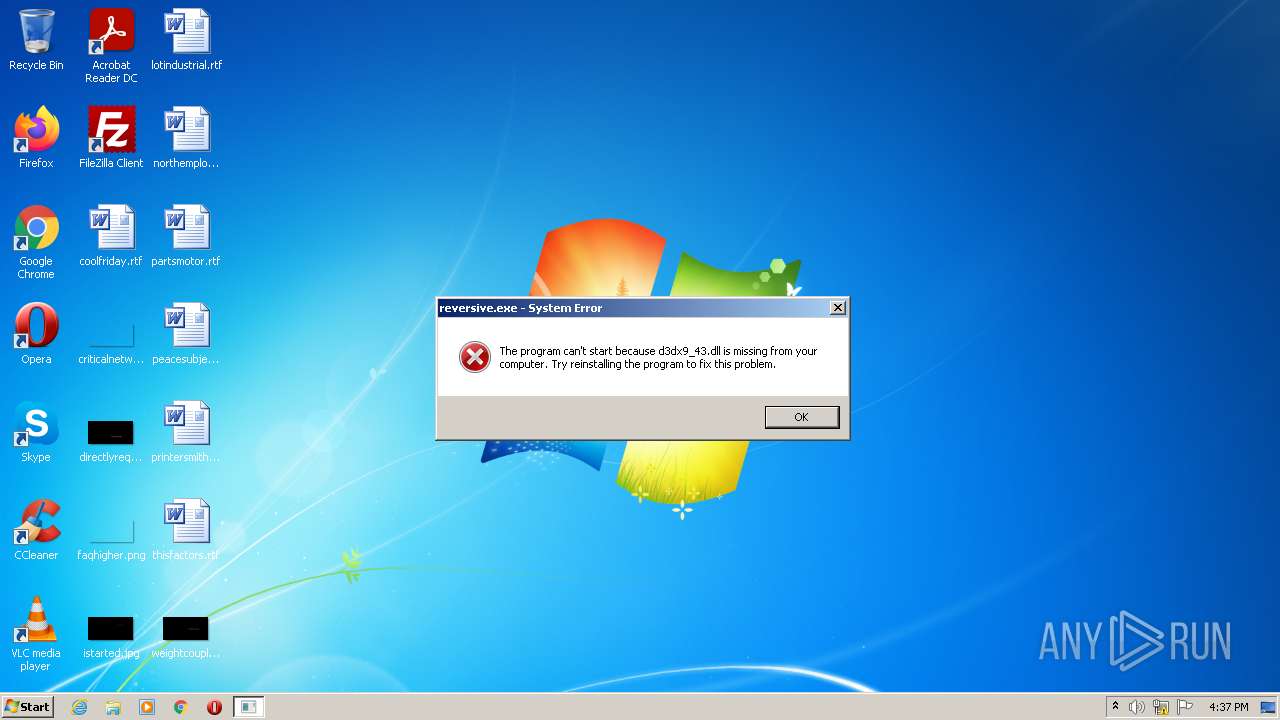
| File name: | reversive.exe |
| Full analysis: | https://app.any.run/tasks/d2c7e6bc-6c89-4ae1-aa08-e51a6c1f0495 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 15:37:32 |
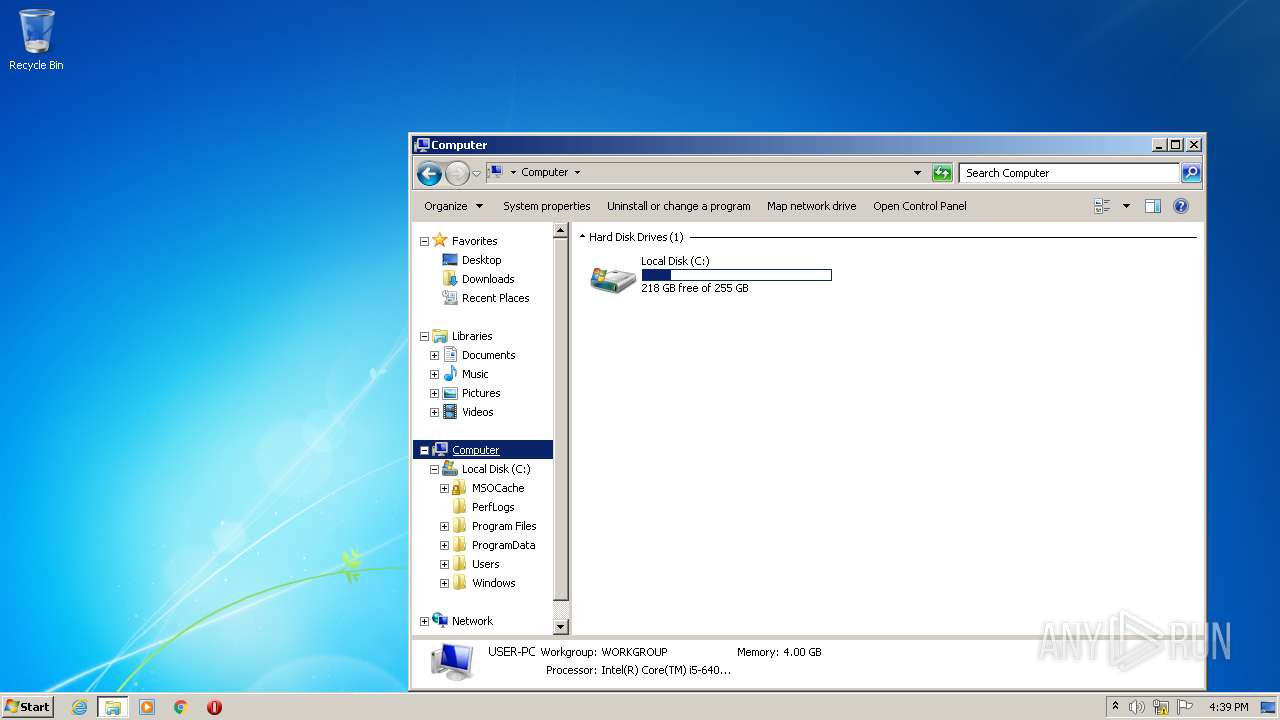
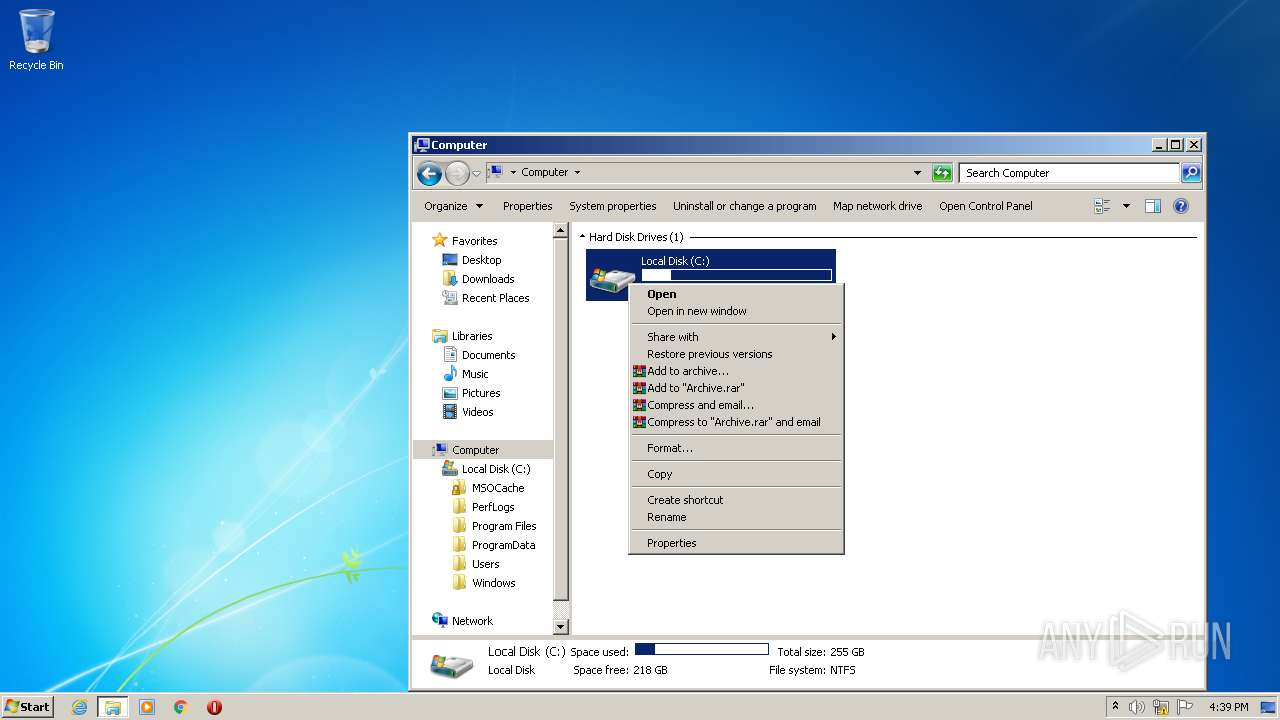
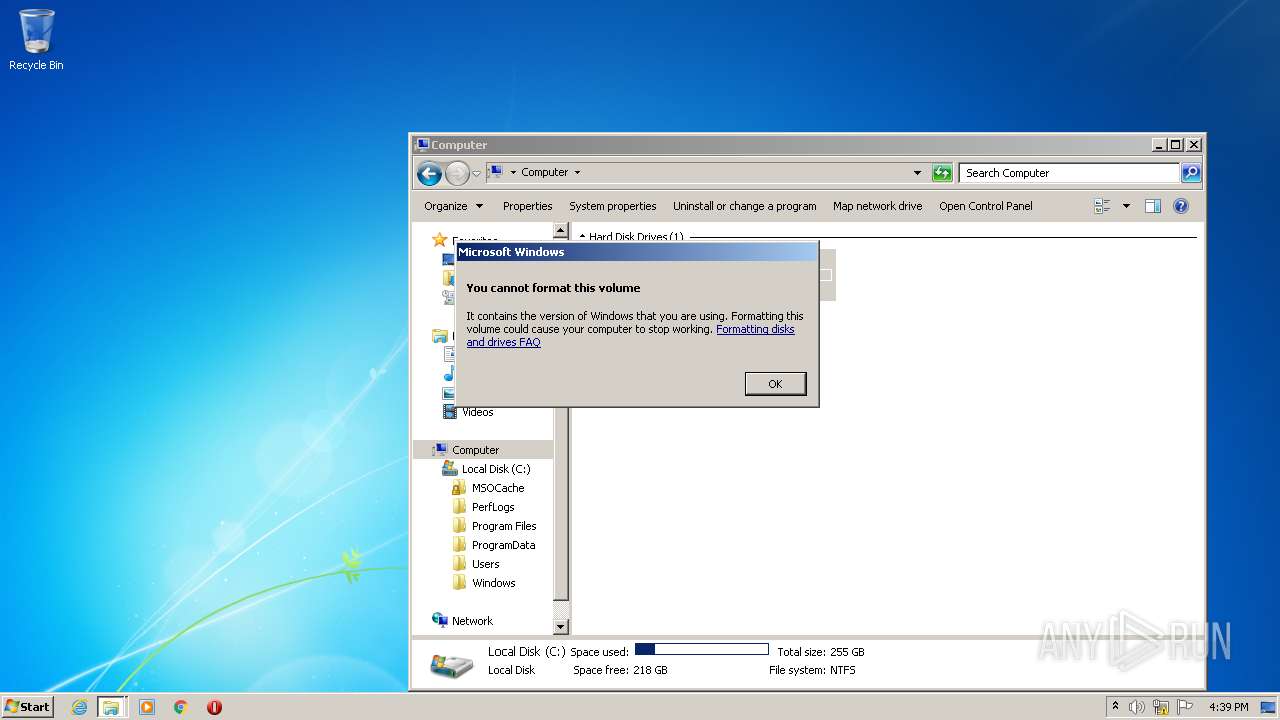
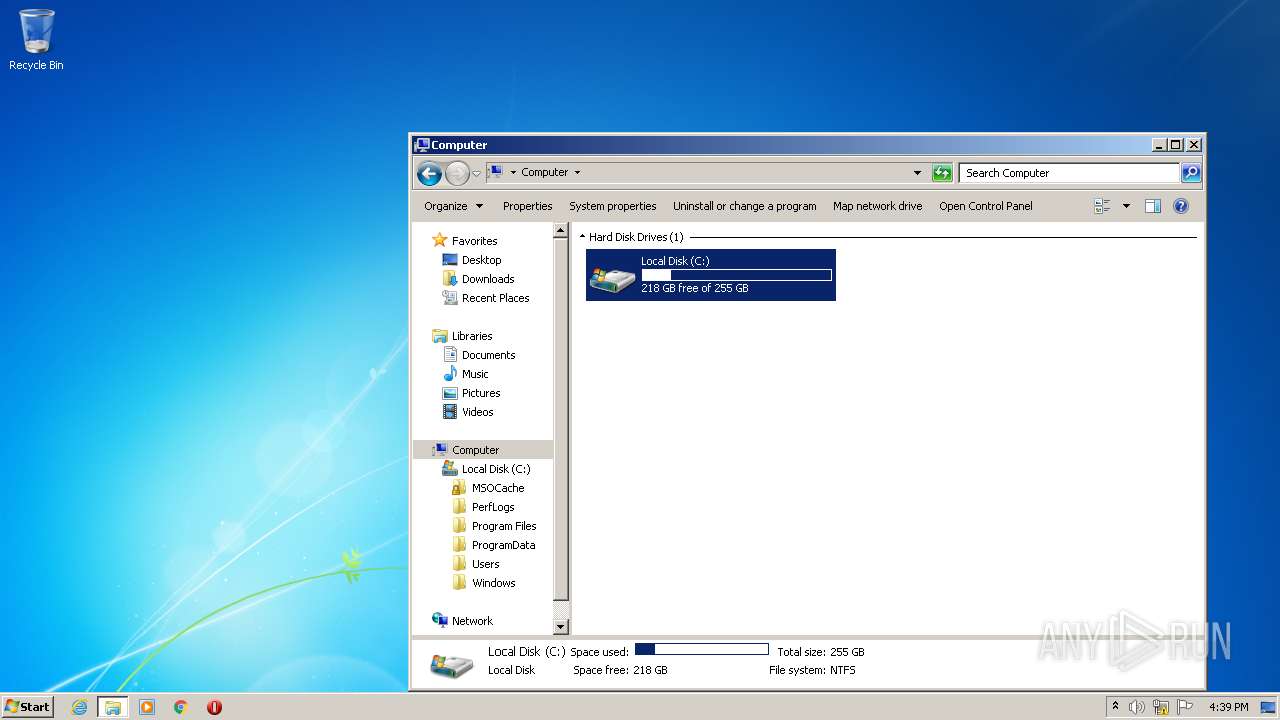
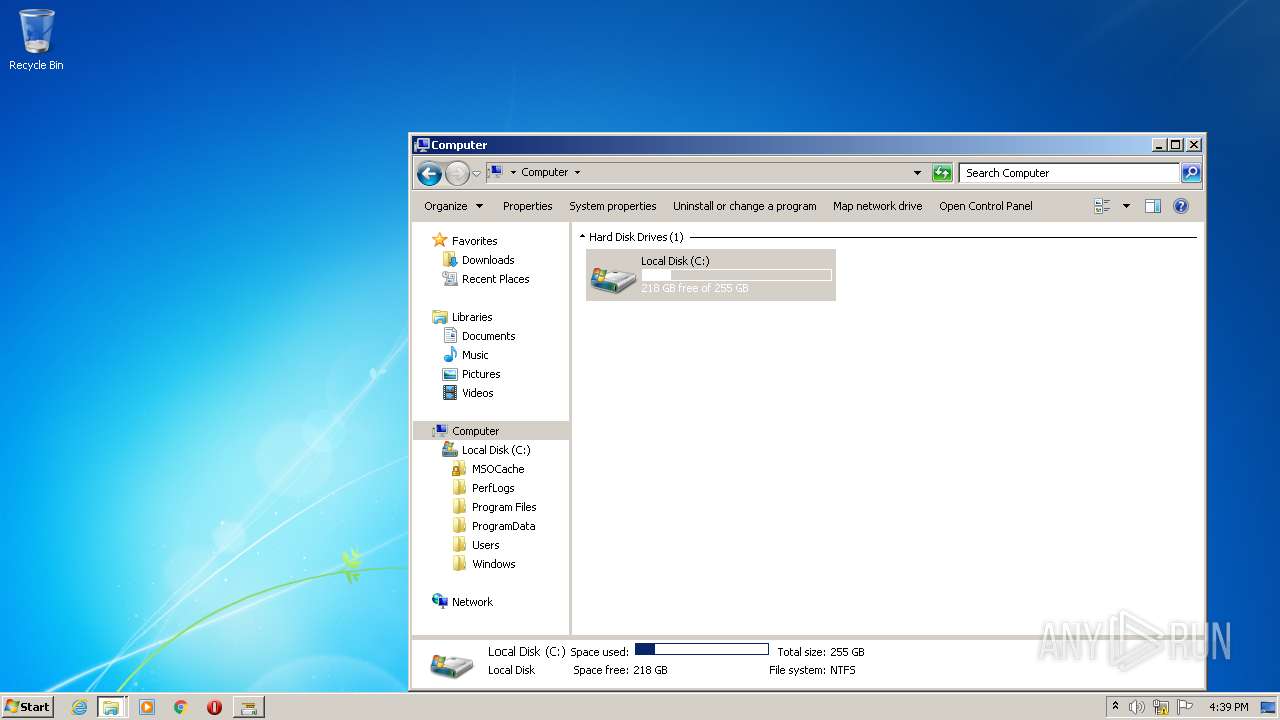
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D4731FA6BE40D8BED562F95D999F1FDE |
| SHA1: | 9F1C33F2E1B7E5708EFCE48799DD04F32E989FBA |
| SHA256: | 3C26858BF4E283A922994082C85B1C133F20C6C7FE7E379FEB7F42601743B9EA |
| SSDEEP: | 98304:LoOs8sCst7GQvj5UMDpaxJ0uFEz0CU9df2jrZvILNAS1RQ7ndbctQcZSxba6:MO3sltHbiMeJJK3U9opIZASmneXZSFB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2500)
Executed via COM
- DllHost.exe (PID: 2676)
- DllHost.exe (PID: 3228)
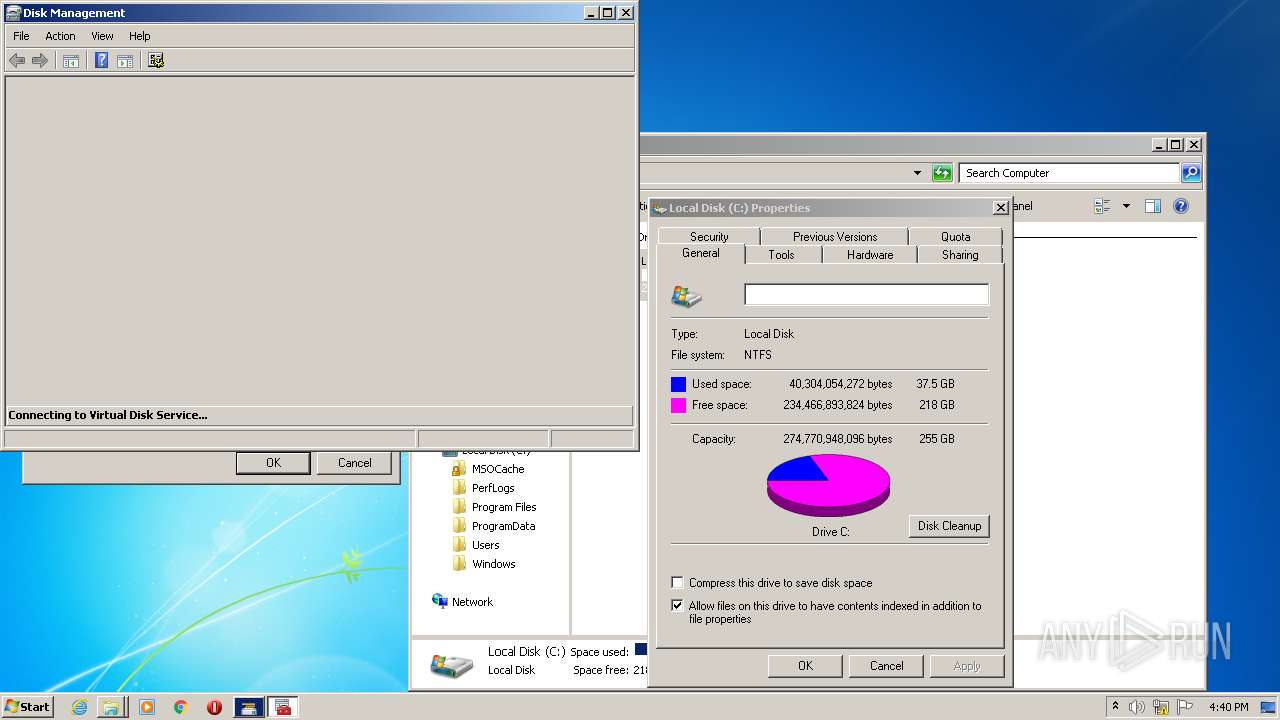
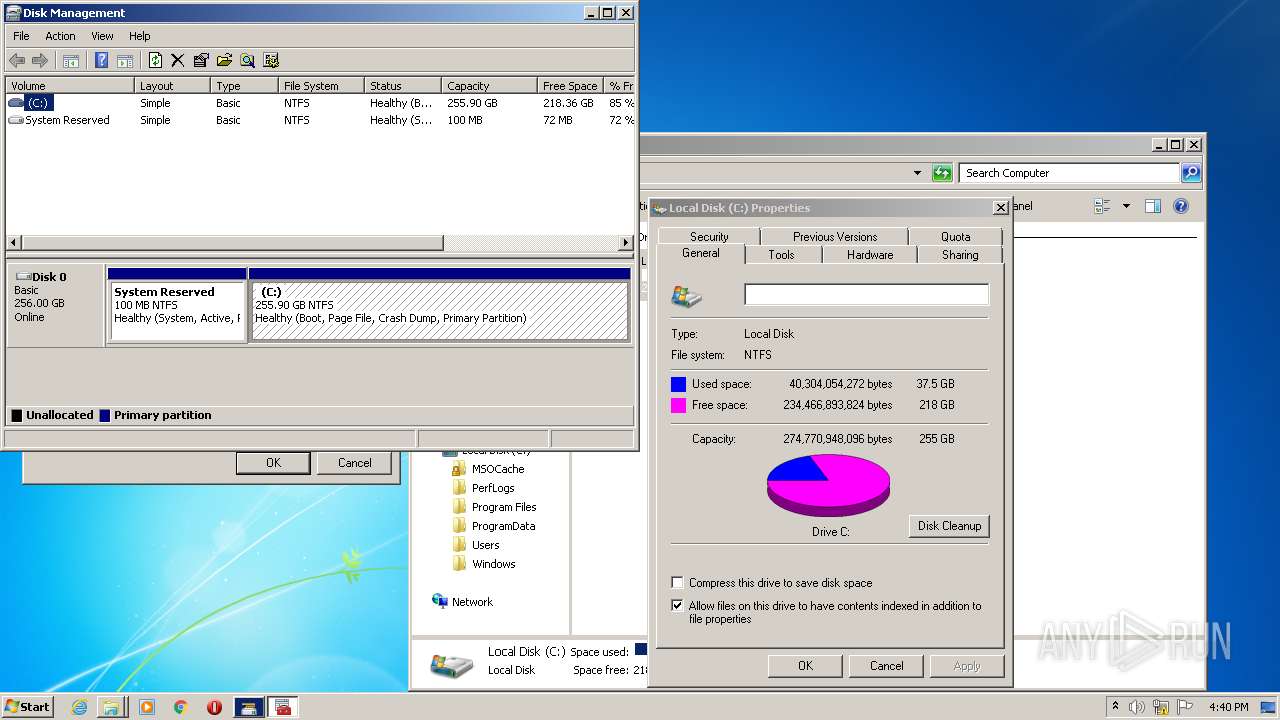
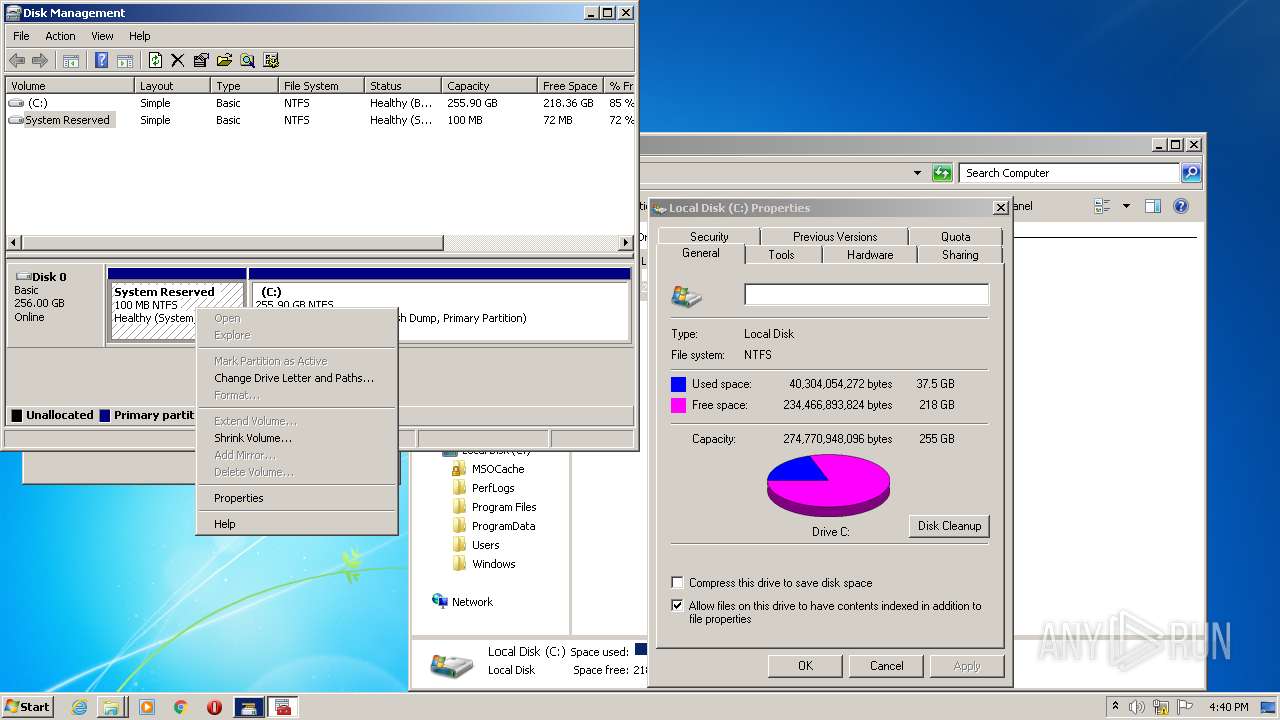
- vdsldr.exe (PID: 3200)
Executed as Windows Service
- vds.exe (PID: 112)
Reads Environment values
- vds.exe (PID: 112)
INFO
Checks supported languages
- chrome.exe (PID: 3372)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 1136)
- chrome.exe (PID: 1816)
- chrome.exe (PID: 1804)
- chrome.exe (PID: 3736)
- chrome.exe (PID: 3336)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 1852)
- explorer.exe (PID: 2364)
- DllHost.exe (PID: 2676)
- DllHost.exe (PID: 3228)
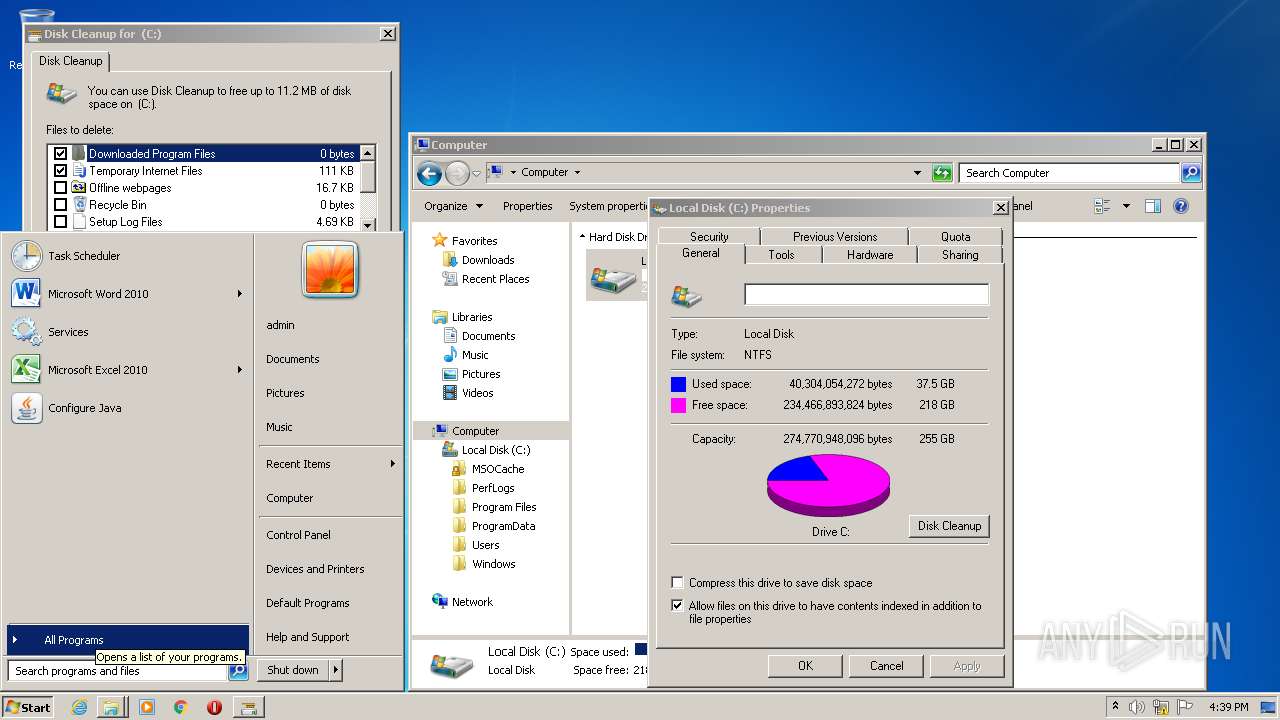
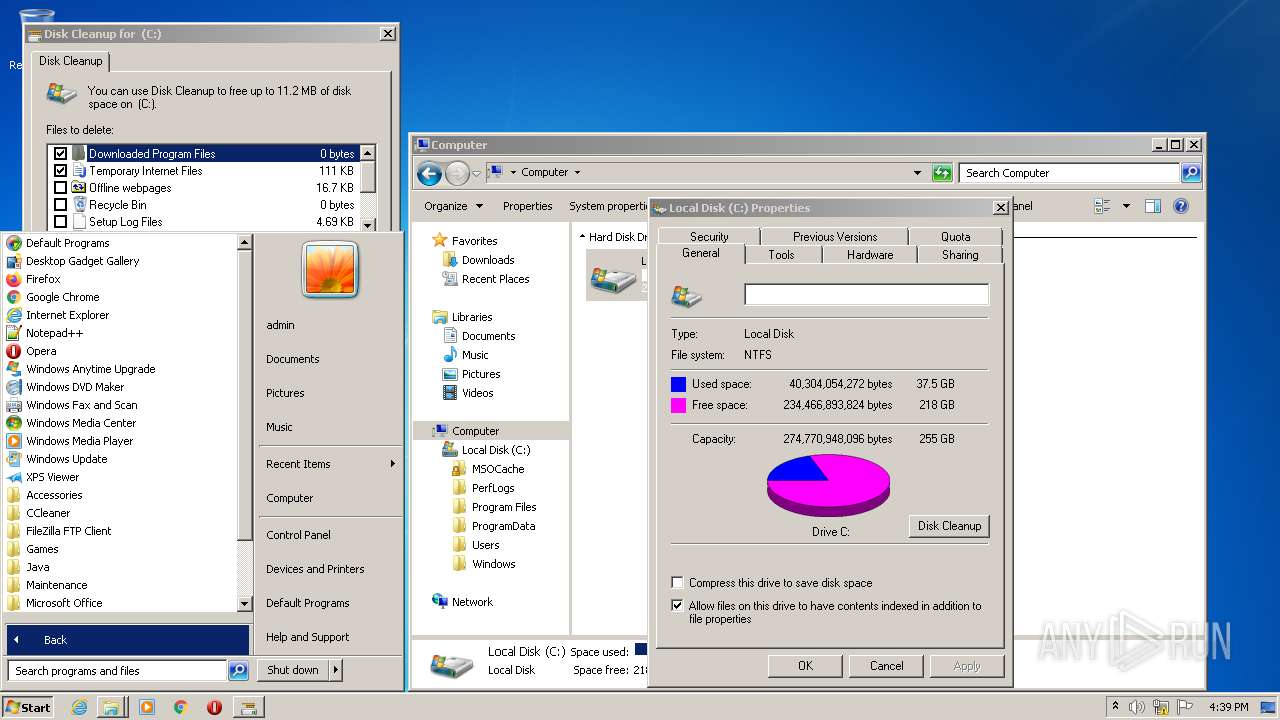
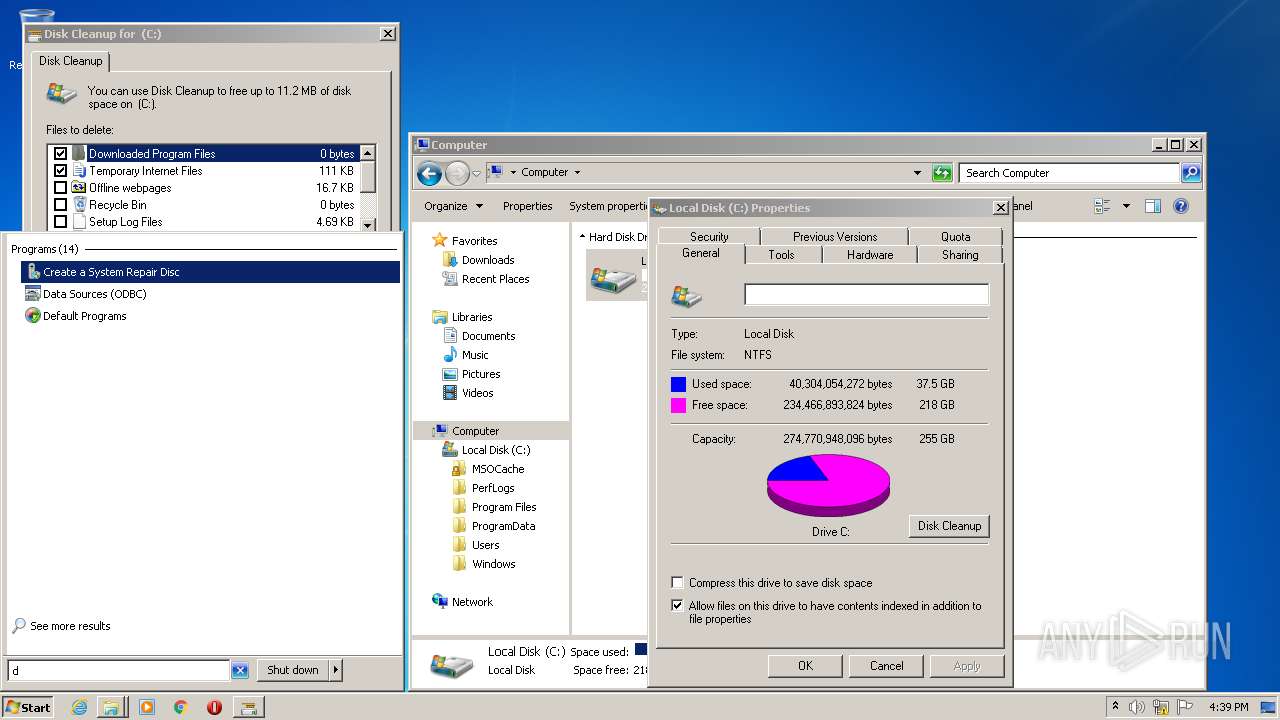
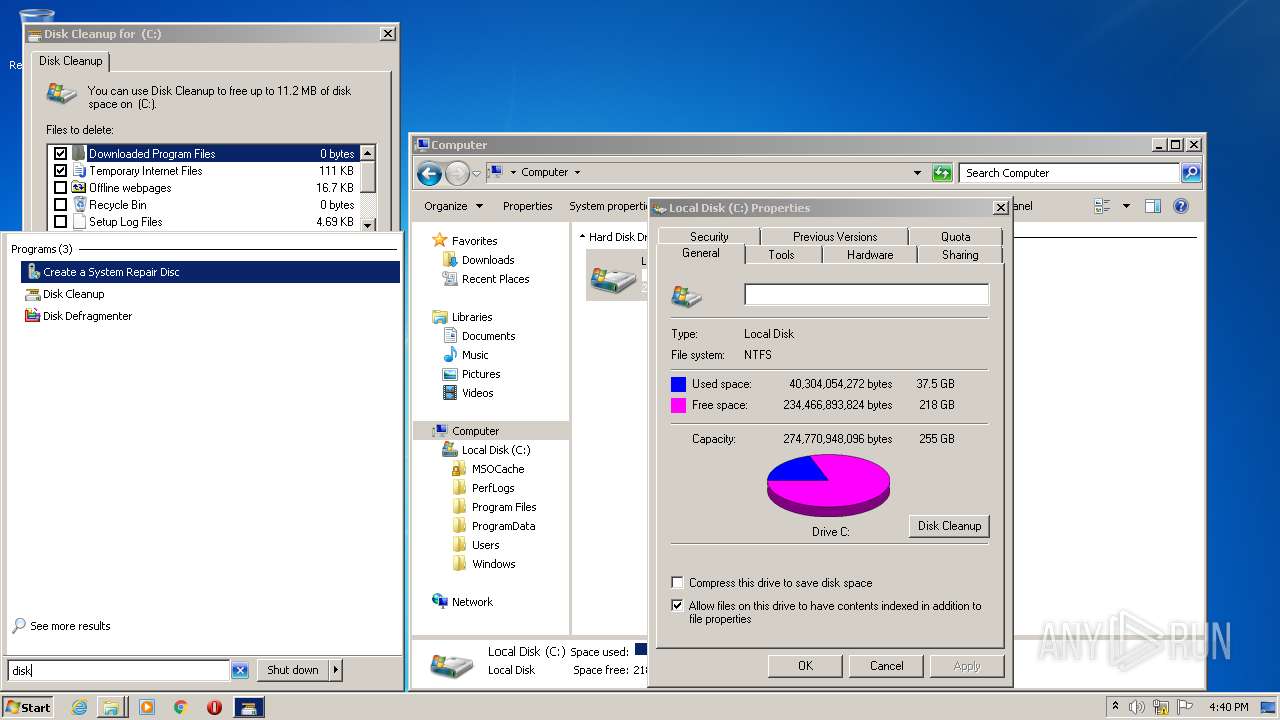
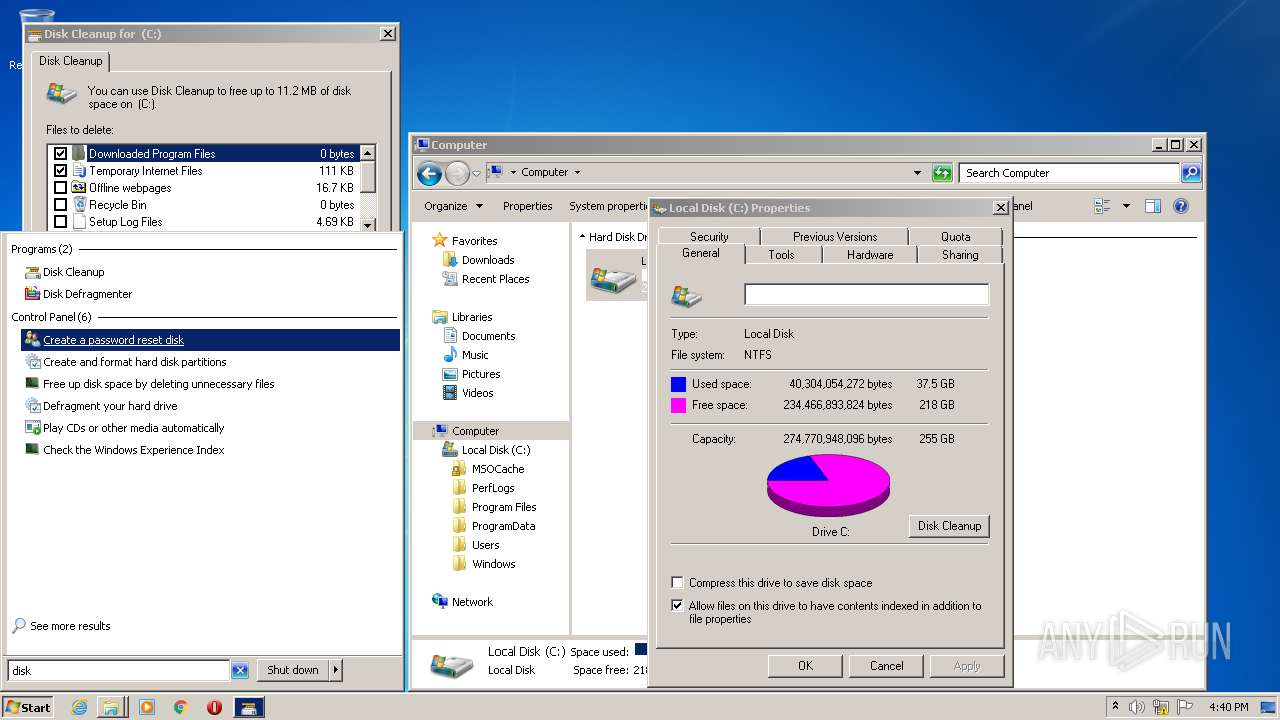
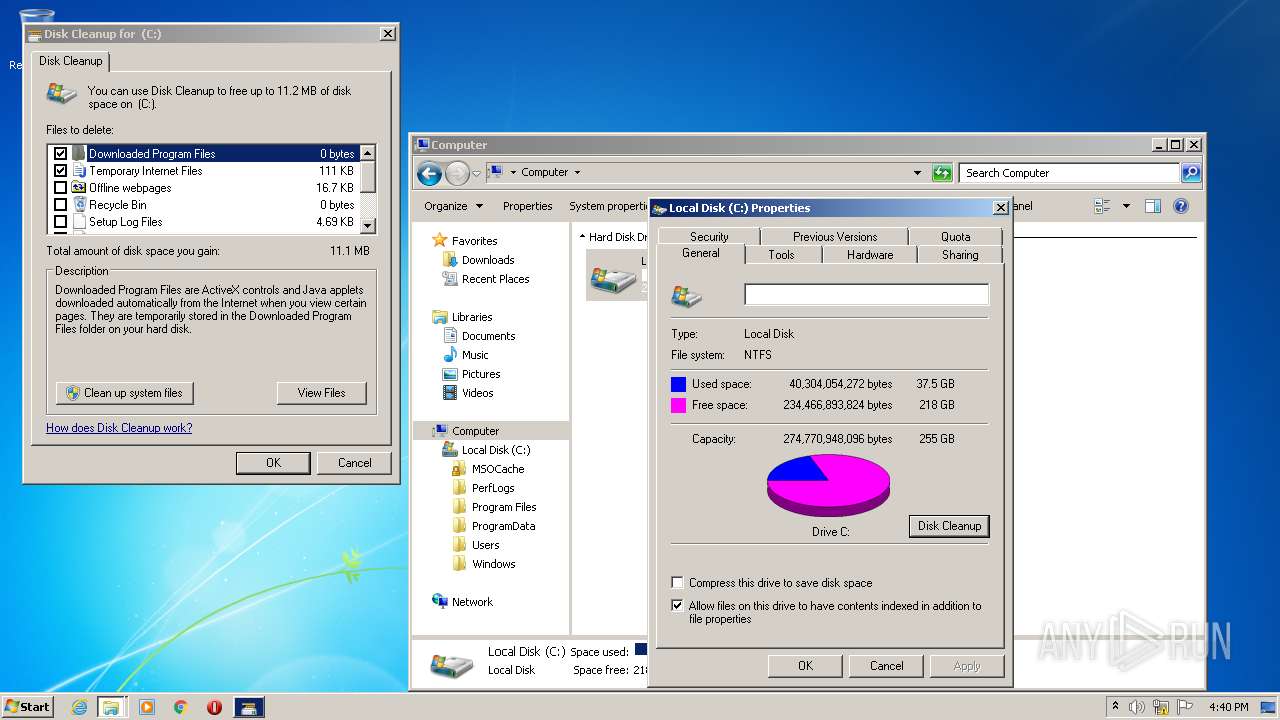
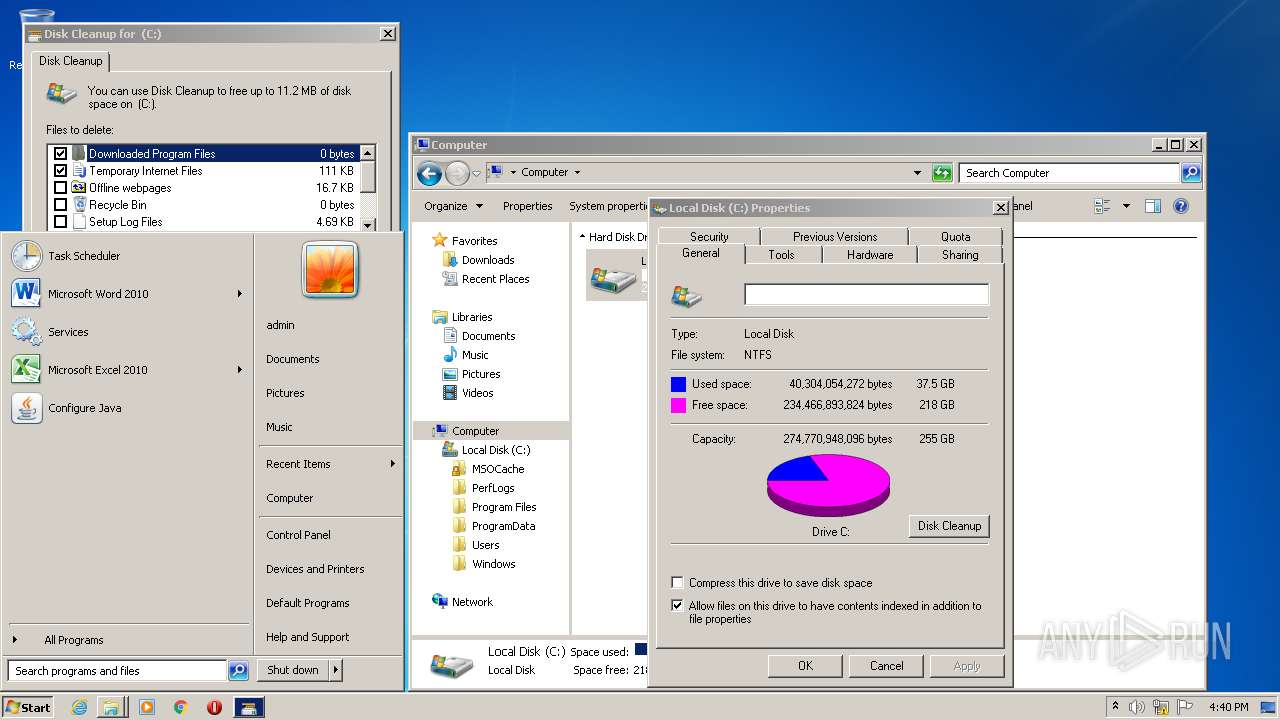
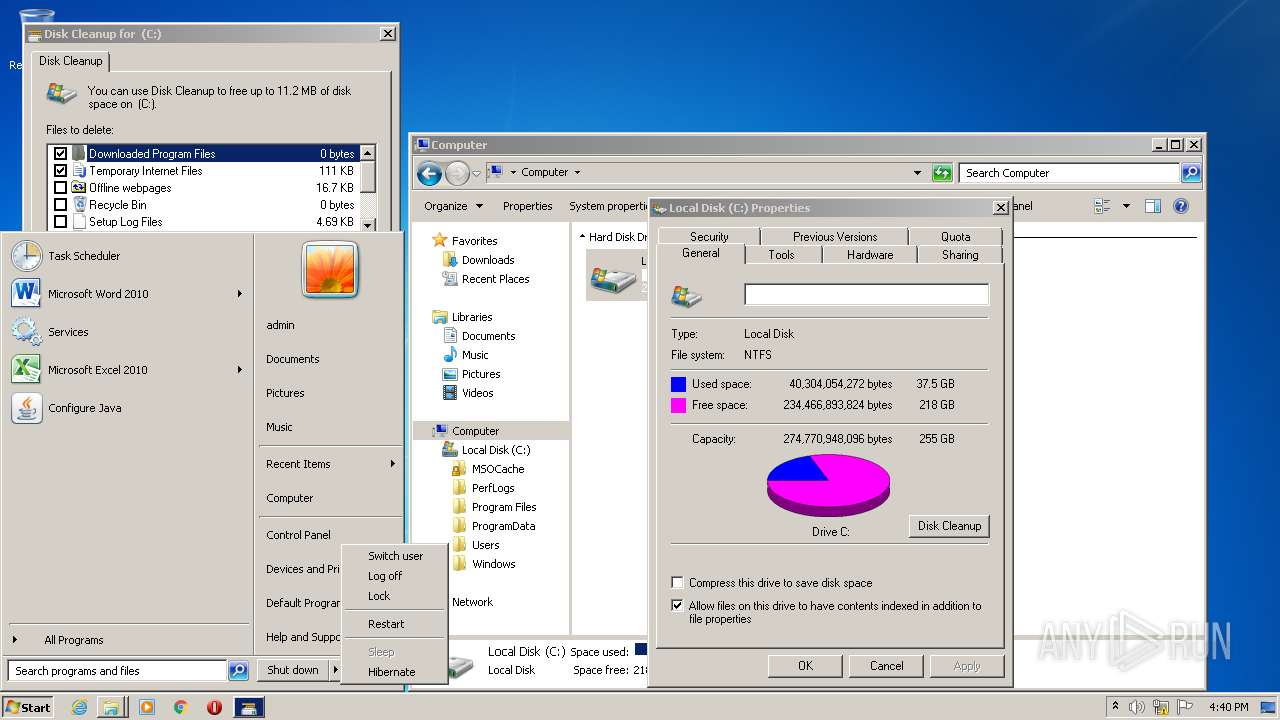
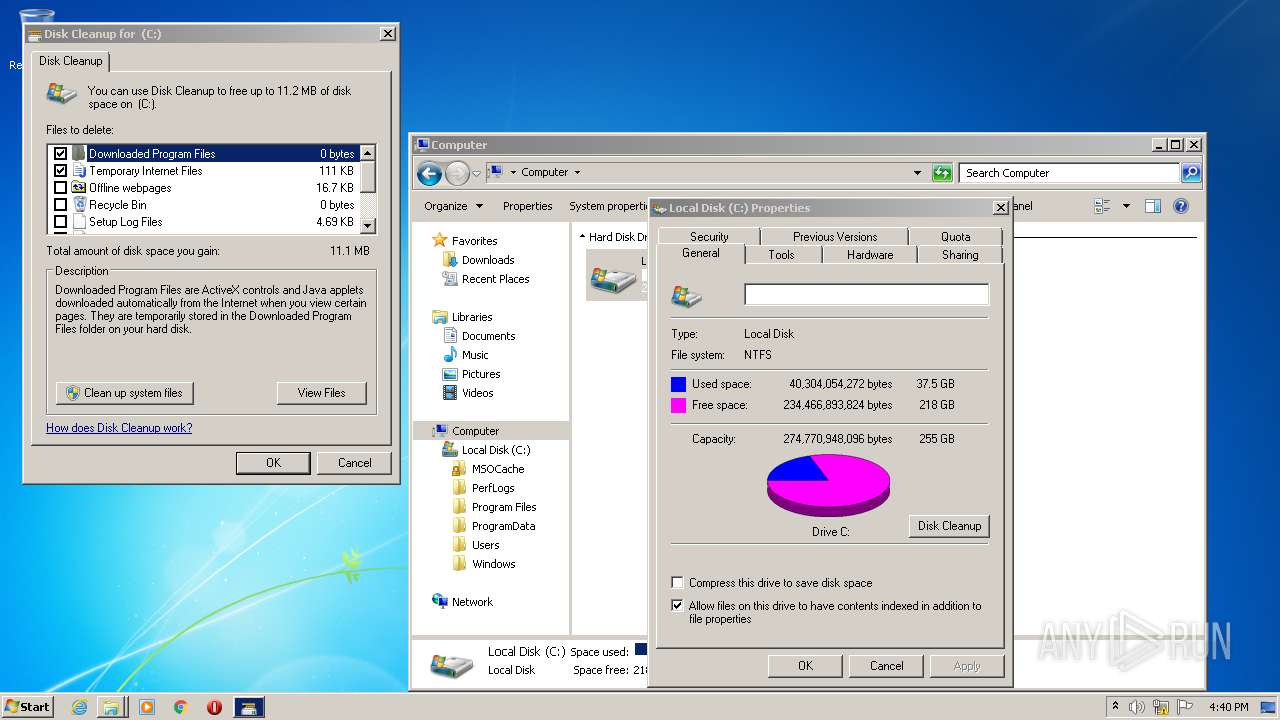
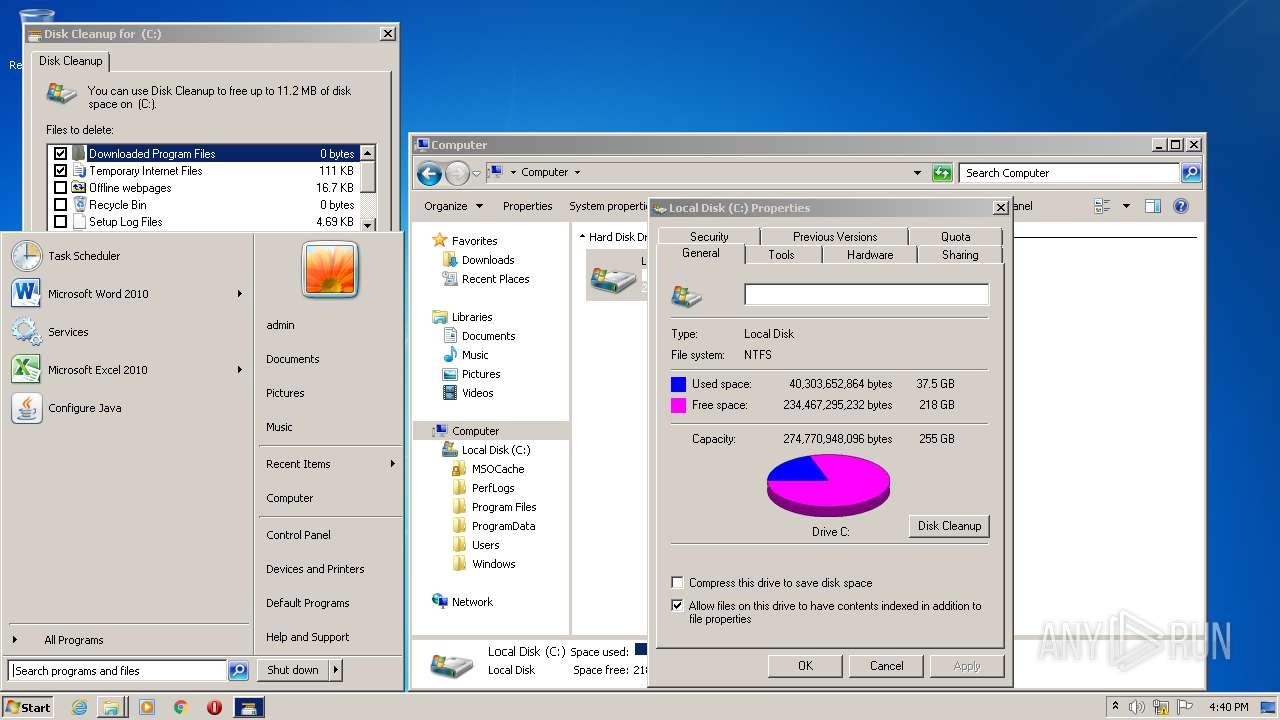
- cleanmgr.exe (PID: 1392)
- cleanmgr.exe (PID: 1776)
- mmc.exe (PID: 3076)
- vds.exe (PID: 112)
- vdsldr.exe (PID: 3200)
Application launched itself
- chrome.exe (PID: 2500)
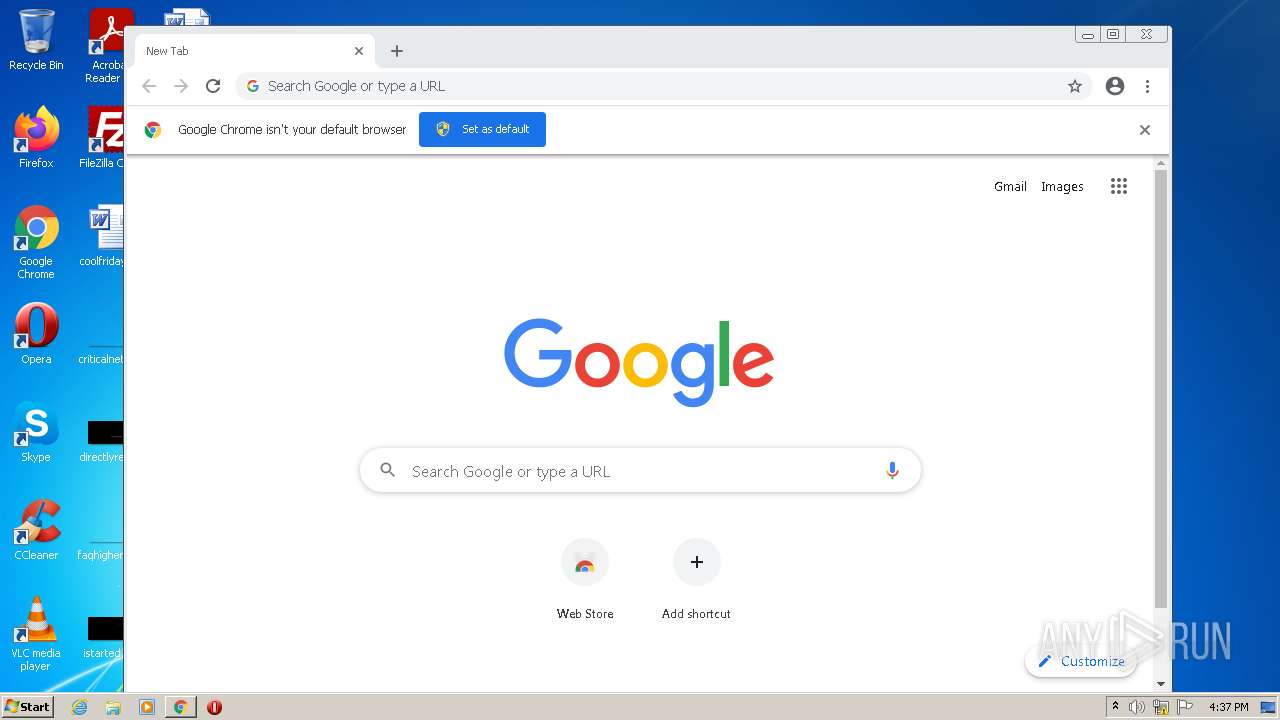
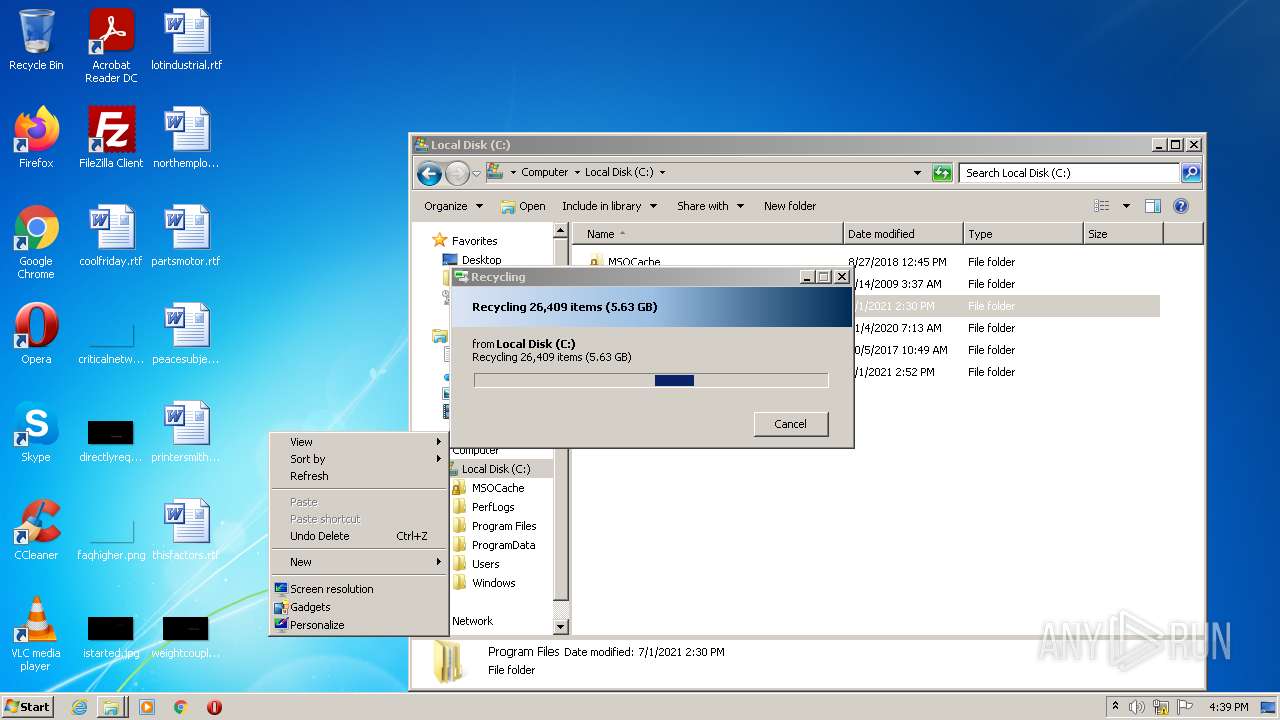
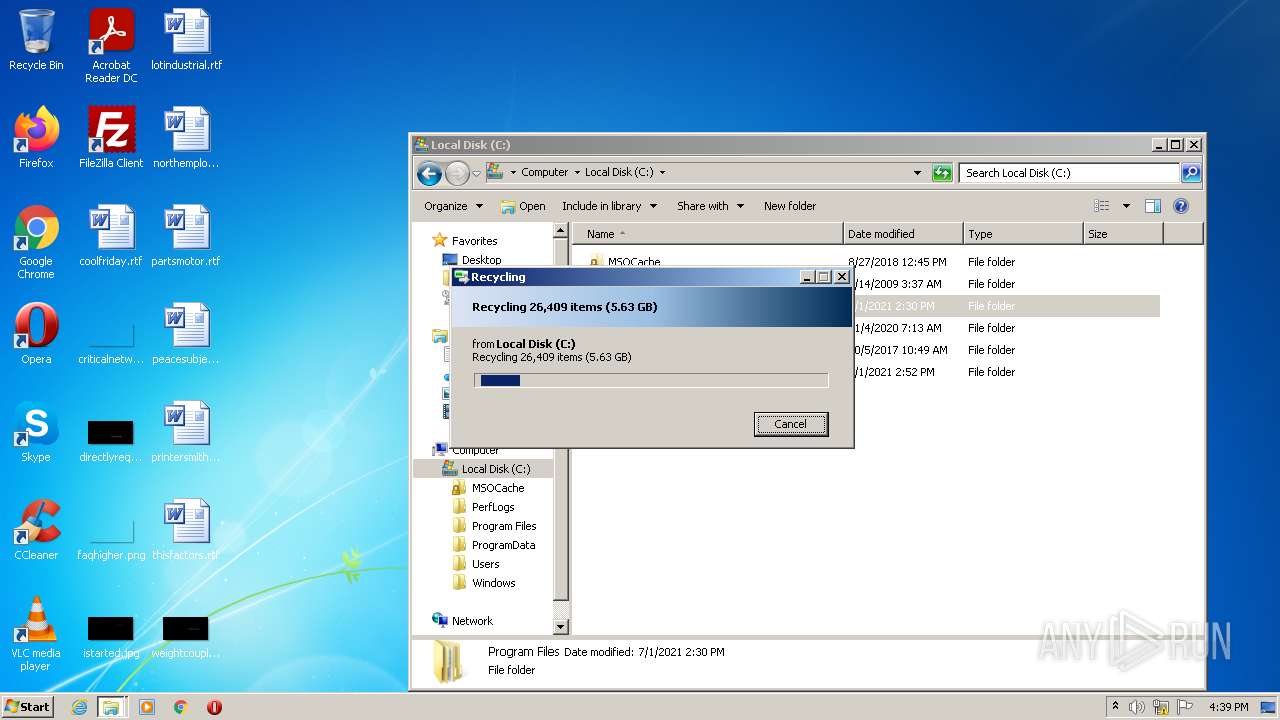
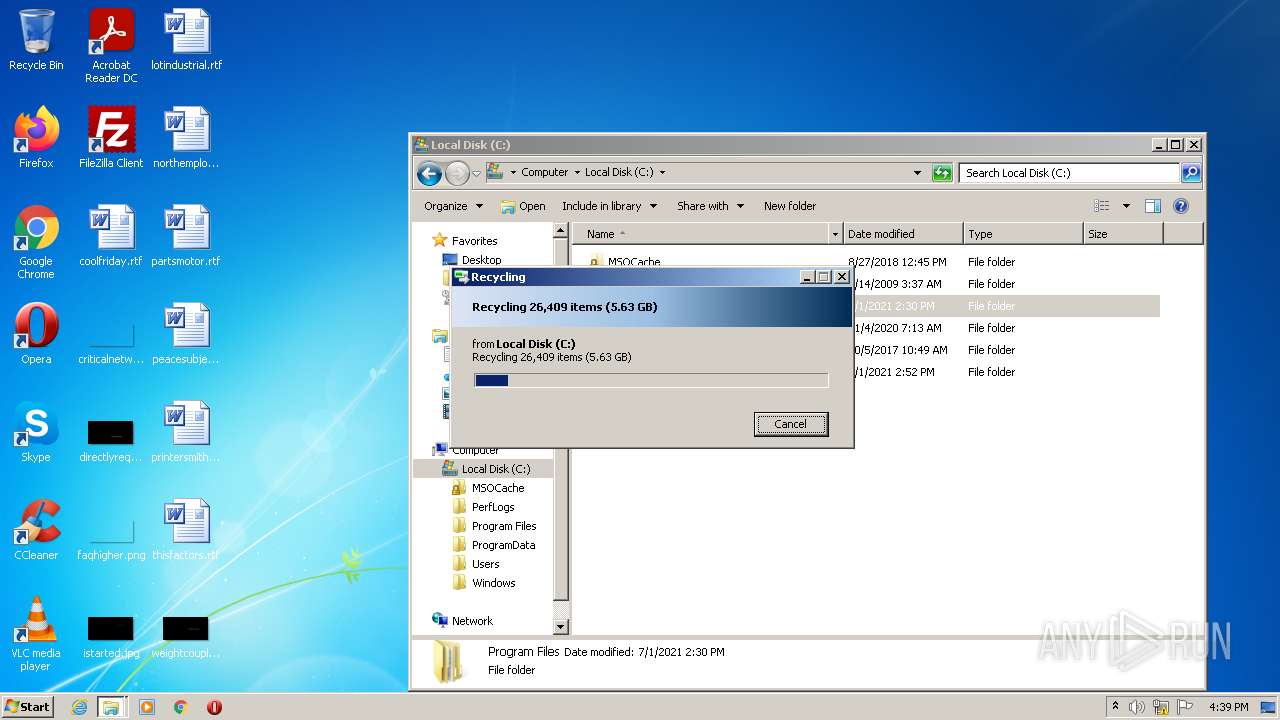
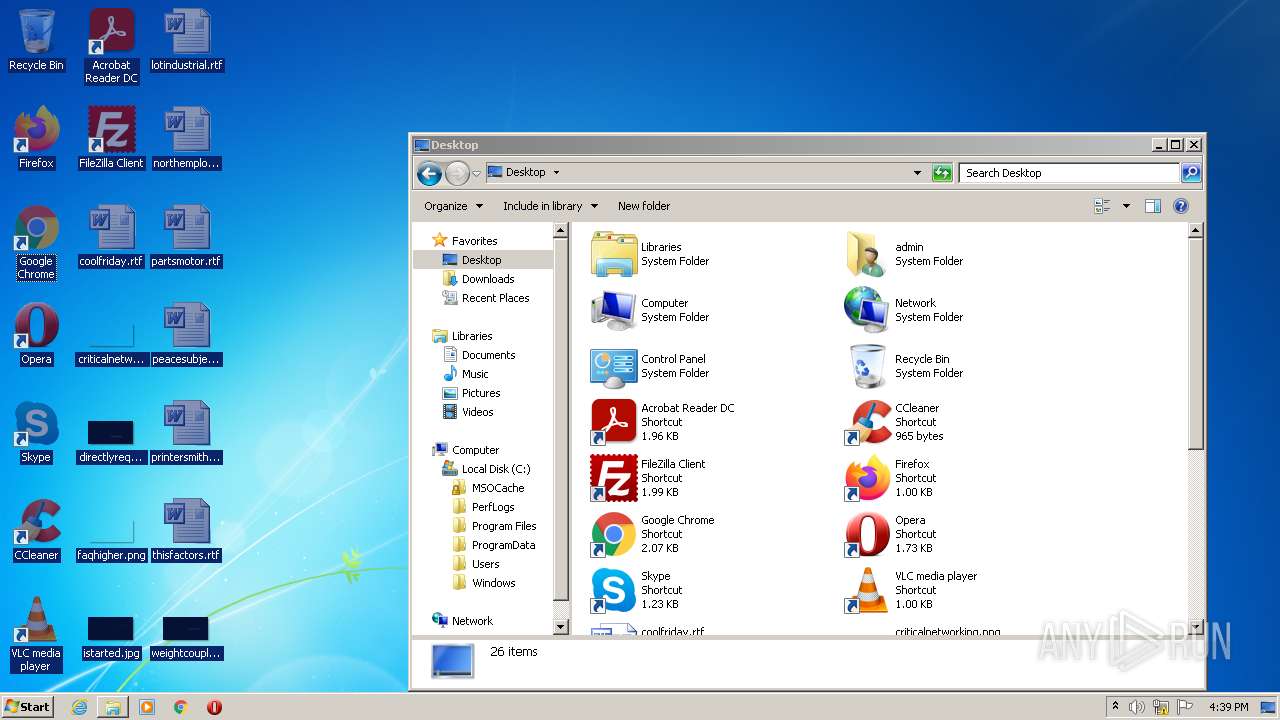
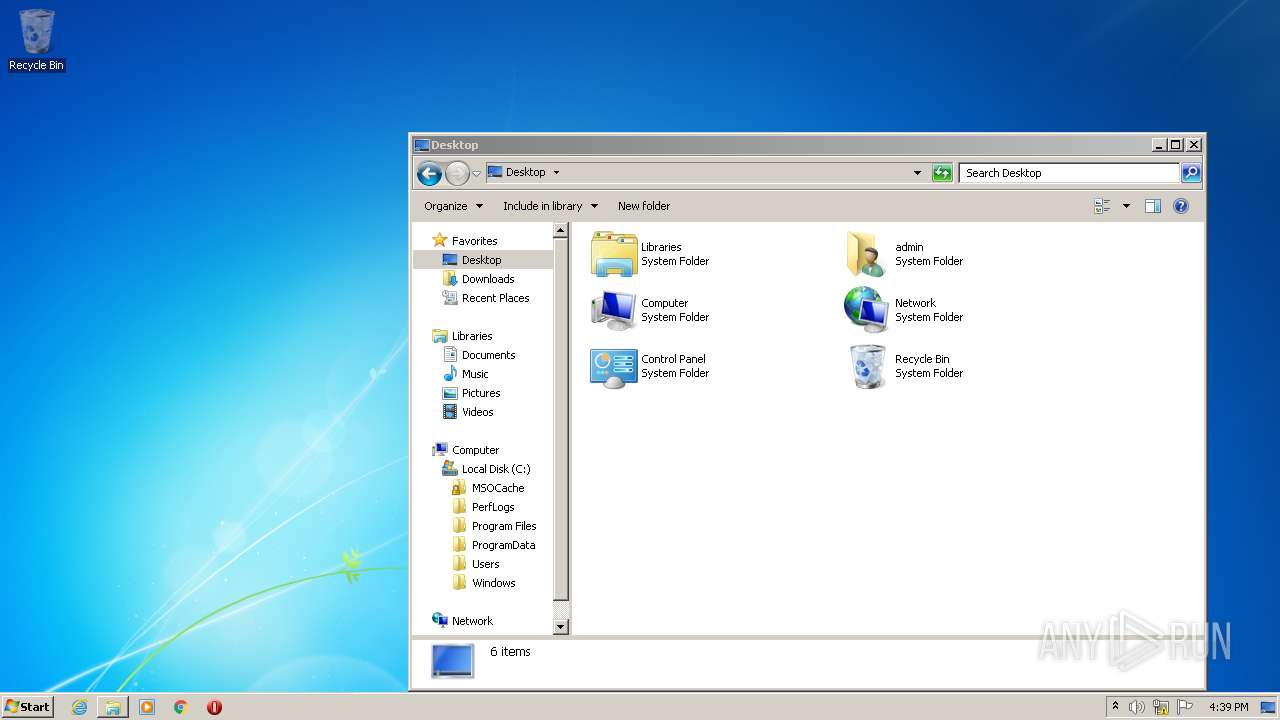
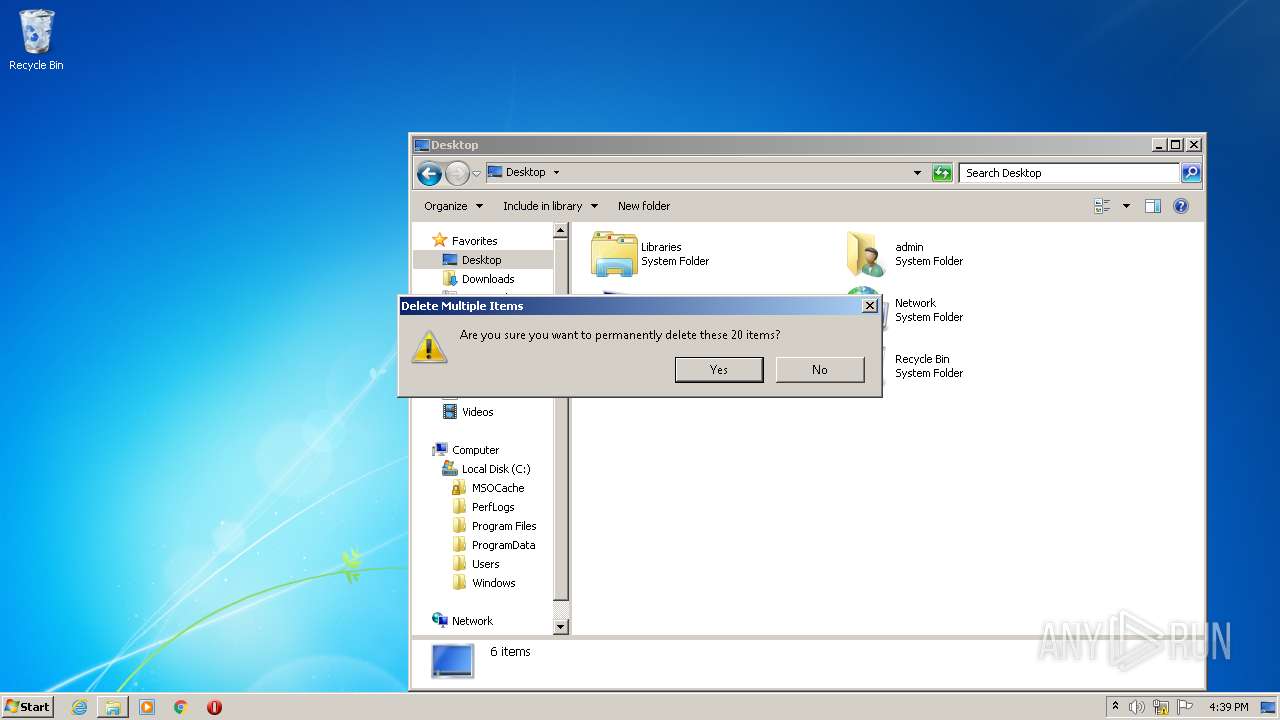
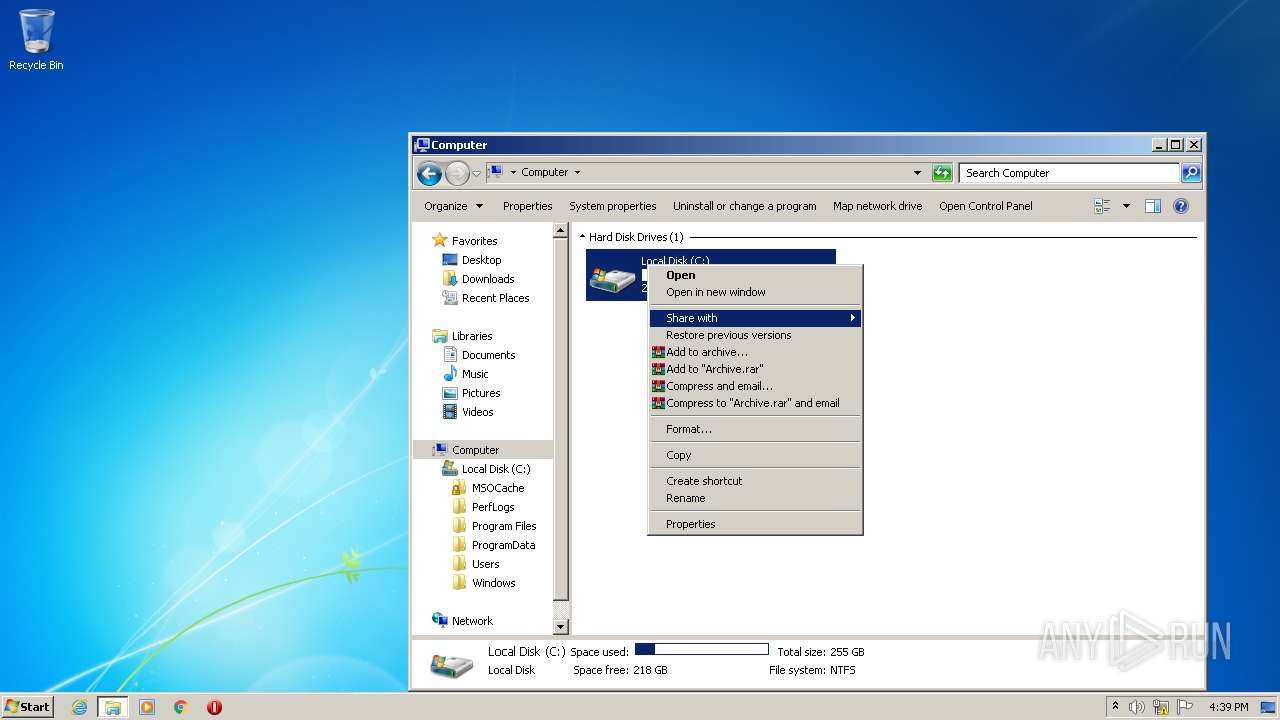
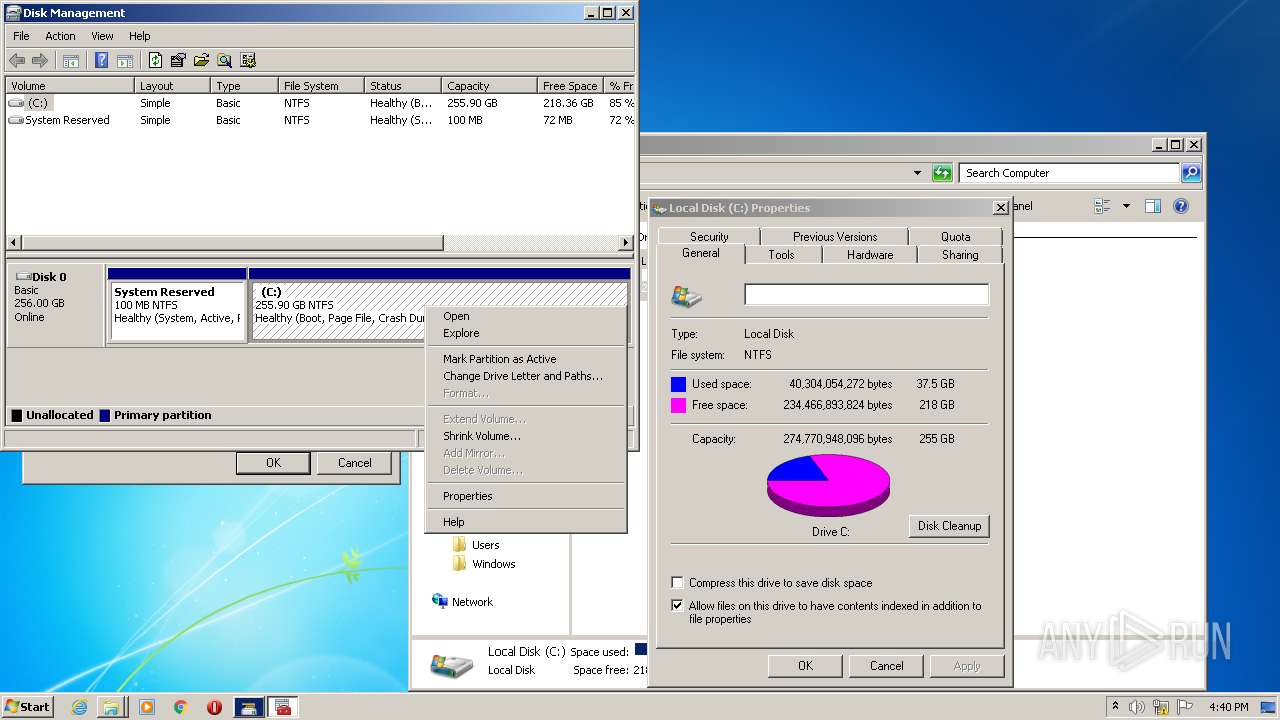
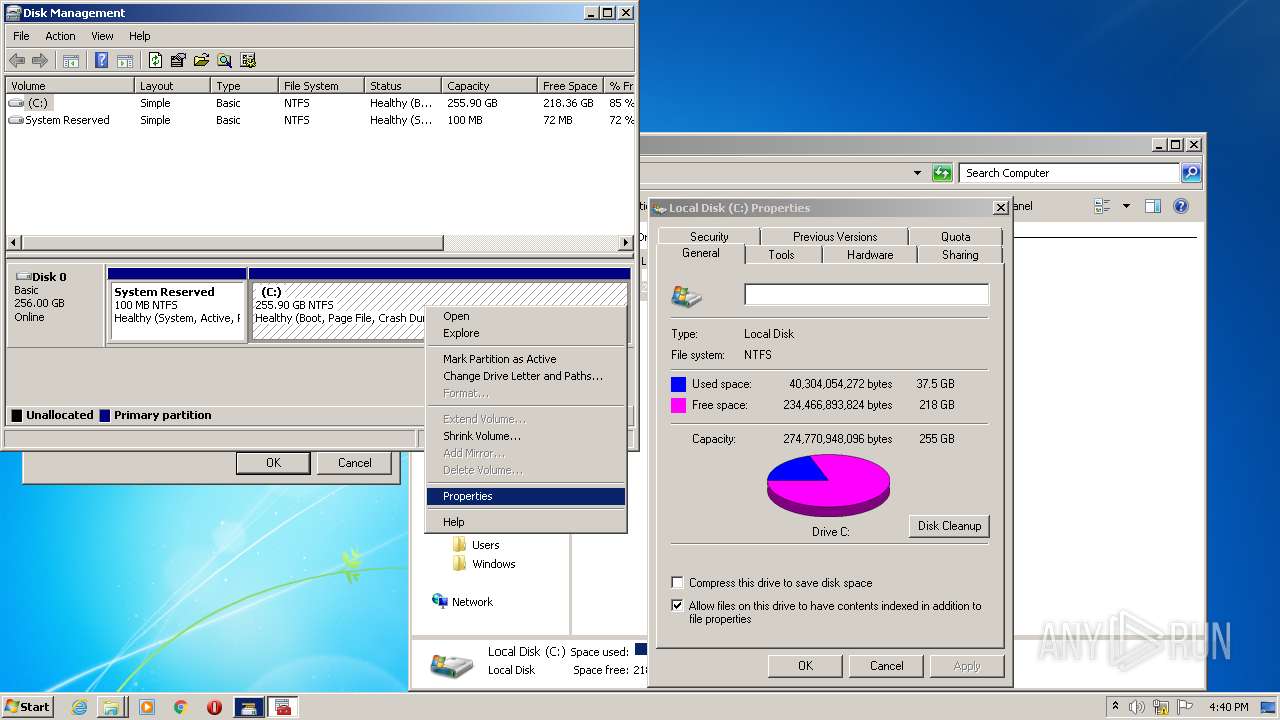
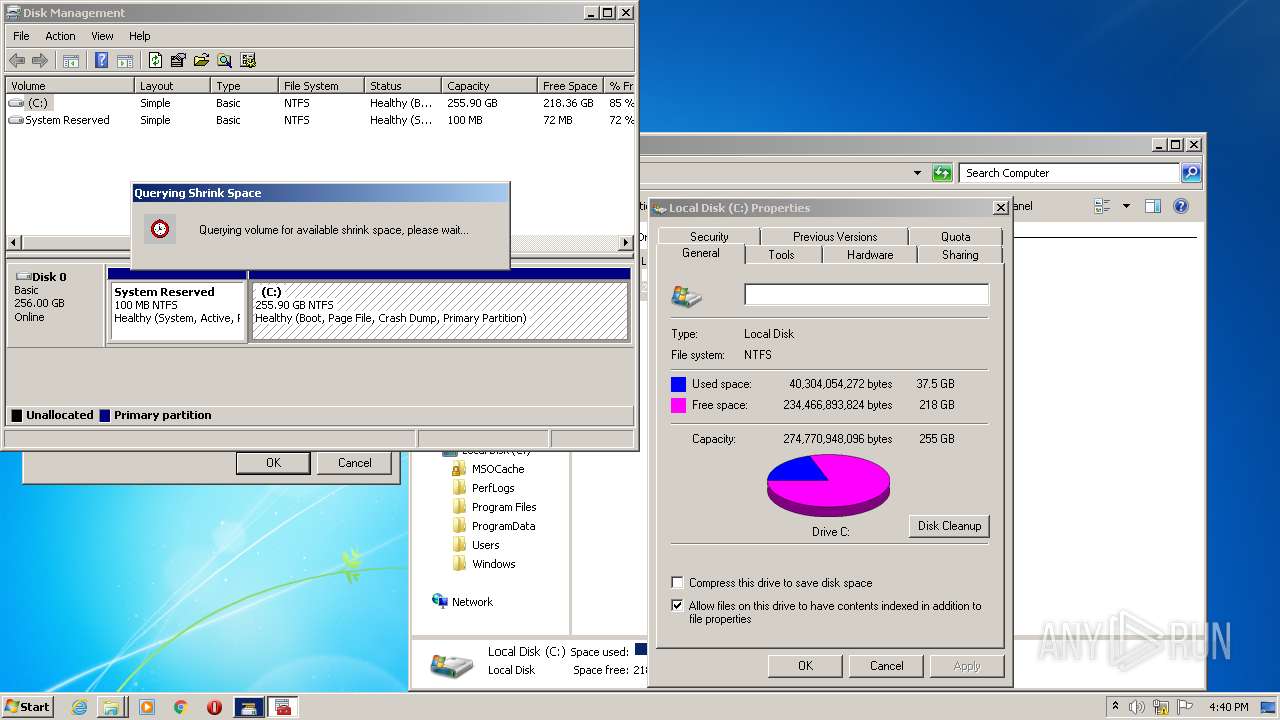
Manual execution by user
- chrome.exe (PID: 2500)
- explorer.exe (PID: 2364)
- mmc.exe (PID: 3716)
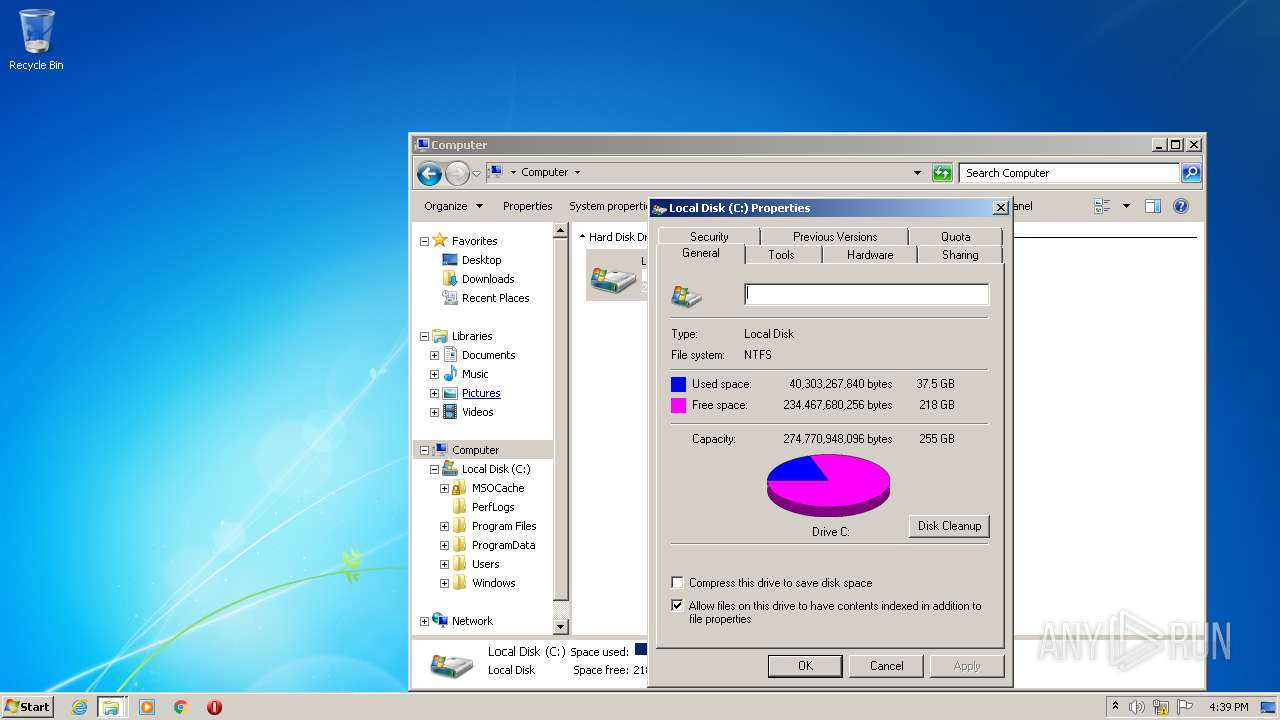
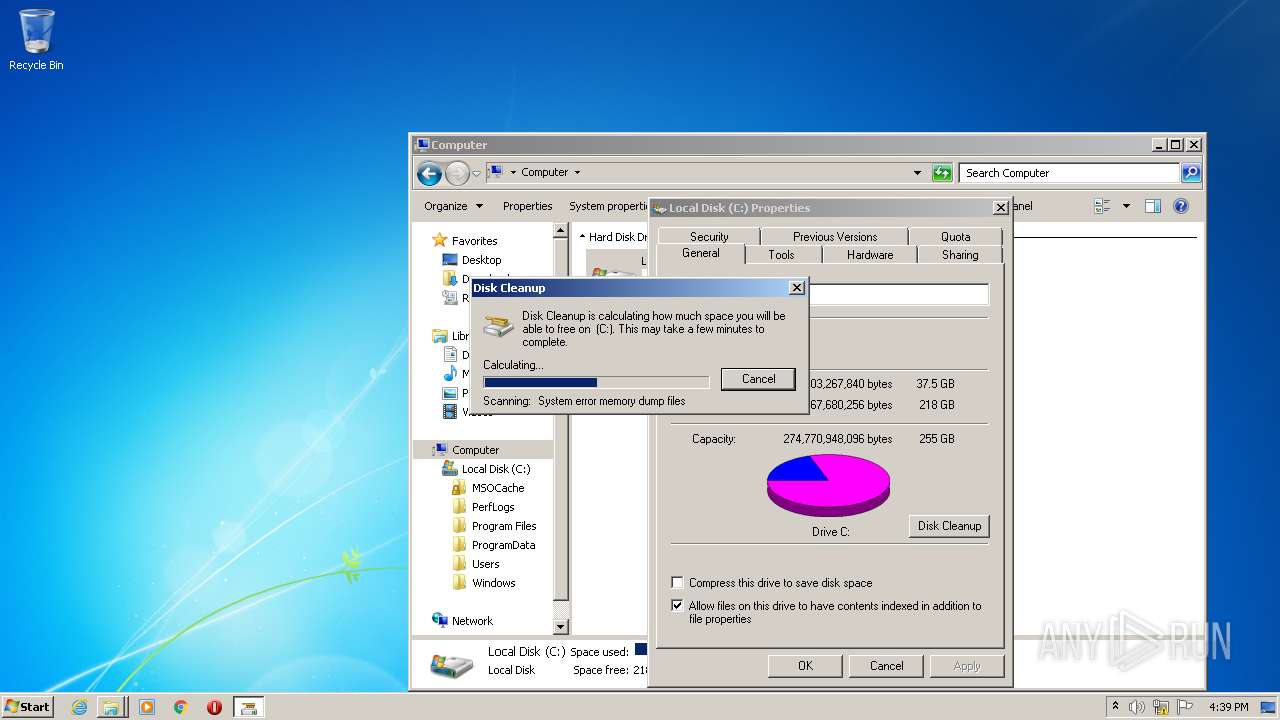
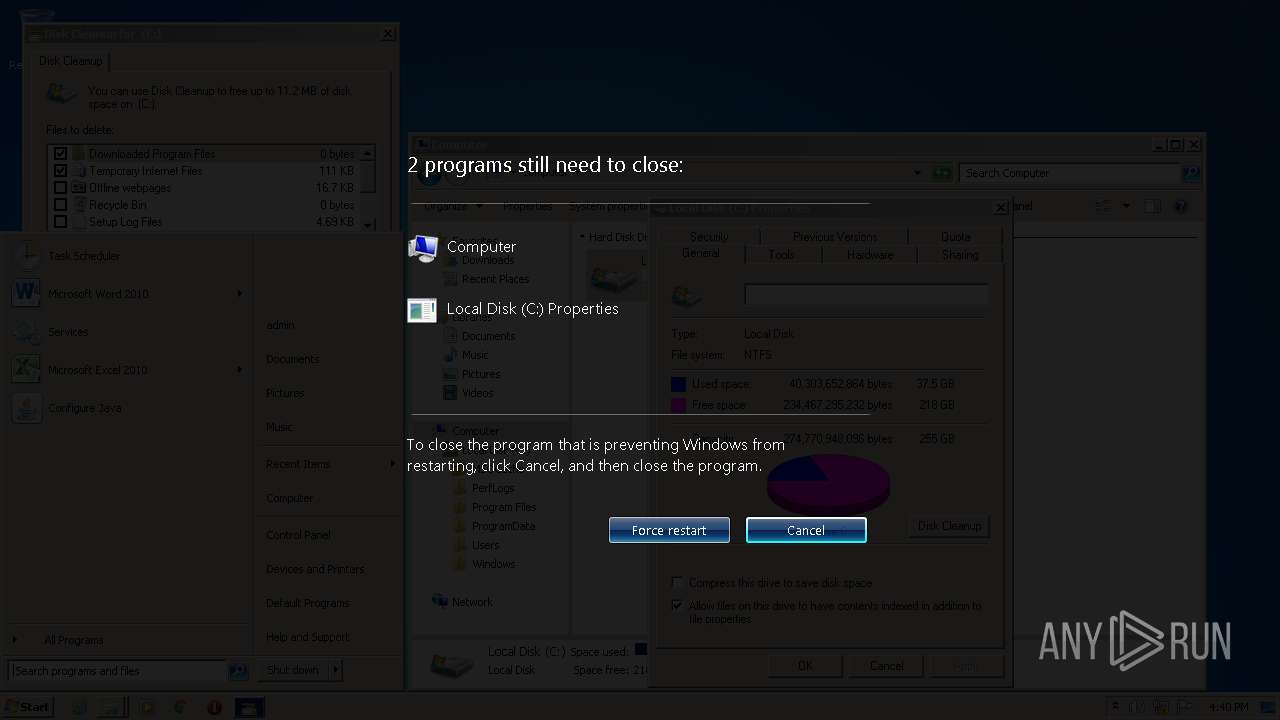
- cleanmgr.exe (PID: 1392)
- cleanmgr.exe (PID: 1776)
- mmc.exe (PID: 3076)
Reads the computer name
- chrome.exe (PID: 2500)
- chrome.exe (PID: 1136)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 3336)
- explorer.exe (PID: 2364)
- DllHost.exe (PID: 3228)
- DllHost.exe (PID: 2676)
- cleanmgr.exe (PID: 1392)
- mmc.exe (PID: 3076)
- vds.exe (PID: 112)
- vdsldr.exe (PID: 3200)
Reads settings of System Certificates
- chrome.exe (PID: 1136)
Reads Microsoft Office registry keys
- cleanmgr.exe (PID: 1392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | v5 |
|---|---|
| ProductName: | REVERSIVE |
| OriginalFileName: | loader.exe |
| LegalCopyright: | Copyright (C) 2022 REVERSIVE.xyz |
| InternalName: | loader.exe |
| FileVersion: | 5.0.0.0 |
| FileDescription: | REVERSIVE Software for CS:GO |
| CompanyName: | REVERSIVE |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.1 |
| FileVersionNumber: | 5.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x5870fe |
| UninitializedDataSize: | - |
| InitializedDataSize: | 868352 |
| CodeSize: | 925696 |
| LinkerVersion: | 14.31 |
| PEType: | PE32 |
| TimeStamp: | 2022:04:30 03:43:05+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Total processes
77
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 112 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1036,8698976230689342103,464256680203125355,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1380 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
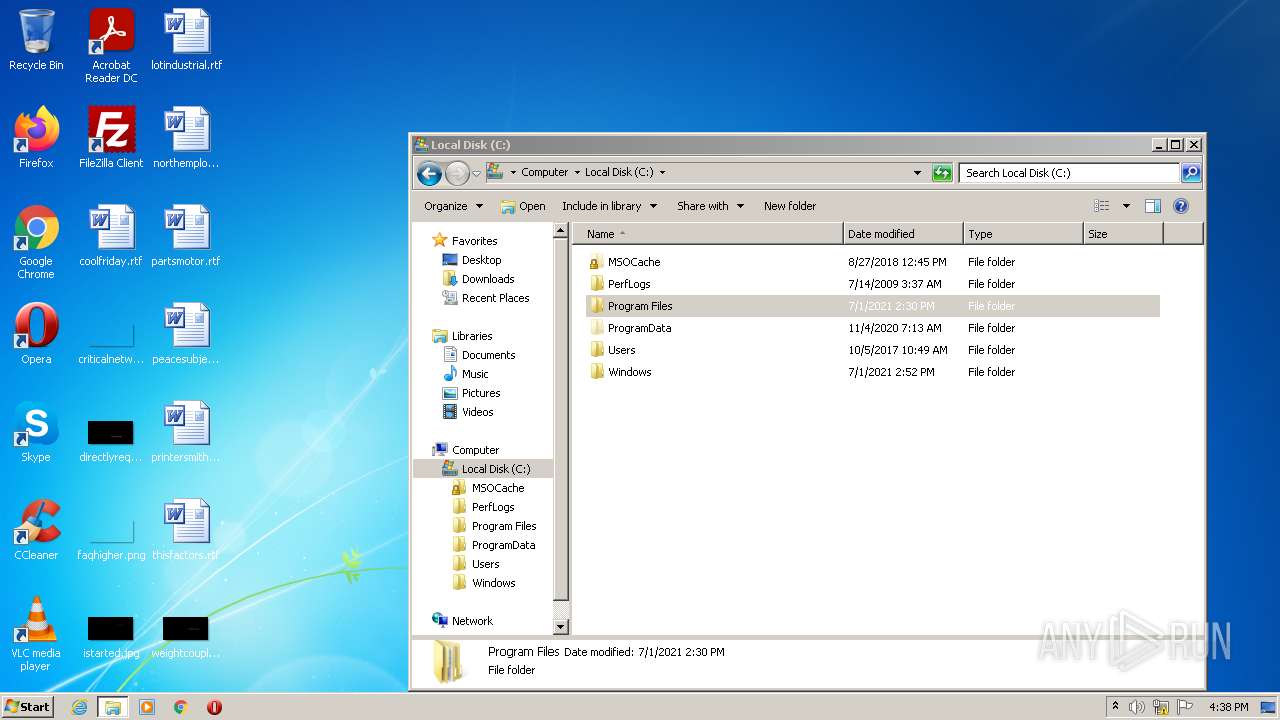
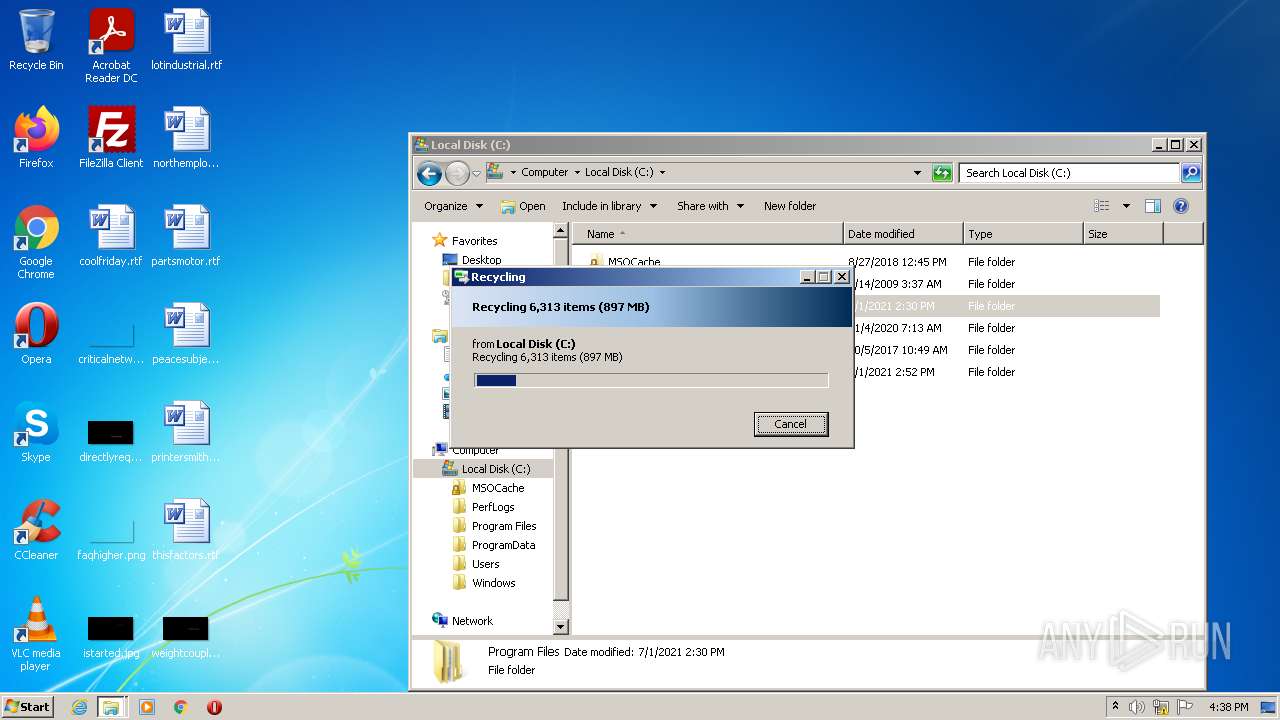
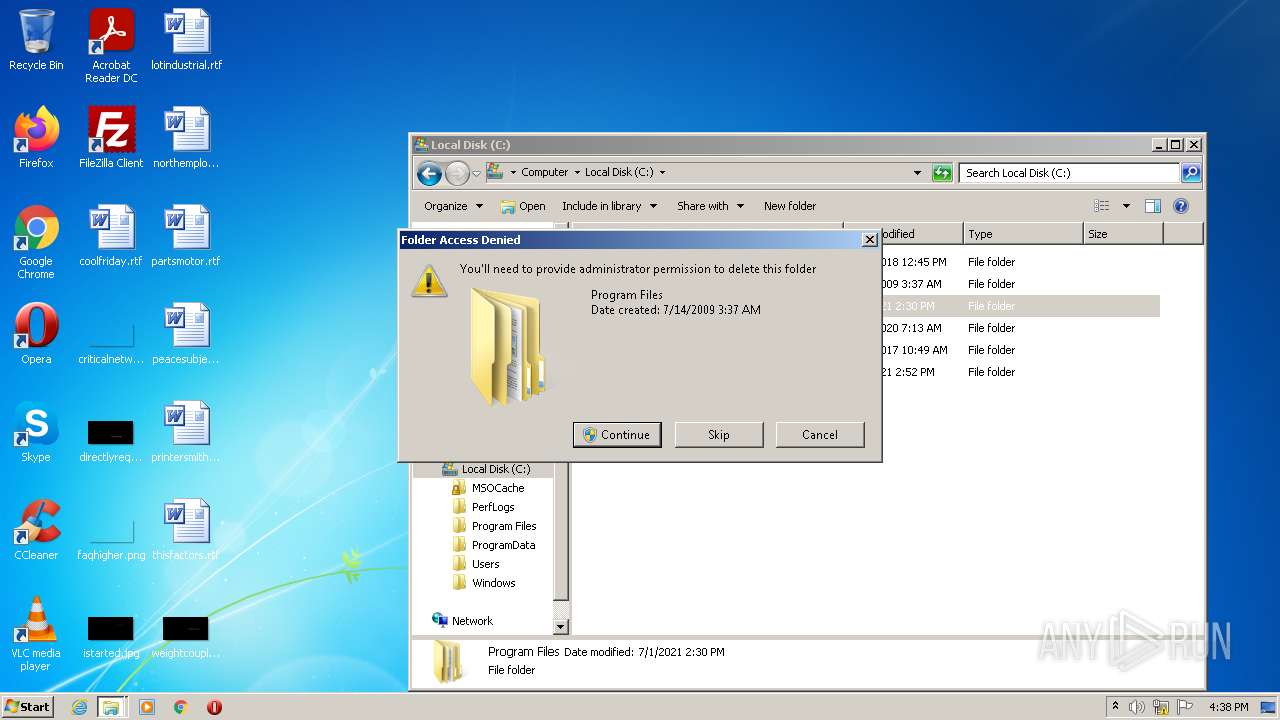
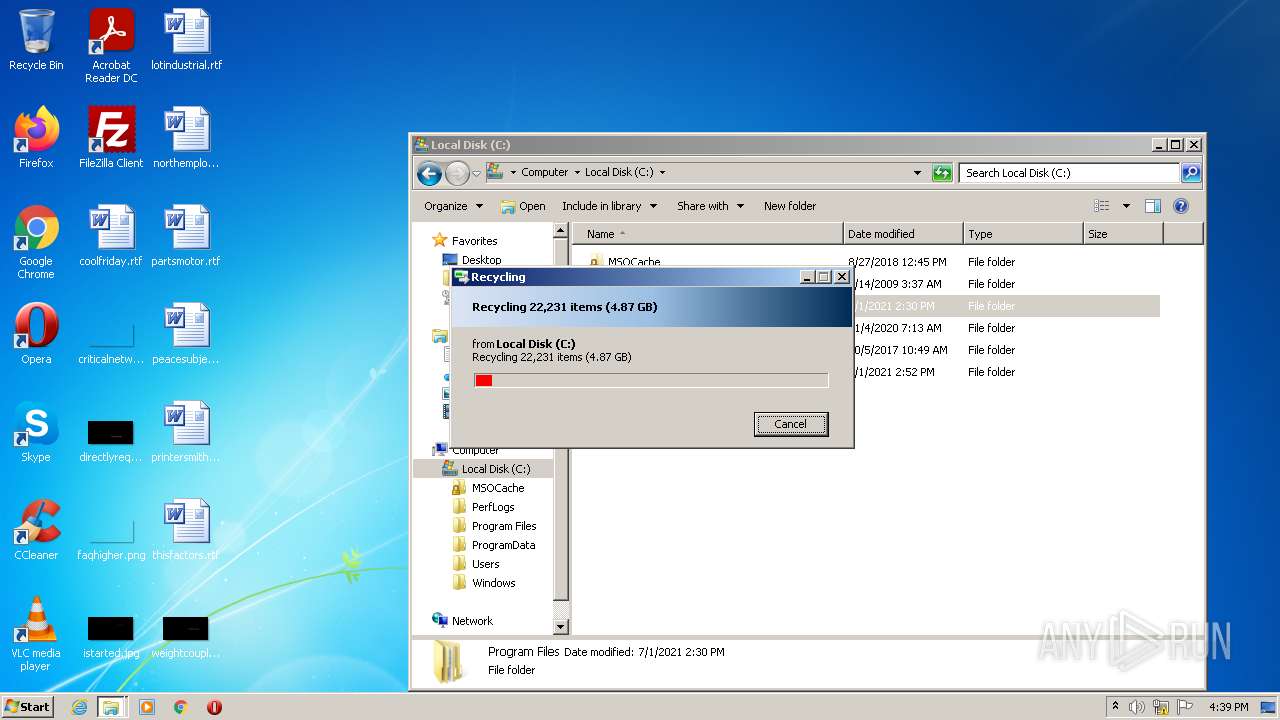
| 1392 | "C:\Windows\System32\cleanmgr.exe" /D C | C:\Windows\System32\cleanmgr.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Disk Space Cleanup Manager for Windows Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1776 | "C:\Windows\System32\cleanmgr.exe" /D C | C:\Windows\System32\cleanmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Disk Space Cleanup Manager for Windows Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8698976230689342103,464256680203125355,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8698976230689342103,464256680203125355,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,8698976230689342103,464256680203125355,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3044 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\AppData\Local\Temp\reversive.exe" | C:\Users\admin\AppData\Local\Temp\reversive.exe | Explorer.EXE | ||||||||||||
User: admin Company: REVERSIVE Integrity Level: HIGH Description: REVERSIVE Software for CS:GO Exit code: 3221225781 Version: 5.0.0.0 Modules
| |||||||||||||||
| 2364 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,8698976230689342103,464256680203125355,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2968 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
8 195
Read events
8 108
Write events
87
Delete events
0
Modification events
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
24
Text files
41
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F673CF-9C4.pma | — | |
MD5:— | SHA256:— | |||
| 1136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF138001.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF138010.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5af35055-1e59-4bf3-8121-a6f66ac69e69.tmp | text | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 1136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_1 | vxd | |
MD5:259E7ED5FB3C6C90533B963DA5B2FC1B | SHA256:35BB2F189C643DCF52ECF037603D104035ECDC490BF059B7736E58EF7D821A09 | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
14
DNS requests
10
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1136 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 142.250.185.196:443 | www.google.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 172.217.18.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 142.250.186.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 142.250.185.205:443 | accounts.google.com | Google Inc. | US | suspicious |
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
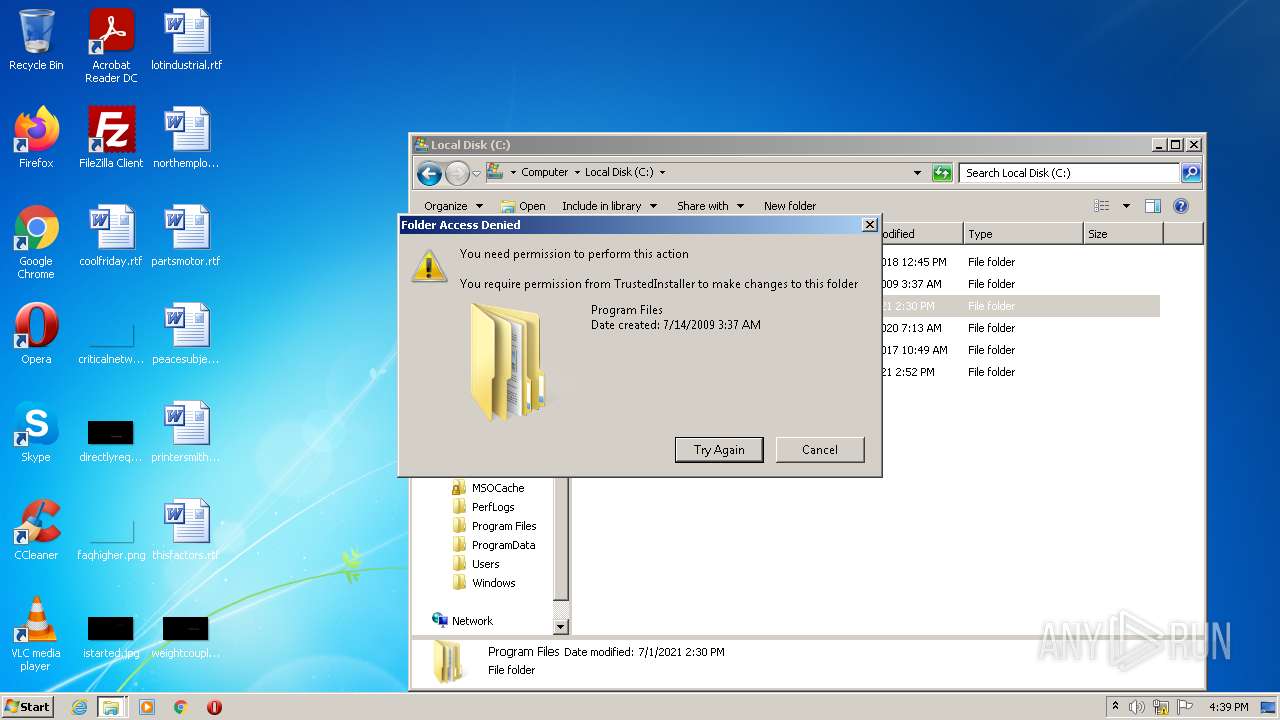
cleanmgr.exe | PID=1392 Failed to create. - CScavengeCleanup::Initialize(hr:0x800702e4) |
cleanmgr.exe | DC:Process is not elevated. |