| File name: | RDPConf.exe |
| Full analysis: | https://app.any.run/tasks/9c6ed0f4-12e6-42d3-8345-a67a25688828 |
| Verdict: | No threats detected |
| Analysis date: | January 30, 2020, 13:06:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 03FB8E478F4BA100D37A136231FA2F78 |
| SHA1: | 98685C37A6140701220C476449BEE3F4E1FD28EF |
| SHA256: | 3C0E5D6863B03283AFDA9BD188501757D47DC57FC4BBA2BDBB0D9BAA34487FE0 |
| SSDEEP: | 24576:JwewFB5btX9uALSTRMab+wBySRX7ADs9UXOAPOA:At9UMSJADsaXOAPOA |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (79.7) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (8.6) |
| .exe | | | Win16/32 Executable Delphi generic (3.9) |
| .exe | | | Generic Win/DOS Executable (3.8) |
| .exe | | | DOS Executable Generic (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:12:27 19:29:54+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 763904 |
| InitializedDataSize: | 331264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xbbc78 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.0.0 |
| ProductVersionNumber: | 1.6.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Stas'M Corp. |
| FileDescription: | RDP Configuration Program |
| FileVersion: | 1.4.0.0 |
| InternalName: | RDPConf |
| LegalCopyright: | Copyright © Stas'M Corp. 2017 |
| LegalTrademarks: | Stas'M Corp. |
| OriginalFileName: | RDPConf.exe |
| ProductName: | RDP Host Support |
| ProductVersion: | 1.6.2.0 |
| Comments: | http://stascorp.com |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Dec-2017 18:29:54 |
| Detected languages: |
|
| CompanyName: | Stas'M Corp. |
| FileDescription: | RDP Configuration Program |
| FileVersion: | 1.4.0.0 |
| InternalName: | RDPConf |
| LegalCopyright: | Copyright © Stas'M Corp. 2017 |
| LegalTrademarks: | Stas'M Corp. |
| OriginalFilename: | RDPConf.exe |
| ProductName: | RDP Host Support |
| ProductVersion: | 1.6.2.0 |
| Comments: | http://stascorp.com |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 27-Dec-2017 18:29:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B986C | 0x000B9A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44185 |
.itext | 0x000BB000 | 0x00000D38 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.98888 |
.data | 0x000BC000 | 0x00002430 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.94644 |
.bss | 0x000BF000 | 0x000052F4 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C5000 | 0x000031D8 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.03245 |
.didata | 0x000C9000 | 0x0000029E | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.85578 |
.tls | 0x000CA000 | 0x0000003C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000CB000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.210826 |
.reloc | 0x000CC000 | 0x00010F14 | 0x00011000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.68711 |
.rsrc | 0x000DD000 | 0x0003A000 | 0x0003A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.38217 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92007 | 850 | UNKNOWN | Russian - Russia | RT_MANIFEST |
2 | 5.53065 | 1128 | UNKNOWN | Russian - Russia | RT_ICON |
3 | 6.87877 | 1720 | UNKNOWN | Russian - Russia | RT_ICON |
4 | 6.71095 | 2440 | UNKNOWN | Russian - Russia | RT_ICON |
5 | 5.69685 | 4264 | UNKNOWN | Russian - Russia | RT_ICON |
6 | 6.44687 | 6760 | UNKNOWN | Russian - Russia | RT_ICON |
7 | 5.58657 | 9640 | UNKNOWN | Russian - Russia | RT_ICON |
8 | 5.48099 | 16936 | UNKNOWN | Russian - Russia | RT_ICON |
9 | 5.3158 | 67624 | UNKNOWN | Russian - Russia | RT_ICON |
4081 | 2.9065 | 240 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
msimg32.dll |
ole32.dll |
oleaut32.dll |
user32.dll |
version.dll |
winspool.drv |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | "C:\Users\admin\AppData\Local\Temp\RDPConf.exe" | C:\Users\admin\AppData\Local\Temp\RDPConf.exe | explorer.exe | ||||||||||||
User: admin Company: Stas'M Corp. Integrity Level: HIGH Description: RDP Configuration Program Exit code: 0 Version: 1.4.0.0 Modules
| |||||||||||||||
| 3952 | "C:\Users\admin\AppData\Local\Temp\RDPConf.exe" | C:\Users\admin\AppData\Local\Temp\RDPConf.exe | — | explorer.exe | |||||||||||
User: admin Company: Stas'M Corp. Integrity Level: MEDIUM Description: RDP Configuration Program Exit code: 3221226540 Version: 1.4.0.0 Modules
| |||||||||||||||
Total events
969
Read events
960
Write events
9
Delete events
0
Modification events
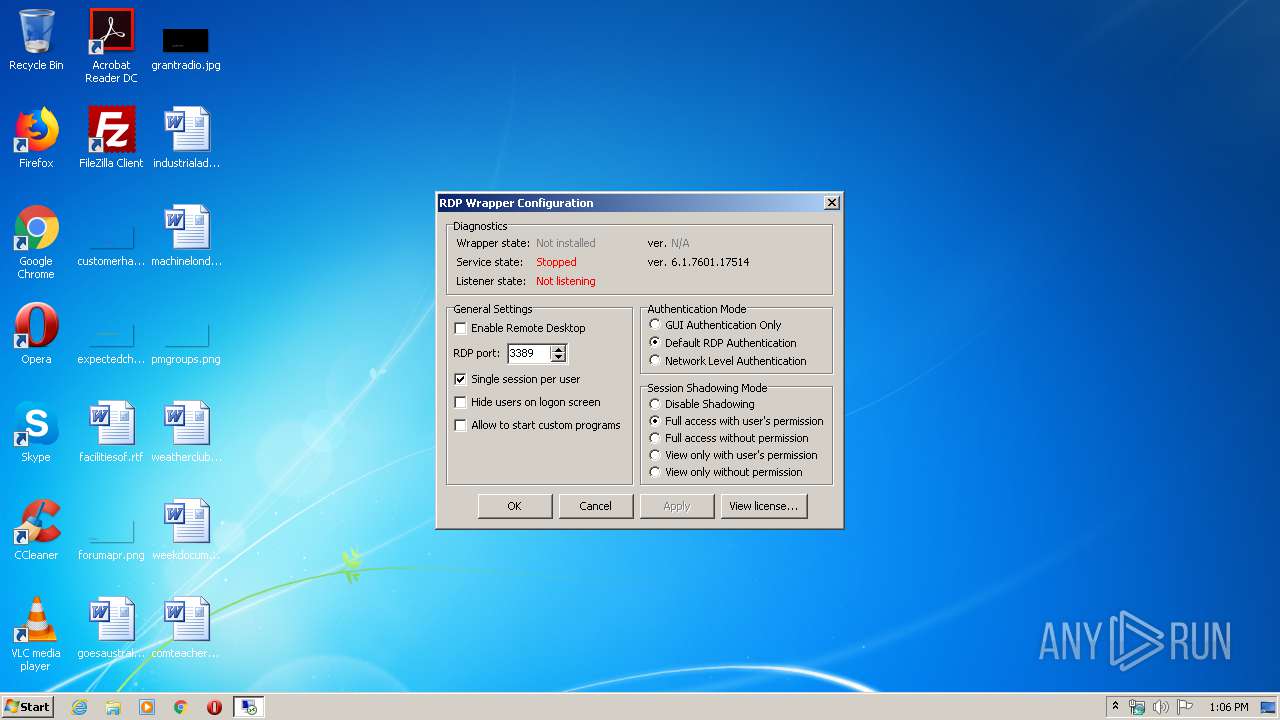
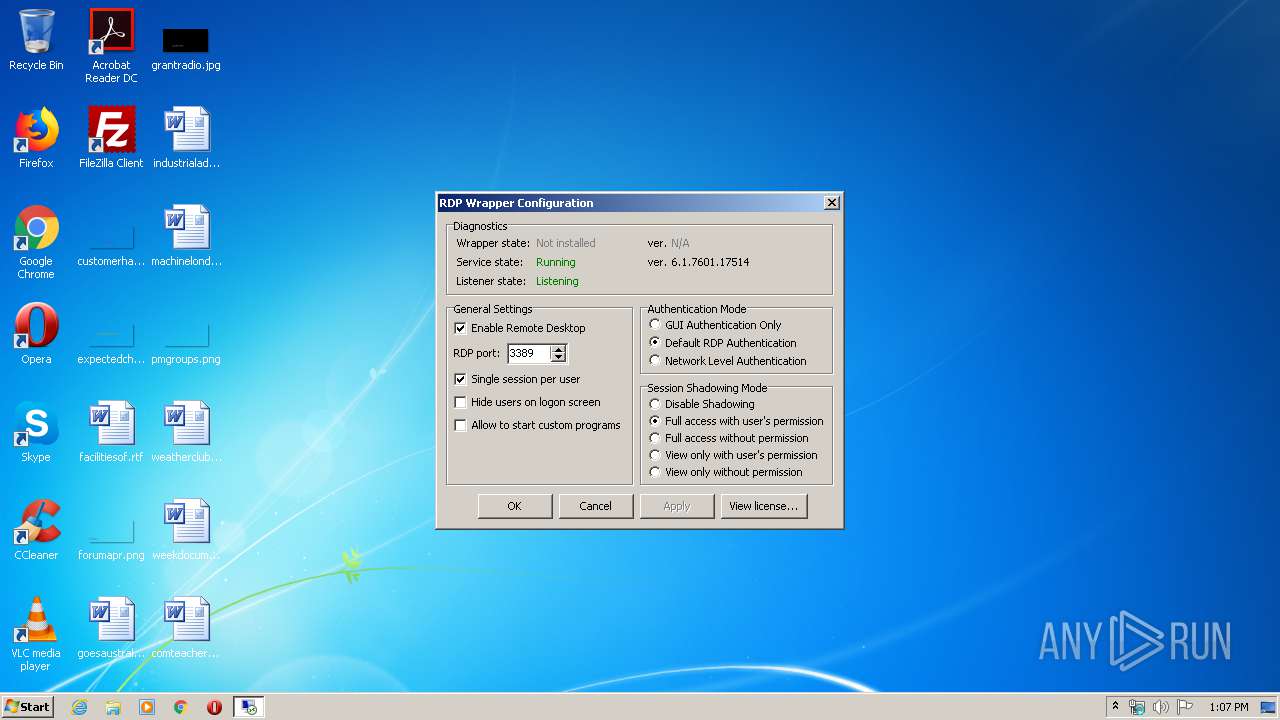
| (PID) Process: | (2132) RDPConf.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server |
| Operation: | write | Name: | fDenyTSConnections |
Value: 0 | |||
| (PID) Process: | (2132) RDPConf.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server |
| Operation: | write | Name: | fSingleSessionPerUser |
Value: 1 | |||
| (PID) Process: | (2132) RDPConf.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server |
| Operation: | write | Name: | HonorLegacySettings |
Value: 0 | |||
| (PID) Process: | (2132) RDPConf.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server\WinStations\RDP-Tcp |
| Operation: | write | Name: | PortNumber |
Value: 3389 | |||
| (PID) Process: | (2132) RDPConf.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server\WinStations\RDP-Tcp |
| Operation: | write | Name: | SecurityLayer |
Value: 1 | |||
| (PID) Process: | (2132) RDPConf.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server\WinStations\RDP-Tcp |
| Operation: | write | Name: | UserAuthentication |
Value: 0 | |||
| (PID) Process: | (2132) RDPConf.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server\WinStations\RDP-Tcp |
| Operation: | write | Name: | Shadow |
Value: 1 | |||
| (PID) Process: | (2132) RDPConf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services |
| Operation: | write | Name: | Shadow |
Value: 1 | |||
| (PID) Process: | (2132) RDPConf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | dontdisplaylastusername |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report