| File name: | CMI_Business_Banking_1.2.5.exe |
| Full analysis: | https://app.any.run/tasks/41f55626-9244-4b7c-ba8d-9bebe966f473 |
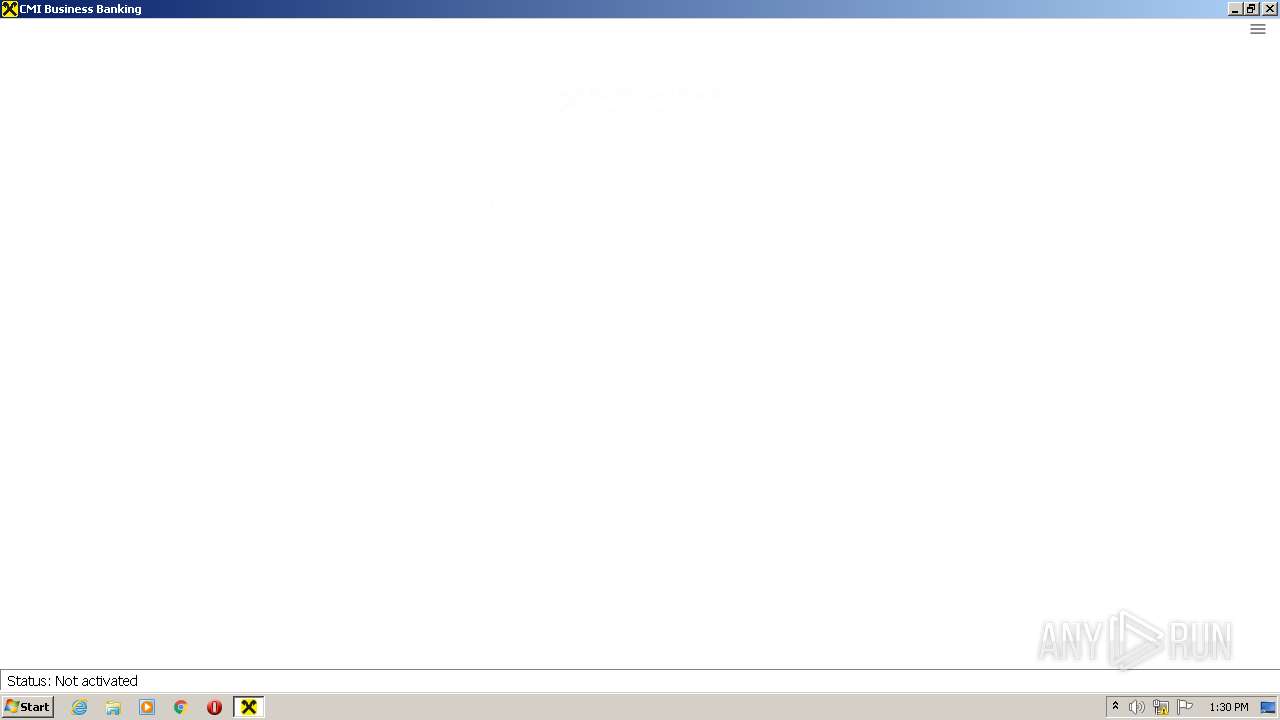
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2022, 13:29:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9AB3219D824AF2291F120AEE21442788 |
| SHA1: | 52B292C9F03612DEEA7535D22F29A38D978ADAFB |
| SHA256: | 3BE920951A580A024845567B331773C459BB30AA462E5C1B2B7544C036CC1A3B |
| SSDEEP: | 196608:K5E+7eYFwTeLkg1YKNAhXRri/asPsr5f1rhPLJfNaycBlmIQUF6hiiQ6i:M7PFwaAgSIAhXVZsPq5f/LVN6eUkhiie |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- CMI_Business_Banking_1.2.5.exe (PID: 2192)
- CMI_Business_Banking_1.2.5.exe (PID: 388)
- CMI_Business_Banking_1.2.5.exe (PID: 3624)
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
Changes IE settings (feature browser emulation)
- CMI_Business_Banking_1.2.5.exe (PID: 2192)
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
Reads Environment values
- CMI_Business_Banking_1.2.5.exe (PID: 2192)
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
Application launched itself
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
- CMI_Business_Banking_1.2.5.exe (PID: 2192)
Reads CPU info
- CMI_Business_Banking_1.2.5.exe (PID: 2192)
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
Reads the computer name
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
- CMI_Business_Banking_1.2.5.exe (PID: 2192)
Reads Microsoft Outlook installation path
- CMI_Business_Banking_1.2.5.exe (PID: 2192)
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3984)
Creates files in the user directory
- CMI_Business_Banking_1.2.5.exe (PID: 2192)
Reads internet explorer settings
- CMI_Business_Banking_1.2.5.exe (PID: 2192)
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
Starts Internet Explorer
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
INFO
Checks Windows Trust Settings
- CMI_Business_Banking_1.2.5.exe (PID: 2192)
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 1464)
- iexplore.exe (PID: 3984)
- AcroRd32.exe (PID: 3060)
Manual execution by user
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
Reads settings of System Certificates
- CMI_Business_Banking_1.2.5.exe (PID: 2192)
- CMI_Business_Banking_1.2.5.exe (PID: 1928)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 1464)
- iexplore.exe (PID: 3984)
- AcroRd32.exe (PID: 3060)
Checks supported languages
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 1464)
- iexplore.exe (PID: 3984)
- AcroRd32.exe (PID: 3360)
- AcroRd32.exe (PID: 3060)
- RdrCEF.exe (PID: 1996)
- RdrCEF.exe (PID: 3824)
- RdrCEF.exe (PID: 116)
- RdrCEF.exe (PID: 2764)
- RdrCEF.exe (PID: 3440)
- RdrCEF.exe (PID: 3464)
- RdrCEF.exe (PID: 2100)
Changes internet zones settings
- iexplore.exe (PID: 1464)
Reads the computer name
- iexplore.exe (PID: 1464)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3984)
- AcroRd32.exe (PID: 3060)
- AcroRd32.exe (PID: 3360)
- RdrCEF.exe (PID: 1996)
Changes settings of System certificates
- iexplore.exe (PID: 1464)
Application launched itself
- iexplore.exe (PID: 1464)
- AcroRd32.exe (PID: 3060)
- RdrCEF.exe (PID: 1996)
Reads internet explorer settings
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3984)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1464)
Searches for installed software
- AcroRd32.exe (PID: 3060)
- AcroRd32.exe (PID: 3360)
Reads CPU info
- AcroRd32.exe (PID: 3360)
Reads the hosts file
- RdrCEF.exe (PID: 1996)
Reads the date of Windows installation
- iexplore.exe (PID: 1464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
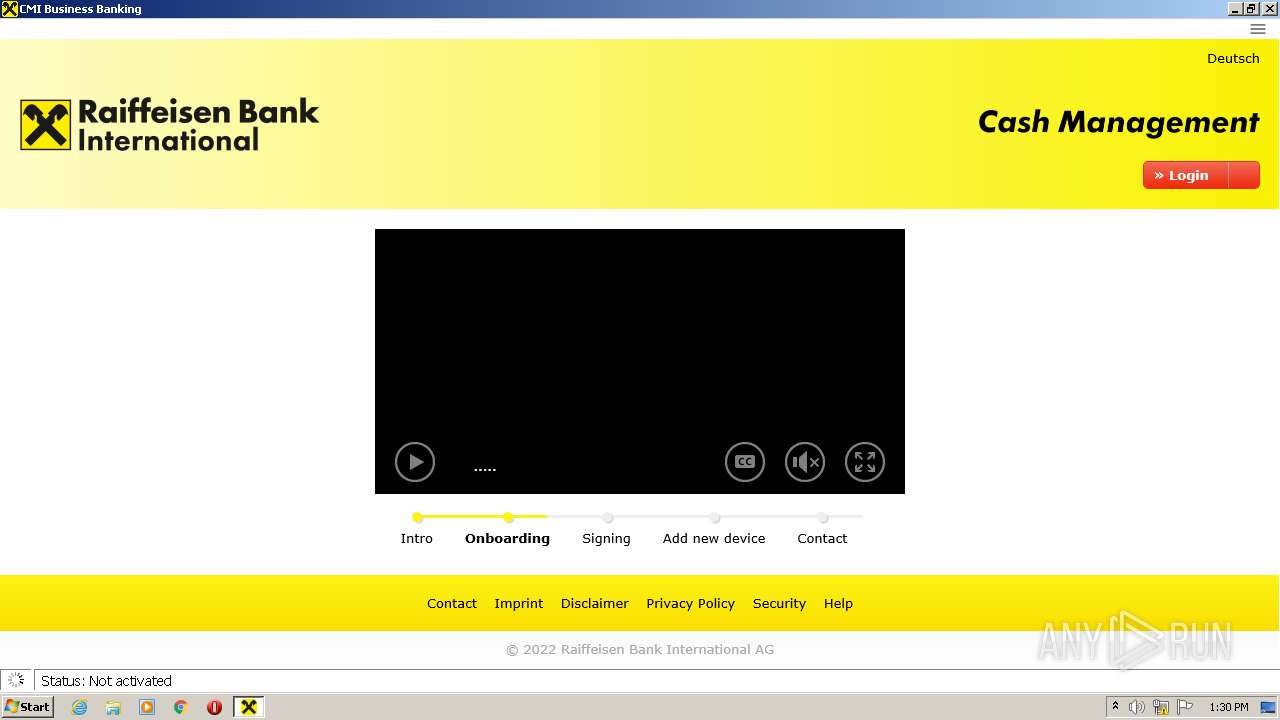
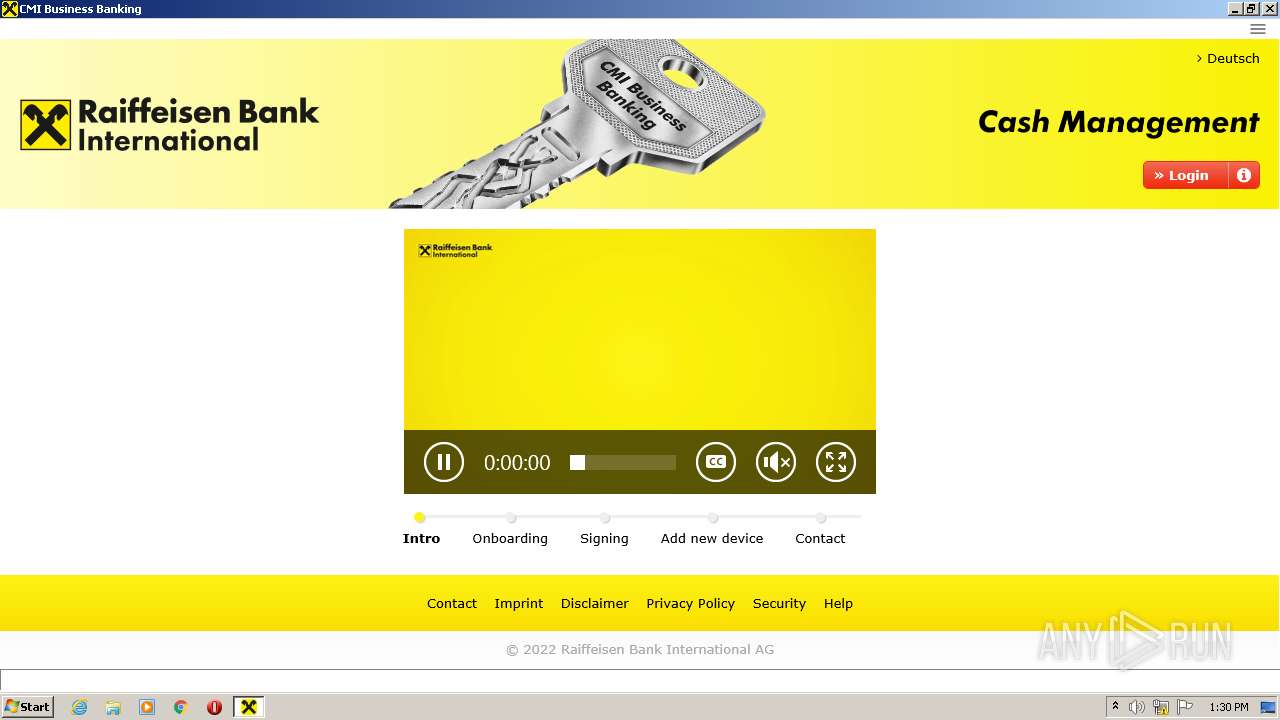
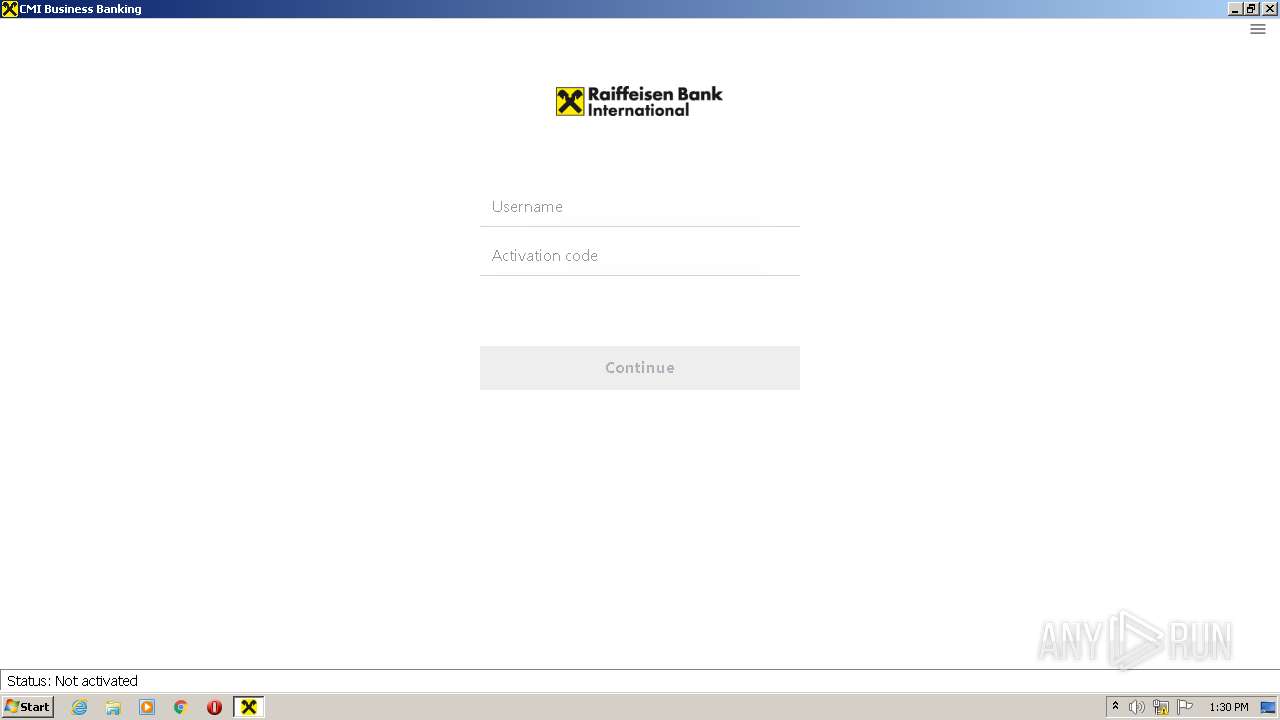
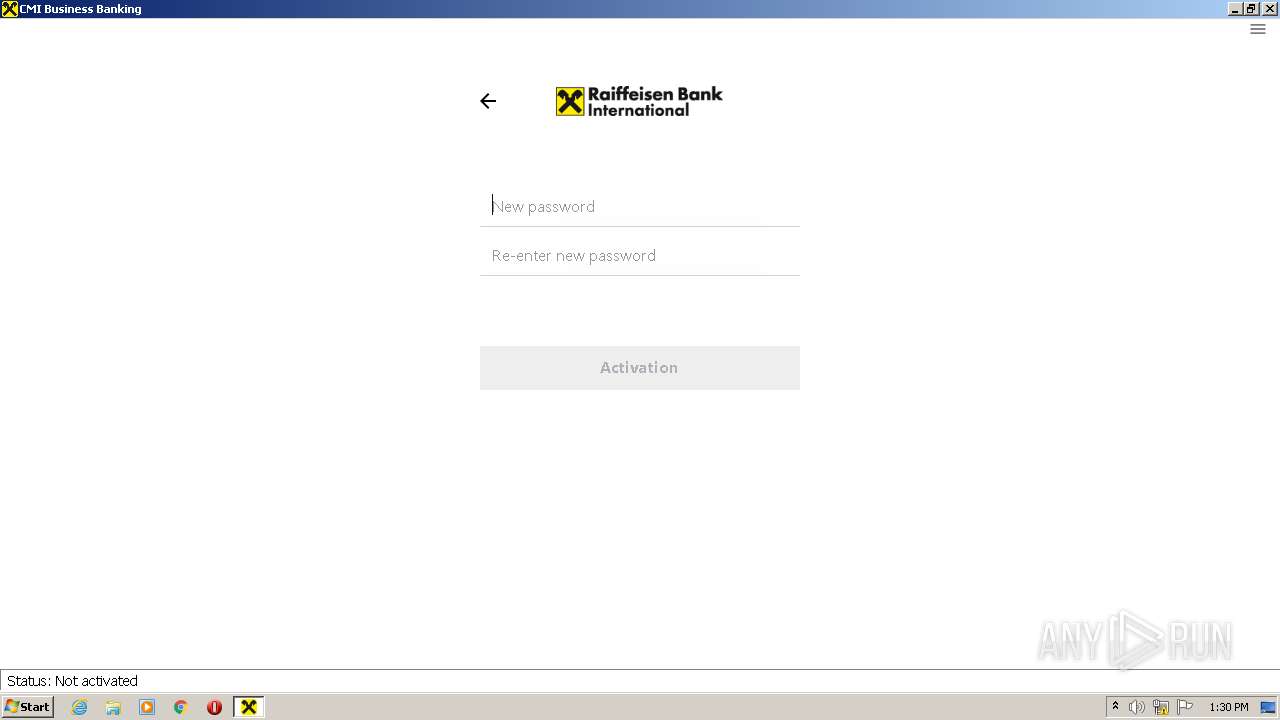
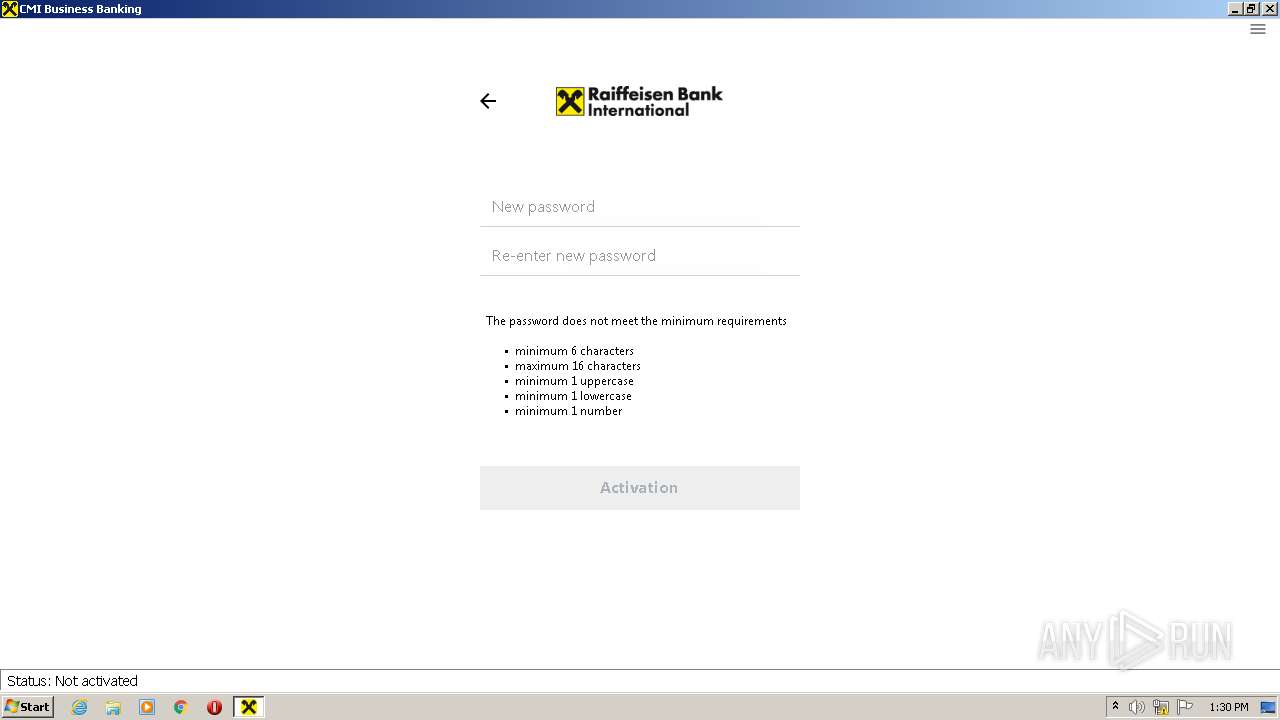
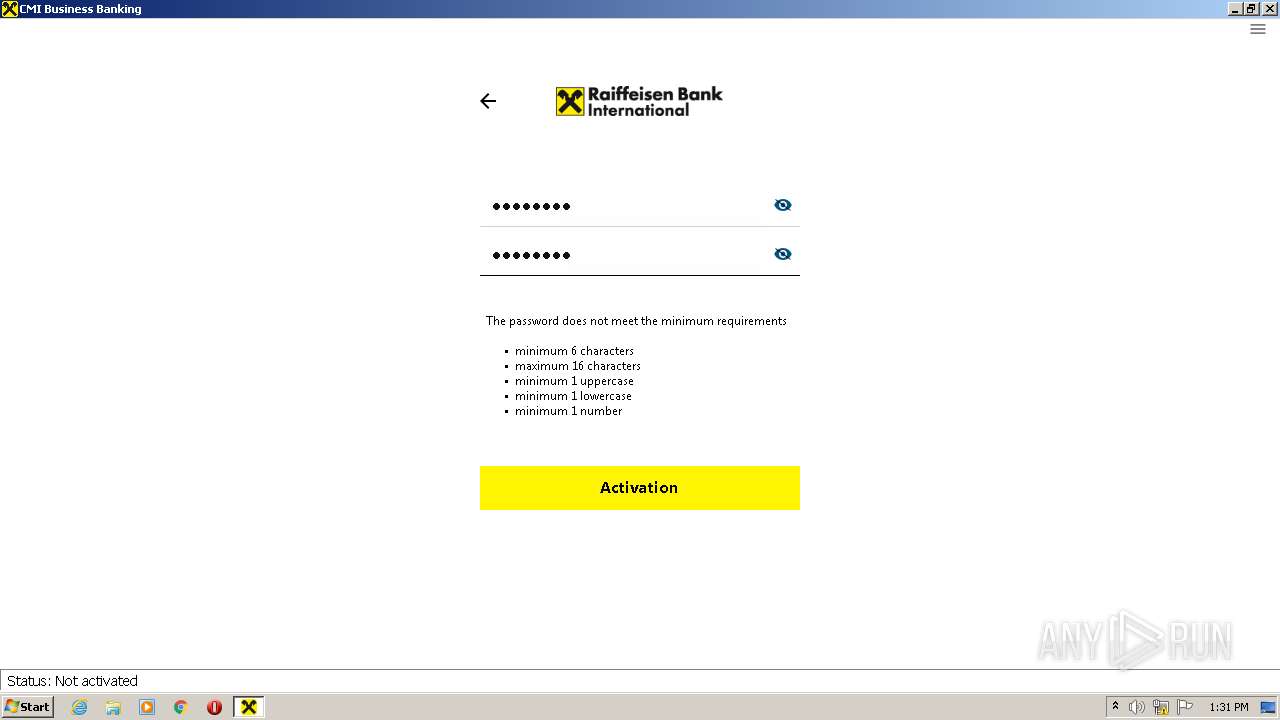
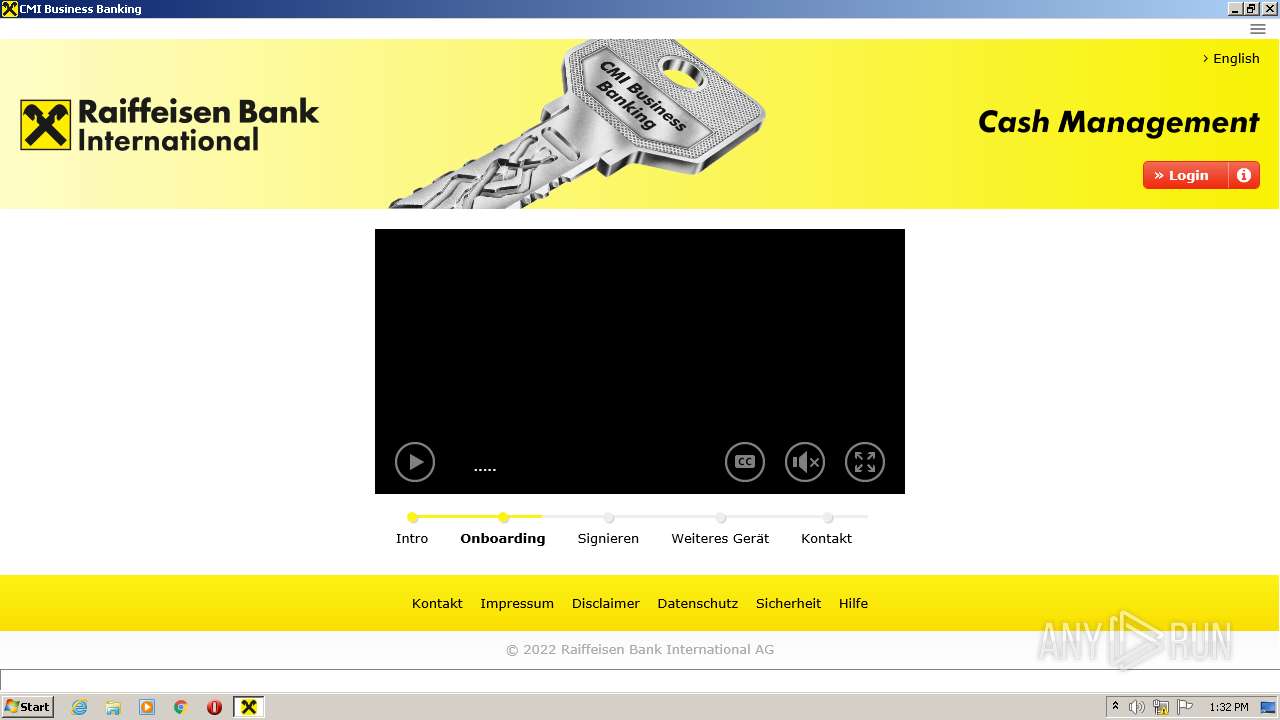
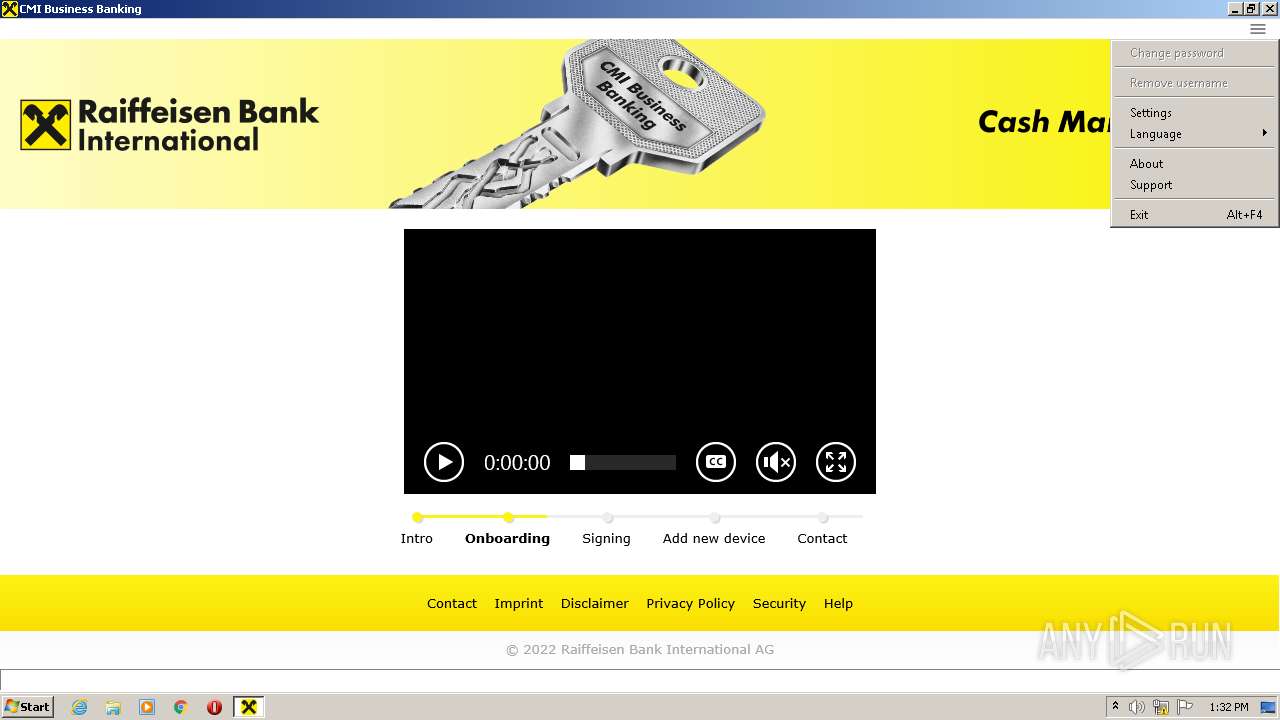
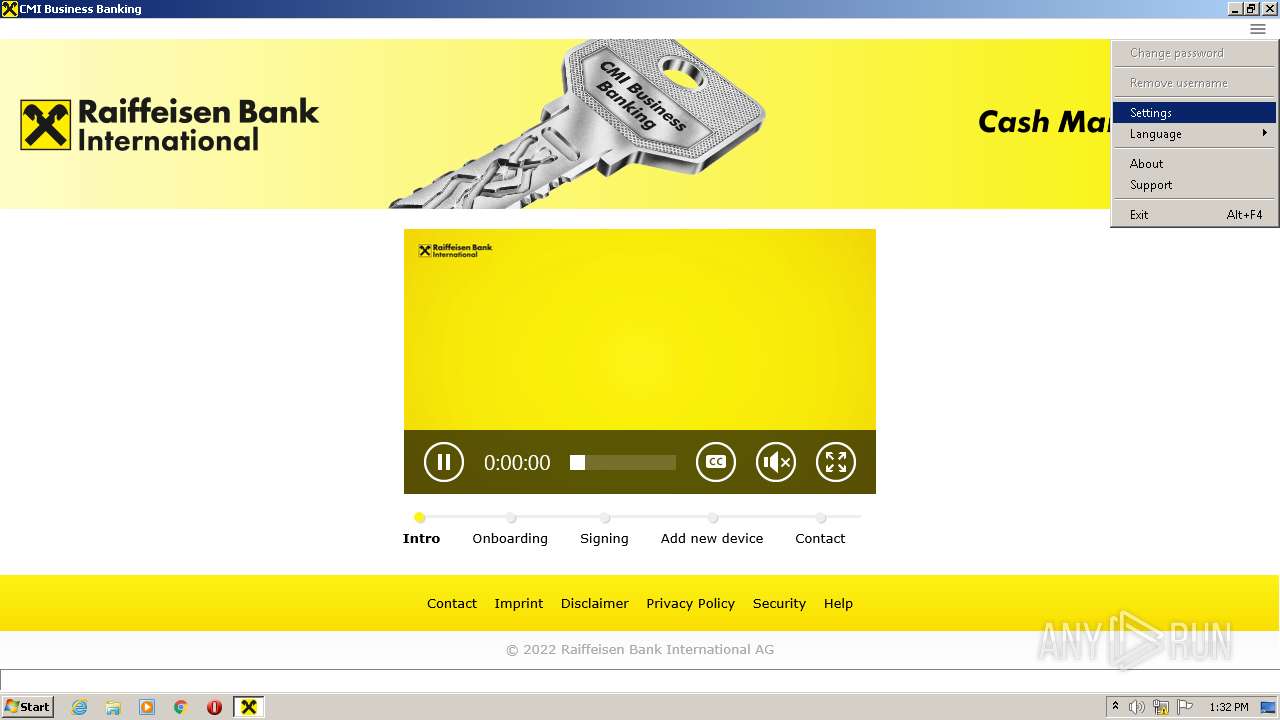
| ProductName: | CMI Business Banking |
|---|---|
| OriginalFileName: | mIDentity.exe |
| LegalCopyright: | Raiffeisen Bank International AG |
| InternalName: | mIDentity.exe |
| FileDescription: | CMI Business Banking |
| CompanyName: | Raiffeisen Bank International AG |
| ProductVersion: | 2012.0011.14.0 |
| FileVersion: | 1, 2, 5, 0 |
| CharacterSet: | Unicode |
| LanguageCode: | German |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2012.11.14.0 |
| FileVersionNumber: | 1.2.5.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x36c36 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 535040 |
| CodeSize: | 370176 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2019:09:04 13:12:13+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Sep-2019 11:12:13 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| FileVersion: | 1, 2, 5, 0 |
| ProductVersion: | 2012.0011.14.0 |
| CompanyName: | Raiffeisen Bank International AG |
| FileDescription: | CMI Business Banking |
| InternalName: | mIDentity.exe |
| LegalCopyright: | Raiffeisen Bank International AG |
| OriginalFilename: | mIDentity.exe |
| ProductName: | CMI Business Banking |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 04-Sep-2019 11:12:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0005A493 | 0x0005A600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.73142 |
.rdata | 0x0005C000 | 0x00023082 | 0x00023200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.77275 |
.data | 0x00080000 | 0x00009234 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.4199 |
.gfids | 0x0008A000 | 0x00000224 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.71418 |
.tls | 0x0008B000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x0008C000 | 0x00056A05 | 0x00056C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.79811 |
.reloc | 0x000E3000 | 0x00005600 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58551 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.83667 | 67624 | UNKNOWN | German - Germany | RT_ICON |
3 | 3.88143 | 9640 | UNKNOWN | German - Germany | RT_ICON |
4 | 4.45943 | 4264 | UNKNOWN | German - Germany | RT_ICON |
5 | 5.29125 | 1128 | UNKNOWN | German - Germany | RT_ICON |
104 | 2.6474 | 76 | Latin 1 / Western European | German - Germany | RT_GROUP_ICON |
Imports
KERNEL32.dll |
PSAPI.DLL |
USER32.dll (delay-loaded) |
VERSION.dll |
WS2_32.dll |
Total processes
56
Monitored processes
17
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1180,11705421027964464199,2610990018264675131,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=118999363411999752 --mojo-platform-channel-handle=1400 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 388 | "C:\Users\admin\Desktop\CMI_Business_Banking_1.2.5.exe" | C:\Users\admin\Desktop\CMI_Business_Banking_1.2.5.exe | — | CMI_Business_Banking_1.2.5.exe | |||||||||||
User: admin Company: Raiffeisen Bank International AG
Integrity Level: MEDIUM Description: CMI Business Banking
Exit code: 0 Version: 1, 2, 5, 0 Modules
| |||||||||||||||
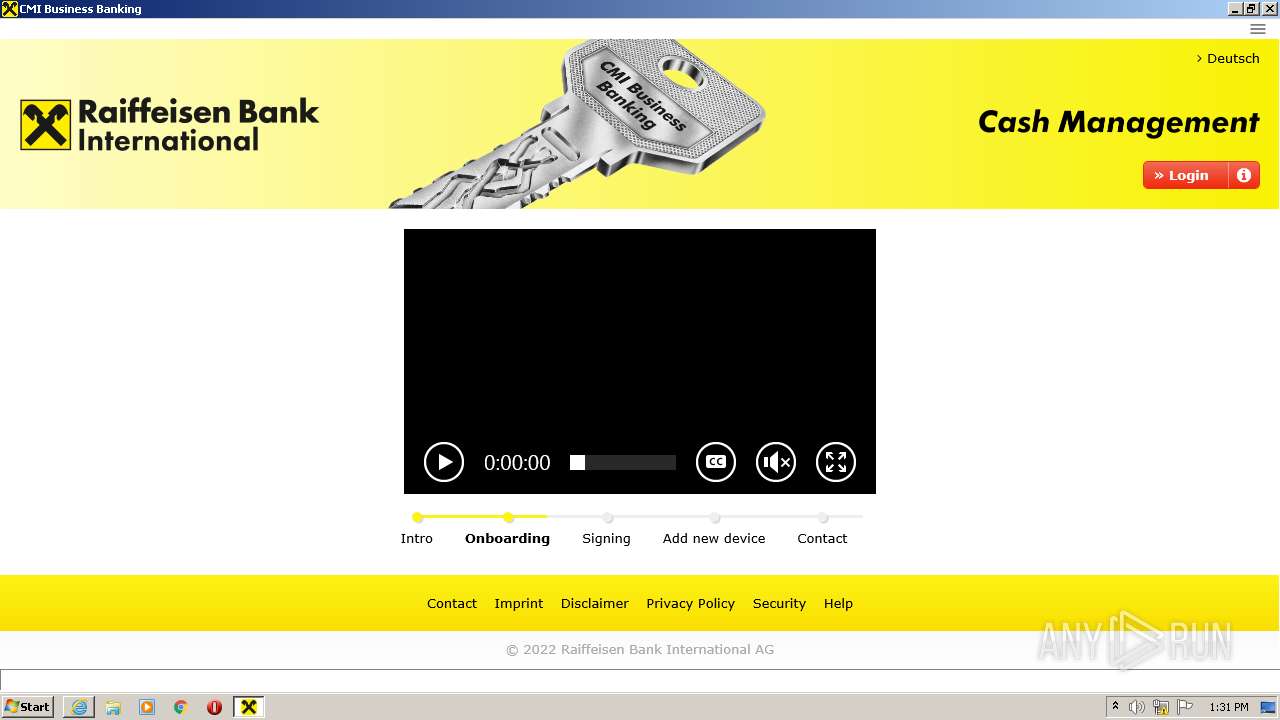
| 1464 | "C:\Program Files\Internet Explorer\iexplore.exe" https://cmi.rbinternational.com/cmimobile/disc_GB.htm | C:\Program Files\Internet Explorer\iexplore.exe | CMI_Business_Banking_1.2.5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1928 | "C:\Users\admin\Desktop\CMI_Business_Banking_1.2.5.exe" | C:\Users\admin\Desktop\CMI_Business_Banking_1.2.5.exe | Explorer.EXE | ||||||||||||
User: admin Company: Raiffeisen Bank International AG
Integrity Level: MEDIUM Description: CMI Business Banking
Exit code: 0 Version: 1, 2, 5, 0 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16514043 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1180,11705421027964464199,2610990018264675131,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9433270693809216571 --renderer-client-id=7 --mojo-platform-channel-handle=1448 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2192 | "C:\Users\admin\Desktop\CMI_Business_Banking_1.2.5.exe" | C:\Users\admin\Desktop\CMI_Business_Banking_1.2.5.exe | Explorer.EXE | ||||||||||||
User: admin Company: Raiffeisen Bank International AG
Integrity Level: MEDIUM Description: CMI Business Banking
Exit code: 0 Version: 1, 2, 5, 0 Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1180,11705421027964464199,2610990018264675131,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4267659212884699821 --renderer-client-id=2 --mojo-platform-channel-handle=1188 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 3060 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3984 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 3076 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3984 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
Total events
34 874
Read events
34 579
Write events
287
Delete events
8
Modification events
| (PID) Process: | (2192) CMI_Business_Banking_1.2.5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2192) CMI_Business_Banking_1.2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | CMI_Business_Banking_1.2.5.exe |
Value: 11000 | |||
| (PID) Process: | (2192) CMI_Business_Banking_1.2.5.exe | Key: | HKEY_CURRENT_USER\Software\WOW6432Node\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | CMI_Business_Banking_1.2.5.exe |
Value: 11000 | |||
| (PID) Process: | (2192) CMI_Business_Banking_1.2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_NINPUT_LEGACYMODE |
| Operation: | write | Name: | CMI_Business_Banking_1.2.5.exe |
Value: 0 | |||
| (PID) Process: | (2192) CMI_Business_Banking_1.2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2192) CMI_Business_Banking_1.2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2192) CMI_Business_Banking_1.2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2192) CMI_Business_Banking_1.2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2192) CMI_Business_Banking_1.2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2192) CMI_Business_Banking_1.2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
30
Text files
30
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2192 | CMI_Business_Banking_1.2.5.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2192 | CMI_Business_Banking_1.2.5.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CDE89F9DCB25D8AC547E3CEFDA4FB6C2_4B682C128718EEAAD12C8C7B8C0A9BFC | binary | |
MD5:— | SHA256:— | |||
| 2192 | CMI_Business_Banking_1.2.5.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EE44ECA143B76F2B9F2A5AA75B5D1EC6_5BFB72FAE1BB9D1928D1C5C92F52E8EA | der | |
MD5:— | SHA256:— | |||
| 2192 | CMI_Business_Banking_1.2.5.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EE44ECA143B76F2B9F2A5AA75B5D1EC6_5BFB72FAE1BB9D1928D1C5C92F52E8EA | binary | |
MD5:— | SHA256:— | |||
| 2192 | CMI_Business_Banking_1.2.5.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CDE89F9DCB25D8AC547E3CEFDA4FB6C2_4B682C128718EEAAD12C8C7B8C0A9BFC | der | |
MD5:— | SHA256:— | |||
| 2192 | CMI_Business_Banking_1.2.5.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0F7788E201A03EF5036E7C8BF55432CB_BDA62707BA70CB0111D9E81215C5BF30 | der | |
MD5:— | SHA256:— | |||
| 2192 | CMI_Business_Banking_1.2.5.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1401C7EC8E96BC79CBFD92F9DF762D_5398732881722BDE3E78D6CA6BB2B78B | binary | |
MD5:— | SHA256:— | |||
| 2192 | CMI_Business_Banking_1.2.5.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0F7788E201A03EF5036E7C8BF55432CB_BDA62707BA70CB0111D9E81215C5BF30 | binary | |
MD5:— | SHA256:— | |||
| 2192 | CMI_Business_Banking_1.2.5.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A583E2A51BFBDC1E492A57B7C8325850 | der | |
MD5:— | SHA256:— | |||
| 2192 | CMI_Business_Banking_1.2.5.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A583E2A51BFBDC1E492A57B7C8325850 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
27
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2192 | CMI_Business_Banking_1.2.5.exe | GET | 200 | 23.37.43.27:80 | http://rb.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTDRSYViRCZTxmZjLENmnwVjLly9QQU1MAGIknrOUvdk%2BJcobhHdglyA1gCEG4svewFC5D%2B%2FNzpNZRtnXw%3D | NL | der | 1.47 Kb | whitelisted |
2192 | CMI_Business_Banking_1.2.5.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAb9%2BQOWA63qAArrPye7uhs%3D | US | der | 471 b | whitelisted |
1928 | CMI_Business_Banking_1.2.5.exe | GET | 200 | 178.18.231.171:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_2010-07-06.crl | RU | der | 557 b | whitelisted |
2192 | CMI_Business_Banking_1.2.5.exe | GET | 200 | 178.18.231.171:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | RU | der | 824 b | whitelisted |
2192 | CMI_Business_Banking_1.2.5.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | der | 564 b | whitelisted |
2192 | CMI_Business_Banking_1.2.5.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ%2FYHKj6JjF6UBieQioTYpFsuEriQQUtnf6aUhHn1MS1cLqBzJ2B9GXBxkCEHwbNTVK59t050FfEWnKa6g%3D | NL | der | 1.51 Kb | shared |
2192 | CMI_Business_Banking_1.2.5.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAFnjx%2FviCJV2LCnDmt7siA%3D | US | der | 471 b | whitelisted |
1464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2192 | CMI_Business_Banking_1.2.5.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSFDxAmS5JEAmWxO0Ue9OdQ9z7zPAQUFQASKxOYspkH7R7for5XDStnAs0CEAMBmgI6%2F1ixa9bV6uYX8GY%3D | US | der | 471 b | whitelisted |
2192 | CMI_Business_Banking_1.2.5.exe | GET | 200 | 178.18.231.171:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | RU | der | 555 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2192 | CMI_Business_Banking_1.2.5.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2192 | CMI_Business_Banking_1.2.5.exe | 178.18.231.171:80 | crl.microsoft.com | Peering Ltd | RU | suspicious |
1928 | CMI_Business_Banking_1.2.5.exe | 217.13.188.144:443 | auth.rbinternational.com | Raiffeisen Informatik GmbH | AT | suspicious |
2192 | CMI_Business_Banking_1.2.5.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
2192 | CMI_Business_Banking_1.2.5.exe | 217.13.188.144:443 | auth.rbinternational.com | Raiffeisen Informatik GmbH | AT | suspicious |
2192 | CMI_Business_Banking_1.2.5.exe | 2.18.233.62:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
— | — | 178.18.231.171:80 | crl.microsoft.com | Peering Ltd | RU | suspicious |
3656 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1464 | iexplore.exe | 217.13.188.80:443 | cmi.rbinternational.com | Raiffeisen Informatik GmbH | AT | unknown |
3656 | iexplore.exe | 217.13.188.80:443 | cmi.rbinternational.com | Raiffeisen Informatik GmbH | AT | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
s.symcd.com |
| shared |
rb.symcd.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
auth.rbinternational.com |
| suspicious |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
cmi.rbinternational.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |