| download: | policies2.vbs.vbs |
| Full analysis: | https://app.any.run/tasks/2fe72236-ec0d-49f7-86c9-cf8a22494bd5 |
| Verdict: | Malicious activity |
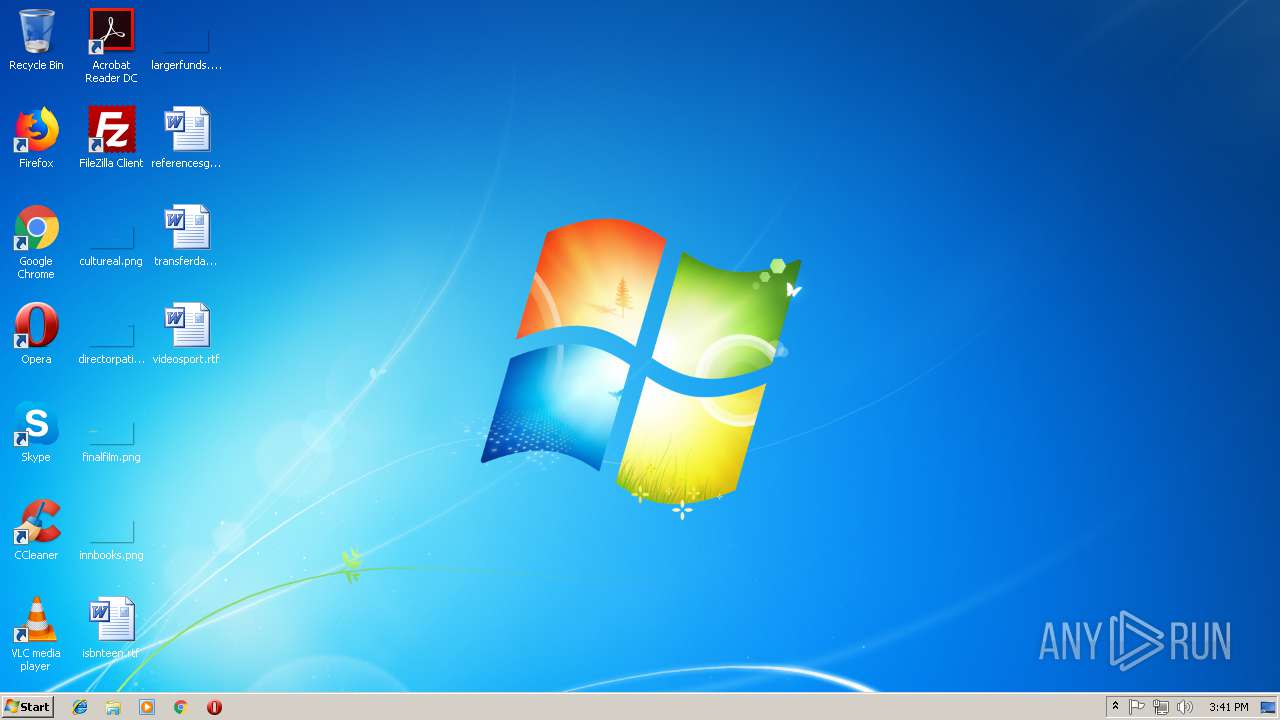
| Analysis date: | November 14, 2018, 15:41:24 |
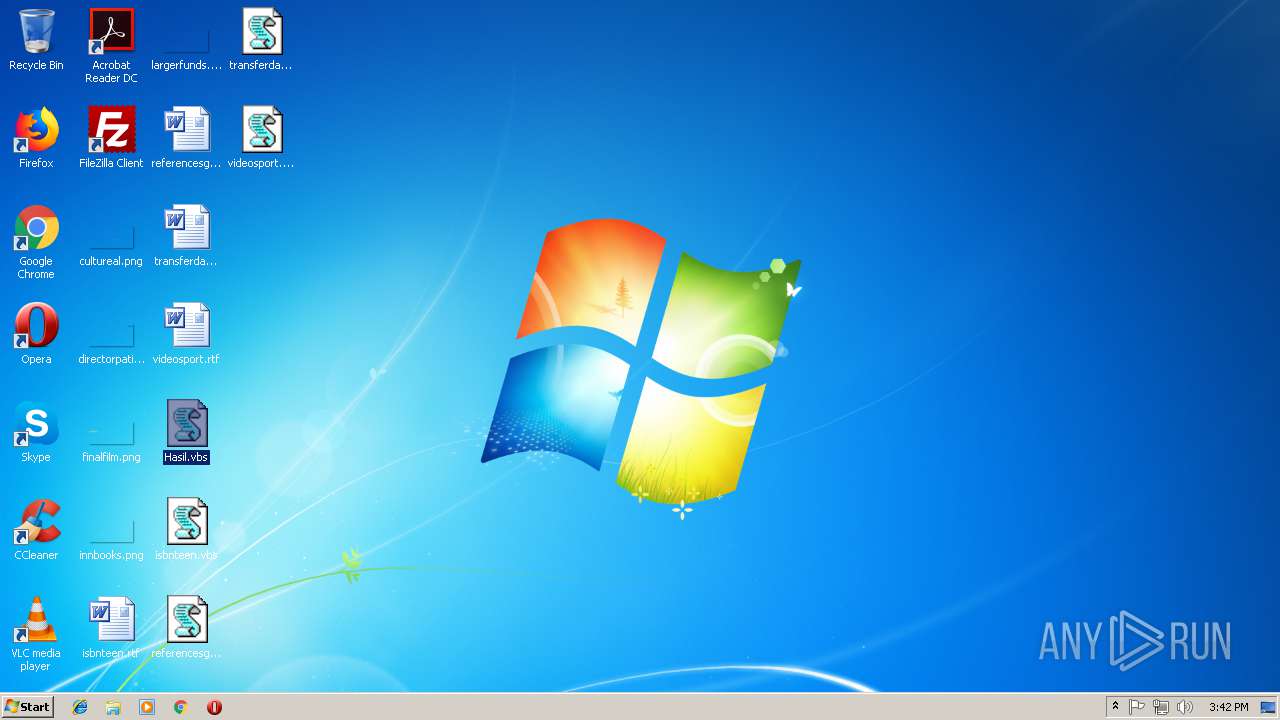
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 2324144699FB795AEC69535D973AB1B6 |
| SHA1: | 4B5A2205C2965DF47A1A627BB7272DCFA72B5747 |
| SHA256: | 3BC7C41336AA27CB1B5B49D7976340209A792BC1FF1C0996AA7BB2E82FFA4E7D |
| SSDEEP: | 96:JA7kcjbsVcAdGX4AAfCABoZZAh0SbAh0S/Ah0SwkAR7sQWAGsRVRhJ4EzrqtdtjG:OkEbsNGXsfQSzSnS8jA0nrkz/Y |
MALICIOUS
Task Manager has been disabled (taskmgr)
- WScript.exe (PID: 2480)
Changes the autorun value in the registry
- WScript.exe (PID: 2480)
SUSPICIOUS
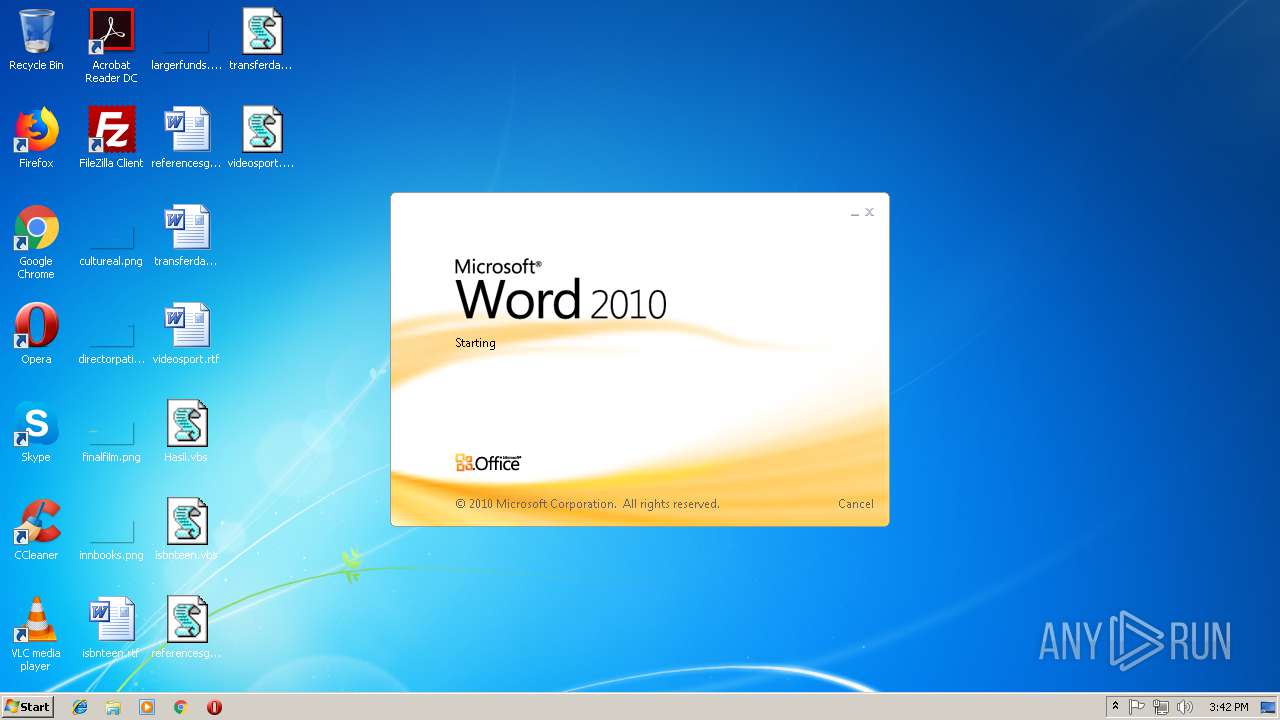
Starts Microsoft Office Application
- WScript.exe (PID: 2480)
Modifies the open verb of a shell class
- WScript.exe (PID: 2480)
Creates files in the user directory
- WScript.exe (PID: 2480)
Creates files in the program directory
- WScript.exe (PID: 2480)
INFO
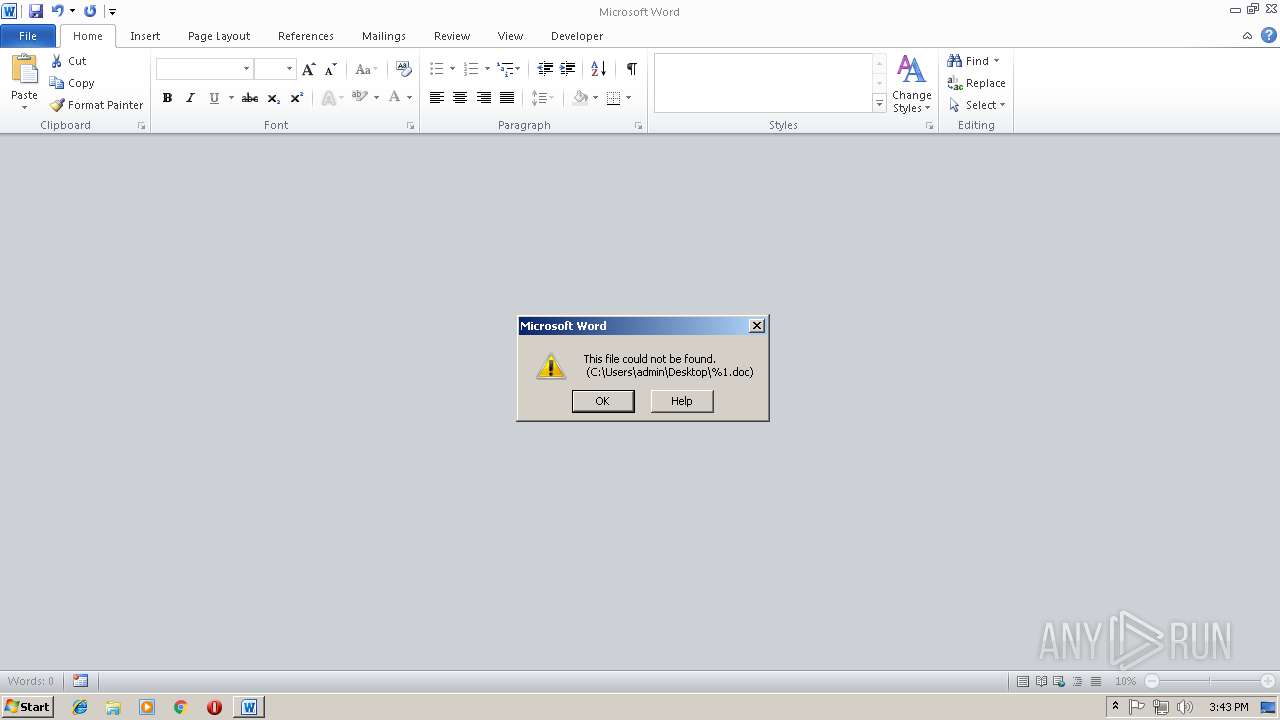
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 944)
Creates files in the user directory
- WINWORD.EXE (PID: 944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
32
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
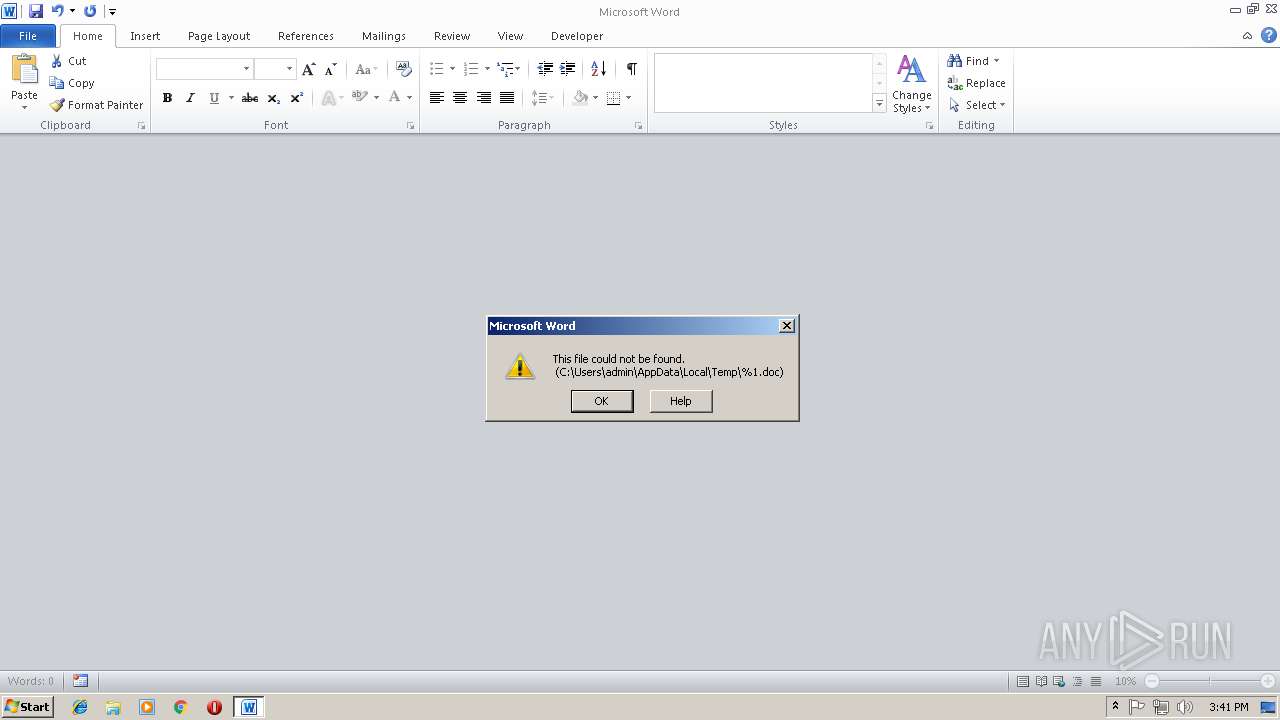
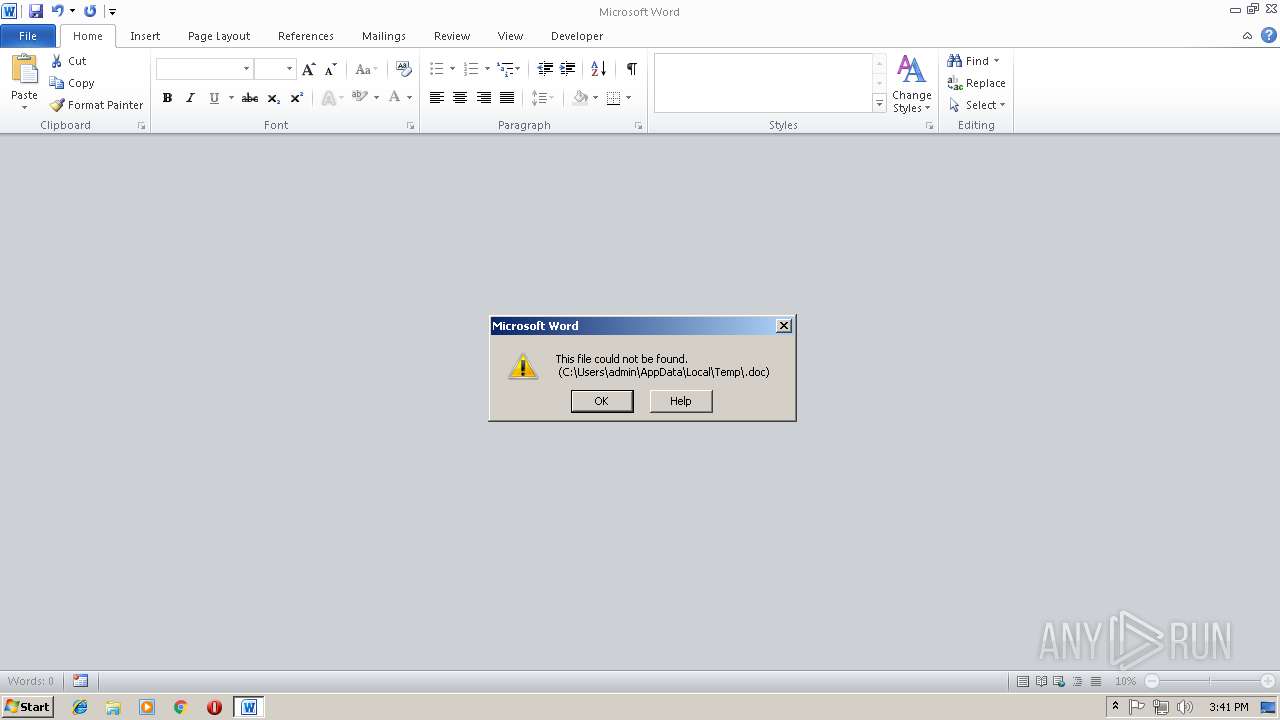
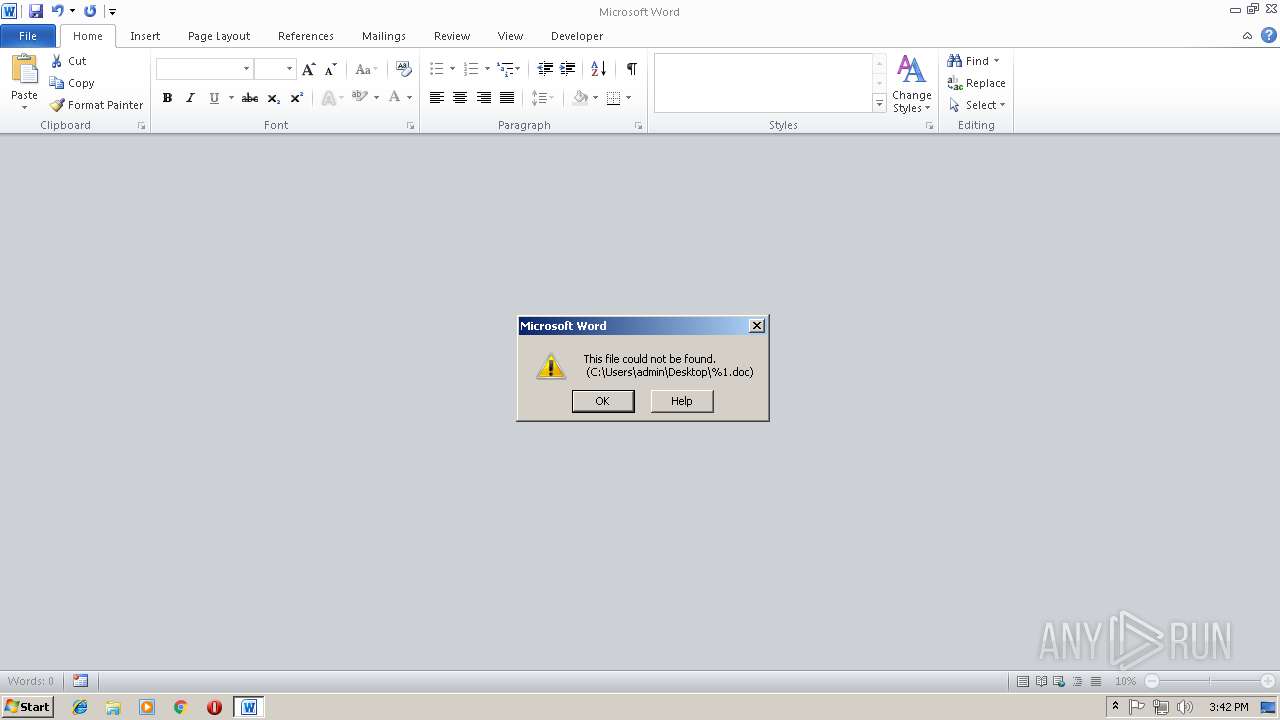
| 944 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "%1" "" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2480 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\policies2.vbs.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
749
Read events
704
Write events
38
Delete events
7
Modification events
| (PID) Process: | (2480) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2480) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2480) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile |
| Operation: | write | Name: | |
Value: Microsoft Word 97 - 2003 Document | |||
| (PID) Process: | (2480) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Windows\Installer\{90140000-003D-0000-0000-0000000FF1CE}\wordicon.exe,1 | |||
| (PID) Process: | (2480) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile |
| Operation: | write | Name: | NeverShowExt |
Value: | |||
| (PID) Process: | (2480) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile |
| Operation: | write | Name: | FriendlyTypeName |
Value: Microsoft Word 97 - 2003 Document | |||
| (PID) Process: | (2480) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\inffile\shell\Install\command |
| Operation: | write | Name: | |
Value: logoff.exe | |||
| (PID) Process: | (2480) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\regfile\shell\open\command |
| Operation: | write | Name: | |
Value: logoff.exe | |||
| (PID) Process: | (2480) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile\Shell\Edit\Command |
| Operation: | write | Name: | |
Value: logoff.exe | |||
| (PID) Process: | (2480) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | Hidden |
Value: 0 | |||
Executable files
0
Suspicious files
70
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR92E5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{0BA39D77-1106-4F42-AE04-8BCC735F1E33}.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | WScript.exe | C:\Users\admin\Favorites\vacbedlover.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2480 | WScript.exe | C:\Users\admin\AppData\Roaming\vacbedlover.vbs | binary | |
MD5:— | SHA256:— | |||
| 2480 | WScript.exe | C:\Program Files\Google\CrashReports\Hasil.vbs | binary | |
MD5:— | SHA256:— | |||
| 2480 | WScript.exe | C:\ProgramData\Money.vbs | binary | |
MD5:— | SHA256:— | |||
| 2480 | WScript.exe | C:\ProgramData\Adobe\Money.vbs | binary | |
MD5:— | SHA256:— | |||
| 2480 | WScript.exe | C:\ProgramData\Adobe\Setup\Hasil.vbs | binary | |
MD5:— | SHA256:— | |||
| 2480 | WScript.exe | C:\ProgramData\Adobe\ARM\Hasil.vbs | binary | |
MD5:— | SHA256:— | |||
| 944 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report