| File name: | pdfopia.msi |
| Full analysis: | https://app.any.run/tasks/f5081164-b4d1-4ef4-88b8-b944efcbe950 |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2024, 16:35:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
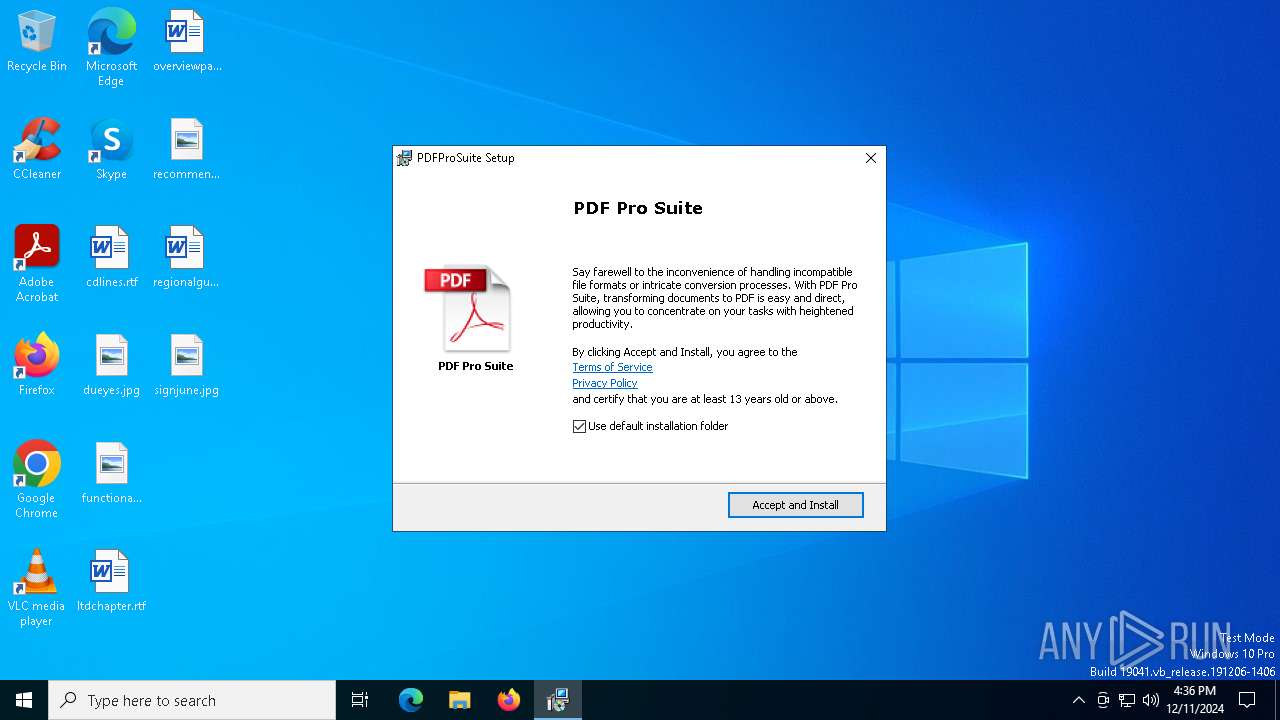
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {86CE85F2-67A7-41B0-96FD-EC844B999B20}, Number of Words: 10, Subject: PDFProSuite, Author: PDF Pro Suite, Name of Creating Application: PDFProSuite, Template: ;1033, Comments: This installer database contains the logic and data required to install PDFProSuite., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Wed Nov 20 01:21:37 2024, Last Saved Time/Date: Wed Nov 20 01:21:37 2024, Last Printed: Wed Nov 20 01:21:37 2024, Number of Pages: 450 |
| MD5: | 13C6C7DFD6B8A6AB0664B65222B82A09 |
| SHA1: | 7BE91F1F0F61EB434D15EB084413C0DBE5FD63E0 |
| SHA256: | 3BA6700C74D680312DC8062669D87F6C2417AD1355F47F93A87D8B60A3A601B0 |
| SSDEEP: | 98304:P9Ixo0SpkXkF8/t66f63RmG6lkaKKHtrlrpPAdOivuCle33GgJHs:pP |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks Windows Trust Settings
- msiexec.exe (PID: 6232)
- msiexec.exe (PID: 4816)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6232)
Executes as Windows Service
- VSSVC.exe (PID: 6968)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 4816)
- MSICBA9.tmp (PID: 1344)
Node.exe was dropped
- msiexec.exe (PID: 4816)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 6364)
INFO
Manages system restore points
- SrTasks.exe (PID: 5788)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6232)
- msiexec.exe (PID: 5208)
The sample compiled with english language support
- msiexec.exe (PID: 5208)
- msiexec.exe (PID: 6232)
- msiexec.exe (PID: 4816)
Reads the computer name
- msiexec.exe (PID: 6364)
- msiexec.exe (PID: 6232)
- msiexec.exe (PID: 4816)
Reads Environment values
- msiexec.exe (PID: 6364)
- msiexec.exe (PID: 4816)
Checks supported languages
- msiexec.exe (PID: 6232)
- msiexec.exe (PID: 4816)
- msiexec.exe (PID: 6364)
- MSICBA9.tmp (PID: 1344)
- pdfprosuite.exe (PID: 6516)
- pdfprosuite.exe (PID: 5916)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6232)
- msiexec.exe (PID: 4816)
Reads the software policy settings
- msiexec.exe (PID: 6232)
- msiexec.exe (PID: 5208)
- msiexec.exe (PID: 4816)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5208)
An automatically generated document
- msiexec.exe (PID: 5208)
Creates files or folders in the user directory
- msiexec.exe (PID: 5208)
Checks proxy server information
- msiexec.exe (PID: 4816)
Starts application with an unusual extension
- msiexec.exe (PID: 6232)
Manual execution by a user
- cmd.exe (PID: 1356)
- cmd.exe (PID: 3984)
Creates a software uninstall entry
- msiexec.exe (PID: 6232)
Process checks computer location settings
- MSICBA9.tmp (PID: 1344)
- msiexec.exe (PID: 6364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {86CE85F2-67A7-41B0-96FD-EC844B999B20} |
| Words: | 10 |
| Subject: | PDFProSuite |
| Author: | PDF Pro Suite |
| LastModifiedBy: | - |
| Software: | PDFProSuite |
| Template: | ;1033 |
| Comments: | This installer database contains the logic and data required to install PDFProSuite. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:11:20 01:21:37 |
| ModifyDate: | 2024:11:20 01:21:37 |
| LastPrinted: | 2024:11:20 01:21:37 |
| Pages: | 450 |
Total processes
151
Monitored processes
20
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1344 | "C:\WINDOWS\Installer\MSICBA9.tmp" /DontWait /HideWindow /dir "C:\Users\admin\AppData\Local\PDFProSuite\" pdfprosuite.exe . --installer | C:\Windows\Installer\MSICBA9.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 0 Version: 21.9.0.0 Modules
| |||||||||||||||
| 1356 | "C:\WINDOWS\system32\cmd.exe" /c "start /min /d "C:\Users\admin\AppData\Local\PDFProSuite\" PDFProSuite ." | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | pdfprosuite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | pdfprosuite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3984 | "C:\WINDOWS\system32\cmd.exe" /c "start /min /d "C:\Users\admin\AppData\Local\PDFProSuite\" PDFProSuite ." | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4628 | "C:\Users\admin\AppData\Local\PDFProSuite\pdfprosuite.exe" . | C:\Users\admin\AppData\Local\PDFProSuite\pdfprosuite.exe | — | cmd.exe | |||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js JavaScript Runtime Exit code: 0 Version: 18.17.1 Modules
| |||||||||||||||
| 4816 | C:\Windows\syswow64\MsiExec.exe -Embedding 00302CE9D6E8AB163CC9B6C1A54D6035 | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4872 | "C:\Windows\SysWOW64\cmd.exe" /c | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4912 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 833
Read events
16 525
Write events
290
Delete events
18
Modification events
| (PID) Process: | (6232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000CC5E5CC8EA4BDB0158180000281B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000039C25EC8EA4BDB0158180000281B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000CD5A9AC8EA4BDB0158180000281B0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000CD5A9AC8EA4BDB0158180000281B0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000F4BD9CC8EA4BDB0158180000281B0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000A985A1C8EA4BDB0158180000281B0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000092A405C9EA4BDB0158180000281B0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009F0808C9EA4BDB0158180000901B0000E8030000010000000000000000000000AB13056A3EA6354B8EA041CD4B15BF9600000000000000000000000000000000 | |||
| (PID) Process: | (6968) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000779711C9EA4BDB01381B0000B01B0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
23
Suspicious files
58
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6232 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5208 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI578F.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
| 5208 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\357F04AD41BCF5FE18FCB69F60C6680F_54E4814457E6B88FC0E5C74B1F0335DA | der | |
MD5:257767E9AD20D58E588334EC3741C42D | SHA256:E7EC8A95C84F85AFA6A340829D94AD2B946B229CAF1D098ECB70BA483BE6B994 | |||
| 5208 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\357F04AD41BCF5FE18FCB69F60C6680F_54E4814457E6B88FC0E5C74B1F0335DA | binary | |
MD5:2E1C533A0E14F1AB0BDE22A2668B5A8A | SHA256:62B38963E31877F9DB3CA488429D709094347E8F0CF5D4543558F9D0065E6809 | |||
| 6232 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:10C8A74CF829590C51481F8A0AE3024A | SHA256:A21F66E6A4732754E72F2FD82873799E2BEDD0DD64867D91529AA1F9B84878FF | |||
| 6232 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{6a0513ab-a63e-4b35-8ea0-41cd4b15bf96}_OnDiskSnapshotProp | binary | |
MD5:10C8A74CF829590C51481F8A0AE3024A | SHA256:A21F66E6A4732754E72F2FD82873799E2BEDD0DD64867D91529AA1F9B84878FF | |||
| 6232 | msiexec.exe | C:\Windows\Installer\MSIA9D0.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
| 6232 | msiexec.exe | C:\Windows\Temp\~DF65935868322357AF.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 6232 | msiexec.exe | C:\Users\admin\AppData\Local\PDFProSuite\node_modules\bindings\package.json | binary | |
MD5:17005447DF8440E0E386849B8FA2B682 | SHA256:A87721FE406E1F1798FEF44D697B46EA1EFE346FDA118010334713346EE4207C | |||
| 5208 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI570F.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
39
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6924 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2624 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2624 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5208 | msiexec.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEQCBTkI%2BxI6x4NL94uMAHTSA | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5208 | msiexec.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDACP4PKUmHSg8coXrA%3D%3D | unknown | — | — | whitelisted |
6352 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4816 | msiexec.exe | GET | 200 | 18.66.145.213:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkzUBtJnwJkc3SmanzgxeYU%3D | unknown | — | — | unknown |
4816 | msiexec.exe | GET | 200 | 52.222.229.217:80 | http://ocsp.r2m03.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQqHI%2BsdmapawQncL1rpCEZZ8gTSAQUVdkYX9IczAHhWLS%2Bq9lVQgHXLgICEA%2BjuCOT1x259UHHR62v01I%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2624 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2624 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5208 | msiexec.exe | 151.101.2.133:80 | ocsp.globalsign.com | FASTLY | US | whitelisted |
5064 | SearchApp.exe | 104.126.37.185:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |