| File name: | GenP-3.4.14.1.exe |
| Full analysis: | https://app.any.run/tasks/bd5deeb3-0a11-430d-bd7f-f0cbad404289 |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2024, 06:15:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 5AA73CE6297B35AAC0067529A47B44C5 |
| SHA1: | 48238C0C52990AB1F64CA8FAA7FC310FD729AF49 |
| SHA256: | 3BDDB83344219A07A43E53F68A0F6920FDD51B7412540D0DAAEAC353B6AB11A2 |
| SSDEEP: | 49152:JE/XUraxm5O9QMal0QRO8tWDqSnXmYwj9hCcGaH6BBpOz46P1VW:J9rem5Oide69VW |
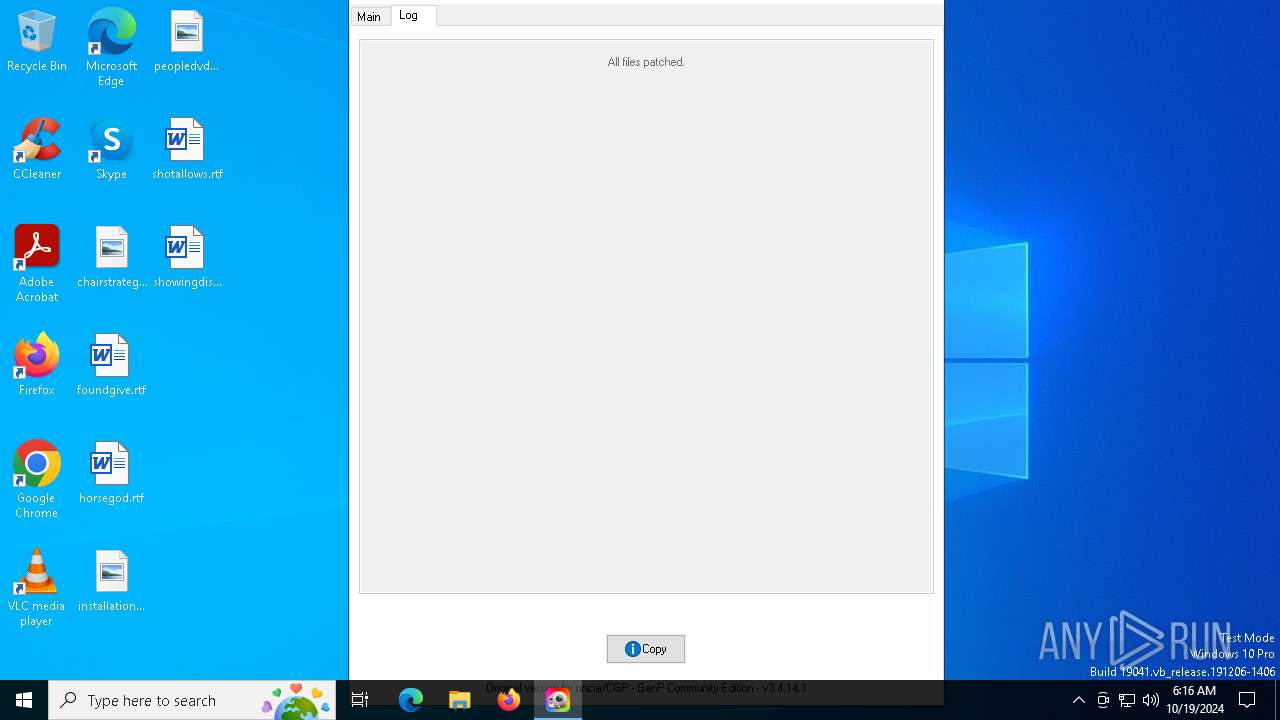
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- GenP-3.4.14.1.exe (PID: 6720)
Reads the date of Windows installation
- GenP-3.4.14.1.exe (PID: 6720)
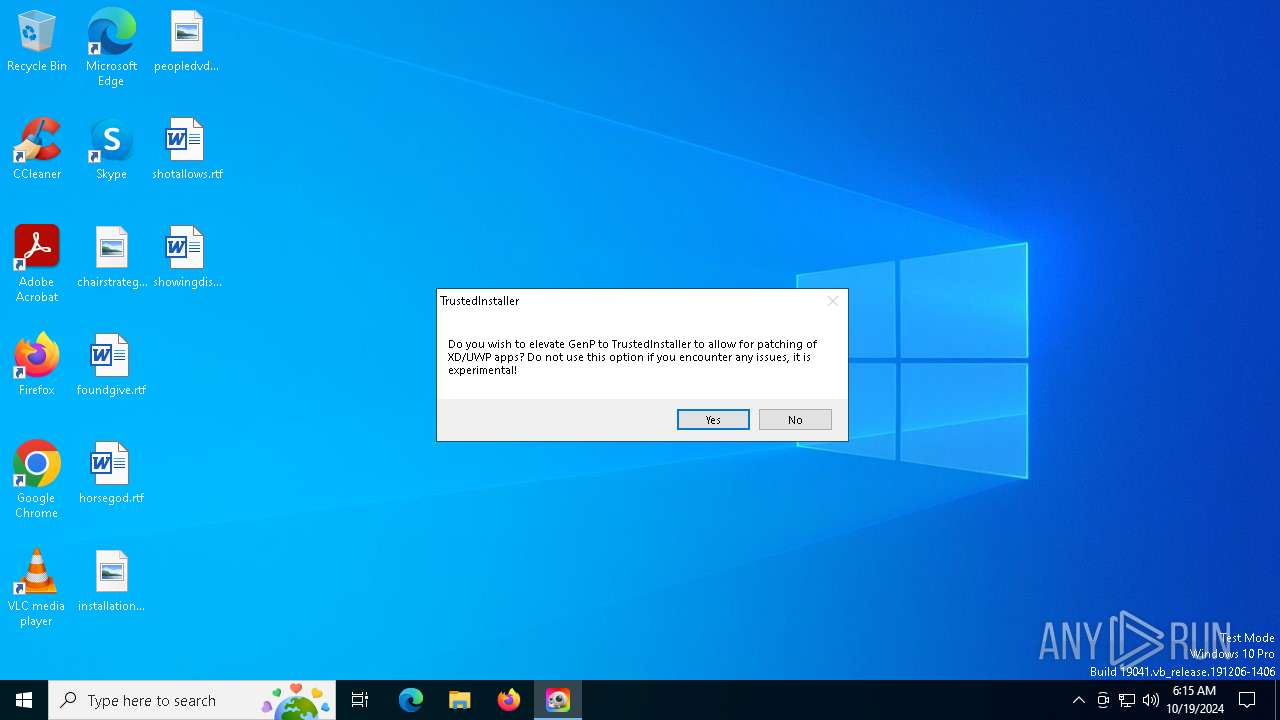
Application launched itself
- GenP-3.4.14.1.exe (PID: 6720)
Executable content was dropped or overwritten
- GenP-3.4.14.1.exe (PID: 6260)
- GenP-3.4.14.1.exe (PID: 2364)
INFO
The process uses the downloaded file
- GenP-3.4.14.1.exe (PID: 6720)
Checks supported languages
- GenP-3.4.14.1.exe (PID: 6720)
- GenP-3.4.14.1.exe (PID: 6260)
- NSudoLG.exe (PID: 5600)
- GenP-3.4.14.1.exe (PID: 2364)
Reads mouse settings
- GenP-3.4.14.1.exe (PID: 6720)
- GenP-3.4.14.1.exe (PID: 6260)
- GenP-3.4.14.1.exe (PID: 2364)
Reads the computer name
- GenP-3.4.14.1.exe (PID: 6720)
- GenP-3.4.14.1.exe (PID: 6260)
- NSudoLG.exe (PID: 5600)
- GenP-3.4.14.1.exe (PID: 2364)
Process checks computer location settings
- GenP-3.4.14.1.exe (PID: 6720)
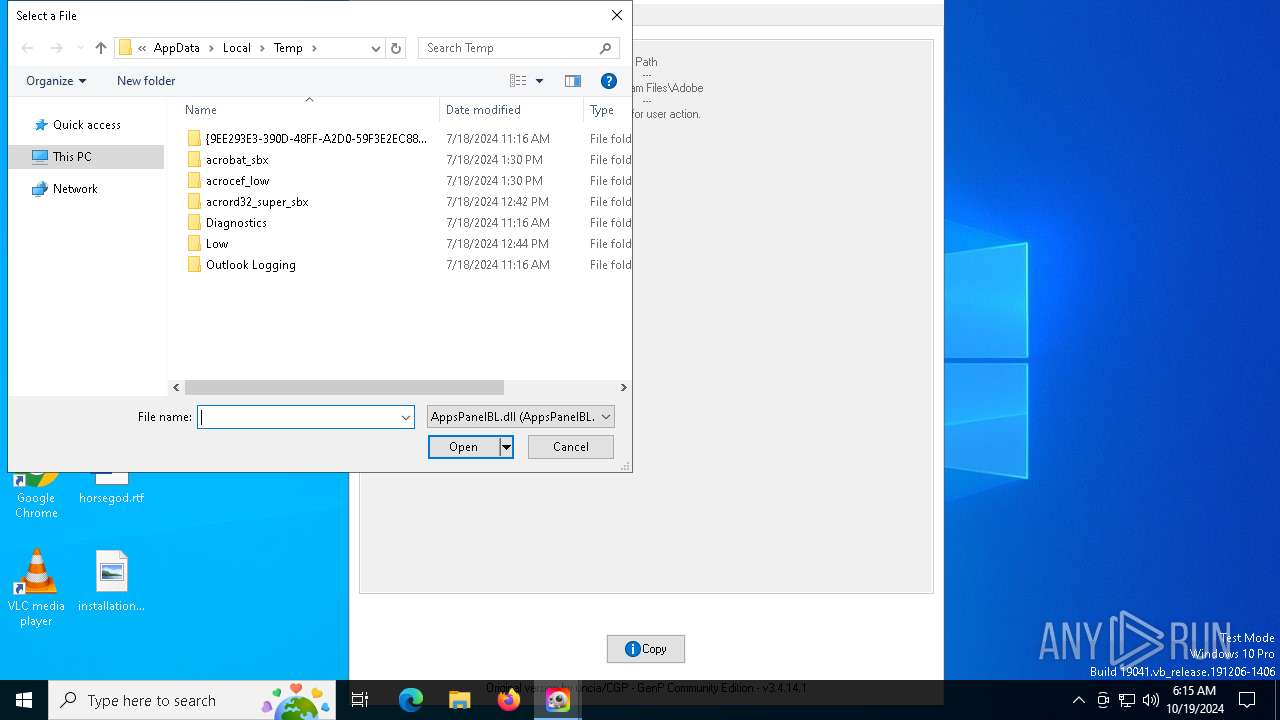
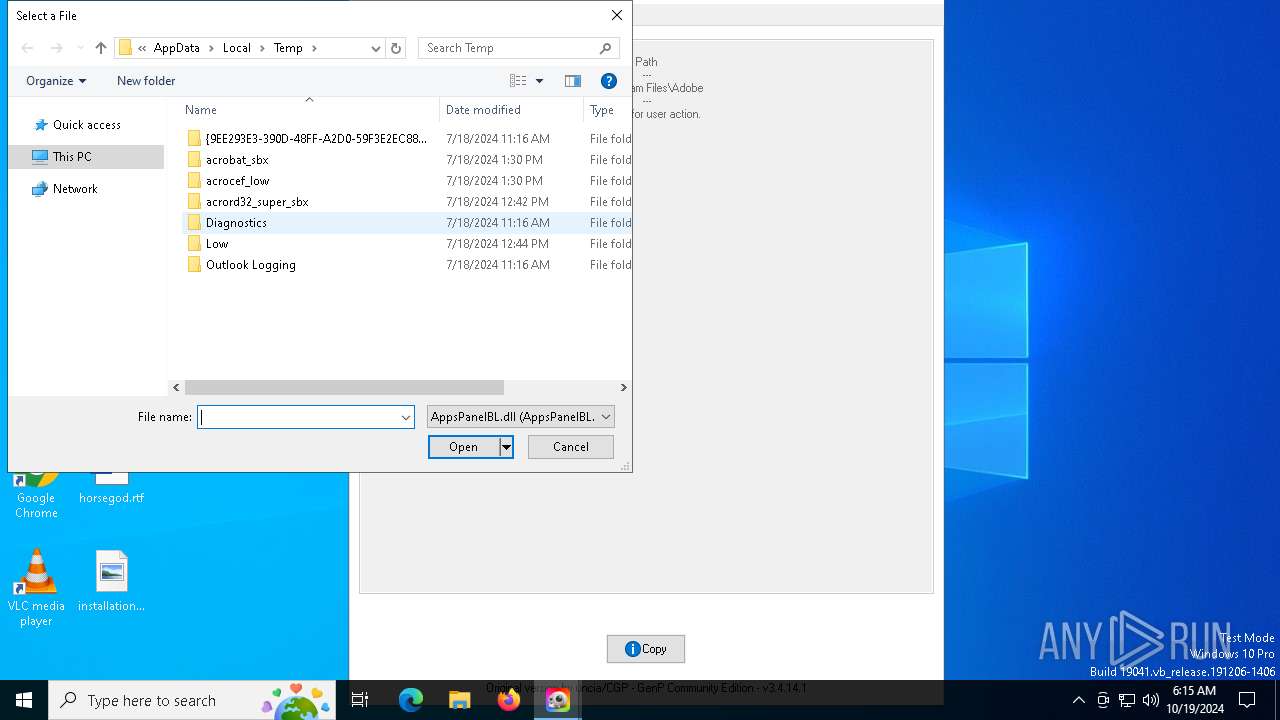
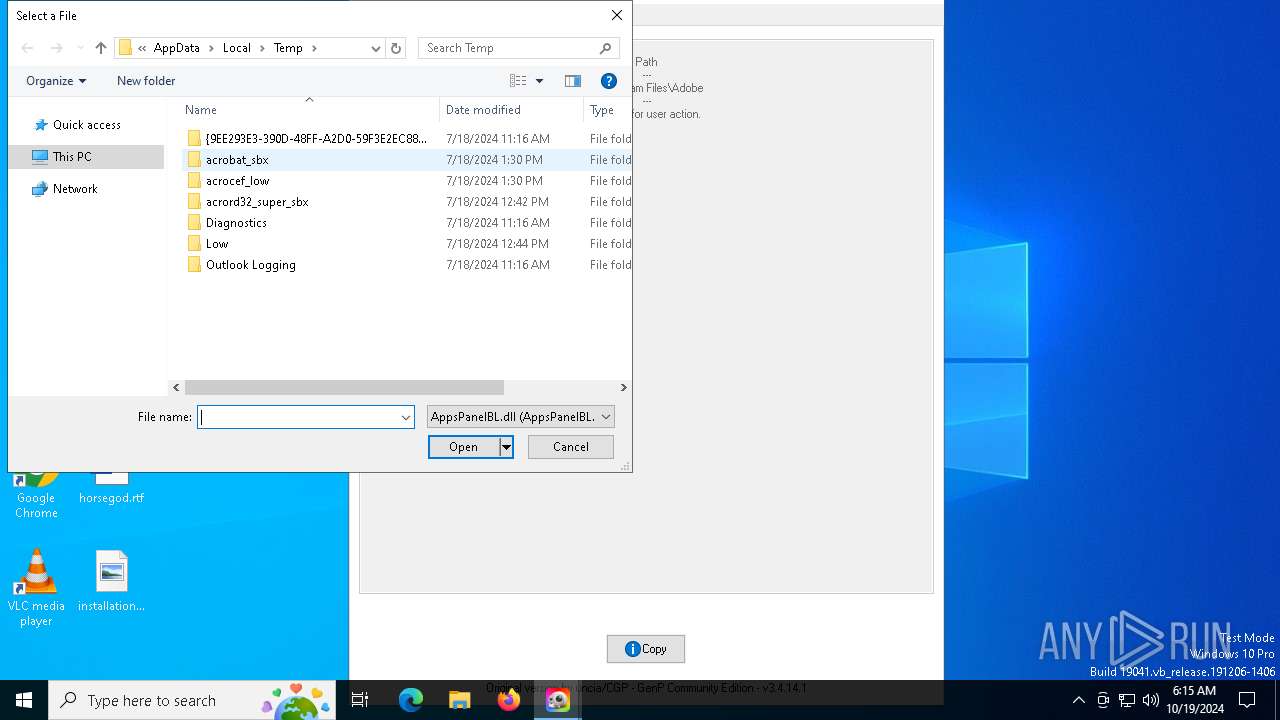
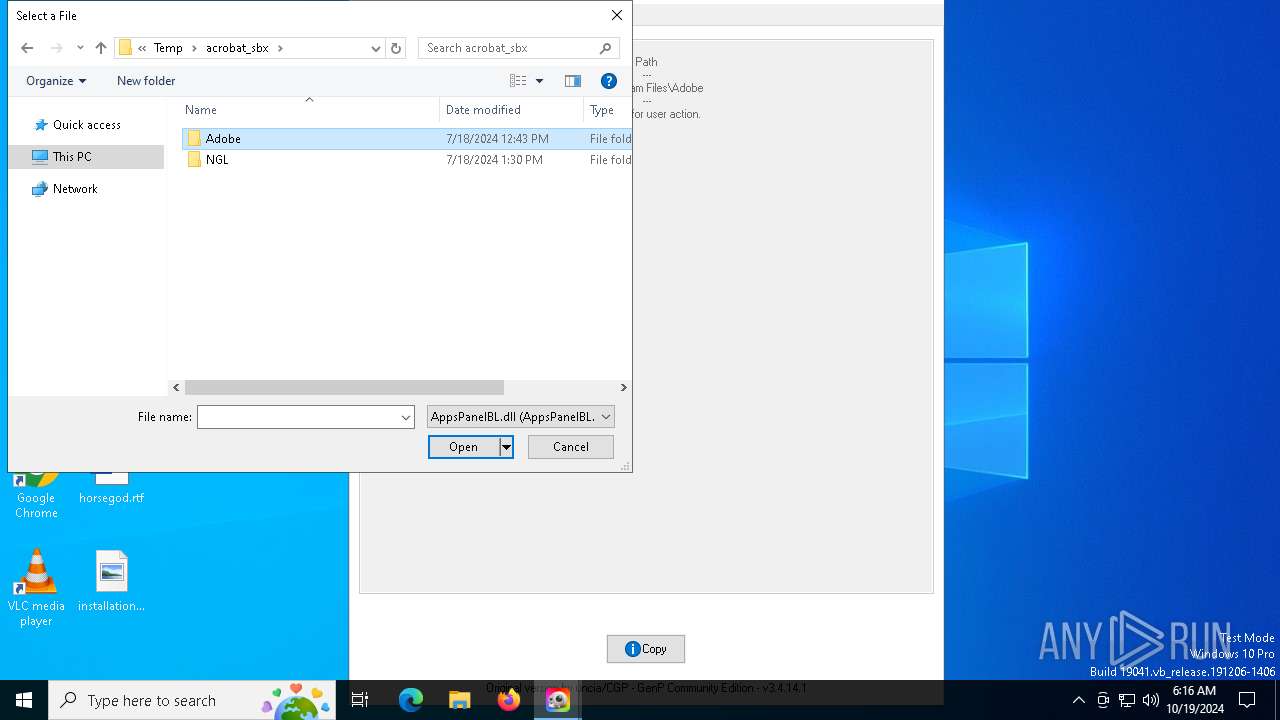
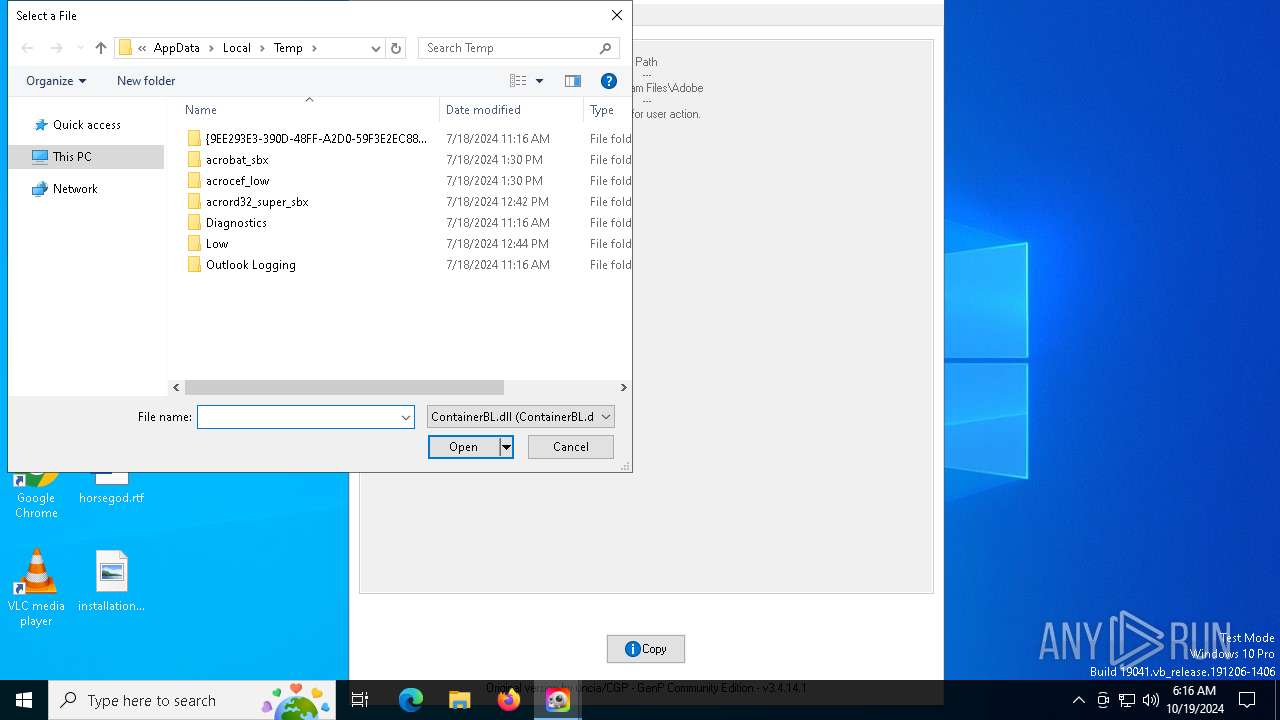
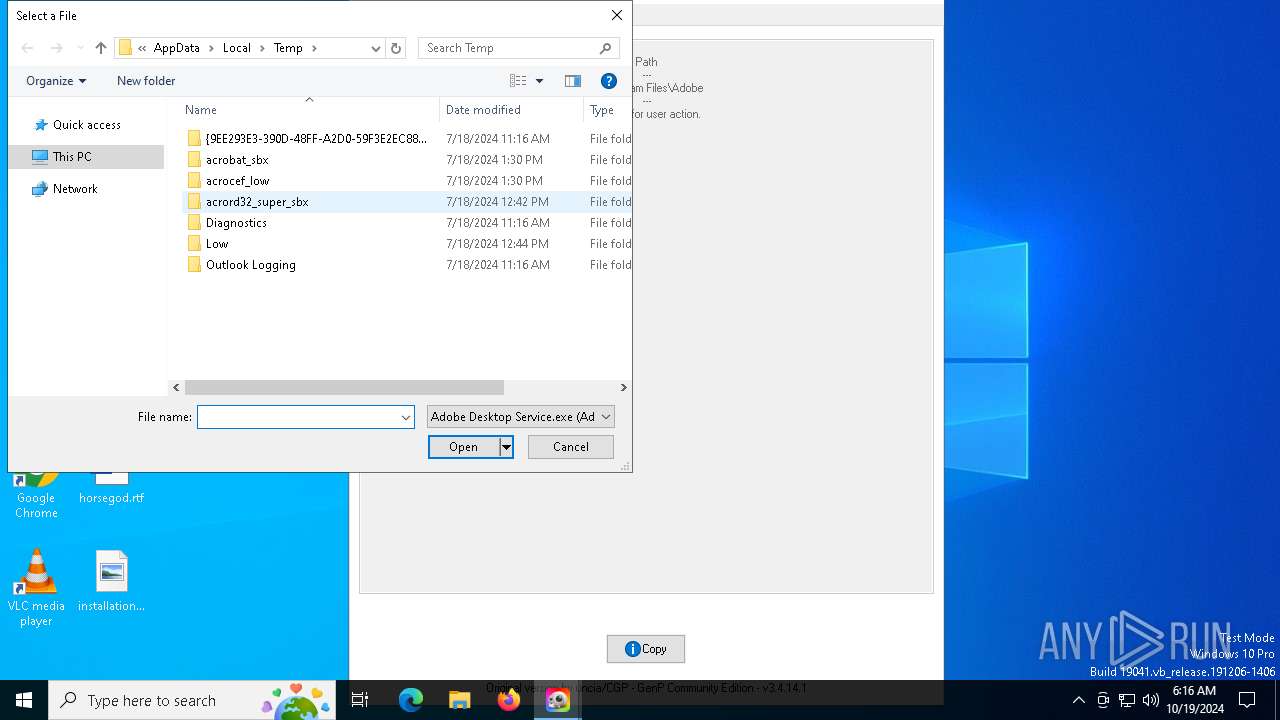
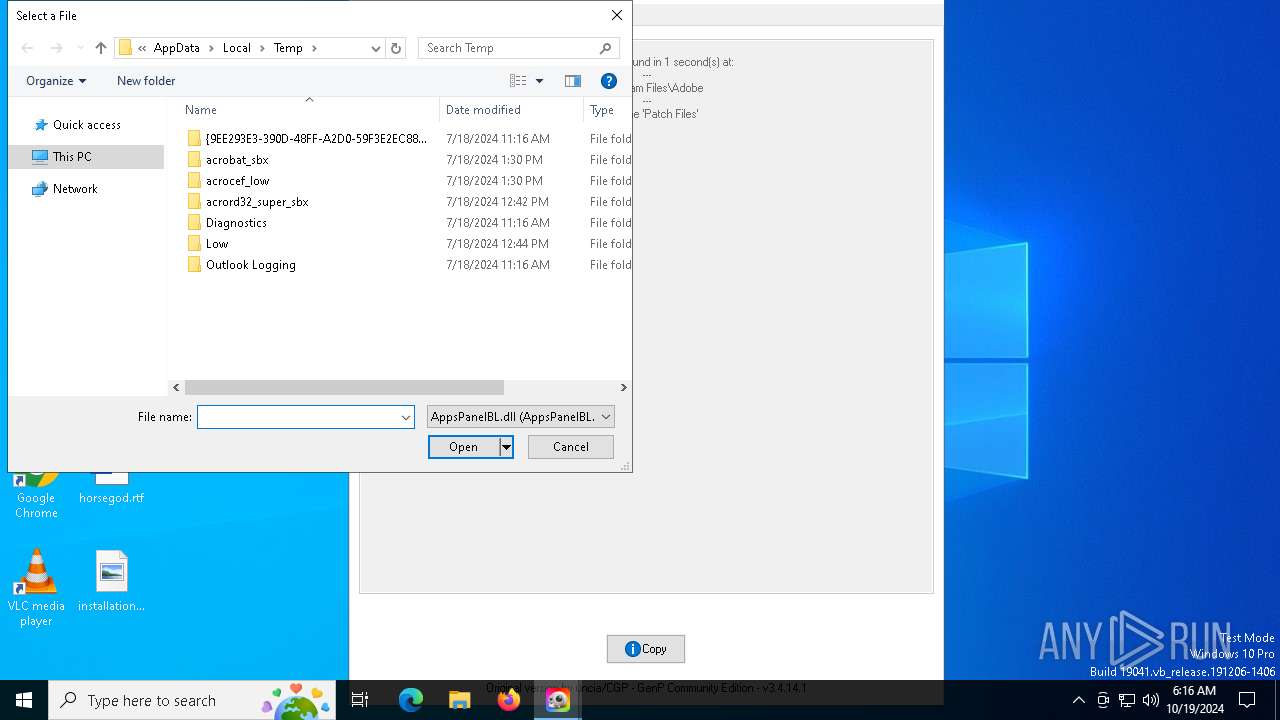
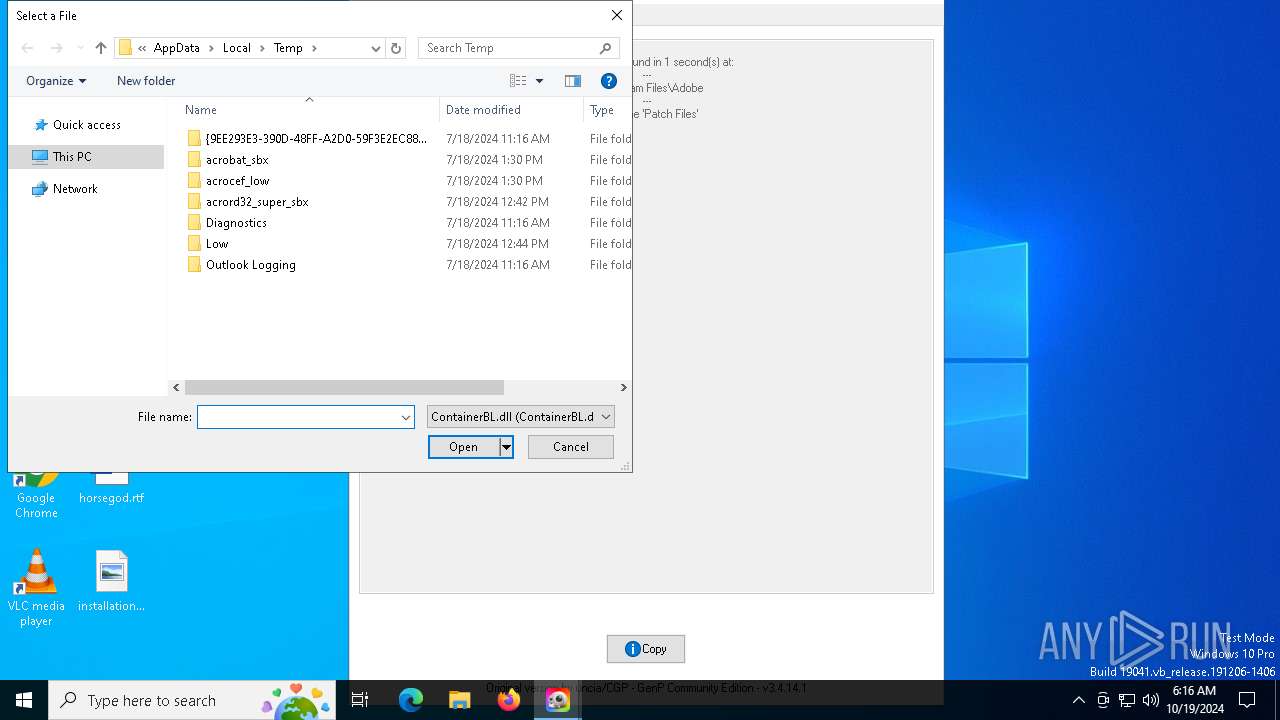
Create files in a temporary directory
- GenP-3.4.14.1.exe (PID: 6260)
The process uses AutoIt
- GenP-3.4.14.1.exe (PID: 2364)
Creates files in the program directory
- GenP-3.4.14.1.exe (PID: 2364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:08:02 21:32:52+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 734208 |
| InitializedDataSize: | 550400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2549c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.4.14.1 |
| ProductVersionNumber: | 3.4.14.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 3.4.14.1 |
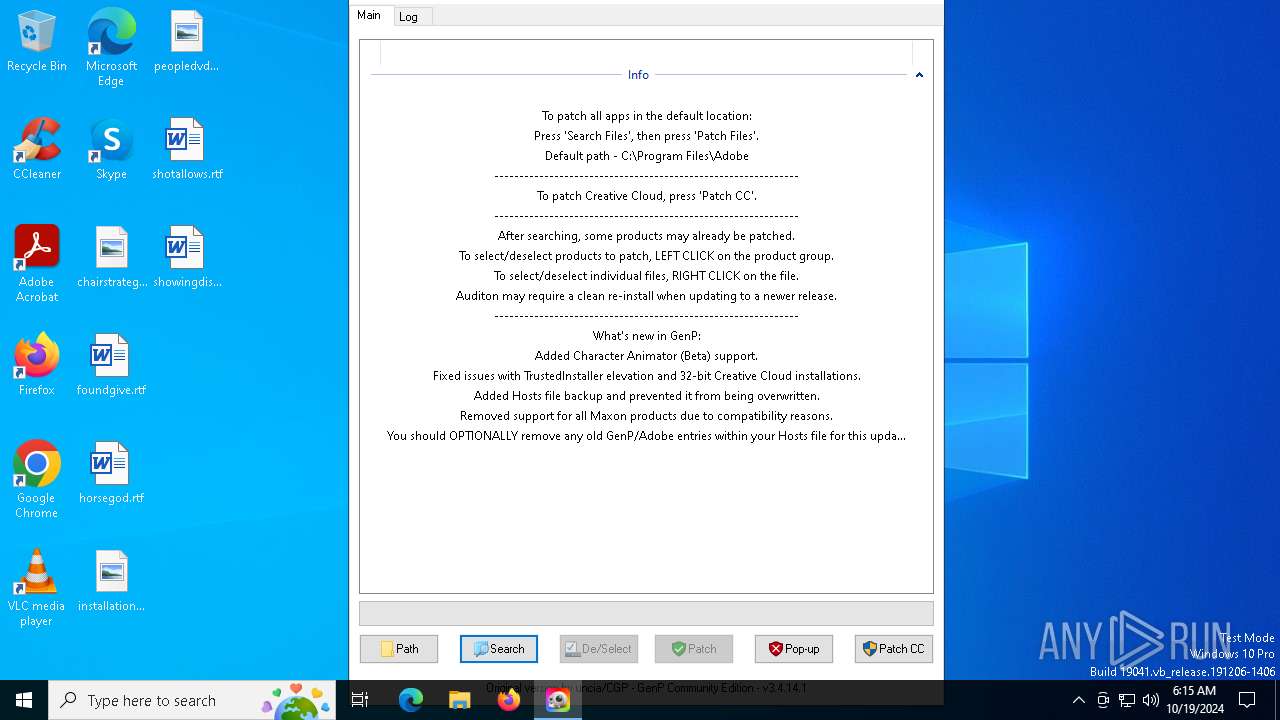
| Comments: | GenP v3.4.14.1 |
| FileDescription: | GenP v3.4.14.1 |
| ProductName: | GenP v3.4.14.1 |
| ProductVersion: | 3.4.14.1 |
| CompanyName: | GenP |
| LegalCopyright: | GenP |
| LegalTradeMarks: | GenP |
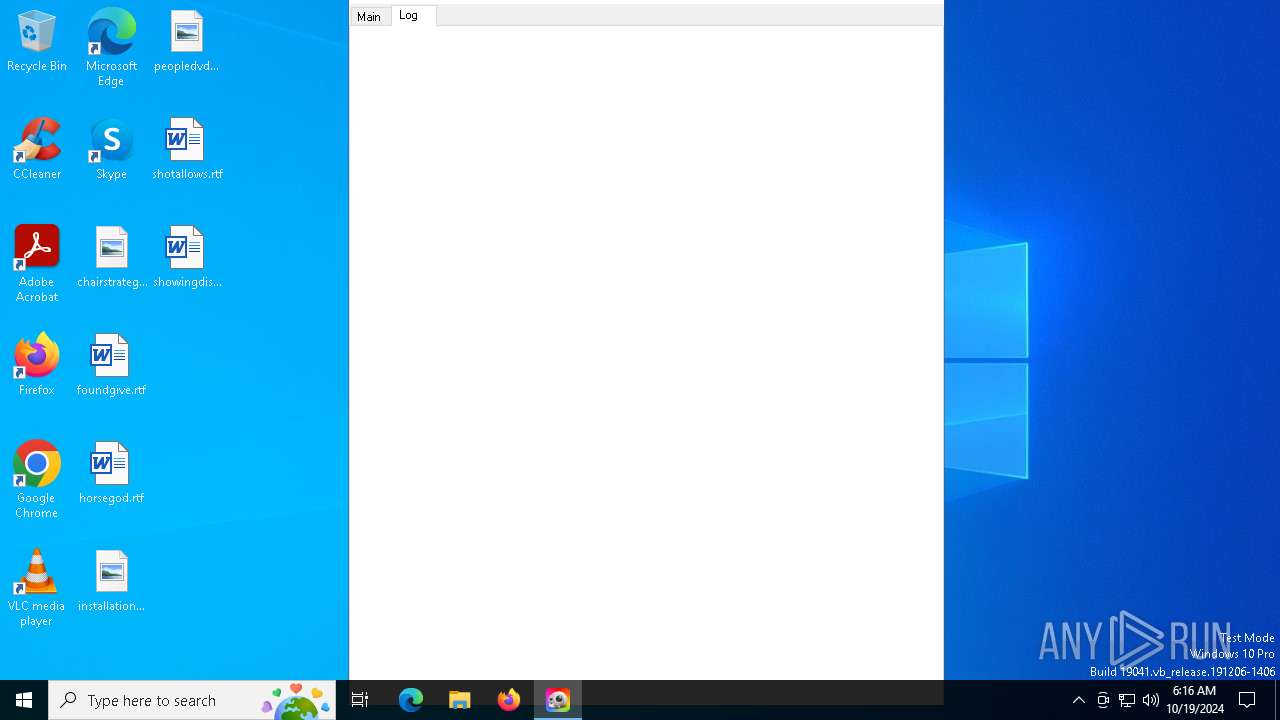
Total processes
121
Monitored processes
4
Malicious processes
4
Suspicious processes
0
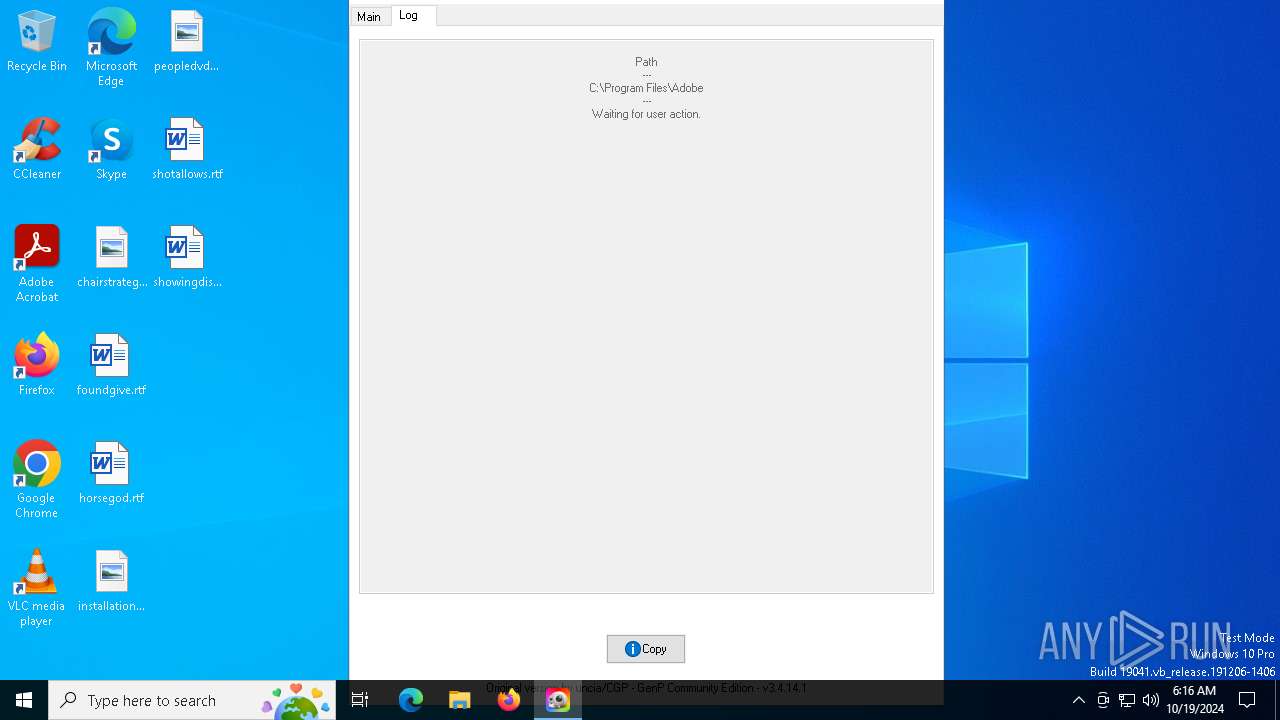
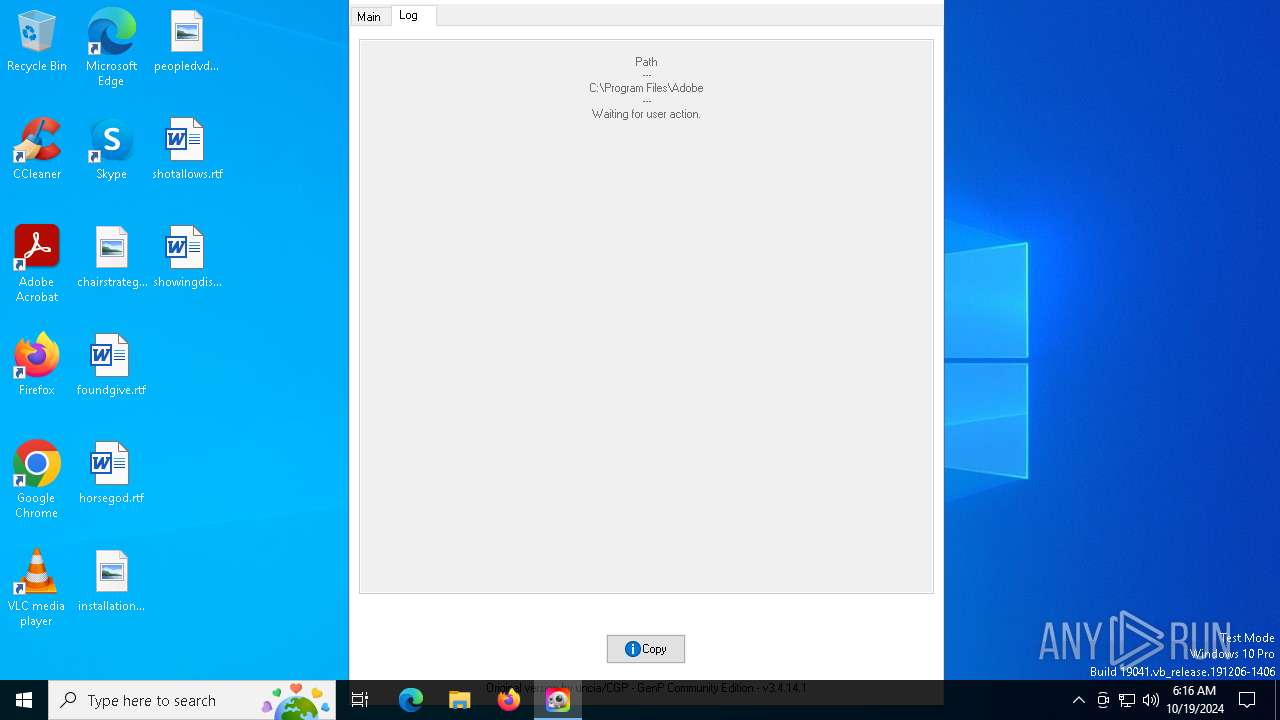
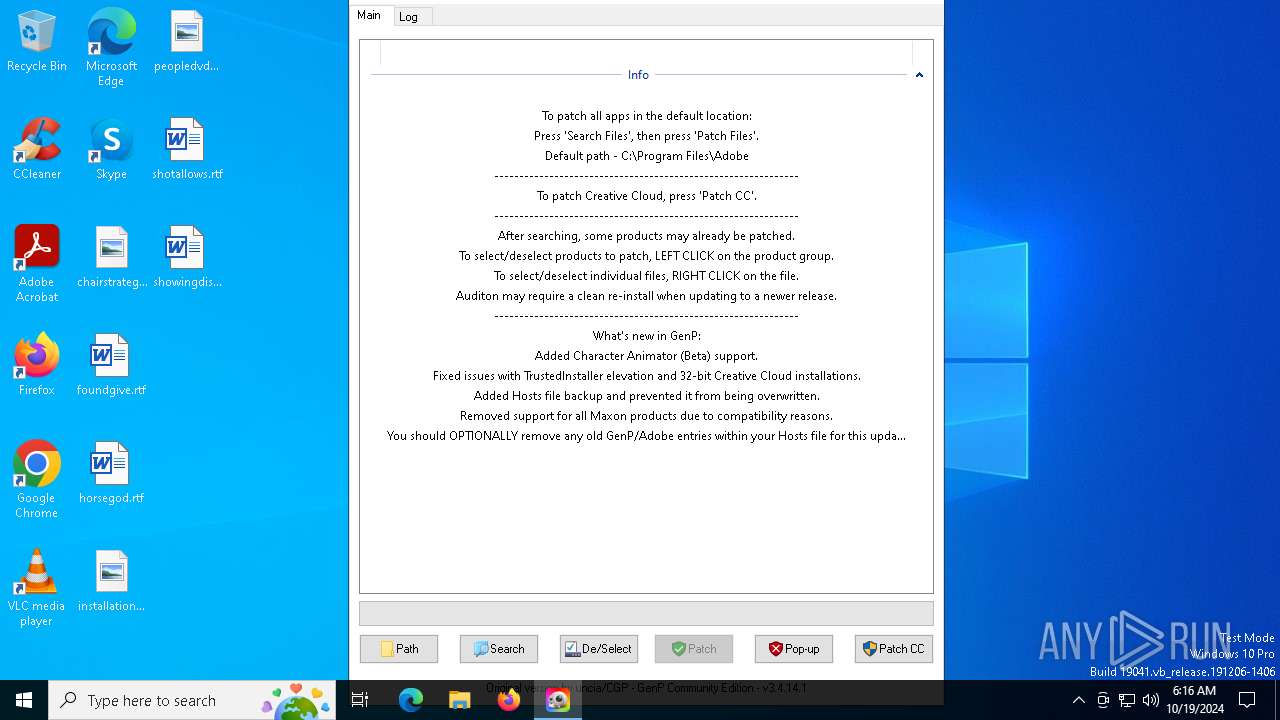
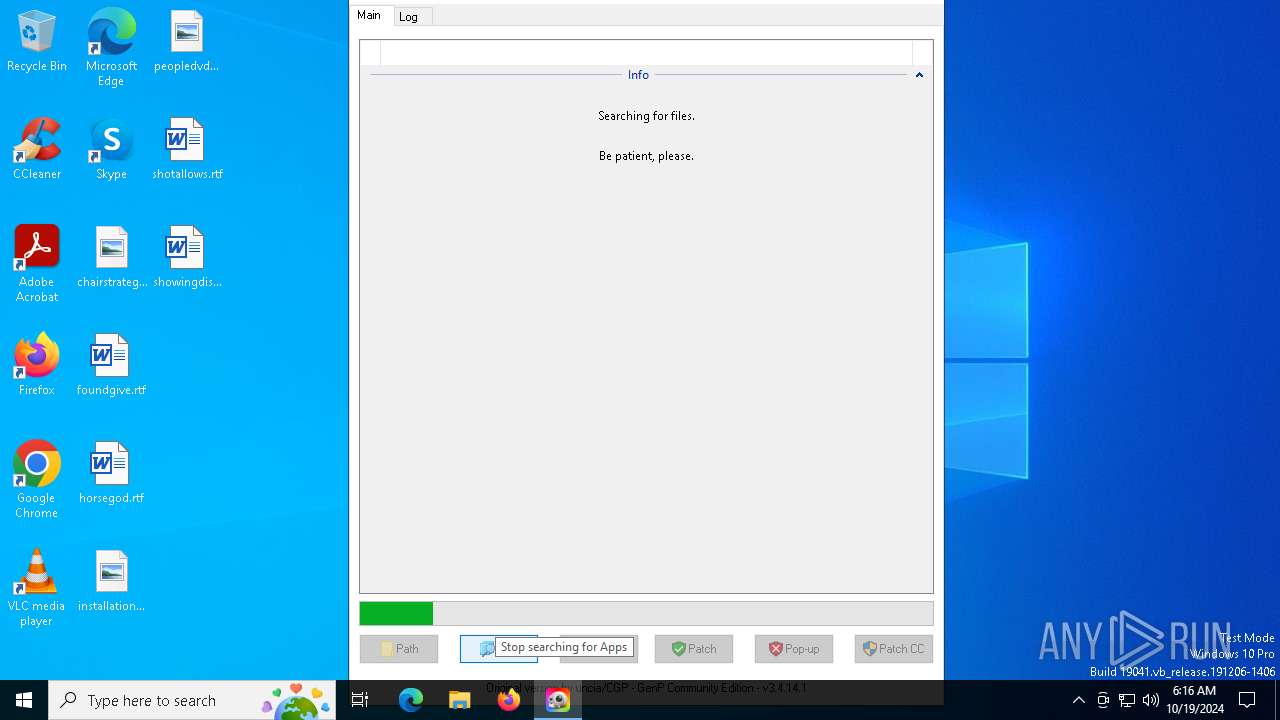
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2364 | "C:\Users\admin\AppData\Local\Temp\GenP-3.4.14.1.exe" | C:\Users\admin\AppData\Local\Temp\GenP-3.4.14.1.exe | NSudoLG.exe | ||||||||||||
User: SYSTEM Company: GenP Integrity Level: SYSTEM Description: GenP v3.4.14.1 Version: 3.4.14.1 Modules
| |||||||||||||||
| 5600 | C:\Users\admin\AppData\Local\Temp\NSudoLG.exe -U:T -P:E -M:S "C:\Users\admin\AppData\Local\Temp\GenP-3.4.14.1.exe" | C:\Users\admin\AppData\Local\Temp\NSudoLG.exe | — | GenP-3.4.14.1.exe | |||||||||||
User: admin Company: M2-Team Integrity Level: HIGH Description: NSudo Launcher Exit code: 0 Version: 8.2.0.0 Modules
| |||||||||||||||
| 6260 | "C:\Users\admin\AppData\Local\Temp\GenP-3.4.14.1.exe" ! | C:\Users\admin\AppData\Local\Temp\GenP-3.4.14.1.exe | GenP-3.4.14.1.exe | ||||||||||||
User: admin Company: GenP Integrity Level: HIGH Description: GenP v3.4.14.1 Exit code: 5600 Version: 3.4.14.1 Modules
| |||||||||||||||
| 6720 | "C:\Users\admin\AppData\Local\Temp\GenP-3.4.14.1.exe" | C:\Users\admin\AppData\Local\Temp\GenP-3.4.14.1.exe | — | explorer.exe | |||||||||||
User: admin Company: GenP Integrity Level: MEDIUM Description: GenP v3.4.14.1 Exit code: 0 Version: 3.4.14.1 Modules
| |||||||||||||||
Total events
2 700
Read events
2 636
Write events
50
Delete events
14
Modification events
| (PID) Process: | (2364) GenP-3.4.14.1.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (2364) GenP-3.4.14.1.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00470065006E0050002D0033002E0034002E00310034002E0031002E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070000000 | |||
| (PID) Process: | (2364) GenP-3.4.14.1.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (2364) GenP-3.4.14.1.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (2364) GenP-3.4.14.1.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (2364) GenP-3.4.14.1.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (2364) GenP-3.4.14.1.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {F02C1A0D-BE21-4350-88B0-7367FC96EF3C} {000214E6-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000007FB5625AEE21DB01 | |||
| (PID) Process: | (2364) GenP-3.4.14.1.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {D9144DCD-E998-4ECA-AB6A-DCD83CCBA16D} {0C6C4200-C589-11D0-999A-00C04FD655E1} 0xFFFF |
Value: 01000000000000005F19655AEE21DB01 | |||
| (PID) Process: | (2364) GenP-3.4.14.1.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {4E77131D-3629-431C-9818-C5679DC83E81} {0C6C4200-C589-11D0-999A-00C04FD655E1} 0xFFFF |
Value: 0100000000000000E77D675AEE21DB01 | |||
| (PID) Process: | (2364) GenP-3.4.14.1.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\CIDOpen\Modules\GlobalSettings\ProperTreeModuleInner |
| Operation: | write | Name: | ProperTreeModuleInner |
Value: 9C000000980000003153505305D5CDD59C2E1B10939708002B2CF9AE3B0000002A000000004E0061007600500061006E0065005F004300460044005F0046006900720073007400520075006E0000000B000000000000004100000030000000004E0061007600500061006E0065005F00530068006F0077004C00690062007200610072007900500061006E00650000000B000000FFFF00000000000000000000 | |||
Executable files
3
Suspicious files
5
Text files
0
Unknown types
0
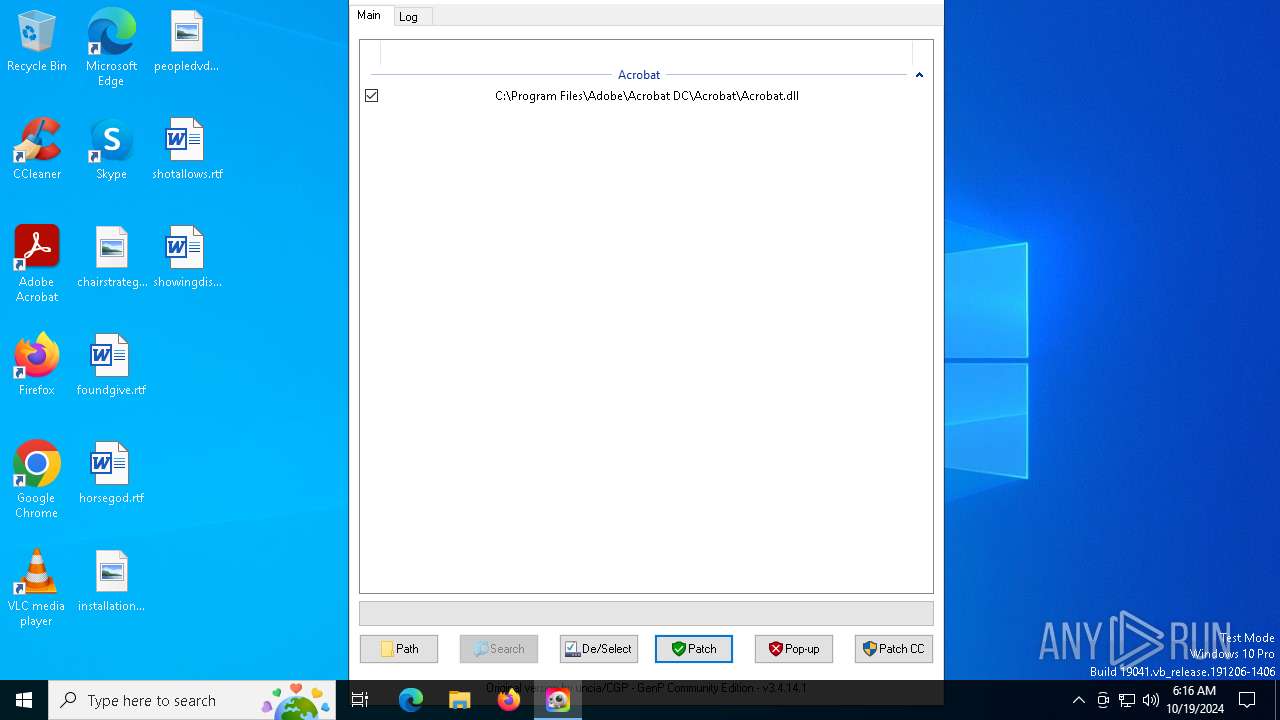
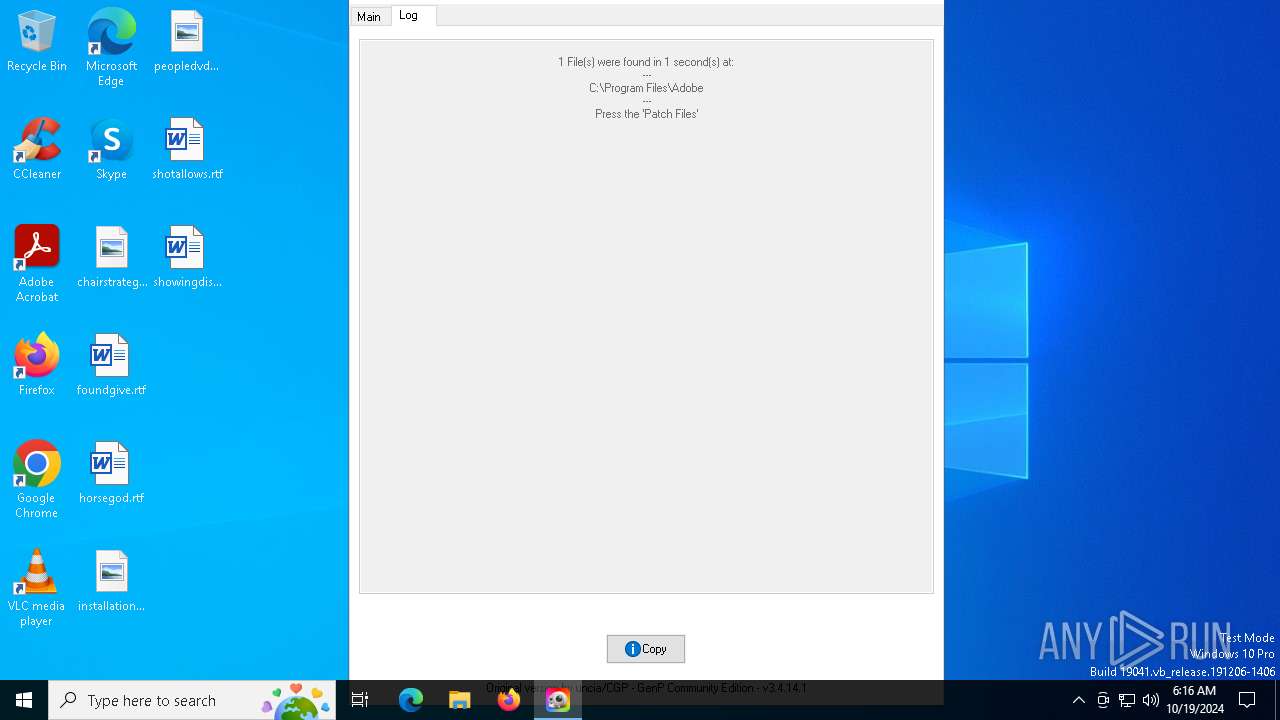
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
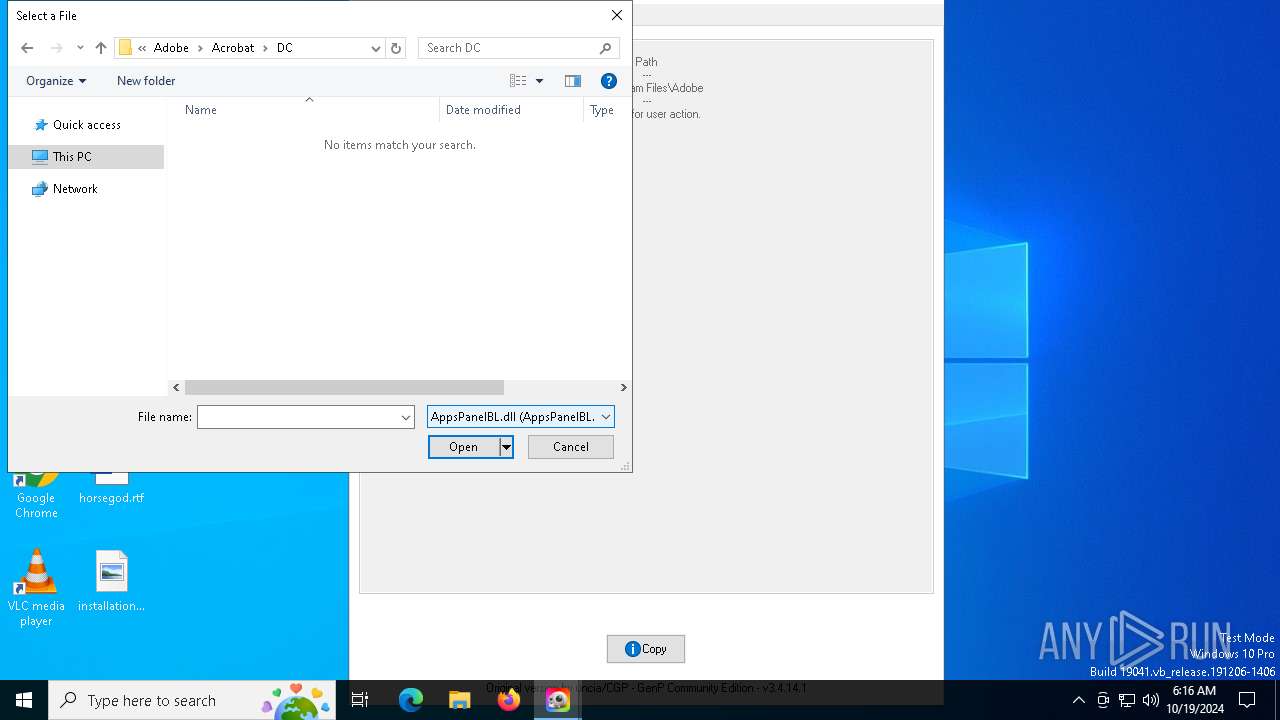
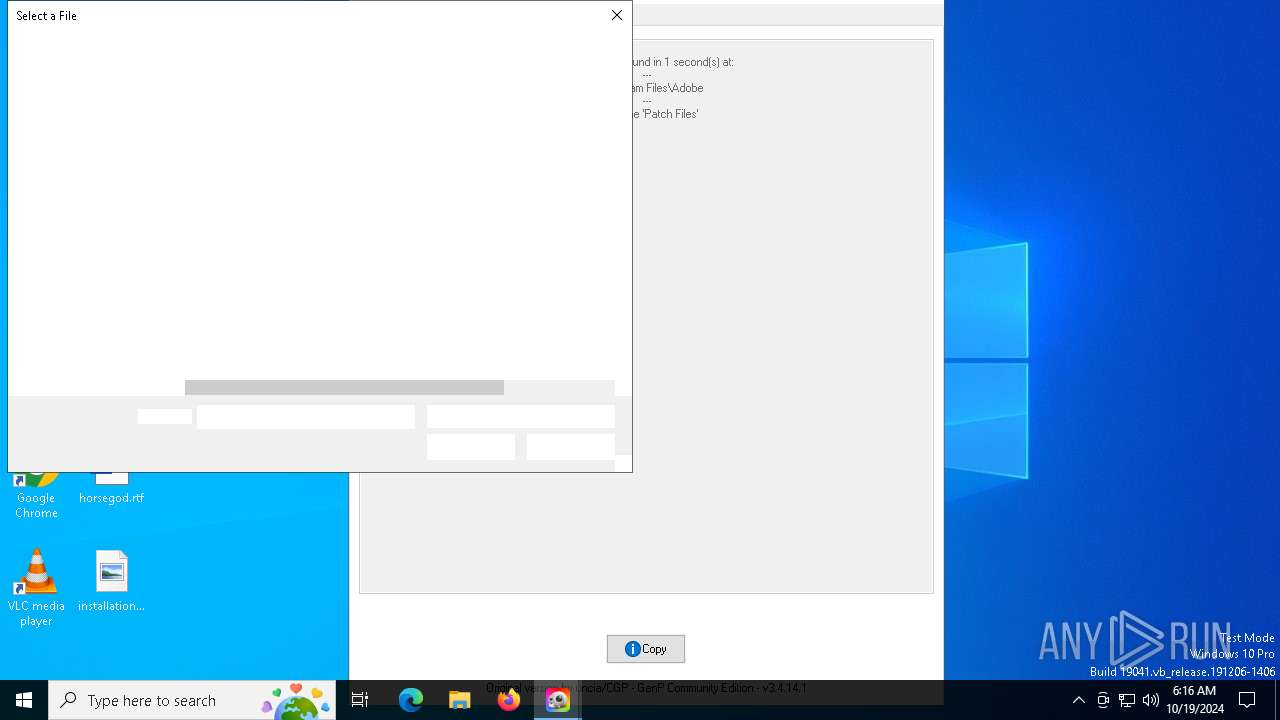
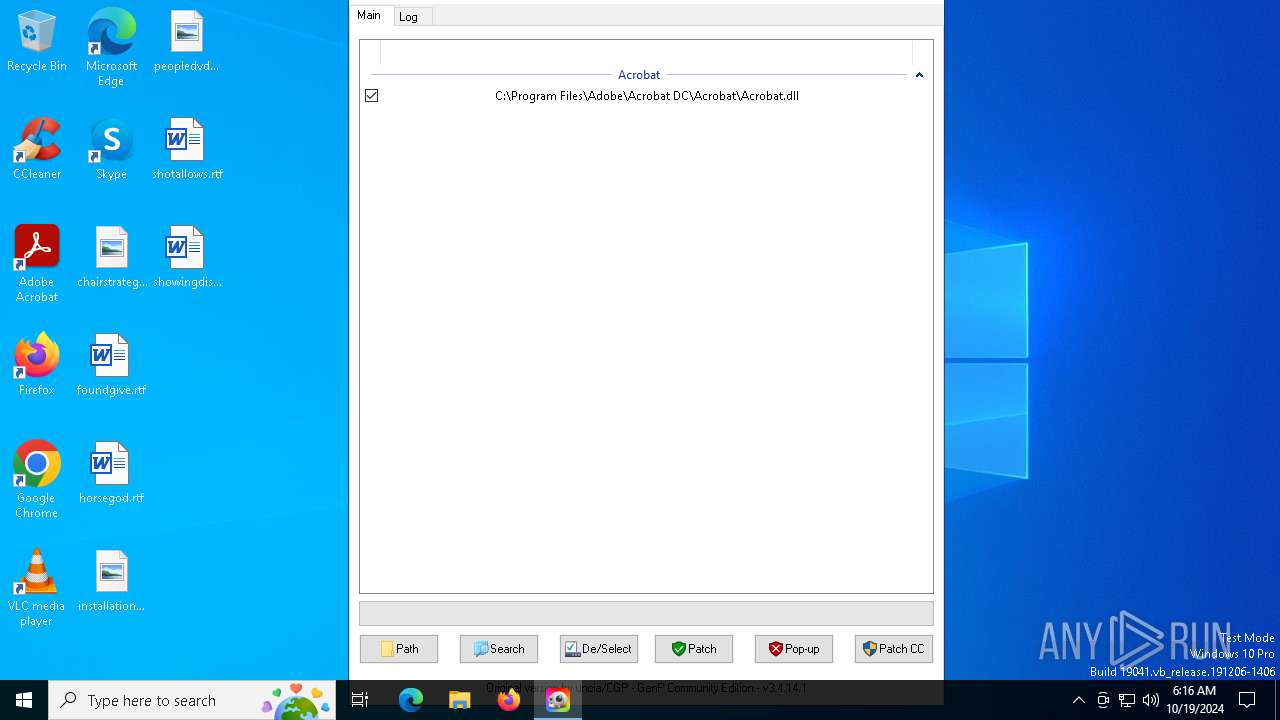
| 2364 | GenP-3.4.14.1.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll.bak | — | |
MD5:— | SHA256:— | |||
| 2364 | GenP-3.4.14.1.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll | — | |
MD5:— | SHA256:— | |||
| 6260 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\config.ini | text | |
MD5:ADD427035968BC6F8BCDF0C5D7580495 | SHA256:66232A4D8677CD50612EAEBC664B2F2F3556B497D5BF8657967C259EF4723B68 | |||
| 6260 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\autB84C.tmp | binary | |
MD5:C8974BCA42D238986F542ECE4EBA859A | SHA256:1AE68F2E79AA2072FFD717E58B162CABF31785D341A398FBF3D9C67BB07332F1 | |||
| 2364 | GenP-3.4.14.1.exe | C:\Windows\Temp\NSudoLG.exe | executable | |
MD5:7AACFD85B8DFF0AA6867BEDE82CFD147 | SHA256:871E4F28FE39BCAD8D295AE46E148BE458778C0195ED660B7DB18EB595D00BD8 | |||
| 6260 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\NSudoLG.exe | executable | |
MD5:7AACFD85B8DFF0AA6867BEDE82CFD147 | SHA256:871E4F28FE39BCAD8D295AE46E148BE458778C0195ED660B7DB18EB595D00BD8 | |||
| 2364 | GenP-3.4.14.1.exe | C:\Windows\Temp\autD059.tmp | binary | |
MD5:6F040B192B47D1D0860045AA30C102A0 | SHA256:A85D89E380CBF4929EE5B6E7D91BE71AF1C3A727A91CF30AFFB414B98E912180 | |||
| 6260 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\autB85D.tmp | binary | |
MD5:6F040B192B47D1D0860045AA30C102A0 | SHA256:A85D89E380CBF4929EE5B6E7D91BE71AF1C3A727A91CF30AFFB414B98E912180 | |||
| 2364 | GenP-3.4.14.1.exe | C:\Windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\Explorer\iconcache_idx.db | binary | |
MD5:546946FC802A2BFC395813150D9C7494 | SHA256:4354D2D9F2E51890C5AB4D842E0572F61728D40FE865D8FB3B28059FF90F0BC5 | |||
| 2364 | GenP-3.4.14.1.exe | C:\Windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\Explorer\iconcache_16.db | binary | |
MD5:14F4F76B352D3C1D2E3430B71B053926 | SHA256:980982E3051A6BF460C09AB9108D758375F25ED9AEA8D0212277A03383C5B2D2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
23
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |