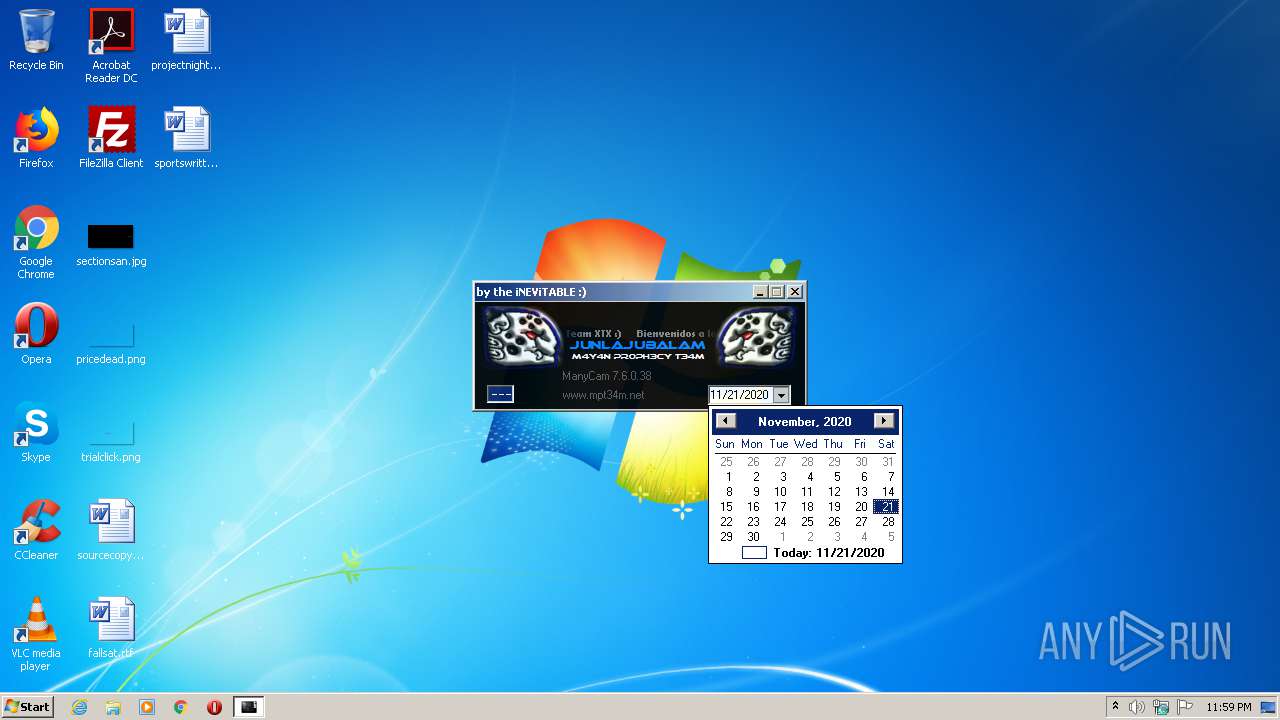
| File name: | manycam.7.6.0.38-MPT.exe |
| Full analysis: | https://app.any.run/tasks/be64c2c1-1c3b-4353-b07a-95eed8bd5bfd |
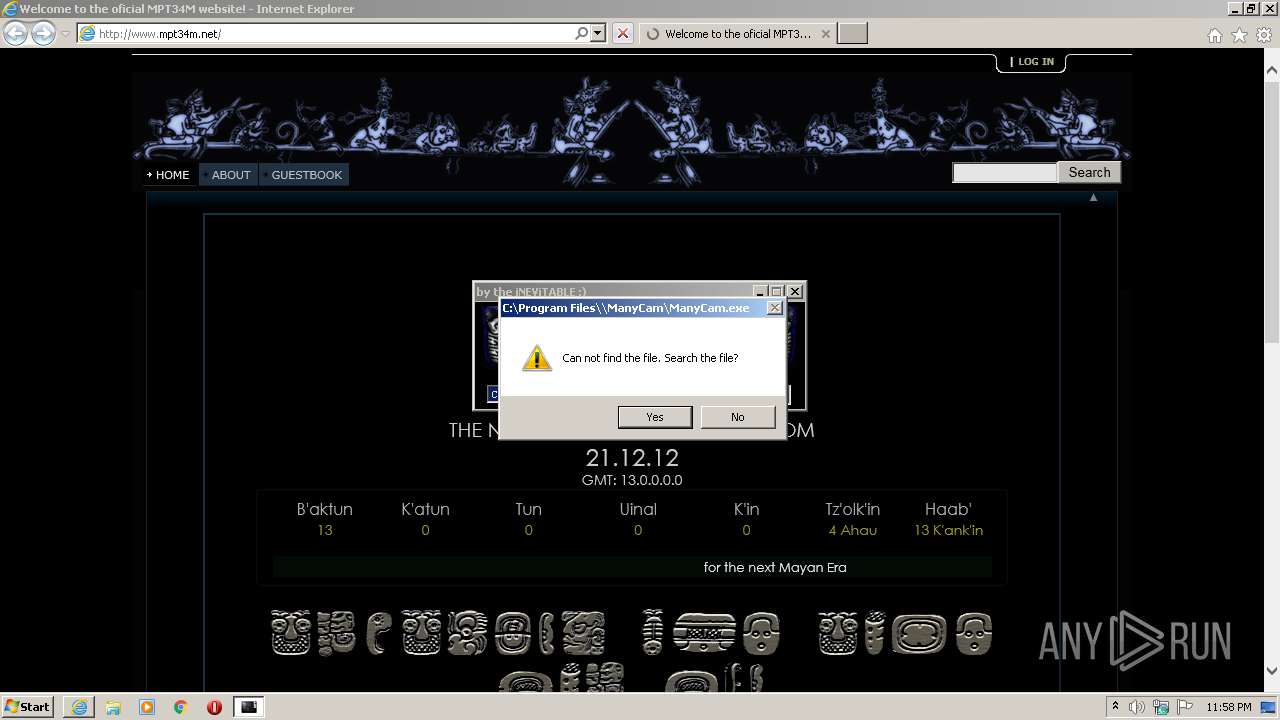
| Verdict: | Malicious activity |
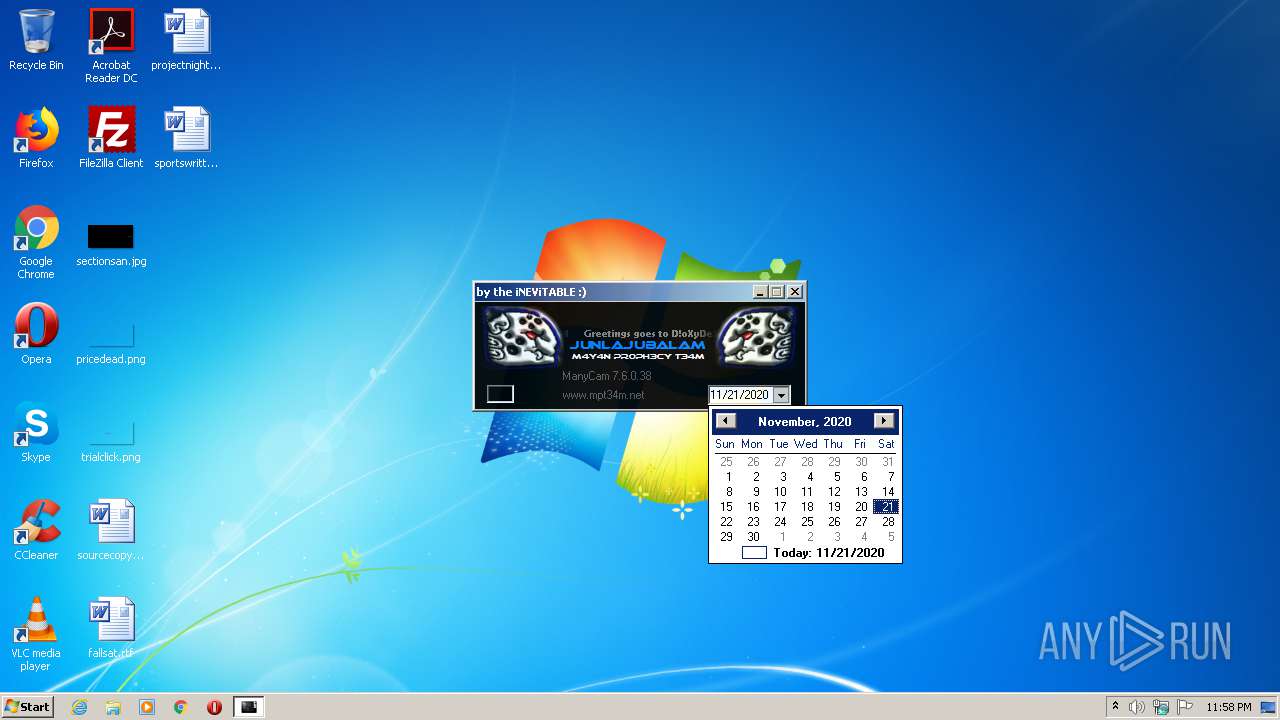
| Analysis date: | November 21, 2020, 23:58:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 99BC00543DD33142549458775FC146A8 |
| SHA1: | 757F6569D16699FDB1F1597D6BAC245FE2F88D27 |
| SHA256: | 3BACBAF79D434A128D3A32792AB8F87AAA4854DACB89F475D4DEC0F3ADDBD33C |
| SSDEEP: | 6144:fodJmiTnPc8G9S7KkzadJeXeD67fOrkz:fPenPcFS2j0eDSOrW |
MALICIOUS
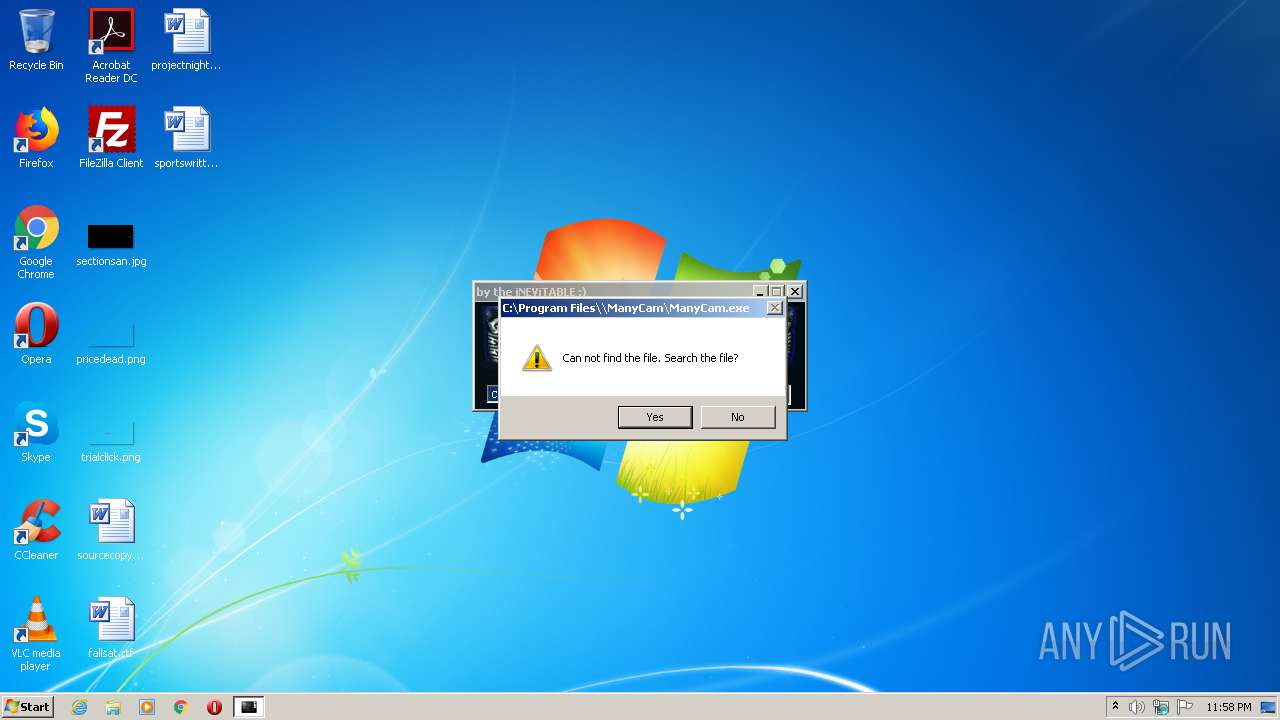
Drops executable file immediately after starts
- manycam.7.6.0.38-MPT.exe (PID: 2884)
SUSPICIOUS
Executable content was dropped or overwritten
- manycam.7.6.0.38-MPT.exe (PID: 2884)
Drops a file with too old compile date
- manycam.7.6.0.38-MPT.exe (PID: 2884)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:21 21:59:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 512 |
| InitializedDataSize: | 232960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x102b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2012 20:59:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2012 20:59:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x0003879C | 0x00038800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.84489 |
.reloc | 0x0003D000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85663 | 898 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.34777 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.08777 | 488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.65367 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.72922 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 6.11731 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 6.09324 | 1736 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 4.62248 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 4.86341 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 4.93104 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
kernel32.dll |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
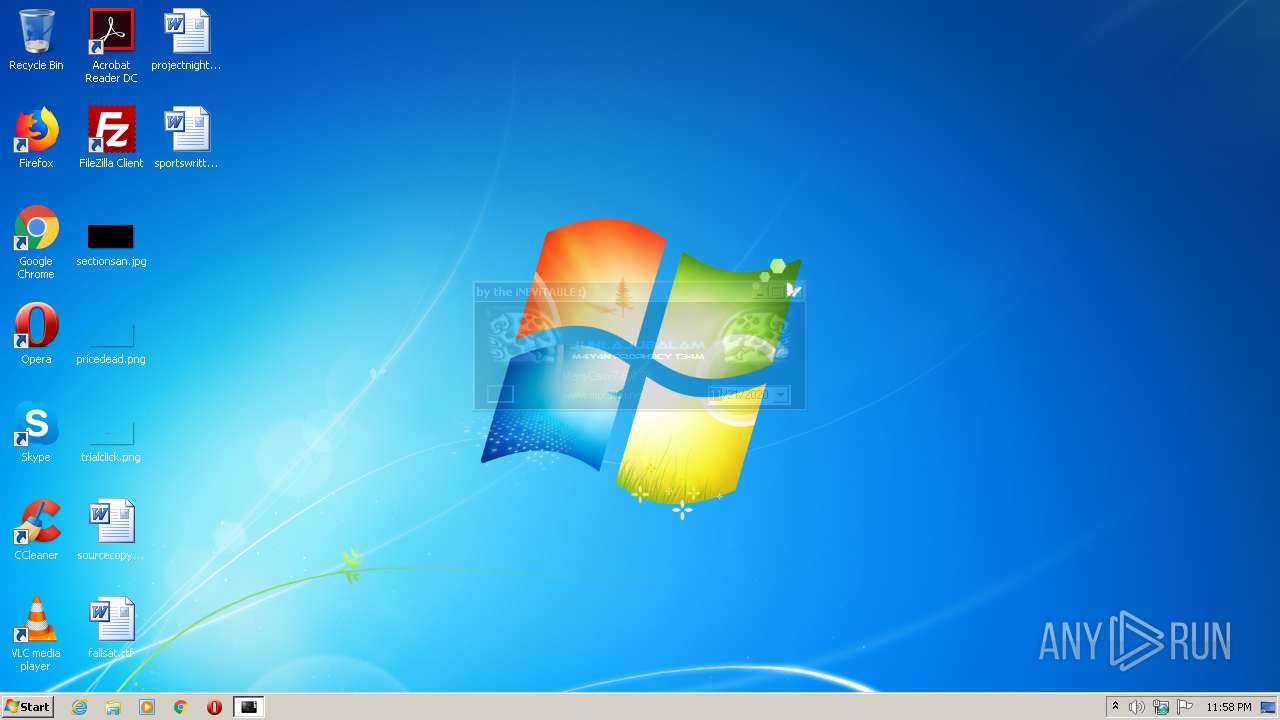
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
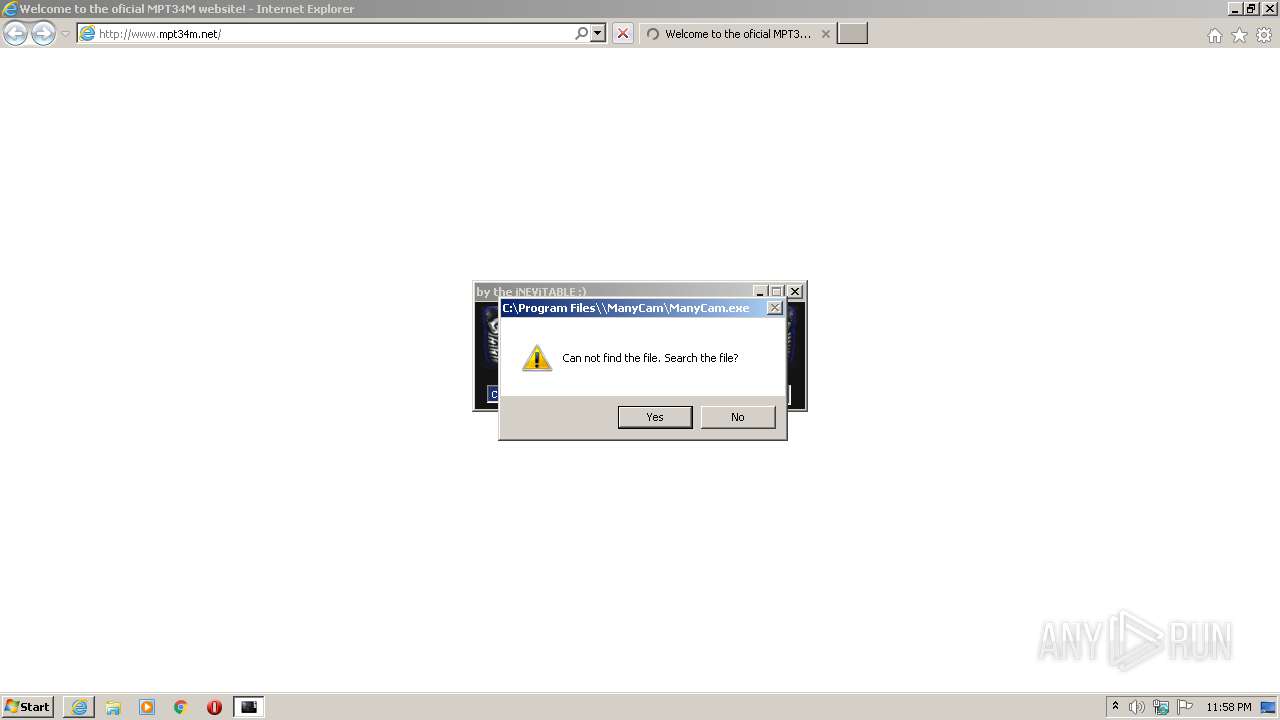
| 2080 | "C:\Users\admin\AppData\Local\Temp\manycam.7.6.0.38-MPT.exe" | C:\Users\admin\AppData\Local\Temp\manycam.7.6.0.38-MPT.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2884 | "C:\Users\admin\AppData\Local\Temp\manycam.7.6.0.38-MPT.exe" | C:\Users\admin\AppData\Local\Temp\manycam.7.6.0.38-MPT.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
11
Read events
11
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | manycam.7.6.0.38-MPT.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | — | |
MD5:— | SHA256:— | |||
| 2884 | manycam.7.6.0.38-MPT.exe | C:\Users\admin\AppData\Local\Temp\Berlin Sans FB.TTF | — | |
MD5:— | SHA256:— | |||
| 2884 | manycam.7.6.0.38-MPT.exe | C:\Users\admin\AppData\Local\Temp\bassmod.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
25
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
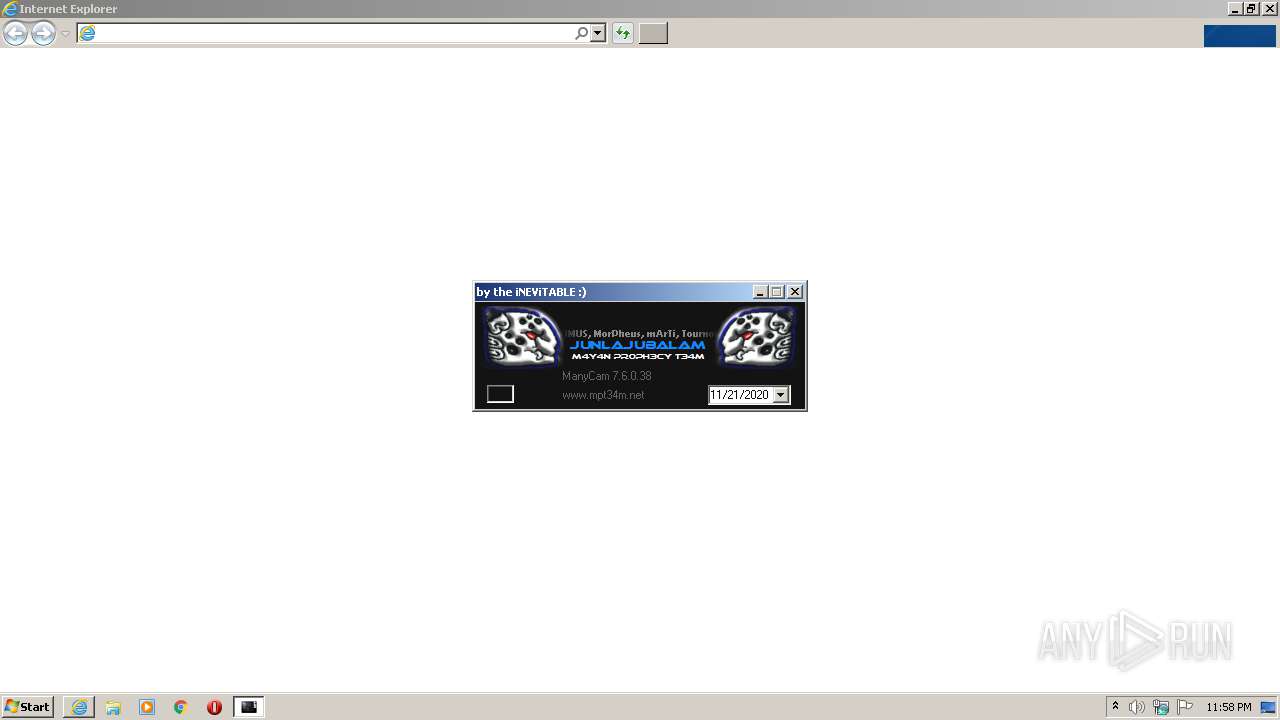
— | — | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/extdocs/rssReader.php?action=true&url=https://www.mpt34m.net/tutos%2Ephp%3Faction%3Drss&headeron=true&h=5&style=12&ima=true&datestyle=8&titleon=true&titlelink=true&dateon=true&twidth=500&df=&loc=EN&descon=true&descstyle=80&max=0&rows=1&e_h=&align=0&rand=true&rev=false&cnt=0&etarget=&tic_h=150&tic_id=rss_9&tic_d=3000&tic_c=4&tic_du=1000&tic_dir=0&novid=1&root=1&tic_nb=1&x=1&l=1 | NL | text | 9.09 Kb | malicious |
— | — | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/ | NL | html | 4.60 Kb | malicious |
— | — | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/images/zen_18_dropdown_v1_2_1.gif | NL | image | 238 b | malicious |
— | — | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/images/zen_18_dropdown_v1_2_4.gif | NL | image | 60 b | malicious |
— | — | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/2bmos.png | NL | image | 30.7 Kb | malicious |
— | — | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/innovaeditor/bootstrap/css/bootstrap.css | NL | text | 6.73 Kb | malicious |
— | — | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/13BAKOPT_midnight_mos.png | NL | image | 159 Kb | malicious |
— | — | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/bitcoin_383_920568_1.png | NL | image | 24.4 Kb | malicious |
— | — | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/images/zen_18_dropdown_v1_2_6.gif | NL | image | 60 b | malicious |
— | — | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/images/zen_18_dropdown_v1_2_8.gif | NL | image | 54 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.223.82.39:80 | www.mpt34m.net | Iws Networks LLC | NL | malicious |
— | — | 172.217.22.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
— | — | 209.197.3.15:80 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
— | — | 172.217.18.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
— | — | 31.13.92.14:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 31.13.92.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 31.13.92.14:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mpt34m.net |
| malicious |
ajax.googleapis.com |
| whitelisted |
netdna.bootstrapcdn.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
connect.facebook.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.facebook.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |