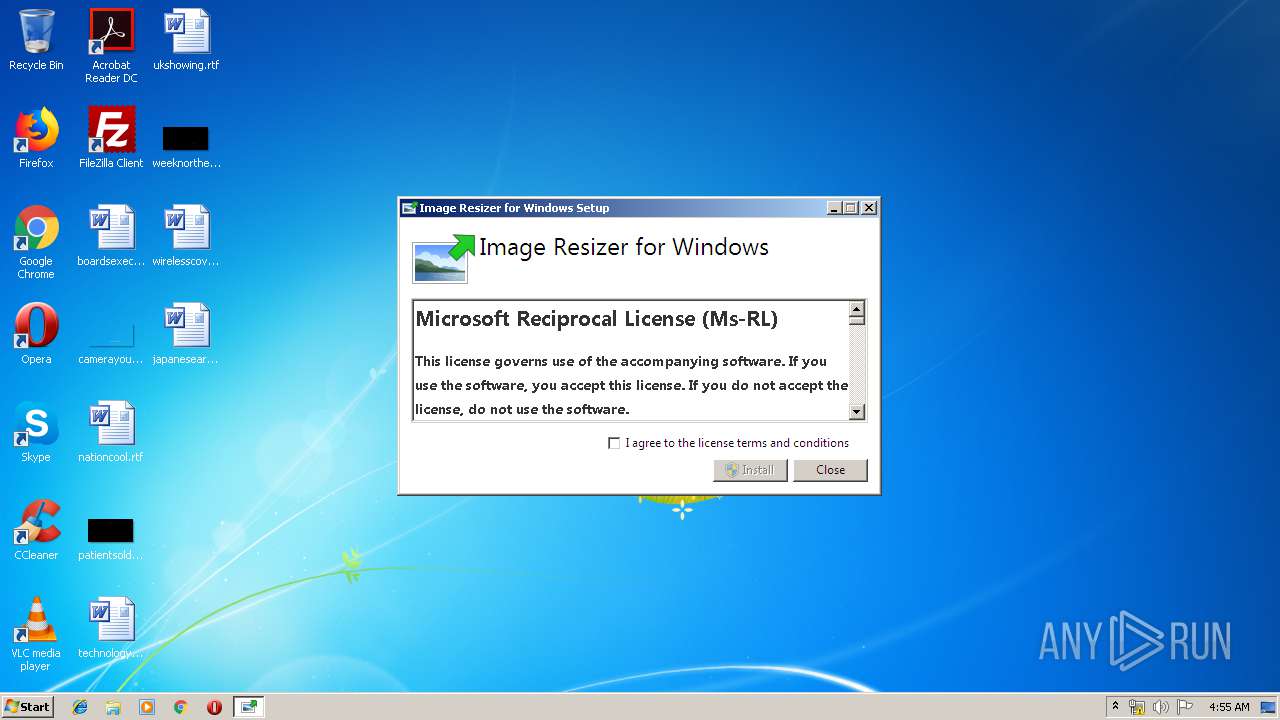
| File name: | ImageResizerSetup-3.1.1.exe |
| Full analysis: | https://app.any.run/tasks/6613dbc2-1eae-4b62-b92e-93eae42381cb |
| Verdict: | No threats detected |
| Analysis date: | April 30, 2019, 03:54:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 47EB5BA643294A470BCC7EB4FAF95583 |
| SHA1: | FE62BF8735E92503DB1A3D2EEC9AE4FF5668D8A2 |
| SHA256: | 3C168AD78E2DE44F9B2BF12D26DE71096DE1995C6F5D8C7D2C67F29E3D60F1DE |
| SSDEEP: | 24576:vu/OfDlEUKWflmTP3+T9YCdTqqfpDy/fnrR/IEkwJ:bfU4Uj+iCdTqqfpW//t/J |
MALICIOUS
Application was dropped or rewritten from another process
- ImageResizerSetup-3.1.1.exe (PID: 3876)
Loads dropped or rewritten executable
- ImageResizerSetup-3.1.1.exe (PID: 3876)
SUSPICIOUS
Executable content was dropped or overwritten
- ImageResizerSetup-3.1.1.exe (PID: 3600)
- ImageResizerSetup-3.1.1.exe (PID: 3876)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:11:18 23:00:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.11 |
| CodeSize: | 301568 |
| InitializedDataSize: | 216064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e2a6 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.1.1.0 |
| ProductVersionNumber: | 3.1.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Brice Lambson |
| FileDescription: | Image Resizer for Windows |
| FileVersion: | 3.1.1.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Brice Lambson. All rights reserved. |
| OriginalFileName: | ImageResizerSetup.exe |
| ProductName: | Image Resizer for Windows |
| ProductVersion: | 3.1.1.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2017 22:00:38 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Brice Lambson |
| FileDescription: | Image Resizer for Windows |
| FileVersion: | 3.1.1.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Brice Lambson. All rights reserved. |
| OriginalFilename: | ImageResizerSetup.exe |
| ProductName: | Image Resizer for Windows |
| ProductVersion: | 3.1.1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 18-Nov-2017 22:00:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00049937 | 0x00049A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57001 |
.rdata | 0x0004B000 | 0x0001ED60 | 0x0001EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.11423 |
.data | 0x0006A000 | 0x00001730 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.15266 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.735162 |
.rsrc | 0x0006D000 | 0x00011334 | 0x00011400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.82364 |
.reloc | 0x0007F000 | 0x00003DFC | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.79434 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.24789 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.12773 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.35703 | 6760 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.22473 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.18771 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.26116 | 1720 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.00236 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3600 | "C:\Users\admin\AppData\Local\Temp\ImageResizerSetup-3.1.1.exe" | C:\Users\admin\AppData\Local\Temp\ImageResizerSetup-3.1.1.exe | explorer.exe | ||||||||||||
User: admin Company: Brice Lambson Integrity Level: MEDIUM Description: Image Resizer for Windows Exit code: 0 Version: 3.1.1.0 Modules
| |||||||||||||||
| 3876 | "C:\Users\admin\AppData\Local\Temp\{CAA08164-18A2-40C0-90EB-6ED6546F06AB}\.cr\ImageResizerSetup-3.1.1.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\ImageResizerSetup-3.1.1.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Users\admin\AppData\Local\Temp\{CAA08164-18A2-40C0-90EB-6ED6546F06AB}\.cr\ImageResizerSetup-3.1.1.exe | ImageResizerSetup-3.1.1.exe | ||||||||||||
User: admin Company: Brice Lambson Integrity Level: MEDIUM Description: Image Resizer for Windows Exit code: 0 Version: 3.1.1.0 Modules
| |||||||||||||||
Total events
42
Read events
42
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3600 | ImageResizerSetup-3.1.1.exe | C:\Users\admin\AppData\Local\Temp\{CAA08164-18A2-40C0-90EB-6ED6546F06AB}\.cr\ImageResizerSetup-3.1.1.exe | executable | |
MD5:— | SHA256:— | |||
| 3876 | ImageResizerSetup-3.1.1.exe | C:\Users\admin\AppData\Local\Temp\{3AB61092-EA84-49A1-8C29-213C764BF5D9}\.ba\thm.xml | xml | |
MD5:F62729C6D2540015E072514226C121C7 | SHA256:F13BAE0EC08C91B4A315BB2D86EE48FADE597E7A5440DCE6F751F98A3A4D6916 | |||
| 3876 | ImageResizerSetup-3.1.1.exe | C:\Users\admin\AppData\Local\Temp\{3AB61092-EA84-49A1-8C29-213C764BF5D9}\.ba\BootstrapperApplicationData.xml | xml | |
MD5:— | SHA256:— | |||
| 3876 | ImageResizerSetup-3.1.1.exe | C:\Users\admin\AppData\Local\Temp\{3AB61092-EA84-49A1-8C29-213C764BF5D9}\.ba\wixstdba.dll | executable | |
MD5:8CA04519005AD03B4D9E062B97D7F79D | SHA256:7B9F919A3D1974FD8FA35AD189EDC8BF287F476BD377E713E616B26864A4B0D3 | |||
| 3876 | ImageResizerSetup-3.1.1.exe | C:\Users\admin\AppData\Local\Temp\{3AB61092-EA84-49A1-8C29-213C764BF5D9}\.ba\logo.png | image | |
MD5:8FF0B9919CBB177BF44AD66BCF266607 | SHA256:B3DC9DC5DA8F81801F3B6DDB28F822382F52317C24A3F275DADF1486CEE3449B | |||
| 3876 | ImageResizerSetup-3.1.1.exe | C:\Users\admin\AppData\Local\Temp\{3AB61092-EA84-49A1-8C29-213C764BF5D9}\.ba\license.rtf | text | |
MD5:92D9A2B716EDE5E5B54C071186265F33 | SHA256:5DF983325886882D9C7C3836096B2F3CA88749E69E09B5467C8E247A3C20D17D | |||
| 3876 | ImageResizerSetup-3.1.1.exe | C:\Users\admin\AppData\Local\Temp\{3AB61092-EA84-49A1-8C29-213C764BF5D9}\.ba\thm.wxl | xml | |
MD5:5D492AF2E8C9B2AB58CA1A10248C726F | SHA256:ACCF0D8BFCEF21F5F80730D90705446FC0253174A484FD73B6523A092224322D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report