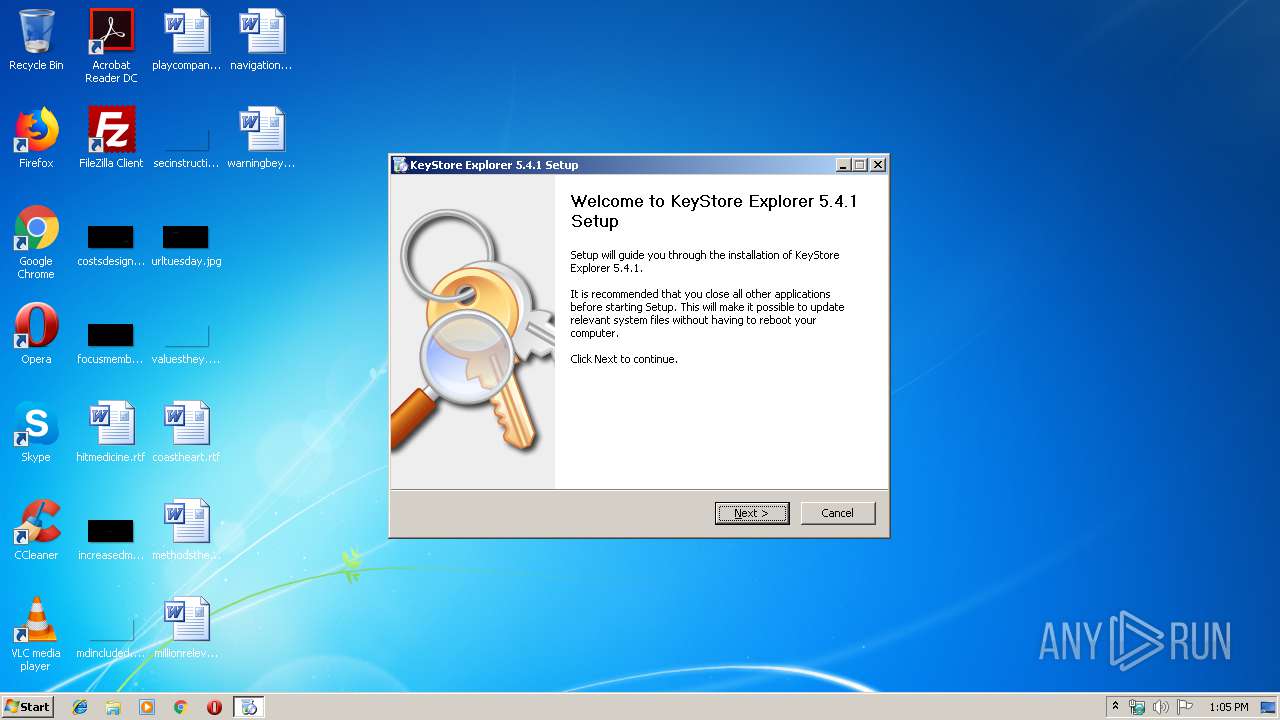
| File name: | kse-541-setup.exe |
| Full analysis: | https://app.any.run/tasks/95b6b2e6-f40a-4cea-b1e8-ae81fbcf3fd0 |
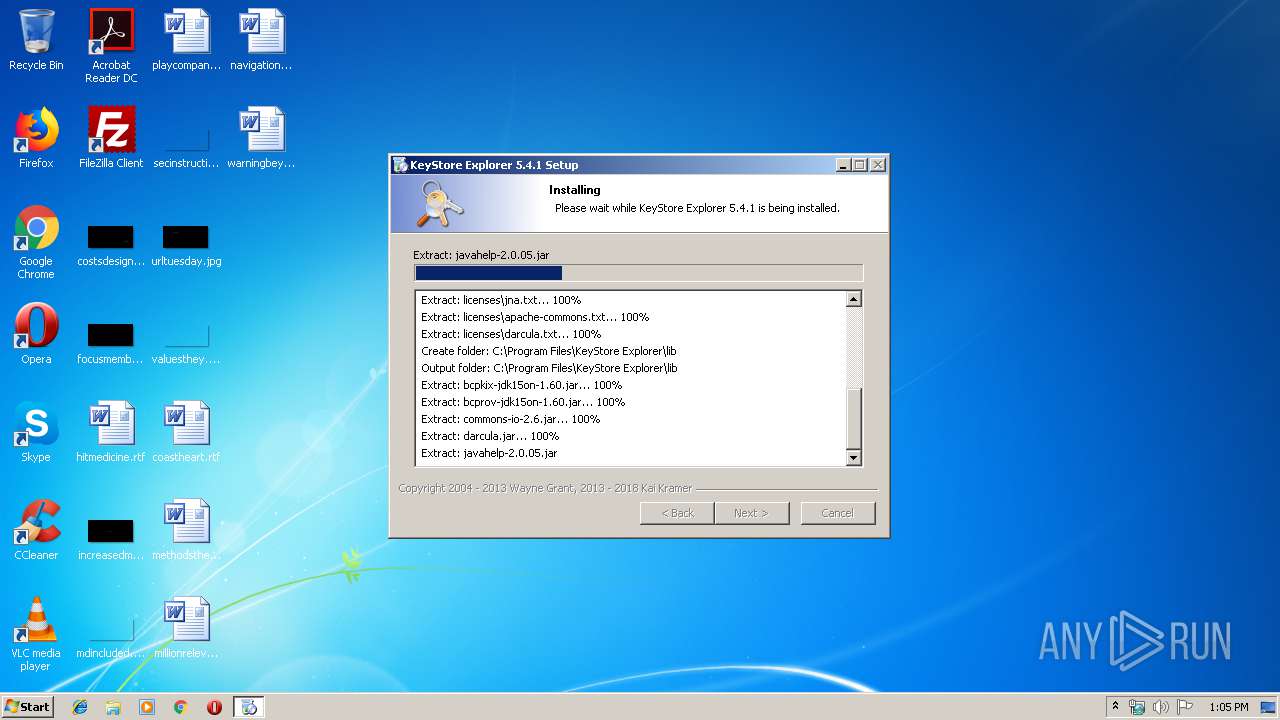
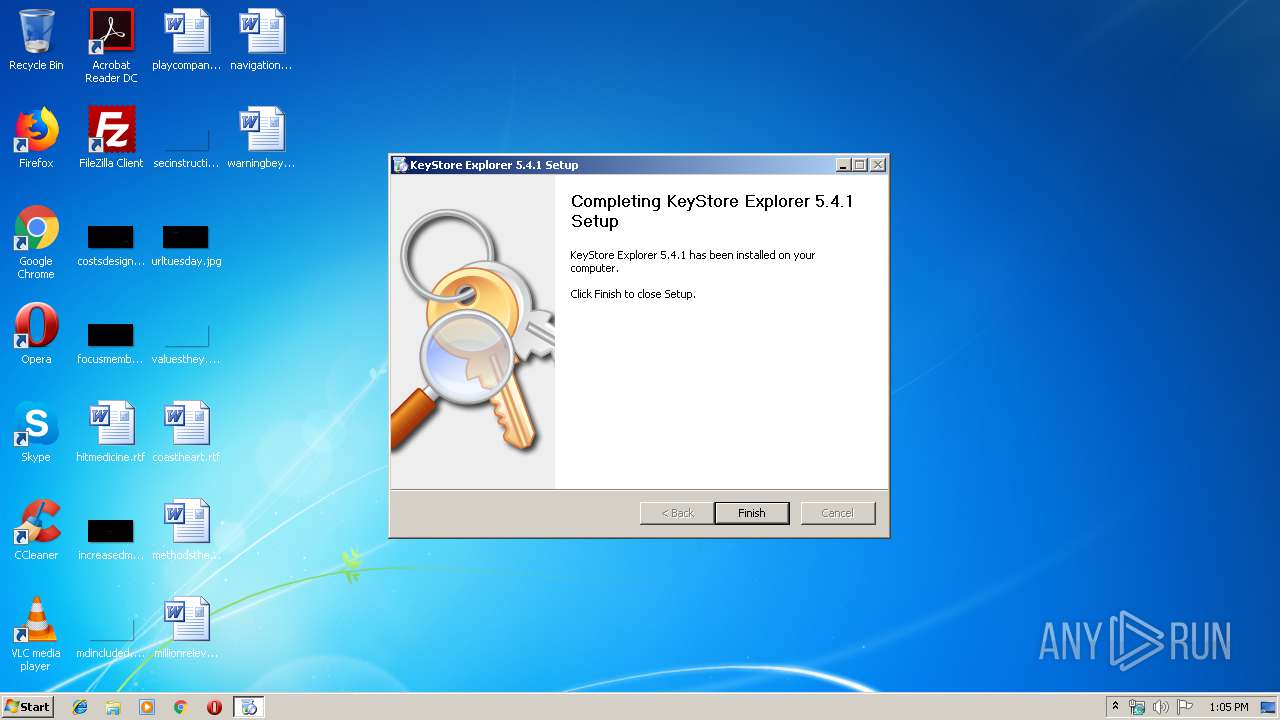
| Verdict: | Malicious activity |
| Analysis date: | June 06, 2019, 12:05:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E1CD6E247D912E014A5C45FA596C5883 |
| SHA1: | 8E69B34EAB93DBC448C6A6B9E1351DF701F50BDB |
| SHA256: | 3C345843A8743B573BBE6965A137FF8C11EA676C708B536D35E3A53D3AACA8E7 |
| SSDEEP: | 196608:tf3reqkNje/440IVGSF7GZQStY1ztjU/Xp97FxR/XUcslEw0+sDSVuyQ:kqb0mlF6Z1EVsXDFxRwCwjGd |
MALICIOUS
Loads dropped or rewritten executable
- kse-541-setup.exe (PID: 3668)
- javaw.exe (PID: 3556)
Application was dropped or rewritten from another process
- kse.exe (PID: 3056)
SUSPICIOUS
Executable content was dropped or overwritten
- kse-541-setup.exe (PID: 3668)
- javaw.exe (PID: 3556)
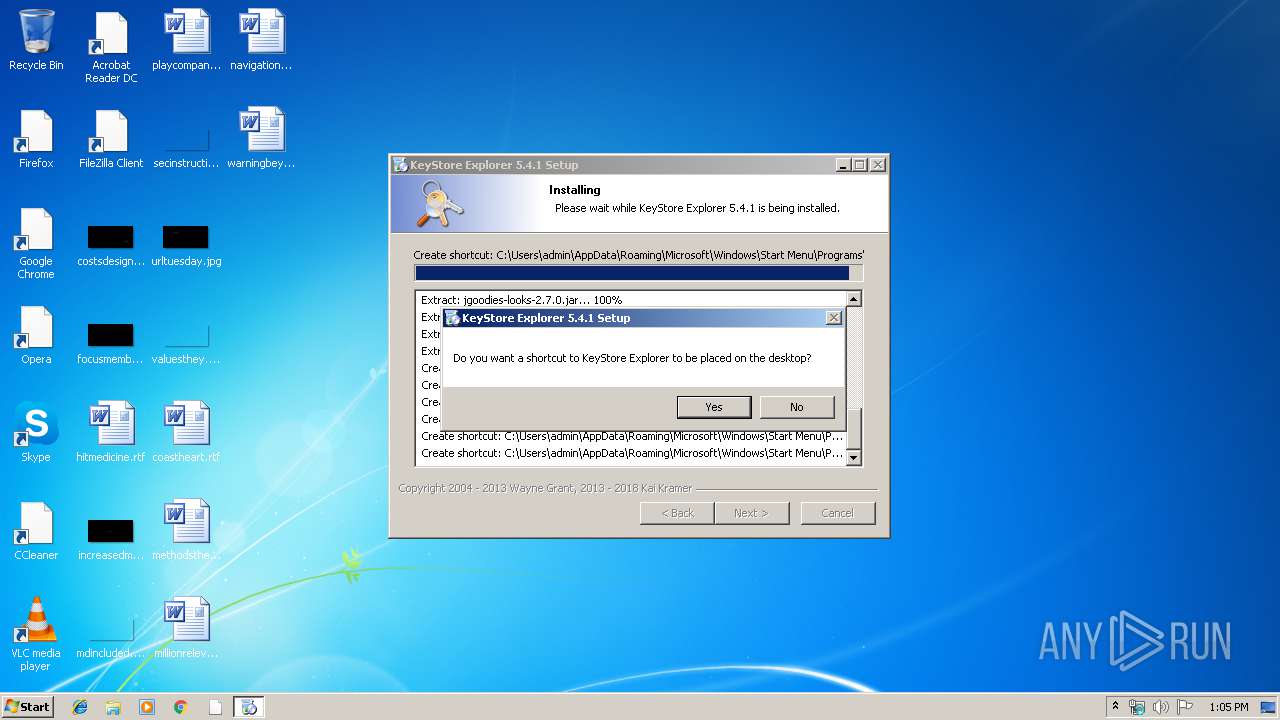
Modifies the open verb of a shell class
- kse-541-setup.exe (PID: 3668)
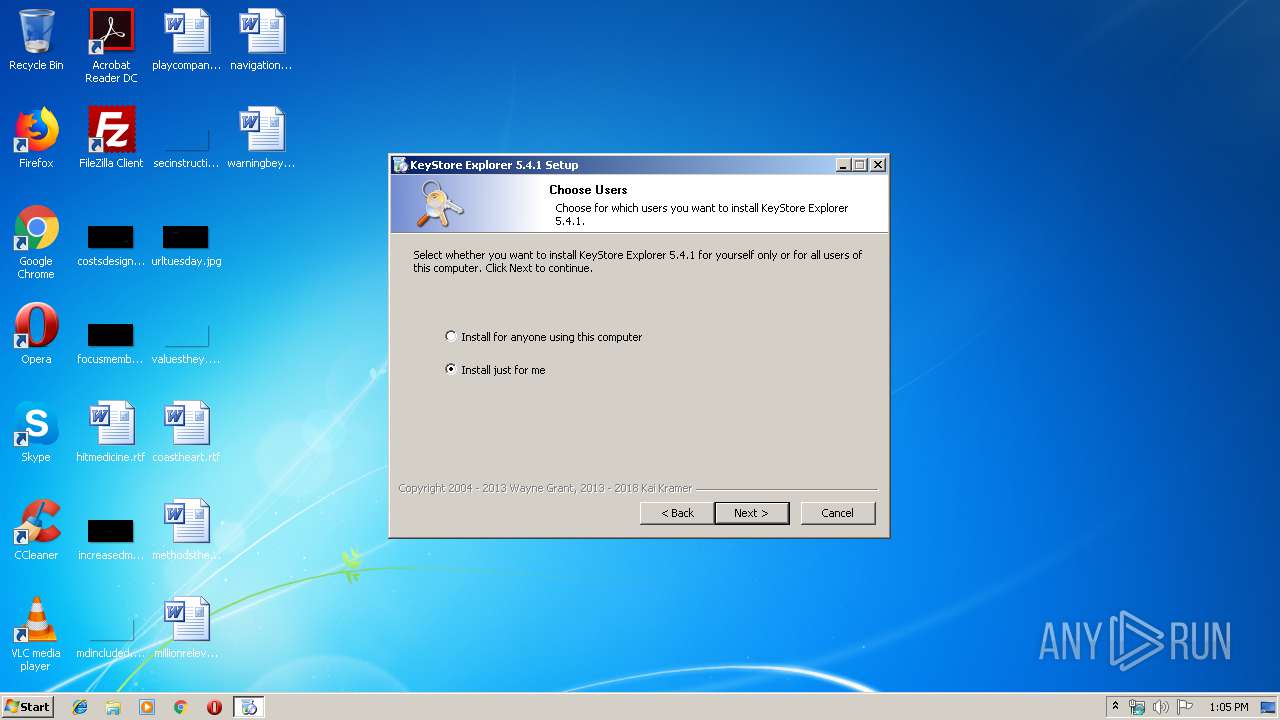
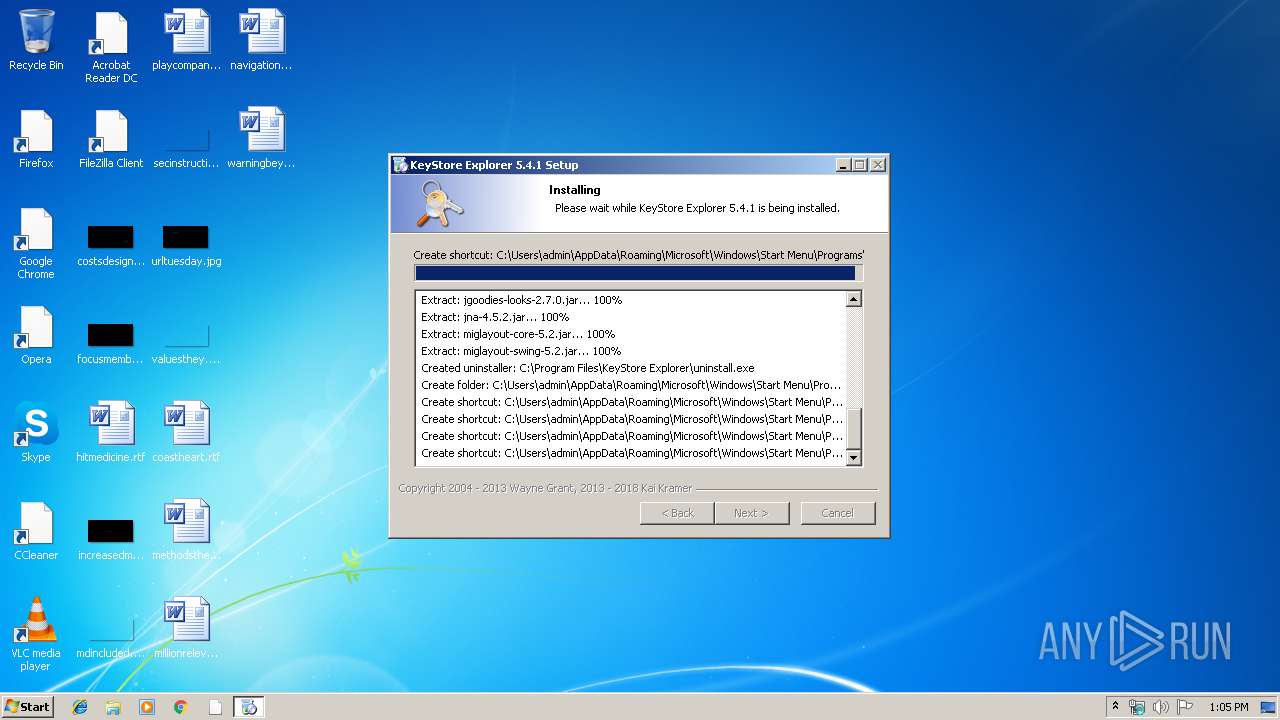
Creates a software uninstall entry
- kse-541-setup.exe (PID: 3668)
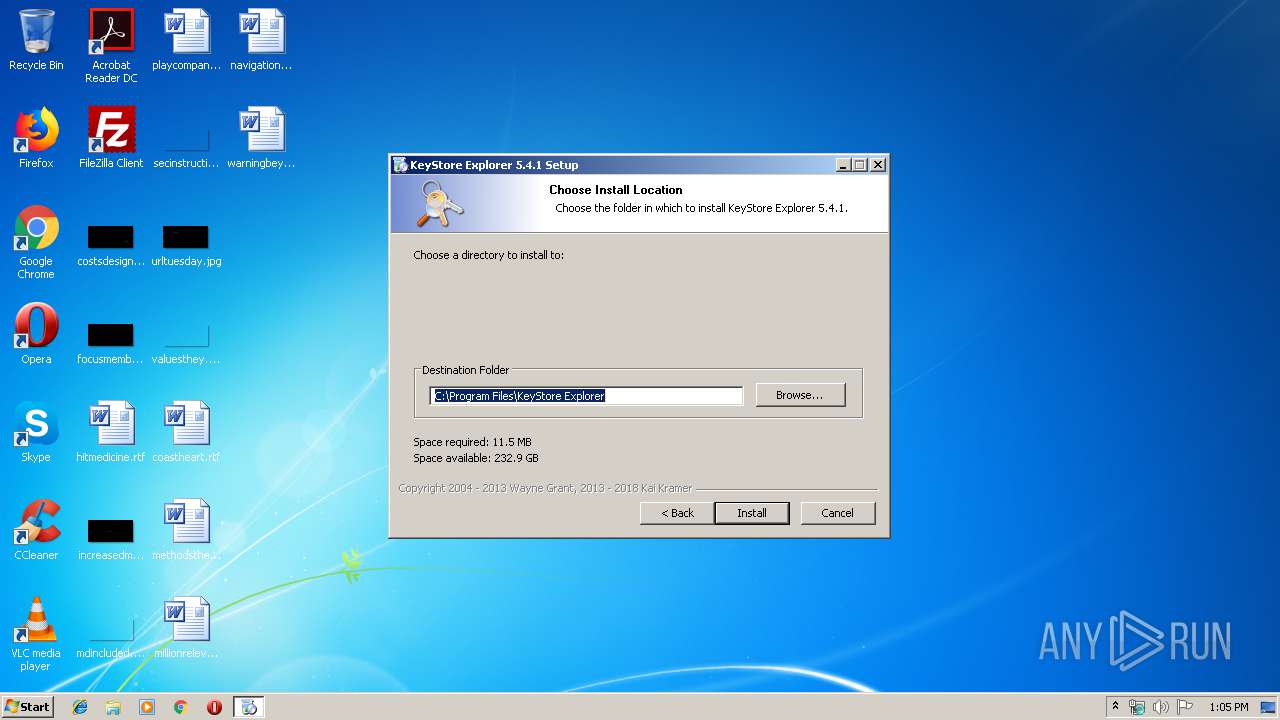
Creates files in the program directory
- kse-541-setup.exe (PID: 3668)
Creates files in the user directory
- kse-541-setup.exe (PID: 3668)
- javaw.exe (PID: 3556)
Executes JAVA applets
- kse.exe (PID: 3056)
INFO
Manual execution by user
- kse.exe (PID: 3056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:45+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x320c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:45 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000628F | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4422 |
.rdata | 0x00008000 | 0x00001354 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23627 |
.data | 0x0000A000 | 0x00025518 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04938 |
.ndata | 0x00030000 | 0x00016000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00046000 | 0x00006FB8 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.31512 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.12895 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 2.07168 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 1.64286 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 2.25482 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.98318 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3056 | "C:\Program Files\KeyStore Explorer\kse.exe" | C:\Program Files\KeyStore Explorer\kse.exe | — | explorer.exe | |||||||||||
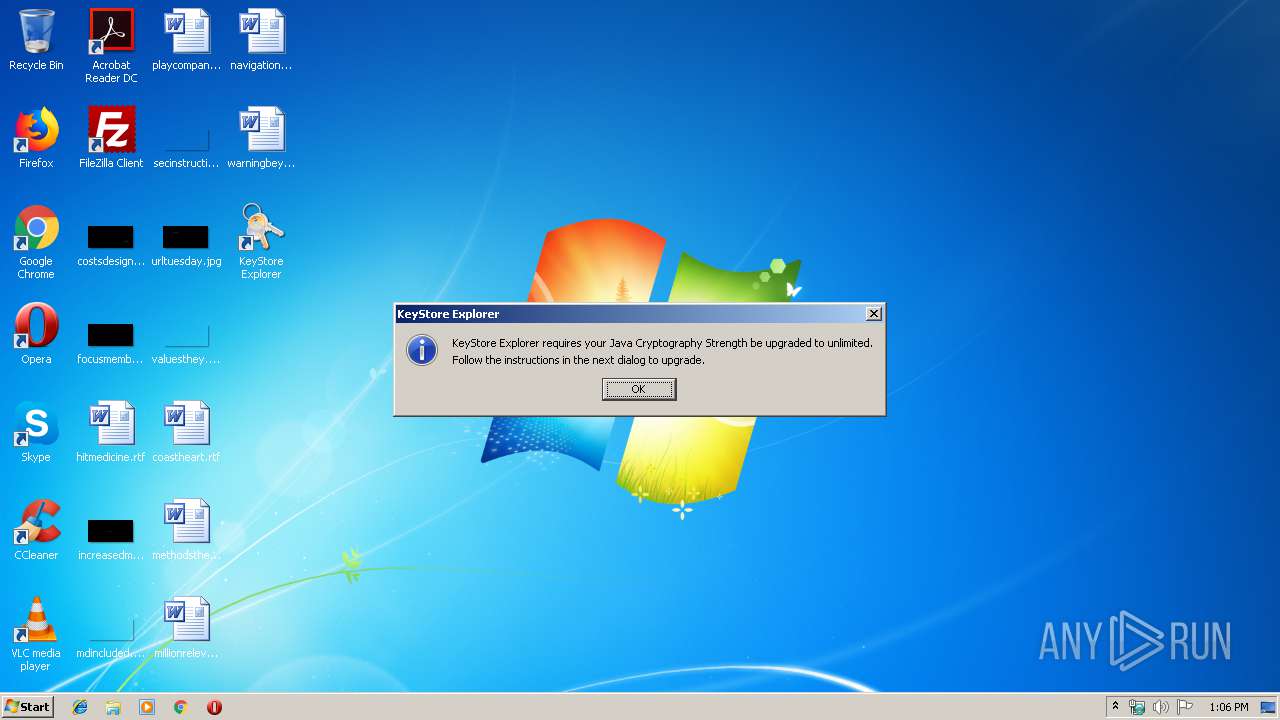
User: admin Integrity Level: MEDIUM Description: KeyStore Explorer Exit code: 0 Version: 5.4.1 Modules
| |||||||||||||||
| 3304 | "C:\Users\admin\AppData\Local\Temp\kse-541-setup.exe" | C:\Users\admin\AppData\Local\Temp\kse-541-setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3556 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Program Files\KeyStore Explorer\kse.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | kse.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3668 | "C:\Users\admin\AppData\Local\Temp\kse-541-setup.exe" | C:\Users\admin\AppData\Local\Temp\kse-541-setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
408
Read events
385
Write events
23
Delete events
0
Modification events
| (PID) Process: | (3668) kse-541-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\KeyStore Explorer |
| Operation: | write | Name: | Install_Dir |
Value: C:\Program Files\KeyStore Explorer | |||
| (PID) Process: | (3668) kse-541-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KeyStore Explorer |
| Operation: | write | Name: | DisplayName |
Value: KeyStore Explorer | |||
| (PID) Process: | (3668) kse-541-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KeyStore Explorer |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\KeyStore Explorer\uninstall.exe /CurrentUser | |||
| (PID) Process: | (3668) kse-541-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KeyStore Explorer |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\KeyStore Explorer\kse.ico | |||
| (PID) Process: | (3668) kse-541-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KeyStore Explorer |
| Operation: | write | Name: | Publisher |
Value: Kai Kramer | |||
| (PID) Process: | (3668) kse-541-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KeyStore Explorer |
| Operation: | write | Name: | DisplayVersion |
Value: 5.4.1 | |||
| (PID) Process: | (3668) kse-541-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KeyStore Explorer |
| Operation: | write | Name: | EstimatedSize |
Value: 10700 | |||
| (PID) Process: | (3668) kse-541-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KeyStore Explorer |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (3668) kse-541-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KeyStore Explorer |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (3668) kse-541-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.ks |
| Operation: | write | Name: | |
Value: Java KeyStore | |||
Executable files
15
Suspicious files
4
Text files
24
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3668 | kse-541-setup.exe | C:\Users\admin\AppData\Local\Temp\nsq2130.tmp | text | |
MD5:— | SHA256:— | |||
| 3668 | kse-541-setup.exe | C:\Users\admin\AppData\Local\Temp\nsoF637.tmp\System.dll | executable | |
MD5:B0C77267F13B2F87C084FD86EF51CCFC | SHA256:A0CAC4CF4852895619BC7743EBEB89F9E4927CCDB9E66B1BCD92A4136D0F9C77 | |||
| 3668 | kse-541-setup.exe | C:\Users\admin\AppData\Local\Temp\nsoF637.tmp\modern-wizard.bmp | image | |
MD5:AA40A2E15380F97FC6967D4A814D39FF | SHA256:EBB5772CF1BF1C8C40AA1F91F9AF85DA9F12A4F4A0D220C495F17F48A7122BE6 | |||
| 3668 | kse-541-setup.exe | C:\Users\admin\AppData\Local\Temp\nsoF637.tmp\modern-header.bmp | image | |
MD5:5EEB77C422DF54815450003A093F036D | SHA256:36E18D7B63F522FEEC6902BD032C6189D93732AA41BAC00C9EB2C80B9CDEE5DA | |||
| 3668 | kse-541-setup.exe | C:\Program Files\KeyStore Explorer\kse.exe | executable | |
MD5:778F5584F4B19E621F109FF2D8563C31 | SHA256:5DA04E3ECDB6F700C571D9819209849F60CFA826C6A763CB44F12712A7042AE8 | |||
| 3668 | kse-541-setup.exe | C:\Program Files\KeyStore Explorer\www.ico | image | |
MD5:51BE75D8A732144EC73C3E7CAB8C9A7D | SHA256:93494F26C7FCF2C13CB7C93F6BD1058681057187CB2E71D24AC6357606E40832 | |||
| 3668 | kse-541-setup.exe | C:\Program Files\KeyStore Explorer\kse.jar | compressed | |
MD5:A2B79333D373EDD956B9C3345B8AD186 | SHA256:28FE8832BA84723907C22B797141DC8D9538B5F4E61D90951A7B4986ECF61DCA | |||
| 3668 | kse-541-setup.exe | C:\Program Files\KeyStore Explorer\licenses.ico | image | |
MD5:BB5BBBBE40A2393749FCCD22273A158F | SHA256:714F36144E57503B6E2115C3AEA0FE940354C52510EAEA3147DA5CC0289928CC | |||
| 3668 | kse-541-setup.exe | C:\Program Files\KeyStore Explorer\kse.ico | image | |
MD5:6155ACDE650C757F5873E51644021E29 | SHA256:772556F5F9A59B198C6B220A7FD6EE7DDD15F8948B723F3431845DEE912FD94E | |||
| 3668 | kse-541-setup.exe | C:\Program Files\KeyStore Explorer\licenses\bouncycastle.txt | text | |
MD5:62C1CC82AE123A9715E48CD2614D8D22 | SHA256:411A63AA42C5702DEC1FAB256E5E47BDD5F74B1D7131E100841A296A4C8C9AD9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report