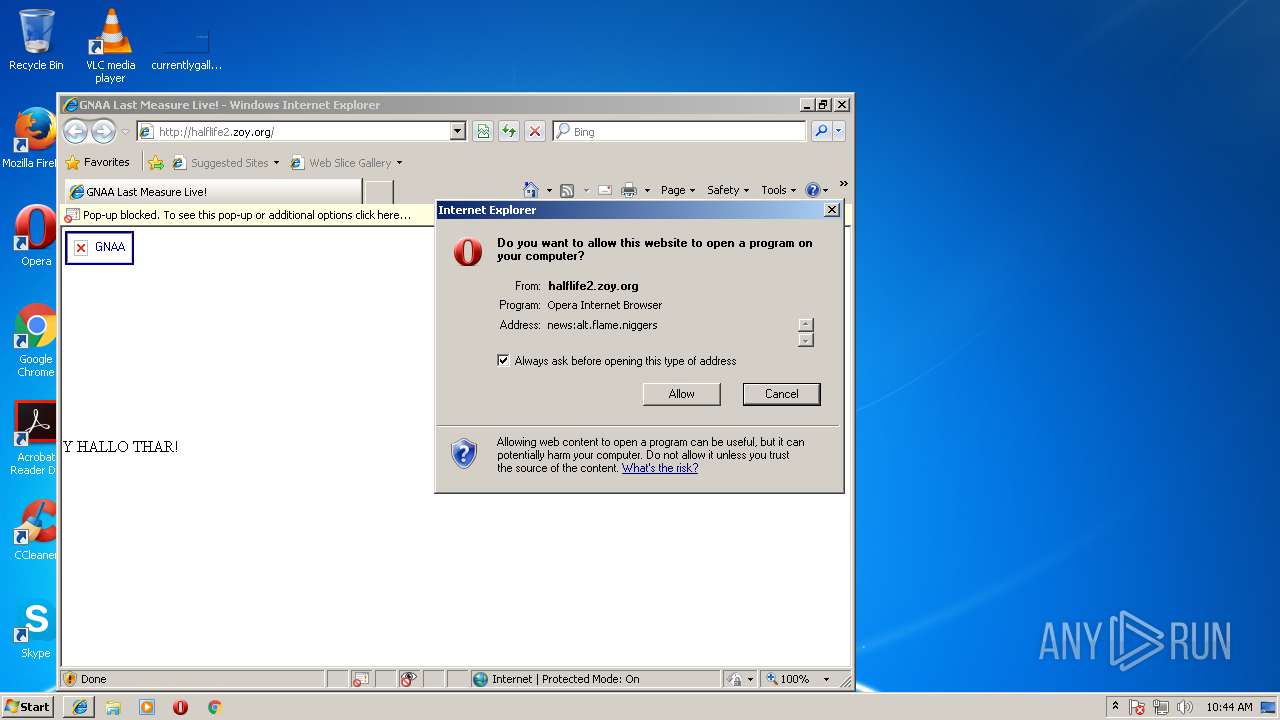
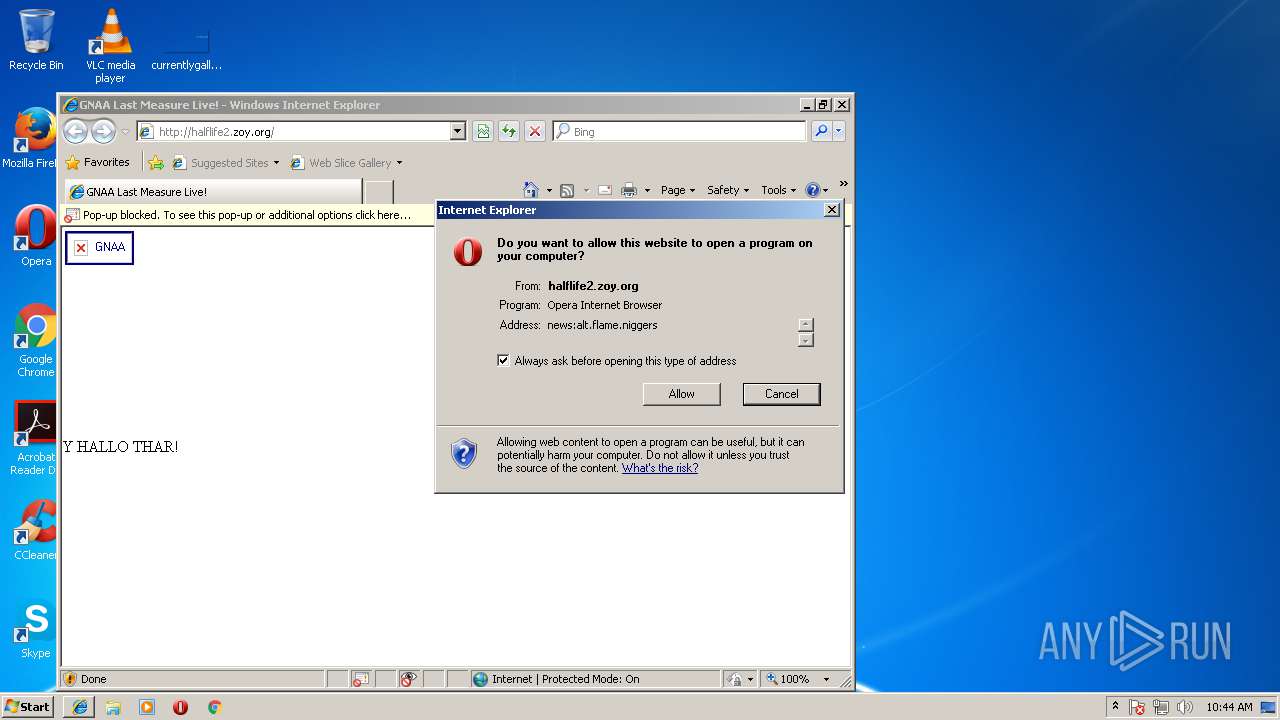
| URL: | http://halflife2.zoy.org |
| Full analysis: | https://app.any.run/tasks/82a86c8c-b251-4954-b8d4-79c899b3682b |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2018, 09:44:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6E12560761706448F73F7422E7AF0BD7 |
| SHA1: | EB078E2999D94EEDEA4F93F060FAF73025C863BB |
| SHA256: | 3BFDBA68B8ED0CD43116DD69051BF96DE44E7743FCD43A3EDFC2B7BEB2544088 |
| SSDEEP: | 3:N1KWEbCA7KcoCn:CW4Ocf |
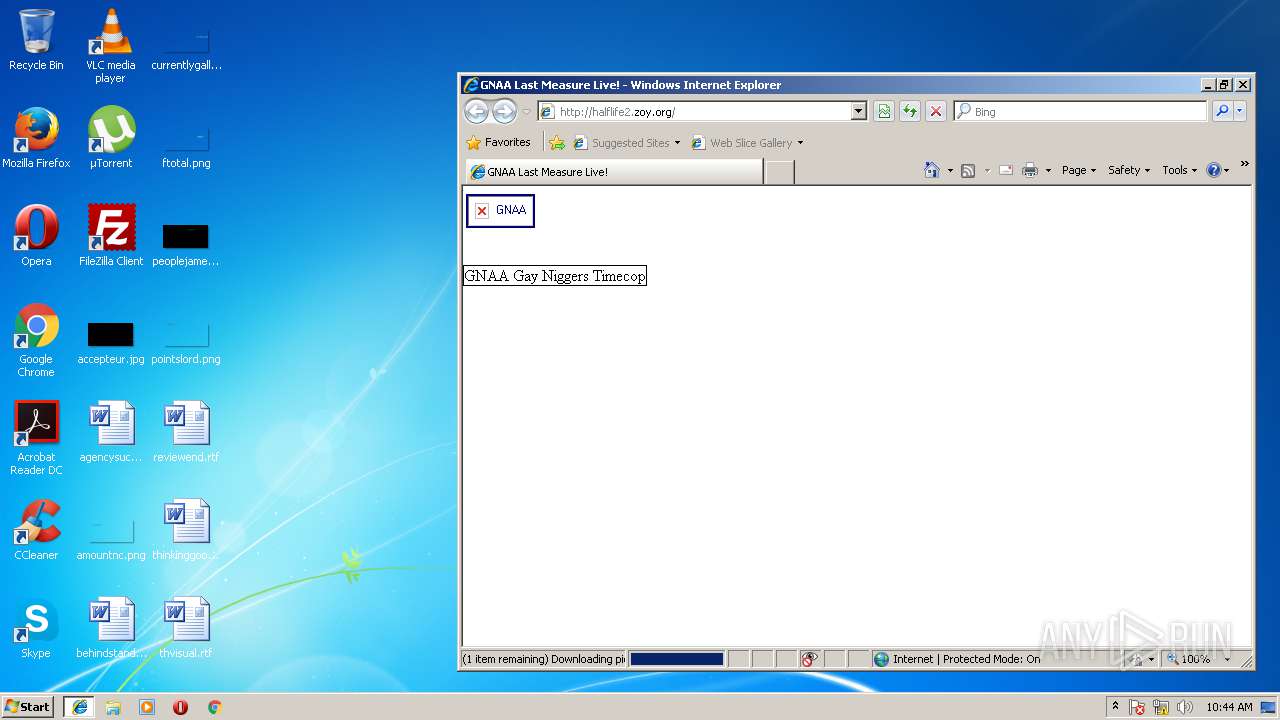
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- FlashUtil32_26_0_0_137_ActiveX.exe (PID: 1732)
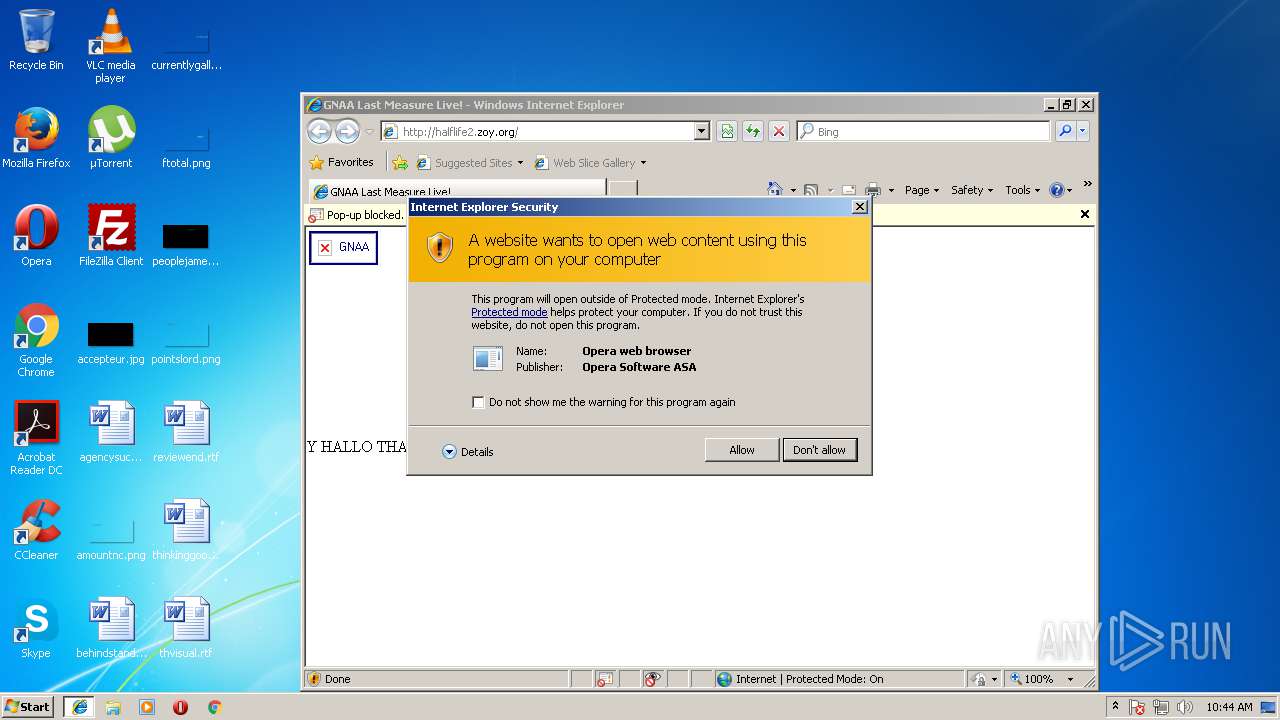
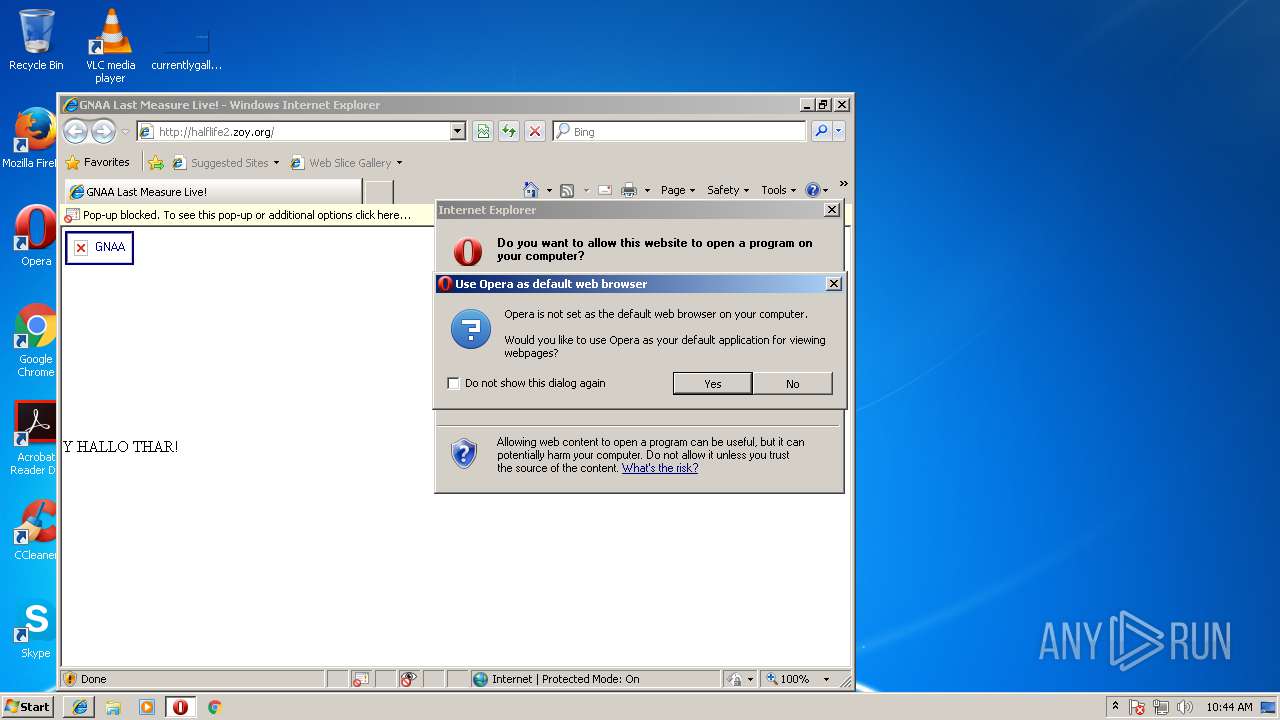
Modifies the open verb of a shell class
- opera.exe (PID: 3556)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3204)
Dropped object may contain URL's
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 3204)
- opera.exe (PID: 3556)
Creates files in the user directory
- iexplore.exe (PID: 3204)
- iexplore.exe (PID: 3348)
- opera.exe (PID: 3556)
Reads Internet Cache Settings
- iexplore.exe (PID: 3348)
Reads internet explorer settings
- iexplore.exe (PID: 3348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1732 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,137 Modules
| |||||||||||||||
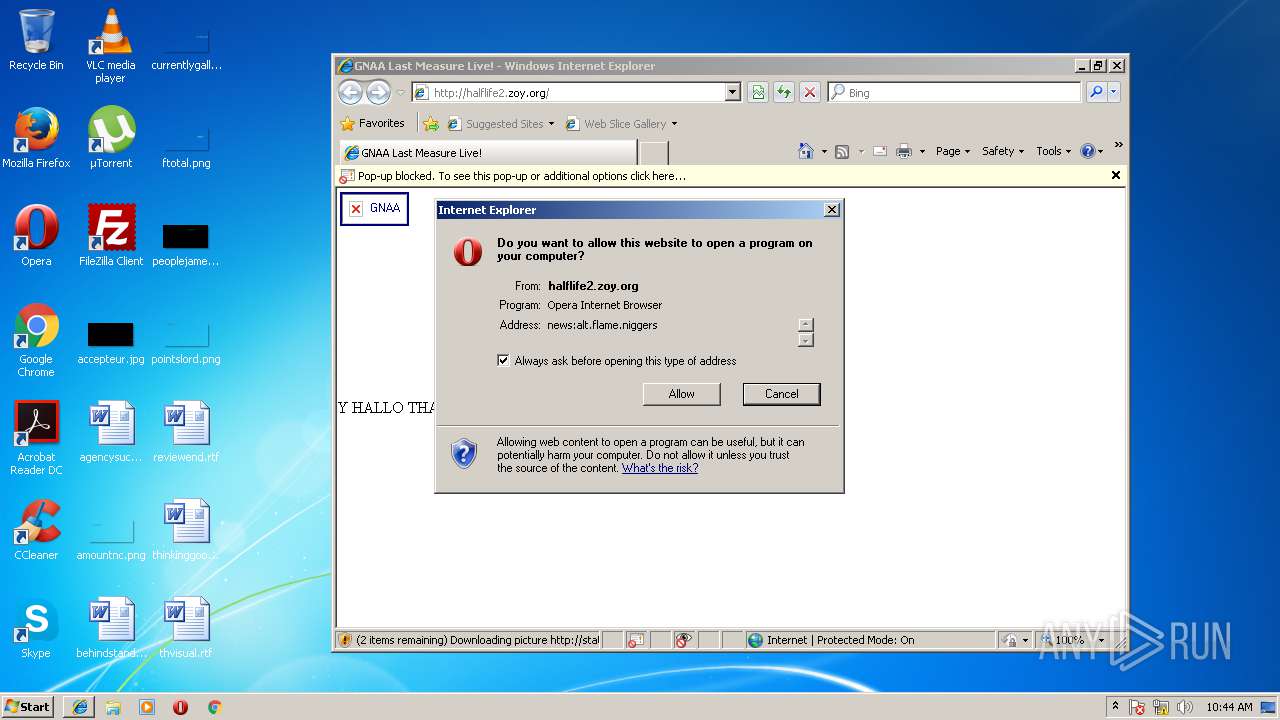
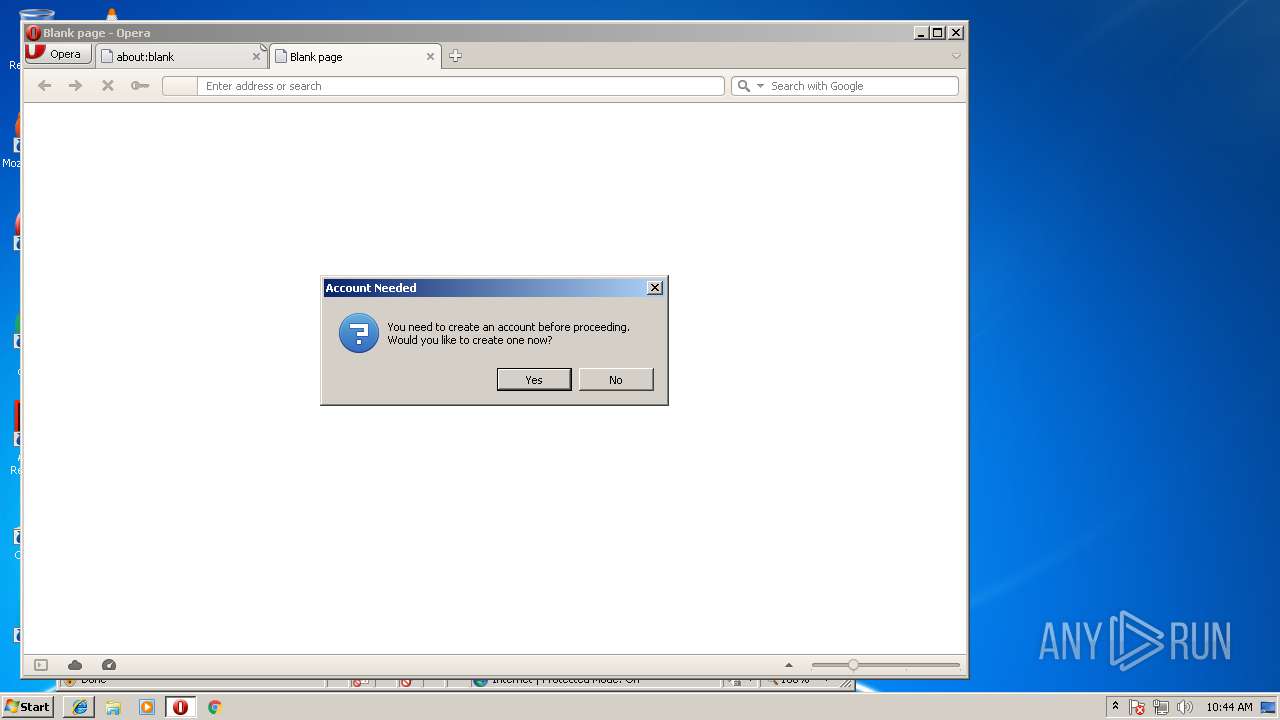
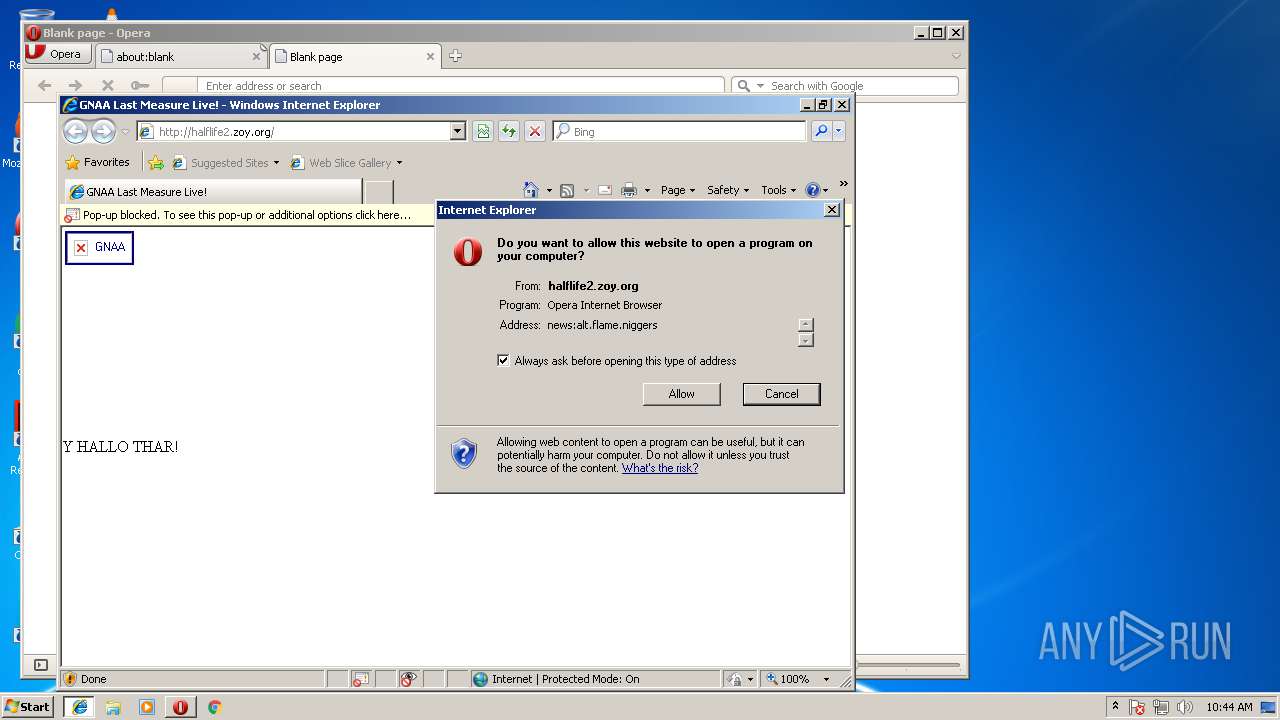
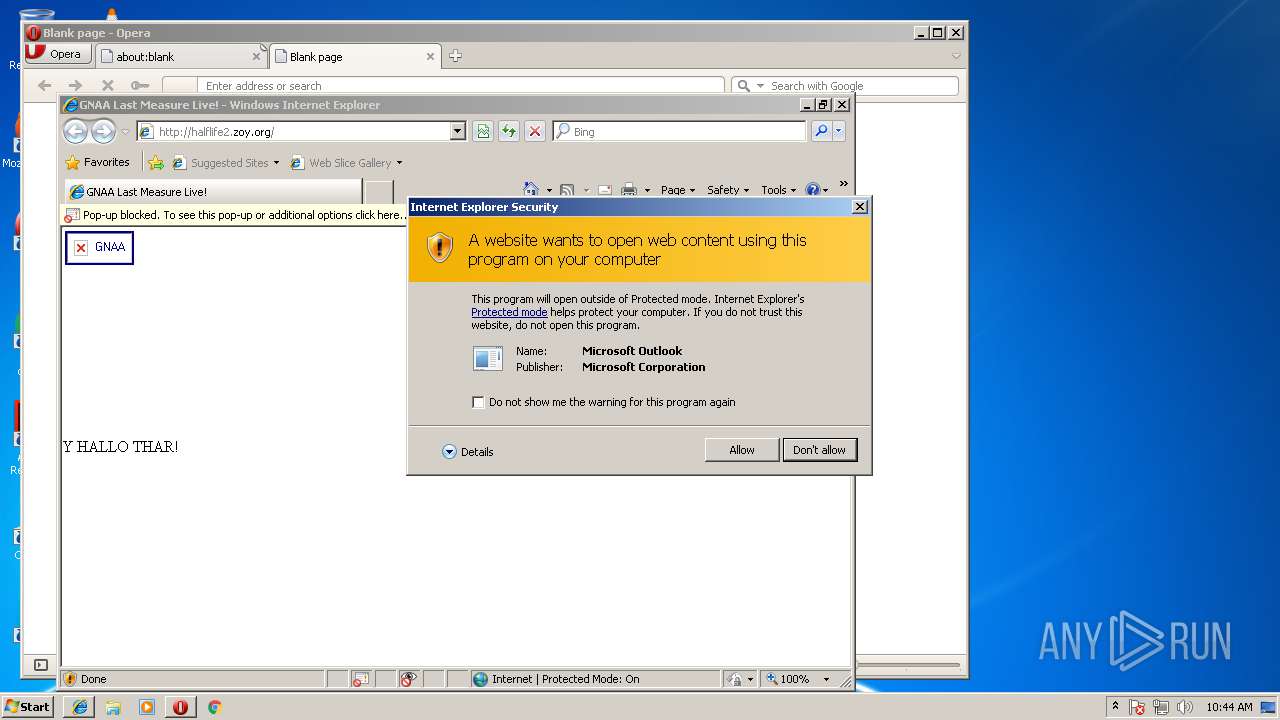
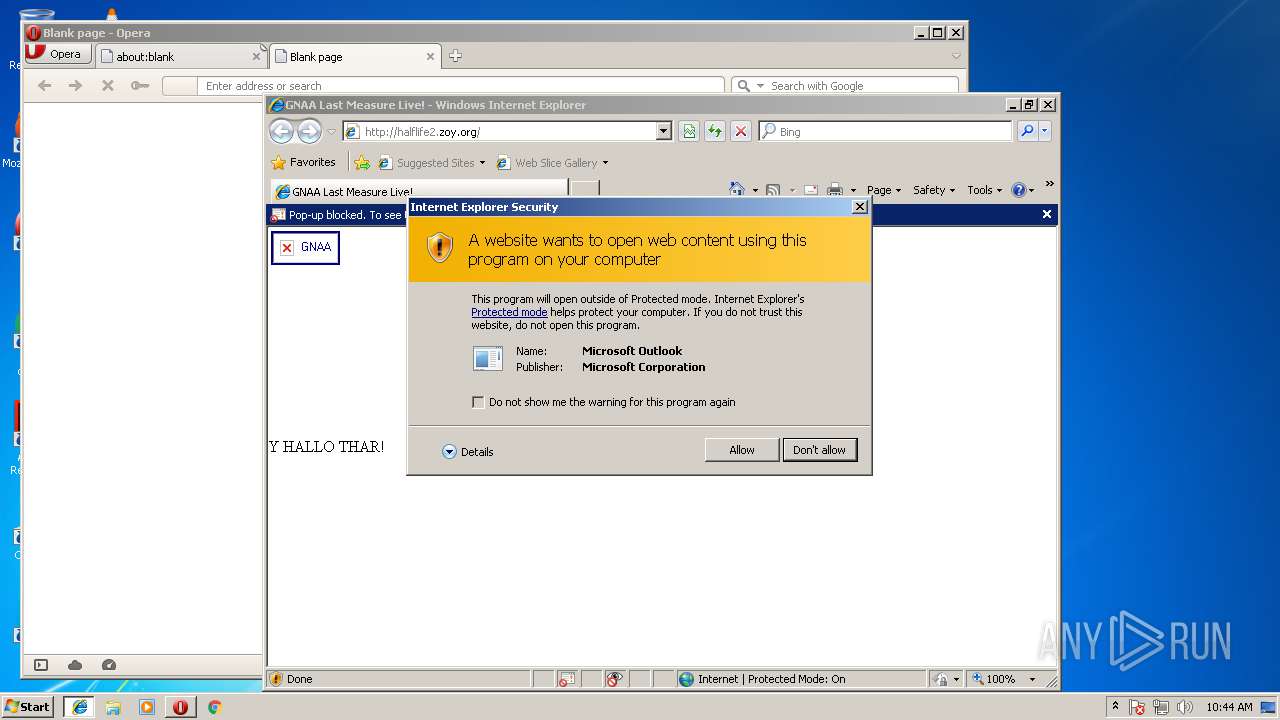
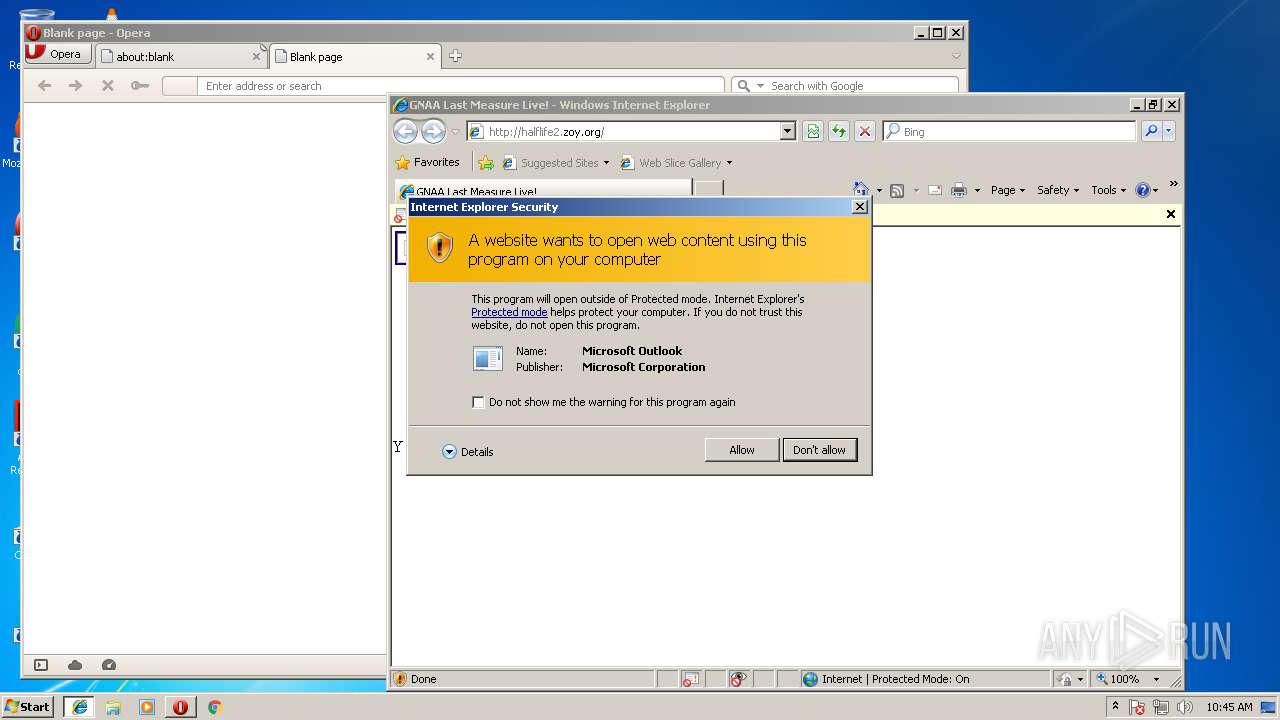
| 2240 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:JOIN@THE.GNAA?subject=2006_RECRUITMENT_DRIVE&body=www.gnaa.us" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
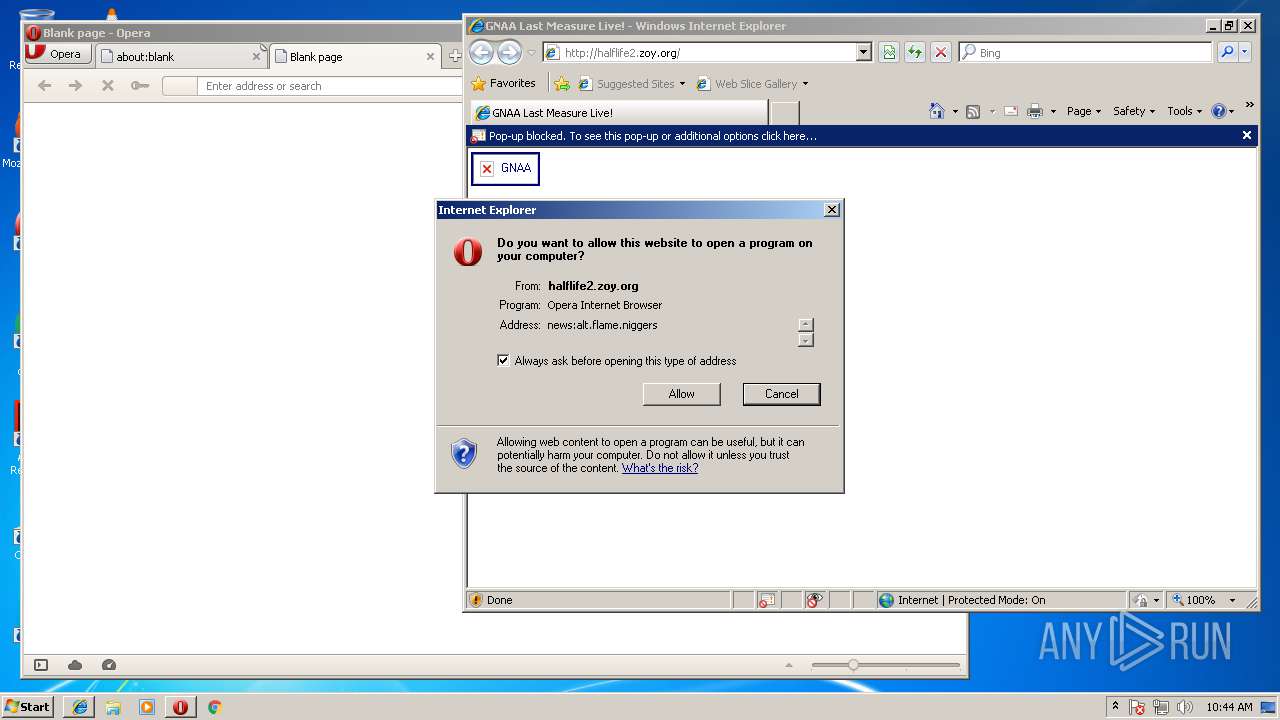
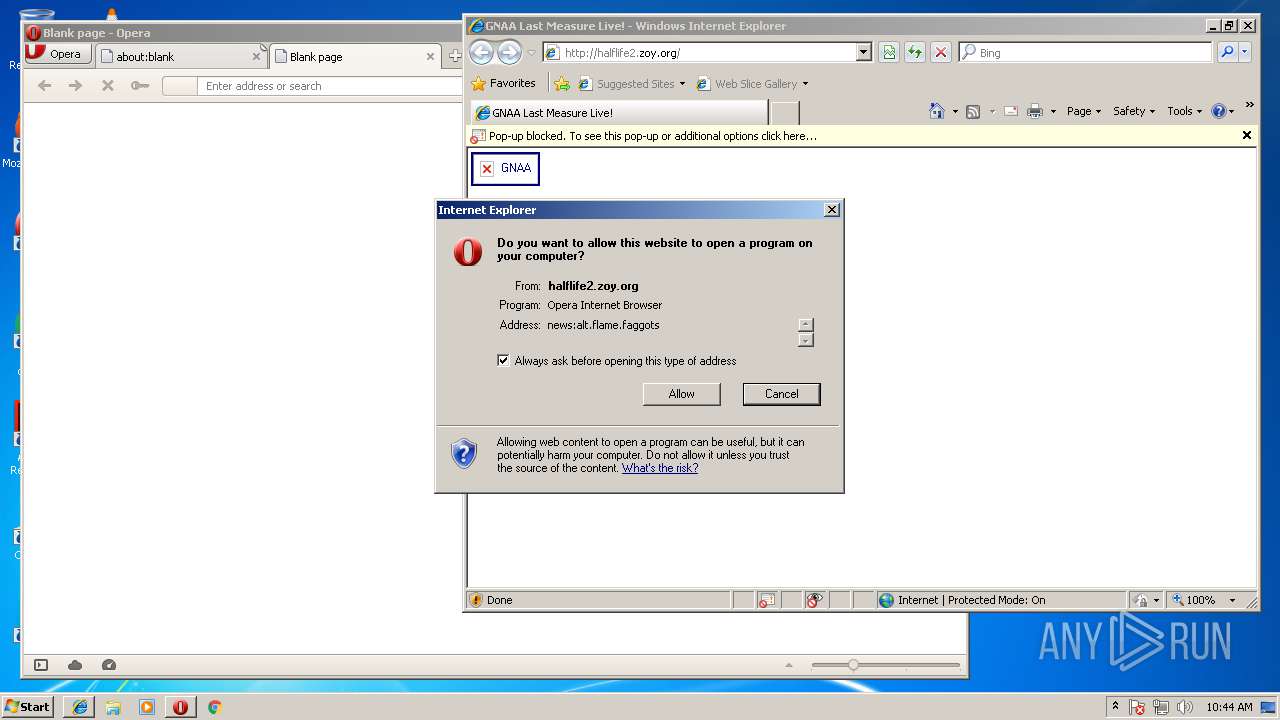
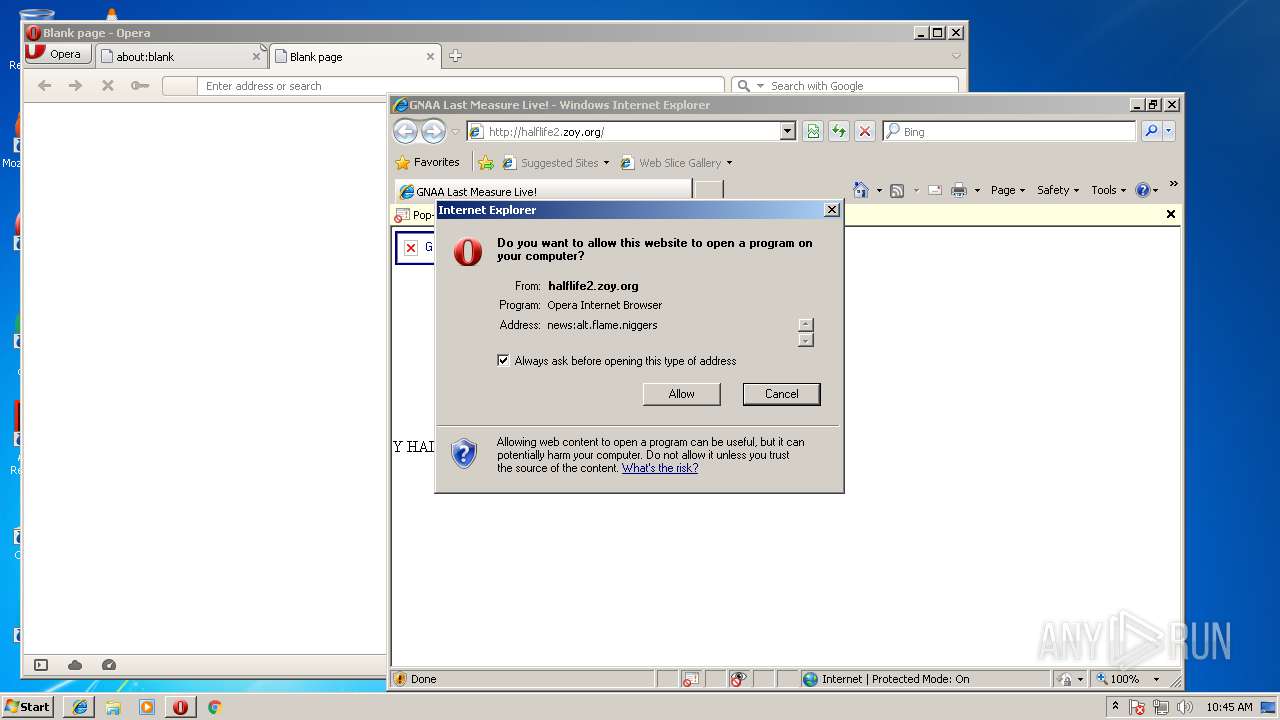
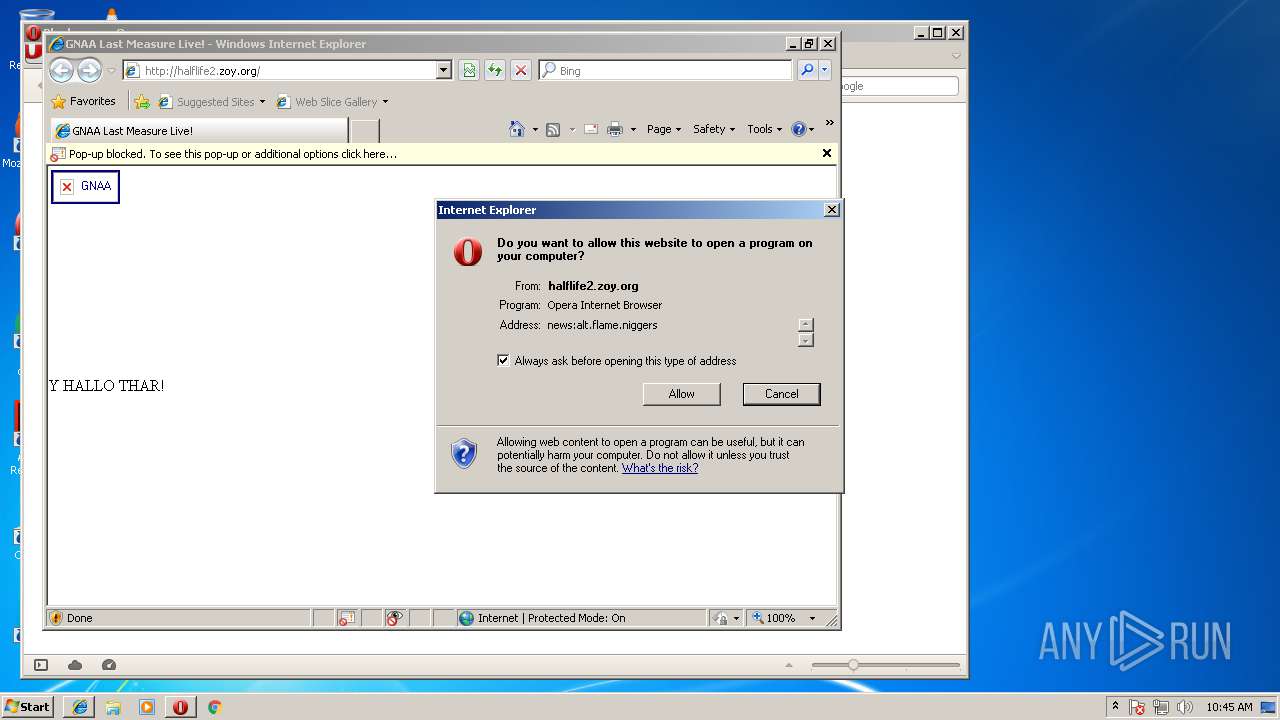
| 2676 | "C:\Program Files\Opera\opera.exe" "news:alt.flame.niggers" | C:\Program Files\Opera\opera.exe | — | iexplore.exe | |||||||||||
User: admin Company: Opera Software Integrity Level: LOW Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2796 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:JOIN@THE.GNAA?subject=2006_RECRUITMENT_DRIVE&body=www.gnaa.us" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3204 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3348 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3204 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3380 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:JOIN@THE.GNAA?subject=2006_RECRUITMENT_DRIVE&body=www.gnaa.us" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3556 | "C:\Program Files\Opera\opera.exe" "news:alt.flame.niggers" | C:\Program Files\Opera\opera.exe | iexplore.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
778
Read events
584
Write events
185
Delete events
9
Modification events
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006B000000010000000000000000000000000000000000000000000000400C35B347C7D301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A801640000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {E05B7E17-59B6-11E8-B27F-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 5 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E20705000400110009002C0017000000 | |||
Executable files
0
Suspicious files
17
Text files
9
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2LKO8ICX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\halflife2_zoy_org[1].txt | — | |
MD5:— | SHA256:— | |||
| 1732 | FlashUtil32_26_0_0_137_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 1732 | FlashUtil32_26_0_0_137_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 3556 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr26B1.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr26B2.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr2701.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr2702.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PIO8XBLAWOPTCCK1DNHV.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
23
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3348 | iexplore.exe | GET | 301 | 91.198.174.208:80 | http://upload.wikimedia.org/wikipedia/en/a/a0/Agent-orange-dead-deformed-babies.jpg | NL | — | — | whitelisted |
3348 | iexplore.exe | GET | 200 | 193.200.42.162:80 | http://halflife2.zoy.org/ | FR | html | 6.85 Kb | suspicious |
3204 | iexplore.exe | GET | 404 | 37.48.65.155:80 | http://static.nimp.org/favicon.ico | NL | text | 9 b | malicious |
3348 | iexplore.exe | GET | 404 | 37.48.65.155:80 | http://static.nimp.org/gnaa.png | NL | text | 9 b | malicious |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
3348 | iexplore.exe | GET | 404 | 37.48.65.155:80 | http://static.nimp.org/flash/hello.swf | NL | text | 9 b | malicious |
3204 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3348 | iexplore.exe | GET | 404 | 37.48.65.155:80 | http://static.nimp.org/gnaa.png | NL | text | 9 b | malicious |
3348 | iexplore.exe | GET | 404 | 37.48.65.155:80 | http://static.nimp.org/gnaa.png | NL | text | 9 b | malicious |
3348 | iexplore.exe | GET | 404 | 37.48.65.155:80 | http://static.nimp.org/flash/hello.swf | NL | text | 9 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3204 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3348 | iexplore.exe | 91.198.174.208:80 | upload.wikimedia.org | Wikimedia Foundation, Inc. | NL | suspicious |
3348 | iexplore.exe | 193.200.42.162:80 | halflife2.zoy.org | Hivane | FR | suspicious |
3348 | iexplore.exe | 91.198.174.208:443 | upload.wikimedia.org | Wikimedia Foundation, Inc. | NL | suspicious |
3348 | iexplore.exe | 37.48.65.155:80 | static.nimp.org | LeaseWeb Netherlands B.V. | NL | malicious |
3556 | opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3204 | iexplore.exe | 37.48.65.155:80 | static.nimp.org | LeaseWeb Netherlands B.V. | NL | malicious |
3556 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
halflife2.zoy.org |
| suspicious |
upload.wikimedia.org |
| whitelisted |
static.nimp.org |
| malicious |
teredo.ipv6.microsoft.com |
| whitelisted |
certs.opera.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
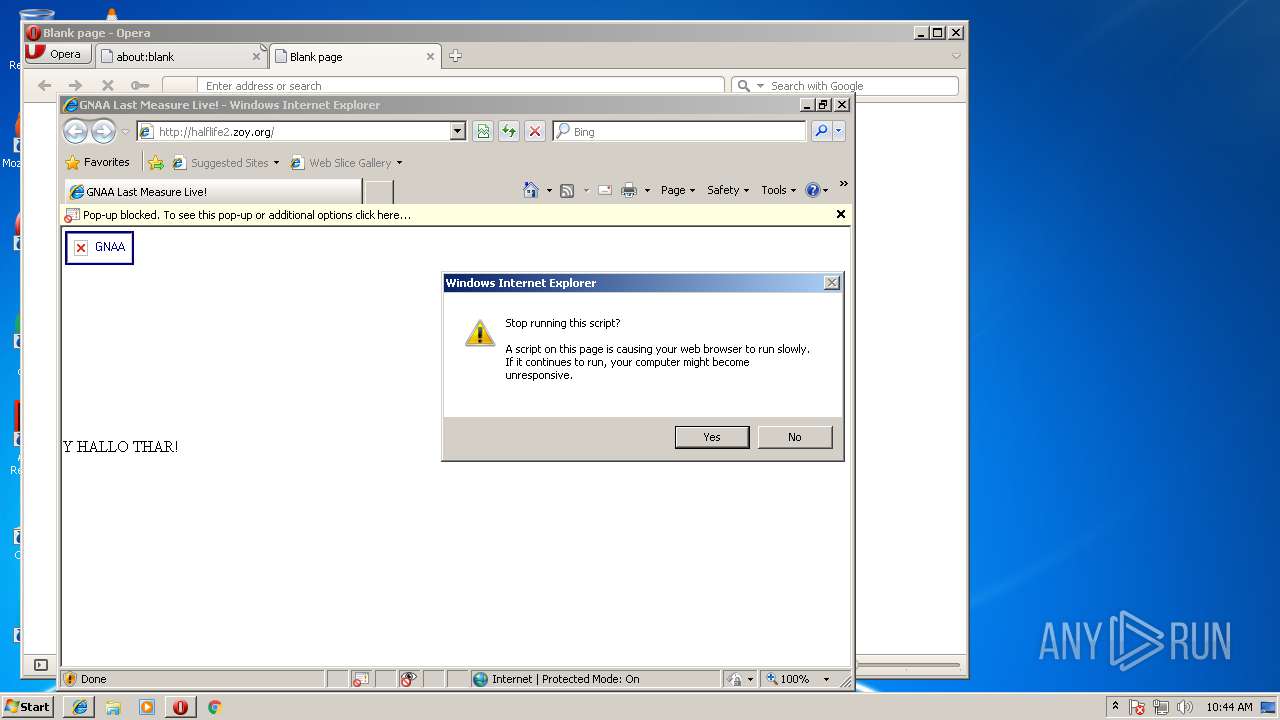
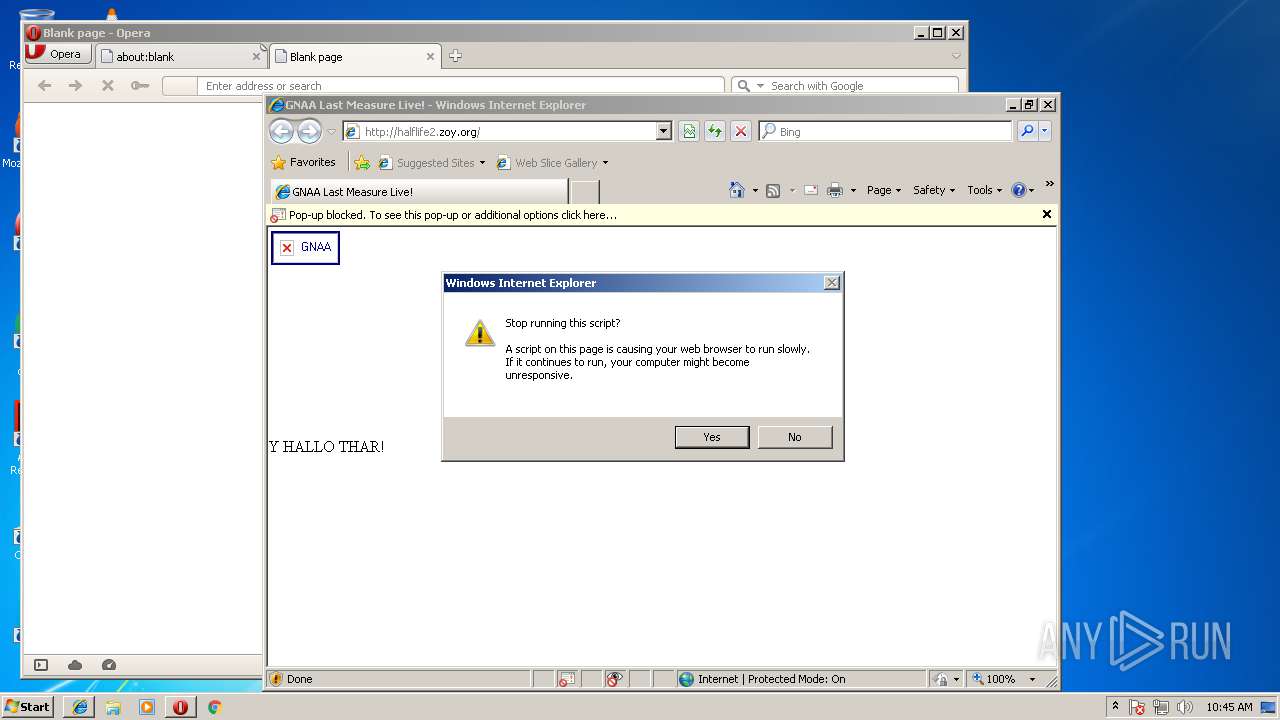
3348 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |