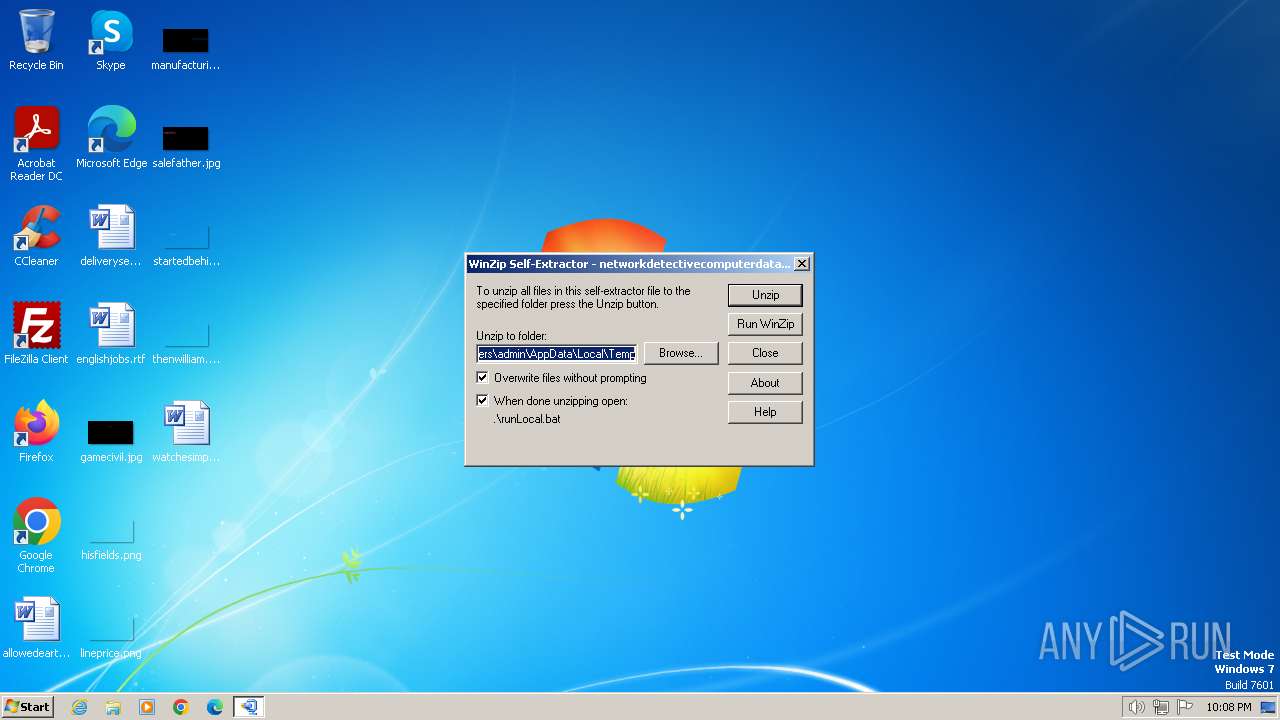
| File name: | networkdetectivecomputerdatacollector (1).exe |
| Full analysis: | https://app.any.run/tasks/483fa28d-891f-4534-b806-4eaae2e72644 |
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2024, 21:08:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F48B6EFB0F8F5455475571C685C618F7 |
| SHA1: | 6DB62956002323BBA1A78277F249A65BCA113272 |
| SHA256: | 3BF9A2249FDA87358586077FBE2C39658C097680DDED287AB46DFC28A07485BE |
| SSDEEP: | 196608:1YNSCjXQwmoMtqegqVIEWis1T5qFoOIBsDV1Kb:DGMokV0is1MFXDXKb |
MALICIOUS
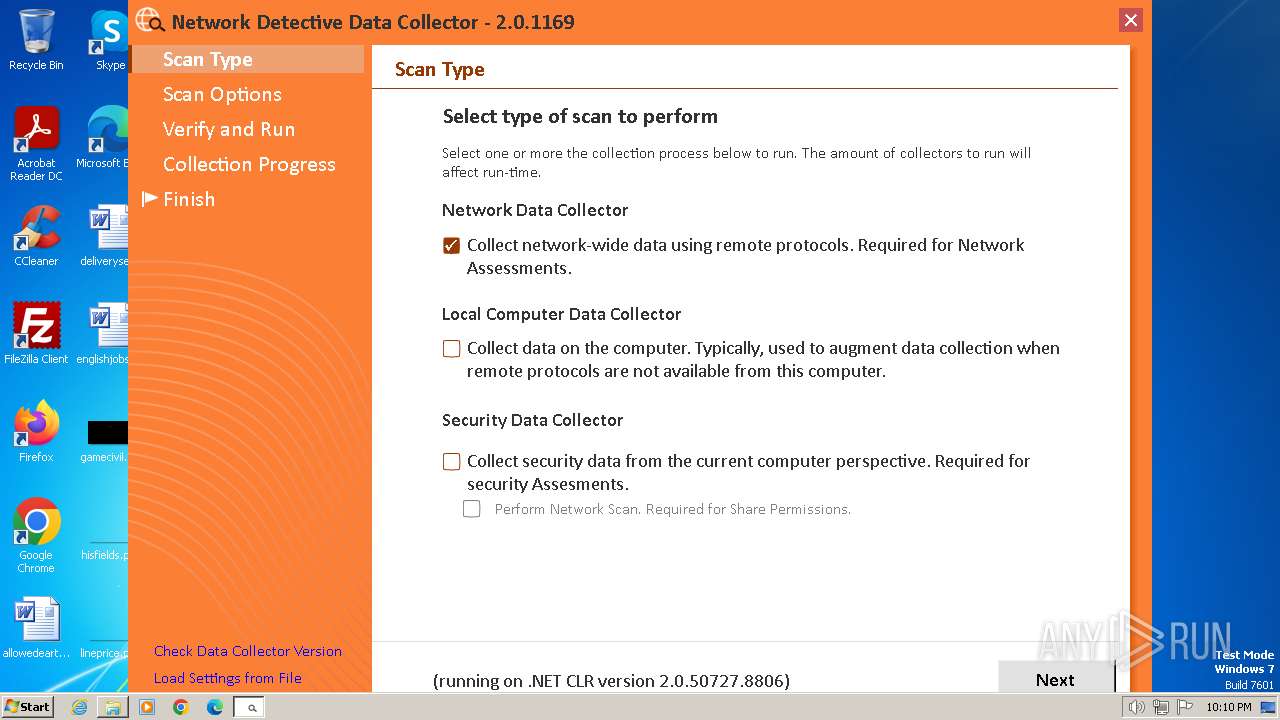
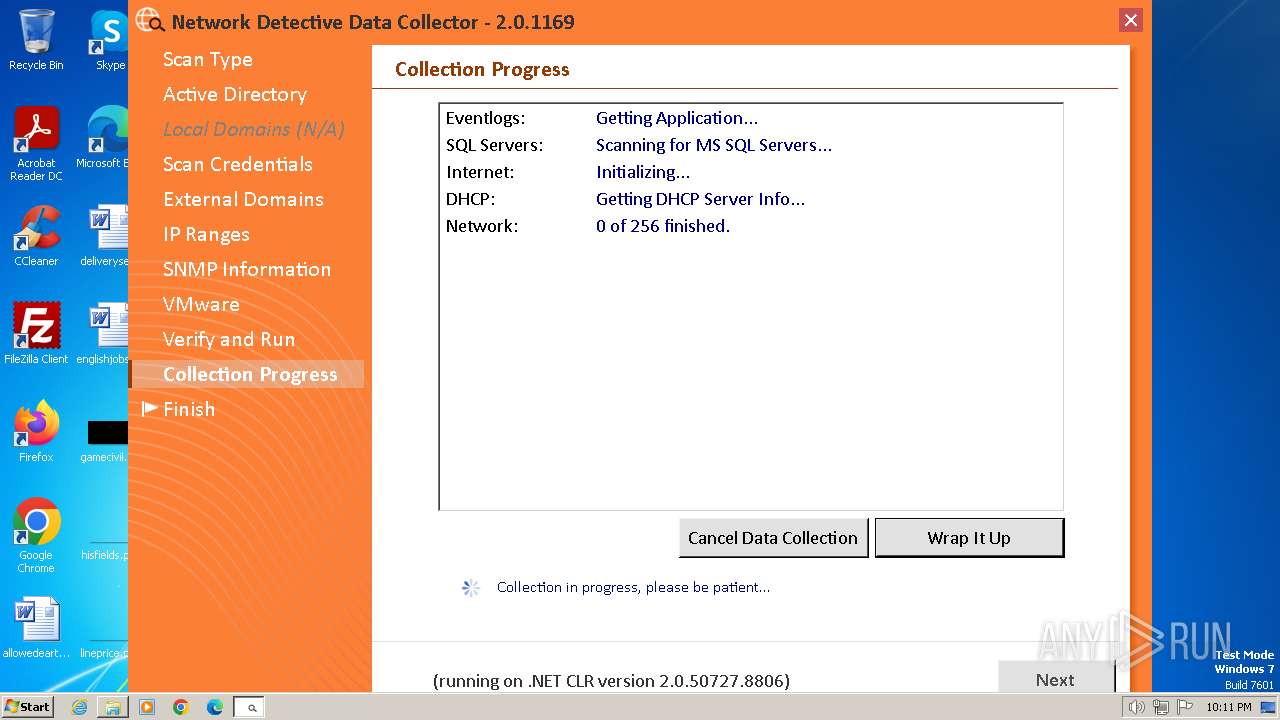
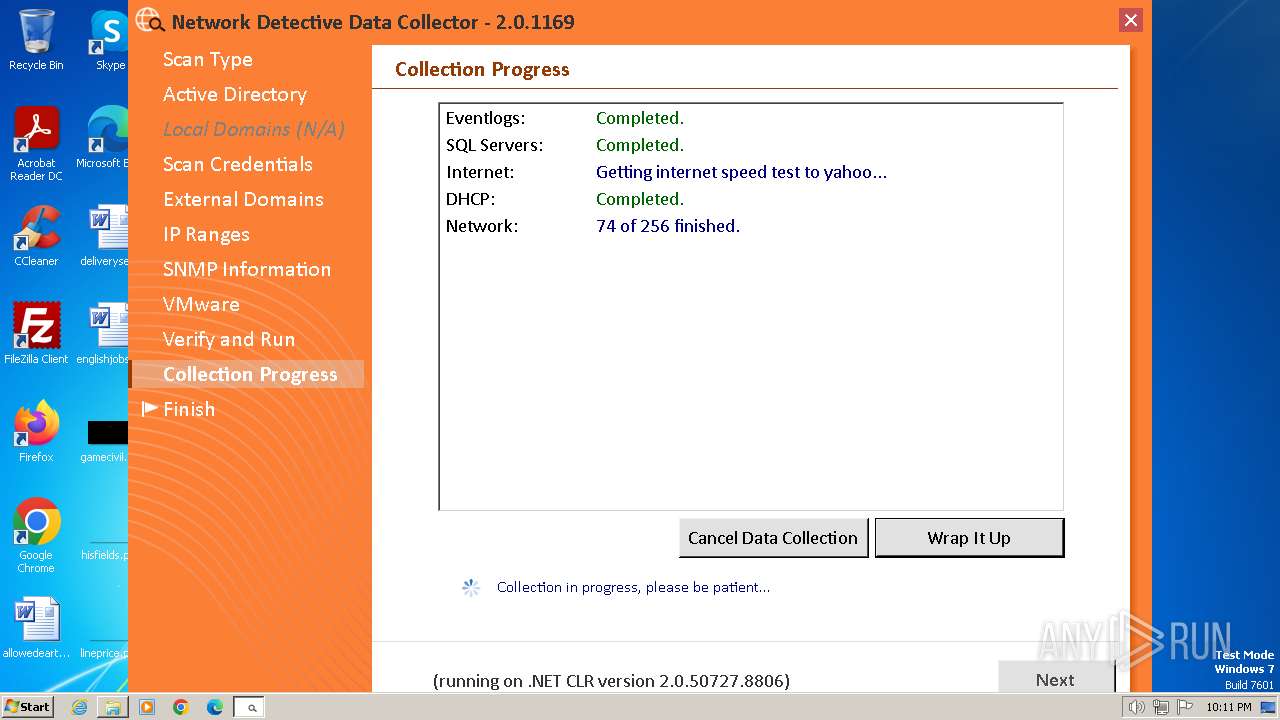
Drops the executable file immediately after the start
- networkdetectivecomputerdatacollector (1).exe (PID: 2124)
- csc.exe (PID: 2548)
Starts Visual C# compiler
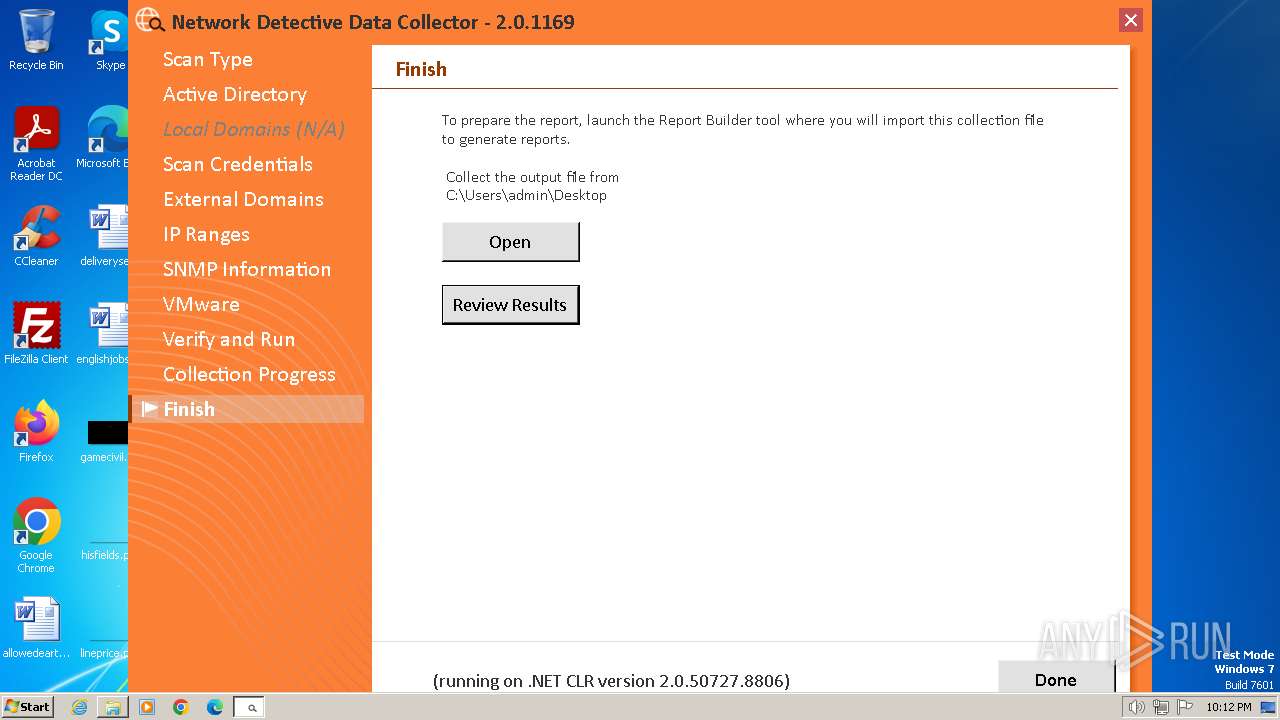
- RunNetworkDetective.exe (PID: 992)
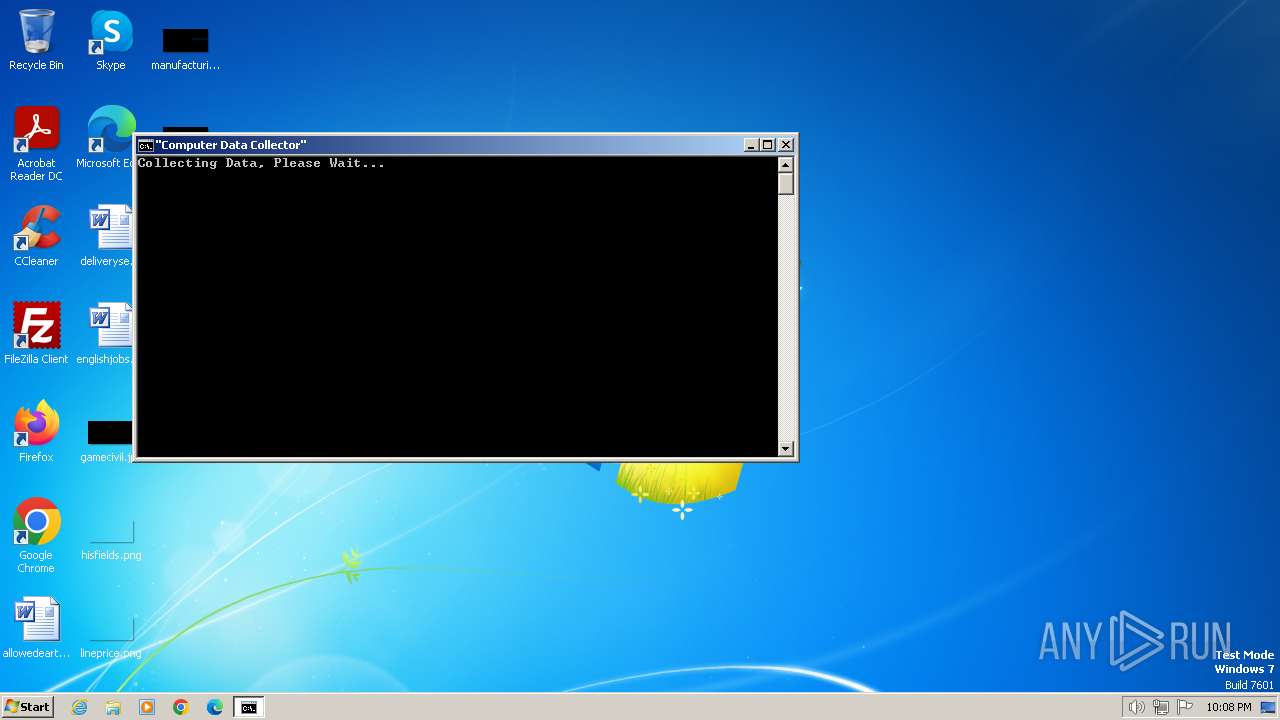
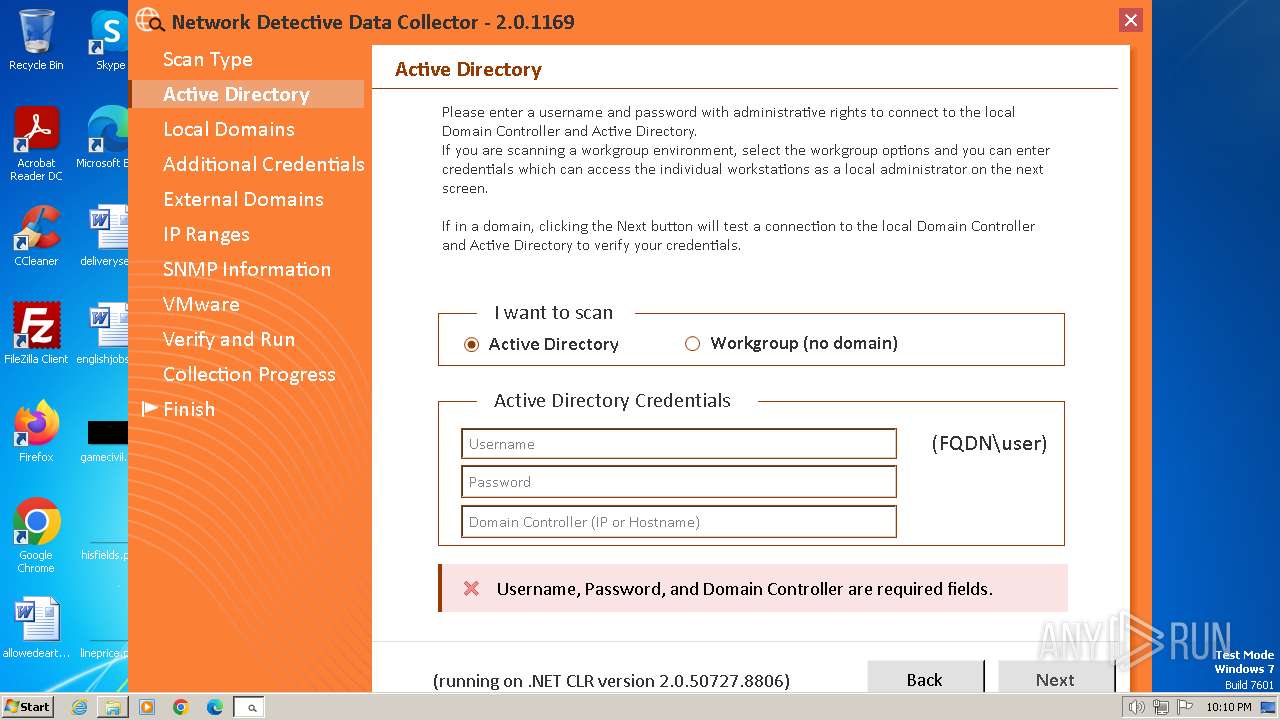
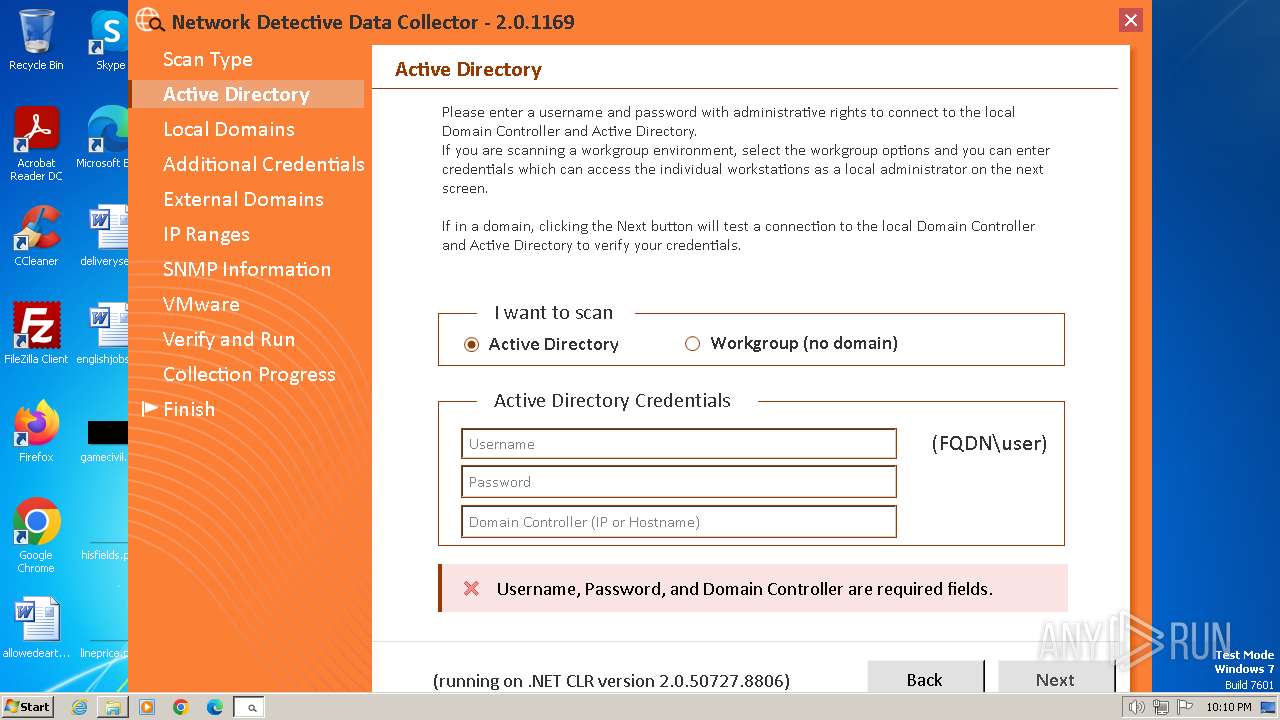
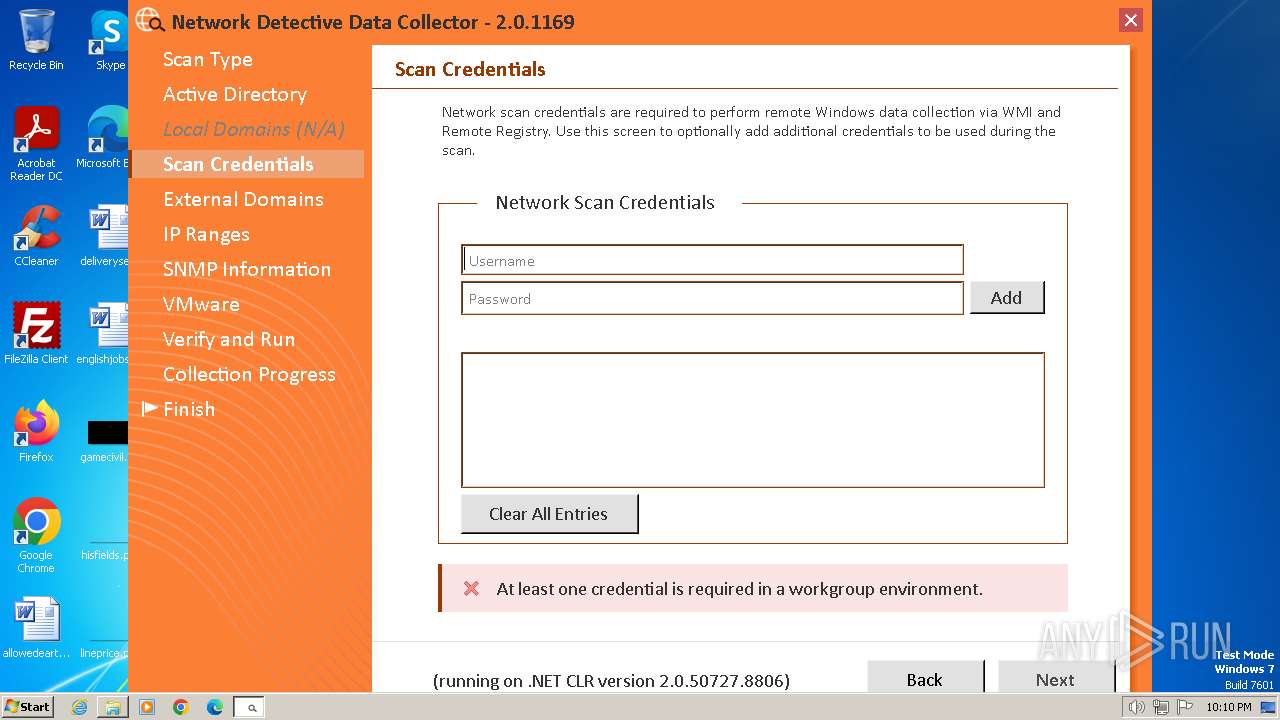
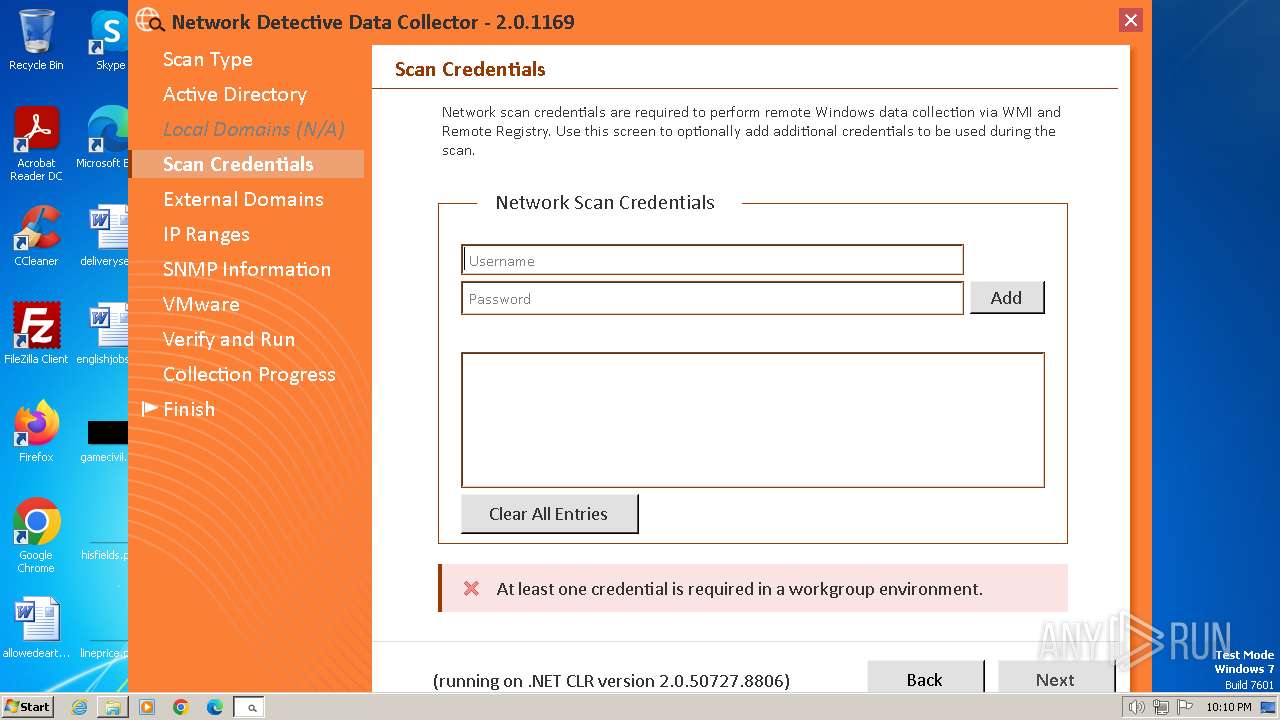
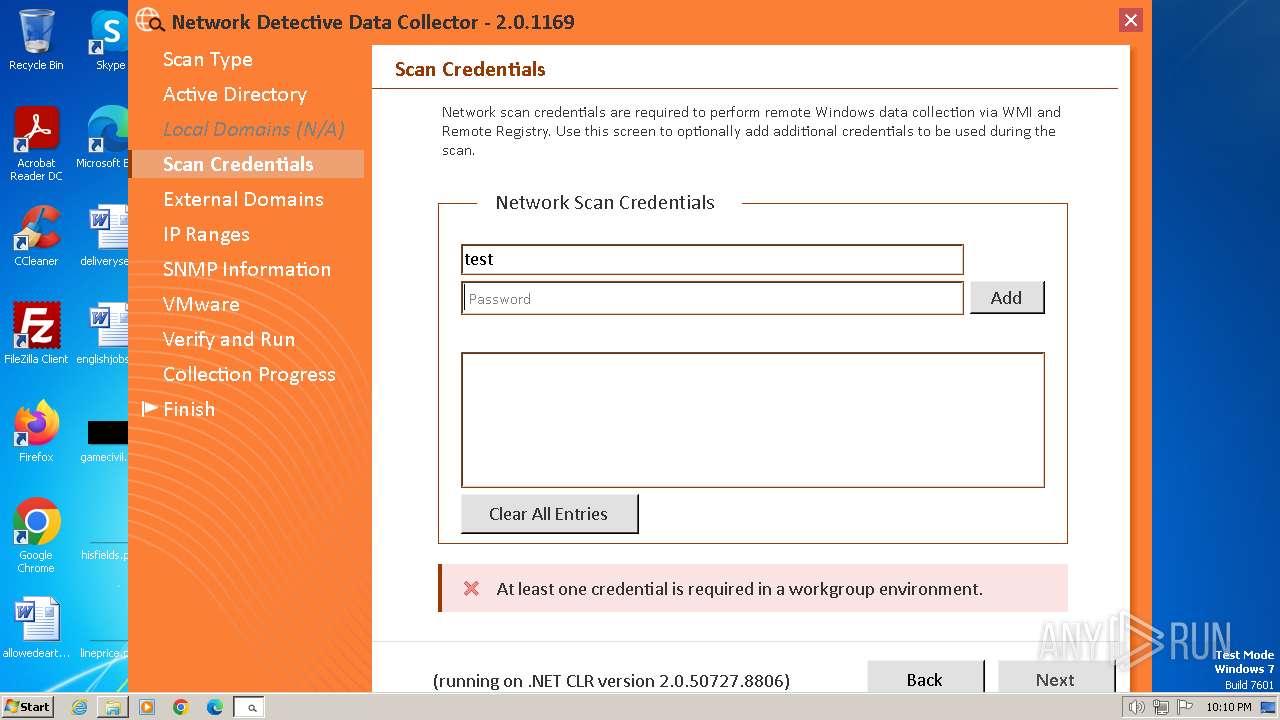
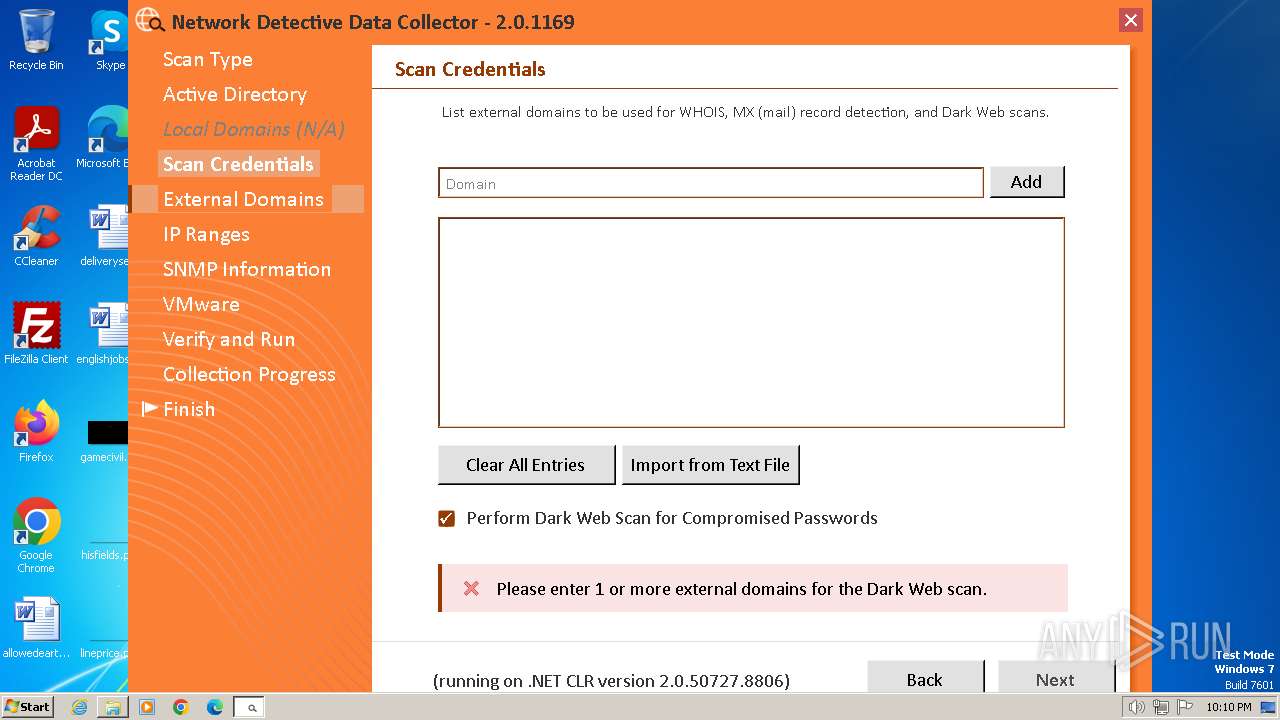
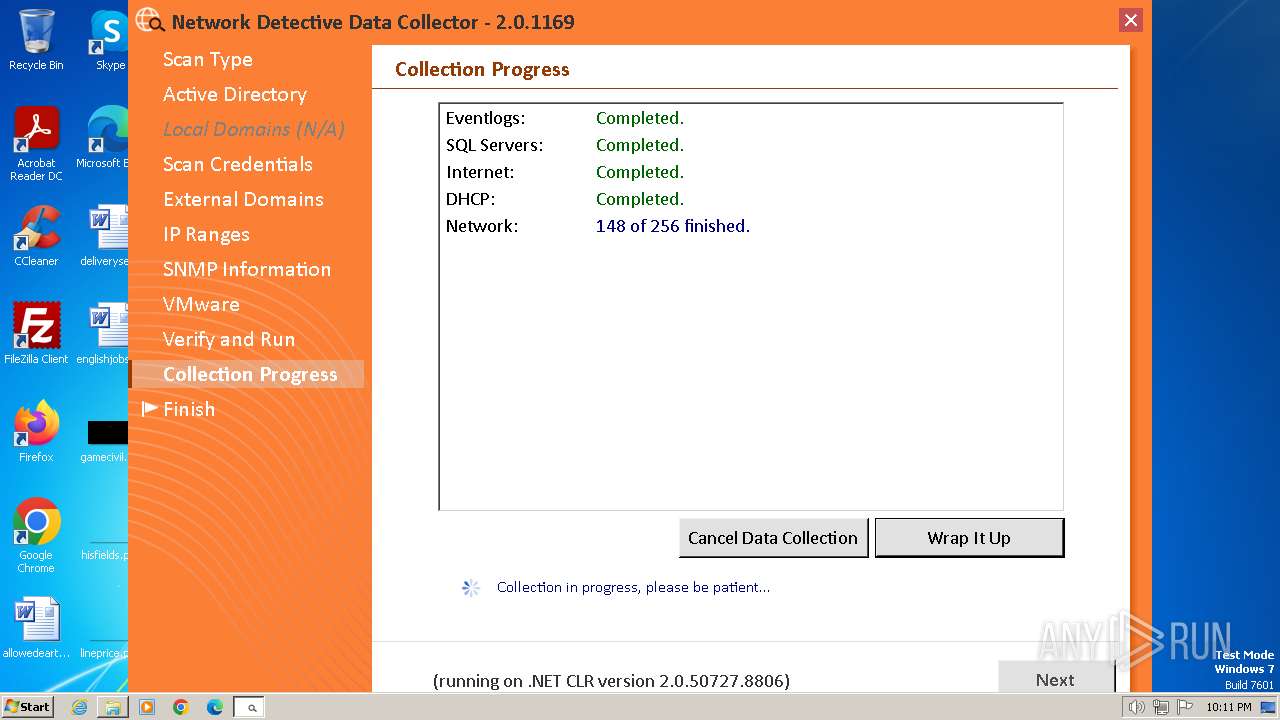
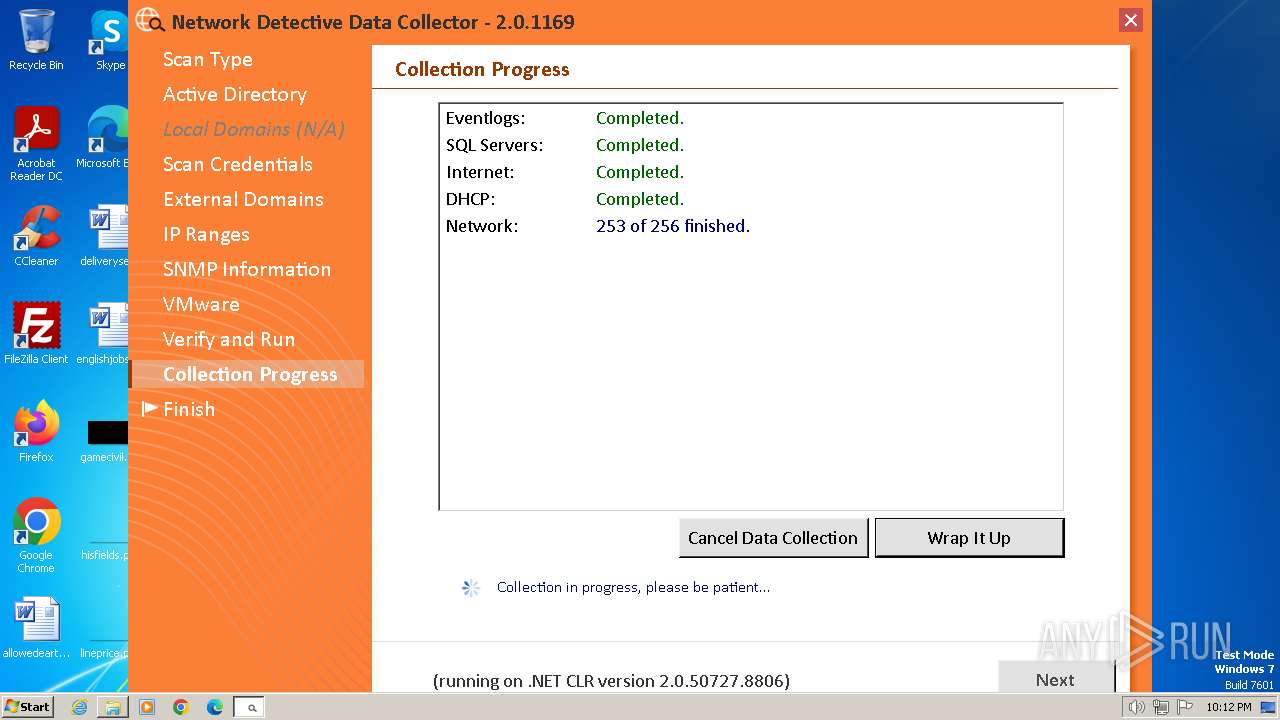
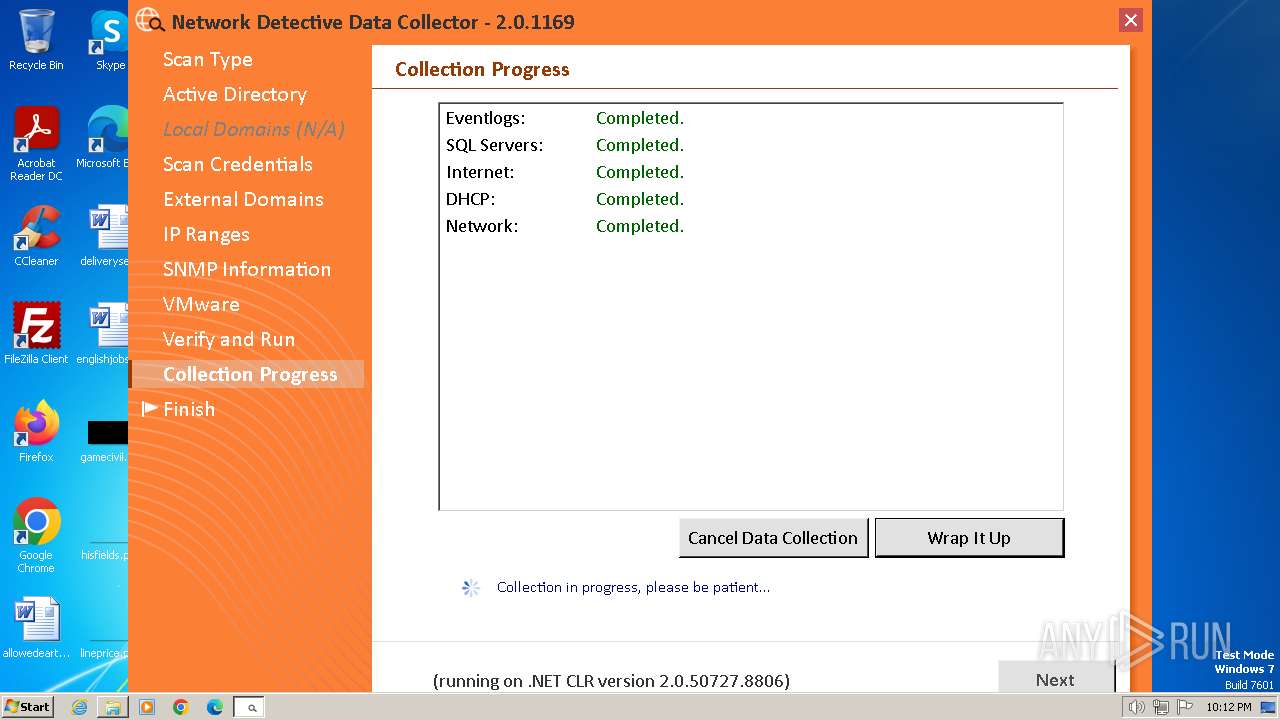
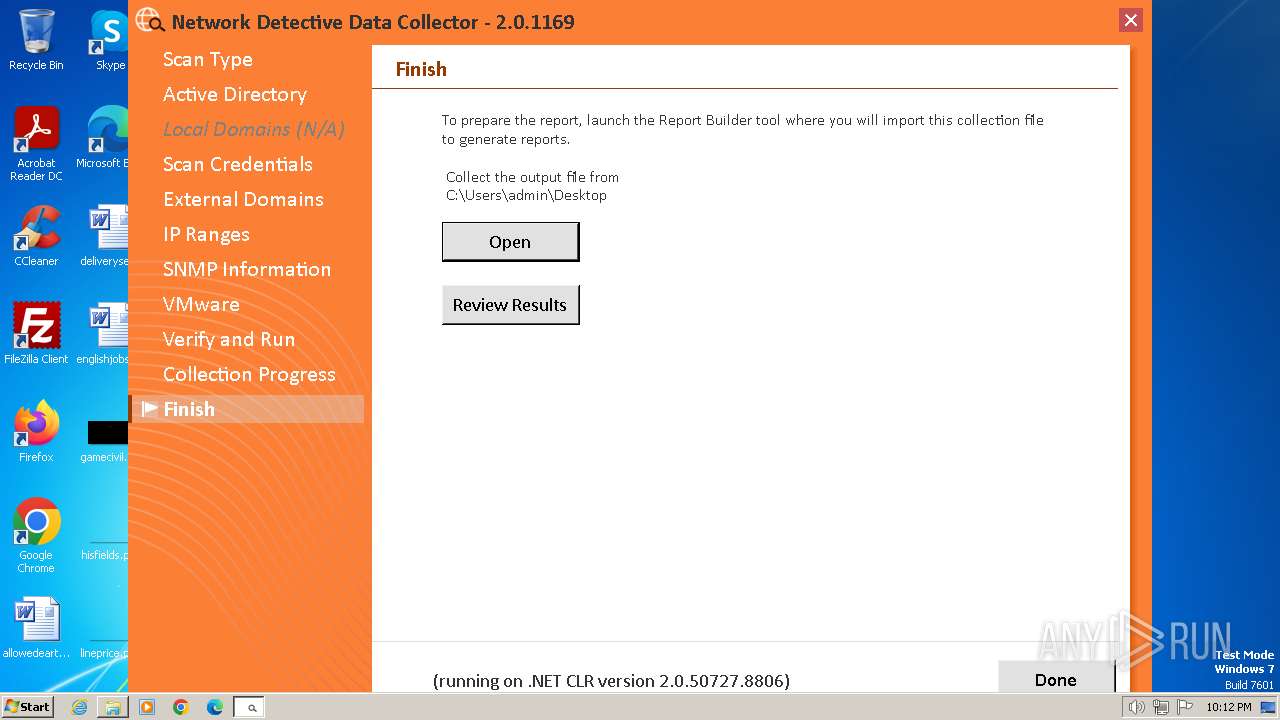
Actions looks like stealing of personal data
- nddc.exe (PID: 3092)
SUSPICIOUS
The executable file from the user directory is run by the CMD process
- nddc.exe (PID: 3092)
Process drops legitimate windows executable
- networkdetectivecomputerdatacollector (1).exe (PID: 2124)
Starts CMD.EXE for commands execution
- networkdetectivecomputerdatacollector (1).exe (PID: 2124)
Reads the Internet Settings
- networkdetectivecomputerdatacollector (1).exe (PID: 2124)
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
Reads security settings of Internet Explorer
- networkdetectivecomputerdatacollector (1).exe (PID: 2124)
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
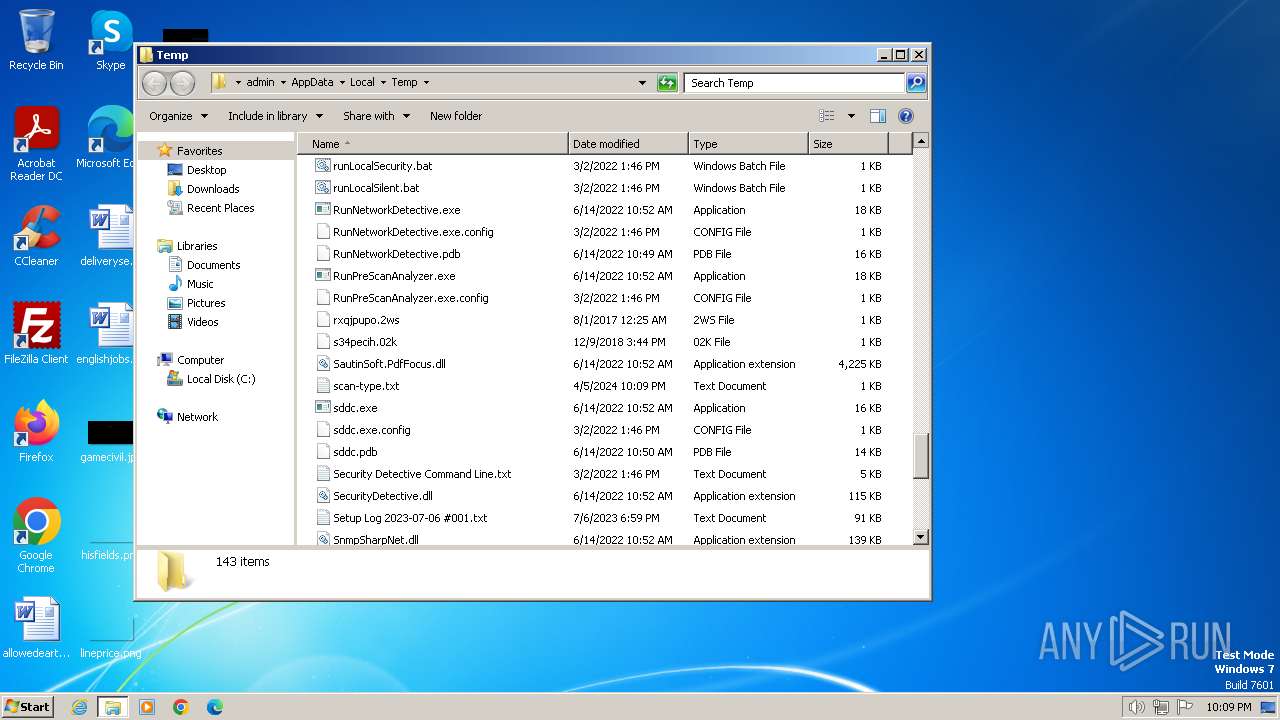
Executing commands from a ".bat" file
- networkdetectivecomputerdatacollector (1).exe (PID: 2124)
Reads settings of System Certificates
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
Checks Windows Trust Settings
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
Group Policy Discovery via Microsoft GPResult Utility
- nddc.exe (PID: 3092)
Reads the Windows owner or organization settings
- nddc.exe (PID: 3092)
Searches for installed software
- nddc.exe (PID: 3092)
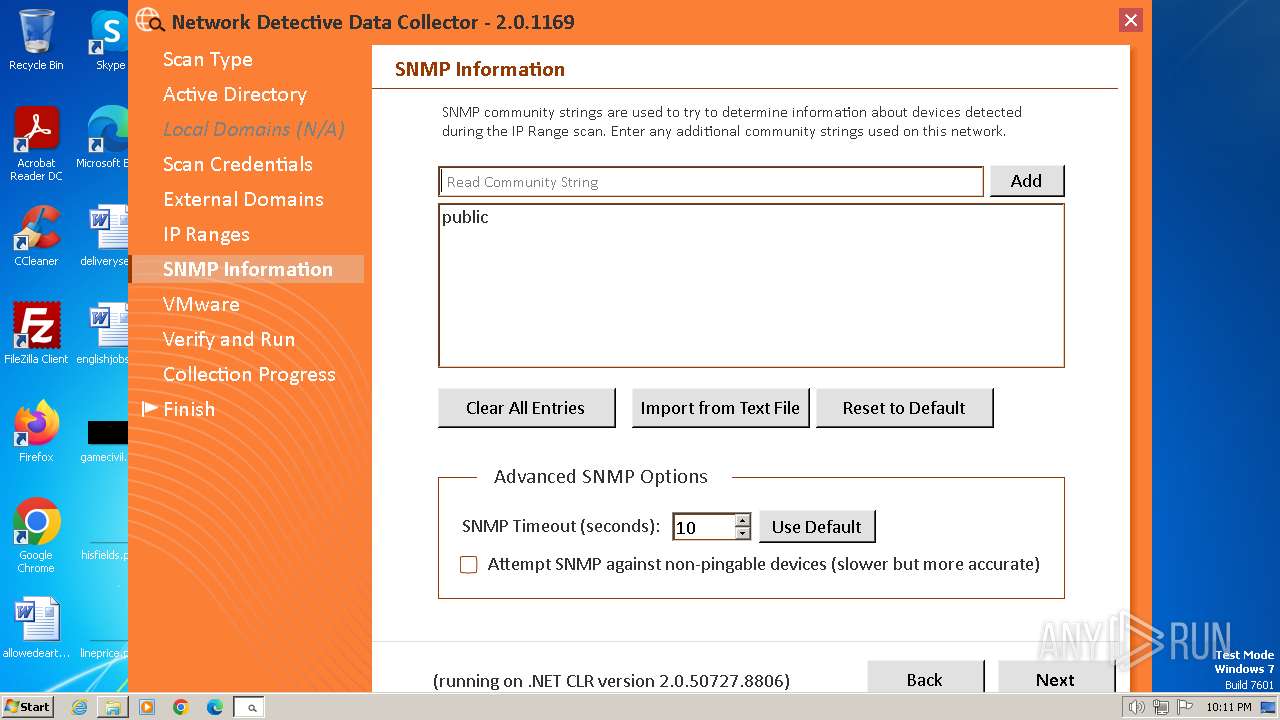
Process uses ARP to discover network configuration
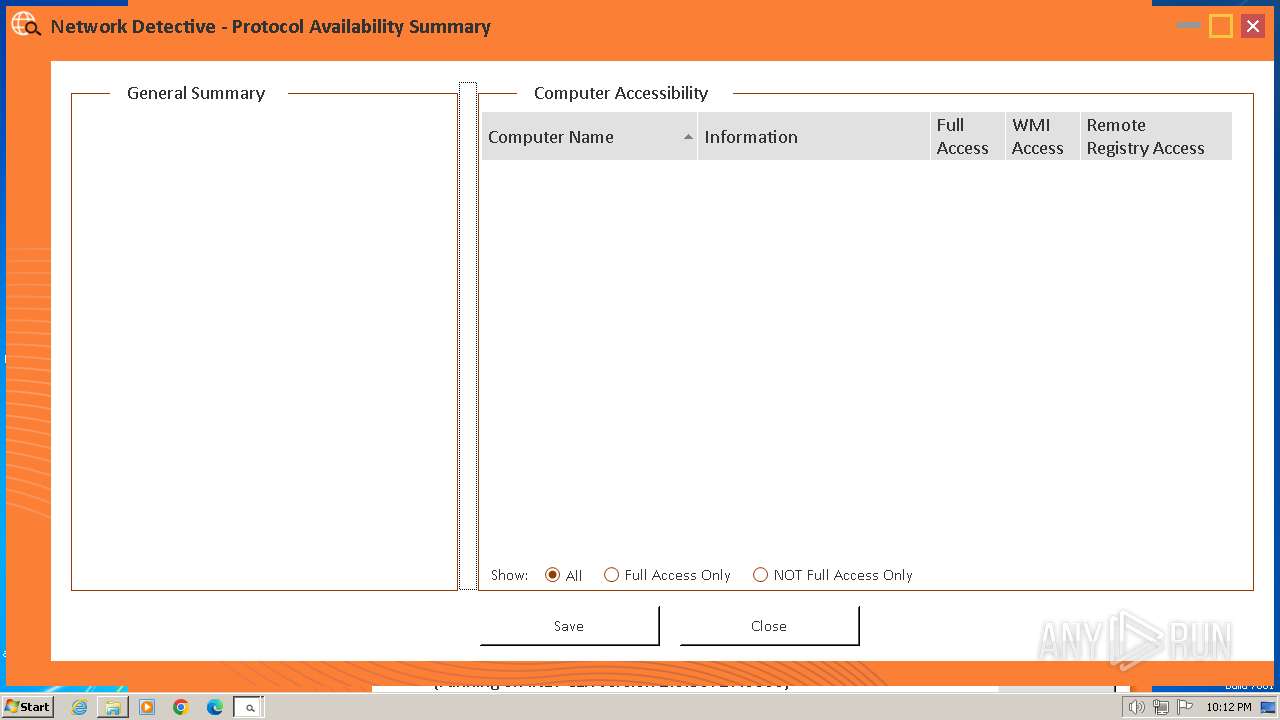
- RunNetworkDetective.exe (PID: 992)
Uses .NET C# to load dll
- RunNetworkDetective.exe (PID: 992)
Process uses IPCONFIG to discover network configuration
- RunNetworkDetective.exe (PID: 992)
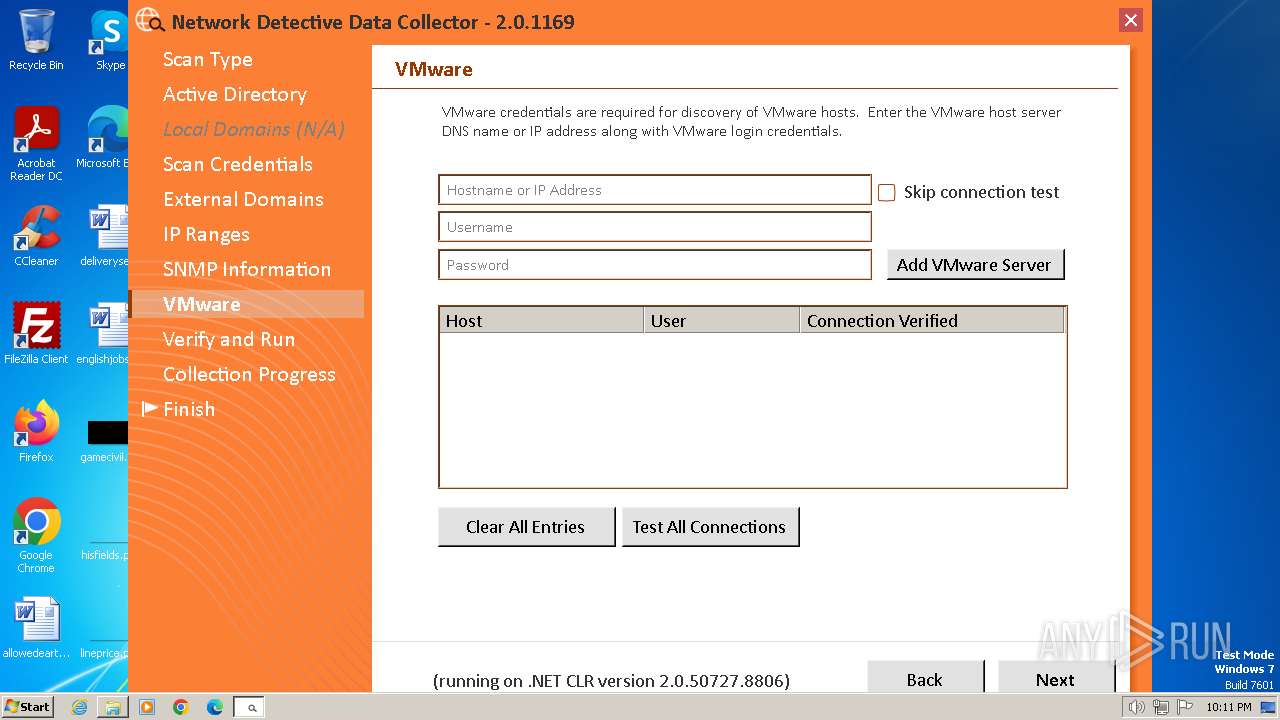
Connects to FTP
- RunNetworkDetective.exe (PID: 992)
Connects to SMTP port
- RunNetworkDetective.exe (PID: 992)
Uses pipe srvsvc via SMB (transferring data)
- RunNetworkDetective.exe (PID: 992)
Connects to SSH
- RunNetworkDetective.exe (PID: 992)
Connects to unusual port
- RunNetworkDetective.exe (PID: 992)
INFO
Checks supported languages
- networkdetectivecomputerdatacollector (1).exe (PID: 2124)
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
- csc.exe (PID: 2548)
- cvtres.exe (PID: 2880)
Reads the computer name
- networkdetectivecomputerdatacollector (1).exe (PID: 2124)
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
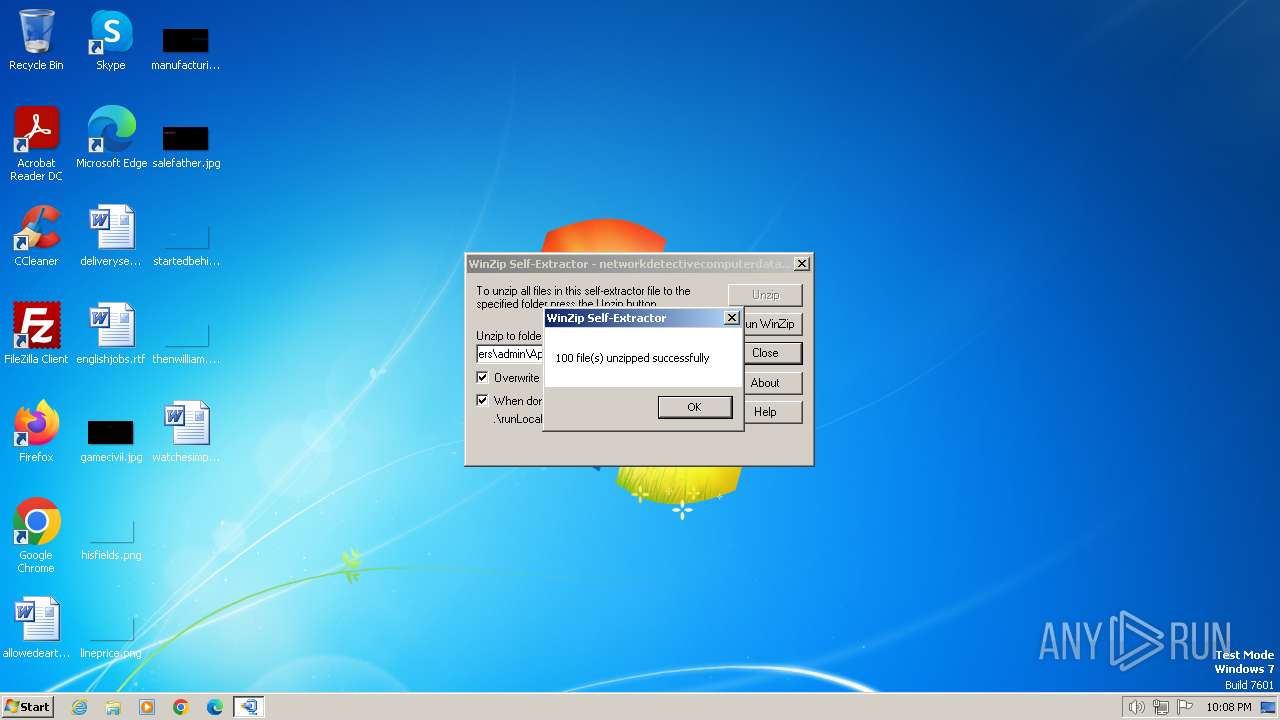
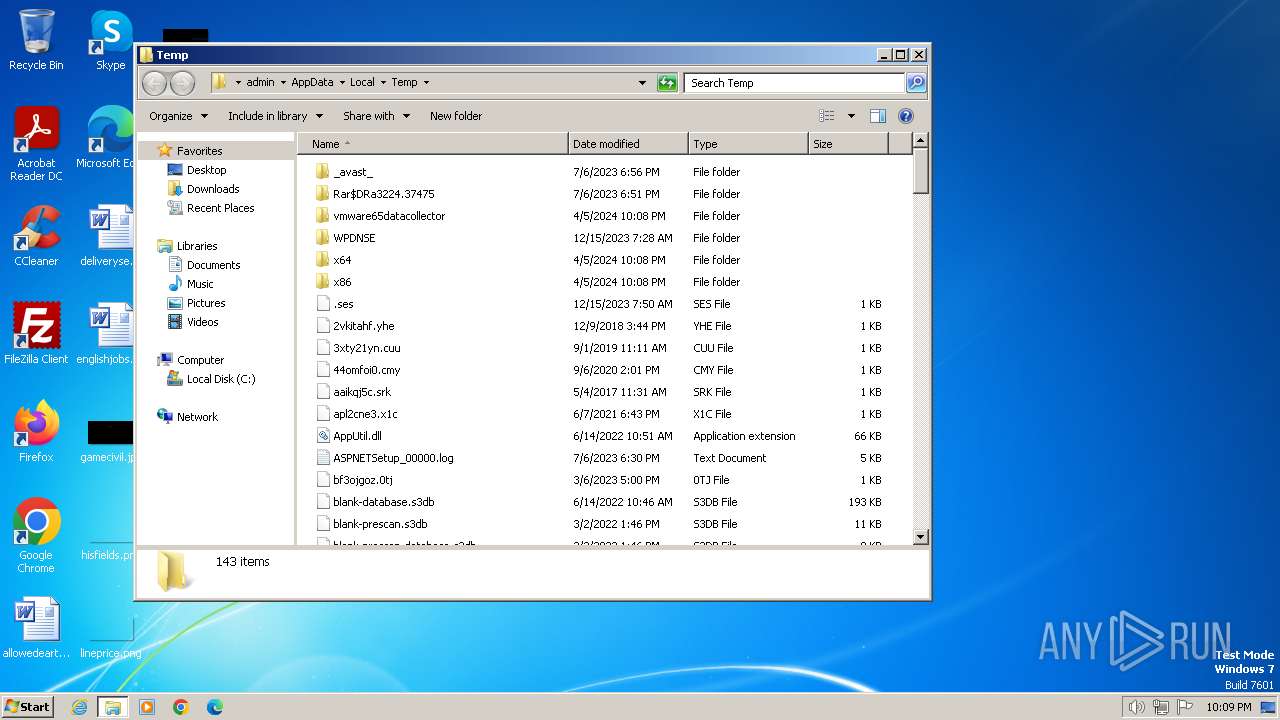
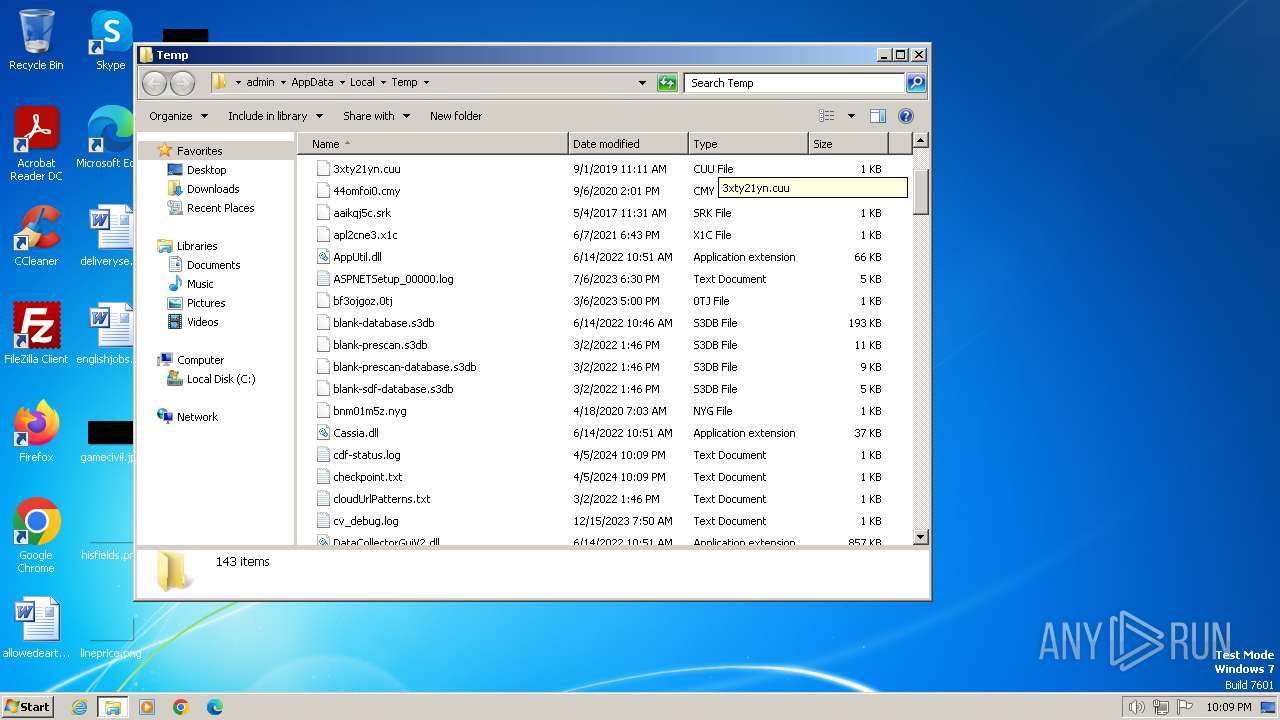
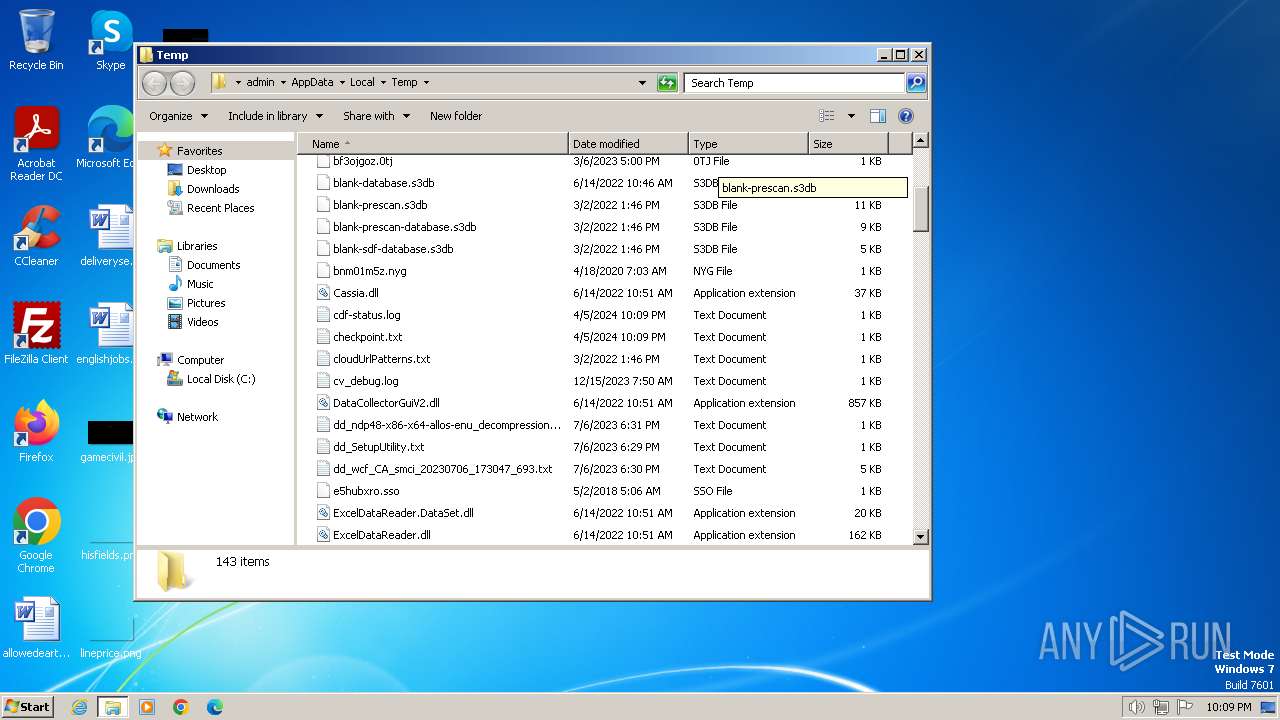
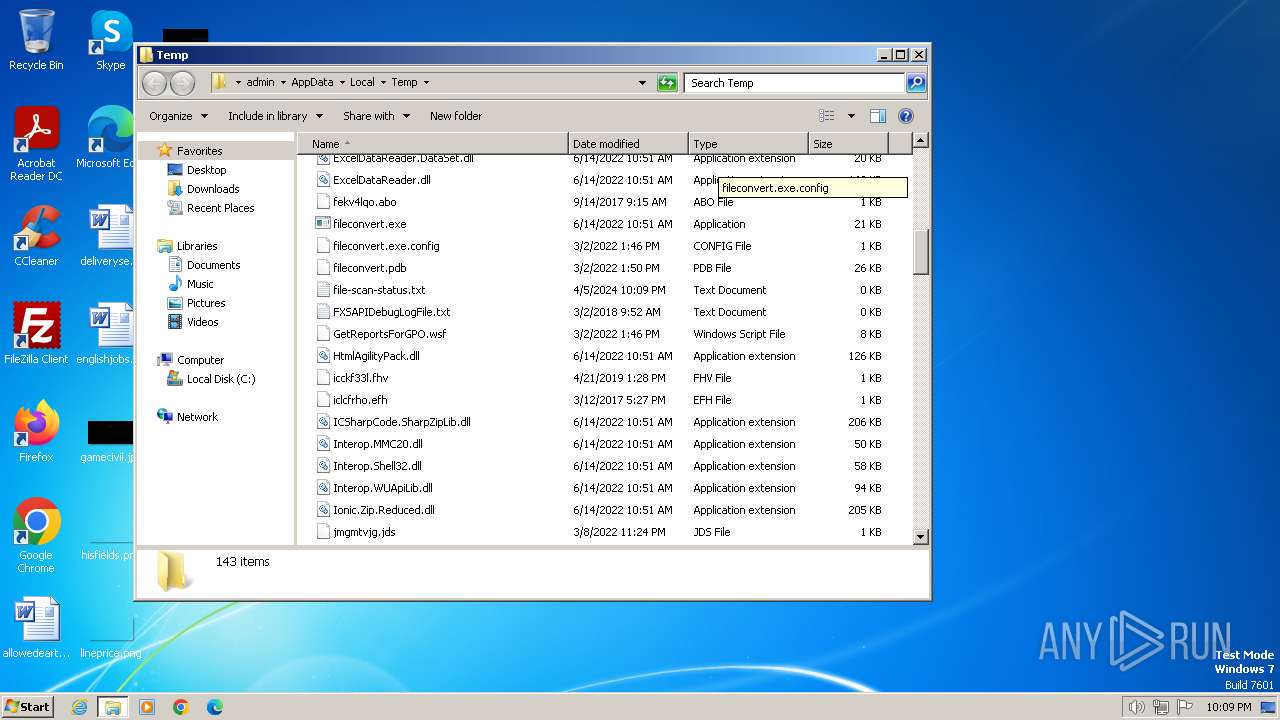
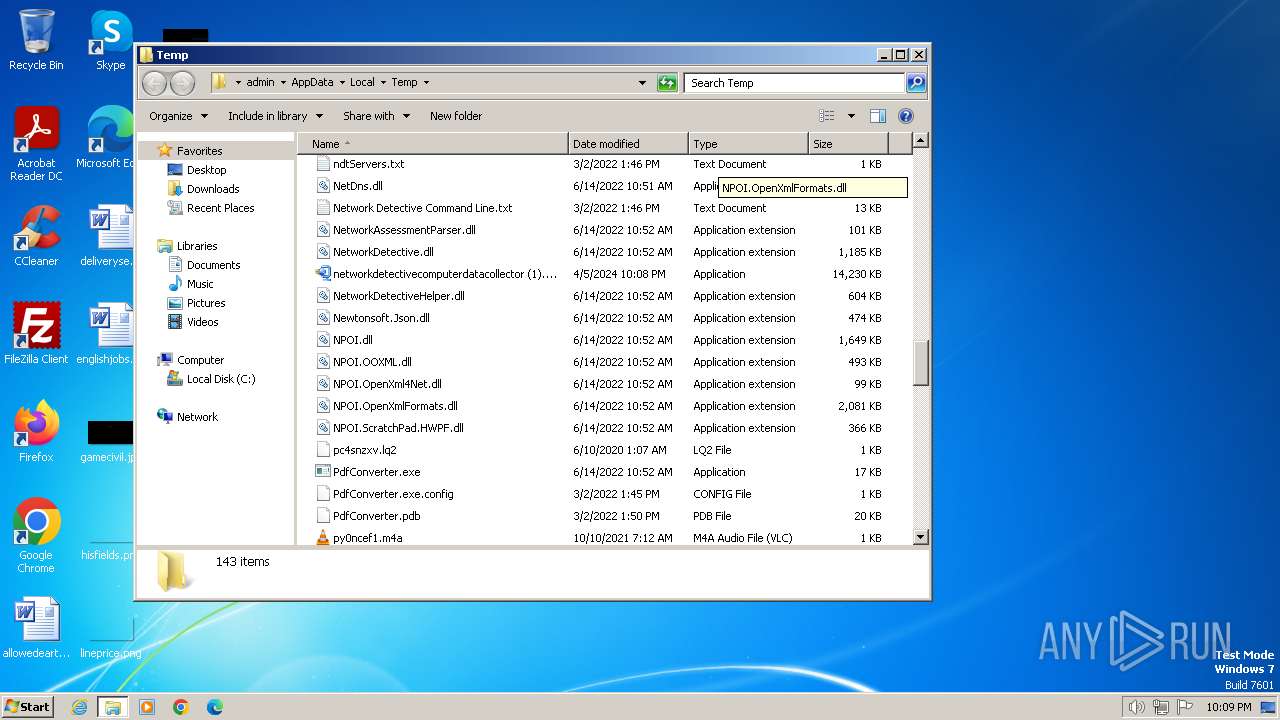
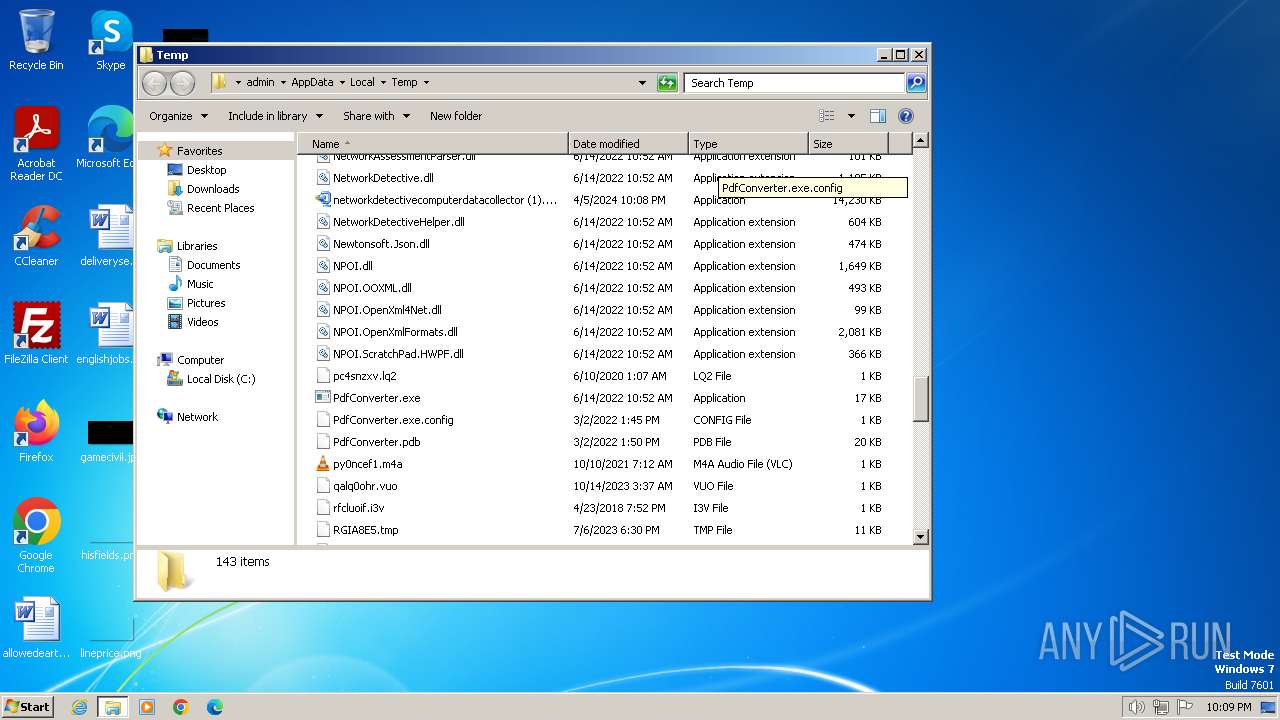
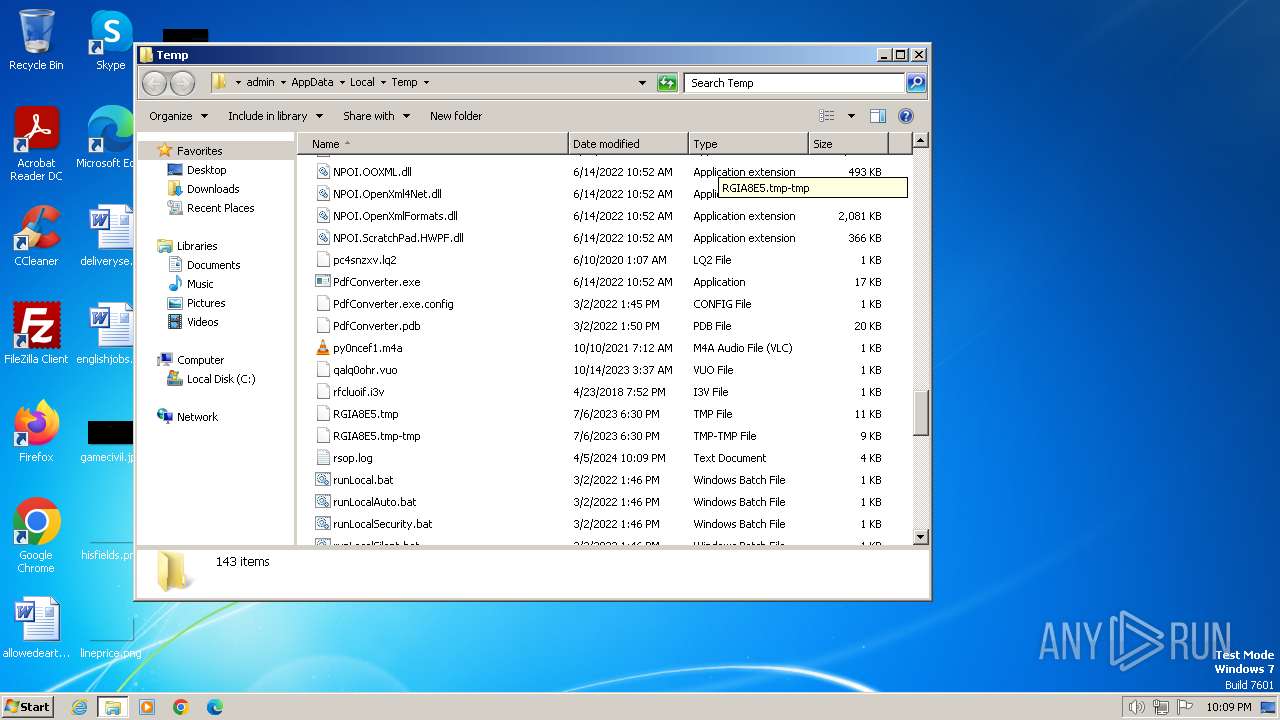
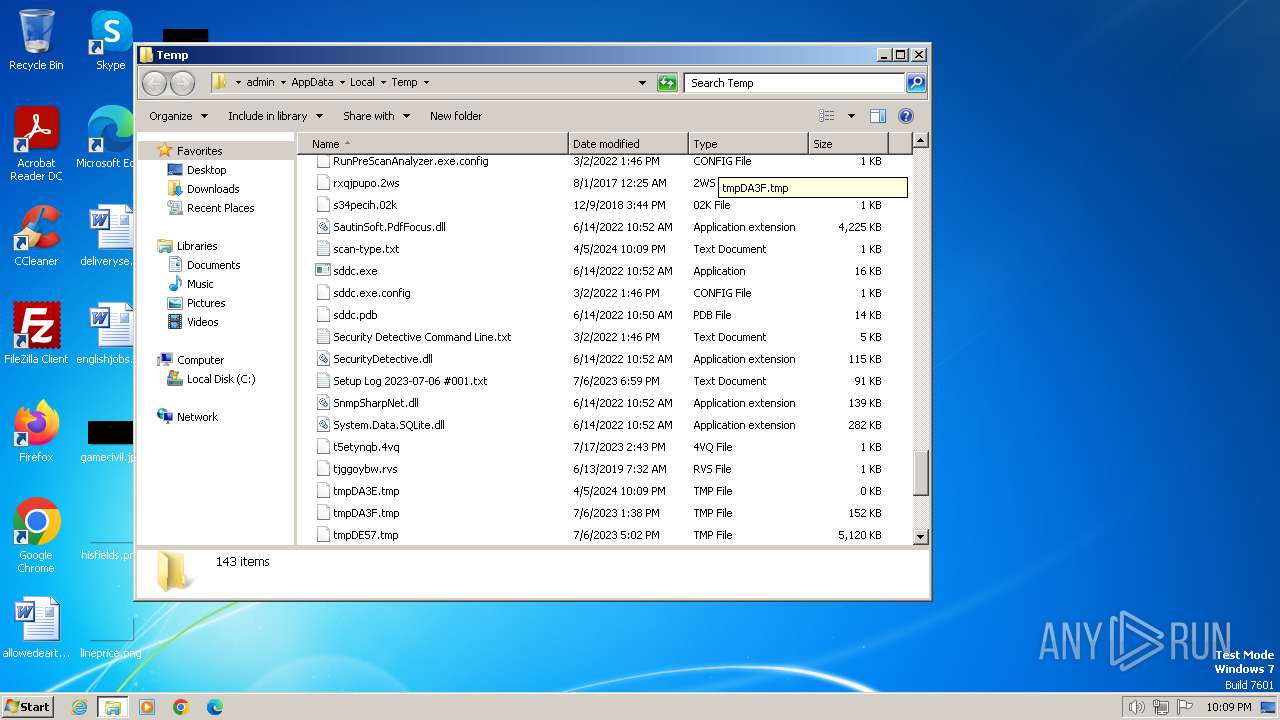
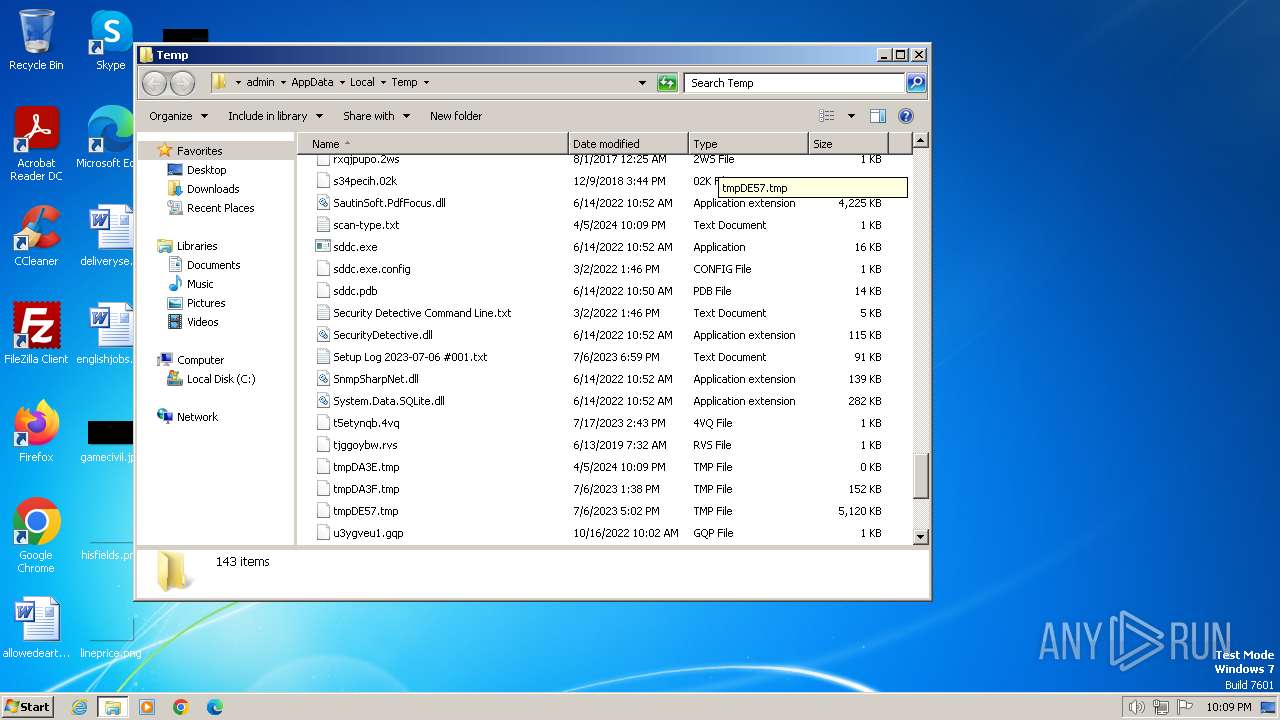
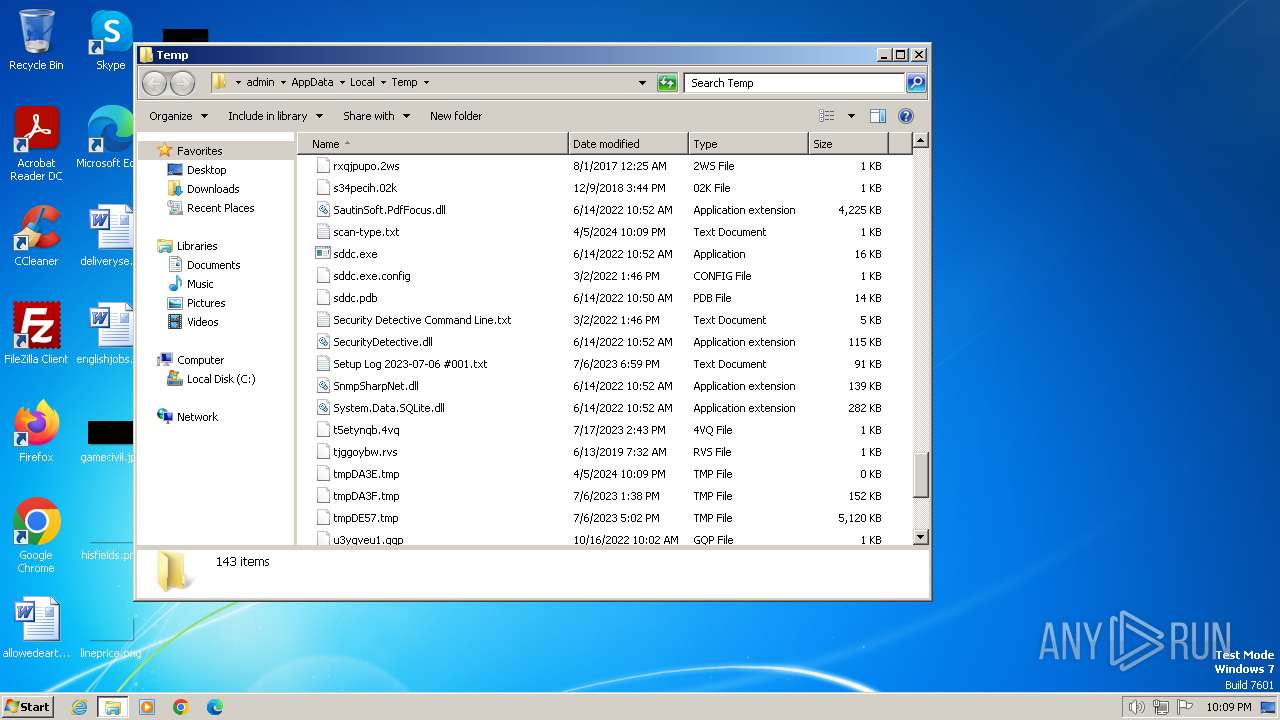
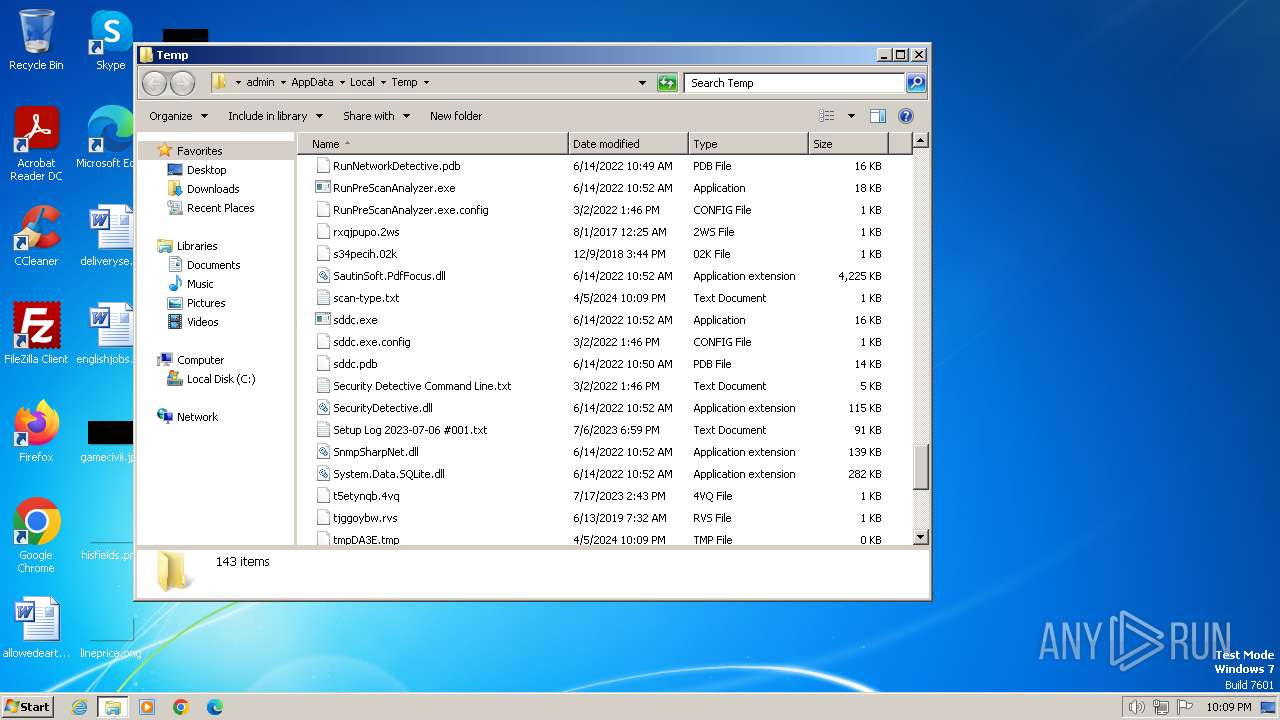
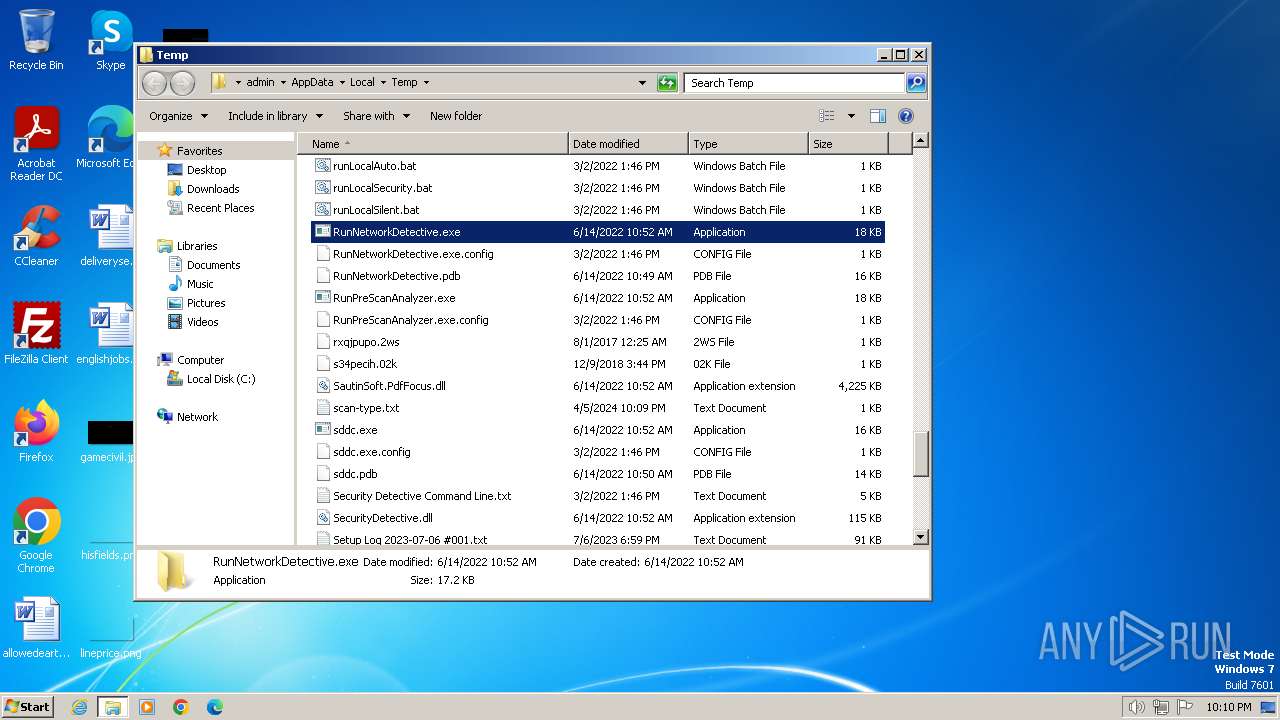
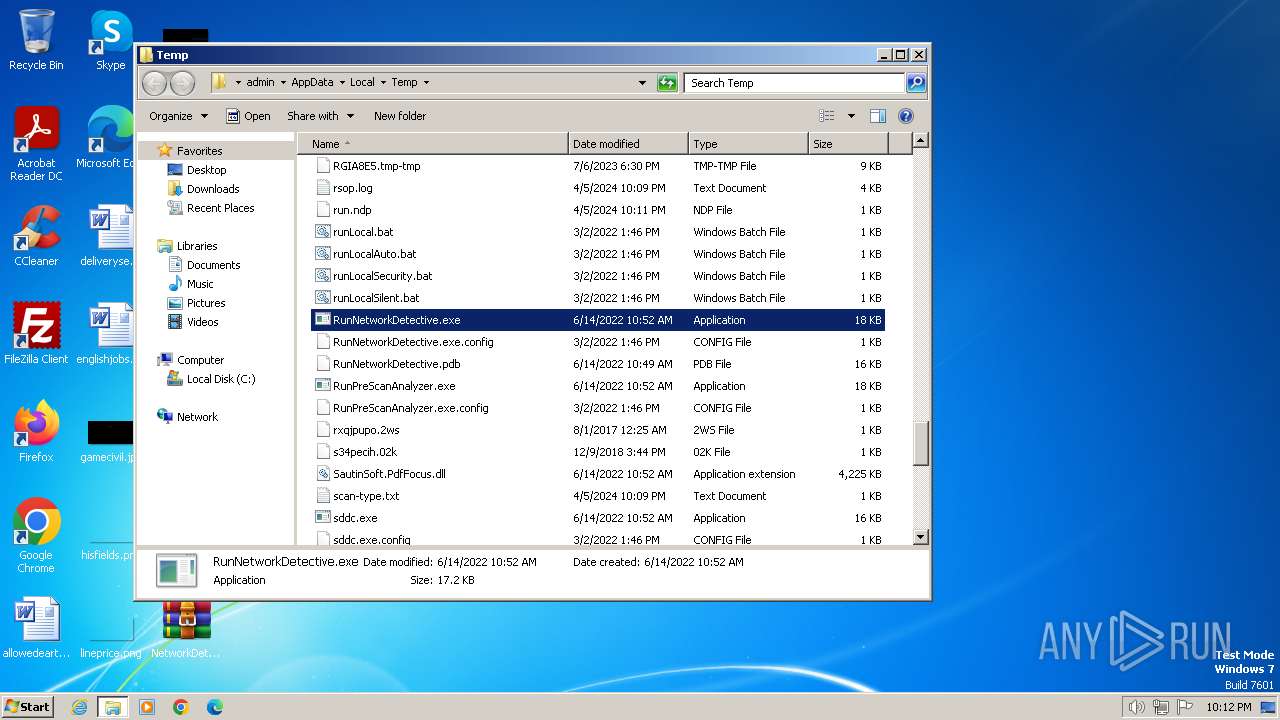
Create files in a temporary directory
- networkdetectivecomputerdatacollector (1).exe (PID: 2124)
- nddc.exe (PID: 3092)
- cvtres.exe (PID: 2880)
- csc.exe (PID: 2548)
- RunNetworkDetective.exe (PID: 992)
Reads the machine GUID from the registry
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
- csc.exe (PID: 2548)
- cvtres.exe (PID: 2880)
Reads the software policy settings
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
Reads Environment values
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
Reads the time zone
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
Reads CPU info
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
Reads Microsoft Office registry keys
- nddc.exe (PID: 3092)
Reads product name
- nddc.exe (PID: 3092)
- RunNetworkDetective.exe (PID: 992)
Checks proxy server information
- nddc.exe (PID: 3092)
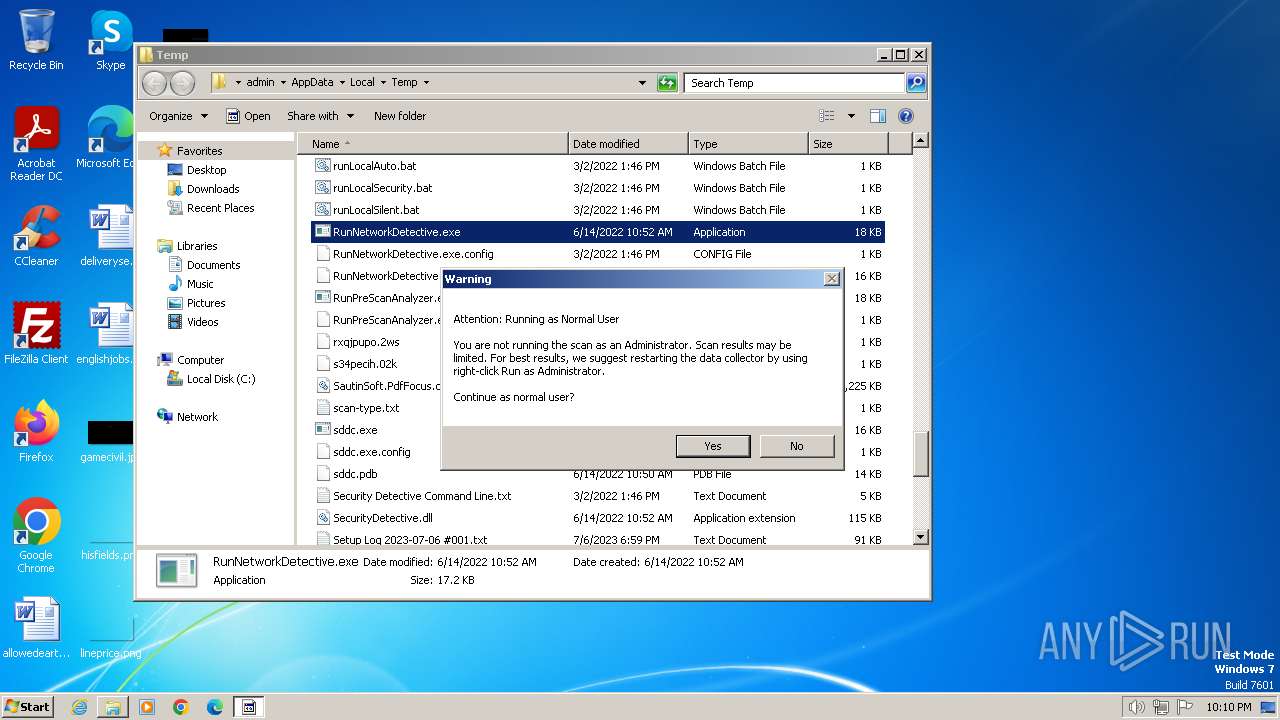
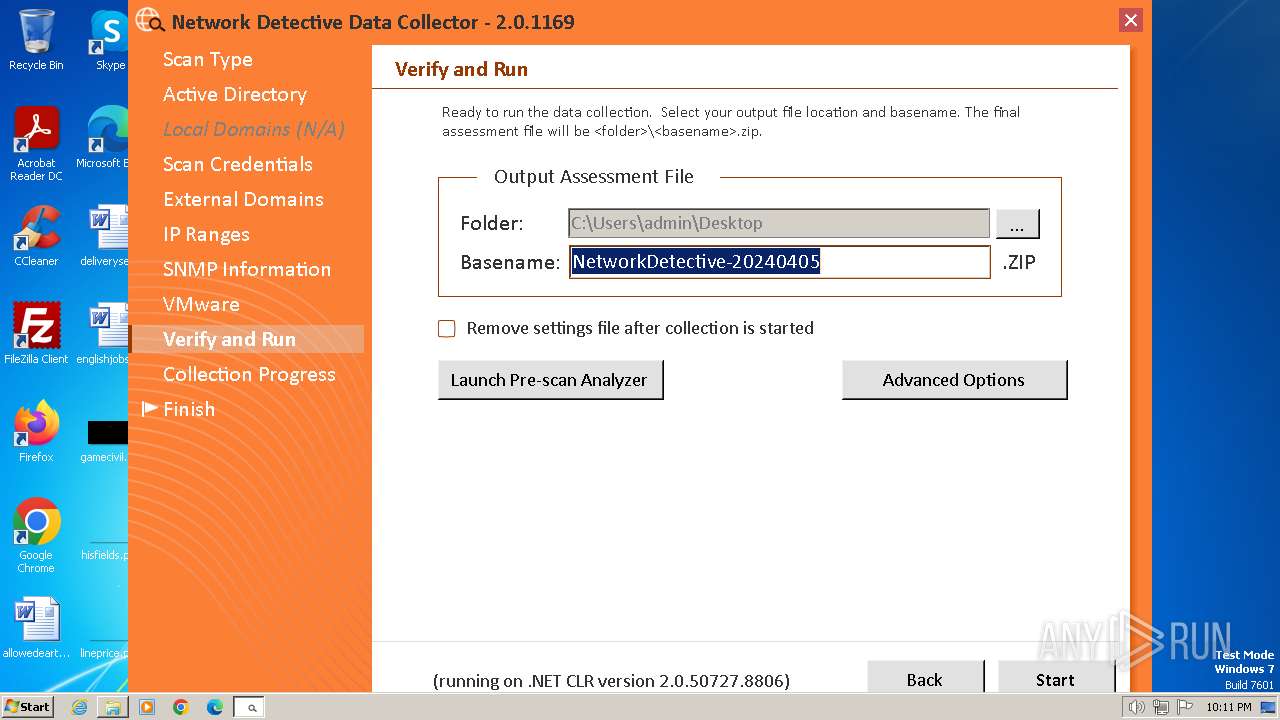
Manual execution by a user
- RunNetworkDetective.exe (PID: 992)
Reads Windows Product ID
- nddc.exe (PID: 3092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (30.7) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (22.2) |
| .exe | | | Win64 Executable (generic) (19.7) |
| .exe | | | Winzip Win32 self-extracting archive (generic) (16.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:11:02 20:23:03+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 73728 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa79e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
65
Monitored processes
11
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "gpresult.exe" /user USER-PC\ADMIN /v | C:\Windows\System32\gpresult.exe | — | nddc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Query Group Policy RSOP Data Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 992 | "C:\Users\admin\AppData\Local\Temp\RunNetworkDetective.exe" | C:\Users\admin\AppData\Local\Temp\RunNetworkDetective.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: DataCollectorGuiNetworkDetective Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1536 | "ipconfig.exe" /all | C:\Windows\System32\ipconfig.exe | — | RunNetworkDetective.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1624 | "subst.exe" | C:\Windows\System32\subst.exe | — | nddc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Subst Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1696 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\runLocal.bat" " | C:\Windows\System32\cmd.exe | — | networkdetectivecomputerdatacollector (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1976 | "gpresult.exe" /user USER-PC\ADMINISTRATOR /v | C:\Windows\System32\gpresult.exe | — | nddc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Query Group Policy RSOP Data Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\AppData\Local\Temp\networkdetectivecomputerdatacollector (1).exe" | C:\Users\admin\AppData\Local\Temp\networkdetectivecomputerdatacollector (1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2548 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\r-m0iol3.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | RunNetworkDetective.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2880 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES768A.tmp" "c:\Users\admin\AppData\Local\Temp\CSC7689.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 3092 | nddc.exe -local | C:\Users\admin\AppData\Local\Temp\nddc.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: NetworkDetectiveDataCollector Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
29 489
Read events
29 435
Write events
50
Delete events
4
Modification events
| (PID) Process: | (2124) networkdetectivecomputerdatacollector (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2124) networkdetectivecomputerdatacollector (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2124) networkdetectivecomputerdatacollector (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2124) networkdetectivecomputerdatacollector (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3092) nddc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3092) nddc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3092) nddc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3092) nddc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3092) nddc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3092) nddc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
Executable files
67
Suspicious files
25
Text files
41
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2124 | networkdetectivecomputerdatacollector (1).exe | C:\Users\admin\AppData\Local\Temp\AppUtil.dll | executable | |
MD5:— | SHA256:— | |||
| 2124 | networkdetectivecomputerdatacollector (1).exe | C:\Users\admin\AppData\Local\Temp\blank-database.s3db | binary | |
MD5:— | SHA256:— | |||
| 2124 | networkdetectivecomputerdatacollector (1).exe | C:\Users\admin\AppData\Local\Temp\blank-prescan-database.s3db | binary | |
MD5:— | SHA256:— | |||
| 2124 | networkdetectivecomputerdatacollector (1).exe | C:\Users\admin\AppData\Local\Temp\blank-prescan.s3db | binary | |
MD5:— | SHA256:— | |||
| 2124 | networkdetectivecomputerdatacollector (1).exe | C:\Users\admin\AppData\Local\Temp\blank-sdf-database.s3db | binary | |
MD5:— | SHA256:— | |||
| 2124 | networkdetectivecomputerdatacollector (1).exe | C:\Users\admin\AppData\Local\Temp\Cassia.dll | executable | |
MD5:— | SHA256:— | |||
| 2124 | networkdetectivecomputerdatacollector (1).exe | C:\Users\admin\AppData\Local\Temp\cloudUrlPatterns.txt | text | |
MD5:— | SHA256:— | |||
| 2124 | networkdetectivecomputerdatacollector (1).exe | C:\Users\admin\AppData\Local\Temp\DataCollectorGuiV2.dll | executable | |
MD5:— | SHA256:— | |||
| 2124 | networkdetectivecomputerdatacollector (1).exe | C:\Users\admin\AppData\Local\Temp\ExcelDataReader.DataSet.dll | executable | |
MD5:— | SHA256:— | |||
| 2124 | networkdetectivecomputerdatacollector (1).exe | C:\Users\admin\AppData\Local\Temp\ExcelDataReader.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
208
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
992 | RunNetworkDetective.exe | POST | 200 | 3.231.135.115:80 | http://go.rapidfiretools.com/remotews3/fmit_na_ws.asmx | unknown | — | — | unknown |
992 | RunNetworkDetective.exe | GET | 429 | 142.250.186.132:80 | http://www.google.com/sorry/index?continue=http://www.google.com/&q=EgTYGNVjGPjRwbAGIjDIJH5OrkYPXSMzjW3RkAIXEEnj3YjNG5Y4Ie2q5v3IAp78Murpnidw3uiPpGyIwZAyAXJKGVNPUlJZX0FCVVNJVkVfTkVUX01FU1NBR0VaAUM | unknown | — | — | unknown |
992 | RunNetworkDetective.exe | GET | 302 | 142.250.186.132:80 | http://www.google.com/ | unknown | — | — | unknown |
992 | RunNetworkDetective.exe | GET | 301 | 87.248.119.251:80 | http://www.yahoo.com/ | unknown | — | — | unknown |
992 | RunNetworkDetective.exe | GET | 301 | 87.248.119.251:80 | http://www.yahoo.com/ | unknown | — | — | unknown |
992 | RunNetworkDetective.exe | GET | 301 | 87.248.119.251:80 | http://www.yahoo.com/ | unknown | — | — | unknown |
992 | RunNetworkDetective.exe | GET | 301 | 87.248.119.251:80 | http://www.yahoo.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
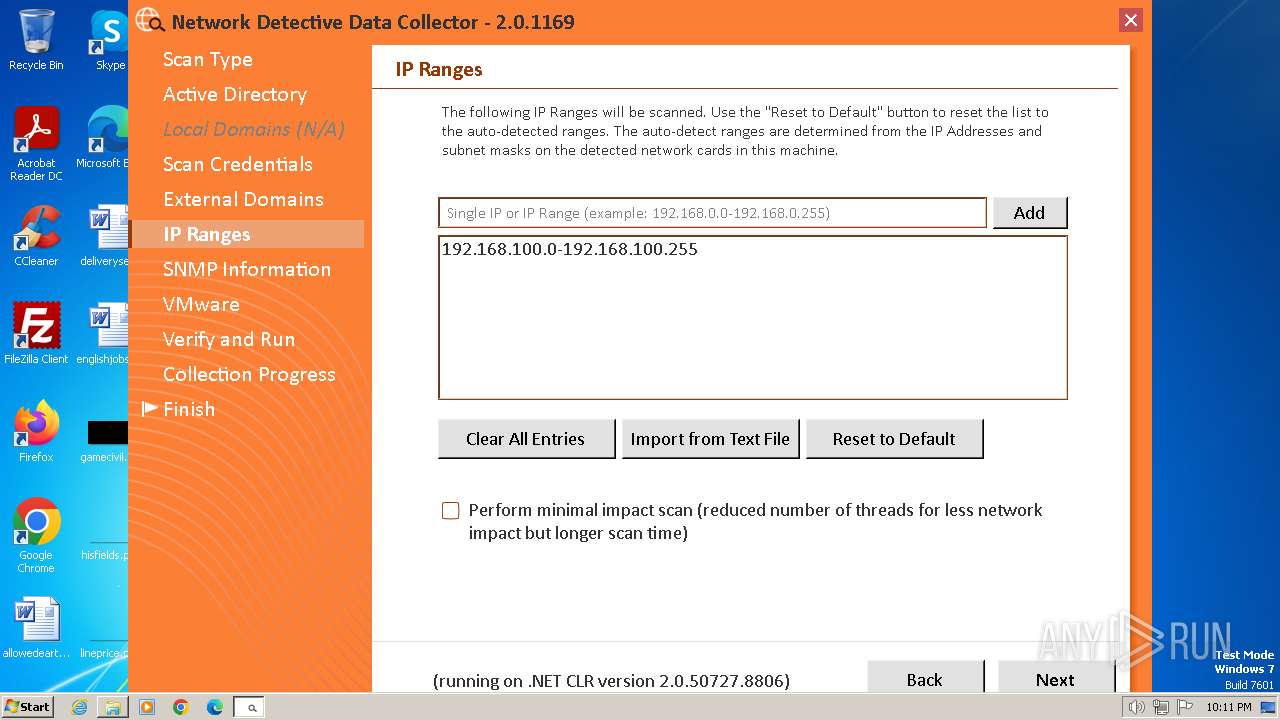
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
— | — | 255.255.255.255:1434 | — | — | — | unknown |
4 | System | 192.168.100.2:137 | — | — | — | whitelisted |
992 | RunNetworkDetective.exe | 3.231.135.115:80 | go.rapidfiretools.com | AMAZON-AES | US | unknown |
992 | RunNetworkDetective.exe | 192.168.100.2:137 | — | — | — | whitelisted |
992 | RunNetworkDetective.exe | 192.168.100.2:21 | — | — | — | whitelisted |
992 | RunNetworkDetective.exe | 192.30.45.30:43 | whois.internic.net | CLT-NIC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
2.100.168.192.in-addr.arpa |
| unknown |
go.rapidfiretools.com |
| unknown |
whois.internic.net |
| unknown |
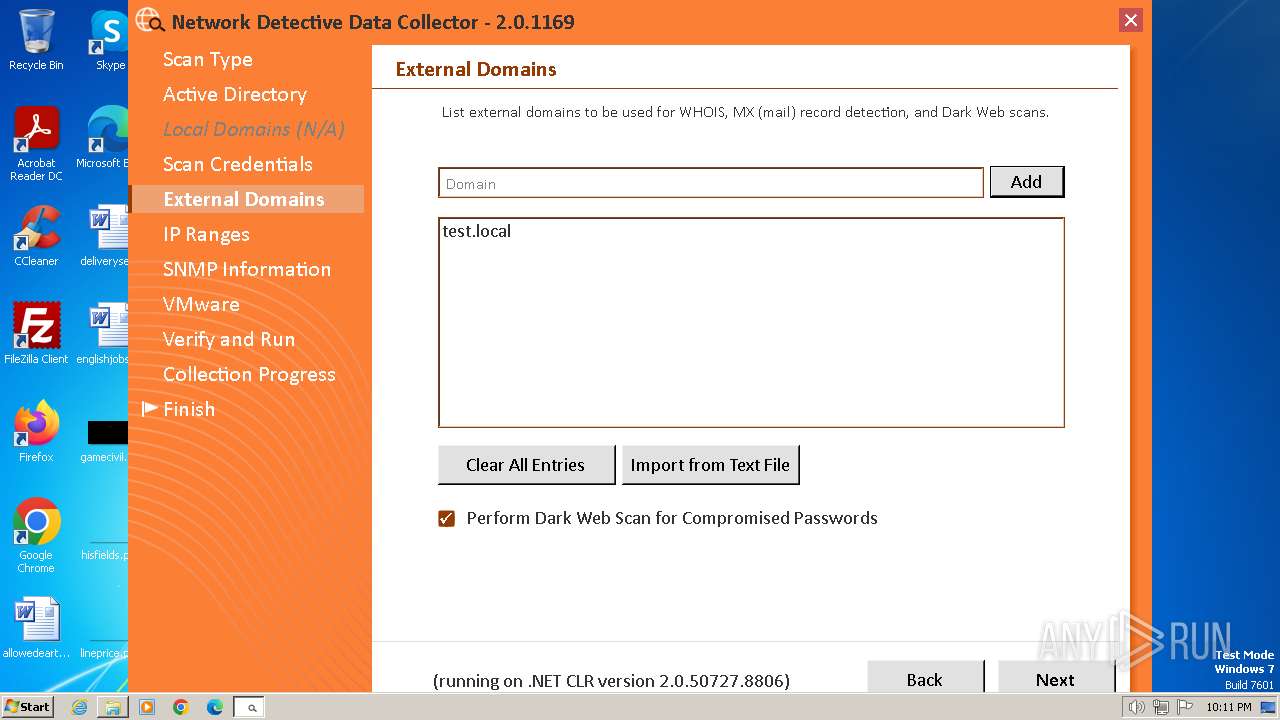
test.local |
| unknown |
www.google.com |
| whitelisted |
www.yahoo.com |
| whitelisted |
de.yahoo.com |
| whitelisted |
1.4.43.10.in-addr.arpa |
| unknown |
37.11.25.154.in-addr.arpa |
| unknown |
be3693.agr41.fra03.atlas.cogentco.com |
| unknown |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
nddc.exe | Native library pre-loader is trying to load native SQLite library "C:\Users\admin\AppData\Local\Temp\x86\SQLite.Interop.dll"...
|
RunNetworkDetective.exe | Native library pre-loader is trying to load native SQLite library "C:\Users\admin\AppData\Local\Temp\x86\SQLite.Interop.dll"...
|
RunNetworkDetective.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
RunNetworkDetective.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
RunNetworkDetective.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
RunNetworkDetective.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
RunNetworkDetective.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
RunNetworkDetective.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
RunNetworkDetective.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
RunNetworkDetective.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|