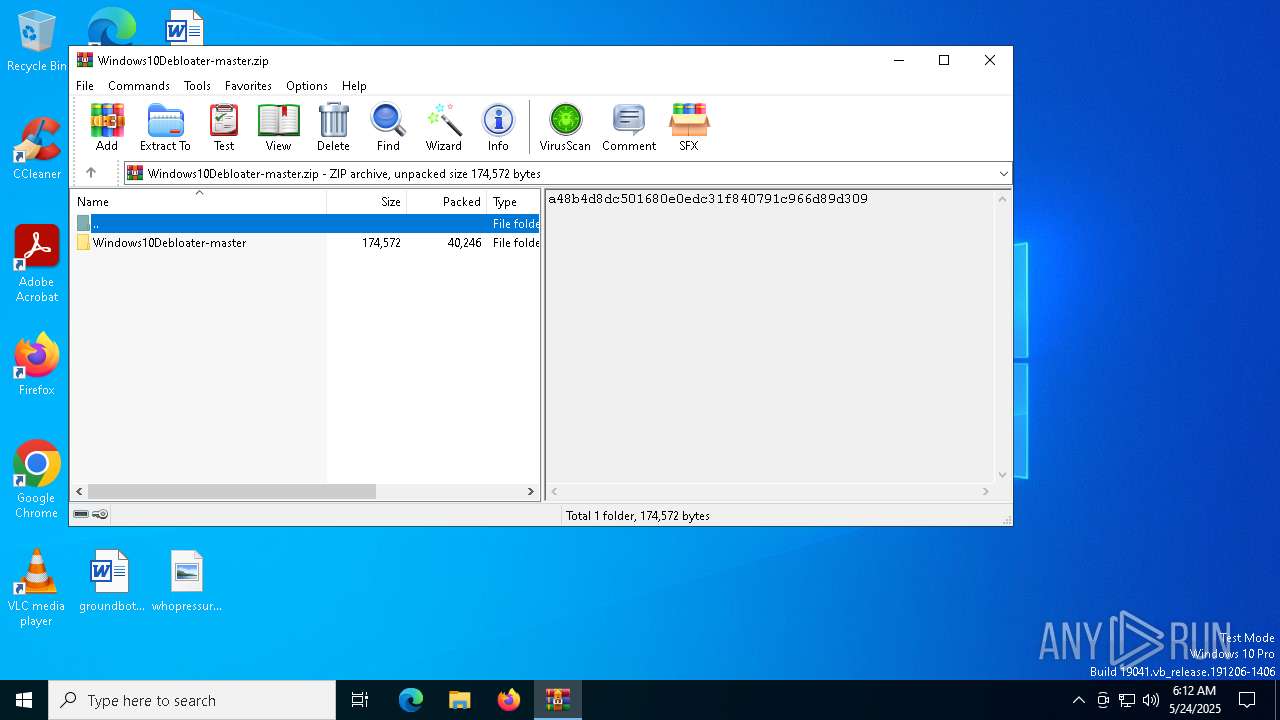
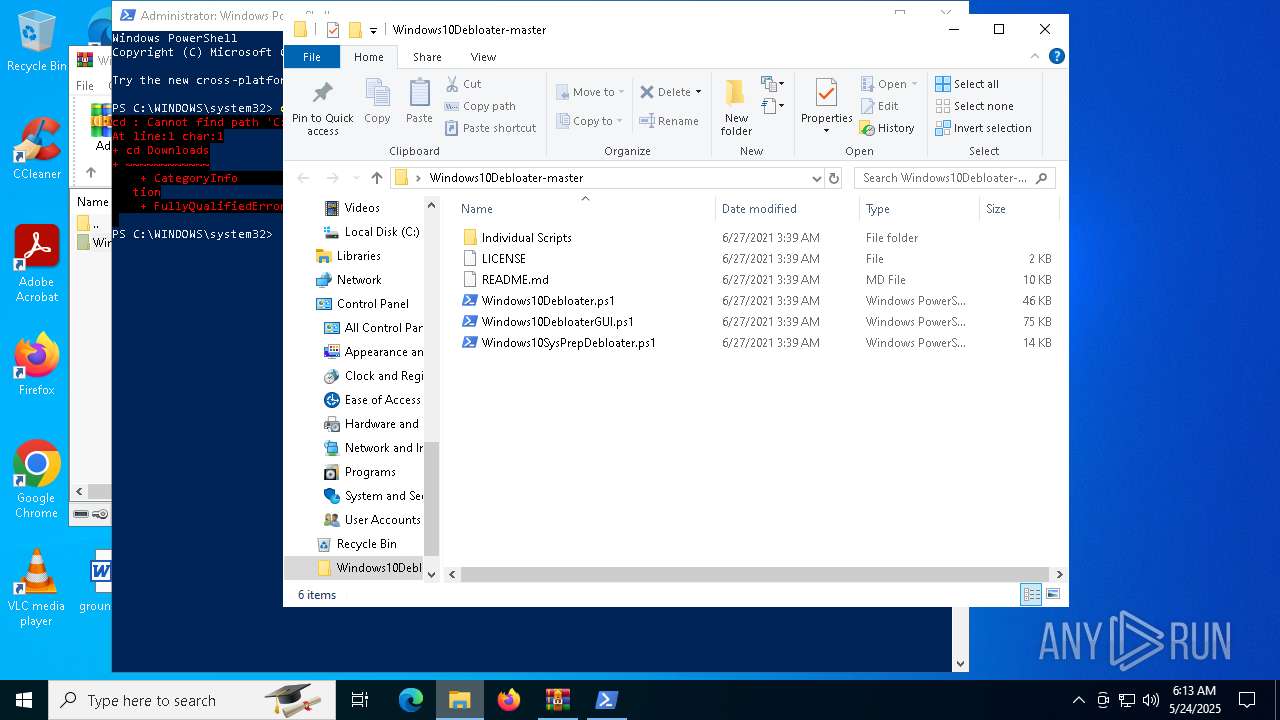
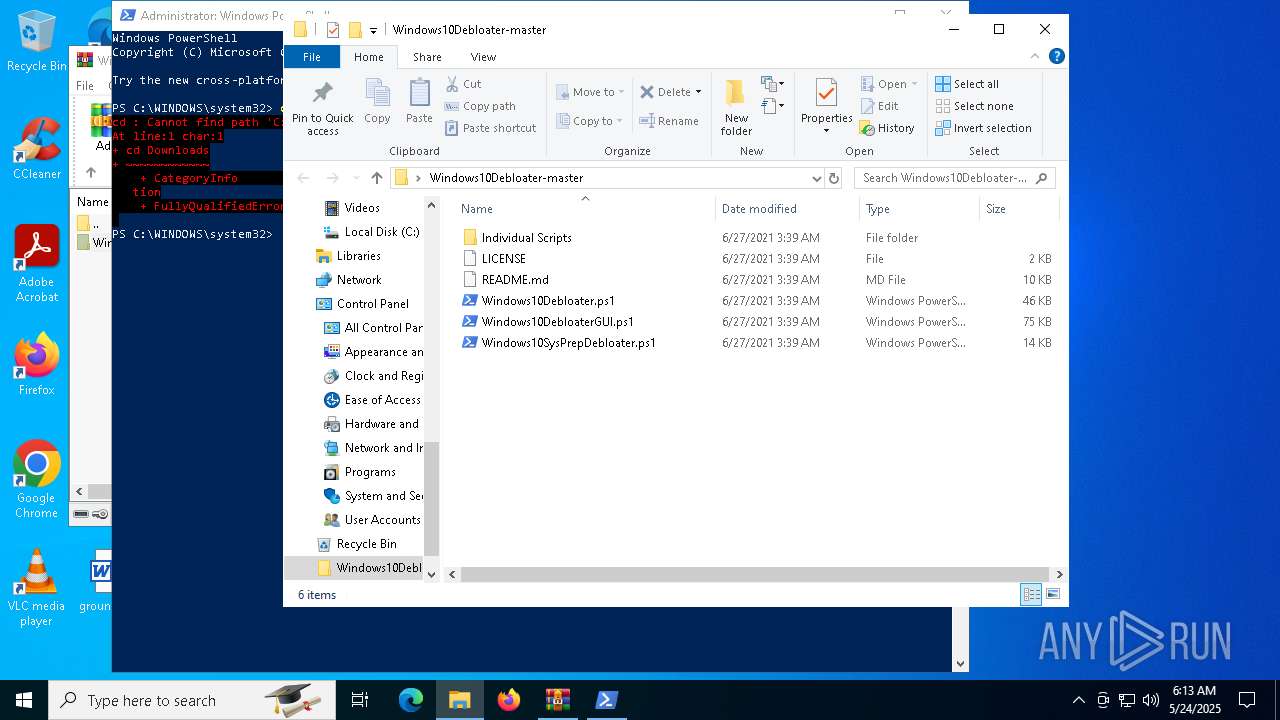
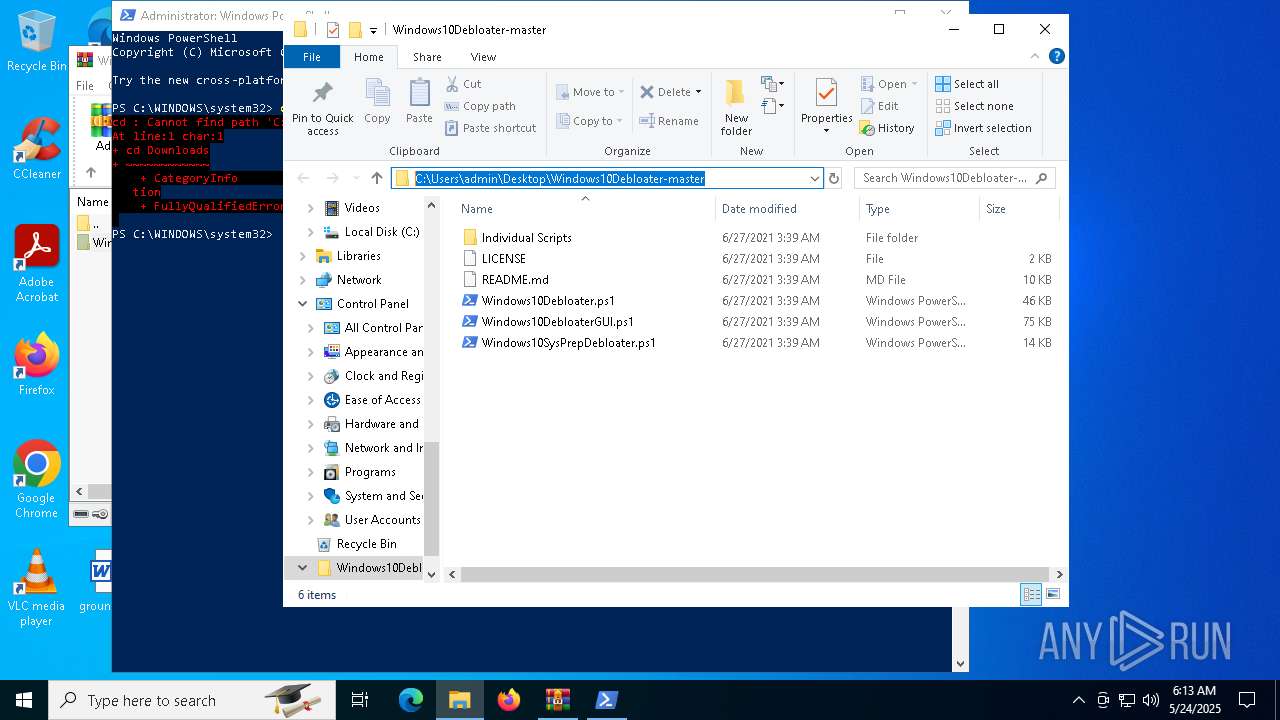
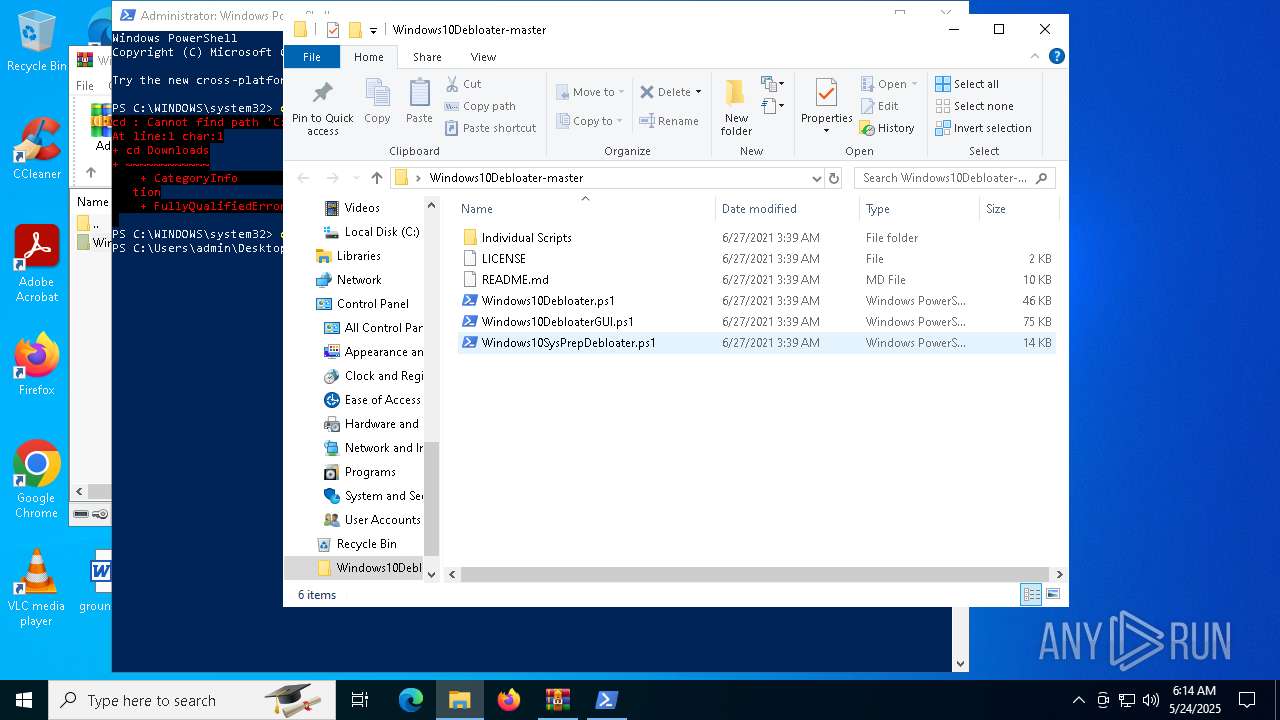
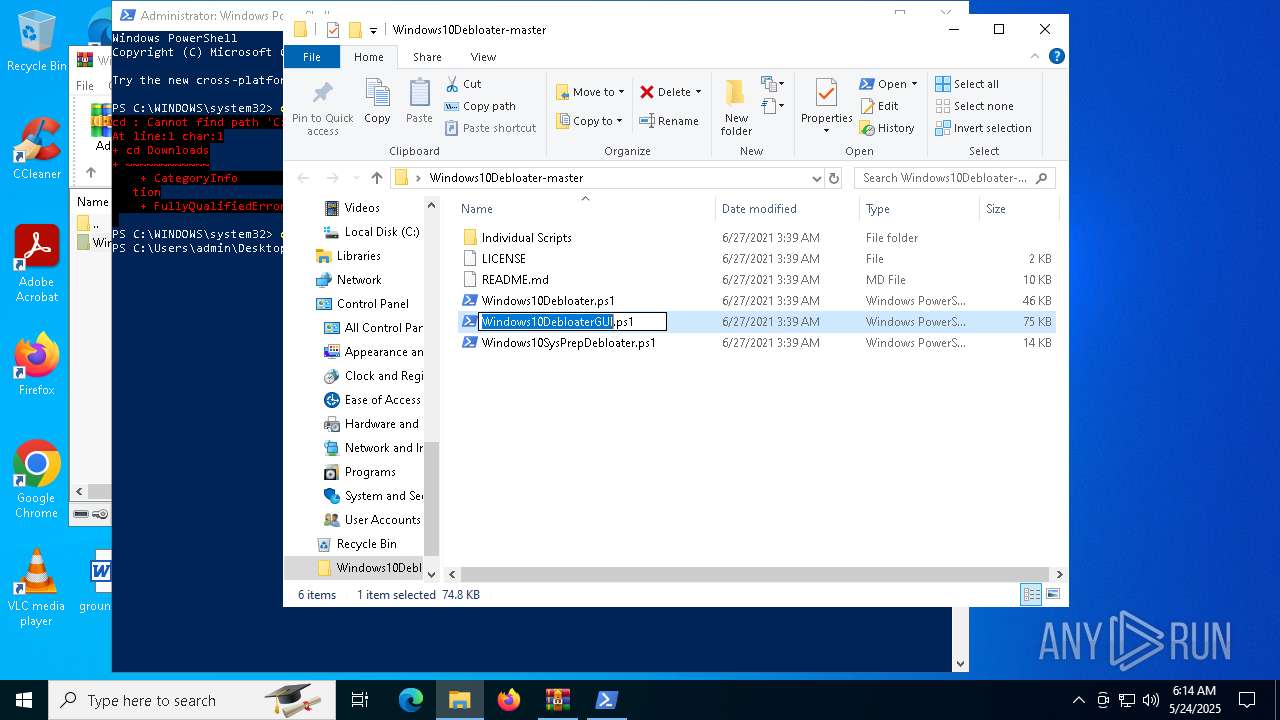
| File name: | Windows10Debloater-master.zip |
| Full analysis: | https://app.any.run/tasks/fc56316e-11d7-4012-b44d-540554125ce7 |
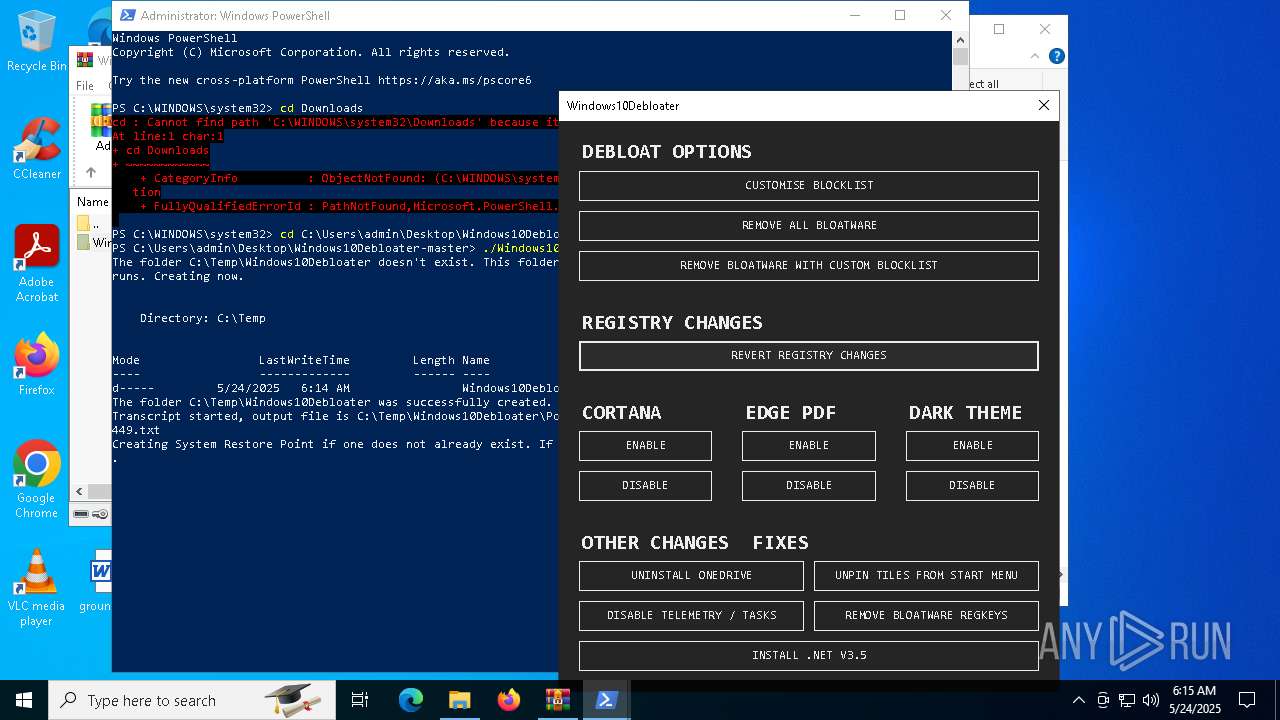
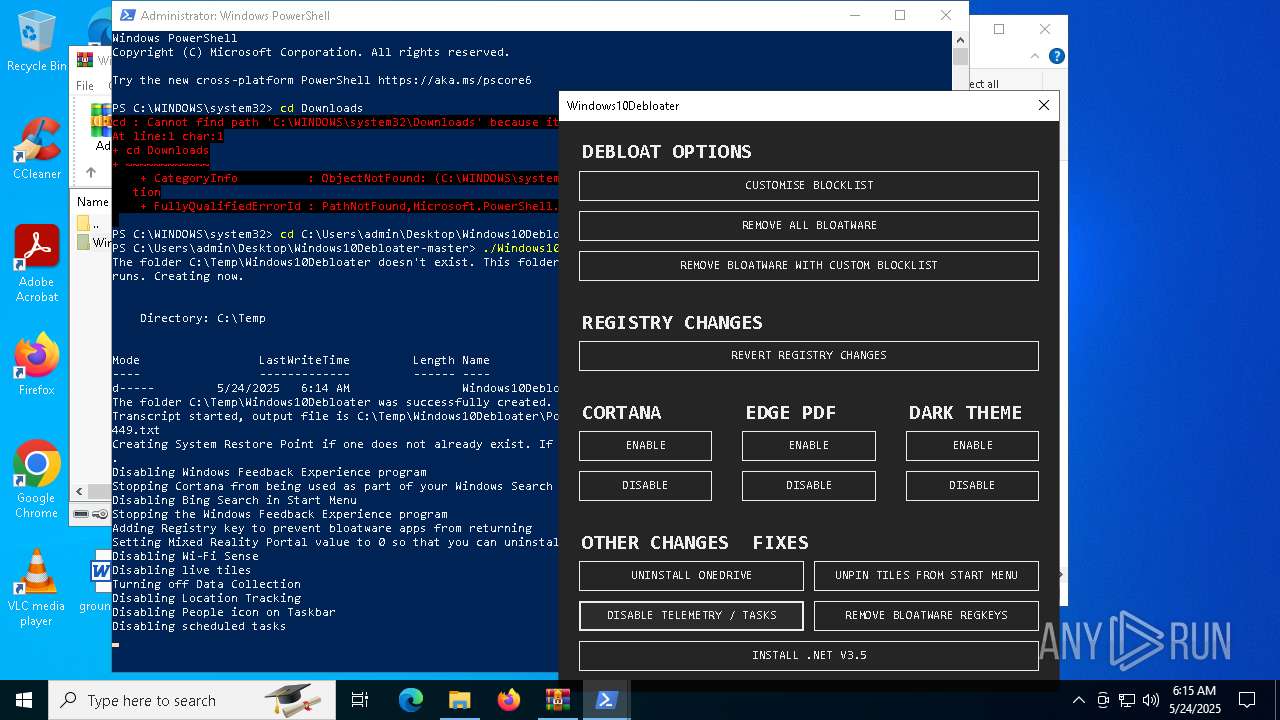
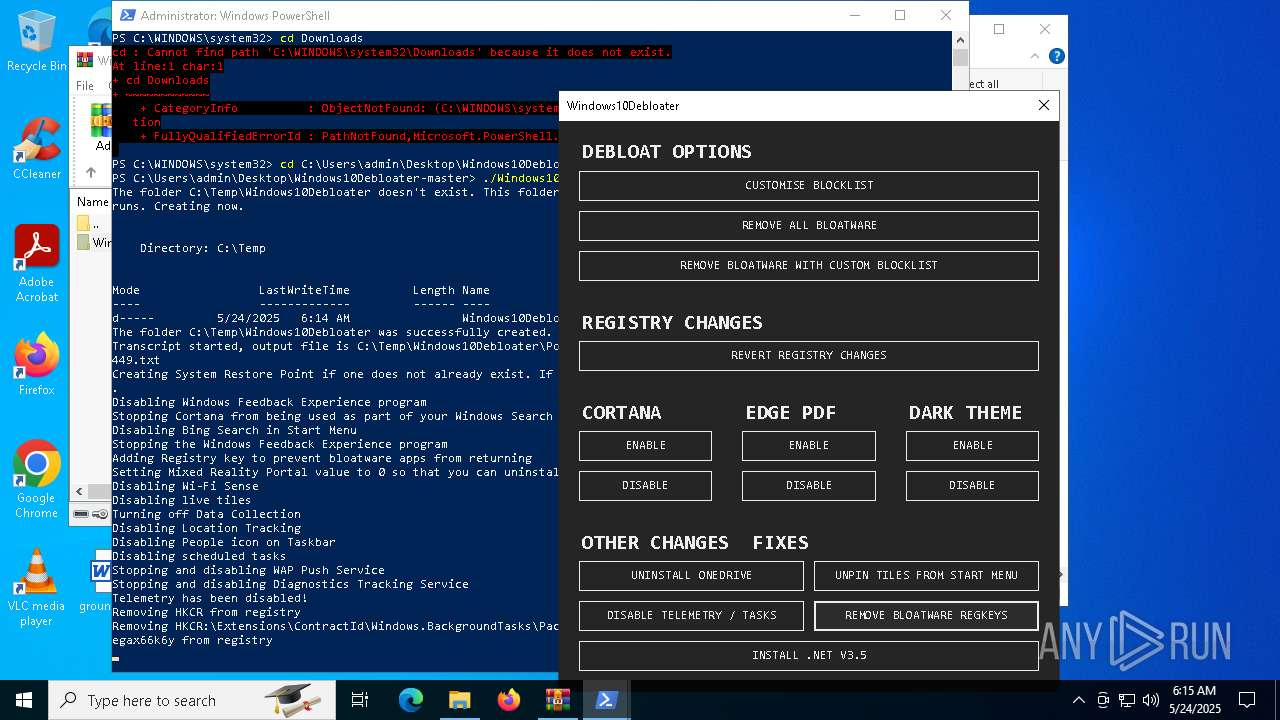
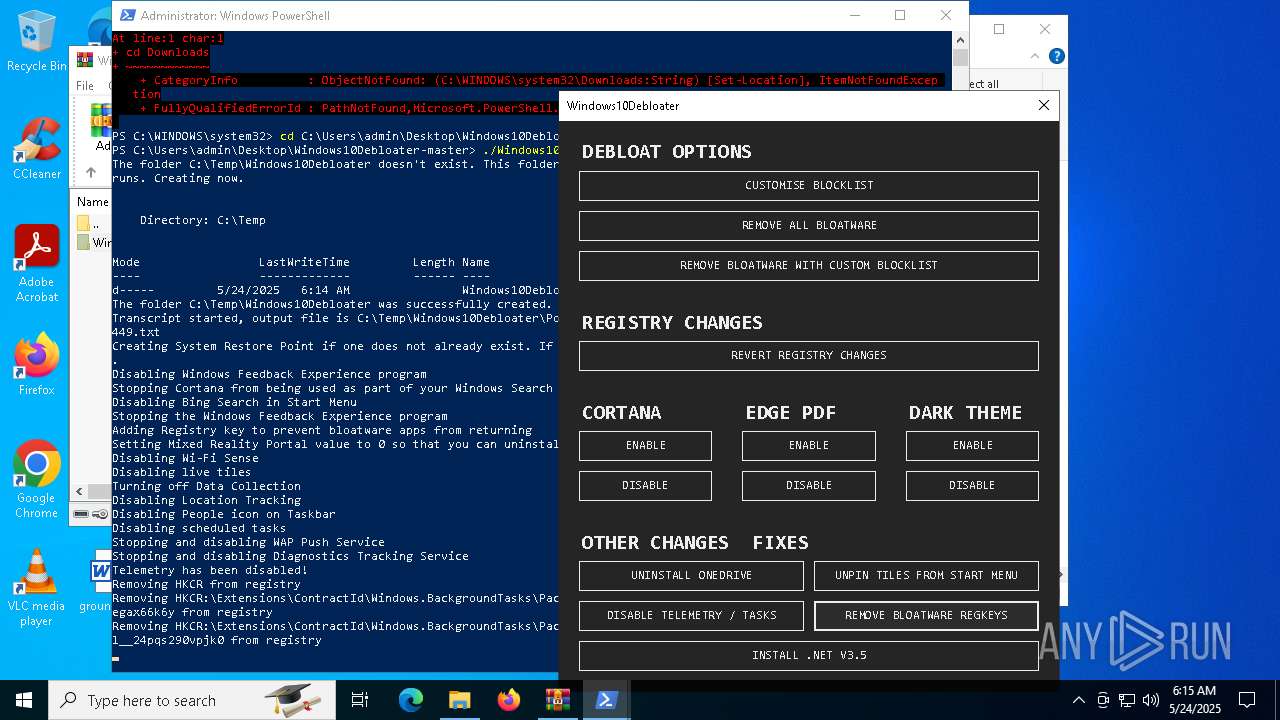
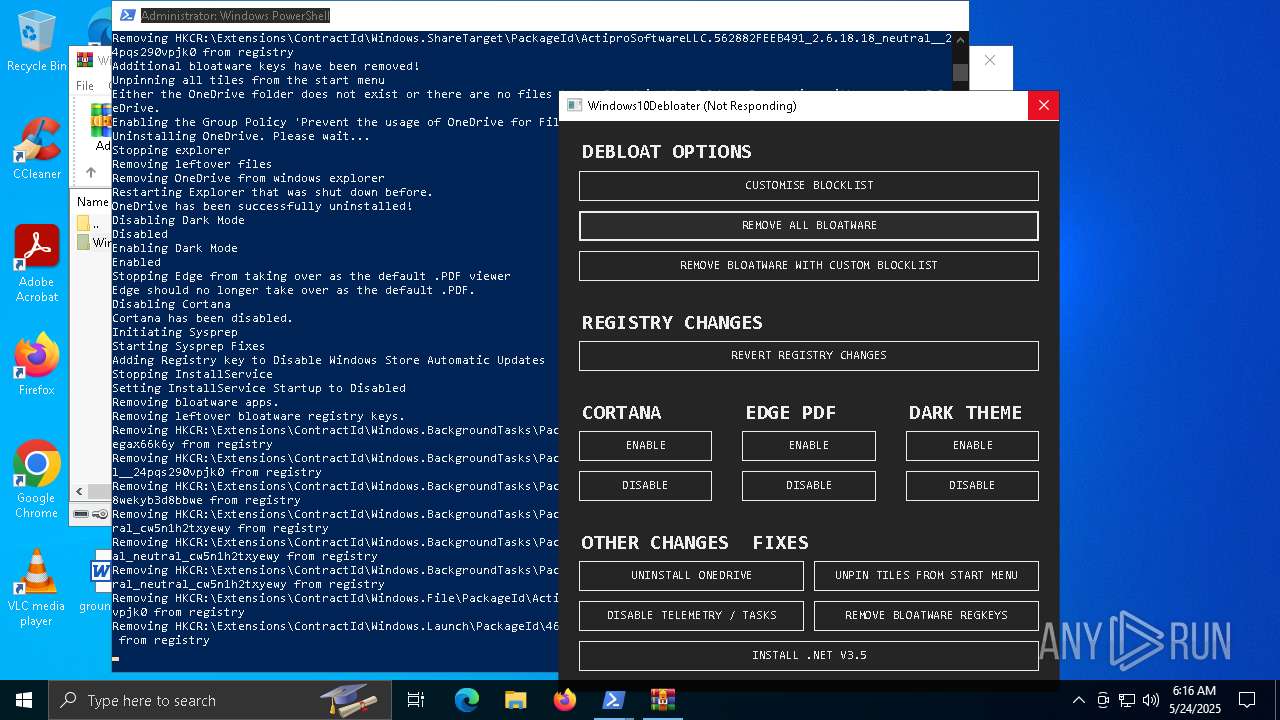
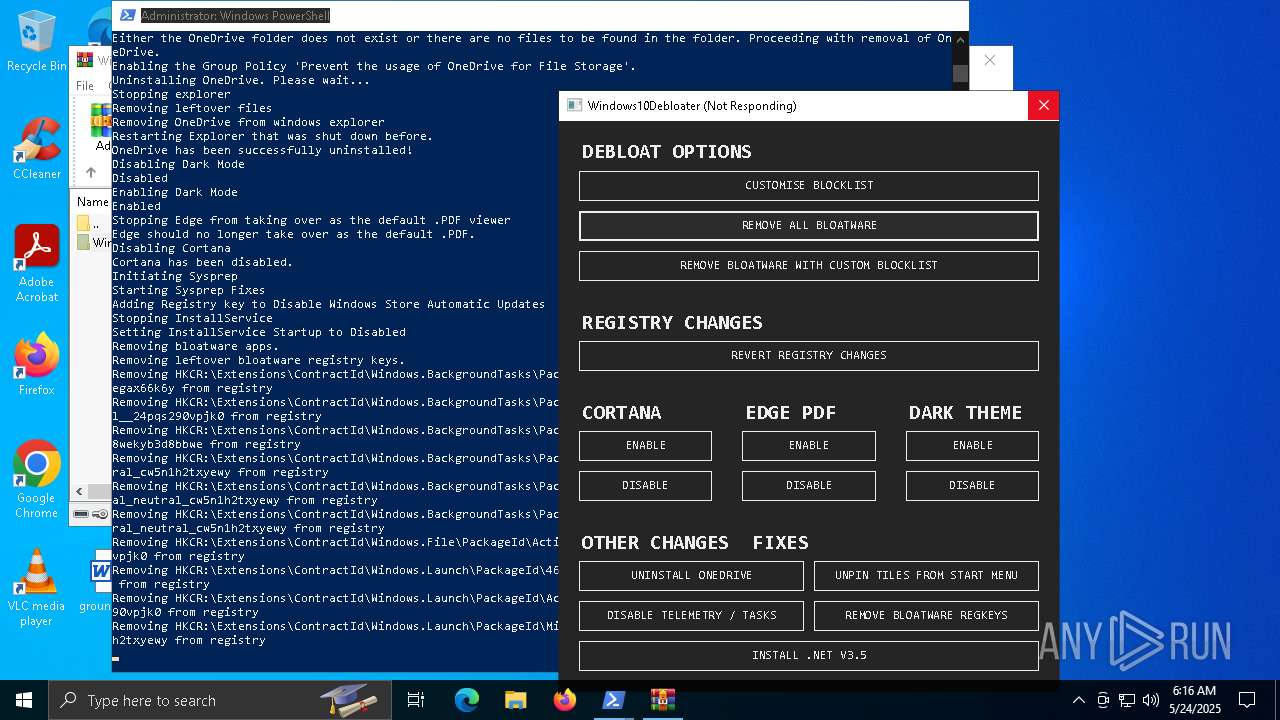
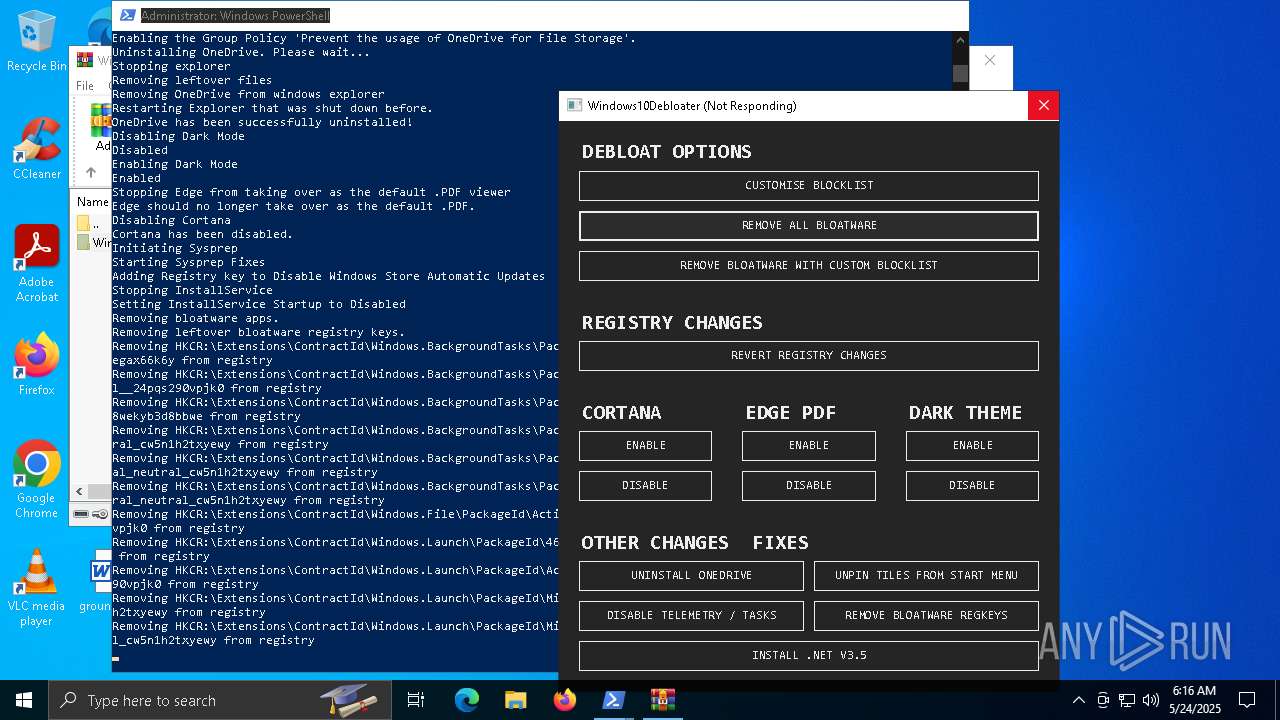
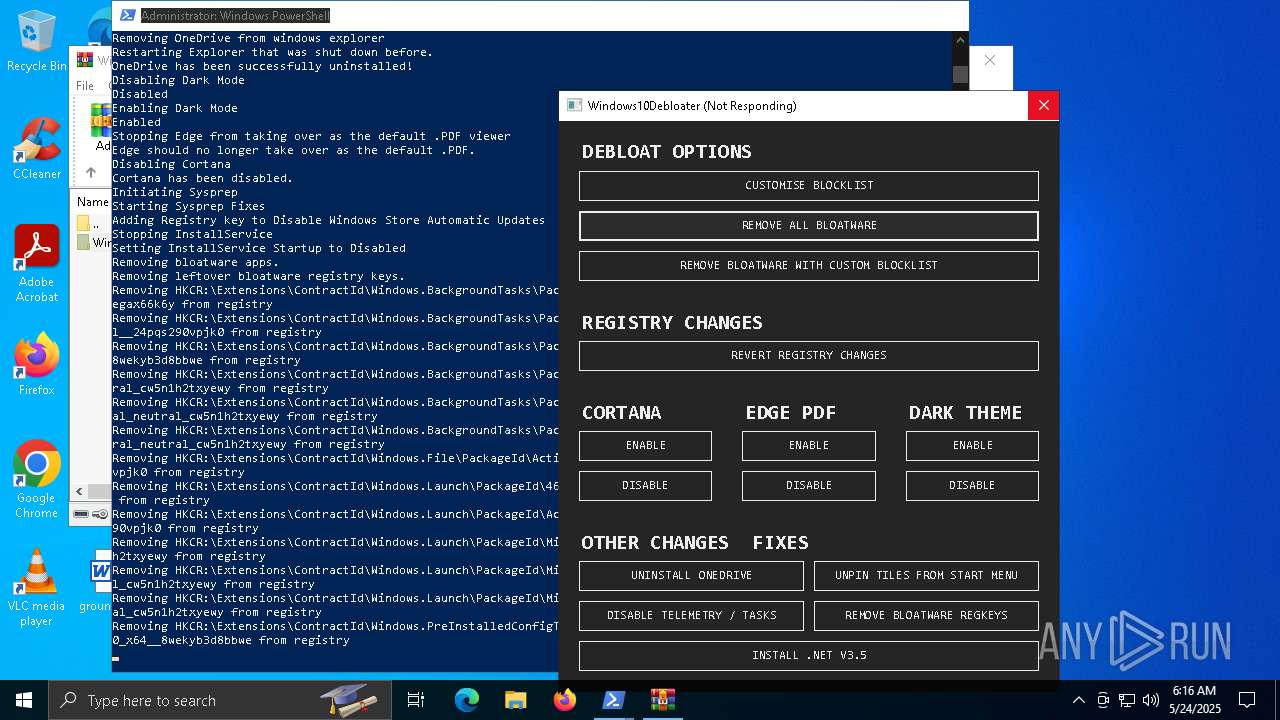
| Verdict: | Malicious activity |
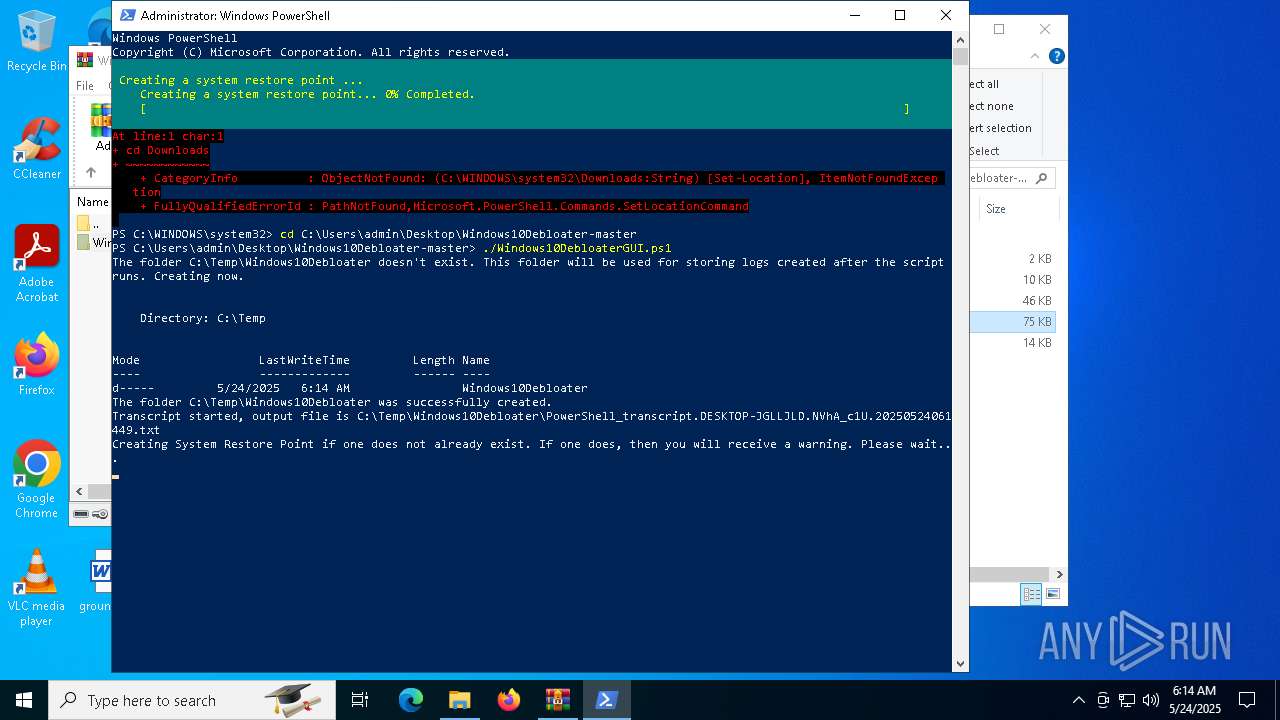
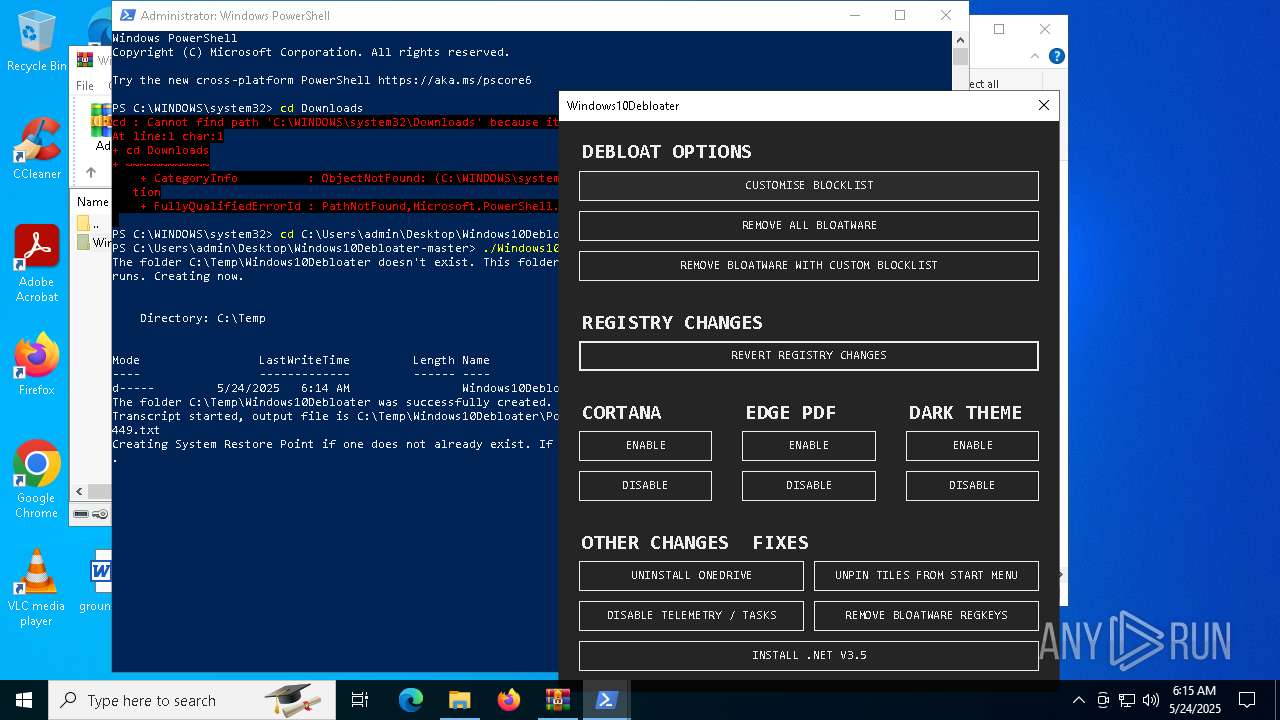
| Analysis date: | May 24, 2025, 06:12:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 4D53BC43C2281F519DC84364FC02D962 |
| SHA1: | 8F0CF61D9F9ACD1E55D89E50228977D811D3E165 |
| SHA256: | 3C157C5B7547905869057BBF7FC5FF054E879DFBD147B6A9D82382180100F74C |
| SSDEEP: | 1536:Ka8kbJEk7J2rABW5H/KQ20+7nJCom7nXQJDKmpBYbNmU77:/82irA0Ub0+NCombAPBYbNH |
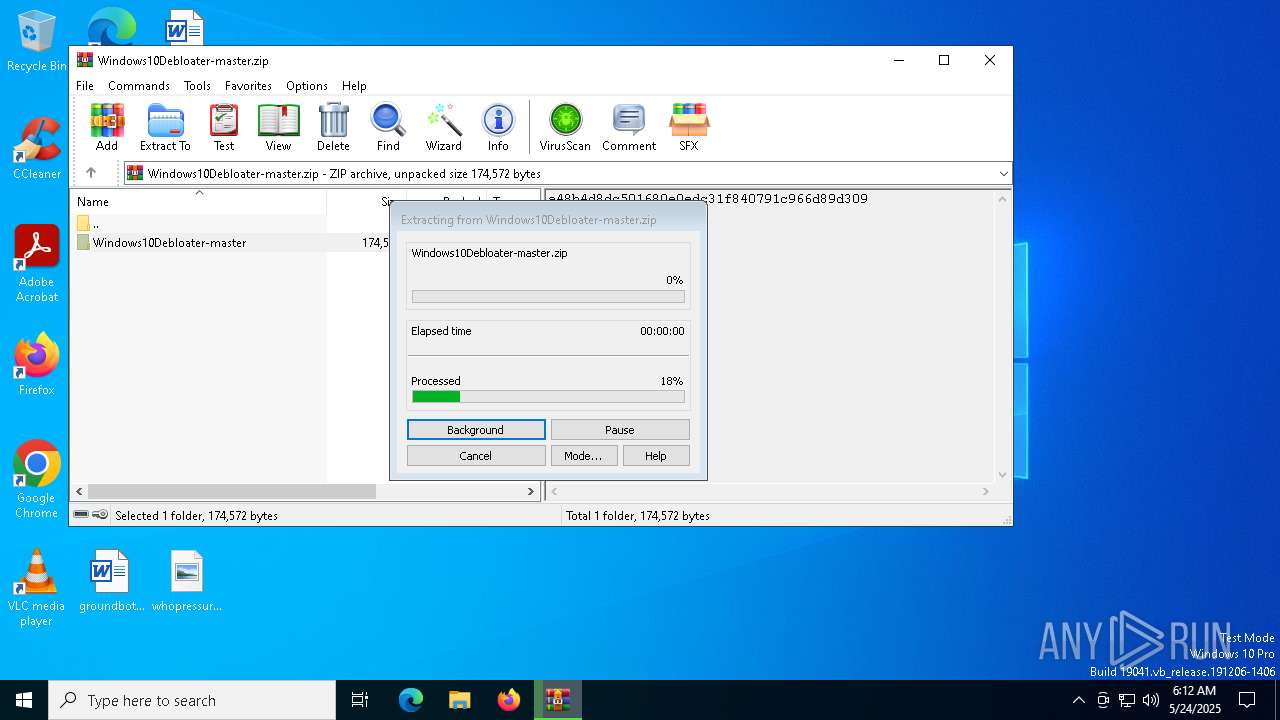
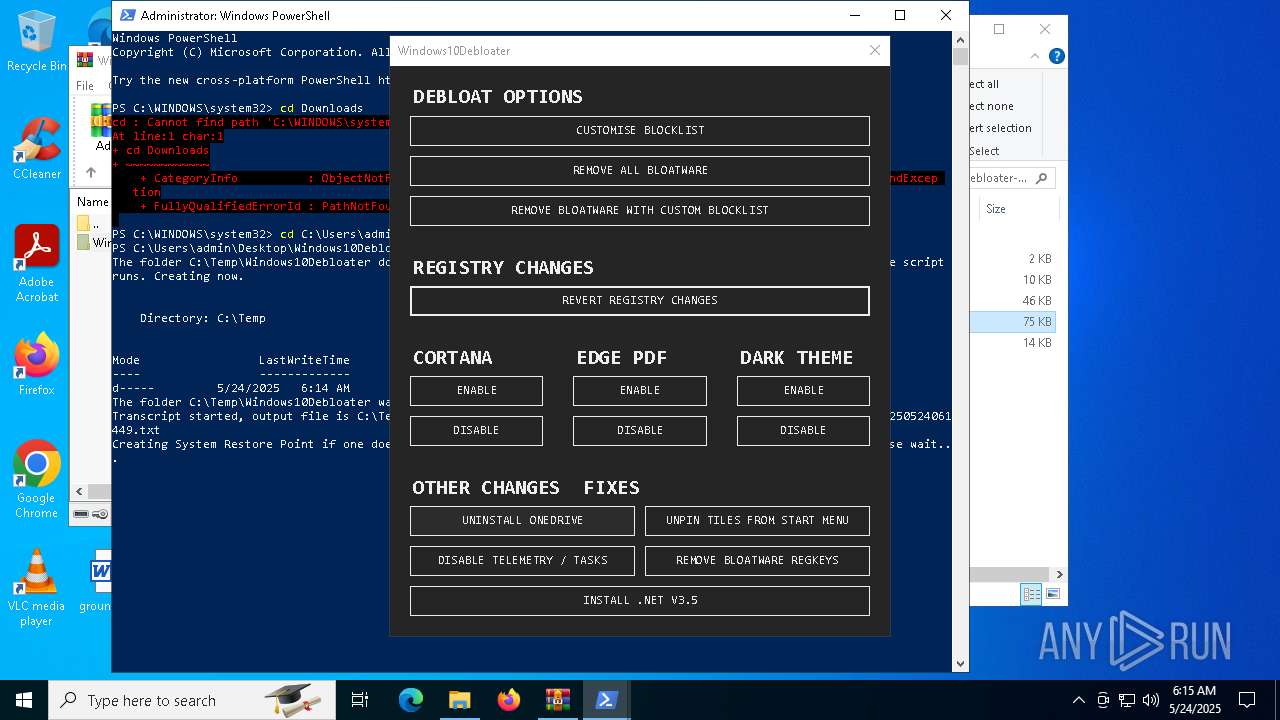
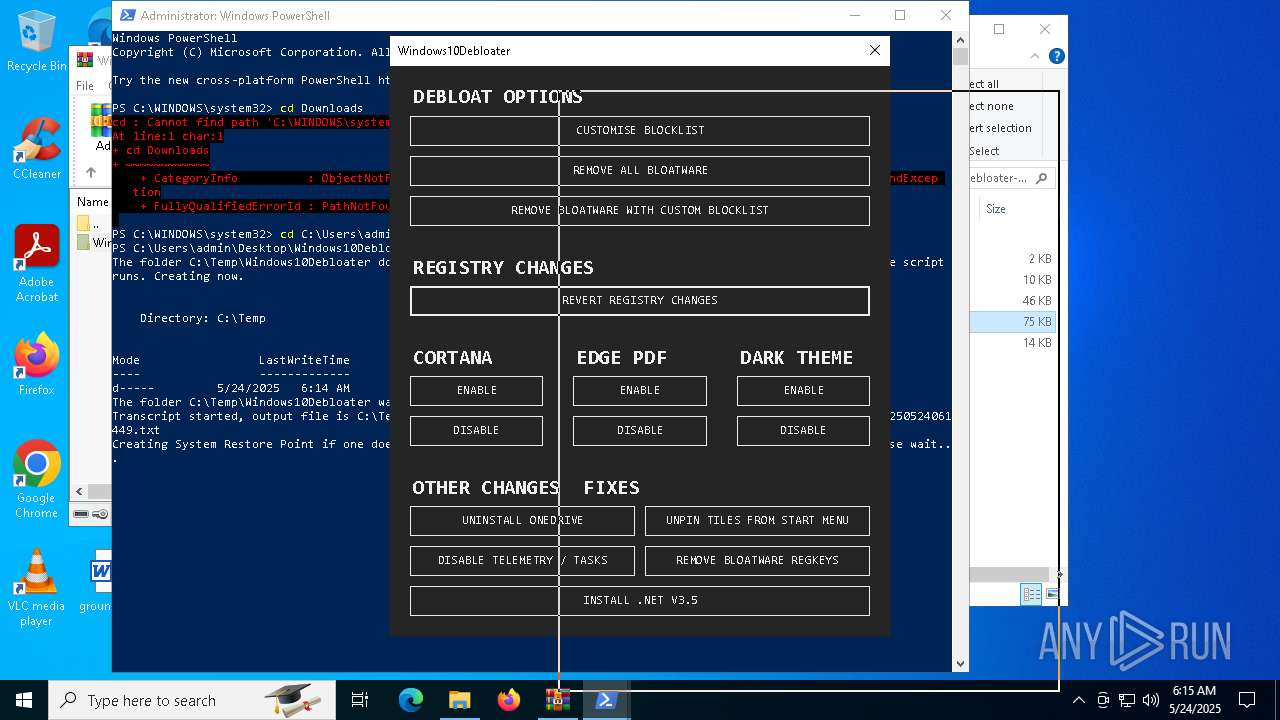
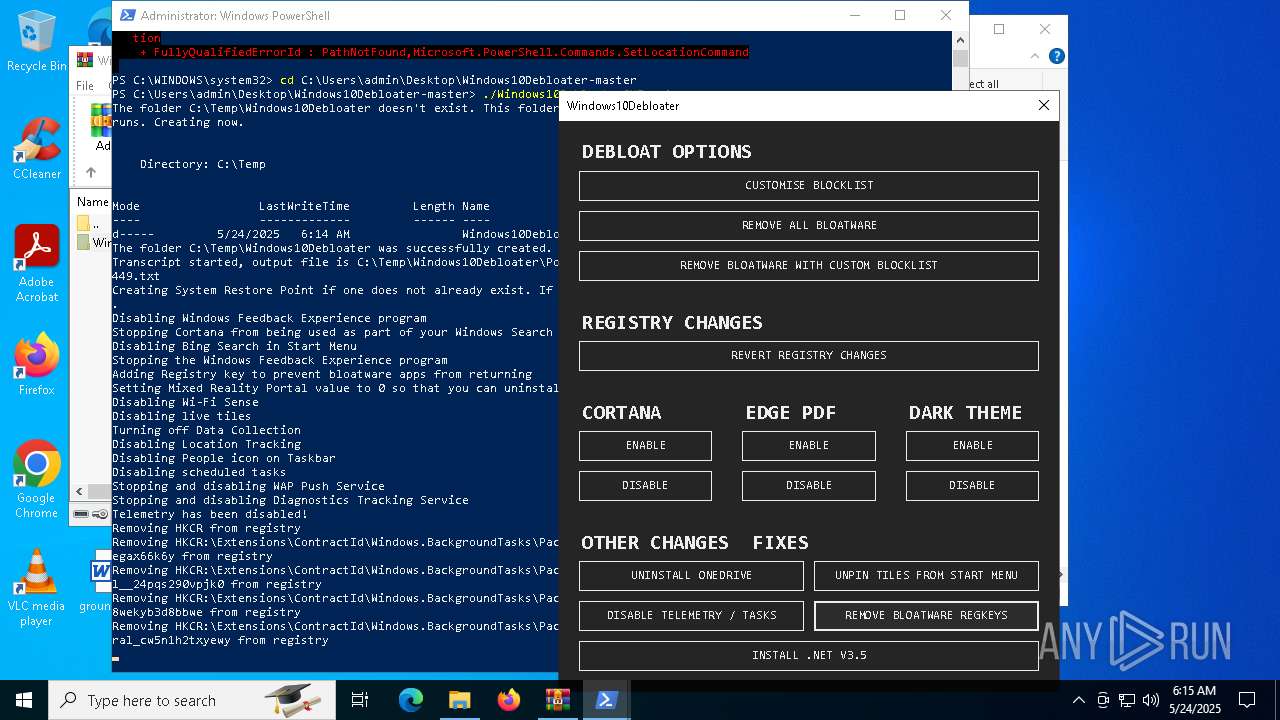
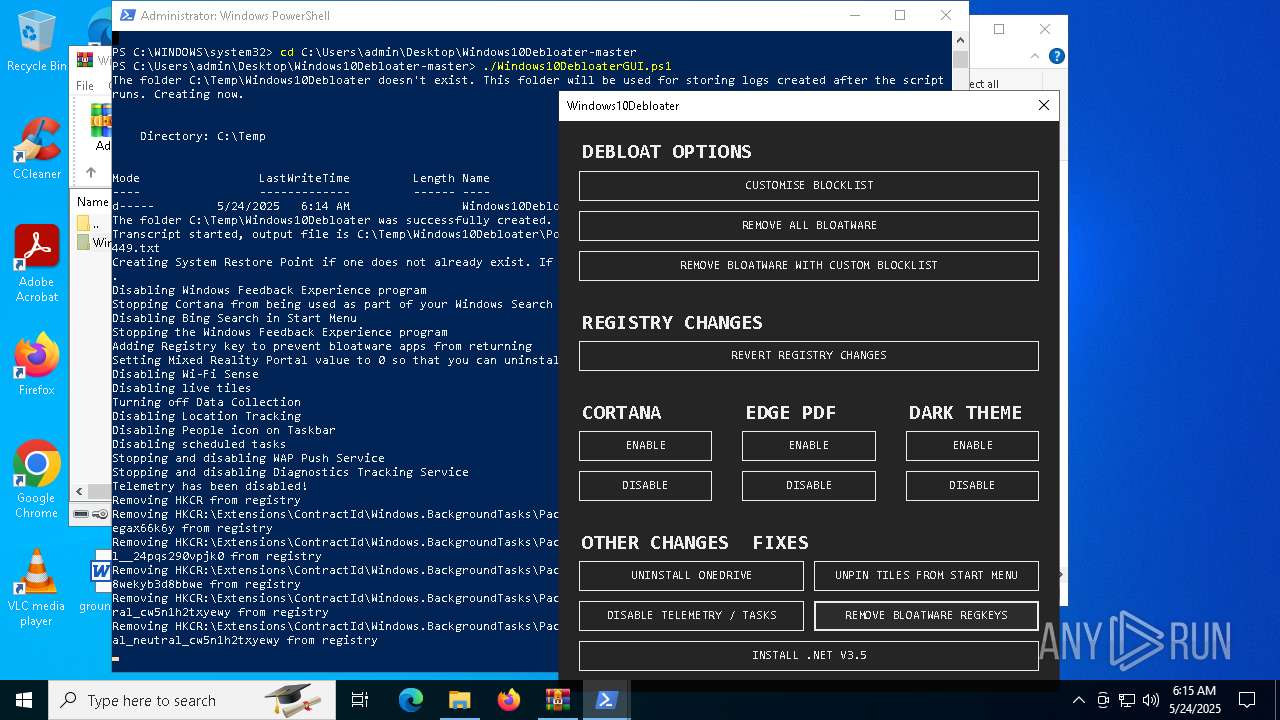
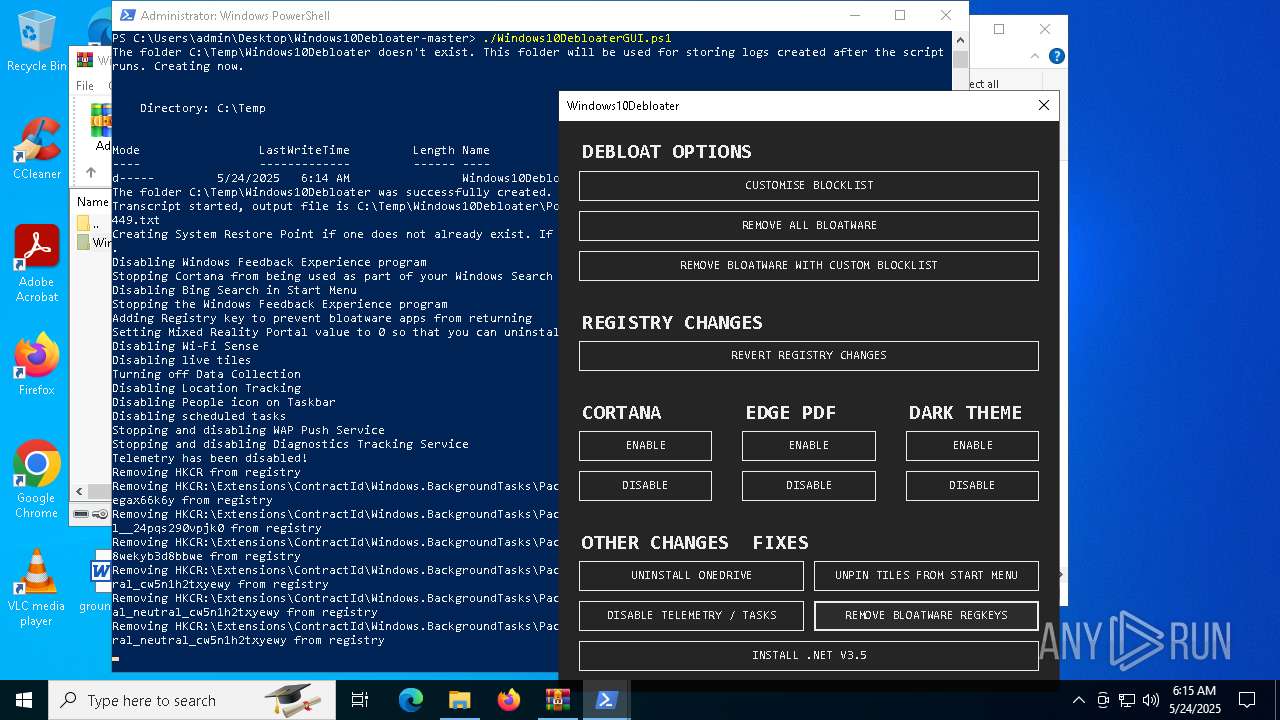
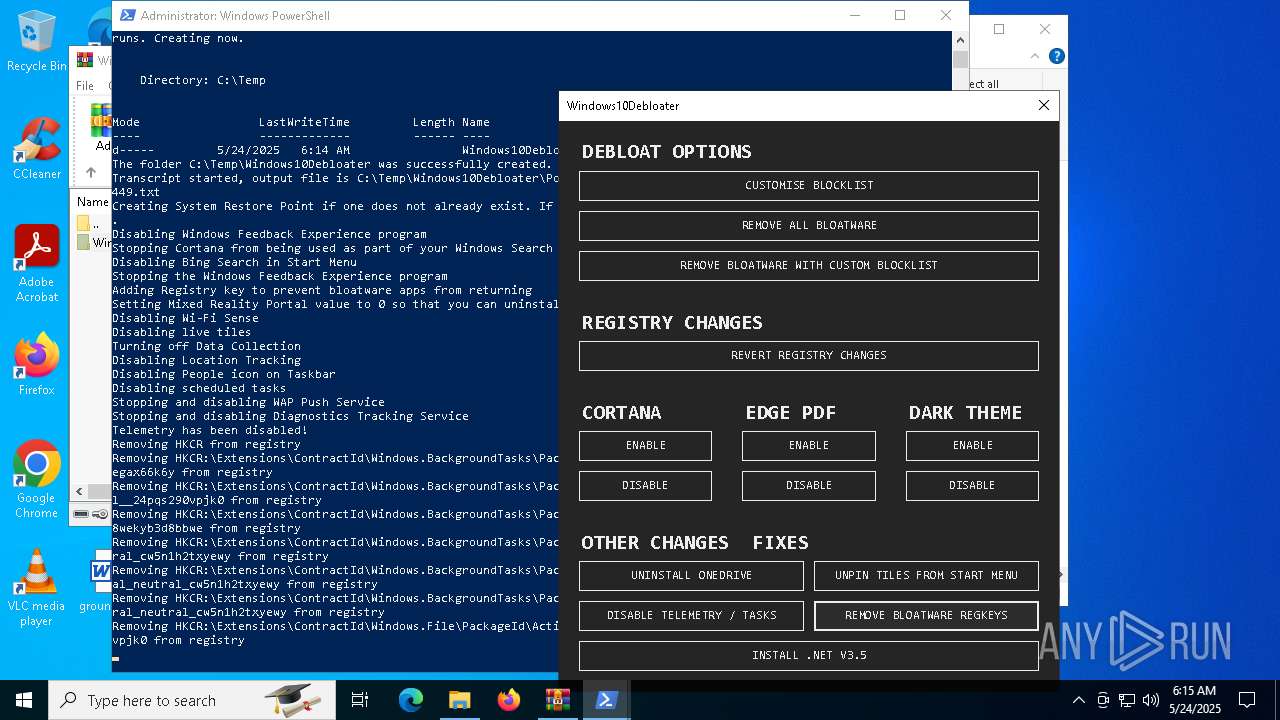
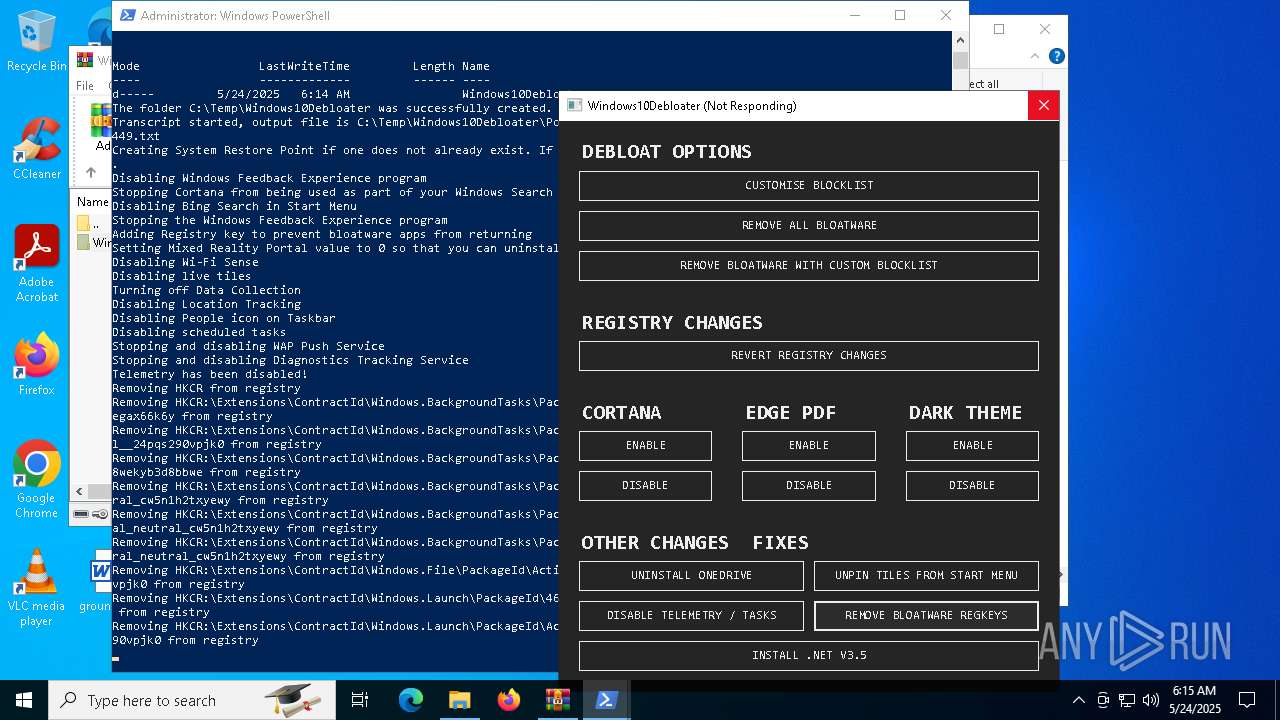
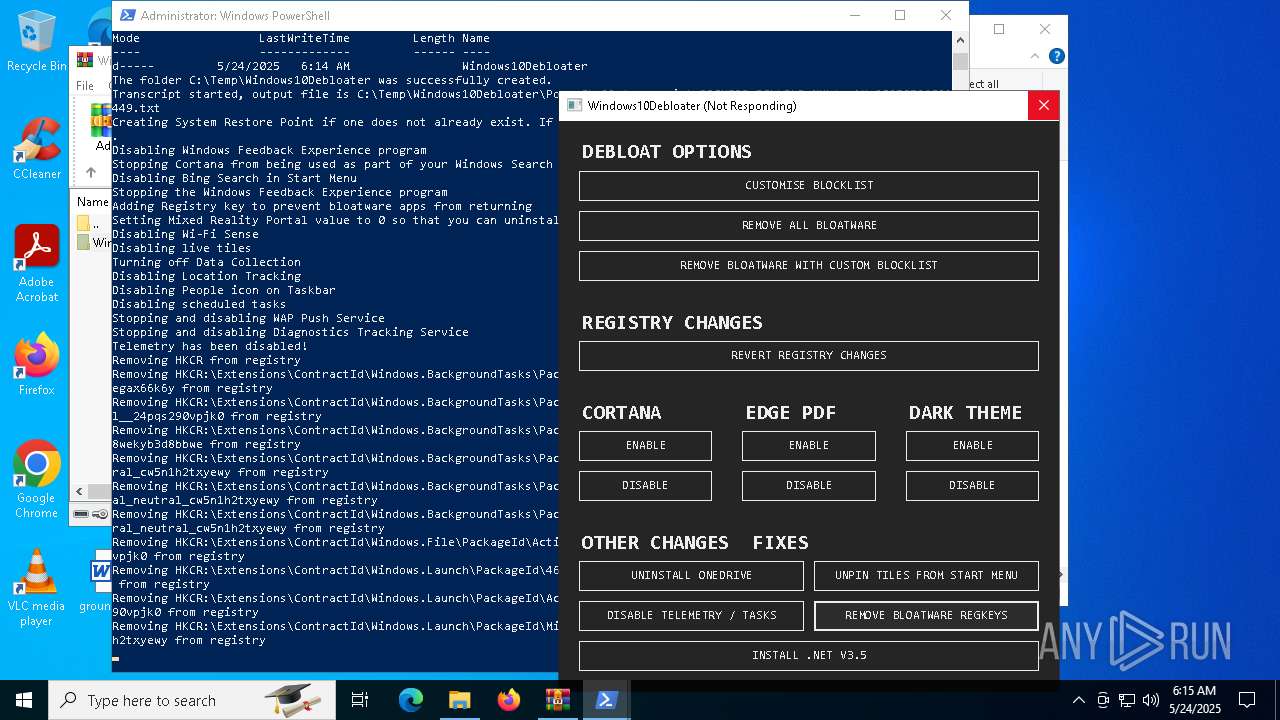
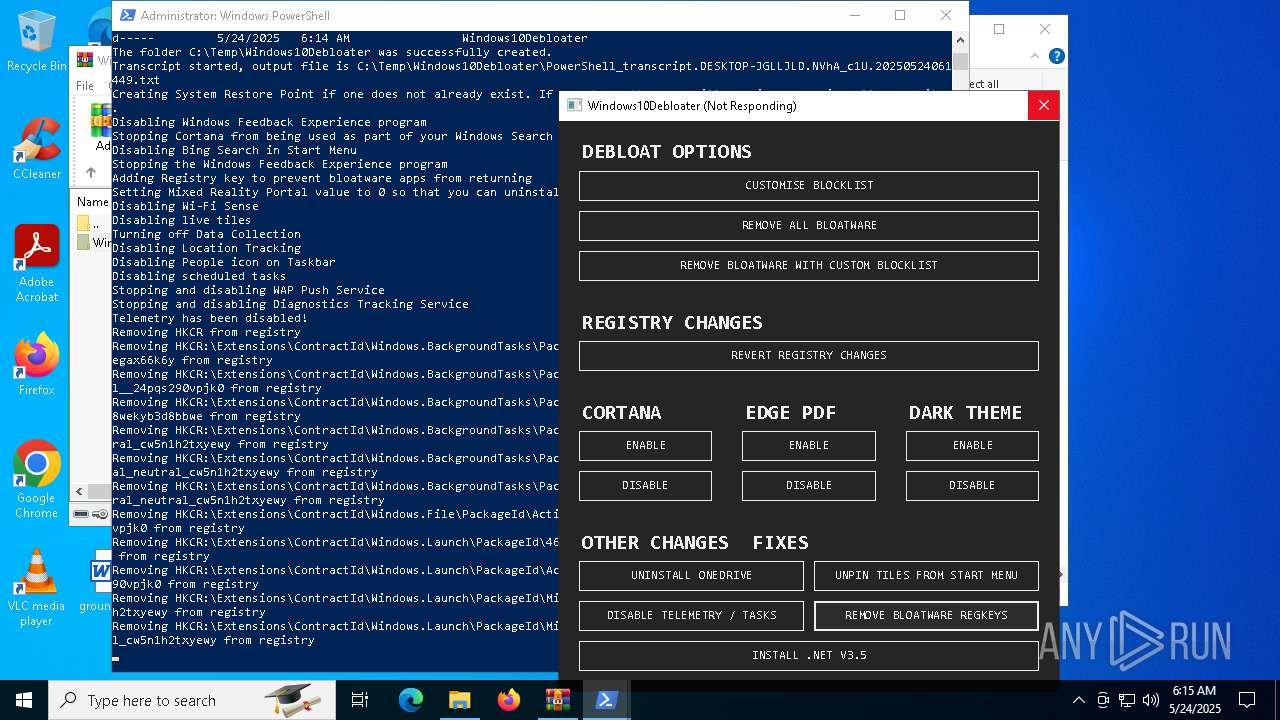
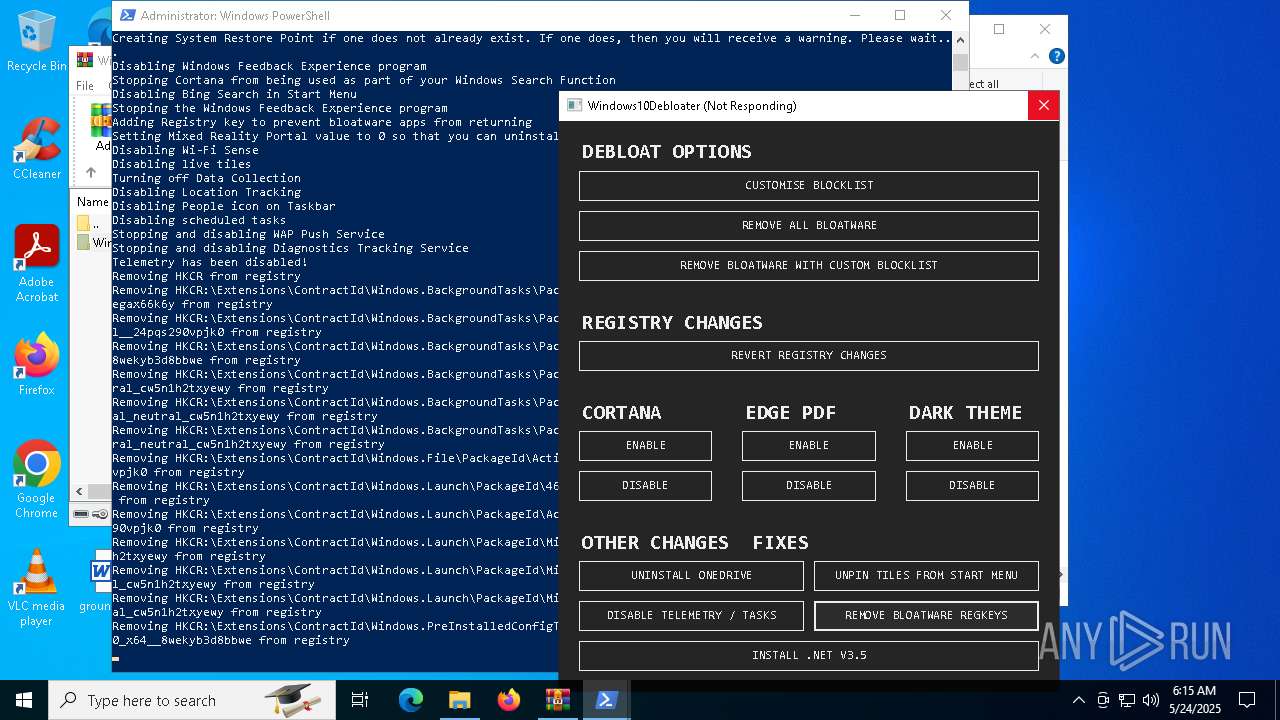
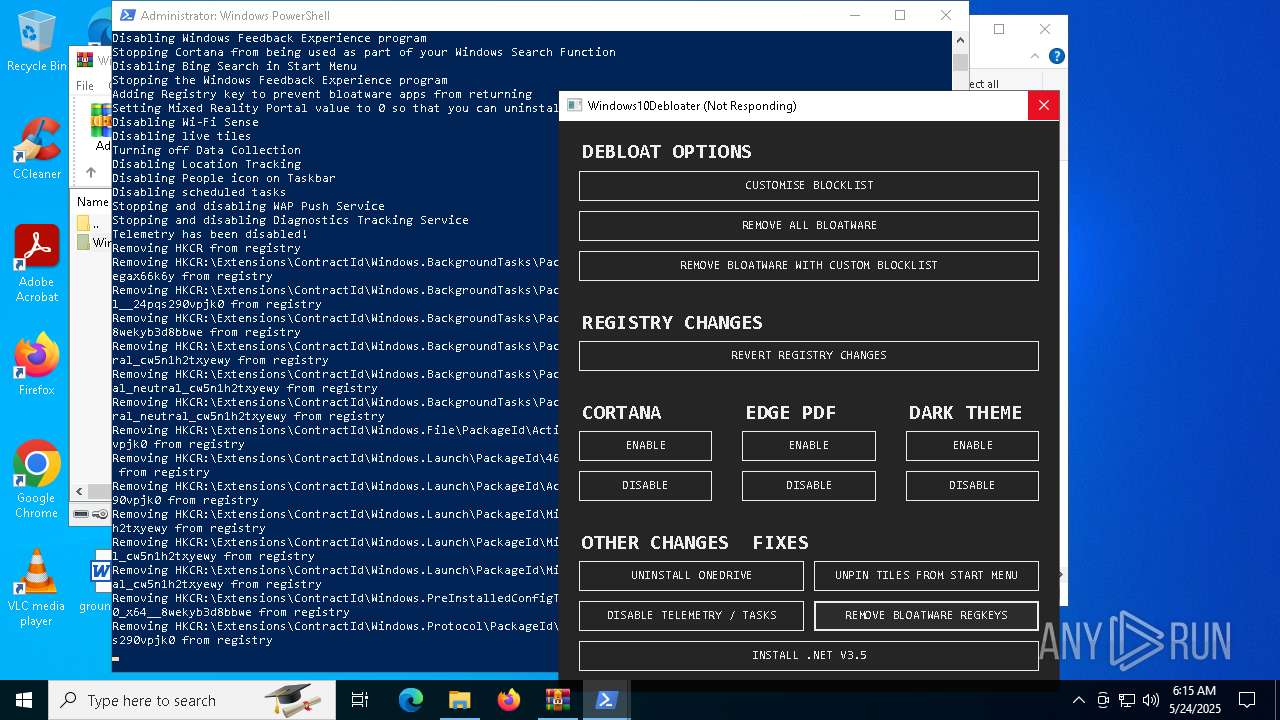
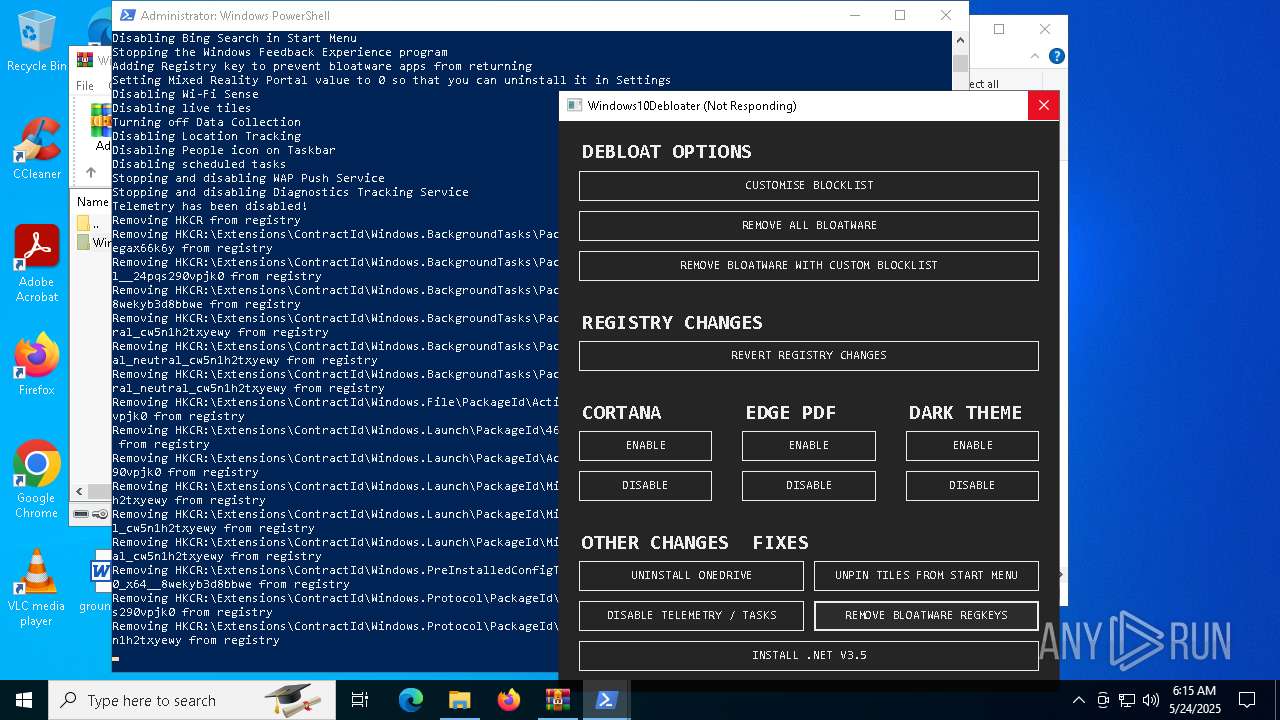
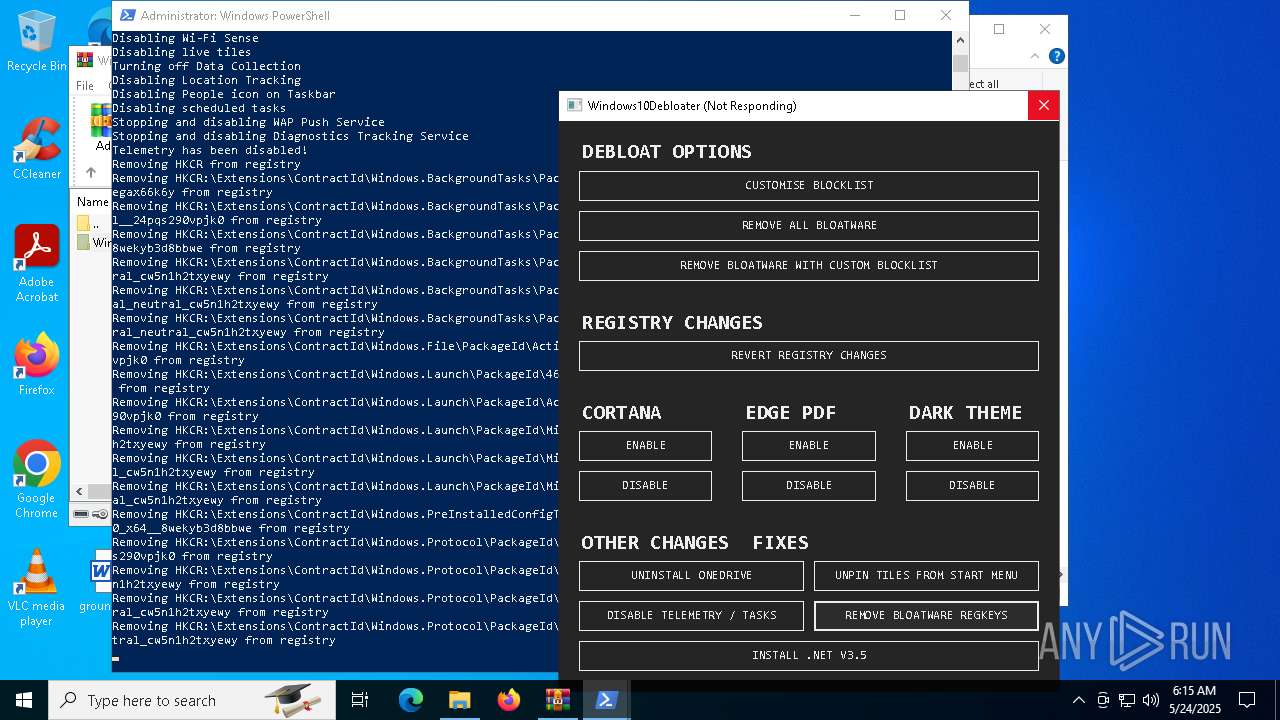
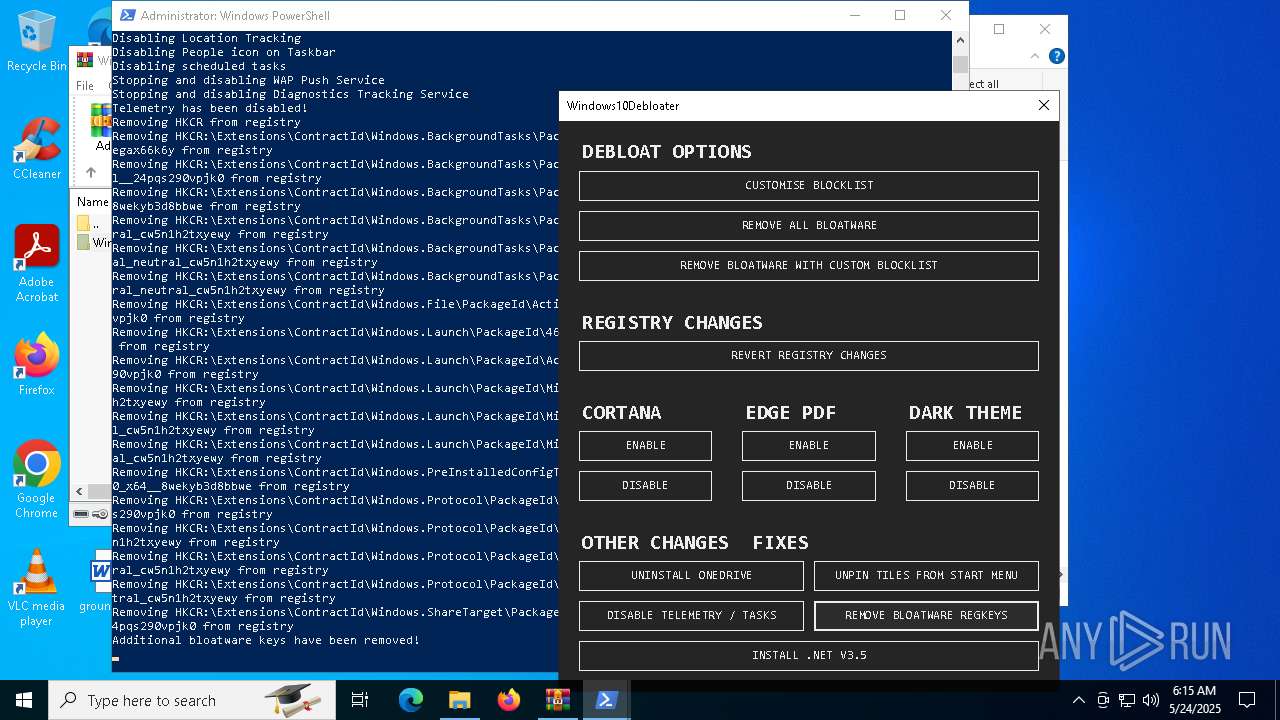
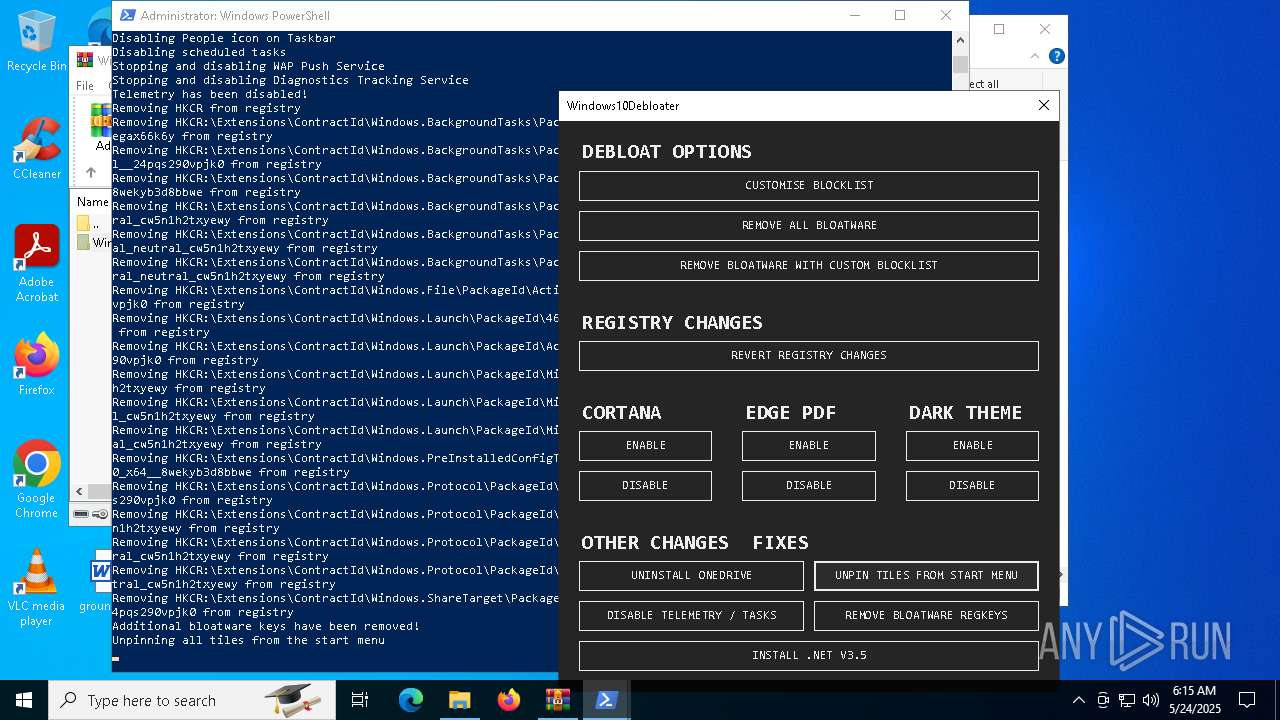
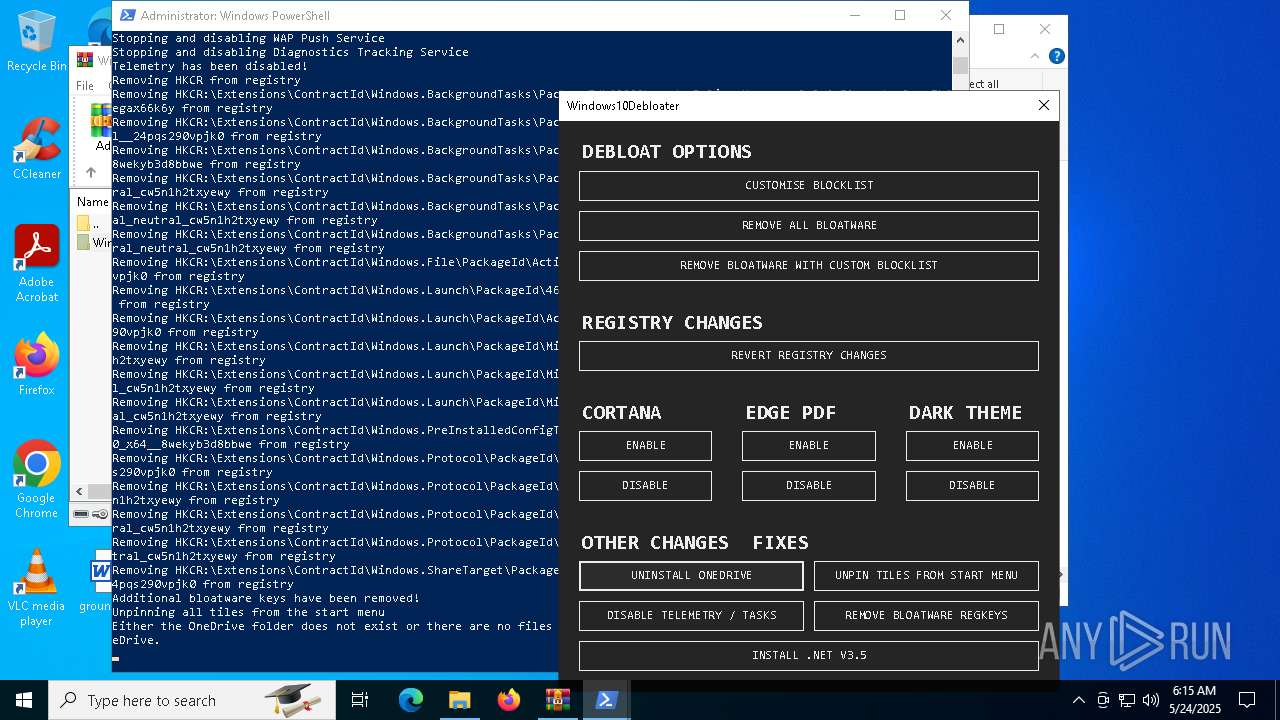
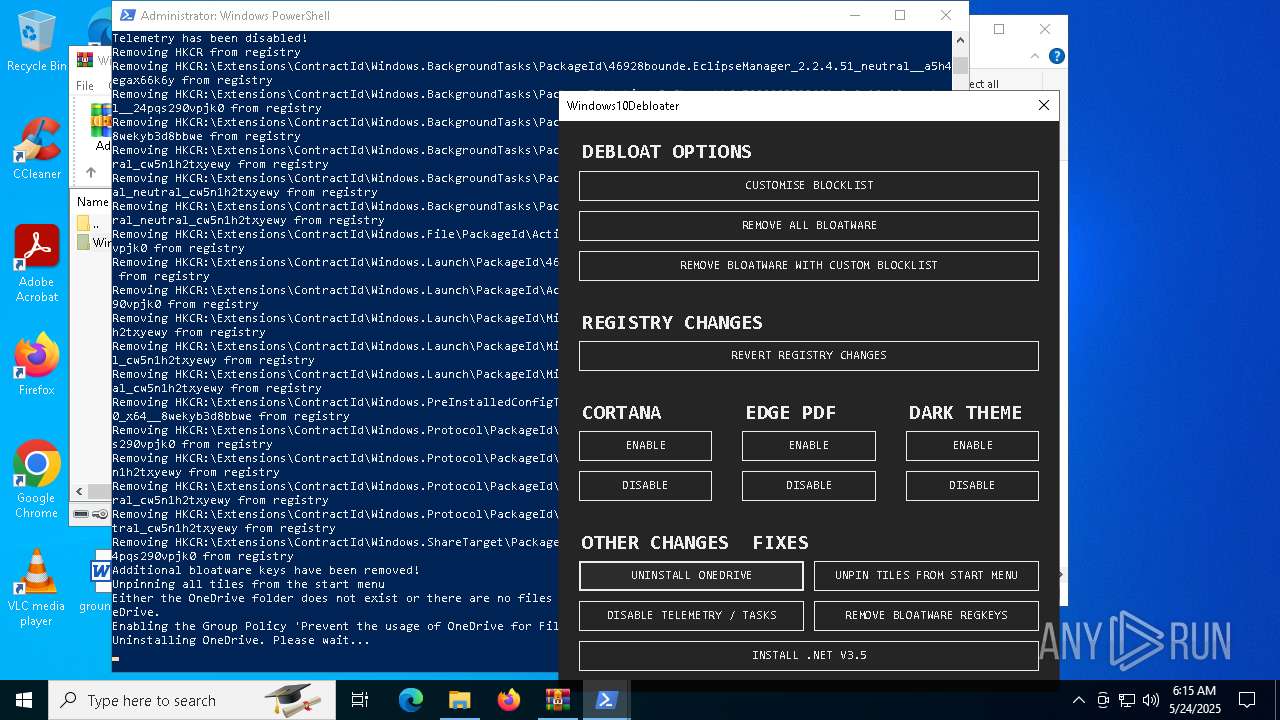
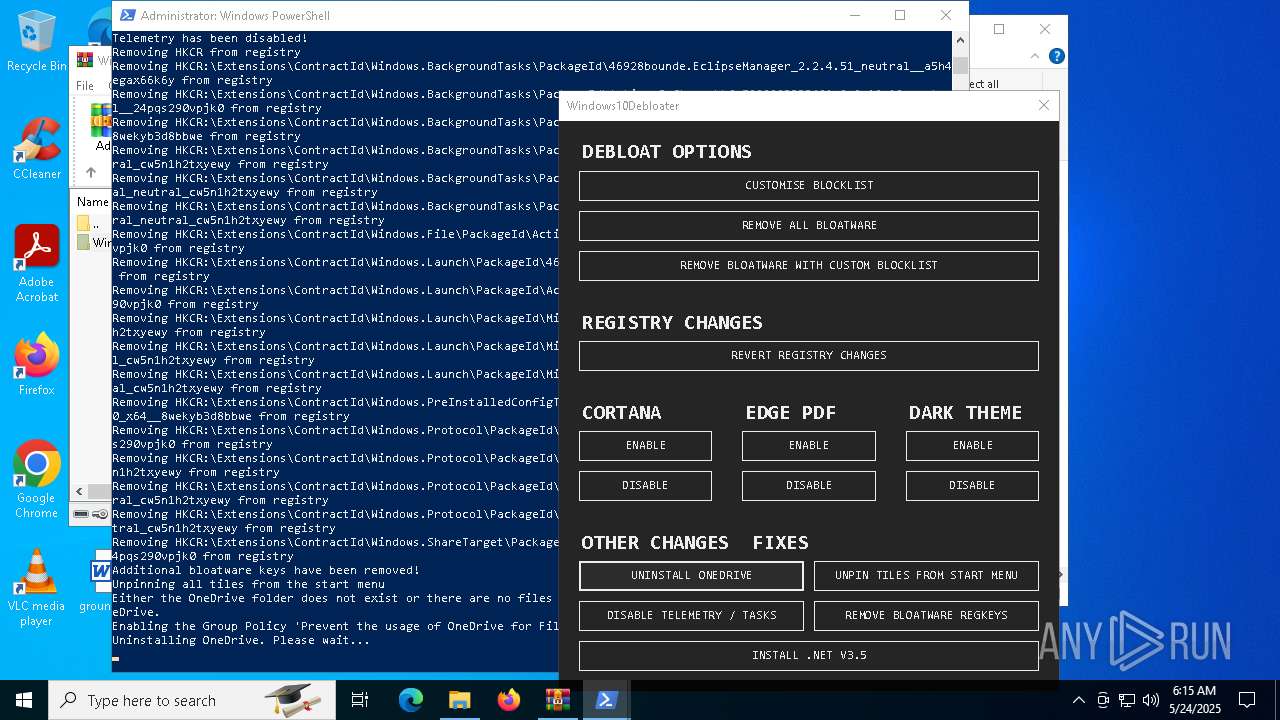
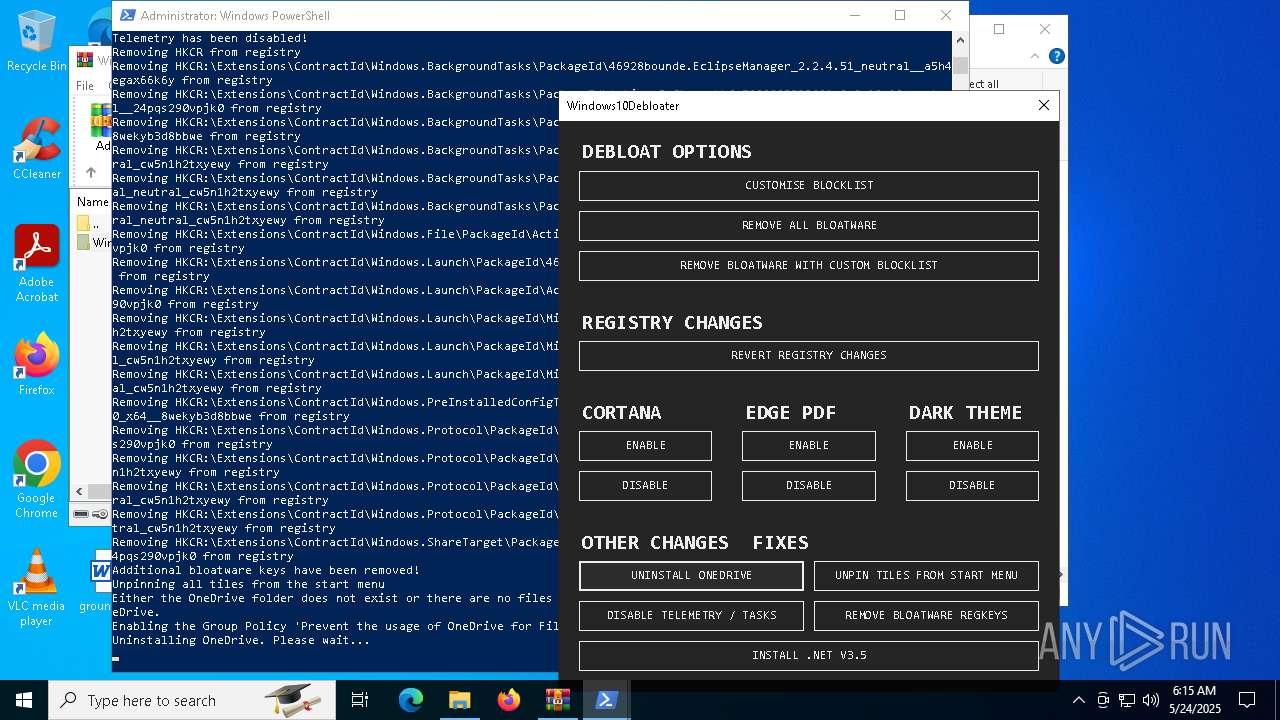
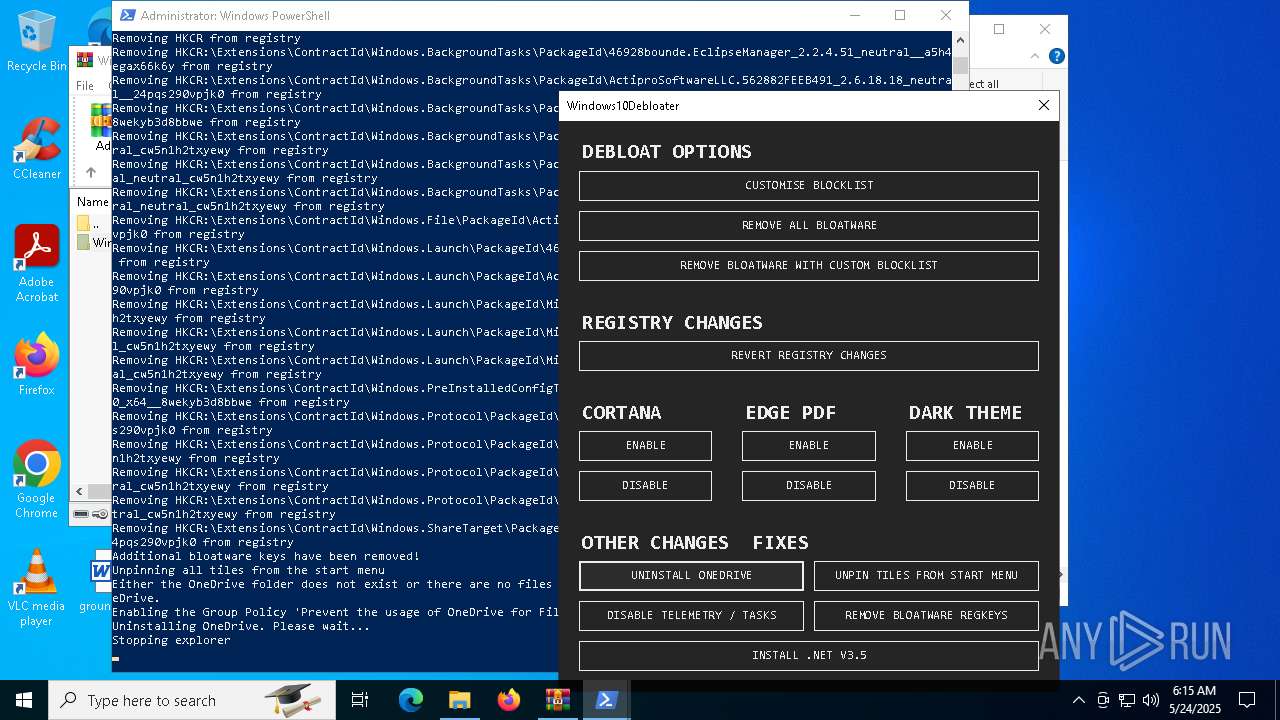
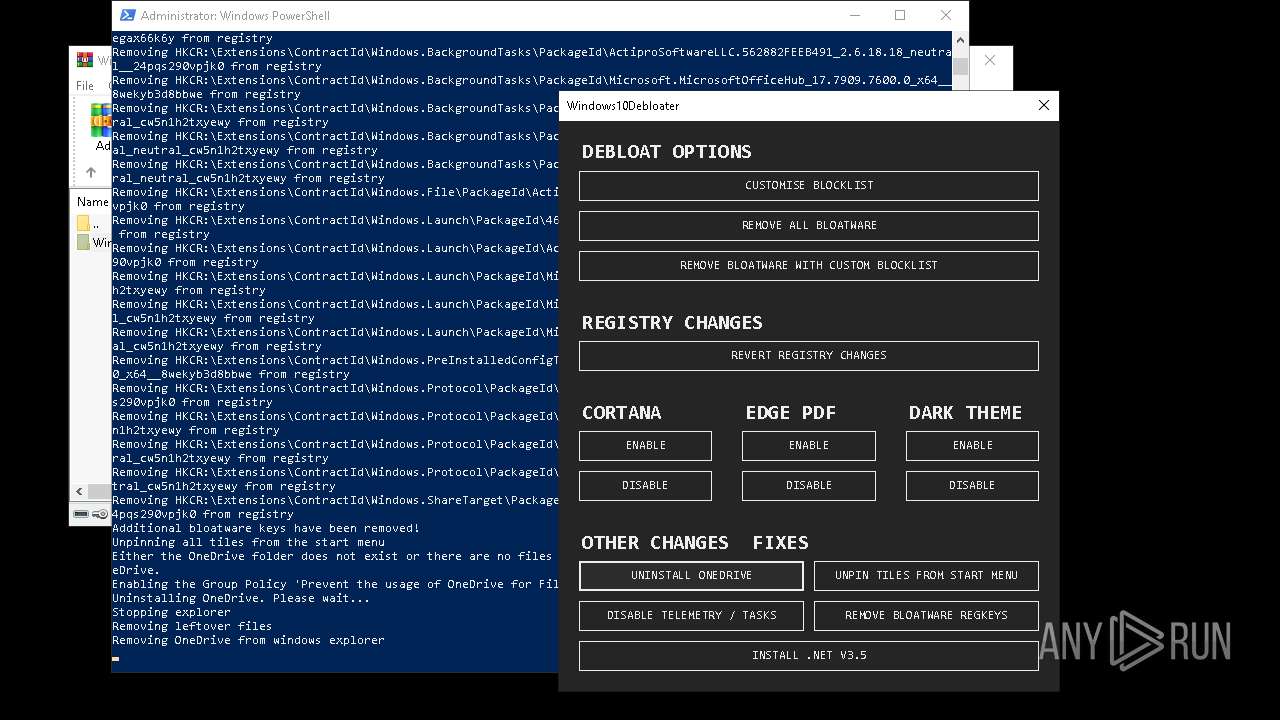
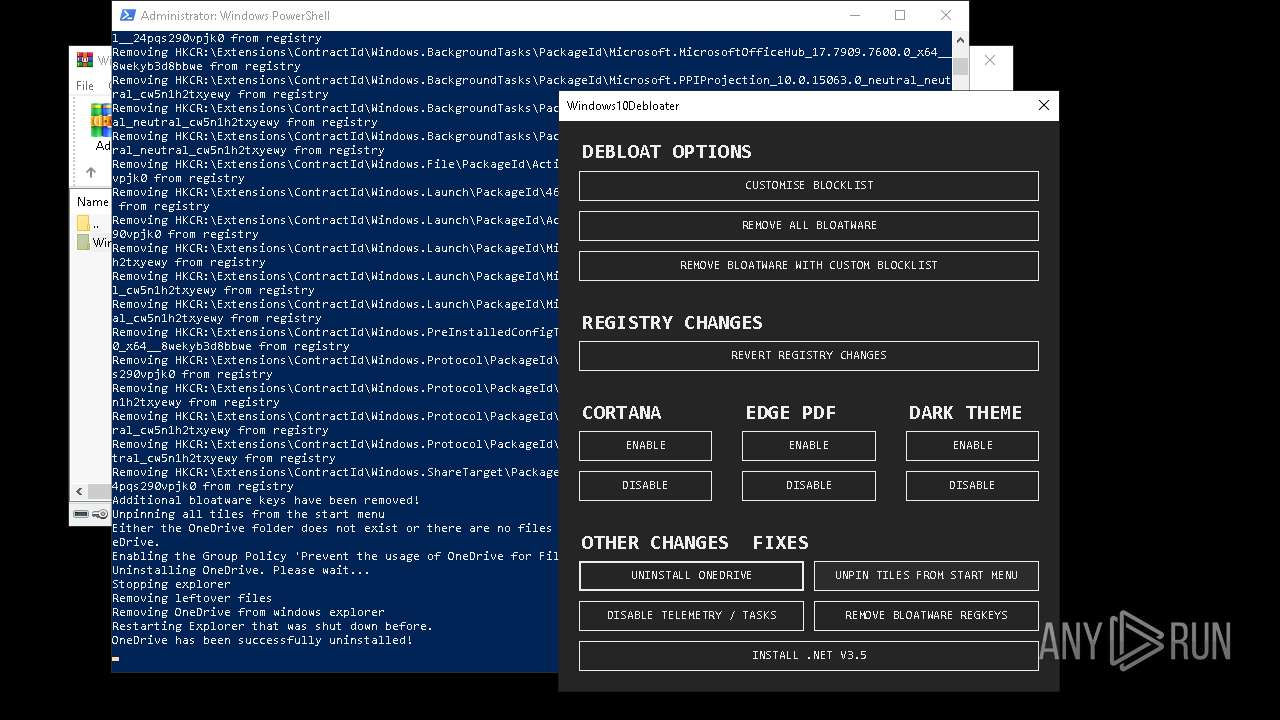
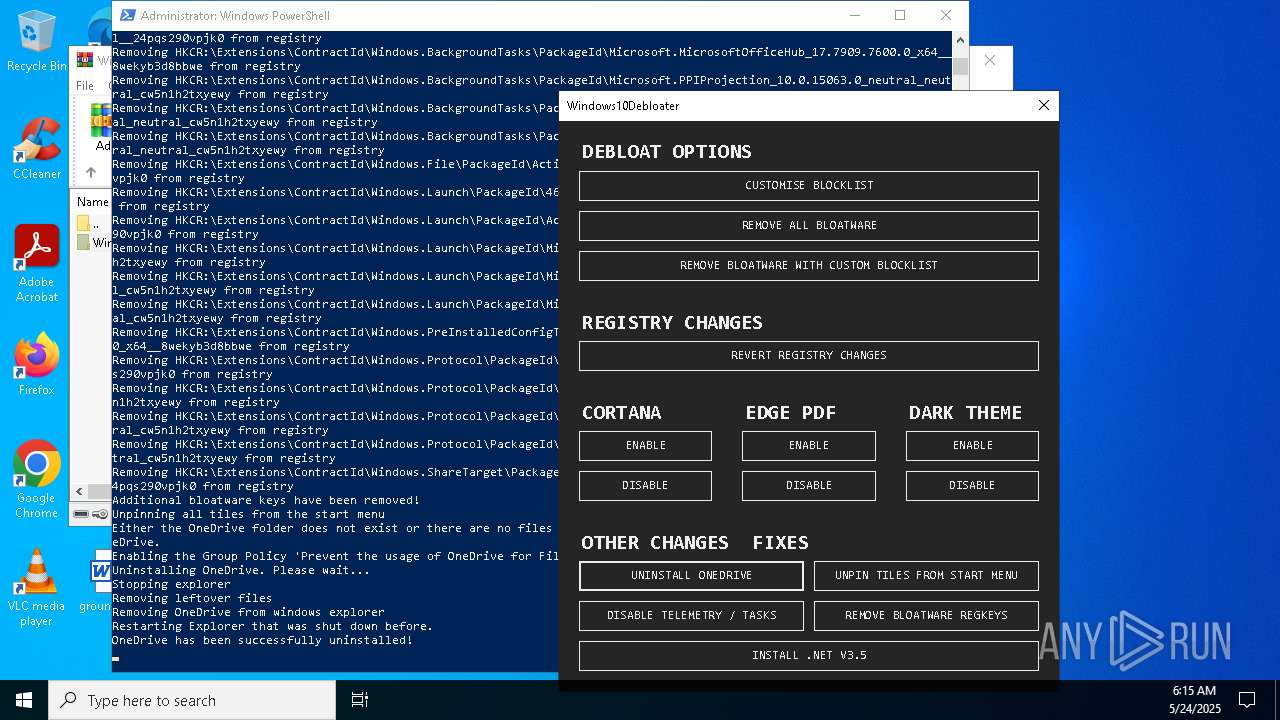
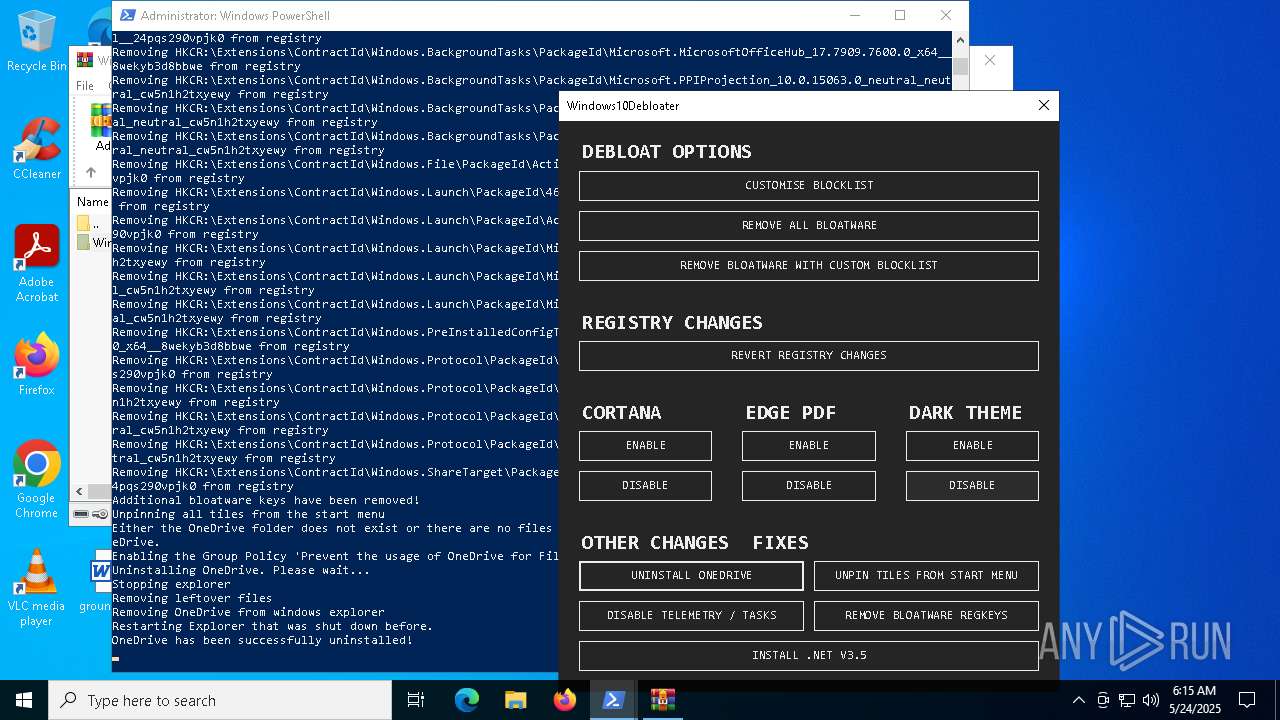
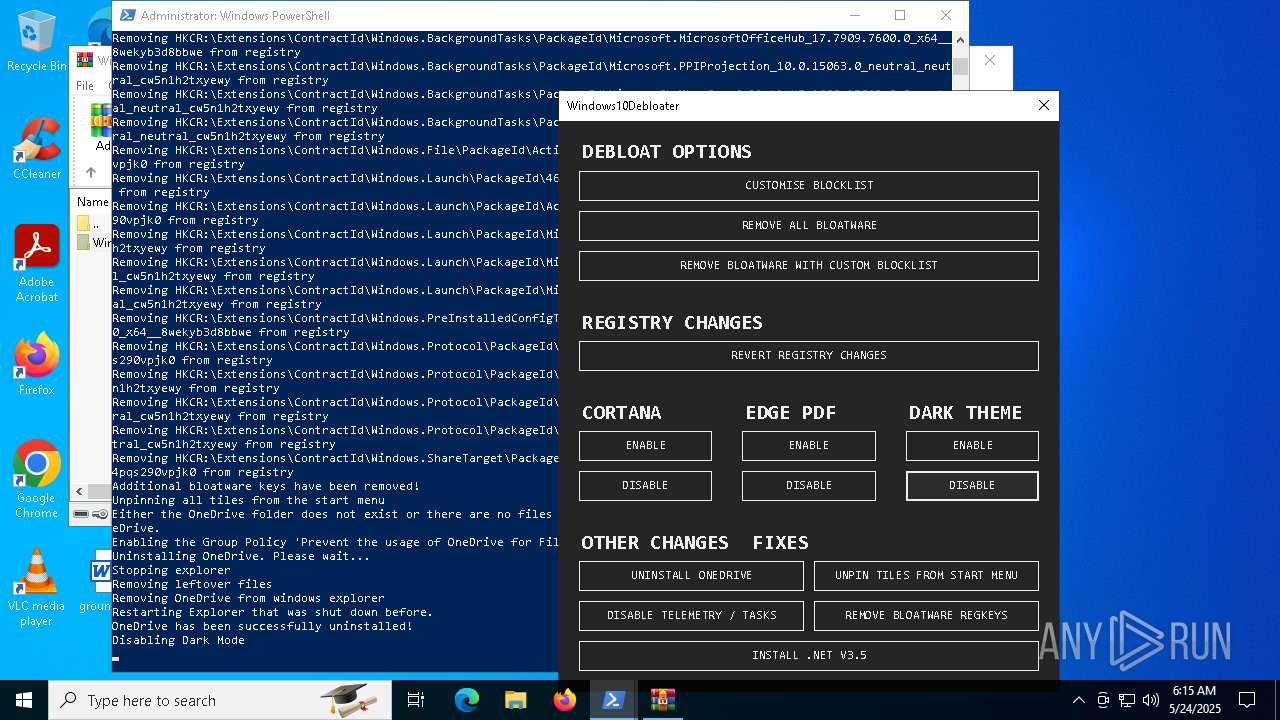
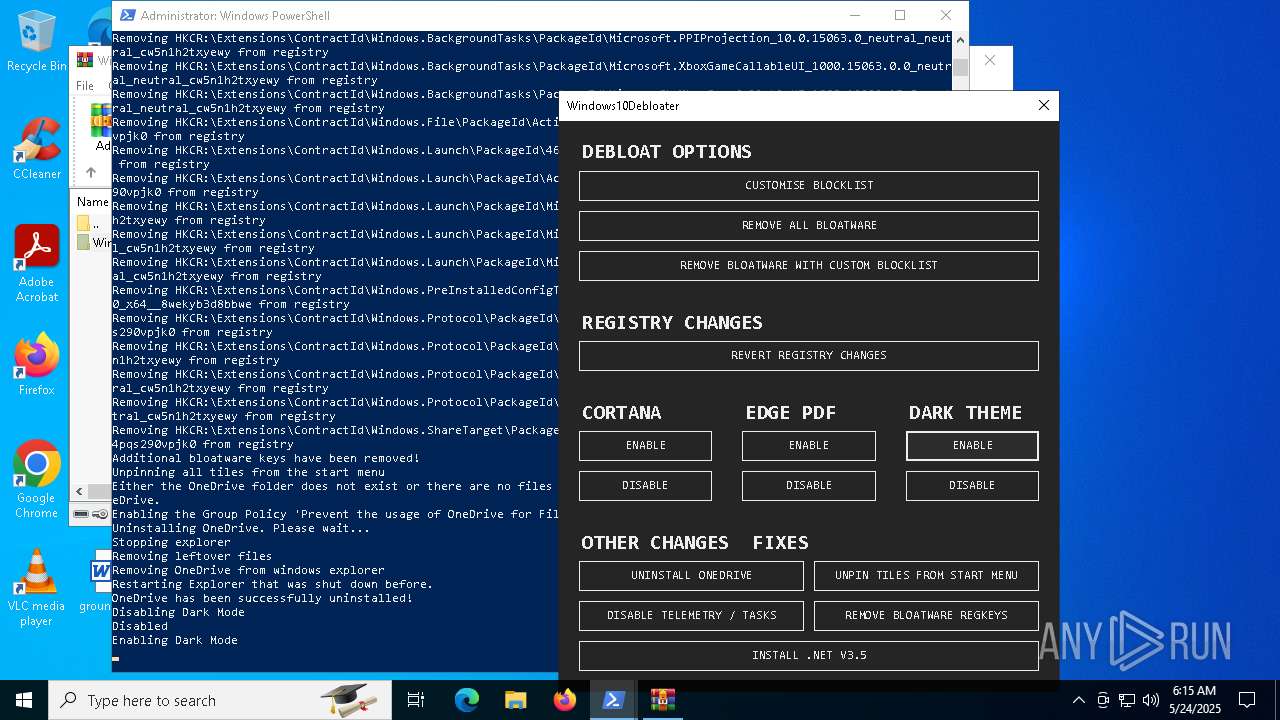
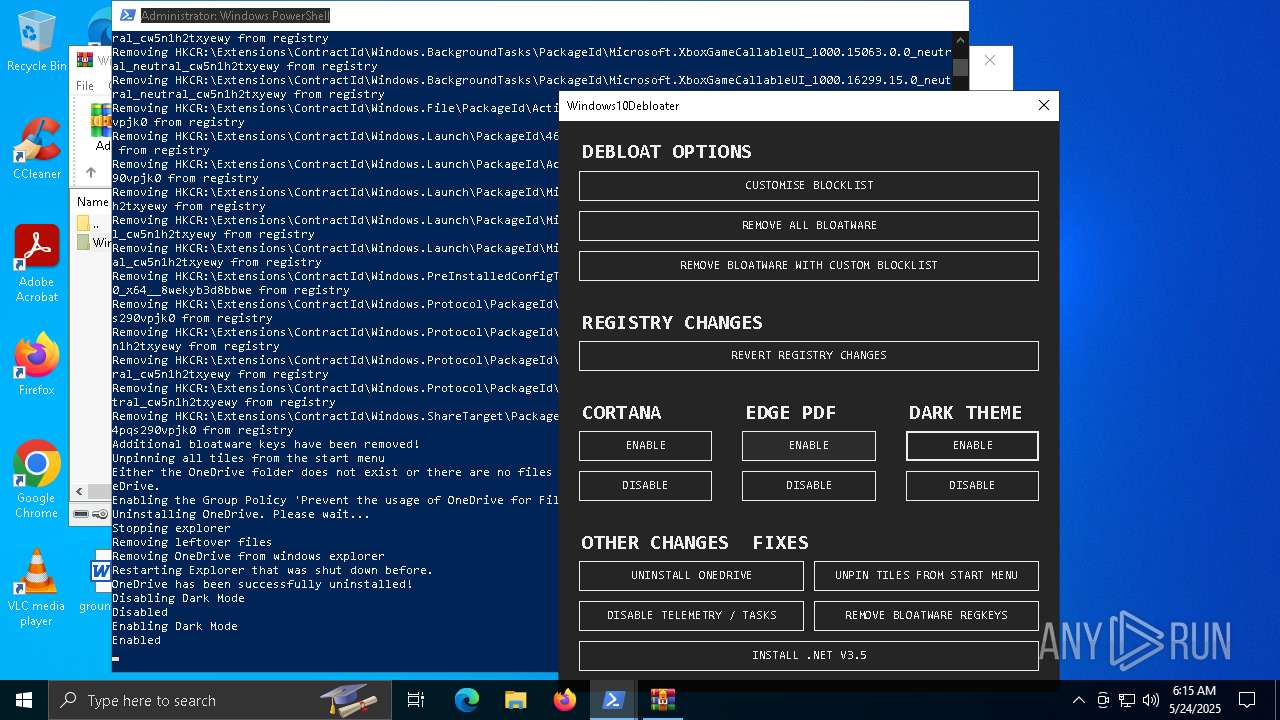
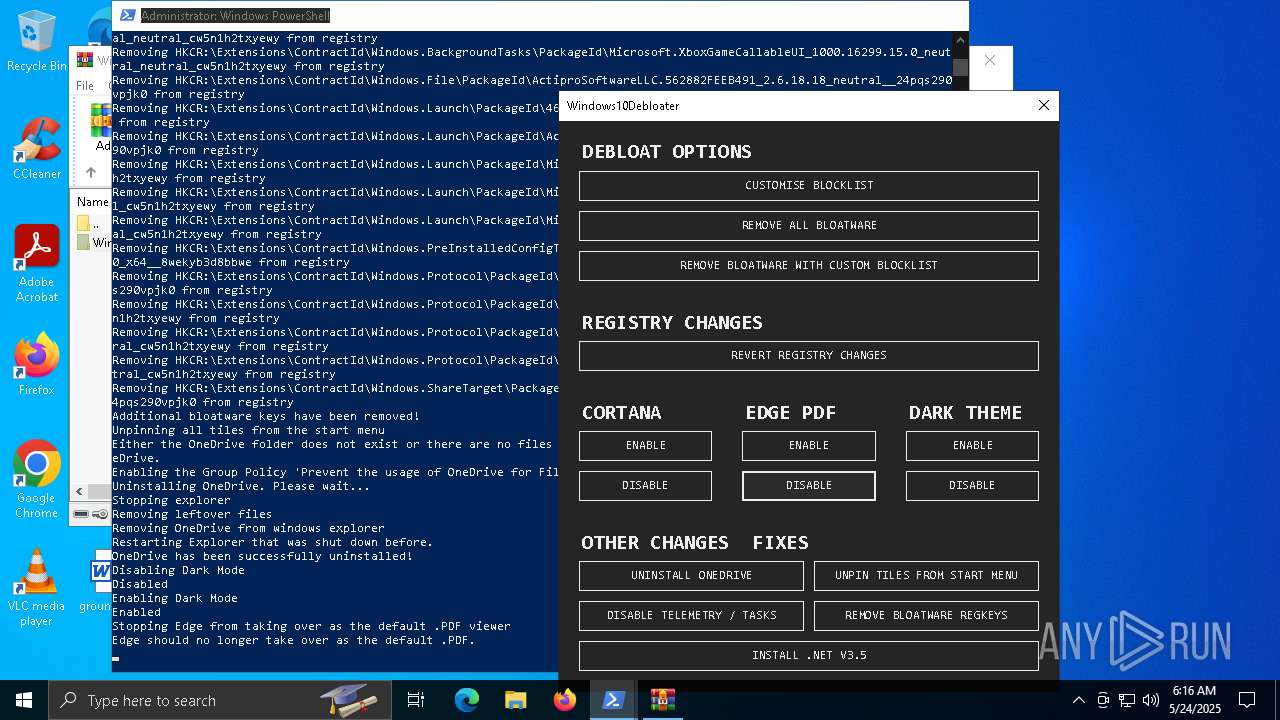
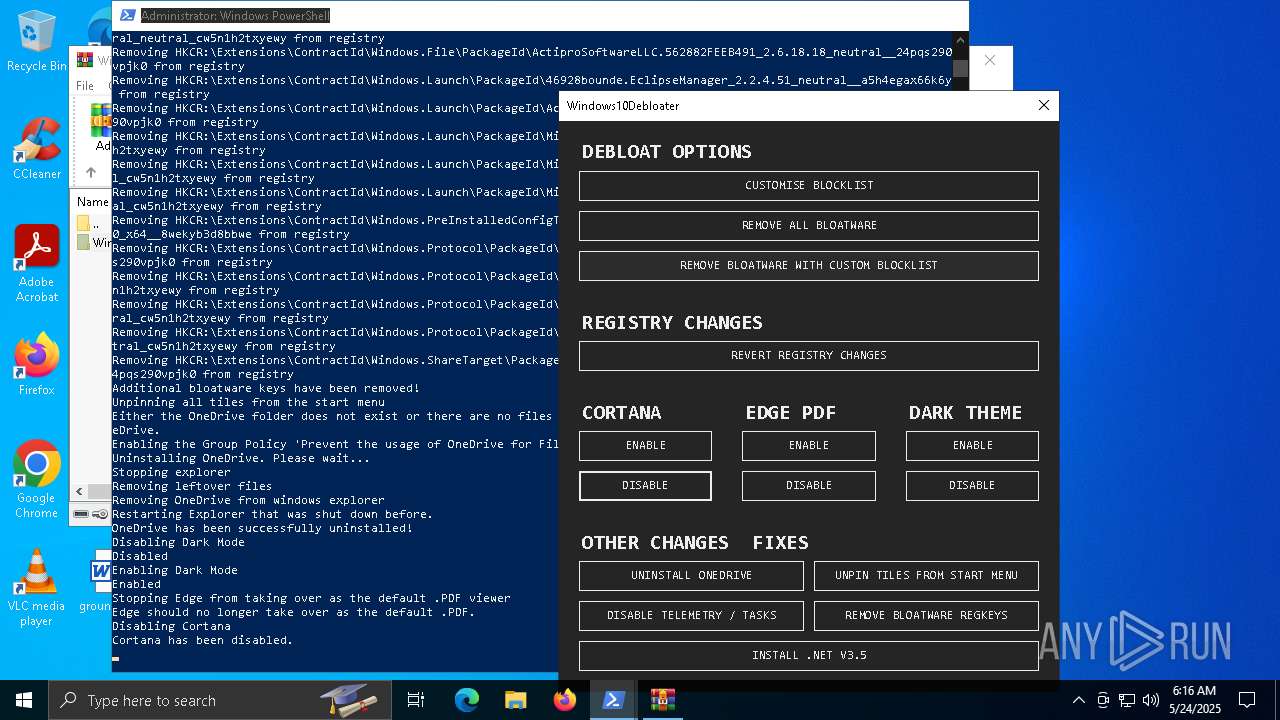
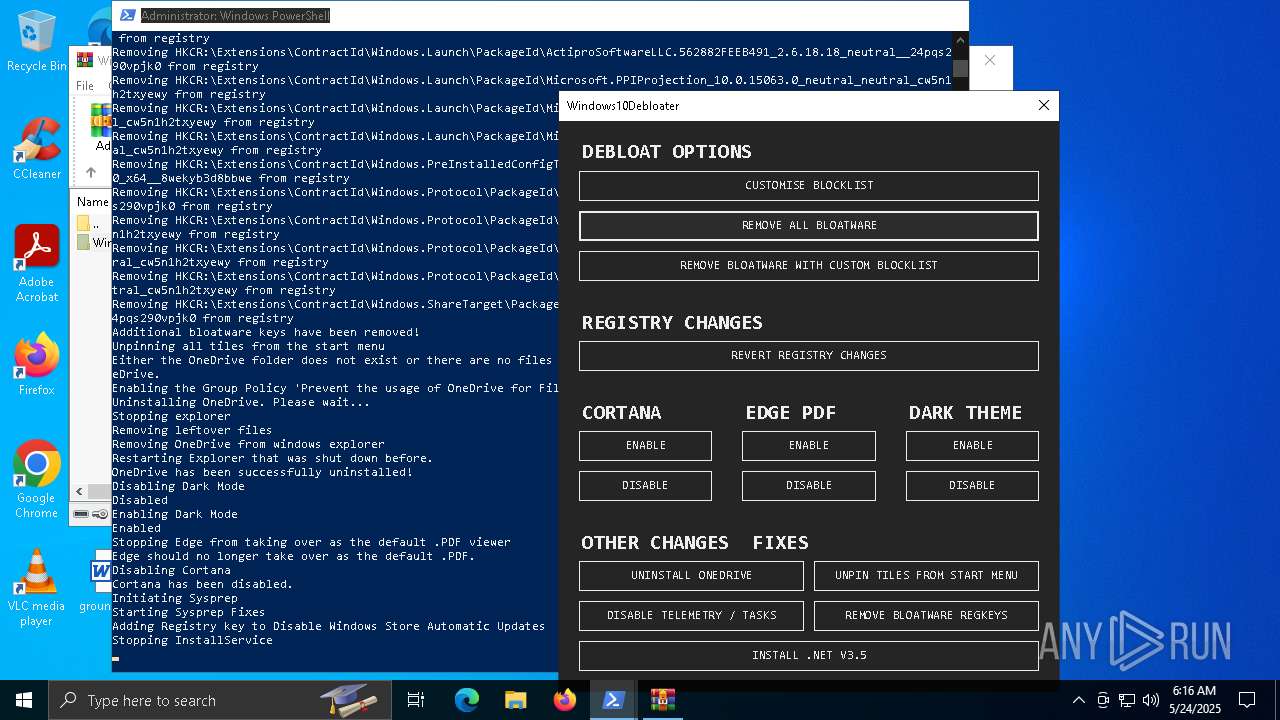
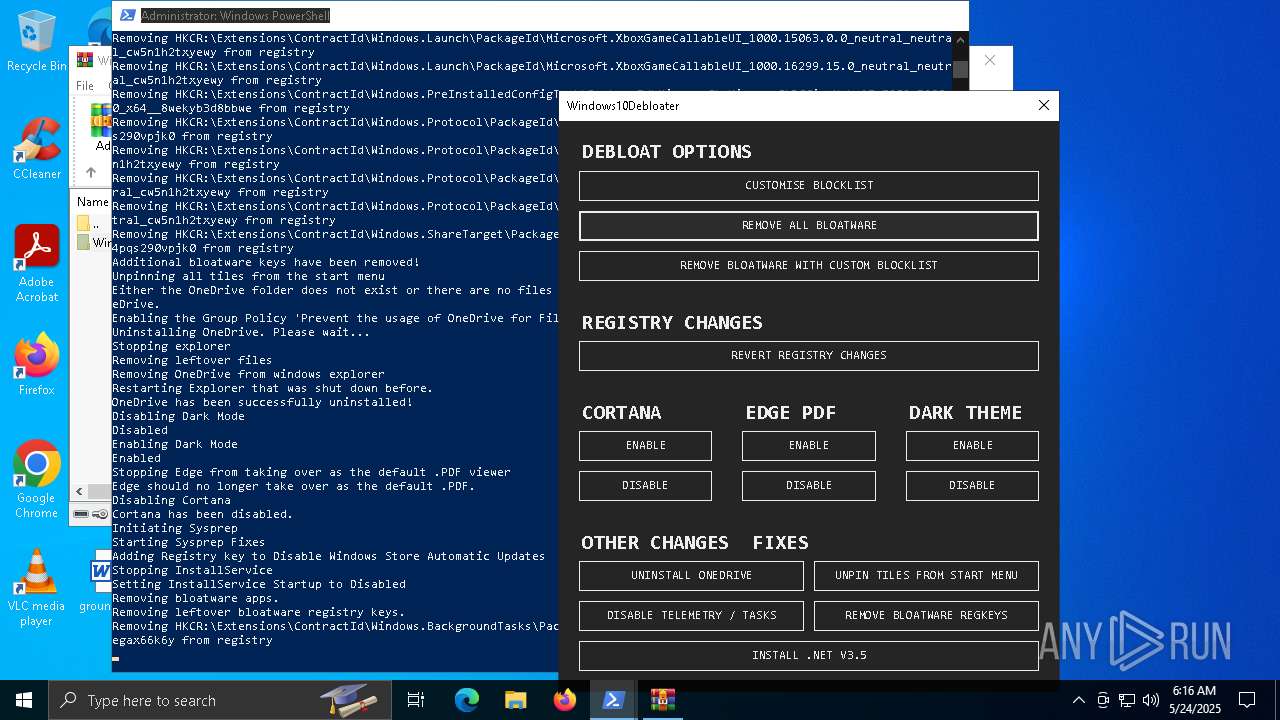
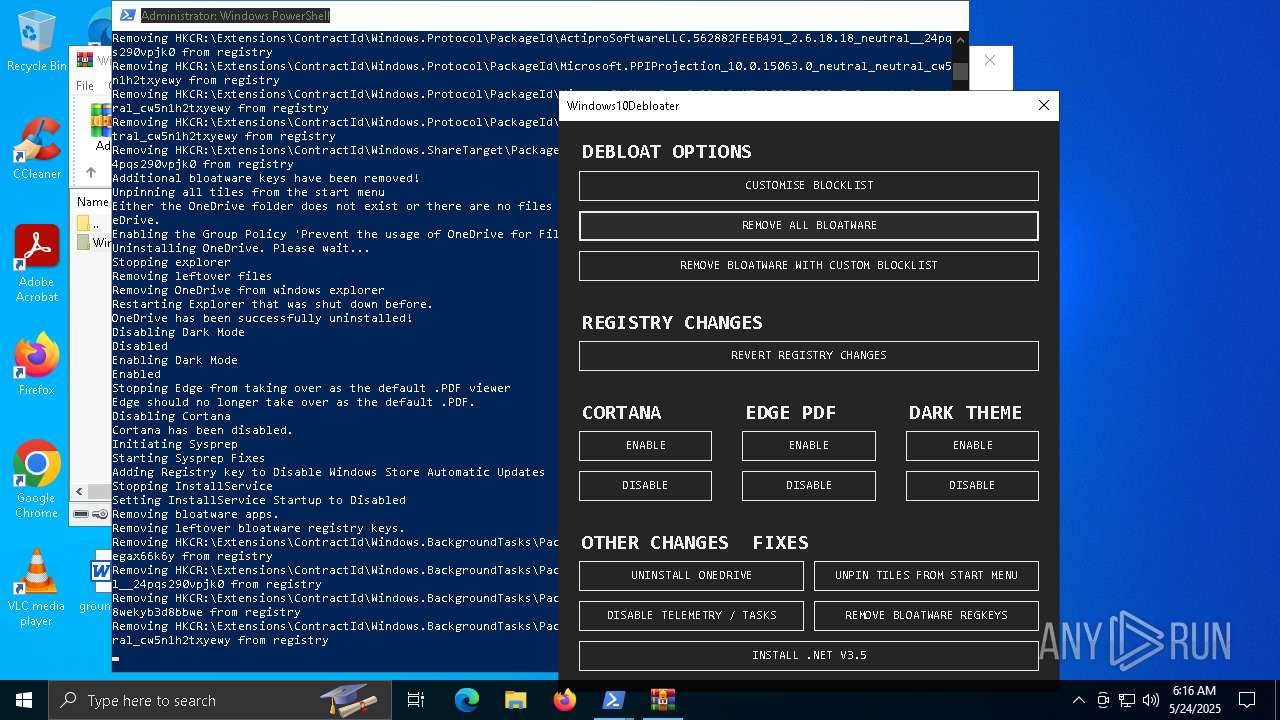
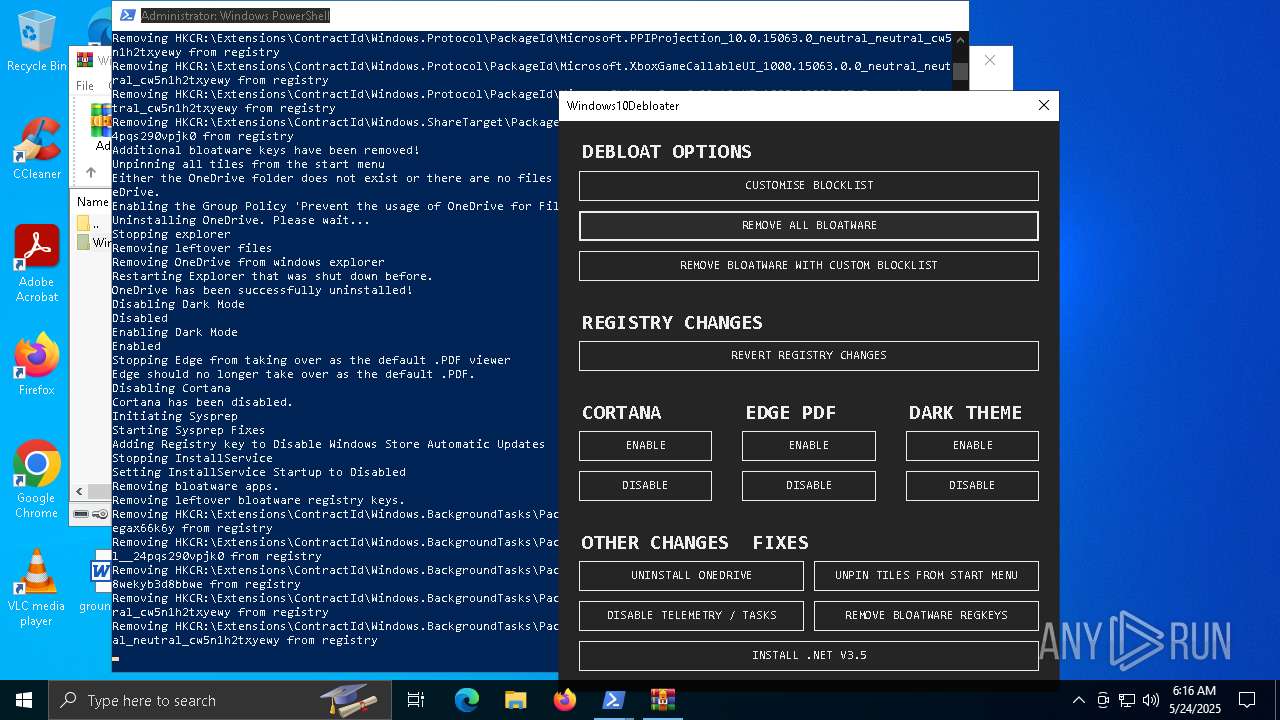
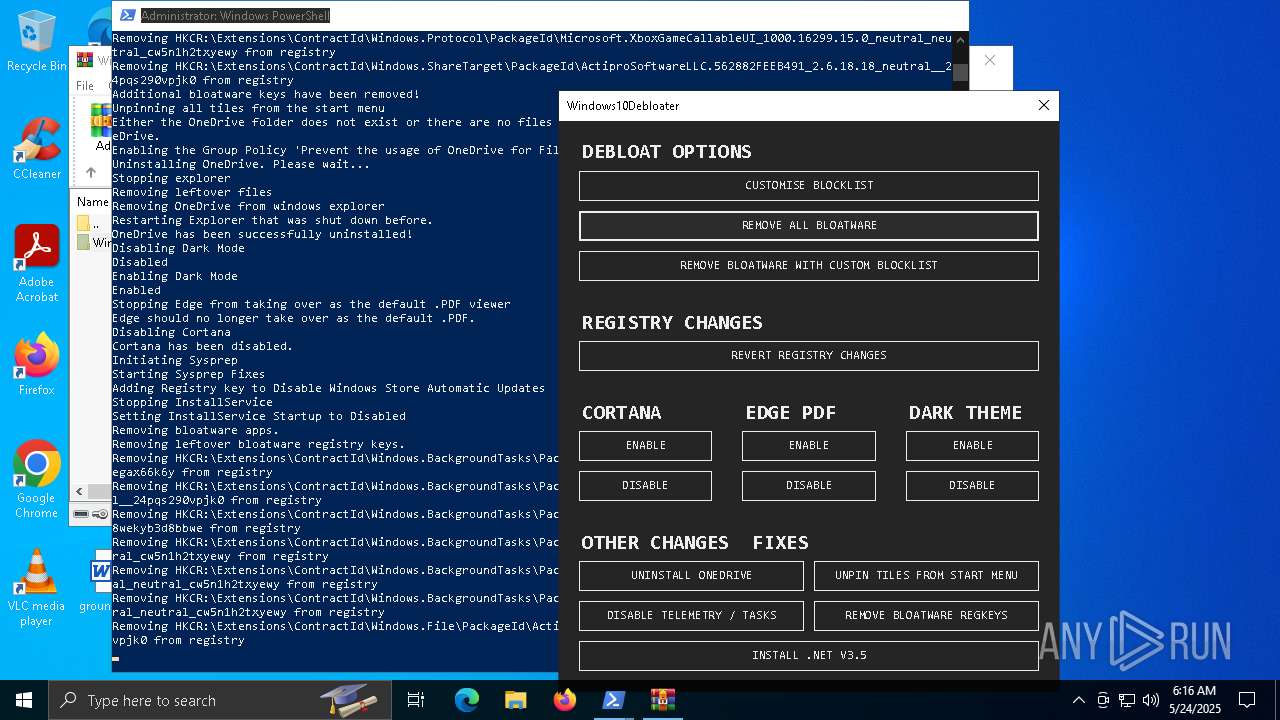
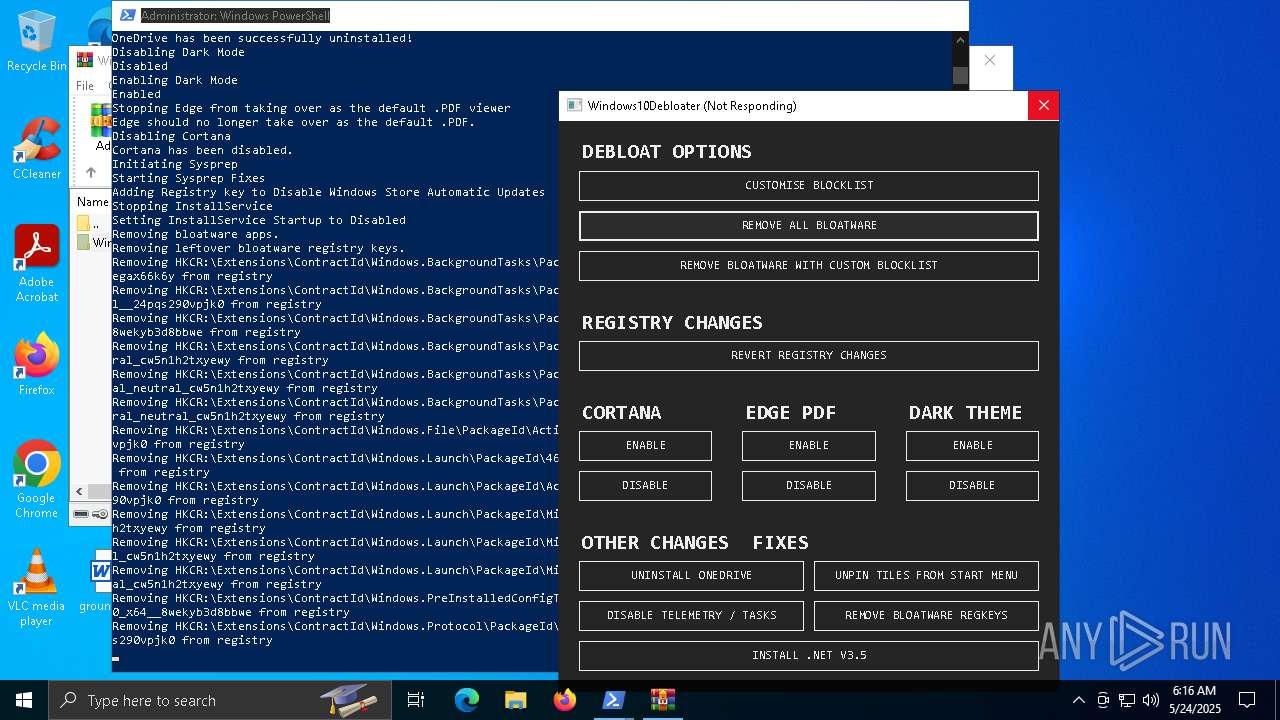
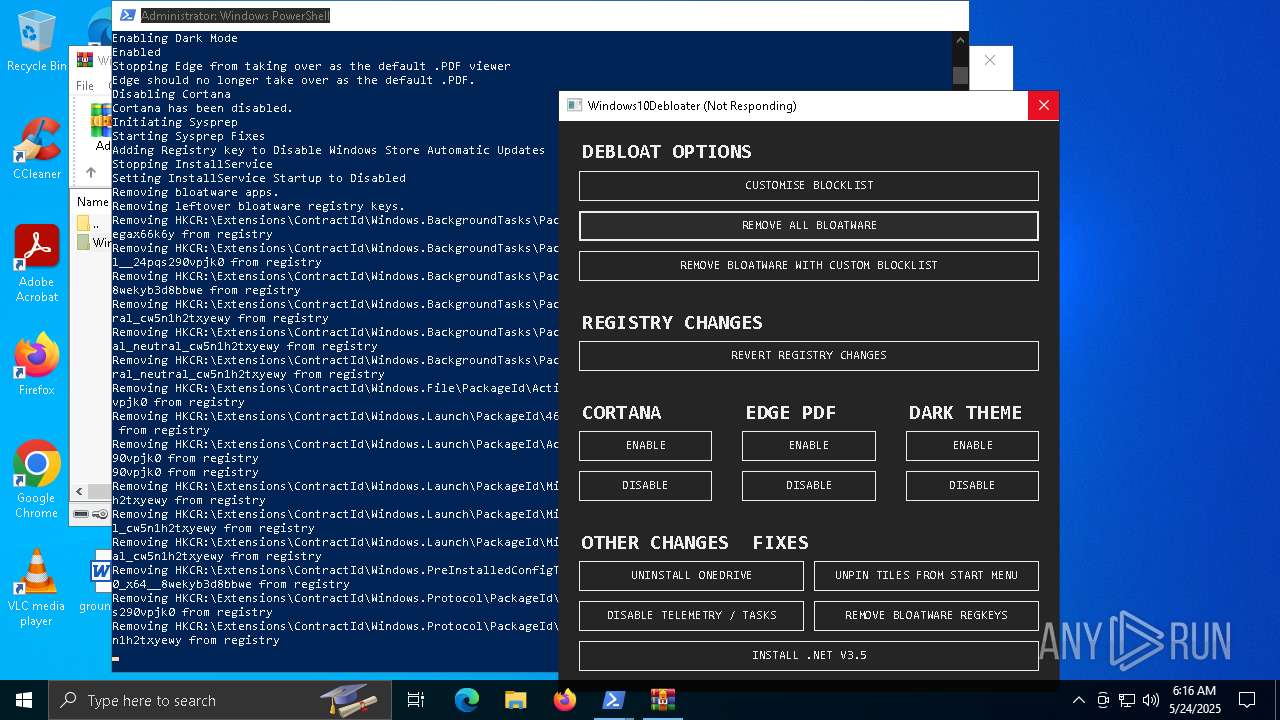
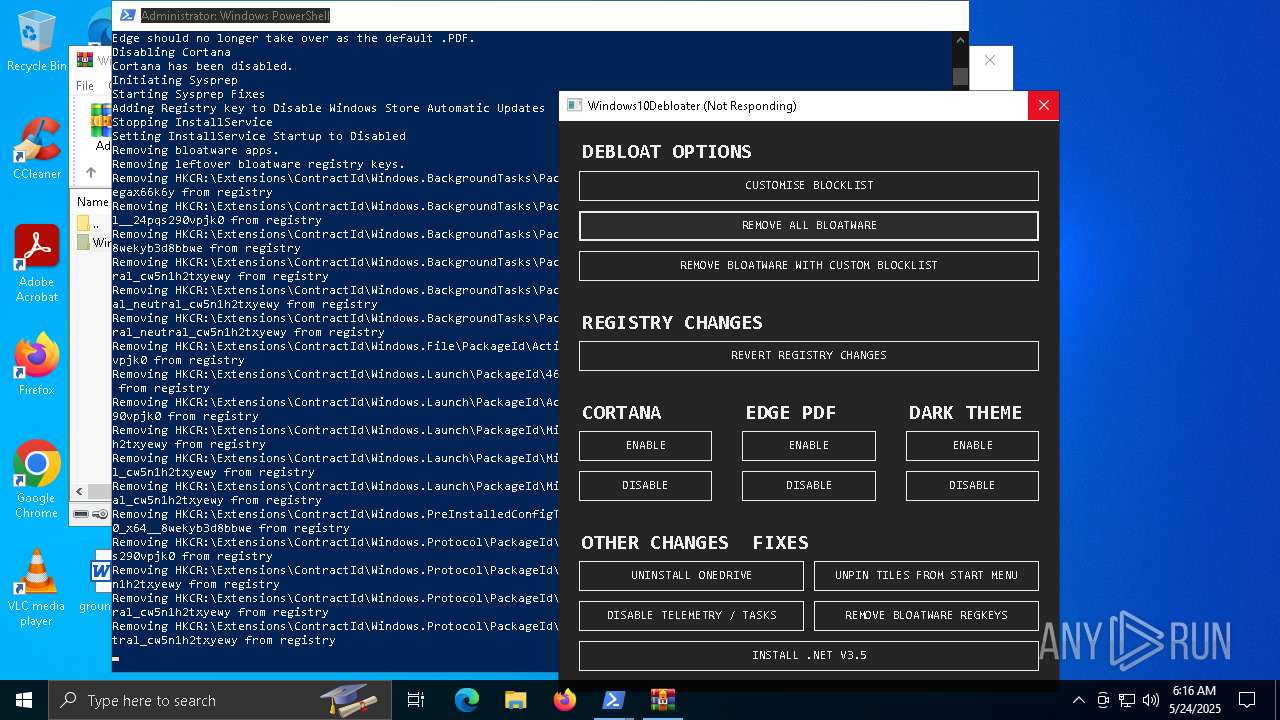
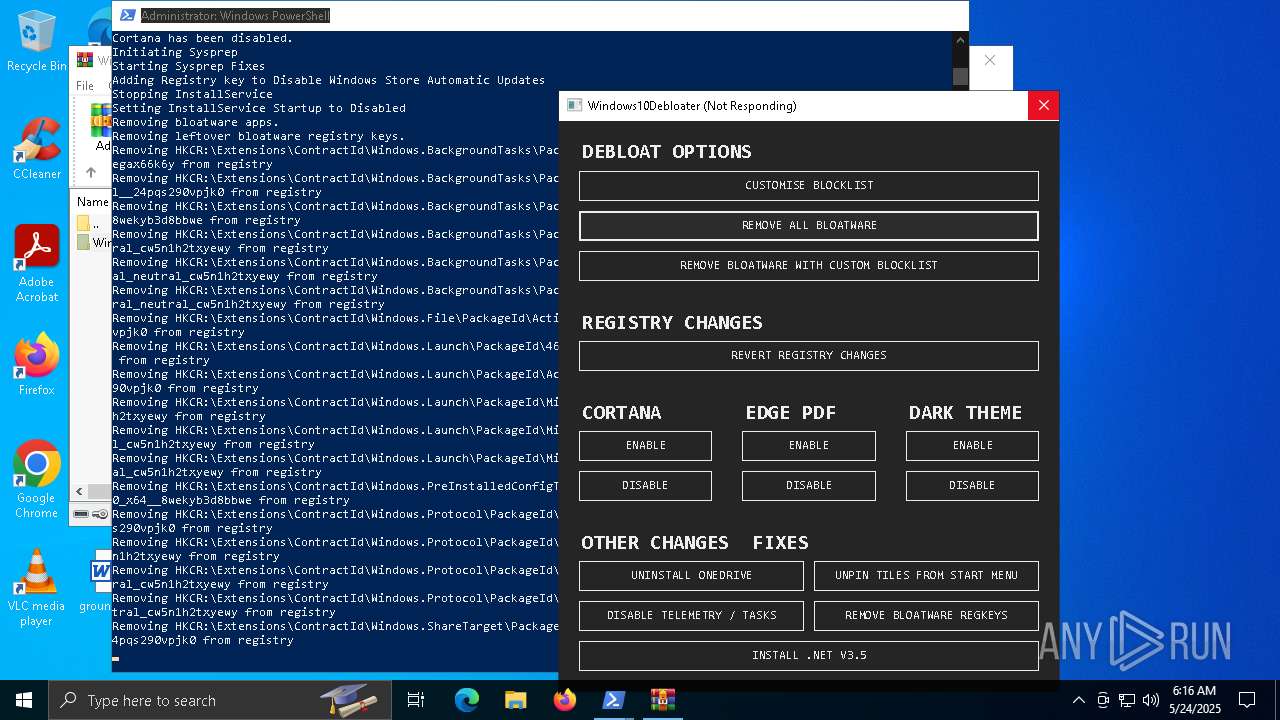
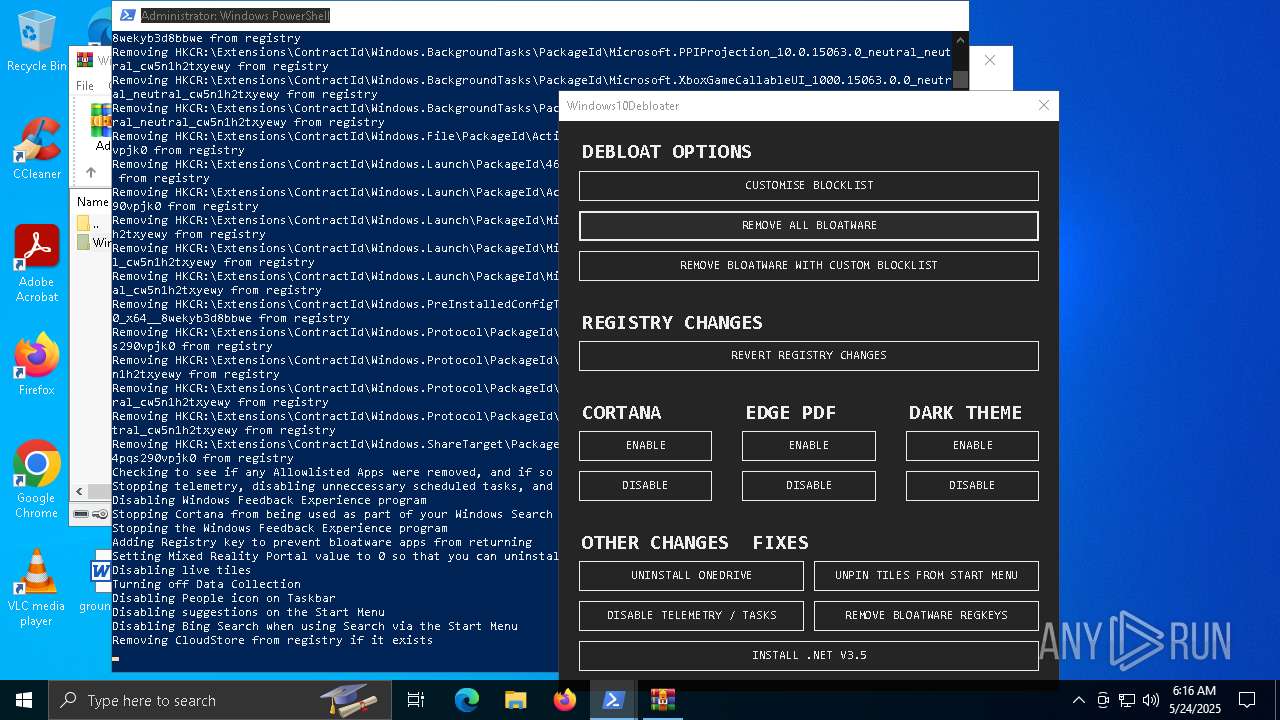
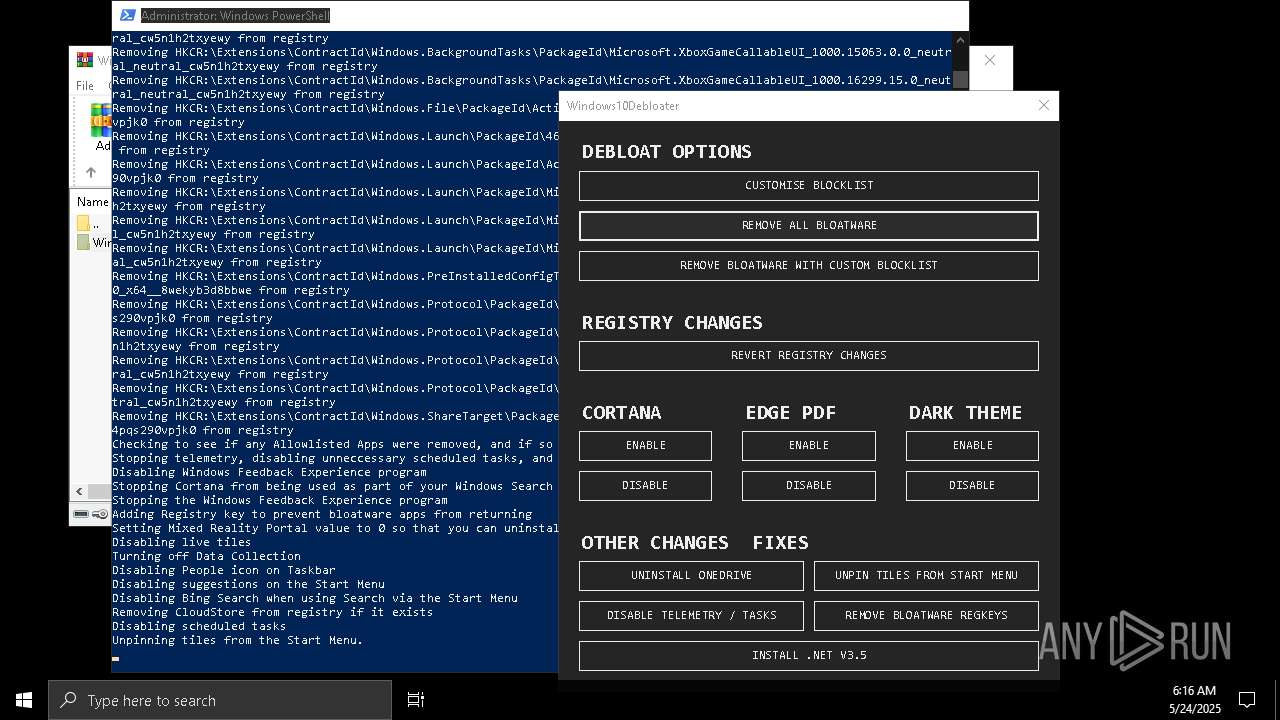
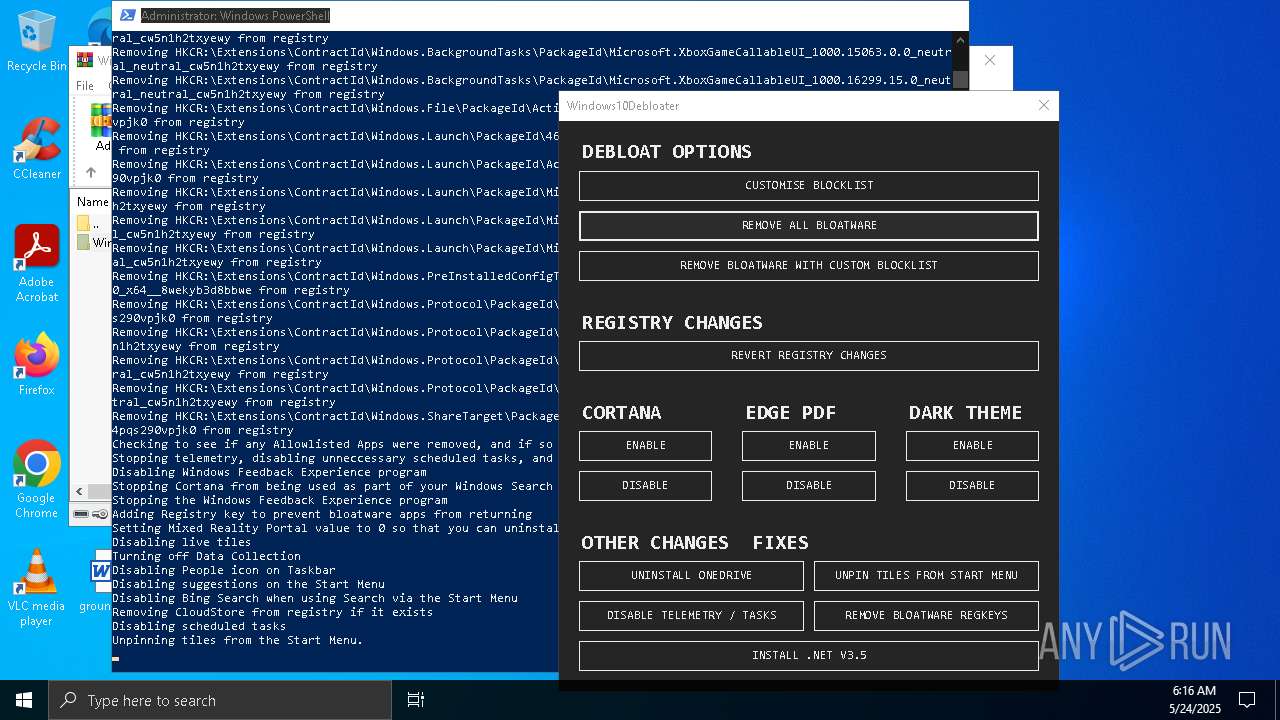
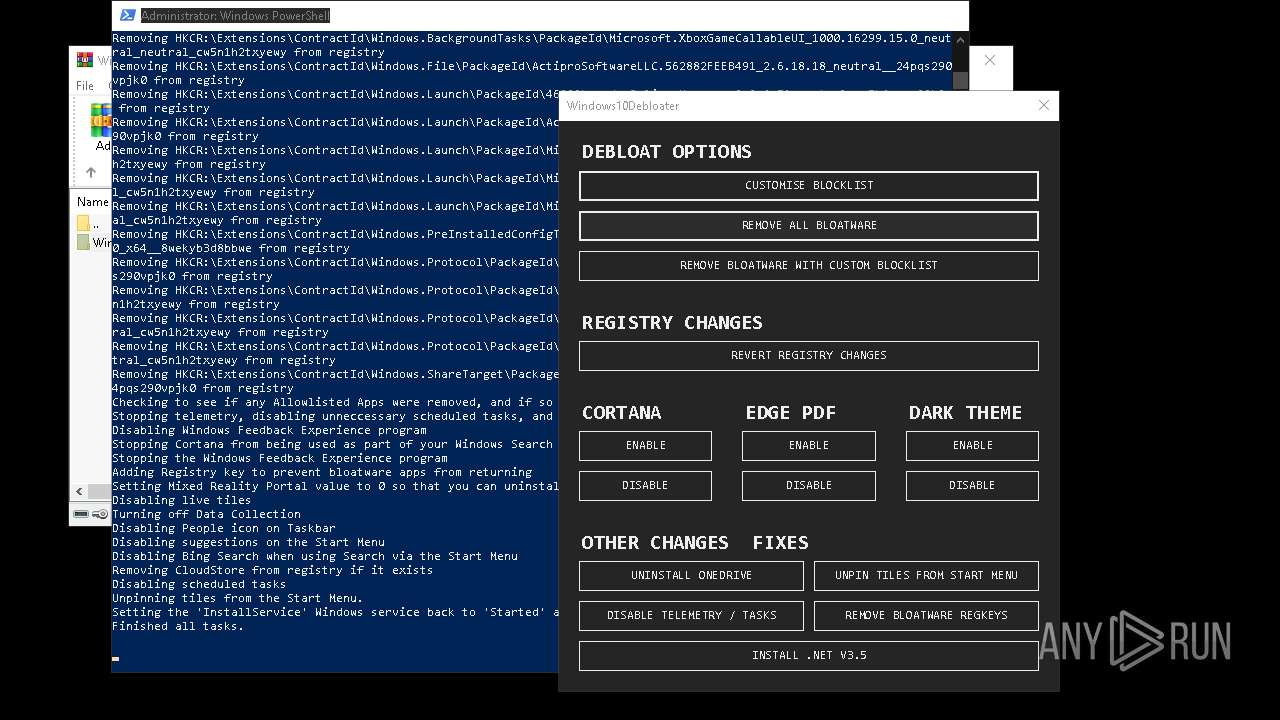
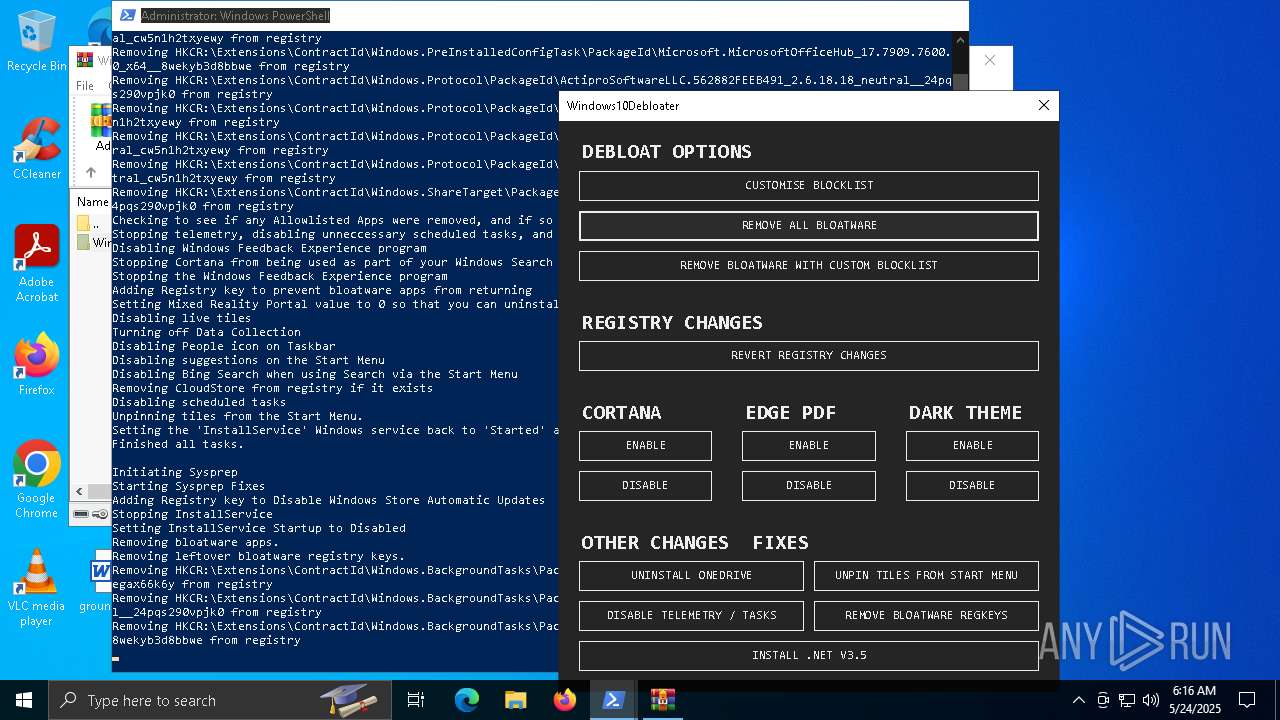
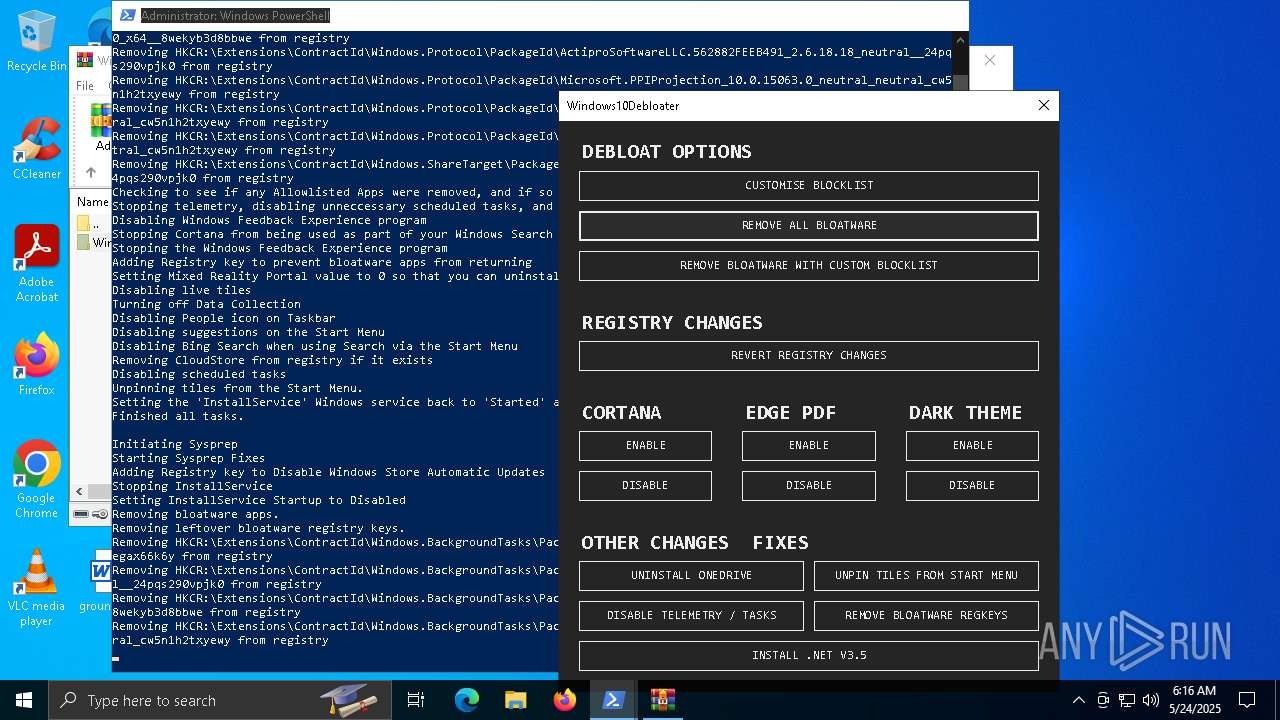
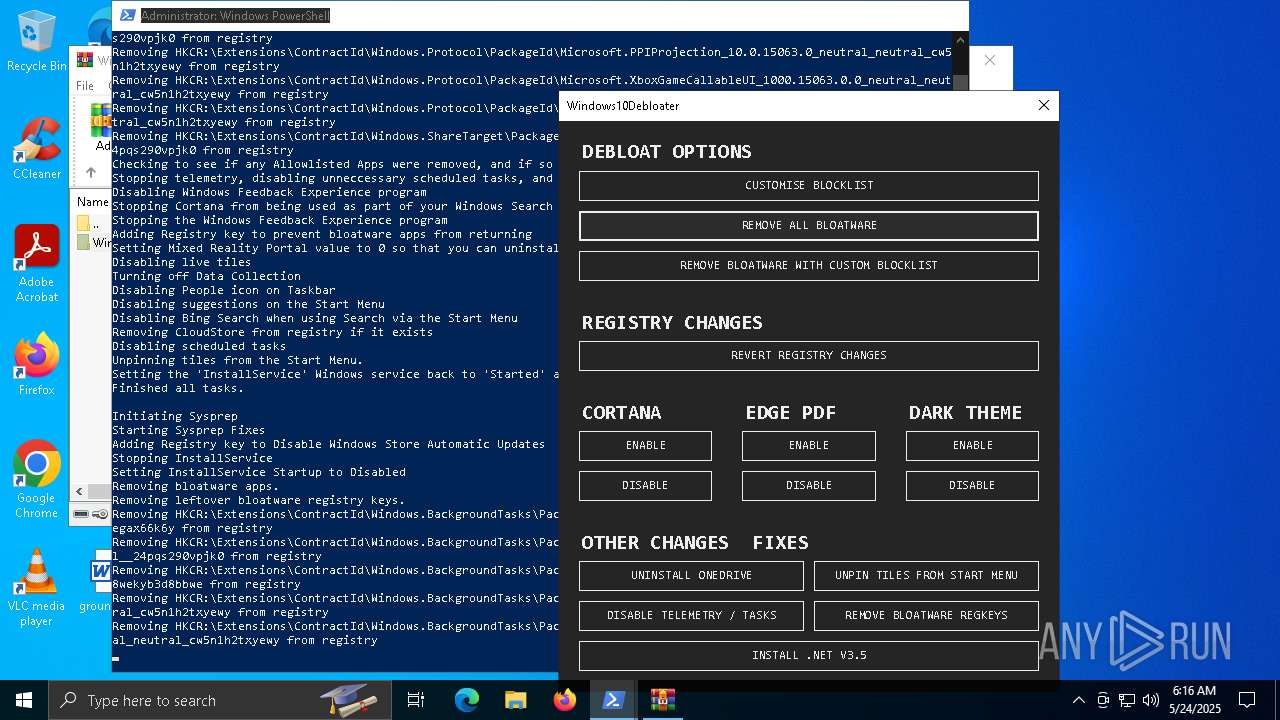
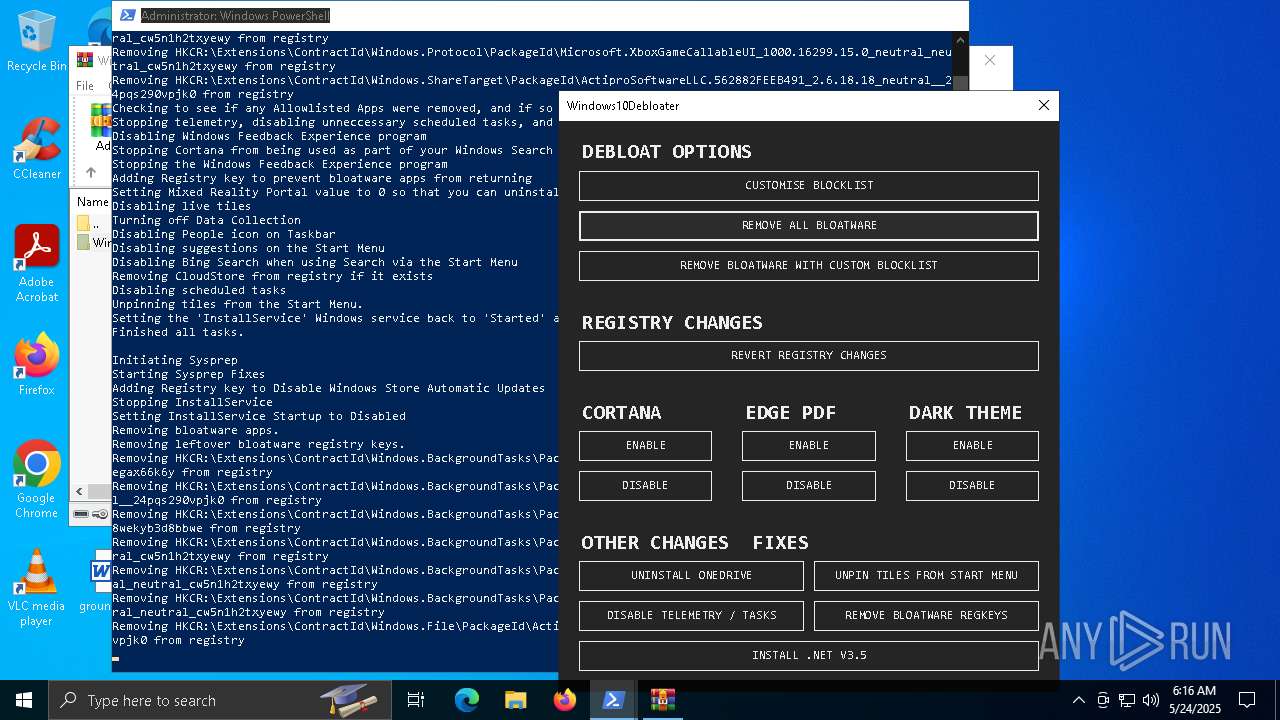
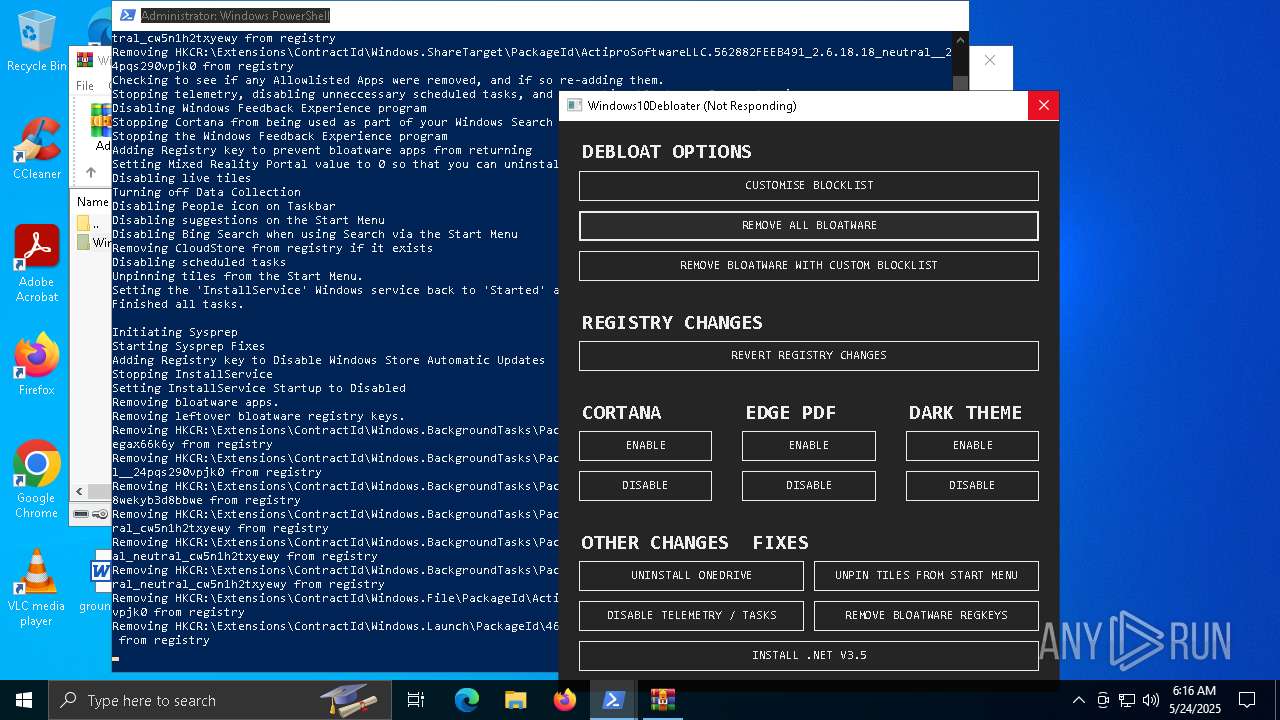
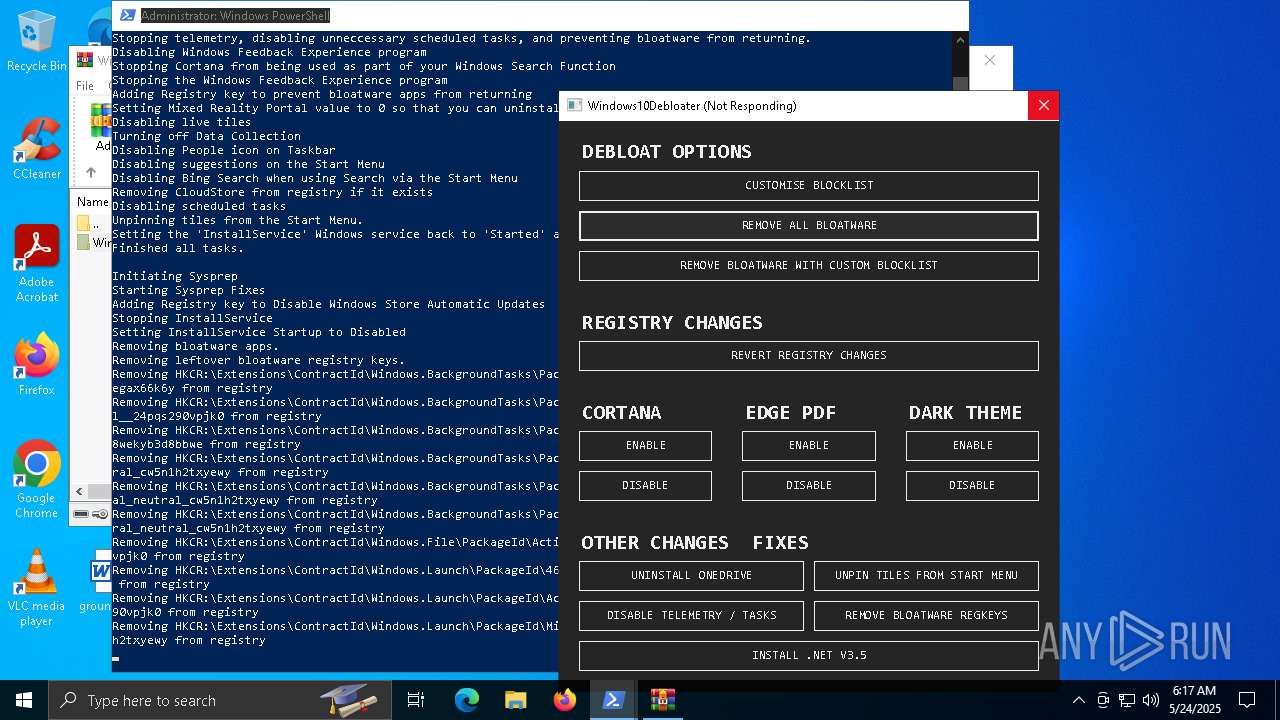
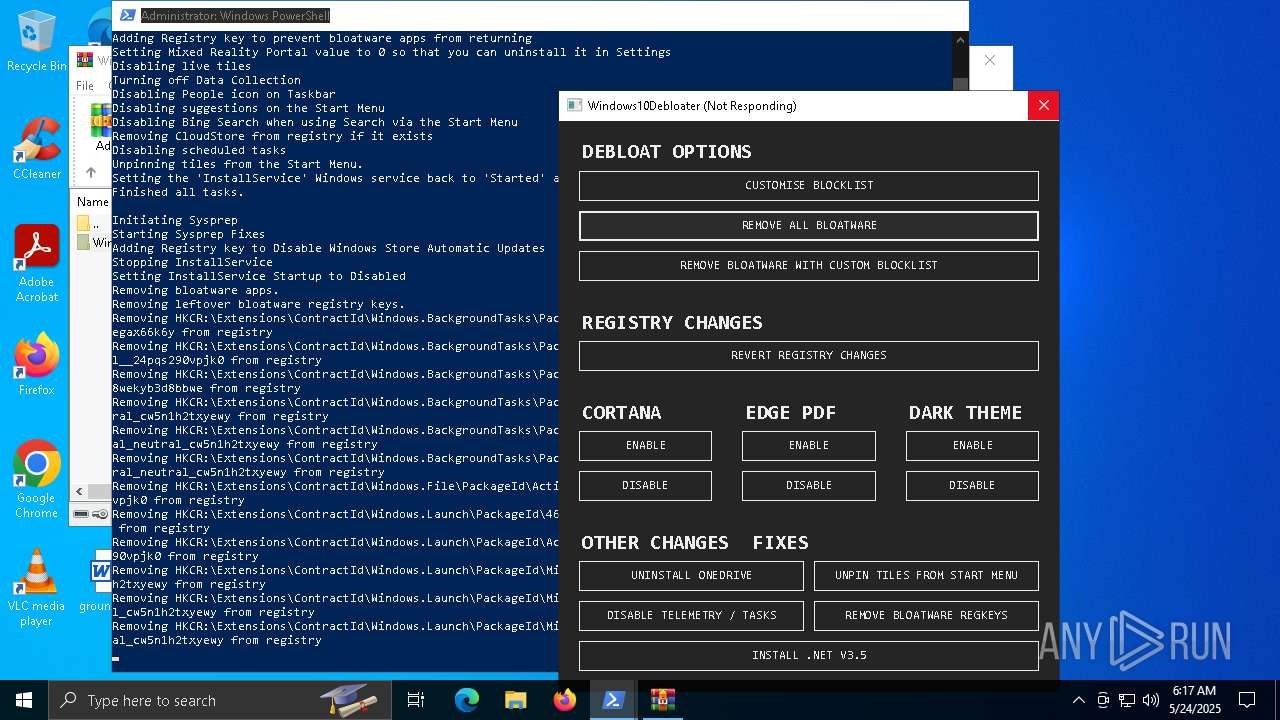
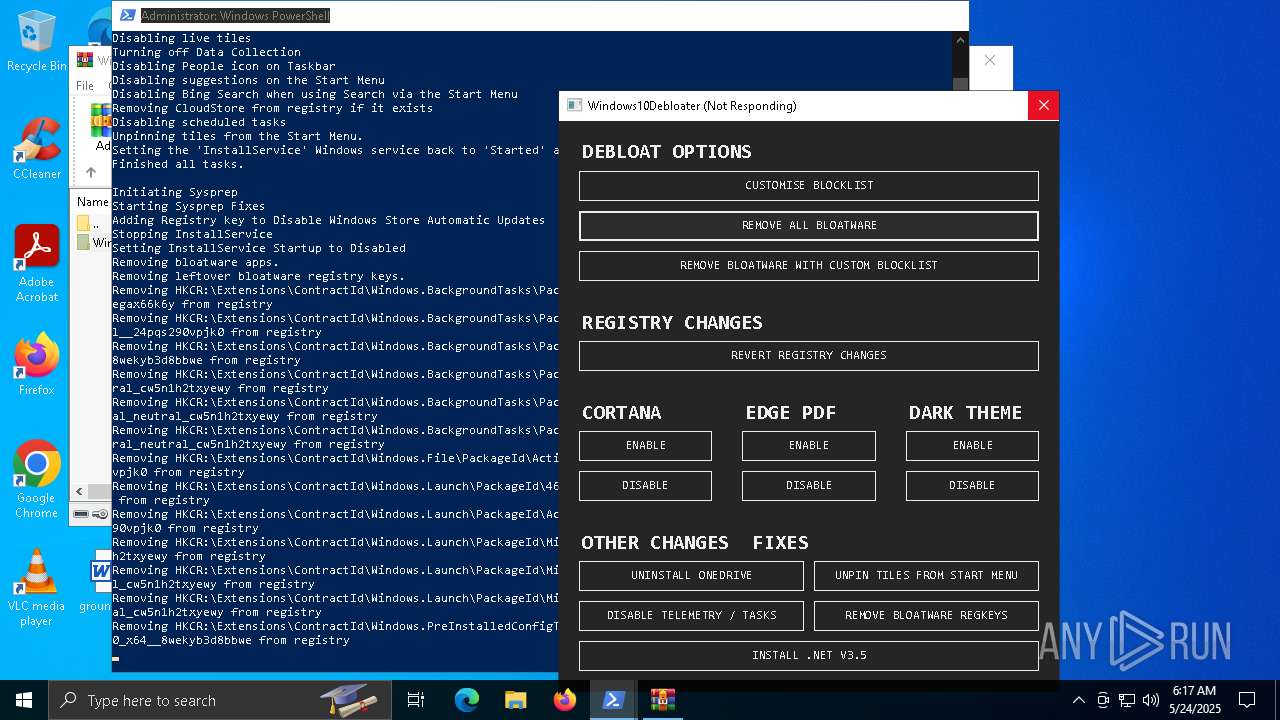
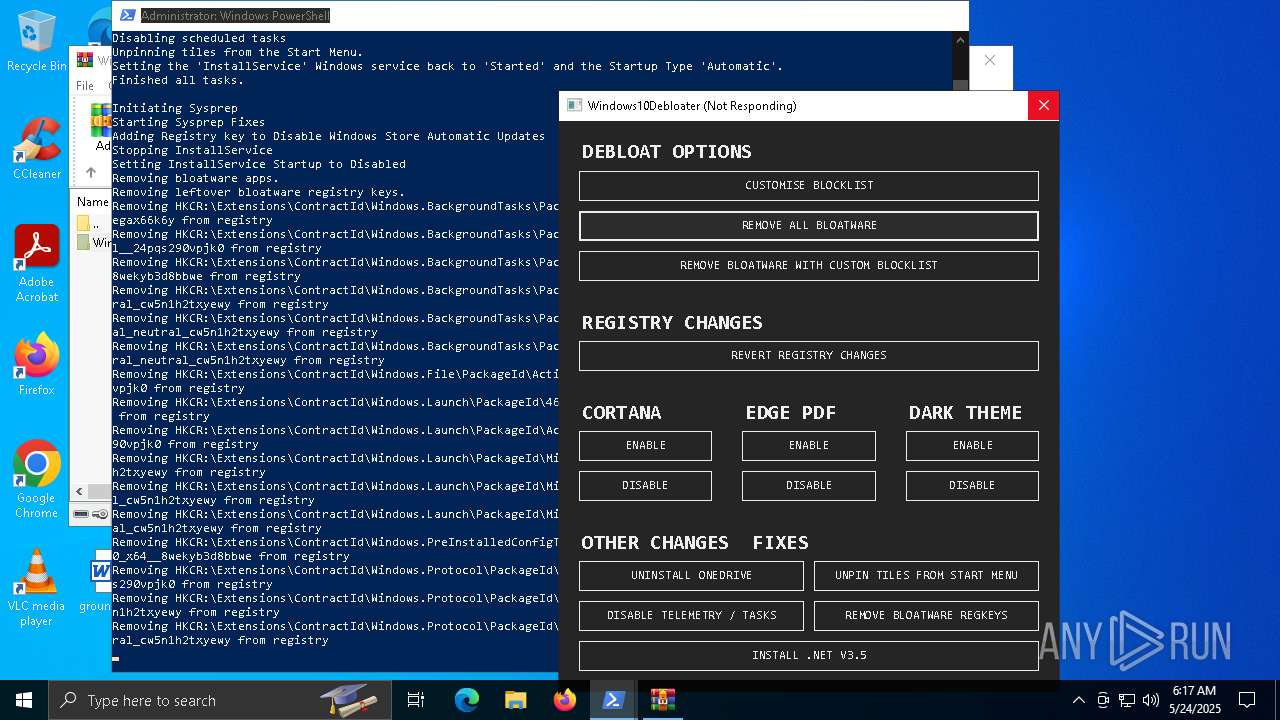
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7480)
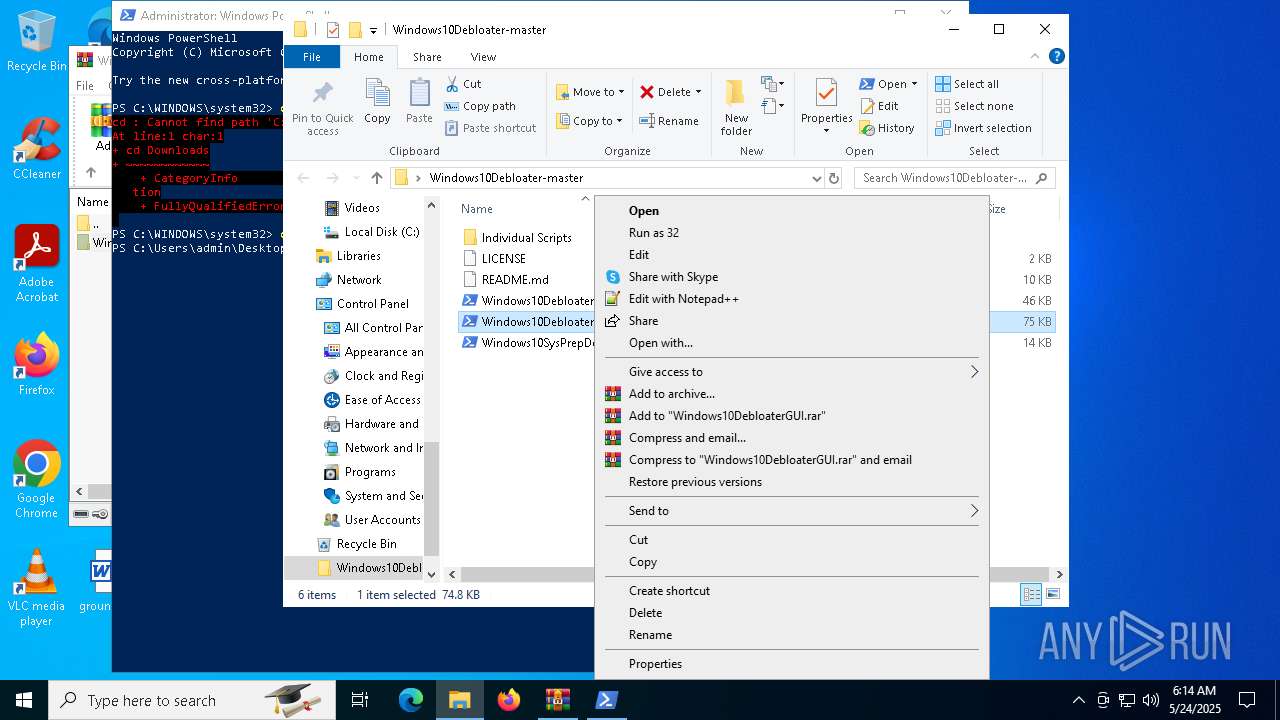
SUSPICIOUS
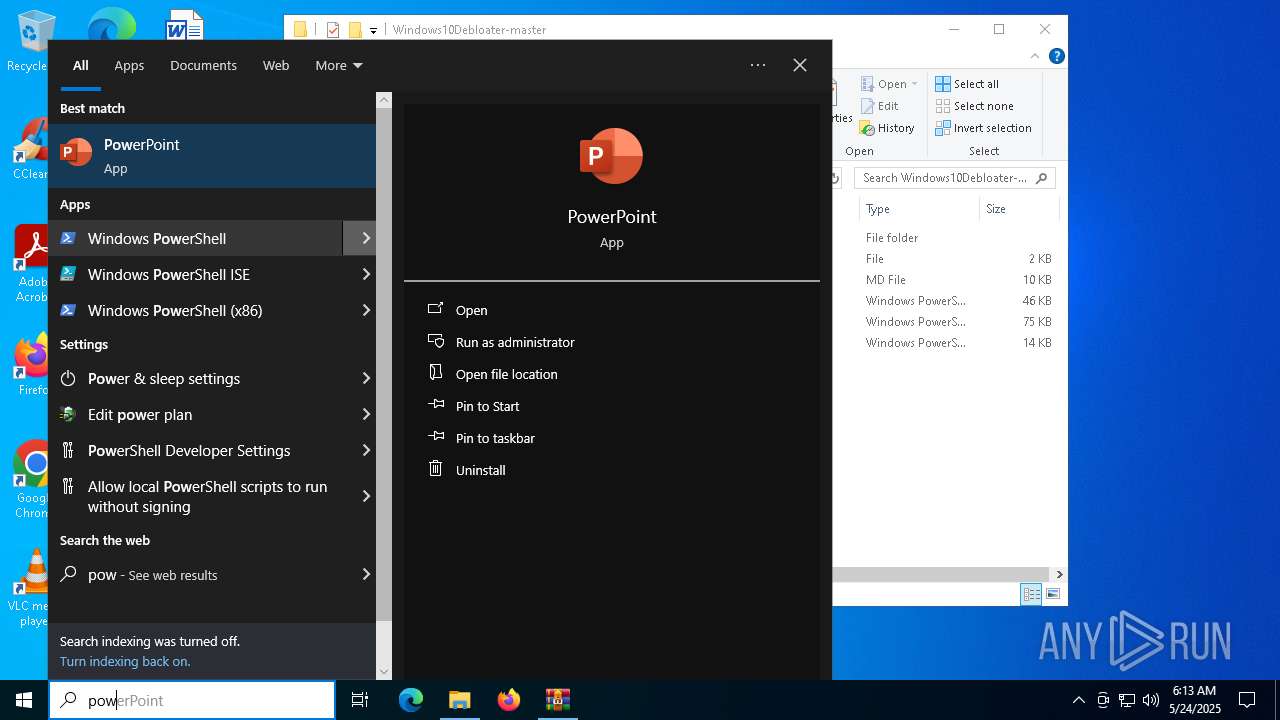
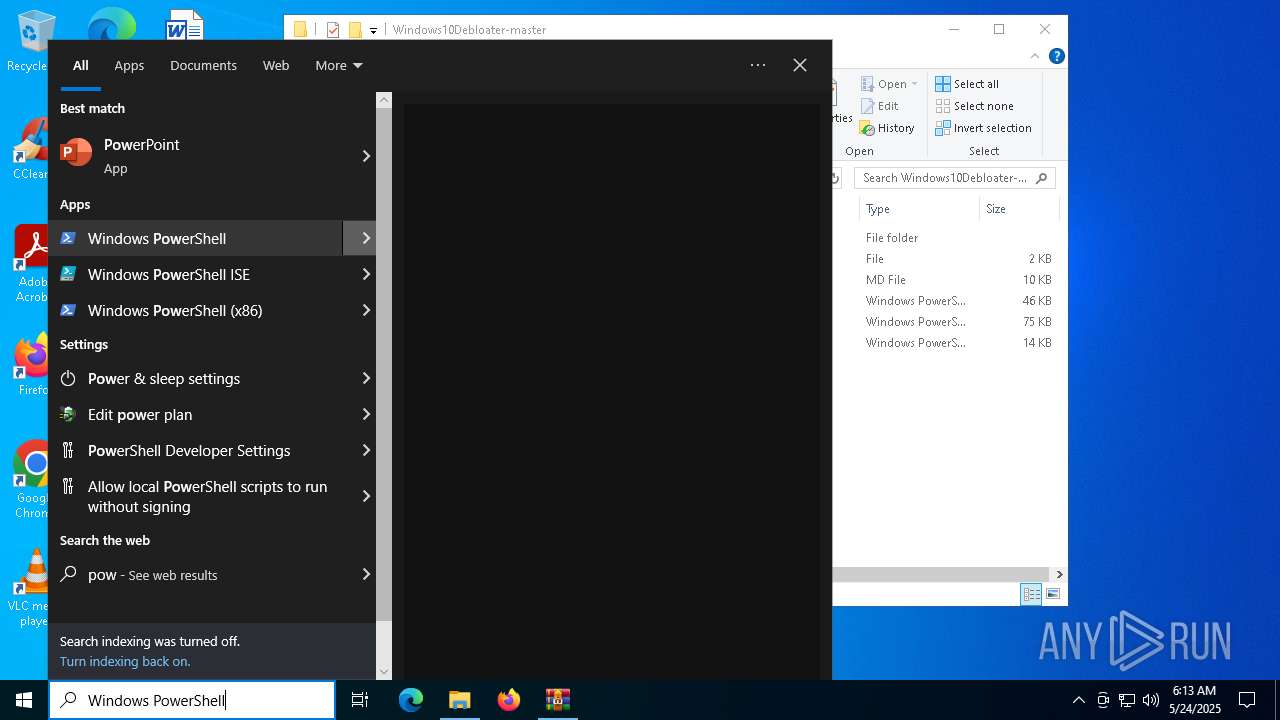
The process executes via Task Scheduler
- powershell.exe (PID: 5244)
- explorer.exe (PID: 7800)
Process drops legitimate windows executable
- powershell.exe (PID: 5244)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 6272)
- DismHost.exe (PID: 2652)
- DismHost.exe (PID: 736)
- DismHost.exe (PID: 6288)
Executable content was dropped or overwritten
- powershell.exe (PID: 5244)
Executes as Windows Service
- VSSVC.exe (PID: 6720)
Application launched itself
- OneDriveSetup.exe (PID: 4040)
Uses TASKKILL.EXE to kill process
- powershell.exe (PID: 5244)
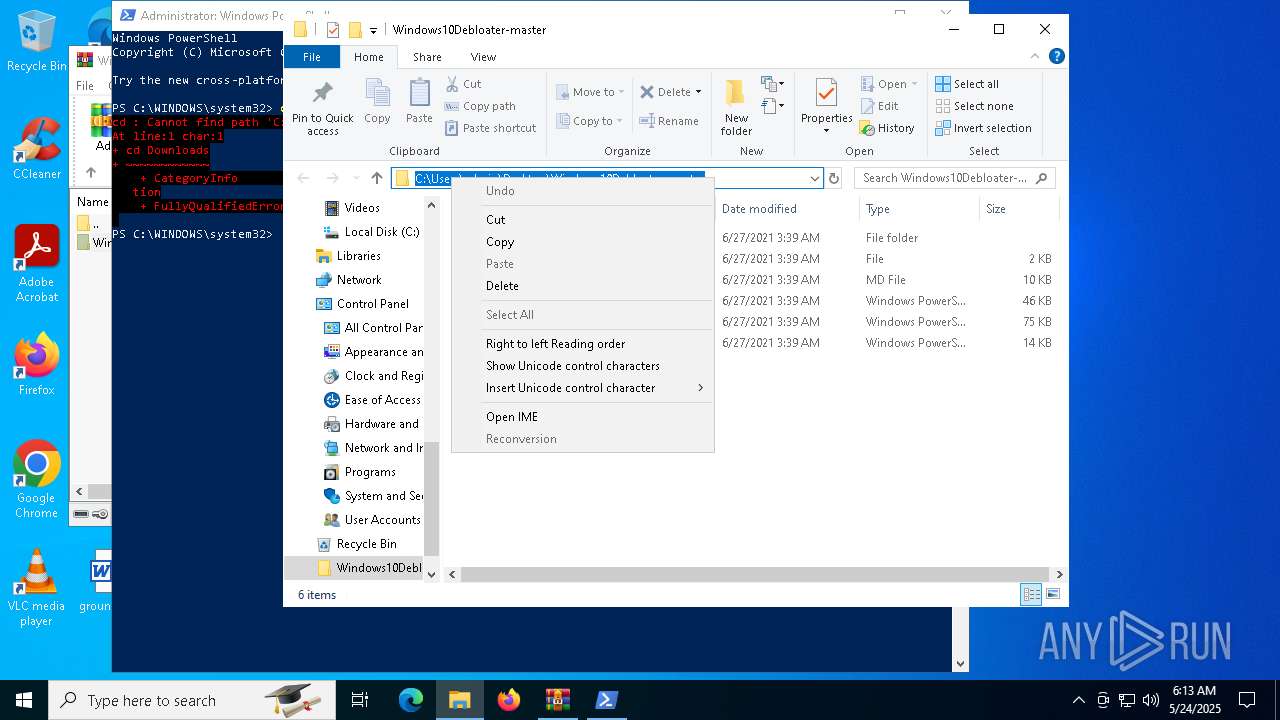
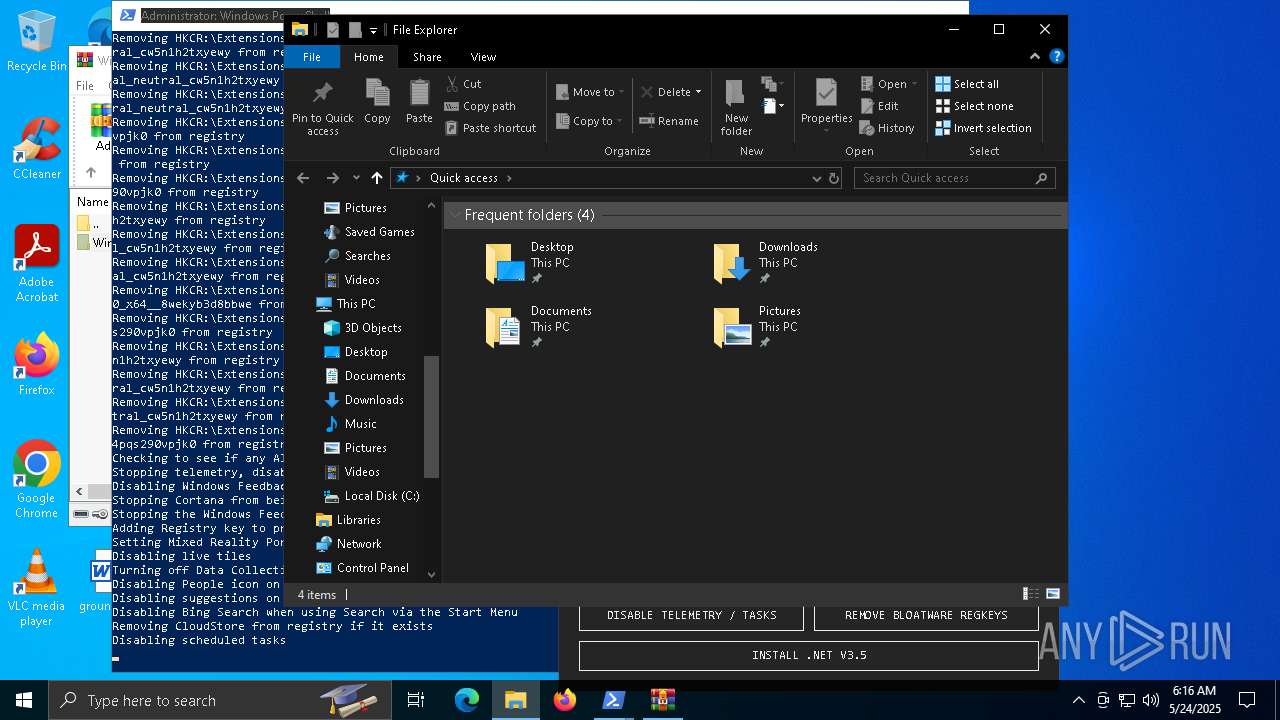
The process deletes folder without confirmation
- explorer.exe (PID: 7800)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 7800)
Uses REG/REGEDIT.EXE to modify registry
- powershell.exe (PID: 5244)
INFO
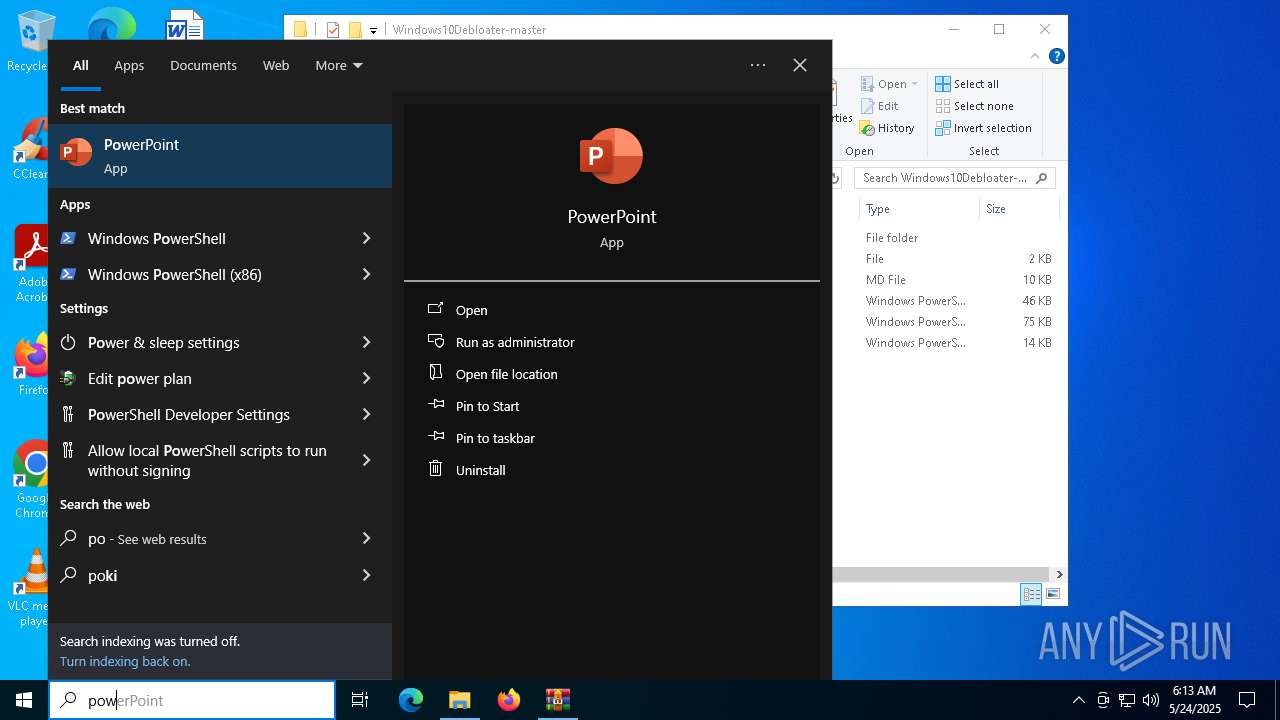
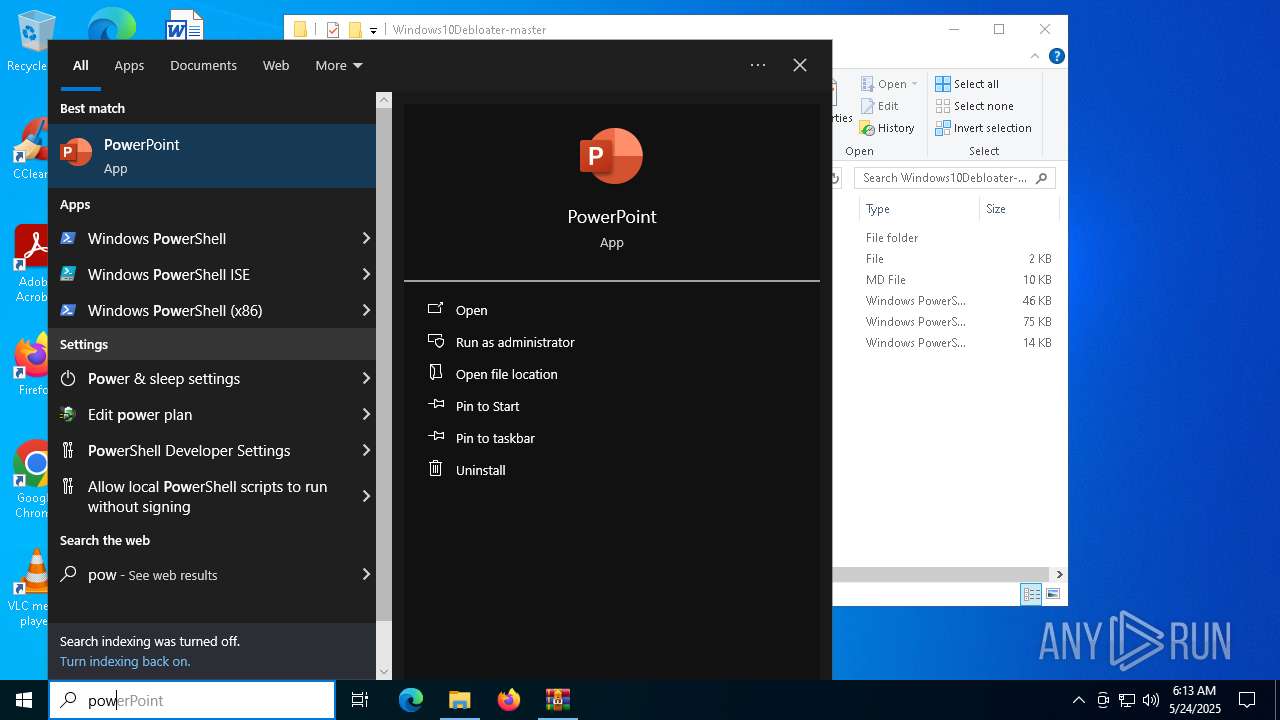
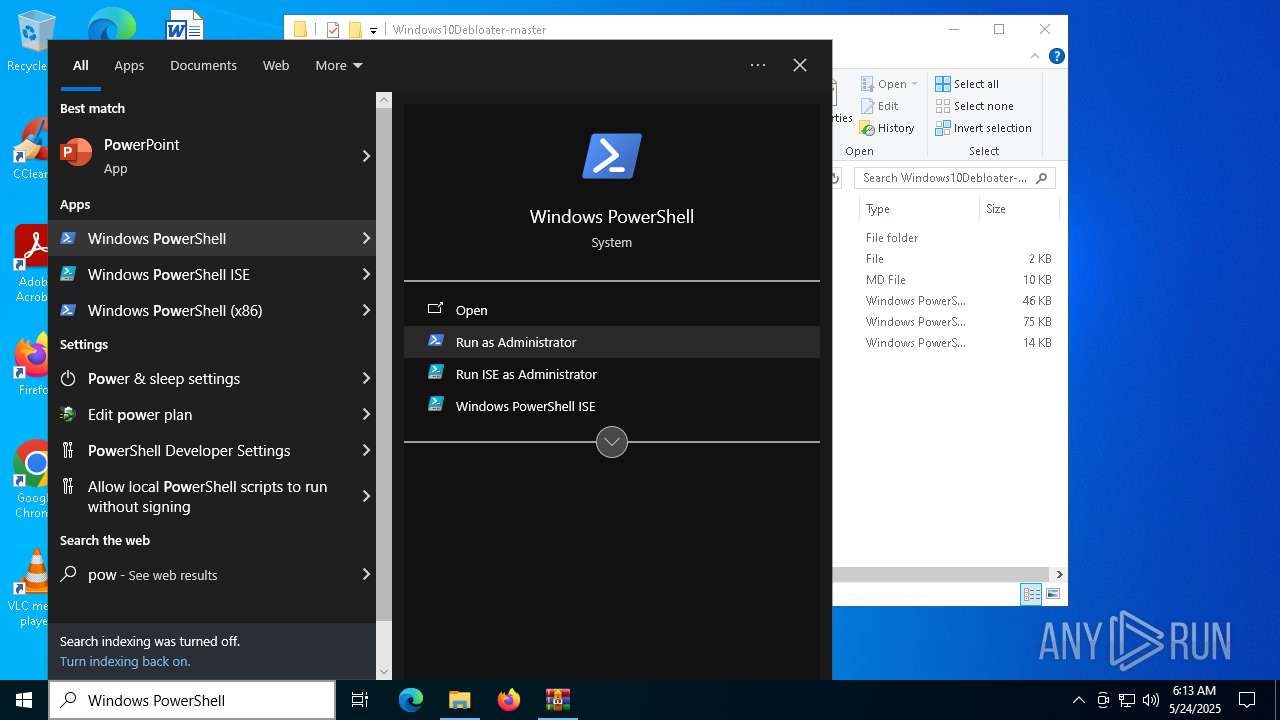
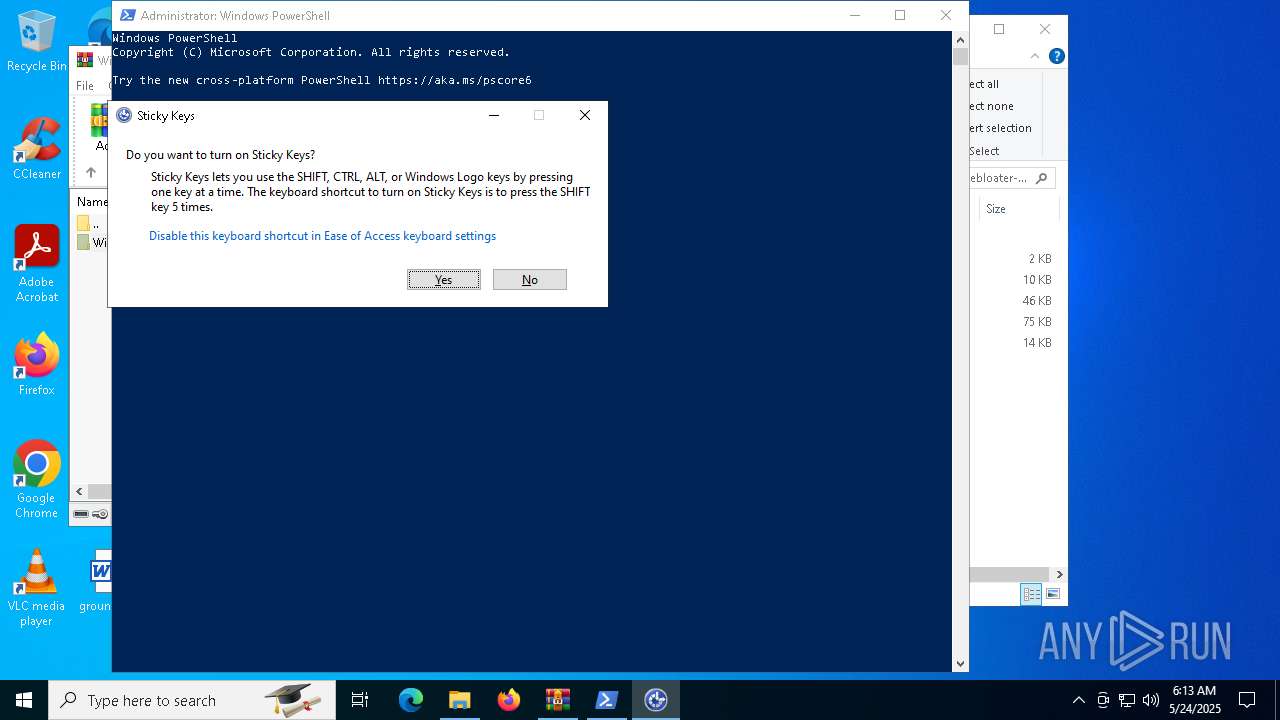
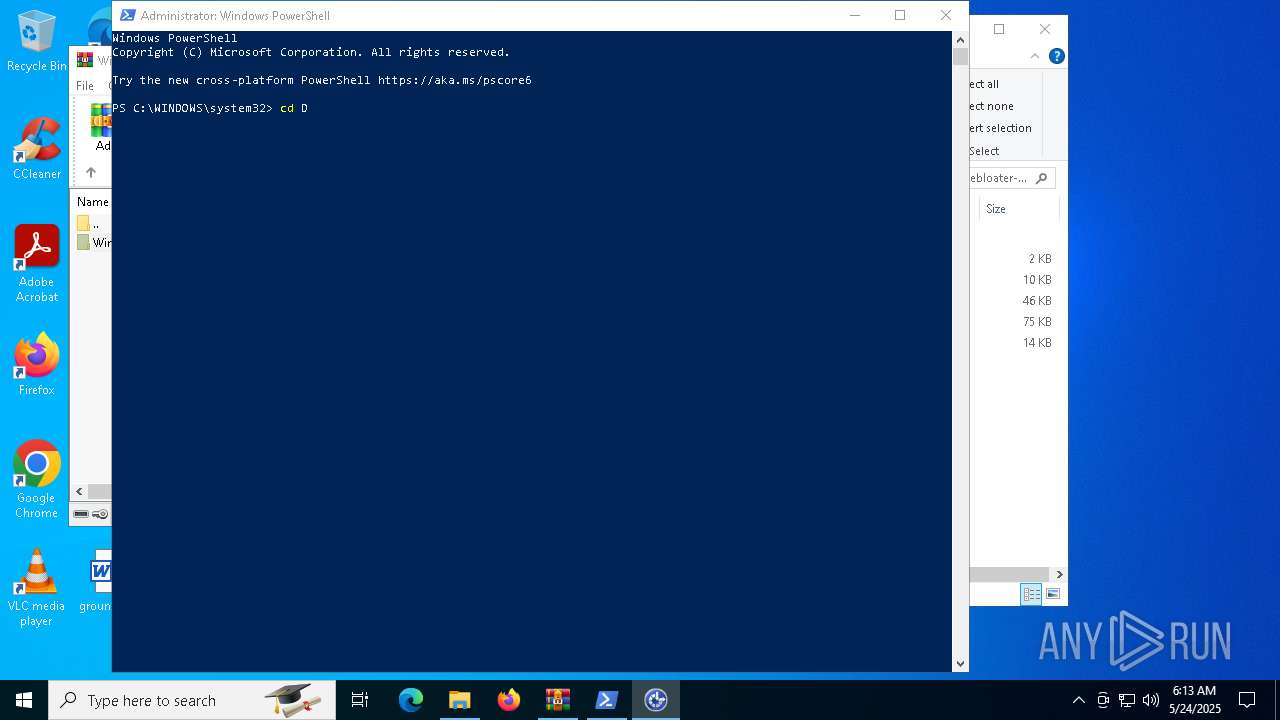
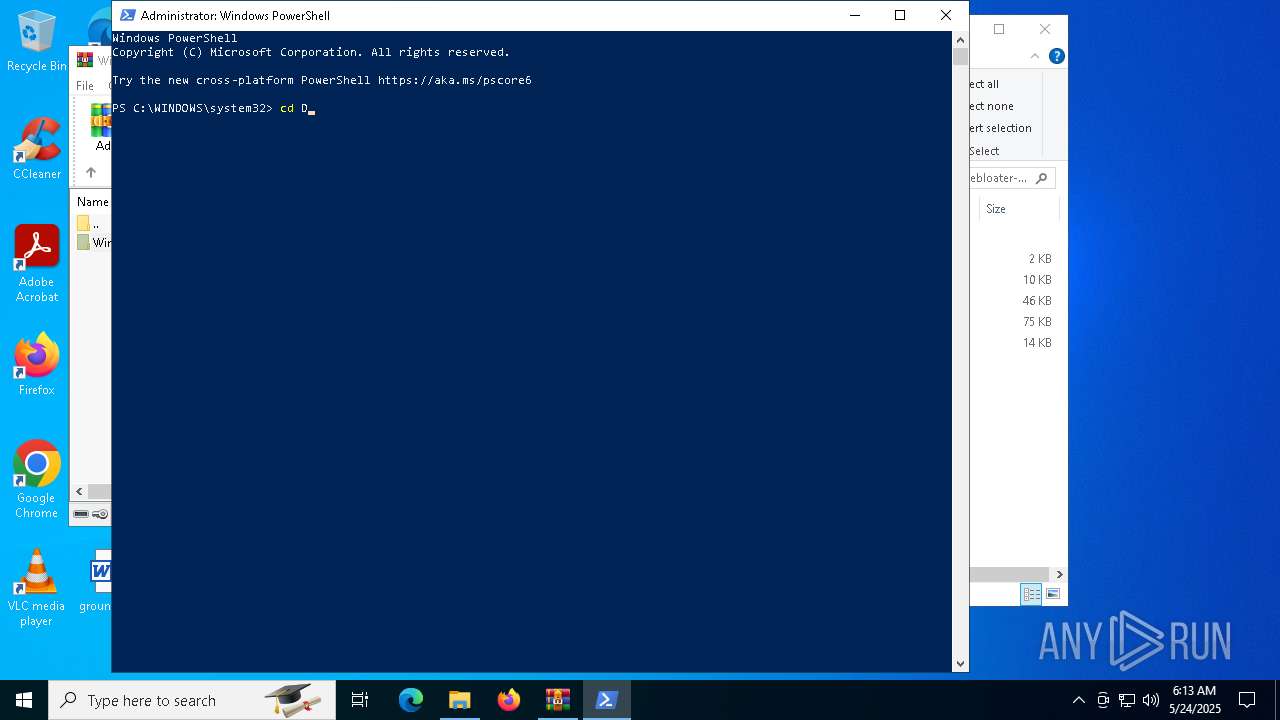
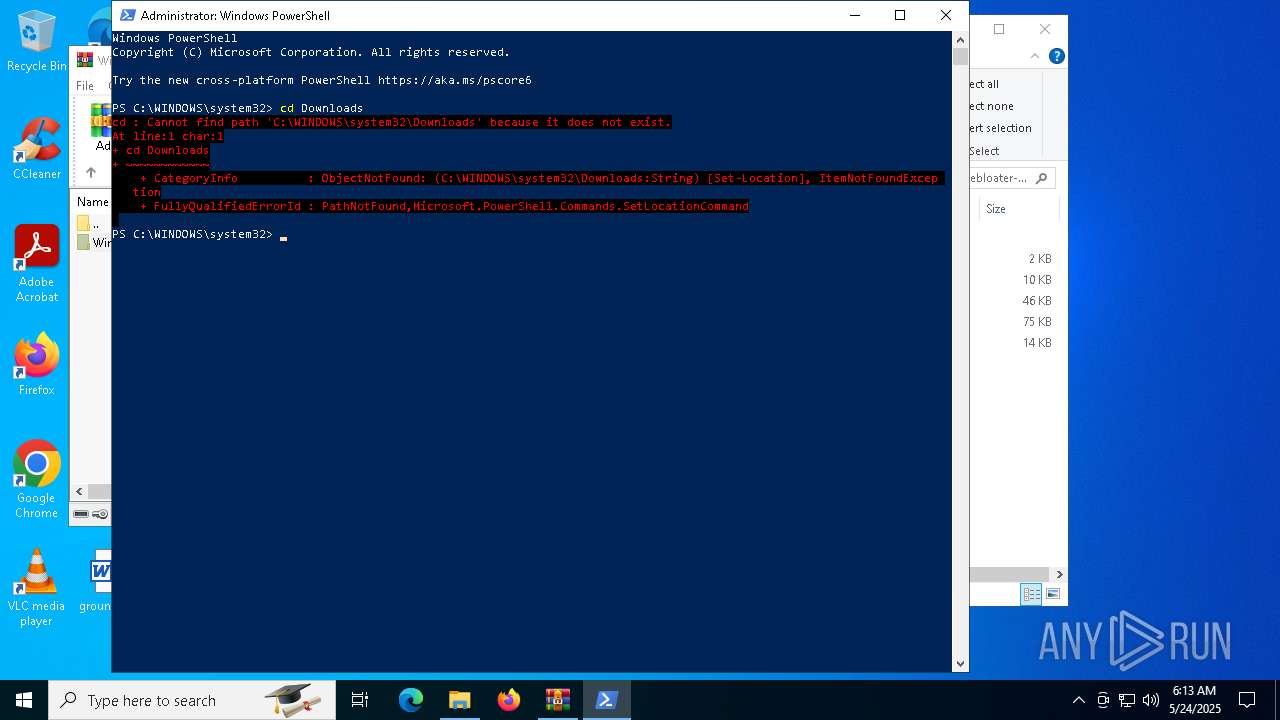
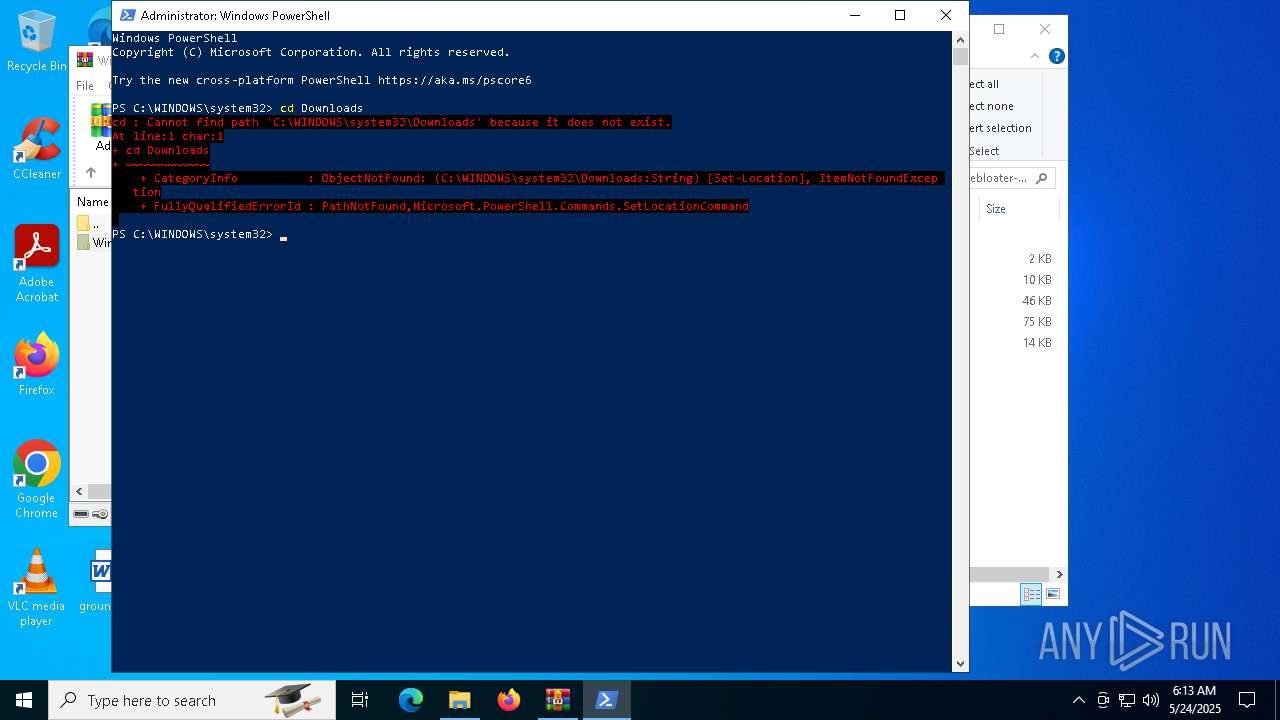
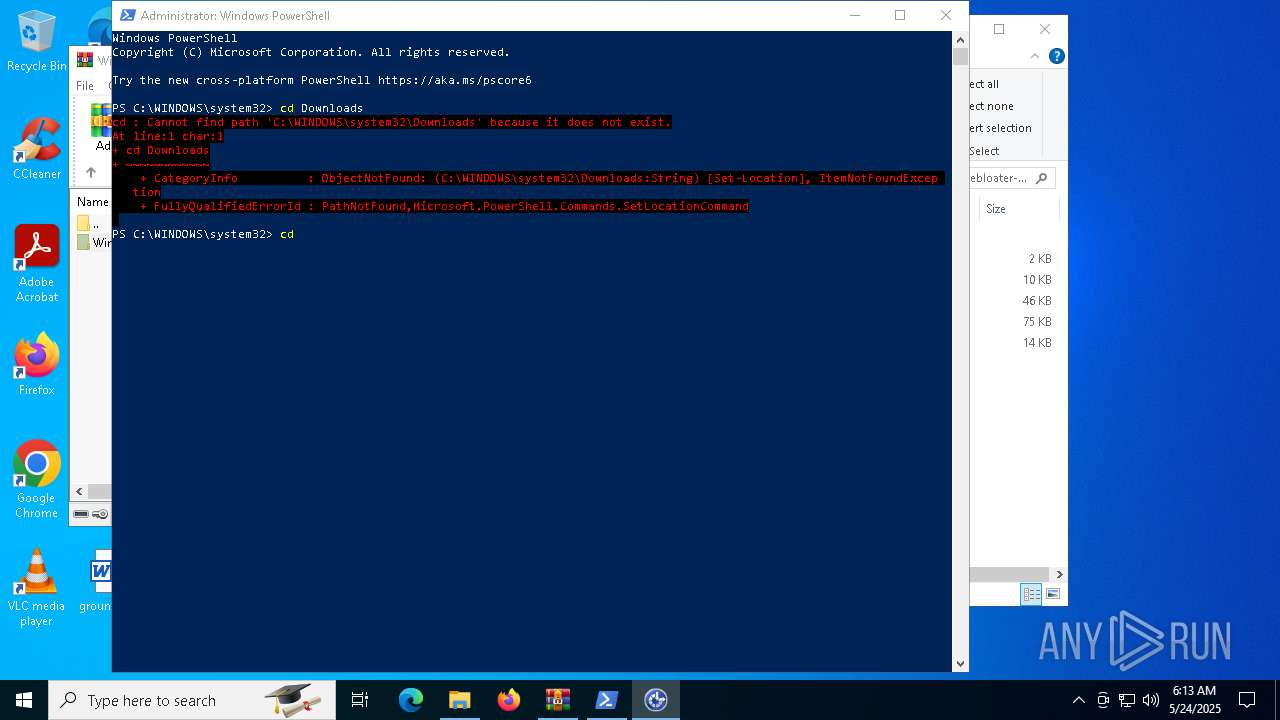
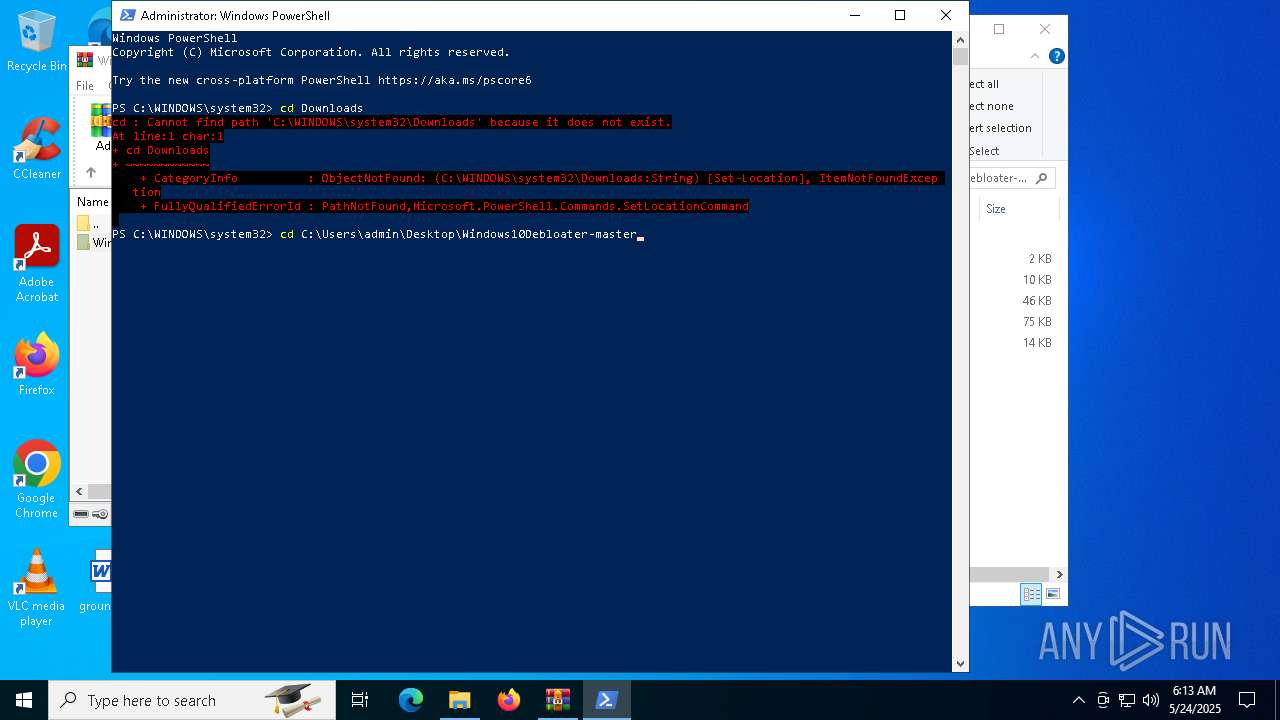
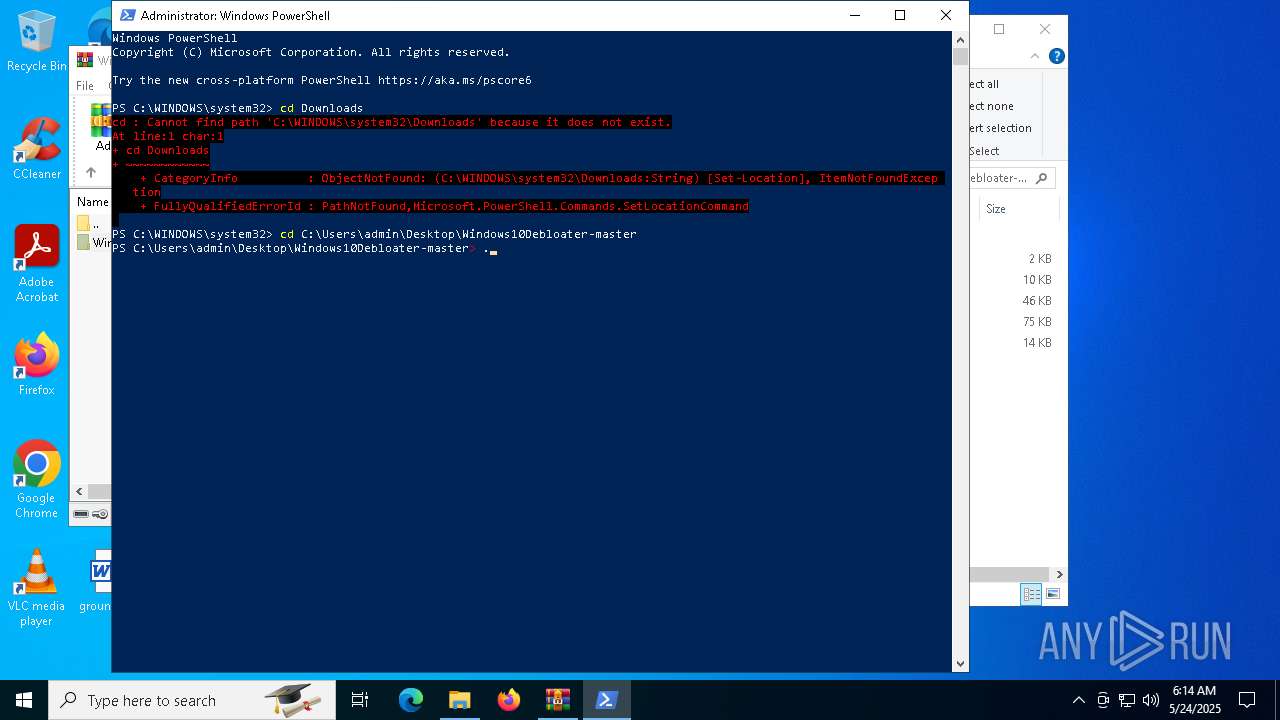
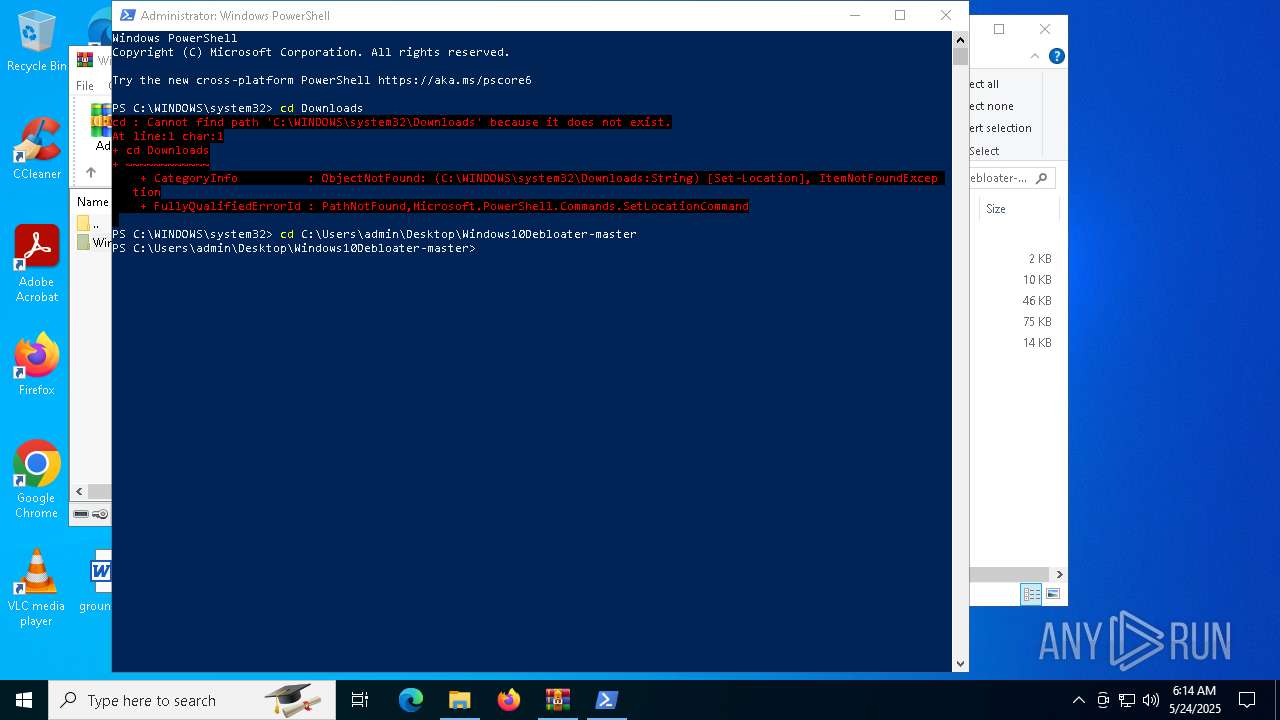
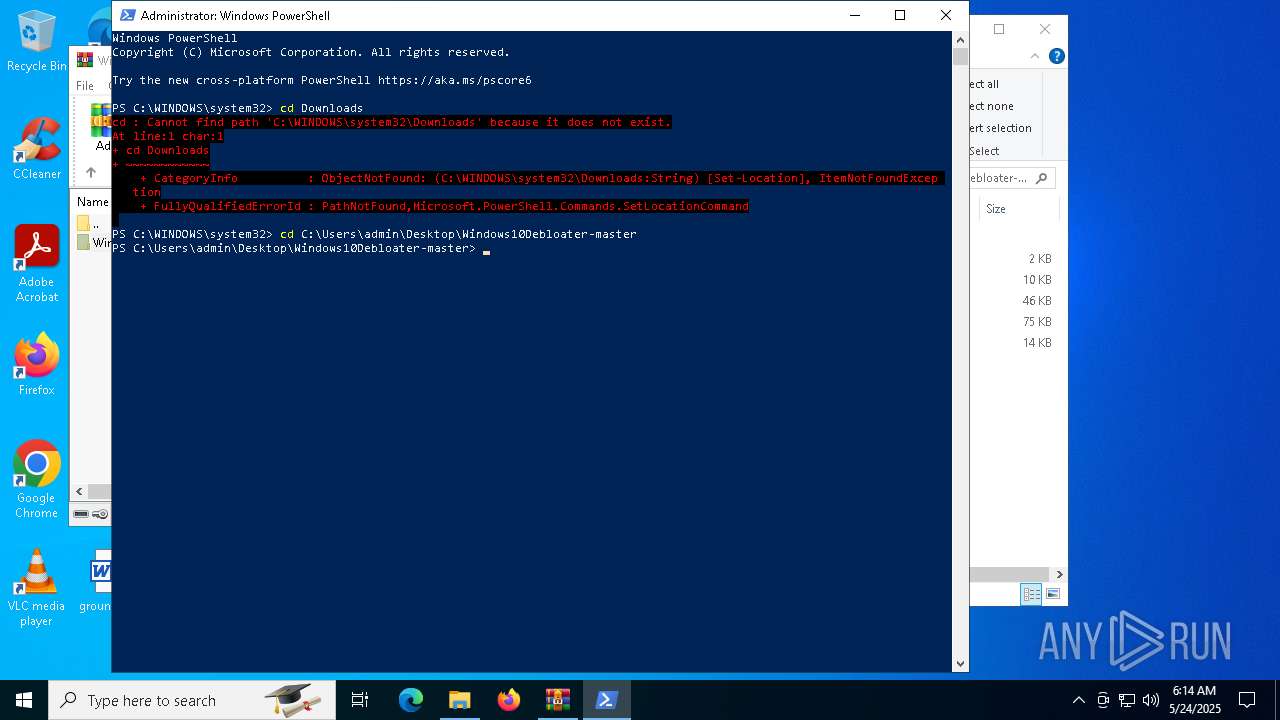
Checks current location (POWERSHELL)
- powershell.exe (PID: 5244)
Reads the software policy settings
- slui.exe (PID: 7688)
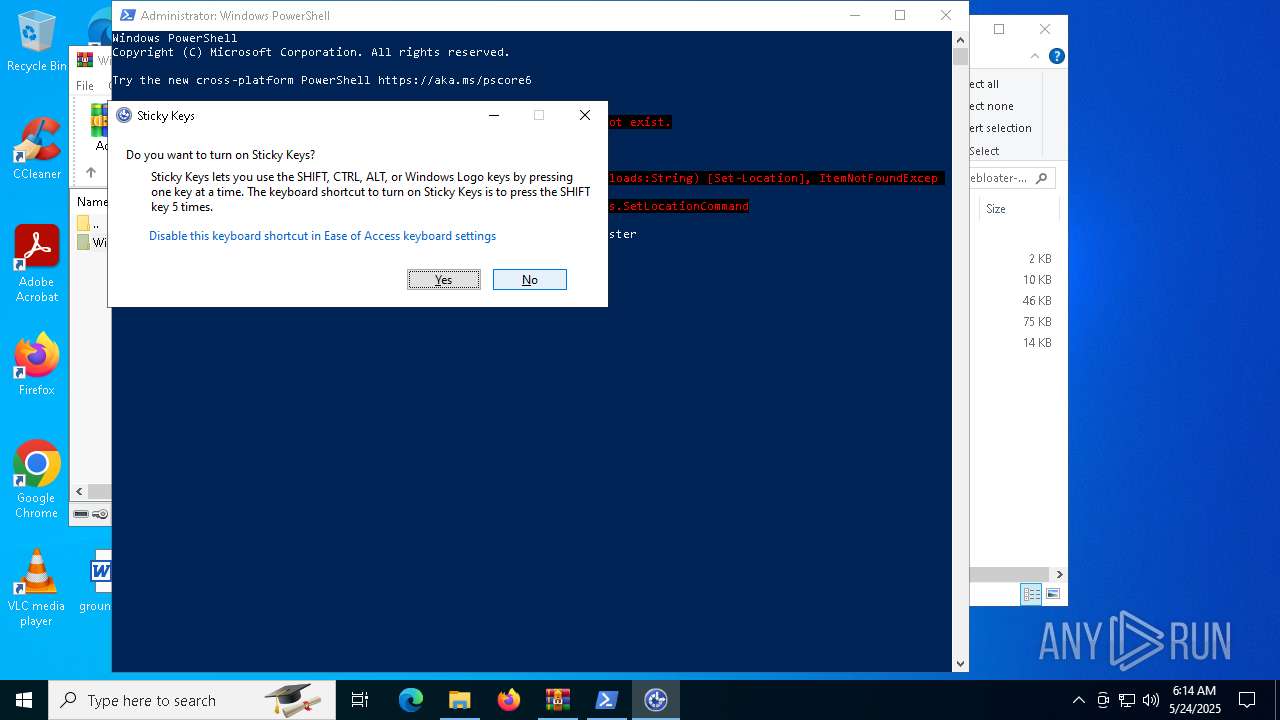
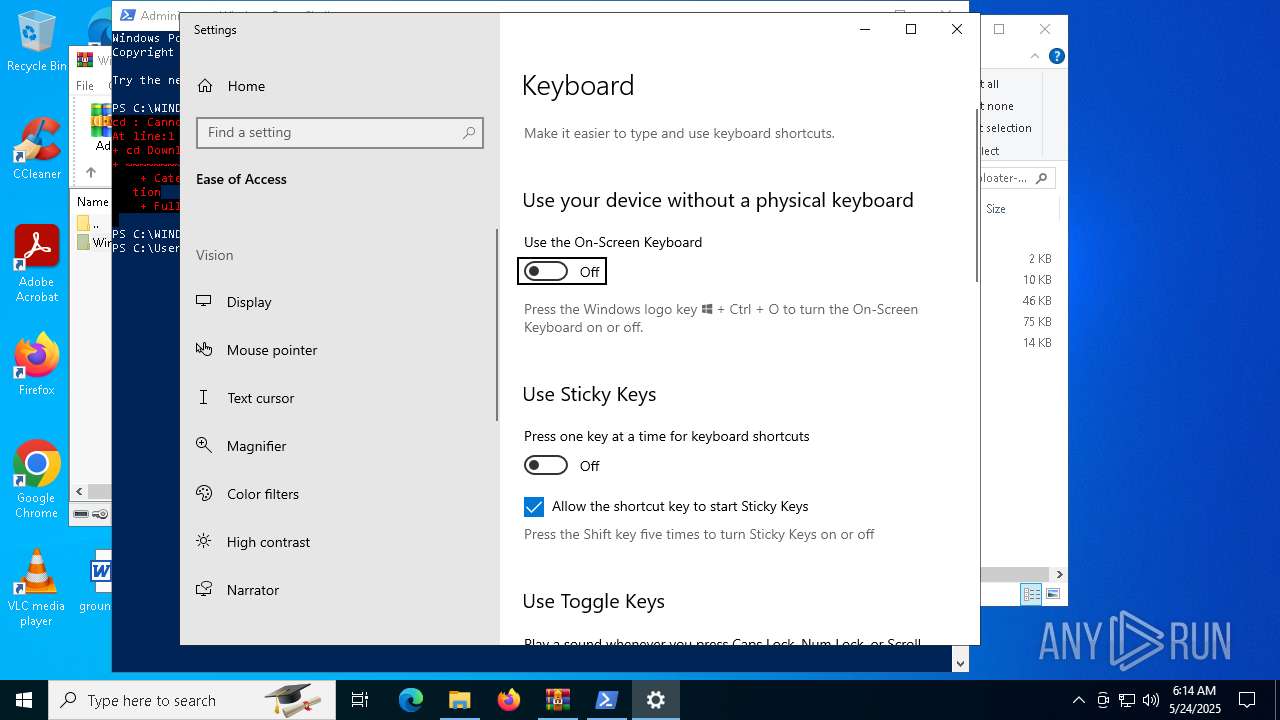
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5244)
The sample compiled with english language support
- powershell.exe (PID: 5244)
Manages system restore points
- SrTasks.exe (PID: 2236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:06:26 20:39:20 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Windows10Debloater-master/ |
Total processes
228
Monitored processes
45
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 704 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | C:\Users\admin\AppData\Local\Temp\1FF84125-592B-437C-BCC2-B67F50965F9F\dismhost.exe {303A37CF-1C5F-4CC8-8F8B-9BD81461C204} | C:\Users\admin\AppData\Local\Temp\1FF84125-592B-437C-BCC2-B67F50965F9F\DismHost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | "C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncConfig.exe" /uninstall | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncConfig.exe | — | OneDriveSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDrive Configuration Application Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 1492 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 1 Version: 123.26505.0.0 Modules
| |||||||||||||||
| 2108 | C:\WINDOWS\System32\mobsync.exe -Embedding | C:\Windows\System32\mobsync.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Sync Center Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Exit code: 1 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | C:\WINDOWS\System32\mobsync.exe -Embedding | C:\Windows\System32\mobsync.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Sync Center Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2652 | C:\Users\admin\AppData\Local\Temp\B5D3E8EC-EC7E-488C-A0C1-853685BF6FBC\dismhost.exe {8FF457F6-0114-4878-9F03-6B98C84382C1} | C:\Users\admin\AppData\Local\Temp\B5D3E8EC-EC7E-488C-A0C1-853685BF6FBC\DismHost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
120 395
Read events
118 865
Write events
580
Delete events
950
Modification events
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Windows10Debloater-master.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (680) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000000EA97B2773CCDB01A8020000EC000000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (680) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000005D34A42773CCDB01A8020000EC000000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
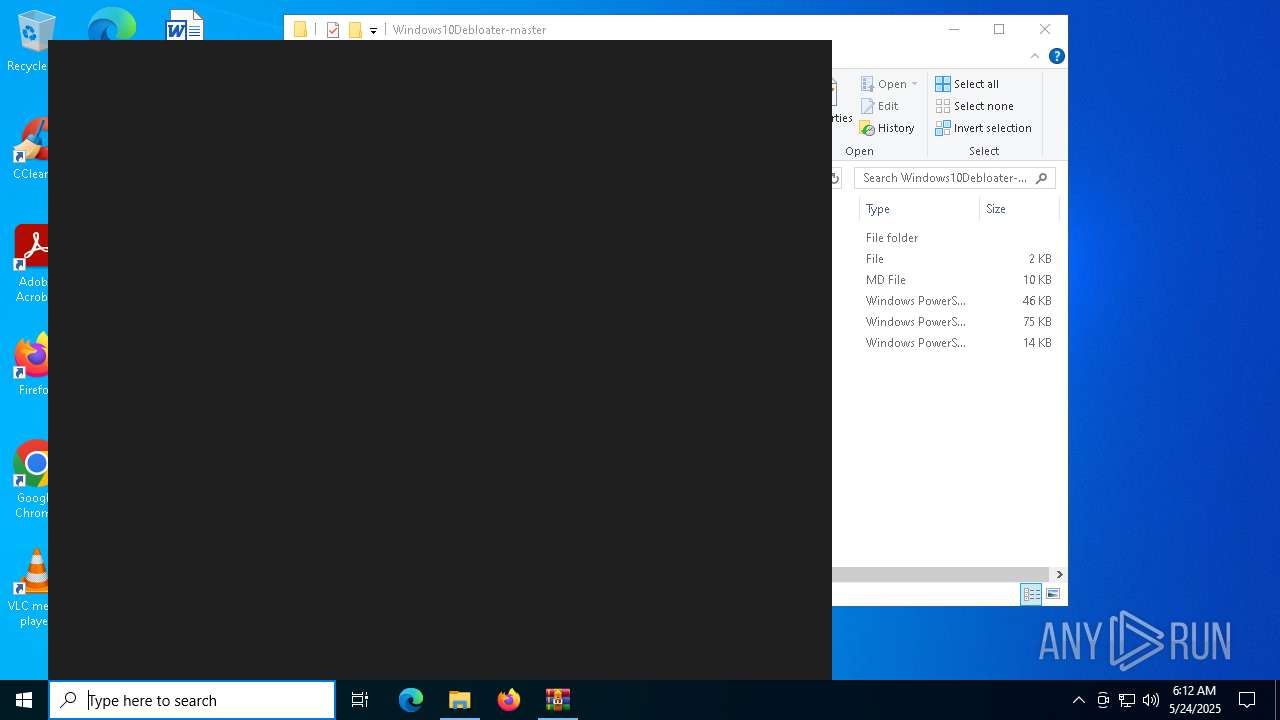
Executable files
205
Suspicious files
19
Text files
89
Unknown types
0
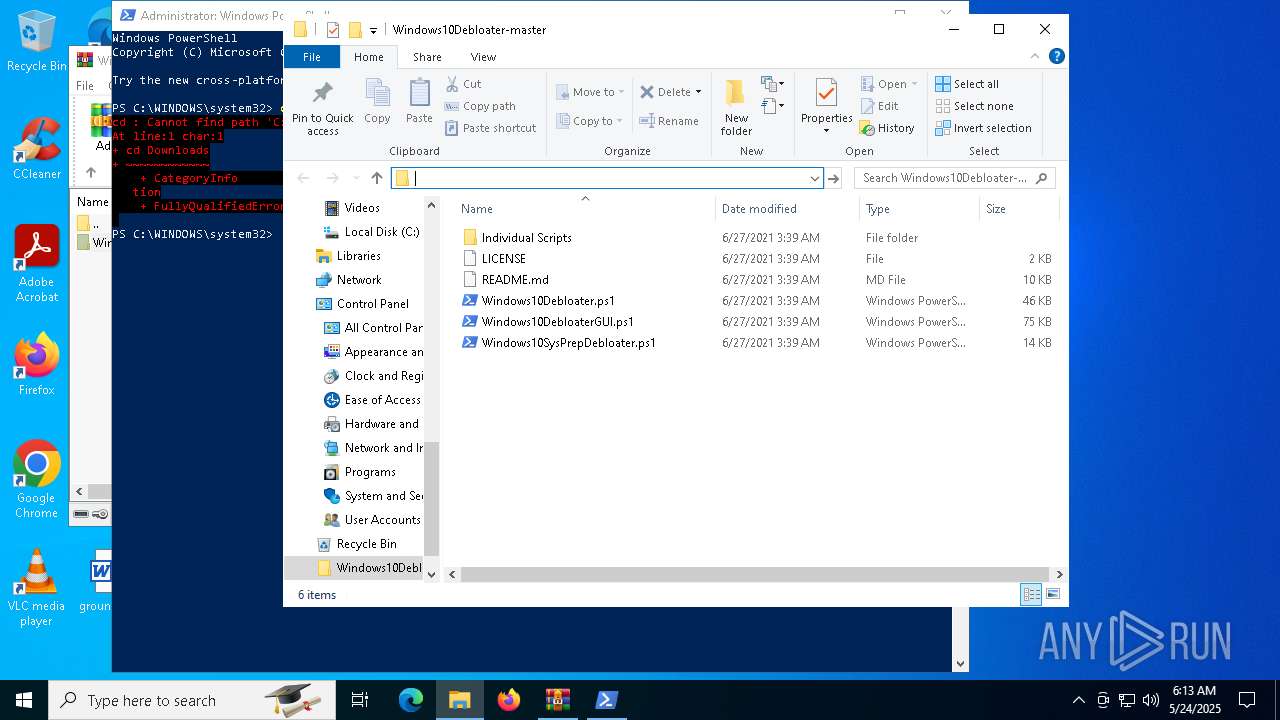
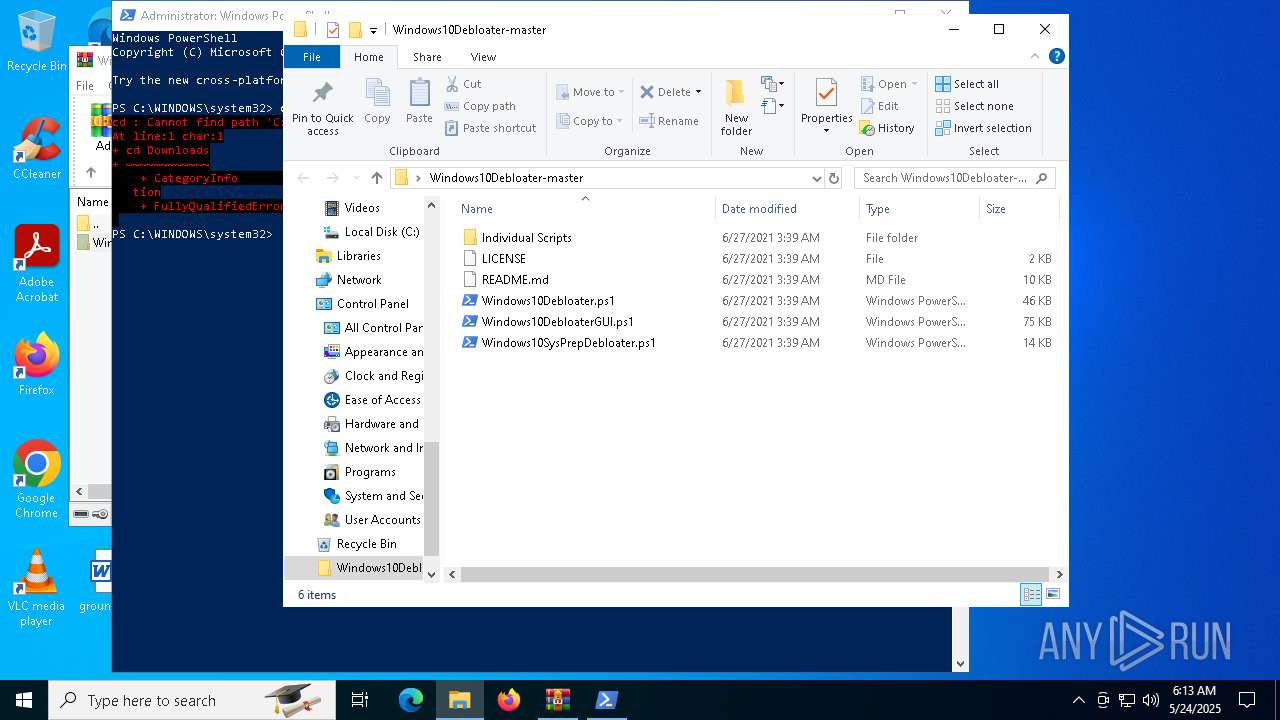
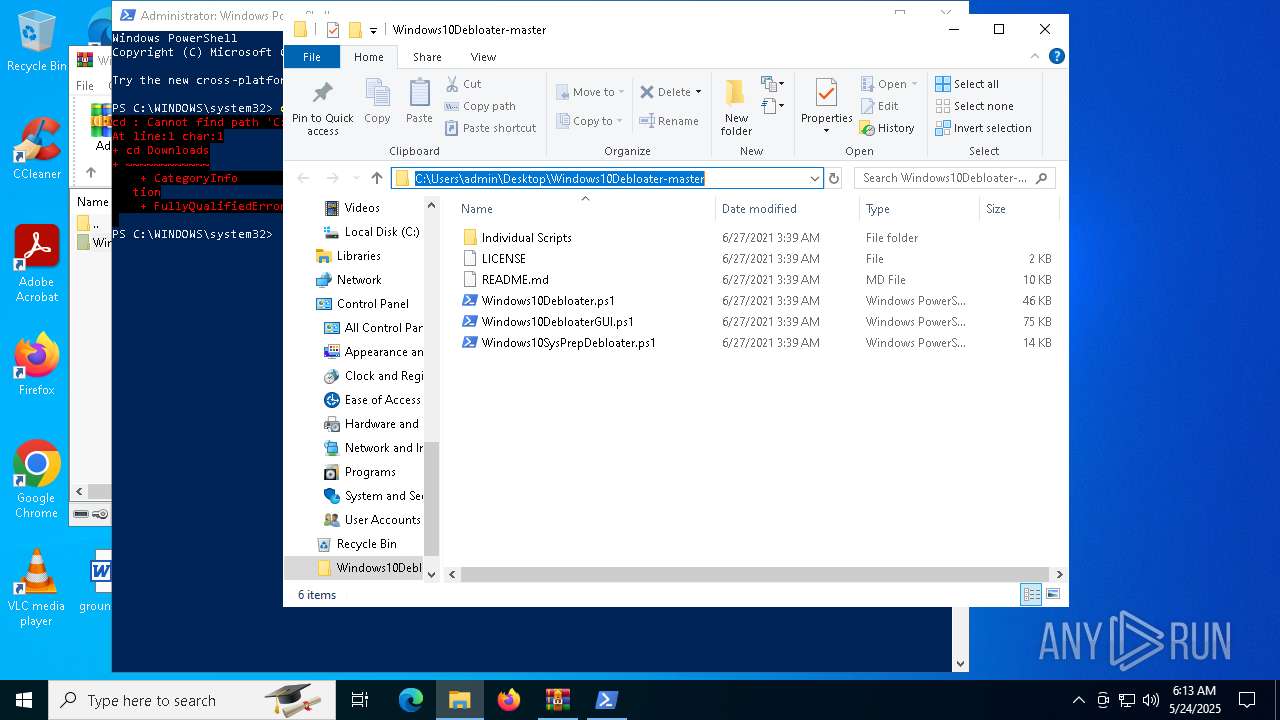
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7480.44245\Windows10Debloater-master\Individual Scripts\Protect Privacy | text | |
MD5:0204760E129C125D3B6432E3C55BFBCC | SHA256:3C1E5367AC277EEEDDDFC67B0C350900F6E60251779BB8D4F5C262C4019EC42F | |||
| 7480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7480.44245\Windows10Debloater-master\Individual Scripts\Disable Cortana | text | |
MD5:6323E777A8ADD8E0C94BF73B29C7E493 | SHA256:5F094AE62D81CD7B7A049D3193802CCF58CBDC738DF285C95FF5CBB73B4876D7 | |||
| 7480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7480.44245\Windows10Debloater-master\Individual Scripts\Unpin Start | text | |
MD5:504E226AB05186CFDB1C29FC6D0D0114 | SHA256:186823F7D920B3E88E2A056AD3CD2FD0181E814CD7E6C1AA09A8D8699FEDD96D | |||
| 7480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7480.44245\Windows10Debloater-master\Individual Scripts\Debloat Windows | text | |
MD5:FE027363EDD3AA71C6A4AE0ECB7CEAAE | SHA256:2152BDD73176E7152A02B79170FE193E0F036B91373F8781937DF67247561DE0 | |||
| 7480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7480.44245\Windows10Debloater-master\Individual Scripts\Clear Last Used Files and Folders.ps1 | text | |
MD5:5DBCB1C9B5458046DB9899E080A0957C | SHA256:9D148276E7BBEDFD397315815F48425D01280F13DB5F3C17CA0B1C0F90D12F79 | |||
| 7480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7480.44245\Windows10Debloater-master\Individual Scripts\Disable Last Used Files and Folders View.ps1 | text | |
MD5:A89CD270851A8B1EF9D645A018B1B8F7 | SHA256:63A2FA69B2AD719F963EA52E573E9777EB66552EA4A618416F19745A234D13B5 | |||
| 7480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7480.44245\Windows10Debloater-master\Individual Scripts\Fix Whitelisted Apps | text | |
MD5:BEB720E264A818EC1C8523B6DE24D705 | SHA256:F9998BFB7DC3FDE2DF313E7E37D22CBEA956CFDD4938BC06D27752974E9C67B8 | |||
| 7480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7480.44245\Windows10Debloater-master\Individual Scripts\Revert Changes | text | |
MD5:5C45C8BFE0A137468C9933131F22ED6E | SHA256:B346D069CE67865979DD979952E2ED148716807015038634247B810C927191DC | |||
| 7480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7480.44245\Windows10Debloater-master\Individual Scripts\Remove Bloatware RegKeys | text | |
MD5:DBA98A6EEDA78832880BCE9452FB2524 | SHA256:6F04F74E2F2AAE8D8AE8413B514A719B9B8A68D7A1580B93D717A477F539C1D5 | |||
| 7480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7480.44245\Windows10Debloater-master\Individual Scripts\Set Explorers LaunchTo Computer.ps1 | text | |
MD5:3919C1C974D775C4765127F2FDECFEB6 | SHA256:F1028C19C2A5CBF132048A3306277434E965C5FADC8046EEFE7C9F423DEBECF9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
46
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
664 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
664 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4156 | SystemSettings.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4156 | SystemSettings.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5796 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2616 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |