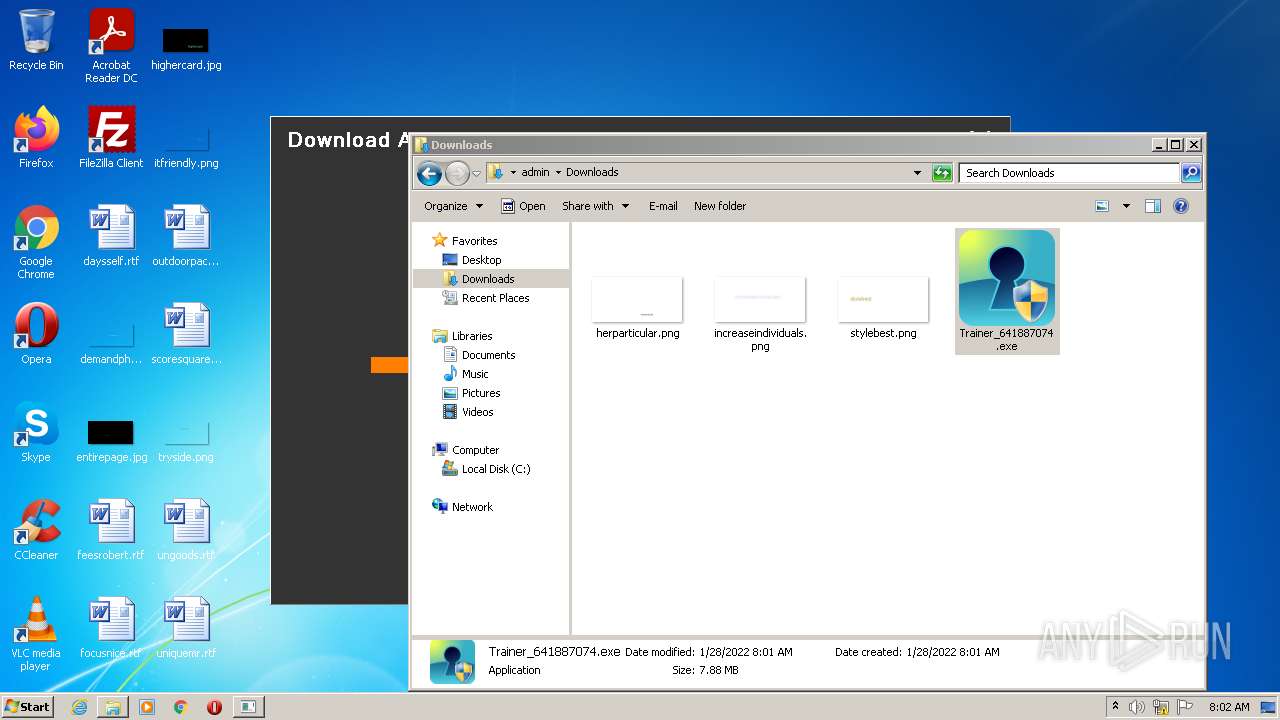
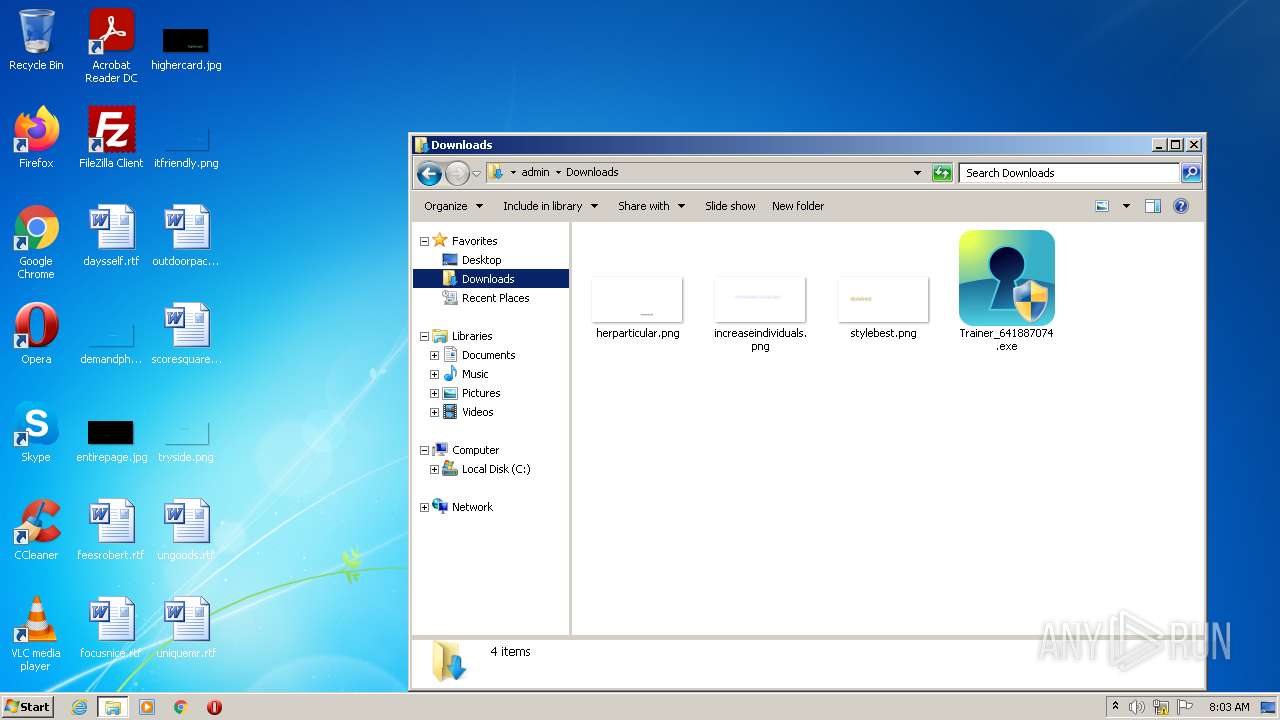
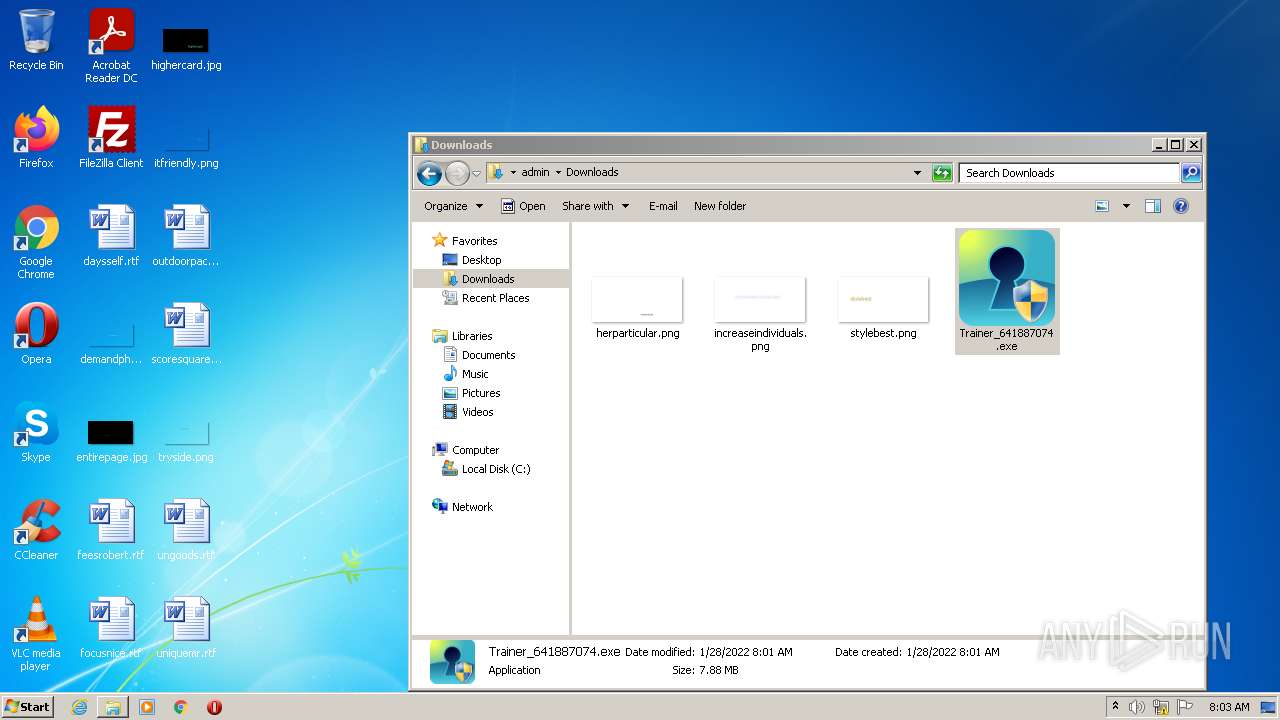
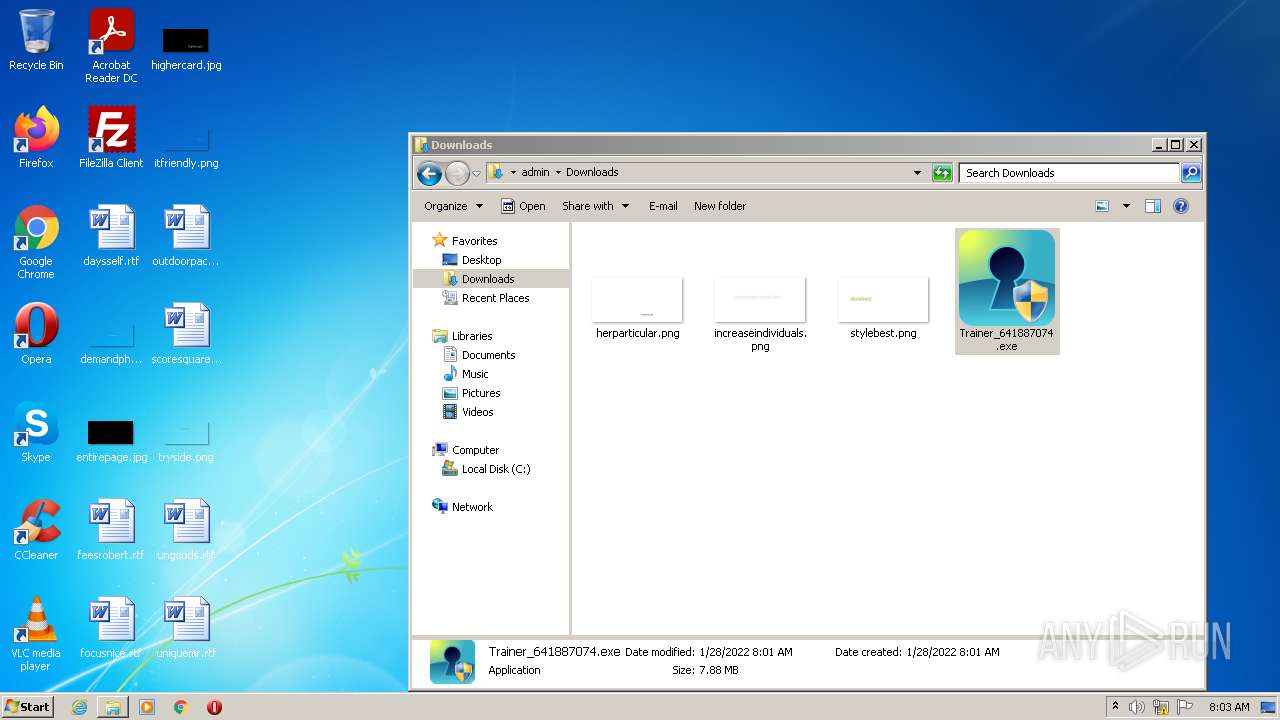
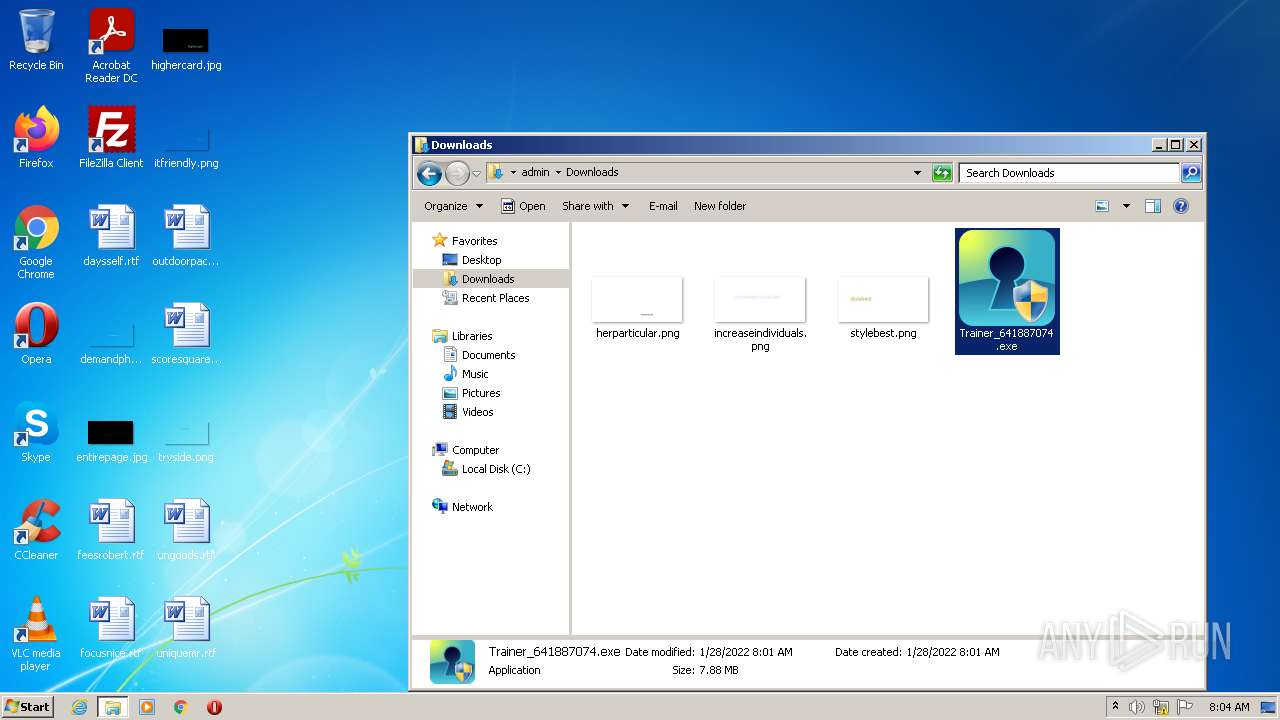
| File name: | Trainer_641887074.exe |
| Full analysis: | https://app.any.run/tasks/1b69b2b7-d532-4283-9d89-2af9214a8025 |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2022, 08:01:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4C2AA12FD4460E9E4F86EC7F12A492E6 |
| SHA1: | DC9F9EE9A3ADFF40133D591287779A2A5E481003 |
| SHA256: | 3C12D41A9E8ADB85667A8E0CE56861B07D0E2C1C2A58D34C5FE1F55B3DCC18EB |
| SSDEEP: | 196608:E2tUWWsVVyjmyfYJfAGQUx0GpC9NVB7BAqtgBCdmHpB+t+ai1fyYD:NDWWyN2f51C95jGBCdmHhNjD |
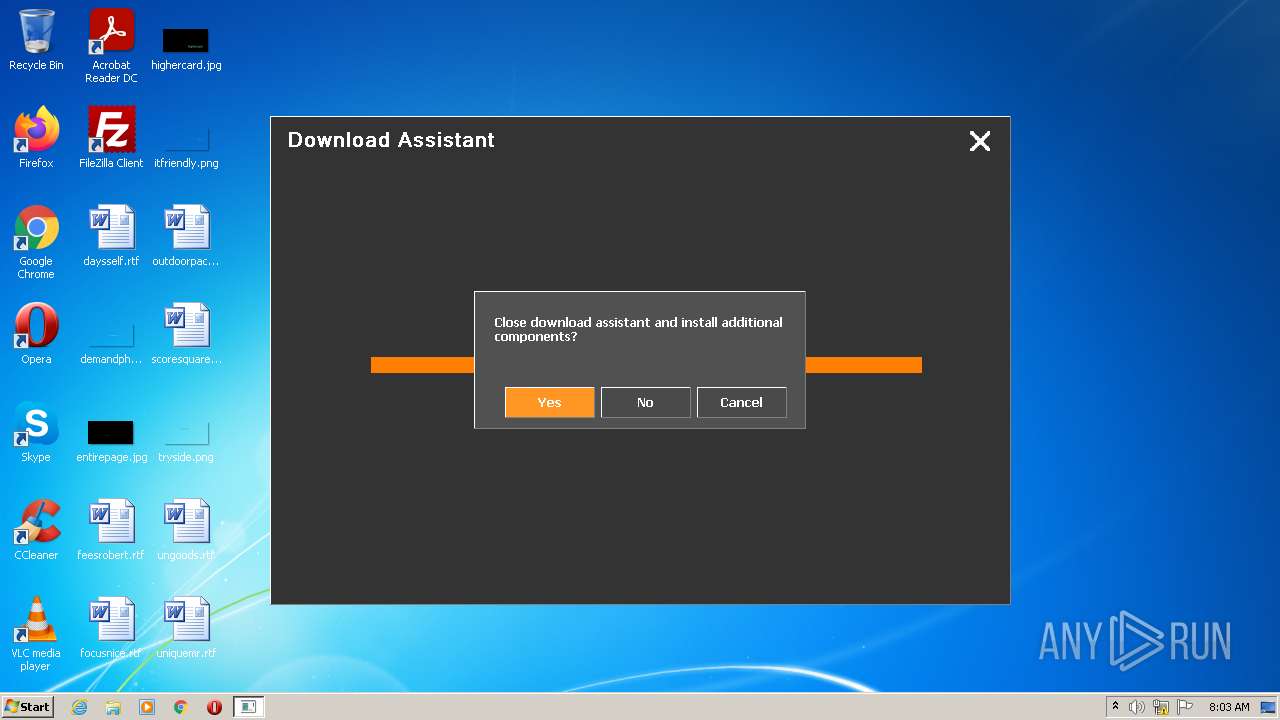
MALICIOUS
Drops executable file immediately after starts
- Trainer_641887074.exe (PID: 3988)
- Trainer_641887074.exe (PID: 3408)
- is-T460V.tmp (PID: 3208)
- Trainer_641887074.exe (PID: 2100)
- is-UR19K.tmp (PID: 440)
- is-KT881.tmp (PID: 3164)
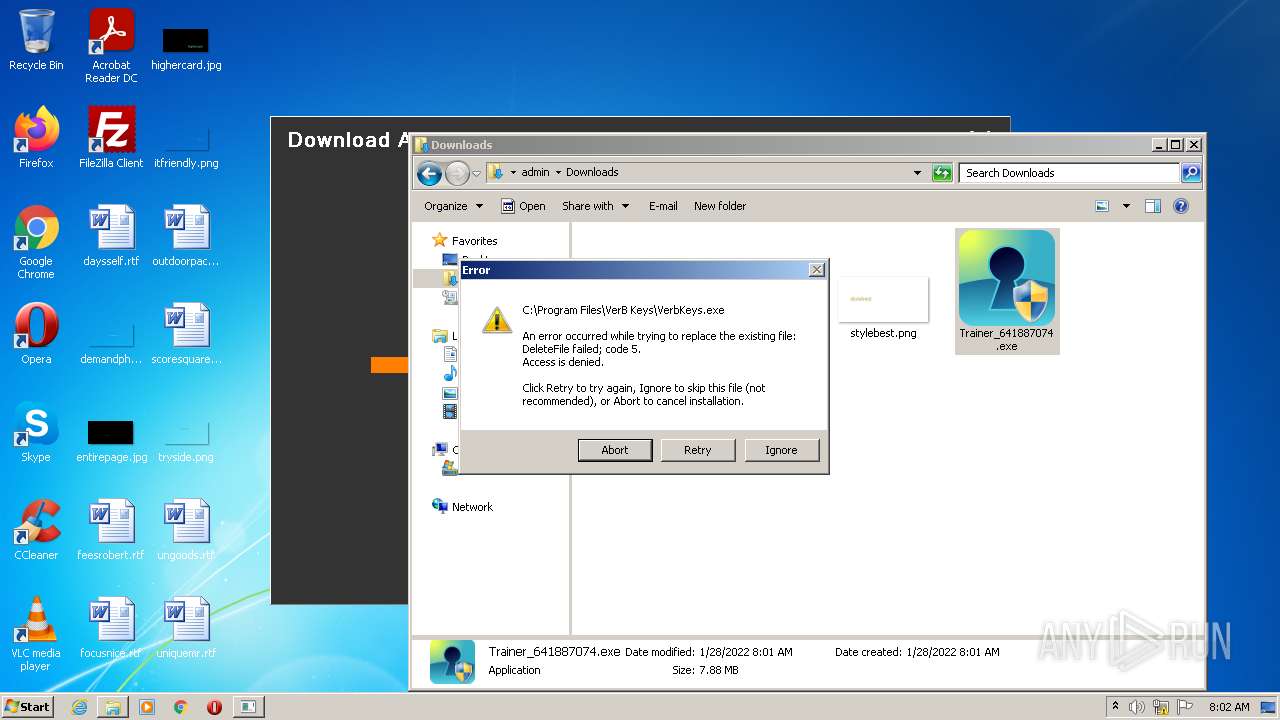
Application was dropped or rewritten from another process
- wmfdist.exe (PID: 2944)
- wmfdist.exe (PID: 2300)
- wmfdist.exe (PID: 2672)
SUSPICIOUS
Checks supported languages
- Trainer_641887074.exe (PID: 3988)
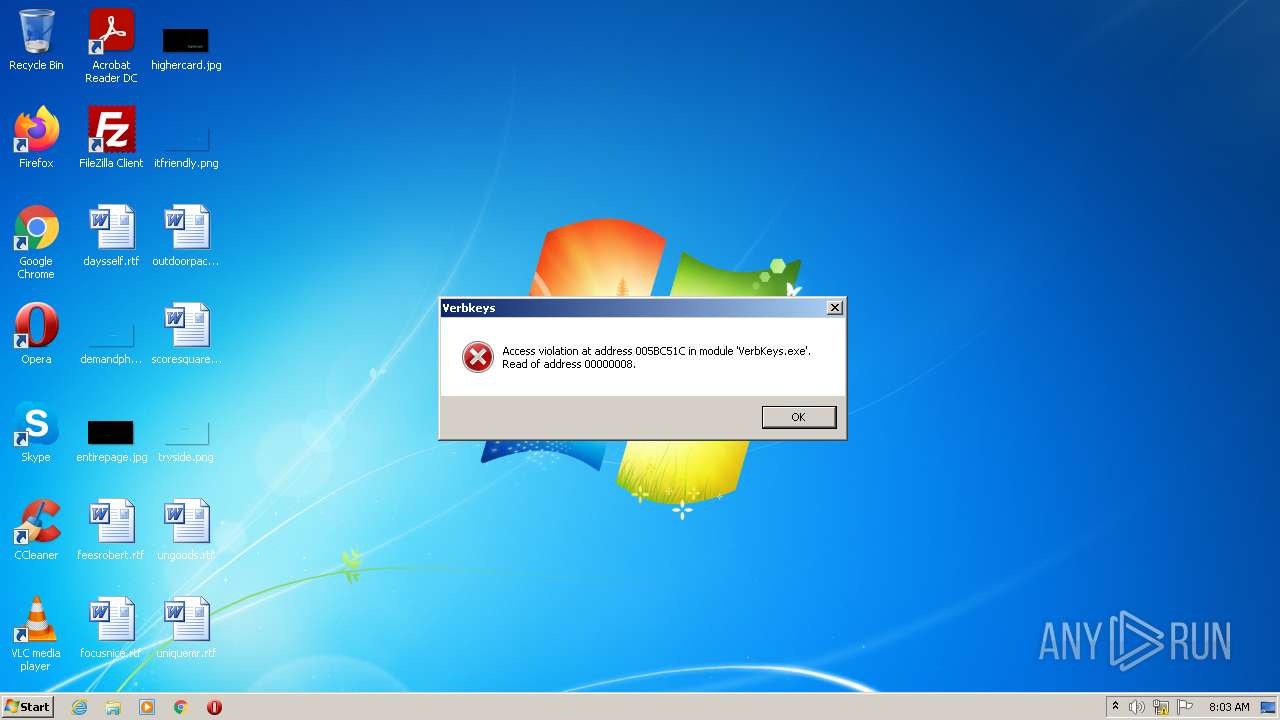
- VerbKeys.exe (PID: 3848)
- is-KT881.tmp (PID: 3164)
- wmfdist.exe (PID: 2944)
- VerbKeys.exe (PID: 2320)
- is-T460V.tmp (PID: 3208)
- Trainer_641887074.exe (PID: 3408)
- VerbKeys.exe (PID: 3048)
- wmfdist.exe (PID: 2300)
- VerbKeys.exe (PID: 3244)
- is-UR19K.tmp (PID: 440)
- Trainer_641887074.exe (PID: 2100)
- VerbKeys.exe (PID: 2928)
- wmfdist.exe (PID: 2672)
- VerbKeys.exe (PID: 3384)
Reads the computer name
- VerbKeys.exe (PID: 3848)
- is-KT881.tmp (PID: 3164)
- VerbKeys.exe (PID: 2320)
- is-T460V.tmp (PID: 3208)
- VerbKeys.exe (PID: 3048)
- VerbKeys.exe (PID: 3244)
- is-UR19K.tmp (PID: 440)
- VerbKeys.exe (PID: 2928)
- VerbKeys.exe (PID: 3384)
Drops a file with too old compile date
- Trainer_641887074.exe (PID: 3988)
- Trainer_641887074.exe (PID: 3408)
- is-T460V.tmp (PID: 3208)
- Trainer_641887074.exe (PID: 2100)
- is-UR19K.tmp (PID: 440)
- is-KT881.tmp (PID: 3164)
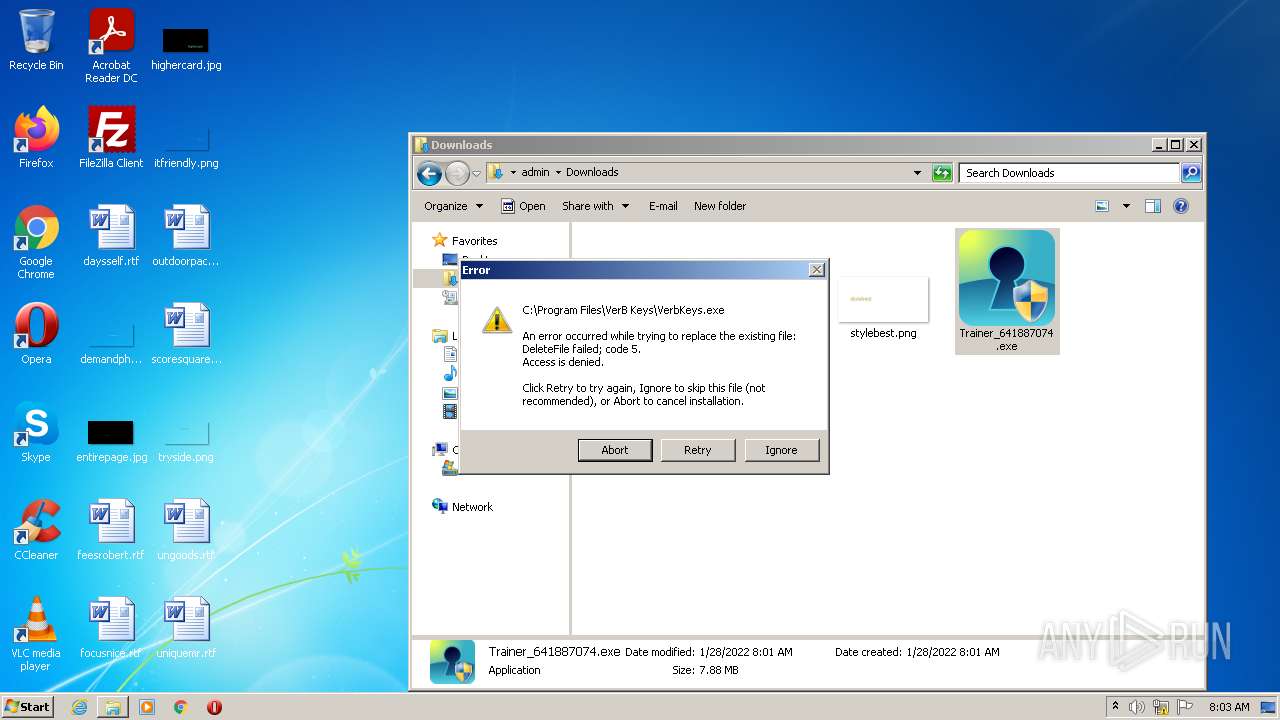
Executable content was dropped or overwritten
- Trainer_641887074.exe (PID: 3988)
- is-KT881.tmp (PID: 3164)
- Trainer_641887074.exe (PID: 3408)
- is-T460V.tmp (PID: 3208)
- Trainer_641887074.exe (PID: 2100)
- is-UR19K.tmp (PID: 440)
Reads Windows owner or organization settings
- is-KT881.tmp (PID: 3164)
- is-T460V.tmp (PID: 3208)
- is-UR19K.tmp (PID: 440)
Drops a file that was compiled in debug mode
- is-KT881.tmp (PID: 3164)
- is-T460V.tmp (PID: 3208)
- is-UR19K.tmp (PID: 440)
Reads the Windows organization settings
- is-T460V.tmp (PID: 3208)
- is-UR19K.tmp (PID: 440)
- is-KT881.tmp (PID: 3164)
Searches for installed software
- is-T460V.tmp (PID: 3208)
- is-UR19K.tmp (PID: 440)
Creates a directory in Program Files
- is-KT881.tmp (PID: 3164)
INFO
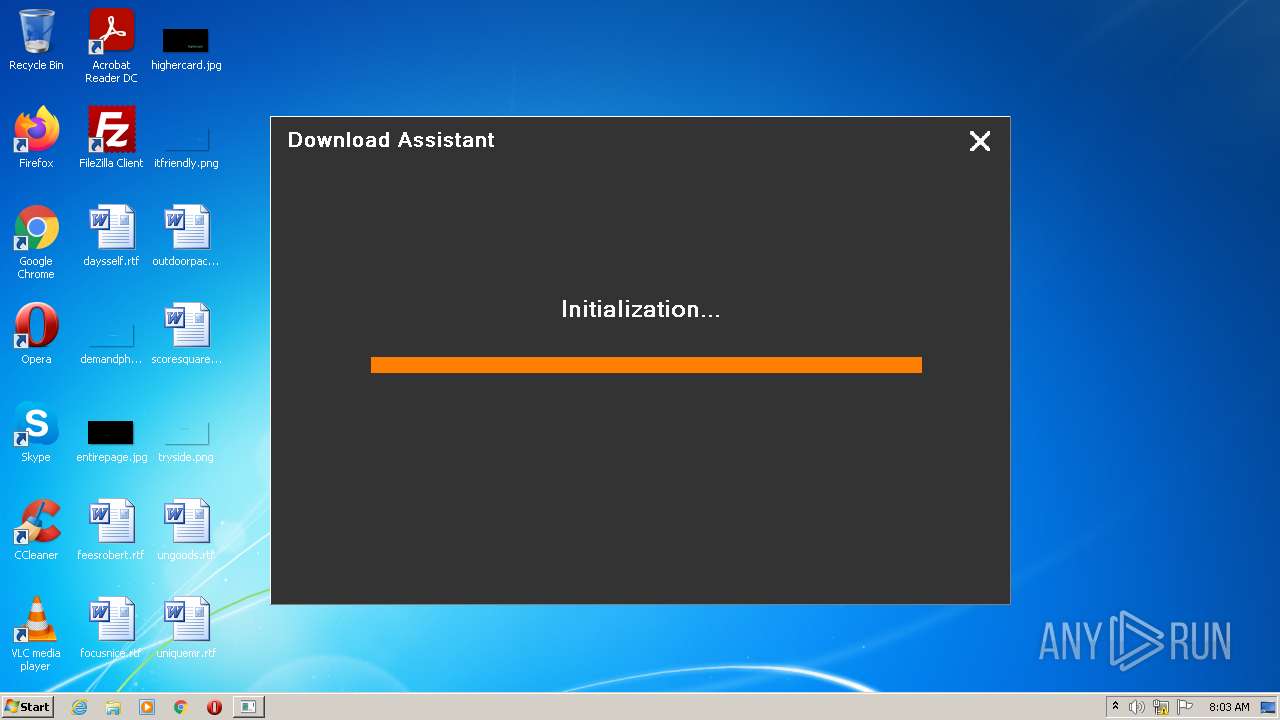
Creates files in the program directory
- is-KT881.tmp (PID: 3164)
- is-T460V.tmp (PID: 3208)
- is-UR19K.tmp (PID: 440)
Application was dropped or rewritten from another process
- is-KT881.tmp (PID: 3164)
- is-T460V.tmp (PID: 3208)
- is-UR19K.tmp (PID: 440)
Creates a software uninstall entry
- is-KT881.tmp (PID: 3164)
- is-T460V.tmp (PID: 3208)
- is-UR19K.tmp (PID: 440)
Loads dropped or rewritten executable
- is-KT881.tmp (PID: 3164)
- is-T460V.tmp (PID: 3208)
- is-UR19K.tmp (PID: 440)
Checks supported languages
- explorer.exe (PID: 392)
- explorer.exe (PID: 776)
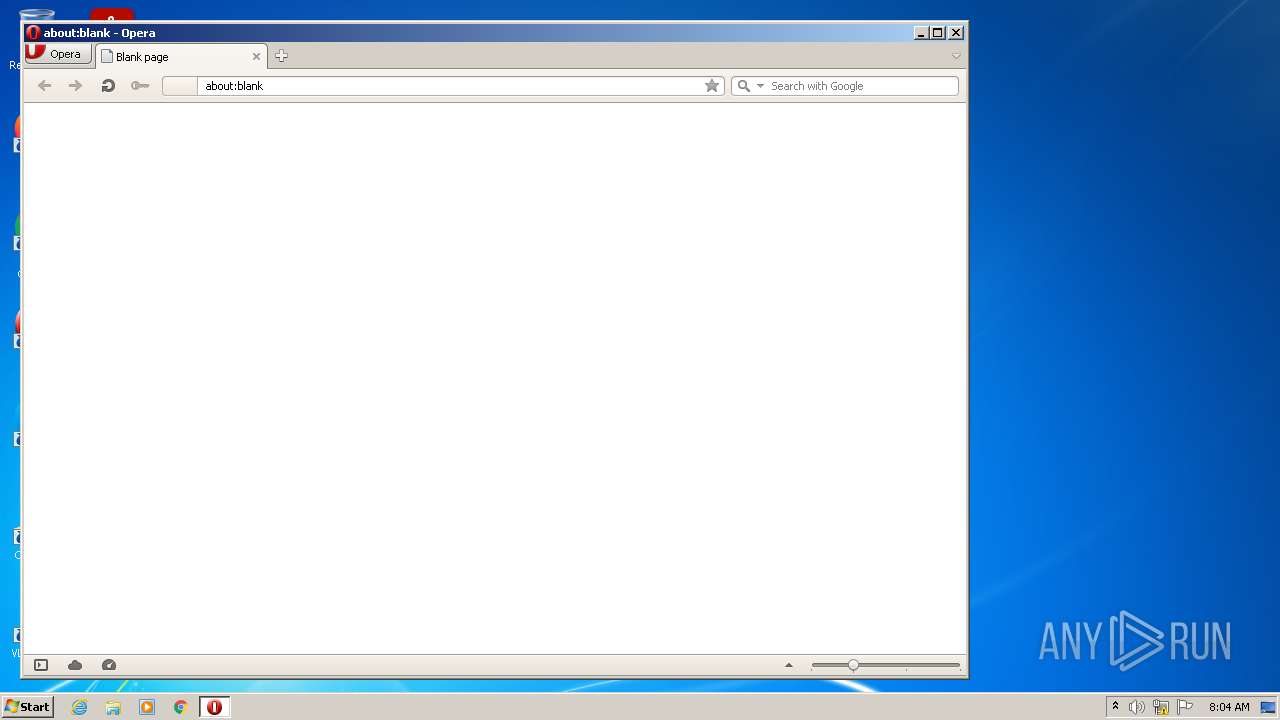
- opera.exe (PID: 1612)
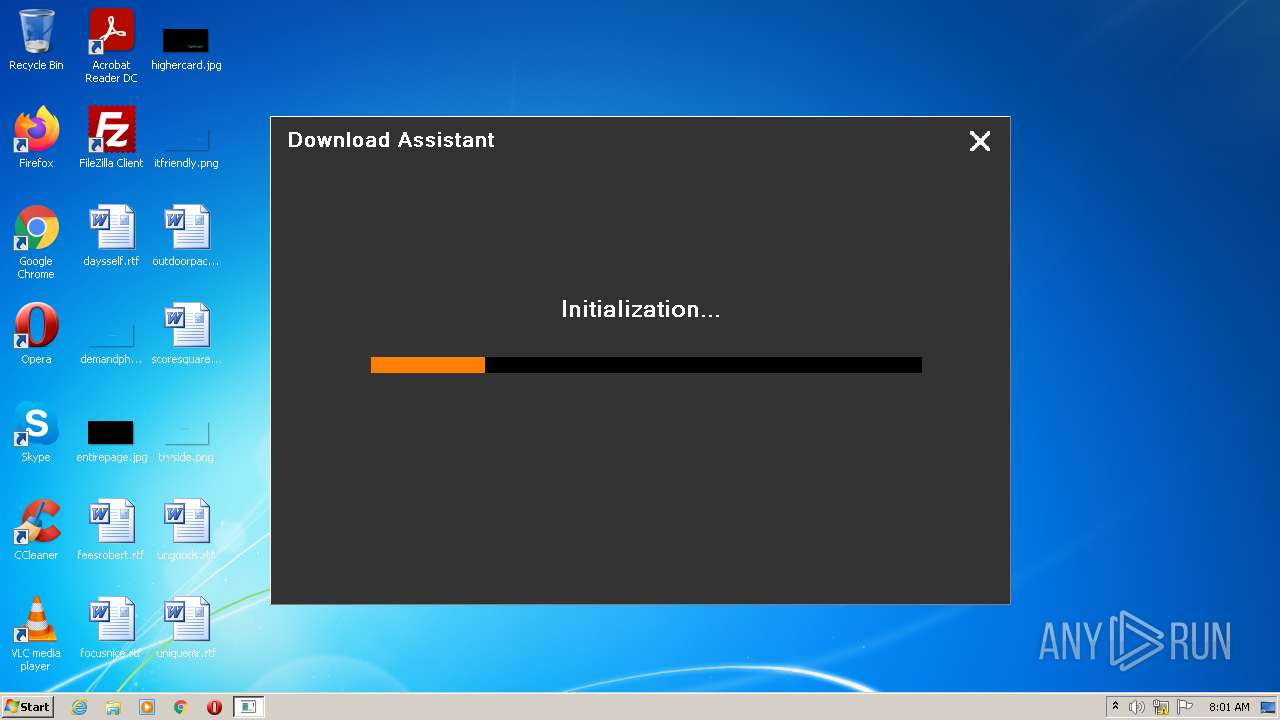
Manual execution by user
- Trainer_641887074.exe (PID: 1096)
- explorer.exe (PID: 392)
- Trainer_641887074.exe (PID: 3408)
- explorer.exe (PID: 776)
- Trainer_641887074.exe (PID: 2676)
- Trainer_641887074.exe (PID: 2100)
- opera.exe (PID: 1612)
Reads the computer name
- explorer.exe (PID: 392)
- explorer.exe (PID: 776)
- opera.exe (PID: 1612)
Check for Java to be installed
- opera.exe (PID: 1612)
Creates files in the user directory
- opera.exe (PID: 1612)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 1612)
Reads the date of Windows installation
- opera.exe (PID: 1612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| LegalCopyright: | |
|---|---|
| FileVersion: | |
| FileDescription: | VerB Keys Setup |
| CompanyName: | VerB Keys |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 1 |
| EntryPoint: | 0x991c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 297984 |
| CodeSize: | 37376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | VerB Keys |
| FileDescription: | VerB Keys Setup |
| FileVersion: | - |
| LegalCopyright: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009040 | 0x00009200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53842 |
DATA | 0x0000B000 | 0x00000248 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.70306 |
BSS | 0x0000C000 | 0x00000E34 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008A4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00047A50 | 0x00047C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.48177 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.87667 | 899 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.79008 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 6.69478 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.89653 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.36583 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
65
Monitored processes
21
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 440 | "C:\Users\admin\AppData\Local\Temp\is-UK629.tmp\is-UR19K.tmp" /SL4 $60232 "C:\Users\admin\Downloads\Trainer_641887074.exe" 7991087 336384 | C:\Users\admin\AppData\Local\Temp\is-UK629.tmp\is-UR19K.tmp | Trainer_641887074.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.45.0.0 Modules
| |||||||||||||||
| 776 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\Downloads\Trainer_641887074.exe" | C:\Users\admin\Downloads\Trainer_641887074.exe | — | Explorer.EXE | |||||||||||
User: admin Company: VerB Keys Integrity Level: MEDIUM Description: VerB Keys Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 1612 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | Explorer.EXE | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2100 | "C:\Users\admin\Downloads\Trainer_641887074.exe" | C:\Users\admin\Downloads\Trainer_641887074.exe | Explorer.EXE | ||||||||||||
User: admin Company: VerB Keys Integrity Level: HIGH Description: VerB Keys Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2300 | "C:\Program Files\VerB Keys\wmfdist.exe" /Q:A /R:N | C:\Program Files\VerB Keys\wmfdist.exe | — | is-T460V.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Media Component Setup Application Exit code: 0 Version: 9.00.00.2926 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\VerB Keys\VerbKeys.exe" 594cc2c9af76aa2afcf9d905a1dd2a66 | C:\Program Files\VerB Keys\VerbKeys.exe | is-KT881.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\VerB Keys\wmfdist.exe" /Q:A /R:N | C:\Program Files\VerB Keys\wmfdist.exe | — | is-UR19K.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Media Component Setup Application Exit code: 0 Version: 9.00.00.2926 Modules
| |||||||||||||||
| 2676 | "C:\Users\admin\Downloads\Trainer_641887074.exe" | C:\Users\admin\Downloads\Trainer_641887074.exe | — | Explorer.EXE | |||||||||||
User: admin Company: VerB Keys Integrity Level: MEDIUM Description: VerB Keys Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
Total events
4 367
Read events
4 254
Write events
111
Delete events
2
Modification events
| (PID) Process: | (3164) is-KT881.tmp | Key: | HKEY_CURRENT_USER\Software\VerB Keyso |
| Operation: | write | Name: | Lang |
Value: English | |||
| (PID) Process: | (3164) is-KT881.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VerB Keys_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.1.10 | |||
| (PID) Process: | (3164) is-KT881.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VerB Keys_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\VerB Keys | |||
| (PID) Process: | (3164) is-KT881.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VerB Keys_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\VerB Keys\ | |||
| (PID) Process: | (3164) is-KT881.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VerB Keys_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: VerB Keys | |||
| (PID) Process: | (3164) is-KT881.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VerB Keys_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (3164) is-KT881.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VerB Keys_is1 |
| Operation: | write | Name: | DisplayName |
Value: VerB Keys | |||
| (PID) Process: | (3164) is-KT881.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VerB Keys_is1 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\VerB Keys\VerbKeys.exe | |||
| (PID) Process: | (3164) is-KT881.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VerB Keys_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\VerB Keys\unins000.exe" | |||
| (PID) Process: | (3164) is-KT881.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\VerB Keys_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\VerB Keys\unins000.exe" /SILENT | |||
Executable files
30
Suspicious files
11
Text files
187
Unknown types
1
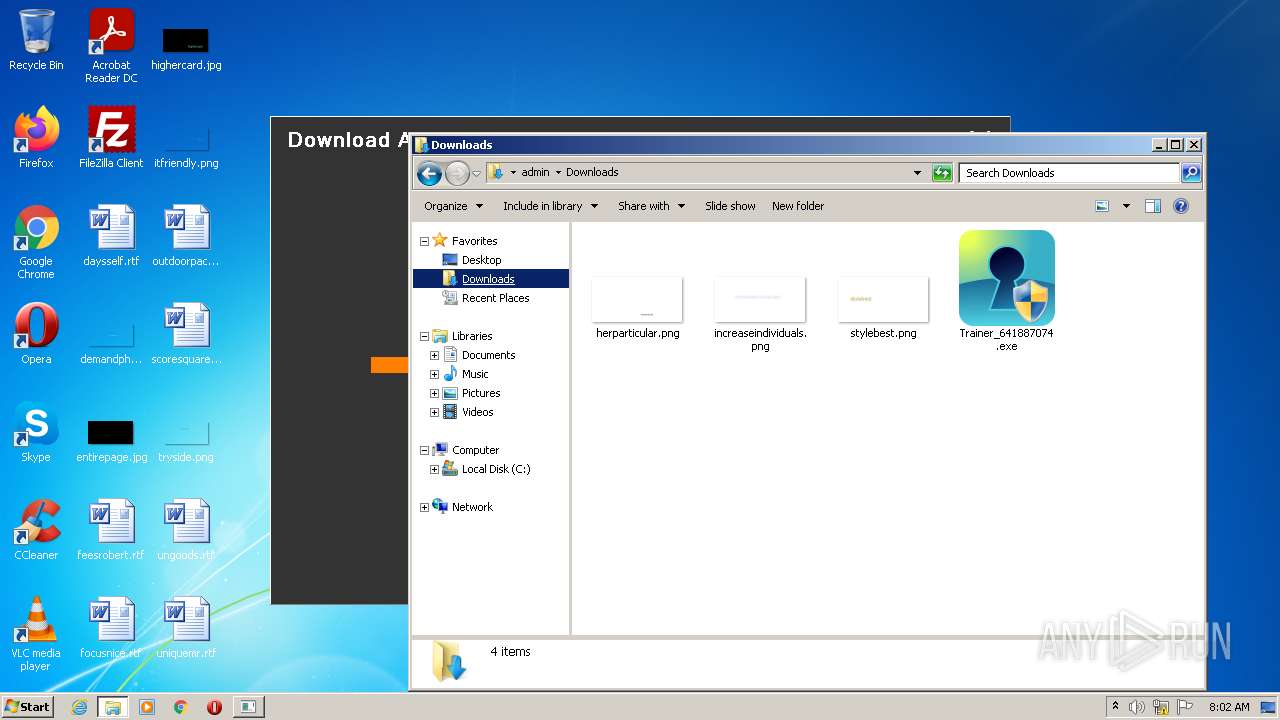
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3164 | is-KT881.tmp | C:\Program Files\VerB Keys\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 3164 | is-KT881.tmp | C:\Program Files\VerB Keys\is-BOHBH.tmp | executable | |
MD5:— | SHA256:— | |||
| 3164 | is-KT881.tmp | C:\Users\admin\AppData\Local\Temp\is-93SPI.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 3988 | Trainer_641887074.exe | C:\Users\admin\AppData\Local\Temp\is-QPGLV.tmp\is-KT881.tmp | executable | |
MD5:E8A53997228F3D021264EBFCFAB4E0B6 | SHA256:CF0BB6F2648E0BA7718EE78AFEFFF62DA30BB4614865CD3ECE24FF67CDE3B22F | |||
| 3164 | is-KT881.tmp | C:\Users\admin\AppData\Local\Temp\is-93SPI.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:C594B792B9C556EA62A30DE541D2FB03 | SHA256:5DCC1E0A197922907BCA2C4369F778BD07EE4B1BBBDF633E987A028A314D548E | |||
| 3164 | is-KT881.tmp | C:\Program Files\VerB Keys\Lang\is-PGQMS.tmp | xml | |
MD5:8C9DEEE400CC9F86890B746C51491F0A | SHA256:B492BA91D758ABE05035B5D789B727C6A5394CA663CE448FAE2DA146924D483C | |||
| 3164 | is-KT881.tmp | C:\Program Files\VerB Keys\Lang\is-A0OPK.tmp | xml | |
MD5:2C2EA437C27F4FE5C7A902EF9144D5B1 | SHA256:7DFDF23E44B5612947162B3F2C5D59EDD6B788A64BCCC377C64F49492F6C7A5D | |||
| 3164 | is-KT881.tmp | C:\Program Files\VerB Keys\Lang\Czech.xml | xml | |
MD5:3192962EF4CF87BC7572C22FC9F50741 | SHA256:70C028F2DBA09ADA187D2CCA37FD01BD4240D6C521C2A9B9B13620211D0E7141 | |||
| 3164 | is-KT881.tmp | C:\Program Files\VerB Keys\Lang\Chinese_Traditional.xml | xml | |
MD5:8F39323F847D7F445F25EEA1BAACAEE5 | SHA256:C116B8B0D7A748B1F933A973B0D5B709FE1F20D78F6140E62B44F8CC749BA2AB | |||
| 3164 | is-KT881.tmp | C:\Program Files\VerB Keys\Lang\is-H863D.tmp | xml | |
MD5:6C009F7BB5463E825D82135D18EE8D76 | SHA256:CEB688D5BAFFC419100635D23F022673169C76F349F2E00698503CF860A7935E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
10
DNS requests
9
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
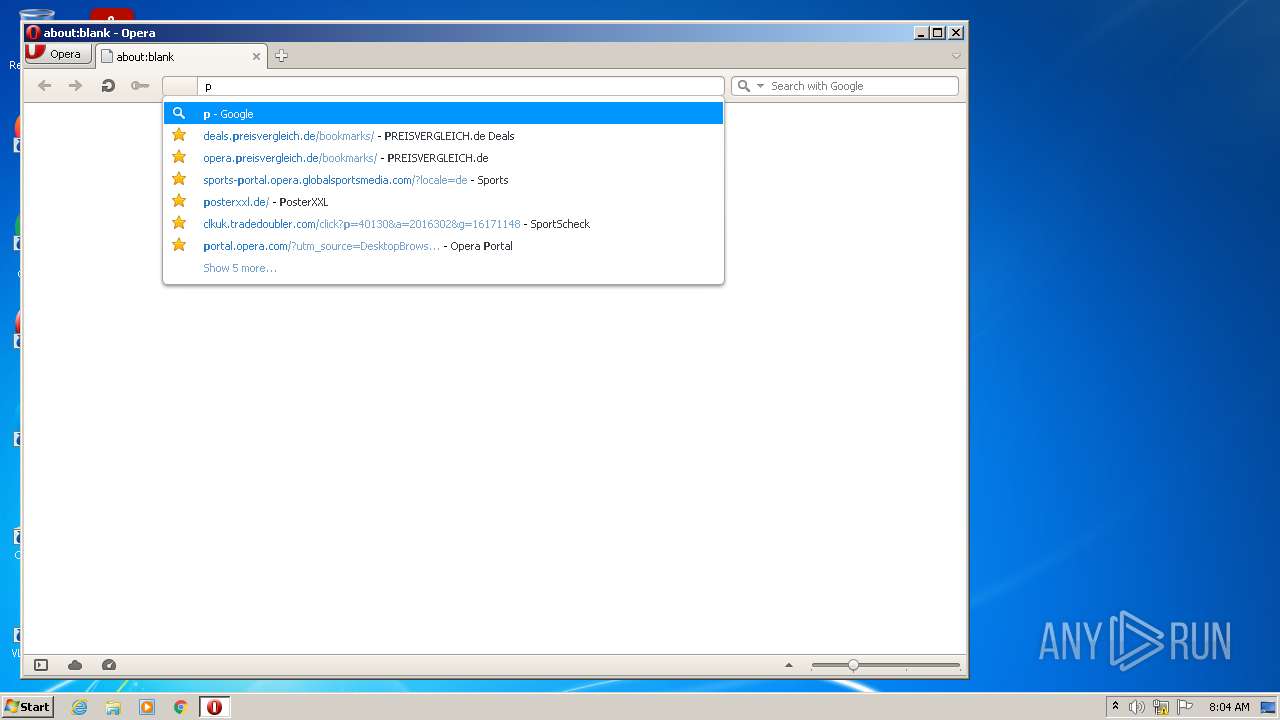
1612 | opera.exe | GET | 200 | 142.250.186.174:80 | http://clients1.google.com/complete/search?q=penap&client=opera-suggest-omnibox&hl=de | US | text | 145 b | whitelisted |
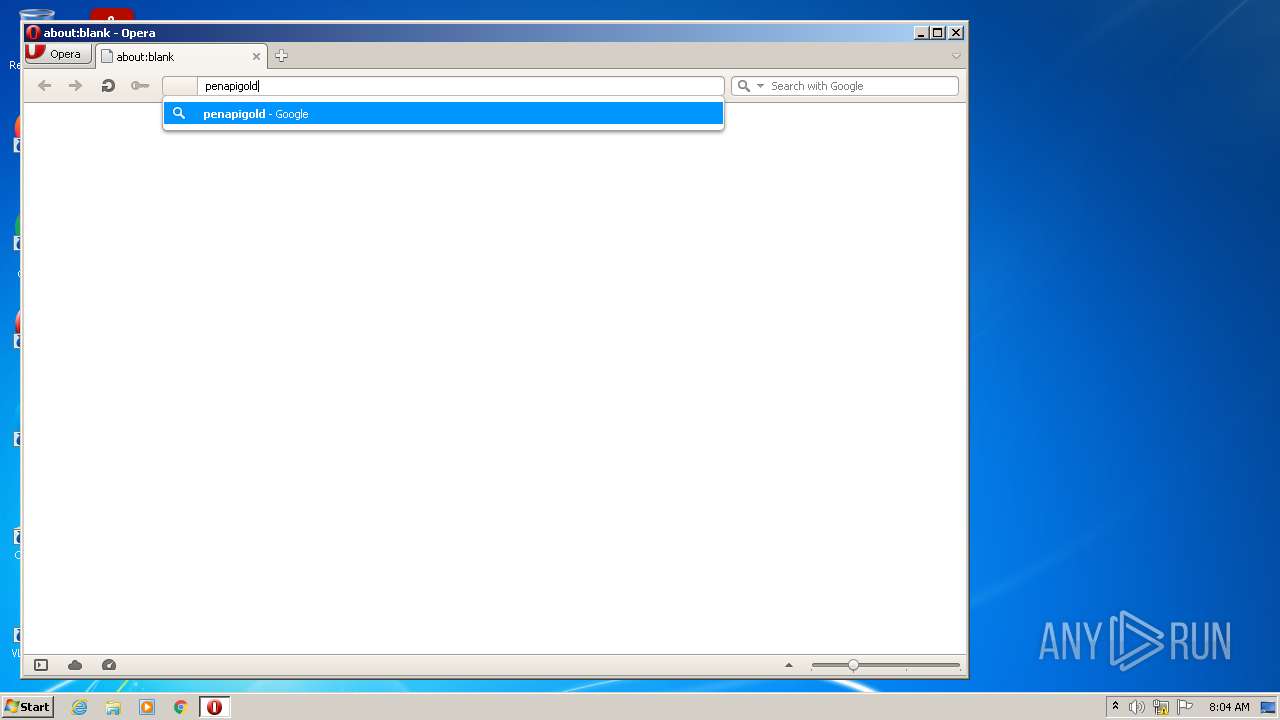
1612 | opera.exe | GET | 200 | 142.250.186.174:80 | http://clients1.google.com/complete/search?q=penapigol&client=opera-suggest-omnibox&hl=de | US | text | 36 b | whitelisted |
1612 | opera.exe | GET | 200 | 142.250.186.174:80 | http://clients1.google.com/complete/search?q=penapigold&client=opera-suggest-omnibox&hl=de | US | text | 37 b | whitelisted |
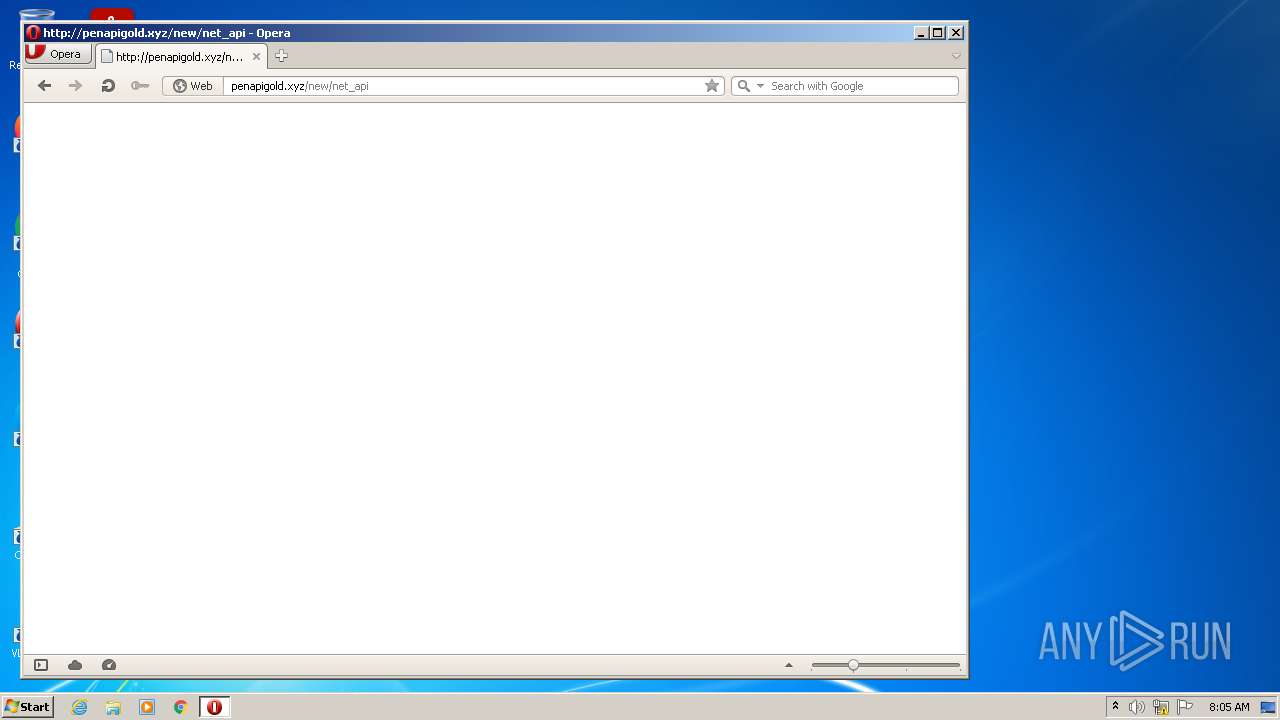
2320 | VerbKeys.exe | POST | — | 172.67.199.124:80 | http://penapigold.xyz/new/net_api | US | — | — | malicious |
1612 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
1612 | opera.exe | GET | 200 | 142.250.186.174:80 | http://clients1.google.com/complete/search?q=pena&client=opera-suggest-omnibox&hl=de | US | text | 139 b | whitelisted |
1612 | opera.exe | GET | 200 | 142.250.186.174:80 | http://clients1.google.com/complete/search?q=pen&client=opera-suggest-omnibox&hl=de | US | text | 157 b | whitelisted |
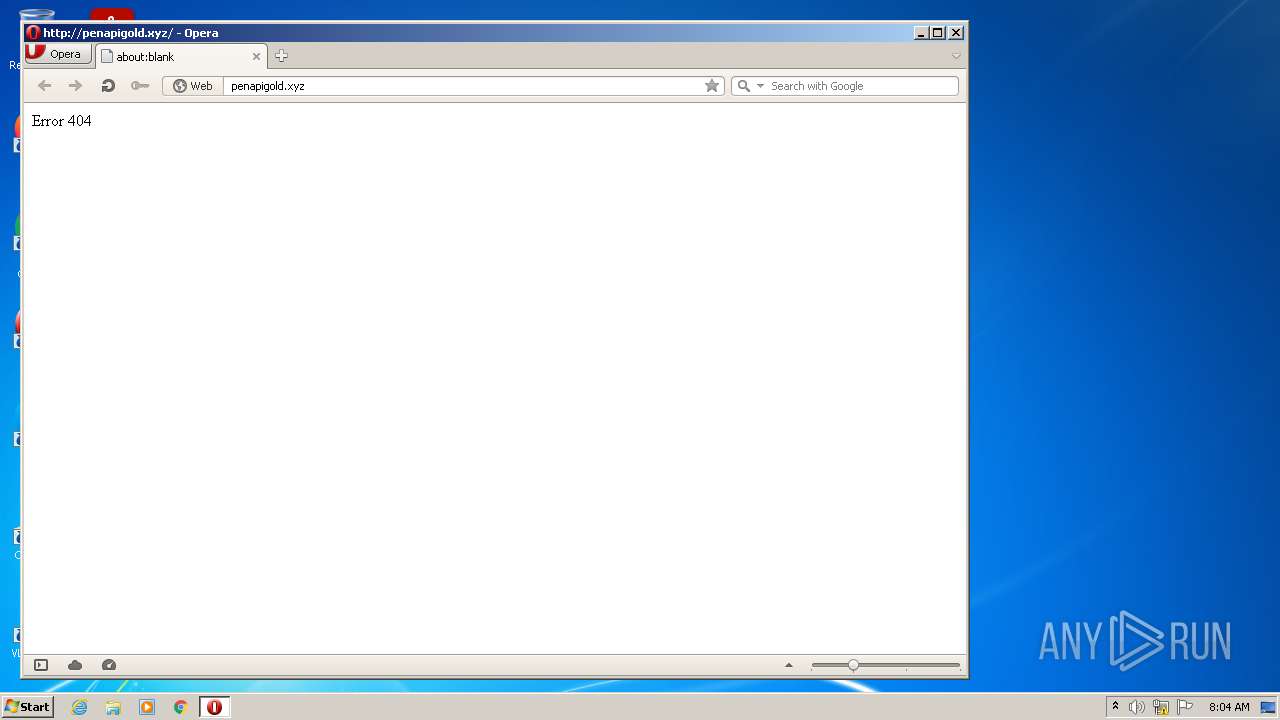
1612 | opera.exe | GET | 400 | 185.26.182.112:80 | http://sitecheck2.opera.com/?host=penapigold.xyz&hdn=M%2BHY2qNuR4gzmRDA3Gc09w== | unknown | html | 150 b | whitelisted |
1612 | opera.exe | GET | 200 | 104.21.58.35:80 | http://penapigold.xyz/ | US | text | 35 b | malicious |
1612 | opera.exe | GET | 404 | 104.21.58.35:80 | http://penapigold.xyz/new/net_api | US | binary | 25 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3848 | VerbKeys.exe | 95.140.236.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | GB | malicious |
2320 | VerbKeys.exe | 172.67.199.124:80 | penapigold.xyz | — | US | suspicious |
3048 | VerbKeys.exe | 178.79.242.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | whitelisted |
2928 | VerbKeys.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1612 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
1612 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1612 | opera.exe | 104.21.58.35:80 | penapigold.xyz | Cloudflare Inc | US | suspicious |
1612 | opera.exe | 142.250.186.174:80 | clients1.google.com | Google Inc. | US | whitelisted |
1612 | opera.exe | 185.26.182.112:80 | sitecheck2.opera.com | Opera Software AS | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
penapigold.xyz |
| malicious |
certs.opera.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2320 | VerbKeys.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1612 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1612 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1612 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1612 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |