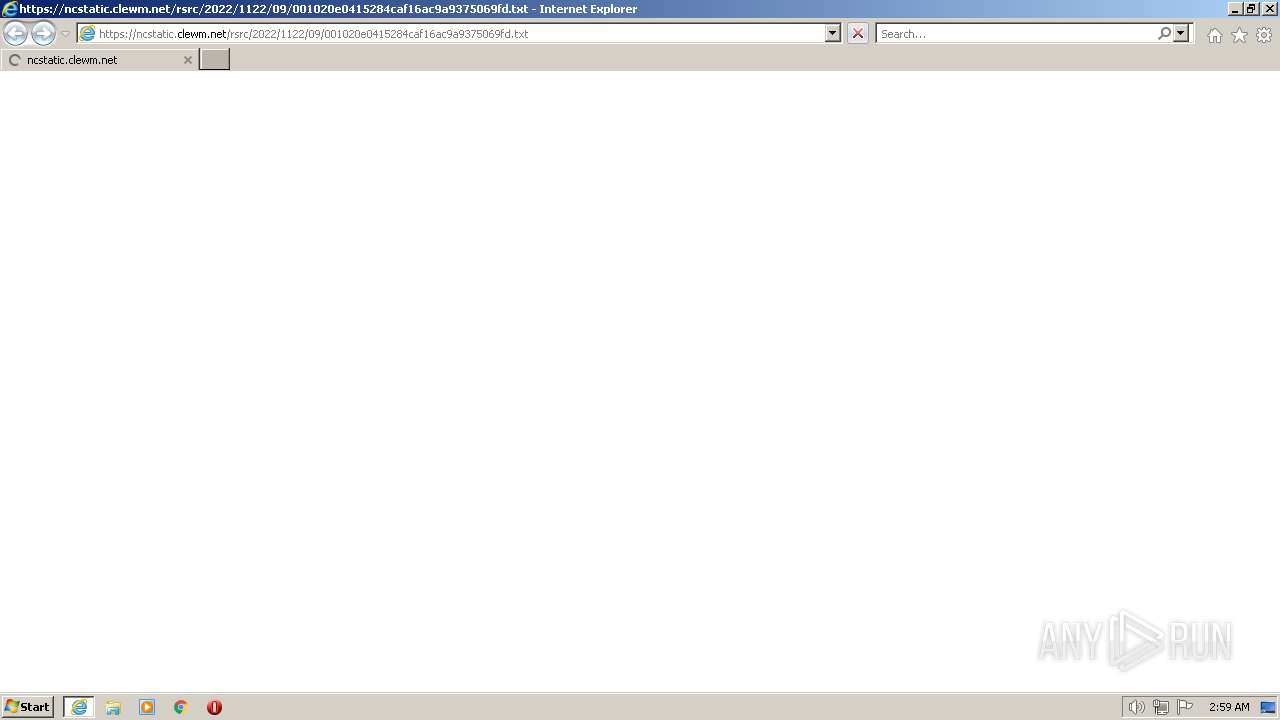
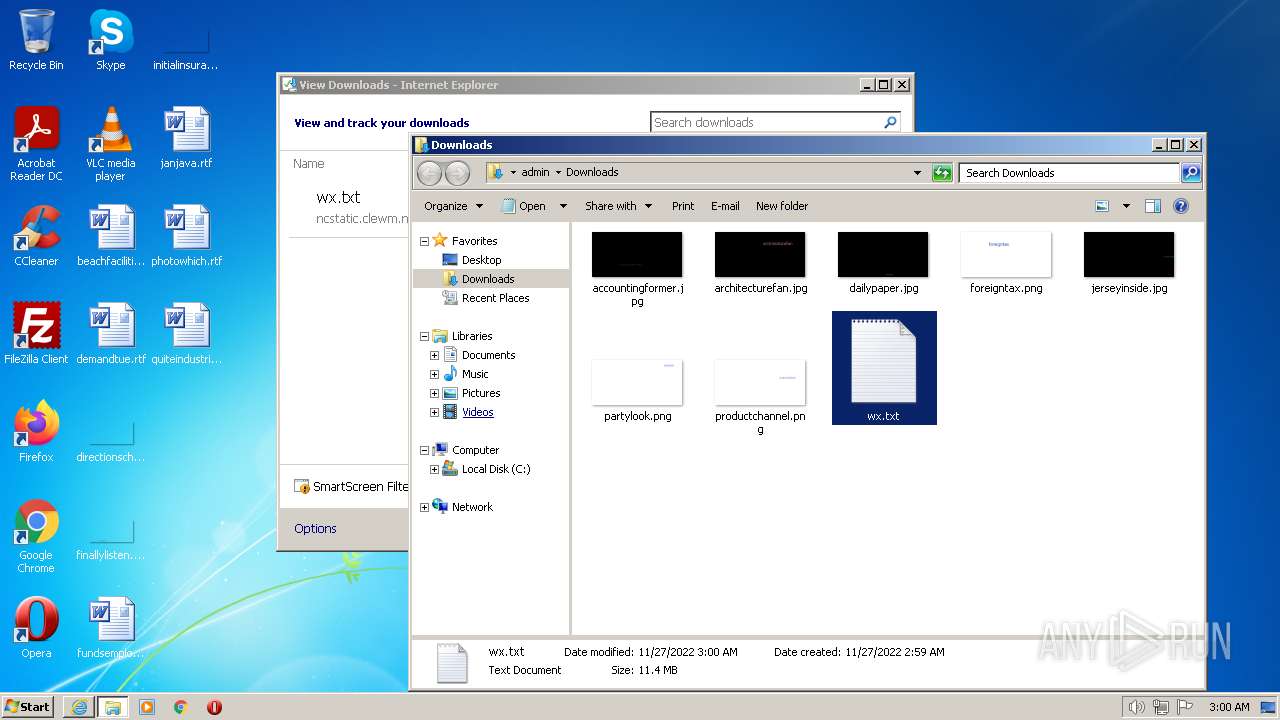
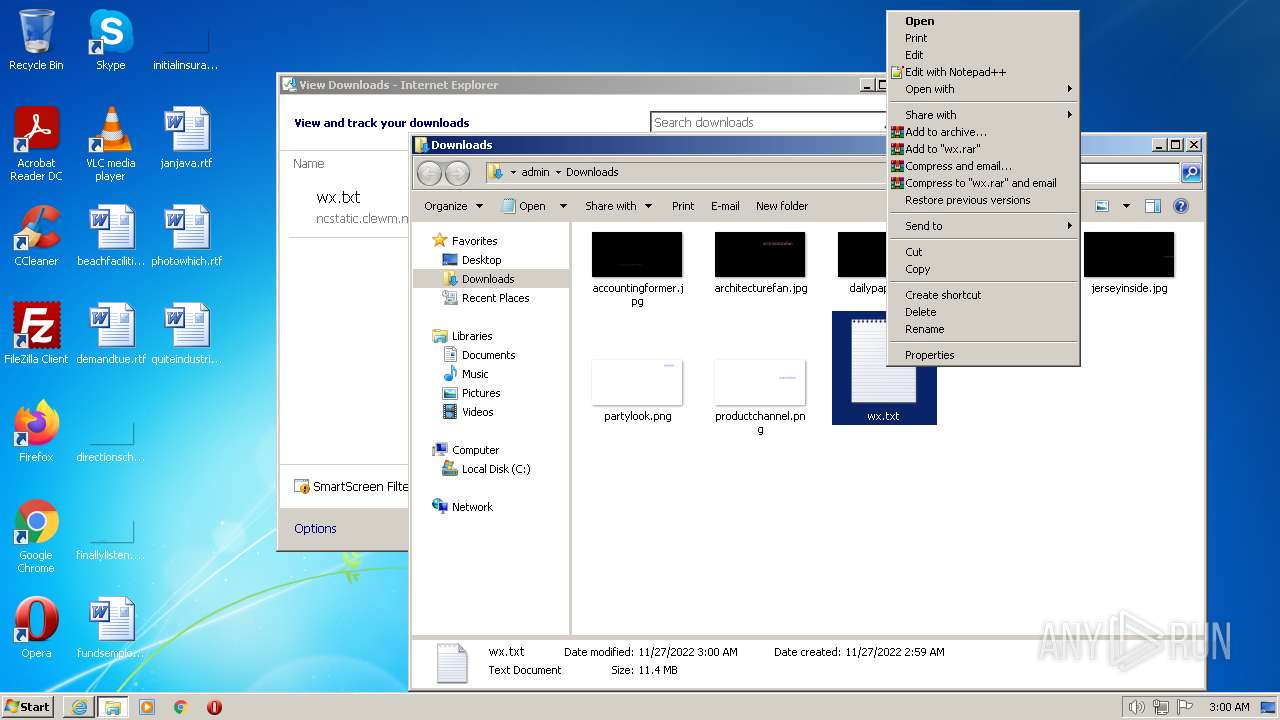
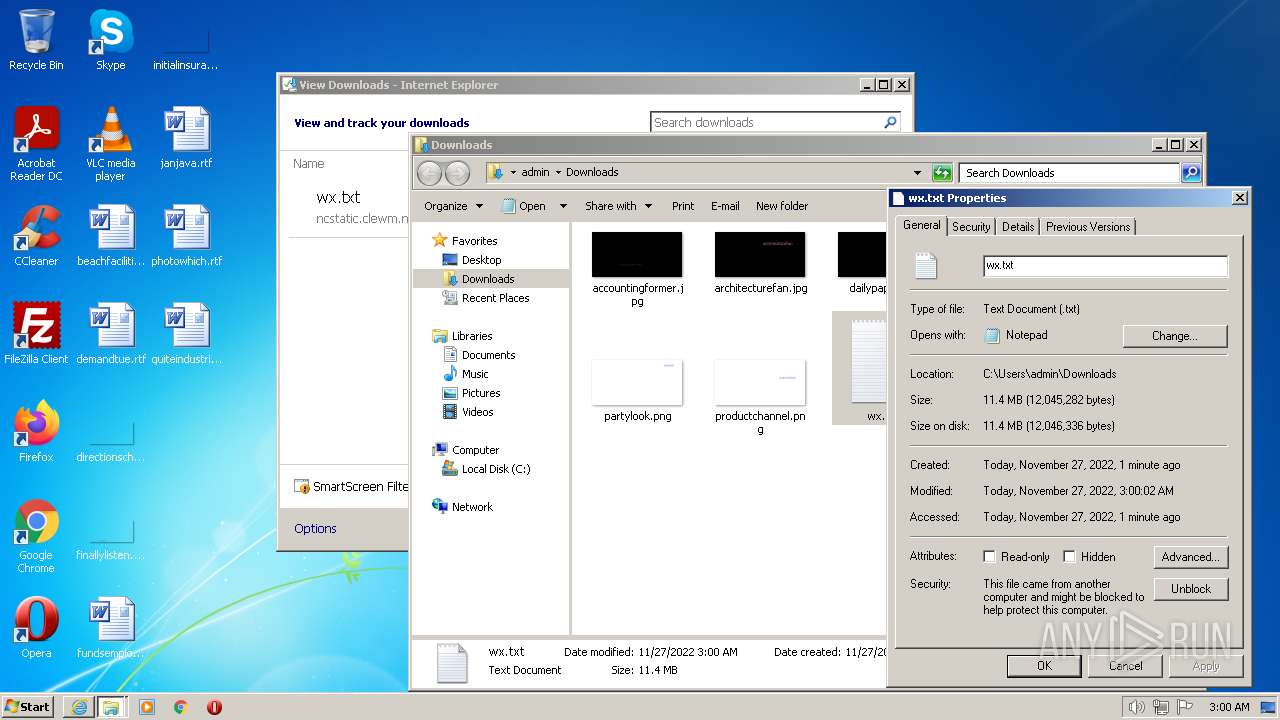
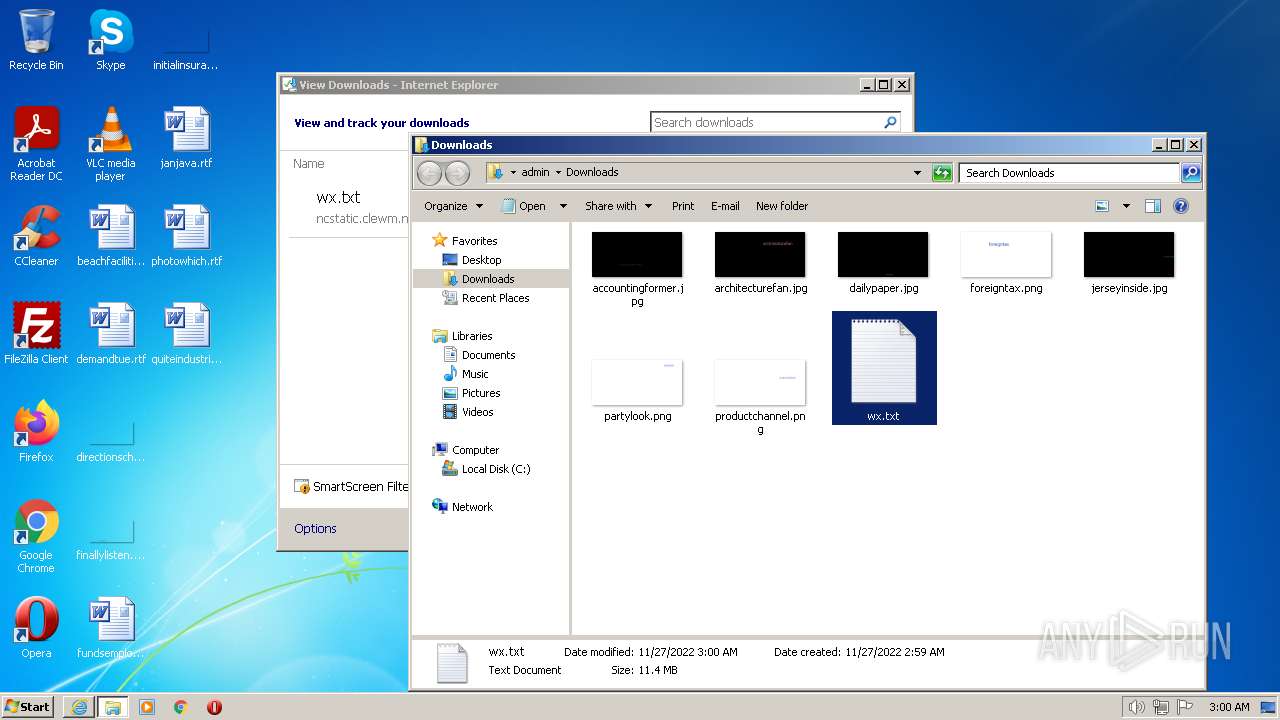
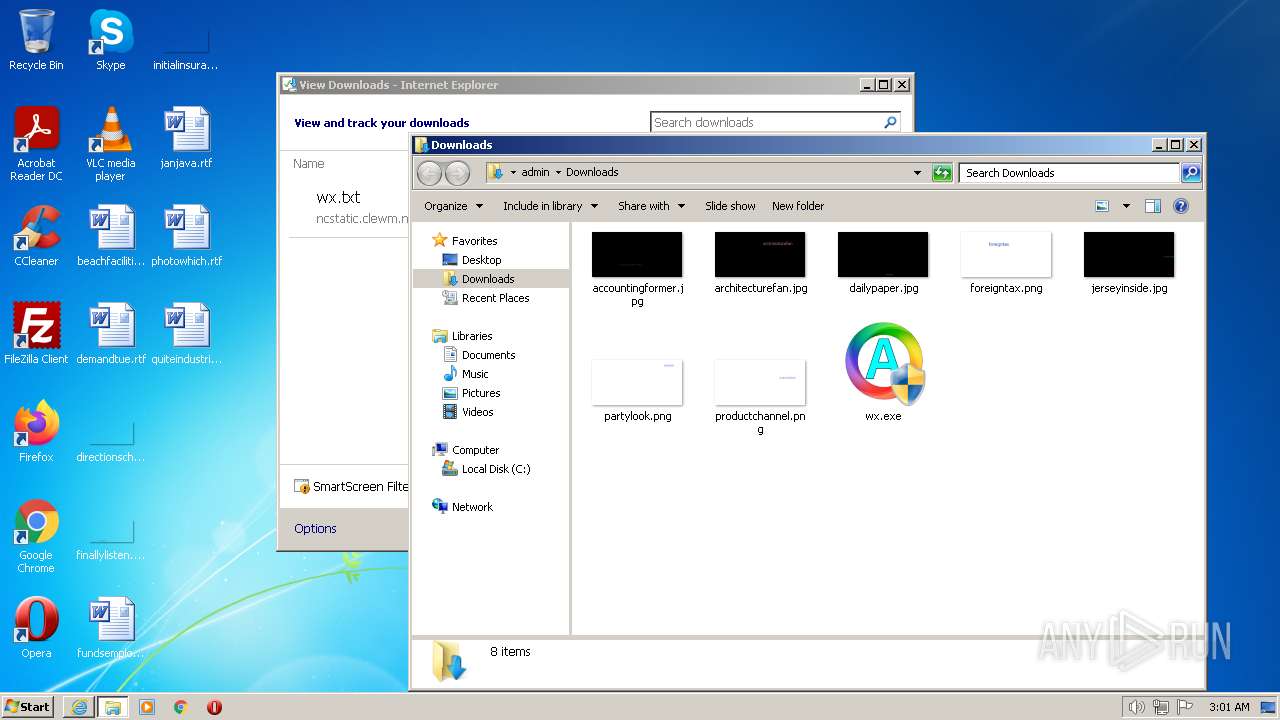
| URL: | https://ncstatic.clewm.net/rsrc/2022/1122/09/001020e0415284caf16ac9a9375069fd.txt |
| Full analysis: | https://app.any.run/tasks/f74c76d2-100b-4f3d-96db-f3b8f9f5d38e |
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2022, 02:59:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3FD63E0F0299CCAF630CB0BAEC4FF68A |
| SHA1: | 0078D4CD2F1049DA0835528B295250E248C26DFF |
| SHA256: | 3BB71976C3EAF55877E819DED874F201C200DFBE271E4E542D128430C9FAB034 |
| SSDEEP: | 3:N8R4MceG0gMSHK26SAVRUQXdRTDUTEG1jCdx:2E30gMeK0AvRTDLdx |
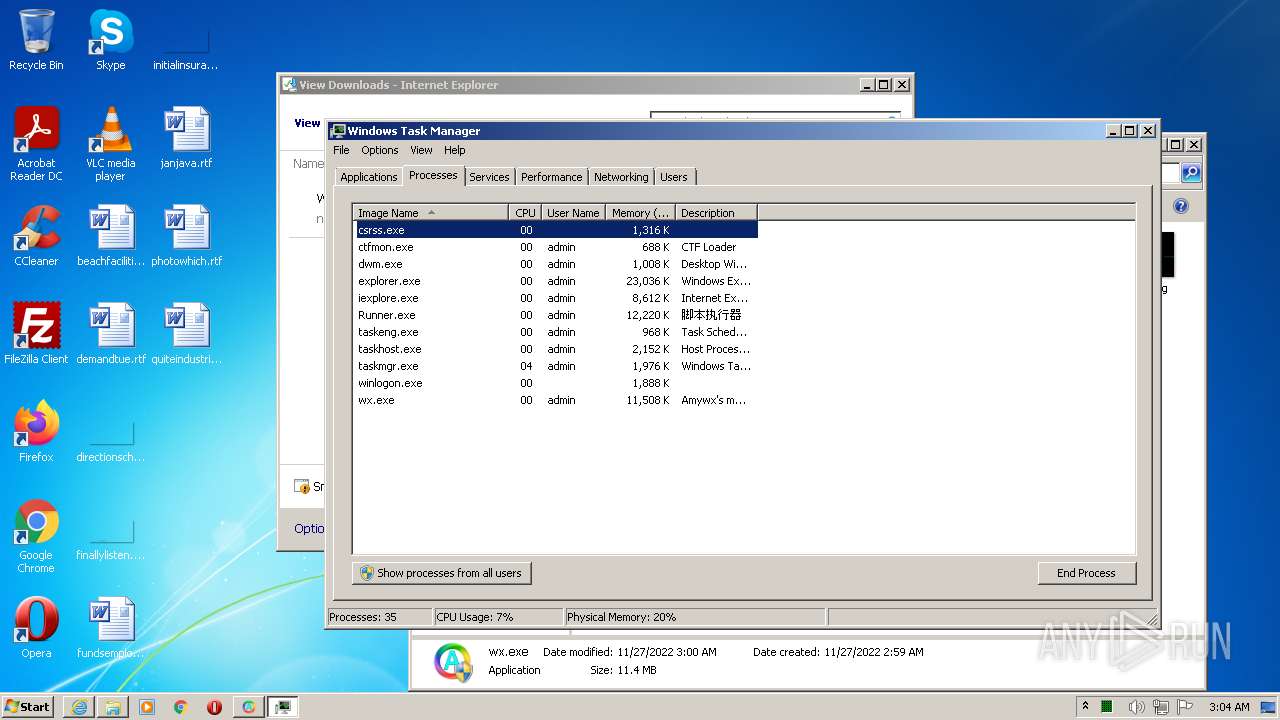
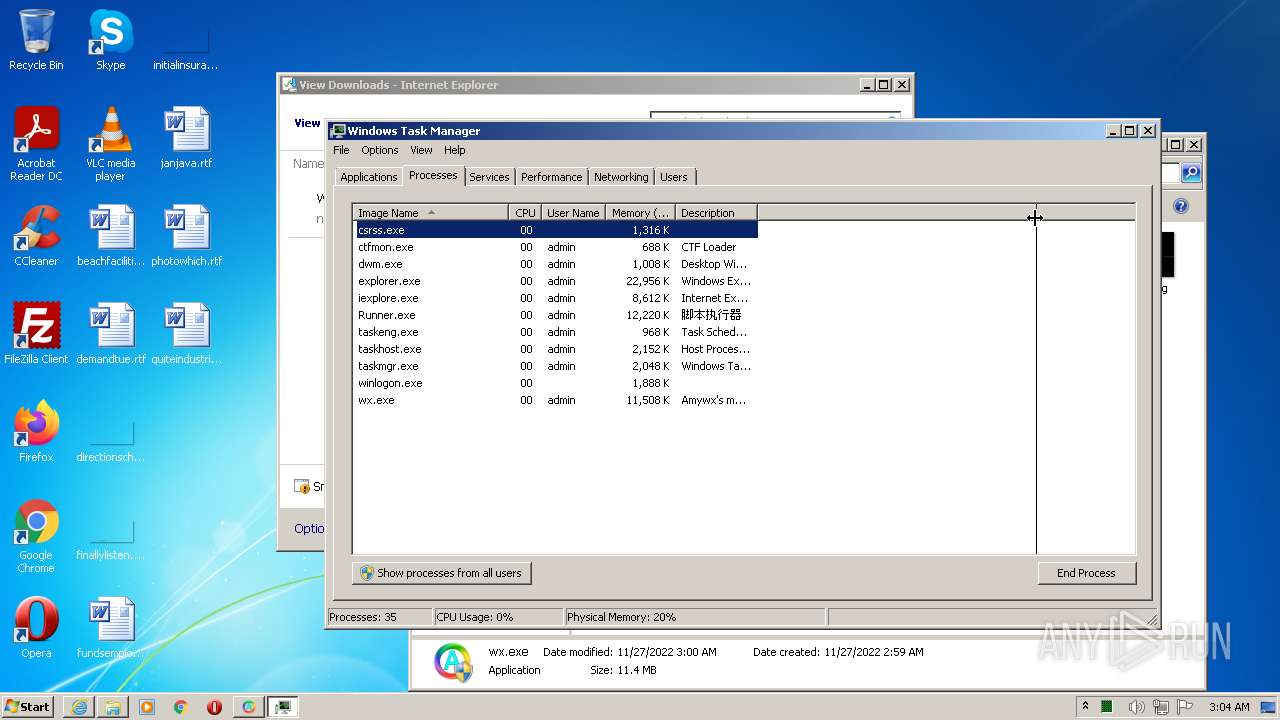
MALICIOUS
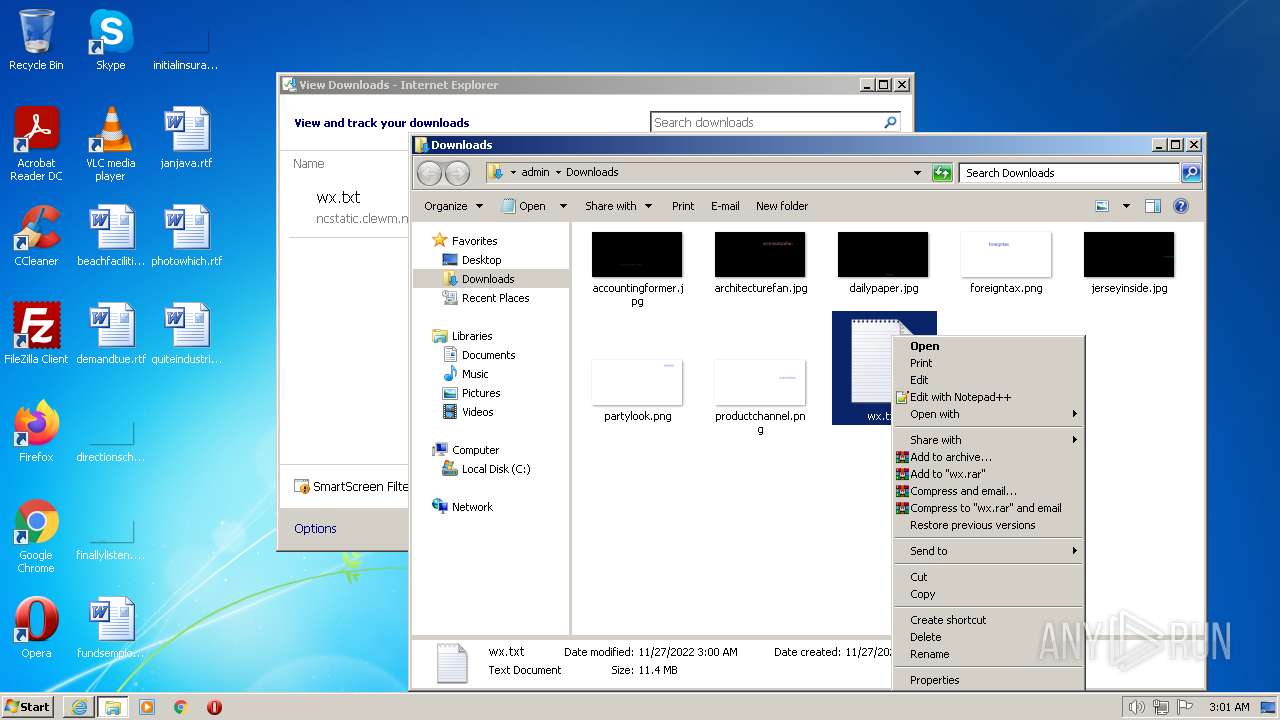
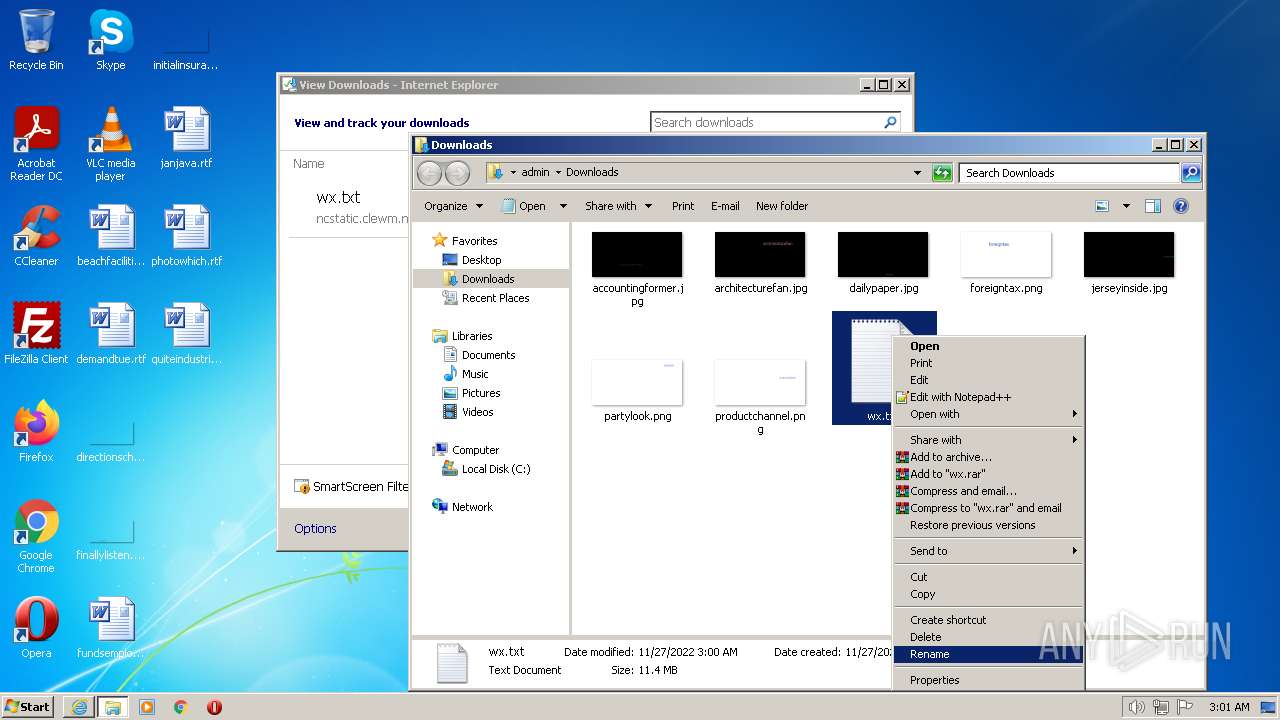
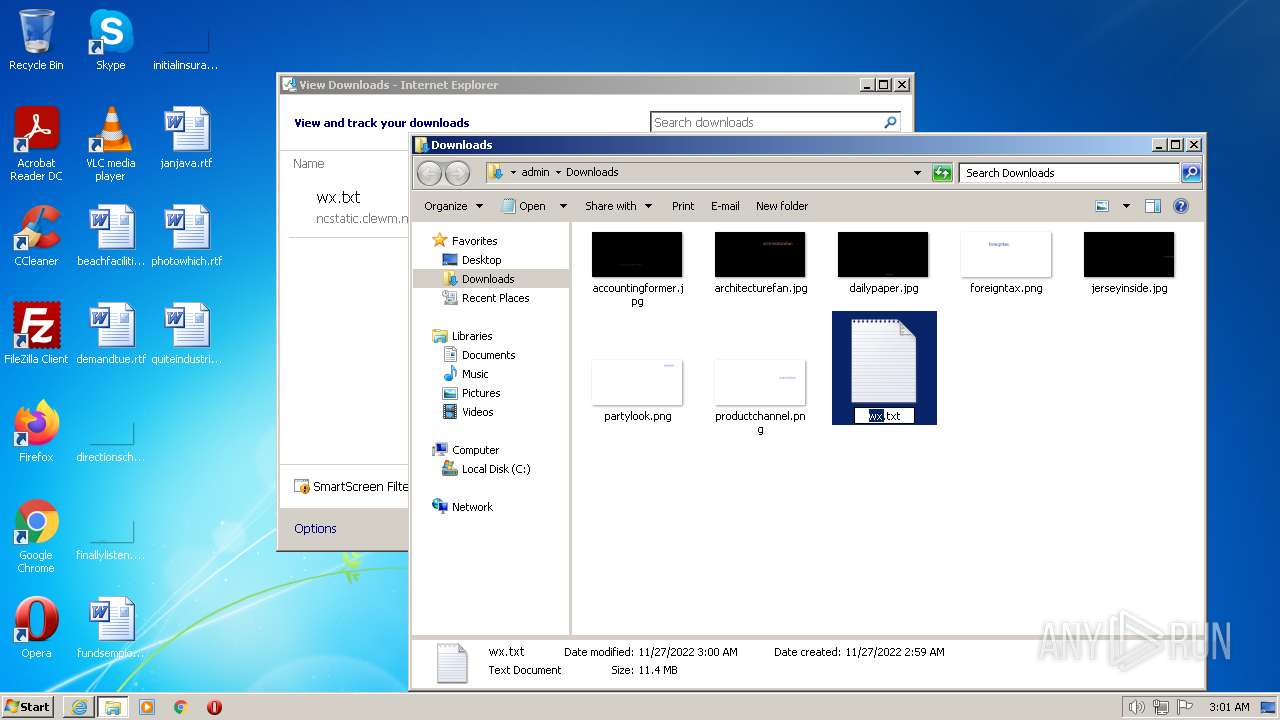
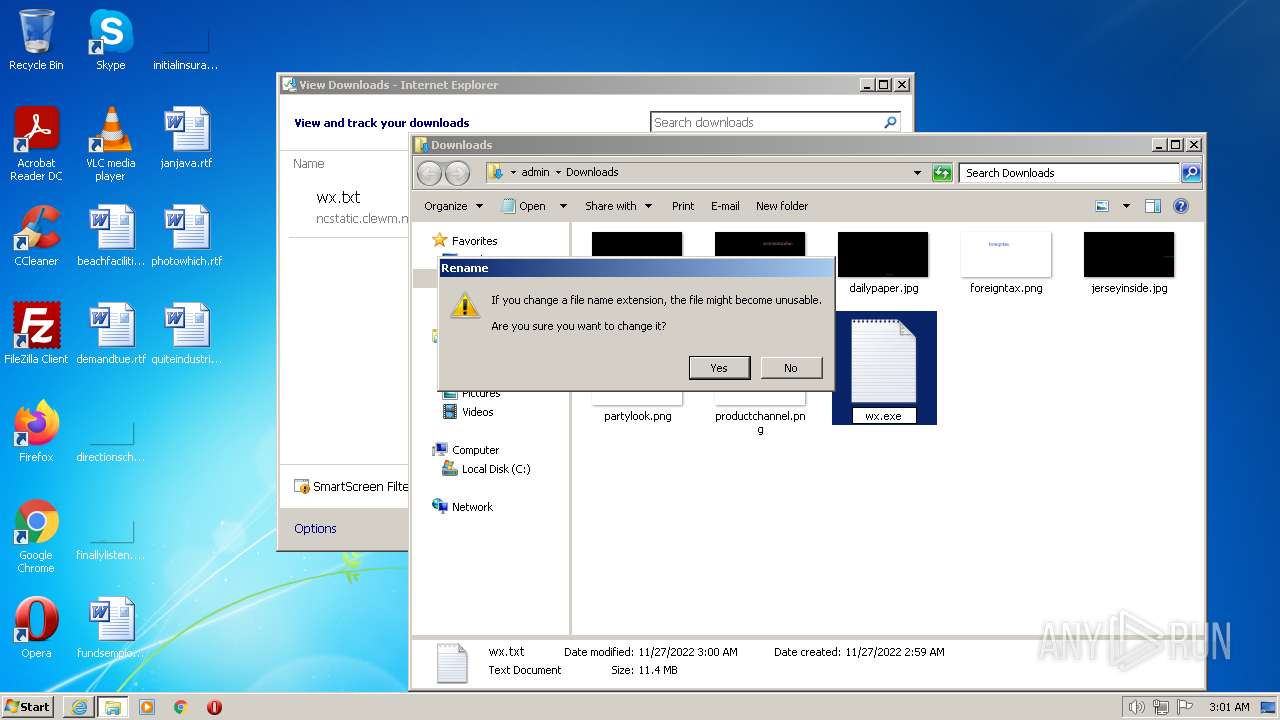
Application was dropped or rewritten from another process
- wx.exe (PID: 2208)
- wx.exe (PID: 3528)
- Runner.exe (PID: 280)
Drops the executable file immediately after the start
- wx.exe (PID: 3528)
- Runner.exe (PID: 280)
Loads dropped or rewritten executable
- Explorer.EXE (PID: 1084)
- Runner.exe (PID: 280)
- taskmgr.exe (PID: 2520)
SUSPICIOUS
Executable content was dropped or overwritten
- wx.exe (PID: 3528)
- Runner.exe (PID: 280)
INFO
Application launched itself
- iexplore.exe (PID: 736)
Drops the executable file immediately after the start
- Explorer.EXE (PID: 1084)
- iexplore.exe (PID: 736)
- iexplore.exe (PID: 2972)
Executable content was dropped or overwritten
- iexplore.exe (PID: 736)
- iexplore.exe (PID: 2972)
Drops a file that was compiled in debug mode
- wx.exe (PID: 3528)
- Runner.exe (PID: 280)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
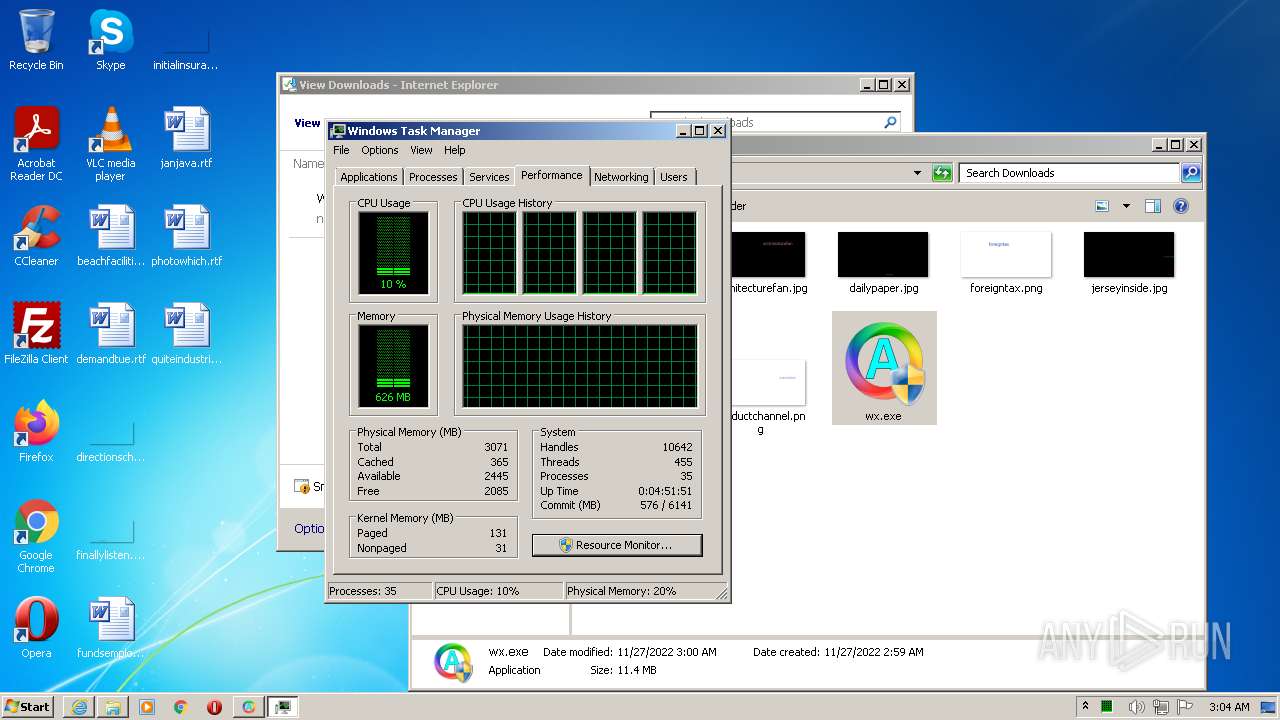
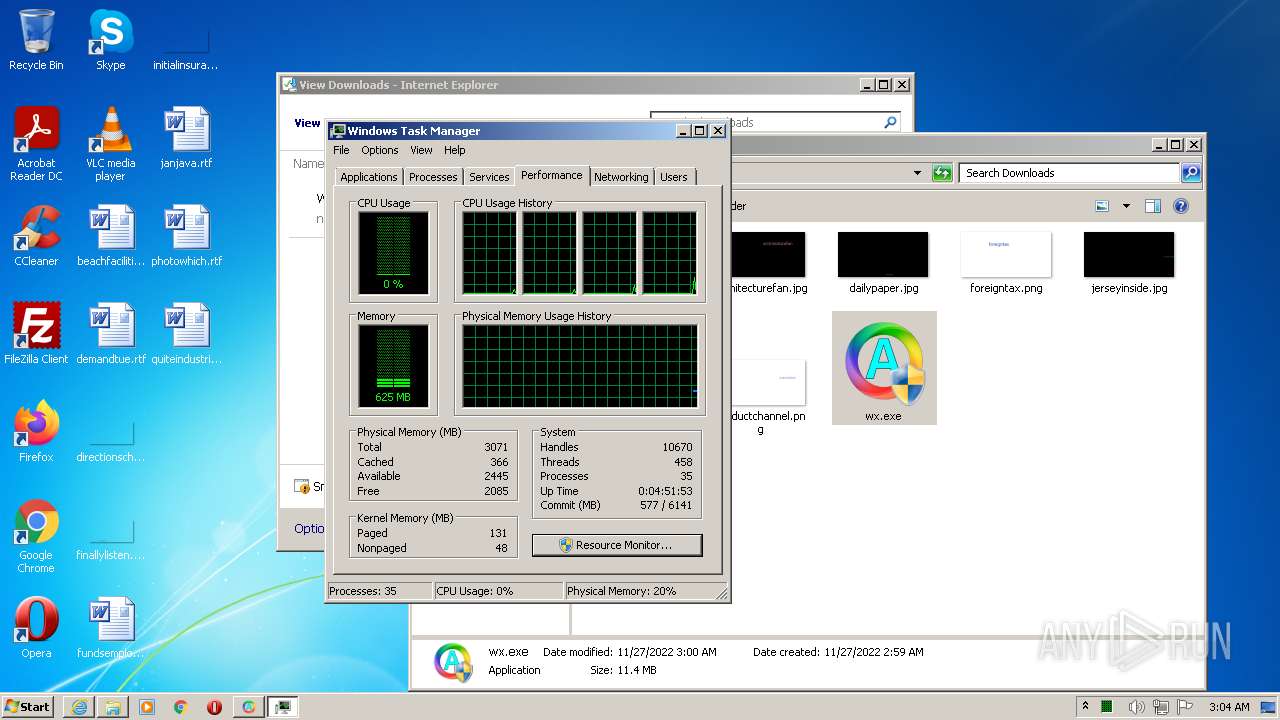
Total processes
54
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
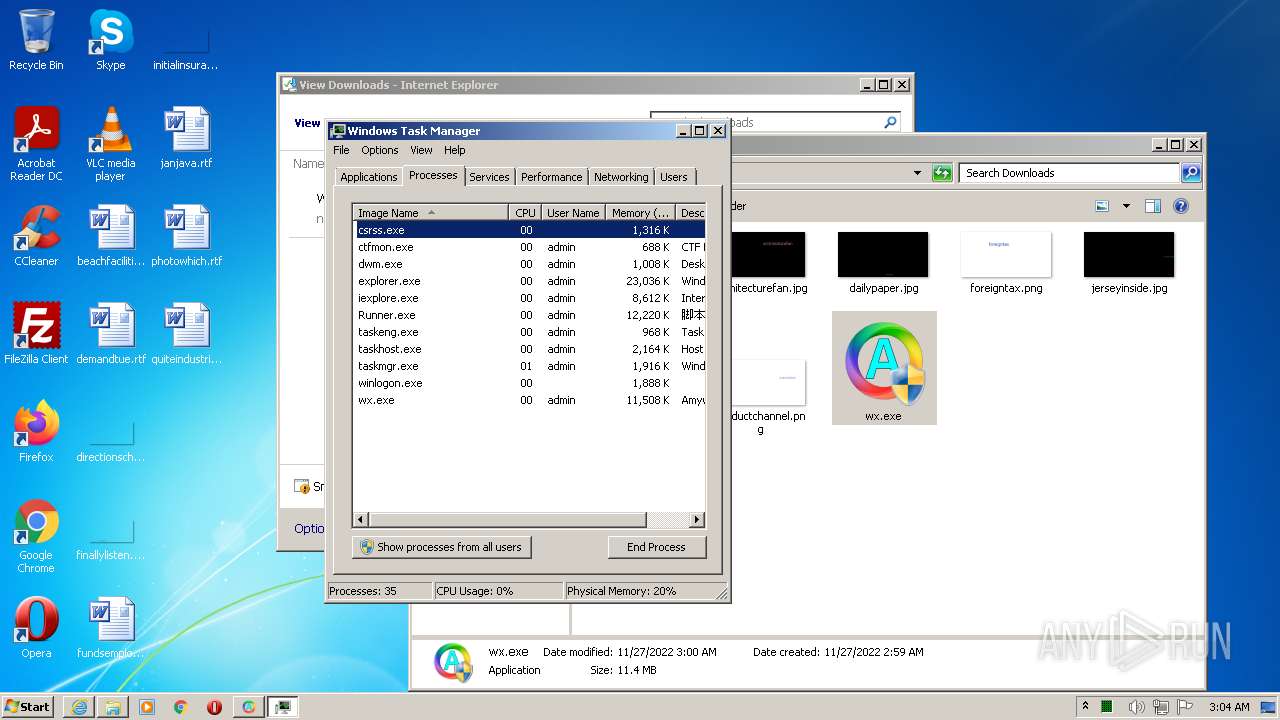
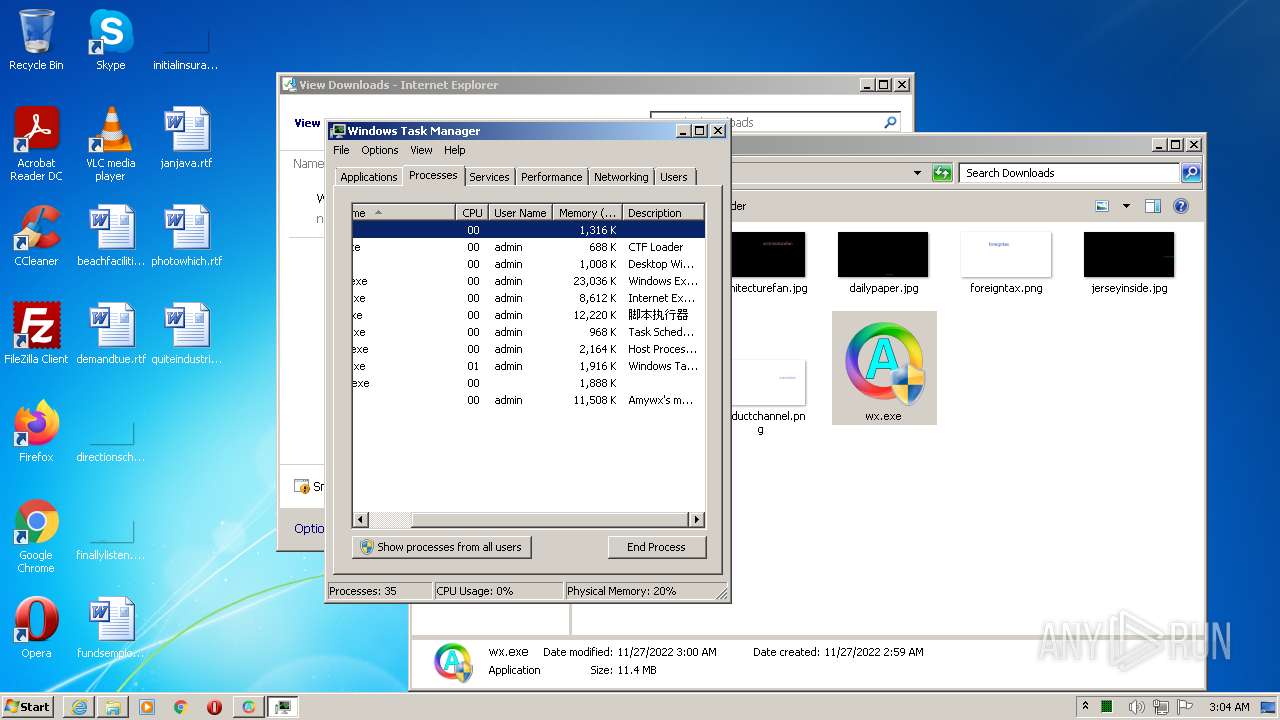
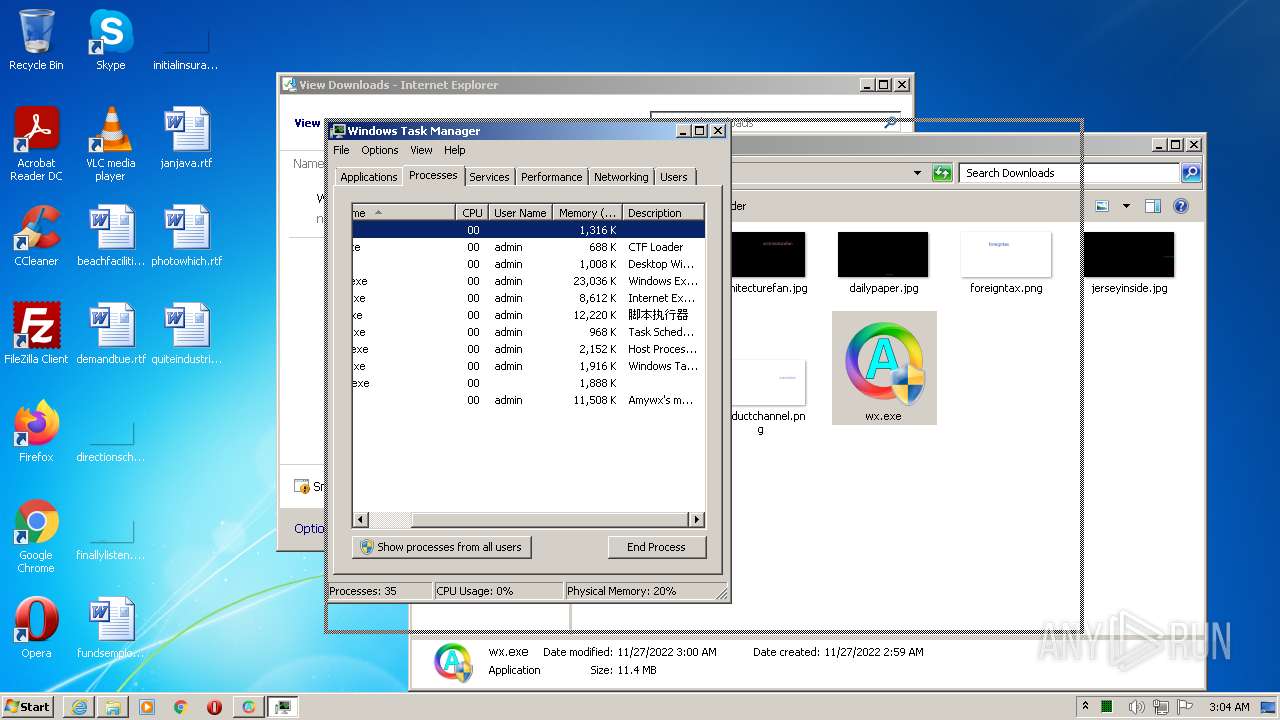
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Windows\System32\PING.EXE" www.baidu.com -n 2 | C:\Windows\System32\PING.EXE | — | wx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 280 | --host_id 5 --verify_key pTvc6amlB1Ur --product "C:\Users\admin\Downloads\wx.exe" --version 2014.05.145683 | C:\Users\admin\AppData\Roaming\MyMacro\Runner.exe | wx.exe | ||||||||||||
User: admin Company: 福建创意嘉和软件有限公司(C)2001-2016 Integrity Level: HIGH Description: 脚本执行器 Exit code: 0 Version: 1.0.0.17762 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ncstatic.clewm.net/rsrc/2022/1122/09/001020e0415284caf16ac9a9375069fd.txt" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1084 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
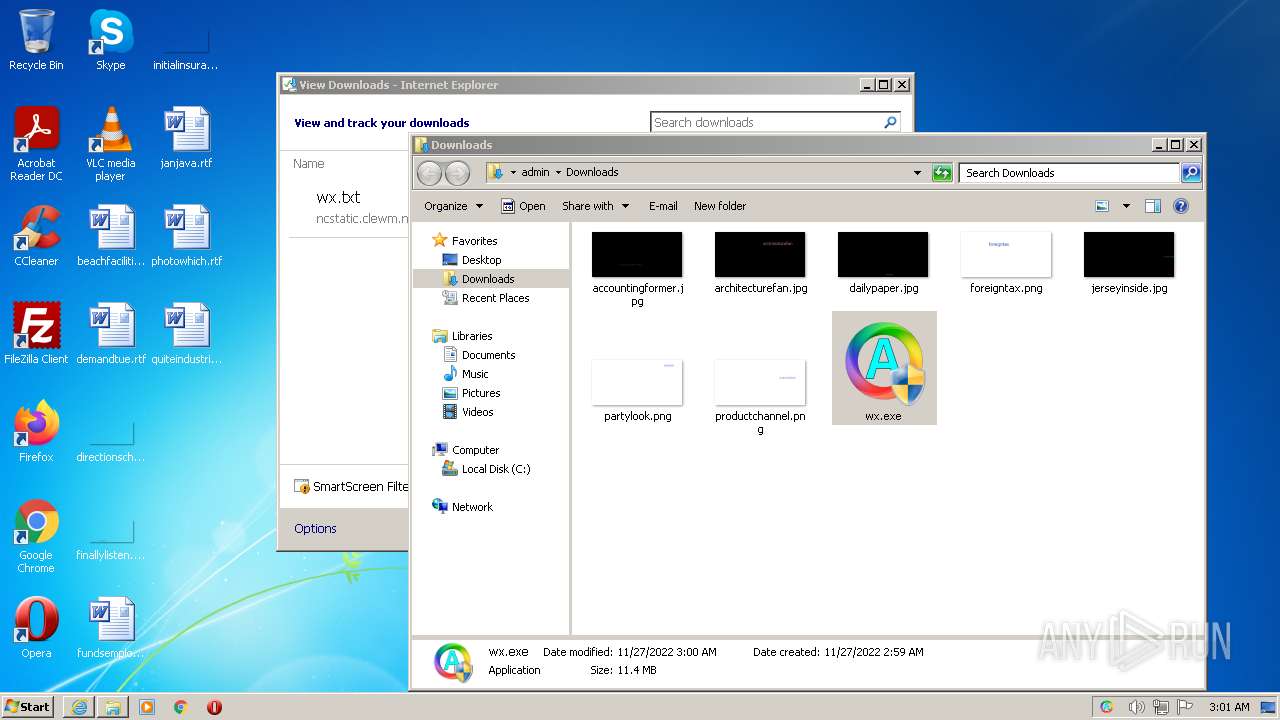
| 2208 | "C:\Users\admin\Downloads\wx.exe" | C:\Users\admin\Downloads\wx.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Amywx Corporation Integrity Level: MEDIUM Description: Amywx's macro runner. Exit code: 3221226540 Version: 2022.0.5.145683 Modules
| |||||||||||||||
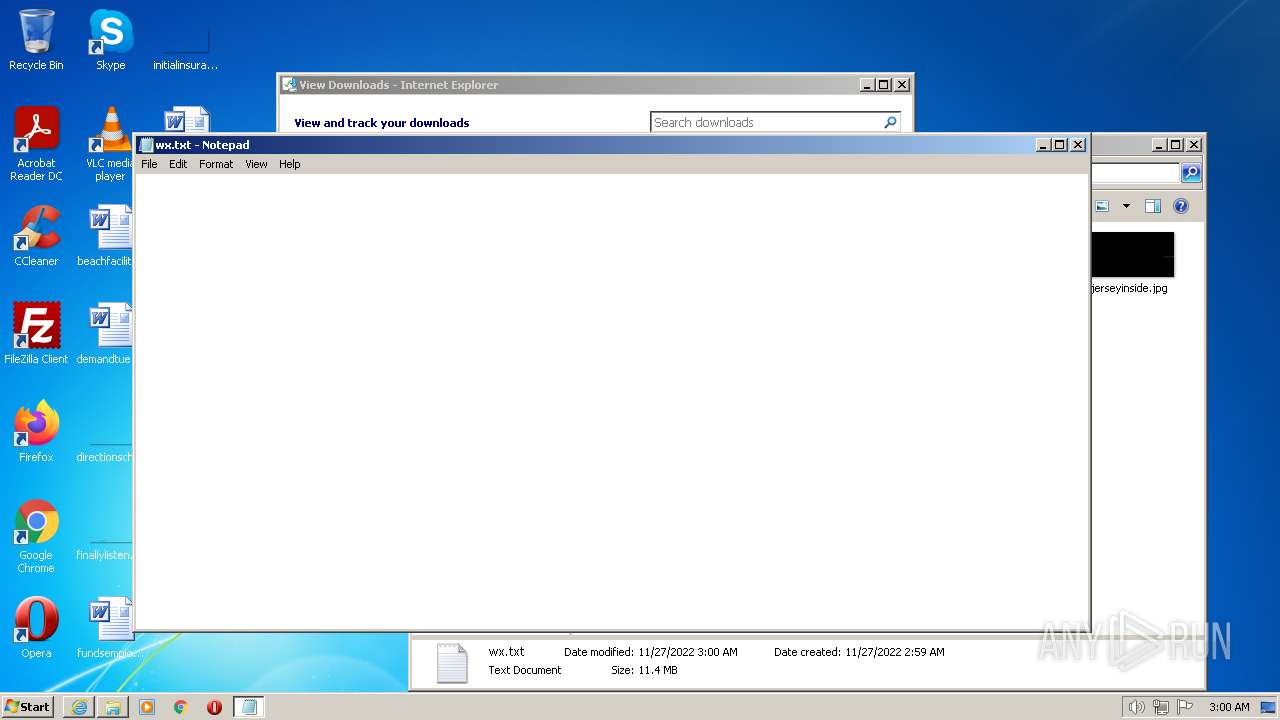
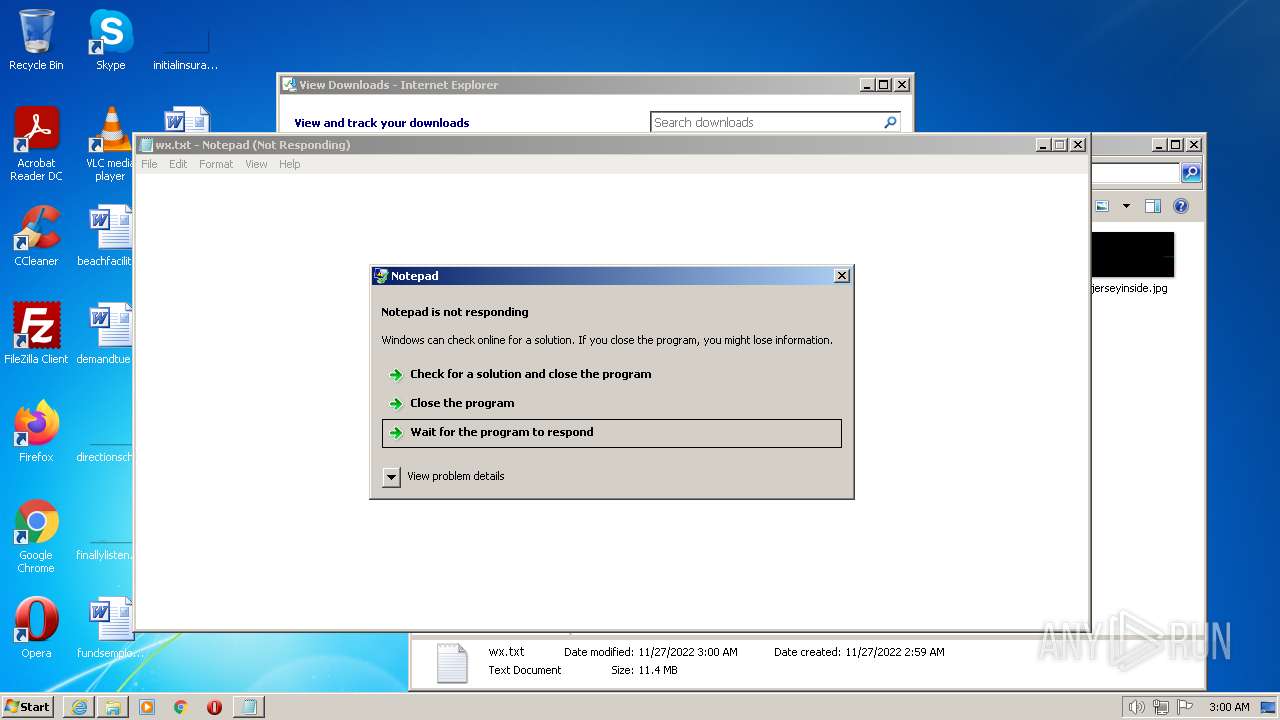
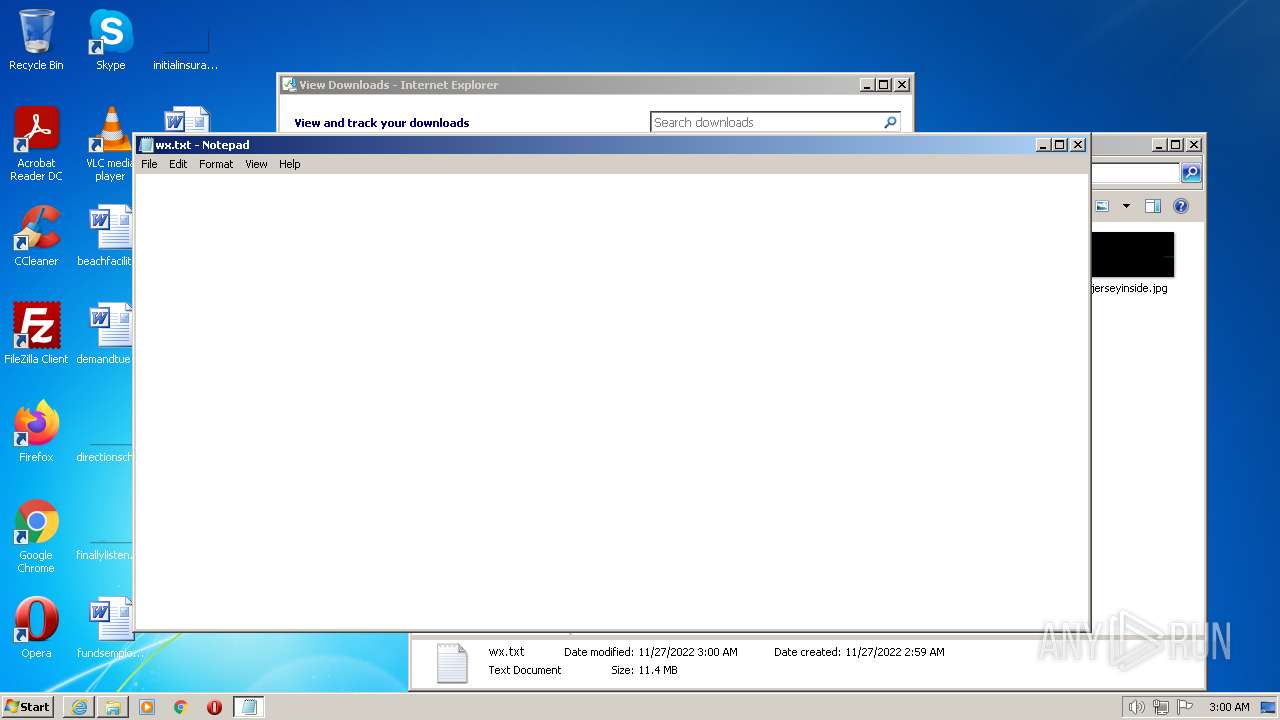
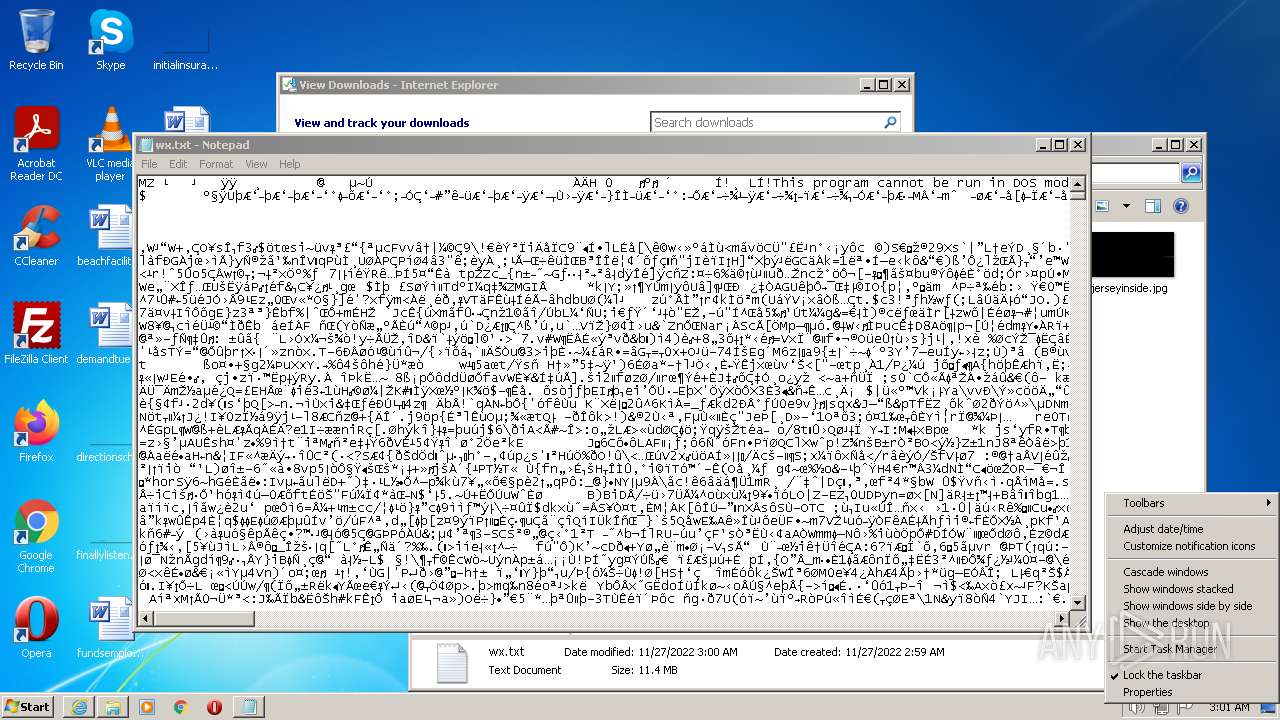
| 2304 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\wx.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
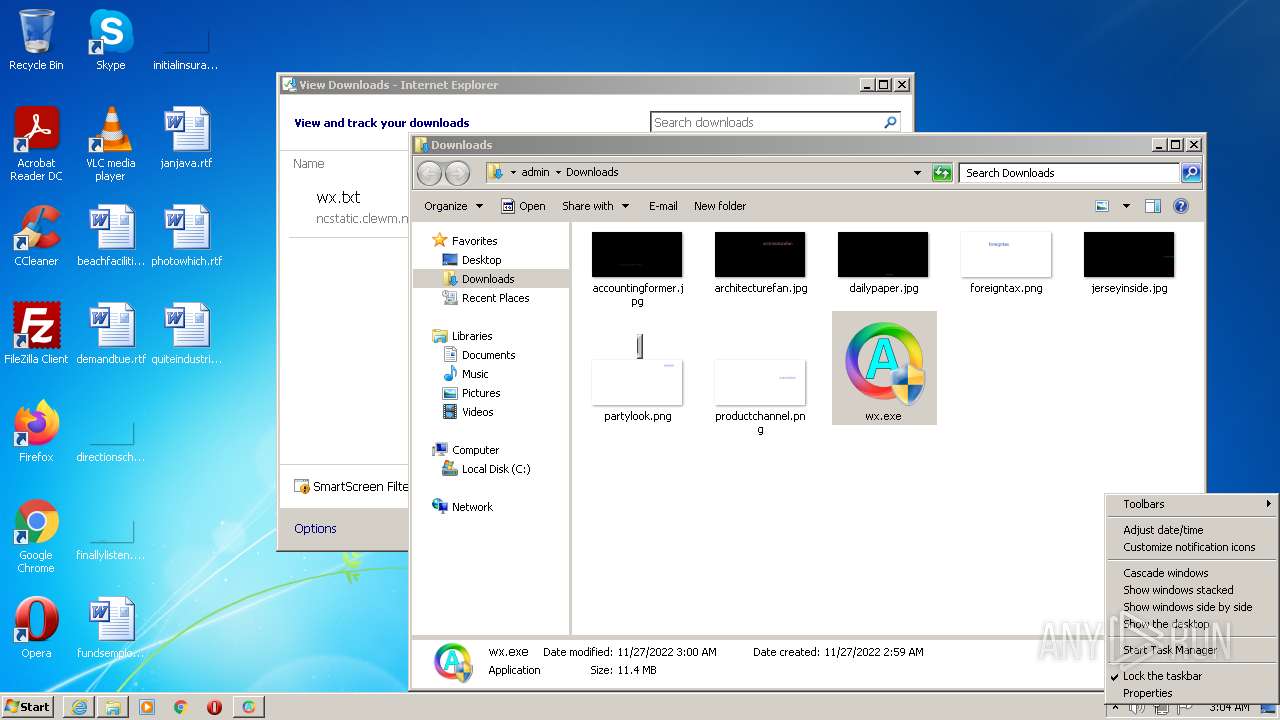
| 2520 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:736 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3520 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\wx.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 3489660927 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3528 | "C:\Users\admin\Downloads\wx.exe" | C:\Users\admin\Downloads\wx.exe | Explorer.EXE | ||||||||||||
User: admin Company: Amywx Corporation Integrity Level: HIGH Description: Amywx's macro runner. Exit code: 0 Version: 2022.0.5.145683 Modules
| |||||||||||||||
Total events
20 486
Read events
20 096
Write events
385
Delete events
5
Modification events
| (PID) Process: | (736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30999052 | |||
| (PID) Process: | (736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30999052 | |||
| (PID) Process: | (736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
18
Suspicious files
22
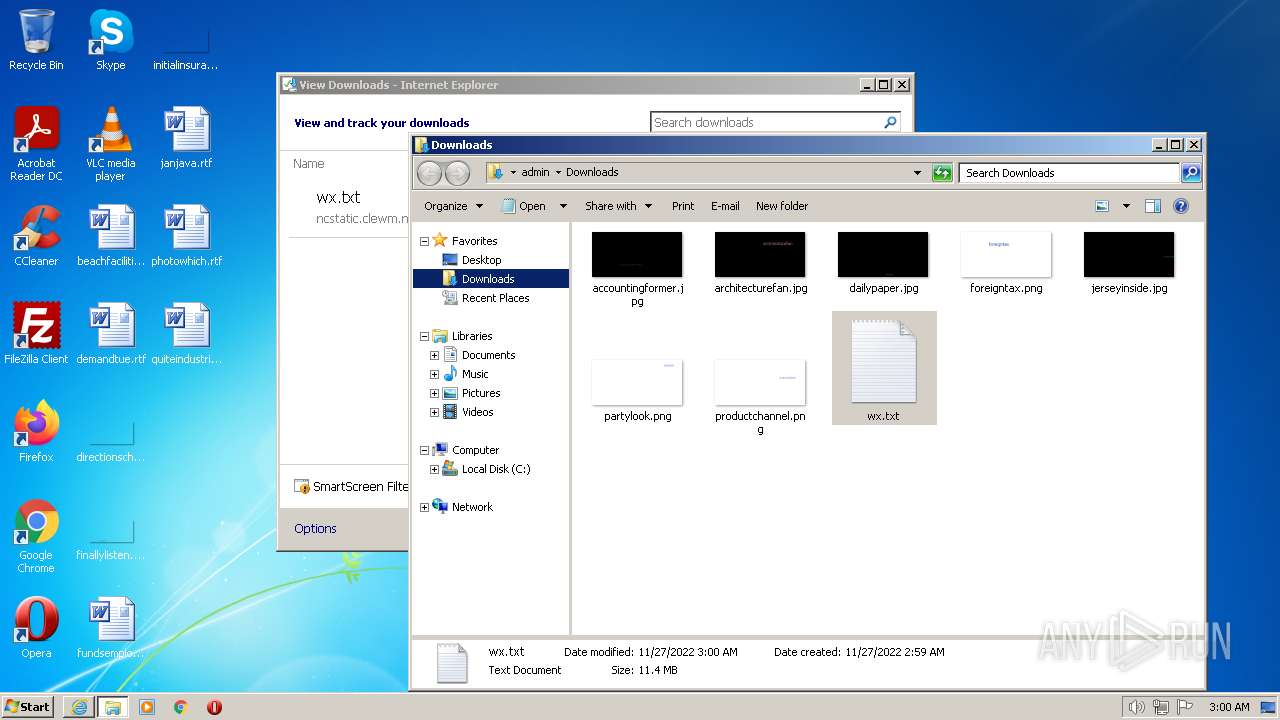
Text files
18
Unknown types
12
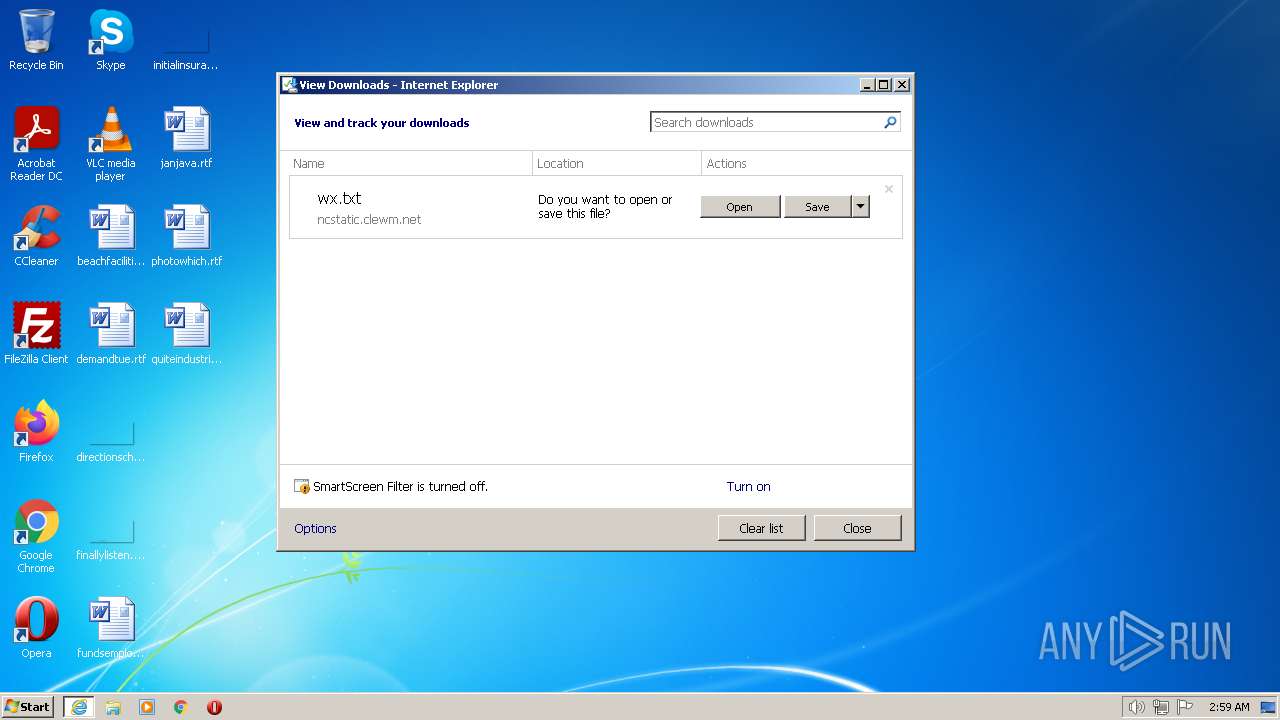
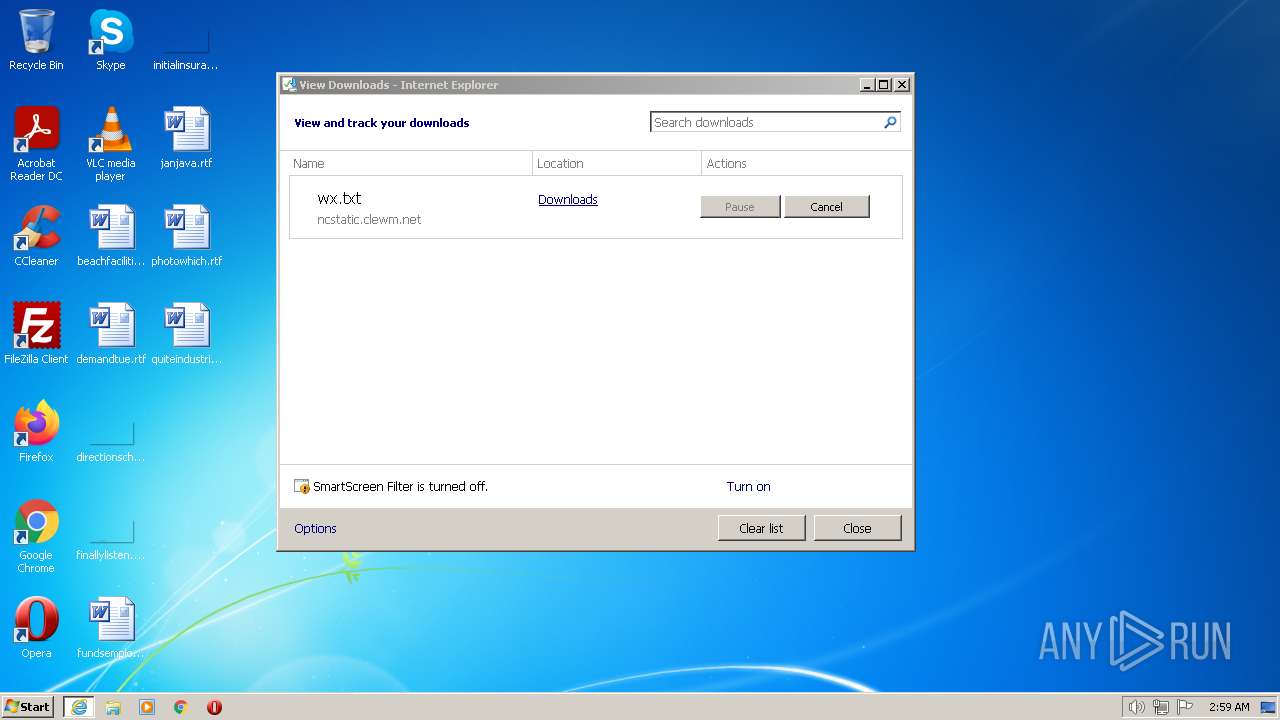
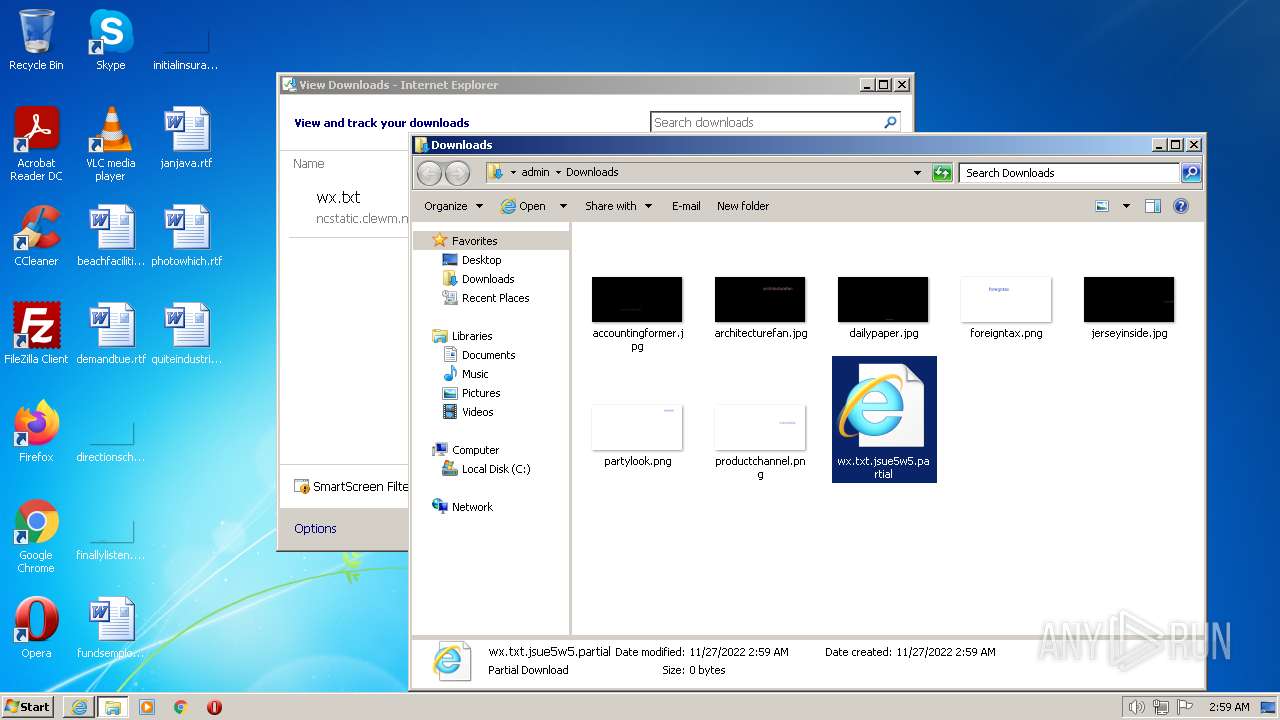
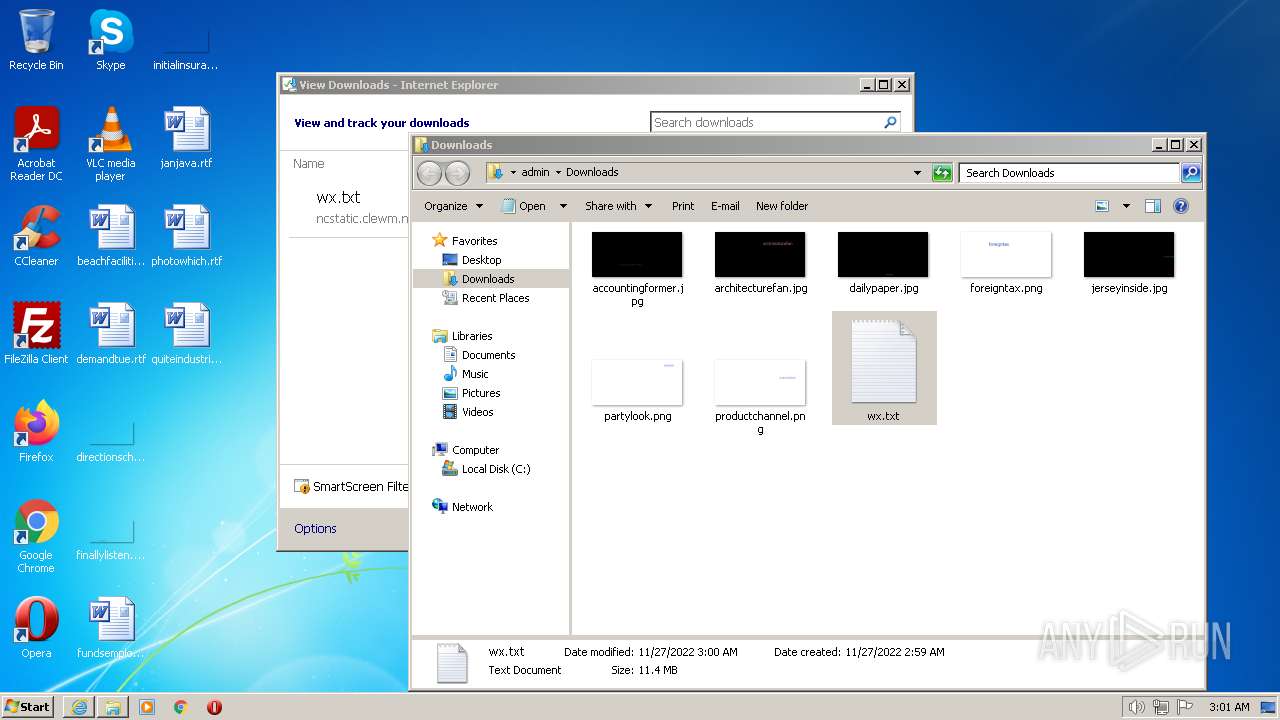
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\wx[1].txt | executable | |
MD5:— | SHA256:— | |||
| 736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF6DDB4653B7CEA9C.TMP | gmc | |
MD5:— | SHA256:— | |||
| 736 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{8375ACF1-6DFF-11ED-80DA-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_23FFFDCAABB8E63694AD1202ED02BF57 | binary | |
MD5:— | SHA256:— | |||
| 736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 1084 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\wx.txt.lnk | lnk | |
MD5:— | SHA256:— | |||
| 736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 1084 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
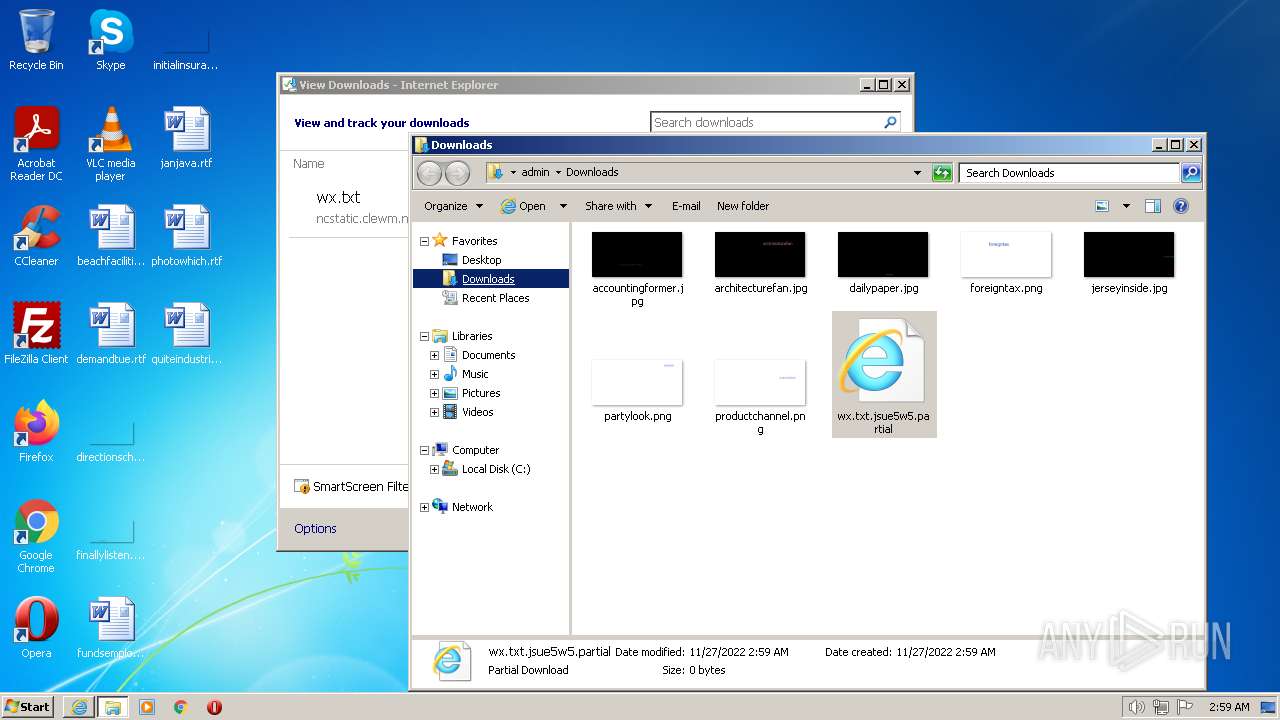
| 2972 | iexplore.exe | C:\Users\admin\Downloads\wx.txt.jsue5w5.partial | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
27
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2972 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAoFmyX1Sz2HlMxmMUd1OKM%3D | US | der | 471 b | whitelisted |
736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2972 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6a8ce60a7665fd4c | US | compressed | 4.70 Kb | whitelisted |
736 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0e34ce5e7d1cc833 | US | compressed | 4.70 Kb | whitelisted |
736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2972 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQlOydjtpho0%2Bholo77zGjGxETUEQQU8JyF%2FaKffY%2FJaLvV1IlNHb7TkP8CEAuqfparO2SQW2NTzAIqo4U%3D | US | der | 727 b | whitelisted |
736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3528 | wx.exe | POST | 200 | 117.27.139.140:80 | http://soft.xiaojl.com/api/SubmitUsageInfor | CN | binary | 144 b | malicious |
736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
736 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
2972 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
736 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
736 | iexplore.exe | 96.16.143.41:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
736 | iexplore.exe | 204.79.197.203:443 | www.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | malicious |
2972 | iexplore.exe | 79.133.177.211:443 | — | Zhejiang Taobao Network Co.,Ltd | RU | unknown |
736 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
736 | iexplore.exe | 20.25.53.147:443 | query.prod.cms.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3528 | wx.exe | 117.27.139.140:80 | soft.xiaojl.com | Fuzhou | CN | malicious |
2972 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| shared |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
wx.exe | g_szDataPath: C:\Users\admin\AppData\Roaming\MyMacro\RKey.dat
|
wx.exe | g_hEventFlag: 248, g_hEvent_CodeInfo: 250
|
wx.exe | g_pCodeFlag: ad0000, g_pCodeInfo: ae0000
|