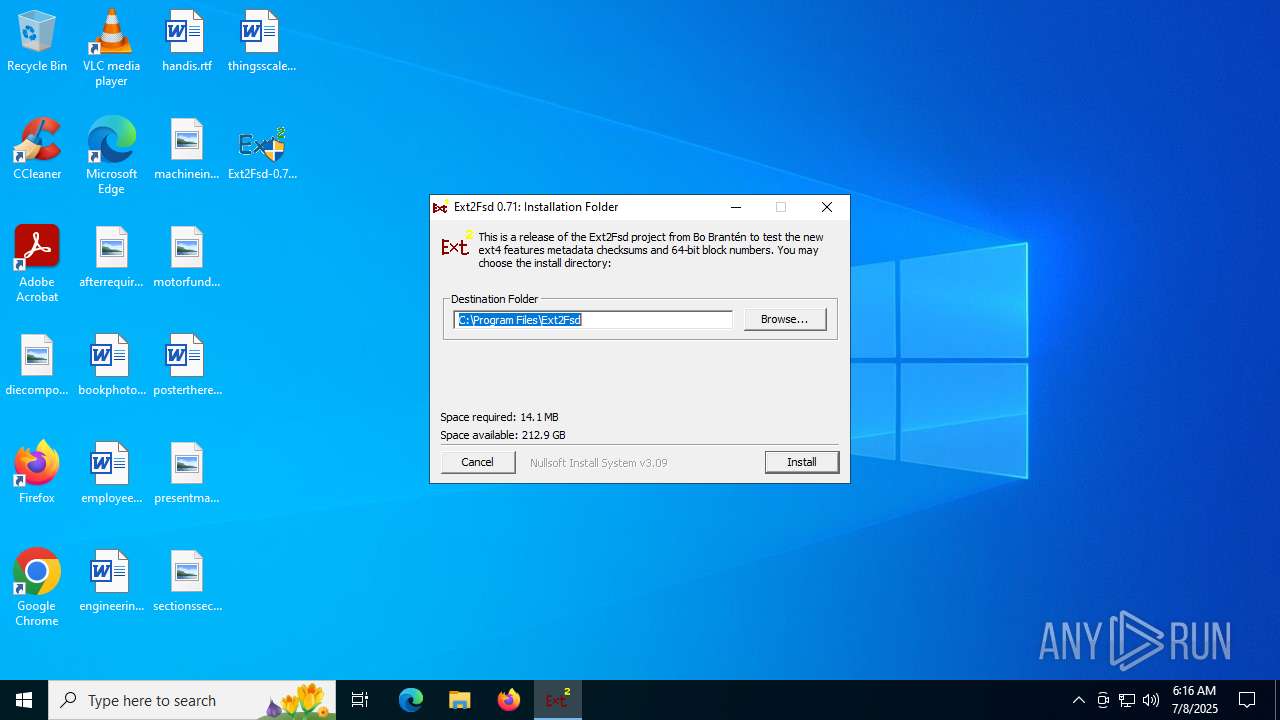
| File name: | Ext2Fsd-0.71-setup.exe |
| Full analysis: | https://app.any.run/tasks/8ed9c0c8-4da8-40e8-8e00-77361abe7c64 |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2025, 06:16:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | E1D7C469B083B7F99ED2D88D6640CBDD |
| SHA1: | 67FC34D65C2EE03D08FFD8D89C626B819C03ED95 |
| SHA256: | 3C127F8E70C6B056A0185850EFB71B9C45D2FF493B7DF6B7B648EB89EC84214D |
| SSDEEP: | 98304:tvi8OCS7s5LeT5IzkR86DbHGlQCz4luG8ft+TXDf9660h5Daf6vcv3elRzNGPR8a:JN3qDzCeMcX2AlRs6 |
MALICIOUS
Changes the autorun value in the registry
- rundll32.exe (PID: 2792)
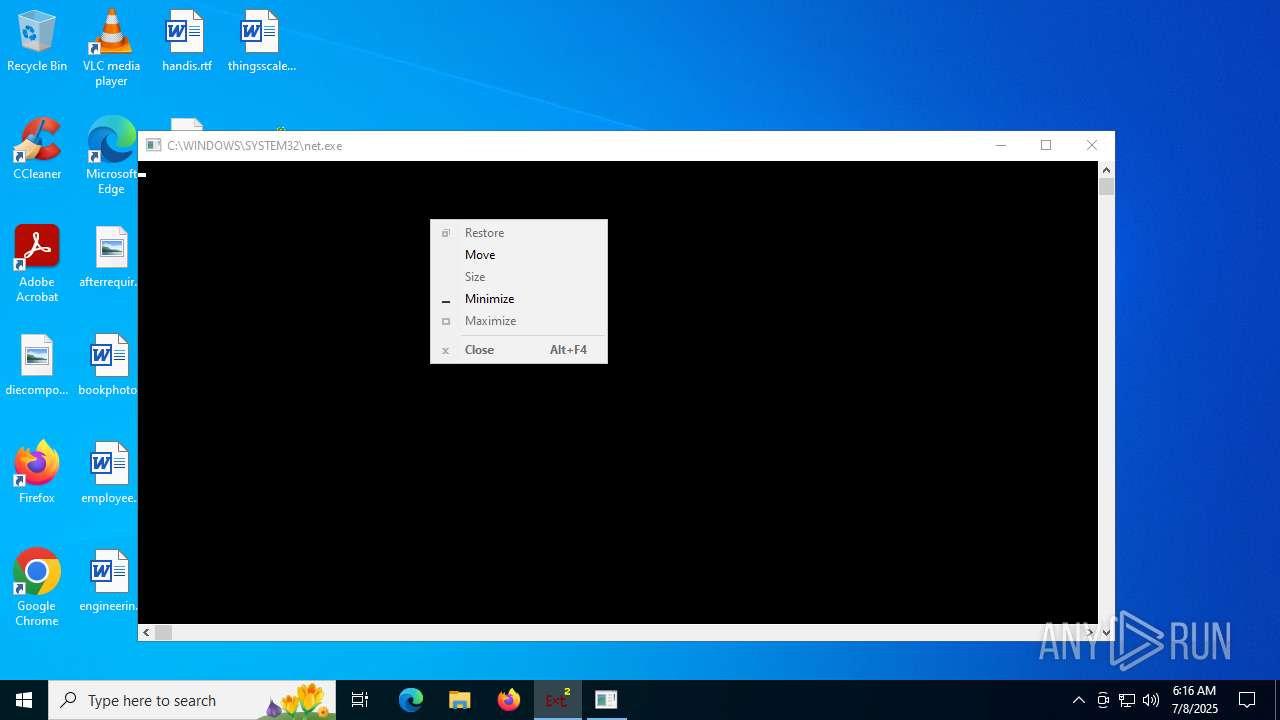
Starts NET.EXE for service management
- Ext2Fsd-0.71-setup.exe (PID: 6896)
- net.exe (PID: 3740)
SUSPICIOUS
The process drops C-runtime libraries
- Ext2Fsd-0.71-setup.exe (PID: 6896)
Process drops legitimate windows executable
- Ext2Fsd-0.71-setup.exe (PID: 6896)
Executable content was dropped or overwritten
- Ext2Fsd-0.71-setup.exe (PID: 6896)
- rundll32.exe (PID: 2792)
- drvinst.exe (PID: 6812)
Drops a system driver (possible attempt to evade defenses)
- Ext2Fsd-0.71-setup.exe (PID: 6896)
- rundll32.exe (PID: 2792)
- drvinst.exe (PID: 6812)
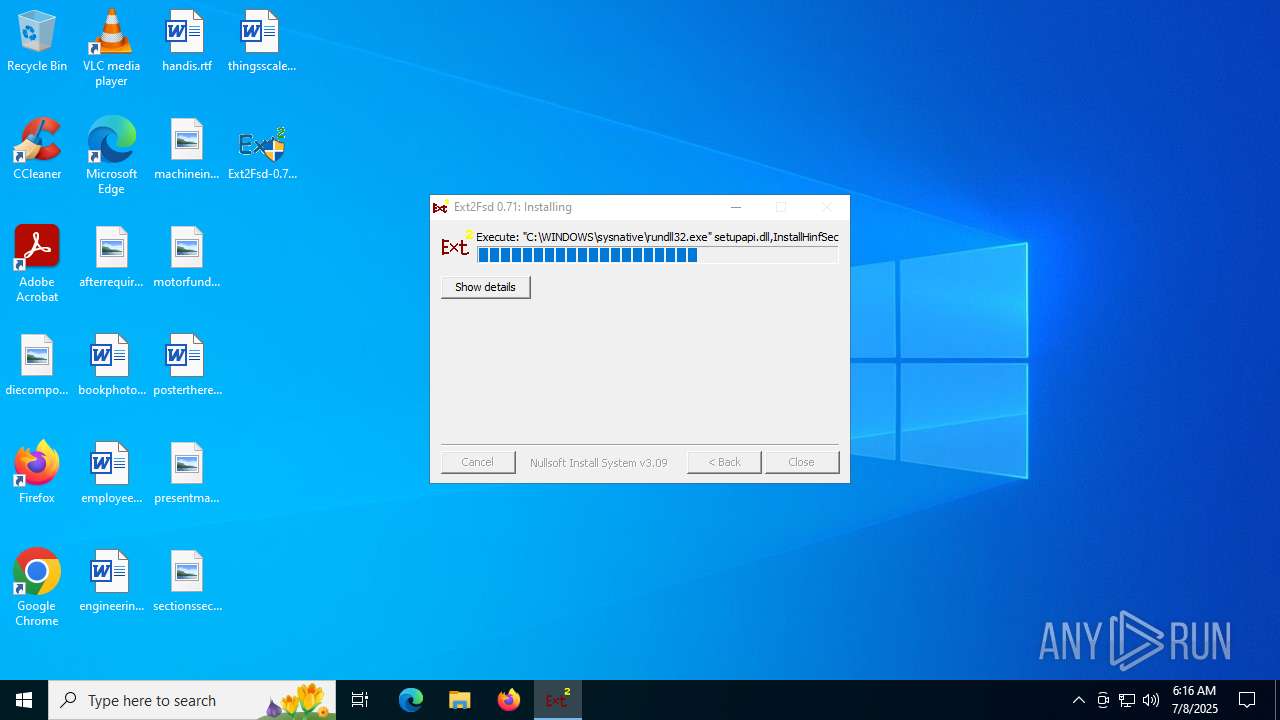
Uses RUNDLL32.EXE to load library
- Ext2Fsd-0.71-setup.exe (PID: 6896)
Creates files in the driver directory
- drvinst.exe (PID: 6812)
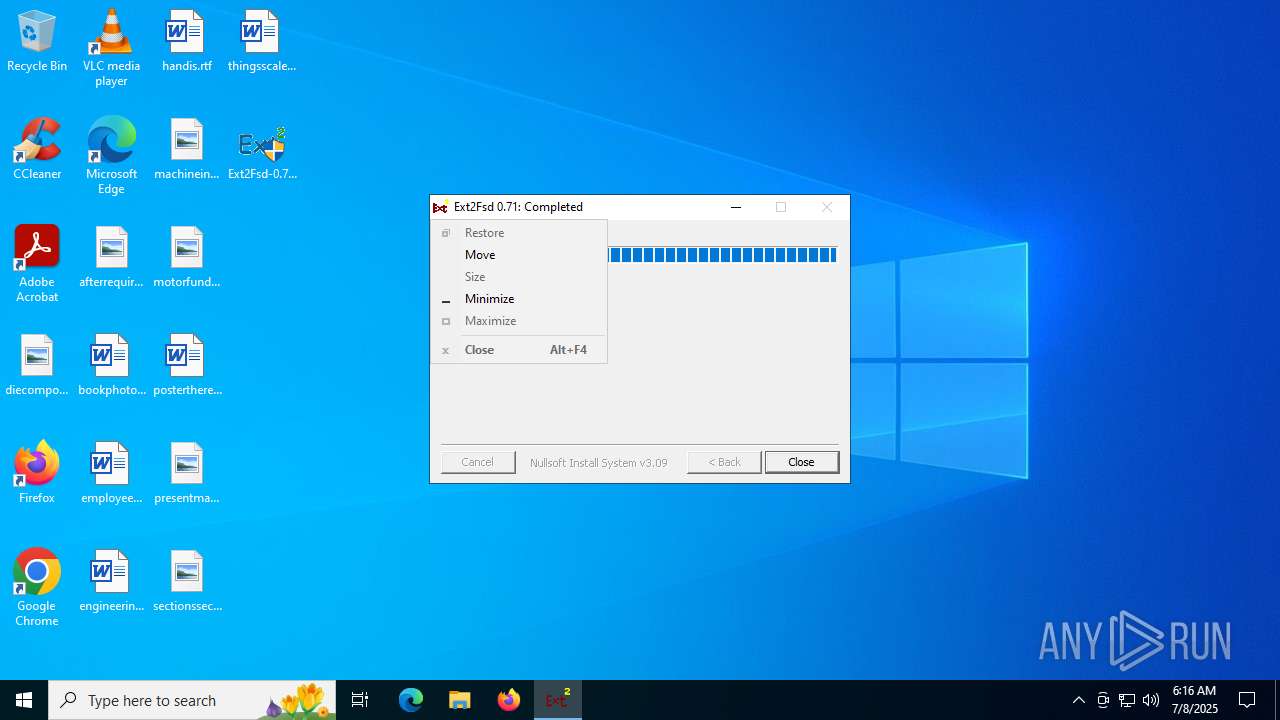
Creates a software uninstall entry
- Ext2Fsd-0.71-setup.exe (PID: 6896)
There is functionality for taking screenshot (YARA)
- Ext2Fsd-0.71-setup.exe (PID: 6896)
INFO
Checks supported languages
- Ext2Fsd-0.71-setup.exe (PID: 6896)
- drvinst.exe (PID: 6812)
- Ext2Srv.exe (PID: 6384)
The sample compiled with english language support
- Ext2Fsd-0.71-setup.exe (PID: 6896)
- rundll32.exe (PID: 2792)
- drvinst.exe (PID: 6812)
Creates files in the program directory
- Ext2Fsd-0.71-setup.exe (PID: 6896)
Reads the computer name
- Ext2Fsd-0.71-setup.exe (PID: 6896)
- Ext2Srv.exe (PID: 6384)
Create files in a temporary directory
- rundll32.exe (PID: 2792)
Creates files in the driver directory
- rundll32.exe (PID: 2792)
Reads security settings of Internet Explorer
- runonce.exe (PID: 5564)
Reads the time zone
- runonce.exe (PID: 5564)
Manual execution by a user
- grpconv.exe (PID: 728)
Launching a file from a Registry key
- rundll32.exe (PID: 2792)
Checks proxy server information
- slui.exe (PID: 1508)
Reads the software policy settings
- slui.exe (PID: 1508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:07:02 02:09:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 184832 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3532 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
151
Monitored processes
13
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | grpconv -o | C:\Windows\System32\grpconv.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1508 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\Desktop\Ext2Fsd-0.71-setup.exe" | C:\Users\admin\Desktop\Ext2Fsd-0.71-setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2792 | "C:\WINDOWS\sysnative\rundll32.exe" setupapi.dll,InstallHinfSection DefaultInstall 132 C:\Program Files\Ext2Fsd\Ext2Fsd.inf | C:\Windows\System32\rundll32.exe | Ext2Fsd-0.71-setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Ext2Srv.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3740 | "net.exe" start Ext2Fsd | C:\Windows\SysWOW64\net.exe | — | Ext2Fsd-0.71-setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4512 | C:\WINDOWS\system32\net1 start Ext2Fsd | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5564 | "C:\WINDOWS\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 272
Read events
4 259
Write events
12
Delete events
1
Modification events
| (PID) Process: | (2792) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Ext2Fsd\Parameters |
| Operation: | write | Name: | AutoMount |
Value: 1 | |||
| (PID) Process: | (2792) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Ext2Fsd\Parameters |
| Operation: | write | Name: | CheckingBitmap |
Value: 0 | |||
| (PID) Process: | (2792) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Ext2Fsd\Parameters |
| Operation: | write | Name: | Ext3ForceWriting |
Value: 1 | |||
| (PID) Process: | (2792) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Ext2Fsd\Parameters |
| Operation: | write | Name: | WritingSupport |
Value: 1 | |||
| (PID) Process: | (2792) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Ext2Fsd\Parameters |
| Operation: | write | Name: | CodePage |
Value: utf8 | |||
| (PID) Process: | (2792) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | GrpConv |
Value: grpconv -o | |||
| (PID) Process: | (5564) runonce.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | GrpConv |
Value: grpconv -o | |||
| (PID) Process: | (2792) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (2792) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\Ext2Fsd |
| Operation: | write | Name: | EventMessageFile |
Value: %SystemRoot%\System32\IoLogMsg.Dll | |||
| (PID) Process: | (2792) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\Ext2Fsd |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
Executable files
13
Suspicious files
12
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6896 | Ext2Fsd-0.71-setup.exe | C:\Program Files\Ext2Fsd\mfc140.dll | executable | |
MD5:824D14B924F8F91116CE09B927C22873 | SHA256:694DDC3842544243C31B586325DB98E30A29EA86D3E96E95DC63CCE537F944F8 | |||
| 6896 | Ext2Fsd-0.71-setup.exe | C:\Program Files\Ext2Fsd\vcruntime140_1.dll | executable | |
MD5:EB49C1D33B41EB49DFED58AAFA9B9A8F | SHA256:6D3A6CDE6FC4D3C79AABF785C04D2736A3E2FD9B0366C9B741F054A13ECD939E | |||
| 6896 | Ext2Fsd-0.71-setup.exe | C:\Program Files\Ext2Fsd\Documents\FAQ.txt | text | |
MD5:683F7D213C0832E09DC71148B2A4EB38 | SHA256:CB49AF4DE44061A0D4EF0B38BE09B431BD8AE35DEE1184CF72E5C910AD5B2509 | |||
| 2792 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{c631e910-ef49-7040-a5a5-a7e960235a6c}\SET77A1.tmp | binary | |
MD5:D36684B97C4805C77CAF463CEBF8E176 | SHA256:B351054958160026B93596296DBA751D2E4345F6ADDAF26F1226441BC48AC635 | |||
| 2792 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{c631e910-ef49-7040-a5a5-a7e960235a6c}\Ext2Fsd.inf | binary | |
MD5:D36684B97C4805C77CAF463CEBF8E176 | SHA256:B351054958160026B93596296DBA751D2E4345F6ADDAF26F1226441BC48AC635 | |||
| 6896 | Ext2Fsd-0.71-setup.exe | C:\Program Files\Ext2Fsd\Documents\readme.txt | text | |
MD5:50A16A34BA25E39296B9217DDDAEFEF6 | SHA256:00631F1CD2F52D1219626206E140830C5271FA562F751E45FEF34140A7E88386 | |||
| 2792 | rundll32.exe | C:\Windows\INF\setupapi.dev.log | text | |
MD5:B92A9D65E2E9117840C7FB6CAD8C3943 | SHA256:D4D85C81F746ED41B21CAA317D2E0D0DA69721884E03D291E141334EAD683C55 | |||
| 2792 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{c631e910-ef49-7040-a5a5-a7e960235a6c}\Ext2Fsd.sys | executable | |
MD5:96CEA9B6EB7BAB8E55CD9EA12CF863E5 | SHA256:06F6B4A6BC7AAF568D0442A3415394B2B7806C1BD94D35B314BEBFA0993898D9 | |||
| 2792 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{c631e910-ef49-7040-a5a5-a7e960235a6c}\SET77A2.tmp | executable | |
MD5:96CEA9B6EB7BAB8E55CD9EA12CF863E5 | SHA256:06F6B4A6BC7AAF568D0442A3415394B2B7806C1BD94D35B314BEBFA0993898D9 | |||
| 6812 | drvinst.exe | C:\Windows\System32\DriverStore\Temp\{86244f55-a55c-ef4e-9edb-a1e95fb3b518}\SET77FF.tmp | executable | |
MD5:96CEA9B6EB7BAB8E55CD9EA12CF863E5 | SHA256:06F6B4A6BC7AAF568D0442A3415394B2B7806C1BD94D35B314BEBFA0993898D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
36
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3688 | RUXIMICS.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3688 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 200 | 20.190.160.22:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 400 | 20.190.160.22:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3688 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
3688 | RUXIMICS.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |