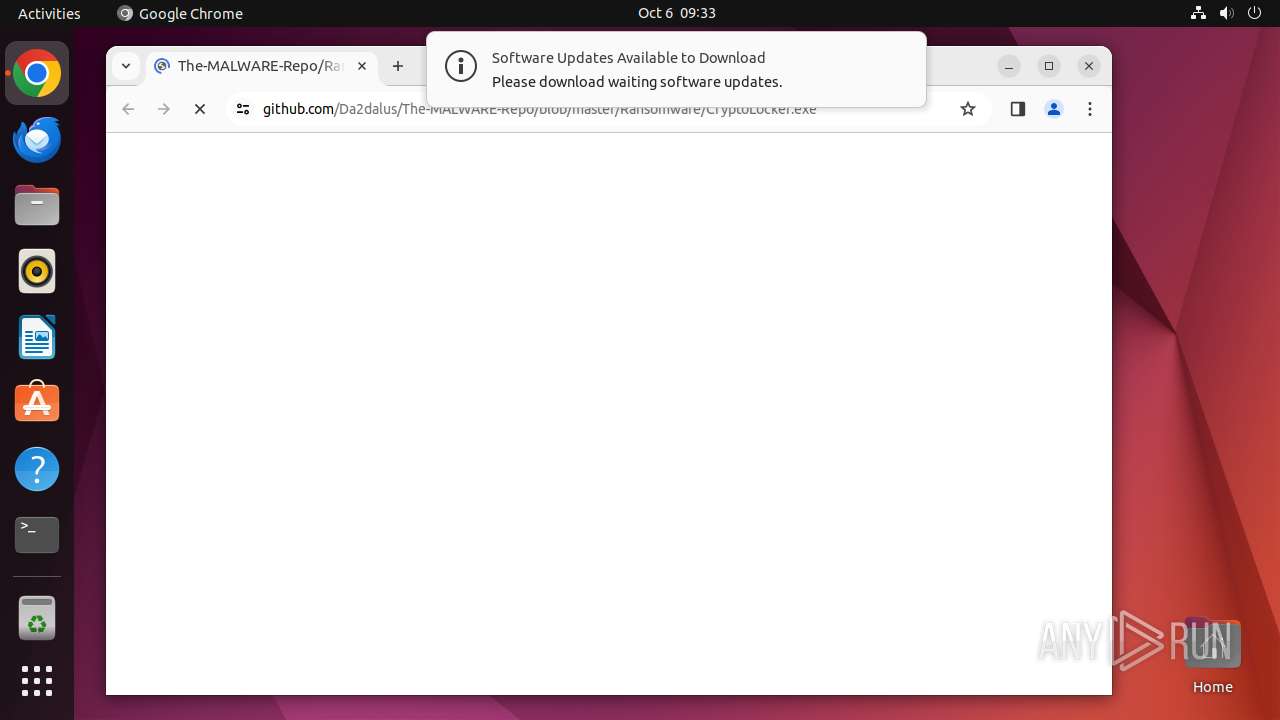
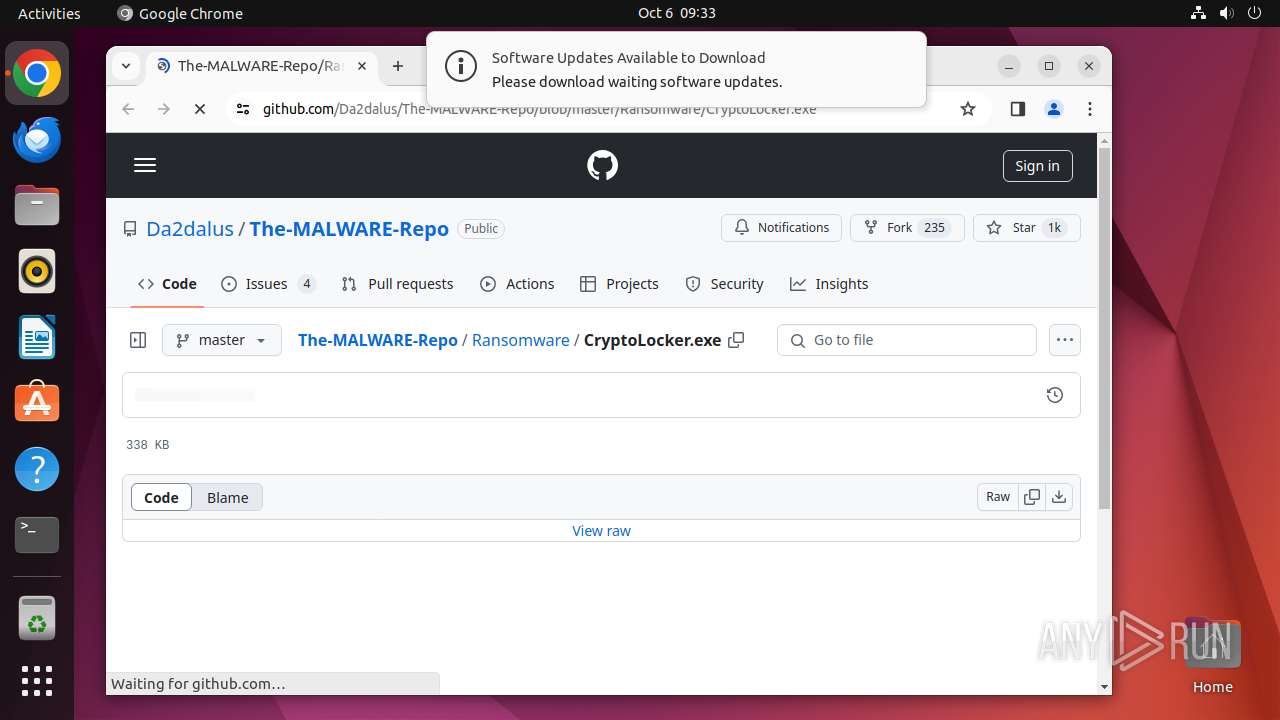
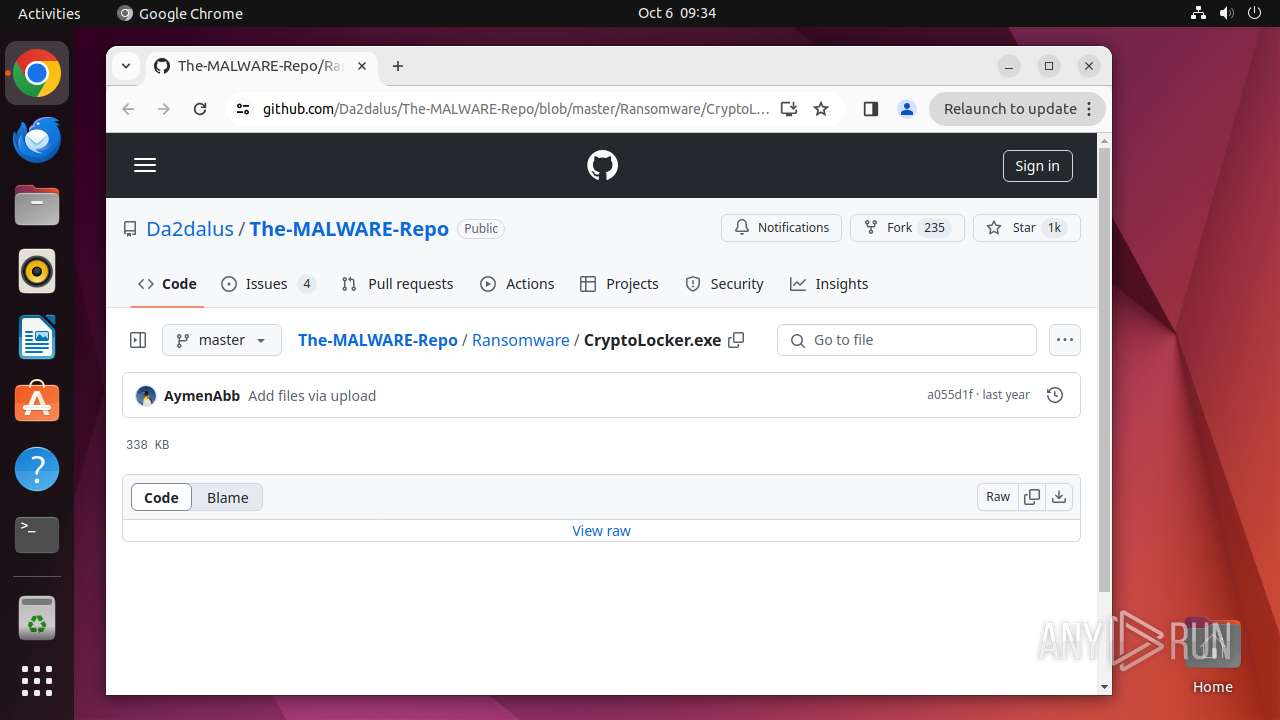
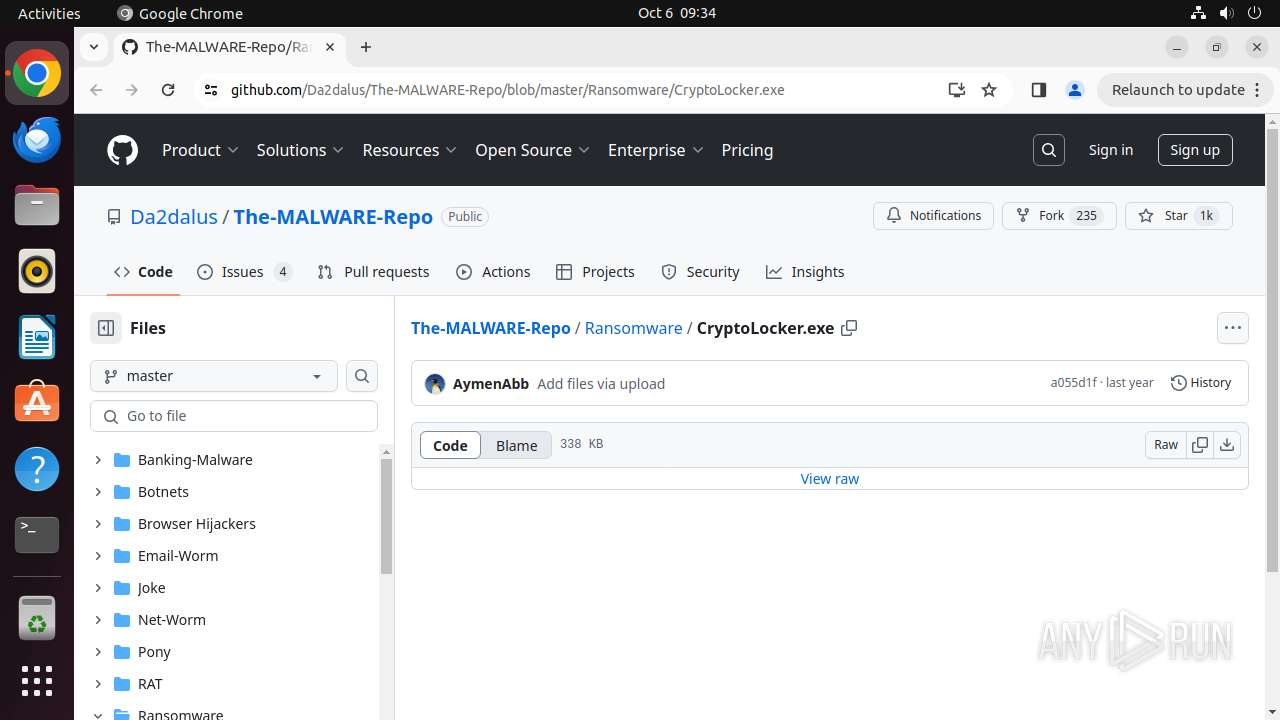
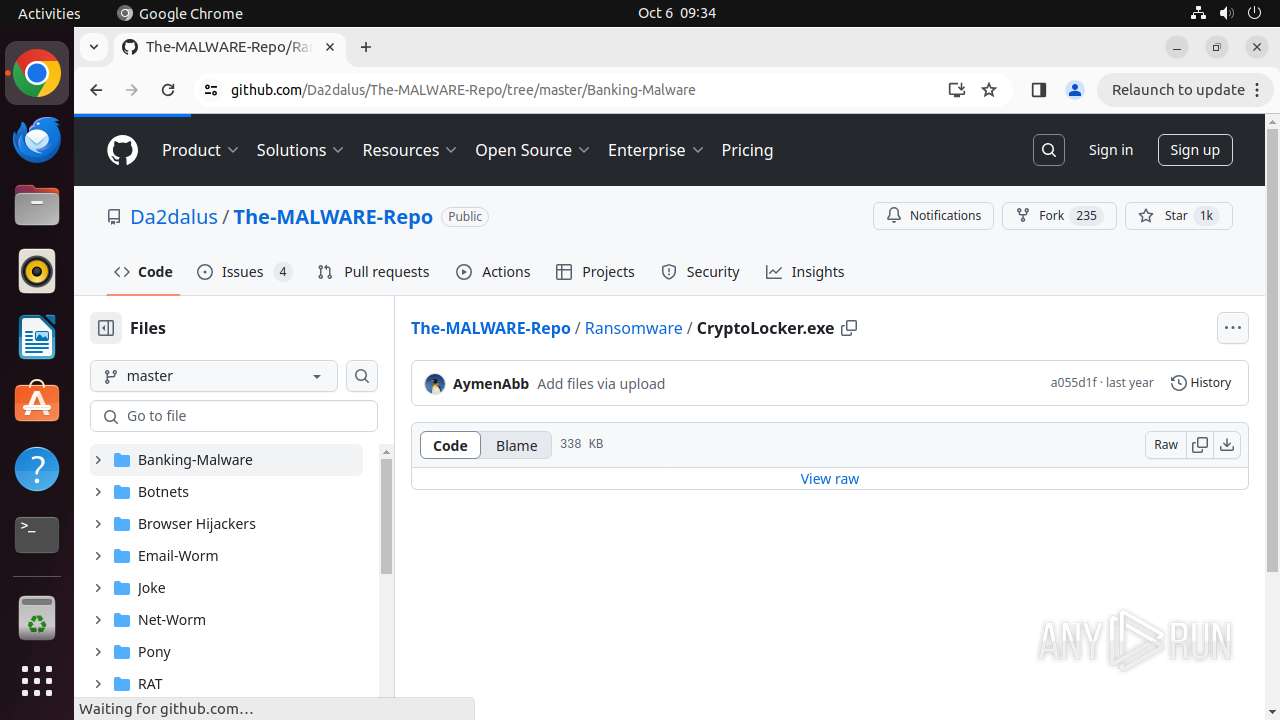
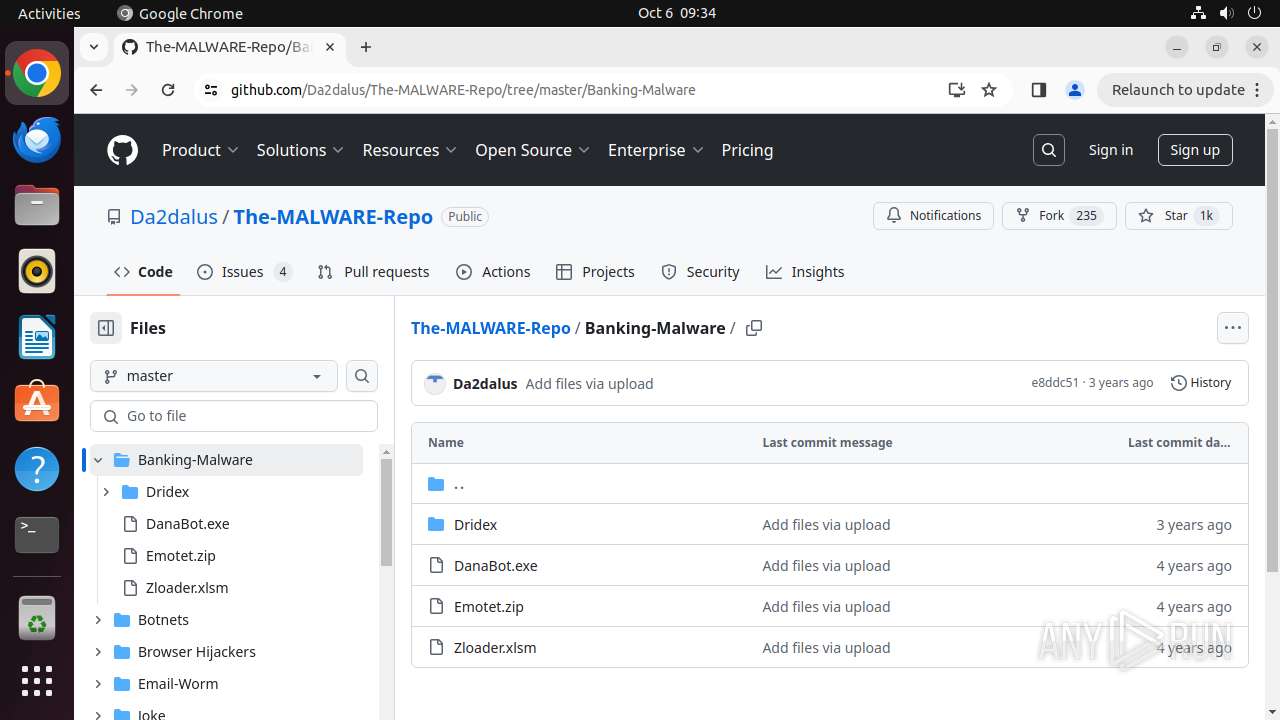
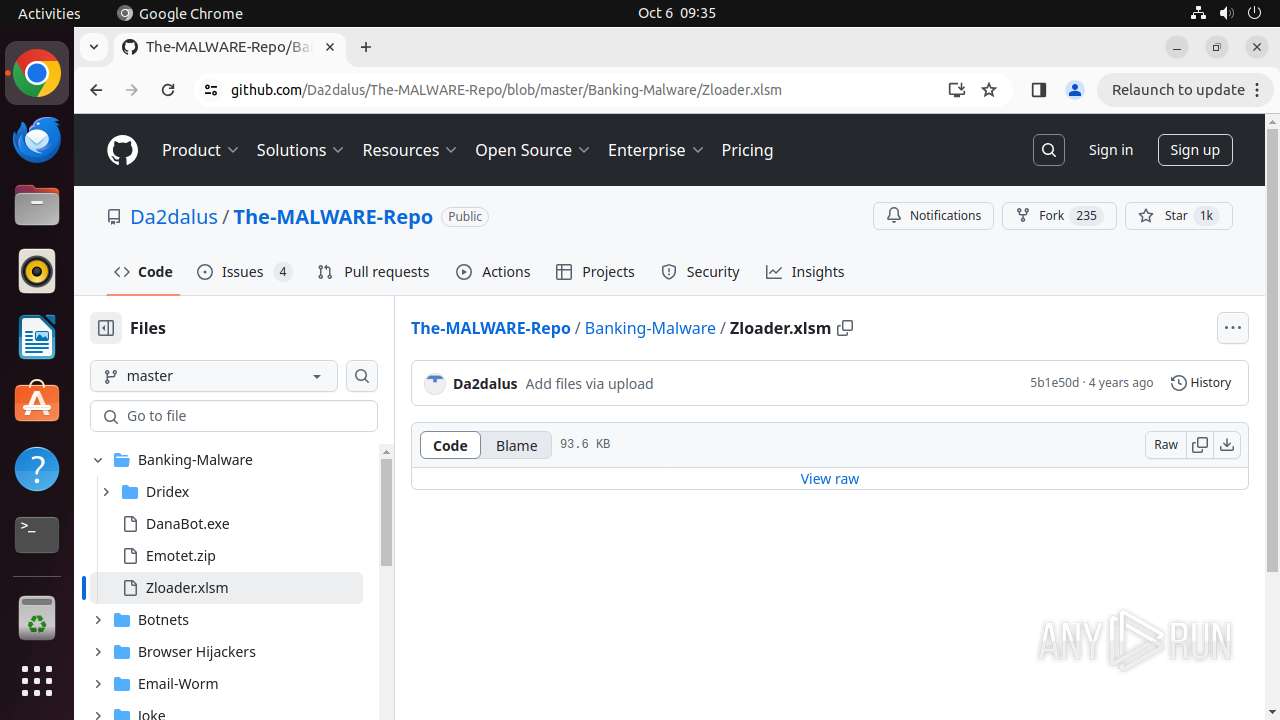
| URL: | https://github.com/Da2dalus/The-MALWARE-Repo/blob/master/Ransomware/CryptoLocker.exe |
| Full analysis: | https://app.any.run/tasks/73d57f38-892a-43c7-9082-533ce511104b |
| Verdict: | Malicious activity |
| Analysis date: | October 06, 2024, 08:33:43 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MD5: | 5AA8230B6818910BE4DD7A38F4FD2322 |
| SHA1: | B57B48B0EEB3FD05A3F5E95586292DD3E7078CB8 |
| SHA256: | 3C1F7DFA76B79CAD4B13D065663190D8547CCAF1C6F37012C41A0DB0A88AD391 |
| SSDEEP: | 3:N8tEdJejSOpykOhuKIEHAz4kokA:2ubYSOcry+Az4Z |
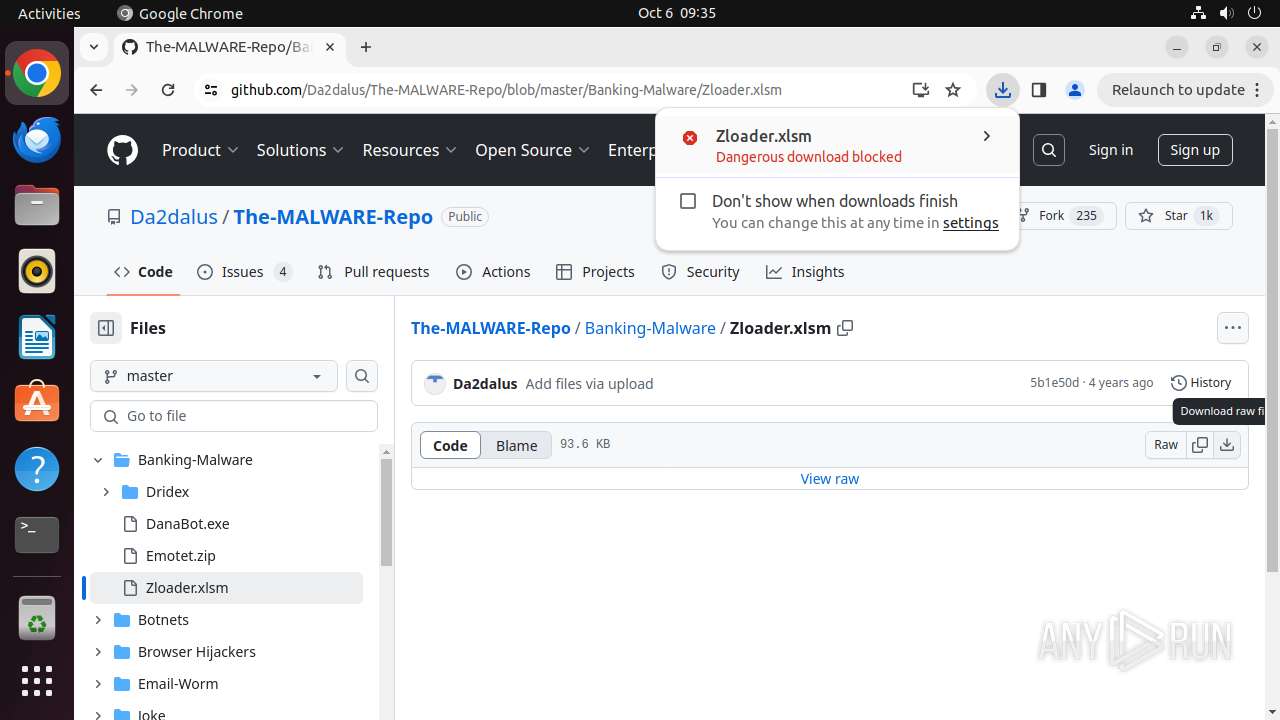
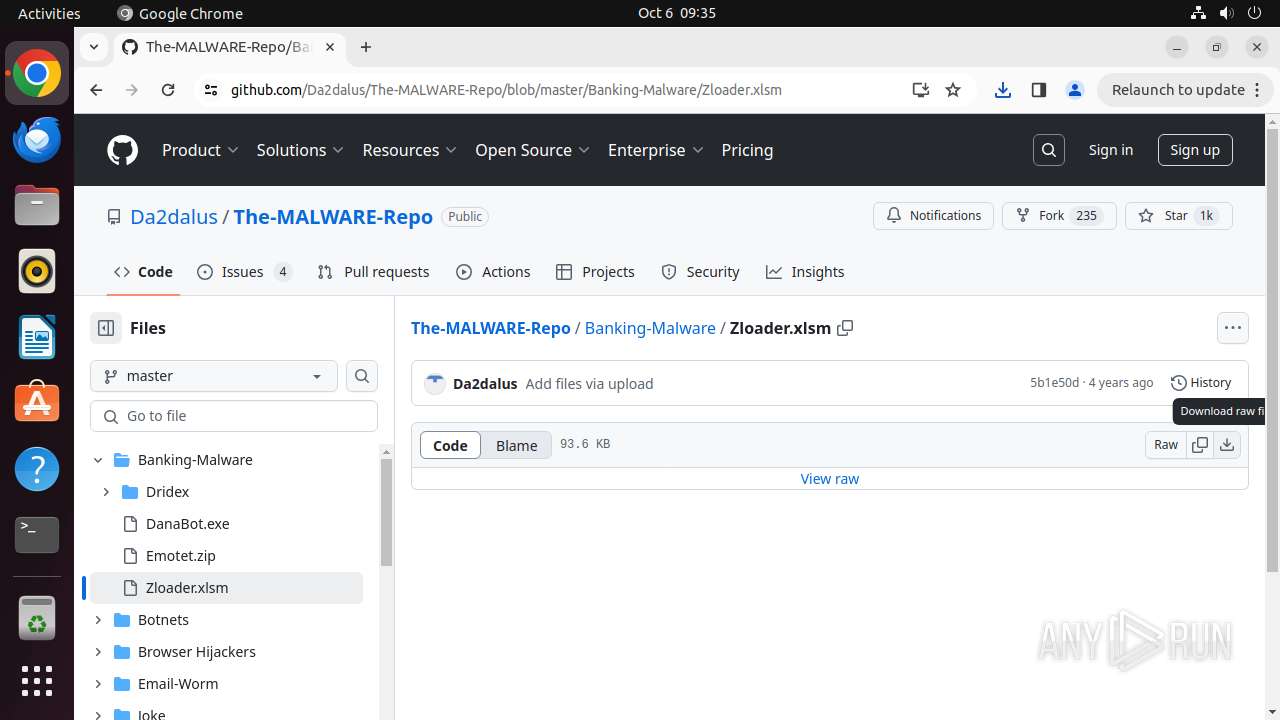
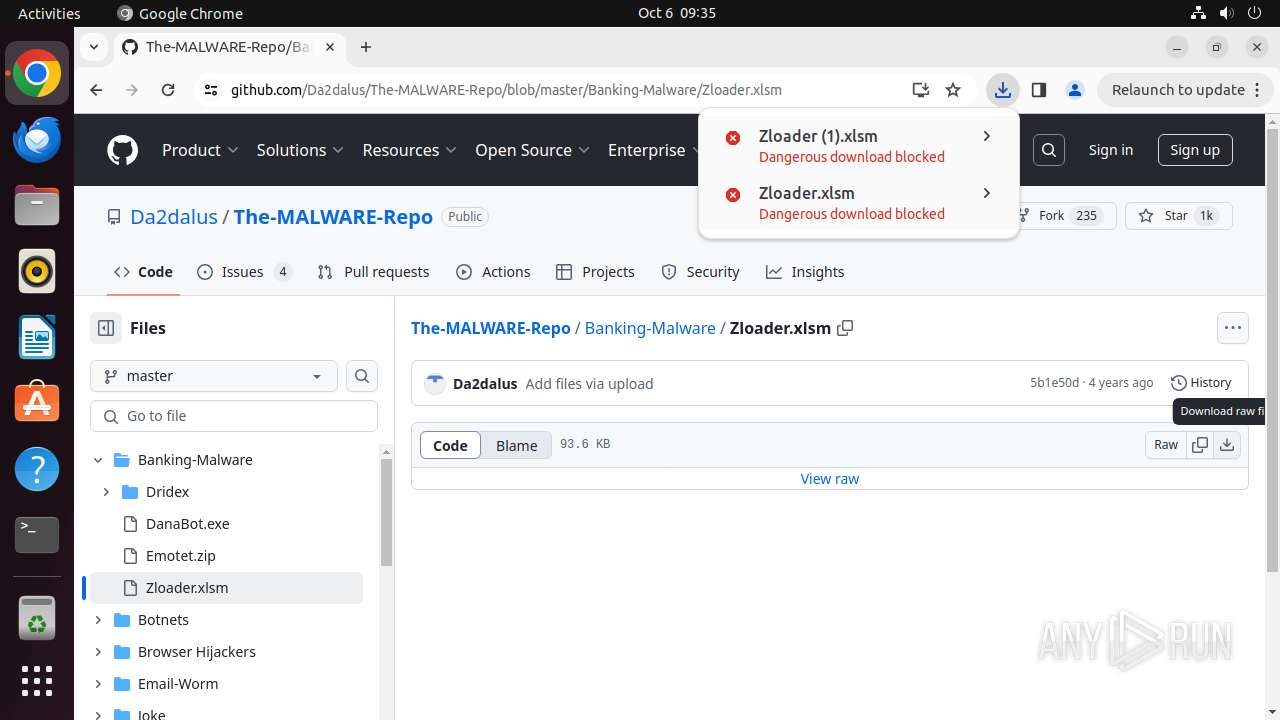
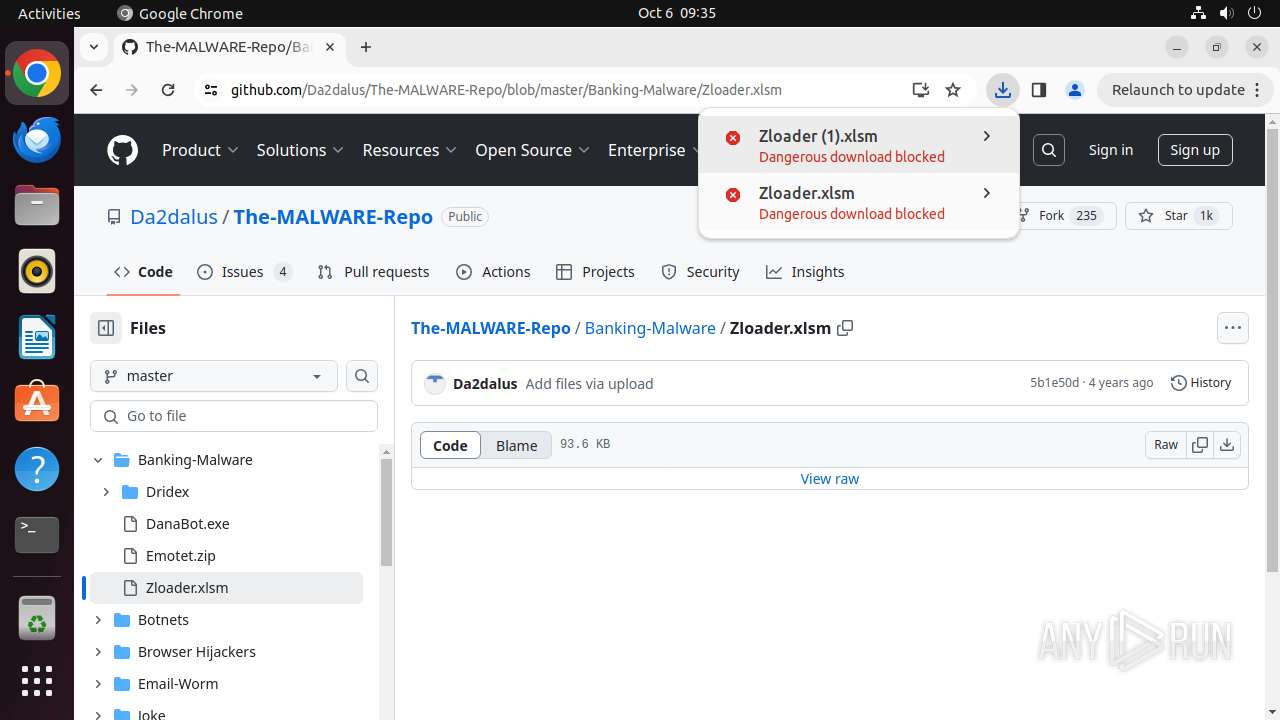
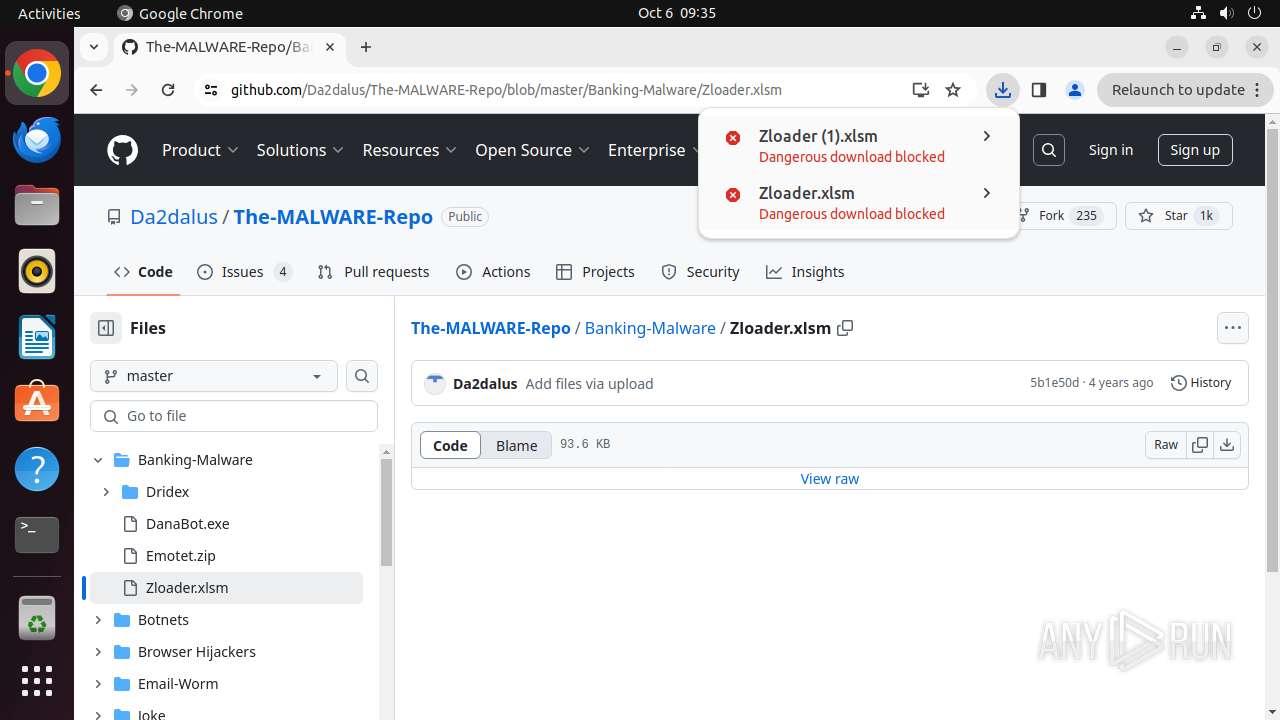
MALICIOUS
Drops known malicious document
- chrome (PID: 13915)
Drops known malicious image
- chrome (PID: 13915)
SUSPICIOUS
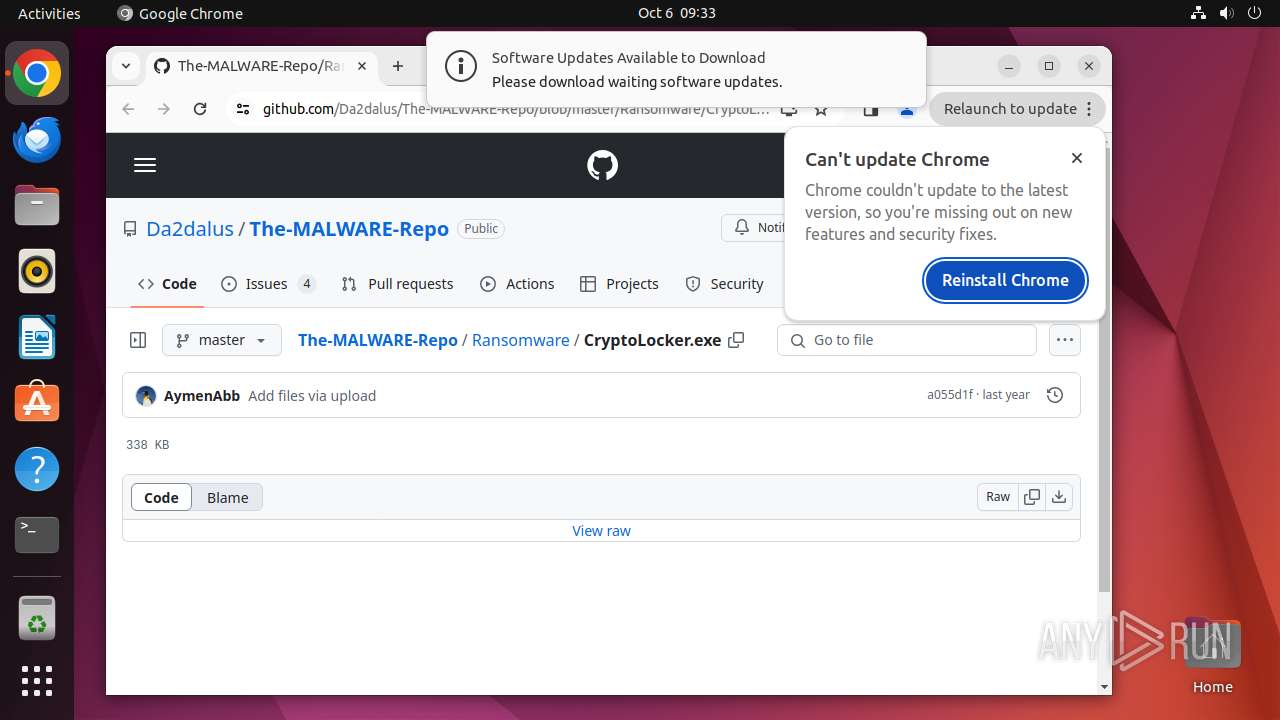
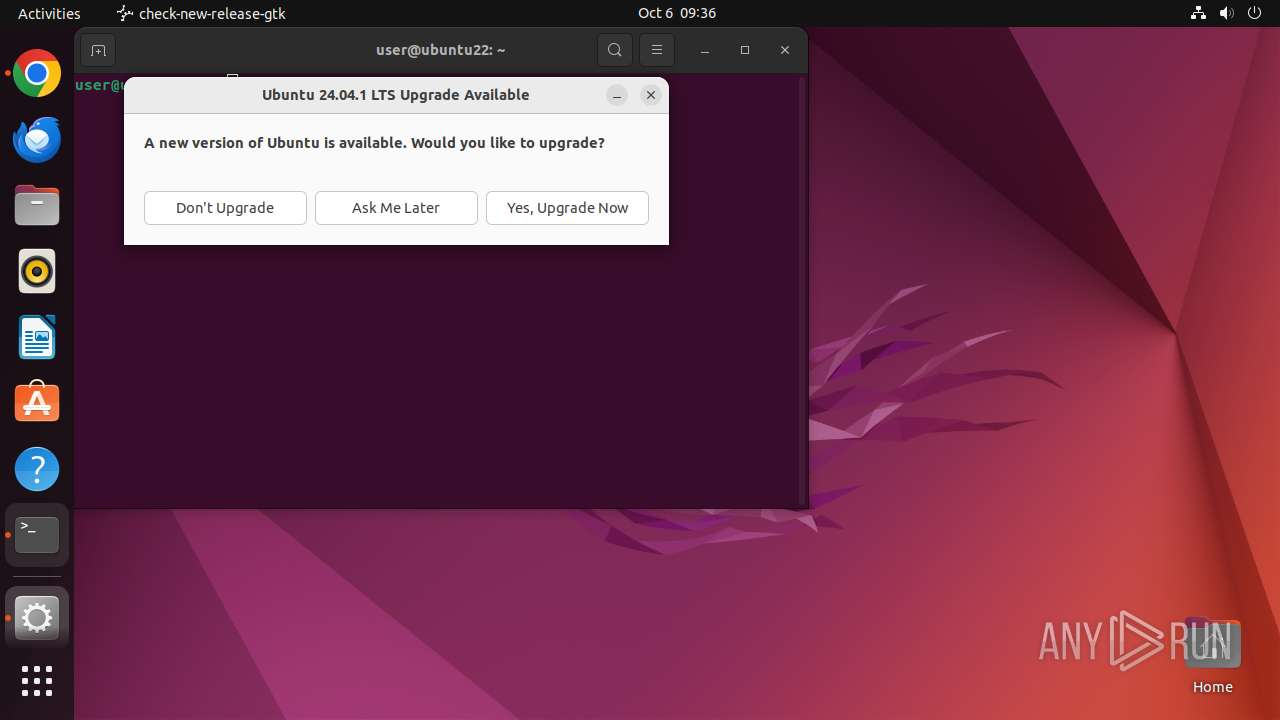
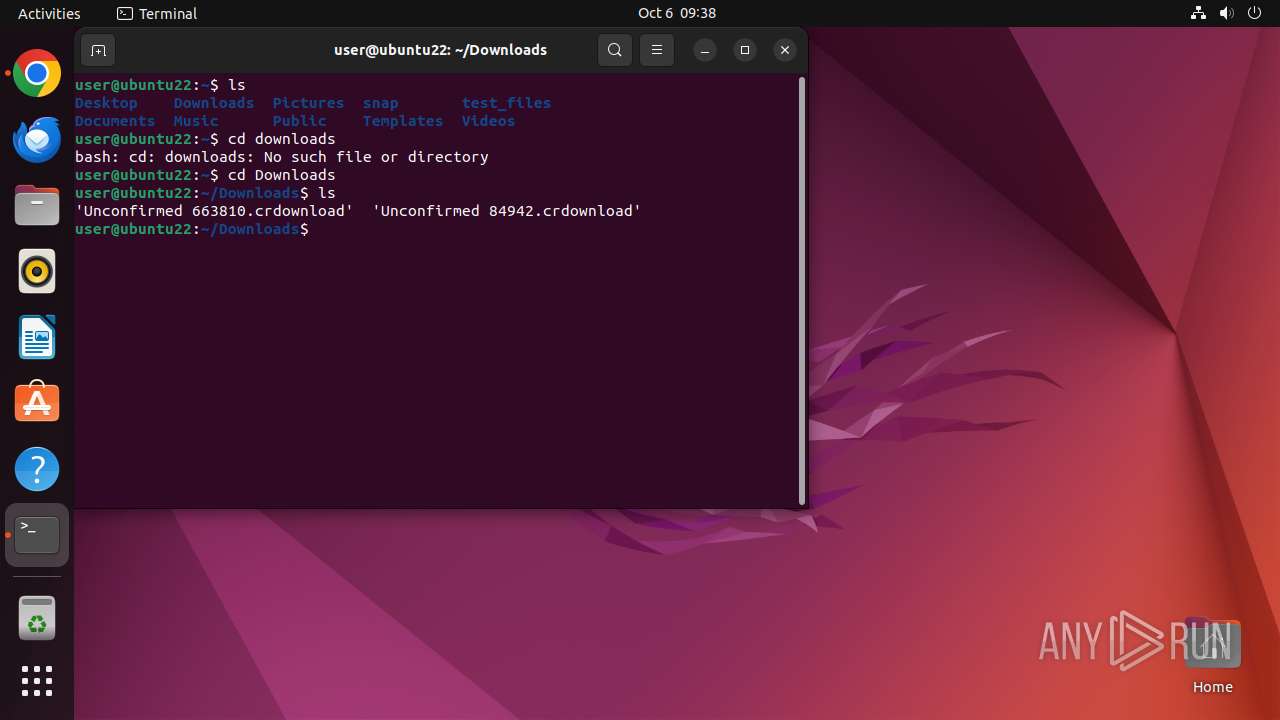
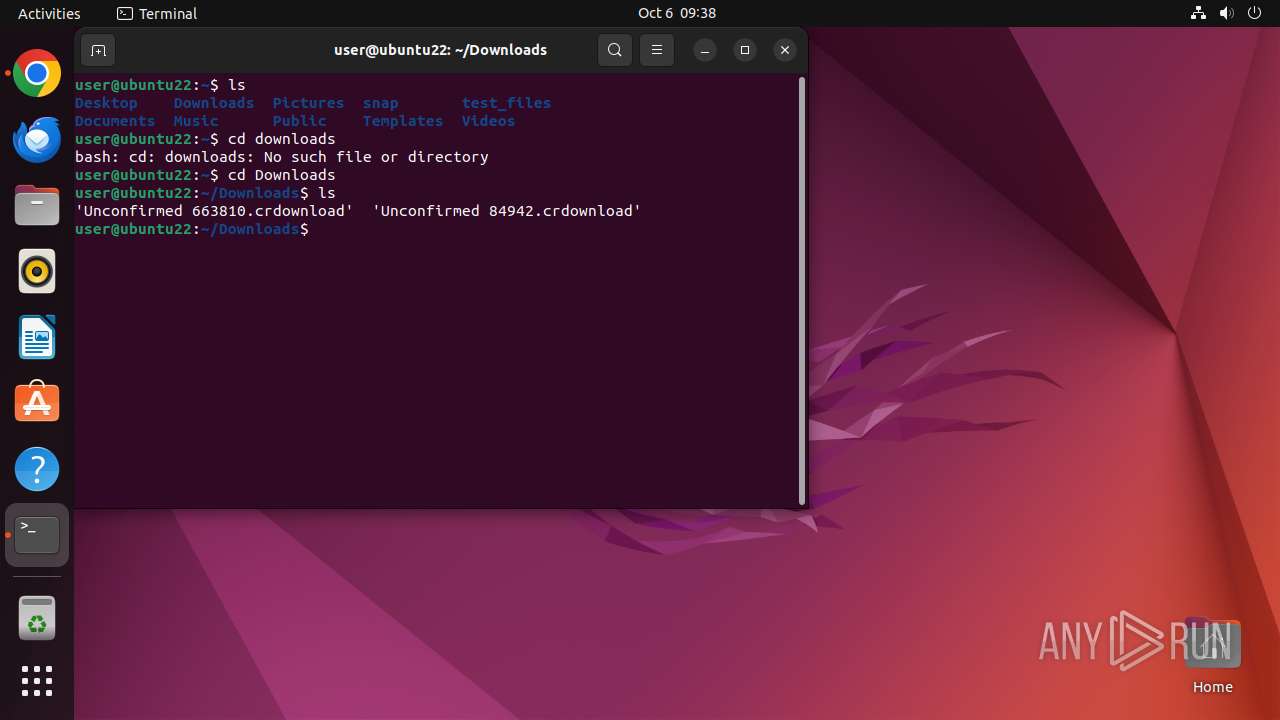
Executes commands using command-line interpreter
- update-notifier (PID: 14322)
- gnome-terminal-server (PID: 14294)
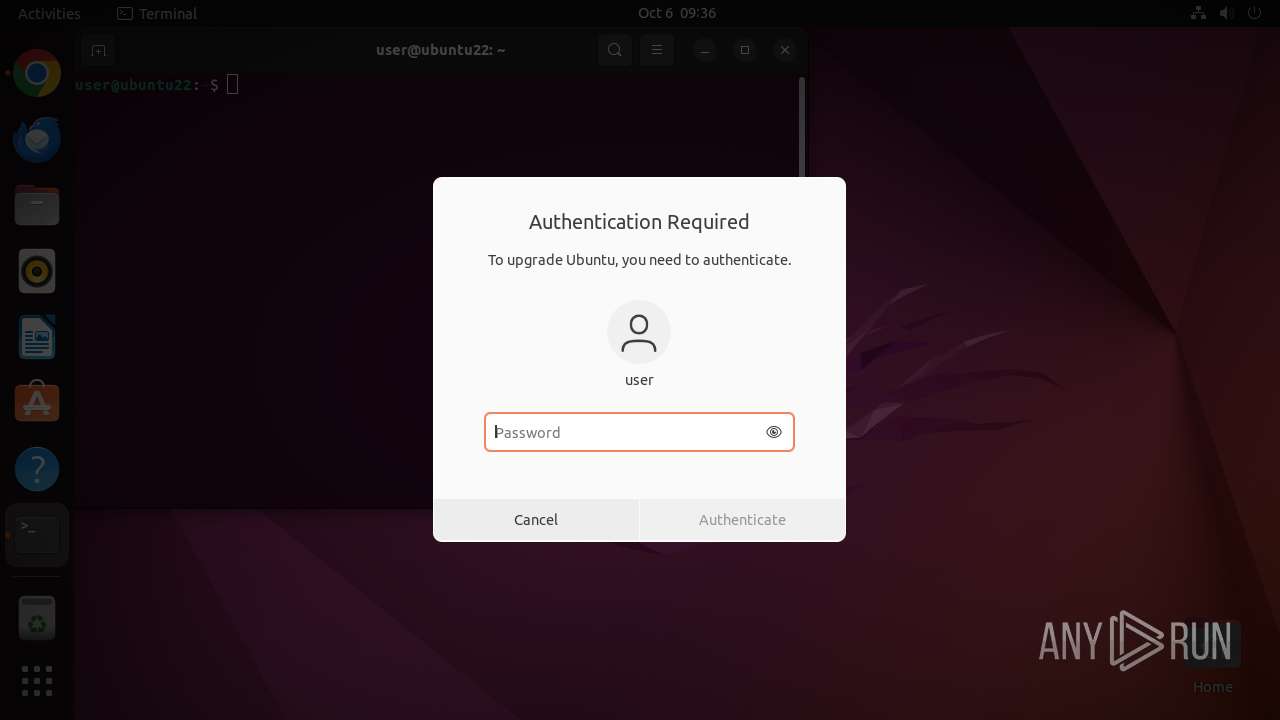
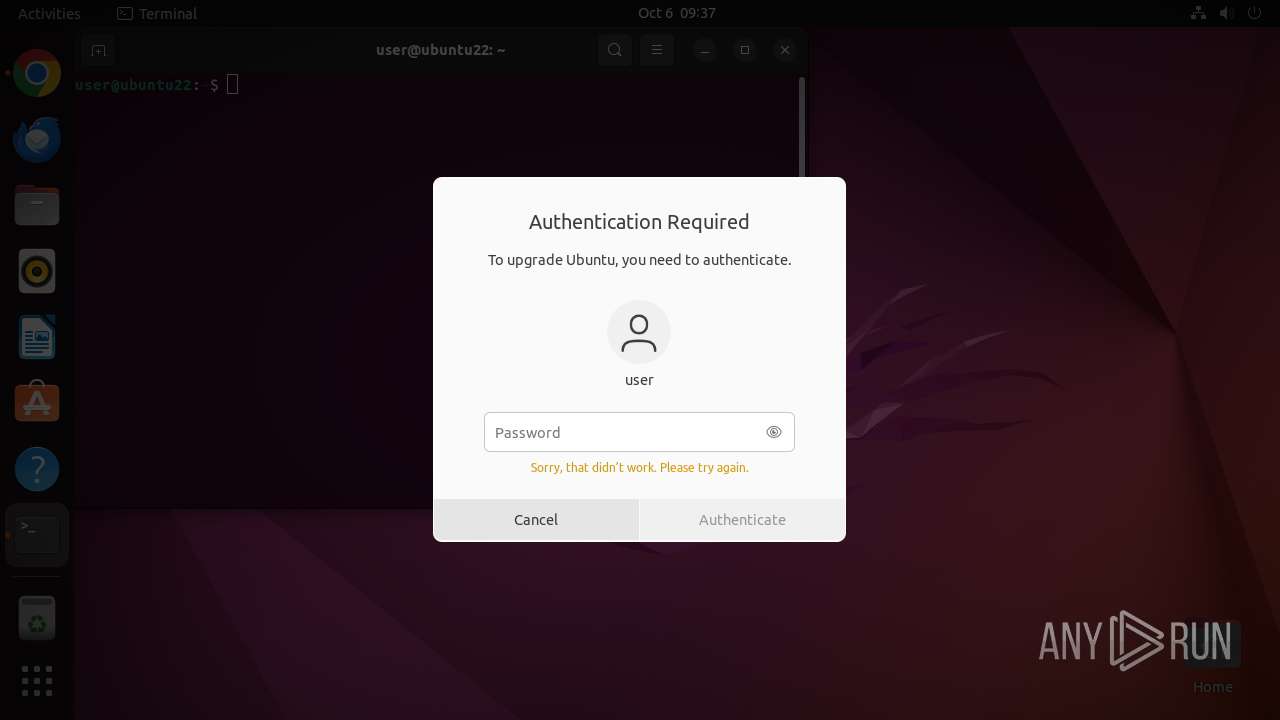
Uses pkexec (likely to bypass security restrictions)
- sh (PID: 14323)
Reads /proc/mounts (likely used to find writable filesystems)
- pkexec (PID: 14324)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
351
Monitored processes
133
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 13909 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://github\.com/Da2dalus/The-MALWARE-Repo/blob/master/Ransomware/CryptoLocker\.exe " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 13910 | sudo -iu user google-chrome https://github.com/Da2dalus/The-MALWARE-Repo/blob/master/Ransomware/CryptoLocker.exe | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 13911 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13912 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13913 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13914 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13915 | /usr/bin/google-chrome https://github.com/Da2dalus/The-MALWARE-Repo/blob/master/Ransomware/CryptoLocker.exe | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 13916 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13917 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13918 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
323
Text files
45
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 13915 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 13915 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 13915 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 13915 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 13915 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 13915 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 13915 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 13915 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 13915 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 13915 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
67
DNS requests
71
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
13961 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/pjnu5jyln4kujhcmwstuyyvyyu_4.10.2830.0/oimompecagnajdejgnnjijobebaeigek_4.10.2830.0_linux_ace35m3jiw32bj5wzzow5nia7yta.crx3 | unknown | — | — | whitelisted |
— | — | GET | 204 | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
13961 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/gcmjkmgdlgnkkcocmoeiminaijmmjnii/1.3651711652892acf34795b2c7e4d401ed2274c20e952f65cf52deeeef5bbf9b5/1.cd1978742a4afdbaaa15bf712d5c90bef4144caa99024df98f6a9ad58043ae85/f57d48f2458d0a8d34ccc2077ca88da0d44e809d2acd717f10ab827dae45743b | unknown | — | — | whitelisted |
13961 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aciueukdrxvb6khkx2mvifmvt57a_20240902.672363756.14/obedbbhbpmojnkanicioggnmelmoomoc_20240902.672363756.14_all_ENGB500000_pioxf2kb34f767sqbe3w4sspgi.crx3 | unknown | — | — | whitelisted |
13961 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/fy6gcuz7d35wpliekinea3enmi_468/lmelglejhemejginpboagddgdfbepgmp_468_all_ZZ_d4nfnzkgqvc2ngwyveswvfctoi.crx3 | unknown | — | — | whitelisted |
13961 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrrdxnjcwfqghe5ldbmjjkfukca_1088/efniojlnjndmcbiieegkicadnoecjjef_1088_all_goahc2youlbog7nygjjmilyci4.crx3 | unknown | — | — | whitelisted |
13961 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adn3tbb2pd3we3bgvlhz7kbeqlca_2024.9.30.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.09.30.01_all_acosqho7p2tdp4gkqv4e3ge37qna.crx3 | unknown | — | — | whitelisted |
13961 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
13961 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad4hpytkvfw66zgvp6ccf22mfbbq_2024.10.4.0/niikhdgajlphfehepabhhblakbdgeefj_2024.10.04.00_all_adwqxuuranzmeclphki5yktwfkaa.crx3 | unknown | — | — | whitelisted |
13961 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/khaoiebndkojlmppeemjhbpbandiljpe/1.05399c5840405f4af2454470ceccaa3d097f07e271705cf37c1e5559ce793eeb/1.1471c6c104c7e11f08fd446f83dcdb396b1fef335f4e3c744007c2272064f538/44367e7bc13464ae48fa3a83edb9a1fc3258aa32540abba470d2ff291e5eaf0e | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.97:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 212.102.56.178:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 91.189.91.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
github.com |
| shared |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |