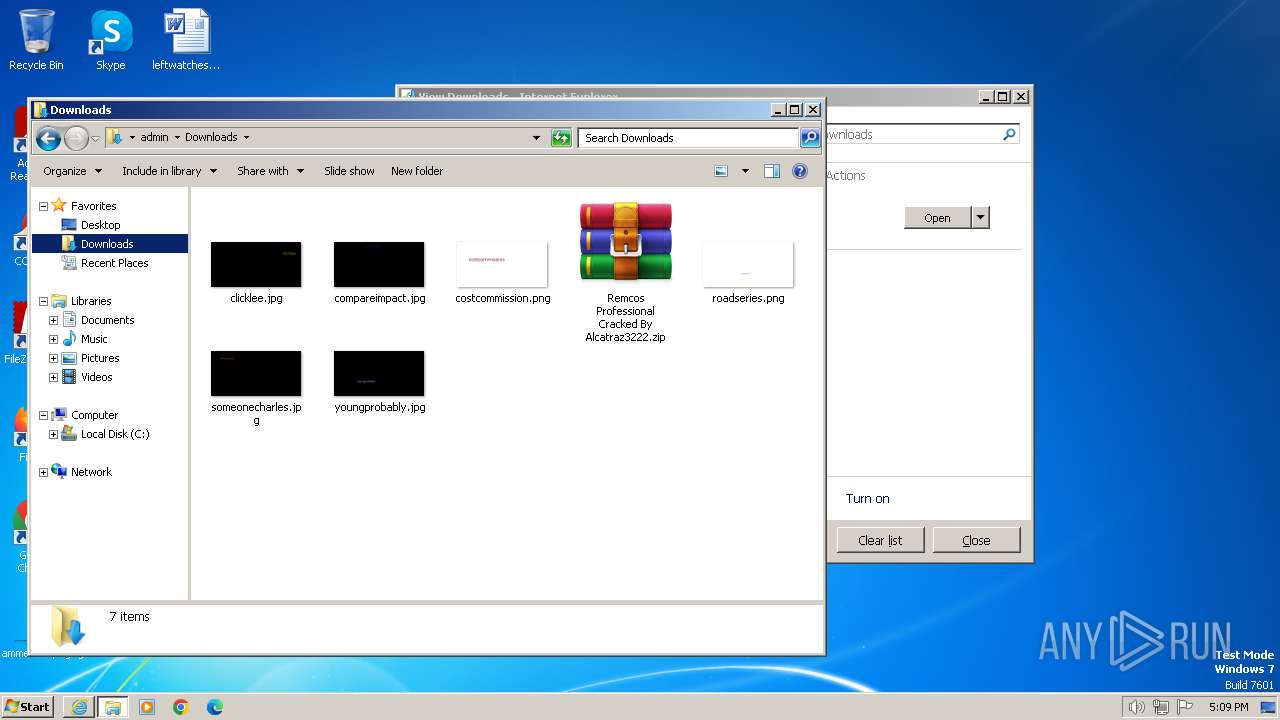
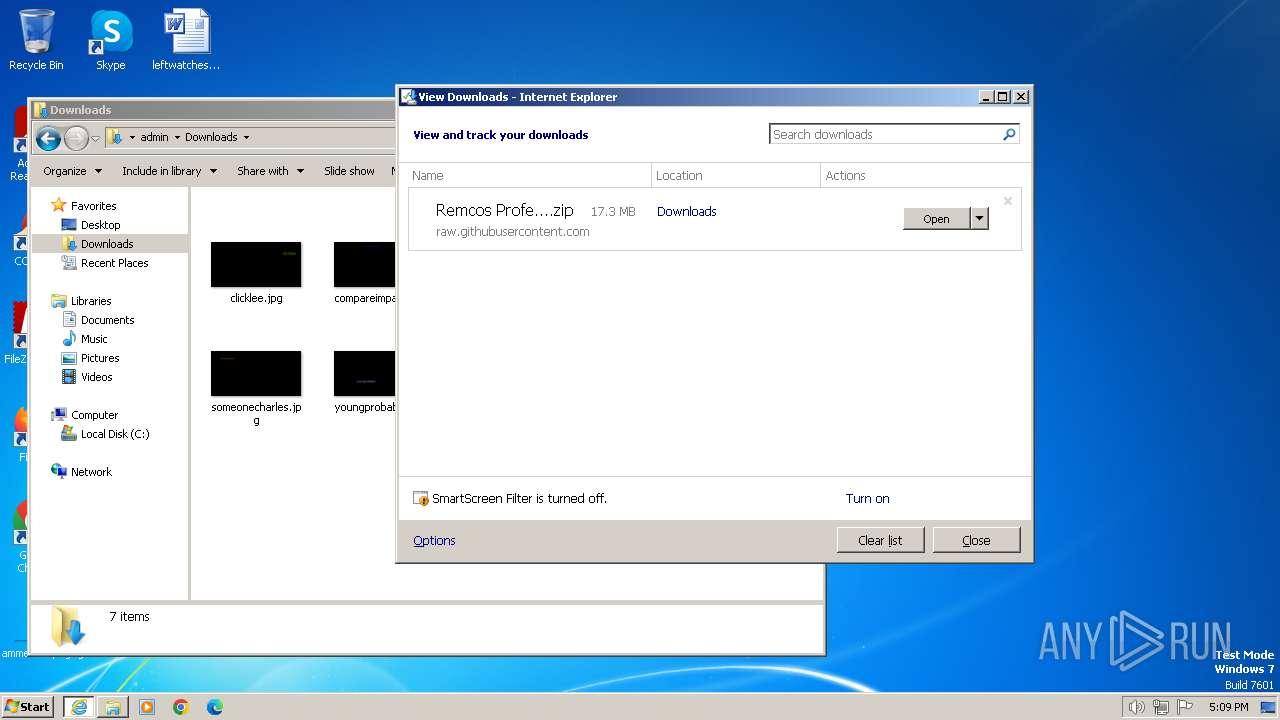
| URL: | https://raw.githubusercontent.com/cybertoxin/Remcos-Professional-Cracked-By-Alcatraz3222/master/Remcos%20Professional%20Cracked%20By%20Alcatraz3222.zip |
| Full analysis: | https://app.any.run/tasks/b5ef8957-bf09-4b37-a319-1dd0190ac672 |
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2024, 17:08:51 |
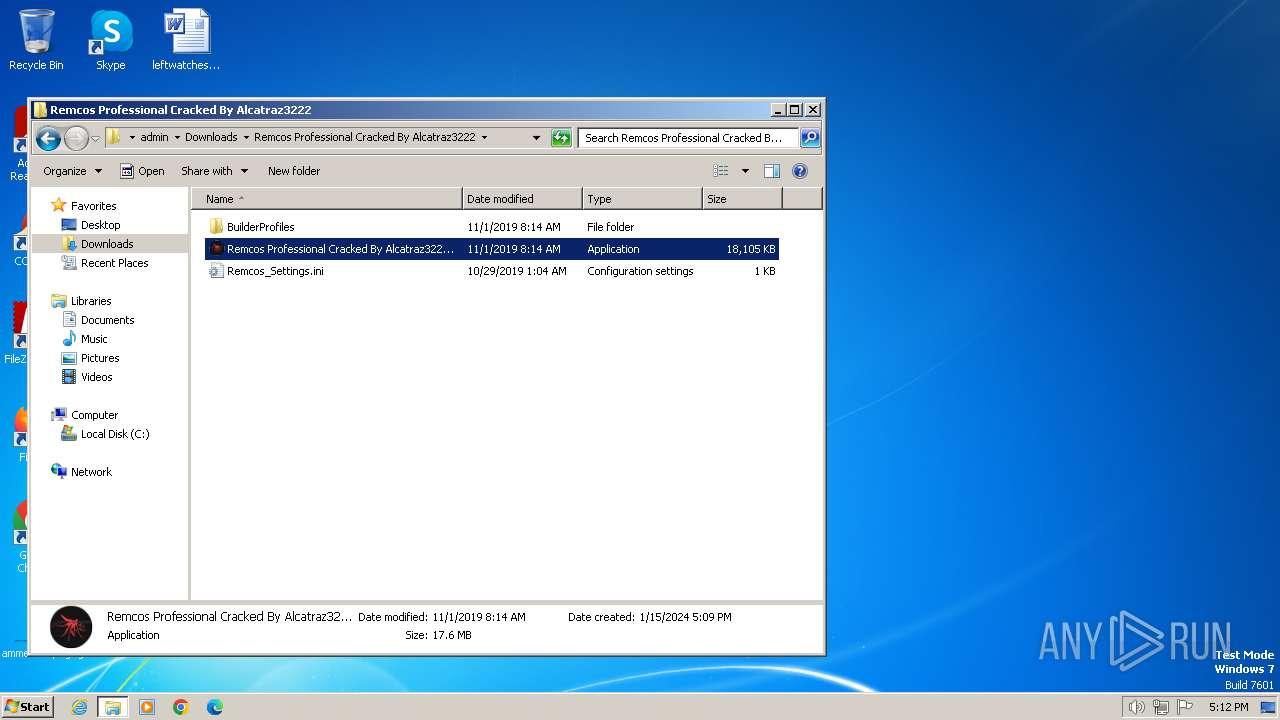
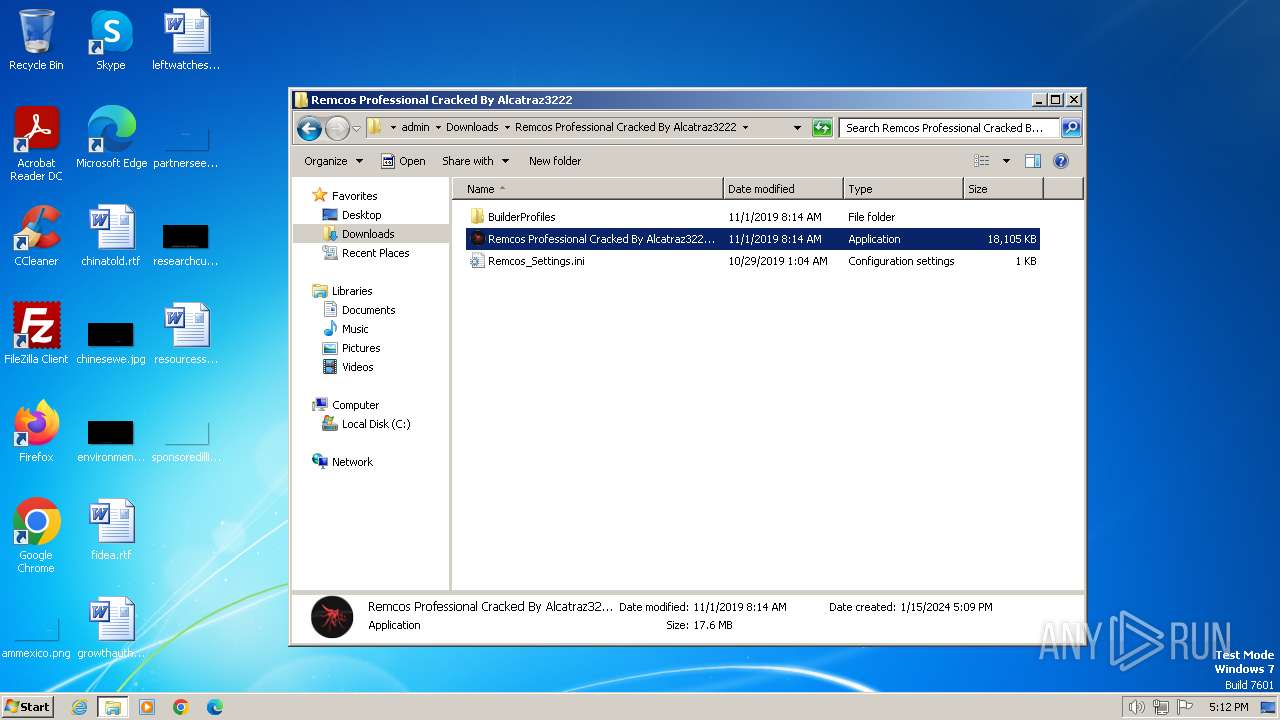
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DA73A1D7AD122C594405385BC6350471 |
| SHA1: | 6472C7F1ADCA227C30593C931147E1F00D63B003 |
| SHA256: | 3C1BF91AAAF52C4716E9A7BB448E69741DD6781C76FA05FDB26BBEE80D7E0574 |
| SSDEEP: | 3:N8SGfALtGTegXRGmIUI+zLQgbXEZAxZI4BXX7mEWAXfaLQgxmzcAUxXX7U:2FMGhXRGm590gzEZMm/yPgxvA6U |
MALICIOUS
Drops the executable file immediately after the start
- cmd.exe (PID: 2660)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2404)
SUSPICIOUS
Reads the Internet Settings
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2404)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2520)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 1644)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 3264)
Starts CMD.EXE for commands execution
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2404)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2520)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 1644)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 3264)
Executable content was dropped or overwritten
- cmd.exe (PID: 2660)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2404)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2688)
- cmd.exe (PID: 3208)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 2772)
The process creates files with name similar to system file names
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2404)
Process drops legitimate windows executable
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2404)
INFO
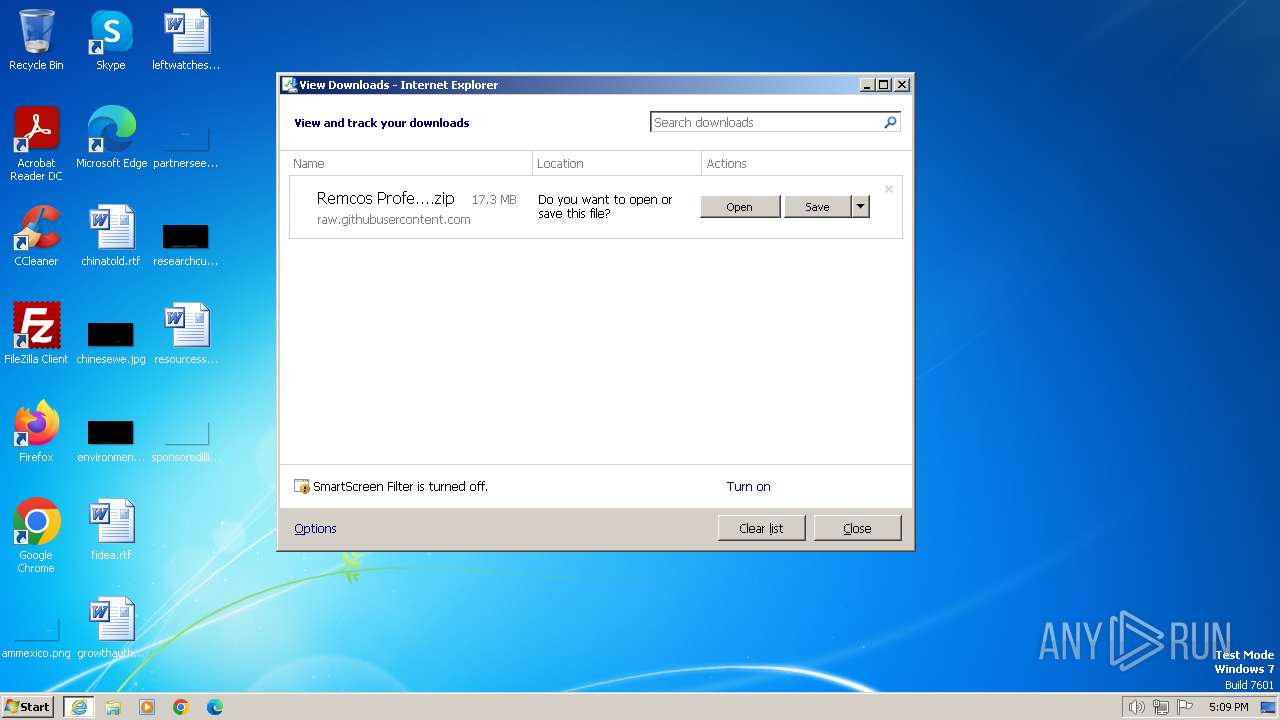
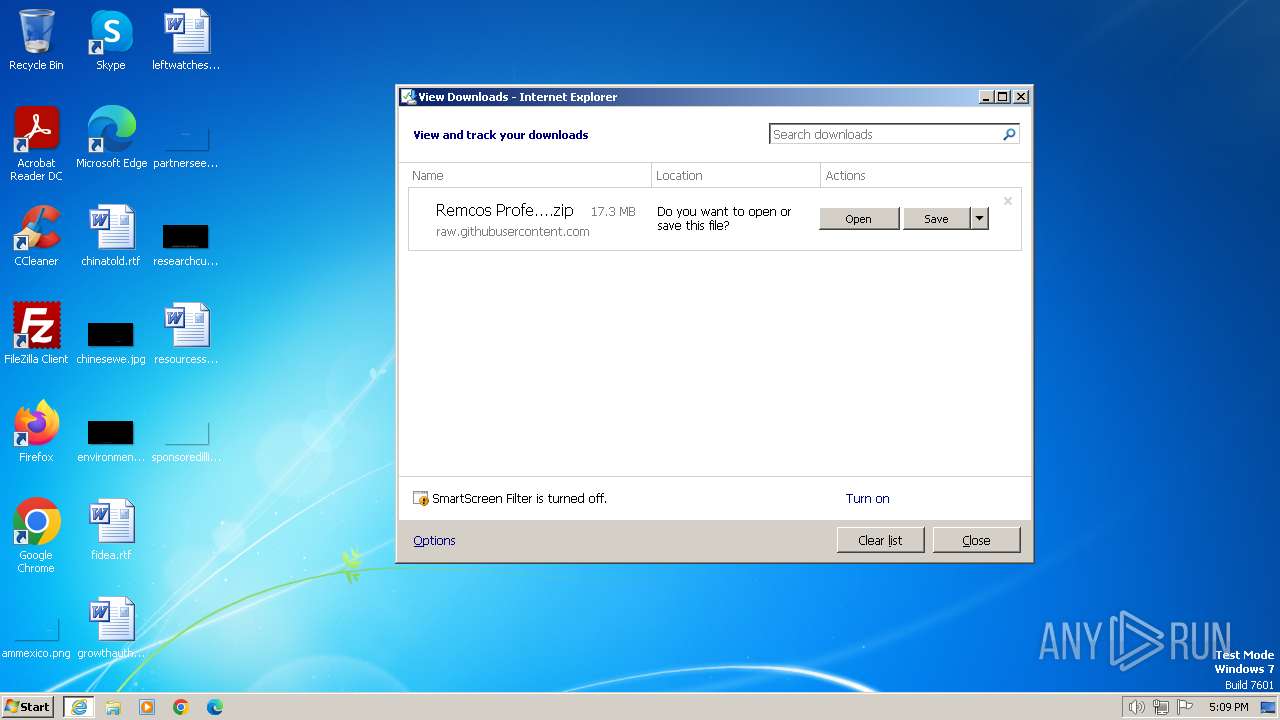
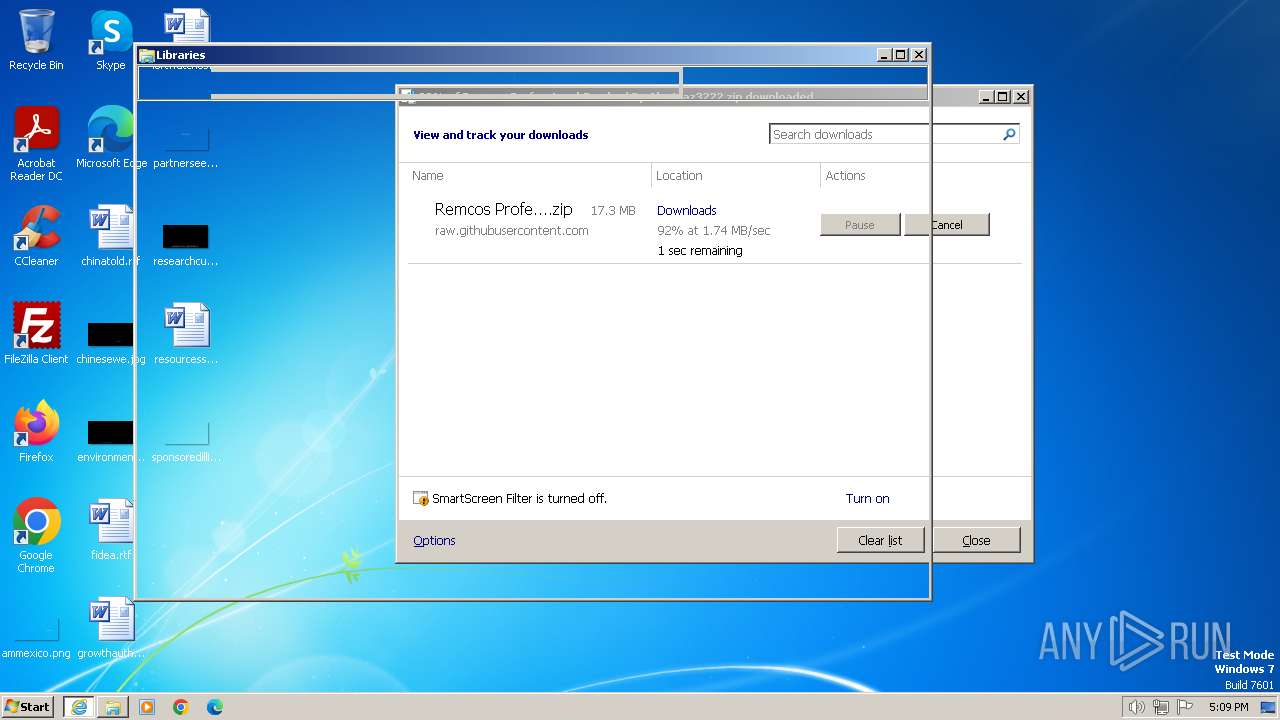
The process uses the downloaded file
- iexplore.exe (PID: 116)
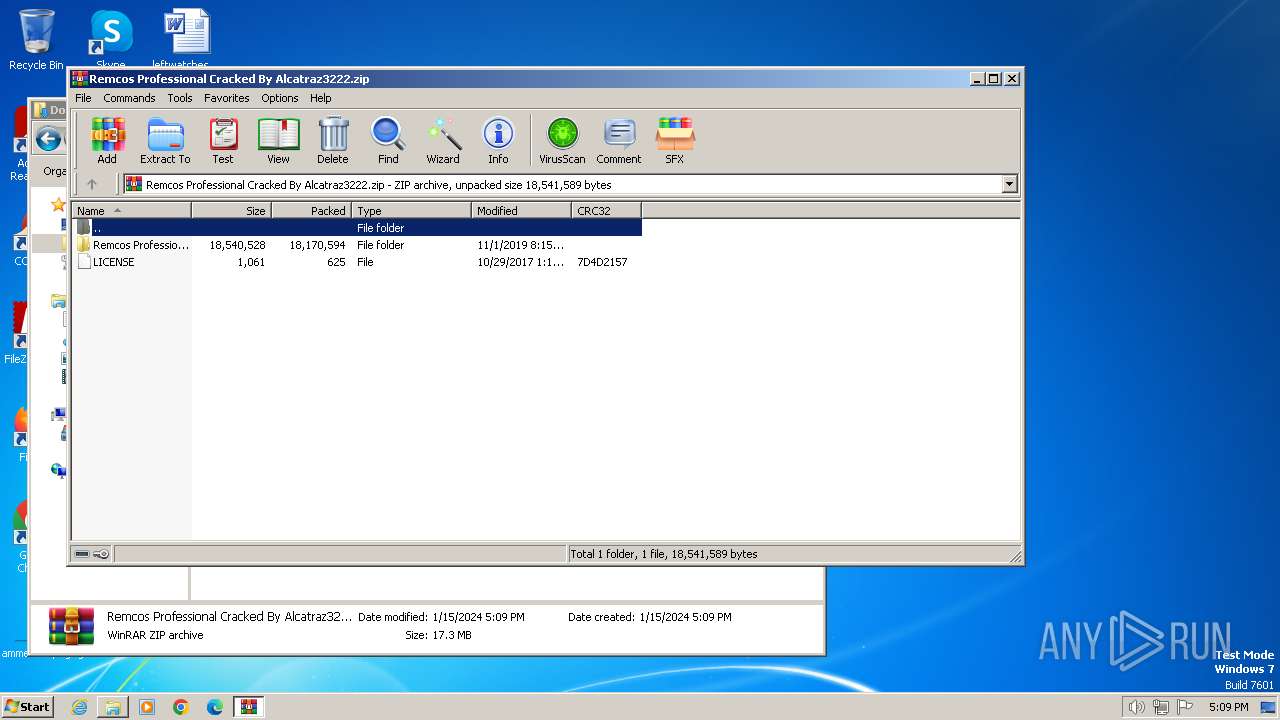
- WinRAR.exe (PID: 2624)
Application launched itself
- iexplore.exe (PID: 116)
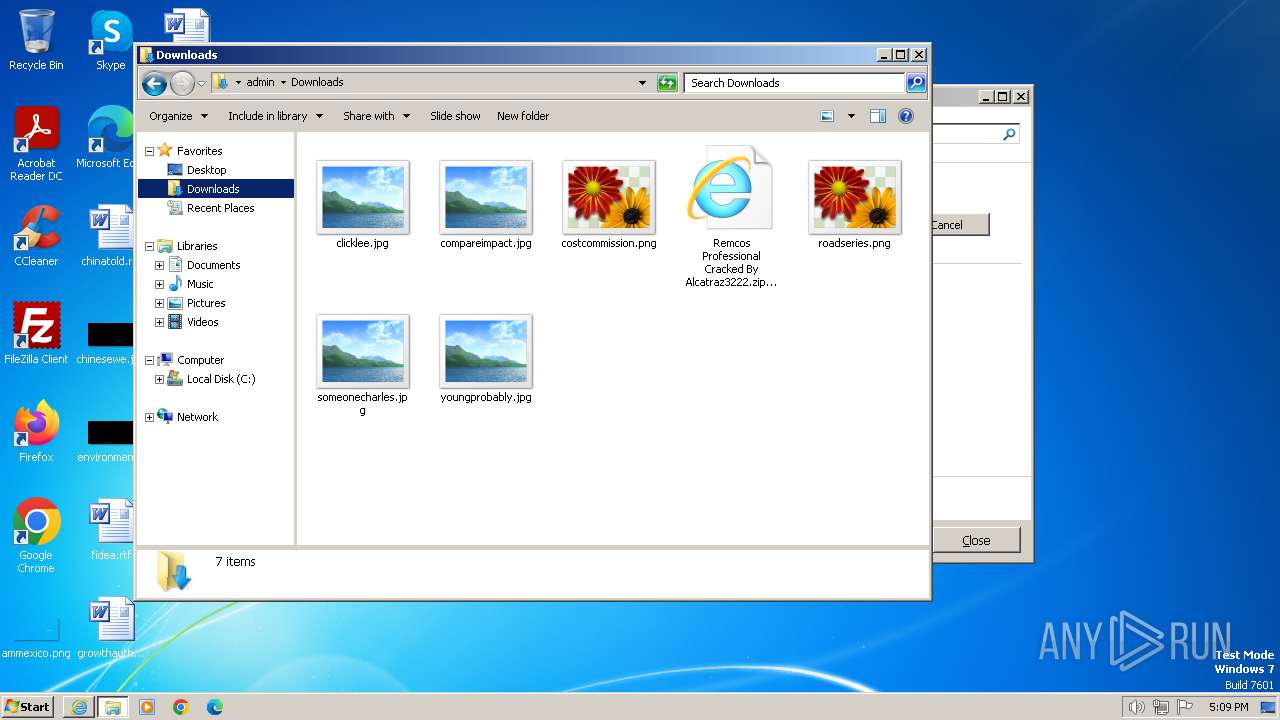
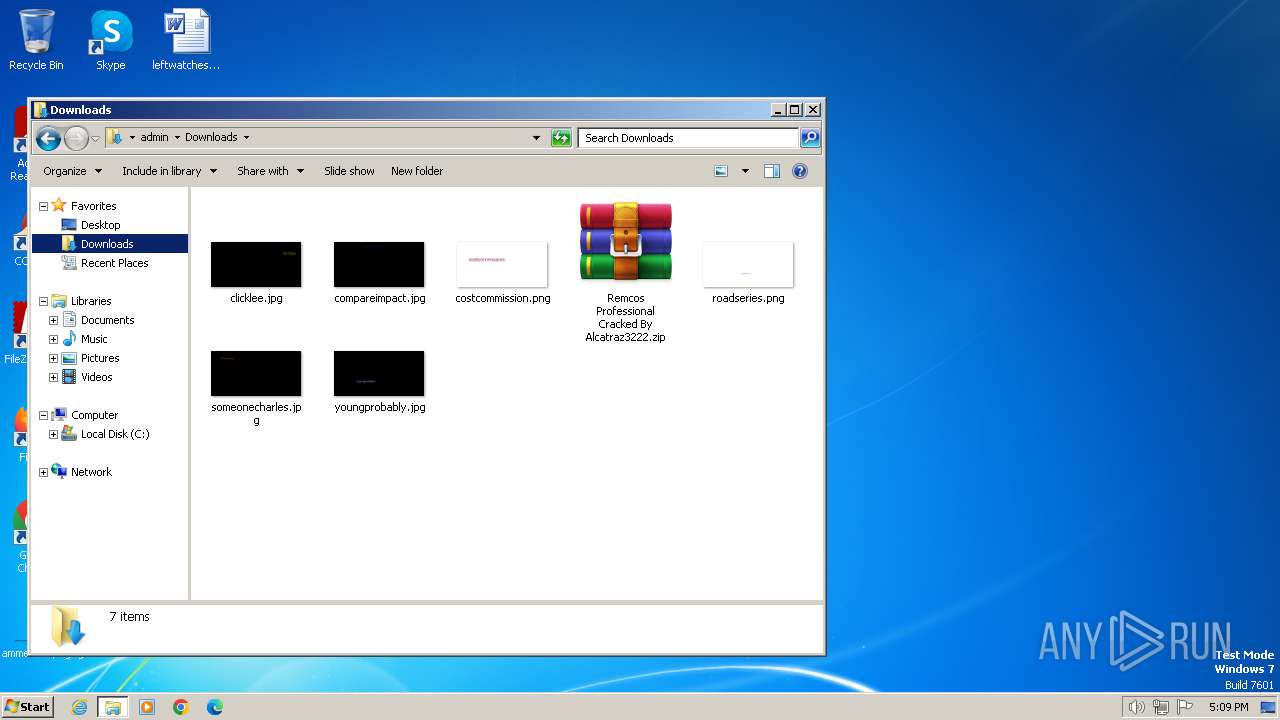
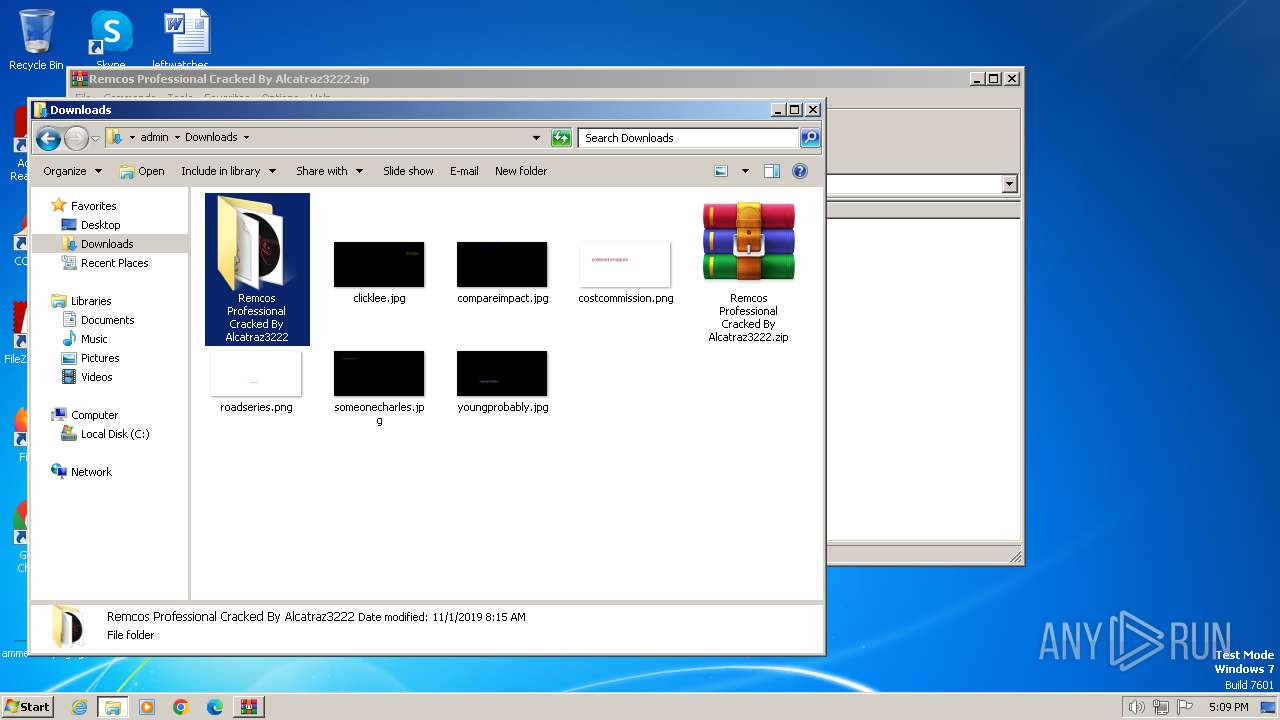
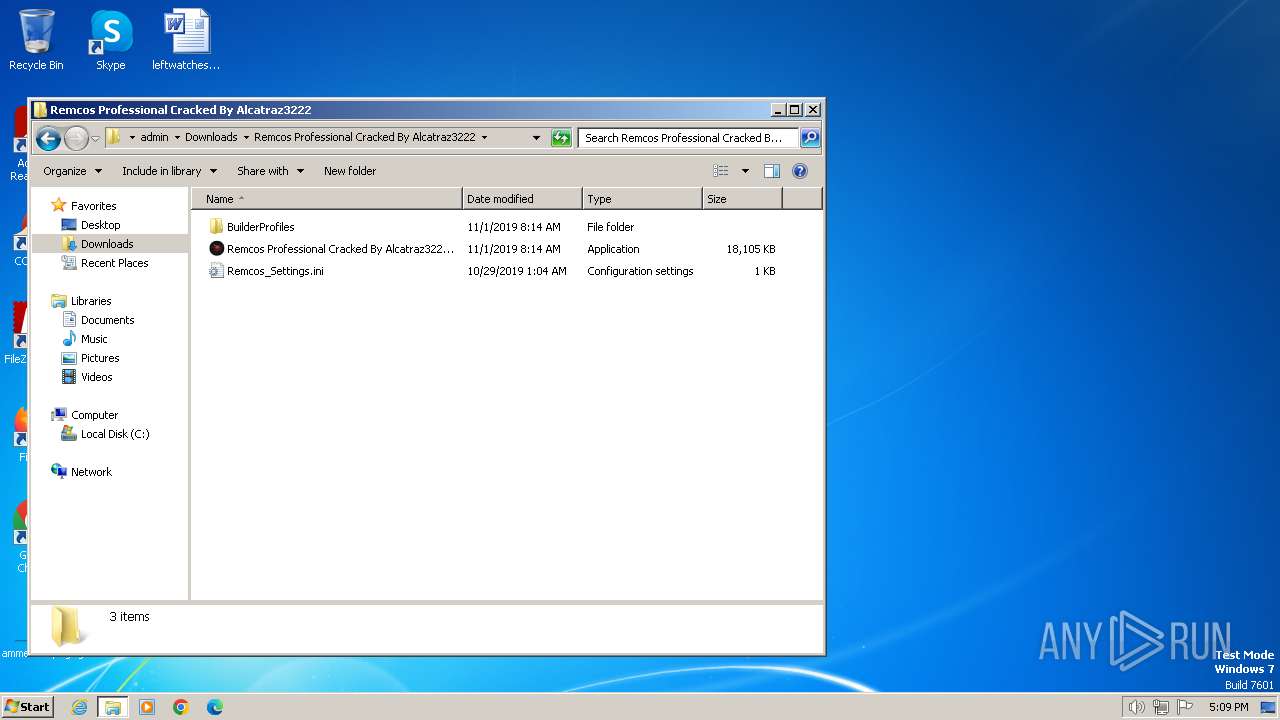
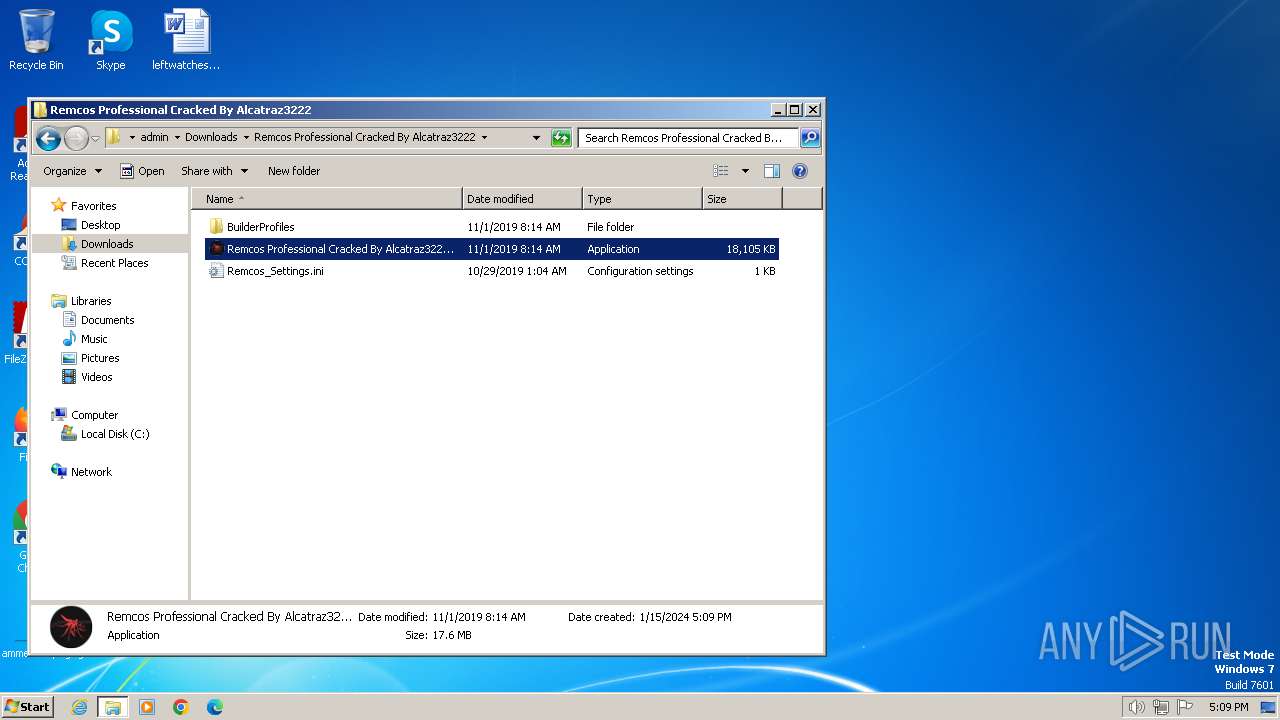
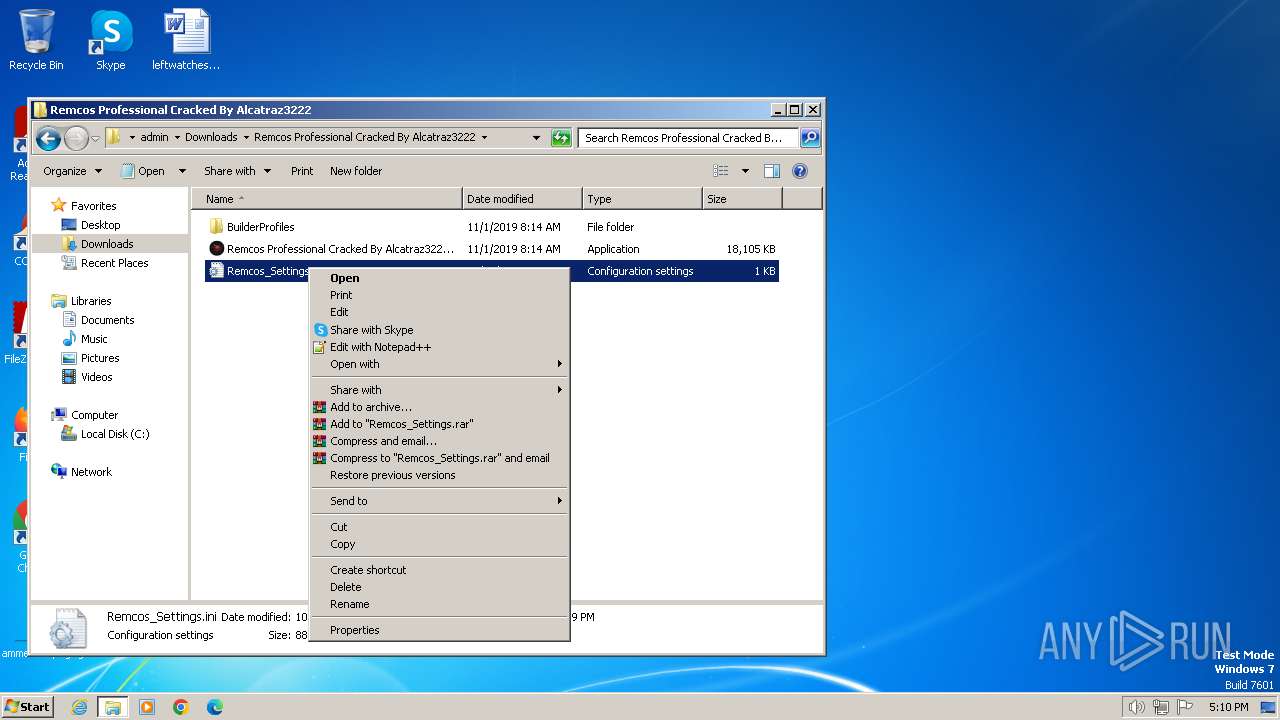
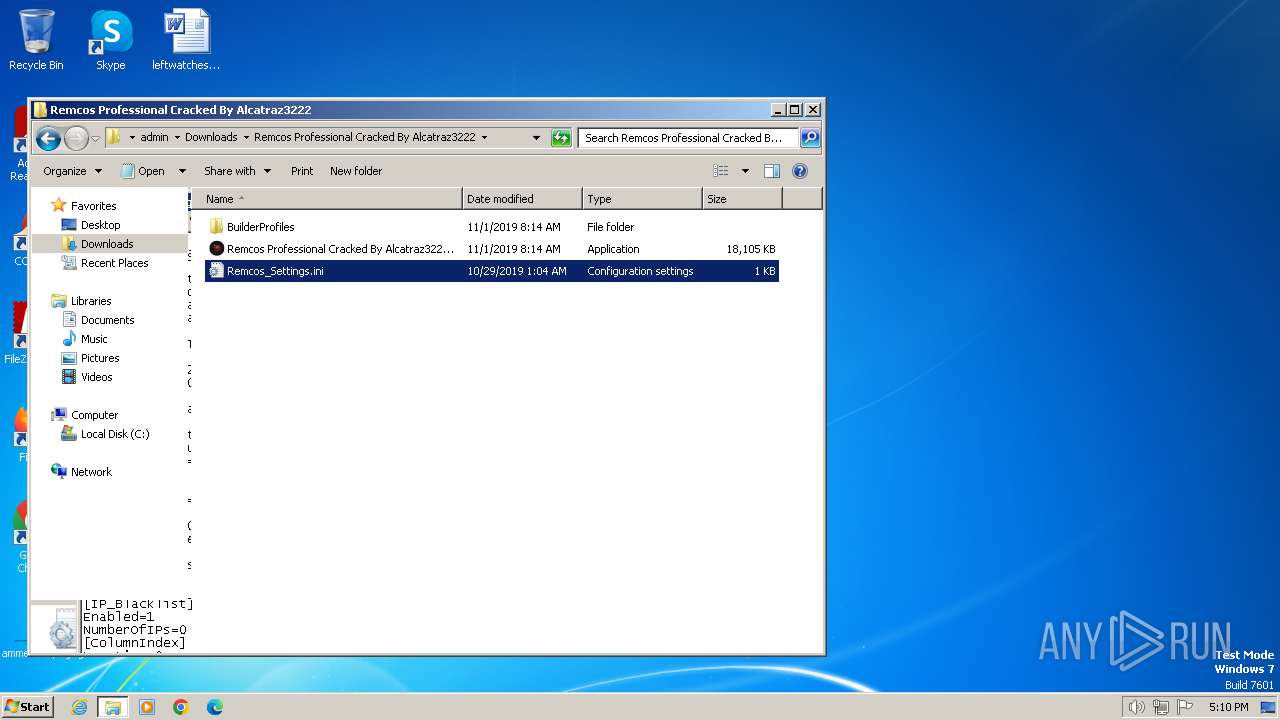
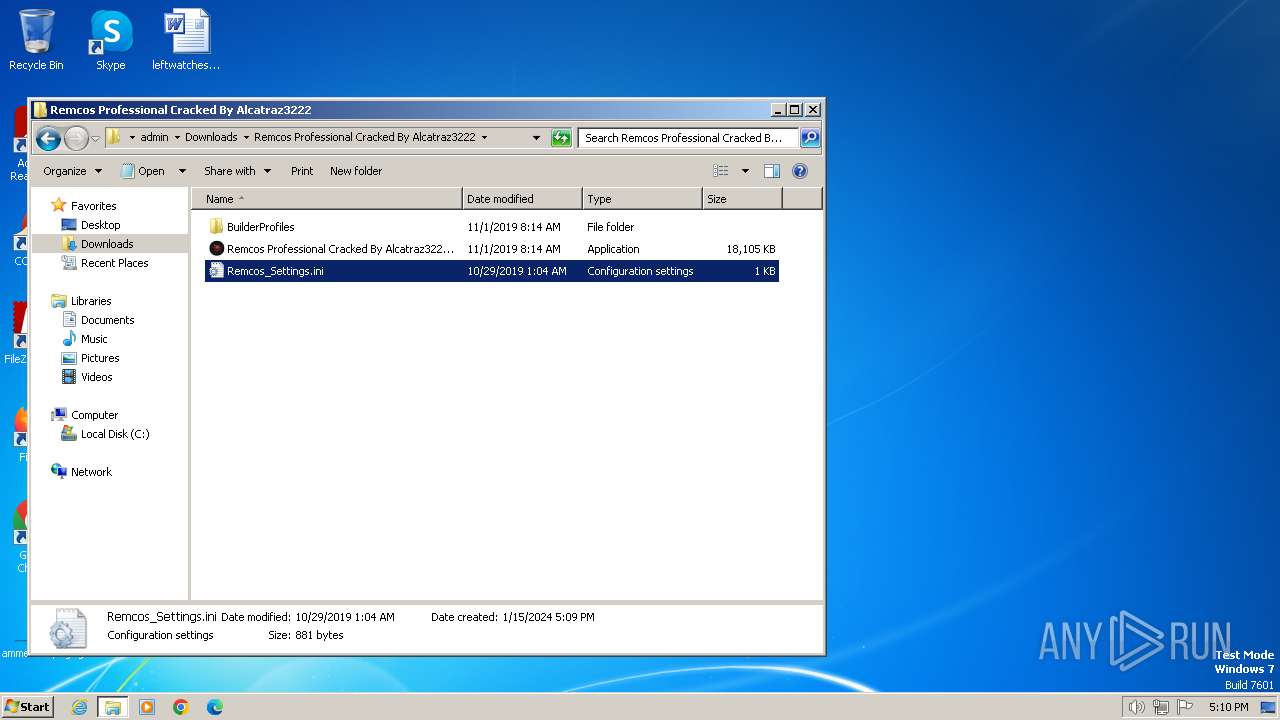
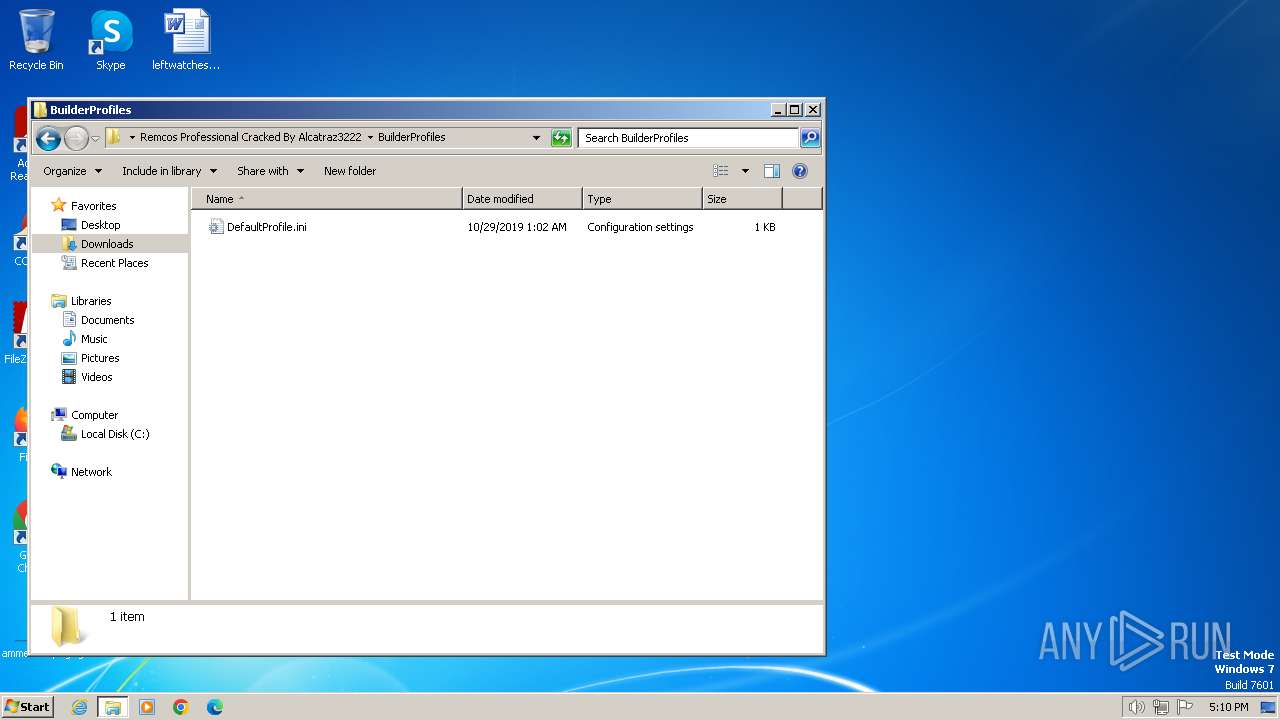
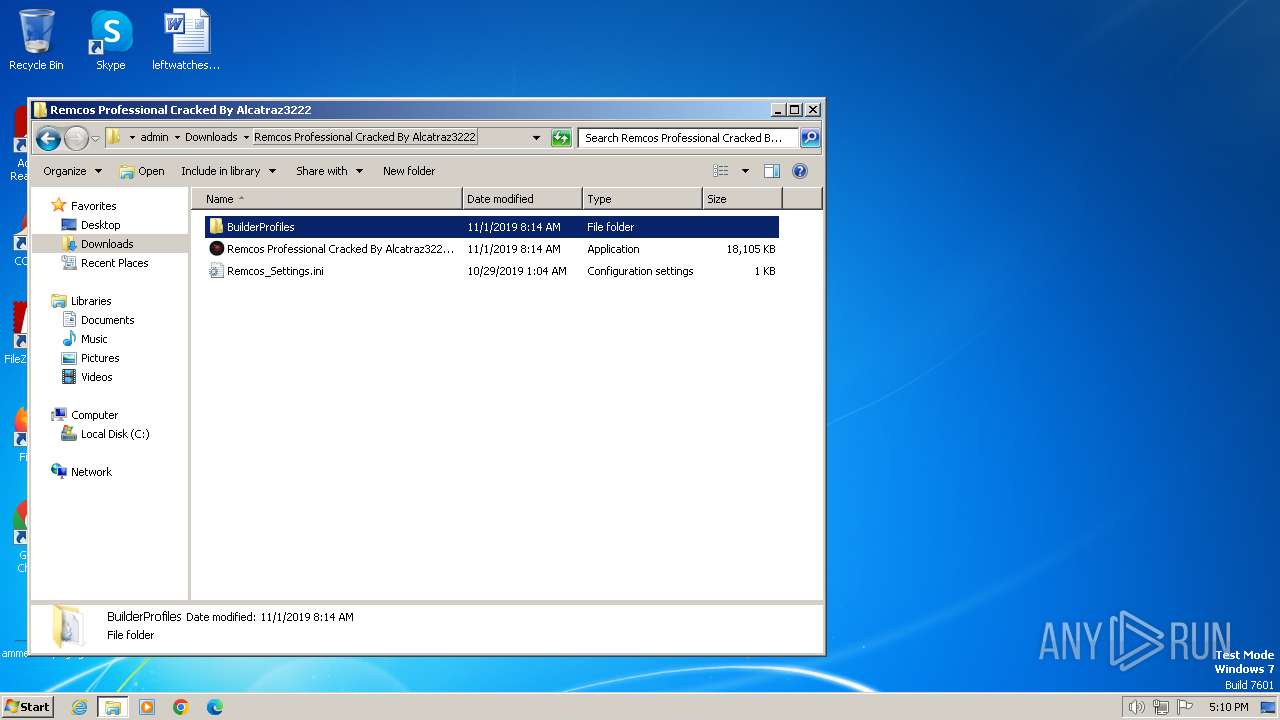
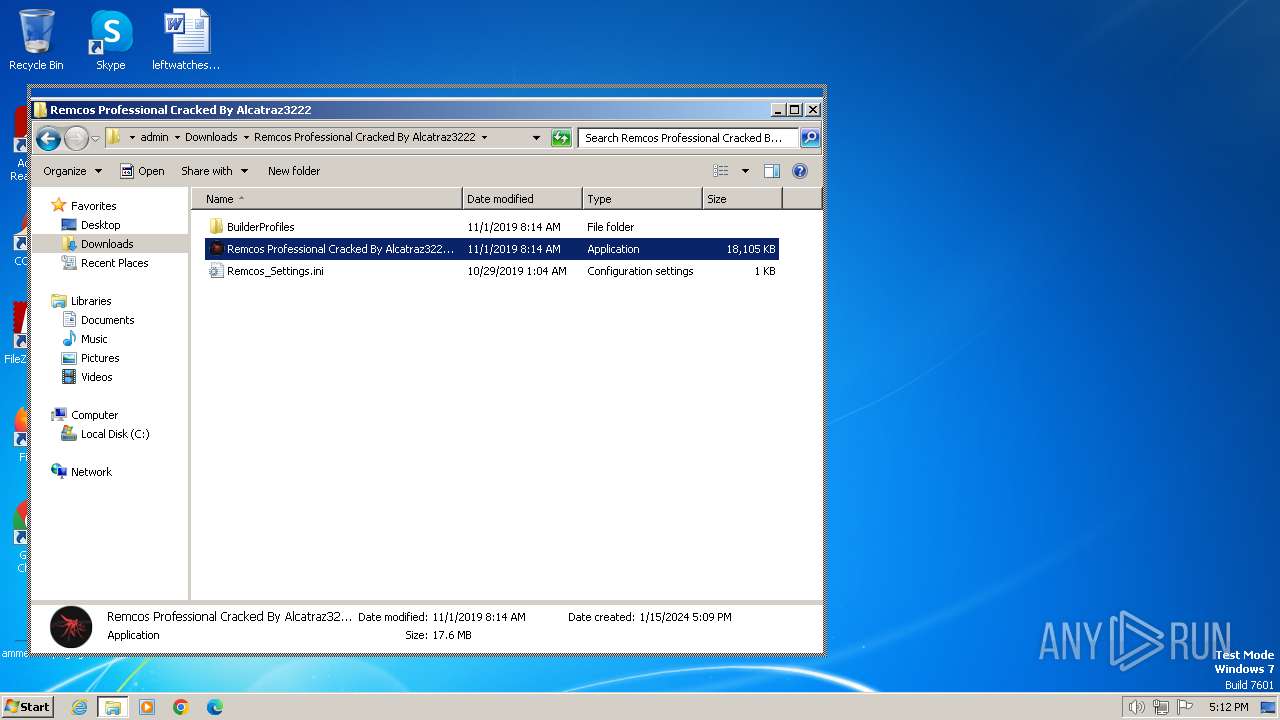
Manual execution by a user
- WinRAR.exe (PID: 2624)
- explorer.exe (PID: 1316)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2404)
- notepad.exe (PID: 2476)
- notepad.exe (PID: 908)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 1644)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 3264)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2520)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2624)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2624)
Checks supported languages
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2404)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 1644)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2520)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 3264)
Reads the computer name
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2404)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2520)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 1644)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 3264)
Reads the machine GUID from the registry
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2404)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2520)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 1644)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 3264)
Create files in a temporary directory
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2404)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 2520)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 1644)
- Remcos Professional Cracked By Alcatraz3222.exe (PID: 3264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
103
Monitored processes
54
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://raw.githubusercontent.com/cybertoxin/Remcos-Professional-Cracked-By-Alcatraz3222/master/Remcos%20Professional%20Cracked%20By%20Alcatraz3222.zip" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
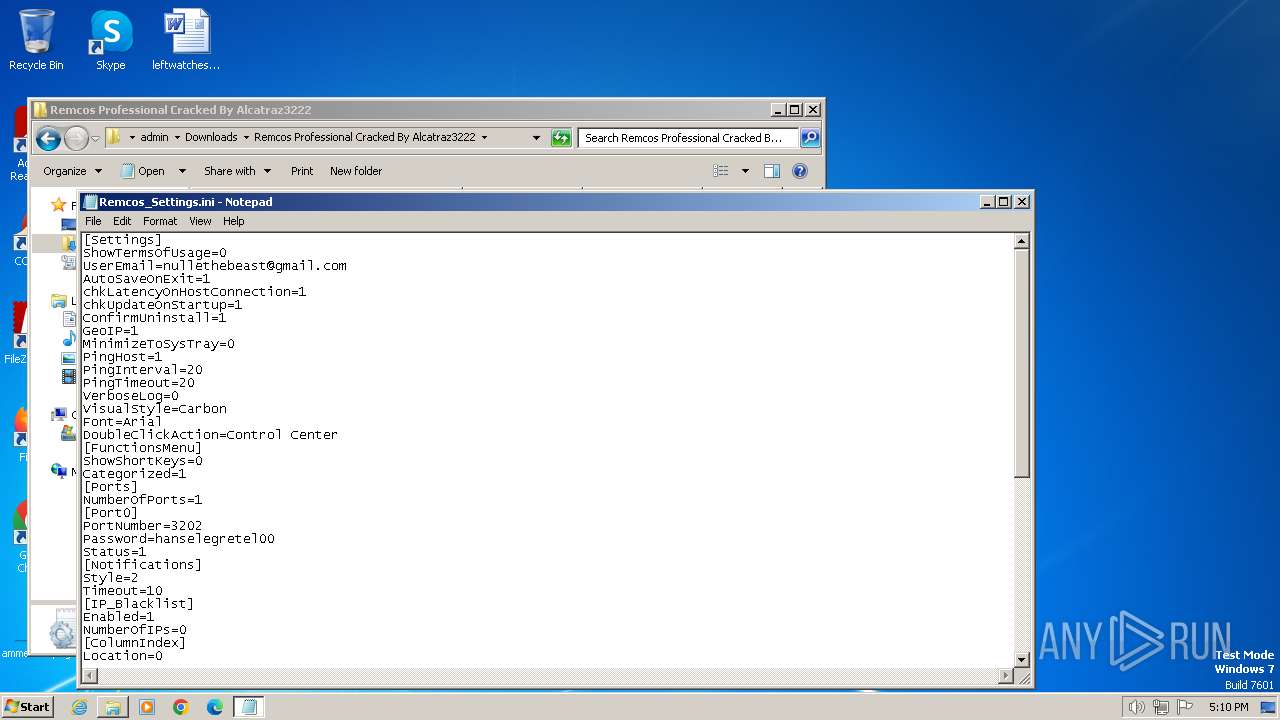
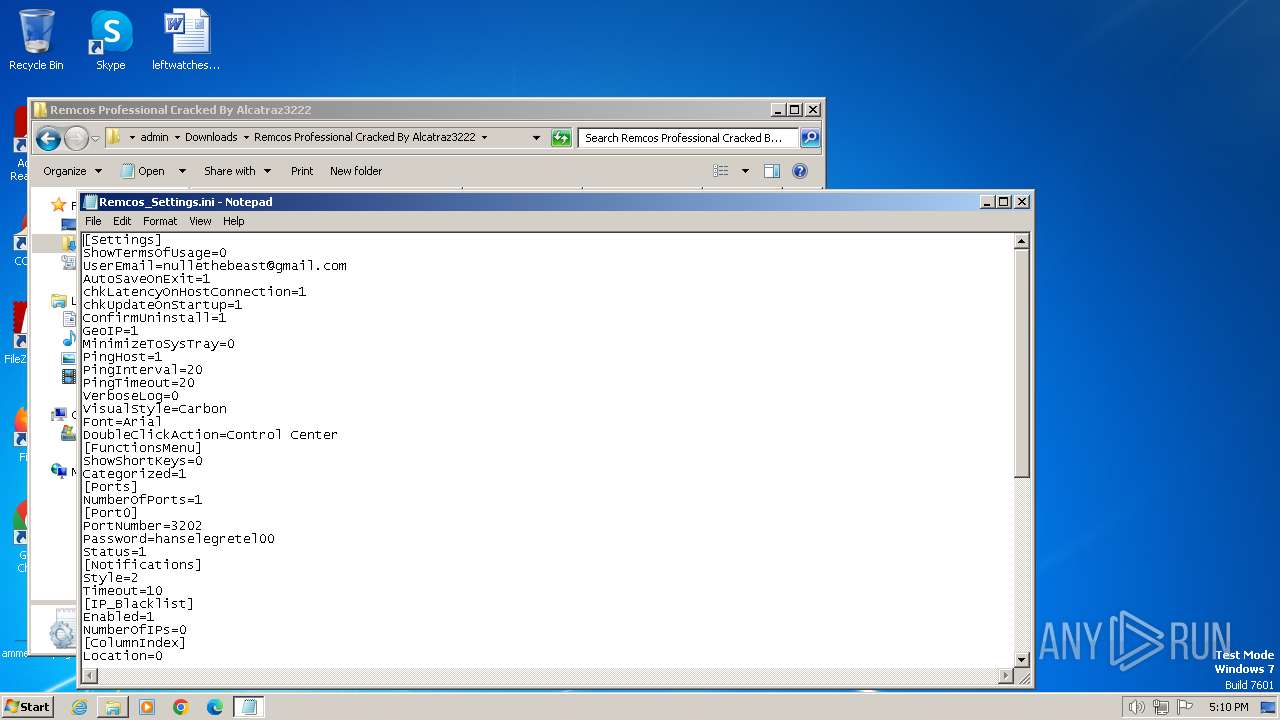
| 908 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\Remcos Professional Cracked By Alcatraz3222\Remcos_Settings.ini | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1028 | "C:\Windows\System32\cmd.exe" /c copy "C:/Users/admin/Downloads/Remcos Professional Cracked By Alcatraz3222/Remcos Professional Cracked By Alcatraz3222.exe" "%temp%\Profile Remcos\Update_Lock_Remcos.exe" /Y | C:\Windows\System32\cmd.exe | — | Remcos Professional Cracked By Alcatraz3222.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1168 | "C:\Windows\System32\cmd.exe" /c echo [zoneTransfer]ZoneID = 2 > %temp%\Profile Remcos\Update_Lock_Remcos.exe:Zone.Identifier | C:\Windows\System32\cmd.exe | — | Remcos Professional Cracked By Alcatraz3222.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1316 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1644 | "C:\Users\admin\Downloads\Remcos Professional Cracked By Alcatraz3222\Remcos Professional Cracked By Alcatraz3222.exe" | C:\Users\admin\Downloads\Remcos Professional Cracked By Alcatraz3222\Remcos Professional Cracked By Alcatraz3222.exe | — | explorer.exe | |||||||||||
User: admin Company: Breaking-Security.net Integrity Level: MEDIUM Description: REMCOS Remote Control & Surveillance Exit code: 0 Version: 2.2.0.0 Modules
| |||||||||||||||
| 1992 | "C:\Users\admin\AppData\Local\Temp\taskhost.exe" | C:\Users\admin\AppData\Local\Temp\taskhost.exe | — | Remcos Professional Cracked By Alcatraz3222.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 | |||||||||||||||
| 2204 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:116 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2404 | "C:\Users\admin\Downloads\Remcos Professional Cracked By Alcatraz3222\Remcos Professional Cracked By Alcatraz3222.exe" | C:\Users\admin\Downloads\Remcos Professional Cracked By Alcatraz3222\Remcos Professional Cracked By Alcatraz3222.exe | explorer.exe | ||||||||||||
User: admin Company: Breaking-Security.net Integrity Level: MEDIUM Description: REMCOS Remote Control & Surveillance Exit code: 0 Version: 2.2.0.0 Modules
| |||||||||||||||
| 2436 | "C:\Users\admin\AppData\Local\Temp\taskhost.exe" | C:\Users\admin\AppData\Local\Temp\taskhost.exe | — | Remcos Professional Cracked By Alcatraz3222.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 | |||||||||||||||
Total events
19 922
Read events
19 810
Write events
111
Delete events
1
Modification events
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
4
Suspicious files
14
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:445A3C0DFFAC4B0EEB593AD343218473 | SHA256:A184D0EC546E2FB8CC49B6DB815F0B078E73E74CF6A56DEA9B8F80C5D2A658A7 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:A4CAA60983BA5C1C1E353E4F1AEC6E8E | SHA256:EB990BE37832FC51290E42F1FD39D57E69D4C8E77D2A7B43EE68E4A9E1D64F84 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Remcos%20Professional%20Cracked%20By%20Alcatraz3222[1].zip | compressed | |
MD5:DA223363F33515F441490E98B458F481 | SHA256:7FFD555D95673442102645C0728BD8FCFFECD1D1AEB0B6E17BED3D4BB5D2A952 | |||
| 116 | iexplore.exe | C:\Users\admin\Downloads\Remcos Professional Cracked By Alcatraz3222.zip.yofcgvy.partial:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:0AB5766FE69629EAEA3D41E212C4ED57 | SHA256:C7B6A083E56980DF9CC95FEC4FBCD367AC60DE128132CB6063B0554293933968 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver7848.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB87C81EA766C22F5.TMP | binary | |
MD5:FF0B505BBAD7980694CA70DEDD6EF84A | SHA256:509BFFBC4B86D1B45CA569F5BC6EE81EDA58F5A29F889B33F54FBE54113657D4 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{C51F411B-B3C8-11EE-AE0A-12A9866C77DE}.dat | binary | |
MD5:9CDE069E1C875780FA19134D3EF406BF | SHA256:CE28EAA3F2C39D6B649C73D4C2C13BD04E8886EE1CC523BE9BC2FA97DEF22181 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
14
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2204 | iexplore.exe | GET | 200 | 23.48.23.7:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?53bfb7cf8a6cf97e | unknown | compressed | 4.66 Kb | unknown |
2204 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
2204 | iexplore.exe | GET | 200 | 23.48.23.7:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b21170b0e7a1648 | unknown | compressed | 4.66 Kb | unknown |
— | — | GET | 304 | 23.32.238.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?eca8823d6d0692d6 | unknown | — | — | unknown |
116 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2204 | iexplore.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
2204 | iexplore.exe | 23.48.23.7:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2204 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 23.32.238.121:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
116 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
116 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |