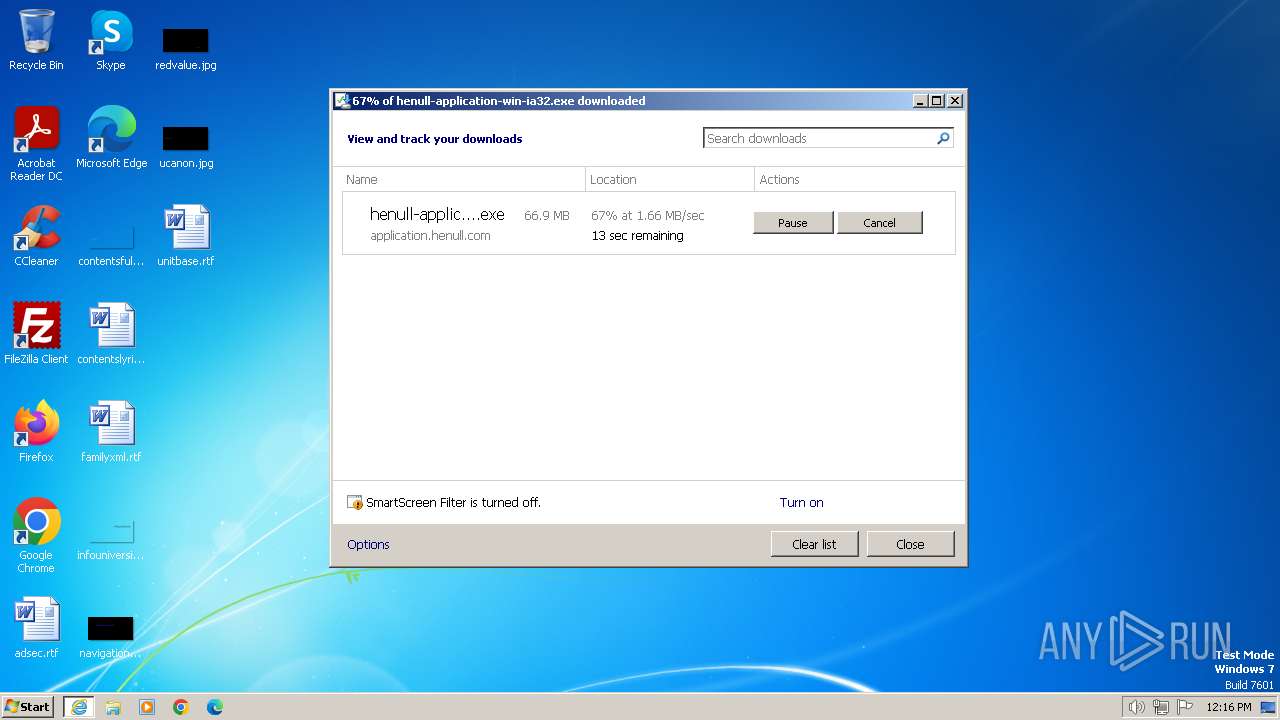
The process uses the downloaded file
- iexplore.exe (PID: 2472)
- henull-application-win-ia32.exe (PID: 2072)
Create files in a temporary directory
- henull-application-win-ia32.exe (PID: 2072)
Creates files or folders in the user directory
- henull-application-win-ia32.exe (PID: 2072)
Reads the machine GUID from the registry
- henull-application-win-ia32.exe (PID: 2072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1860 | tasklist /FI "USERNAME eq admin" /FI "IMAGENAME eq HEnull Application.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
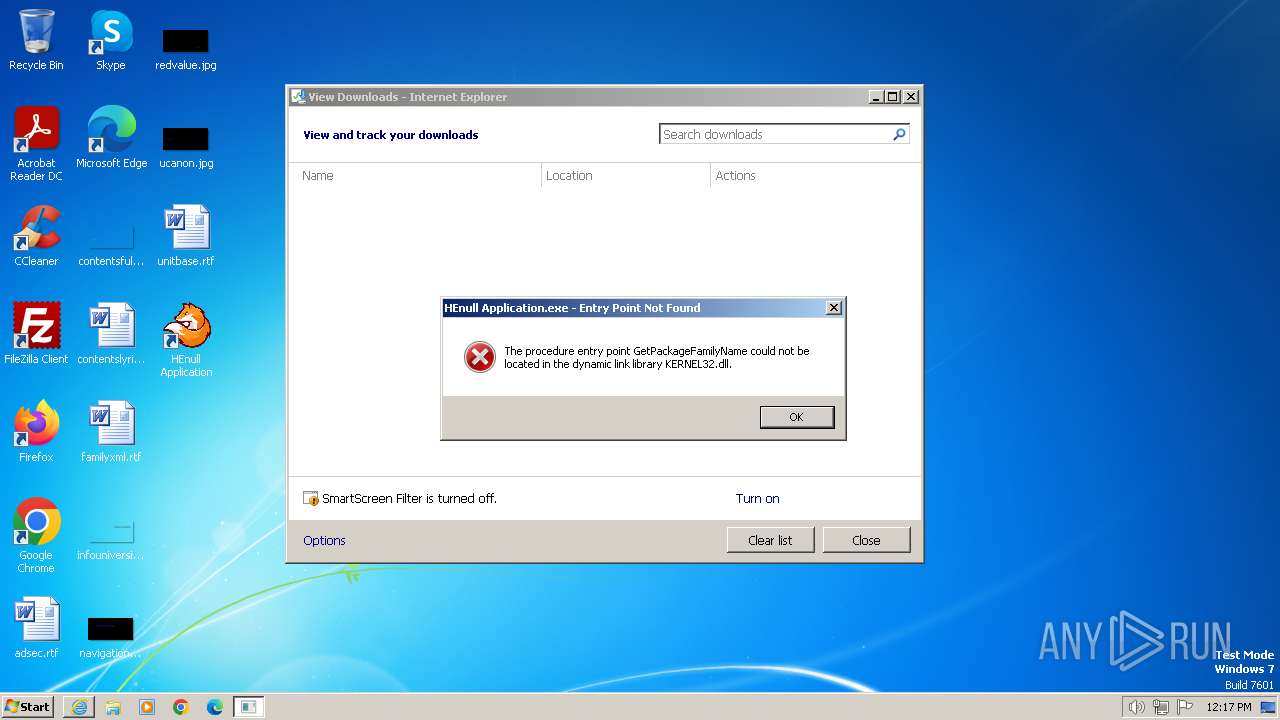
| 1864 | "C:\Users\admin\AppData\Local\Programs\henull-application\HEnull Application.exe" | C:\Users\admin\AppData\Local\Programs\henull-application\HEnull Application.exe | — | explorer.exe | |||||||||||
User: admin Company: nice Integrity Level: MEDIUM Description: HEnull Application Exit code: 3221225785 Version: 1.8.0 Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\henull-application-win-ia32.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\henull-application-win-ia32.exe | iexplore.exe | ||||||||||||
User: admin Company: nice Integrity Level: MEDIUM Exit code: 0 Version: 1.8.0 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://application.henull.com/henull-application-win-ia32.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2596 | cmd /c tasklist /FI "USERNAME eq %USERNAME%" /FI "IMAGENAME eq HEnull Application.exe" | %SYSTEMROOT%\System32\find.exe "HEnull Application.exe" | C:\Windows\System32\cmd.exe | — | ns18D0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2832 | C:\Windows\System32\find.exe "HEnull Application.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2860 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3348 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2472 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3616 | "C:\Users\admin\AppData\Local\Programs\henull-application\HEnull Application.exe" | C:\Users\admin\AppData\Local\Programs\henull-application\HEnull Application.exe | — | explorer.exe | |||||||||||
User: admin Company: nice Integrity Level: MEDIUM Description: HEnull Application Exit code: 0 Version: 1.8.0 Modules
| |||||||||||||||
| 3776 | "C:\Users\admin\AppData\Local\Temp\nsv1852.tmp\ns18D0.tmp" cmd /c tasklist /FI "USERNAME eq %USERNAME%" /FI "IMAGENAME eq HEnull Application.exe" | %SYSTEMROOT%\System32\find.exe "HEnull Application.exe" | C:\Users\admin\AppData\Local\Temp\nsv1852.tmp\ns18D0.tmp | — | henull-application-win-ia32.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
23 481
Read events
23 355
Write events
98
Delete events
28
Modification events
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 35507632 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31090258 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 335507632 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31090258 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
25
Suspicious files
146
Text files
615
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:65B2324331817BE0F8D8192FD5D75F5E | SHA256:5460A926EE84DBA605BBE833CC262E906C60288E722E5F8A5C85317180B1D40E | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:0592A654F5C478ECB7C82CB1427D2E6B | SHA256:BC55B3D87F98232A8AB898545A4377689D965514735CEDAD003A9D964B28CC7E | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\TKL3OVX9.txt | text | |
MD5:C0A080E857FBFD434CFD4958DBC36448 | SHA256:49DC2DFA0EED1FCBC8BB6AF30BD523D3680E2154558F51371EB80361C9CD4099 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver6AFA.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_C0427F5F77D9B3A439FC620EDAAB6177 | binary | |
MD5:7C4B1E22AD769F8289E481981C45370A | SHA256:D0284B1BF3D1BF2BC45A025B1793D6169779B7B320C462AB61E1632F15B0DEE3 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\8R3SVPK4.txt | text | |
MD5:F37B6CF1B997AE59BA8FED2F7C80B82E | SHA256:1AE2EFD9E36BC46D728393AD20FC8D59C15B7B624FEAD712FFA91B0B7C918867 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\henull-application-win-ia32.exe.uednp5o.partial | — | |
MD5:— | SHA256:— | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\PDM0SS7N.txt | text | |
MD5:8DCFEDDE38E1E8ABAABCDC3A31C02400 | SHA256:1F12BED905E47FF2D35704A881FCA4B0E7FE5C6AAF4848CB7745B8845368AF12 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
20
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3348 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bd117e088266f0f9 | unknown | — | — | unknown |
3348 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | unknown | — | — | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a414549a770d7263 | unknown | compressed | 65.2 Kb | unknown |
3348 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
2472 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?89bca2e7018c82c0 | unknown | compressed | 65.2 Kb | unknown |
2472 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | unknown | binary | 471 b | unknown |
2472 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
2472 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3348 | iexplore.exe | 188.114.97.3:443 | application.henull.com | CLOUDFLARENET | NL | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3348 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3348 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2472 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
2472 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2472 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
application.henull.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |