| File name: | fa_rss.exe |
| Full analysis: | https://app.any.run/tasks/8be92913-05ce-4611-b9ef-b5af545e6e5a |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2024, 18:08:47 |
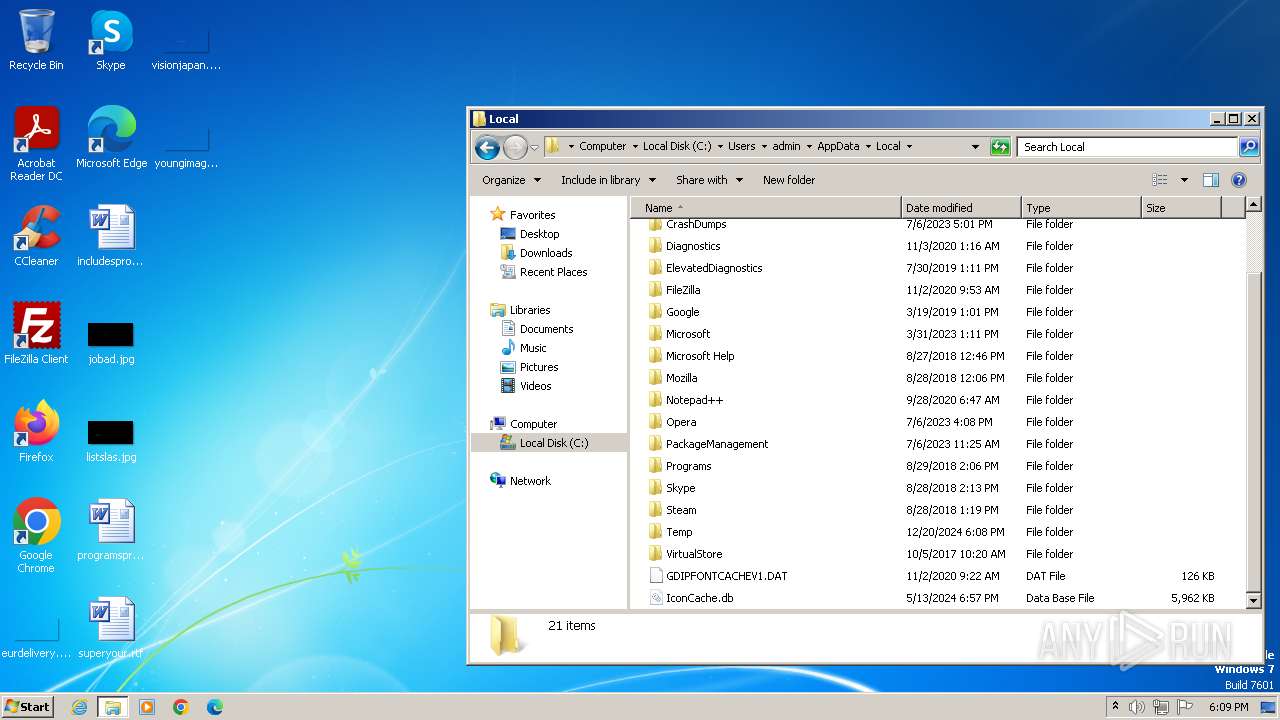
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | B7819E2C9ADA79F6123BA7A492E39715 |
| SHA1: | E7F05363626233ACE6DFD7C7E8055B5B304B7257 |
| SHA256: | 3C153E1C96C5FFF2C5ED5AADA23E1EC65EECE4A64891B104164B5728276FEFAE |
| SSDEEP: | 3072:omaX65xLxSxLMxSxxK6Ea9tos/+fe3+vVqCQ0yINRmxB6VSL5kbLqCwx5MPM0lqt:oNCzSixSBSzI2Vu0yINRmxBB4AhPudm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- fa_rss.exe (PID: 1932)
- fa_rss.exe (PID: 2472)
Reads settings of System Certificates
- fa_rss.exe (PID: 1932)
- fa_rss.exe (PID: 2472)
Reads the Internet Settings
- fa_rss.exe (PID: 2472)
- fa_rss.exe (PID: 1932)
Checks Windows Trust Settings
- fa_rss.exe (PID: 1932)
- fa_rss.exe (PID: 2472)
INFO
Reads the computer name
- fa_rss.exe (PID: 1932)
- wmpnscfg.exe (PID: 2184)
Checks supported languages
- fa_rss.exe (PID: 1932)
- wmpnscfg.exe (PID: 2184)
Reads the software policy settings
- fa_rss.exe (PID: 1932)
- fa_rss.exe (PID: 2472)
Reads the machine GUID from the registry
- fa_rss.exe (PID: 1932)
- fa_rss.exe (PID: 2472)
Checks proxy server information
- fa_rss.exe (PID: 1932)
- fa_rss.exe (PID: 2472)
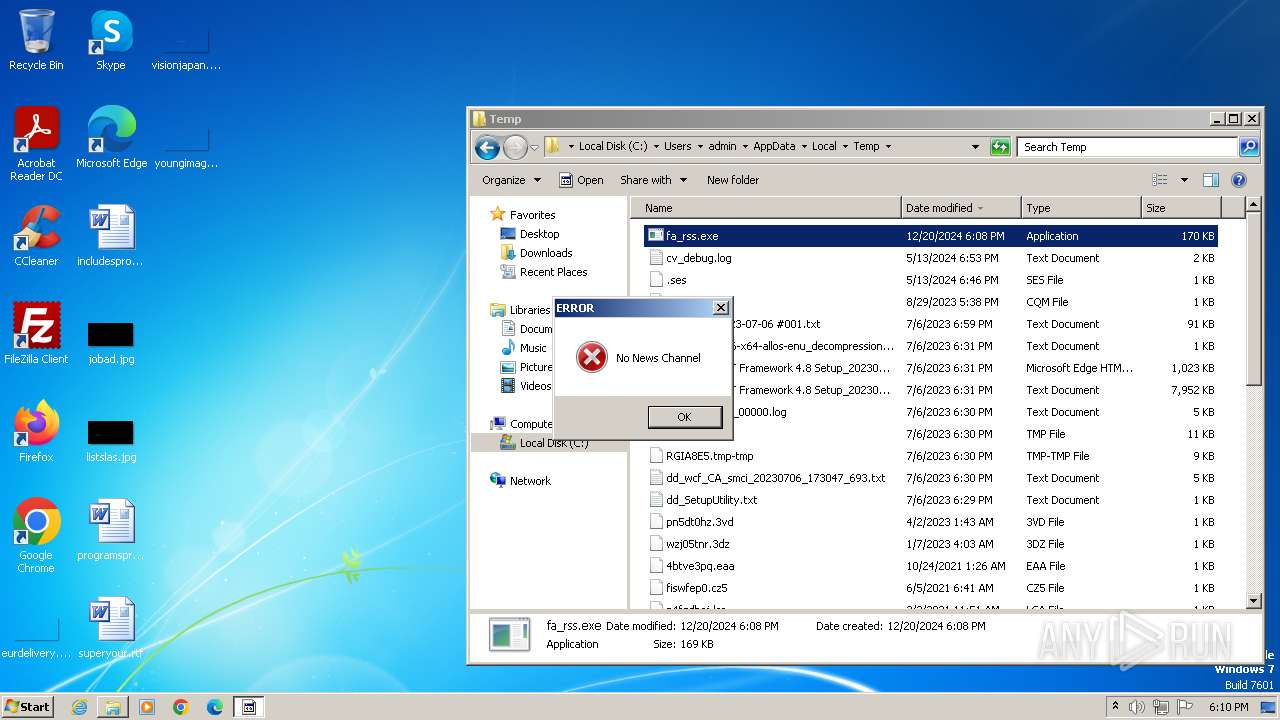
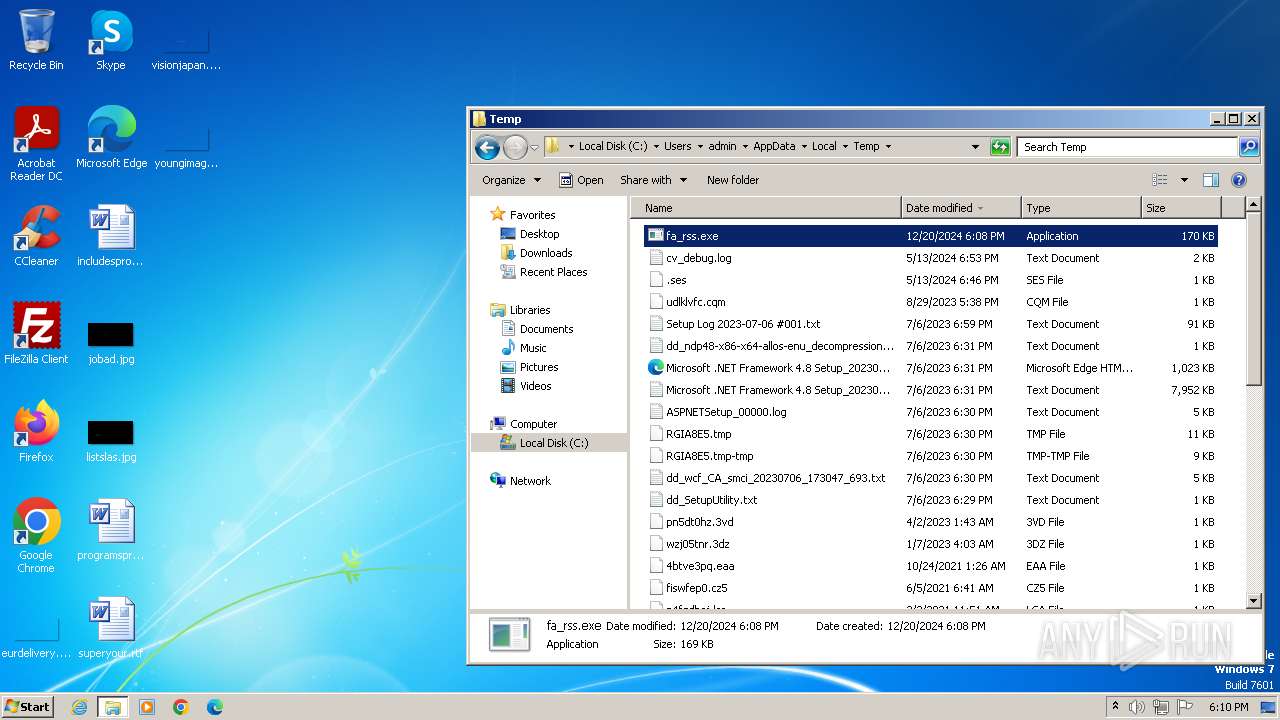
Manual execution by a user
- fa_rss.exe (PID: 2472)
- wmpnscfg.exe (PID: 2184)
- explorer.exe (PID: 2128)
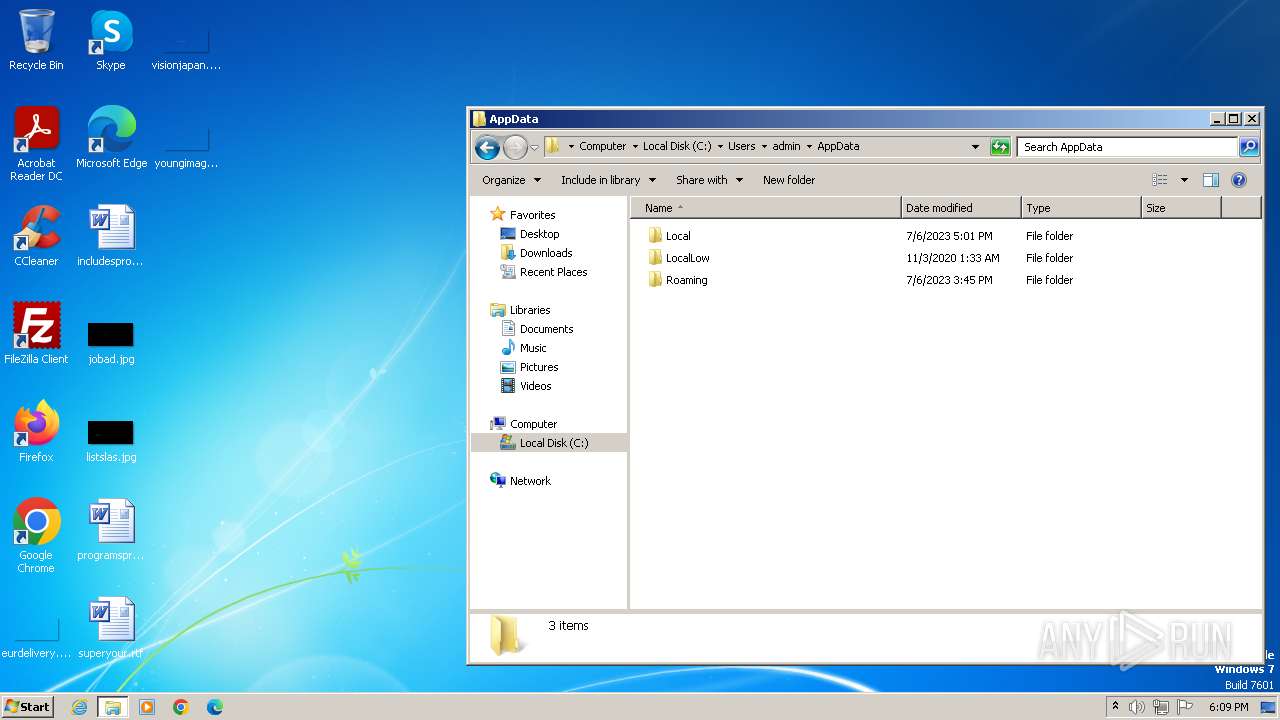
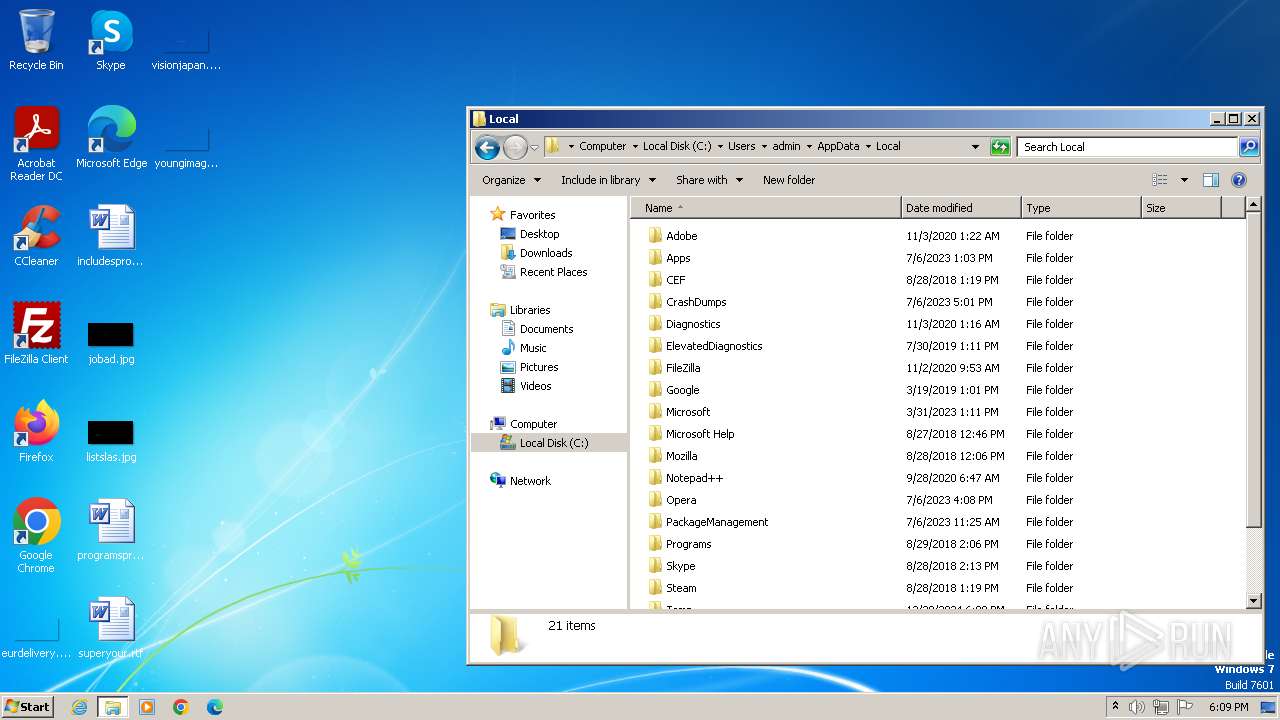
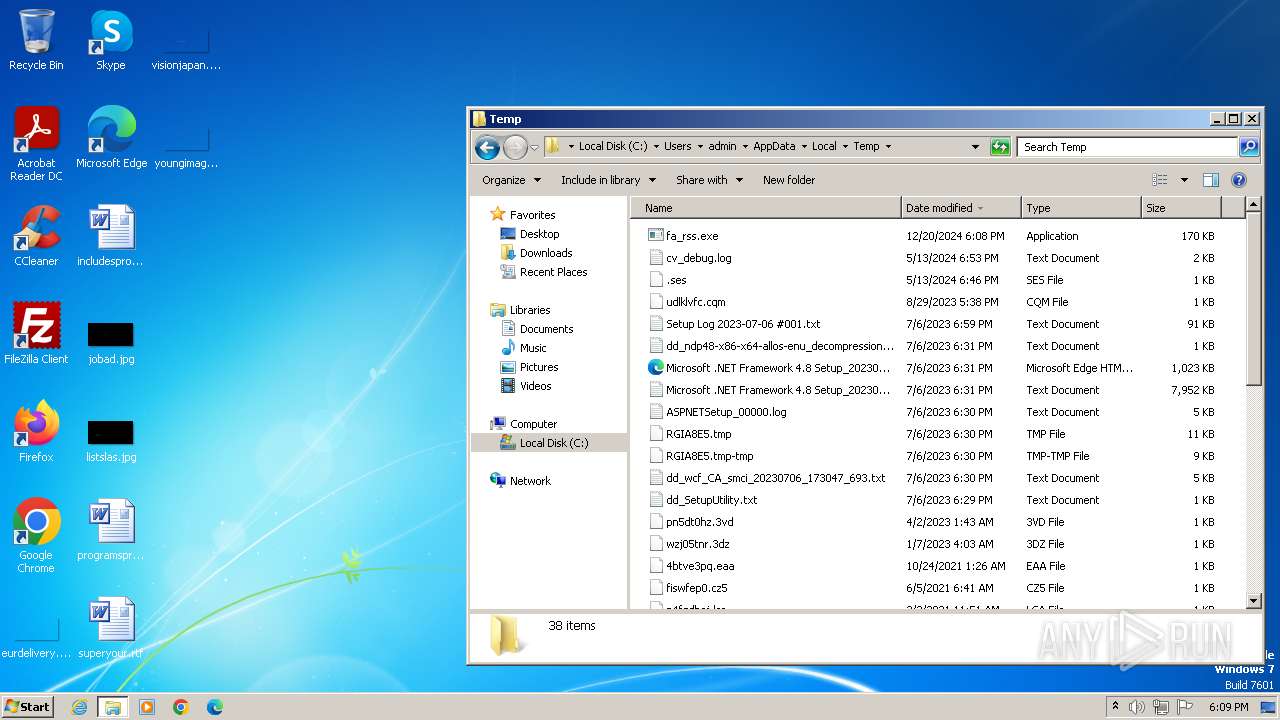
Create files in a temporary directory
- fa_rss.exe (PID: 1932)
- fa_rss.exe (PID: 2472)
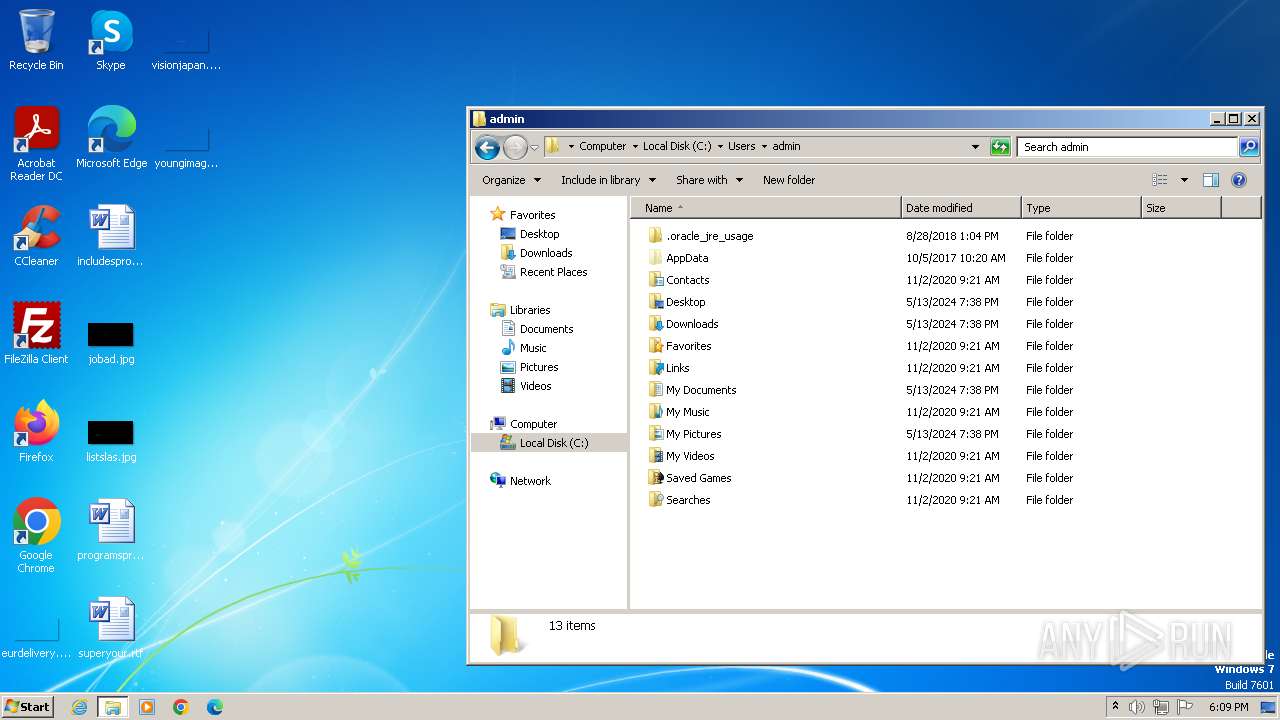
Creates files or folders in the user directory
- fa_rss.exe (PID: 1932)
- fa_rss.exe (PID: 2472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:18 23:27:31+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.24 |
| CodeSize: | 113664 |
| InitializedDataSize: | 81408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5cfb |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
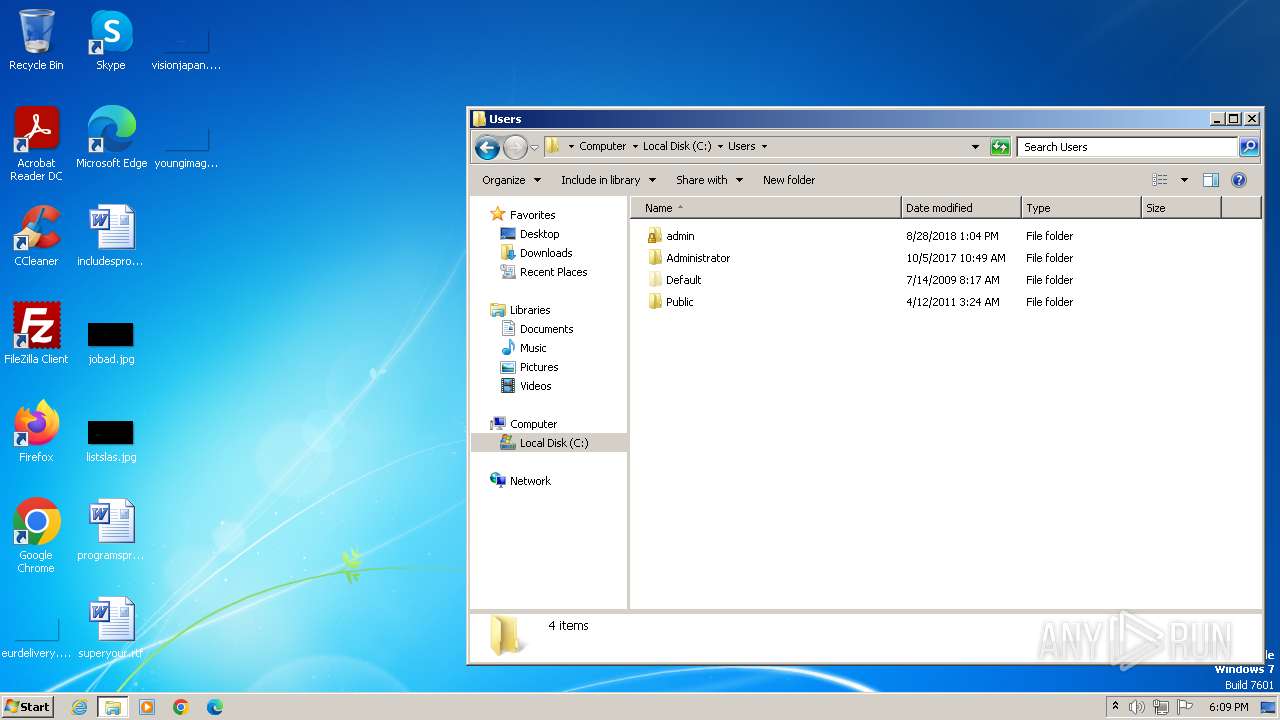
| 1932 | "C:\Users\admin\AppData\Local\Temp\fa_rss.exe" | C:\Users\admin\AppData\Local\Temp\fa_rss.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 2128 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Users\admin\AppData\Local\Temp\fa_rss.exe" | C:\Users\admin\AppData\Local\Temp\fa_rss.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
Total events
8 359
Read events
8 271
Write events
75
Delete events
13
Modification events
| (PID) Process: | (1932) fa_rss.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1932) fa_rss.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1932) fa_rss.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1932) fa_rss.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1932) fa_rss.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1932) fa_rss.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (1932) fa_rss.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (1932) fa_rss.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (1932) fa_rss.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (1932) fa_rss.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005F010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
6
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1932 | fa_rss.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:7D1685CE74DC2CA343C94892E2AAE6FB | SHA256:5922930535937F06C54E372C1BB63EEBEC8A939F1D5071C0F704184F0B3607F0 | |||
| 1932 | fa_rss.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\773CFF2C7835D48C4E76FE153DBA9F81_B7B1925BDA9E33CE0A92ECF660593288 | binary | |
MD5:ADA0DB50D4E9E62B9ADC05CF72A357C9 | SHA256:9D577619DCB754F089A283B13DAFA0C87D8F6502C2715837390236DEE8E3DD84 | |||
| 1932 | fa_rss.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_C39E9DBC666D19C07EEE7CD1E11AF8BE | binary | |
MD5:D836F00107C0F68D757231DFE0C2AB01 | SHA256:95746A439AAA48B491981543300BB783CDC96F4E9D5F31FB18DC2E50CC17FB68 | |||
| 1932 | fa_rss.exe | C:\Users\admin\AppData\Local\Temp\temp_event | image | |
MD5:D89746888DA2D9510B64A9F031EAECD5 | SHA256:EF1955AE757C8B966C83248350331BD3A30F658CED11F387F8EBF05AB3368629 | |||
| 2472 | fa_rss.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\pixel[2].gif | image | |
MD5:D89746888DA2D9510B64A9F031EAECD5 | SHA256:EF1955AE757C8B966C83248350331BD3A30F658CED11F387F8EBF05AB3368629 | |||
| 1932 | fa_rss.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\pixel[1].gif | image | |
MD5:D89746888DA2D9510B64A9F031EAECD5 | SHA256:EF1955AE757C8B966C83248350331BD3A30F658CED11F387F8EBF05AB3368629 | |||
| 1932 | fa_rss.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\773CFF2C7835D48C4E76FE153DBA9F81_B7B1925BDA9E33CE0A92ECF660593288 | binary | |
MD5:D8736A101B9274A45E0D0B520AD82F8B | SHA256:CC02865BBDE2027A056E8A45C951A8A381B04918C880A73D422376F77111D0EB | |||
| 2472 | fa_rss.exe | C:\Users\admin\AppData\Local\Temp\temp_event | image | |
MD5:D89746888DA2D9510B64A9F031EAECD5 | SHA256:EF1955AE757C8B966C83248350331BD3A30F658CED11F387F8EBF05AB3368629 | |||
| 1932 | fa_rss.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_C39E9DBC666D19C07EEE7CD1E11AF8BE | binary | |
MD5:BC028B922E8269B88DE4E69733F37465 | SHA256:C35439405ADA9BB07B86FD47899AE837C6BE6F0905752D2BF708394C4023A235 | |||
| 1932 | fa_rss.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:77B20B5CD41BC6BB475CCA3F91AE6E3C | SHA256:5511A9B9F9144ED7BDE4CCB074733B7C564D918D2A8B10D391AFC6BE5B3B1509 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
11
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1932 | fa_rss.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2db5c274590d502f | unknown | — | — | whitelisted |
1932 | fa_rss.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAsllCLO2YEqFaBOmVKKDvo%3D | unknown | — | — | whitelisted |
1932 | fa_rss.exe | GET | 200 | 192.229.221.95:80 | http://status.rapidssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJiUKgT2m88fZ4nxc1Lu6M%2FjvkagQUDNtsgkkPSmcKuBTuesRIUojrVjgCEAECyHKLsbZHFMkaaaqQRe8%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1932 | fa_rss.exe | 64.227.17.224:443 | veryfast.io | DIGITALOCEAN-ASN | US | unknown |
1932 | fa_rss.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1932 | fa_rss.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2472 | fa_rss.exe | 64.227.17.224:443 | veryfast.io | DIGITALOCEAN-ASN | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
veryfast.io |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.rapidssl.com |
| whitelisted |