| File name: | zulasetup.exe |
| Full analysis: | https://app.any.run/tasks/0687b509-c044-4ddb-b883-bbeb5190ed24 |
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2024, 18:45:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 24C1A81CAA52C5506902AF67399C9603 |
| SHA1: | DA96DAB45AC9212C23216019F2A1CF0130CF4313 |
| SHA256: | 3C3928B7B8029C0879E2EF9BCBA326DD713D19C0C98192C7913A3A4B7BF5E35F |
| SSDEEP: | 98304:ks9w7LxbXKotRLcbzbiy/2FFugKETxxqkJSABE3+nXgx751qRepUAUlrYStyGgM9:HyaI14SJ42eD8pHv |
MALICIOUS
Scans artifacts that could help determine the target
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
SUSPICIOUS
Reads security settings of Internet Explorer
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
Reads Microsoft Outlook installation path
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
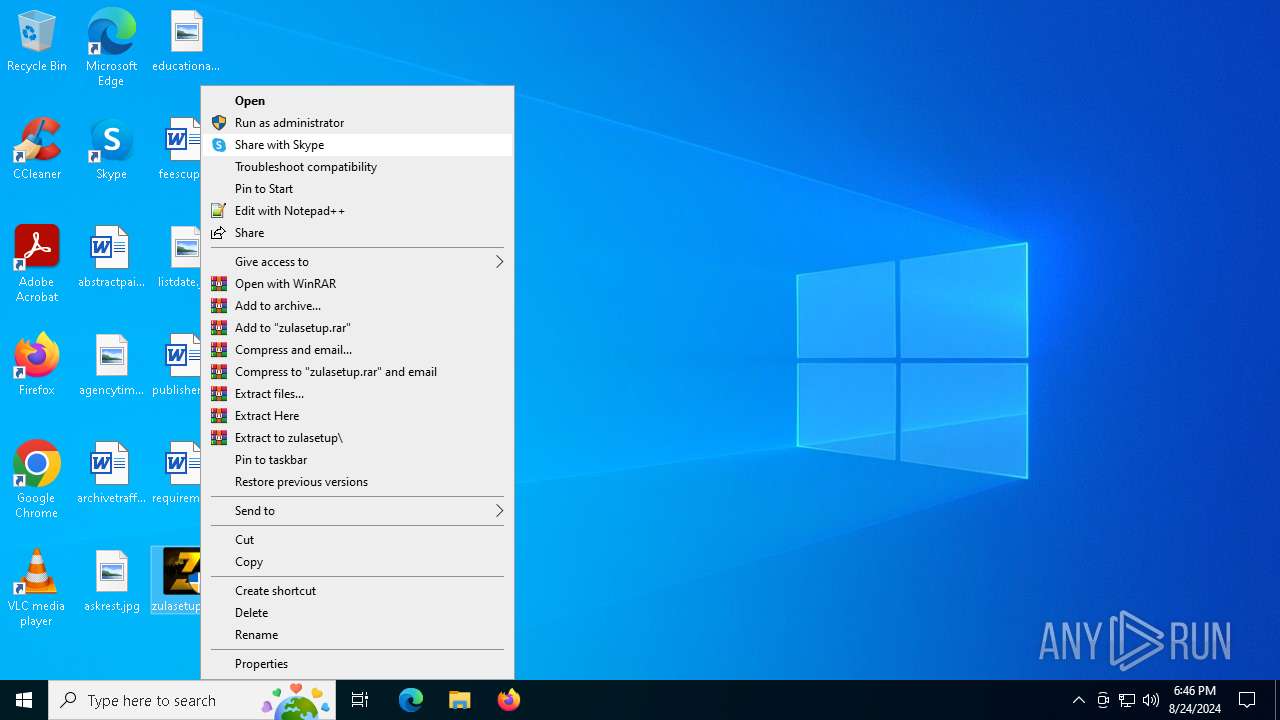
Drops the executable file immediately after the start
- zulasetup.exe (PID: 6736)
- zulasetup.exe (PID: 6452)
Checks Windows Trust Settings
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
Executable content was dropped or overwritten
- zulasetup.exe (PID: 6736)
- zulasetup.exe (PID: 6452)
Reads Internet Explorer settings
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
There is functionality for taking screenshot (YARA)
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
INFO
Creates files or folders in the user directory
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
Checks supported languages
- autorun.exe (PID: 6840)
- zulasetup.exe (PID: 6736)
- zulasetup.exe (PID: 6452)
- autorun.exe (PID: 6392)
Checks proxy server information
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
Process checks Internet Explorer phishing filters
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
Reads CPU info
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
Reads the computer name
- zulasetup.exe (PID: 6736)
- autorun.exe (PID: 6840)
- zulasetup.exe (PID: 6452)
- autorun.exe (PID: 6392)
Process checks computer location settings
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
Create files in a temporary directory
- zulasetup.exe (PID: 6736)
- autorun.exe (PID: 6840)
- zulasetup.exe (PID: 6452)
- autorun.exe (PID: 6392)
Reads the machine GUID from the registry
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
Reads the software policy settings
- autorun.exe (PID: 6840)
- autorun.exe (PID: 6392)
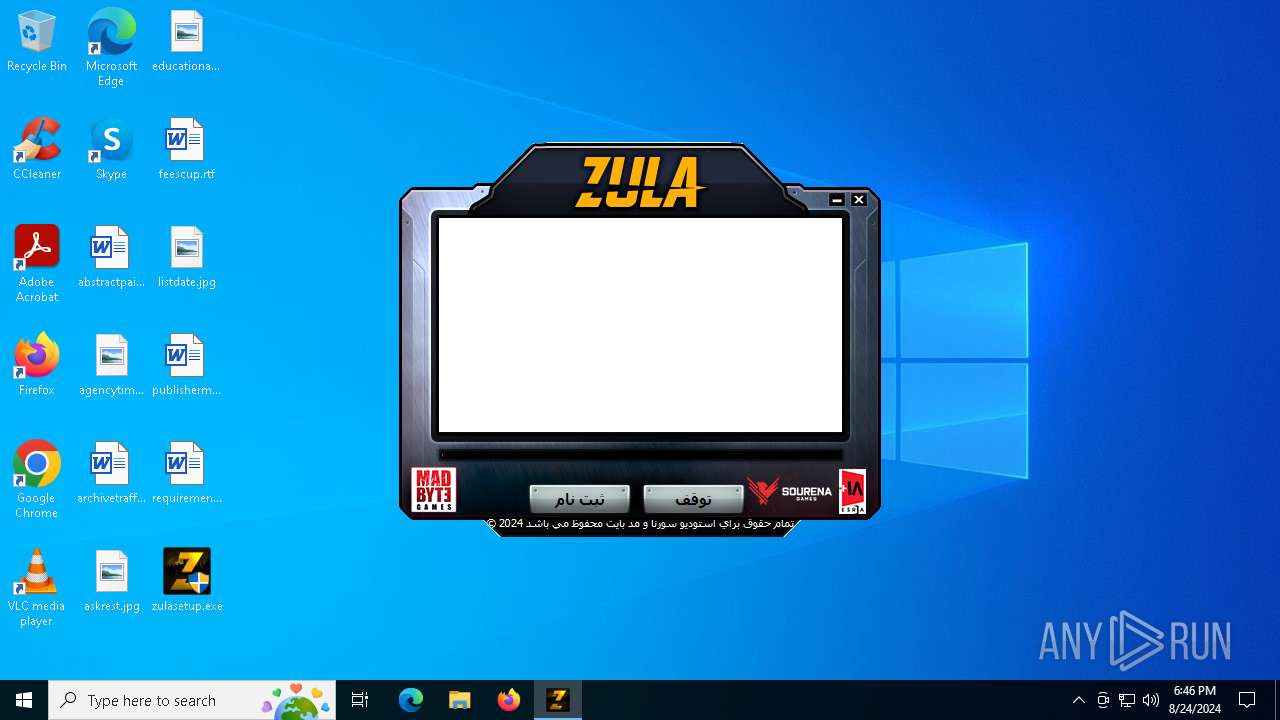
Manual execution by a user
- zulasetup.exe (PID: 6452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (56.1) |
|---|---|---|
| .scr | | | Windows screen saver (26.6) |
| .exe | | | Win32 Executable (generic) (9.1) |
| .exe | | | Generic Win/DOS Executable (4) |
| .exe | | | DOS Executable Generic (4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:09 13:12:53+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 259584 |
| InitializedDataSize: | 375296 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2cbbc |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.16.4.22 |
| ProductVersionNumber: | 1.23.7.17 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | Created with AutoPlay Media Studio (www.indigorose.com) |
| CompanyName: | MadByte Games |
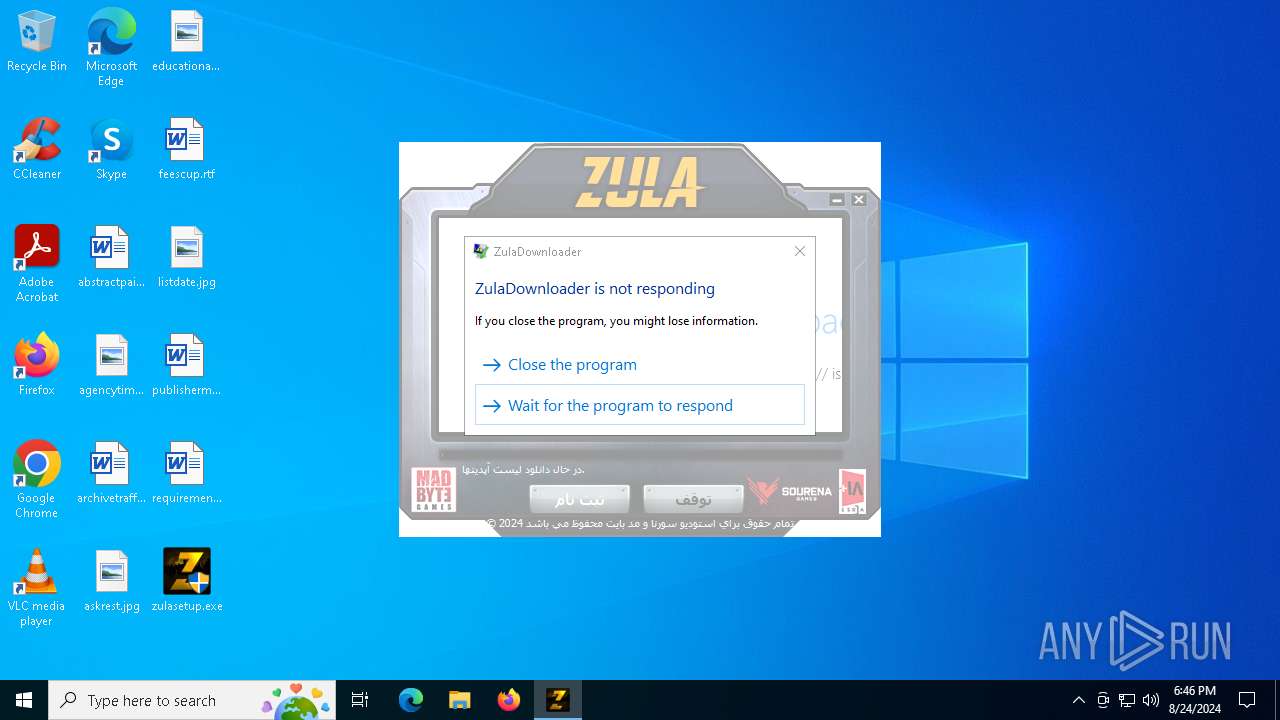
| FileDescription: | ZulaDownloader |
| FileVersion: | 1.16.4.22 |
| InternalName: | ams_launch |
| LegalCopyright: | Runtime Engine Copyright © 2015 MadByte Games (www.madbytegames.com) |
| OriginalFileName: | zula_downloader.exe |
| ProductName: | Zula Game |
| ProductVersion: | 1.23.7.17 |
Total processes
131
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6392 | "C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\autorun.exe" "SFXSOURCE:C:\Users\admin\Desktop\zulasetup.exe" | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\autorun.exe | zulasetup.exe | ||||||||||||
User: admin Company: MadByte Games Integrity Level: HIGH Description: ZulaDownloader Exit code: 3489660927 Version: 1.16.4.22 Modules
| |||||||||||||||
| 6452 | "C:\Users\admin\Desktop\zulasetup.exe" | C:\Users\admin\Desktop\zulasetup.exe | explorer.exe | ||||||||||||
User: admin Company: MadByte Games Integrity Level: HIGH Description: ZulaDownloader Exit code: 3489660927 Version: 1.16.4.22 Modules
| |||||||||||||||
| 6688 | "C:\Users\admin\Desktop\zulasetup.exe" | C:\Users\admin\Desktop\zulasetup.exe | — | explorer.exe | |||||||||||
User: admin Company: MadByte Games Integrity Level: MEDIUM Description: ZulaDownloader Exit code: 3221226540 Version: 1.16.4.22 Modules
| |||||||||||||||
| 6736 | "C:\Users\admin\Desktop\zulasetup.exe" | C:\Users\admin\Desktop\zulasetup.exe | explorer.exe | ||||||||||||
User: admin Company: MadByte Games Integrity Level: HIGH Description: ZulaDownloader Exit code: 0 Version: 1.16.4.22 Modules
| |||||||||||||||
| 6840 | "C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\autorun.exe" "SFXSOURCE:C:\Users\admin\Desktop\zulasetup.exe" | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\autorun.exe | zulasetup.exe | ||||||||||||
User: admin Company: MadByte Games Integrity Level: HIGH Description: ZulaDownloader Exit code: 0 Version: 1.16.4.22 Modules
| |||||||||||||||
Total events
10 200
Read events
10 171
Write events
27
Delete events
2
Modification events
| (PID) Process: | (6840) autorun.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (6840) autorun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6840) autorun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6840) autorun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6840) autorun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6840) autorun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6840) autorun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6840) autorun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6840) autorun.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Explorer\ControlPanel\NameSpace |
| Operation: | write | Name: | 3540227f04db7071 |
Value: R4c2edMqzSrUIgAuGjCSFFLC1Ak5eznt3zyg7MiRF3SySd+Ea8vXtlsGTH+NfRKl | |||
| (PID) Process: | (6840) autorun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
Executable files
10
Suspicious files
38
Text files
96
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6736 | zulasetup.exe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\btnkapat.btn | compressed | |
MD5:67C351D9E4BDEB9CEA0CC9490297DAD9 | SHA256:71A648090997F2F854972F40531D13CB5ADED056A9D0B57FBB9DC4DB60FE5EFA | |||
| 6736 | zulasetup.exe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\btninstall.btn | compressed | |
MD5:DFBE1F166E60EB6354D9A1EB5E67E189 | SHA256:C65B6A47375B4640F0AE817B94FB09271D79AA57A2BA3C354CA411074C9EF4B2 | |||
| 6736 | zulasetup.exe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\btnsimge.btn | compressed | |
MD5:35A7E4A24AC8D0E0D548A99E4410E6BB | SHA256:12B112DE0021AC3214B768EF7CE1C10959AA14BBE4442FB332C5DD81D63B95A0 | |||
| 6736 | zulasetup.exe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Audio\High1.ogg | ogg | |
MD5:FC2A595F574B1EAD82A6DCF06492C985 | SHA256:EE9A4903A8DF90EFF4C5B65A8073E564A3581CF73772A72EB82396E69932E769 | |||
| 6736 | zulasetup.exe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\btnok.btn | compressed | |
MD5:DA6C17C47D3C01FB78C75D6BD873C477 | SHA256:E79617A4B1431E51AB43C325B559BB2AB19415BE8B5D515D78279A0D31A67C9D | |||
| 6736 | zulasetup.exe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\0002-royale.btn | compressed | |
MD5:0B933456BBFFD11B50F14F391A4B0695 | SHA256:89786C6CC4CBF430C9AEE1F8131EFEFF8A4ADF6617535AADE525FA909441A38F | |||
| 6736 | zulasetup.exe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\btn_start.btn | compressed | |
MD5:A477DEC8ACFF26DAFFD4882E3682608C | SHA256:D035A8C02B2BB4DEE98C570366C924B834D41ABA9A17E3EDCA1F679DB27D7283 | |||
| 6736 | zulasetup.exe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\lokumgames_logo.btn | compressed | |
MD5:F96D877D3C872935FC811A08F7EA7B39 | SHA256:84999067593C4337188A2F970AB297627A8D37B90BB9E5BAEB7A9B7B5739A32F | |||
| 6736 | zulasetup.exe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\esra_logo.btn | compressed | |
MD5:4F602F60C6425B79A6F001E9C42523E8 | SHA256:A932F2641107EE1D889F8742C625A919290654C85E828E57A5B321B5595FD1E0 | |||
| 6736 | zulasetup.exe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\btn_ok.btn | compressed | |
MD5:607F5DC3C8F7F3523758C653BDFB70B0 | SHA256:84CF57B9C8BB6A91ABAC271CD91E32162BB566A90B61217D60C89DD2880D50C2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
22
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6840 | autorun.exe | GET | 200 | 142.250.74.206:80 | http://www.google-analytics.com/collect?ev=1&el=Start&ea=Start&cid=fb59%2d33f5a315%2de7b9%2d10019045%2d40902565%2dbf11&ec=Downloader&t=event&tid=UA%2d60166227%2d7&v=1 | unknown | — | — | whitelisted |
6392 | autorun.exe | GET | 200 | 142.250.74.206:80 | http://www.google-analytics.com/collect?ev=1&el=Start&ea=Start&cid=fb59%2d33f5a315%2de7b9%2d10019045%2d40902565%2dbf11&ec=Downloader&t=event&tid=UA%2d60166227%2d7&v=1 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
2096 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2456 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6840 | autorun.exe | 194.50.216.44:443 | account.zula.ir | Sourena Pardazesh Arya Software co. LLC | IR | unknown |
6840 | autorun.exe | 142.250.74.206:80 | www.google-analytics.com | GOOGLE | US | whitelisted |
4324 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6840 | autorun.exe | 194.50.216.54:443 | zulaapi.zula.ir | Sourena Pardazesh Arya Software co. LLC | IR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
account.zula.ir |
| whitelisted |
www.google-analytics.com |
| whitelisted |
zulaapi.zula.ir |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |