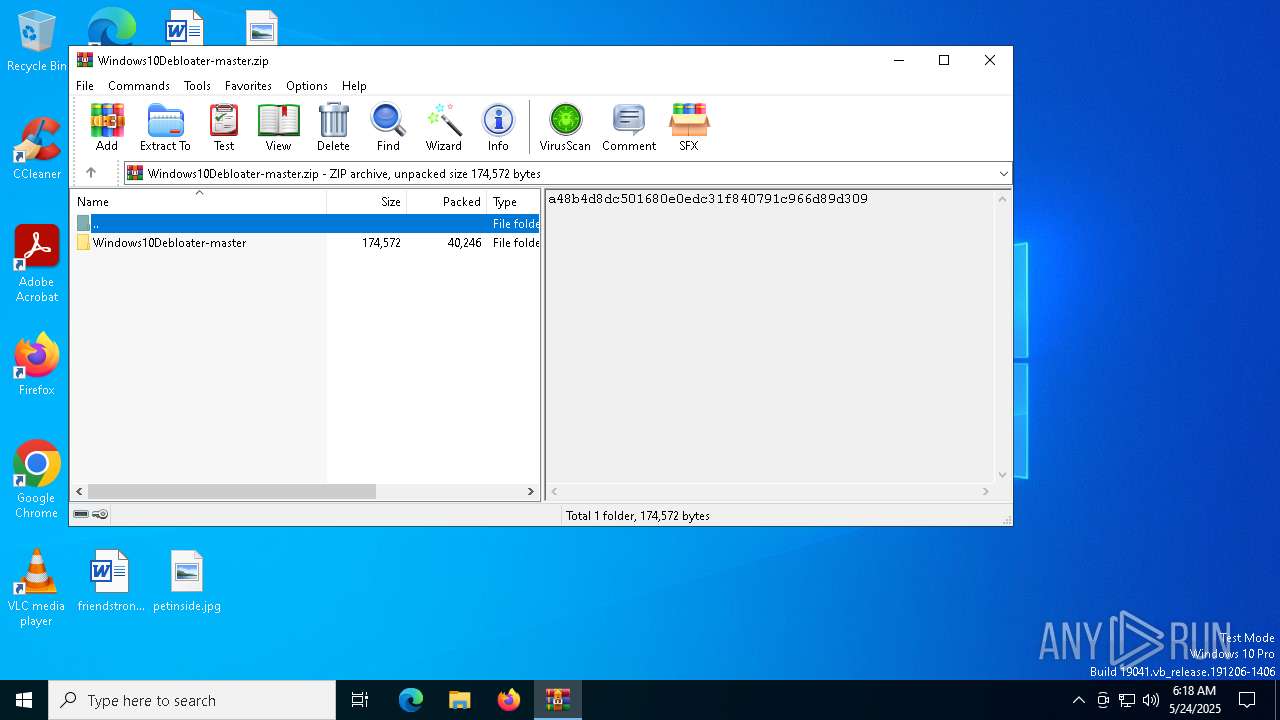
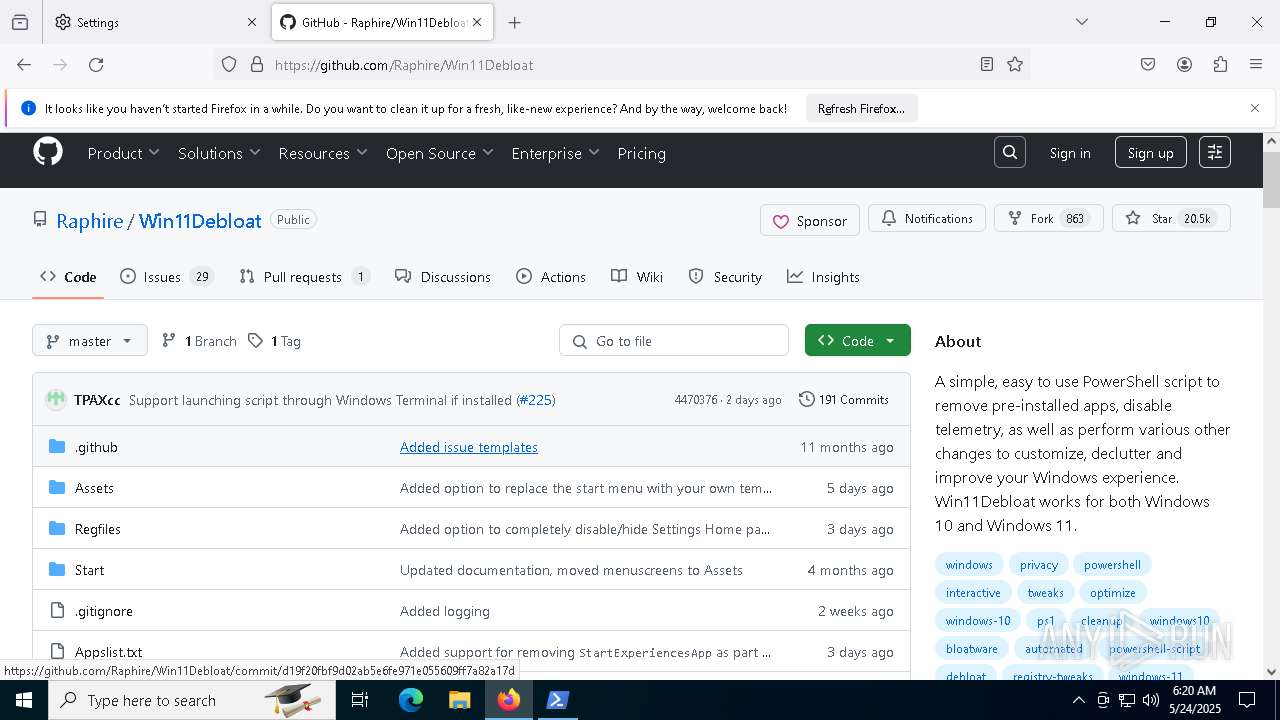
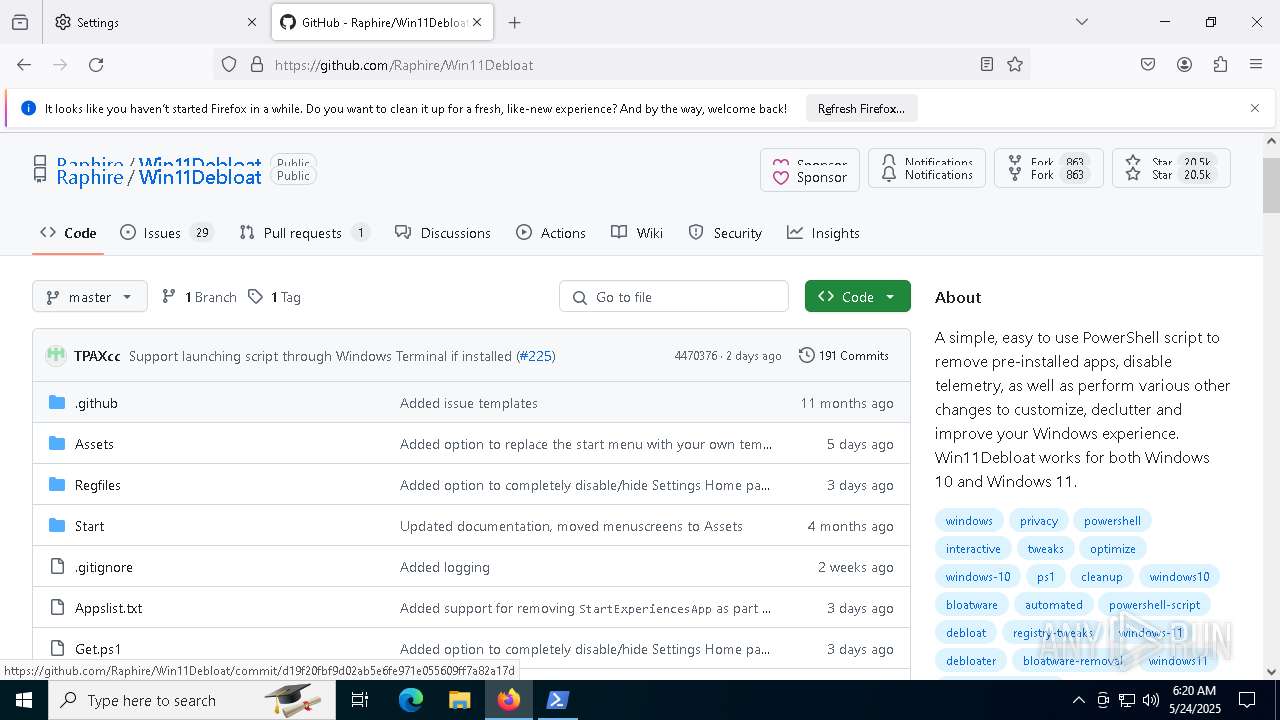
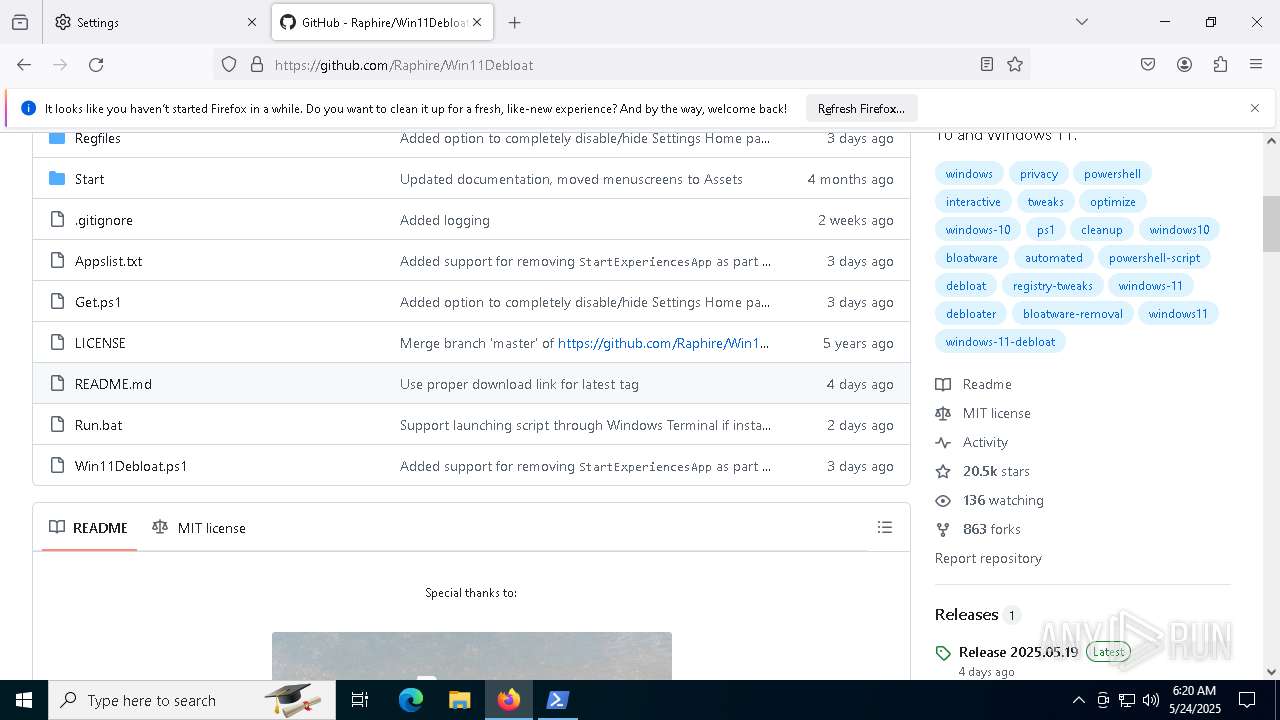
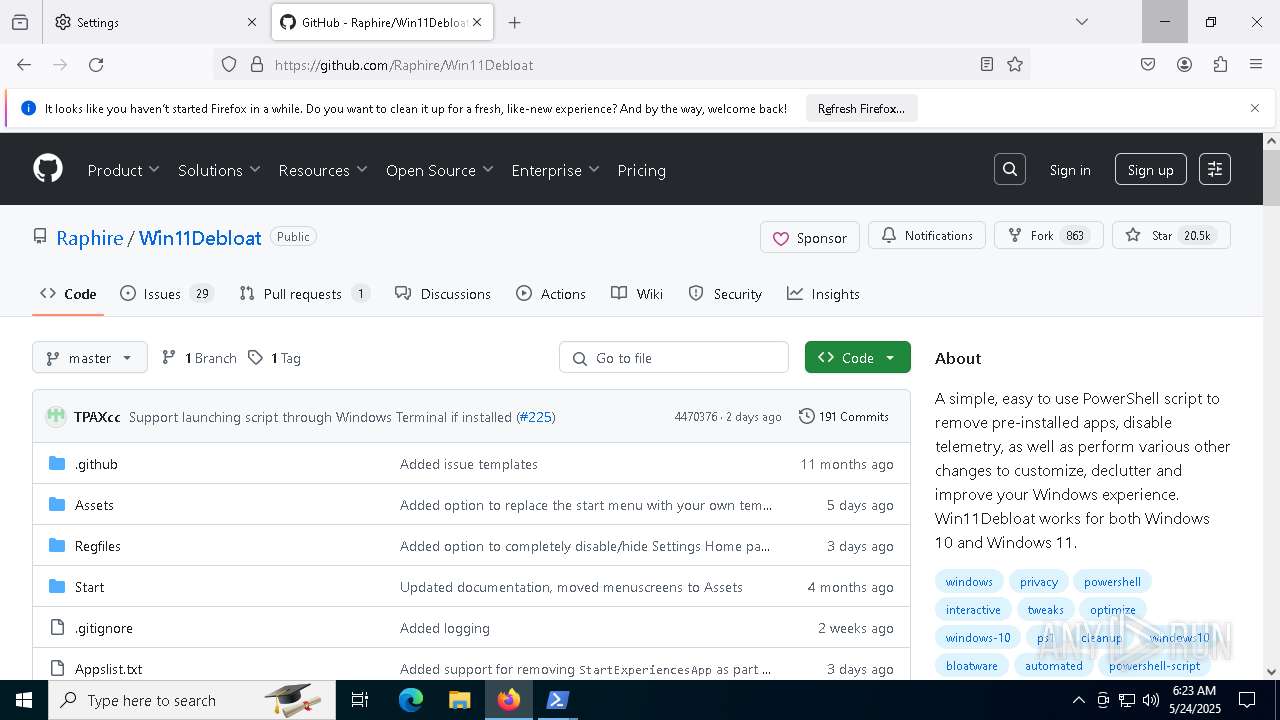
| File name: | Windows10Debloater-master.zip |
| Full analysis: | https://app.any.run/tasks/45e95145-d185-4462-aed6-b1ae8d0d4eac |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2025, 06:18:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 4D53BC43C2281F519DC84364FC02D962 |
| SHA1: | 8F0CF61D9F9ACD1E55D89E50228977D811D3E165 |
| SHA256: | 3C157C5B7547905869057BBF7FC5FF054E879DFBD147B6A9D82382180100F74C |
| SSDEEP: | 1536:Ka8kbJEk7J2rABW5H/KQ20+7nJCom7nXQJDKmpBYbNmU77:/82irA0Ub0+NCombAPBYbNH |
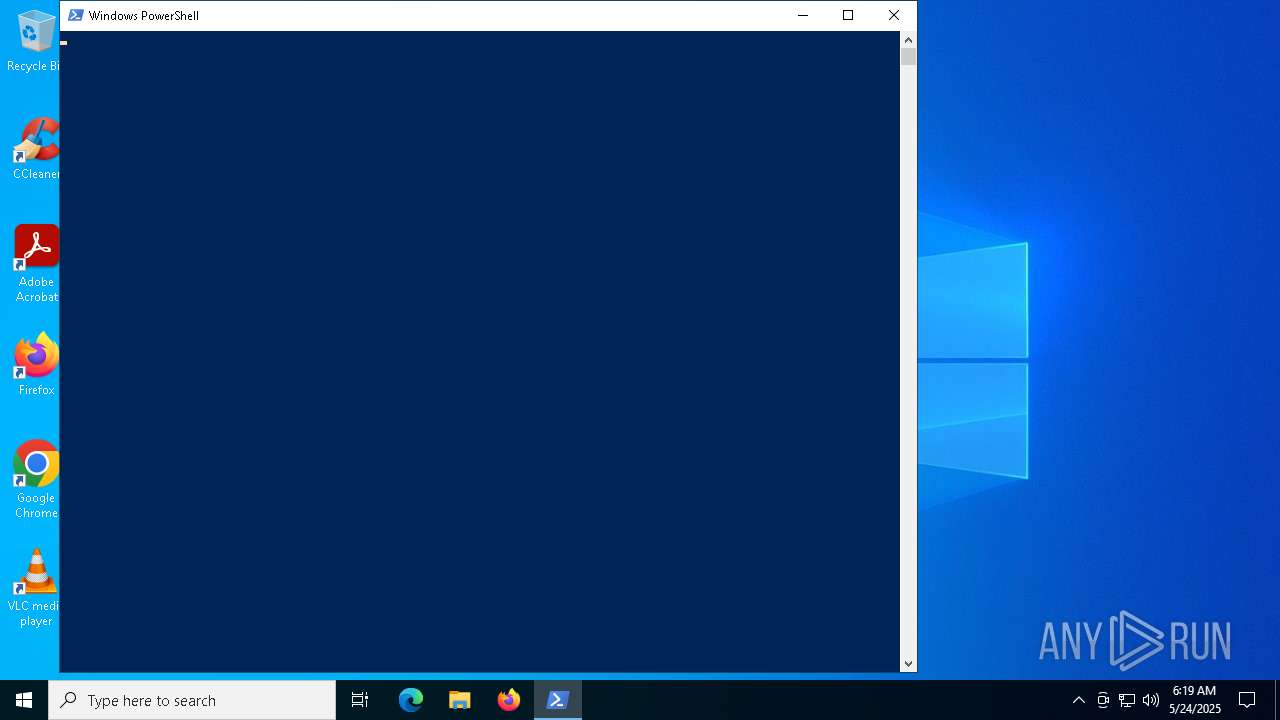
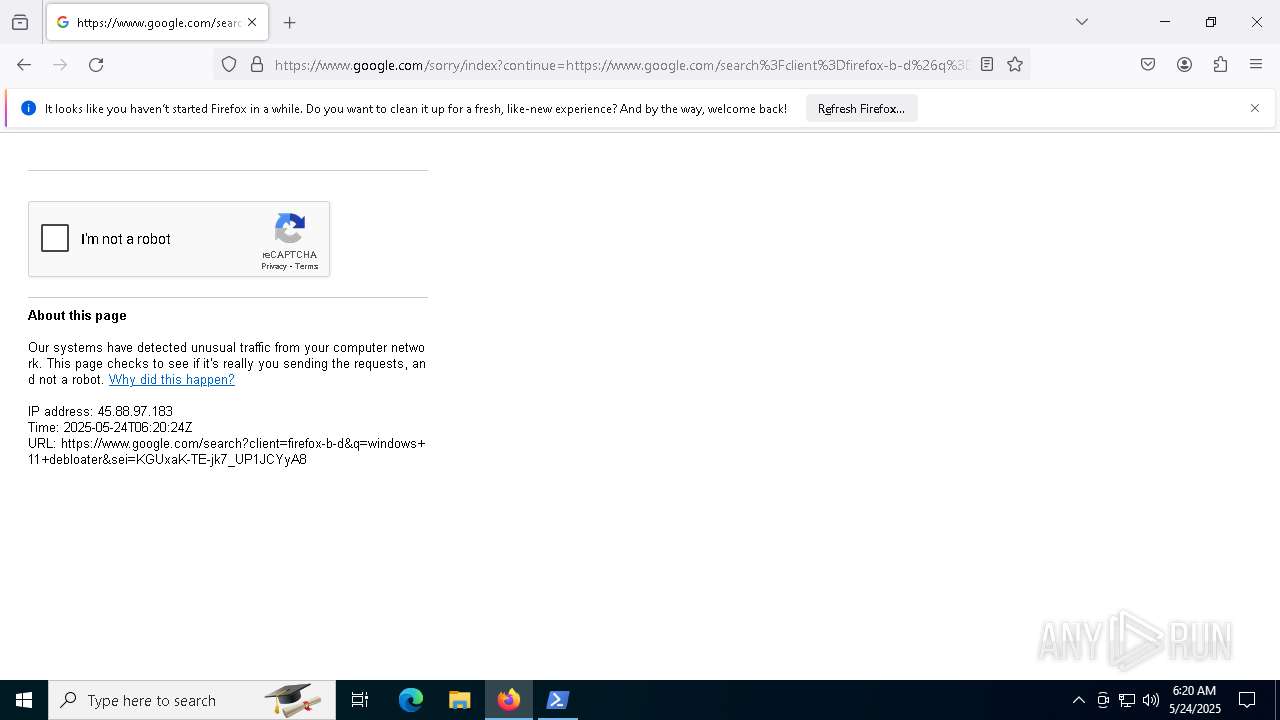
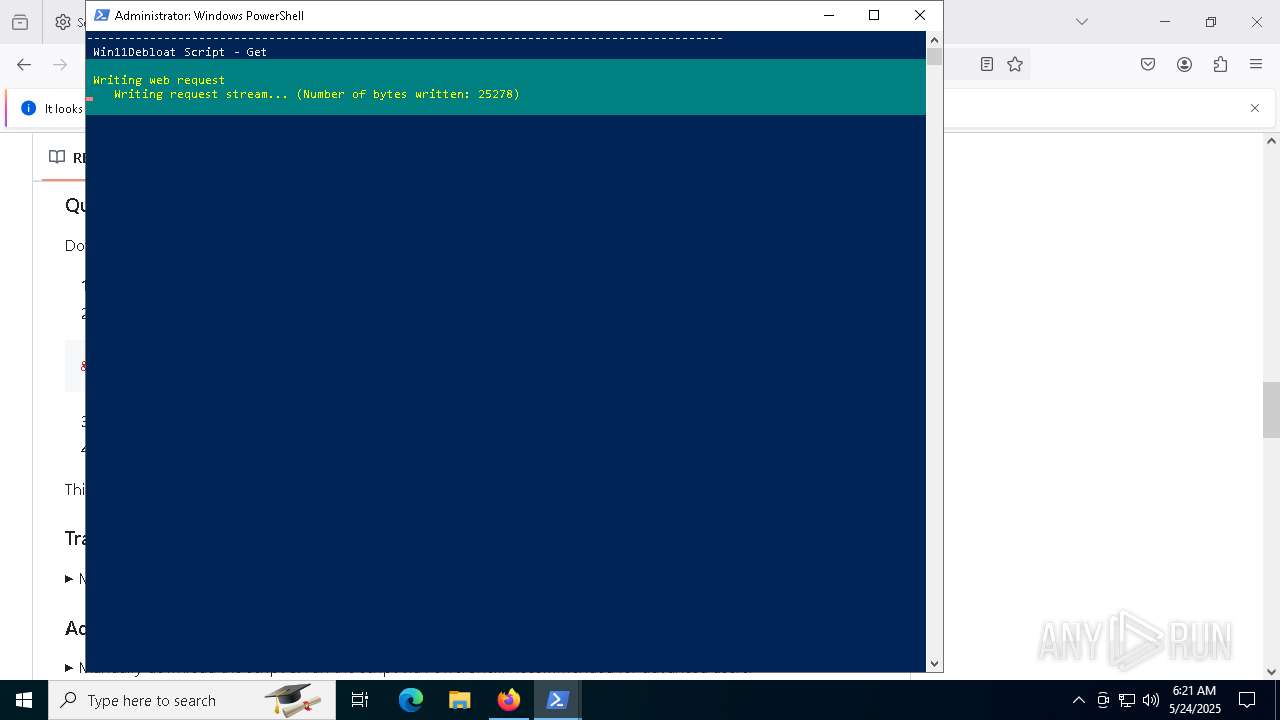
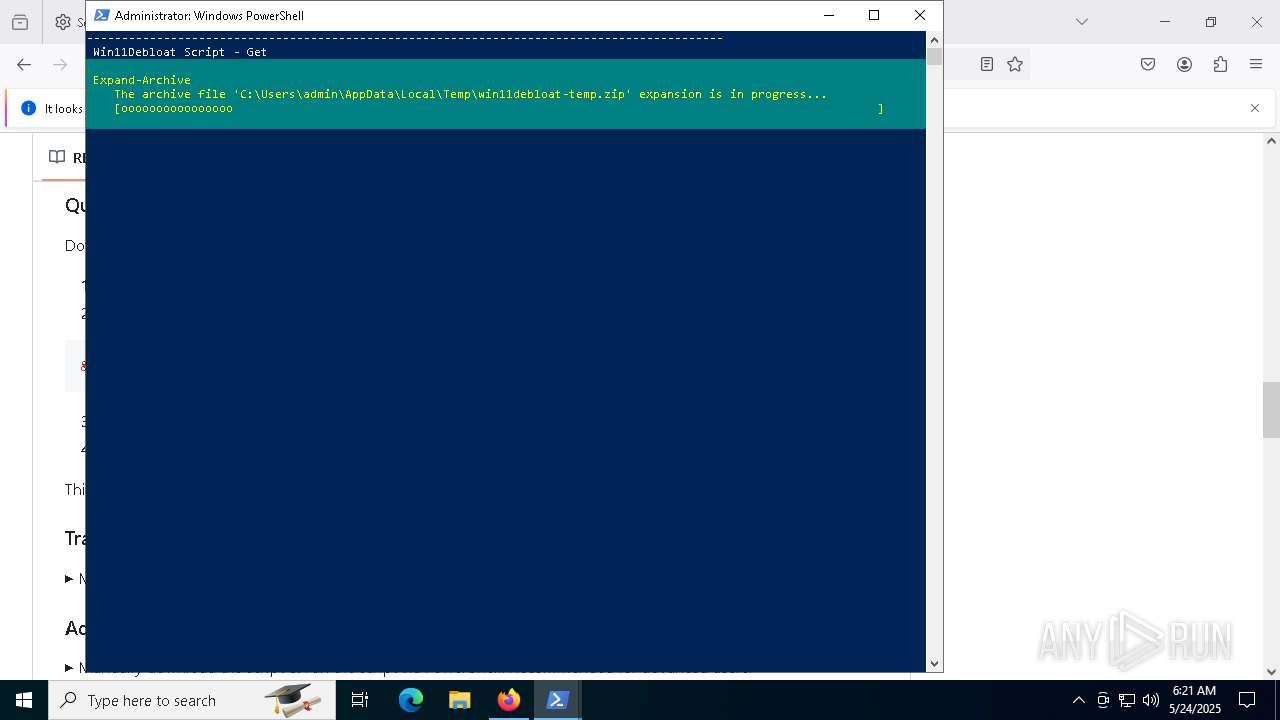
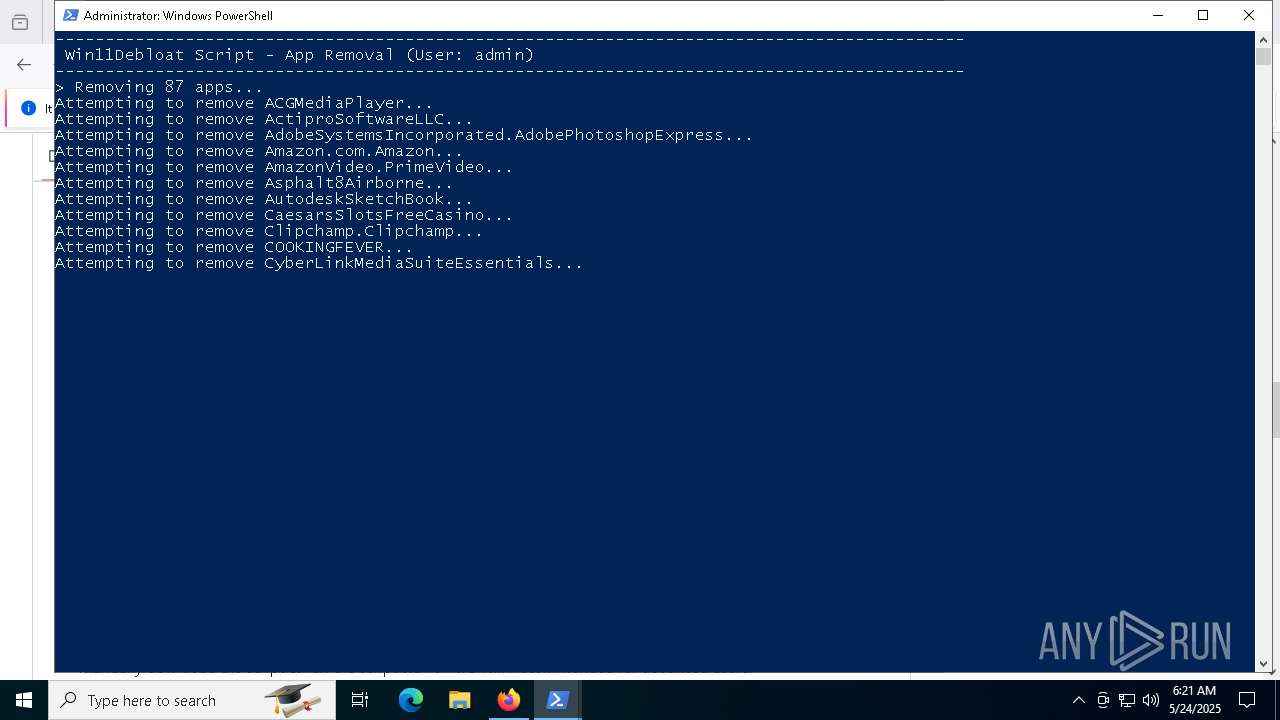
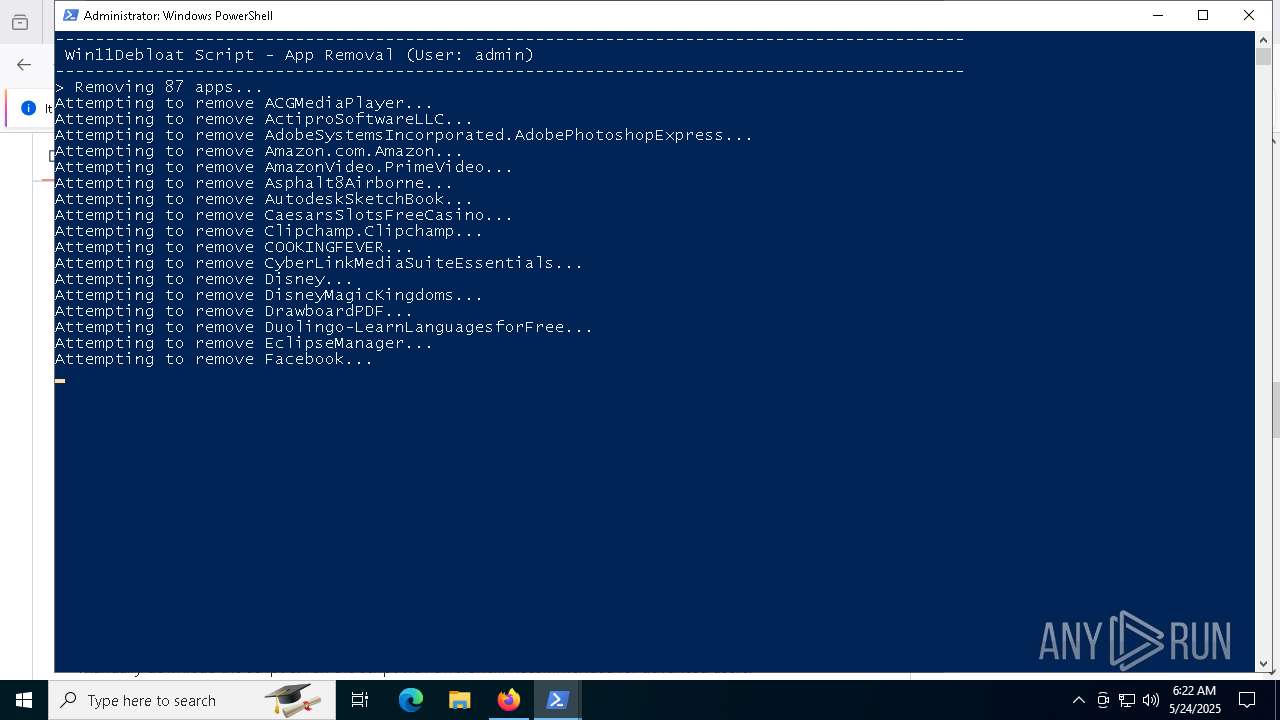
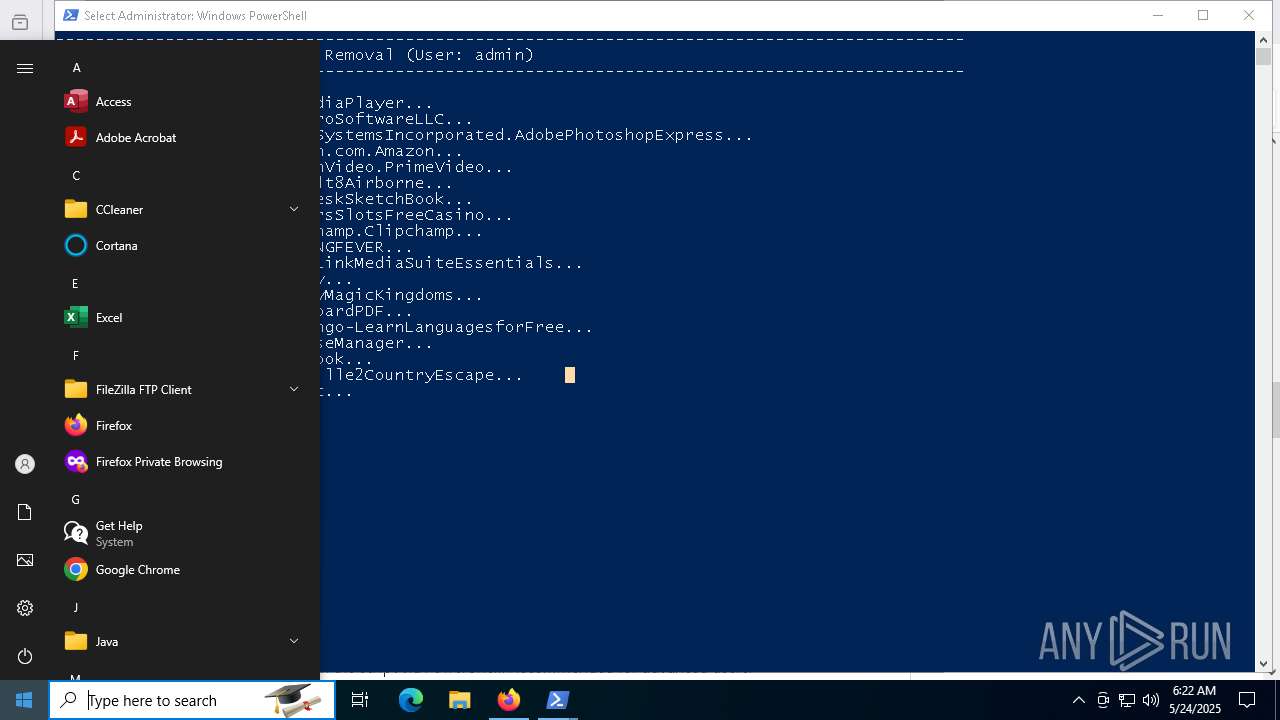
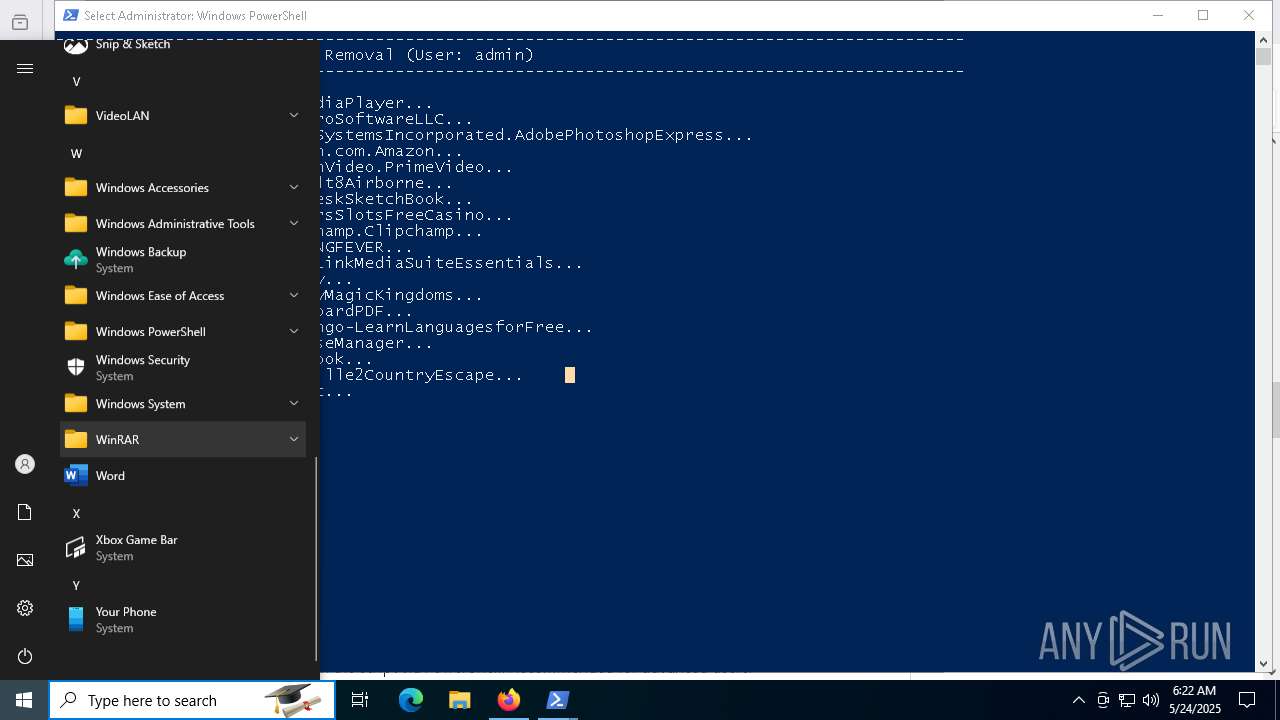
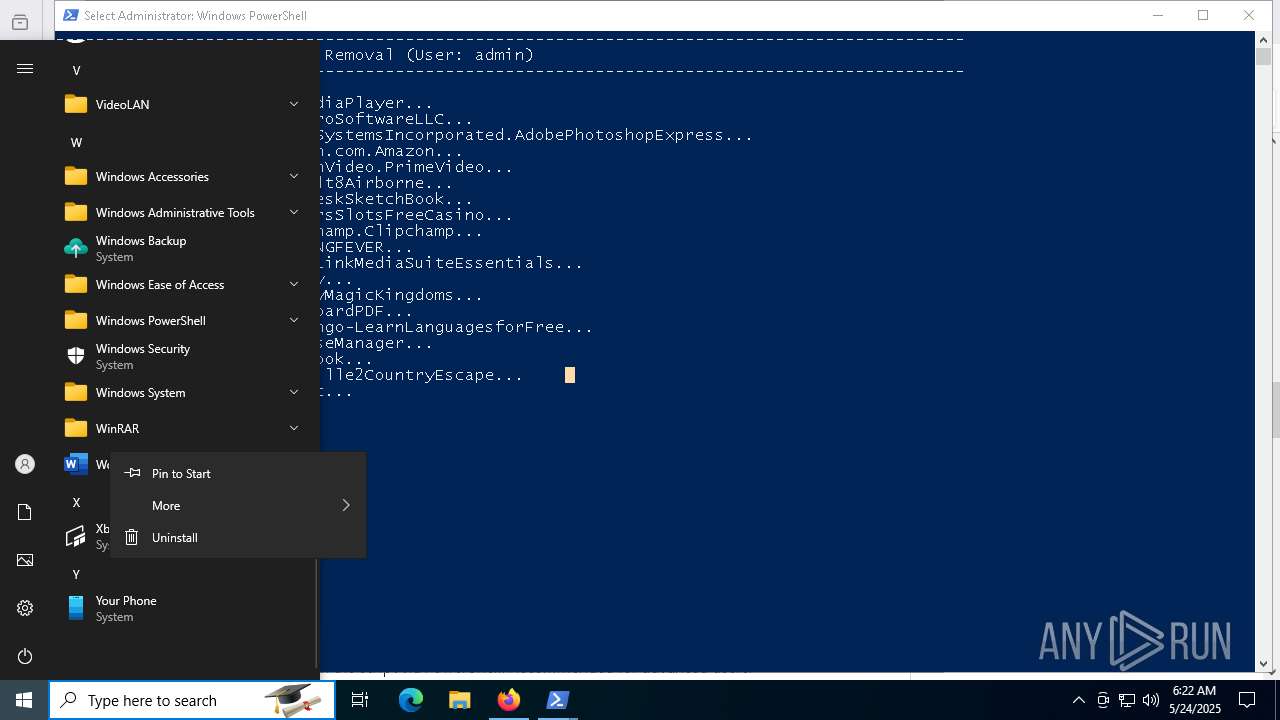
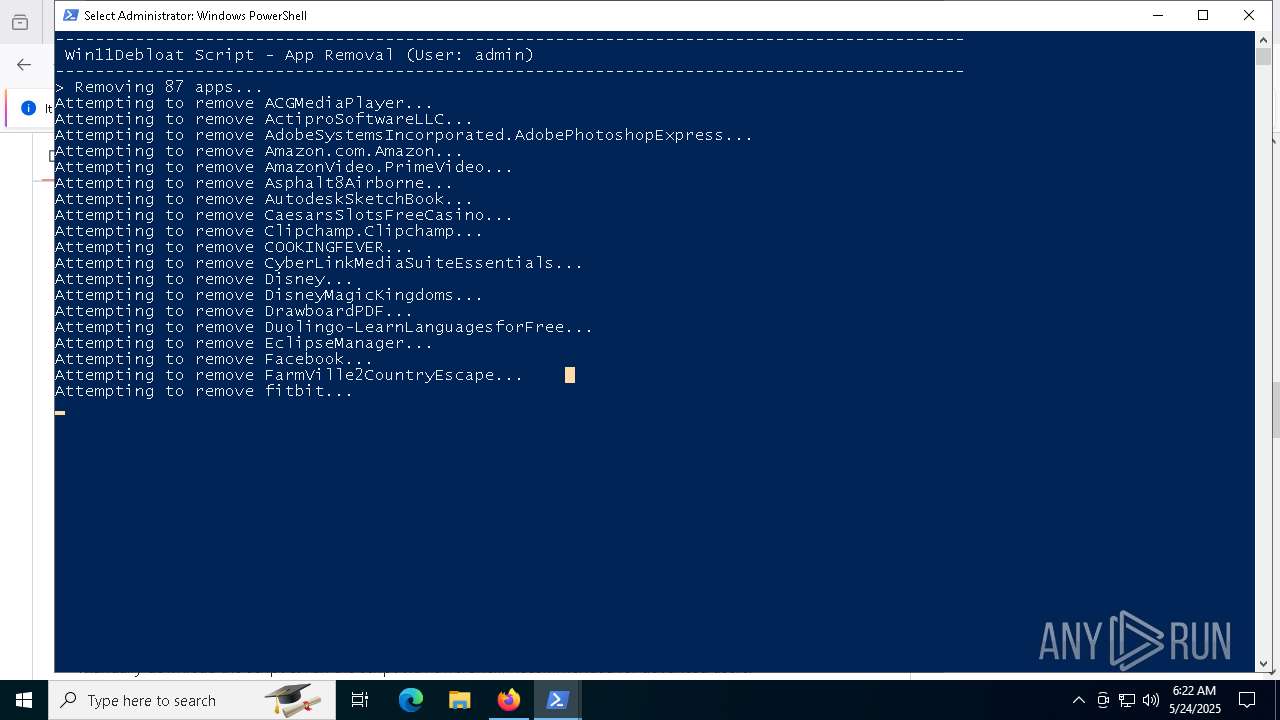
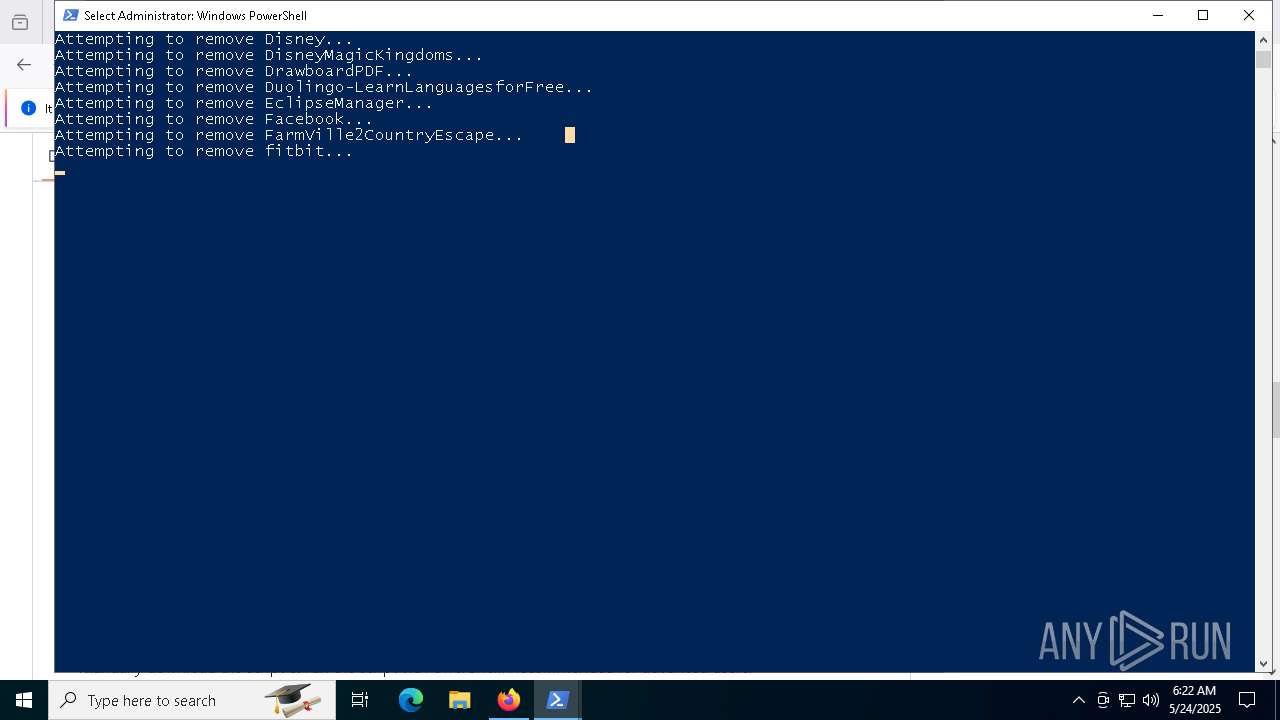
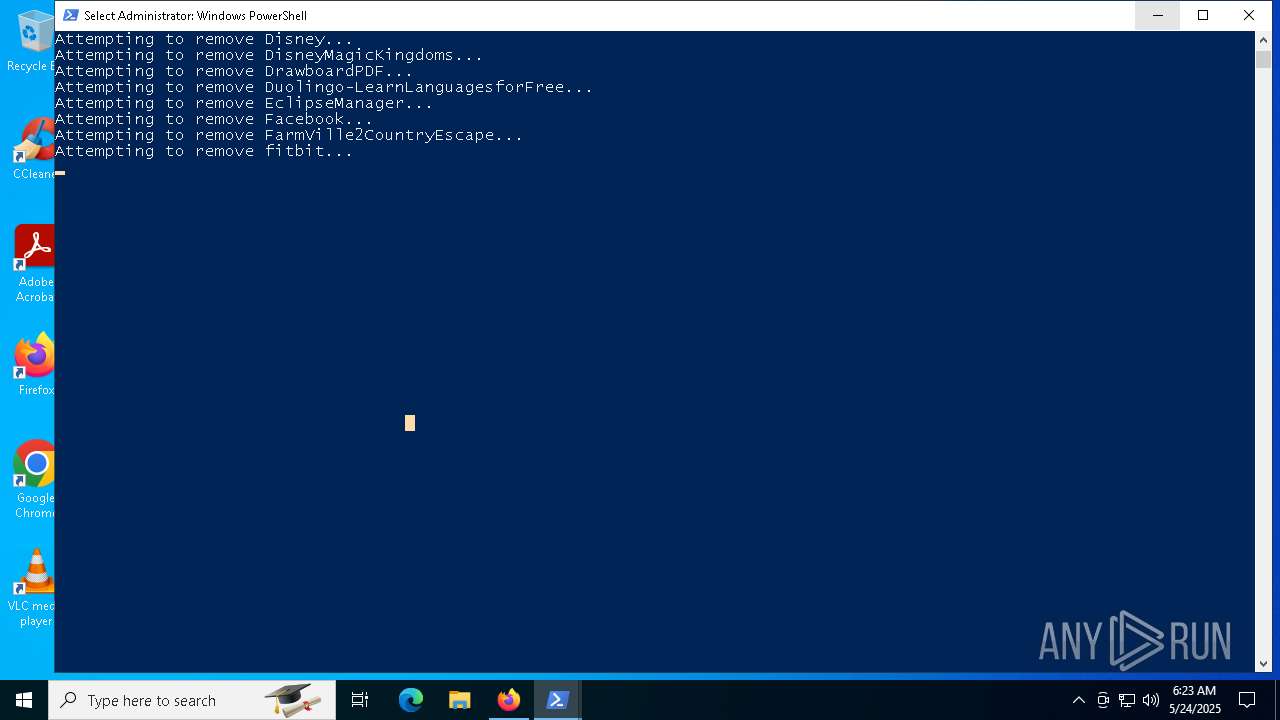
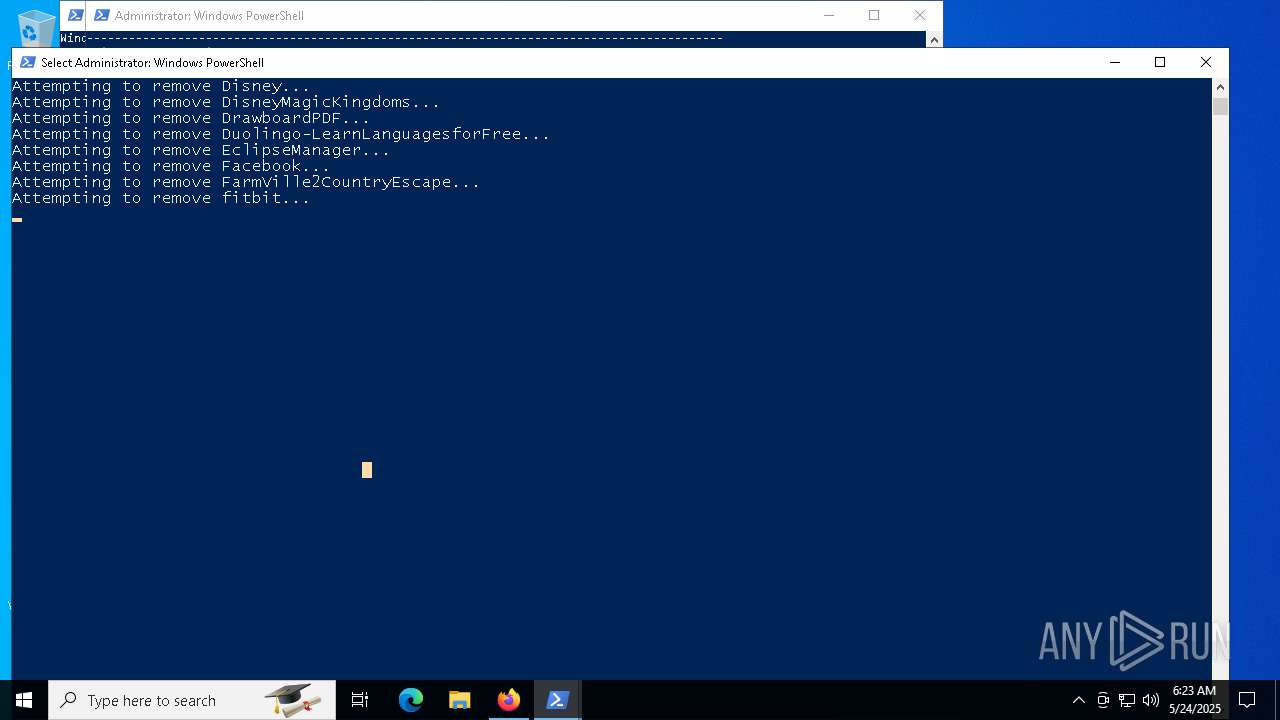
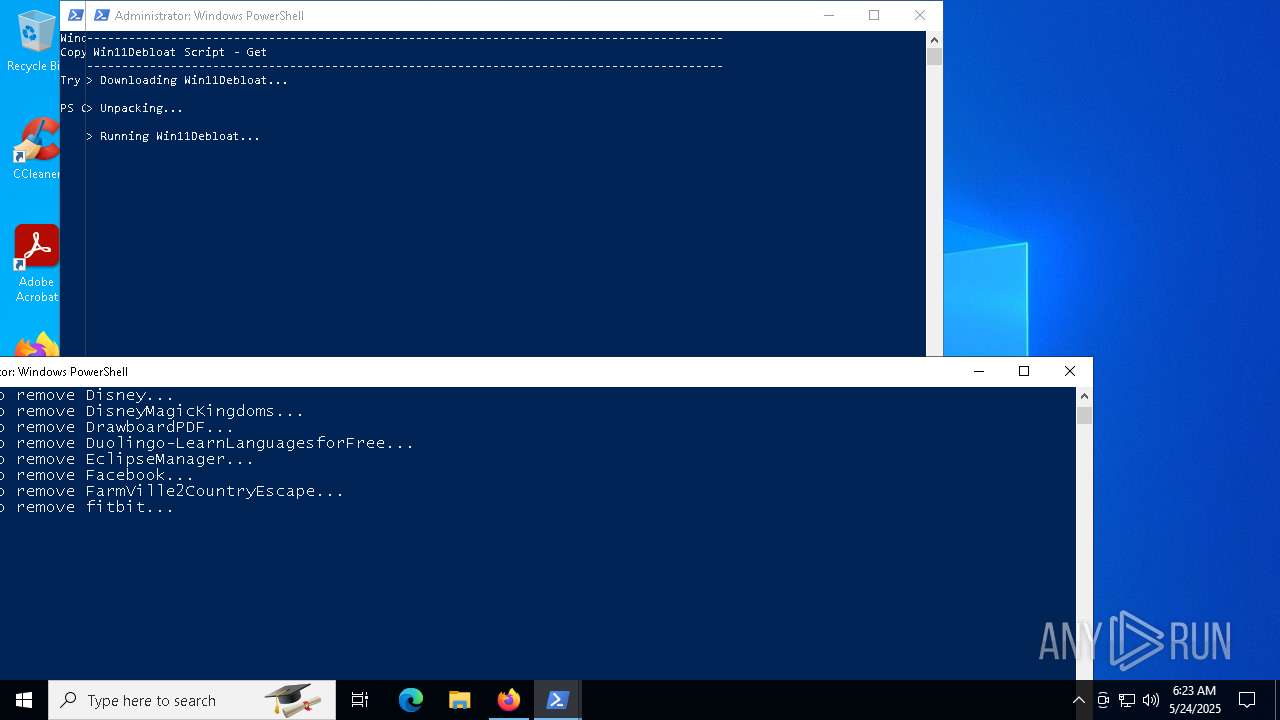
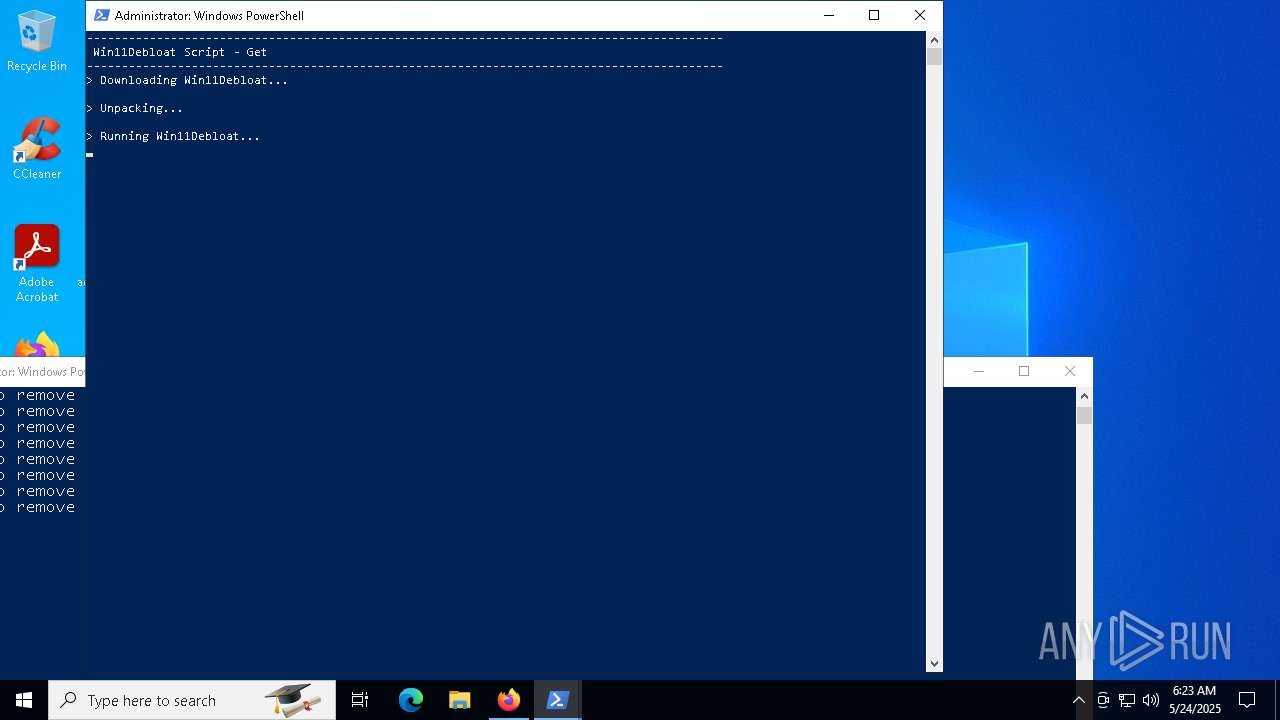
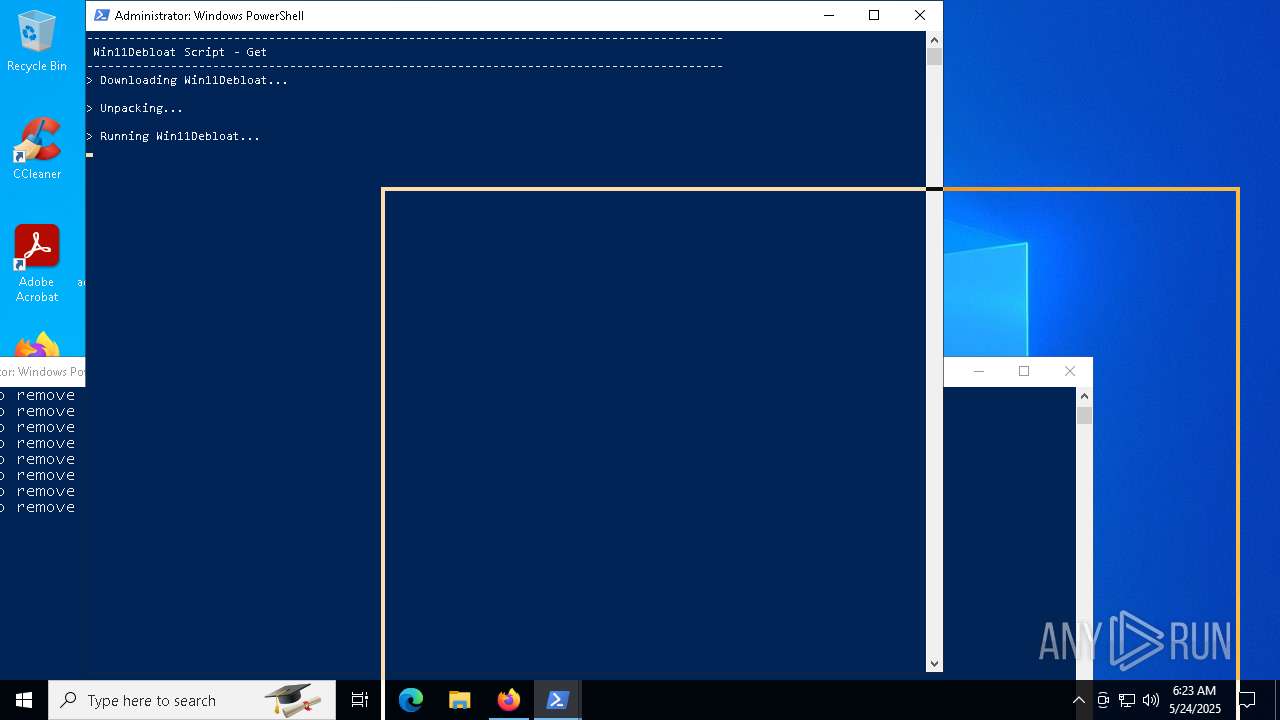
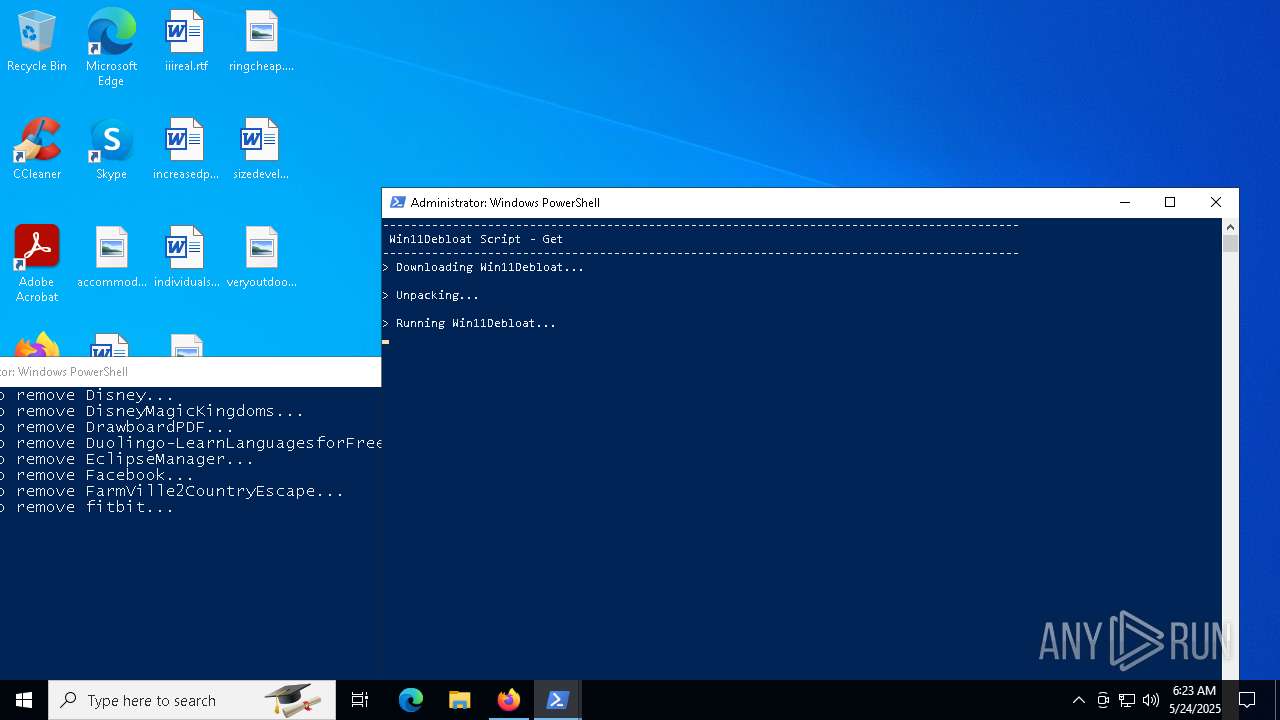
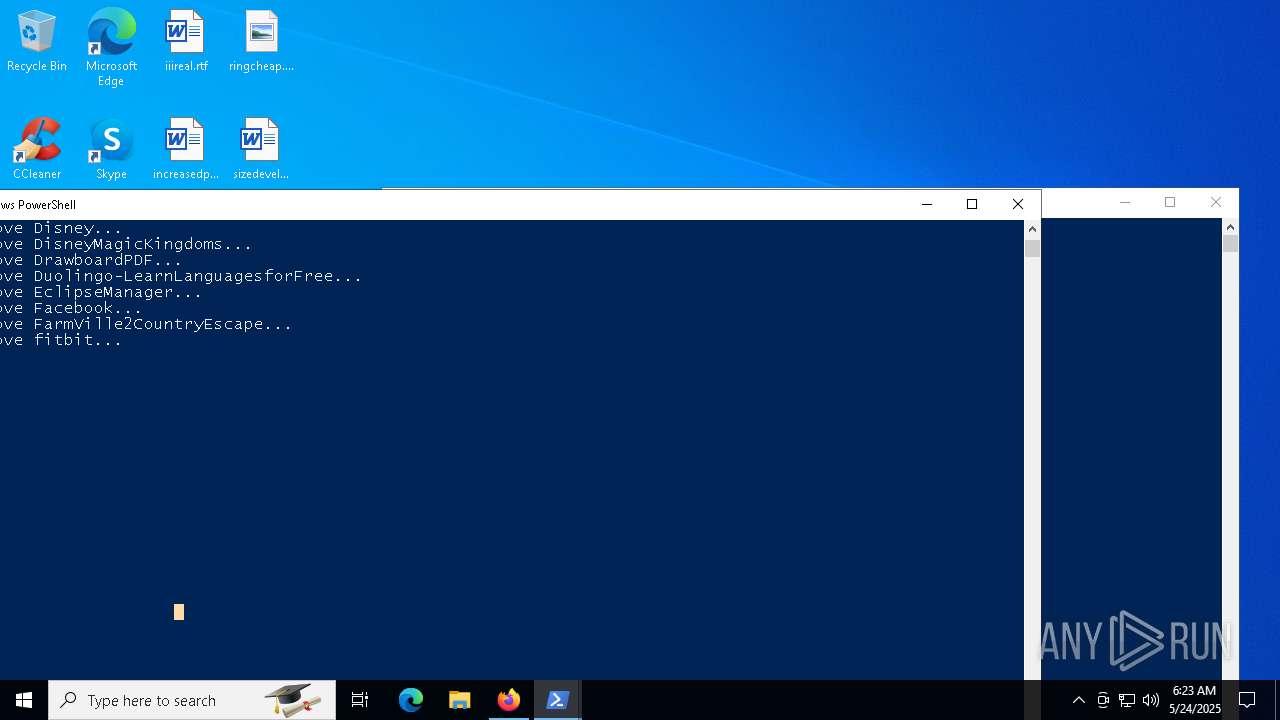
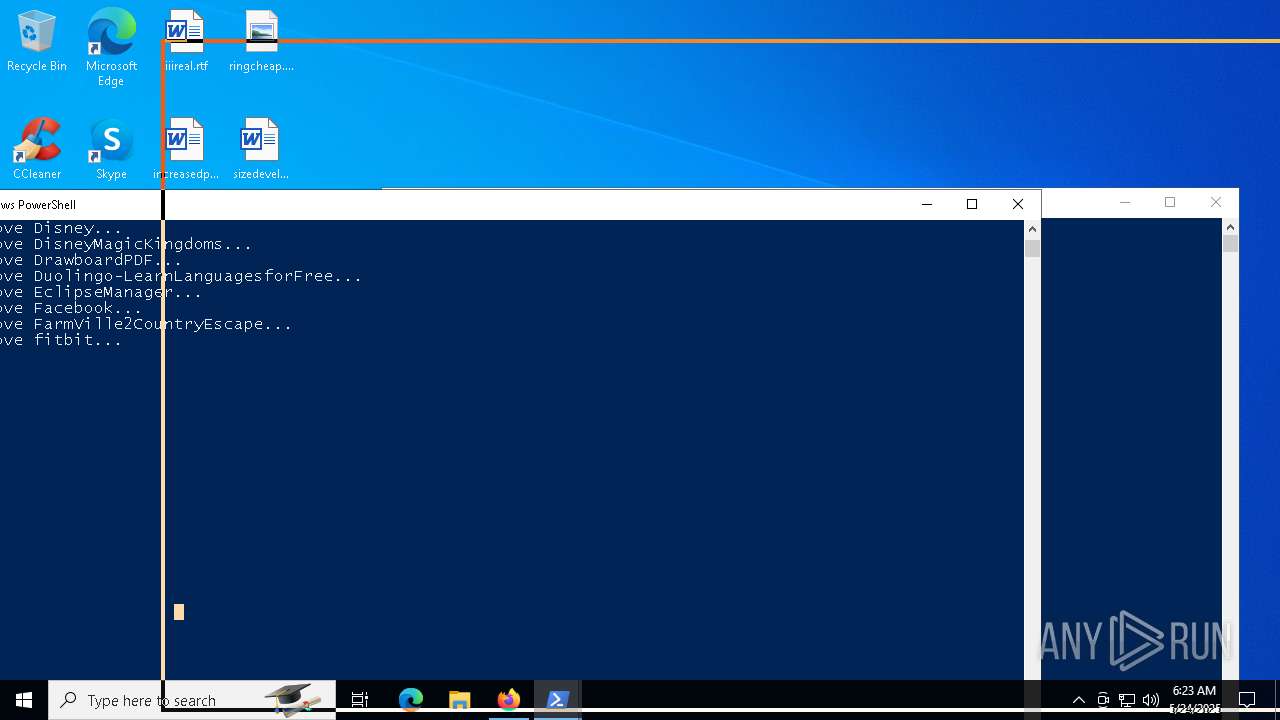
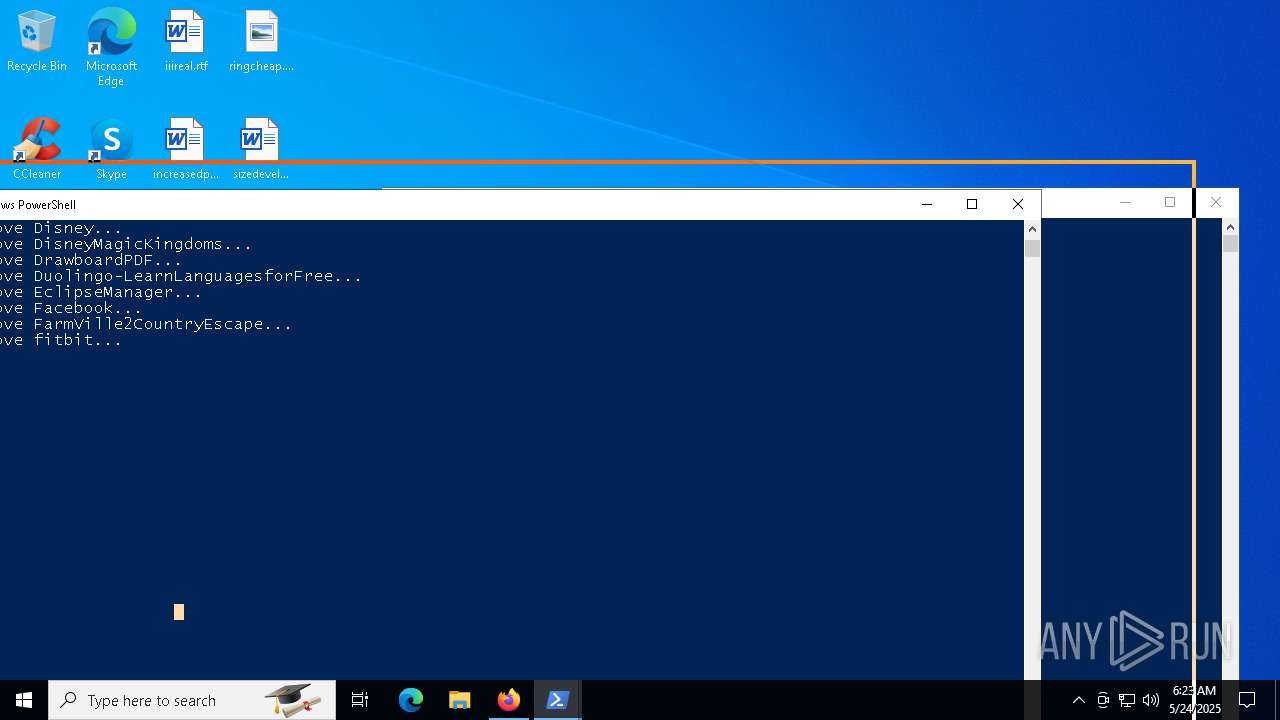
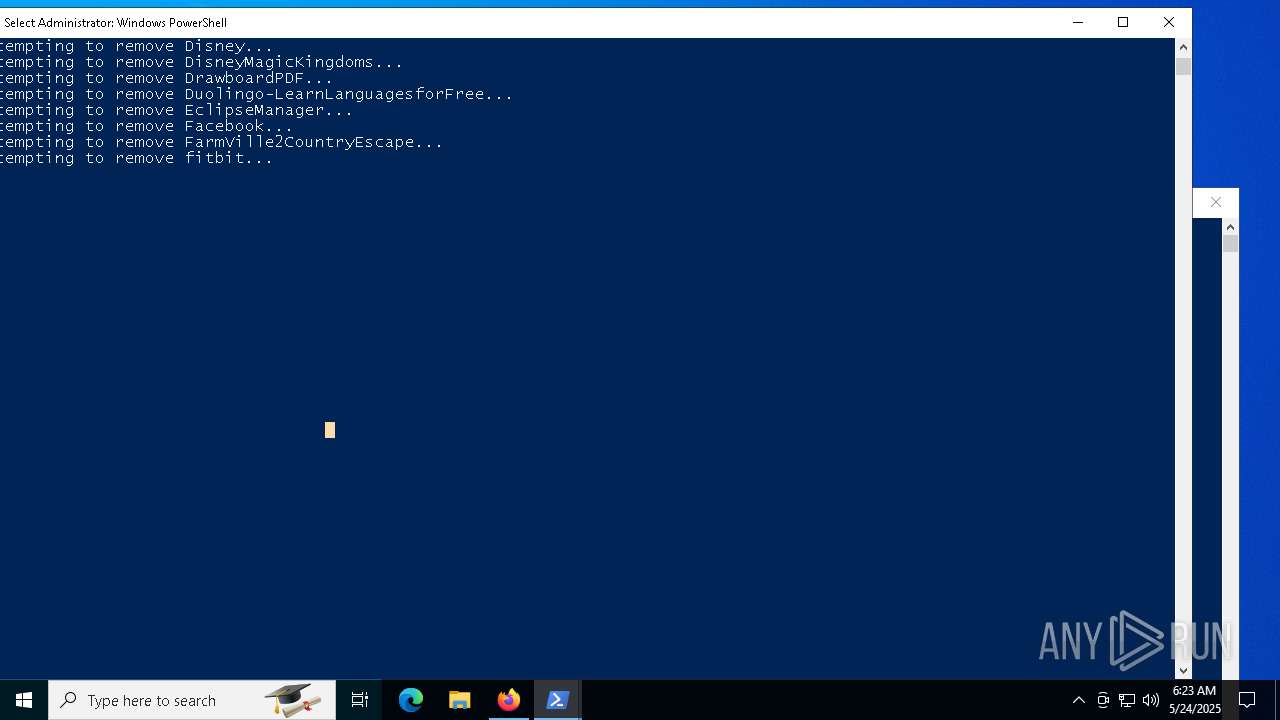
MALICIOUS
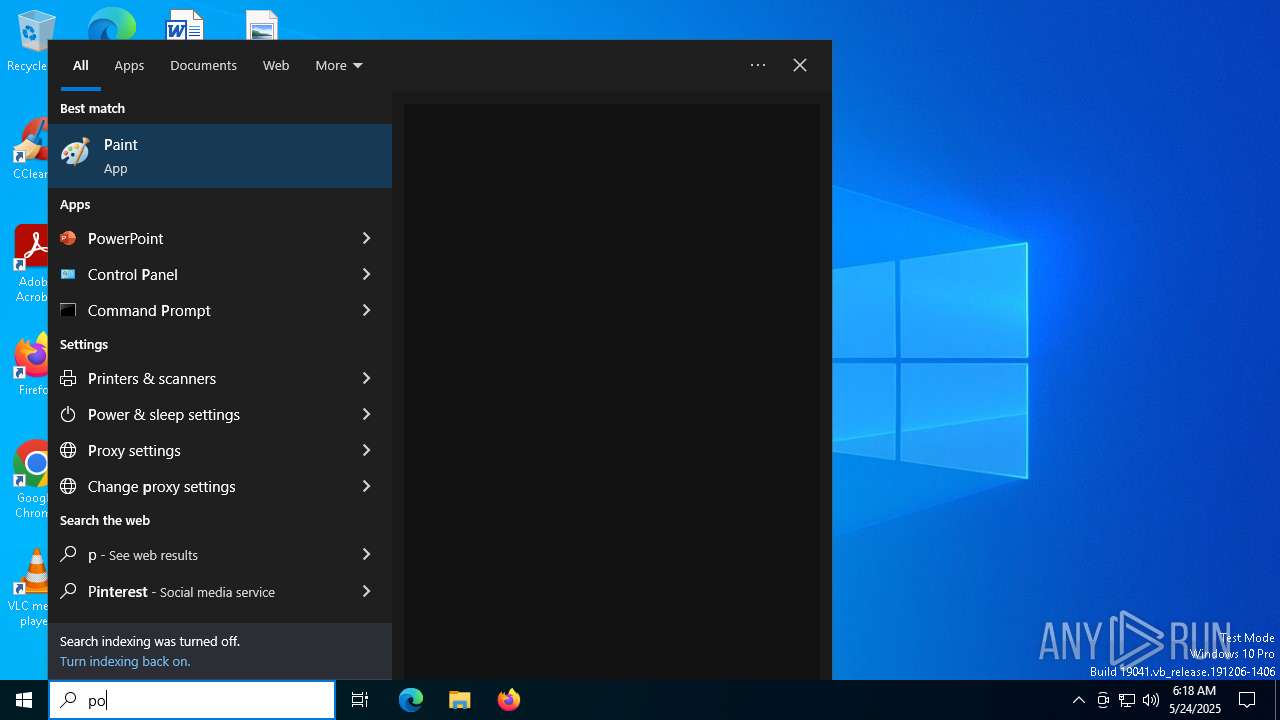
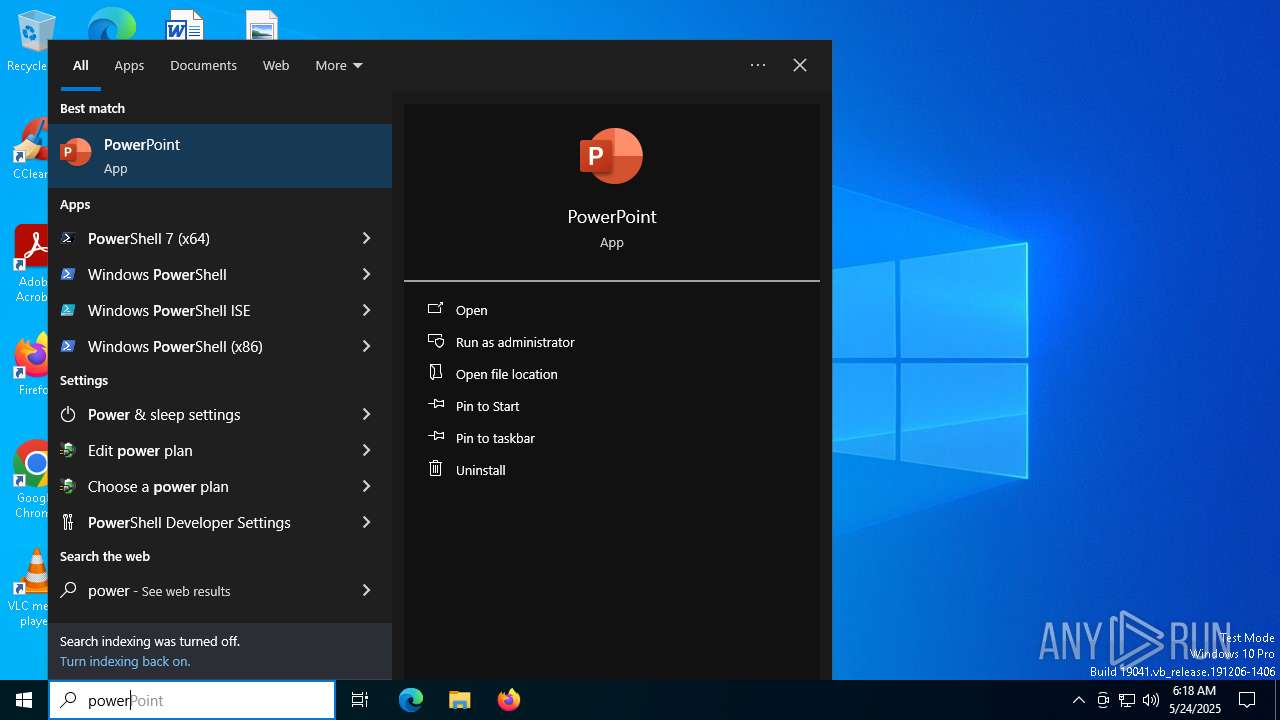
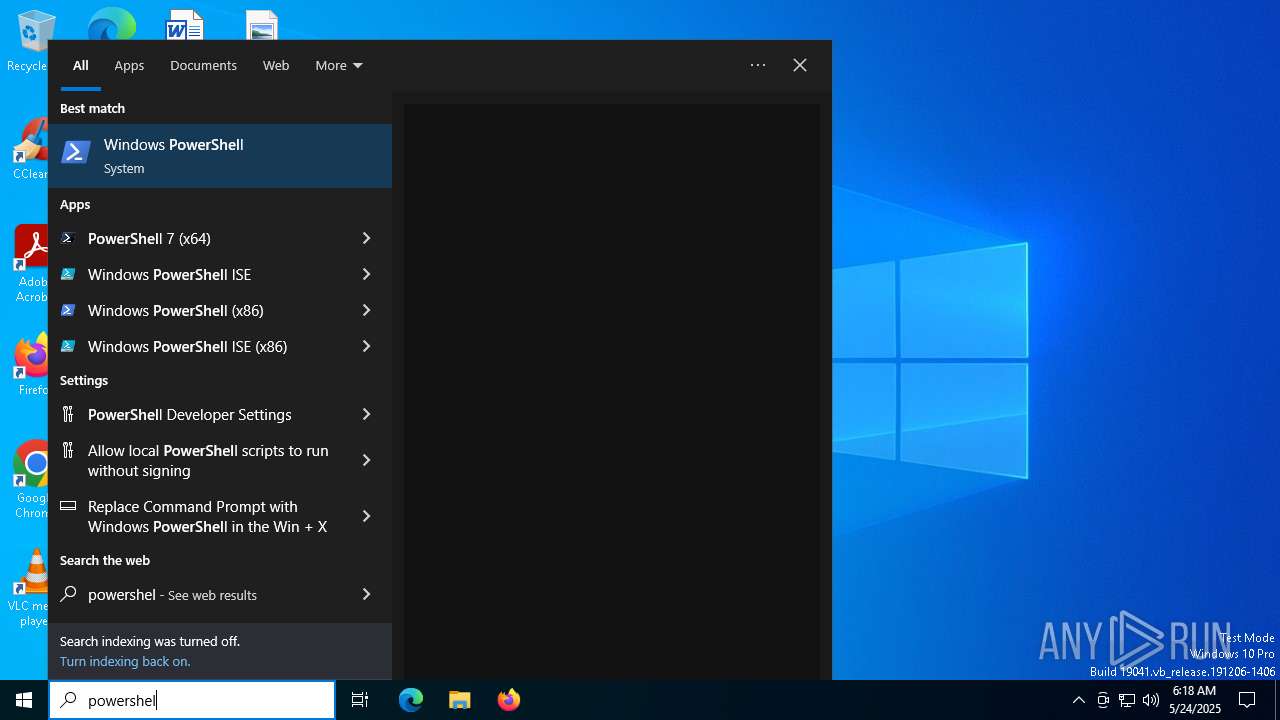
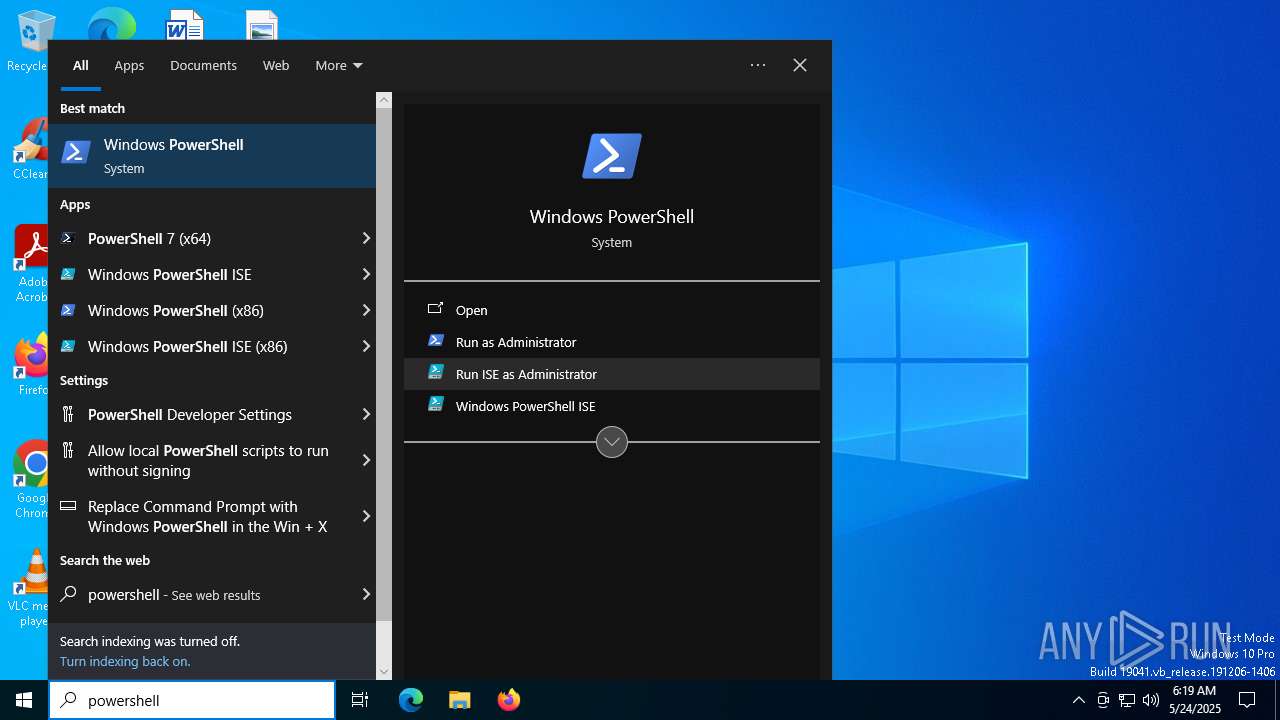
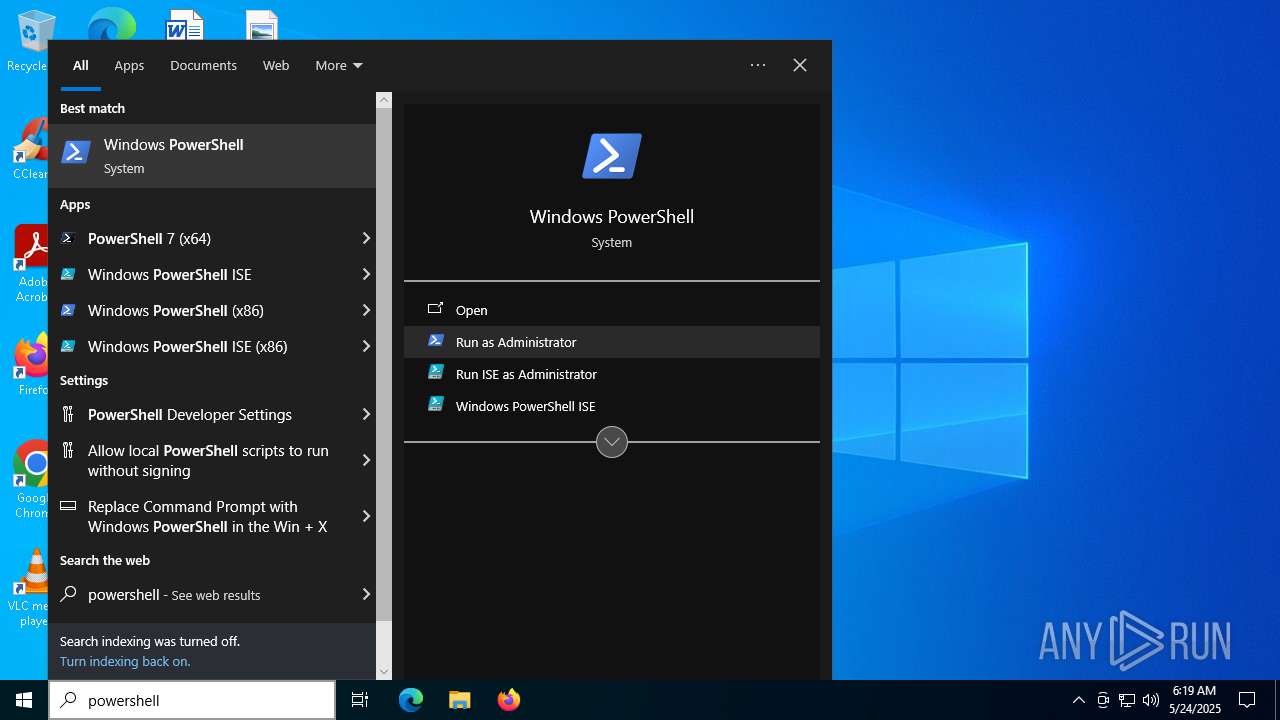
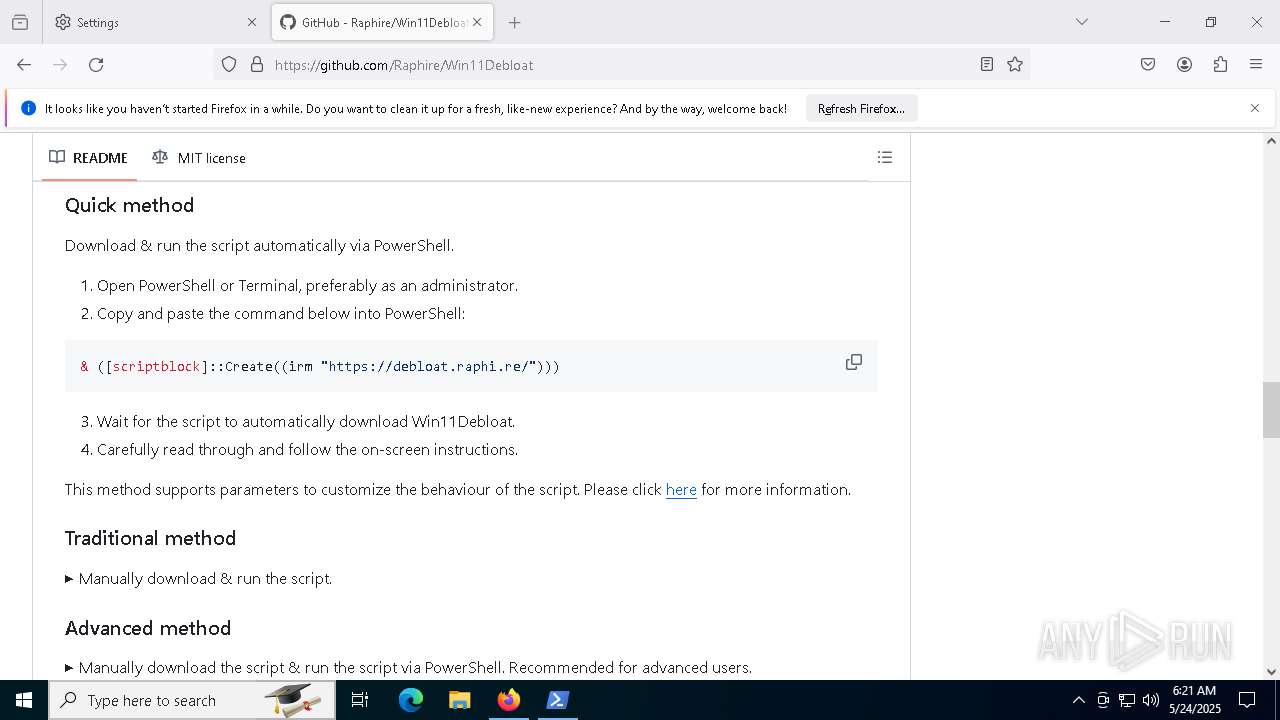
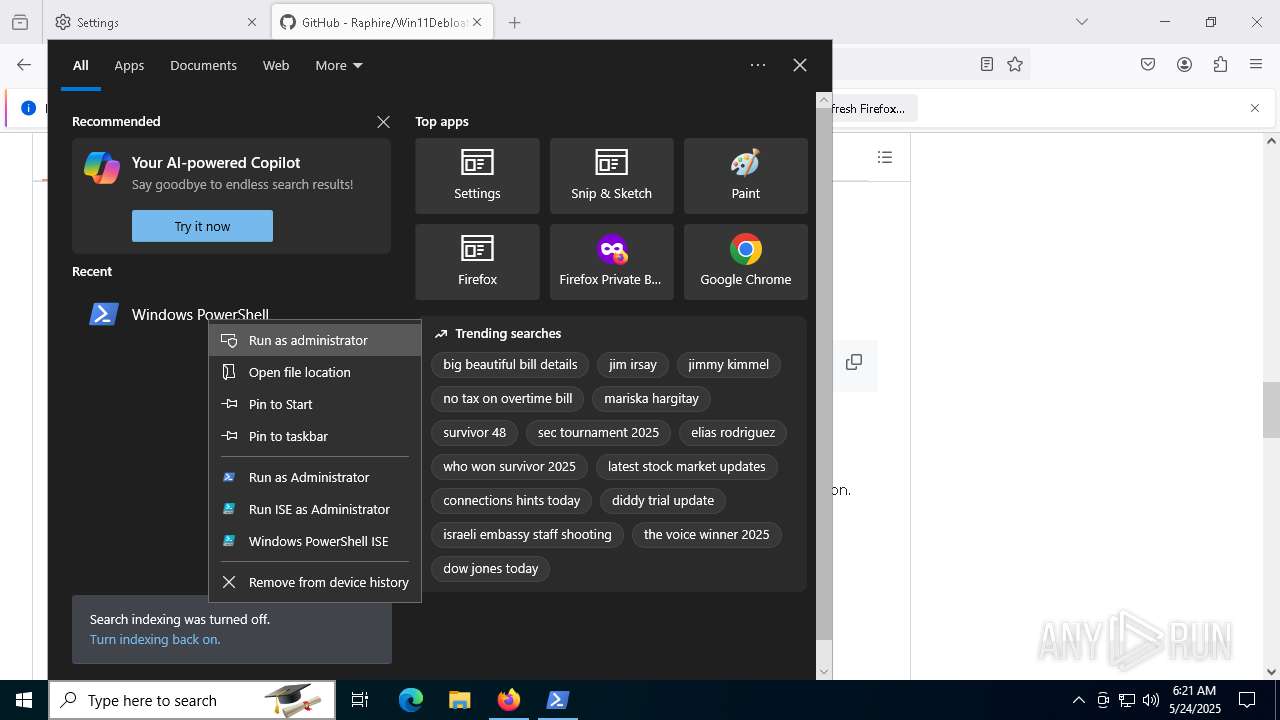
Bypass execution policy to execute commands
- powershell.exe (PID: 5256)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 5964)
Generic archive extractor
- WinRAR.exe (PID: 3020)
SUSPICIOUS
The process executes via Task Scheduler
- powershell.exe (PID: 8052)
Application launched itself
- powershell.exe (PID: 5964)
Executable content was dropped or overwritten
- powershell.exe (PID: 5256)
Process drops legitimate windows executable
- powershell.exe (PID: 5256)
The process executes Powershell scripts
- powershell.exe (PID: 5964)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 5964)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 7384)
- DismHost.exe (PID: 7376)
- DismHost.exe (PID: 7620)
- DismHost.exe (PID: 7000)
- DismHost.exe (PID: 2408)
- DismHost.exe (PID: 7372)
- DismHost.exe (PID: 6392)
- DismHost.exe (PID: 6768)
- DismHost.exe (PID: 4608)
- DismHost.exe (PID: 3968)
- DismHost.exe (PID: 7320)
- DismHost.exe (PID: 2968)
- DismHost.exe (PID: 6820)
- DismHost.exe (PID: 5172)
- DismHost.exe (PID: 2644)
- DismHost.exe (PID: 7560)
- DismHost.exe (PID: 5600)
- DismHost.exe (PID: 3124)
- DismHost.exe (PID: 6372)
INFO
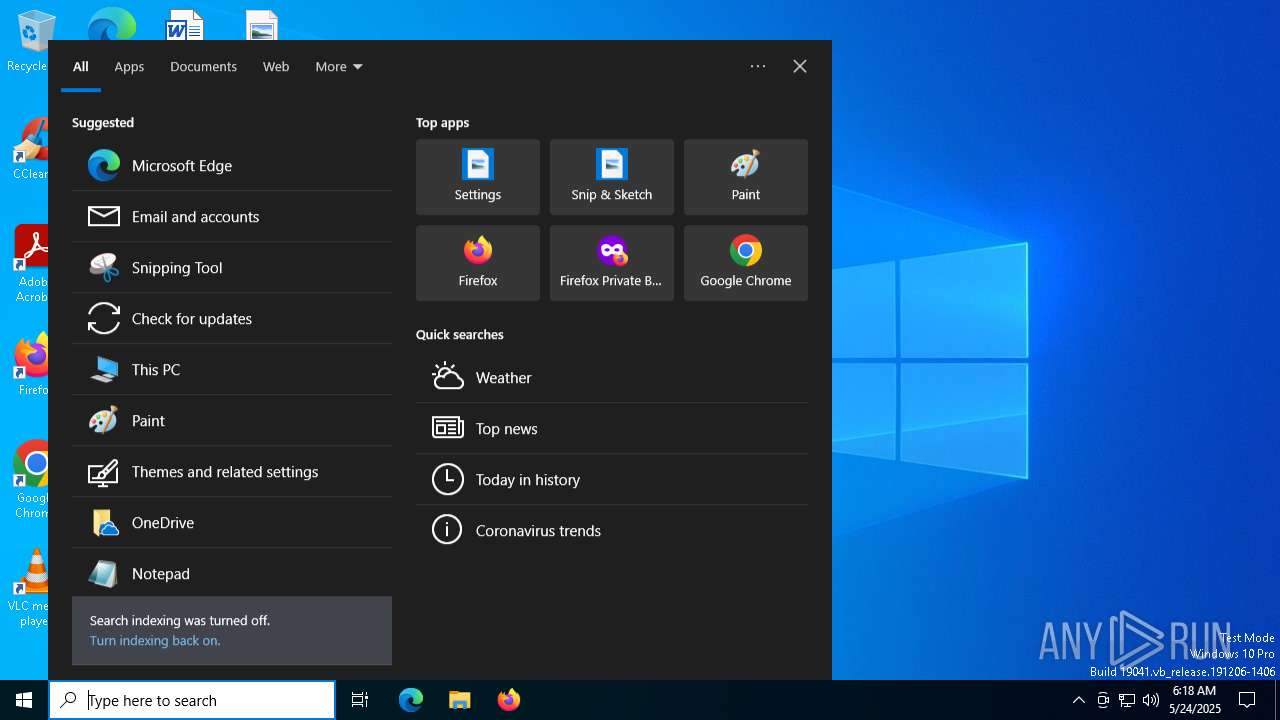
Checks current location (POWERSHELL)
- powershell.exe (PID: 8052)
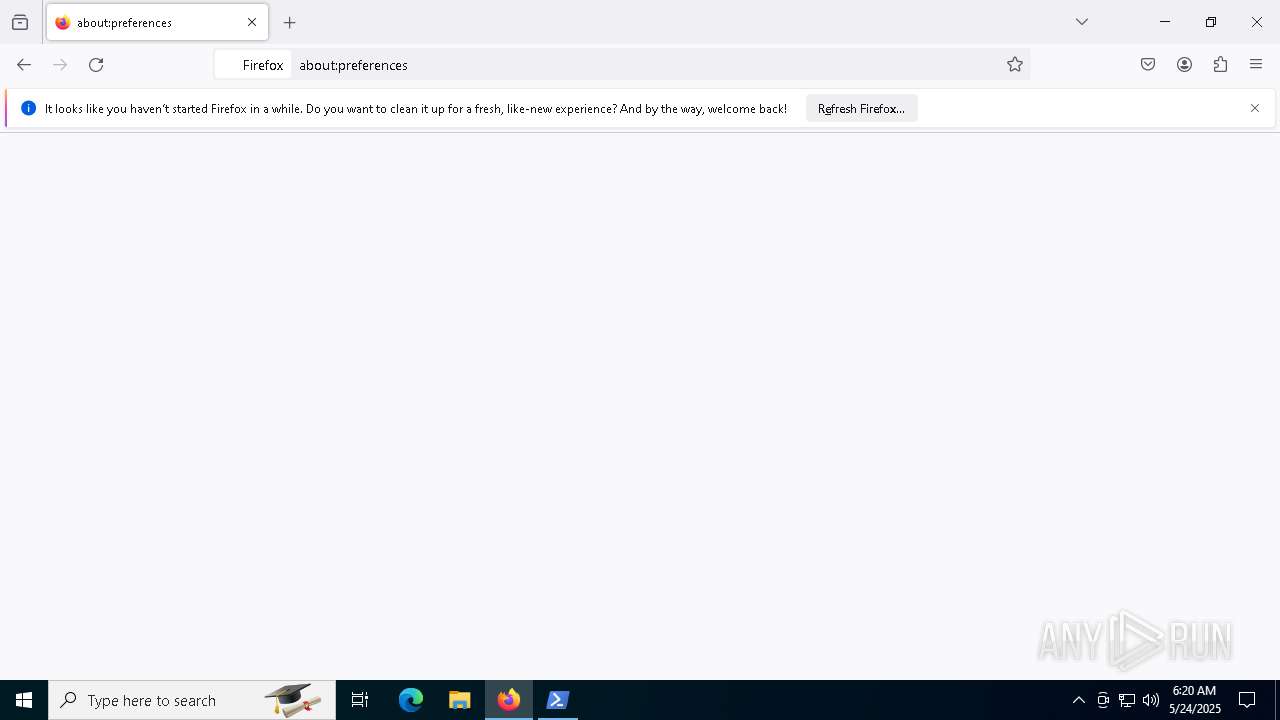
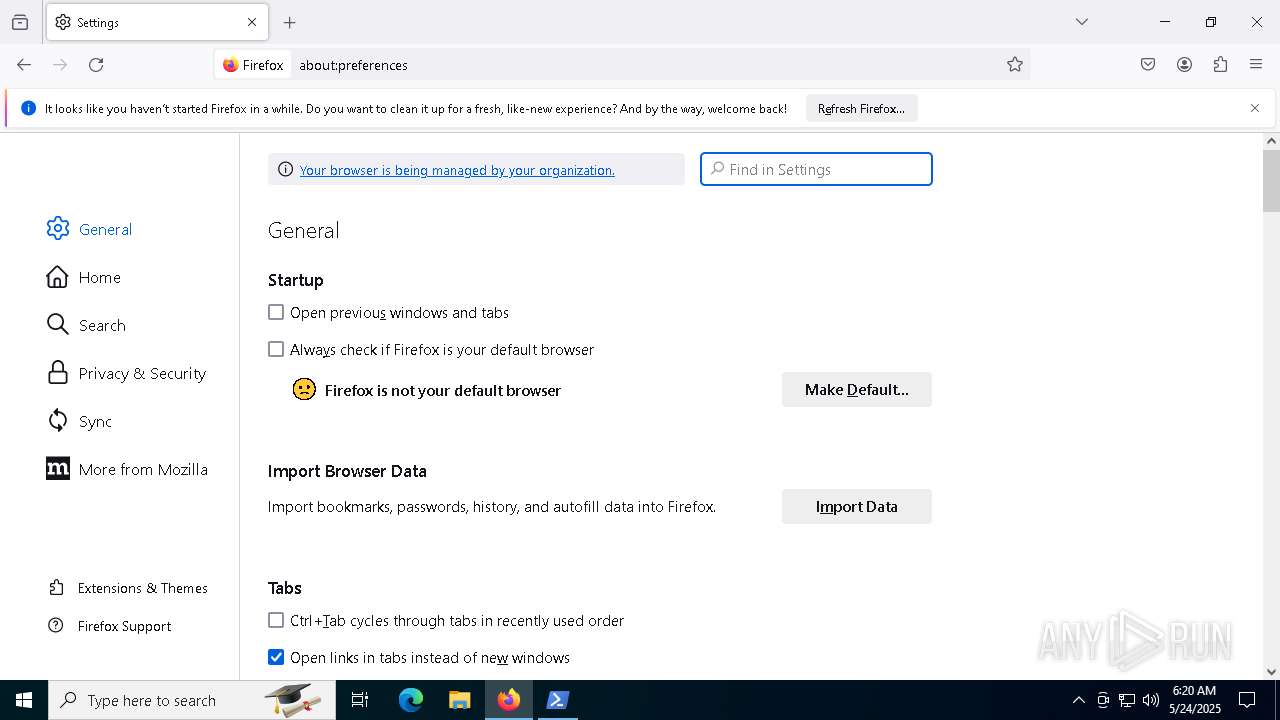
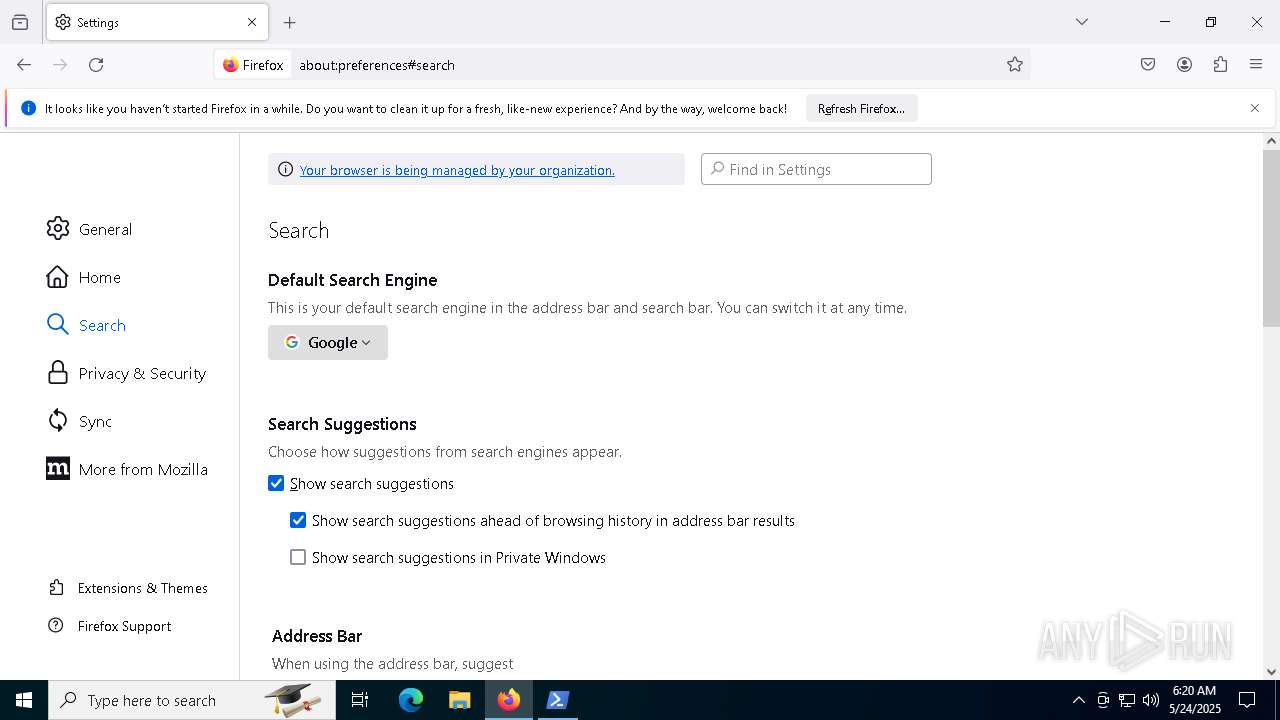
Application launched itself
- firefox.exe (PID: 5864)
- firefox.exe (PID: 7172)
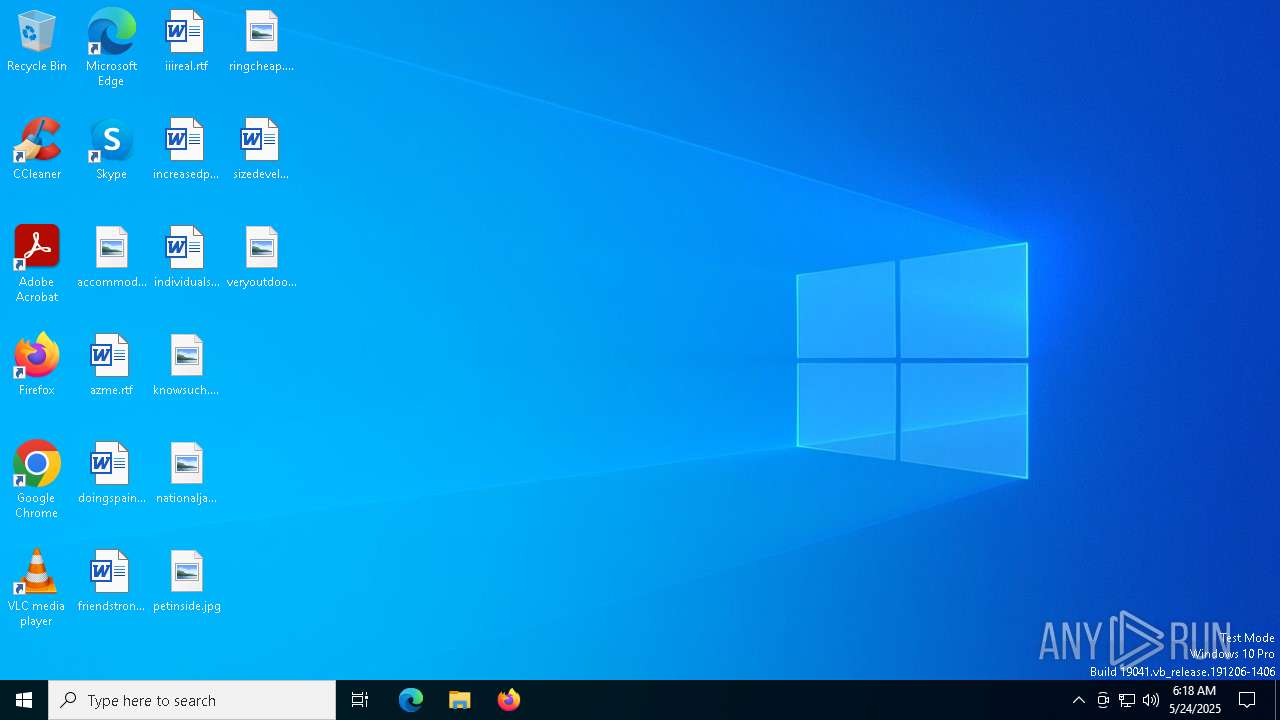
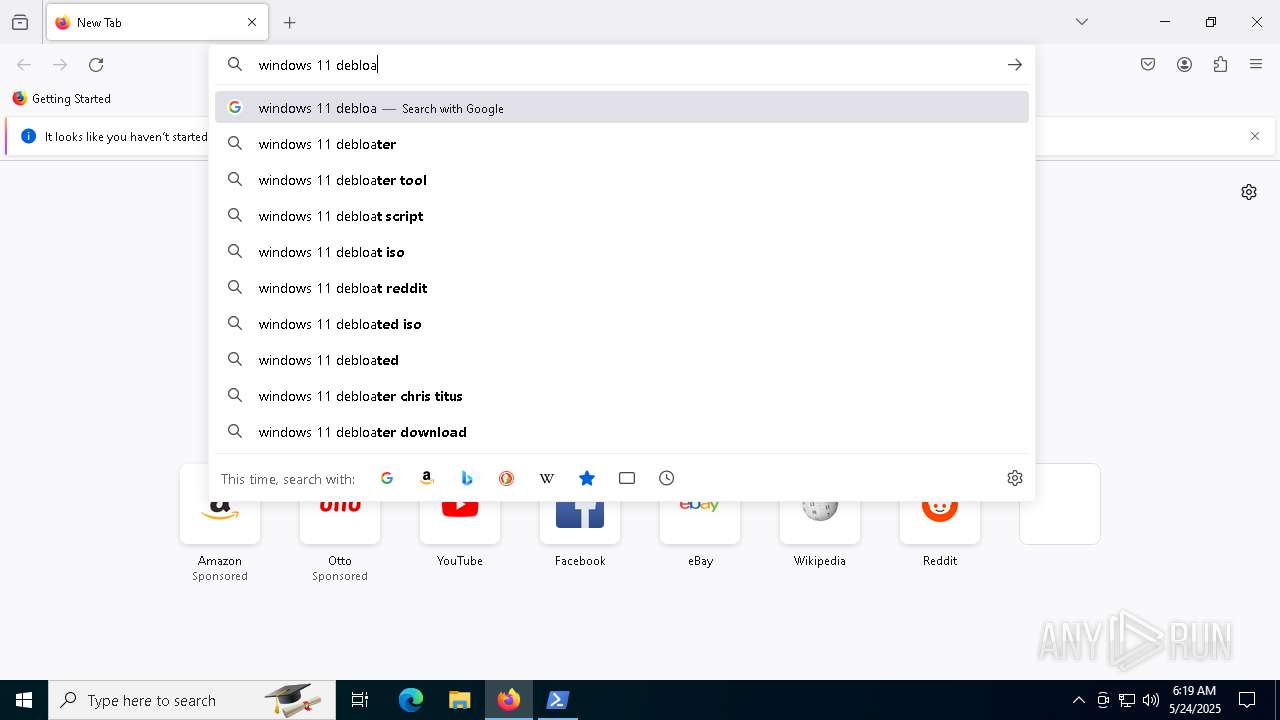
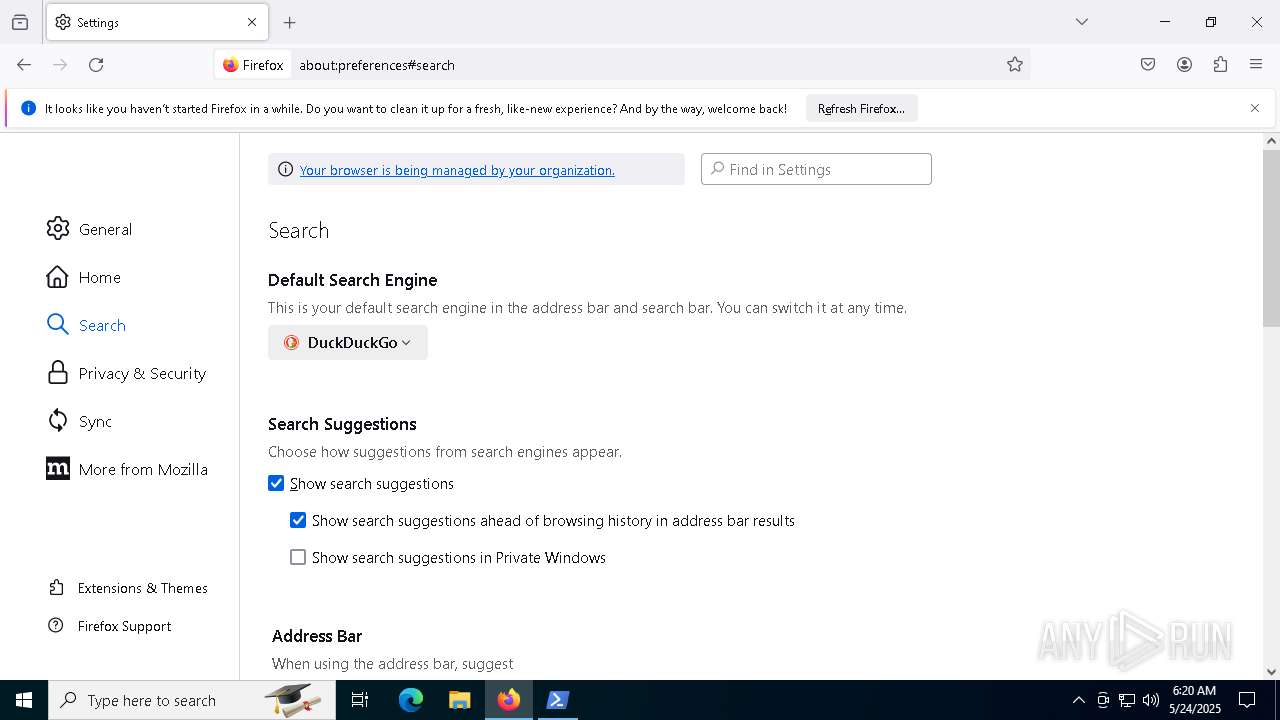
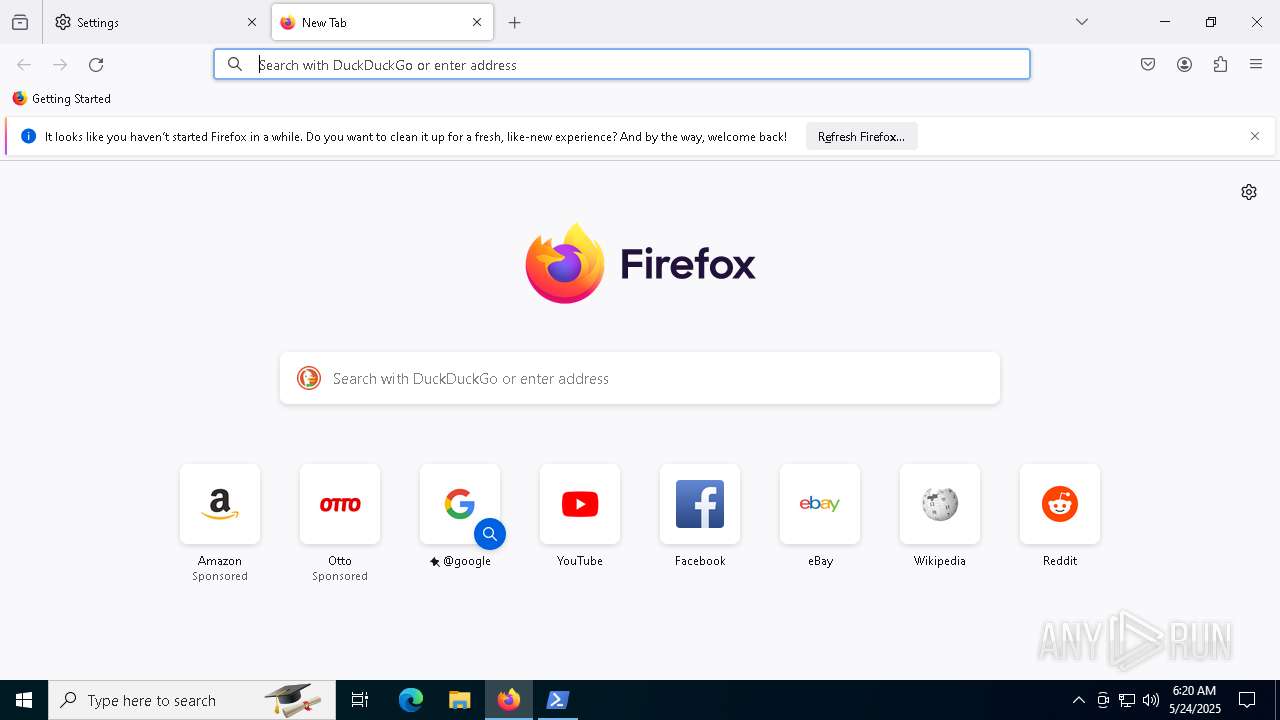
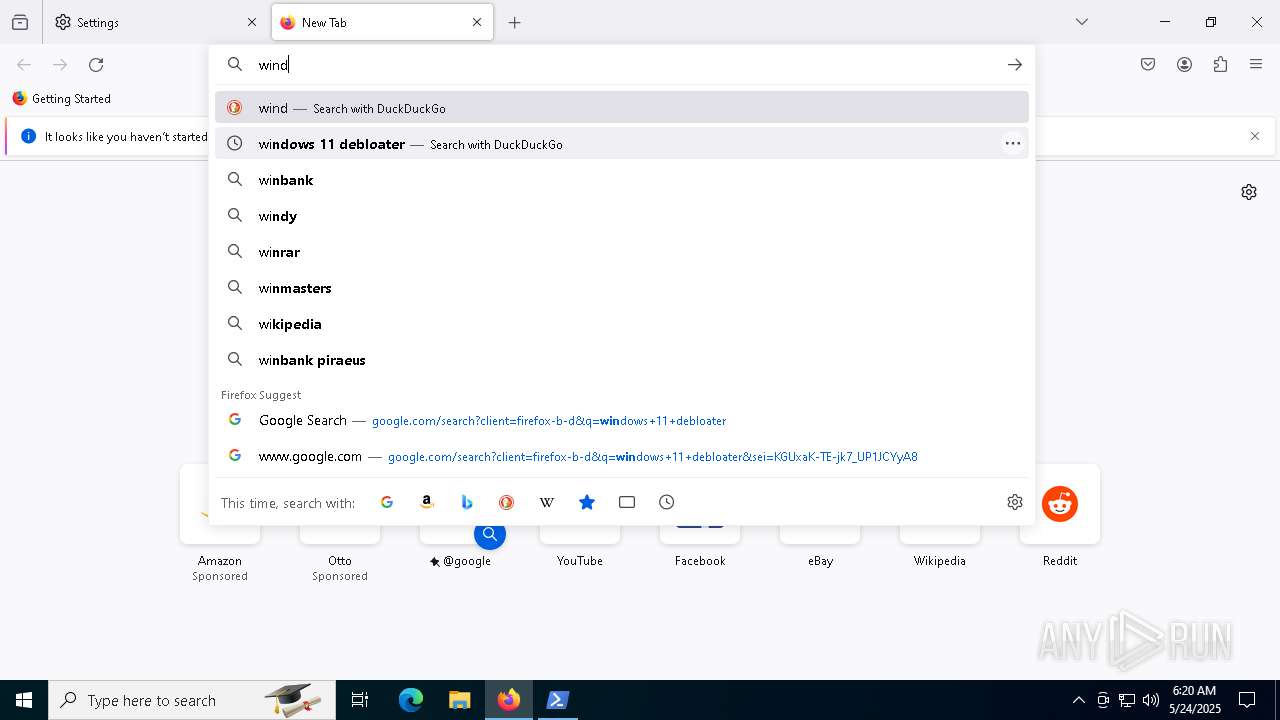
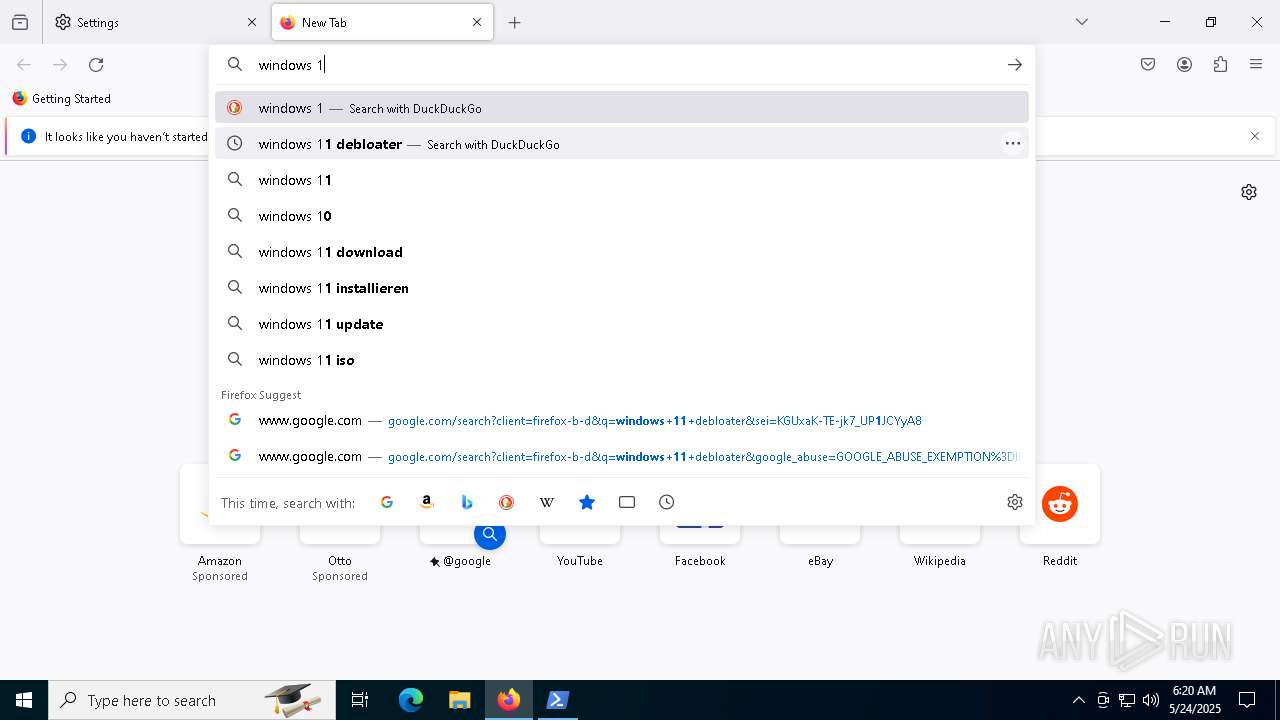
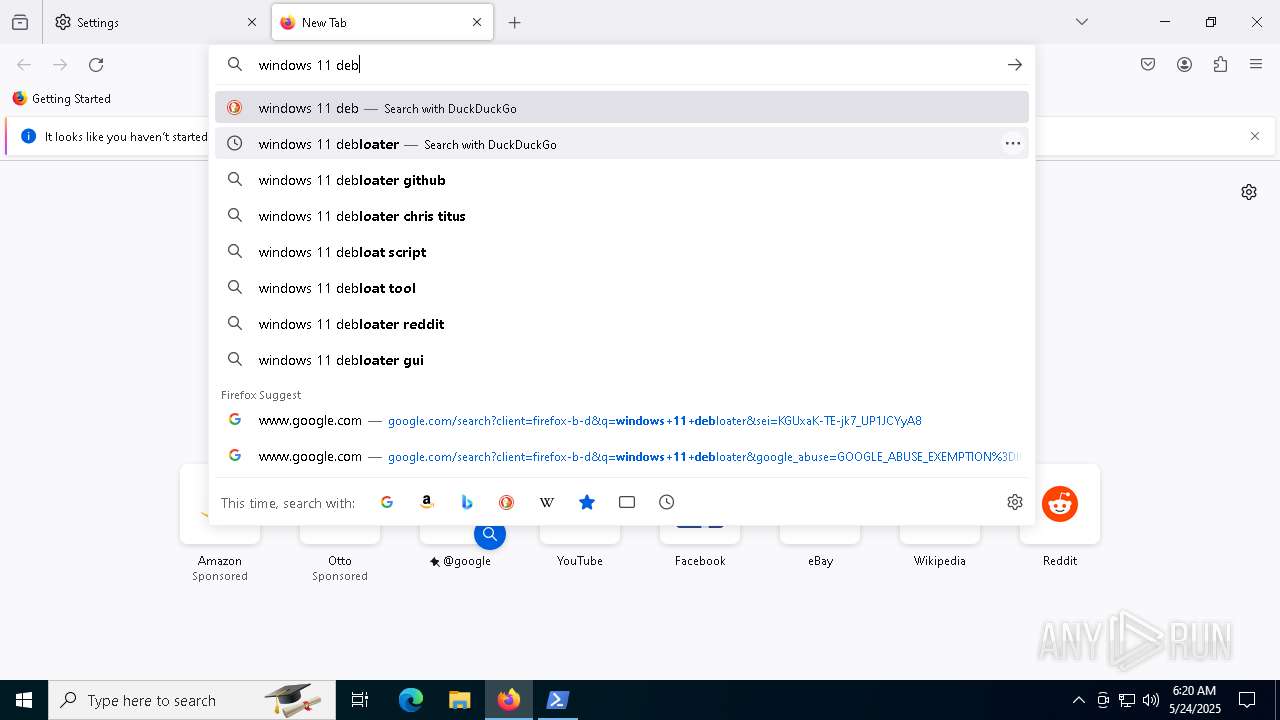
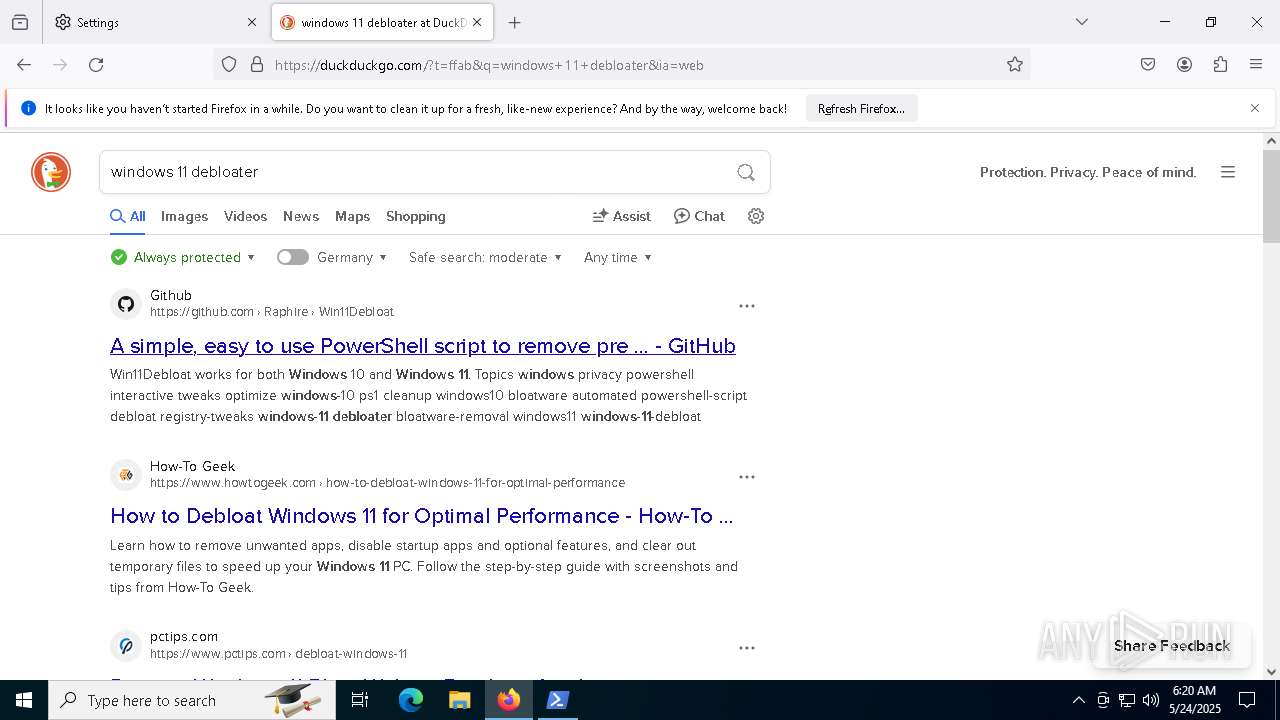
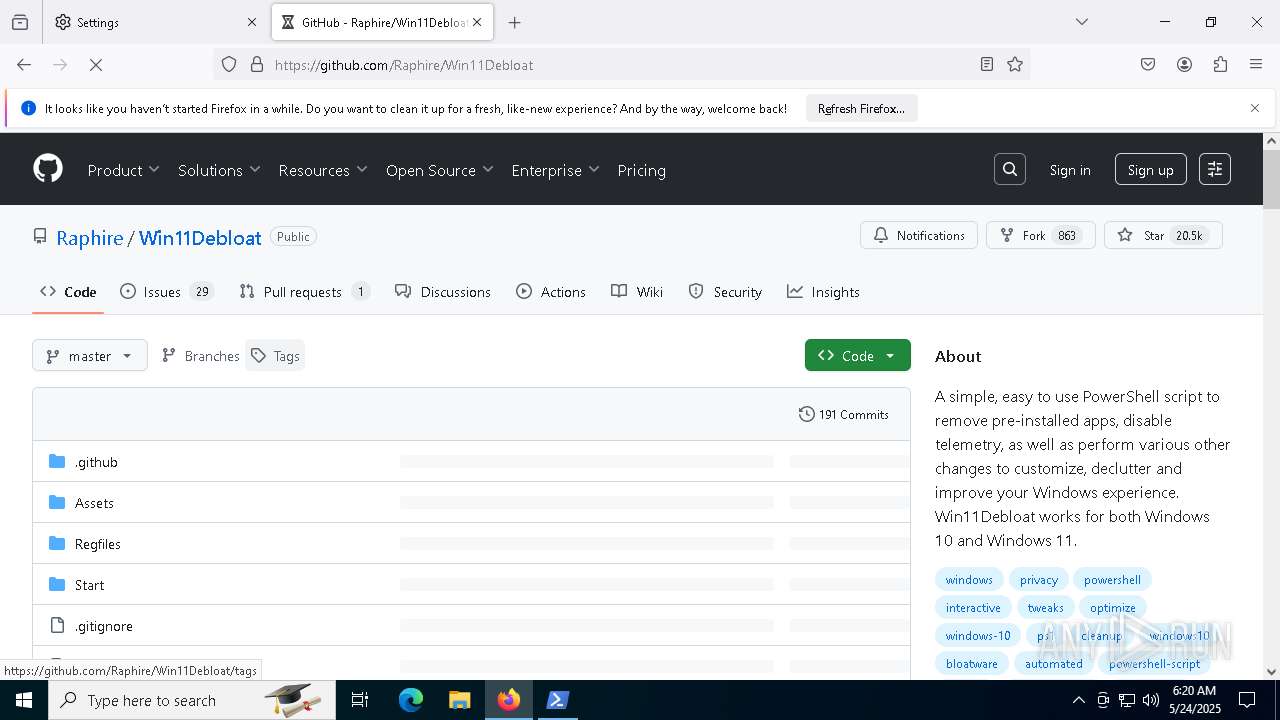
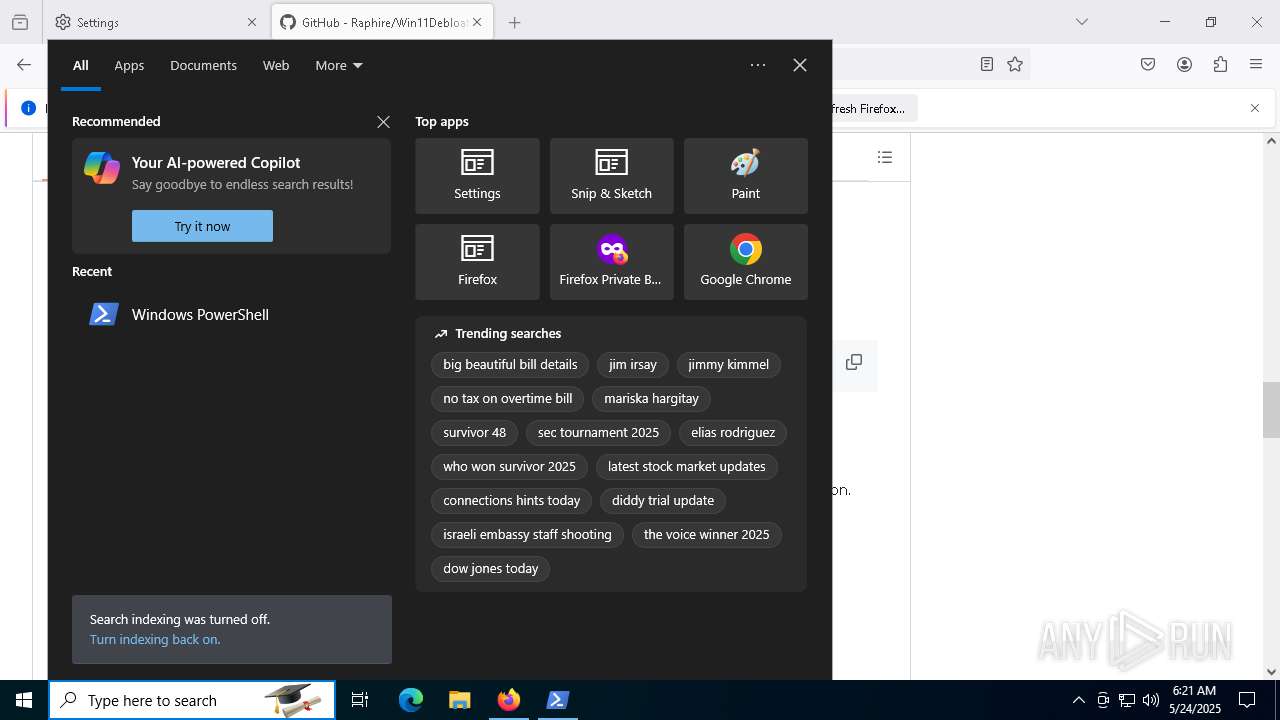
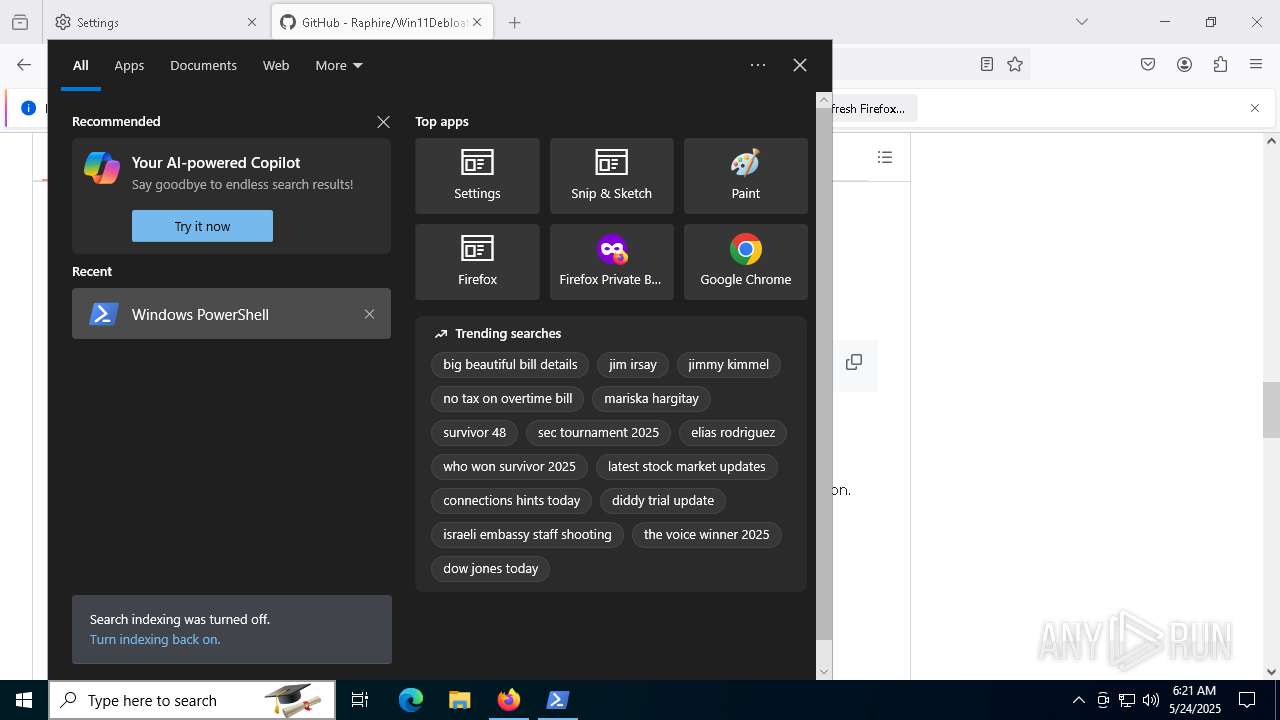
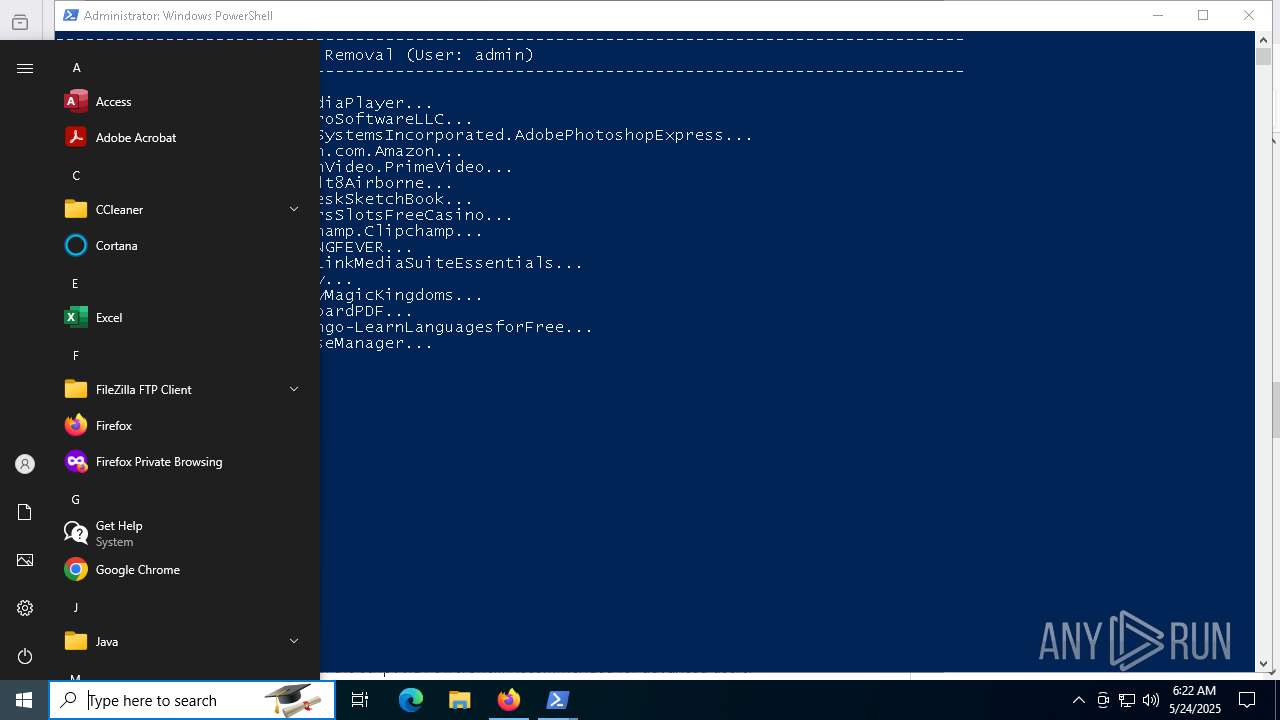
Manual execution by a user
- firefox.exe (PID: 5864)
- powershell.exe (PID: 5964)
Reads the software policy settings
- slui.exe (PID: 7264)
The sample compiled with english language support
- powershell.exe (PID: 5256)
The executable file from the user directory is run by the Powershell process
- DismHost.exe (PID: 7384)
- DismHost.exe (PID: 7376)
- DismHost.exe (PID: 3968)
- DismHost.exe (PID: 2968)
- DismHost.exe (PID: 6392)
- DismHost.exe (PID: 7372)
- DismHost.exe (PID: 4608)
- DismHost.exe (PID: 7620)
- DismHost.exe (PID: 6768)
- DismHost.exe (PID: 7320)
- DismHost.exe (PID: 7000)
- DismHost.exe (PID: 2408)
- DismHost.exe (PID: 6820)
- DismHost.exe (PID: 6372)
- DismHost.exe (PID: 2644)
- DismHost.exe (PID: 5172)
- DismHost.exe (PID: 7560)
- DismHost.exe (PID: 5600)
- DismHost.exe (PID: 3124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:06:26 20:39:20 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Windows10Debloater-master/ |
Total processes
179
Monitored processes
43
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5088 -childID 3 -isForBrowser -prefsHandle 5104 -prefMapHandle 4392 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1536 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {96ee844d-ca35-41ea-bf29-58f1768d3d72} 7172 "\\.\pipe\gecko-crash-server-pipe.7172" 243161cfd90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2408 | C:\Users\admin\AppData\Local\Temp\4EB8764D-FBF0-4793-955B-1F5BE6F55E9F\dismhost.exe {7A1787C4-5B2C-47F5-9614-D62E2AFD1A81} | C:\Users\admin\AppData\Local\Temp\4EB8764D-FBF0-4793-955B-1F5BE6F55E9F\DismHost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | C:\Users\admin\AppData\Local\Temp\0D1AFCBE-D7C1-4F9D-BF38-16CB61E1C014\dismhost.exe {32FE4A08-DA76-452E-98D5-788ED9622D30} | C:\Users\admin\AppData\Local\Temp\0D1AFCBE-D7C1-4F9D-BF38-16CB61E1C014\DismHost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2968 | C:\Users\admin\AppData\Local\Temp\B2A35395-9C42-4361-9ACC-EAF4BBA1674E\dismhost.exe {7707C6C8-75C7-4935-A7E7-79387327E058} | C:\Users\admin\AppData\Local\Temp\B2A35395-9C42-4361-9ACC-EAF4BBA1674E\DismHost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3020 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Windows10Debloater-master.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3124 | C:\Users\admin\AppData\Local\Temp\98F2BAE0-CAF0-4BC1-ADE9-37DAE2559AD9\dismhost.exe {C2DB344C-AF63-44BC-8A50-1F1E859B21E3} | C:\Users\admin\AppData\Local\Temp\98F2BAE0-CAF0-4BC1-ADE9-37DAE2559AD9\DismHost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3968 | C:\Users\admin\AppData\Local\Temp\27DB679B-A9F0-45C3-BD23-9E82050CE561\dismhost.exe {3ADF142B-B435-4E78-A72D-90E1345339D1} | C:\Users\admin\AppData\Local\Temp\27DB679B-A9F0-45C3-BD23-9E82050CE561\DismHost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4068 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4332 -childID 2 -isForBrowser -prefsHandle 4328 -prefMapHandle 4324 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1536 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {9b910eb4-3f3f-44c7-930c-8885cf515ce1} 7172 "\\.\pipe\gecko-crash-server-pipe.7172" 2431326d4d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4164 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6328 -childID 8 -isForBrowser -prefsHandle 6368 -prefMapHandle 6364 -prefsLen 31605 -prefMapSize 244583 -jsInitHandle 1536 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {fe70e83c-c2f5-44fa-8376-c2dc9e36483e} 7172 "\\.\pipe\gecko-crash-server-pipe.7172" 24314b224d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4608 | C:\Users\admin\AppData\Local\Temp\7660DFEB-16E2-4B26-92D9-50FA6DBB2F2D\dismhost.exe {BCFA13C9-D0C0-431C-A68B-C97029590751} | C:\Users\admin\AppData\Local\Temp\7660DFEB-16E2-4B26-92D9-50FA6DBB2F2D\DismHost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
41 422
Read events
41 413
Write events
9
Delete events
0
Modification events
| (PID) Process: | (3020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Windows10Debloater-master.zip | |||
| (PID) Process: | (3020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7172) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
Executable files
950
Suspicious files
220
Text files
165
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7172 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 8052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10e32e.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7172 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 8052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:F10390AE5A600584B5143EE76ACF6C57 | SHA256:E1290A3397955C24F6FD965D183915B1F3354CE42702980828616B08BA95A114 | |||
| 8052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zofh3rh5.h3b.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ypn5x3ci.tlj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2BB27B70770BD2F897DF4EE2CA0BF4DB | SHA256:AD8FE0AF9F19FAE6CD564B9C037B1D646168A1BF858A7FDCE5B42605753D3E9C | |||
| 7172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
172
DNS requests
211
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 304 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7172 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
1324 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7172 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1324 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.204.155:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2924 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
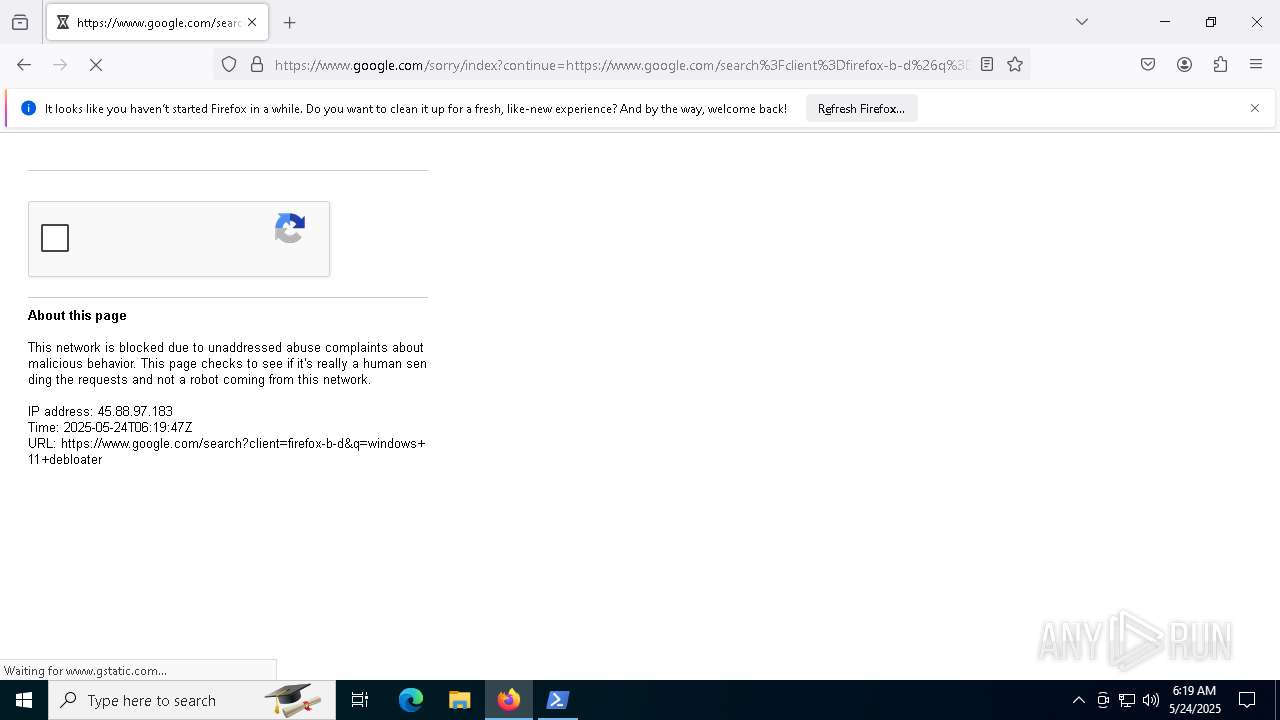
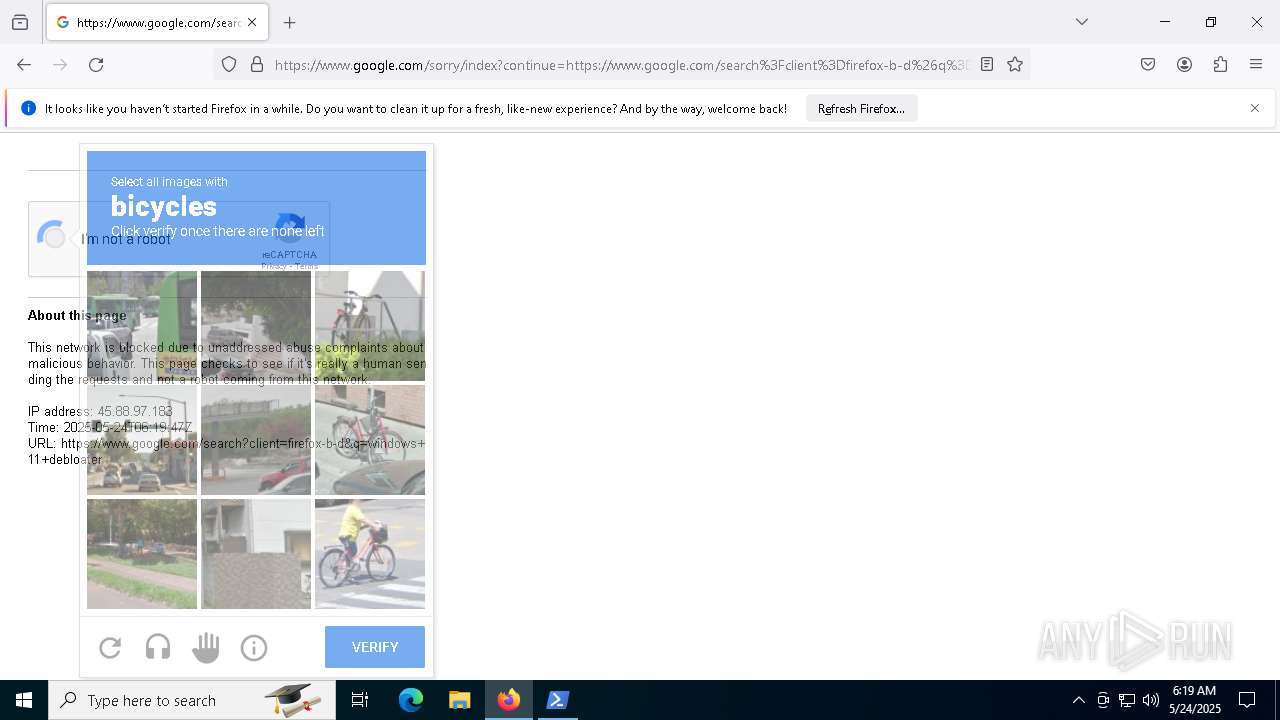
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
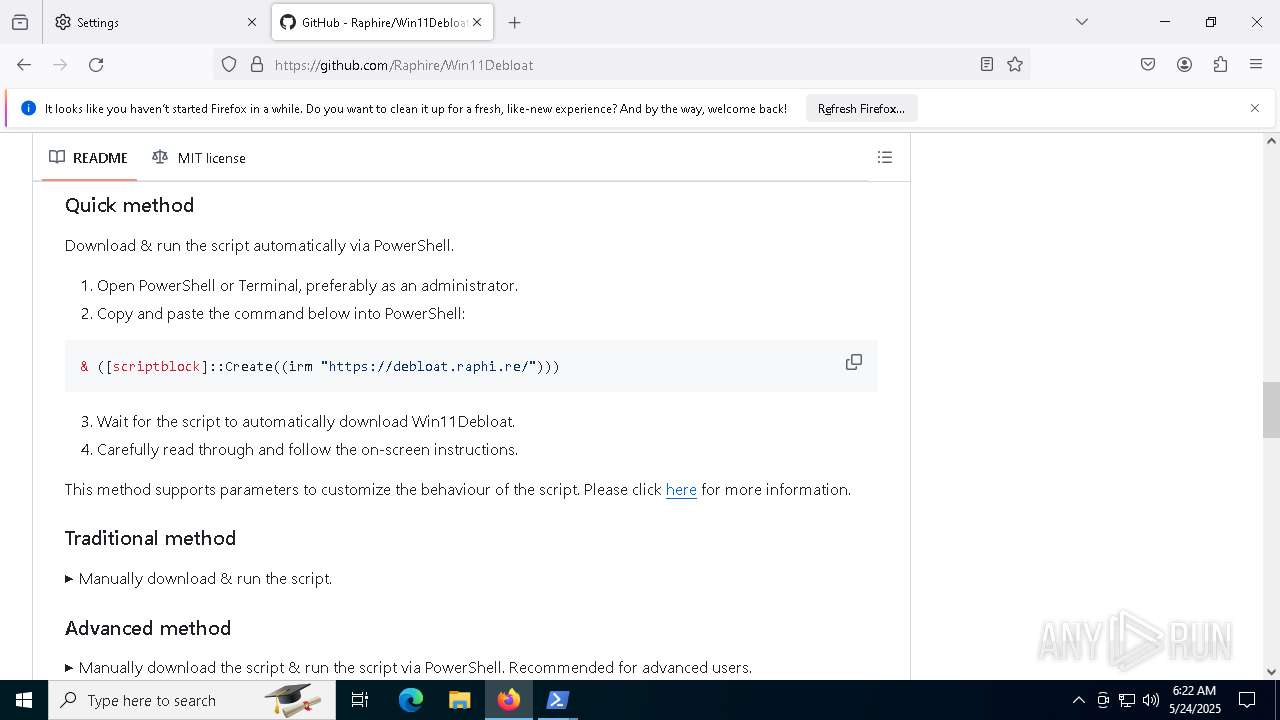
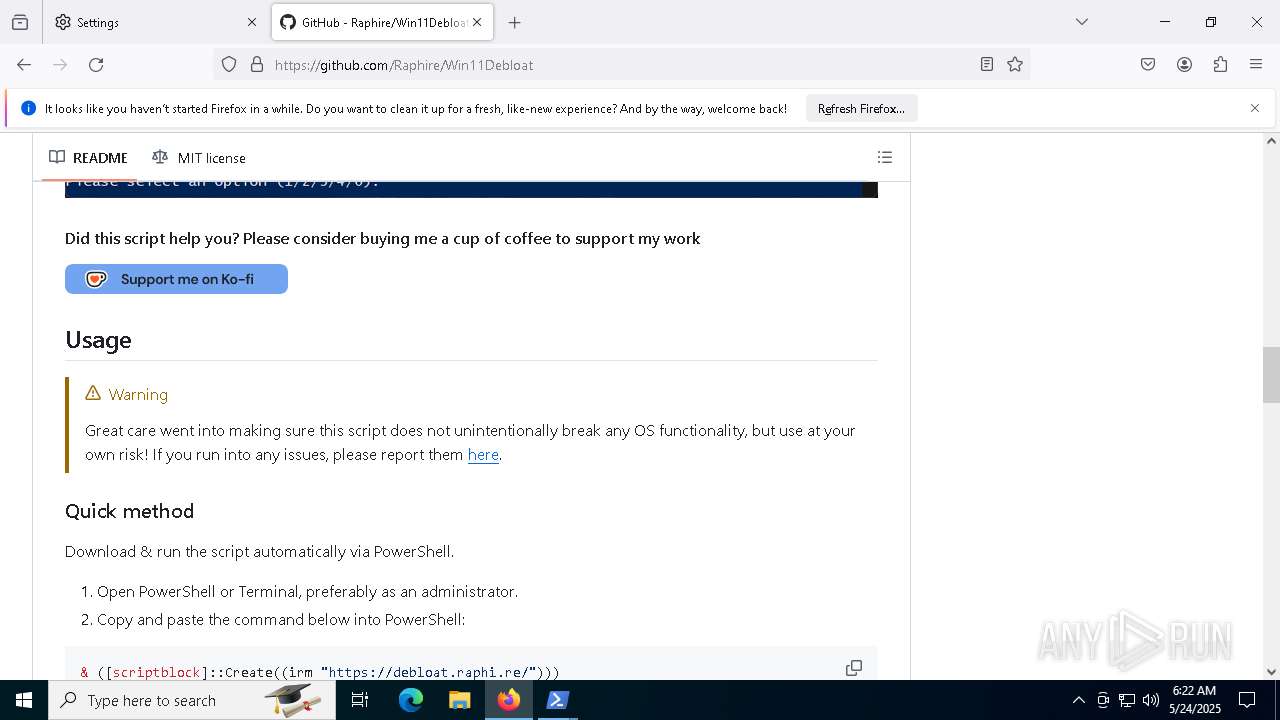
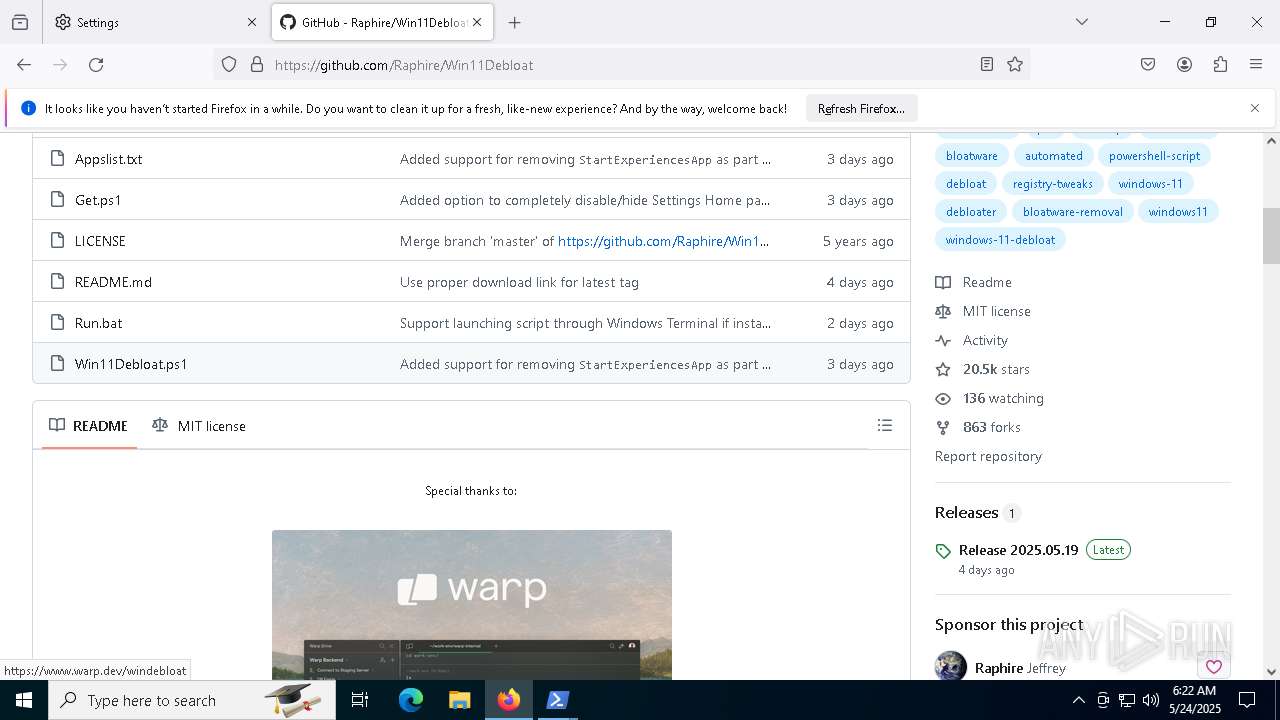
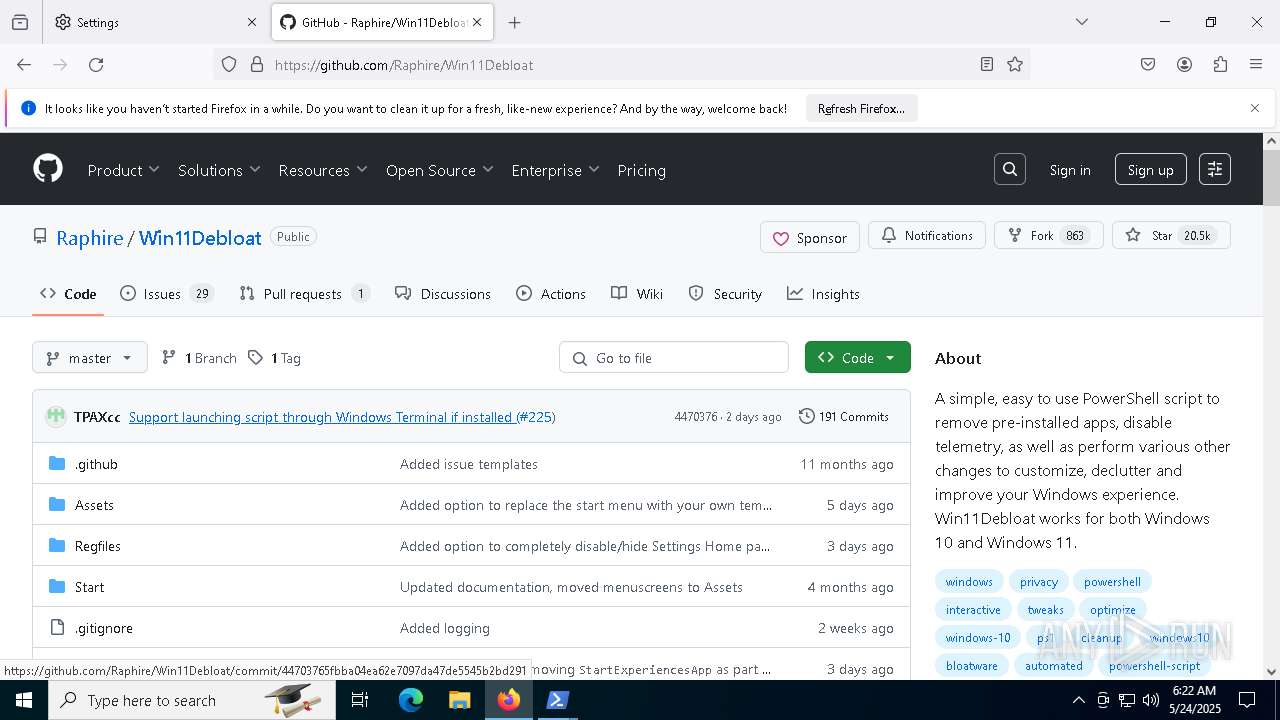
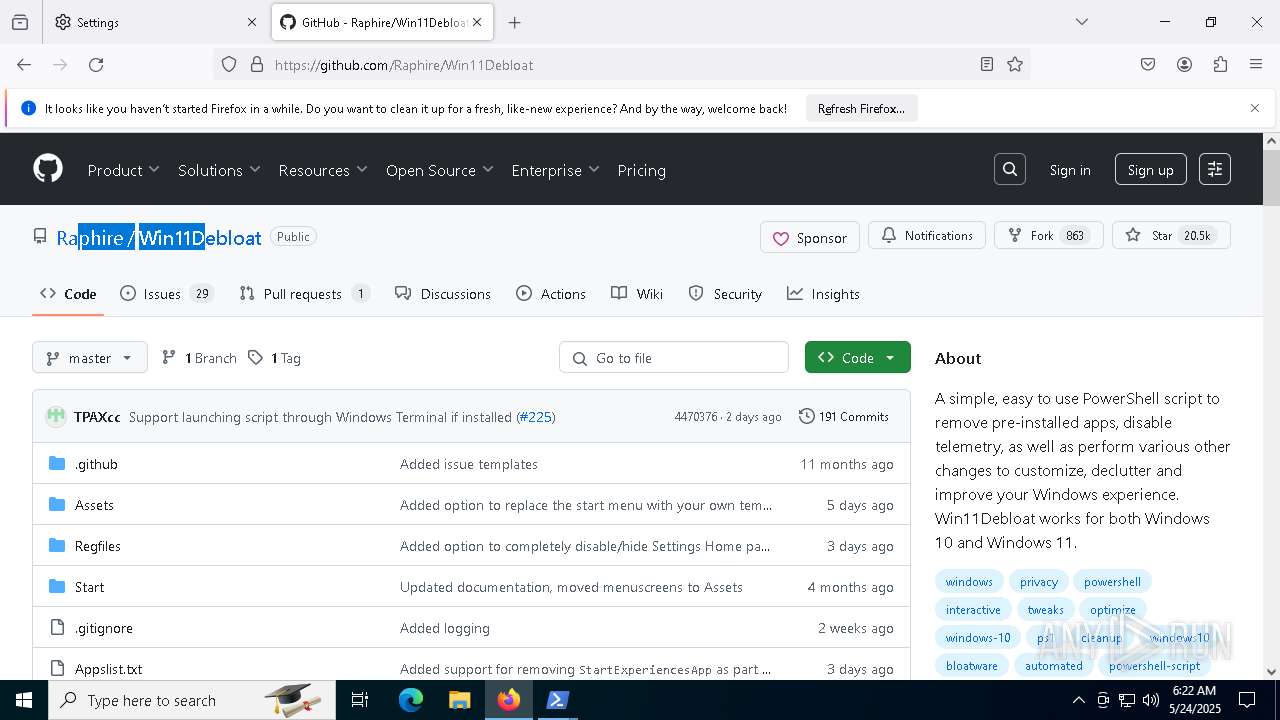
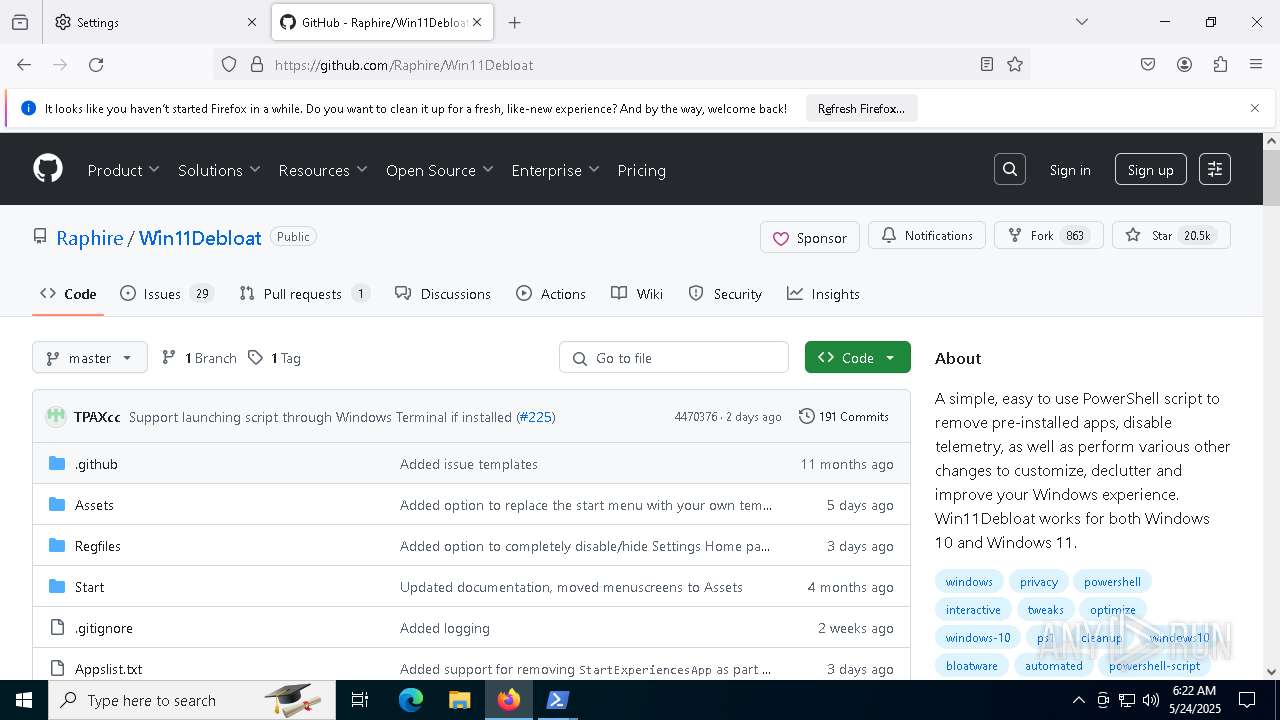
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |